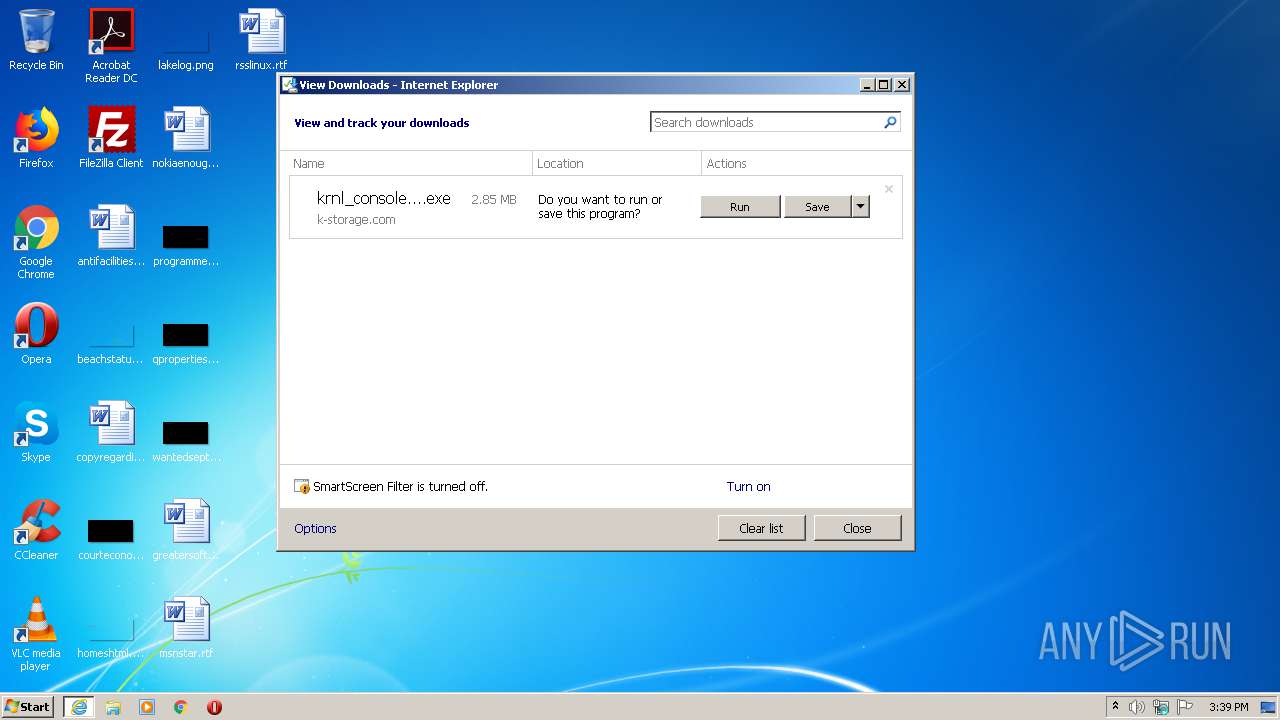
| URL: | https://k-storage.com/krnl_console_bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/83650847-1968-46a4-adfc-6184e212c86b |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2021, 14:39:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F7CEBB00B0CDE2288CBF2276F0E8F803 |
| SHA1: | CA6A985BD5620F87019C6C024FBC47C7C0D0072E |
| SHA256: | D1E54509F59C494355FCC5DB97C087C82D7AA6166BCC7A001D540D0B5FB1C1B2 |
| SSDEEP: | 3:N8EsXA3OXL0JNJPWXEw4A:2EsXDXbEw4A |
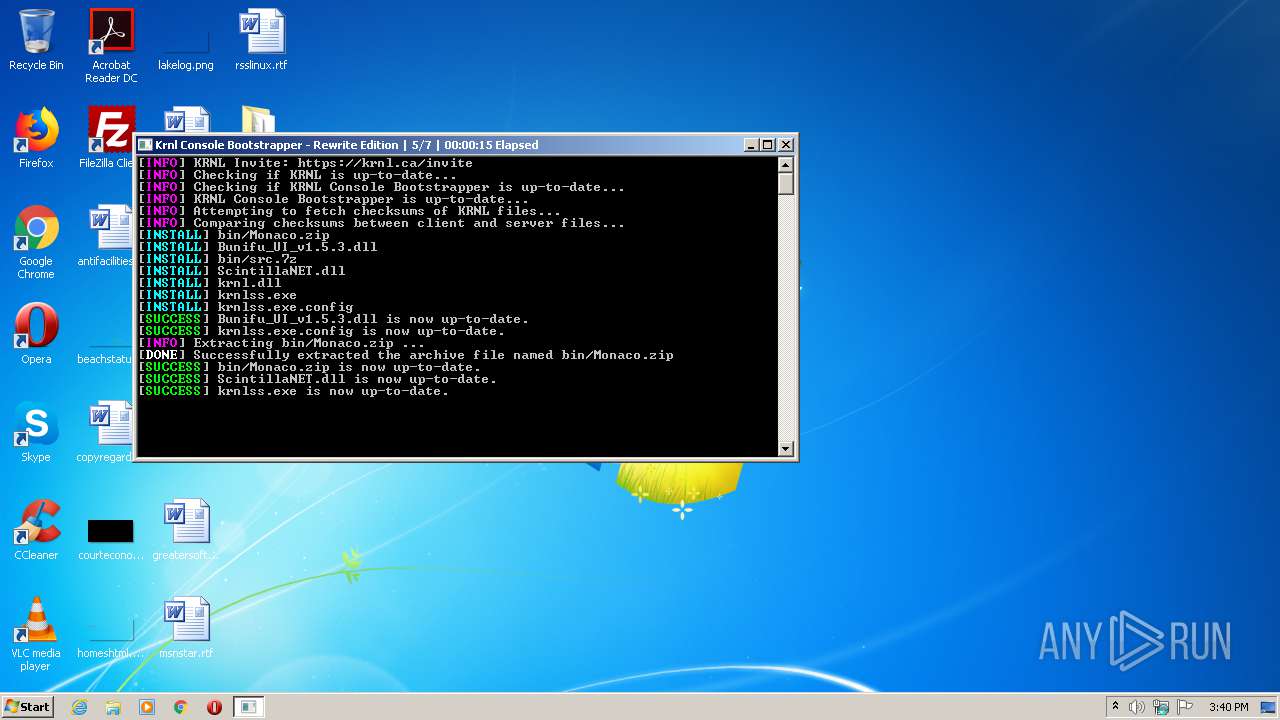
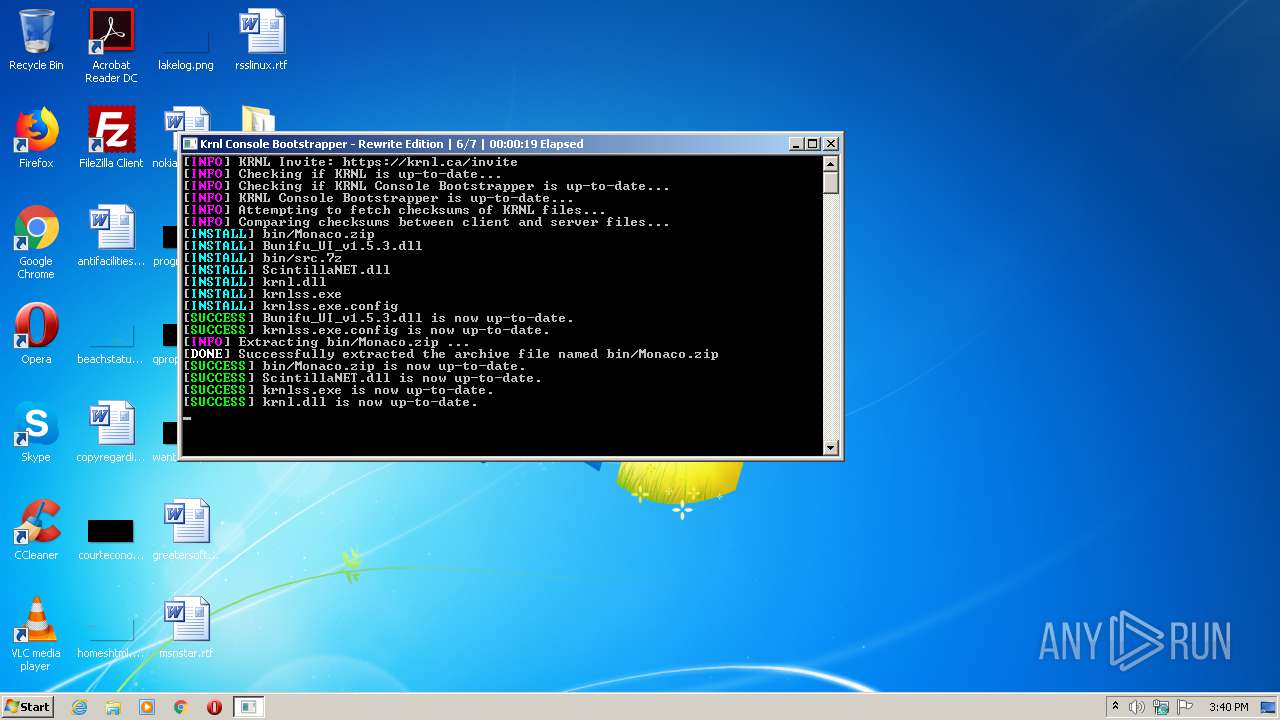
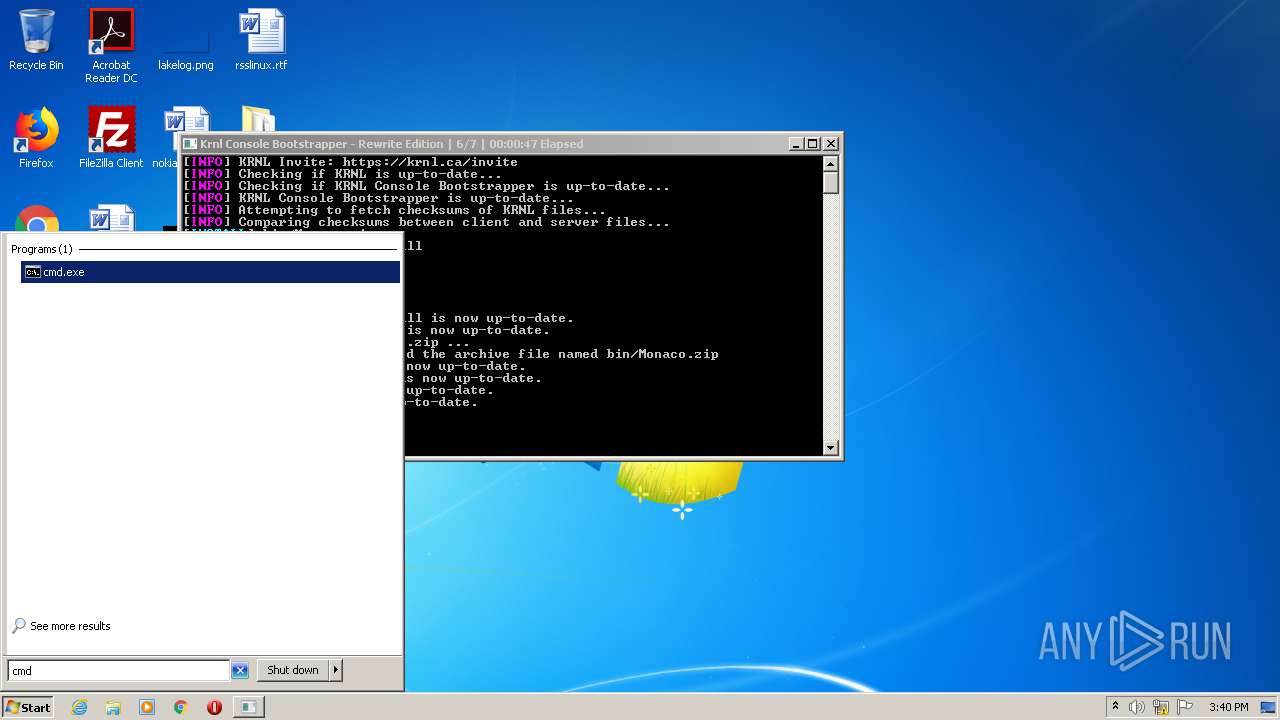
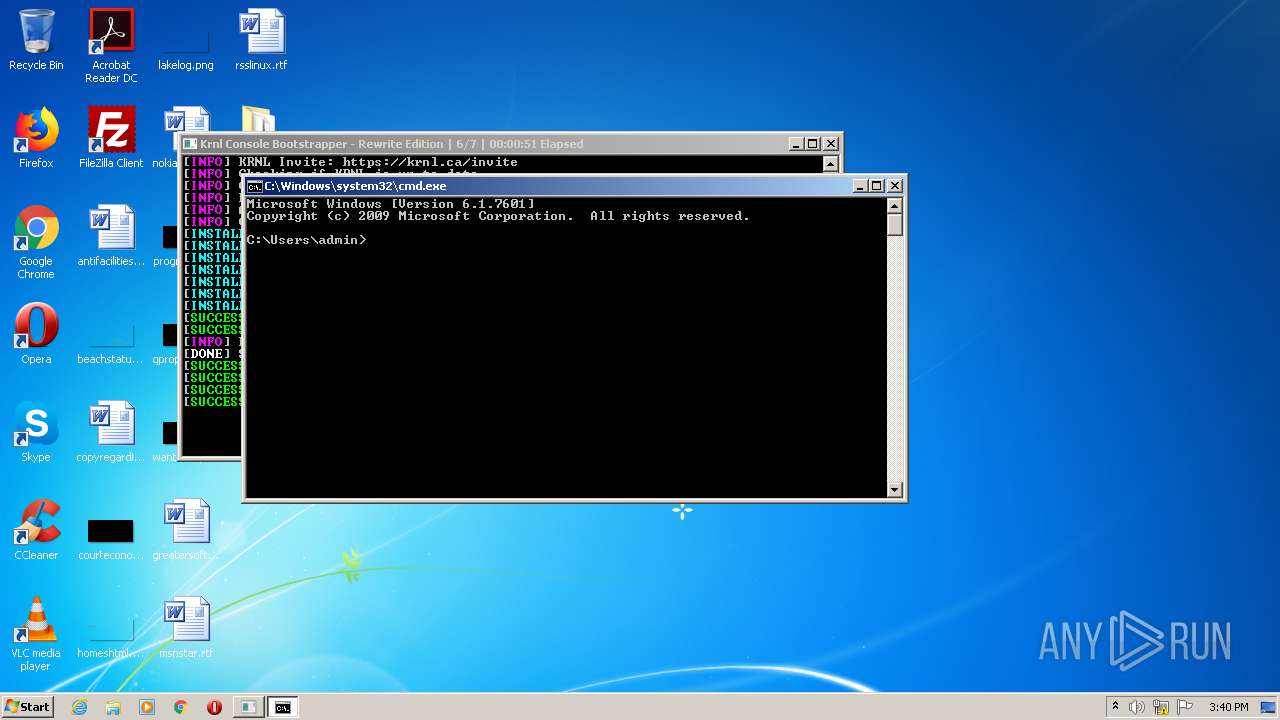
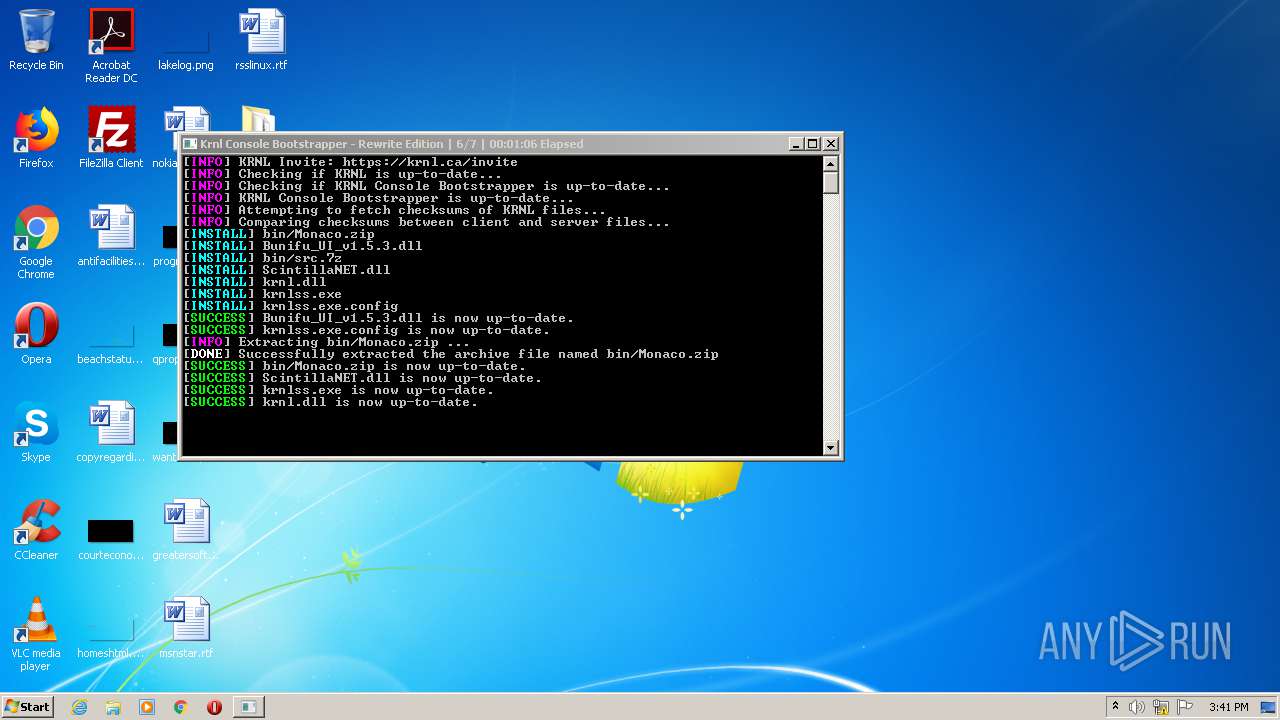
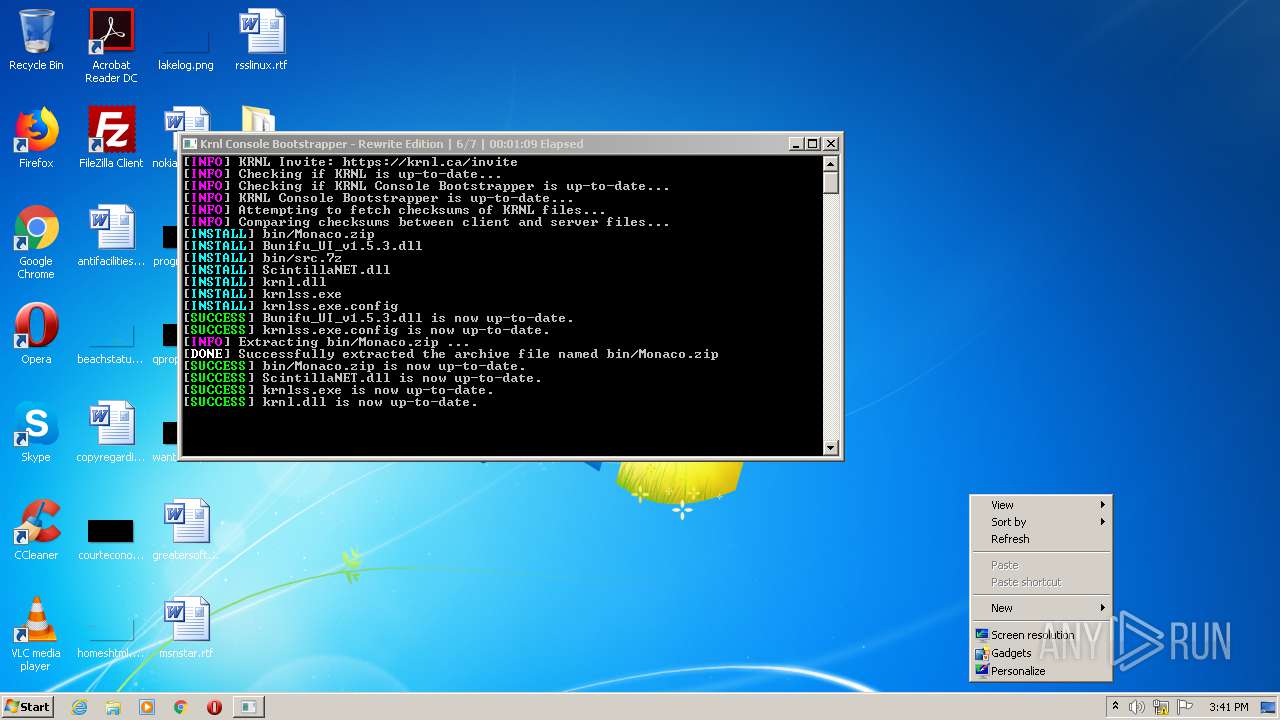
MALICIOUS
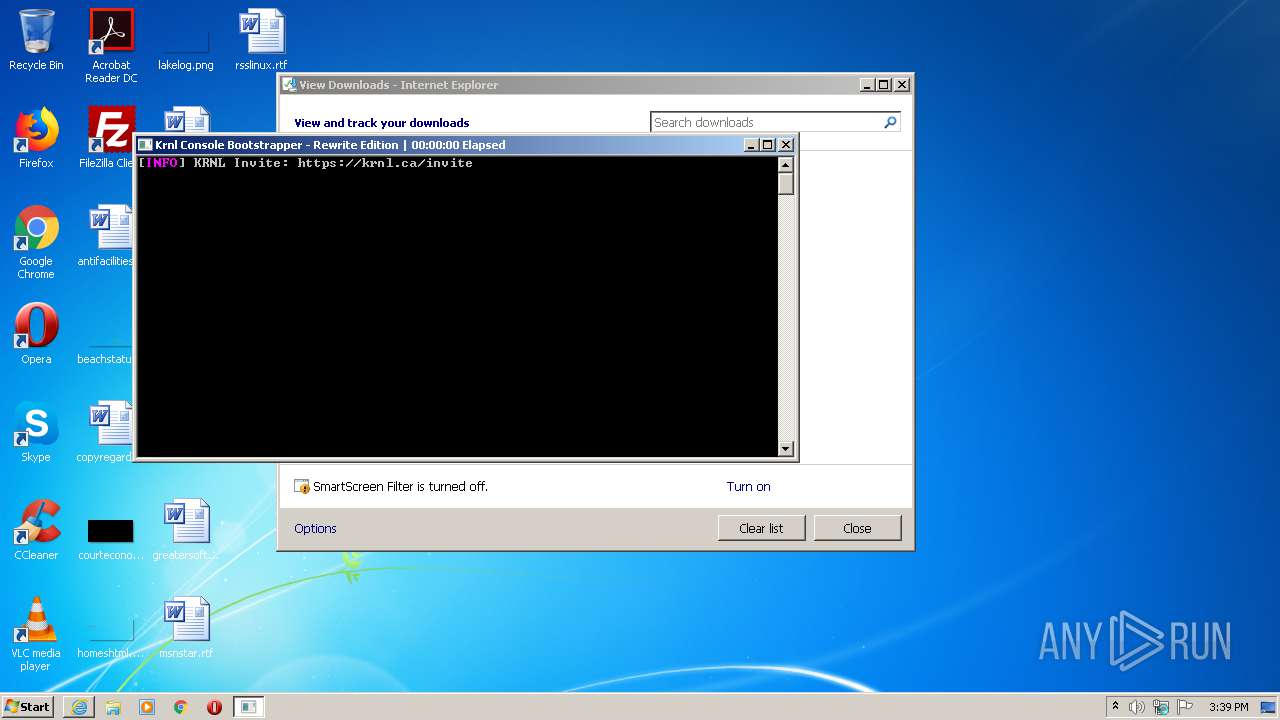
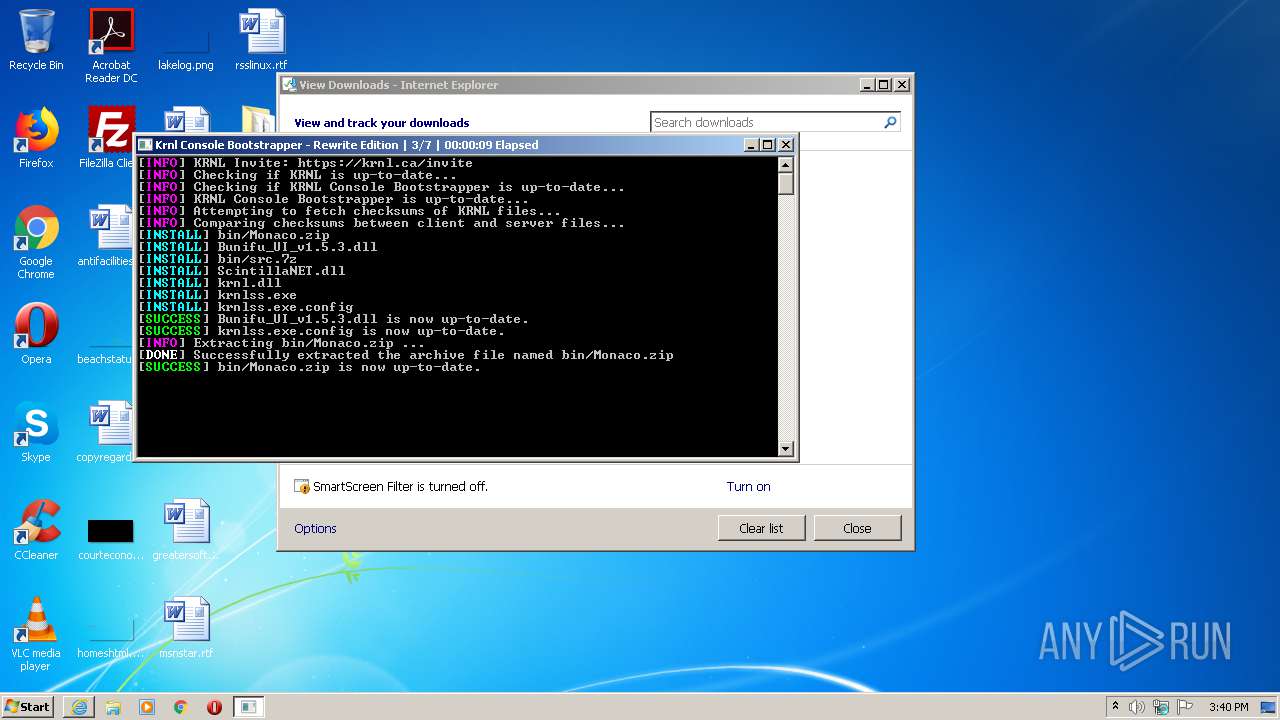
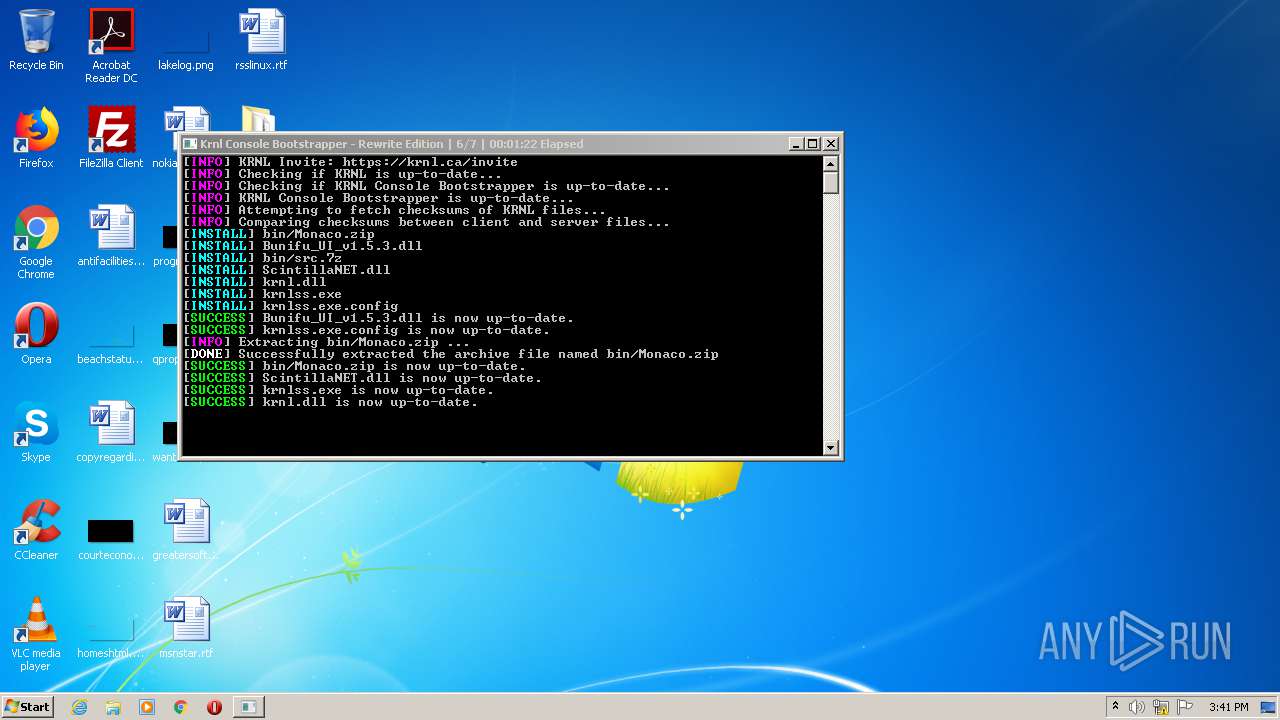
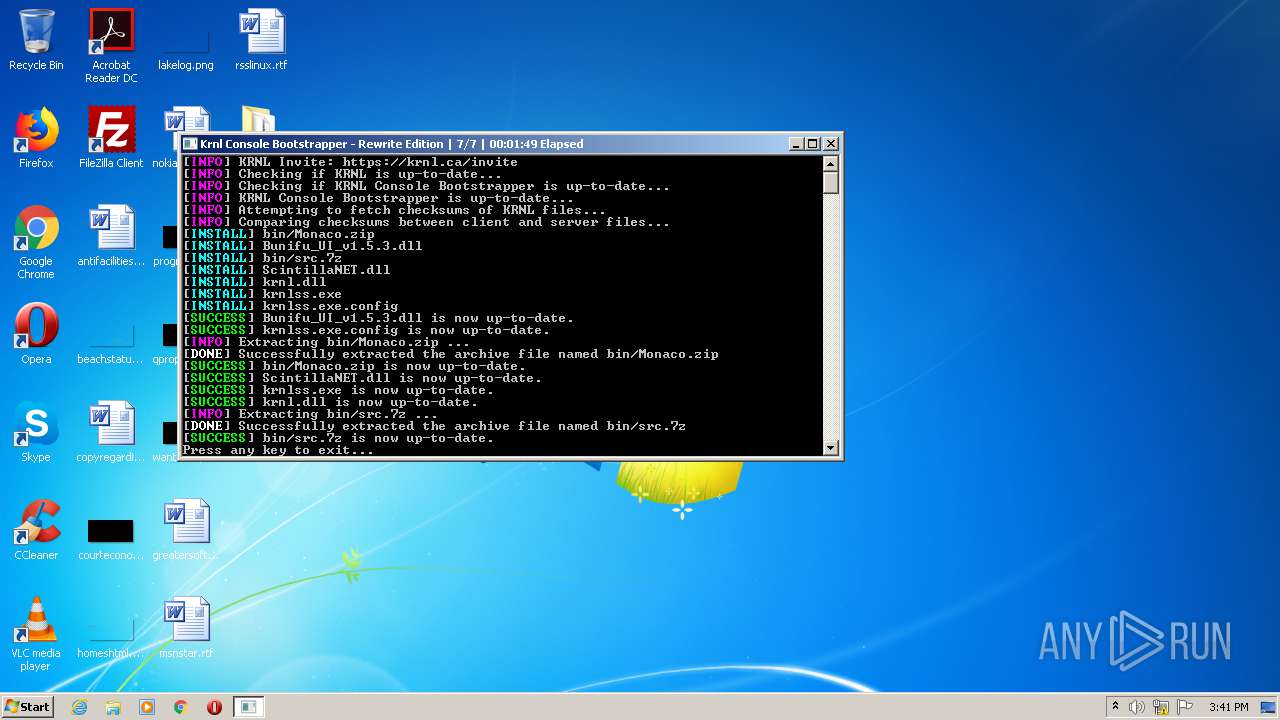
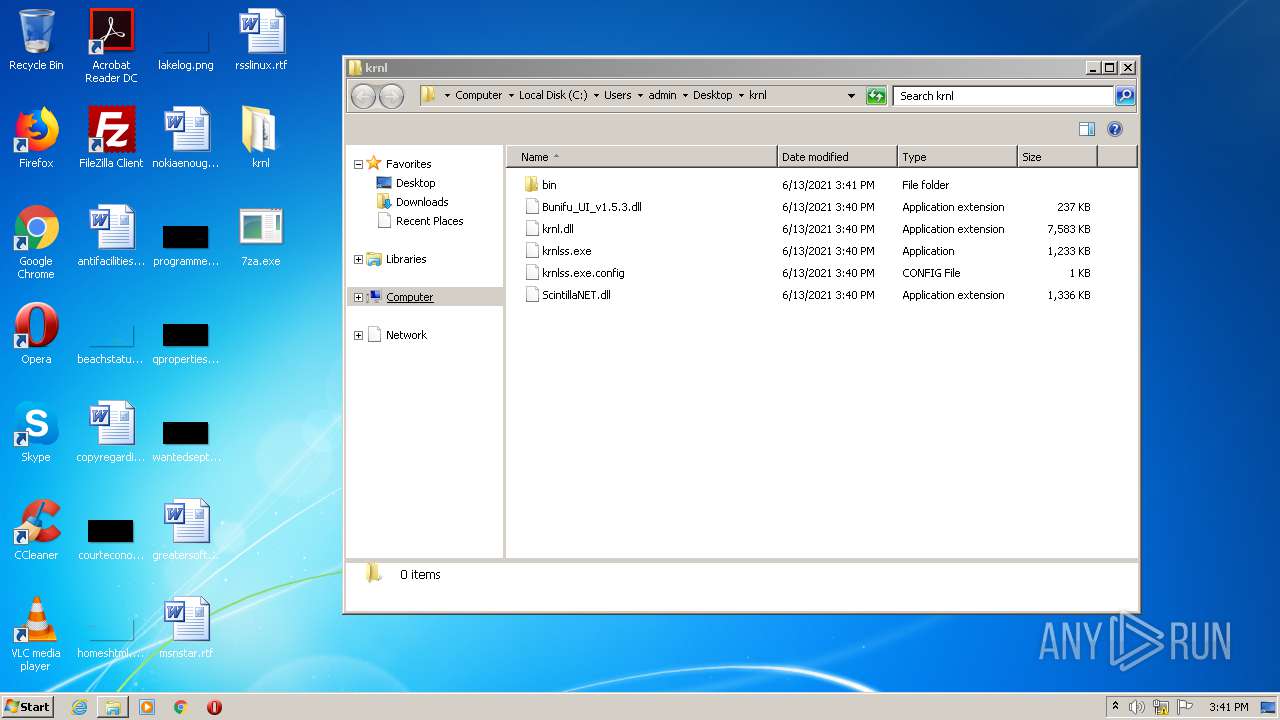
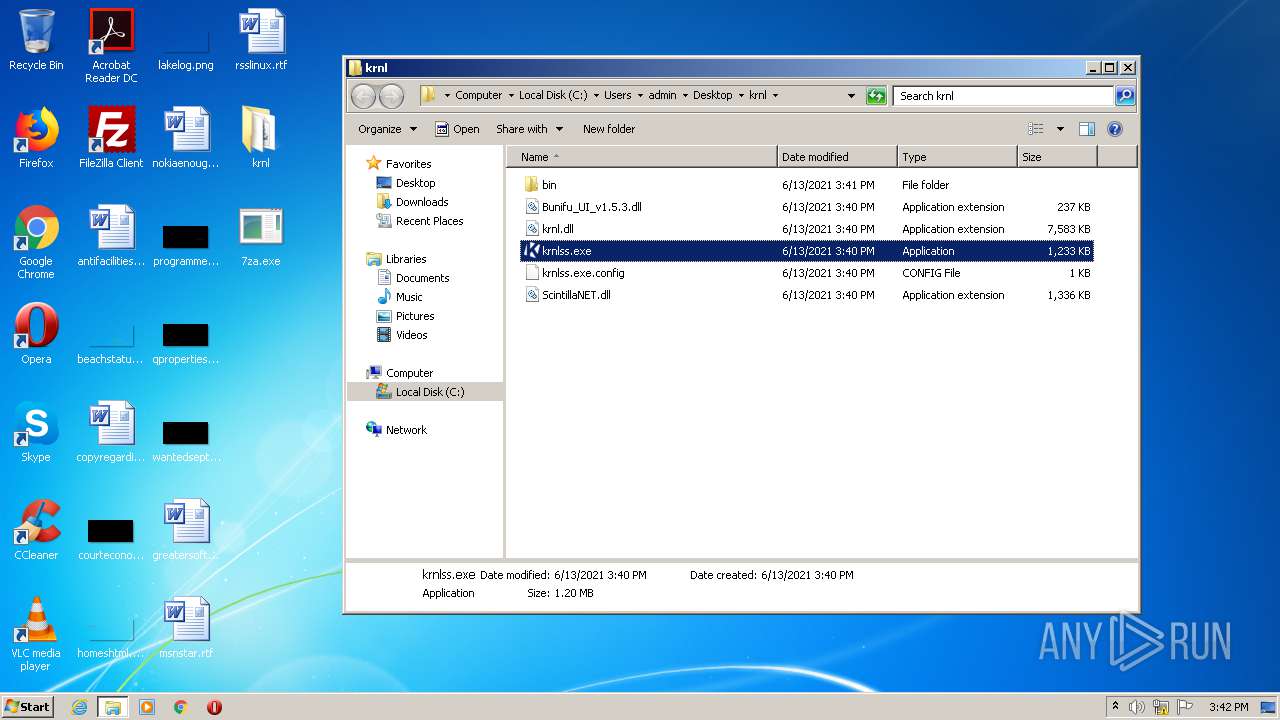
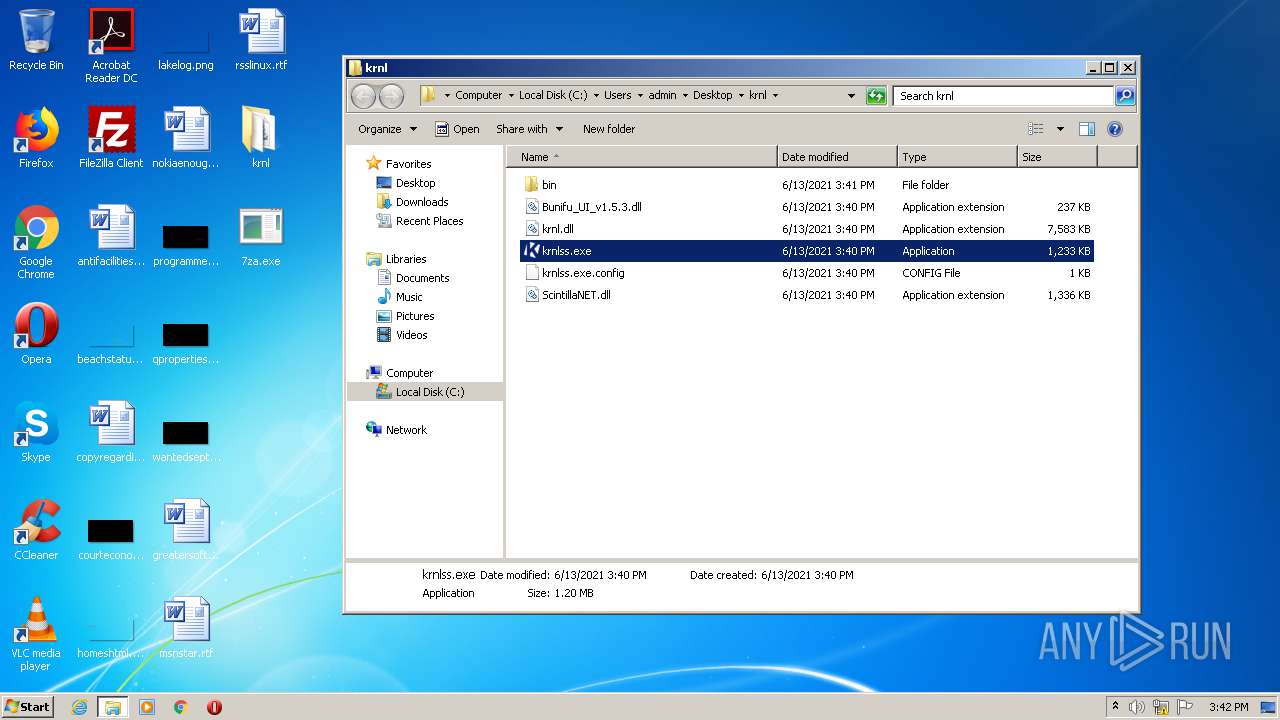
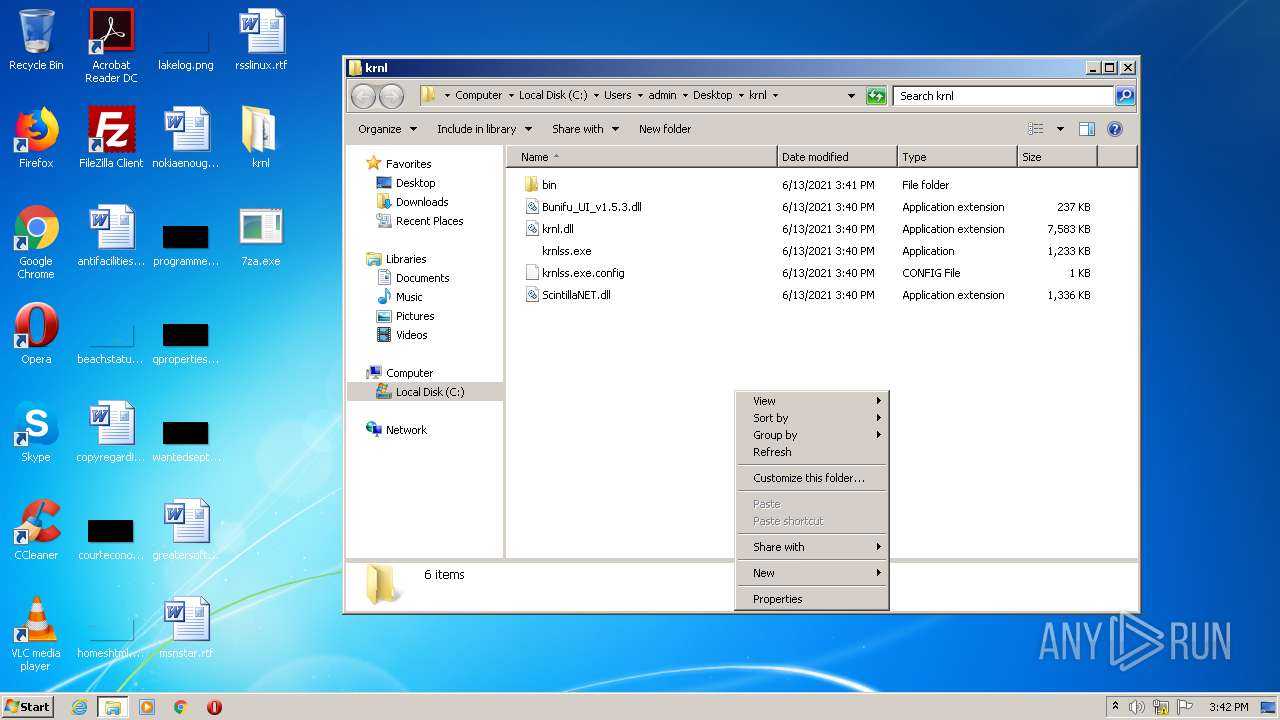
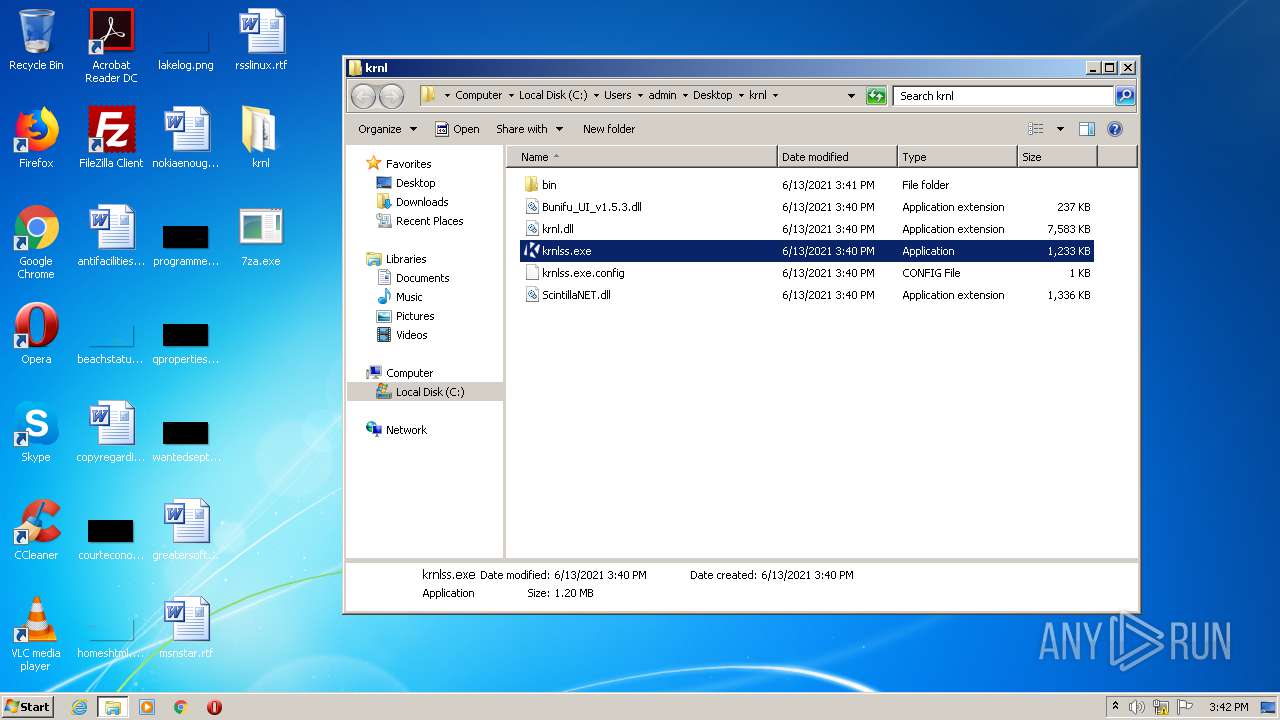
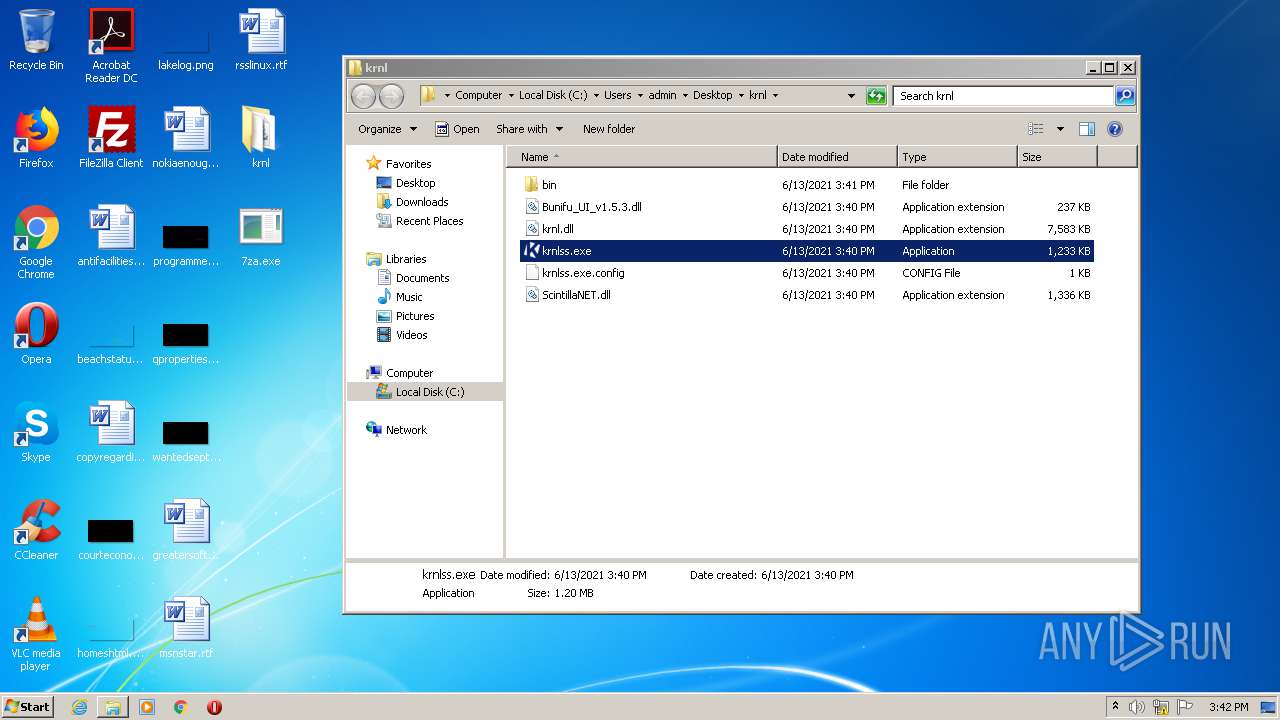
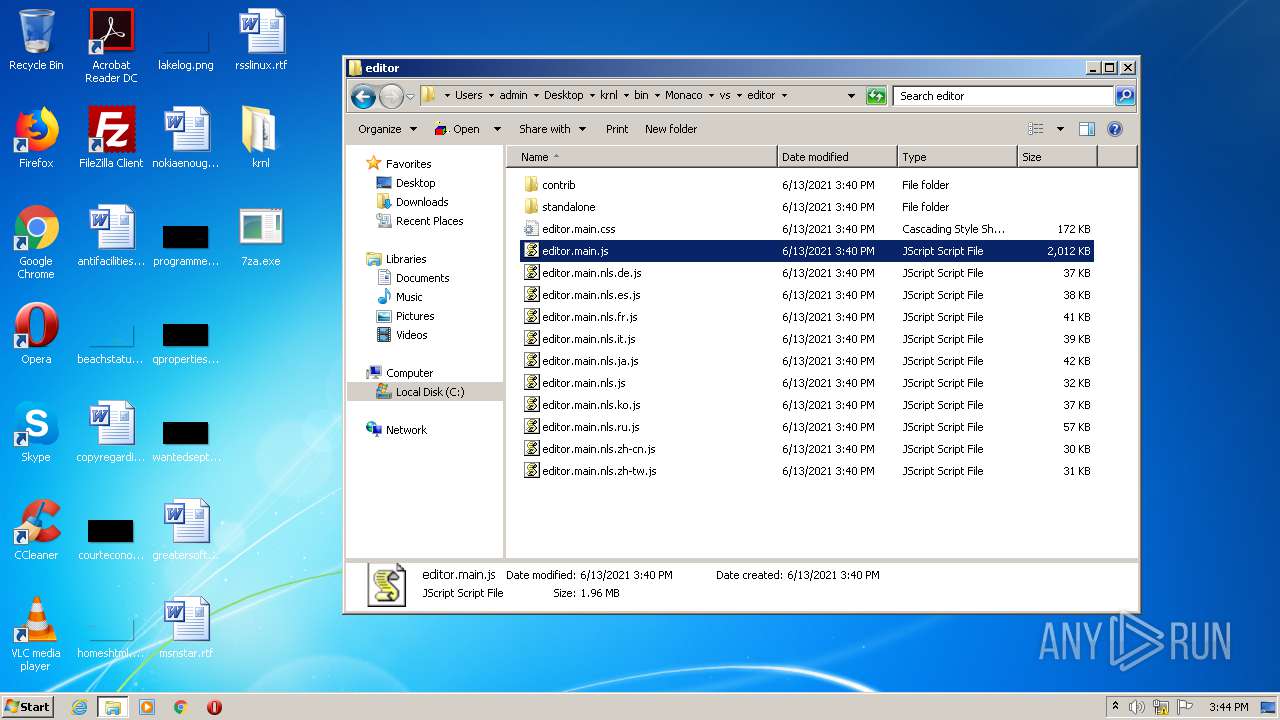
Application was dropped or rewritten from another process
- krnl_console_bootstrapper.exe (PID: 2292)
- krnlss.exe (PID: 3876)
Loads dropped or rewritten executable
- krnlss.exe (PID: 3876)
- explorer.exe (PID: 4028)
- SearchProtocolHost.exe (PID: 3088)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3360)
- iexplore.exe (PID: 2228)
- krnl_console_bootstrapper.exe (PID: 2292)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3360)
- krnl_console_bootstrapper.exe (PID: 2292)
- iexplore.exe (PID: 2228)
Reads Environment values
- krnl_console_bootstrapper.exe (PID: 2292)
Executed via COM
- explorer.exe (PID: 4028)
Drops a file with too old compile date
- krnl_console_bootstrapper.exe (PID: 2292)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2216)
Reads default file associations for system extensions
- explorer.exe (PID: 4028)
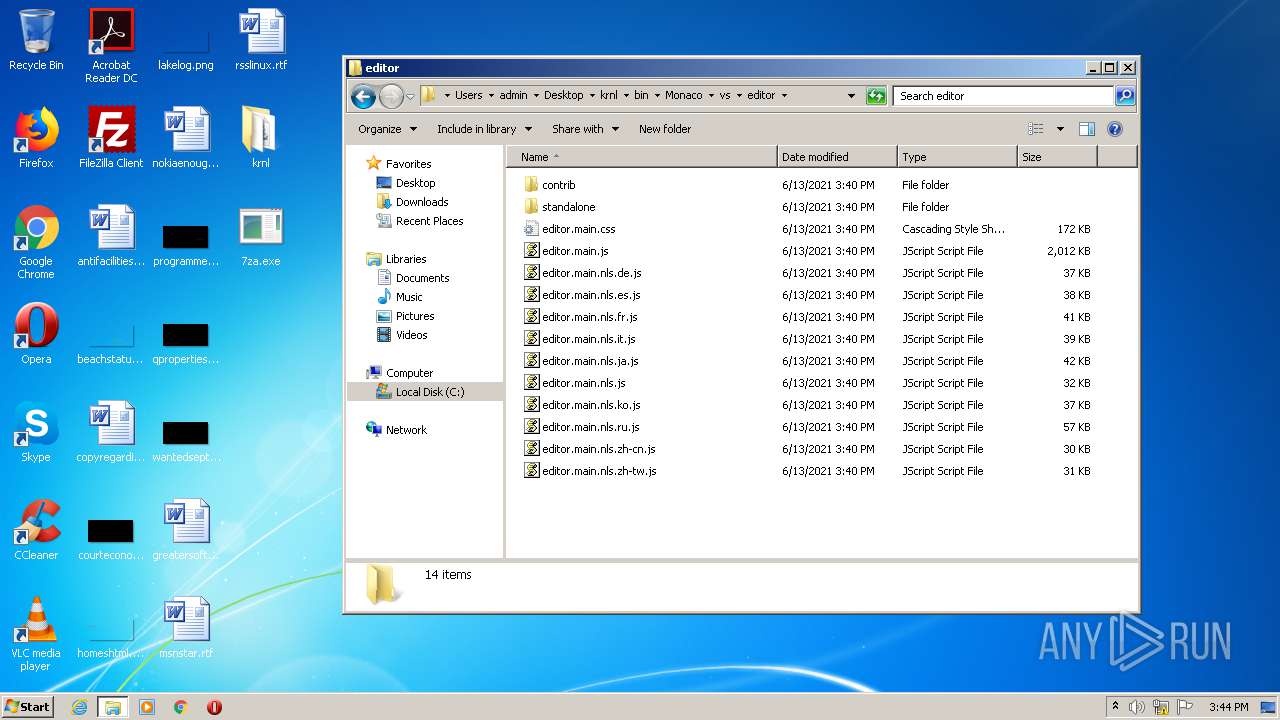
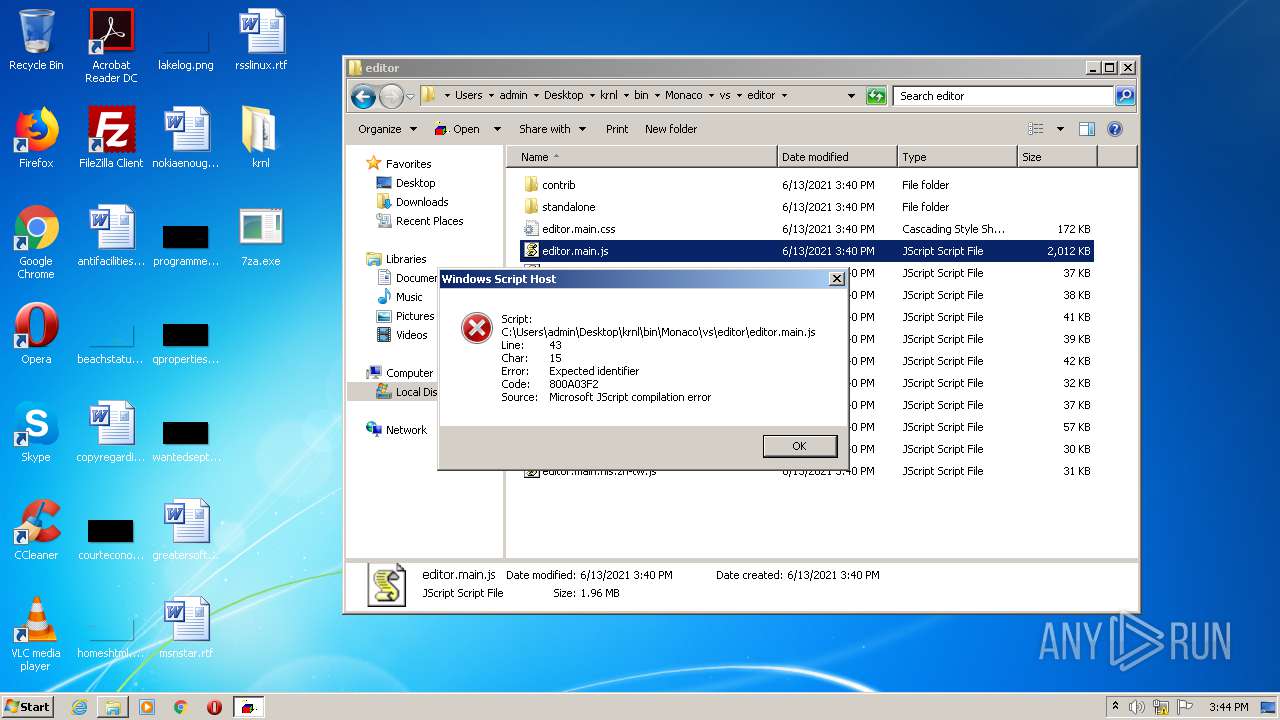
Executes scripts
- explorer.exe (PID: 4028)
Drops a file that was compiled in debug mode
- krnl_console_bootstrapper.exe (PID: 2292)
INFO
Application launched itself
- iexplore.exe (PID: 2228)
- chrome.exe (PID: 2216)
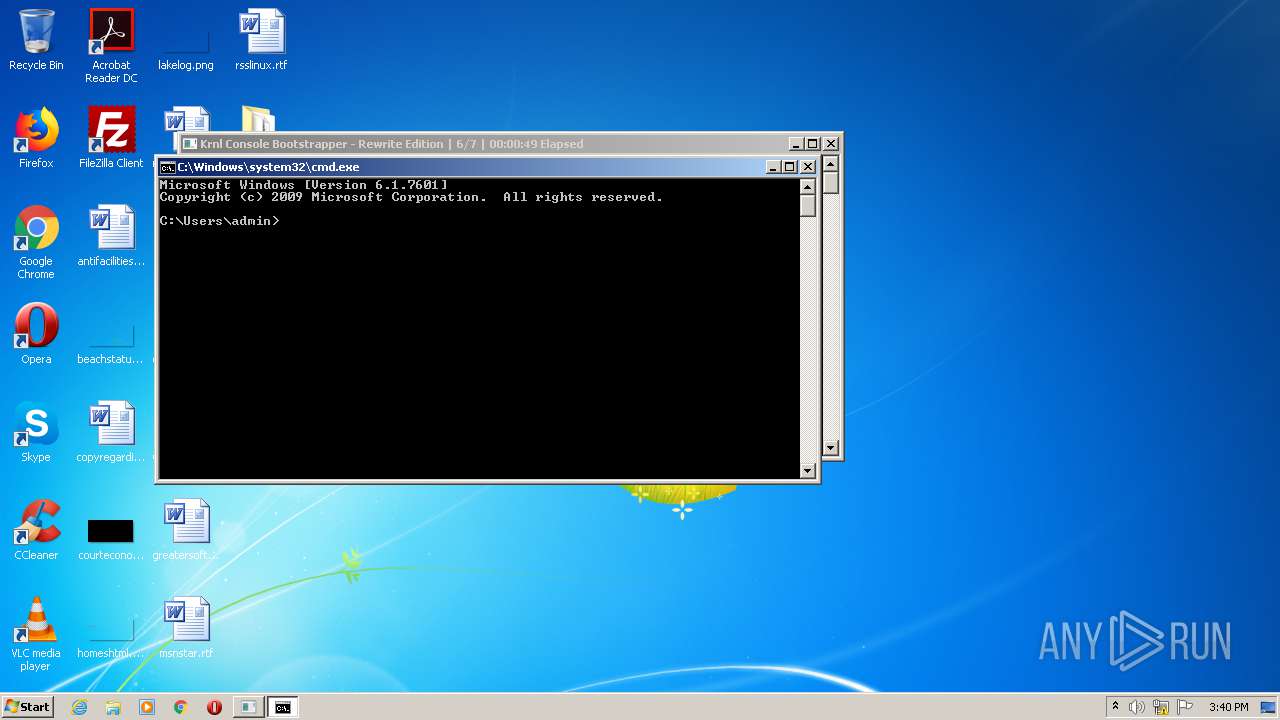
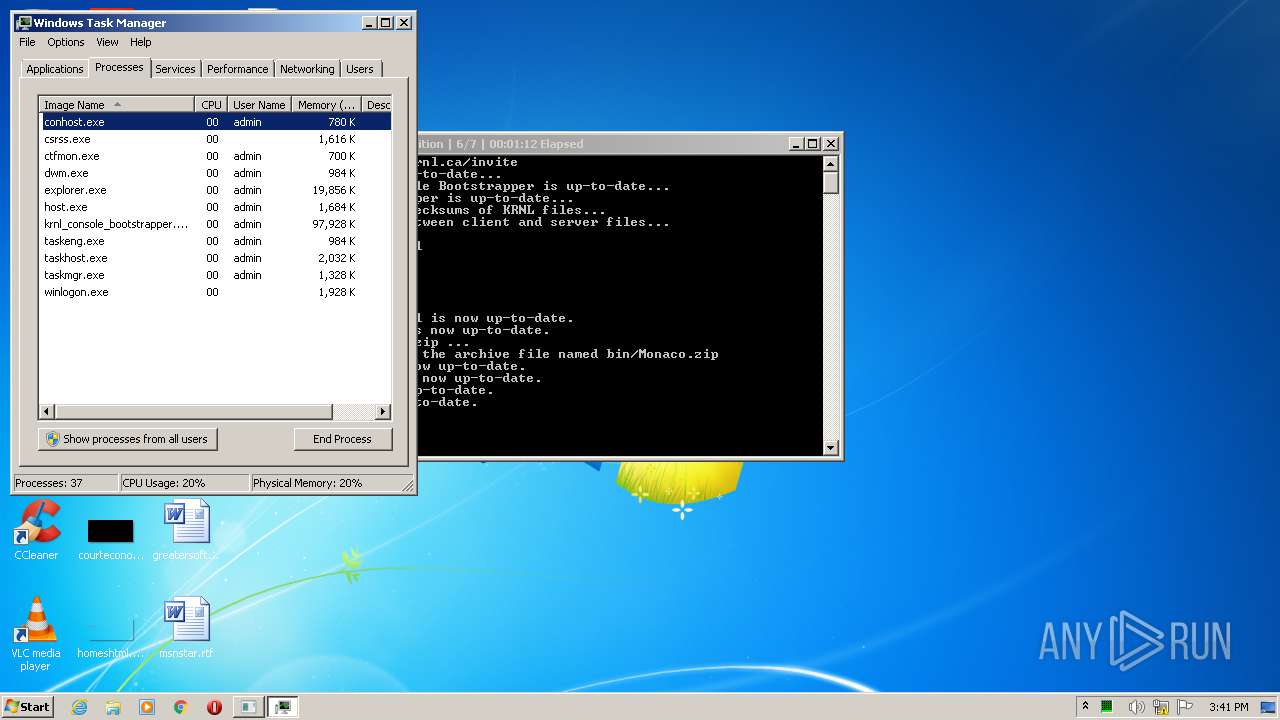
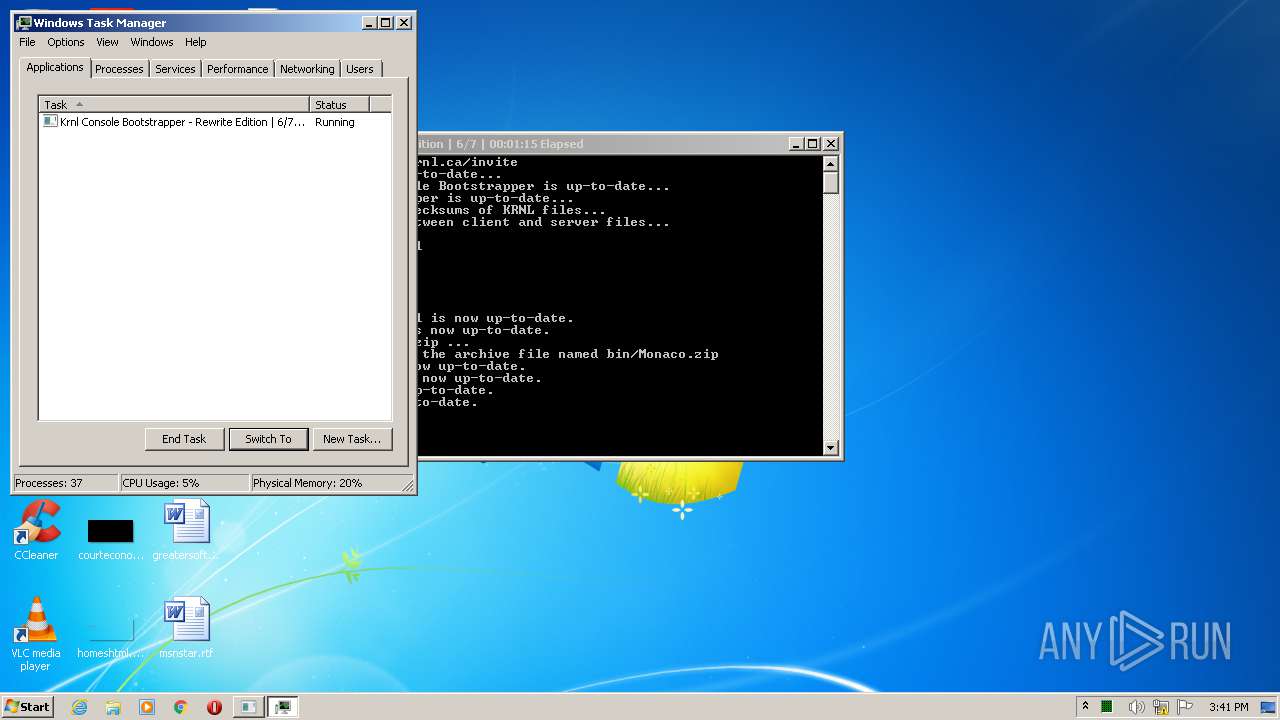
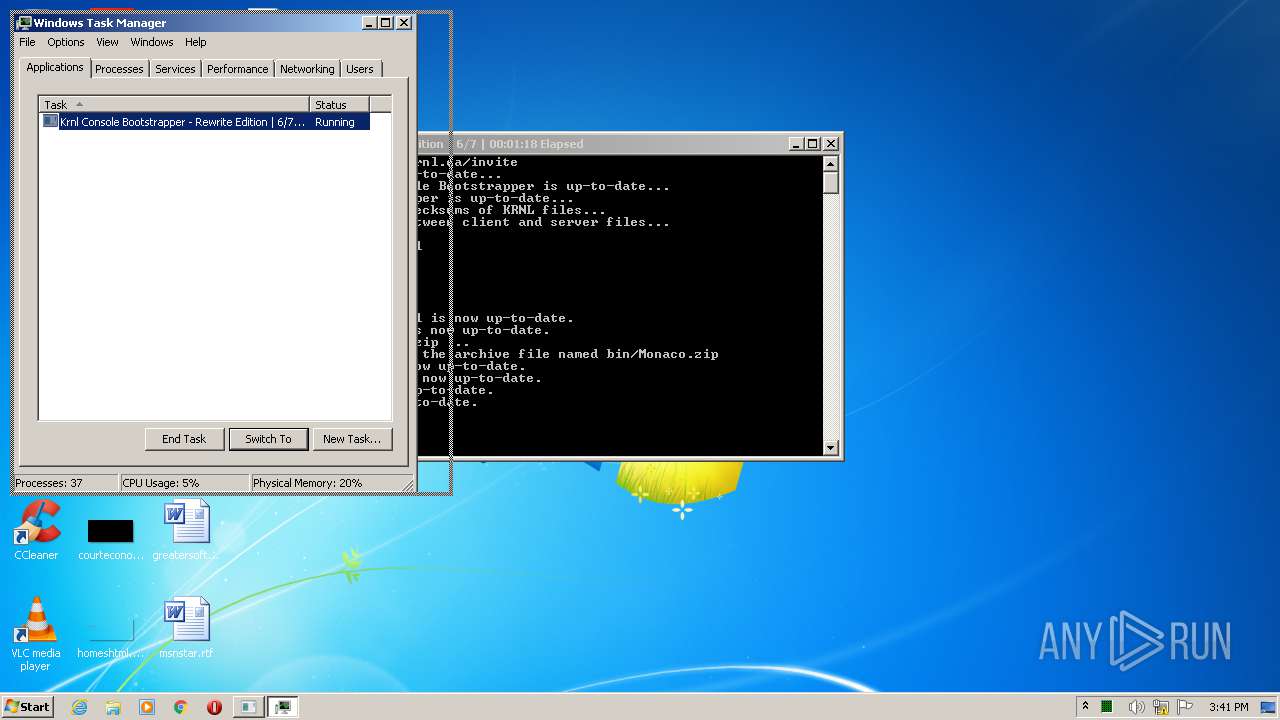
Manual execution by user
- chrome.exe (PID: 2216)
- cmd.exe (PID: 996)
- taskmgr.exe (PID: 2668)
Reads the hosts file
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2988)
Reads settings of System Certificates
- chrome.exe (PID: 2988)
- iexplore.exe (PID: 3360)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2228)
Changes internet zones settings
- iexplore.exe (PID: 2228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
48
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17138683872150476076,8494448610348441357,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10115639029818451139 --mojo-platform-channel-handle=2428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17138683872150476076,8494448610348441357,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3314470871784820312 --mojo-platform-channel-handle=3796 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17138683872150476076,8494448610348441357,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=130298318617432199 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17138683872150476076,8494448610348441357,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11349661657209010489 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
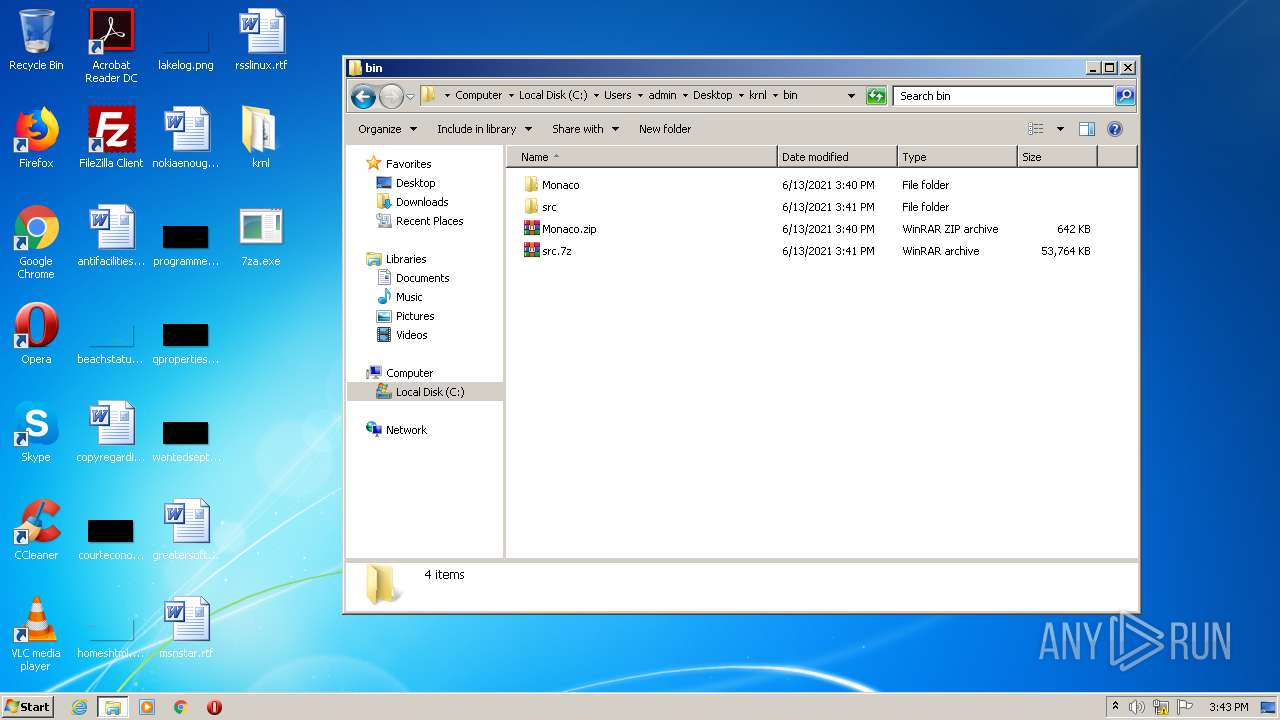
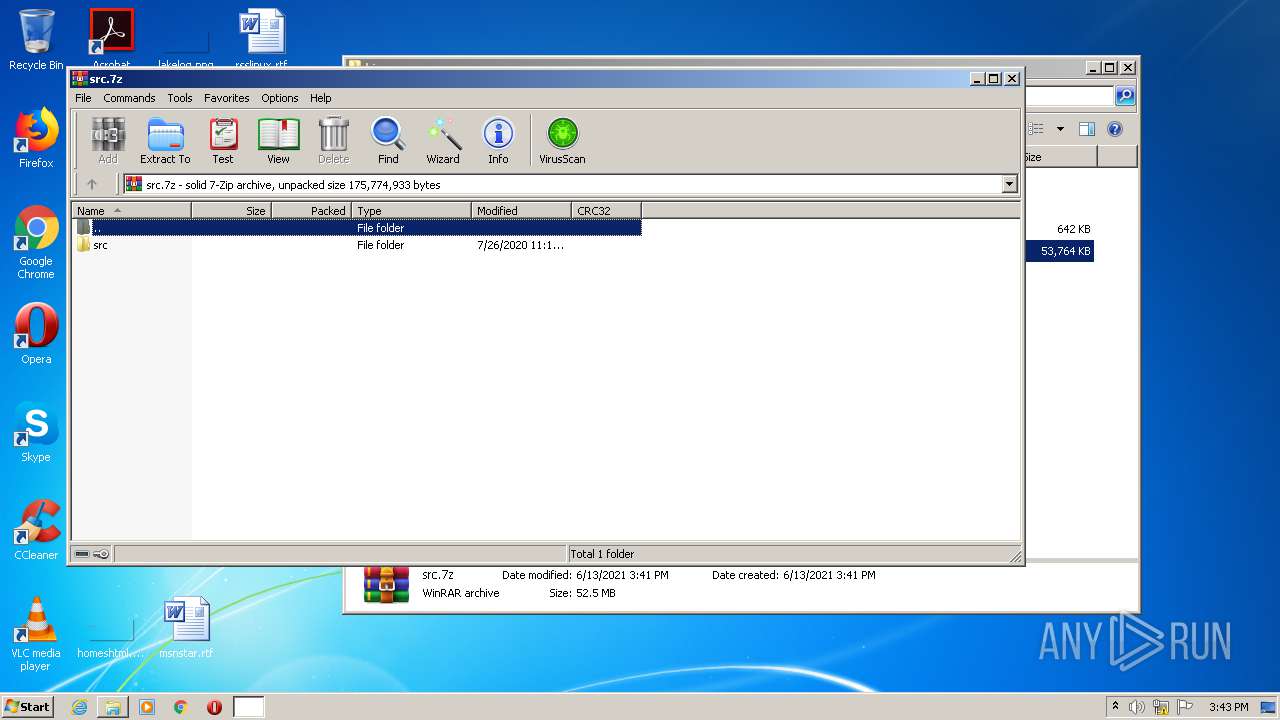
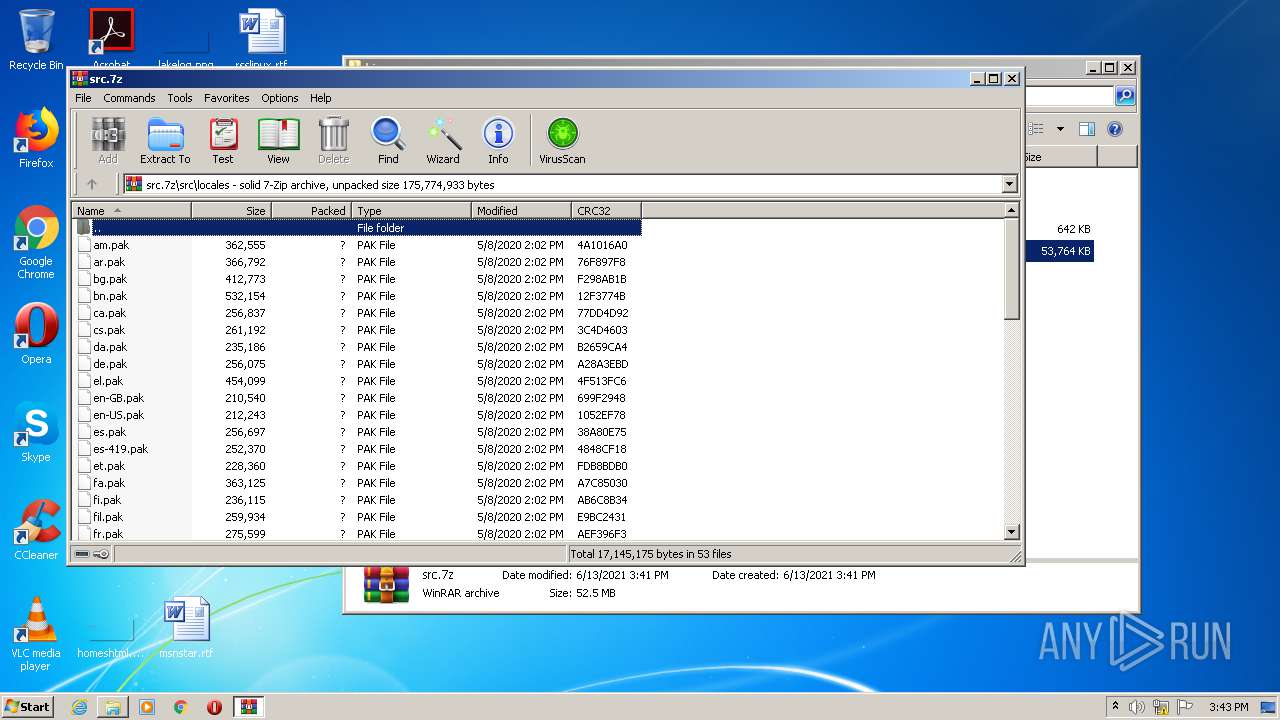
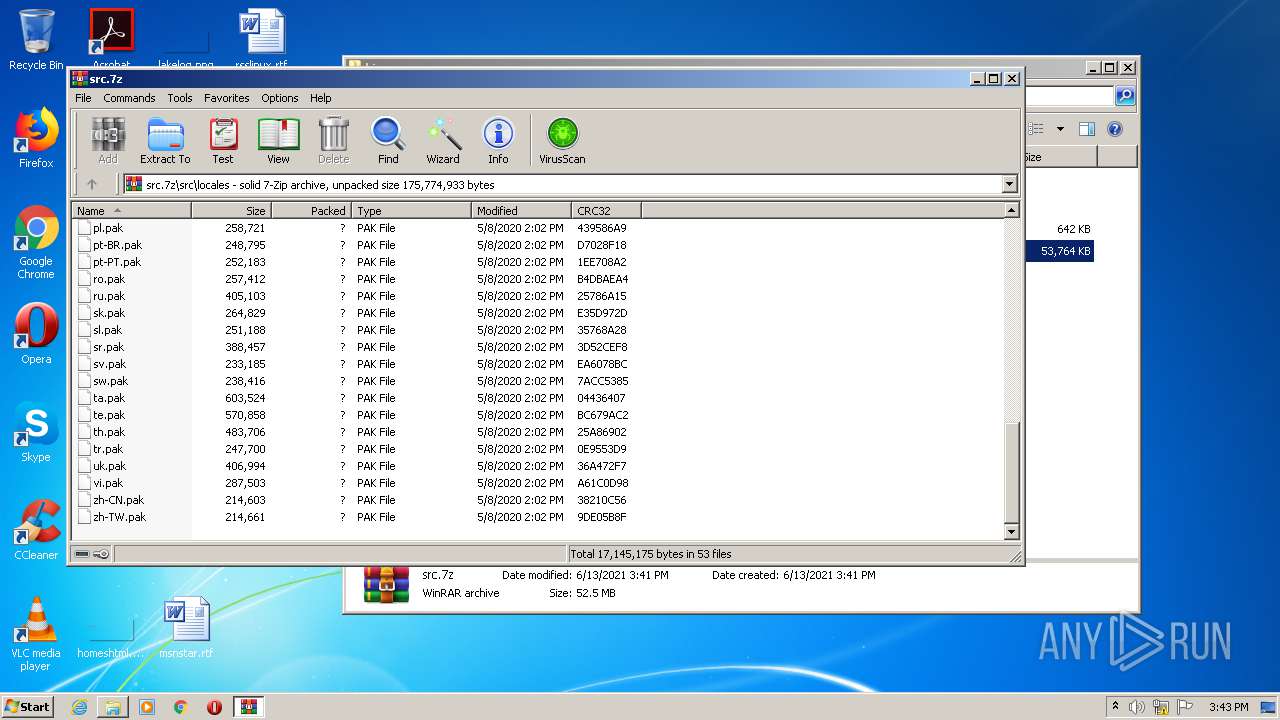
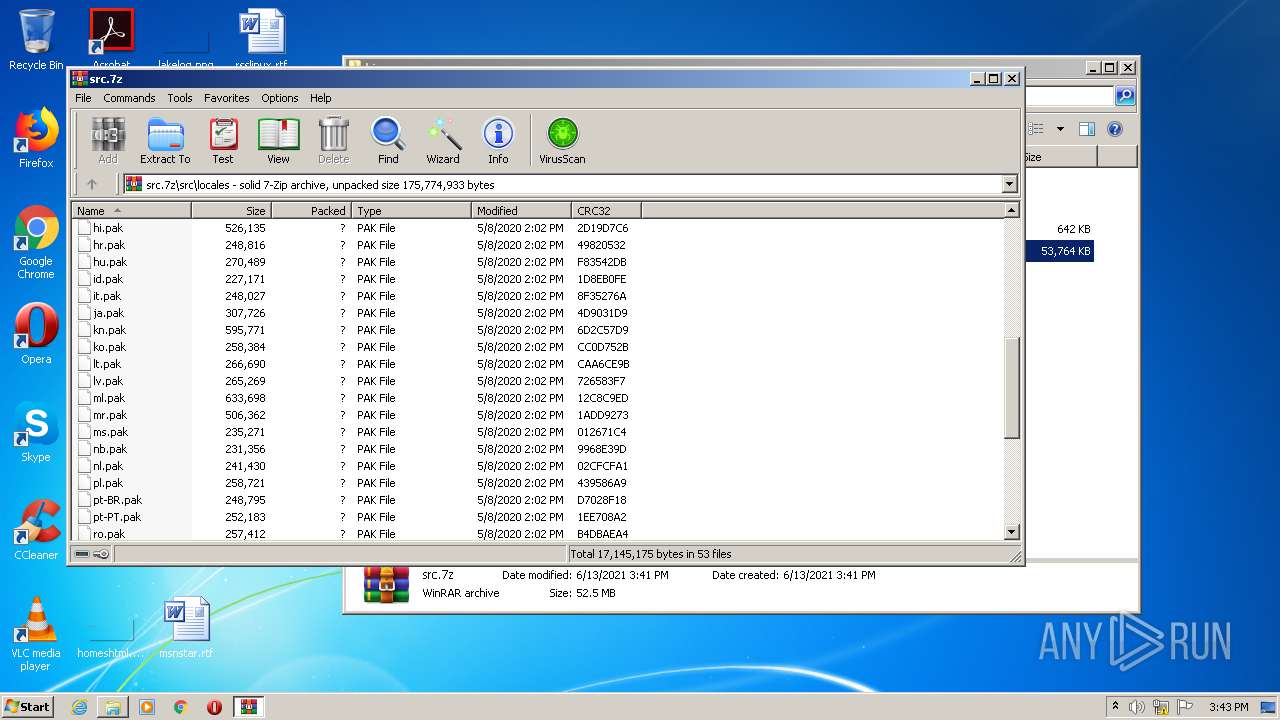
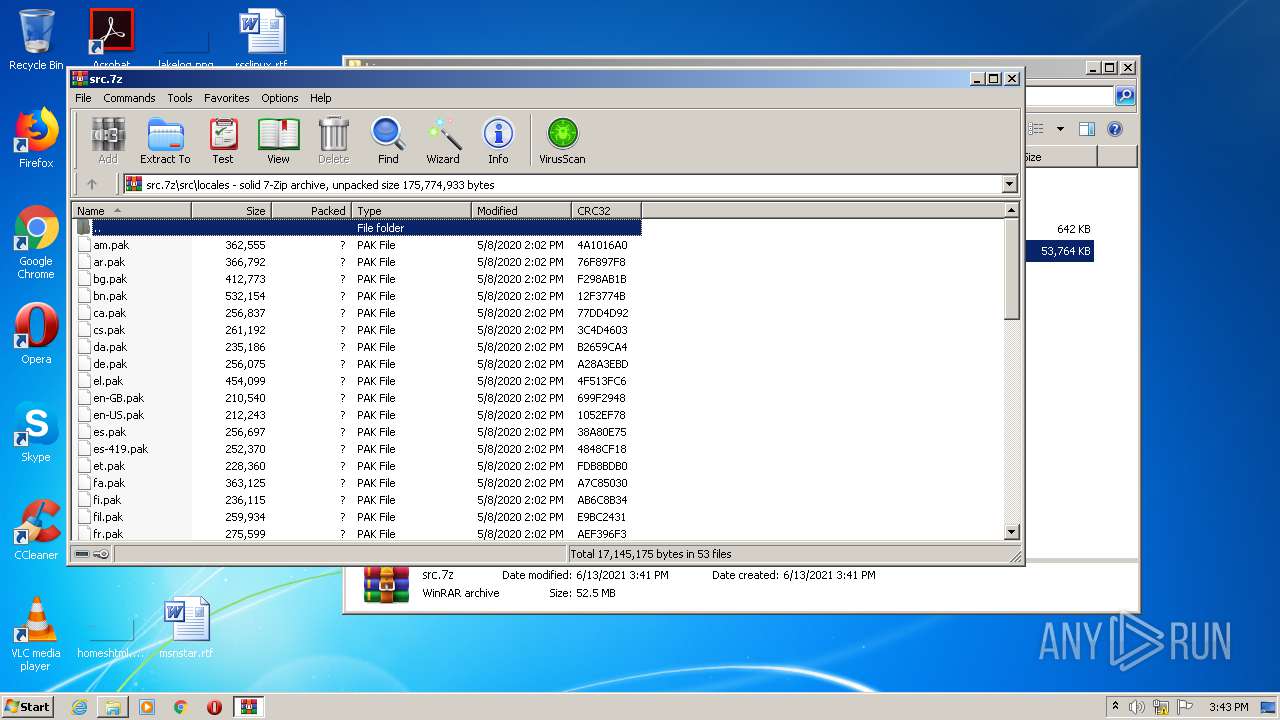
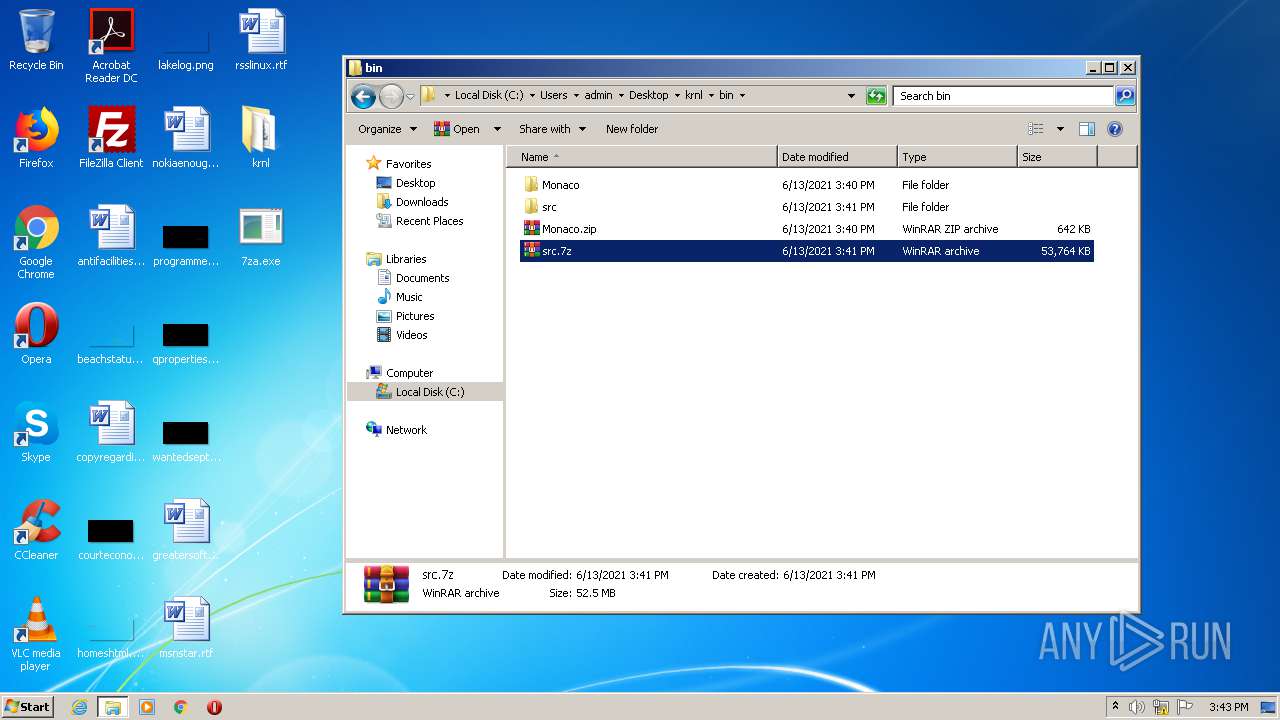
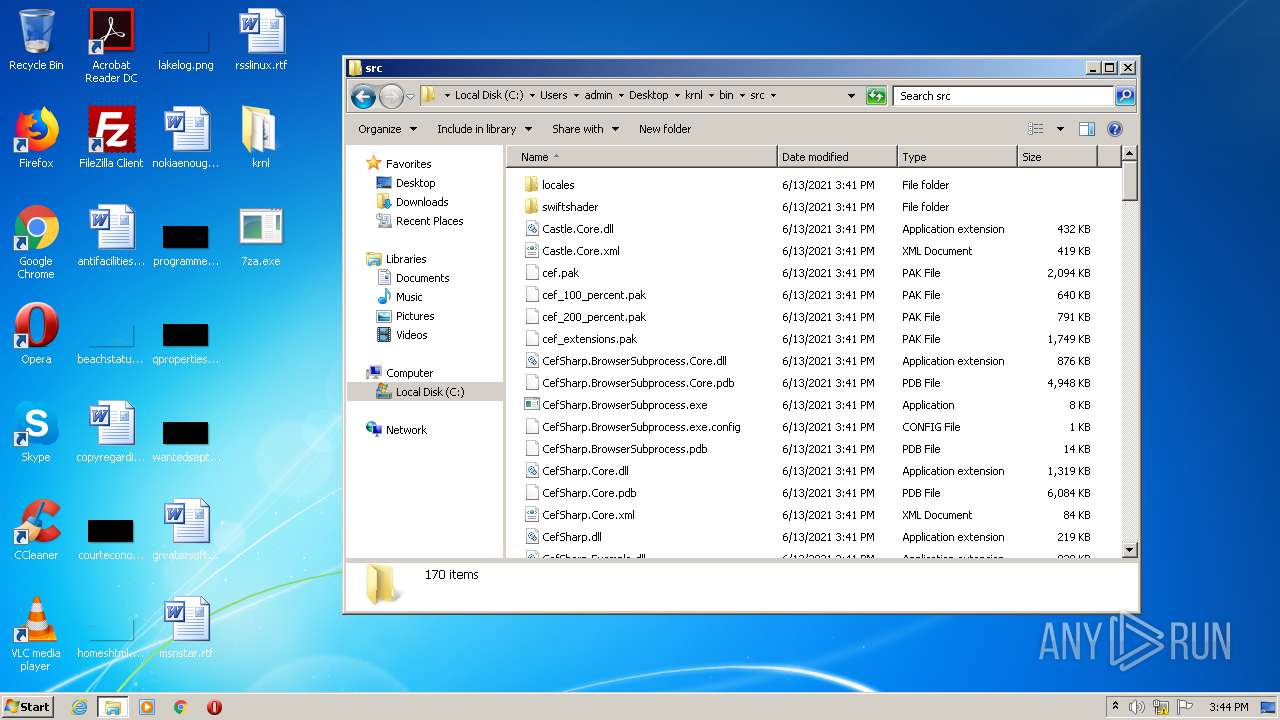
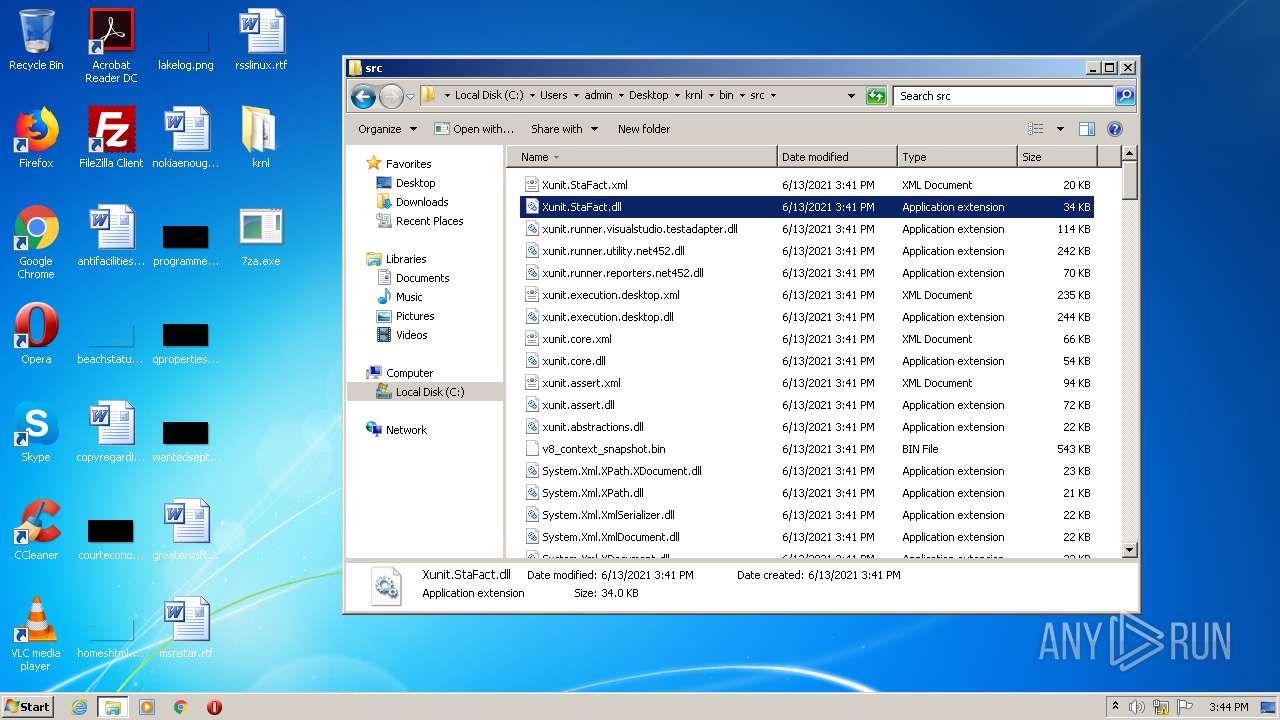
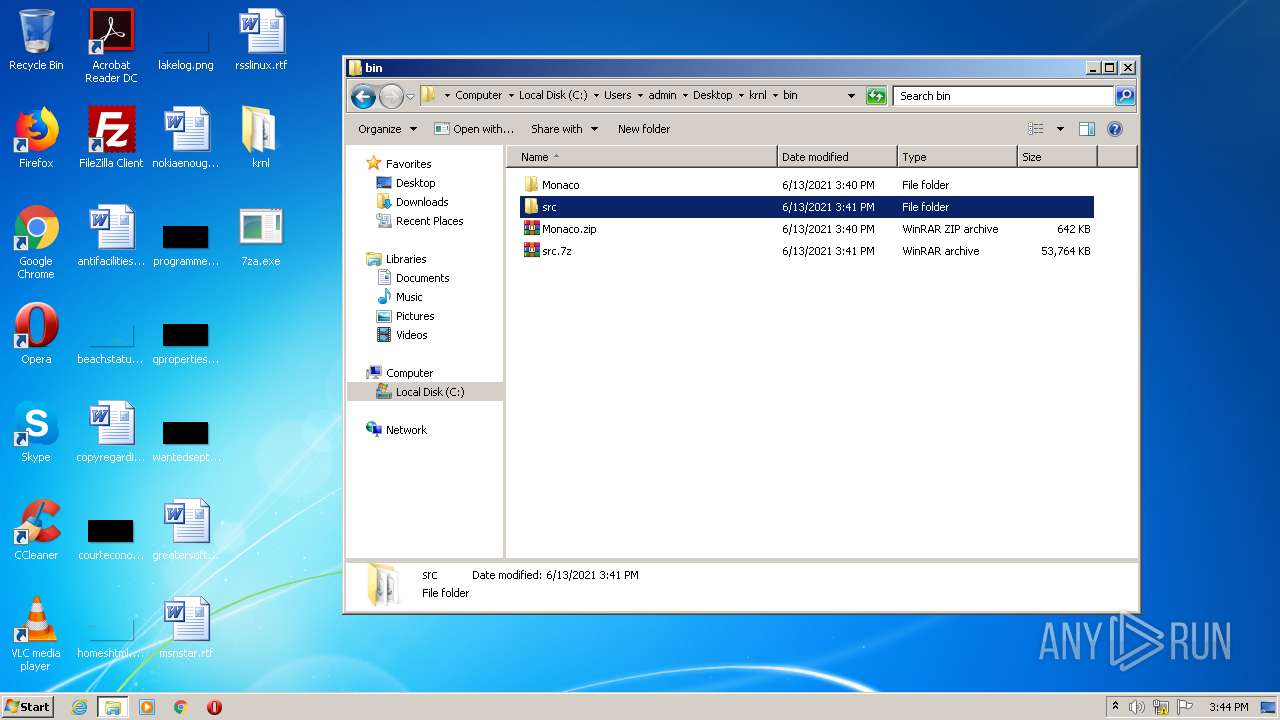
| 1432 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\krnl\bin\src.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
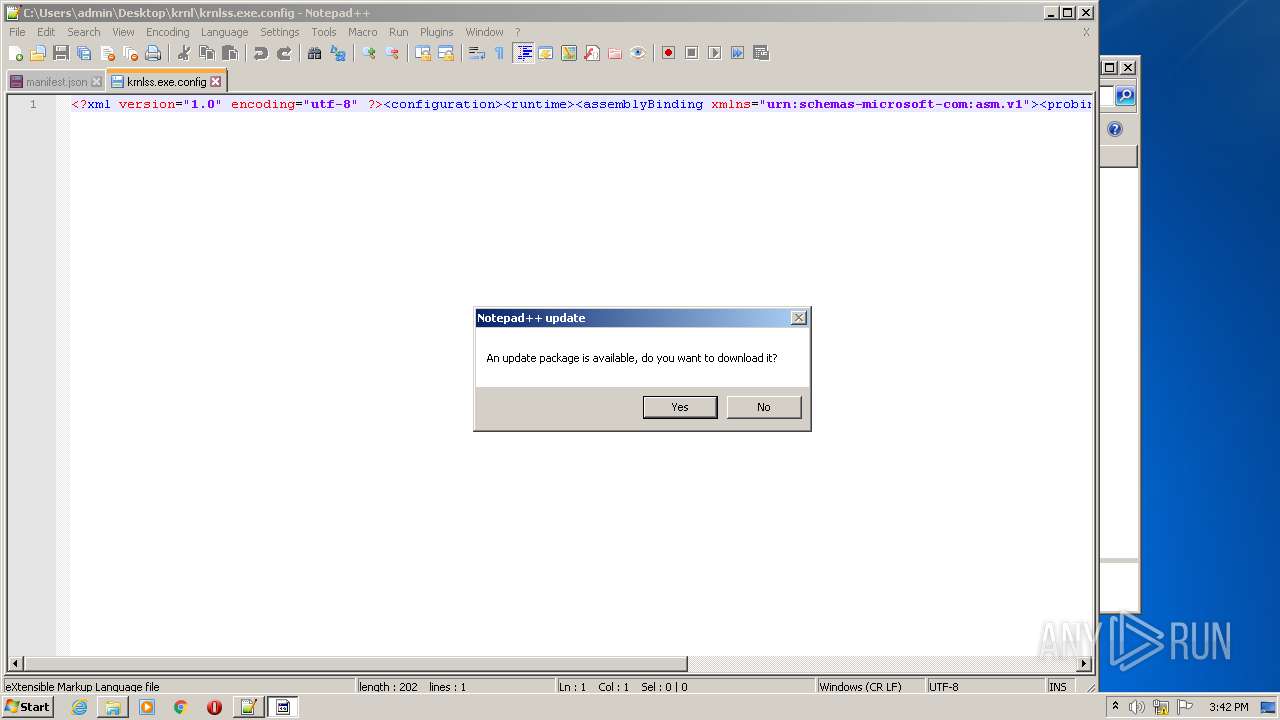
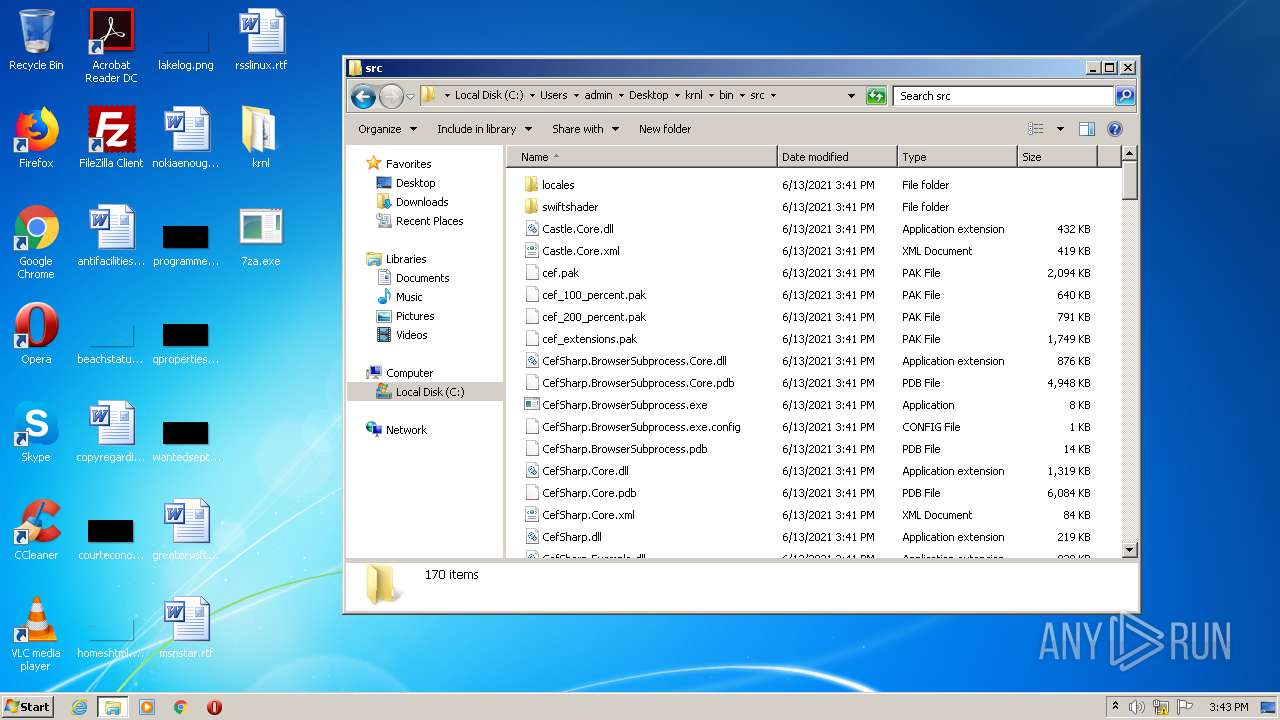
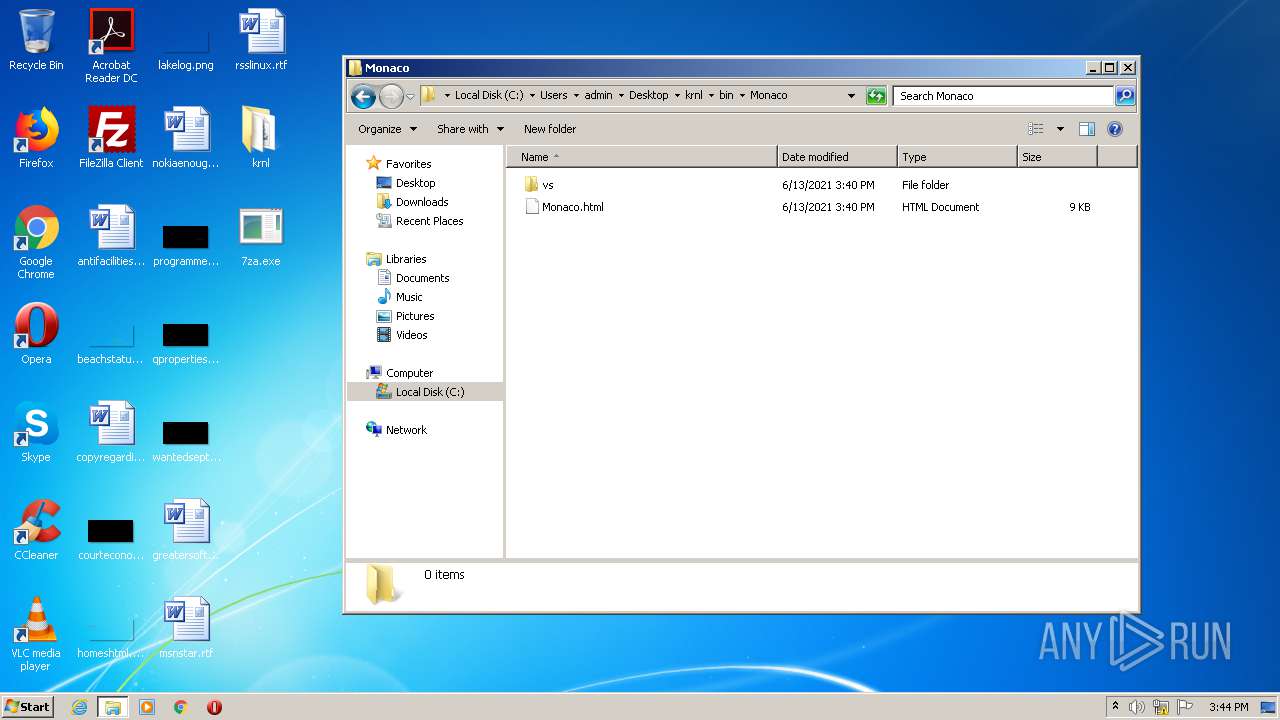
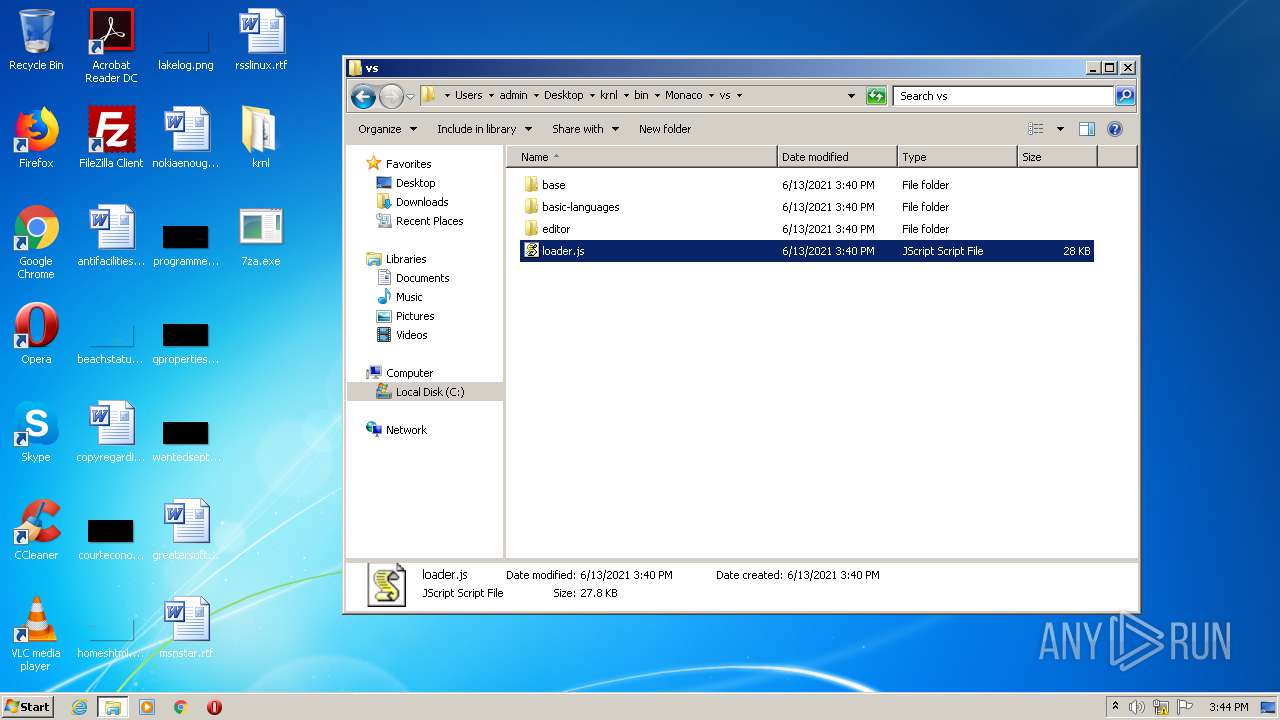
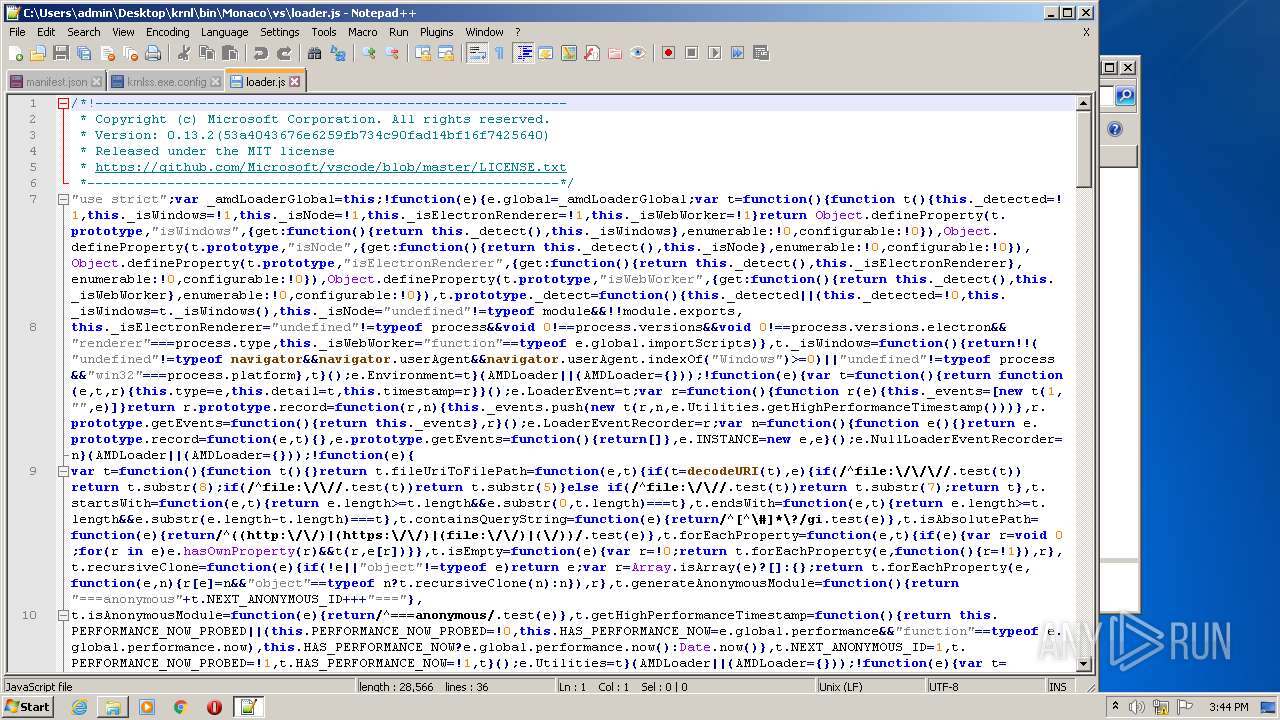
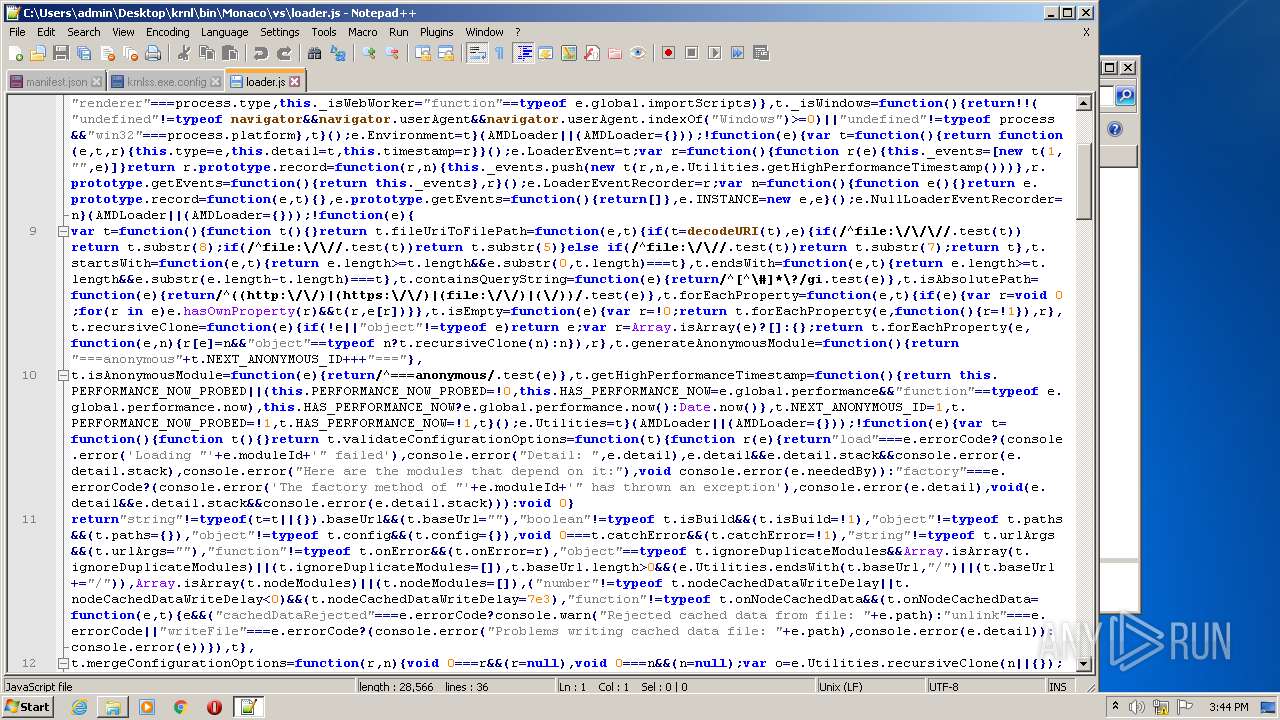
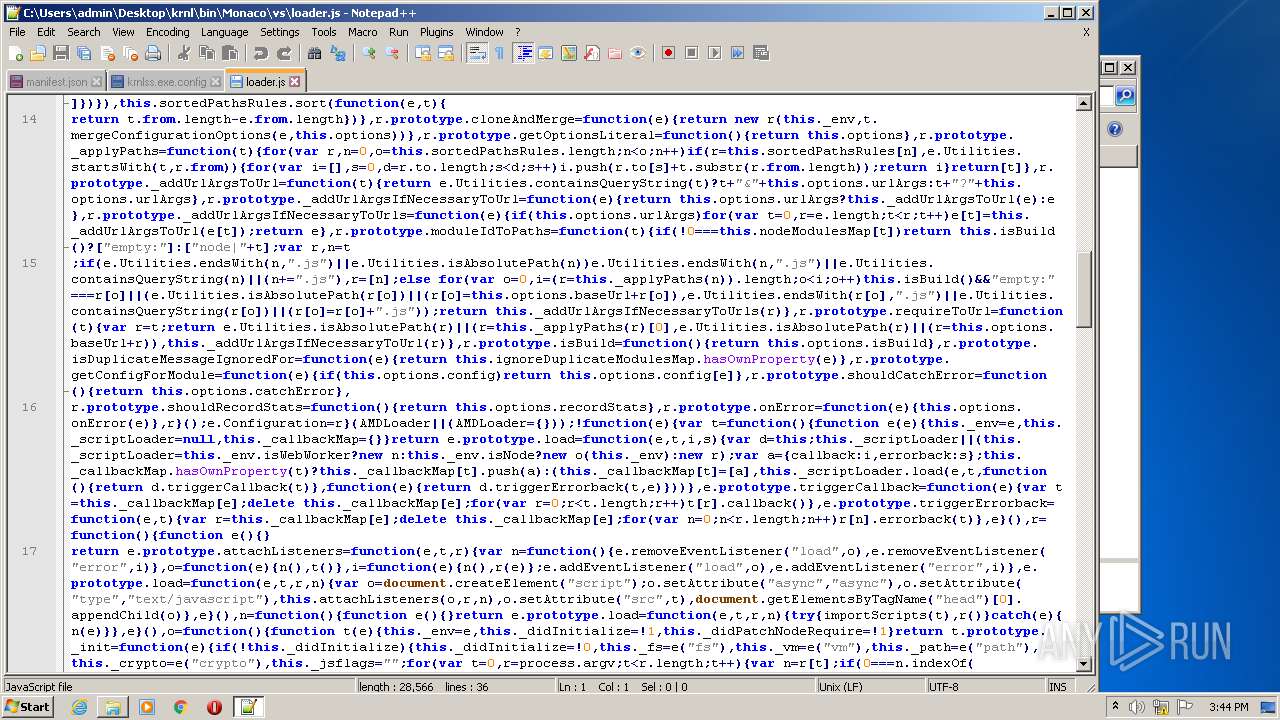
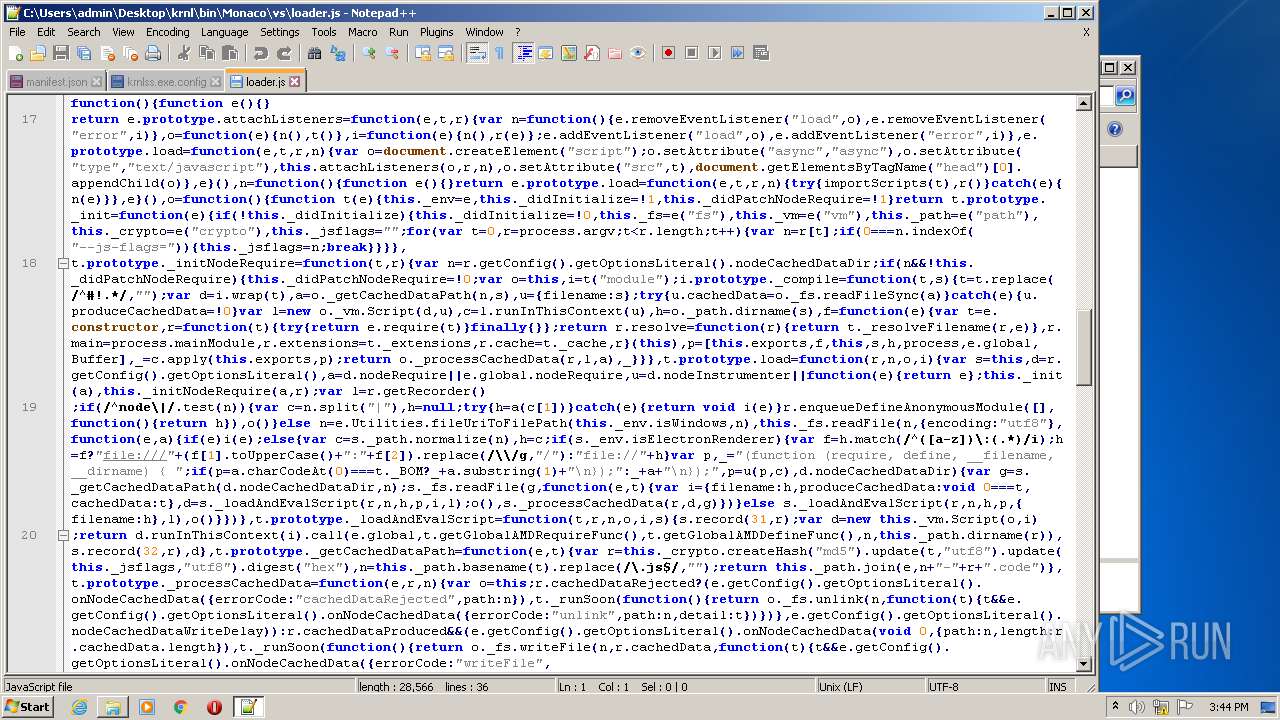
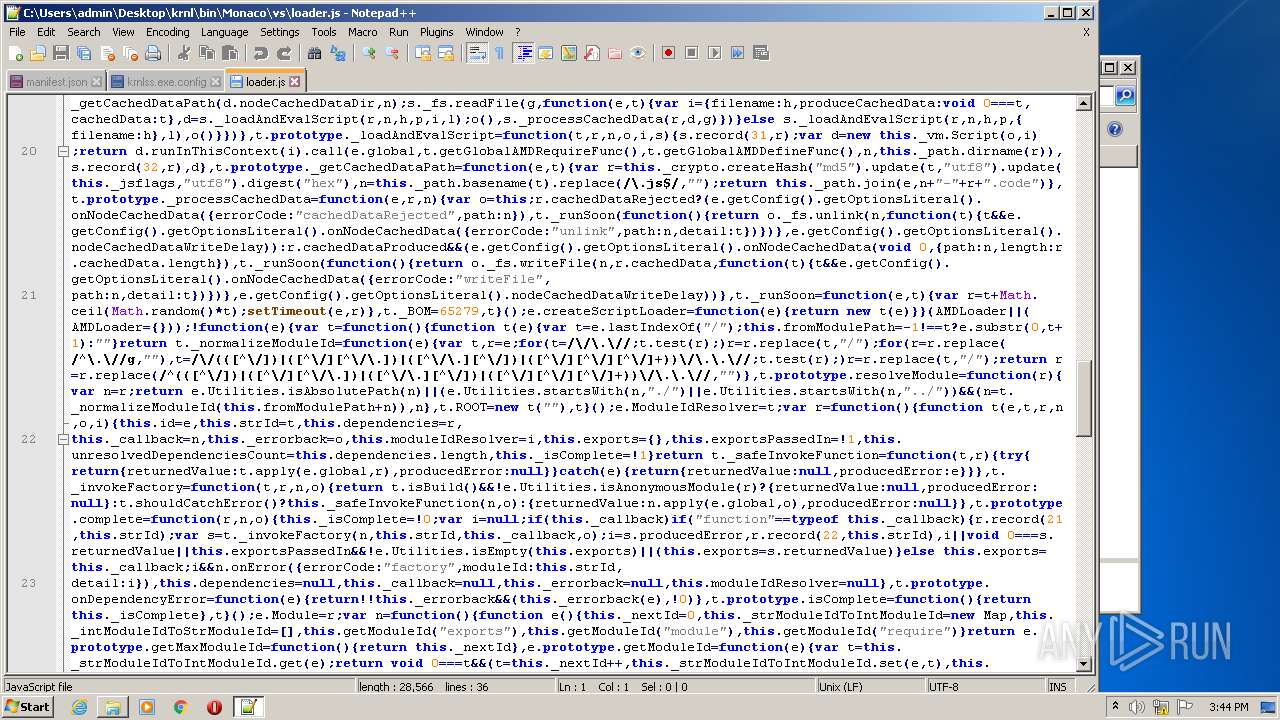
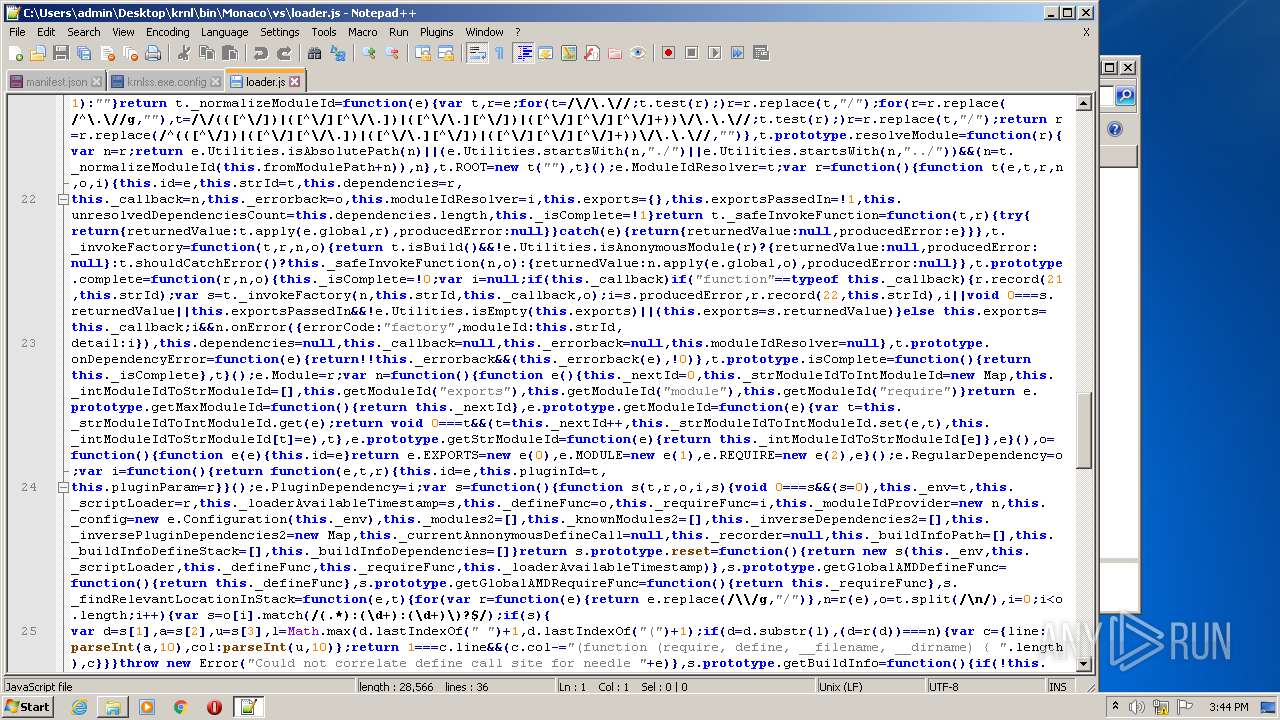
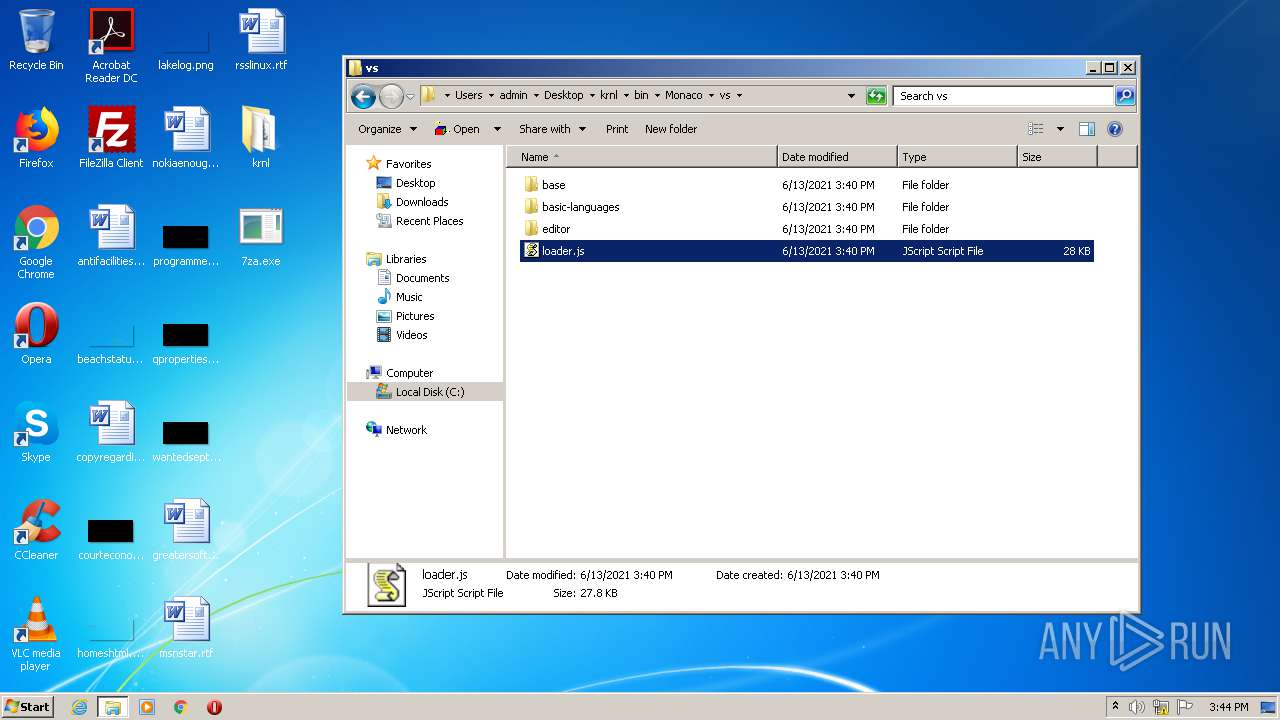
| 1496 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\krnl\bin\Monaco\vs\loader.js" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17138683872150476076,8494448610348441357,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3556436556102527860 --mojo-platform-channel-handle=3432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3516 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,17138683872150476076,8494448610348441357,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15160735135779333942 --mojo-platform-channel-handle=1060 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 003
Read events
3 361
Write events
636
Delete events
6
Modification events
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 59592020 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30892130 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
136
Suspicious files
46
Text files
352
Unknown types
85
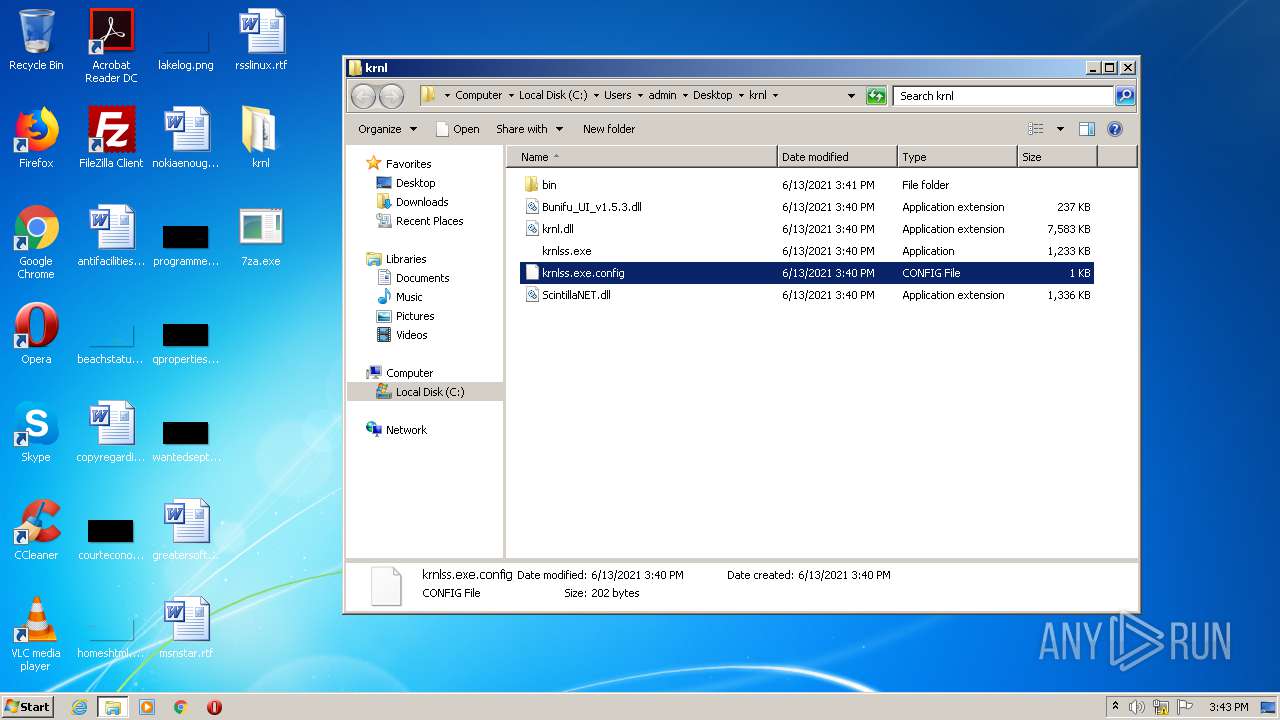
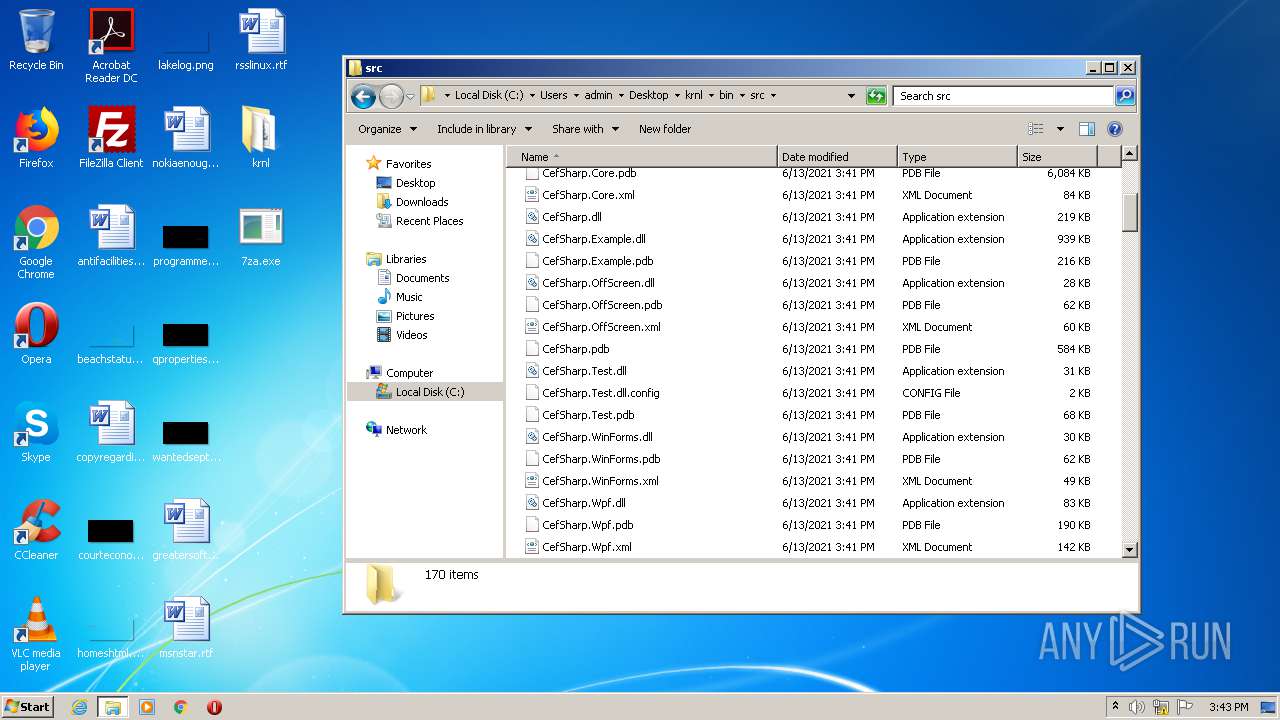
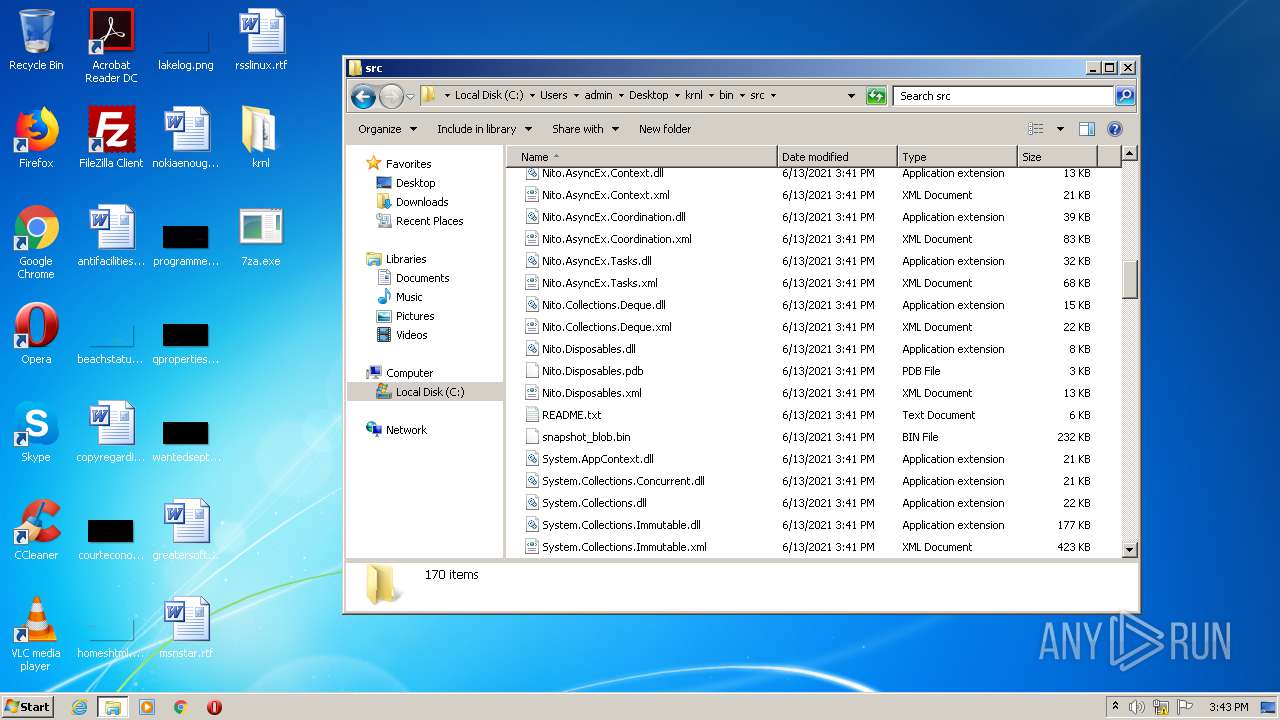
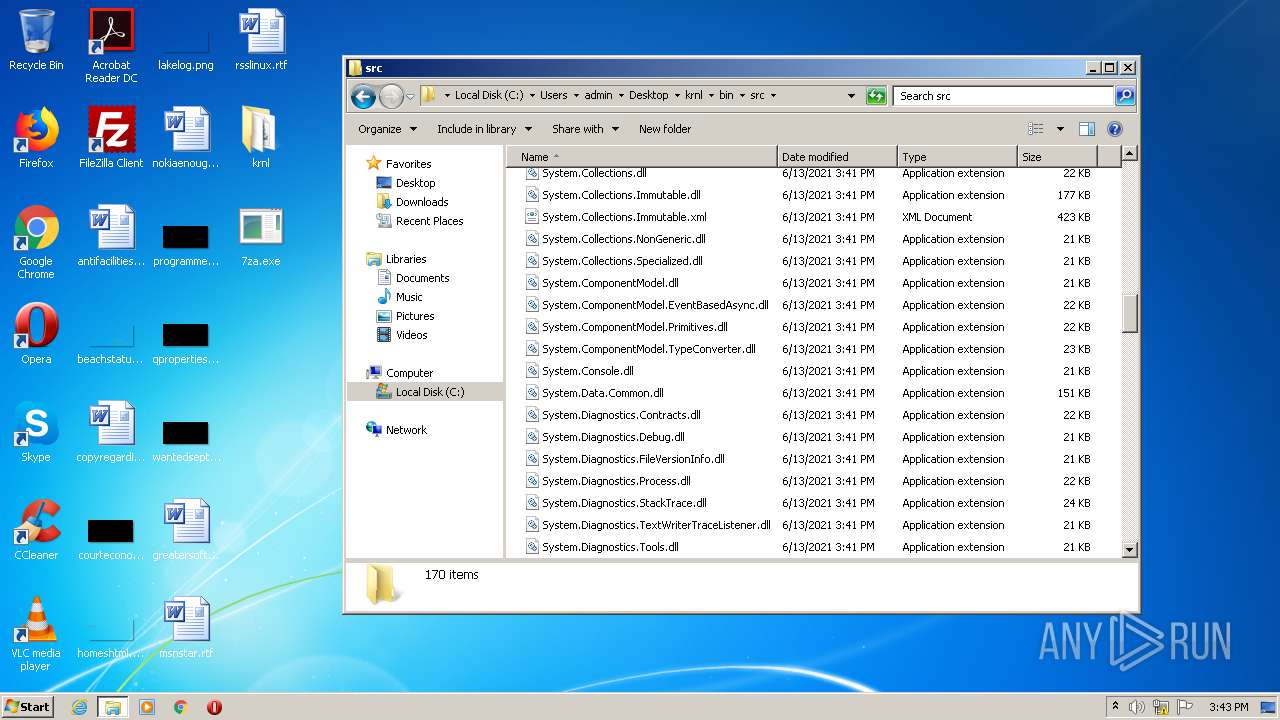
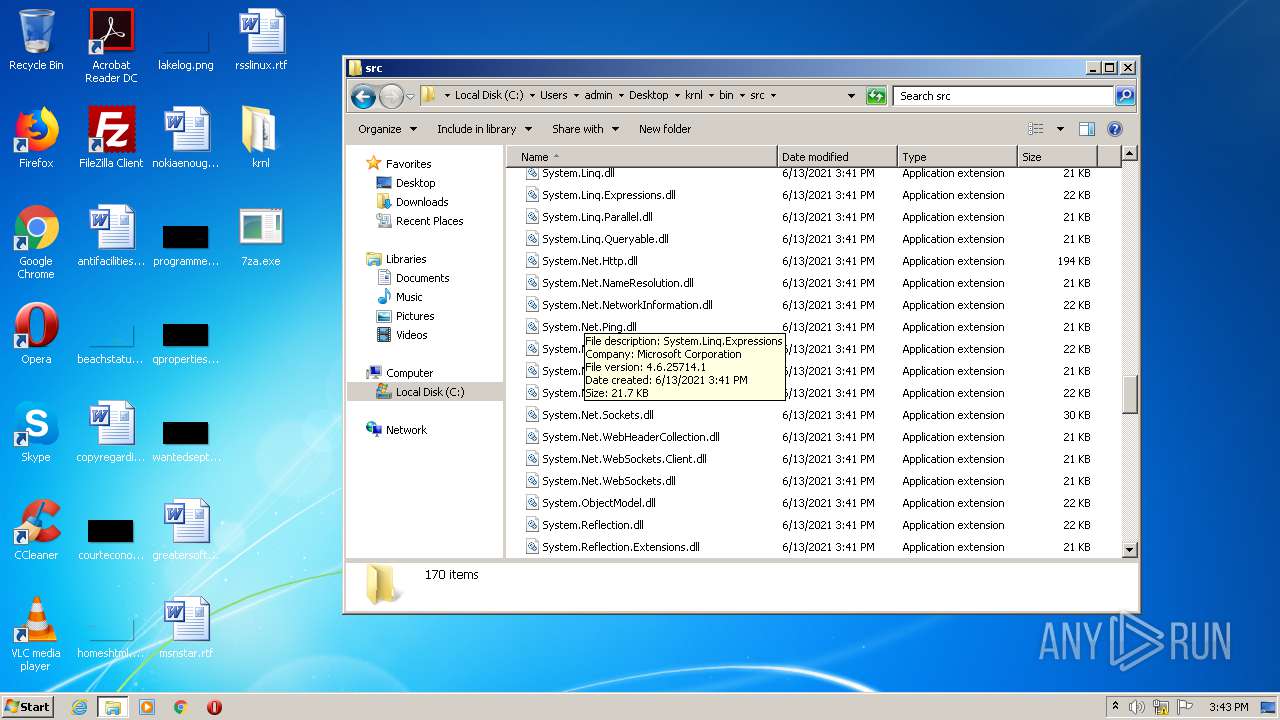
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF521.tmp | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF522.tmp | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\krnl_console_bootstrapper.exe.cb3zlpj.partial | — | |
MD5:— | SHA256:— | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF31B3A183C0D3776B.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\krnl_console_bootstrapper.exe.cb3zlpj.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2292 | krnl_console_bootstrapper.exe | C:\Users\admin\Desktop\krnl_bootstrapper_console_test.txt | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
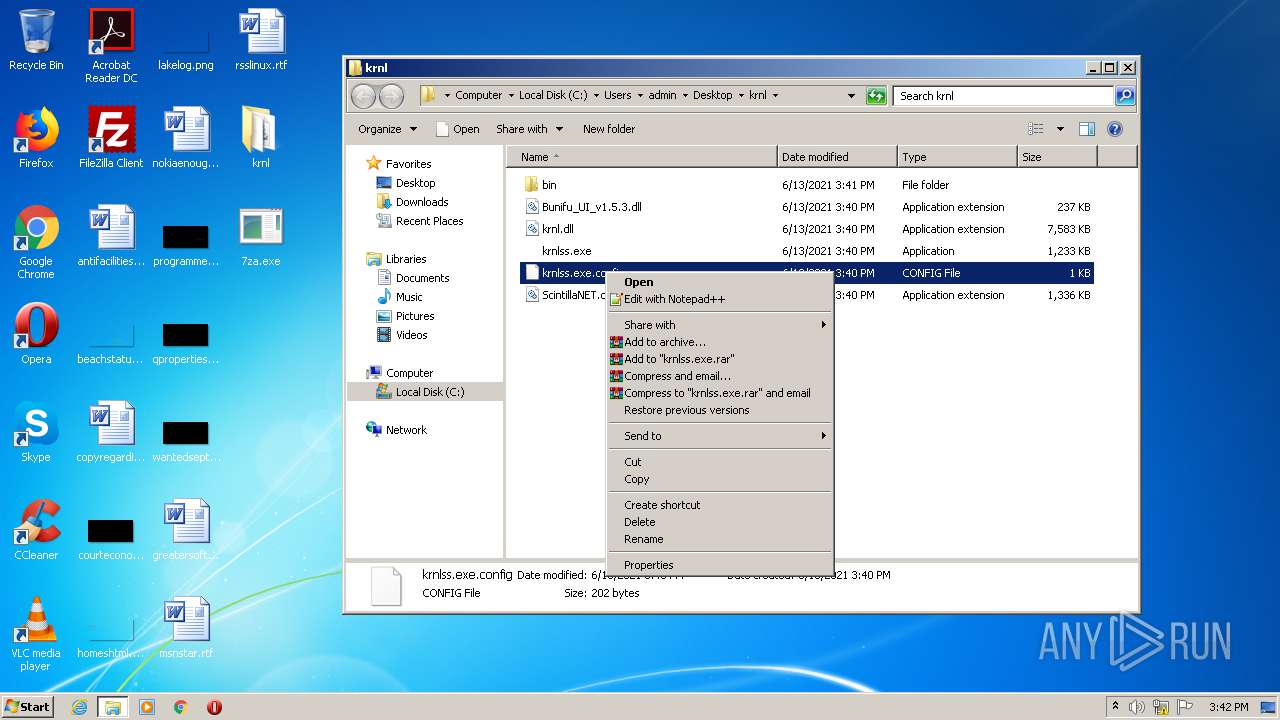
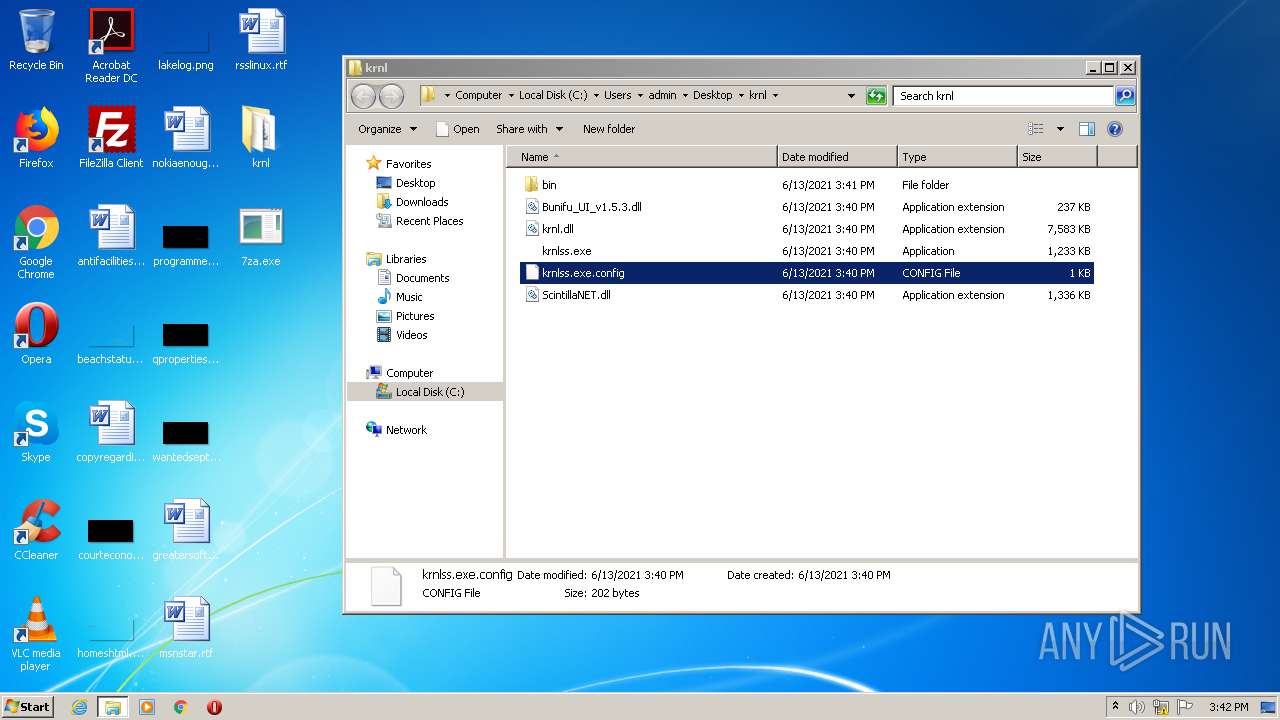
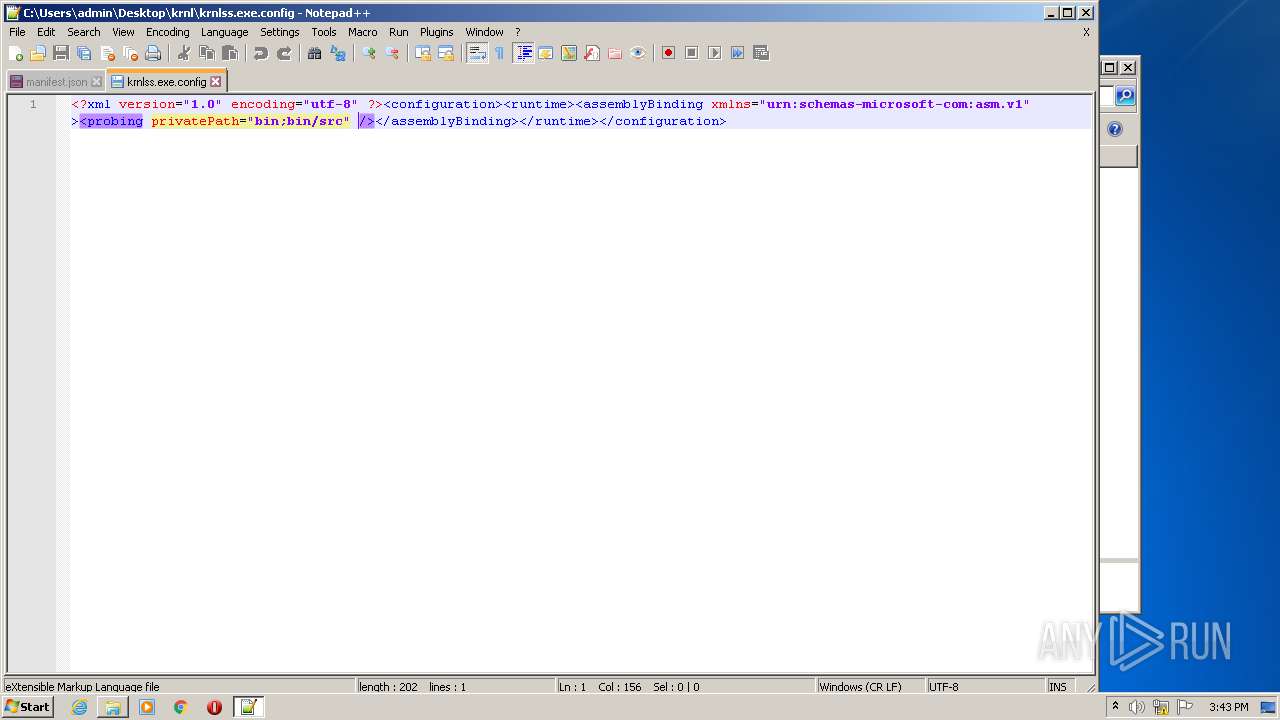
| 2292 | krnl_console_bootstrapper.exe | C:\Users\admin\Desktop\krnl\krnlss.exe.config | xml | |
MD5:0ED4B3831FF5E91DFF636145F68AAC4C | SHA256:03962AE5A55DFC70E2717771A9A7AA37B956B2C5B4C62E3CFF9FE24360250347 | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\krnl_console_bootstrapper.exe | executable | |
MD5:2C037F847CFF23CA356F1D0C443C3647 | SHA256:33AA53BB27EE095F72BBFB206BE36D4DC74A0BAA7DB0246A60221B0F953A11AB | |||
| 2292 | krnl_console_bootstrapper.exe | C:\Users\admin\Desktop\krnl\bin\Monaco\Monaco.html | html | |
MD5:F872D6BB3D3364428DB47E8DB7050D43 | SHA256:0F4292152A1F55A75E7DE8A5DEF919A7DDACFB9A774FD02C4B82C8FA99715E96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
39
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3360 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3360 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2988 | chrome.exe | GET | 302 | 142.250.185.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 593 b | whitelisted |
2988 | chrome.exe | GET | 200 | 173.194.139.202:80 | http://r5---sn-h5q7knes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=45.130.136.10&mm=28&mn=sn-h5q7knes&ms=nvh&mt=1623594978&mv=m&mvi=5&pl=24&rmhost=r3---sn-h5q7knes.gvt1.com&shardbypass=yes&smhost=r3---sn-h5q7knel.gvt1.com | US | crx | 242 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCB1hFTiyruqn | US | binary | 5 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3360 | iexplore.exe | 172.67.208.22:443 | k-storage.com | — | US | unknown |
3360 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2292 | krnl_console_bootstrapper.exe | 172.67.155.145:443 | cdn.krnl.ca | — | US | unknown |
2292 | krnl_console_bootstrapper.exe | 172.67.208.22:443 | k-storage.com | — | US | unknown |
2988 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 142.250.180.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
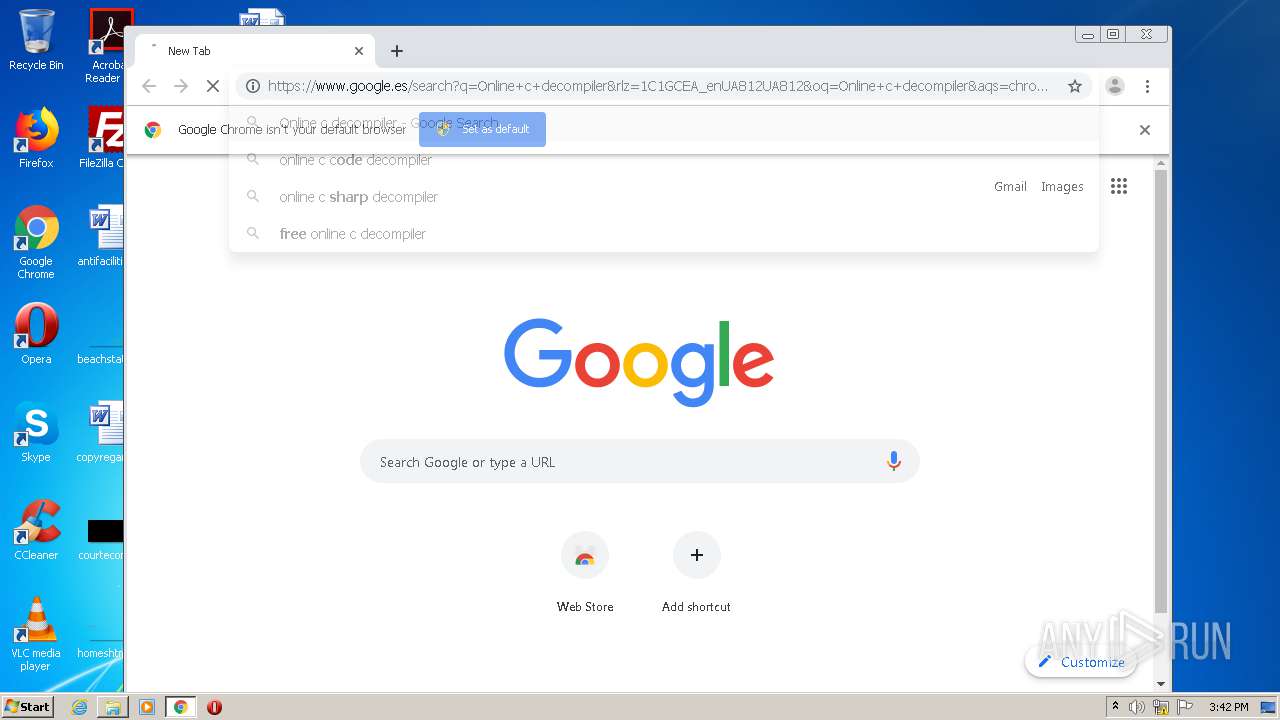
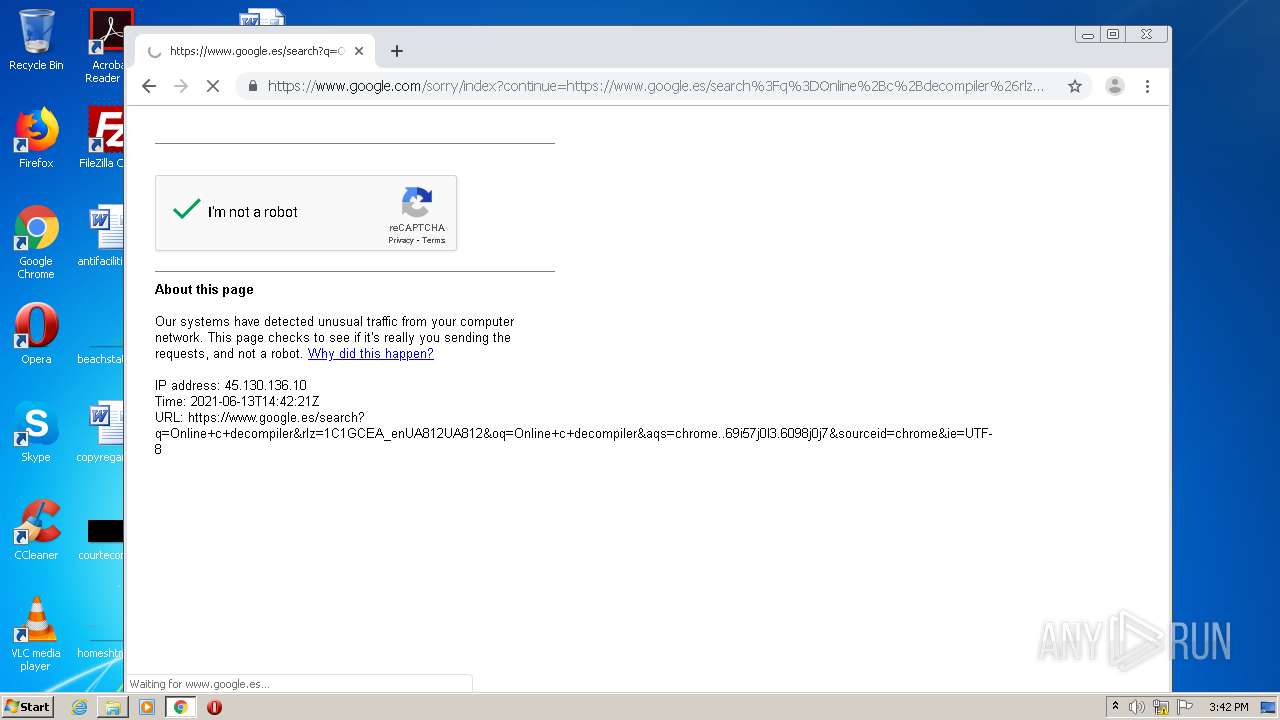
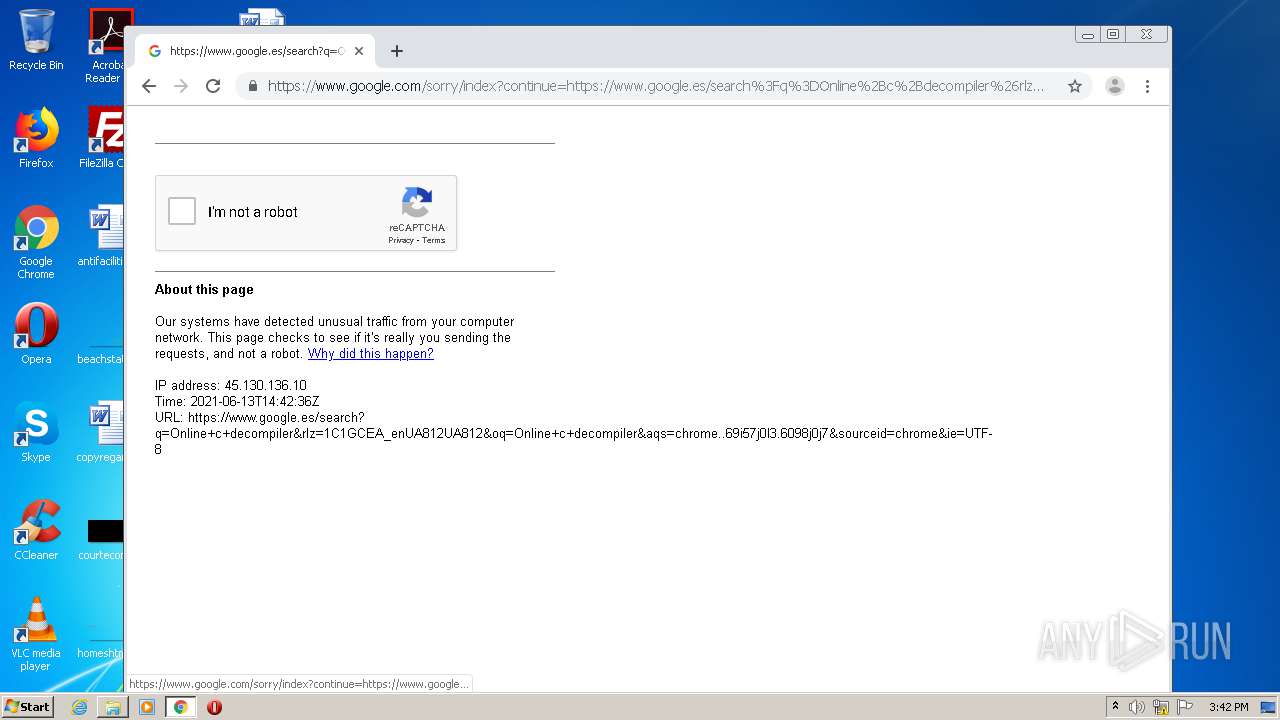
2988 | chrome.exe | 172.217.20.3:443 | www.google.es | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.19.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
k-storage.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
cdn.krnl.ca |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |