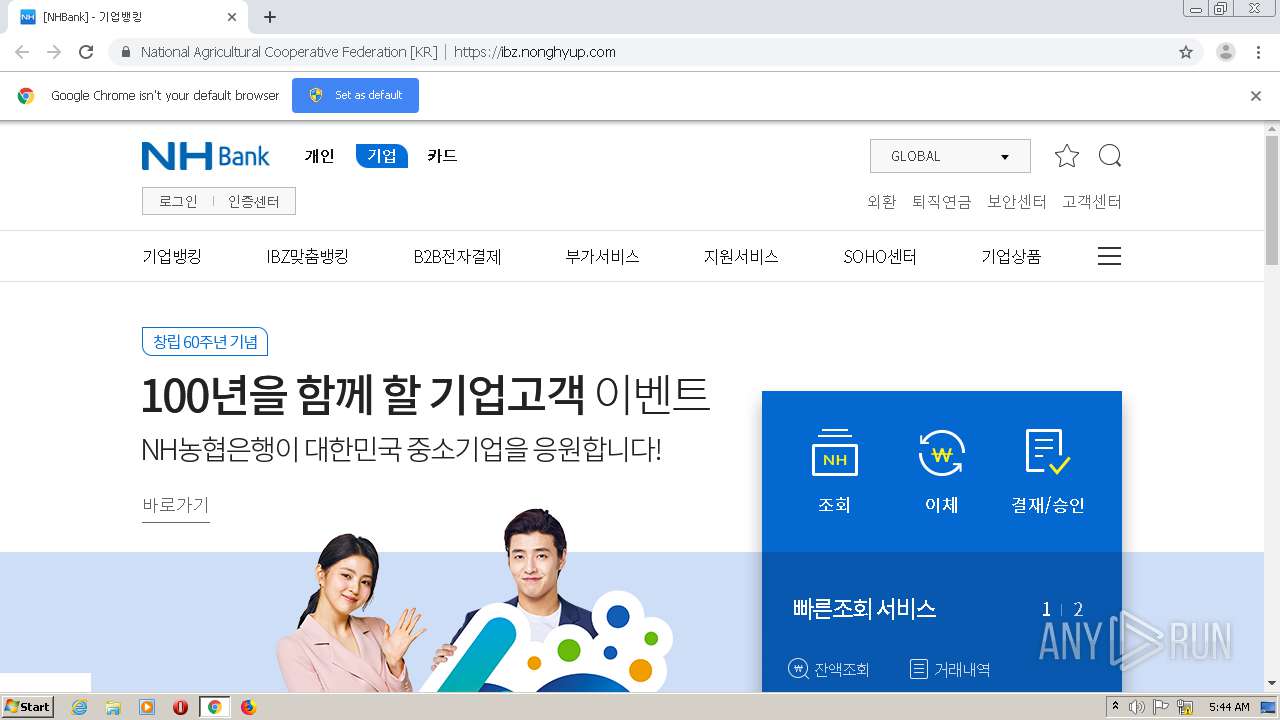
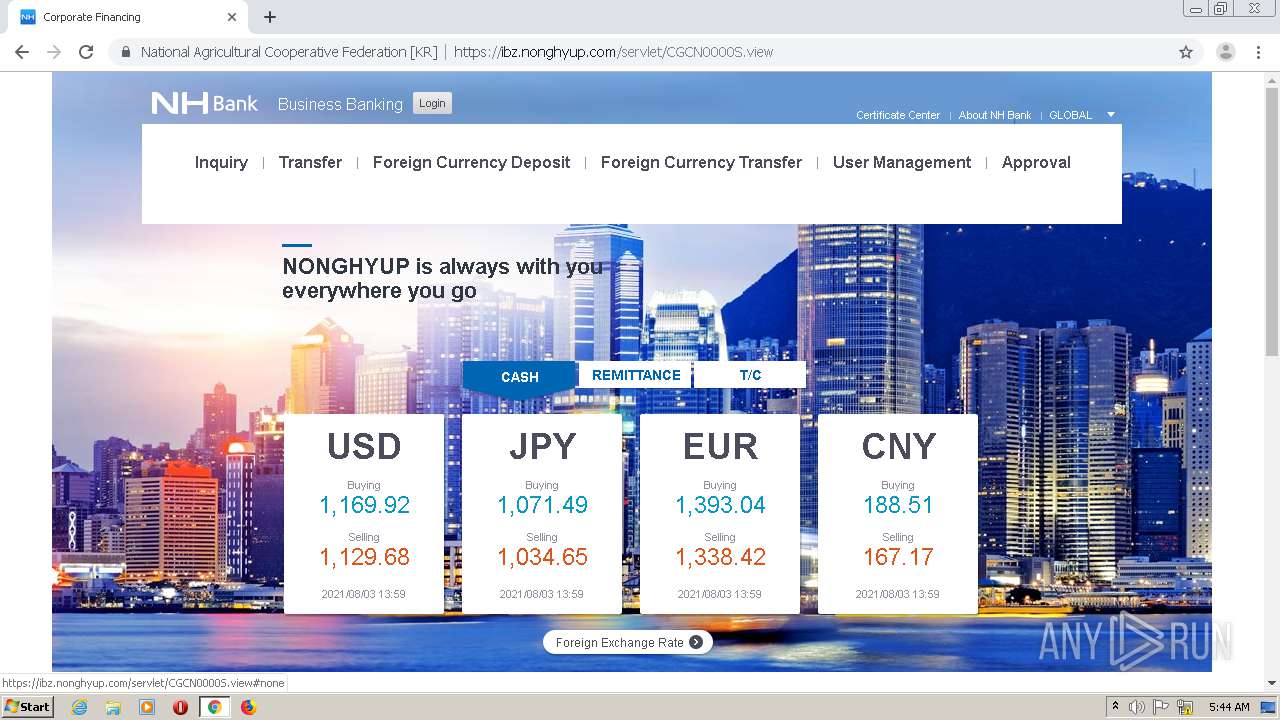
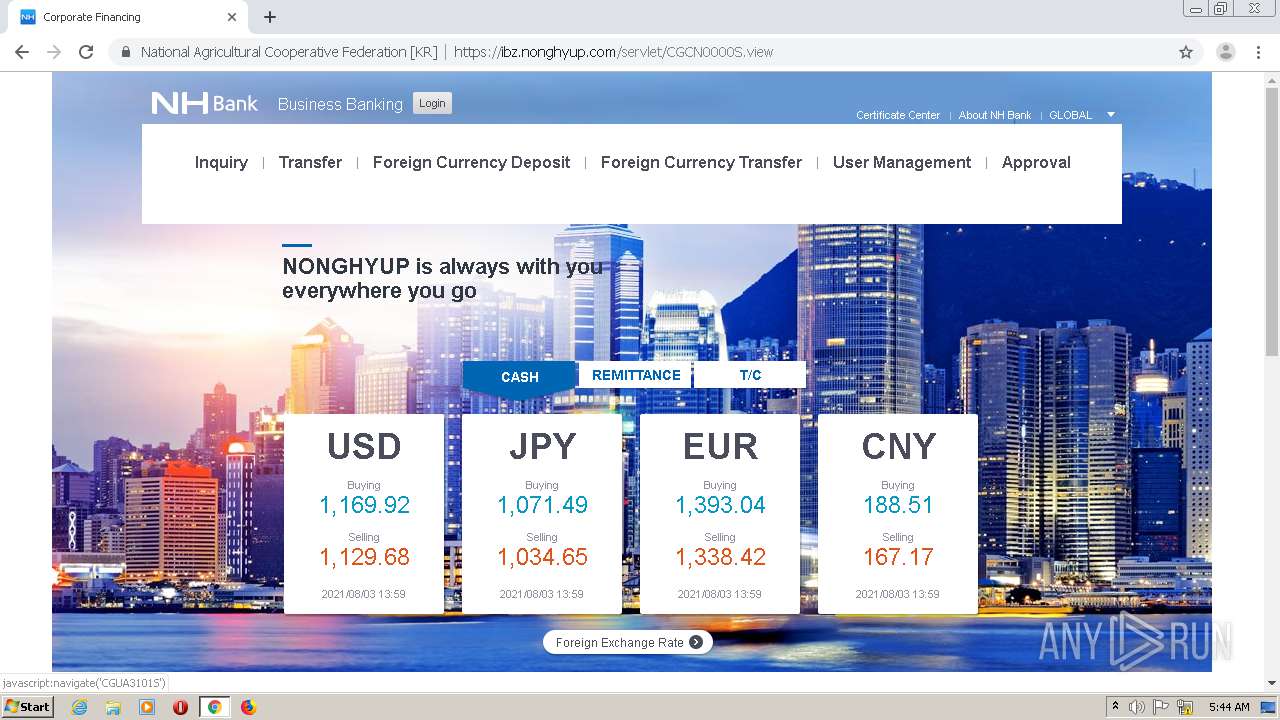
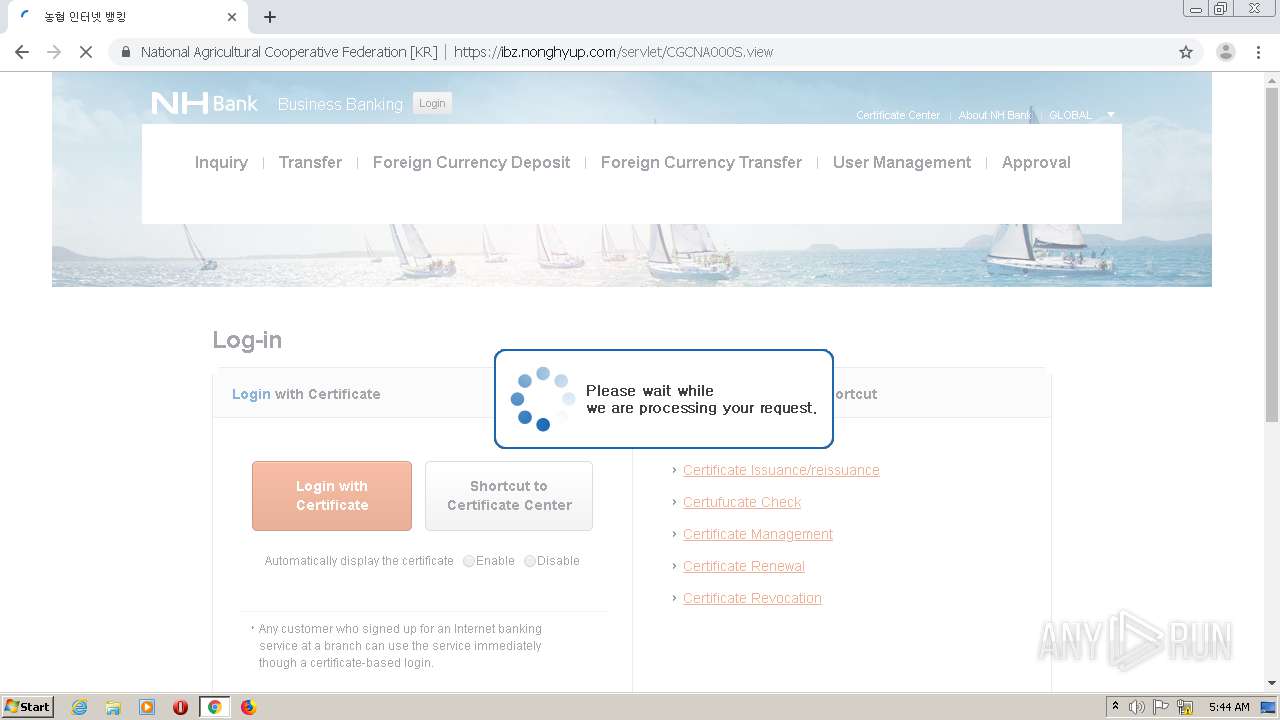
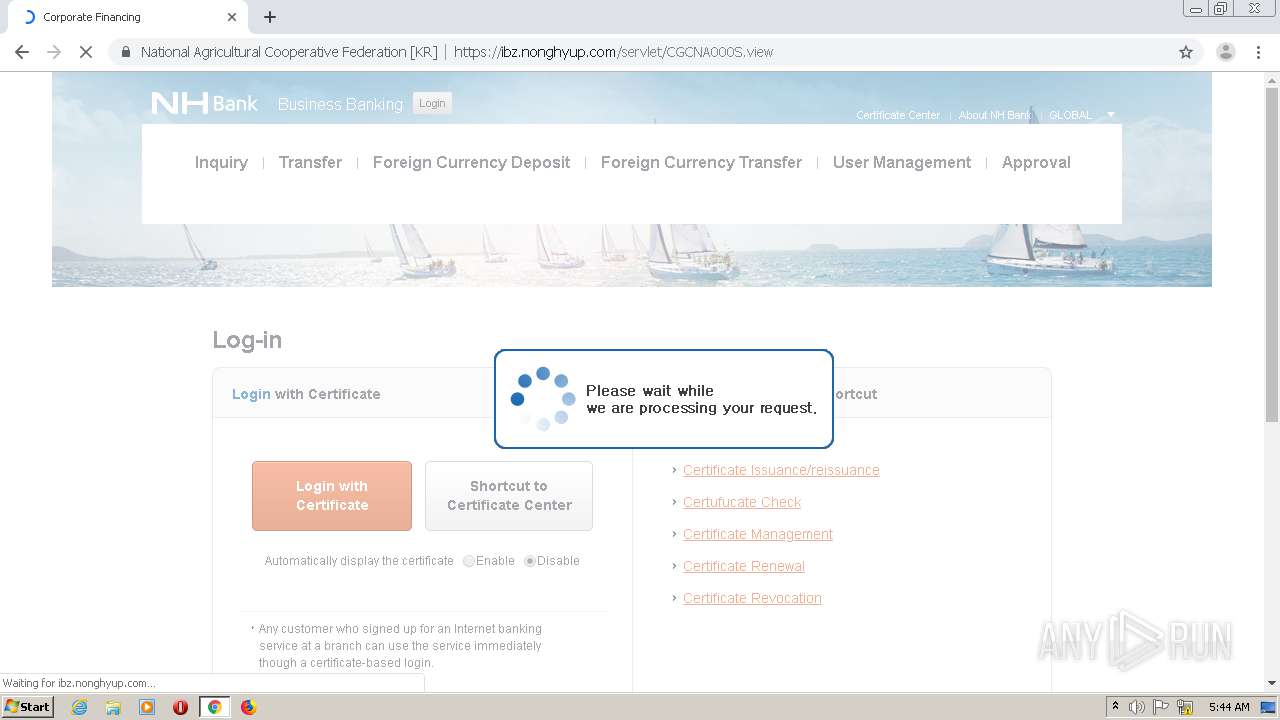
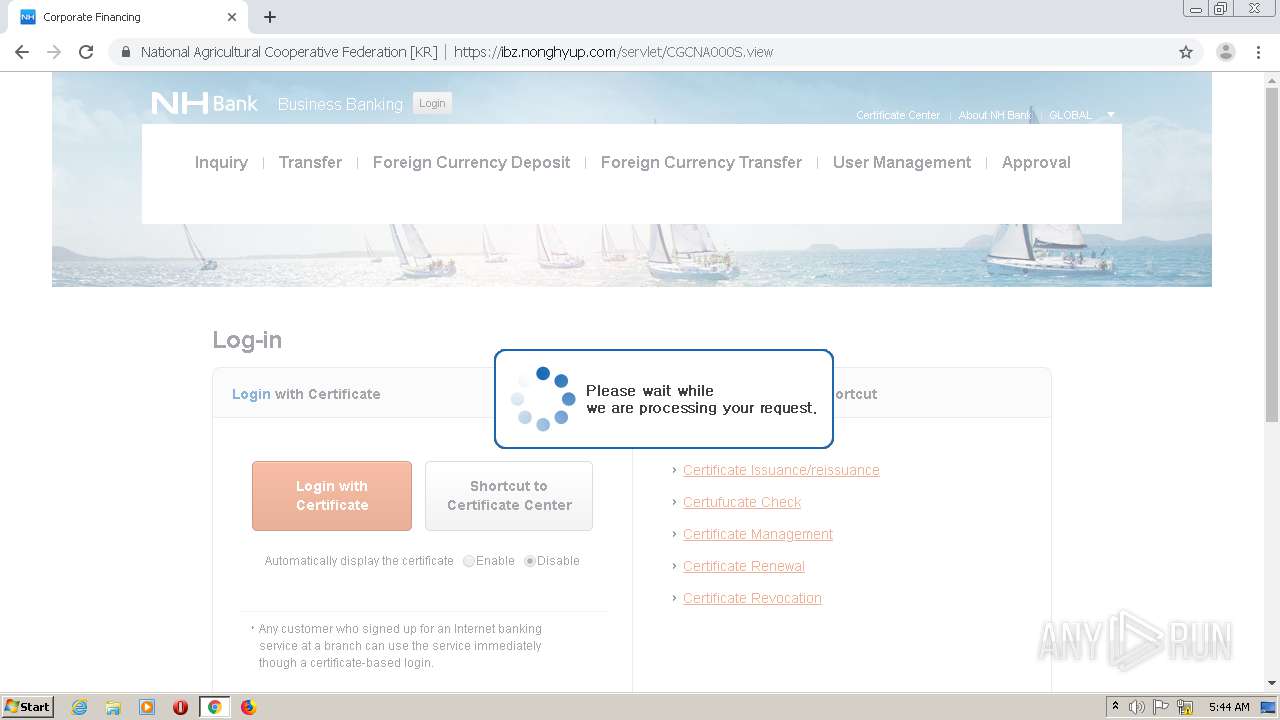
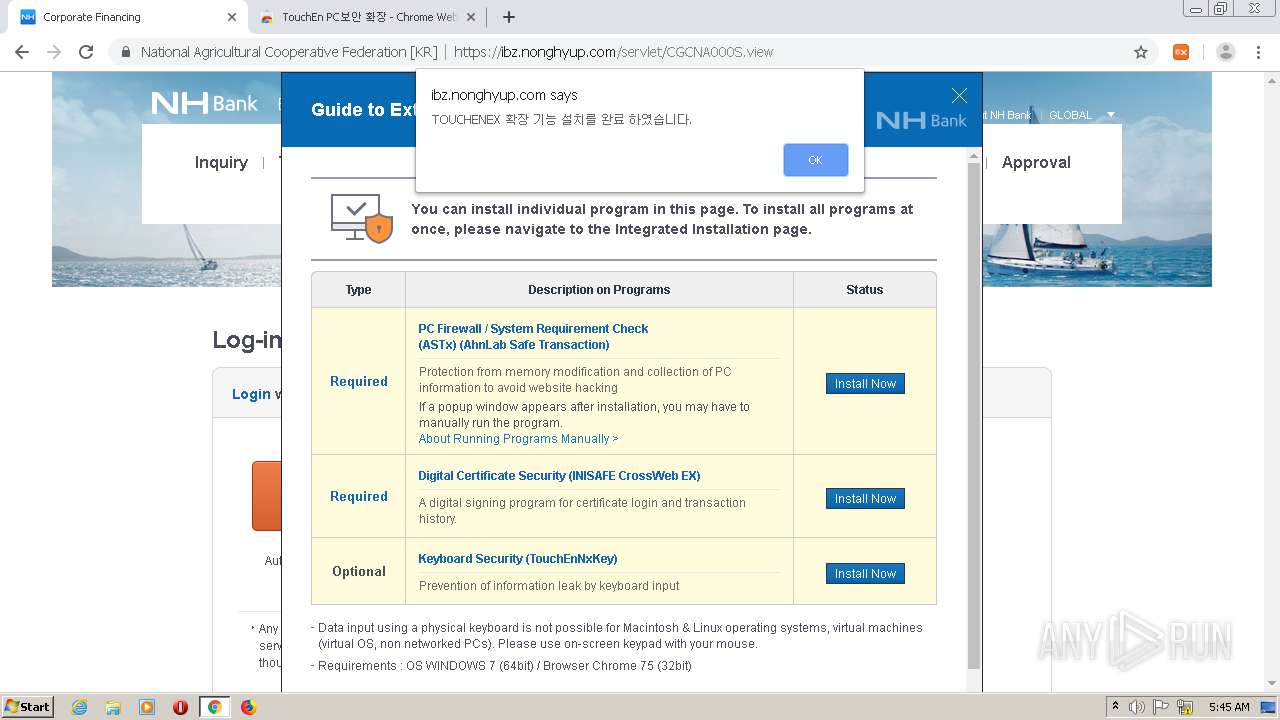
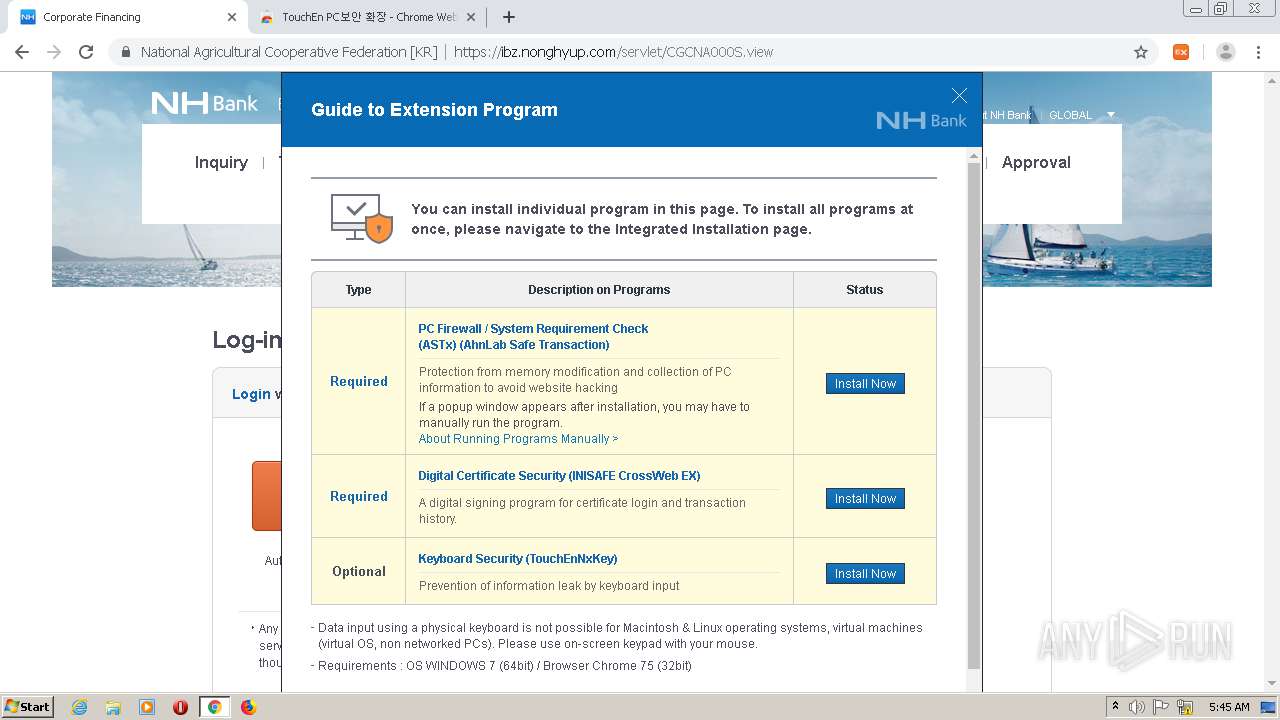
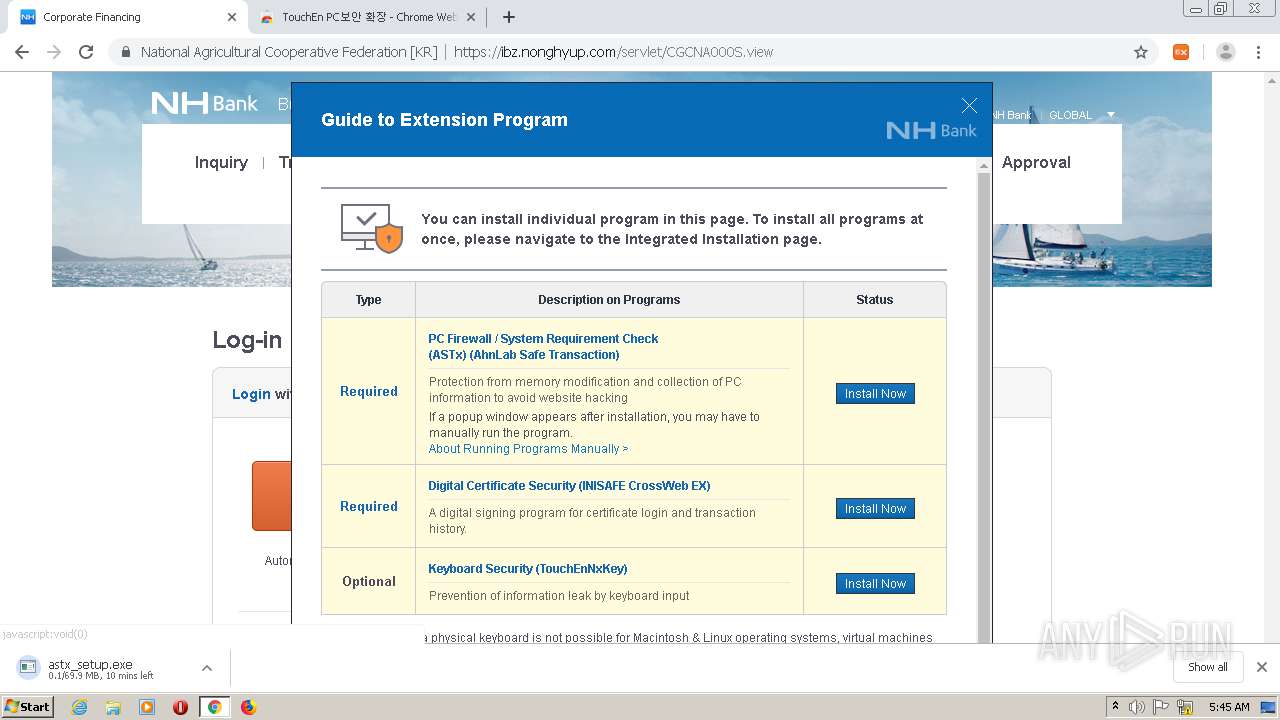
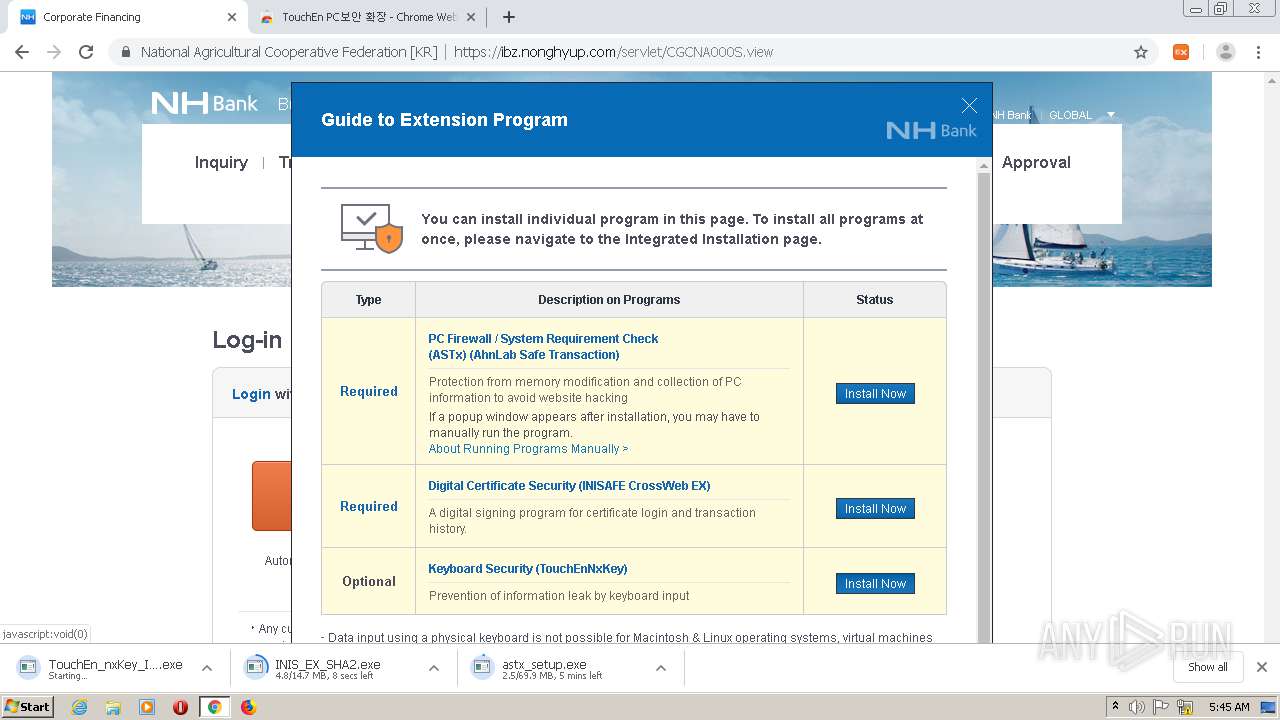
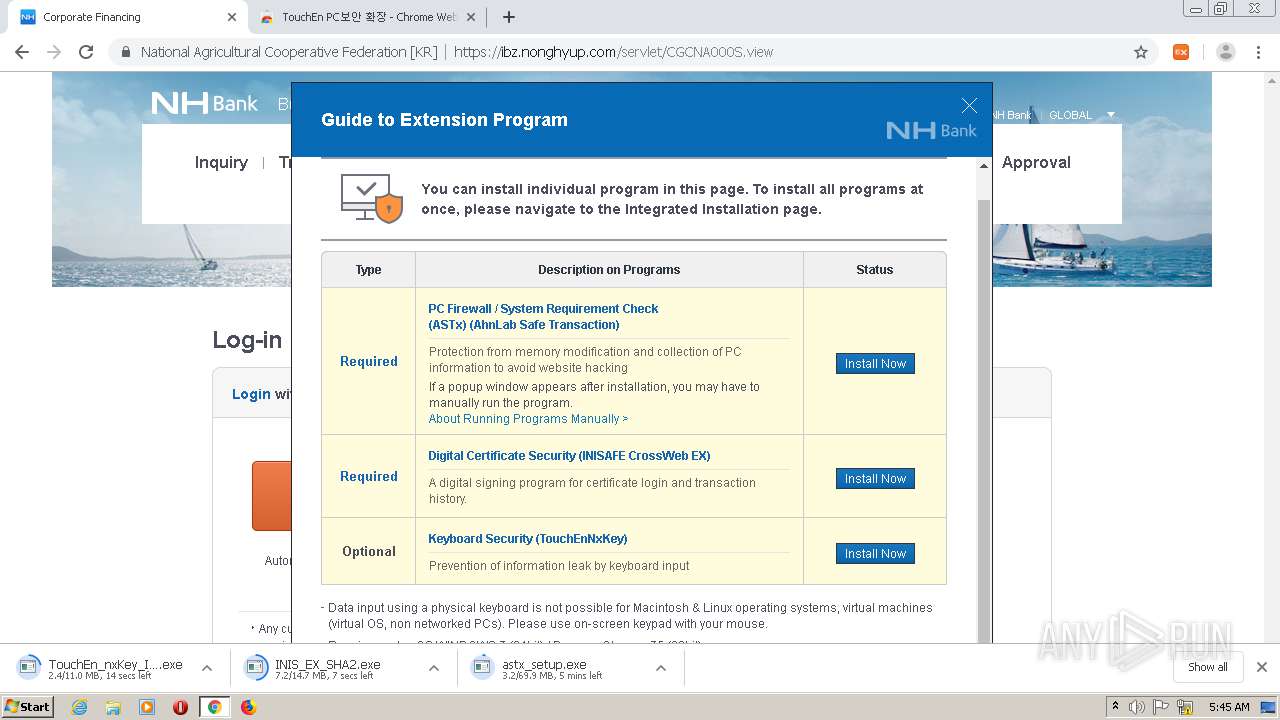
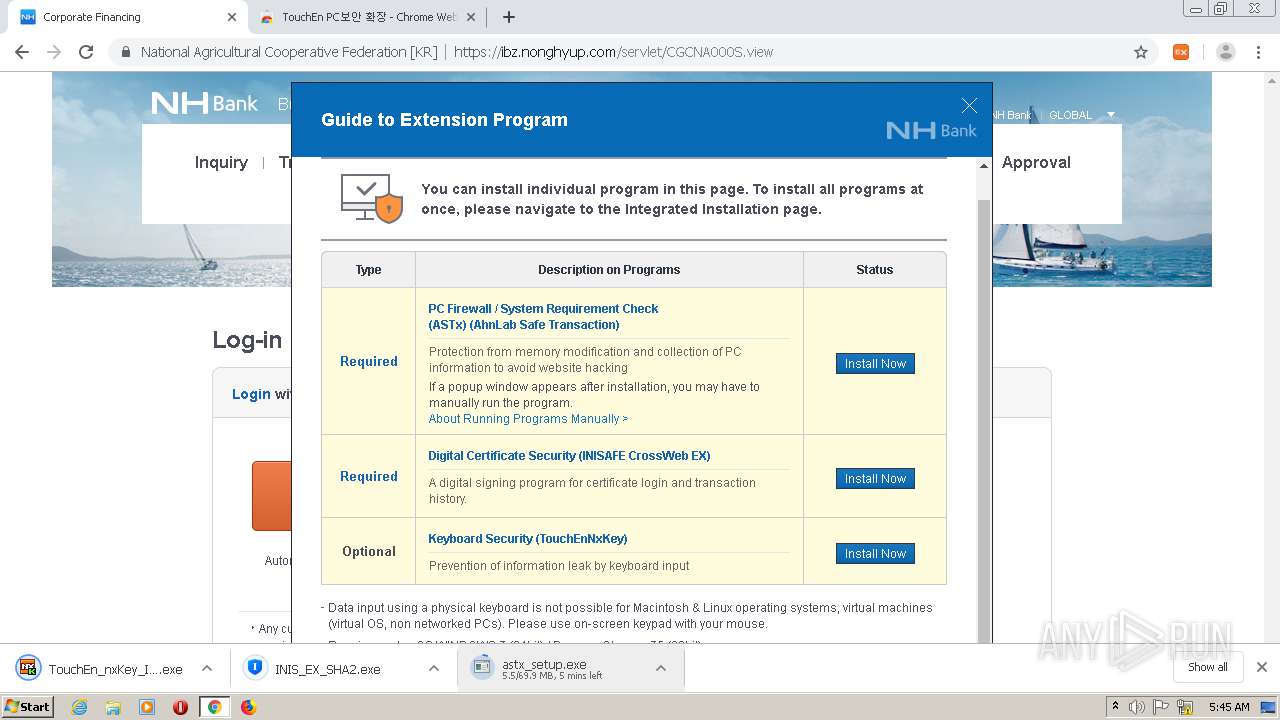
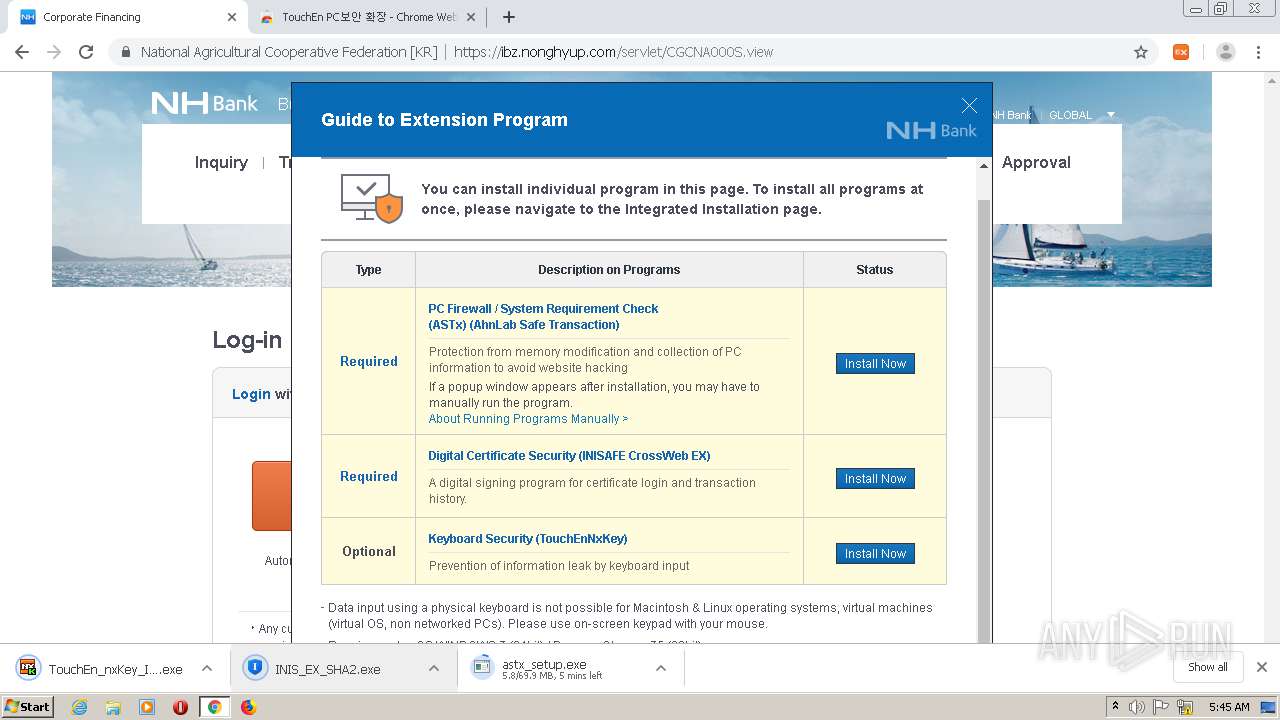
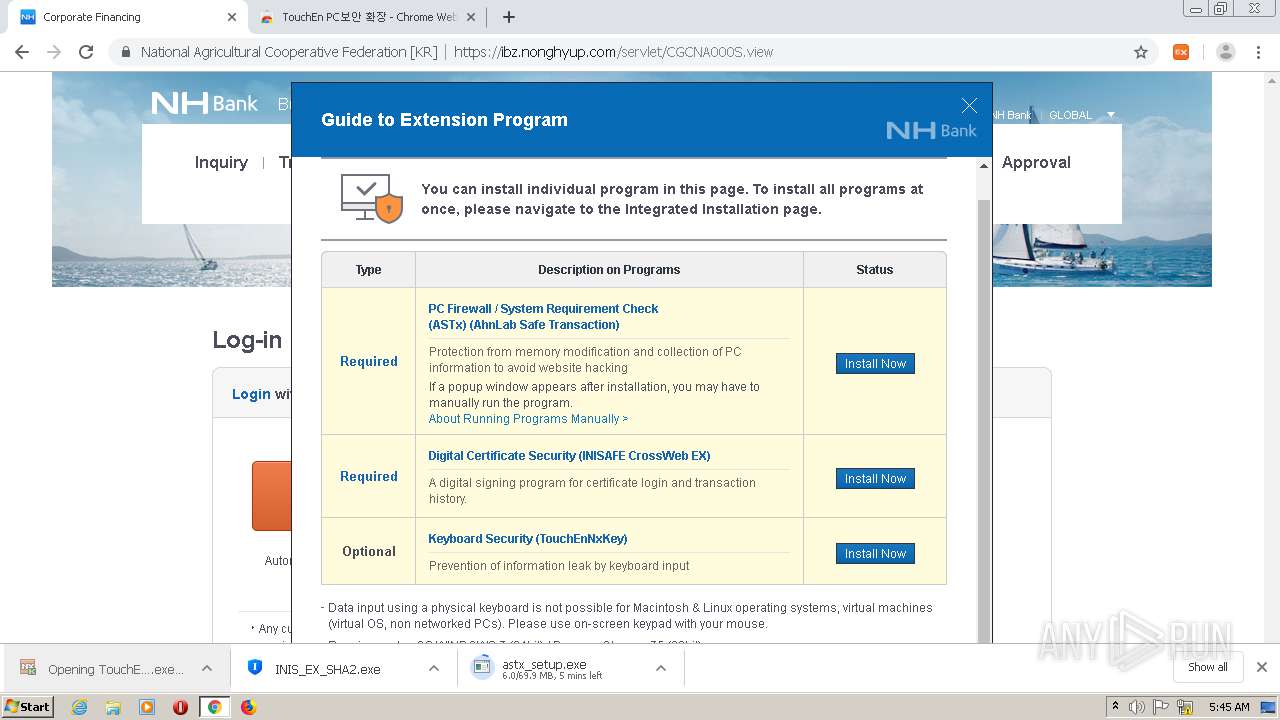
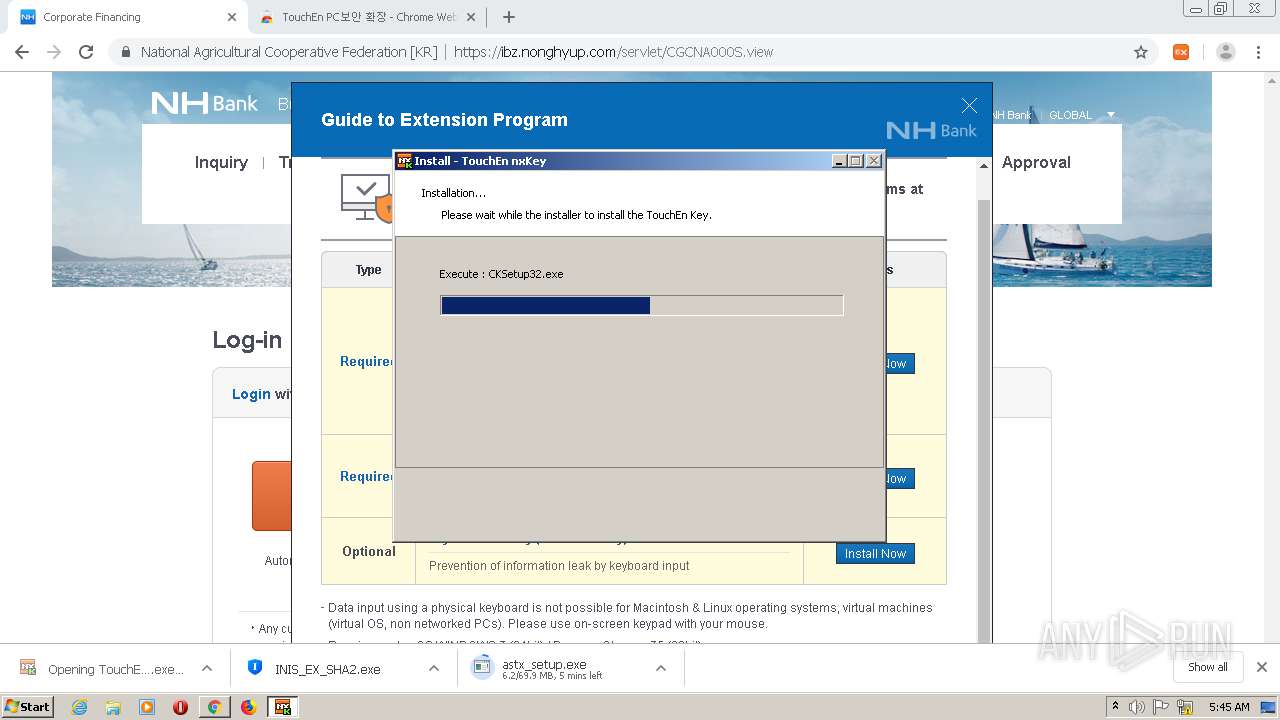
| URL: | https://ibz.nonghyup.com/ |
| Full analysis: | https://app.any.run/tasks/fd803c40-55c4-474e-8428-e8f997c9694a |
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2021, 05:43:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MD5: | 2B8312903933BD6A14777E7A1227FDF9 |
| SHA1: | 8F28010515F14D7E96EA76067C4E45DB5E02B7B9 |
| SHA256: | D1A8EB0C0C42EE737D924DBA0B2BA9031FC0F43FEBF2BFE10BD78DCAB60474ED |
| SSDEEP: | 3:N8WL0CH:2WICH |
MALICIOUS
Application was dropped or rewritten from another process
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 2960)
- CKSetup32.exe (PID: 1408)
- CKSetup64.exe (PID: 3952)
- CKSetup64.exe (PID: 3152)
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- FFCert.exe (PID: 3404)
- ObCrossEXService.exe (PID: 2940)
- certutil.exe (PID: 2748)
- certutil.exe (PID: 3708)
- Firefox_CertUtil.exe (PID: 3580)
- CrossEXChrome.exe (PID: 1292)
- ckagentNXE.exe (PID: 1772)
- CrossEXService.exe (PID: 3784)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2832)
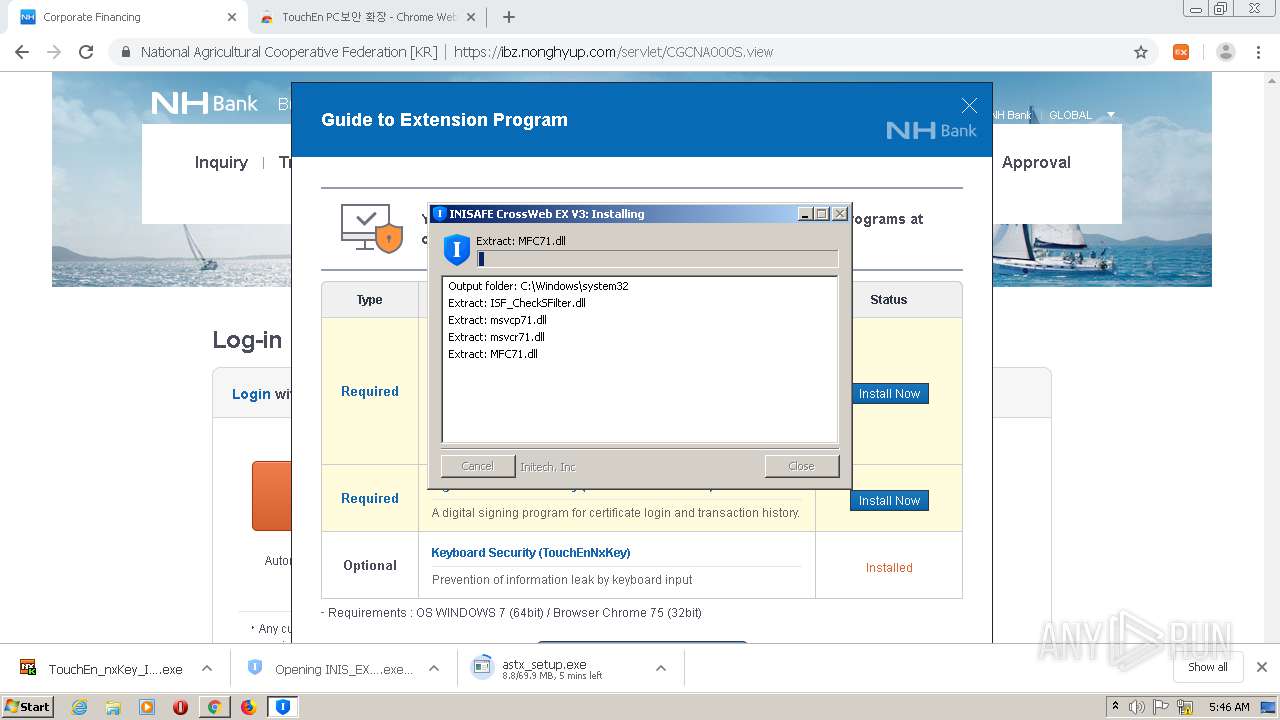
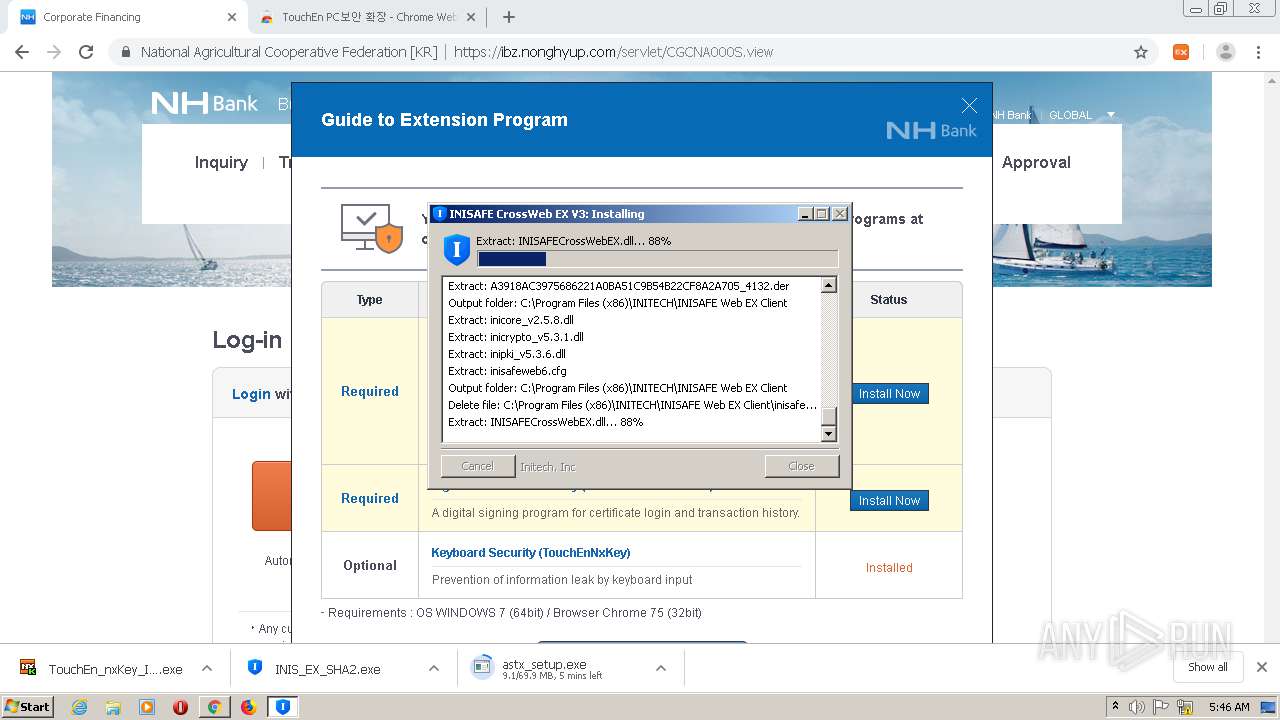
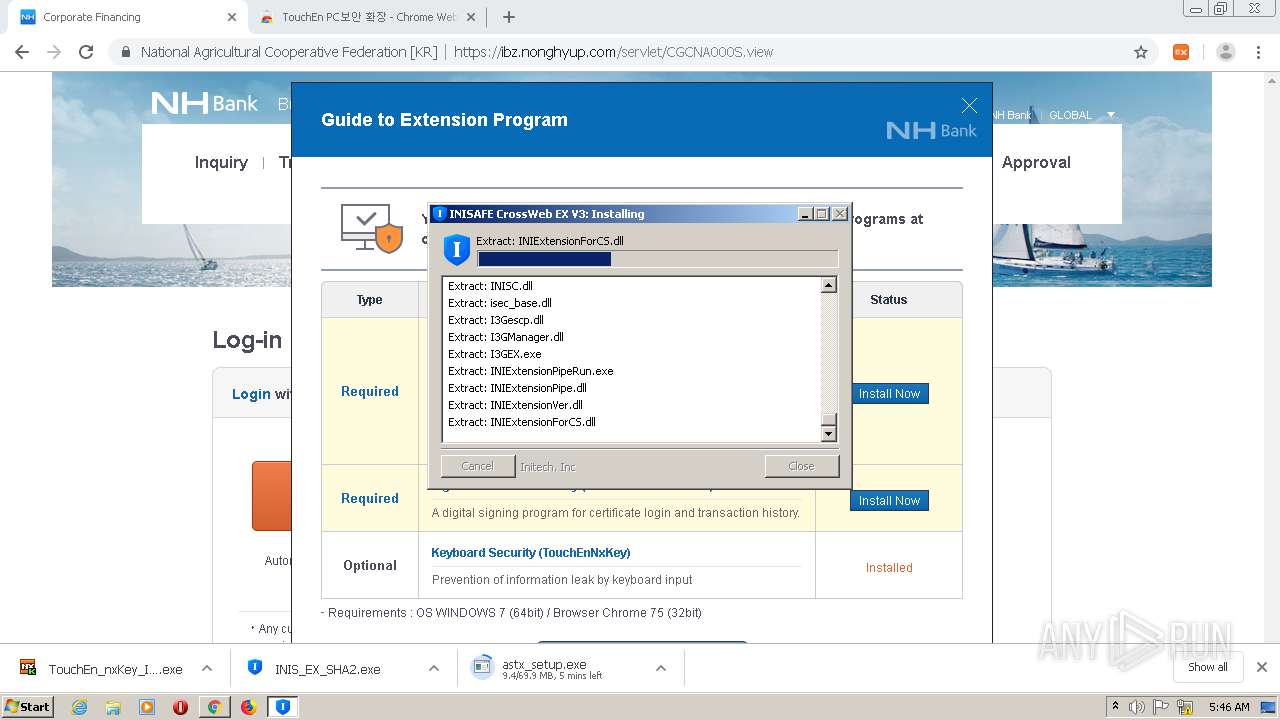
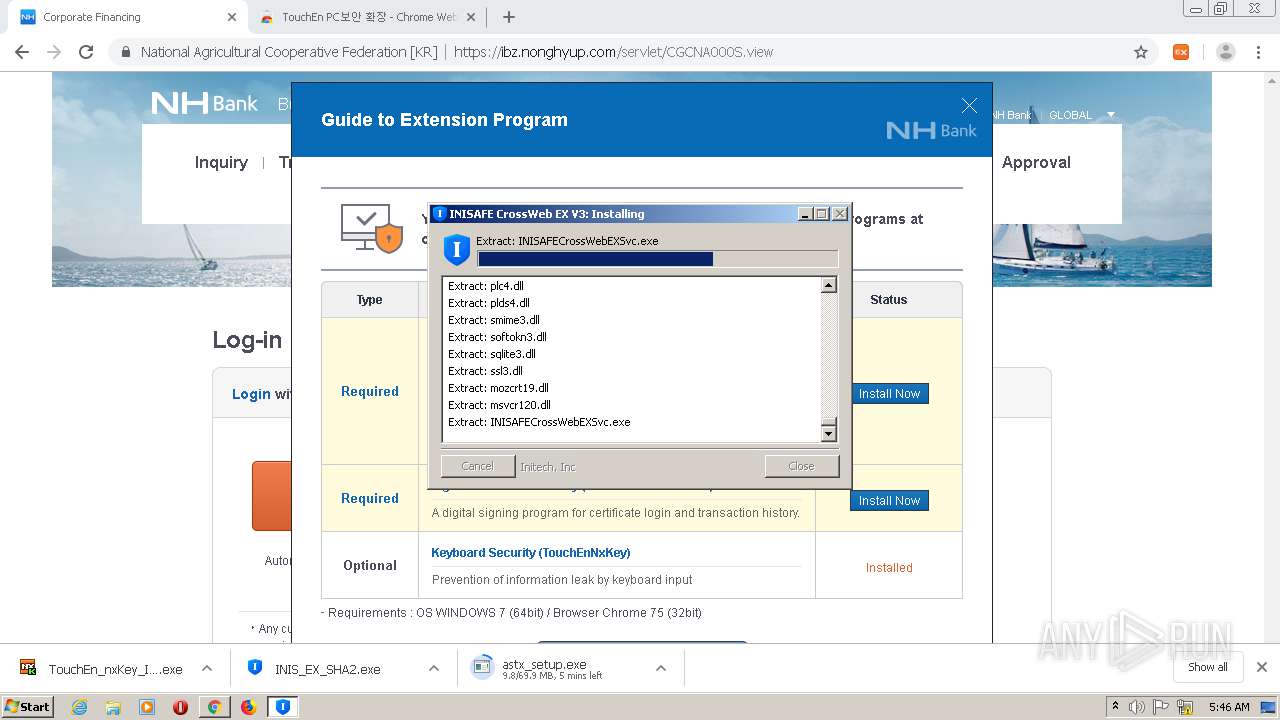
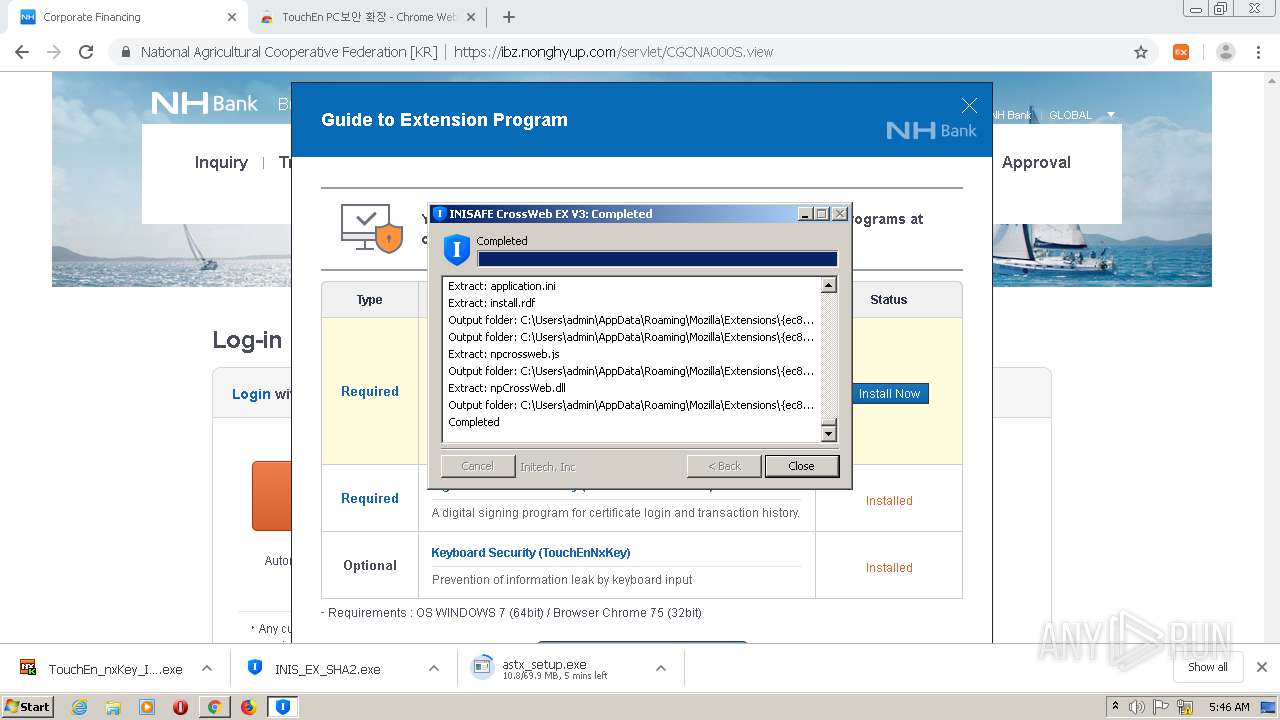
- INIS_EX_SHA2.exe (PID: 500)
- INIS_EX_SHA2.exe (PID: 3956)
- INISAFETrayEX.exe (PID: 3684)
- iniline_crosswebex_Install.exe (PID: 3544)
- KillBrowser.exe (PID: 1600)
- certutil.exe (PID: 3452)
- certutil.exe (PID: 2712)
- INISAFEAdminUtil.exe (PID: 3704)
- INISAFECrossWebEXSvc.exe (PID: 3748)
- INISAFETrayEX.exe (PID: 2608)
- IniClientSvc_x64.exe (PID: 2500)
Drops executable file immediately after starts
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- CKSetup32.exe (PID: 1408)
- CKSetup64.exe (PID: 3952)
- CKSetup64.exe (PID: 3152)
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- FFCert.exe (PID: 3404)
- INIS_EX_SHA2.exe (PID: 3956)
- INIS_EX_SHA2.exe (PID: 500)
- iniline_crosswebex_Install.exe (PID: 3544)
- DllHost.exe (PID: 2960)
Changes settings of System certificates
- CrossEX_LocalService_Install.exe (PID: 2776)
- IniClientSvc_x64.exe (PID: 2500)
Changes the autorun value in the registry
- CrossEX_LocalService_Install.exe (PID: 2776)
Loads dropped or rewritten executable
- CrossEX_LocalService_Install.exe (PID: 2776)
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- raon_touchenex_Install.exe (PID: 2236)
- certutil.exe (PID: 2748)
- certutil.exe (PID: 2832)
- certutil.exe (PID: 3708)
- CrossEXChrome.exe (PID: 1292)
- certutil.exe (PID: 3724)
- ckagentNXE.exe (PID: 1772)
- INIS_EX_SHA2.exe (PID: 500)
- INISAFETrayEX.exe (PID: 3684)
- INIS_EX_SHA2.exe (PID: 3956)
- iniline_crosswebex_Install.exe (PID: 3544)
- certutil.exe (PID: 2712)
- certutil.exe (PID: 3452)
- INISAFEAdminUtil.exe (PID: 3704)
- INISAFETrayEX.exe (PID: 2608)
- INISAFECrossWebEXSvc.exe (PID: 3748)
Steals credentials from Web Browsers
- Firefox_CertUtil.exe (PID: 3580)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2832)
- certutil.exe (PID: 2748)
- certutil.exe (PID: 2712)
Actions looks like stealing of personal data
- Firefox_CertUtil.exe (PID: 3580)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2748)
- certutil.exe (PID: 2832)
- certutil.exe (PID: 2712)
SUSPICIOUS
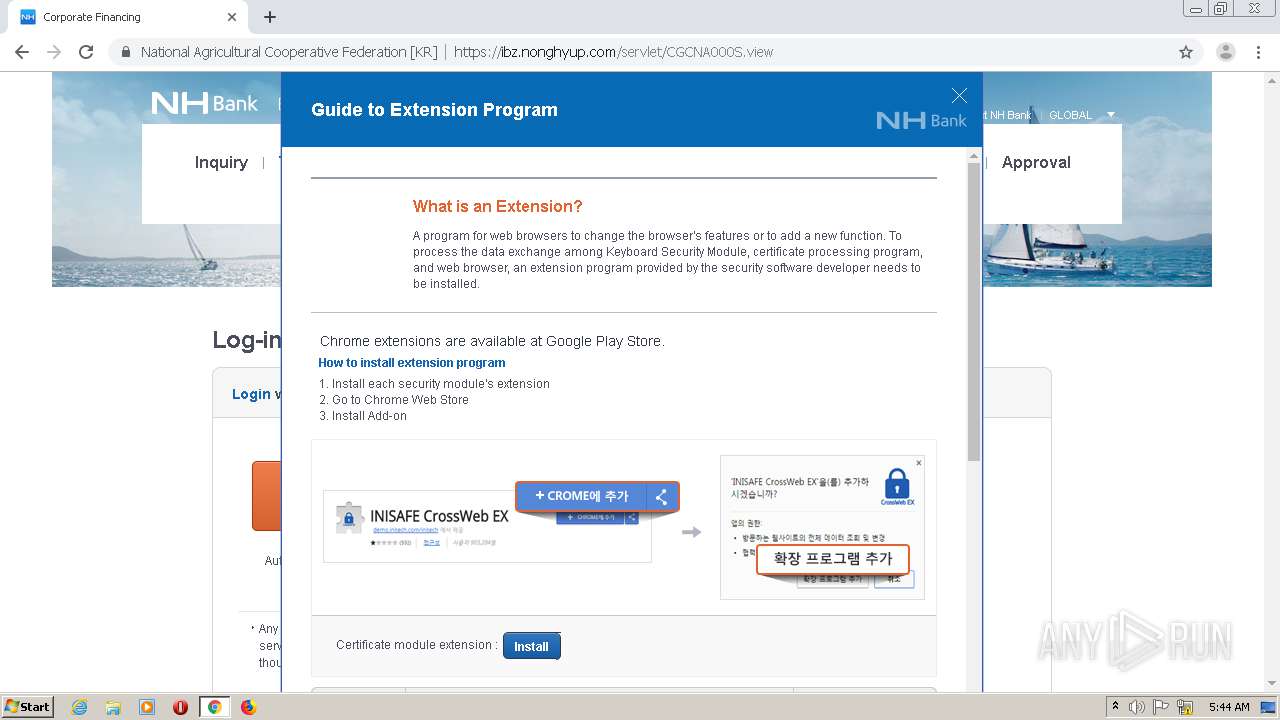
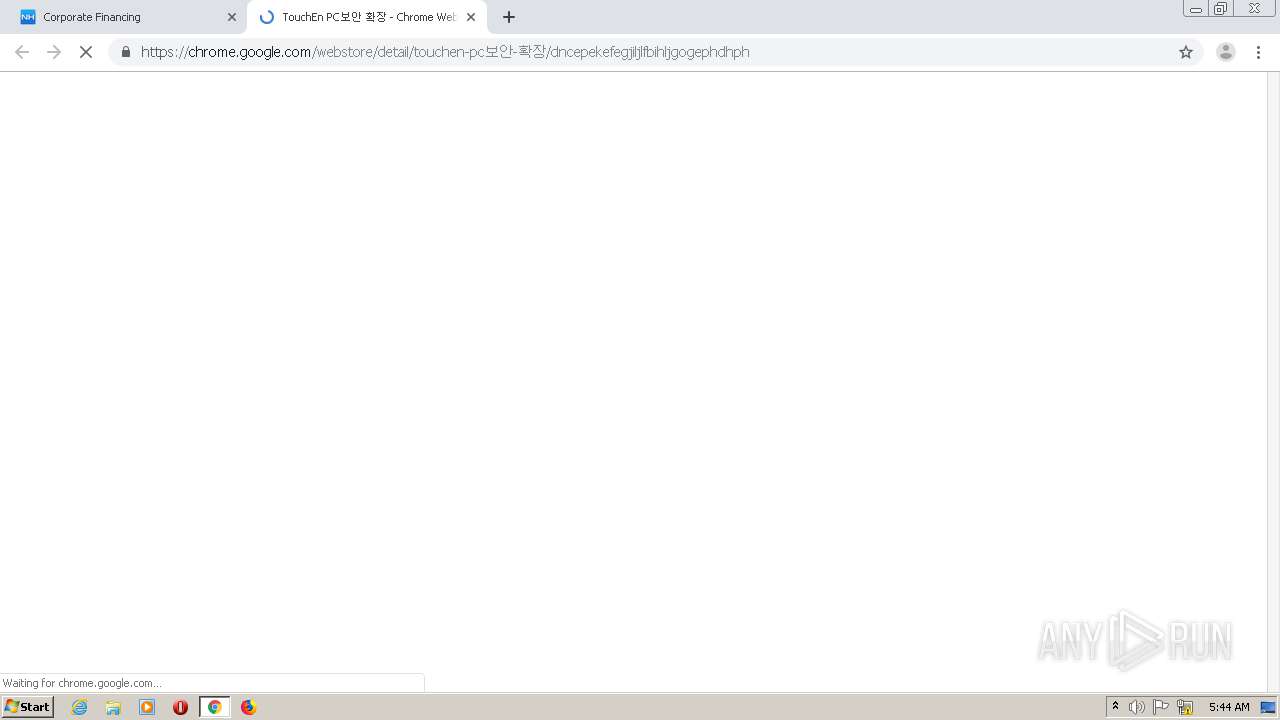
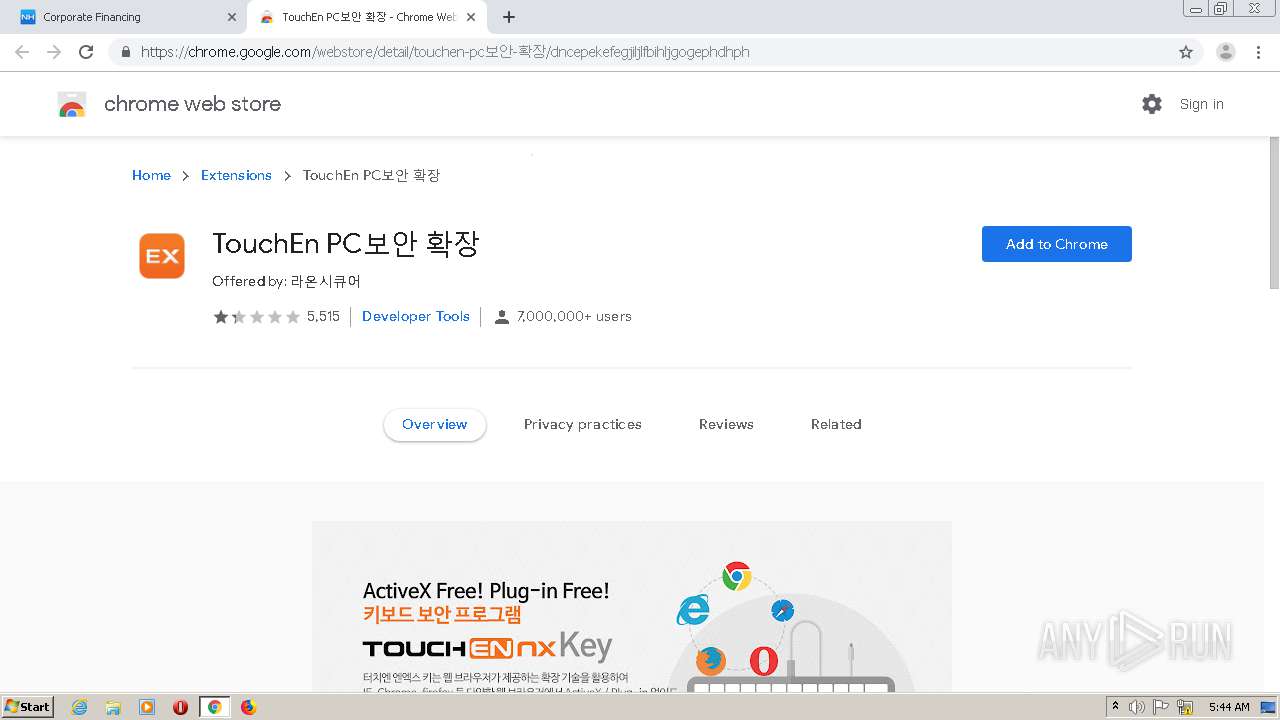
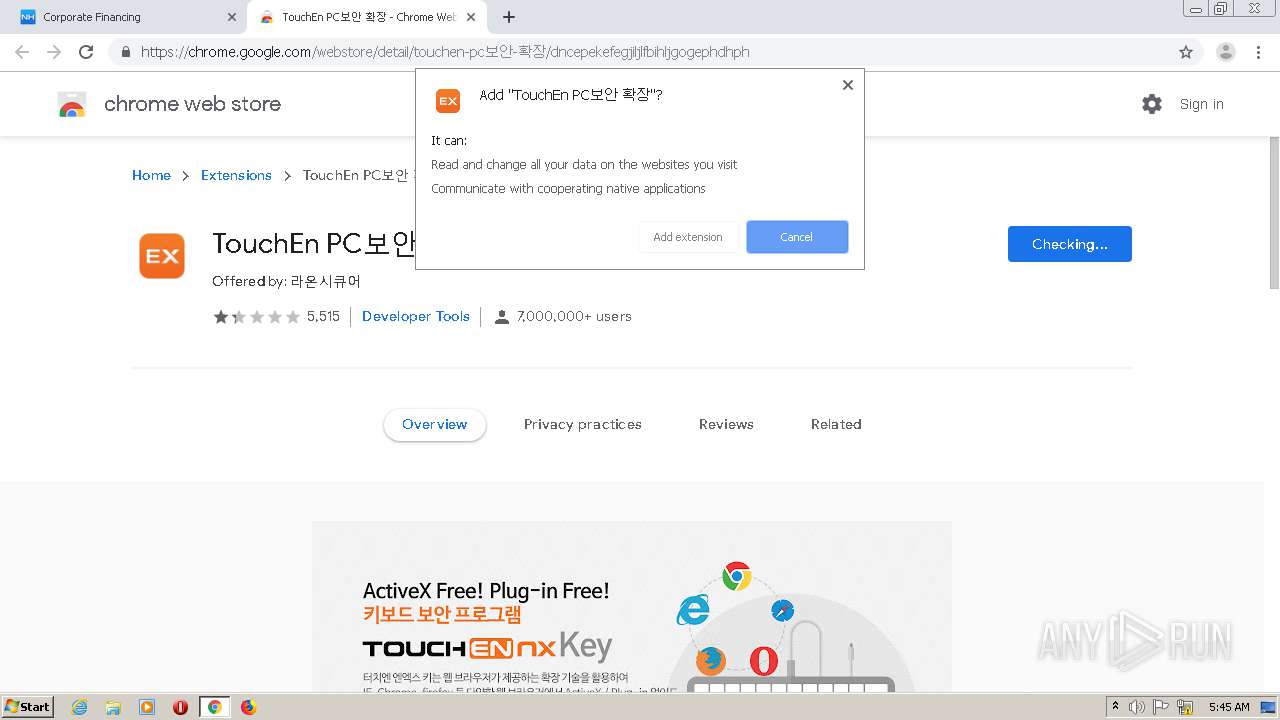
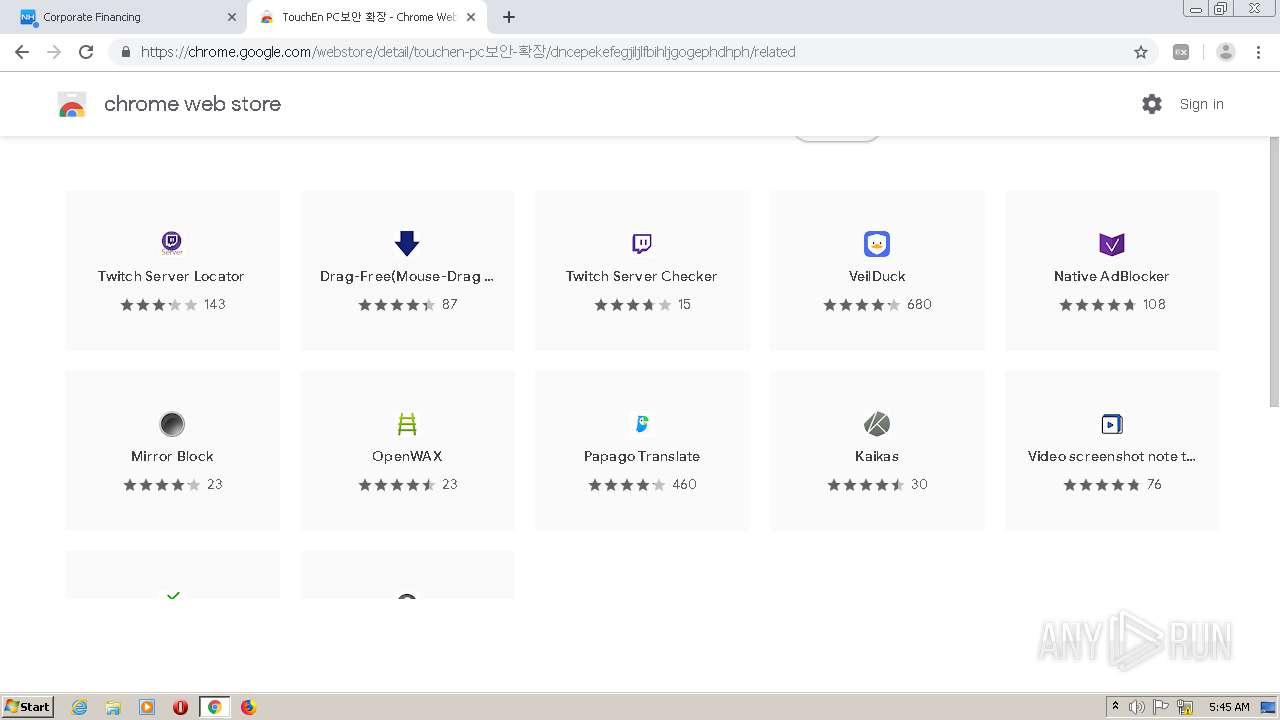
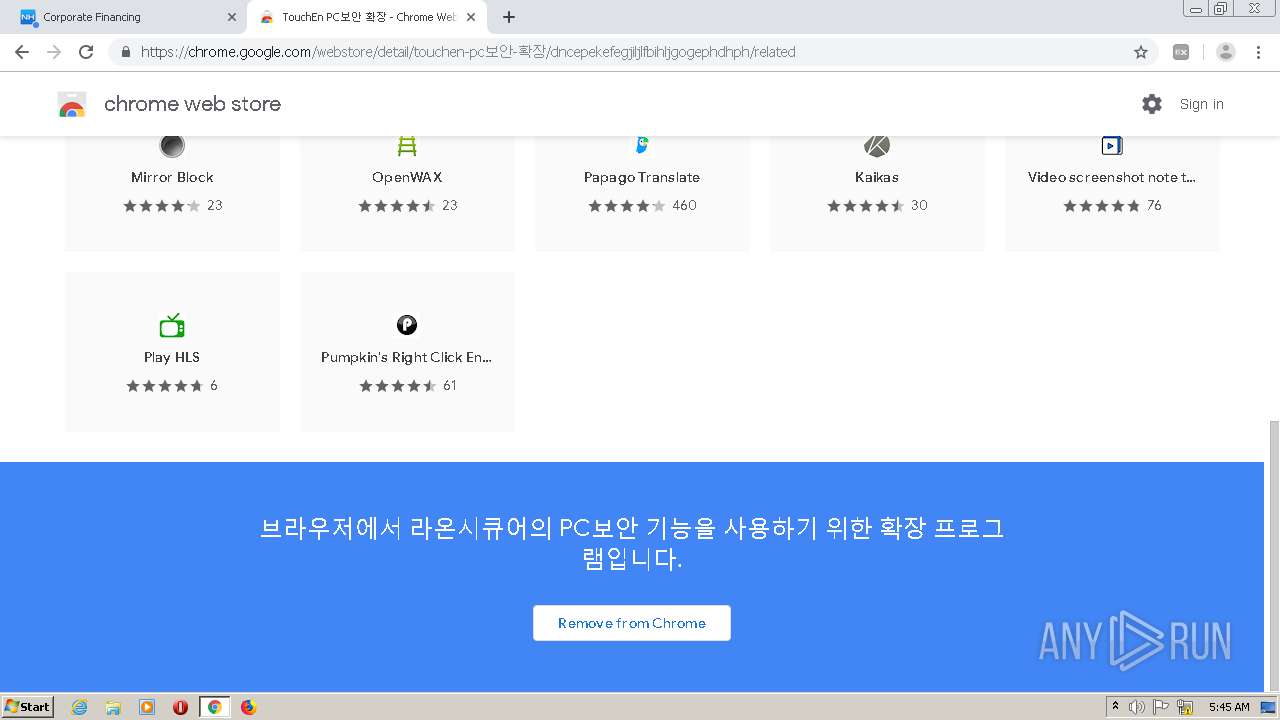
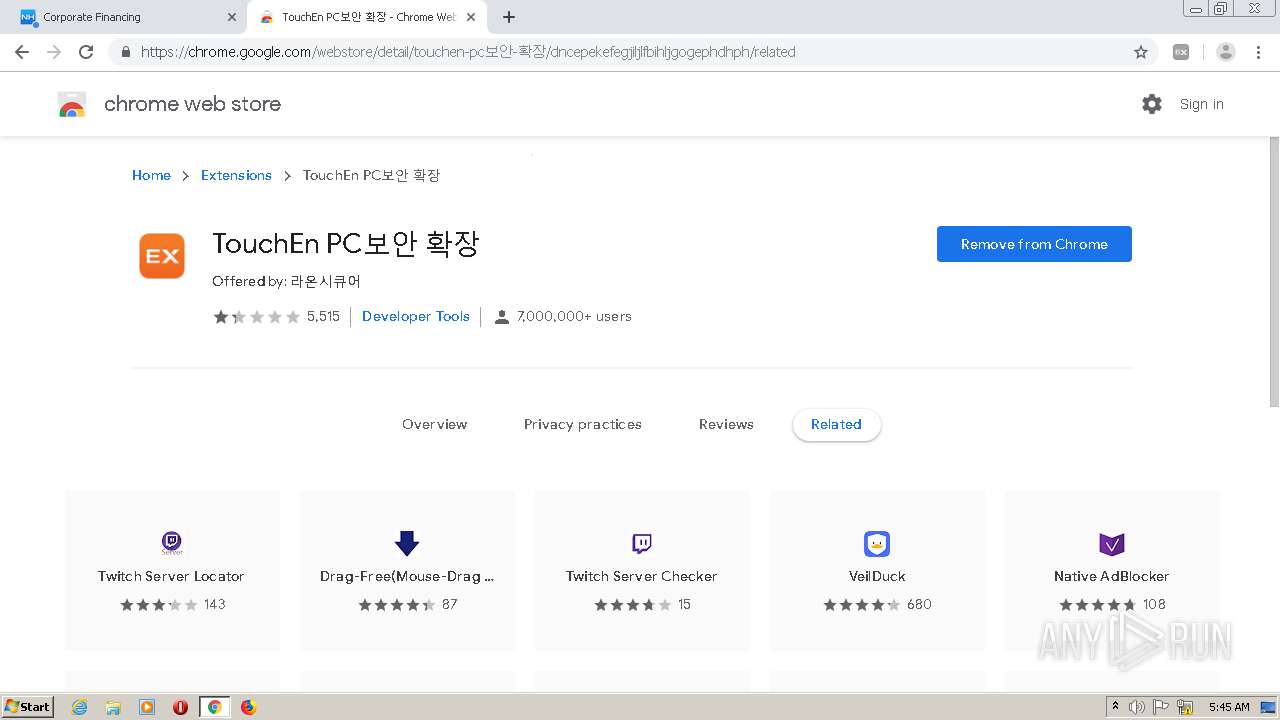
Modifies files in Chrome extension folder
- chrome.exe (PID: 2732)
Executable content was dropped or overwritten
- chrome.exe (PID: 2732)
- CKSetup64.exe (PID: 3952)
- CKSetup64.exe (PID: 3152)
- CKSetup32.exe (PID: 1408)
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- FFCert.exe (PID: 3404)
- INIS_EX_SHA2.exe (PID: 3956)
- iniline_crosswebex_Install.exe (PID: 3544)
- INIS_EX_SHA2.exe (PID: 500)
Checks supported languages
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- CKSetup32.exe (PID: 1408)
- CKSetup64.exe (PID: 3952)
- CKSetup64.exe (PID: 3152)
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- CrossEXService.exe (PID: 3784)
- ObCrossEXService.exe (PID: 2940)
- FFCert.exe (PID: 3404)
- Firefox_CertUtil.exe (PID: 3580)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 3708)
- certutil.exe (PID: 2832)
- certutil.exe (PID: 2748)
- CrossEXChrome.exe (PID: 1292)
- ckagentNXE.exe (PID: 1772)
- cmd.exe (PID: 852)
- INIS_EX_SHA2.exe (PID: 3956)
- INIS_EX_SHA2.exe (PID: 500)
- INISAFETrayEX.exe (PID: 3684)
- iniline_crosswebex_Install.exe (PID: 3544)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 360)
- KillBrowser.exe (PID: 1600)
- certutil.exe (PID: 3452)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 2224)
- IniClientSvc_x64.exe (PID: 2500)
- INISAFEAdminUtil.exe (PID: 3704)
- certutil.exe (PID: 2712)
- INISAFECrossWebEXSvc.exe (PID: 3748)
- INISAFETrayEX.exe (PID: 2608)
Reads the computer name
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- CKSetup32.exe (PID: 1408)
- CKSetup64.exe (PID: 3952)
- CKSetup64.exe (PID: 3152)
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- ObCrossEXService.exe (PID: 2940)
- CrossEXService.exe (PID: 3784)
- FFCert.exe (PID: 3404)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 3708)
- certutil.exe (PID: 2832)
- certutil.exe (PID: 2748)
- CrossEXChrome.exe (PID: 1292)
- ckagentNXE.exe (PID: 1772)
- INIS_EX_SHA2.exe (PID: 3956)
- INIS_EX_SHA2.exe (PID: 500)
- iniline_crosswebex_Install.exe (PID: 3544)
- certutil.exe (PID: 3452)
- IniClientSvc_x64.exe (PID: 2500)
- certutil.exe (PID: 2712)
- INISAFECrossWebEXSvc.exe (PID: 3748)
- INISAFETrayEX.exe (PID: 2608)
Creates files in the Windows directory
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- CKSetup64.exe (PID: 3952)
- CKSetup32.exe (PID: 1408)
- CKSetup64.exe (PID: 3152)
- INIS_EX_SHA2.exe (PID: 500)
Drops a file that was compiled in debug mode
- CKSetup64.exe (PID: 3952)
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- FFCert.exe (PID: 3404)
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- INIS_EX_SHA2.exe (PID: 500)
- iniline_crosswebex_Install.exe (PID: 3544)
Removes files from Windows directory
- CKSetup64.exe (PID: 3952)
Creates a directory in Program Files
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- INIS_EX_SHA2.exe (PID: 500)
- iniline_crosswebex_Install.exe (PID: 3544)
Creates a software uninstall entry
- CKSetup32.exe (PID: 1408)
- CrossEX_LocalService_Install.exe (PID: 2776)
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- INIS_EX_SHA2.exe (PID: 500)
Creates files in the program directory
- raon_touchenex_Install.exe (PID: 2236)
- CrossEX_LocalService_Install.exe (PID: 2776)
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- iniline_crosswebex_Install.exe (PID: 3544)
- INIS_EX_SHA2.exe (PID: 500)
Creates/Modifies COM task schedule object
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- raon_touchenex_Install.exe (PID: 2236)
- INIS_EX_SHA2.exe (PID: 500)
- iniline_crosswebex_Install.exe (PID: 3544)
Starts SC.EXE for service management
- CrossEX_LocalService_Install.exe (PID: 2776)
Executed as Windows Service
- ObCrossEXService.exe (PID: 2940)
- IniClientSvc_x64.exe (PID: 2500)
Creates files in the user directory
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2712)
- INIS_EX_SHA2.exe (PID: 500)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 2732)
- INIS_EX_SHA2.exe (PID: 500)
Reads Environment values
- INIS_EX_SHA2.exe (PID: 3956)
- INIS_EX_SHA2.exe (PID: 500)
Drops a file with too old compile date
- INIS_EX_SHA2.exe (PID: 3956)
- INIS_EX_SHA2.exe (PID: 500)
- iniline_crosswebex_Install.exe (PID: 3544)
Application launched itself
- INIS_EX_SHA2.exe (PID: 3956)
Drops a file with a compile date too recent
- INIS_EX_SHA2.exe (PID: 500)
- DllHost.exe (PID: 2960)
Creates or modifies windows services
- INIS_EX_SHA2.exe (PID: 500)
Executed via COM
- DllHost.exe (PID: 2960)
- INISAFETrayEX.exe (PID: 2608)
INFO
Checks supported languages
- chrome.exe (PID: 2732)
- chrome.exe (PID: 1392)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 1348)
- chrome.exe (PID: 320)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 344)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2304)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 1156)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 376)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3852)
- sc.exe (PID: 3720)
- sc.exe (PID: 2888)
- sc.exe (PID: 3952)
- DllHost.exe (PID: 2960)
Application launched itself
- chrome.exe (PID: 2732)
Reads the hosts file
- chrome.exe (PID: 2732)
- chrome.exe (PID: 344)
Reads the computer name
- chrome.exe (PID: 2732)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2304)
- sc.exe (PID: 2888)
- sc.exe (PID: 3720)
- sc.exe (PID: 3952)
- DllHost.exe (PID: 2960)
Reads settings of System Certificates
- chrome.exe (PID: 344)
- chrome.exe (PID: 2732)
- CrossEX_LocalService_Install.exe (PID: 2776)
- TouchEn_nxKey_Installer_32bit_new.exe (PID: 4004)
- CrossEXChrome.exe (PID: 1292)
- IniClientSvc_x64.exe (PID: 2500)
- INISAFECrossWebEXSvc.exe (PID: 3748)
Reads the date of Windows installation
- chrome.exe (PID: 3472)
Checks Windows Trust Settings
- chrome.exe (PID: 2732)
- CrossEXChrome.exe (PID: 1292)
- INISAFECrossWebEXSvc.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
117
Monitored processes
58
Malicious processes
22
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1064,15511103232740209742,944026085554697342,131072 --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17944577611365953549 --mojo-platform-channel-handle=3360 /prefetch:2 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 344 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,15511103232740209742,944026085554697342,131072 --lang=en-US --service-sandbox-type=network --service-request-channel-token=1825150937400375131 --mojo-platform-channel-handle=1444 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 360 | C:\Windows\system32\cmd.exe /C ""C:\Program Files (x86)\INITECH\INISAFE Web EX Client\certutil.exe" -A -n "Initech Root Authority - CrossWeb EX" -t "TCu,Cuw,Tuw" -i "inirootcert.cer" -d "C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles/nltxvmn2.default"" | C:\Windows\SysWOW64\cmd.exe | — | INIS_EX_SHA2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 376 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,15511103232740209742,944026085554697342,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12614372727864878532 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
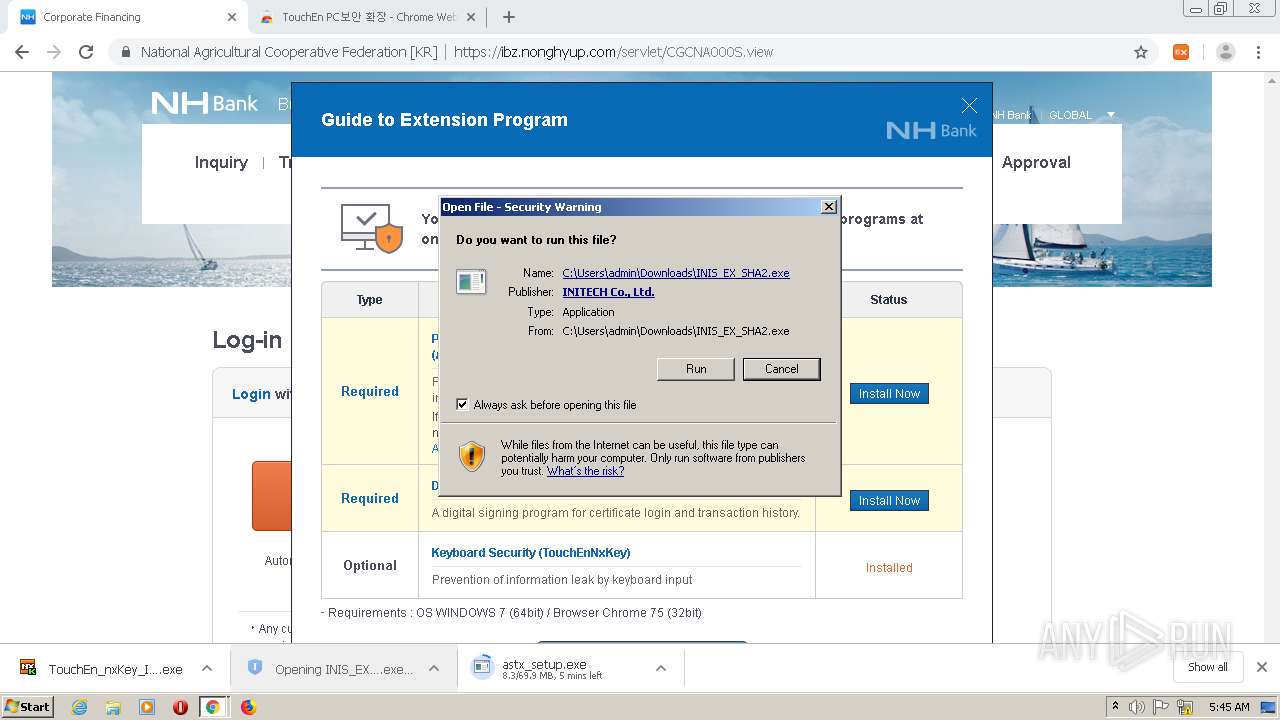
| 500 | "C:\Users\admin\Downloads\INIS_EX_SHA2.exe" /UAC:20196 /NCRC | C:\Users\admin\Downloads\INIS_EX_SHA2.exe | INIS_EX_SHA2.exe | ||||||||||||
User: admin Company: Initech (c) Integrity Level: HIGH Description: INISAFE CrossWeb EX V3 Installer Exit code: 0 Version: 3.3.2.23 Modules
| |||||||||||||||
| 852 | C:\Windows\system32\cmd.exe /d /c "C:\Program Files (x86)\RaonSecure\bridge\CrossEX\touchenex\1.0.1.1243\.\CrossEXChrome.exe" chrome-extension://dncepekefegjiljlfbihljgogephdhph/ --parent-window=0 < \\.\pipe\chrome.nativeMessaging.in.dbff1c4c5b6e3406 > \\.\pipe\chrome.nativeMessaging.out.dbff1c4c5b6e3406 | C:\Windows\system32\cmd.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1156 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,15511103232740209742,944026085554697342,131072 --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11320675334751738146 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3020 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files (x86)\RaonSecure\bridge\CrossEX\touchenex\1.0.1.1243\.\CrossEXChrome.exe" chrome-extension://dncepekefegjiljlfbihljgogephdhph/ --parent-window=0 | C:\Program Files (x86)\RaonSecure\bridge\CrossEX\touchenex\1.0.1.1243\CrossEXChrome.exe | — | cmd.exe | |||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: MEDIUM Description: CrossEXChrome Exit code: 0 Version: 1.0.1.1243 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,15511103232740209742,944026085554697342,131072 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14427846616790256259 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x84,0x88,0x8c,0x80,0x90,0x7fef3e83ef8,0x7fef3e83f08,0x7fef3e83f18 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
21 953
Read events
21 598
Write events
344
Delete events
11
Modification events
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
168
Suspicious files
133
Text files
145
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6108D786-AAC.pma | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
66
DNS requests
29
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
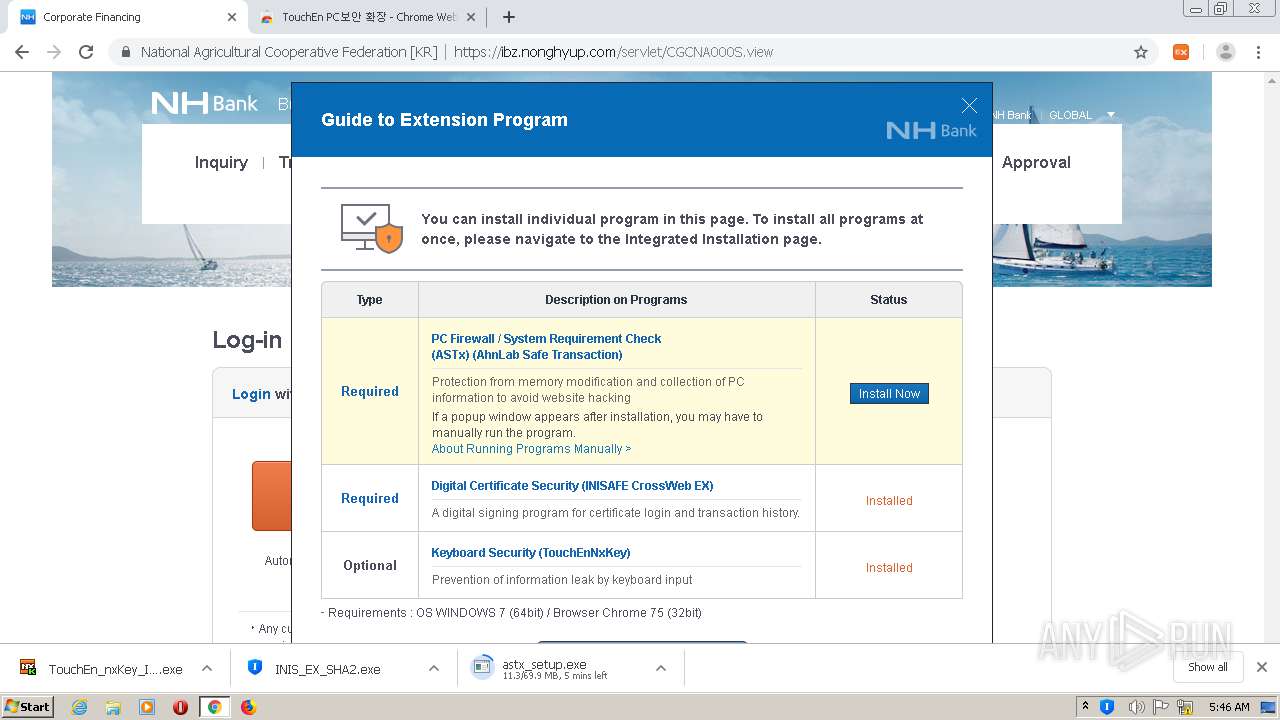
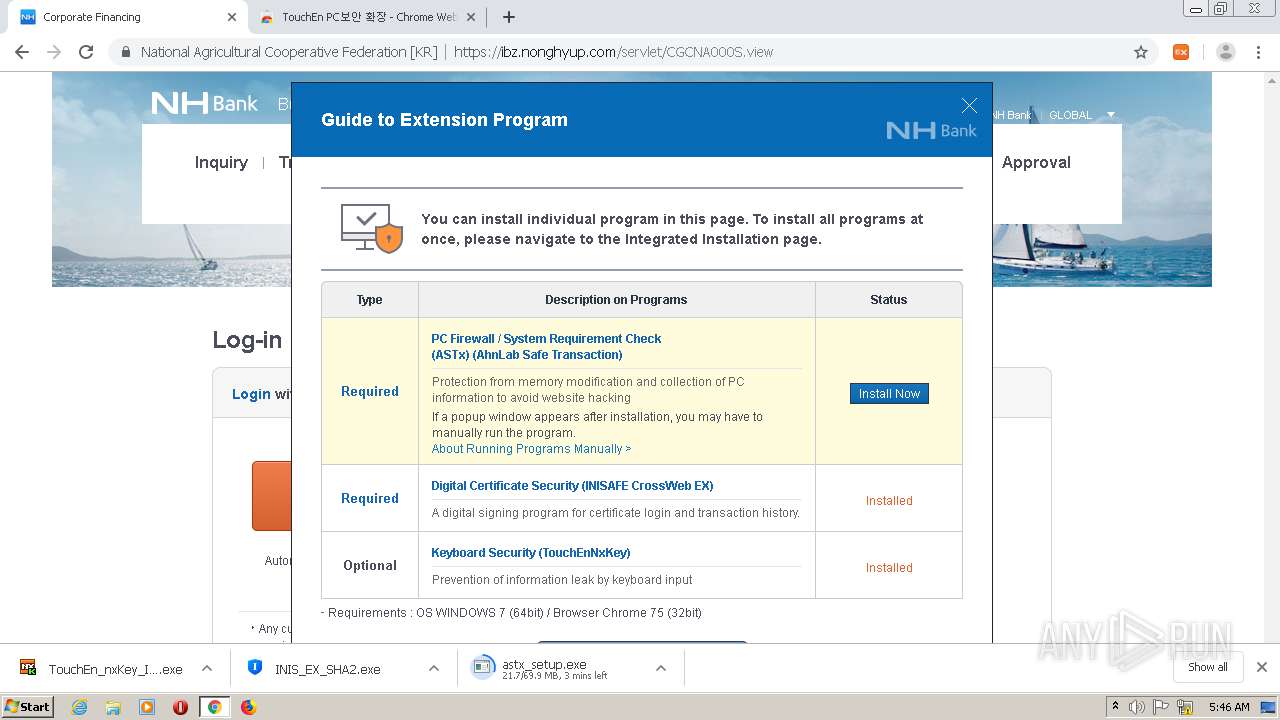
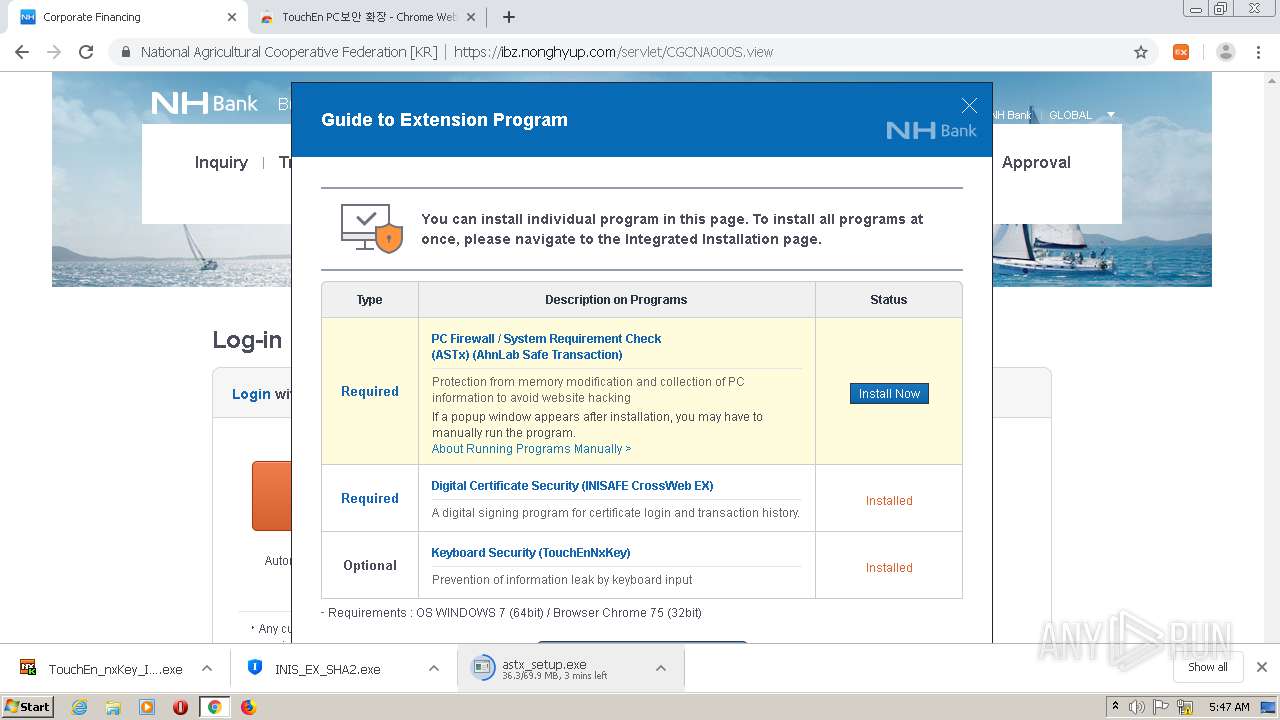
344 | chrome.exe | GET | — | 163.171.75.68:80 | http://safetx.ahnlab.com/master/win/default/all/astx_setup.exe | US | — | — | suspicious |
344 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAway38RTf9cfPGbgMYU1iw%3D | US | der | 471 b | whitelisted |
344 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
344 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAx5RYFBe4VxsHBHixCtaFU%3D | US | der | 471 b | whitelisted |
344 | chrome.exe | GET | 200 | 2.16.186.24:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ba4cb34f77a160a7 | unknown | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
344 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
344 | chrome.exe | 2.16.186.24:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
344 | chrome.exe | 61.37.254.76:443 | ibz.nonghyup.com | National Agricultural Cooperative federation | KR | unknown |
344 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
344 | chrome.exe | 61.37.254.103:443 | ebizhub.nonghyup.com | National Agricultural Cooperative federation | KR | unknown |
344 | chrome.exe | 142.250.186.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
344 | chrome.exe | 142.250.186.142:443 | apis.google.com | Google Inc. | US | whitelisted |
344 | chrome.exe | 142.250.185.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
344 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
344 | chrome.exe | 142.250.74.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ibz.nonghyup.com |
| unknown |
accounts.google.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ebizhub.nonghyup.com |
| unknown |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
chrome.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
344 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
TouchEn_nxKey_Installer_32bit_new.exe | 20141130 fn : C:\Users\admin\AppData\Local\Temp\~RAPack1919843\_Chunk.zip, C:\Users\admin\AppData\Local\Temp\~RAPack1919843 333
|
TouchEn_nxKey_Installer_32bit_new.exe | 20141211 1.szResVersion : 3,1,1,43
|
TouchEn_nxKey_Installer_32bit_new.exe | 20141130 fn : C:\Windows\system32\CKSetup32.exe, C:\Windows\system32(size=2868896) 565
|
TouchEn_nxKey_Installer_32bit_new.exe | 20141130 1240_.\TouchEn_nxKey_Installer.cpp
|
TouchEn_nxKey_Installer_32bit_new.exe | C:\Windows\system32\CKSetup32.exe /install appm
|
CKSetup64.exe | update CKAgentNXE |
CKSetup64.exe | [TK] KillProcessByImageName = CKAgentNXE.exe
|
CKSetup64.exe | [TK] KillProcessByImageName return = 0
|
CKSetup64.exe | update CKAgent |
CKSetup64.exe | [TK] KillProcessByImageName = CKAgent.exe
|