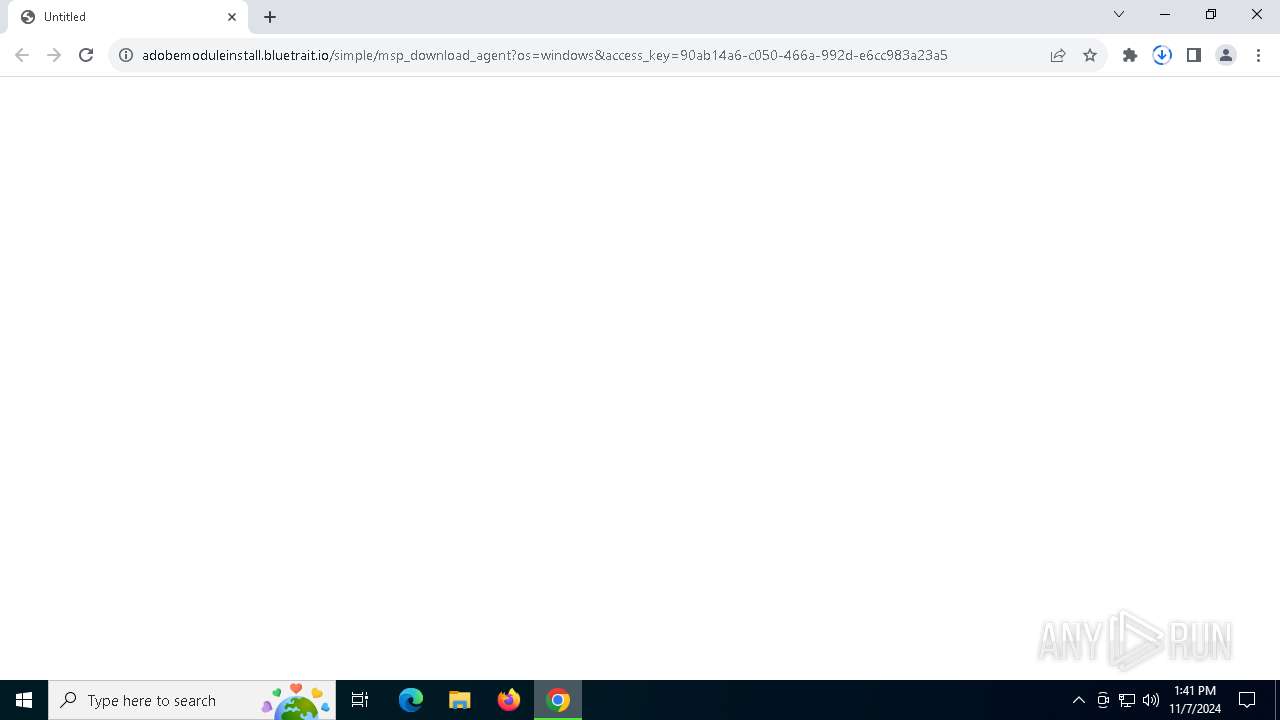
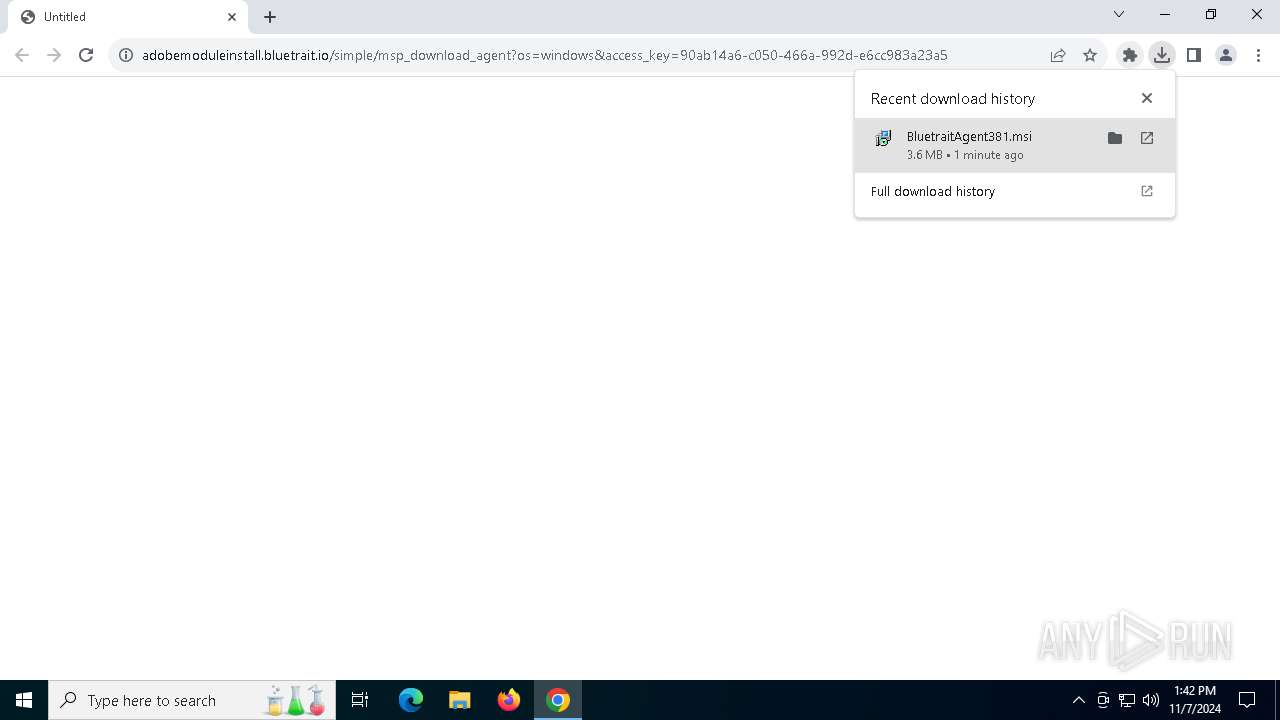
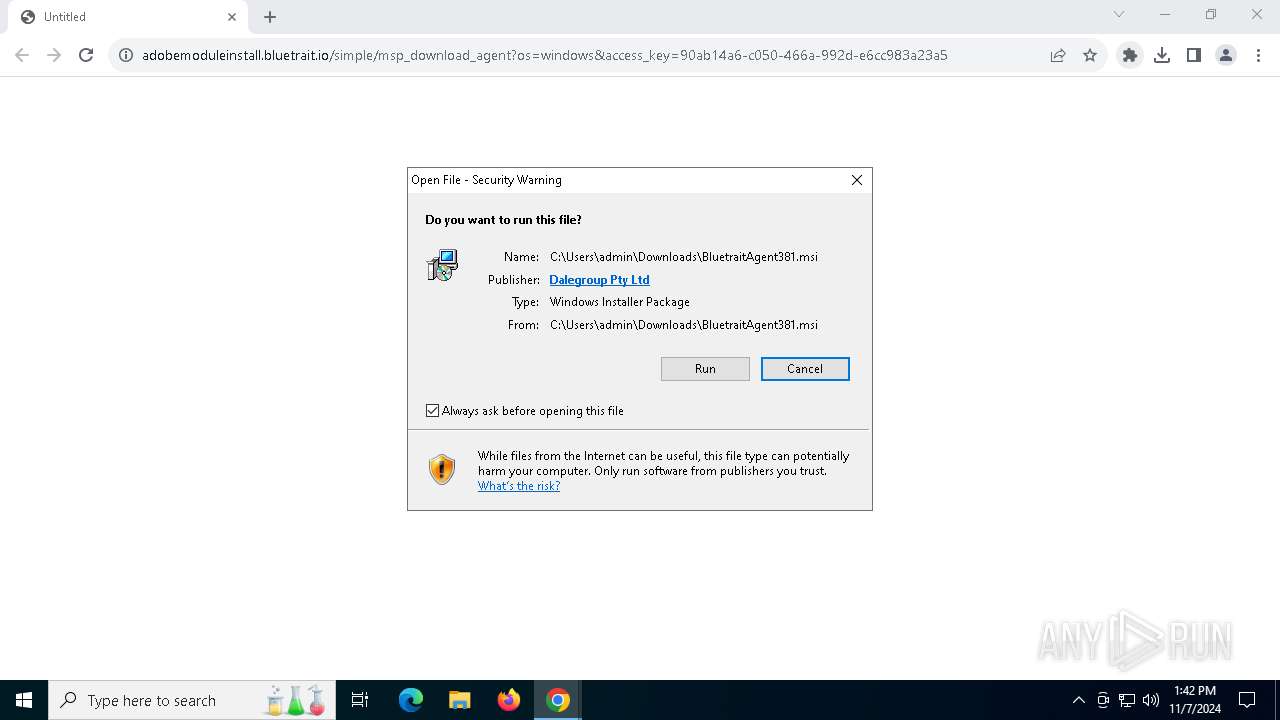
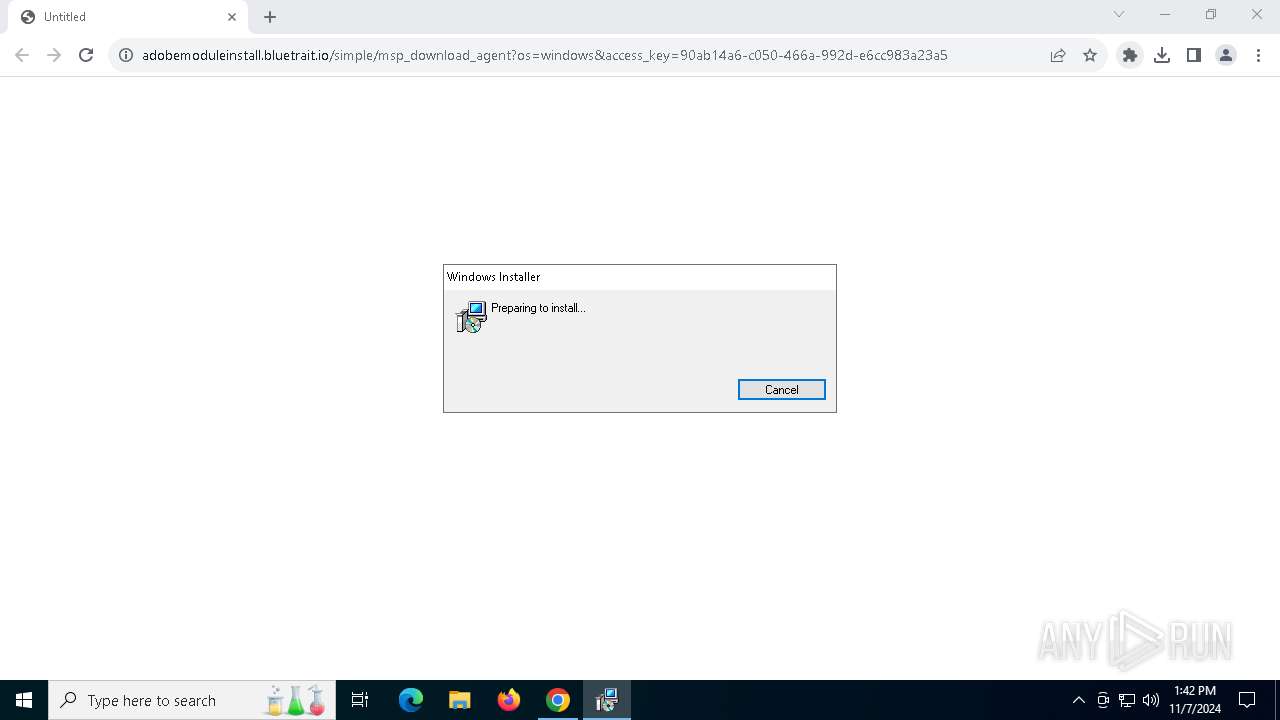
| URL: | https://adobemoduleinstall.bluetrait.io/simple/msp_download_agent?os=windows&access_key=90ab14a6-c050-466a-992d-e6cc983a23a5 |
| Full analysis: | https://app.any.run/tasks/35d19af4-5430-46c9-aeb4-bfebd8135b2e |
| Verdict: | Malicious activity |
| Analysis date: | November 07, 2024, 13:41:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 0D6EEB4487090898FC977F87CB0C0FFD |
| SHA1: | 57204144AA8B3377279B611AF42475DF3F467993 |
| SHA256: | D1A6C9C0E71B9109A3F5943563AF398C17426C5B86E3E78B8E18C8E3EDD52170 |
| SSDEEP: | 3:N8hg3BclDrh3jATWV6D9UreddK5zVEHUwIG3jl/TR6Qn:2CcluTWQOkInEHNIAhd6Qn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 5372)
- WmiApSrv.exe (PID: 6440)
- Bluetrait MSP Agent.exe (PID: 5464)
- WmiApSrv.exe (PID: 8068)
- level.exe (PID: 624)
Uses WMIC.EXE to obtain operating system information
- install_windows.exe (PID: 7976)
Executable content was dropped or overwritten
- Bluetrait MSP Agent.exe (PID: 5464)
- install_windows.exe (PID: 7976)
- level-windows-amd64.exe (PID: 4996)
Starts SC.EXE for service management
- install_windows.exe (PID: 7976)
- level.exe (PID: 624)
- level-windows-amd64.exe (PID: 4996)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 8044)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 2816)
Starts CMD.EXE for commands execution
- level-windows-amd64.exe (PID: 4996)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 1524)
Starts POWERSHELL.EXE for commands execution
- level.exe (PID: 624)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 5956)
- msiexec.exe (PID: 7176)
Manages system restore points
- SrTasks.exe (PID: 5912)
Application launched itself
- chrome.exe (PID: 5956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
70
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files\Level\level.exe" --key eMA9cVei2hbmCCxMWWRWKi4w --action=run | C:\Program Files\Level\level.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 712 | powershell -Command "& {param ( [string]$CommandName, [string]$CommandArguments, [int]$IntervalMinutes, [string]$TaskPath, [string]$RunAsUser, [string]$Description ) $action = New-ScheduledTaskAction -Execute $CommandName -Argument $CommandArguments $trigger=$null if ([Environment]::OSVersion.Version -ge (new-object 'Version' 10,0)) { $trigger = New-ScheduledTaskTrigger -Once -At (Get-Date) -RepetitionInterval (New-TimeSpan -Minutes $IntervalMinutes) } else { # Windows 8/Windows Server 2012 or older $trigger = New-ScheduledTaskTrigger -Once -At (Get-Date) -RepetitionInterval (New-TimeSpan -Minutes $IntervalMinutes) -RepetitionDuration ([System.TimeSpan]::MaxValue) } $settings = New-ScheduledTaskSettingsSet -AllowStartIfOnBatteries -DontStopIfGoingOnBatteries $task = New-ScheduledTask -Action $action -Description $Description -Trigger $trigger -Settings $settings Register-ScheduledTask -Force -TaskName $TaskPath -InputObject $task -User $RunAsUser }" -CommandName "'C:\Program Files\Level\level.exe'" -CommandArguments '--check-service' -IntervalMinutes 10 -TaskPath "'Level\Level Watchdog'" -RunAsUser 'system' -Description "'Ensures the Level service is always running. For more details, see https://docs.level.io/1.0/admin-guides/level-watchdog-task.'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | level.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1248 | "C:\Program Files\Level\osqueryi.exe" -S --verbose --alarm_timeout 10 --disable_carver --disable_enrollment --disable_extensions --disable_reenrollment --disable_watchdog --disable_caching --disable_database --disable_events --disable_hash_cache --ephemeral --config_path "C:\Program Files\Level\osquery_config.conf" --json " SELECT address, mask FROM interface_addresses " | C:\Program Files\Level\osqueryi.exe | — | level.exe | |||||||||||
User: SYSTEM Company: Osquery Foundation Integrity Level: SYSTEM Description: osquery daemon and shell Exit code: 0 Version: 5.9.1.0 | |||||||||||||||
| 1252 | "C:\Program Files\Level\osqueryi.exe" -S --verbose --alarm_timeout 10 --disable_carver --disable_enrollment --disable_extensions --disable_reenrollment --disable_watchdog --disable_caching --disable_database --disable_events --disable_hash_cache --ephemeral --config_path "C:\Program Files\Level\osquery_config.conf" --json " SELECT ld.device_id AS mount_point, coalesce(bi.protection_status, 0) AS encrypted, ld.size, ld.free_space, ld.file_system, ld.description AS label, ld.boot_partition AS \"primary\" FROM logical_drives ld LEFT JOIN bitlocker_info bi ON bi.drive_letter = ld.device_id " | C:\Program Files\Level\osqueryi.exe | — | level.exe | |||||||||||
User: SYSTEM Company: Osquery Foundation Integrity Level: SYSTEM Description: osquery daemon and shell Exit code: 0 Version: 5.9.1.0 | |||||||||||||||
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | osqueryi.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3084 --field-trial-handle=1920,i,9035192237652380884,17030930559181733277,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1976 --field-trial-handle=1920,i,9035192237652380884,17030930559181733277,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1524 | cmd /C "netsh advfirewall firewall add rule name=\"Level Agent\" description=\"Remote device management - https://level.io\" dir=in action=allow program=\"C:\Program Files\Level\level.exe\" enable=yes" | C:\Windows\System32\cmd.exe | — | level-windows-amd64.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
12 059
Read events
12 018
Write events
32
Delete events
9
Modification events
| (PID) Process: | (5956) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5956) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5956) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5956) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5956) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4584) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000005716D0CA1A31DB01 | |||
| (PID) Process: | (5956) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (7176) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000FB9FBEF51A31DB01081C00000C0F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7176) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000FB9FBEF51A31DB01081C00000C0F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7176) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000000D8946F61A31DB01081C00000C0F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
32
Suspicious files
214
Text files
54
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8c4a1.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8c4b0.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8c4b0.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8c4b0.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8c4a1.TMP | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8c4b0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
86
DNS requests
46
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7564 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6956 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7564 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
7564 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5956 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1440 | chrome.exe | 167.99.228.32:443 | adobemoduleinstall.bluetrait.io | DIGITALOCEAN-ASN | US | unknown |
1440 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
adobemoduleinstall.bluetrait.io |
| unknown |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1440 | chrome.exe | Misc activity | ET INFO RMM Software Domain in DNS Lookup (bluetrait .io) |
1440 | chrome.exe | Misc activity | ET INFO Observed RMM Software Domain (bluetrait .io) in TLS SNI |
1440 | chrome.exe | Misc activity | ET INFO RMM Software Domain in DNS Lookup (bluetrait .io) |
— | — | Misc activity | ET INFO RMM Software Domain in DNS Lookup (bluetrait .io) |
— | — | Misc activity | ET INFO Observed RMM Software Domain (bluetrait .io) in TLS SNI |
— | — | Misc activity | ET INFO Observed RMM Software Domain (bluetrait .io) in TLS SNI |
— | — | Misc activity | ET INFO Observed RMM Software Domain (bluetrait .io) in TLS SNI |
— | — | Misc activity | ET INFO Observed RMM Software Domain (bluetrait .io) in TLS SNI |
— | — | Misc activity | ET INFO Level.io Download Agent Domain in DNS Lookup (downloads .level .io) |
— | — | Misc activity | ET INFO Level.io Agent Update Domain in DNS Lookup (builds .level .io) |