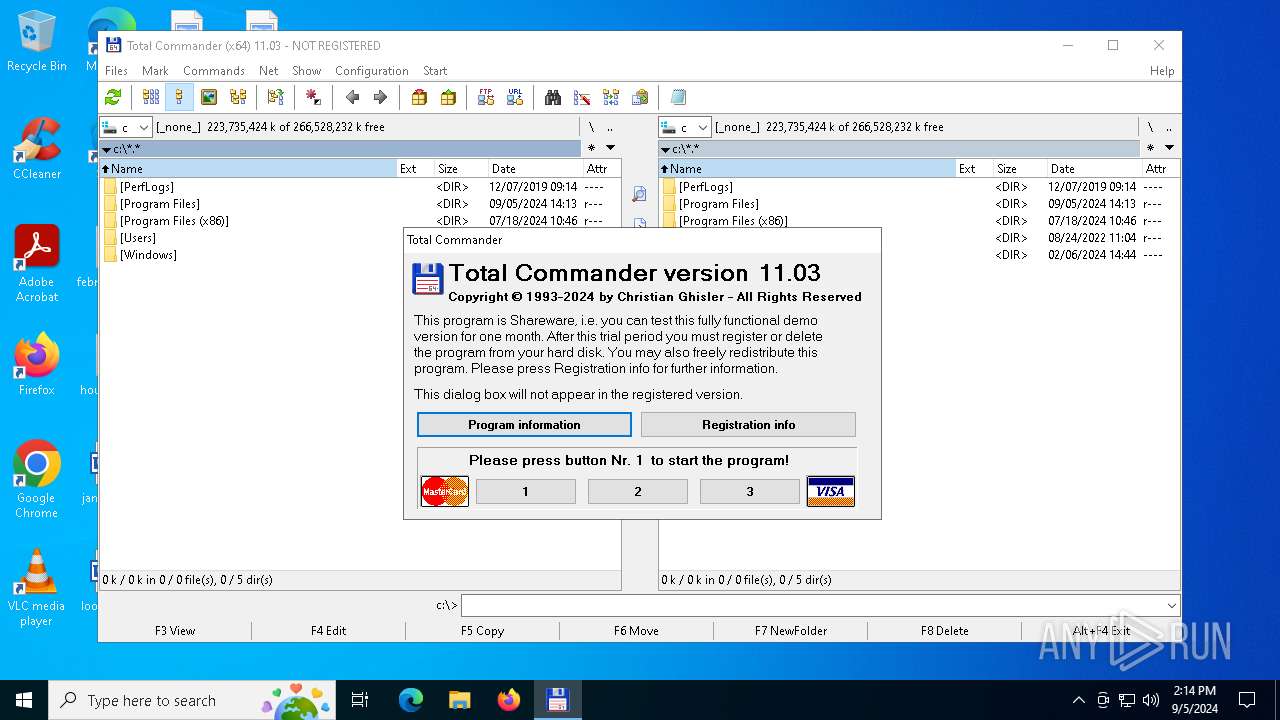
| File name: | tcmd1103x64.exe |
| Full analysis: | https://app.any.run/tasks/925ed7b4-2cb4-46af-9543-755fd796faf5 |
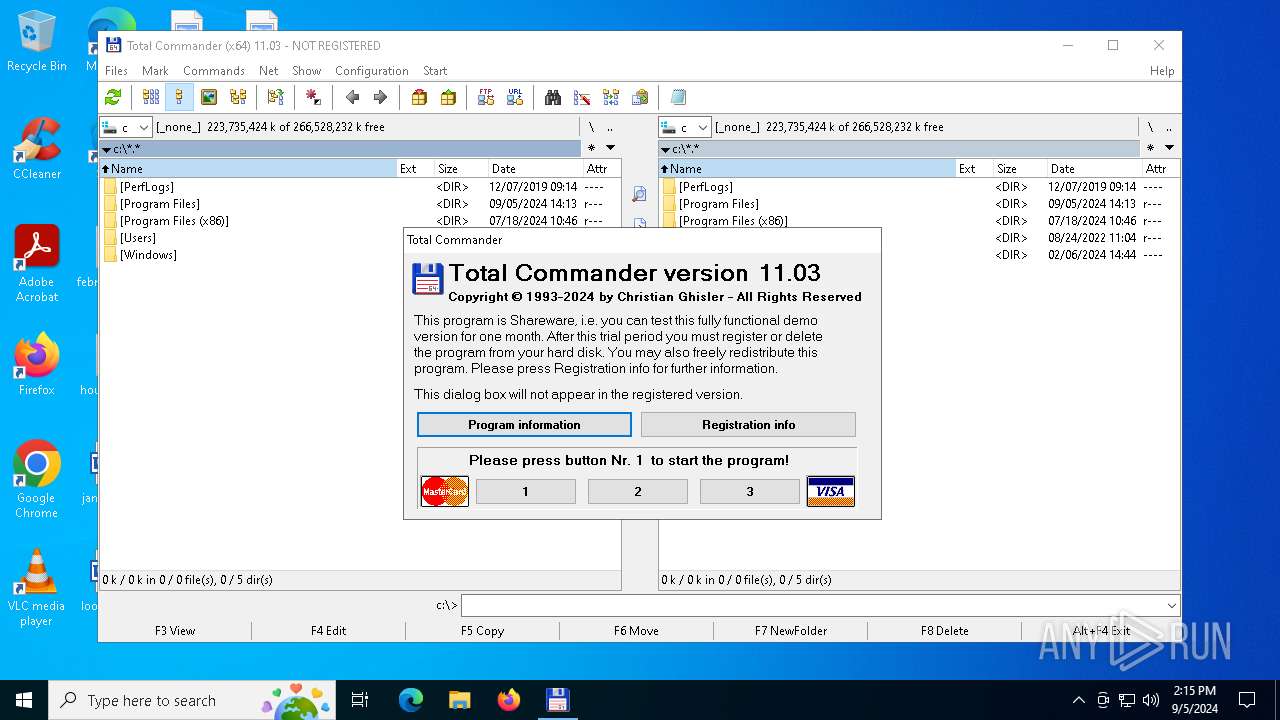
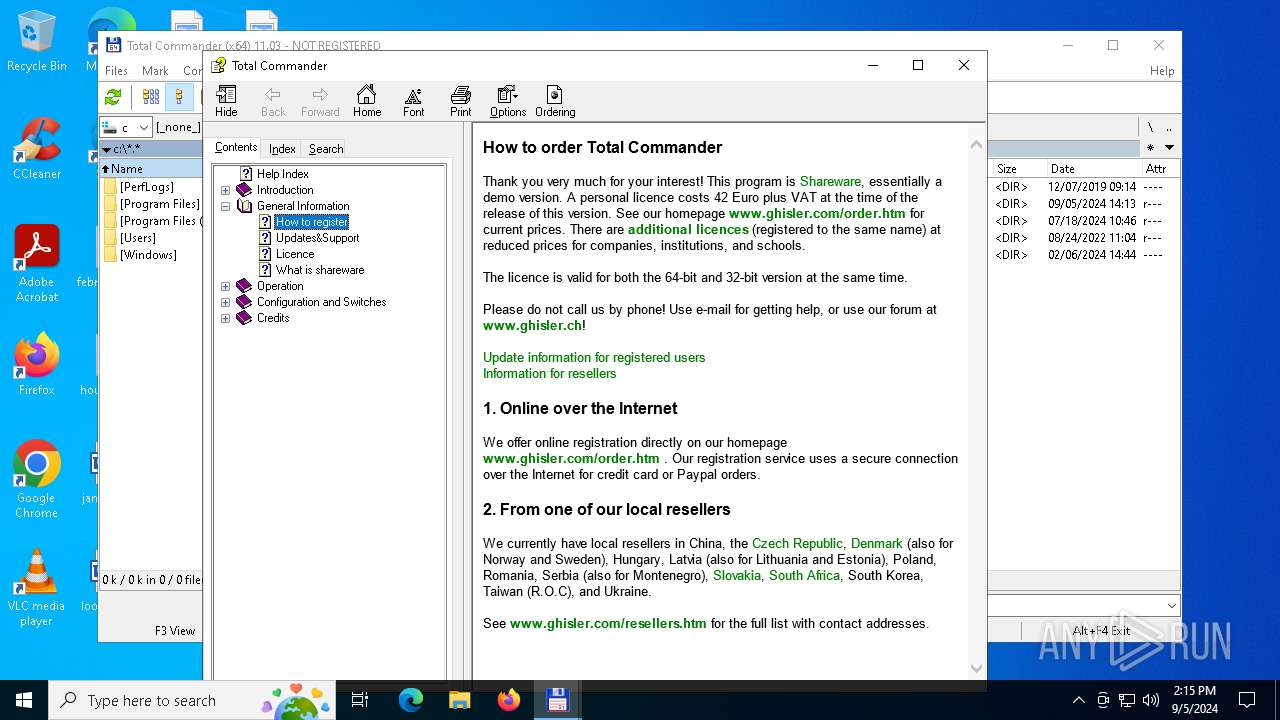
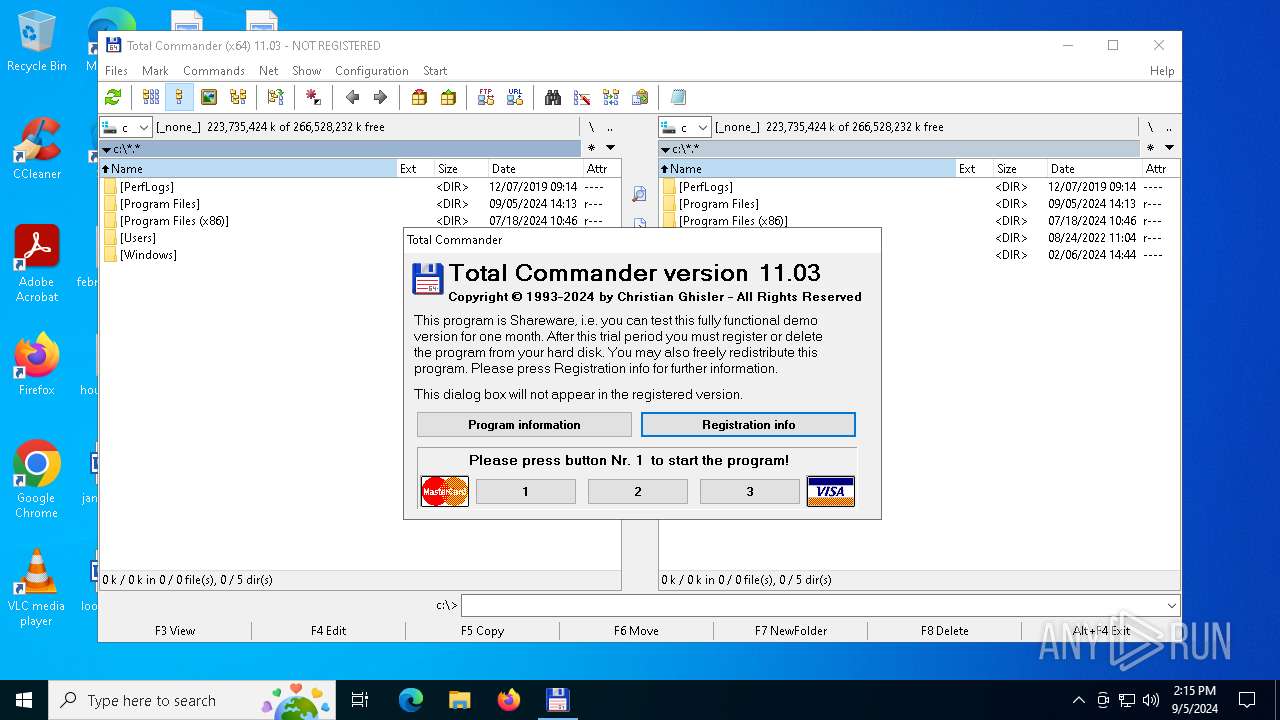
| Verdict: | Malicious activity |
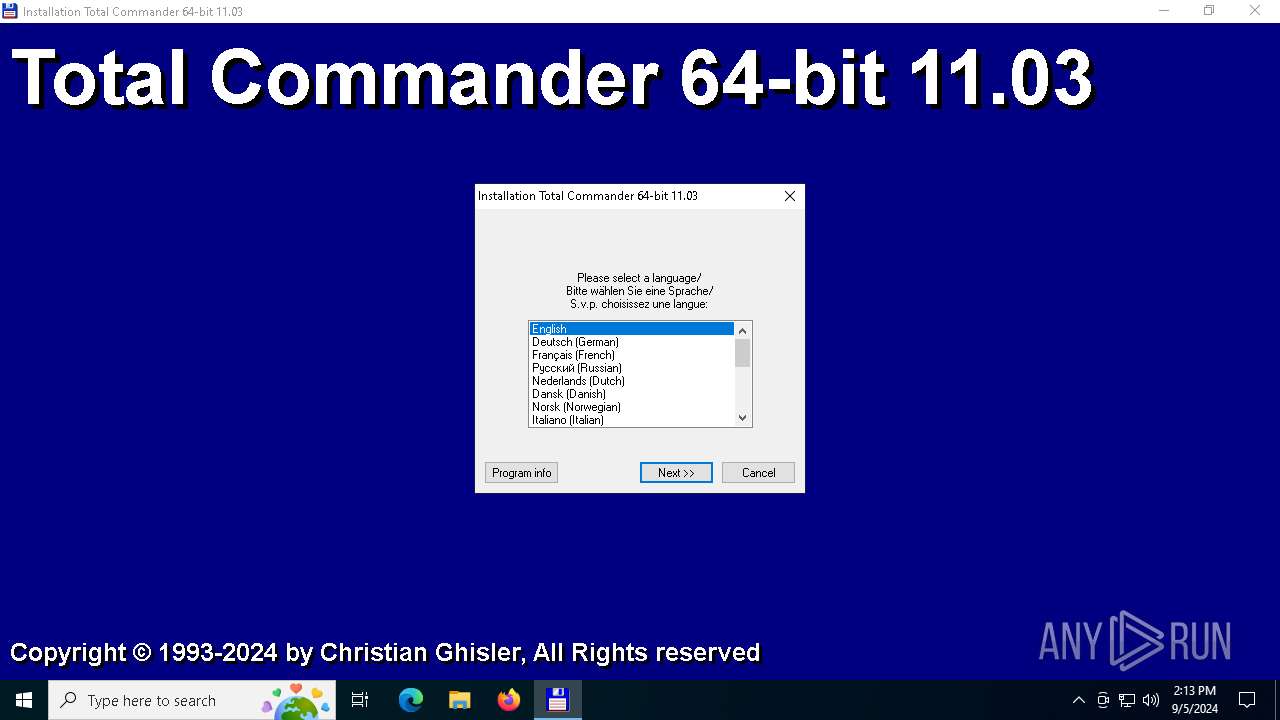
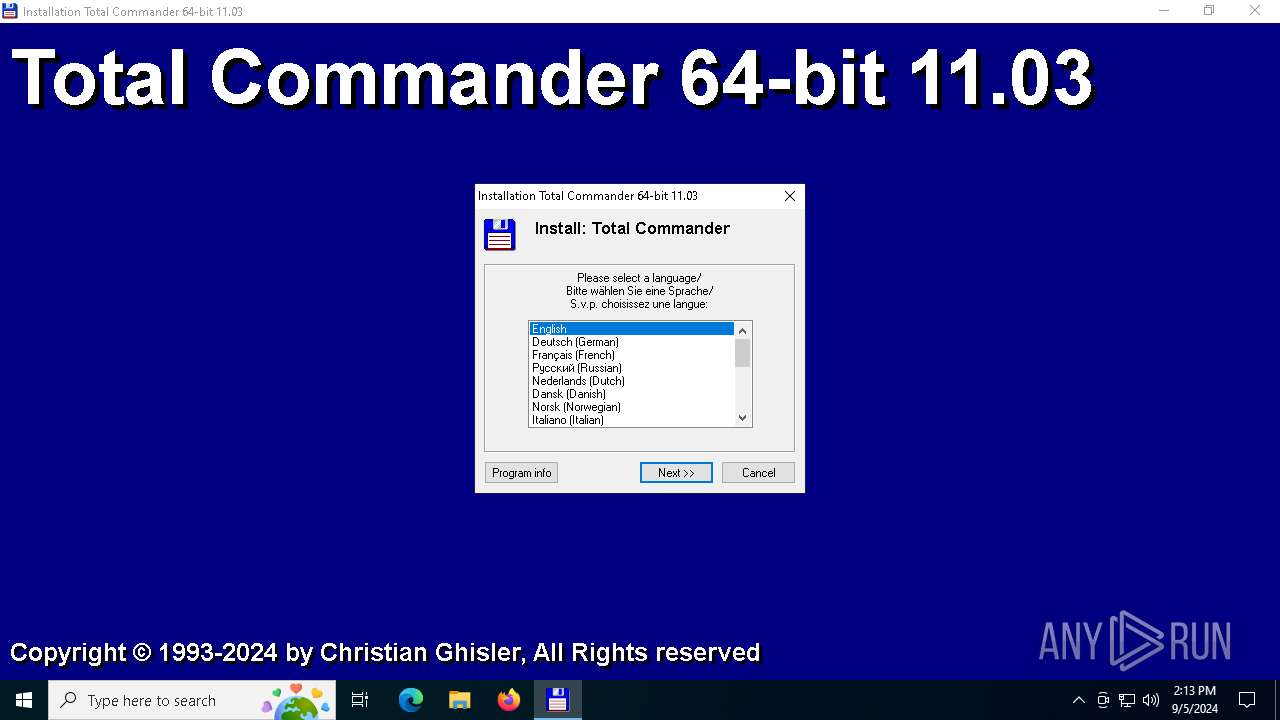
| Analysis date: | September 05, 2024, 14:13:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, InstallShield self-extracting archive |
| MD5: | 2BC1009B18915F773803AA5CE0C8C5AA |
| SHA1: | E7CE87C81DA0ED4EDA263C0BC1A6E87EA2F5B6EC |
| SHA256: | D1B9E3A7E548EEDBBE122287B8589F1EB42023F77E8F7D6856DC1644F038F617 |
| SSDEEP: | 98304:iLN9adTPCNVz04b8KweSkGq/iXHsmOPZa9XKXtICIatAEOhLP88KFs7FmhnwEpJa:ukevjpuYgUYf9zQh2D |
MALICIOUS
No malicious indicators.SUSPICIOUS
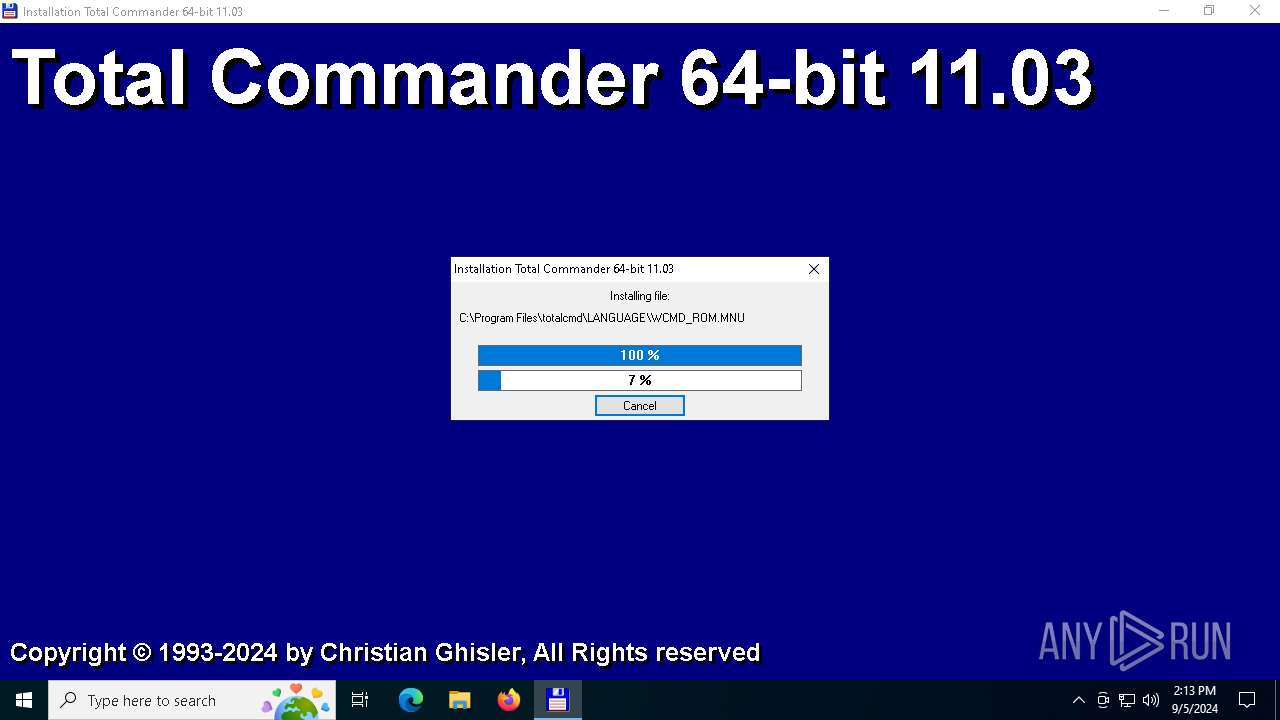
Executable content was dropped or overwritten
- tcmd1103x64.exe (PID: 3728)
Drops 7-zip archiver for unpacking
- tcmd1103x64.exe (PID: 3728)
Reads security settings of Internet Explorer
- TOTALCMD64.EXE (PID: 3208)
Reads Microsoft Outlook installation path
- TOTALCMD64.EXE (PID: 3208)
Reads Internet Explorer settings
- TOTALCMD64.EXE (PID: 3208)
Drops a system driver (possible attempt to evade defenses)
- tcmd1103x64.exe (PID: 3728)
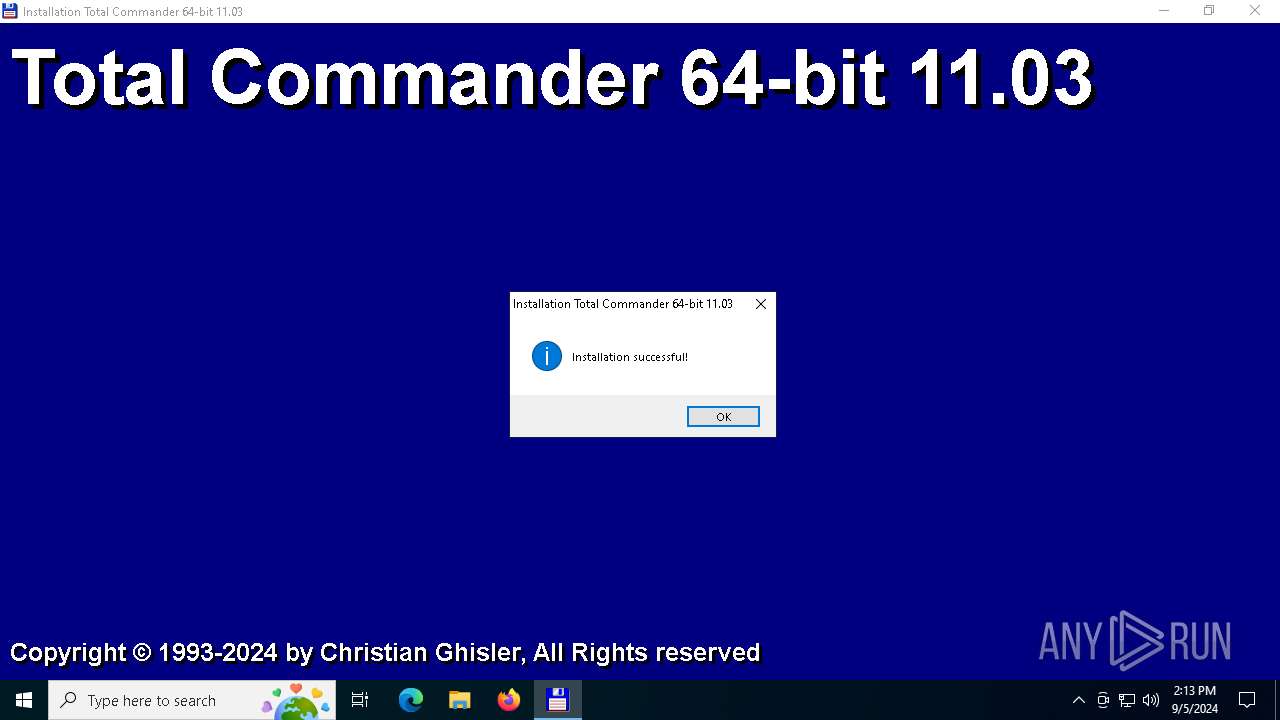
Creates a software uninstall entry
- tcmd1103x64.exe (PID: 3728)
INFO
Checks supported languages
- tcmd1103x64.exe (PID: 3728)
- TOTALCMD64.EXE (PID: 1020)
- TOTALCMD64.EXE (PID: 3208)
- TOTALCMD64.EXE (PID: 1640)
Reads the computer name
- tcmd1103x64.exe (PID: 3728)
- TOTALCMD64.EXE (PID: 3208)
- TOTALCMD64.EXE (PID: 1640)
- TOTALCMD64.EXE (PID: 1020)
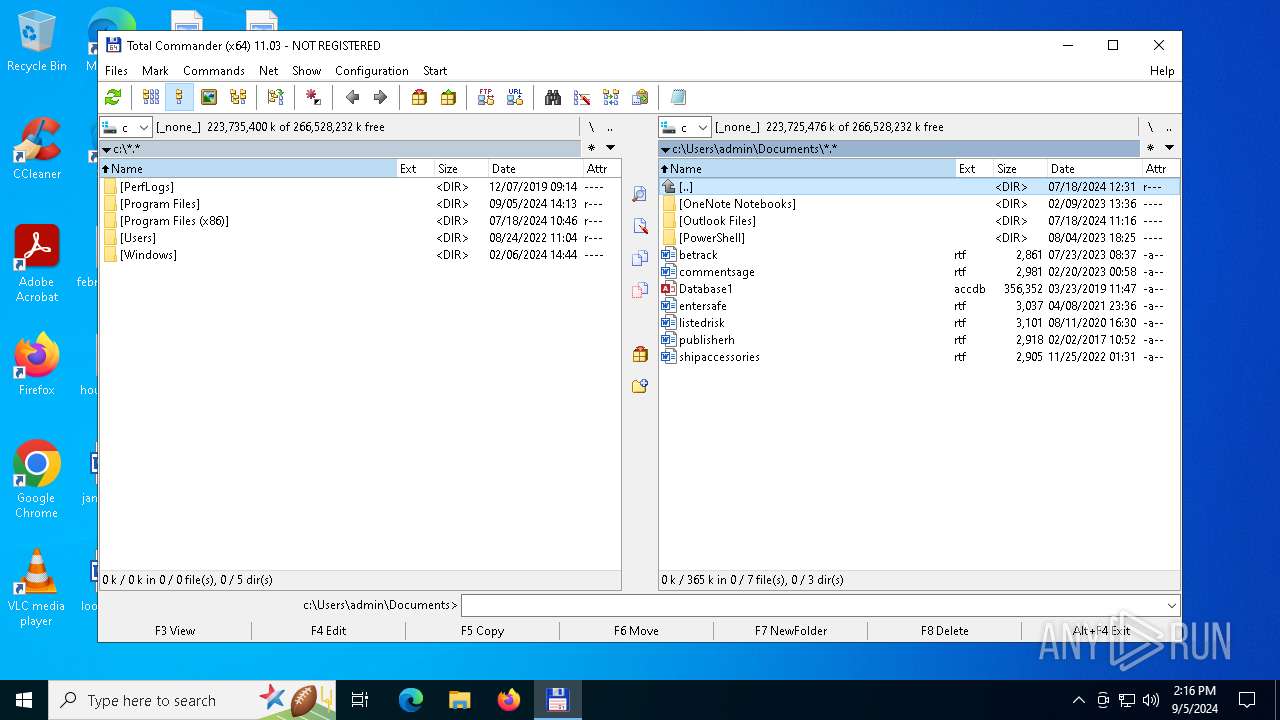
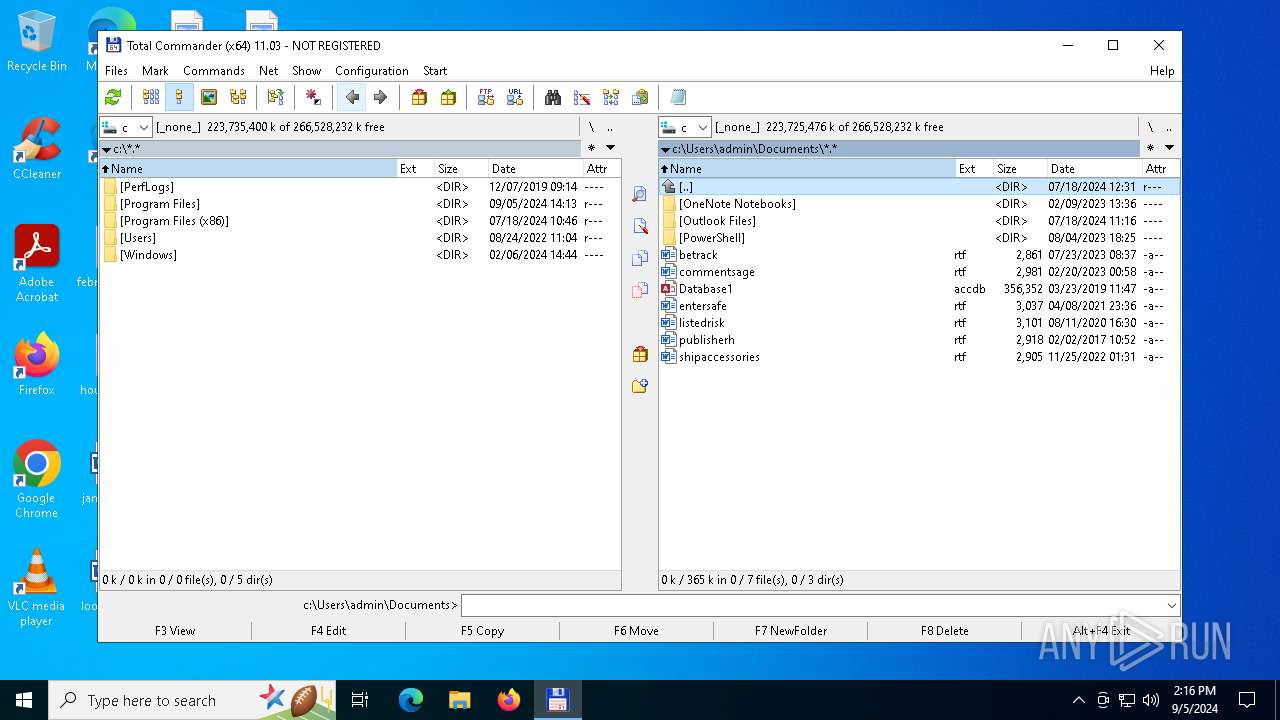
Creates files or folders in the user directory
- tcmd1103x64.exe (PID: 3728)
- TOTALCMD64.EXE (PID: 1020)
- TOTALCMD64.EXE (PID: 3208)
Process checks whether UAC notifications are on
- TOTALCMD64.EXE (PID: 3208)
- TOTALCMD64.EXE (PID: 1640)
- TOTALCMD64.EXE (PID: 1020)
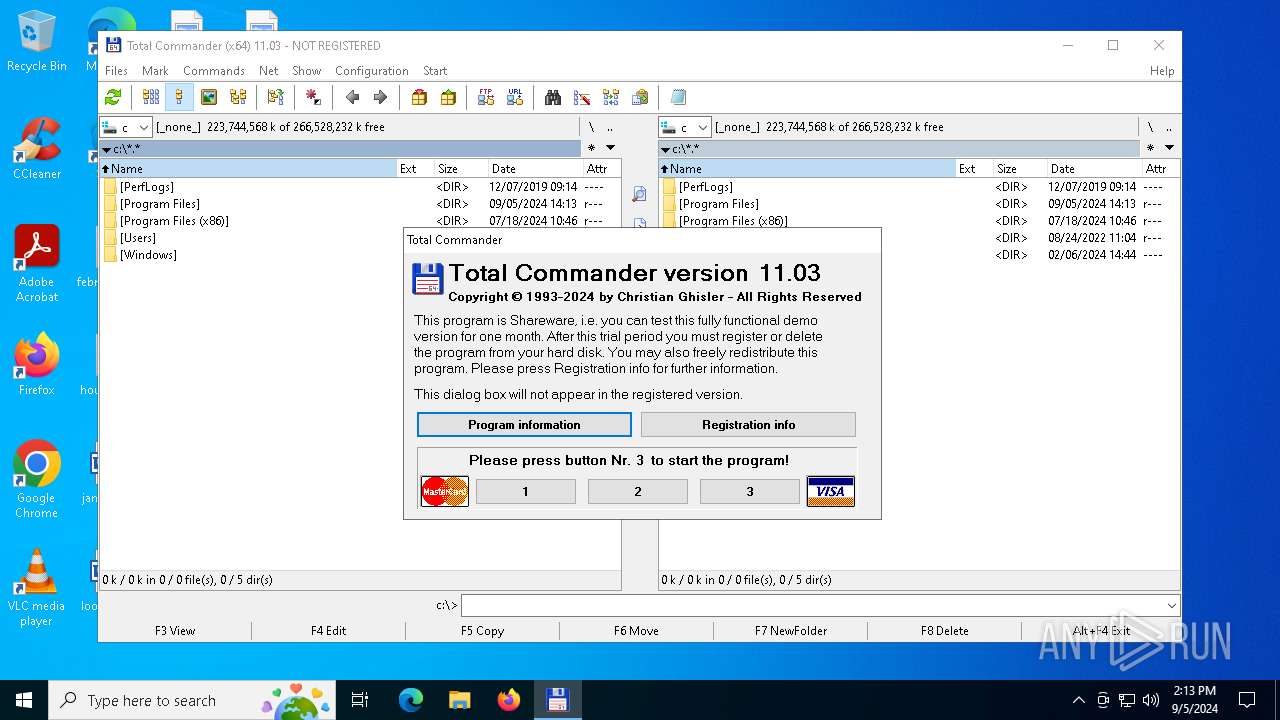
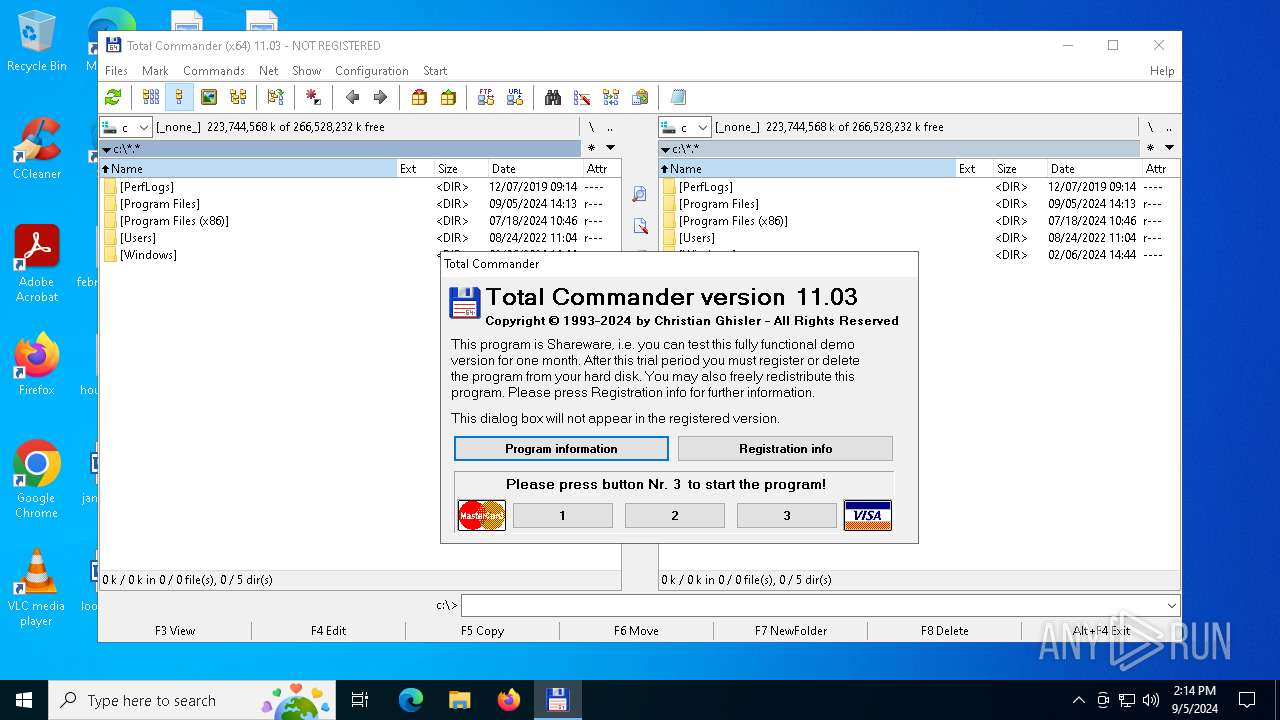
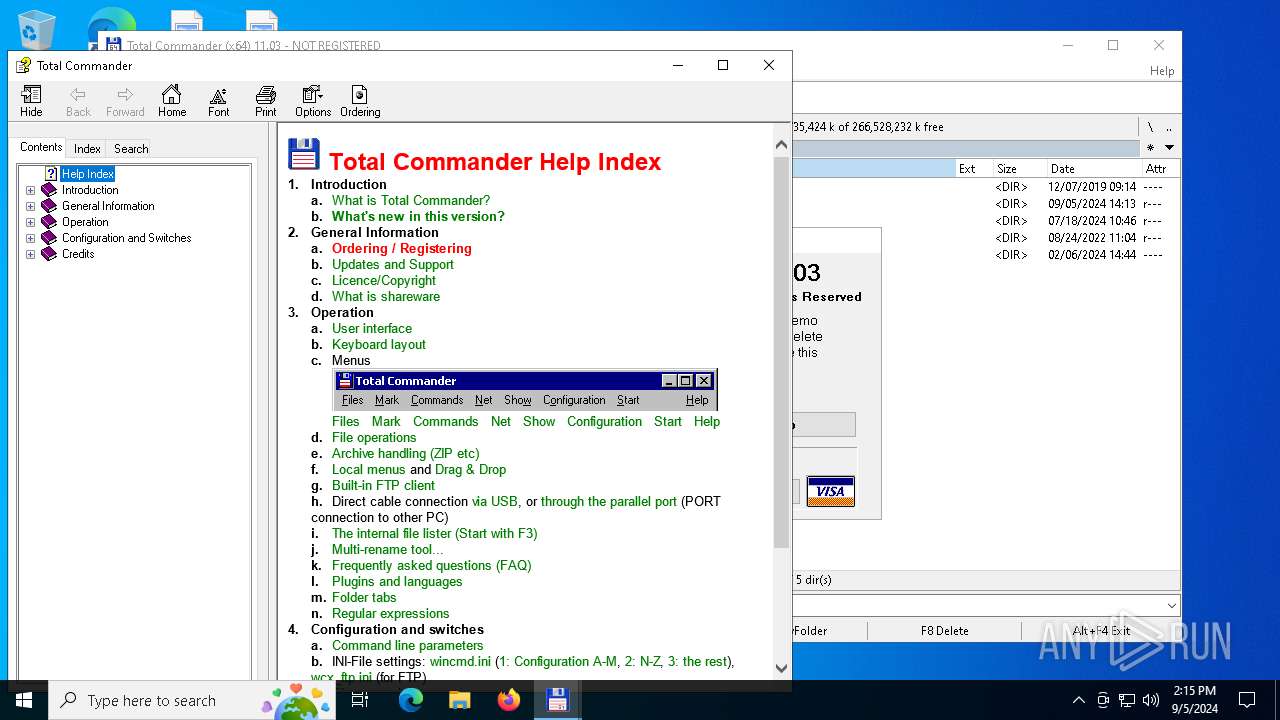
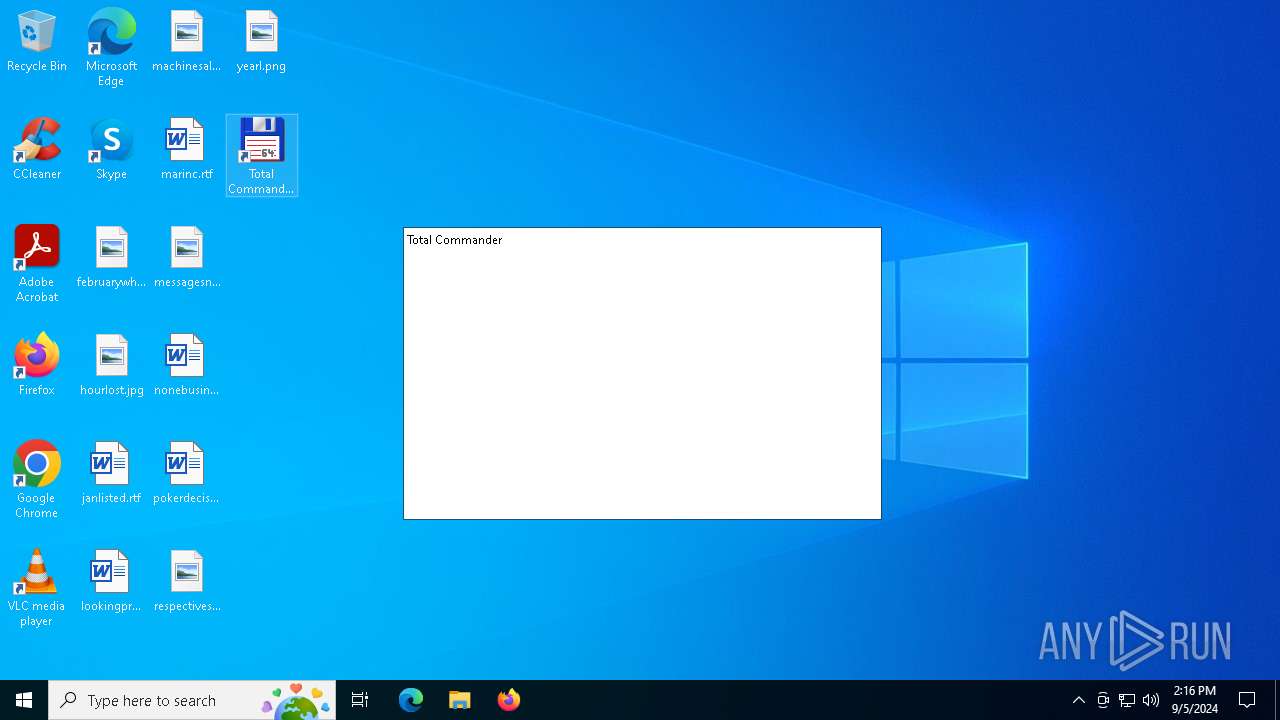
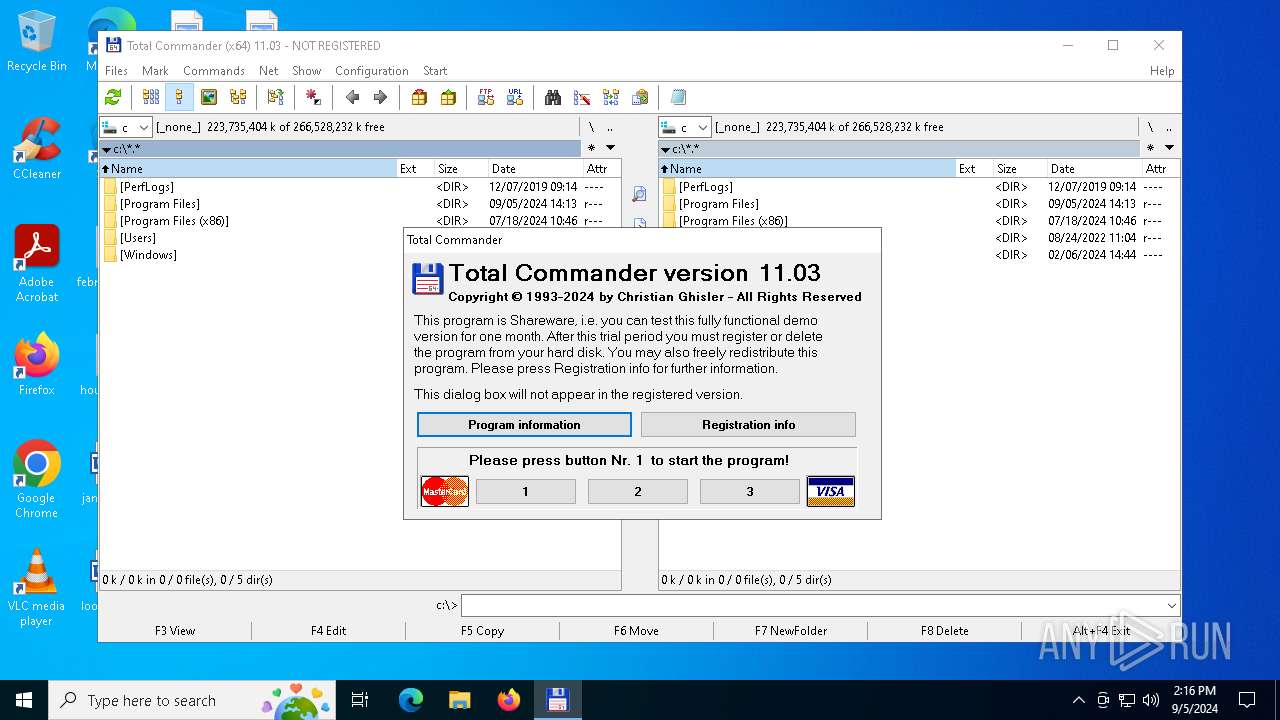
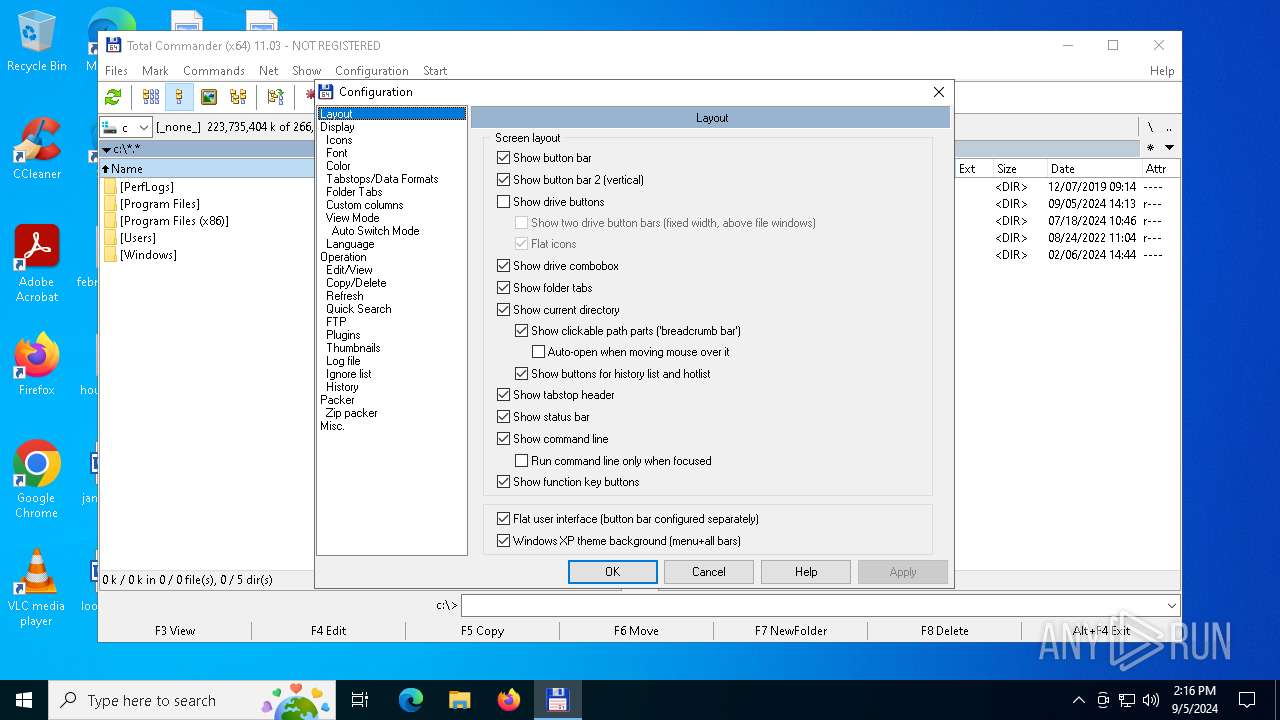
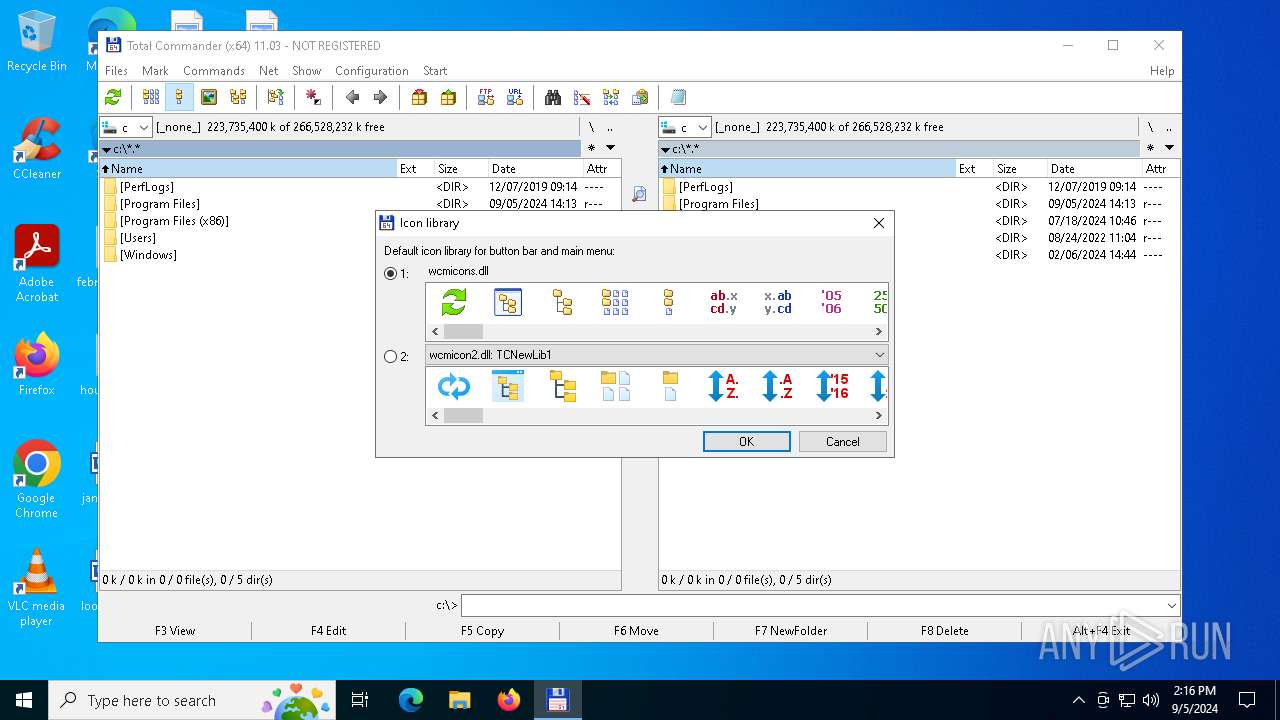
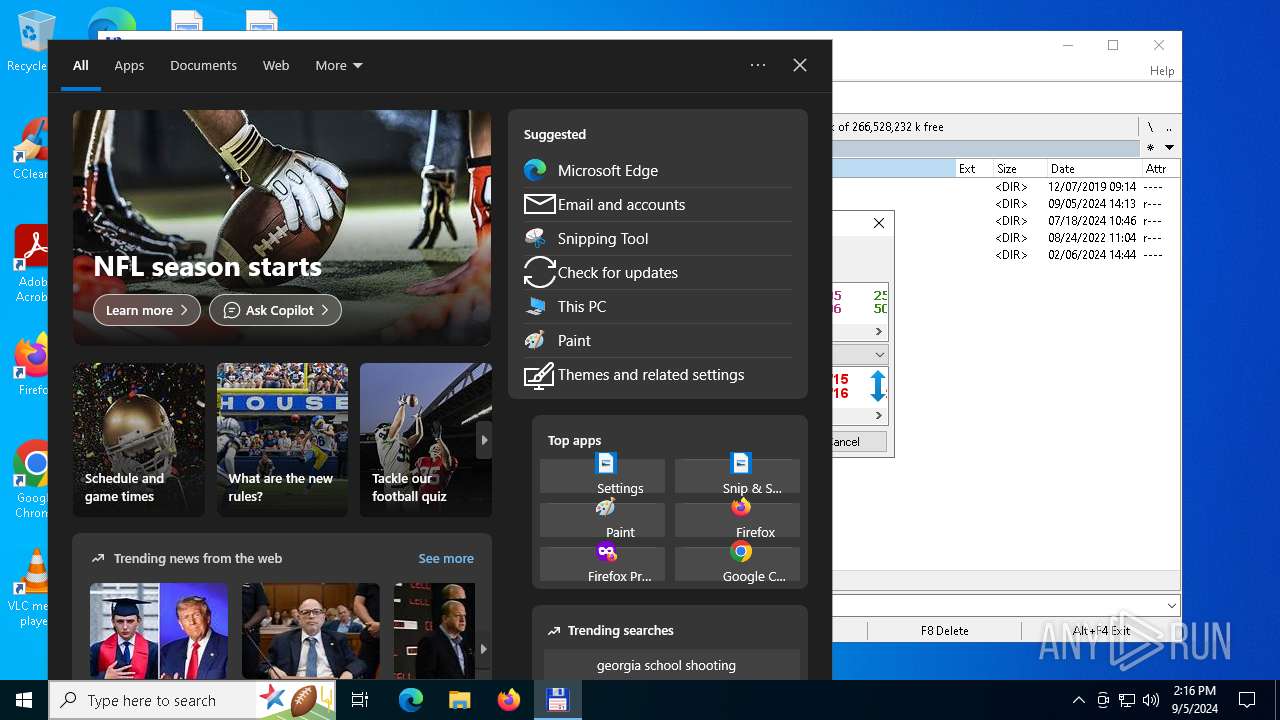
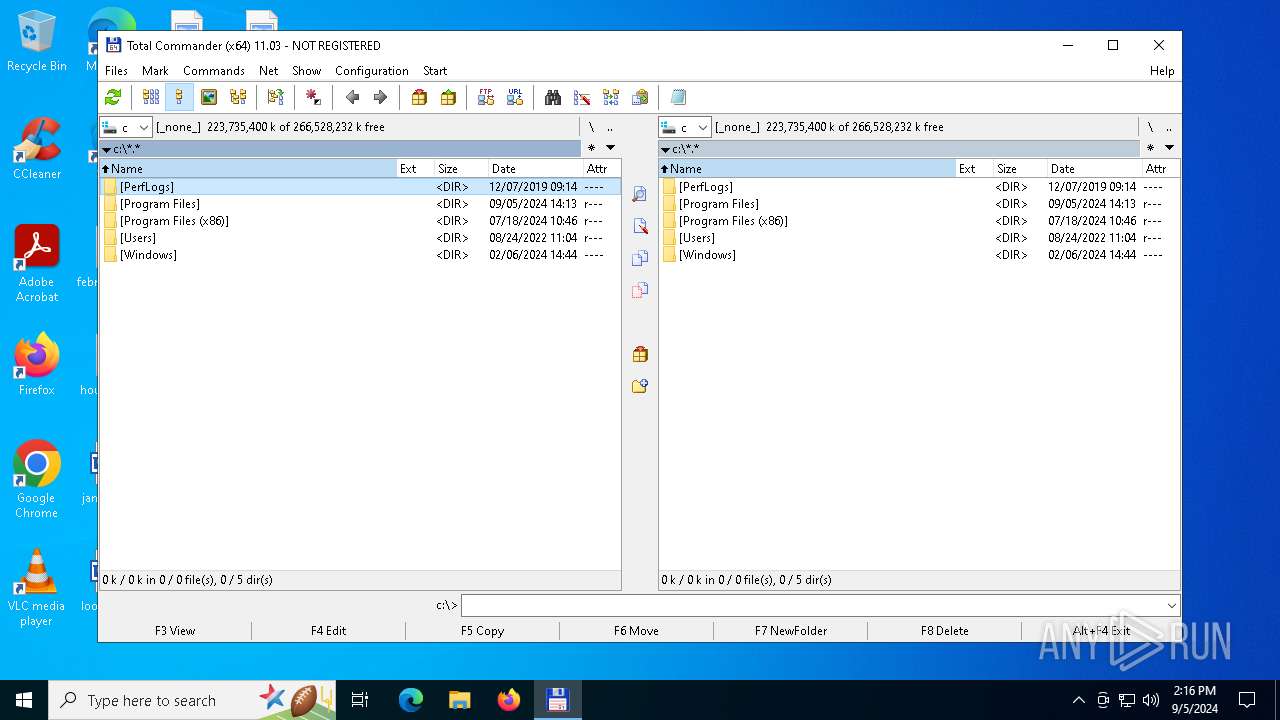
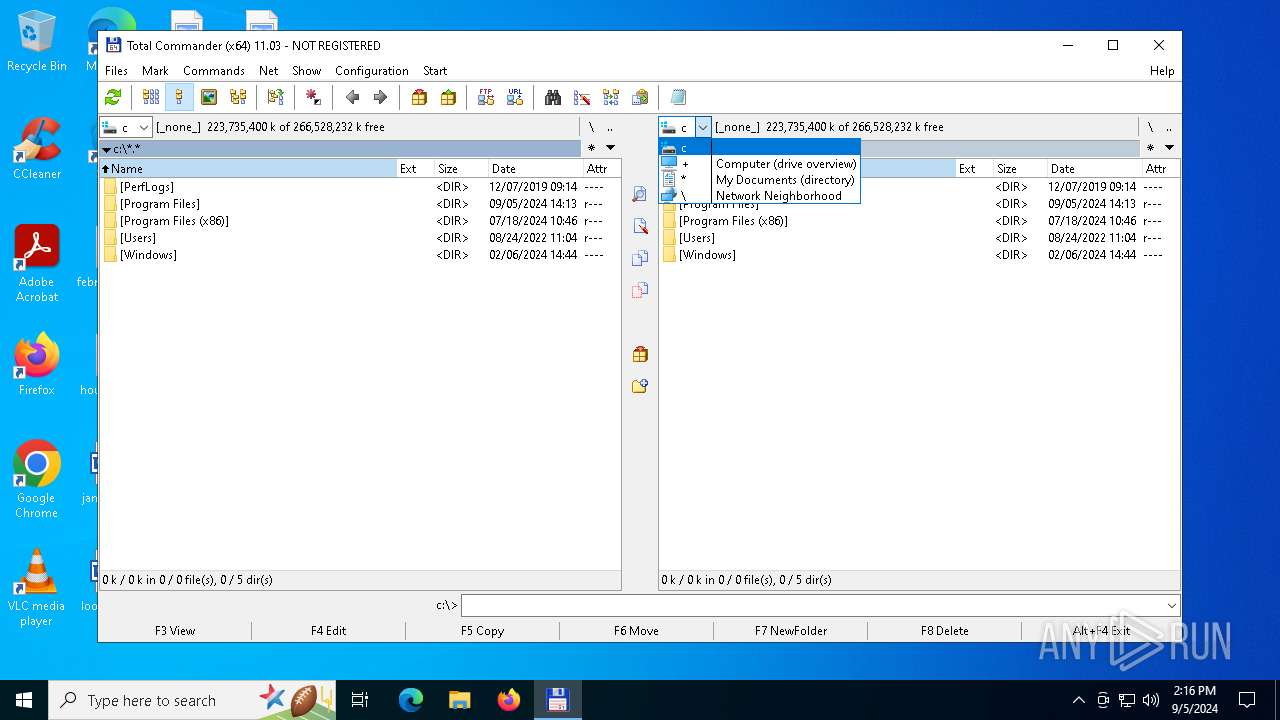
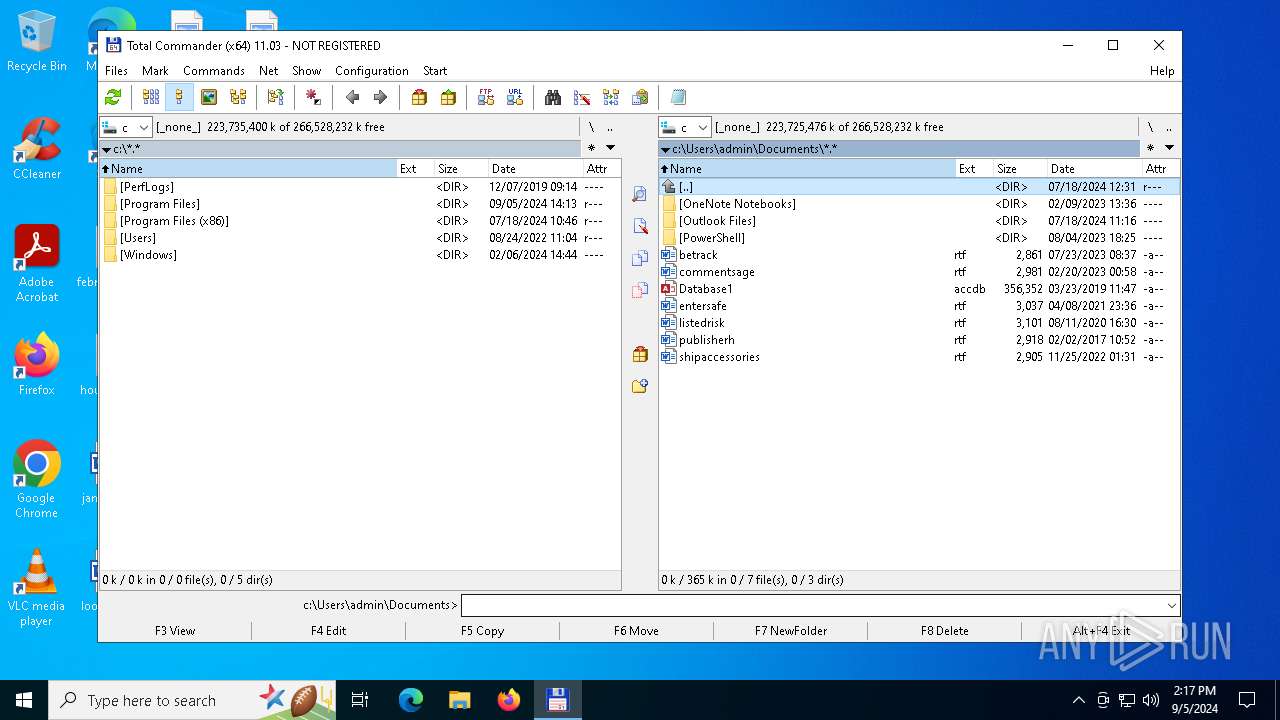
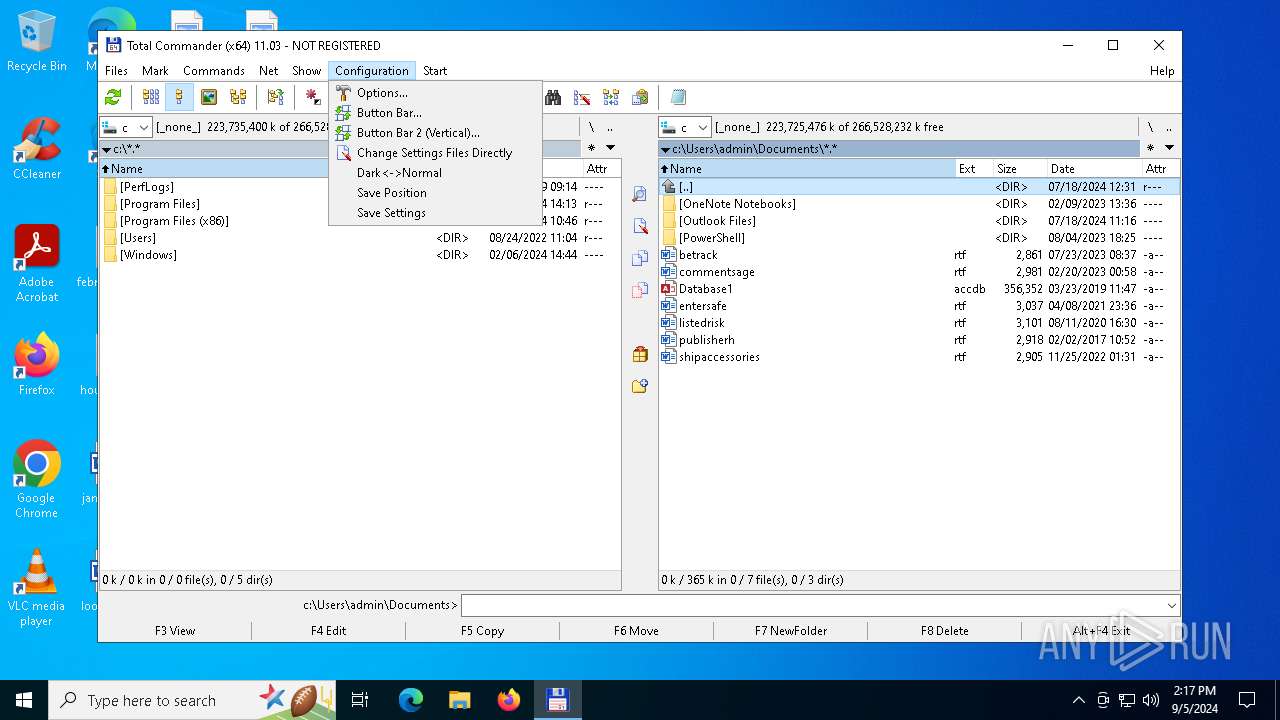
Manual execution by a user
- TOTALCMD64.EXE (PID: 3208)
- TOTALCMD64.EXE (PID: 1640)
- TOTALCMD64.EXE (PID: 1020)
Create files in a temporary directory
- TOTALCMD64.EXE (PID: 3208)
The process uses the downloaded file
- TOTALCMD64.EXE (PID: 3208)
Checks proxy server information
- TOTALCMD64.EXE (PID: 3208)
Creates files in the program directory
- tcmd1103x64.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:01:18 10:23:34+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 148480 |
| InitializedDataSize: | 66048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x18200 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.3.0.0 |
| ProductVersionNumber: | 11.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Ghisler Software GmbH |
| FileDescription: | Total Commander Installer |
| FileVersion: | 11.03 |
| InternalName: | INSTALL |
| LegalCopyright: | Copyright © Ghisler Software GmbH 1993-2024 |
| OriginalFileName: | install.exe |
| ProductName: | Total Commander Installer |
| ProductVersion: | 11.03 |
Total processes
137
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
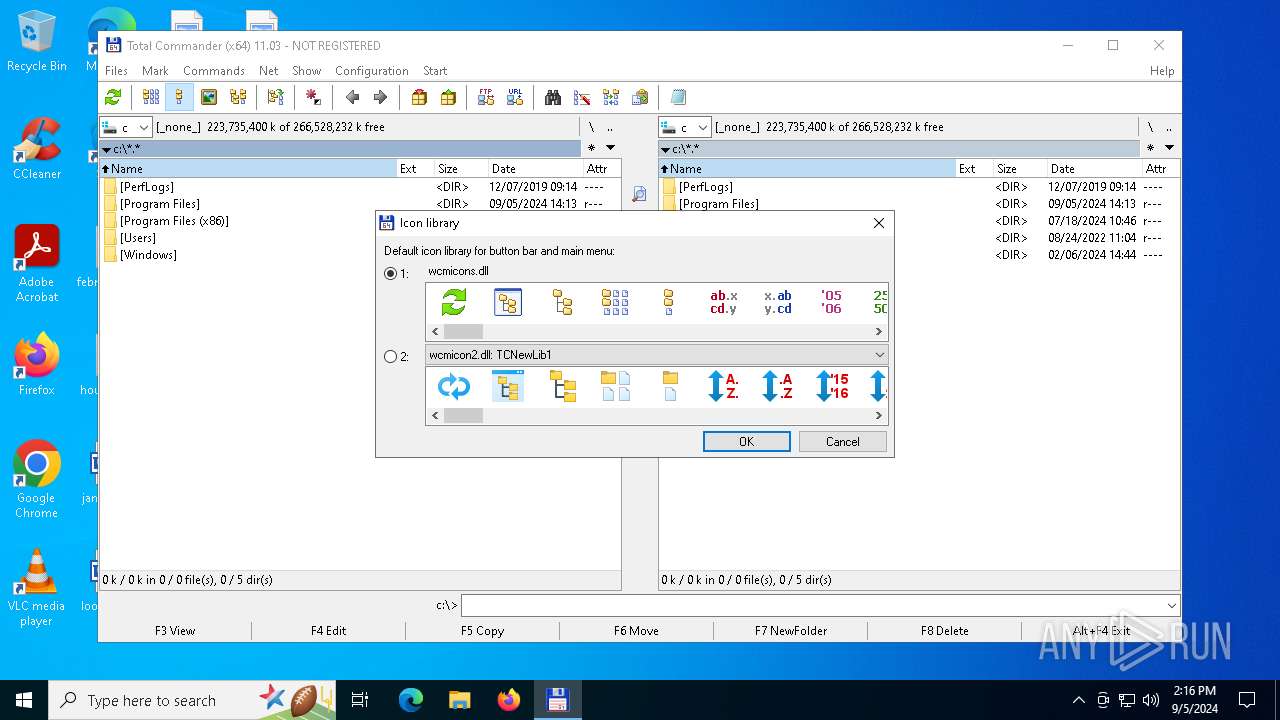
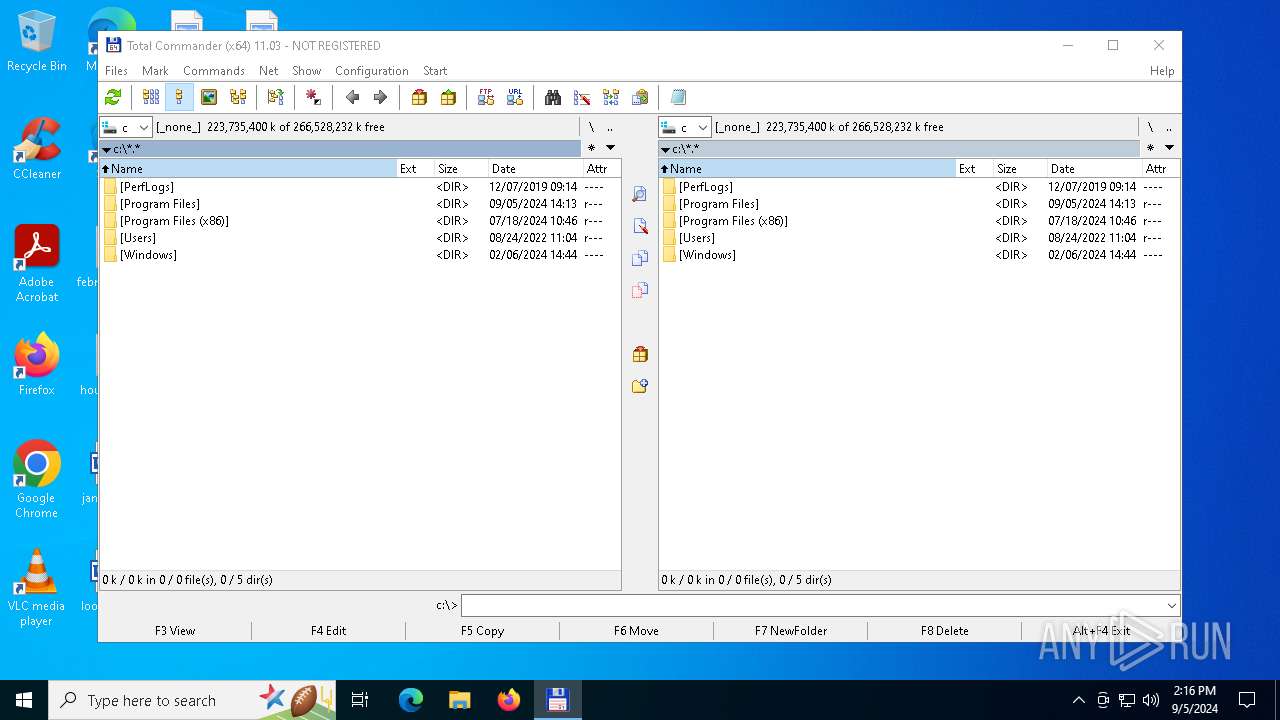
| 1020 | "C:\Program Files\totalcmd\TOTALCMD64.EXE" | C:\Program Files\totalcmd\TOTALCMD64.EXE | — | explorer.exe | |||||||||||
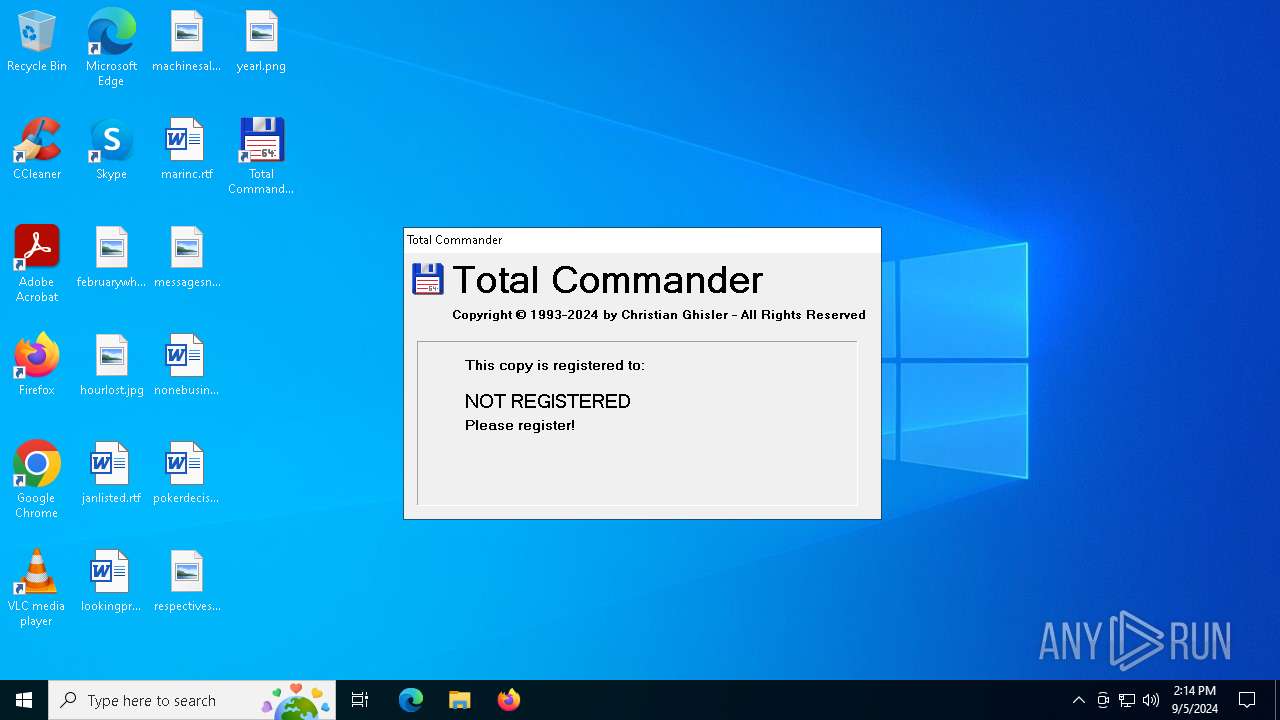
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander Exit code: 0 Version: 11.3.0.0 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\totalcmd\TOTALCMD64.EXE" | C:\Program Files\totalcmd\TOTALCMD64.EXE | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander Version: 11.3.0.0 Modules
| |||||||||||||||
| 3208 | "C:\Program Files\totalcmd\TOTALCMD64.EXE" | C:\Program Files\totalcmd\TOTALCMD64.EXE | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander Exit code: 0 Version: 11.3.0.0 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\tcmd1103x64.exe" | C:\Users\admin\AppData\Local\Temp\tcmd1103x64.exe | explorer.exe | ||||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: HIGH Description: Total Commander Installer Exit code: 0 Version: 11.03 Modules
| |||||||||||||||
| 4996 | "C:\Users\admin\AppData\Local\Temp\tcmd1103x64.exe" | C:\Users\admin\AppData\Local\Temp\tcmd1103x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander Installer Exit code: 3221226540 Version: 11.03 Modules
| |||||||||||||||
Total events
3 877
Read events
3 850
Write events
23
Delete events
4
Modification events
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | IniFileName |
Value: %APPDATA%\GHISLER\wincmd.ini | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | FtpIniName |
Value: %APPDATA%\GHISLER\wcx_ftp.ini | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\totalcmd | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | IniFileName |
Value: %APPDATA%\GHISLER\wincmd.ini | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | FtpIniName |
Value: %APPDATA%\GHISLER\wcx_ftp.ini | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\totalcmd | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ghisler\Total Commander |
| Operation: | write | Name: | IniFileName |
Value: %APPDATA%\GHISLER\wincmd.ini | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ghisler\Total Commander |
| Operation: | write | Name: | FtpIniName |
Value: %APPDATA%\GHISLER\wcx_ftp.ini | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ghisler\Total Commander |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\totalcmd | |||
| (PID) Process: | (3728) tcmd1103x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Totalcmd64 |
| Operation: | write | Name: | DisplayName |
Value: Total Commander 64-bit (Remove or Repair) | |||
Executable files
22
Suspicious files
16
Text files
73
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | tcmd1103x64.exe | C:\Users\admin\AppData\Roaming\GHISLER\wincmd.ini | text | |
MD5:8D158FF6C3D1872A17896CA8A116C9B1 | SHA256:6F54122F094088382BACECFEE05210769EA957F5CDD35B6F4E1E69EA6851EBE8 | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\KEYBOARD.TXT | text | |
MD5:D182D9DFE03704BEC3CDED09CF11B8BF | SHA256:CFEDDACEC4BC2E94FADD55E3C650D41D51B7DACF910D1245252DFC57788D7B39 | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\LANGUAGE\WCMD_CZ.MNU | text | |
MD5:274B975F020BCA432F36F940DBE1F079 | SHA256:3F2DCEB5678A39E6A301AABA1FAF02D5D2C06FDC6AEFF4C7ABF2E4A89936E6BE | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\LANGUAGE\WCMD_CZ.LNG | text | |
MD5:EFD9133693BB3177D500D055FA0E45F7 | SHA256:D4C8FEF1CE5A0318ECC0EB15A2F06D84F786AB1683D5EE0515133189A91AF179 | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\LANGUAGE\WCMD_CZ.INC | text | |
MD5:29101427611EFBBBE19FFA4BE2ACA09A | SHA256:2C521A1865949F10303F47E5139877086AE844E15A5DFC062F5FEA1B864A84DD | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\LANGUAGE\WCMD_DAN.LNG | text | |
MD5:7F304F328DA46114164290D0681F31A0 | SHA256:80002AE67F1F40573703C681A0D9CFF673926A6412A16E9B6F1E56A08D868053 | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\LANGUAGE\WCMD_DAN.MNU | text | |
MD5:53D7C6BD7EA5A438B014916E3A29A121 | SHA256:DF48EBB26915756DDE7F4BB74A0AE1291053E3E4F6B914FD5F2F624F285D3B64 | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\LANGUAGE\WCMD_DAN.INC | text | |
MD5:EF0D7351577997B7BA453D115245C734 | SHA256:9B84F9AF70791F2844B275F94860F9C09D2F6123B82D947942B0FBE8600AE2F1 | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\TOTALCMD.CHM | binary | |
MD5:15E5A2A061C8FA36A8C583F1635182B2 | SHA256:916C790A30D9EA59B41759218F71A87DDE78BDD4179ED29C2F17792CC7773053 | |||
| 3728 | tcmd1103x64.exe | C:\Program Files\totalcmd\LANGUAGE\WCMD_DEU.MNU | text | |
MD5:BBA71DF7344537B832F84FD845697CD3 | SHA256:44CB36B58BADDD7C53DDFB2DFCC8CA1FA47054F7CD5083E710B4D74B07FEF9F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
42
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3652 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4760 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4708 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4708 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4276 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4760 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4760 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3652 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3652 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |