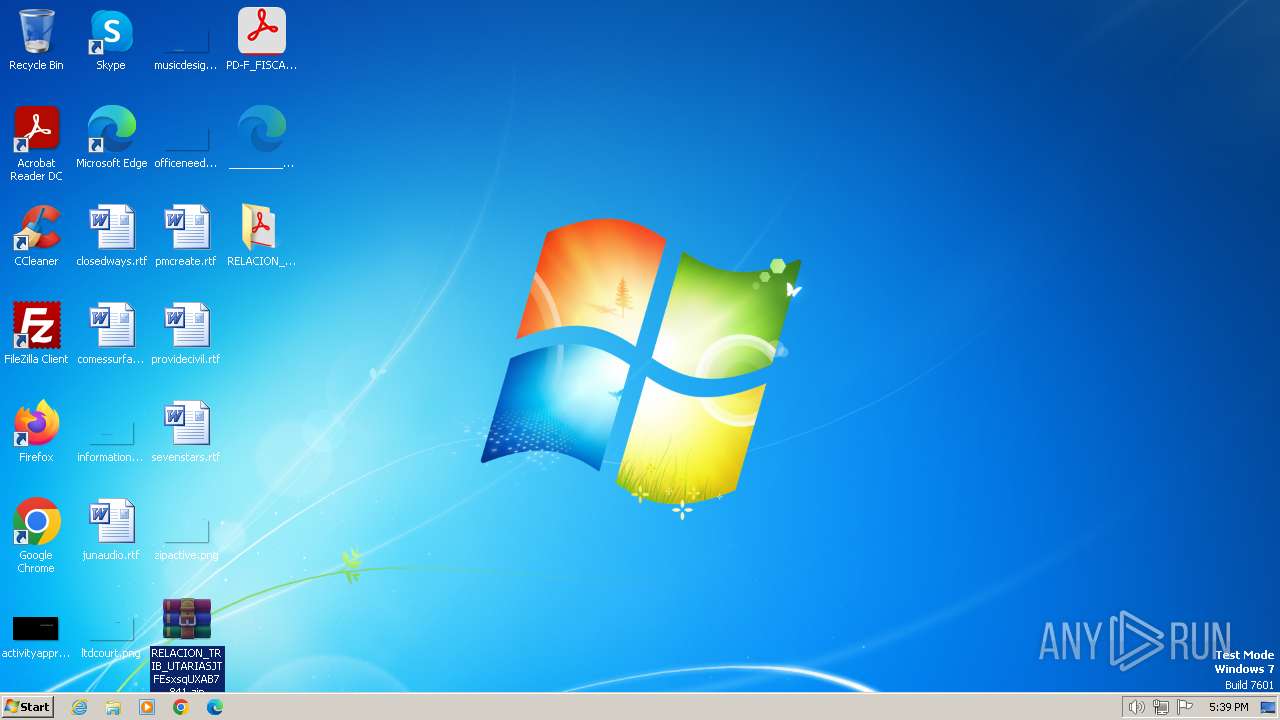
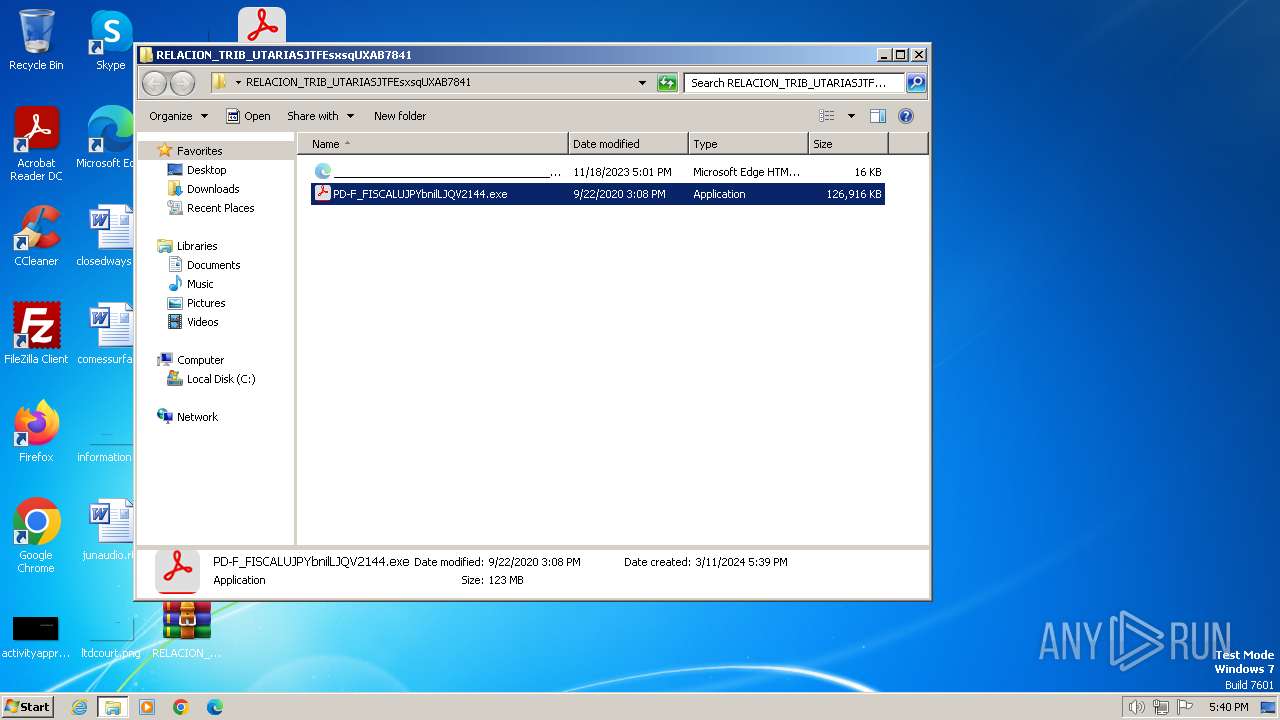
| File name: | RELACION_TRIB_UTARIASJTFEsxsqUXAB7841.zip |
| Full analysis: | https://app.any.run/tasks/57b8374d-5d29-4291-ad08-c8e13b8f5af3 |
| Verdict: | Malicious activity |
| Threats: | Grandoreiro is a Latin American banking trojan first observed in 2016. It targets mostly Spanish-speaking countries, such as Brazil, Spain, Mexico and Peru. This malware is operated as a Malware-as-a-Service (MaaS), which makes it easily accessible for cybercriminals. Besides, it uses advanced techniques to evade detection. |
| Analysis date: | March 11, 2024, 17:39:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
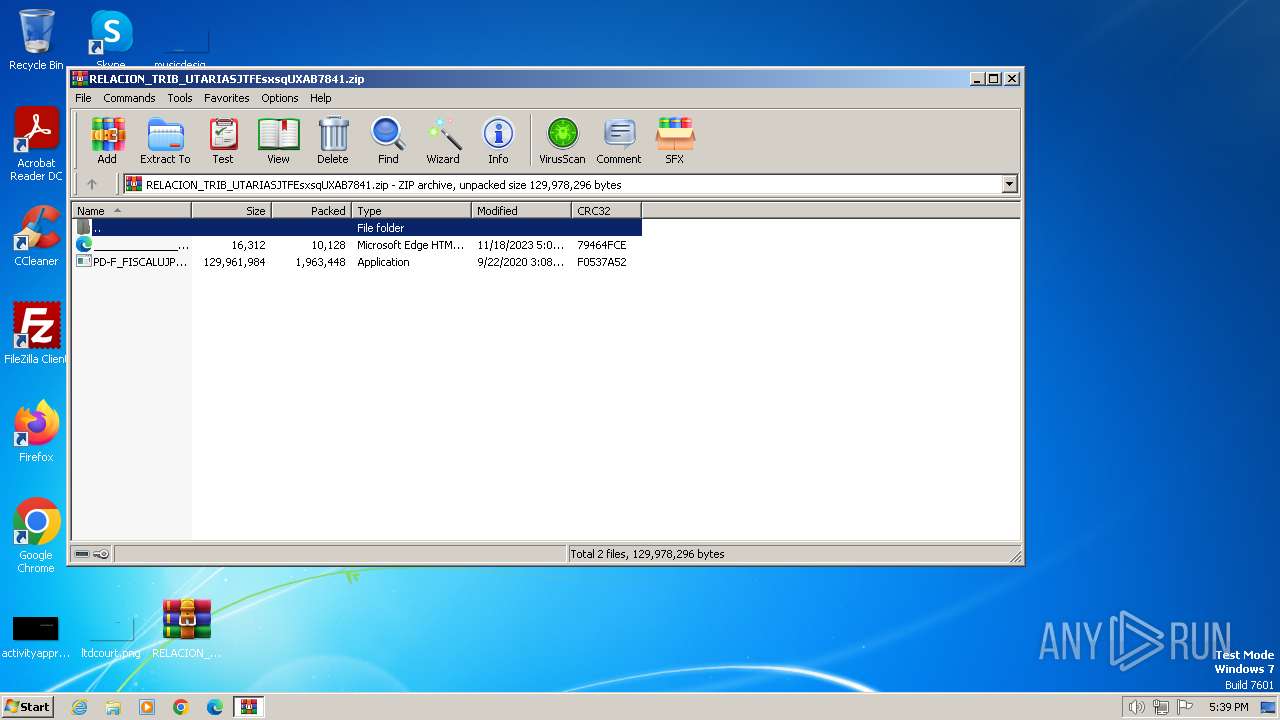
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | CD0F794A35A0C313AB10BCBE3EBB8F88 |
| SHA1: | EA11DD1E6EB13D5523A710443FD306FF820E8893 |
| SHA256: | D1AE993E4F2027E5046C86014C599635A7B35A274B2B5D068E5AE0135D73D799 |
| SSDEEP: | 98304:33CpqDR13+Ykl/JyRQVtfXQx1mtmPJgzSaTv4pP3k7Re2HbCYjv/EOSs21mLtWe4:jcswV6 |
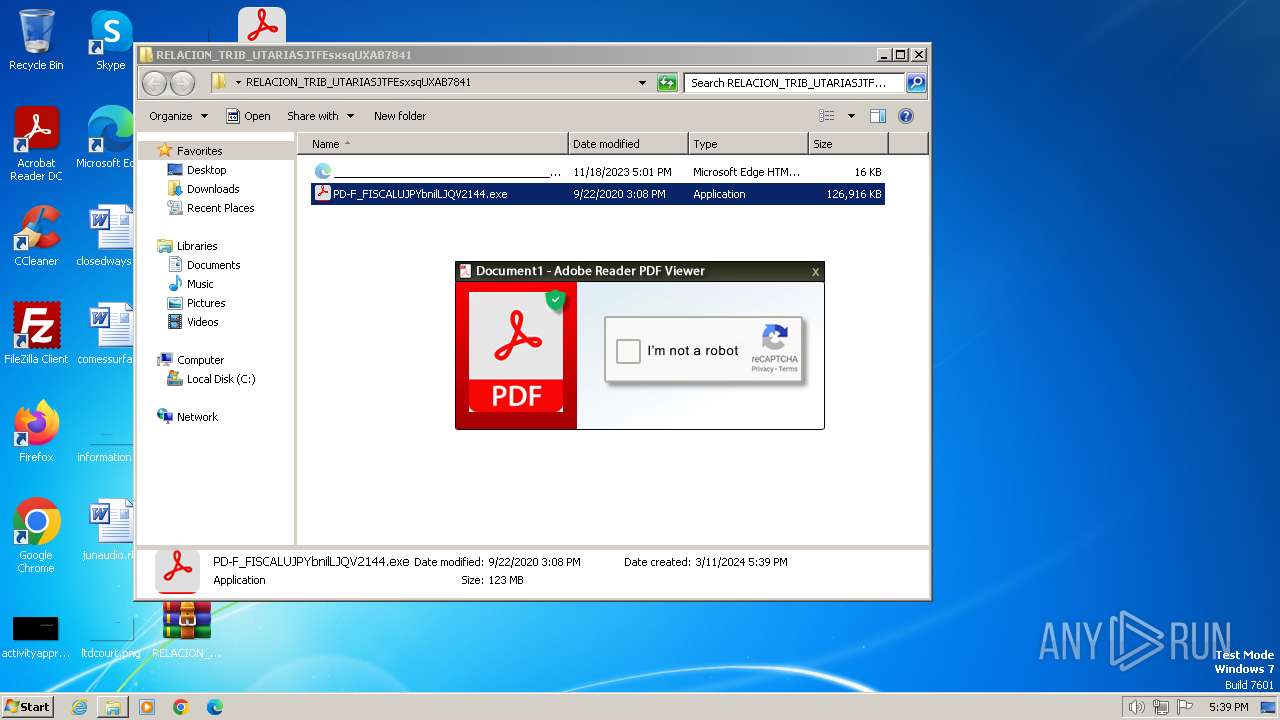
MALICIOUS
GRANDOREIRO has been detected (SURICATA)
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
Actions looks like stealing of personal data
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
SUSPICIOUS
Reads settings of System Certificates
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
Checks for external IP
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
Connects to unusual port
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
INFO
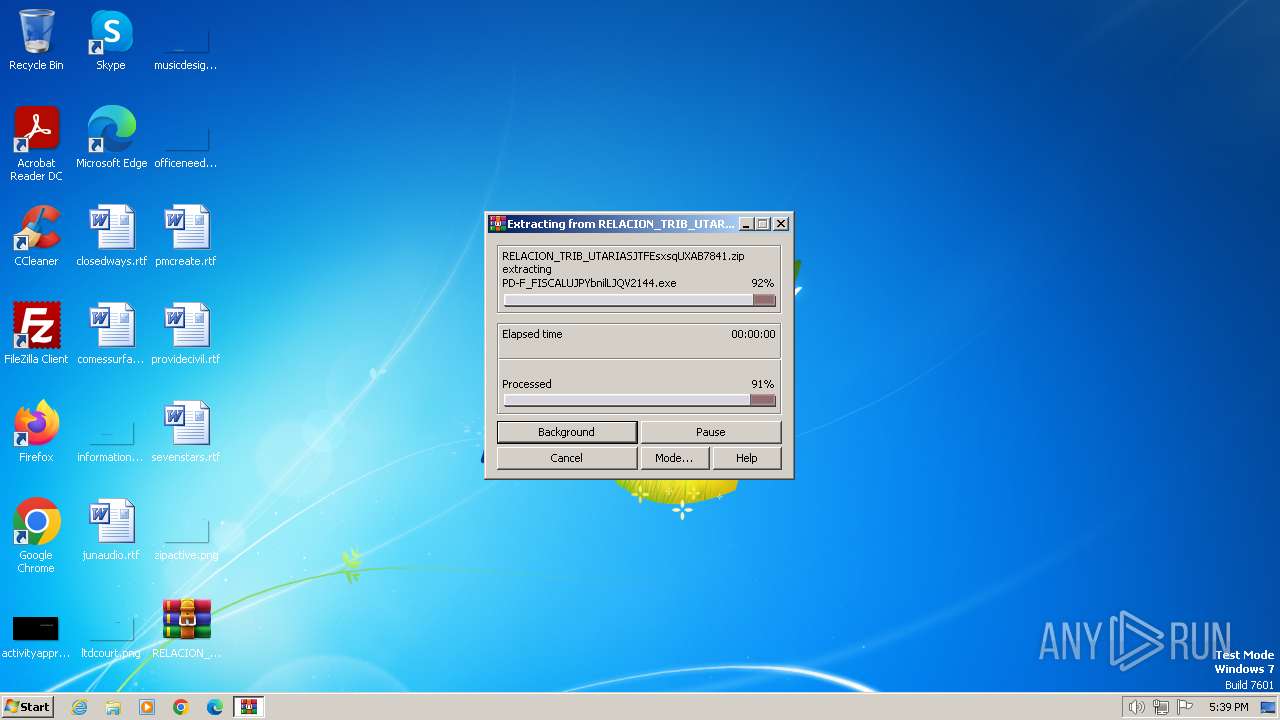
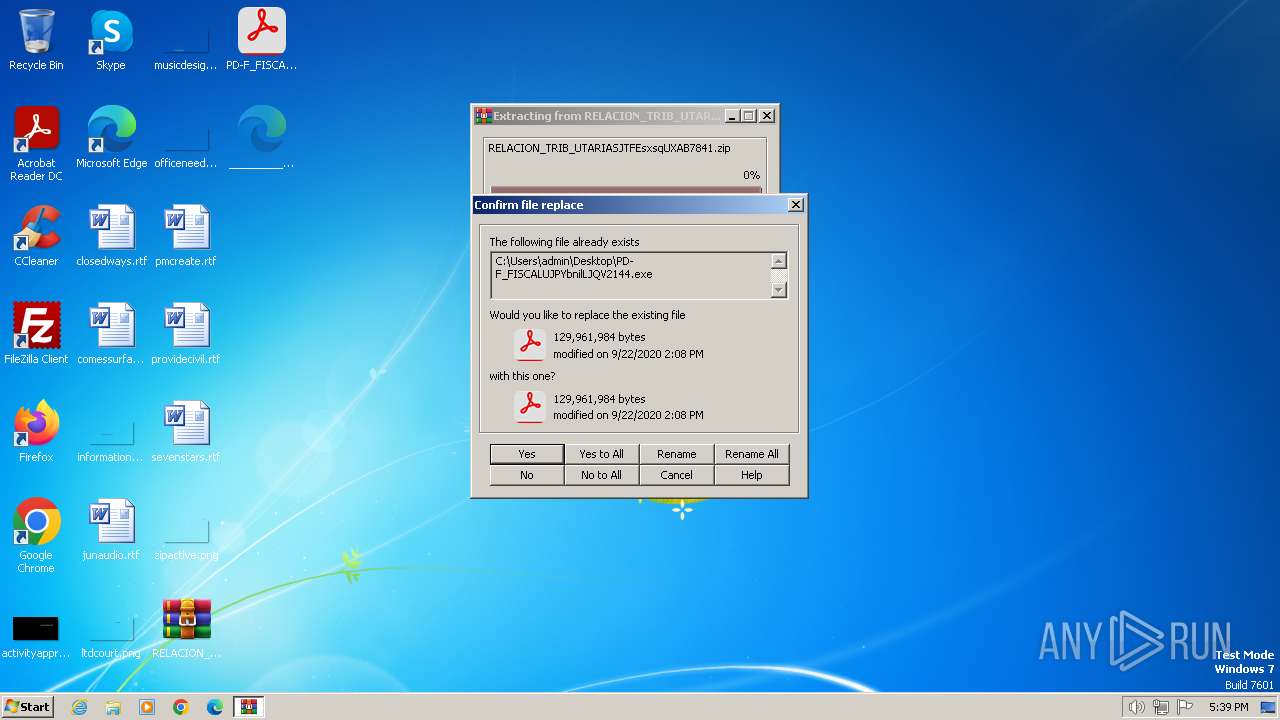
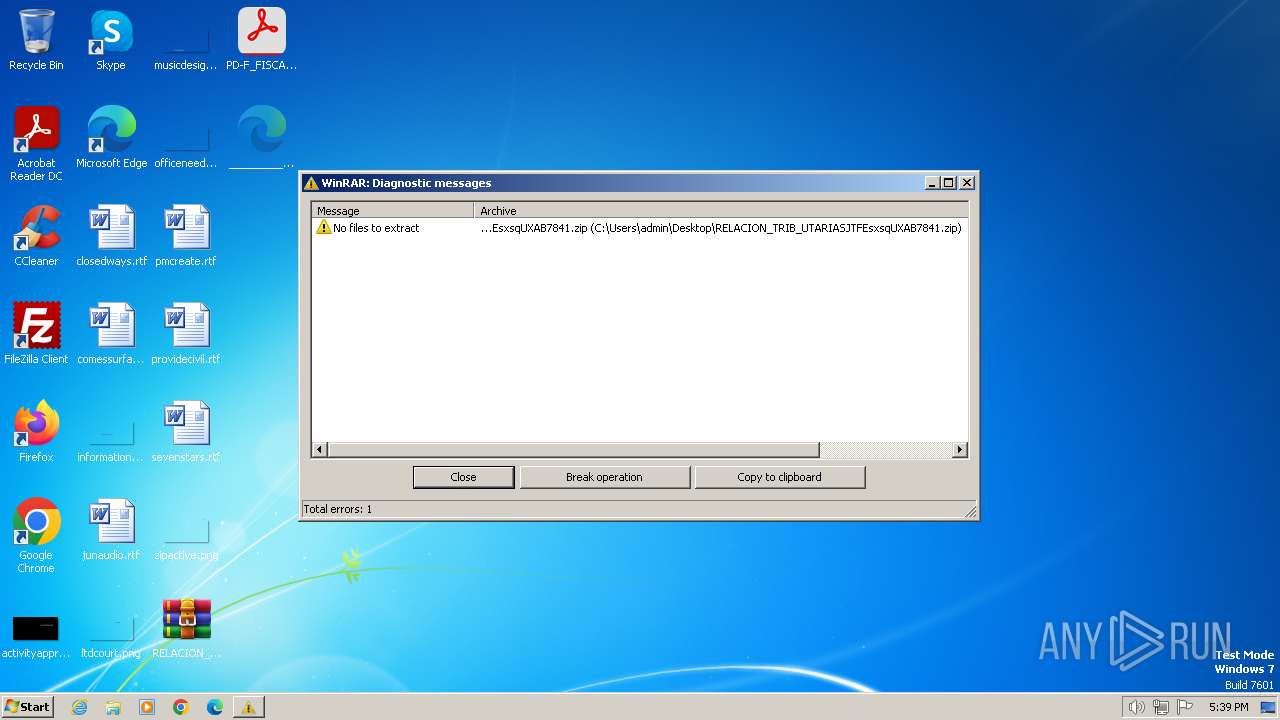
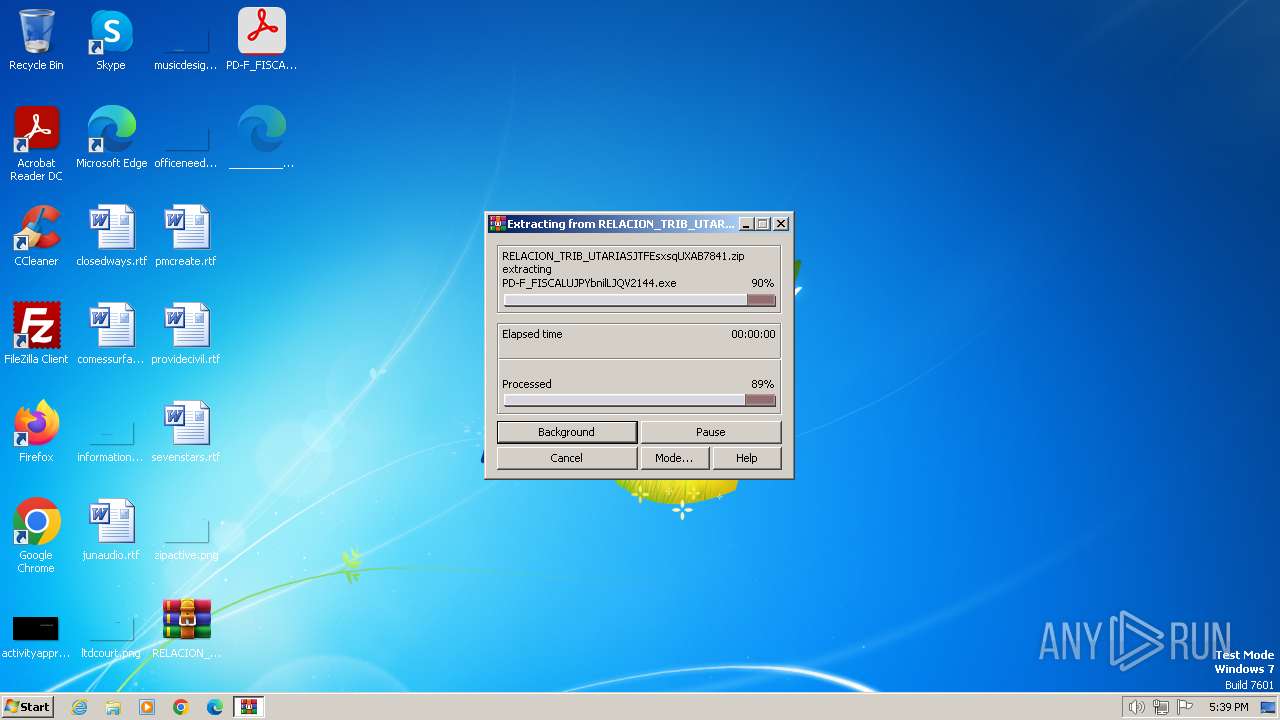
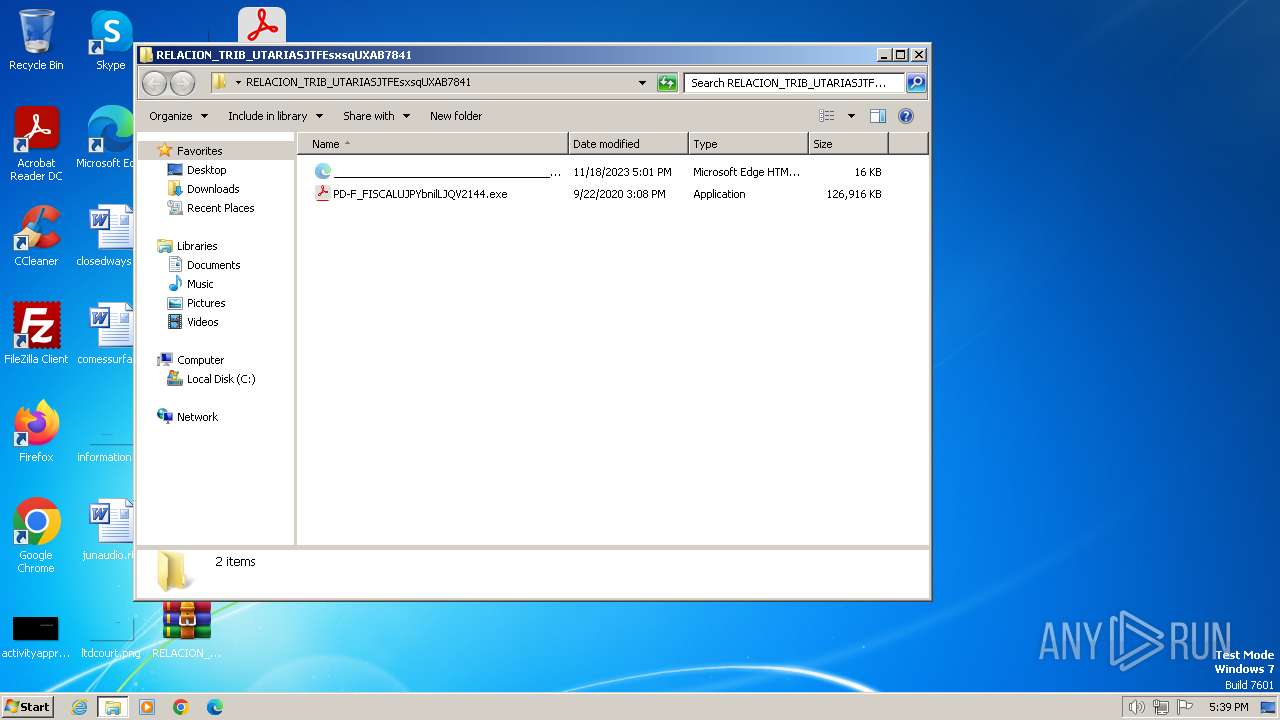
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3660)
- WinRAR.exe (PID: 120)
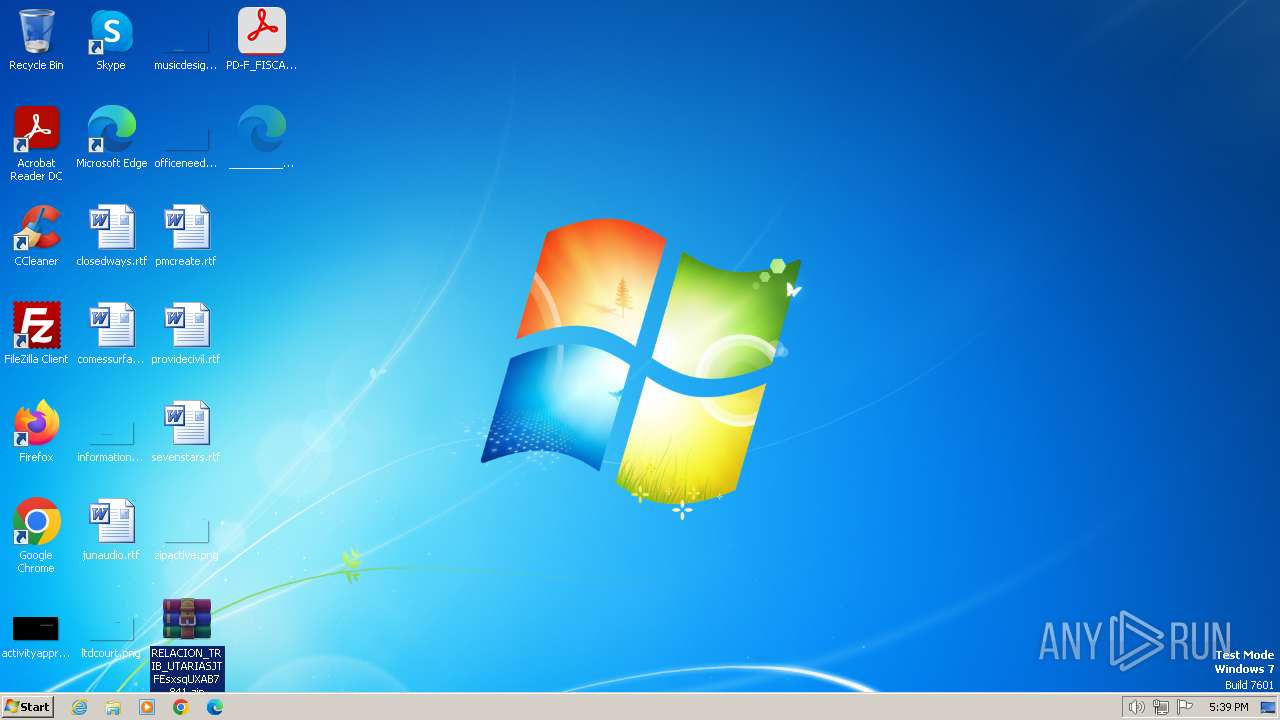
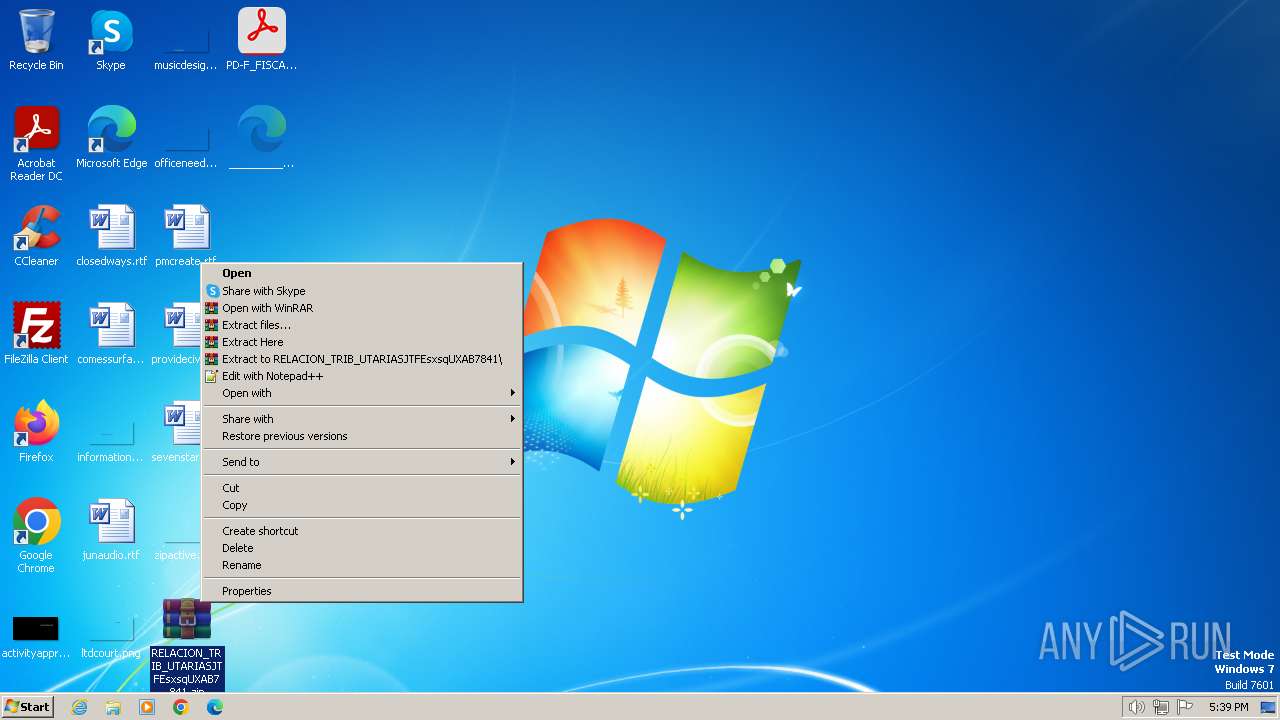
Manual execution by a user
- WinRAR.exe (PID: 3660)
- WinRAR.exe (PID: 2328)
- WinRAR.exe (PID: 120)
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
- wmpnscfg.exe (PID: 1740)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 120)
- WinRAR.exe (PID: 3660)
Reads CPU info
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
Checks supported languages
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
- wmpnscfg.exe (PID: 1740)
Reads the computer name
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
- wmpnscfg.exe (PID: 1740)
Reads the machine GUID from the registry
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
Reads the software policy settings
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
Creates files in the program directory
- PD-F_FISCALUJPYbnilLJQV2144.exe (PID: 3964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:09:22 15:08:36 |
| ZipCRC: | 0xf0537a52 |
| ZipCompressedSize: | 1963448 |
| ZipUncompressedSize: | 129961984 |
| ZipFileName: | PD-F_FISCALUJPYbnilLJQV2144.exe |
Total processes
43
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
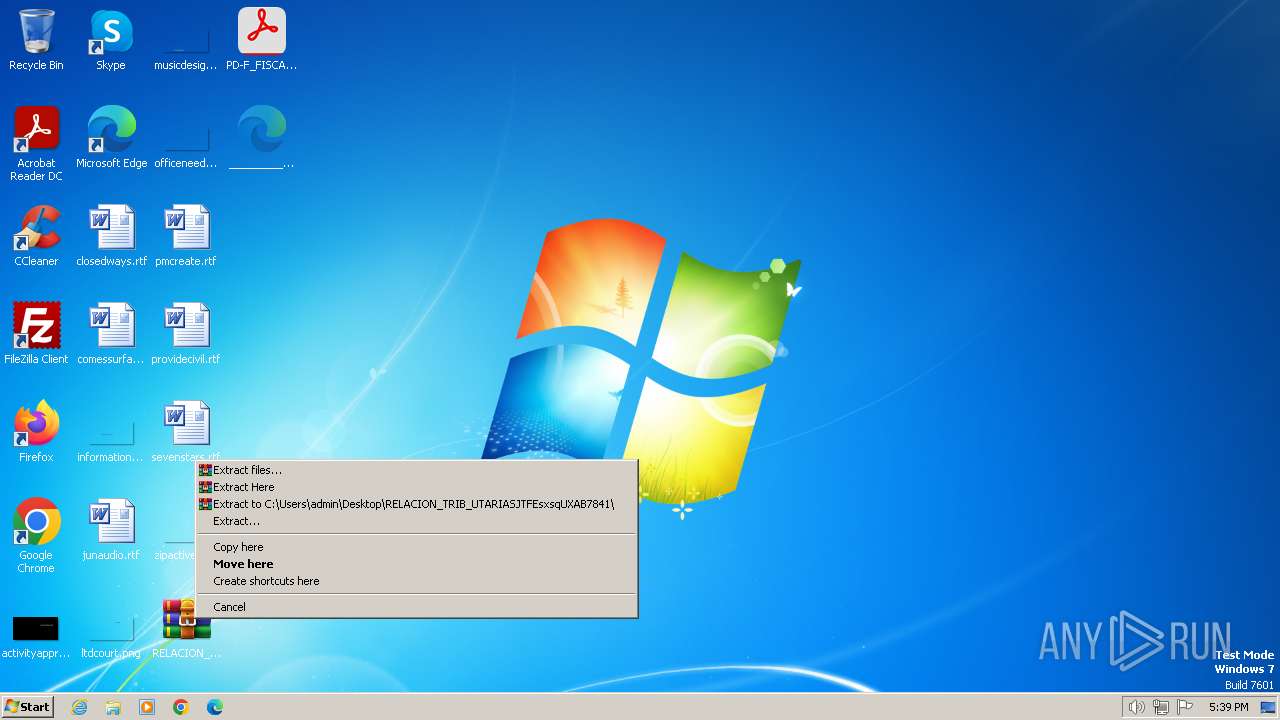
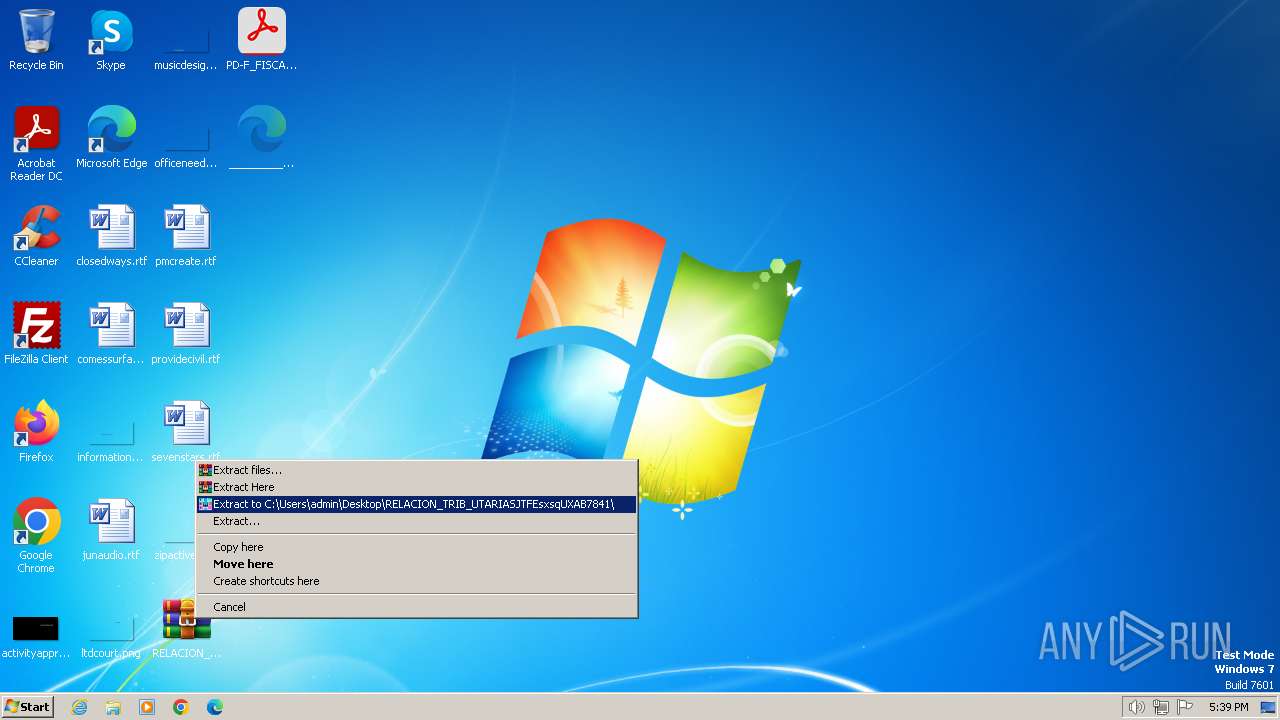
| 120 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841.zip" C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 10 Version: 5.91.0 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3660 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
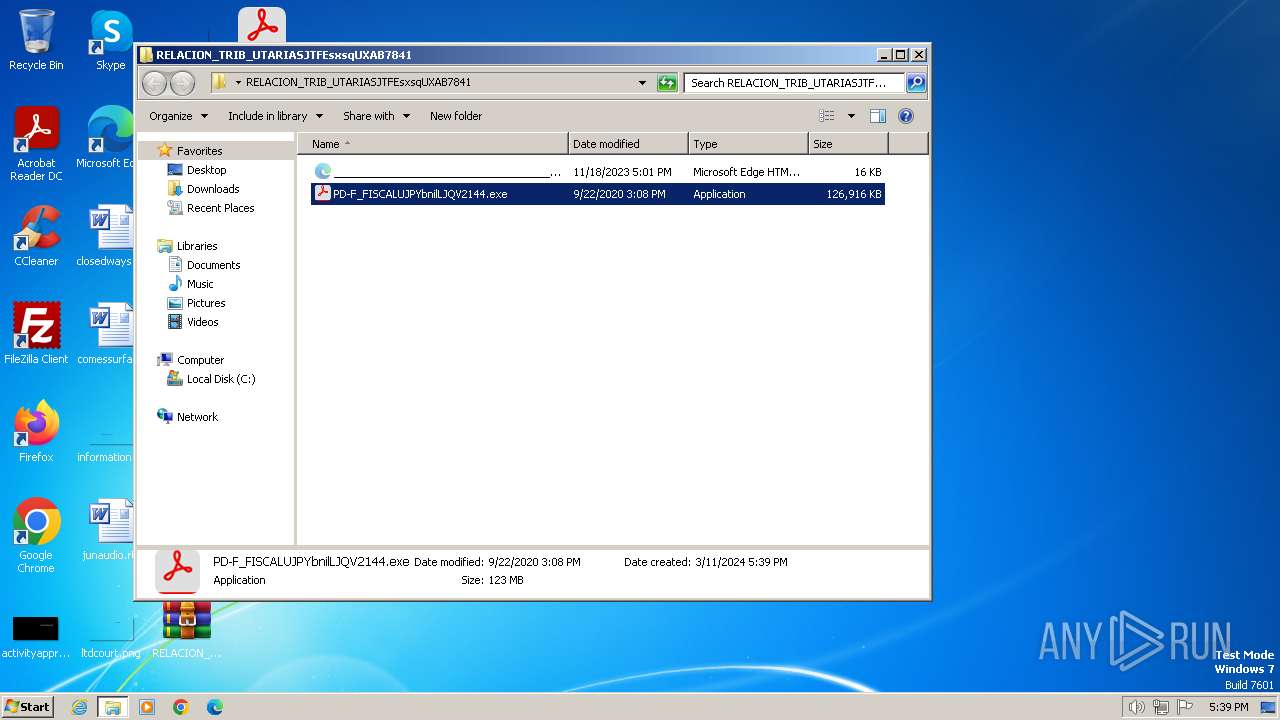
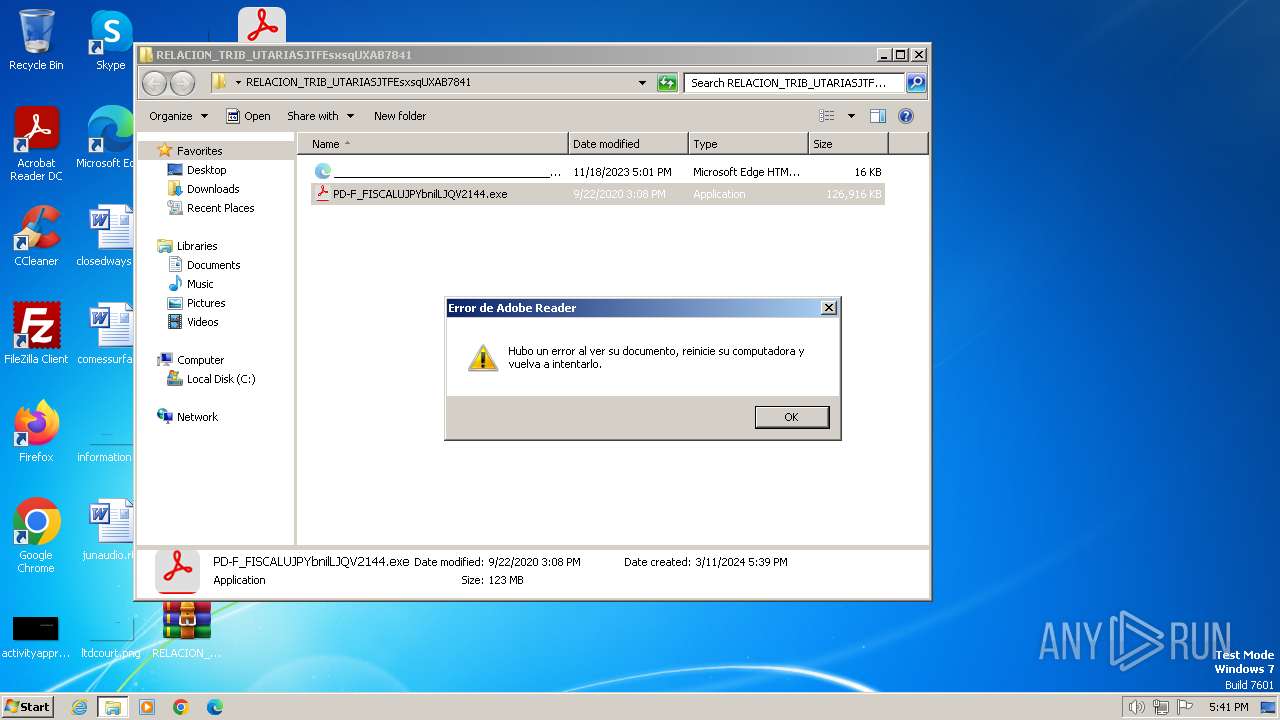
| 3964 | "C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841\PD-F_FISCALUJPYbnilLJQV2144.exe" | C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841\PD-F_FISCALUJPYbnilLJQV2144.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BreadBrock PDF Re-View 2 Exit code: 0 Version: 75.6002.411.7 Modules
| |||||||||||||||
Total events
7 635
Read events
7 581
Write events
54
Delete events
0
Modification events
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | WinRAR.exe | C:\Users\admin\Desktop\PD-F_FISCALUJPYbnilLJQV2144.exe | — | |
MD5:— | SHA256:— | |||
| 120 | WinRAR.exe | C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841\PD-F_FISCALUJPYbnilLJQV2144.exe | — | |
MD5:— | SHA256:— | |||
| 3660 | WinRAR.exe | C:\Users\admin\Desktop\___________________________________________________________________________________9052809621402231.xml | executable | |
MD5:4A77FB2014F6D9A165A139BD550916AE | SHA256:F2D850025DD7B65C44D979EC74A3F5A77E1C15B4070812BE5656887CEE95DC59 | |||
| 120 | WinRAR.exe | C:\Users\admin\Desktop\RELACION_TRIB_UTARIASJTFEsxsqUXAB7841\___________________________________________________________________________________9052809621402231.xml | executable | |
MD5:4A77FB2014F6D9A165A139BD550916AE | SHA256:F2D850025DD7B65C44D979EC74A3F5A77E1C15B4070812BE5656887CEE95DC59 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
12
DNS requests
4
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | GET | — | 208.95.112.1:80 | http://ip-api.com/json | unknown | — | — | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json | unknown | binary | 289 b | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json | unknown | binary | 289 b | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json | unknown | binary | 289 b | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json | unknown | binary | 289 b | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | GET | 200 | 15.229.10.166:4917 | http://15.229.10.166:4917/UU,WUV@VS)*VTW*STW)$%25TU@C$S,C,VX$)GPVW%25GV@W,VT,PXCX*G))T%25*SP)VWTG)W*)UV,,WTU%25WX$WU*$S%25P$P$%25@TQU,**QU$UT$UV@QWGGCGG@SW*%25TS$%25G)TUW,TCP*UQ,@QVW@%25V%25PX@W,PV$CT%25*CV,STQT%25%25TS$PP*SQC,TGXGXCV$%25XWWC)TUCPP,SQW$,QX%25SU*CQG%25*@SC*CUQ$)T$*%25TCT$@,VW*,QP%25@Q%25,GSS%25)W)*GPSC,@P%25TQT,GU),GQCPS)U)SV%25CSCPG%25$)XGUU*QG$VU$GU,$%25XQTCUT,$UG%25W,SQ,$WUQC@,SU%25$*T)UG*TU)%25@UPPQ$VXPV,%25QWS%25GX*%25)Q@@$VT%25XW*XCS,$PTTTXUU$VU%25),TPSUP)@$QVPT)%25QS$WWVTS%25C@@QVCC%25*WS),SV*,TU@CQ%25W)XW)G),*UXCCWTW,@$%25WU@,UT$*PX$G,XUWSTWQ$,QTT*GVT*WX@SUCVP%25@P%25)X*Q)%25WGC**U,P)P,$,SPPC%25XU)PG%25UW$V$@XGT)XWQX,*S)P@,TUUP$%25VS%25XXUP@GSW,$UCCS,%25G)*TTWW@VSWSTTTPWXSC*SQ,)*UWC$VU@WGU*PXWQS$%25W,%25SQ*V%25TSTUX)WG*SUV$UUQ$GQ%25$QQ%25)PSX*$T)UC)CUW$@VQ*PQXCP%25VGTGG*QQ)P%25PS*$Q*$@GPCVG%25*QGC%25GV%25SW%25X%25*VX$ST,WV%25PQ%25%25WGQ$WQ*$UTVG)CQS,,US$,TX%25*TVS,*T$SW,SQ*$QUP$VTW*XTWWGXGVC$)QQPX)TVT%25TGT@@GV$USW@$V)PX@WGC)Q*$T%25**U%25)Q@*@PC$@)@S@U | unknown | text | 746 b | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | GET | — | 15.229.10.166:6017 | http://15.229.10.166:6017/qCjccY.xml | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | 8.8.4.4:443 | dns.google | GOOGLE | US | whitelisted |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | 15.229.10.166:4917 | — | AMAZON-02 | BR | unknown |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | 15.229.10.166:6017 | — | AMAZON-02 | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
dns.google |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (Clever Internet Suite) |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (Clever Internet Suite) |
— | — | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
— | — | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (Clever Internet Suite) |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3964 | PD-F_FISCALUJPYbnilLJQV2144.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (Clever Internet Suite) |