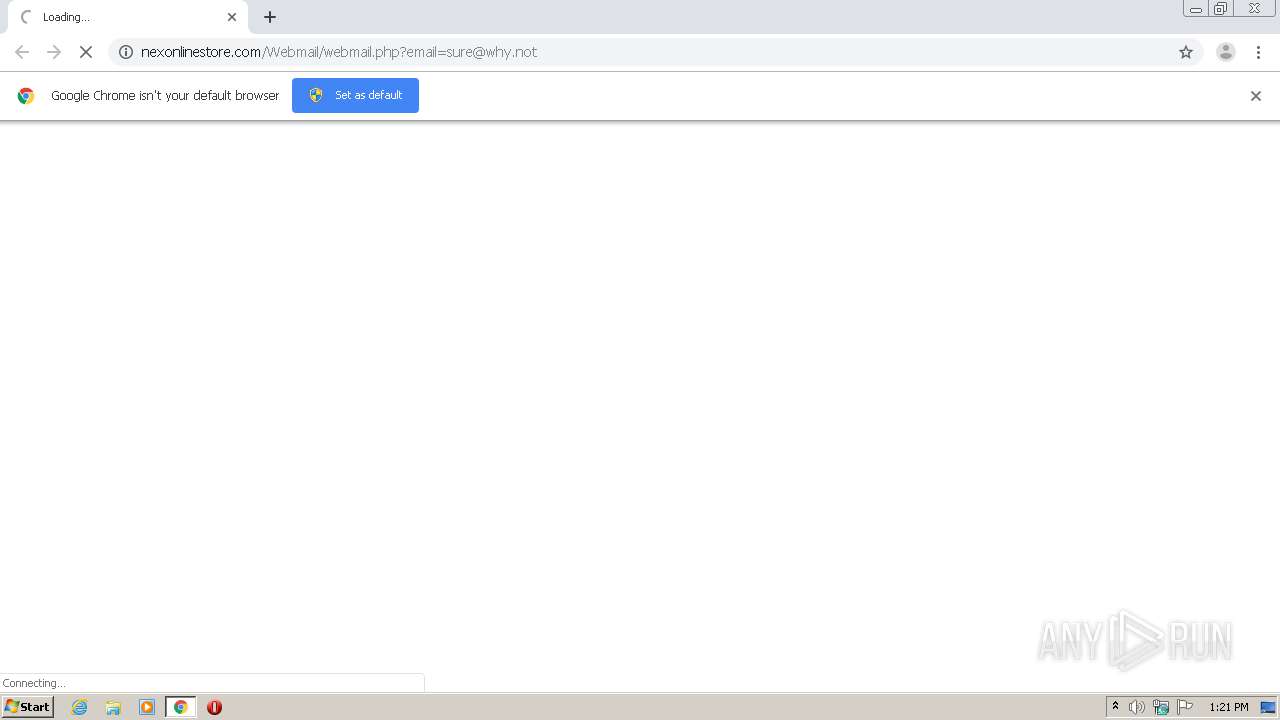
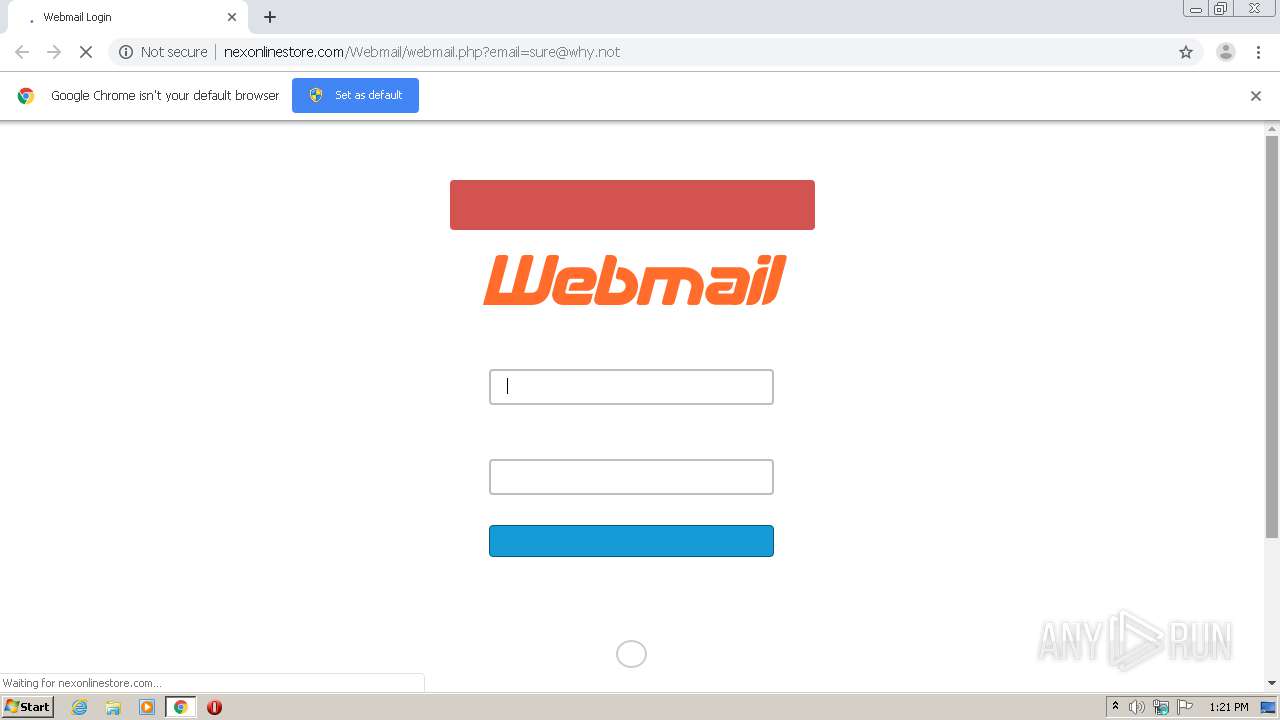
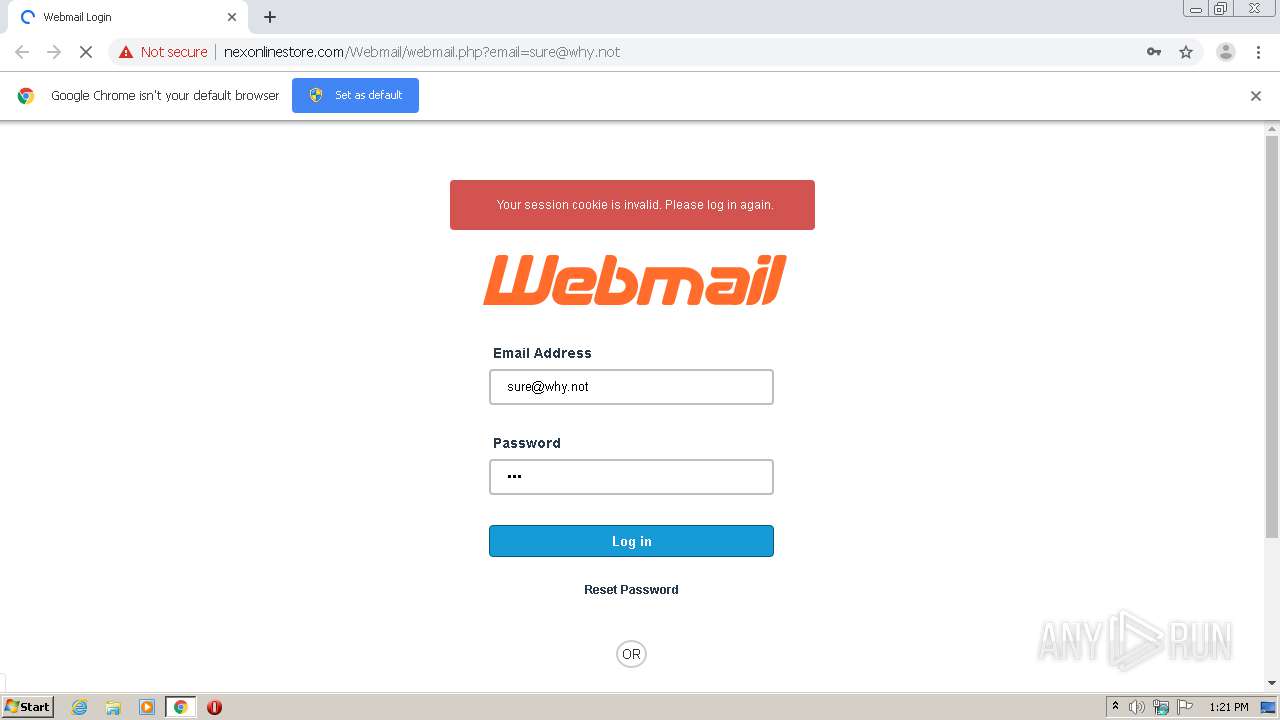
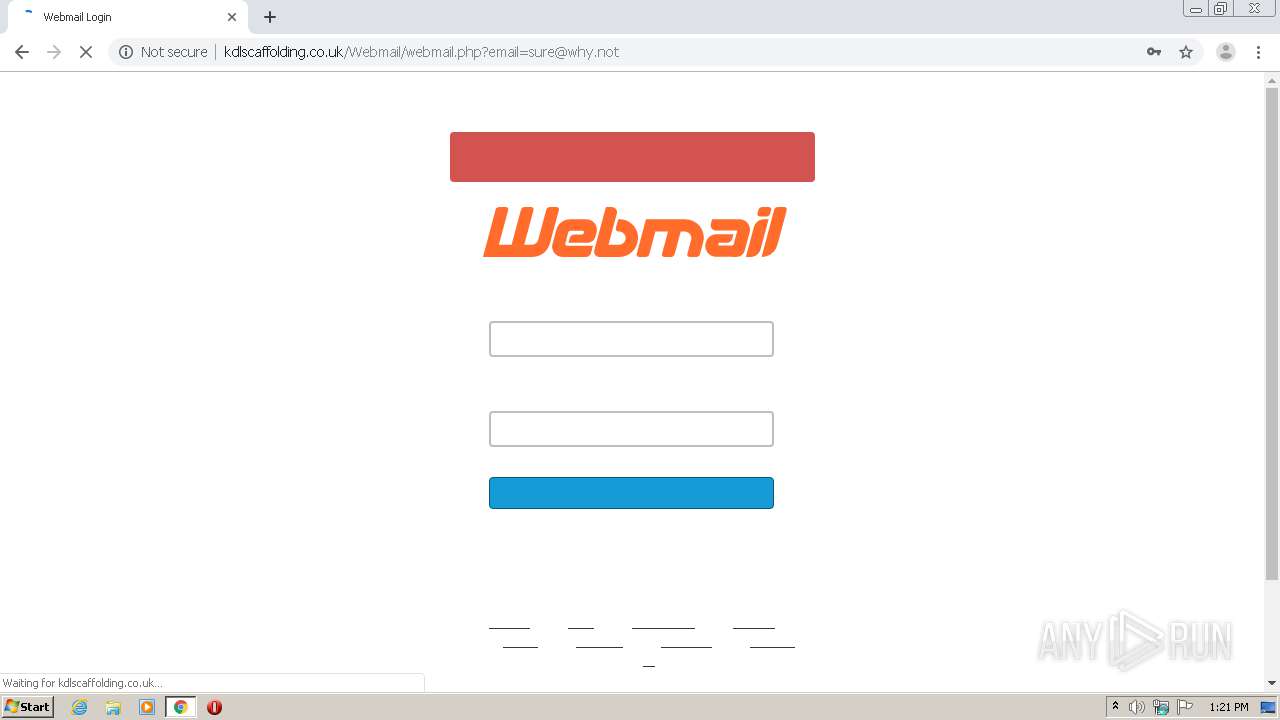
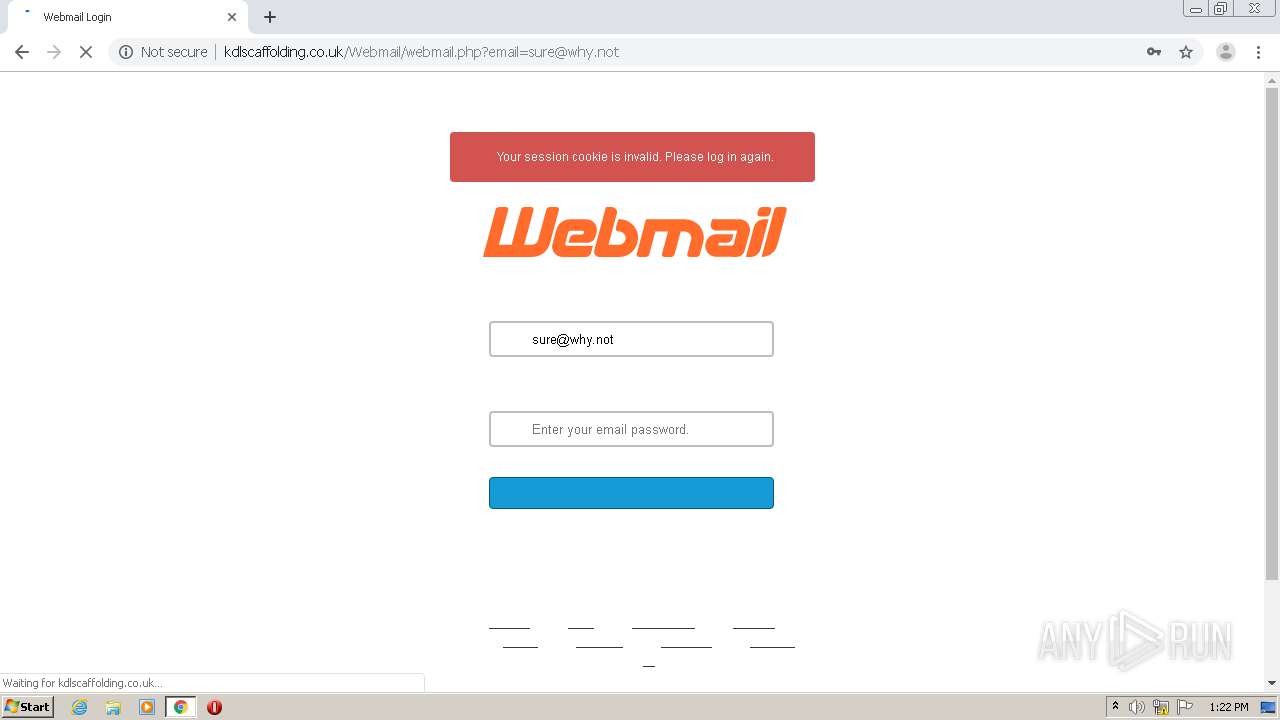
| URL: | http://nexonlinestore.com/Webmail/webmail.php?email=sure@why.not |
| Full analysis: | https://app.any.run/tasks/394d2b4f-1bc0-45c9-92c2-d5a43fcbfe9c |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2021, 13:20:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 021127A3BAFA41438A5D9E9FCAA0D5FF |
| SHA1: | 088F21944ADBB2E8E512396A0150C1C1D1334ECA |
| SHA256: | D1B185D7394AAEFAA849A1B007D4E9D9F3392DAC2060C5FCF1AF6166FF784843 |
| SSDEEP: | 3:N1KQ4KEADTIIFAyJxSJ7QQsRn:CQkeMI6yJYJUJRn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3960)
Reads the hosts file
- chrome.exe (PID: 3988)
- chrome.exe (PID: 3960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5422290537647149555 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1896286123415633644 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3964 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15244808482946293256 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3048 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18164285887581473430 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17755333645353718892 --mojo-platform-channel-handle=1996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6b1ea9d0,0x6b1ea9e0,0x6b1ea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3142662298004276289 --mojo-platform-channel-handle=3528 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10308137343648731286 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14094044934308972999 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
589
Read events
517
Write events
69
Delete events
3
Modification events
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3960-13259856073027625 |
Value: 259 | |||
Executable files
0
Suspicious files
11
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6048C7C9-F78.pma | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d2ebbd5f-da4b-4528-a0eb-5b6abb4f4966.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1321f3.TMP | text | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1323b8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
108
TCP/UDP connections
72
DNS requests
18
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3988 | chrome.exe | GET | — | 209.58.169.75:80 | http://nexonlinestore.com/cPanel_magic_revision_1386192033/unprotected/cpanel/fonts/open_sans/OpenSans-Semibold-webfont.woff | SG | — | — | malicious |
3988 | chrome.exe | GET | — | 209.58.169.75:80 | http://nexonlinestore.com/cPanel_magic_revision_1386192033/unprotected/cpanel/fonts/open_sans/OpenSans-Semibold-webfont.ttf | SG | — | — | malicious |
3988 | chrome.exe | GET | — | 209.58.169.75:80 | http://nexonlinestore.com/cPanel_magic_revision_1386192031/unprotected/cpanel/fonts/open_sans/OpenSans-Bold-webfont.ttf | SG | — | — | malicious |
3988 | chrome.exe | GET | 404 | 209.58.169.75:80 | http://nexonlinestore.com/cPanel_magic_revision_1445551417/unprotected/cpanel/images/warning.png | SG | text | 6.19 Kb | malicious |
3988 | chrome.exe | GET | 404 | 209.58.169.75:80 | http://nexonlinestore.com/cPanel_magic_revision_1386192031/unprotected/cpanel/fonts/open_sans/OpenSans-Bold-webfont.woff | SG | text | 6.19 Kb | malicious |
3988 | chrome.exe | GET | 404 | 209.58.169.75:80 | http://nexonlinestore.com/cPanel_magic_revision_1386192033/unprotected/cpanel/fonts/open_sans/OpenSans-Regular-webfont.ttf | SG | text | 6.19 Kb | malicious |
3988 | chrome.exe | GET | 404 | 209.58.169.75:80 | http://nexonlinestore.com/cPanel_magic_revision_1445551417/unprotected/cpanel/images/icon-password.png | SG | text | 6.19 Kb | malicious |
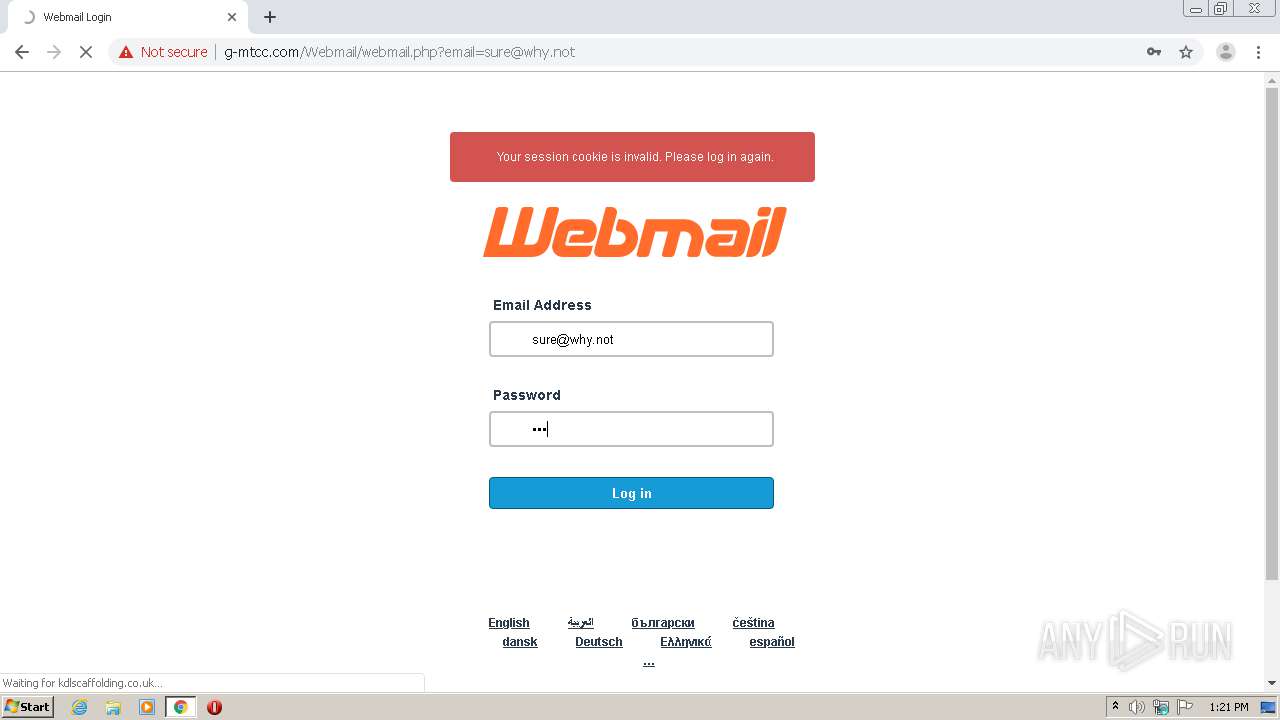
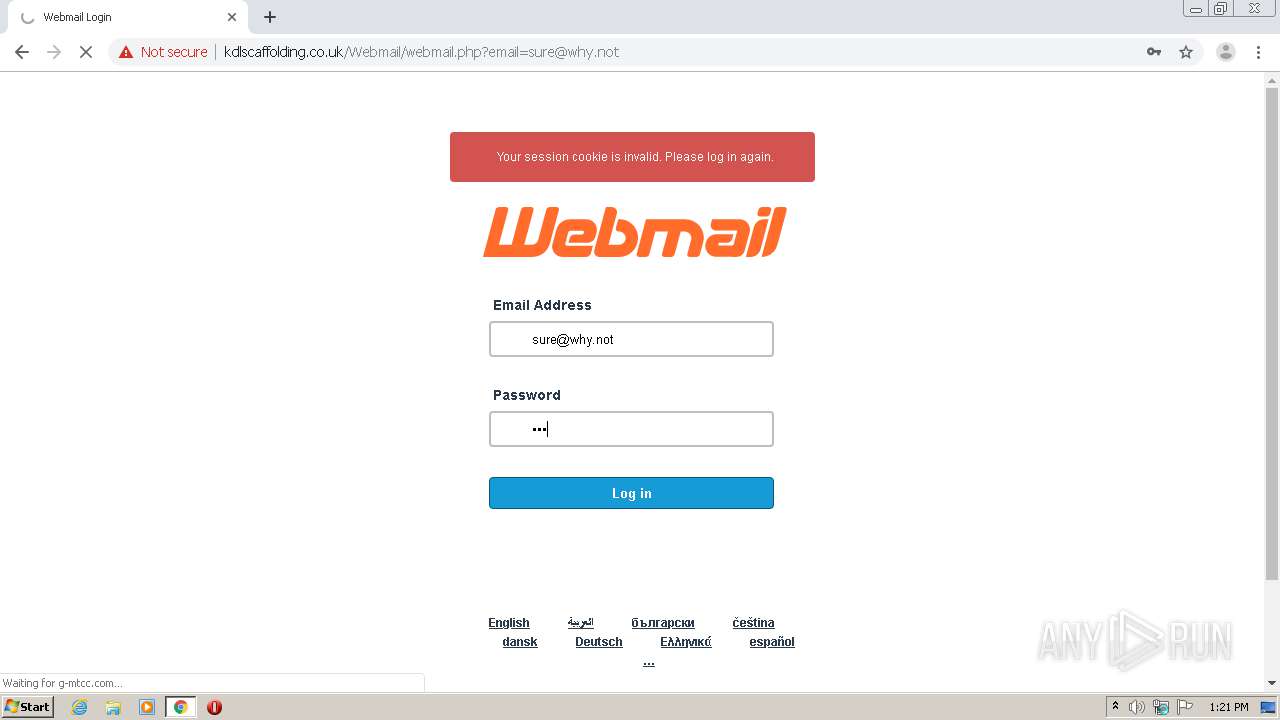
3988 | chrome.exe | POST | 302 | 107.154.161.112:80 | http://alshaheq-int.me/login.php | US | — | — | suspicious |
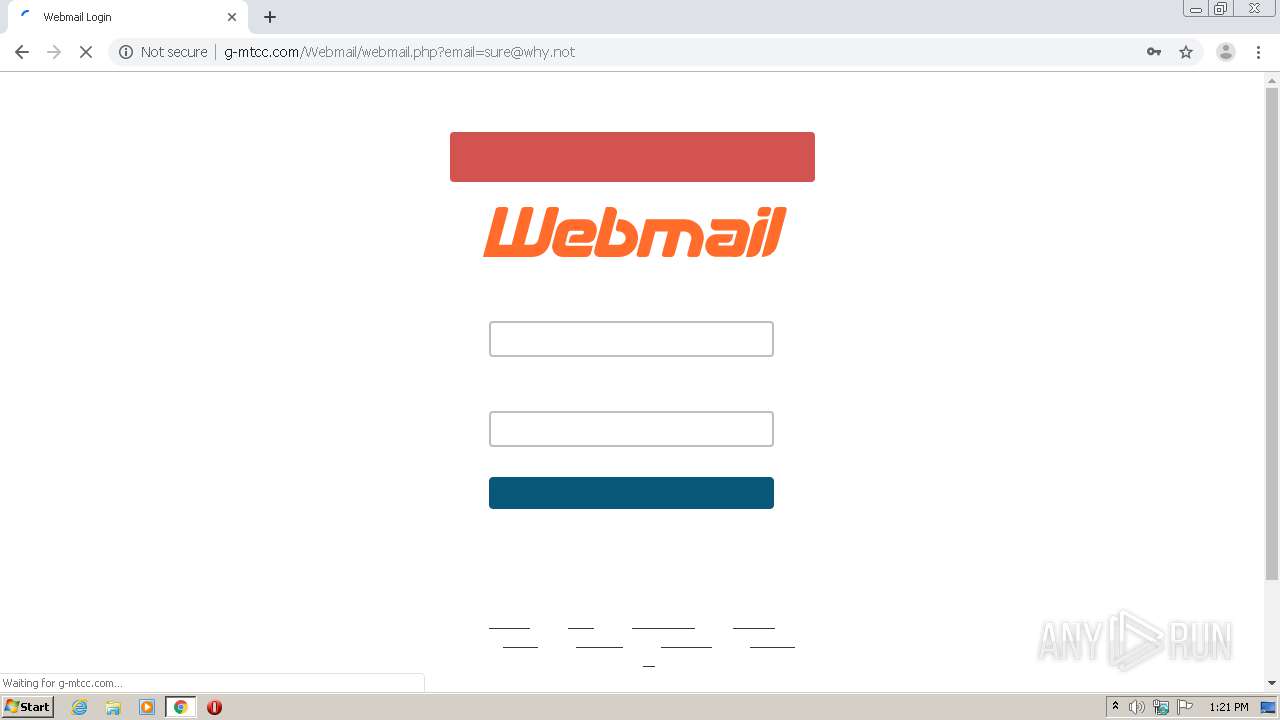
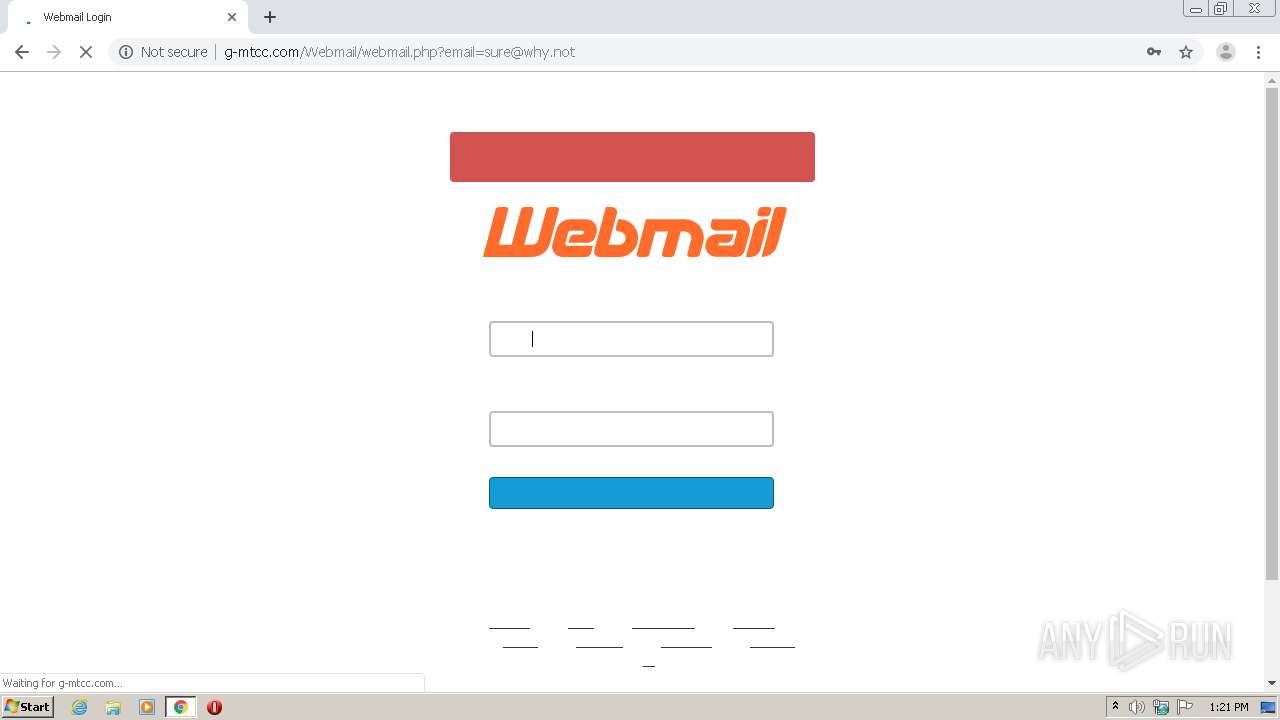
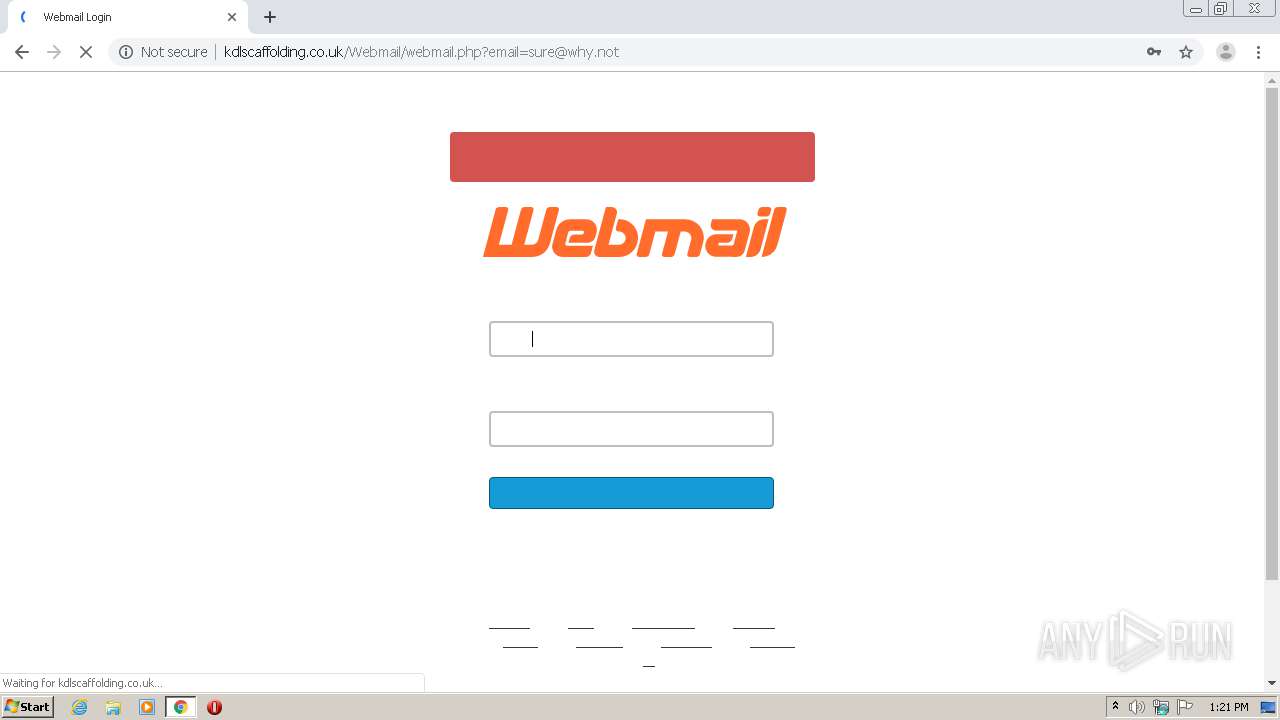
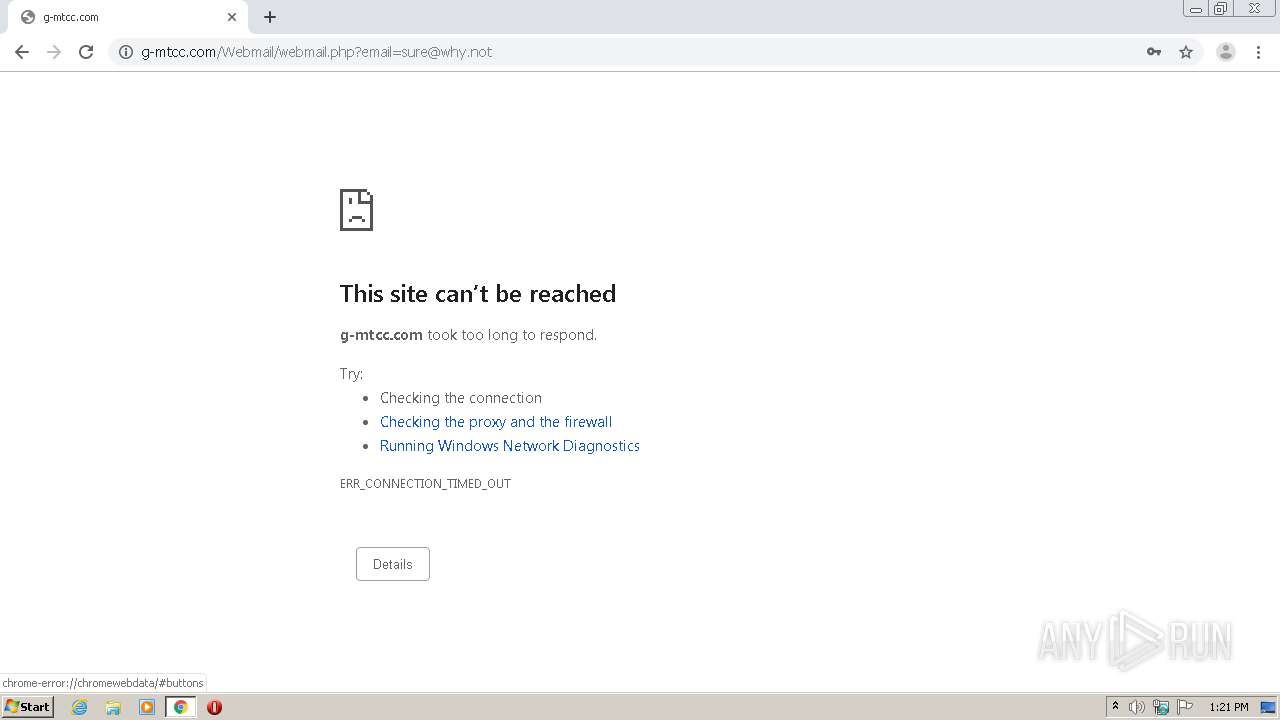
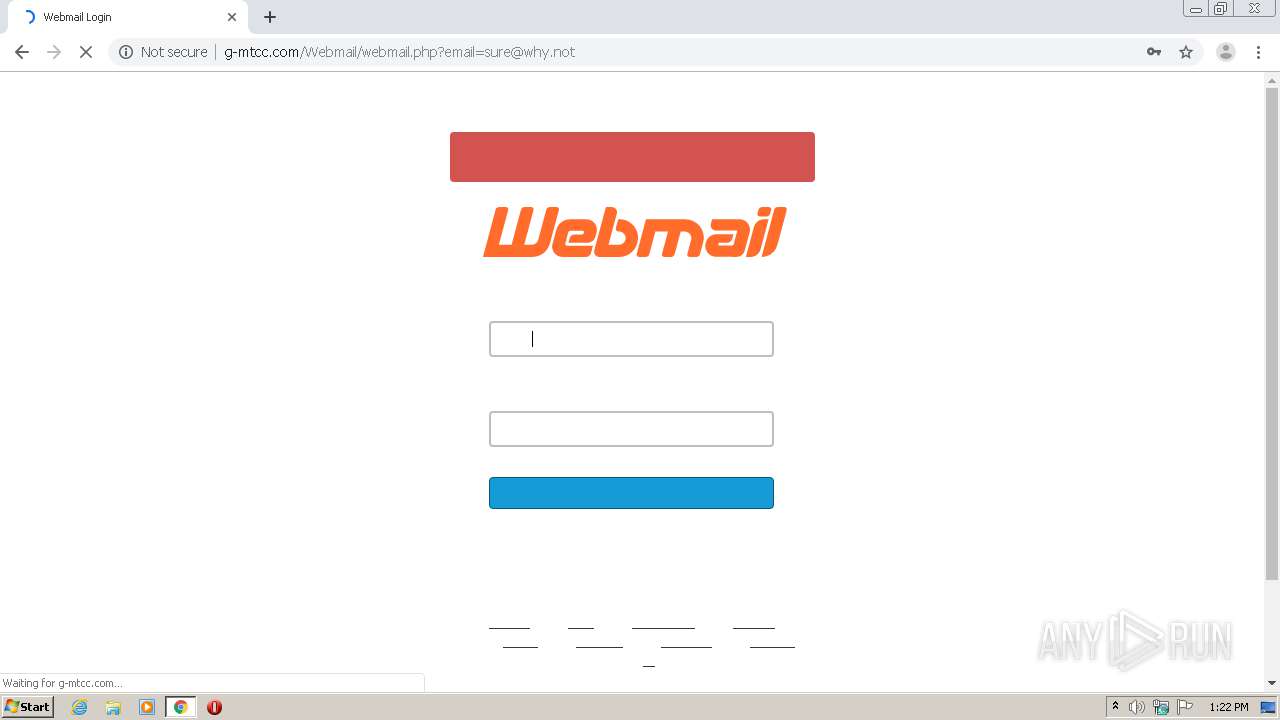
3988 | chrome.exe | GET | 200 | 192.185.37.183:80 | http://g-mtcc.com/Webmail/webmail.php?email=sure@why.not | US | html | 9.94 Kb | malicious |
3988 | chrome.exe | GET | 200 | 192.185.37.183:80 | http://g-mtcc.com/google_analytics_auto.js | US | text | 299 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3988 | chrome.exe | 209.58.169.75:80 | nexonlinestore.com | Leaseweb Asia Pacific pte. ltd. | SG | malicious |
3988 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3988 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3988 | chrome.exe | 107.154.161.112:80 | alshaheq-int.me | Incapsula Inc | US | suspicious |
3988 | chrome.exe | 192.185.37.183:80 | g-mtcc.com | CyrusOne LLC | US | malicious |
3988 | chrome.exe | 142.250.186.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3988 | chrome.exe | 173.194.76.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 142.250.185.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.163:443 | www.google.com.pk | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nexonlinestore.com |
| malicious |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
cloud305.mxserver.ro |
| unknown |
coilprofil.ro |
| unknown |
pmrsupports.com |
| unknown |
alshaheq-int.me |
| suspicious |
g-mtcc.com |
| malicious |
www.google-analytics.com |
| whitelisted |
webmail.emdaddesign.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Generic Personalized Phish 2018-09-27 M2 |
3988 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY HTTP POST contains pass= in cleartext |
3988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Webmail Update Phish 2015-10-08 |
3988 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP invalid response field folding |
3988 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP response header invalid |
3988 | chrome.exe | A Network Trojan was detected | ET WEB_CLIENT Suspicious Redirect - Possible Phishing May 25 2016 |
3988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Generic Personalized Phish 2018-09-27 M2 |
3988 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY HTTP POST contains pass= in cleartext |
3988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Webmail Update Phish 2015-10-08 |
3988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Generic Personalized Phish 2018-09-27 M2 |
5 ETPRO signatures available at the full report