analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
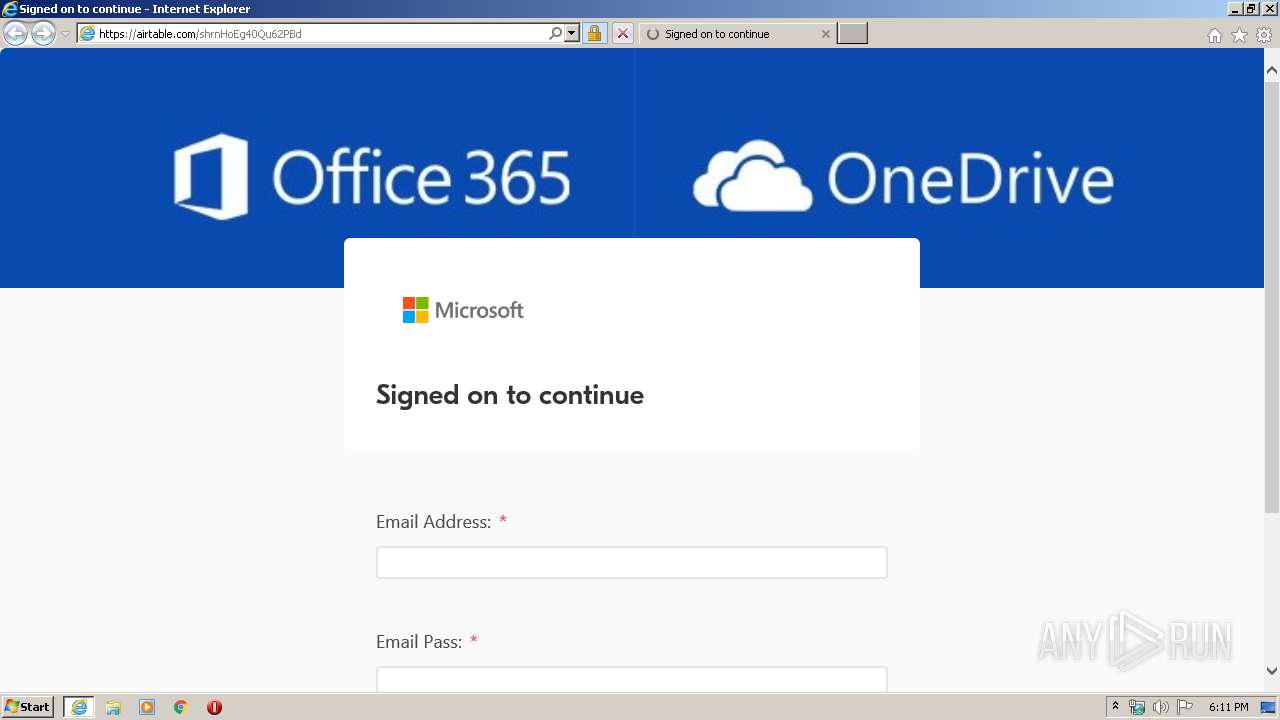
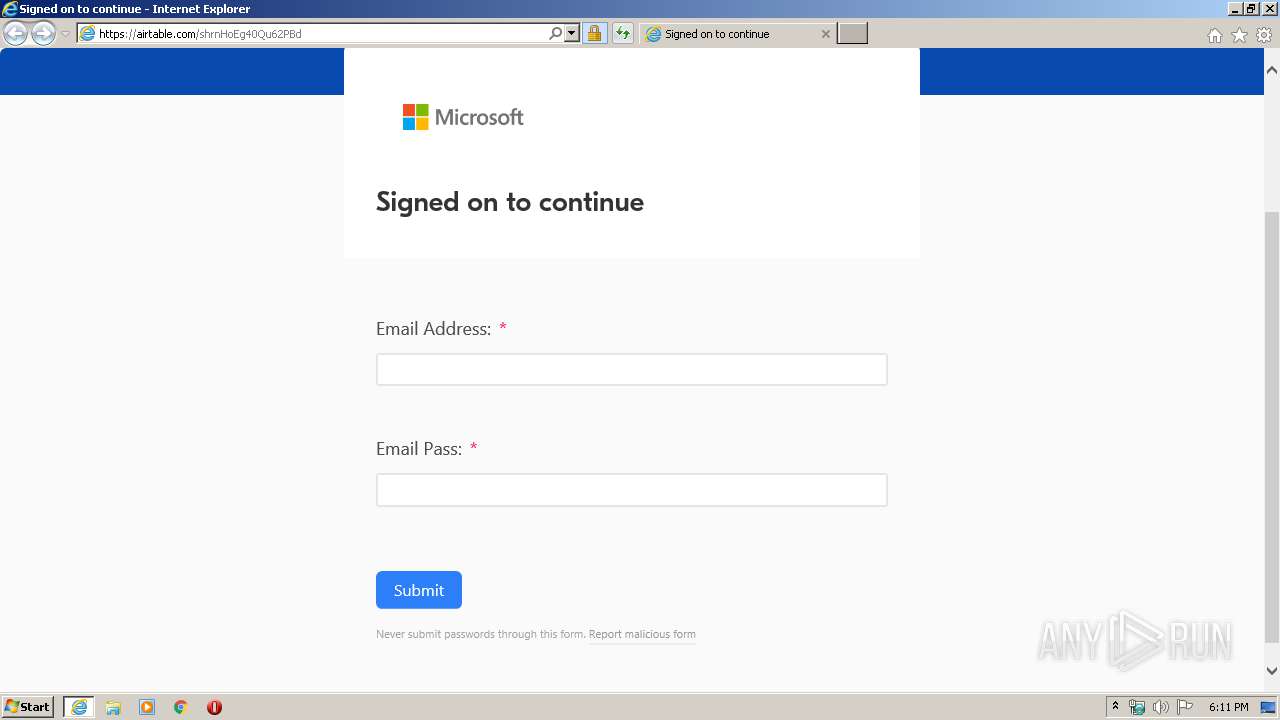
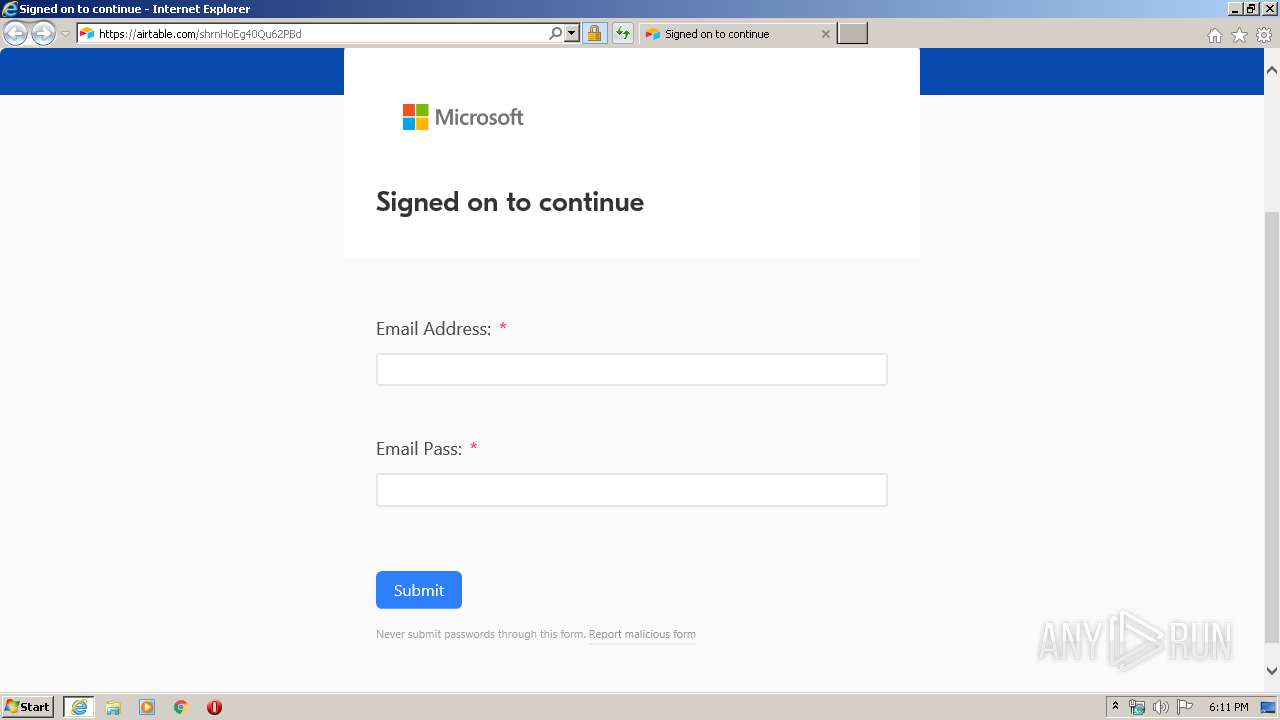
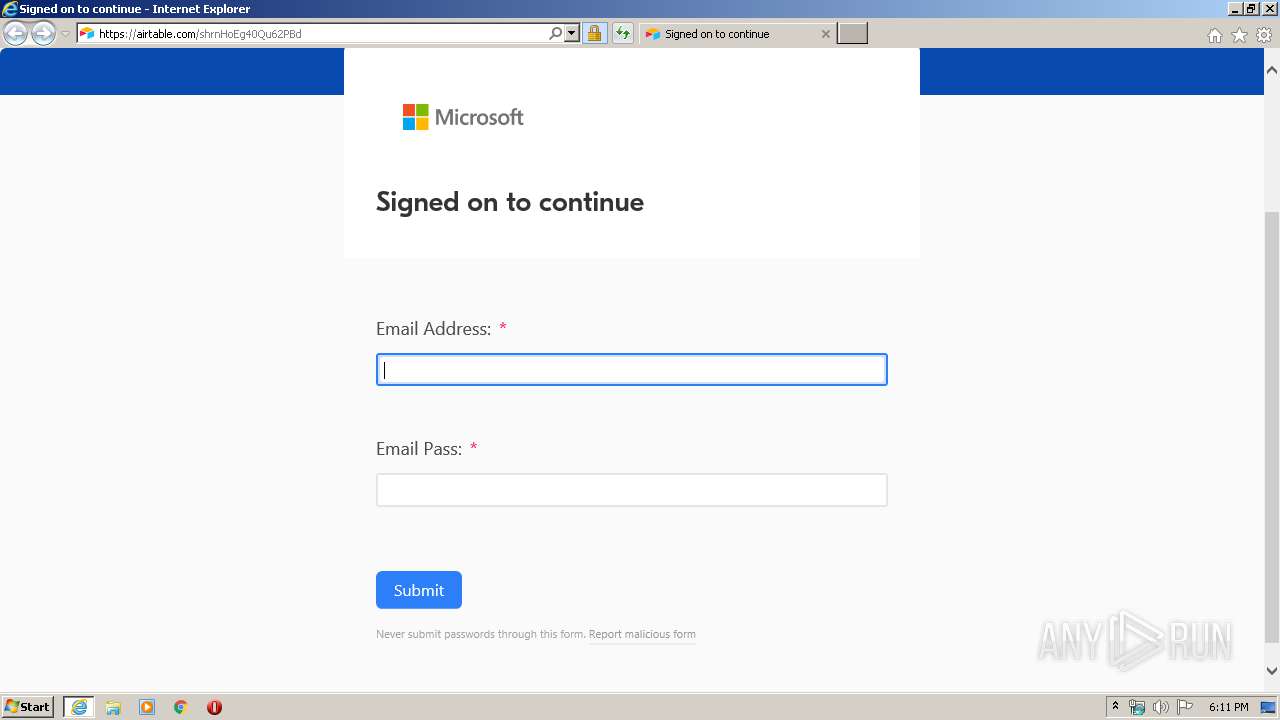
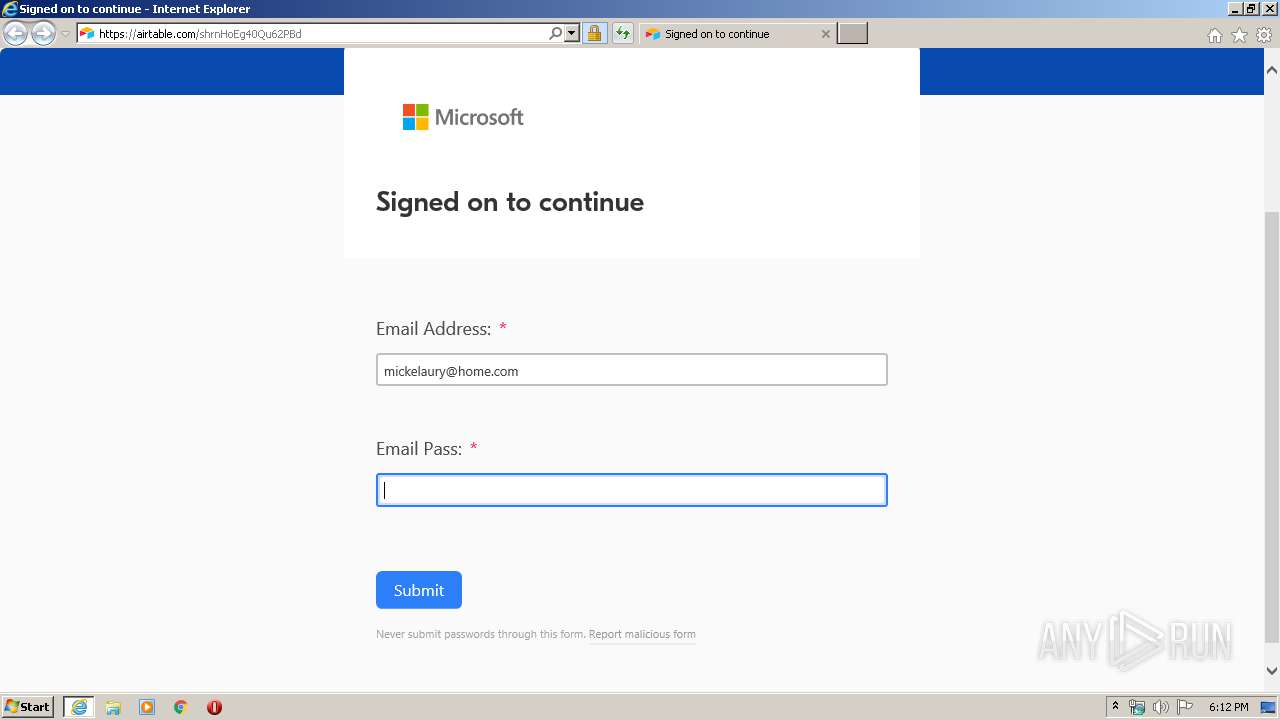
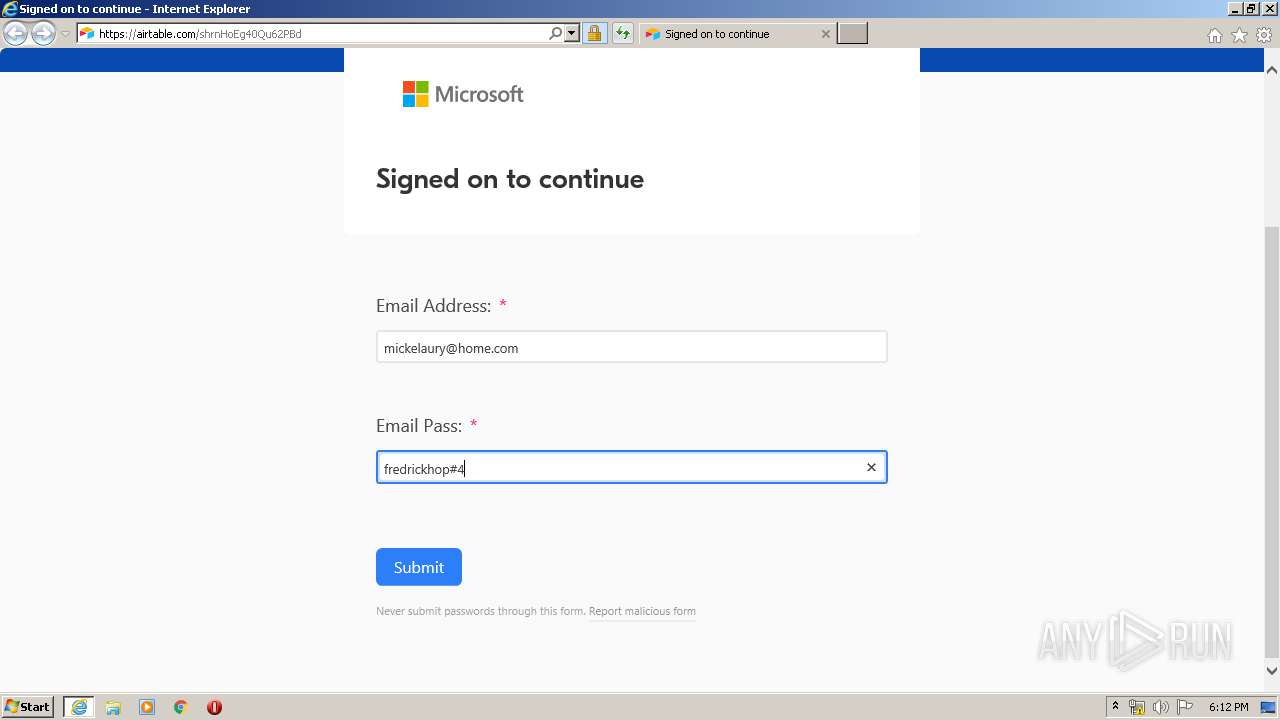
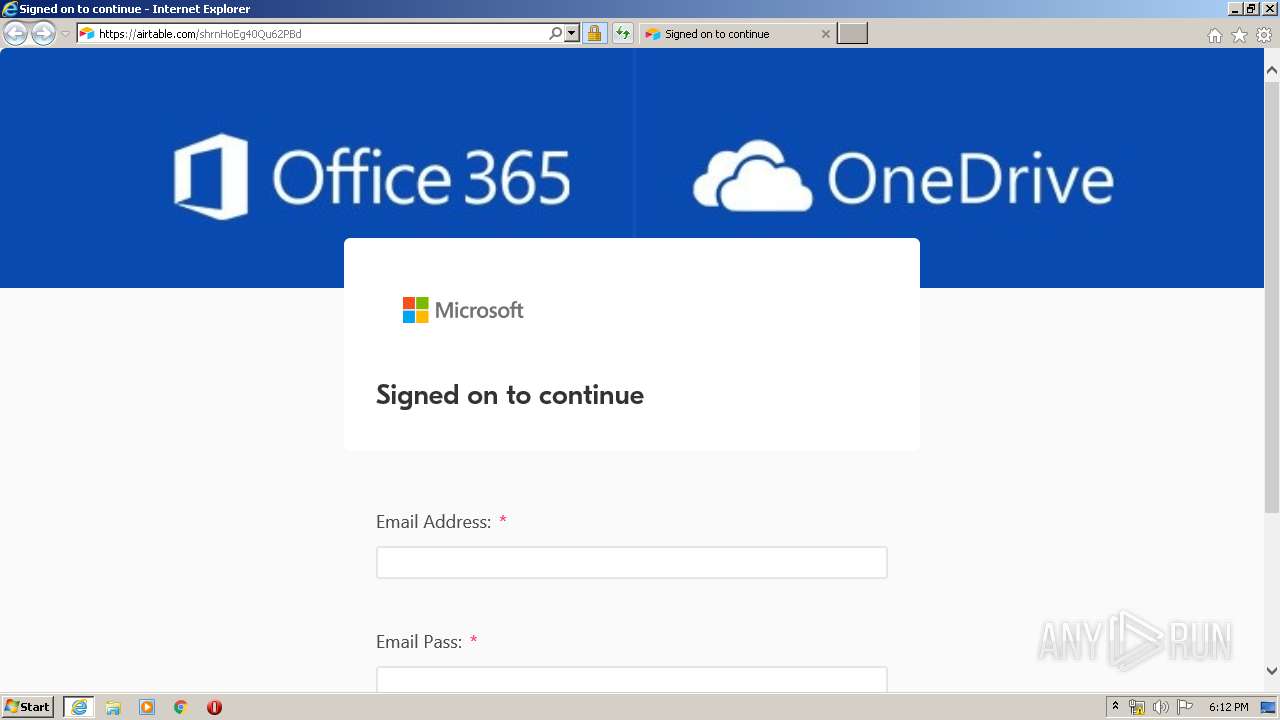
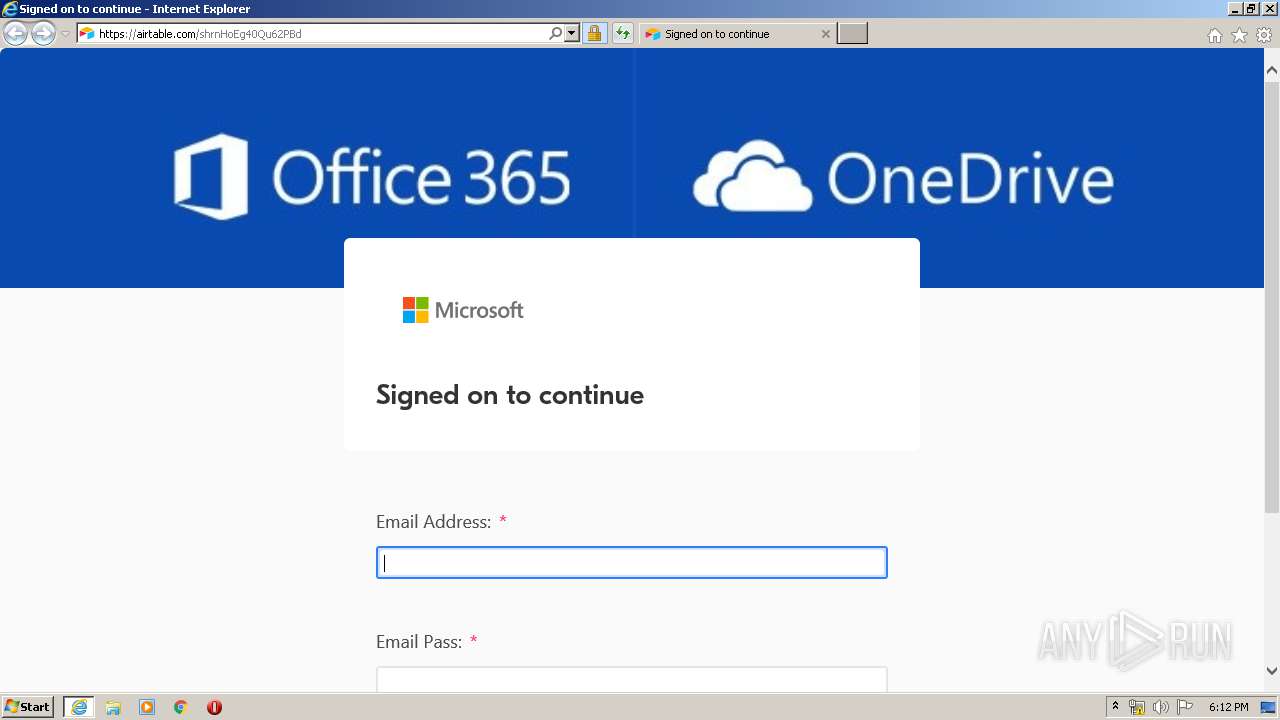
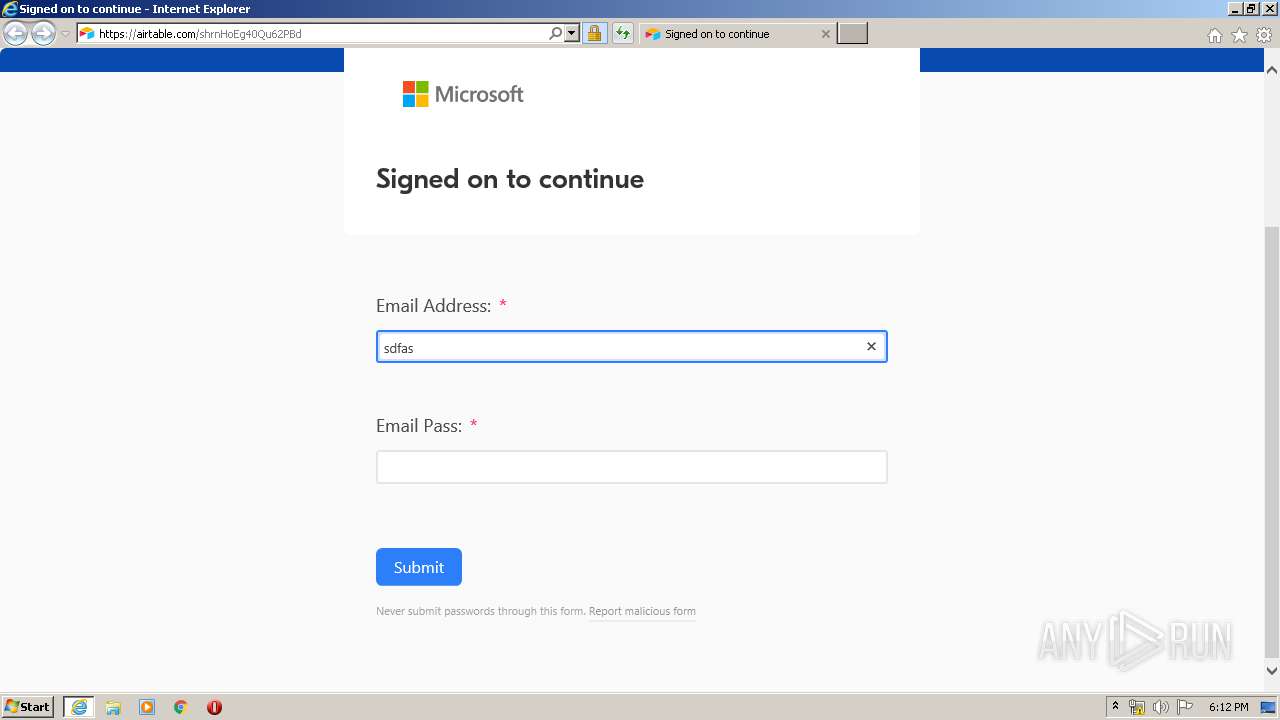
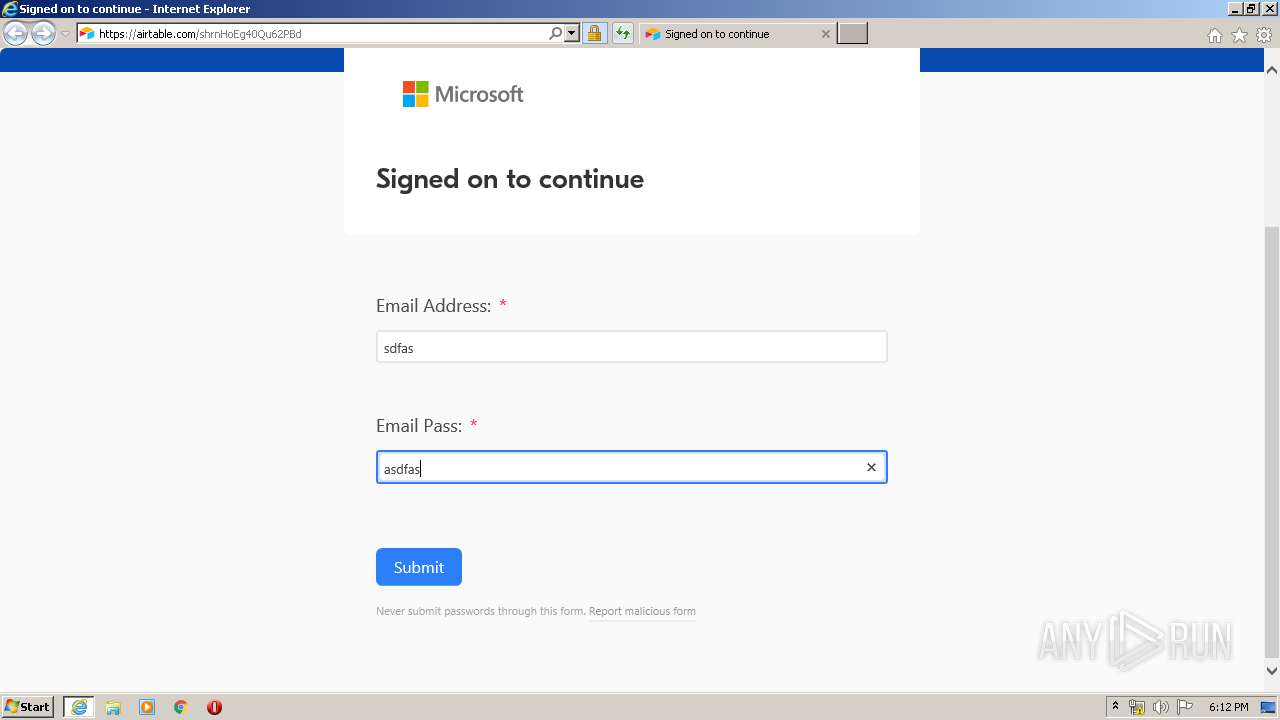
| URL: | https://airtable.com/shrnHoEg40Qu62PBd |
| Full analysis: | https://app.any.run/tasks/e59b63d5-fe84-4410-8426-7a0a43ced81b |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 18:11:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 767CA4F001CA97D1DEAC80141E62FCE7 |
| SHA1: | 98B7E9CAD3C3FEEBDF8313F1988B7FA204FDDC9F |
| SHA256: | D20C824E66DC4902D566AF7DB5CE9359B392DD17473C5017A27B2EDCD7D66FDD |
| SSDEEP: | 3:N8kOkNA9Xz:2eNA1z |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1748)
- iexplore.exe (PID: 3864)
Changes internet zones settings
- iexplore.exe (PID: 1748)
Reads settings of System Certificates
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 1748)
Reads internet explorer settings
- iexplore.exe (PID: 3864)
Application launched itself
- iexplore.exe (PID: 1748)
Creates files in the user directory
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 1748)
Changes settings of System certificates
- iexplore.exe (PID: 1748)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1748 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://airtable.com/shrnHoEg40Qu62PBd" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 3864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1748 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
Total events
5 816
Read events
608
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
41
Text files
35
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9D61.tmp | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9D62.tmp | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\I62BBKP0.txt | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4IT734EV.txt | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\137XNXRM.txt | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PEY6WIWY.txt | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\shared_form_view[1].js | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JX2N06Z7.txt | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:43AC500D589FCFAF053FB988CDC3B1C9 | SHA256:8839AC6BF994C13BF6102DE97F2023983DECF556104DD4602D77D4798B94A26D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
44
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3864 | iexplore.exe | GET | 200 | 143.204.208.145:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAXzUznT%2FJxP7%2FRFZu6voYA%3D | US | der | 471 b | whitelisted |
1748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3864 | iexplore.exe | GET | 200 | 143.204.208.145:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAaqjKlrwSC3BZuEzH06frM%3D | US | der | 471 b | whitelisted |
3864 | iexplore.exe | GET | 200 | 143.204.208.145:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAXzUznT%2FJxP7%2FRFZu6voYA%3D | US | der | 471 b | whitelisted |
3864 | iexplore.exe | GET | 200 | 143.204.208.145:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAaqjKlrwSC3BZuEzH06frM%3D | US | der | 471 b | whitelisted |
3864 | iexplore.exe | GET | 200 | 13.35.254.226:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3864 | iexplore.exe | GET | 200 | 13.35.254.155:80 | http://crl.rootg2.amazontrust.com/rootg2.crl | US | der | 608 b | whitelisted |
3864 | iexplore.exe | GET | 200 | 13.35.254.192:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1748 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1748 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3864 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3864 | iexplore.exe | 13.35.254.57:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
3864 | iexplore.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3864 | iexplore.exe | 13.35.254.124:80 | crl.rootg2.amazontrust.com | — | US | whitelisted |
1748 | iexplore.exe | 34.234.14.184:443 | airtable.com | Amazon.com, Inc. | US | unknown |
3864 | iexplore.exe | 143.204.208.145:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
3864 | iexplore.exe | 13.35.254.192:80 | o.ss2.us | — | US | unknown |
3864 | iexplore.exe | 13.35.253.55:443 | static.airtable.com | — | US | malicious |
3864 | iexplore.exe | 13.35.254.41:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
airtable.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
crl.rootg2.amazontrust.com |
| whitelisted |
static.airtable.com |
| shared |
cdnjs.cloudflare.com |
| whitelisted |