| File name: | BRT87652.msi |
| Full analysis: | https://app.any.run/tasks/642197d9-4f82-46c3-b110-df2f445deec9 |
| Verdict: | Malicious activity |
| Analysis date: | October 23, 2019, 16:35:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Title: Installation Database, Keywords: Installer, MSI, Database, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Number of Pages: 200, Security: 0, Code page: 1252, Revision Number: {F8FE4415-37E2-467B-B357-9E208629474E}, Number of Words: 10, Subject: Usermode Font Driver, Author: Usermode Font Driver, Name of Creating Application: Advanced Installer 12.3 build 64631, Template: ;1033, Comments: Usermode Font Driver Usermode Font Driver. |
| MD5: | 628717661E0B0859A241C5CA1B098462 |
| SHA1: | 41A3D2C1F290856005B5BADF54A38693A959D580 |
| SHA256: | D1E711B5FFE90830CC7240D1DB0EDC66131DC7A8E1F6B162D5FDC51C64652857 |
| SSDEEP: | 3072:SurnV9B3DlY5AtU6ij4qpXqnnDibAJBVkCU6McB3RUN46ILJ9+ZB5yOanA/:Suj53DlY5AtTqp4nwETUprx/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 688)
INFO
Application launched itself
- msiexec.exe (PID: 688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Title: | Installation Database |
|---|---|
| Keywords: | Installer, MSI, Database |
| LastPrinted: | 2009:12:11 11:47:44 |
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Pages: | 200 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {F8FE4415-37E2-467B-B357-9E208629474E} |
| Words: | 10 |
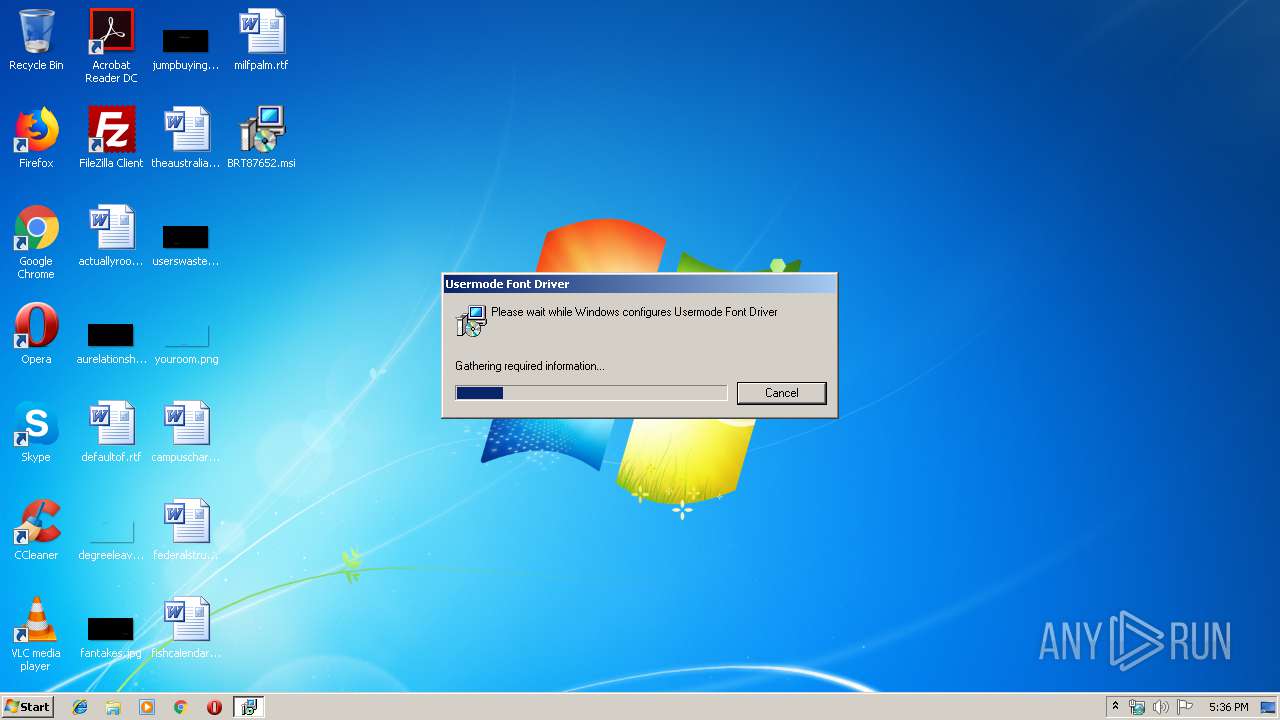
| Subject: | Usermode Font Driver |
| Author: | Usermode Font Driver |
| LastModifiedBy: | - |
| Software: | Advanced Installer 12.3 build 64631 |
| Template: | ;1033 |
| Comments: | Usermode Font Driver Usermode Font Driver. |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
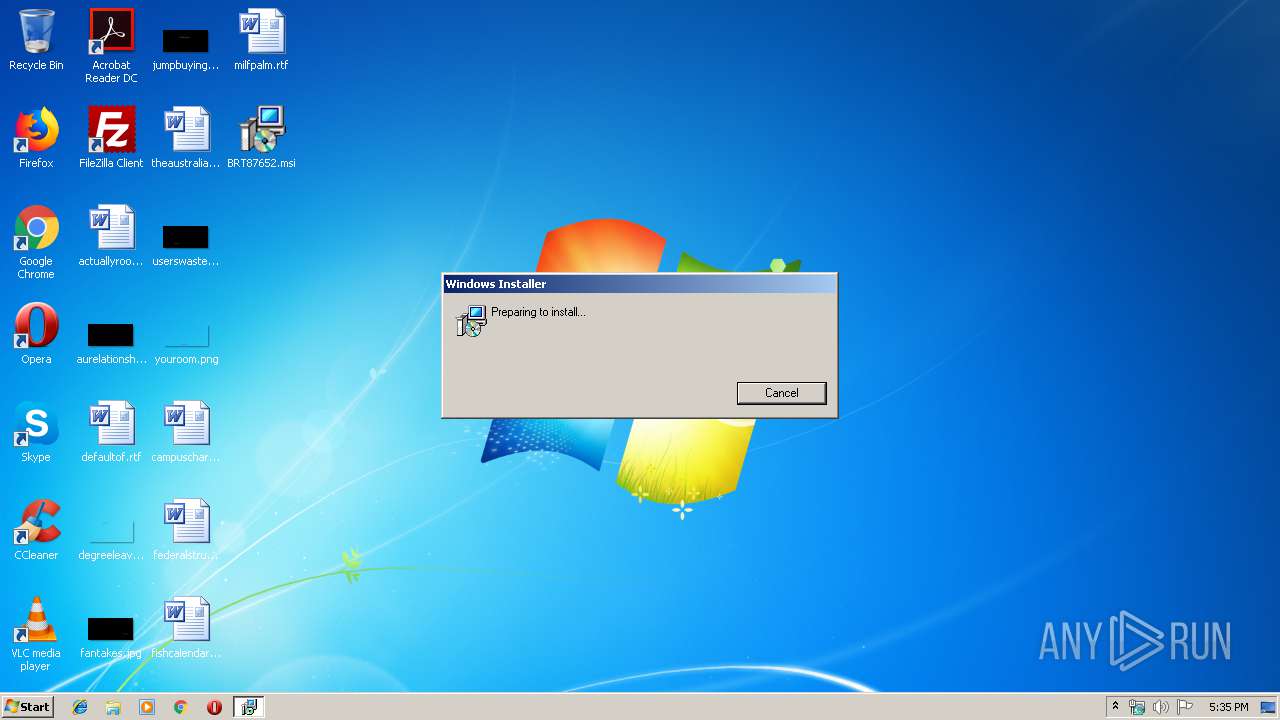
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\BRT87652.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 688 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3944 | C:\Windows\system32\MsiExec.exe -Embedding 81A09649C4FCDC478C43C099A7CFB7C9 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
435
Read events
413
Write events
22
Delete events
0
Modification events
| (PID) Process: | (688) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B002000014252EF0BF89D501 | |||
| (PID) Process: | (688) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 889CD0178FD57D8970612B8FD0F4B534C2B09661206BE295C4E5C0C243C0C744 | |||
| (PID) Process: | (688) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (688) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | |
Value: C:\Windows\Installer\39ada2.ipi | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 688 | msiexec.exe | C:\Windows\Installer\MSIAE3C.tmp | — | |
MD5:— | SHA256:— | |||
| 688 | msiexec.exe | C:\Windows\Installer\MSIAEBA.tmp | — | |
MD5:— | SHA256:— | |||
| 688 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF17230A28BD4A3883.TMP | — | |
MD5:— | SHA256:— | |||
| 688 | msiexec.exe | C:\Windows\Installer\39ada0.msi | executable | |
MD5:— | SHA256:— | |||
| 688 | msiexec.exe | C:\Windows\Installer\39ada2.ipi | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3944 | MsiExec.exe | GET | — | 54.153.111.225:80 | http://54.153.111.225/dados.zip | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3944 | MsiExec.exe | 54.153.111.225:80 | — | Amazon.com, Inc. | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3944 | MsiExec.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
3944 | MsiExec.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Loader (Trojan.Agent.DDSA) Requesting Zip Archive |