| File name: | psiphon3 (3).exe |
| Full analysis: | https://app.any.run/tasks/474f8665-29c9-4b05-b512-6b8dd48fdca2 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2025, 09:35:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 4C2F8BC0CE351D4AED83A308CB5E0760 |
| SHA1: | 3424014225D878E3674053DBCE9ACAEBA501989E |
| SHA256: | D173CE07AC7FC8A8384A057188B4E6FB662C51C982BFA3CF081331C2C3786FF1 |
| SSDEEP: | 98304:jT5H+4yXLWyL0o++4toPW2nBG2sHiKDM9AiU+cQSMpaVdlDV7iiCy4HCl0eovYWm:dqQ4RgYkvPtVuI7Y6ztdoGV+2adkXw |
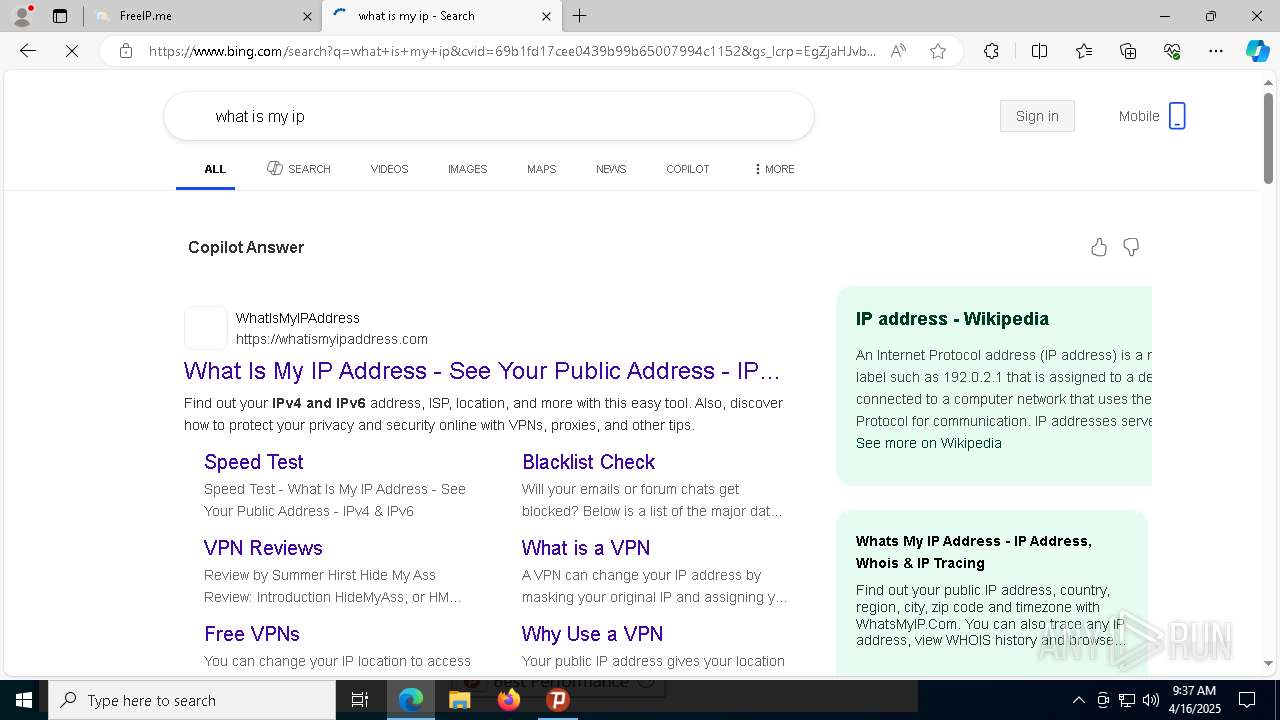
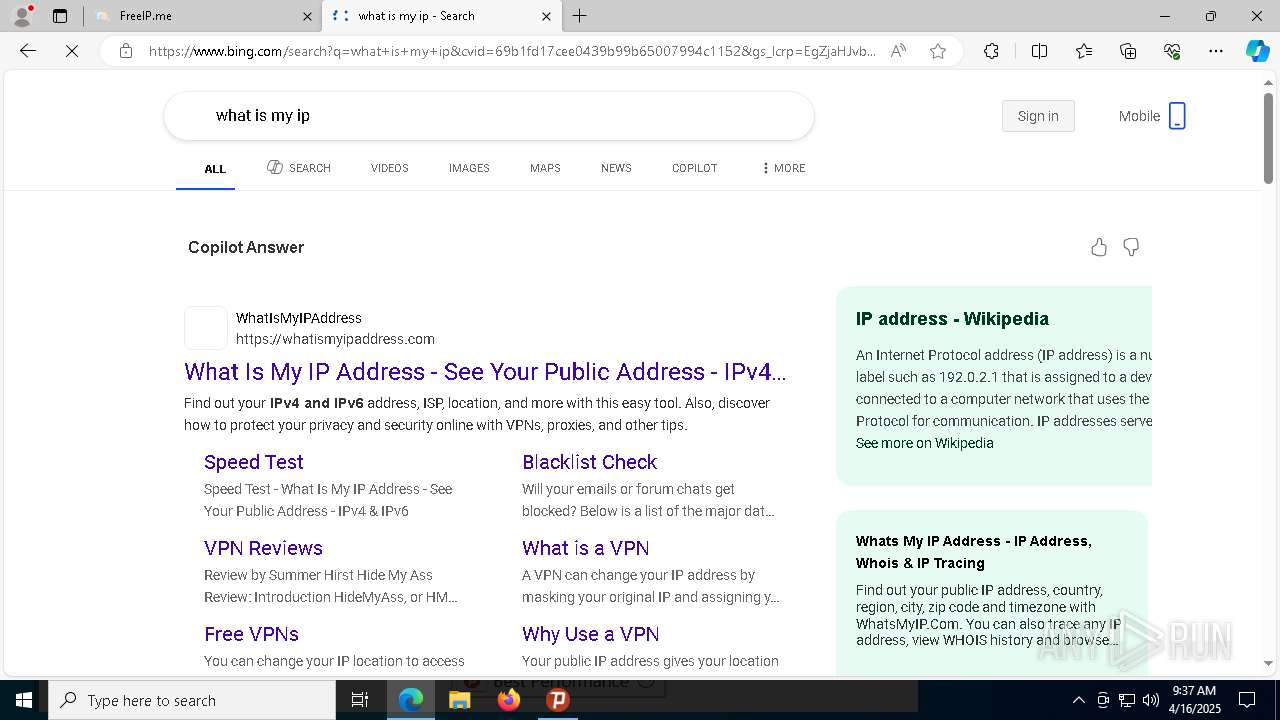
MALICIOUS
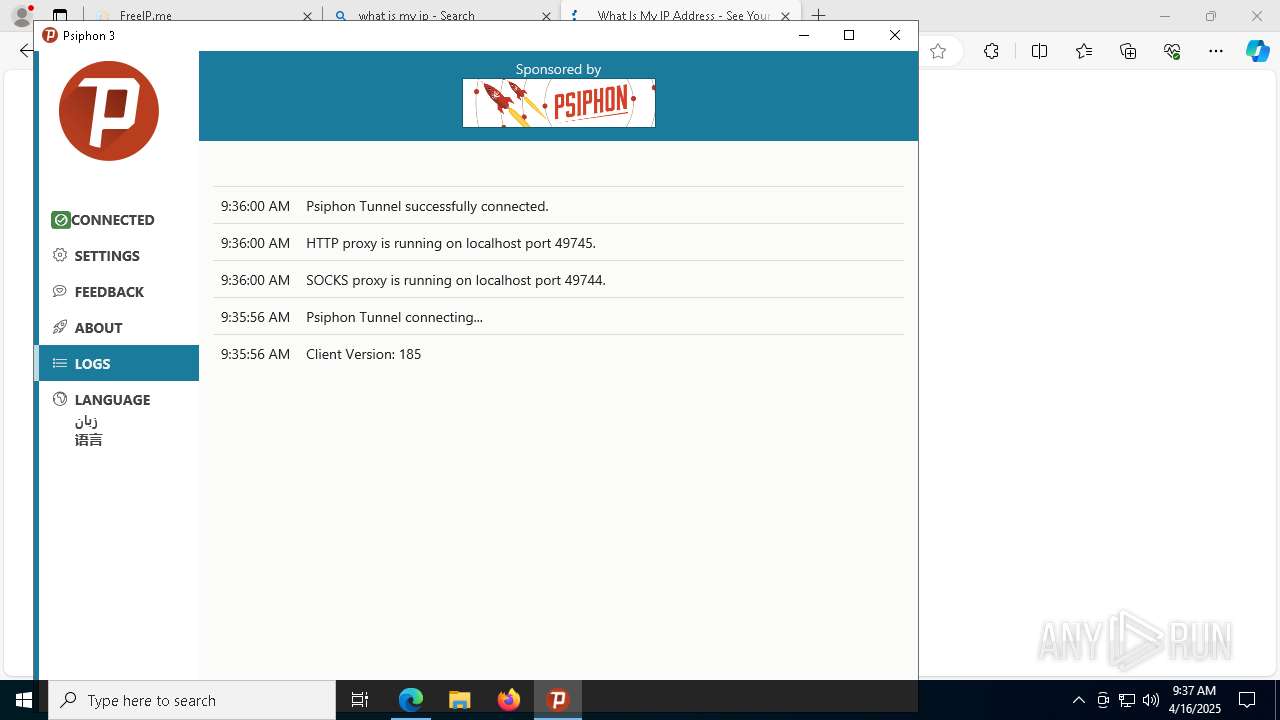
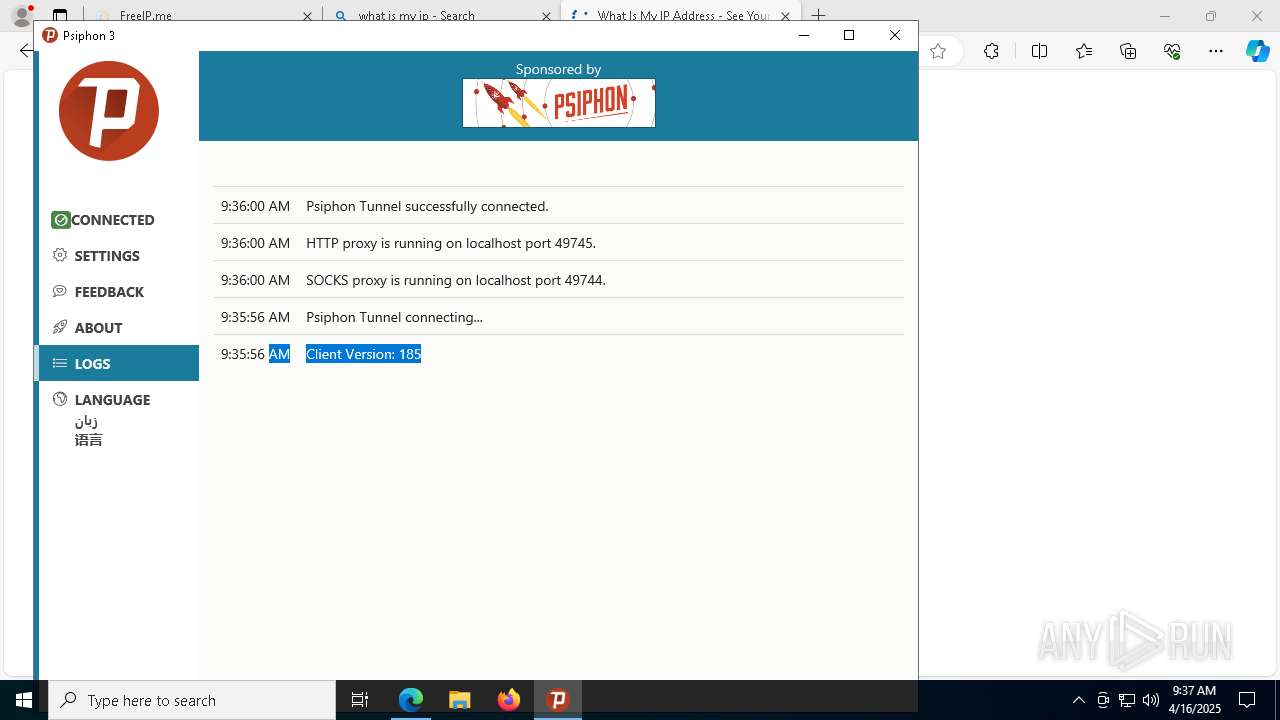
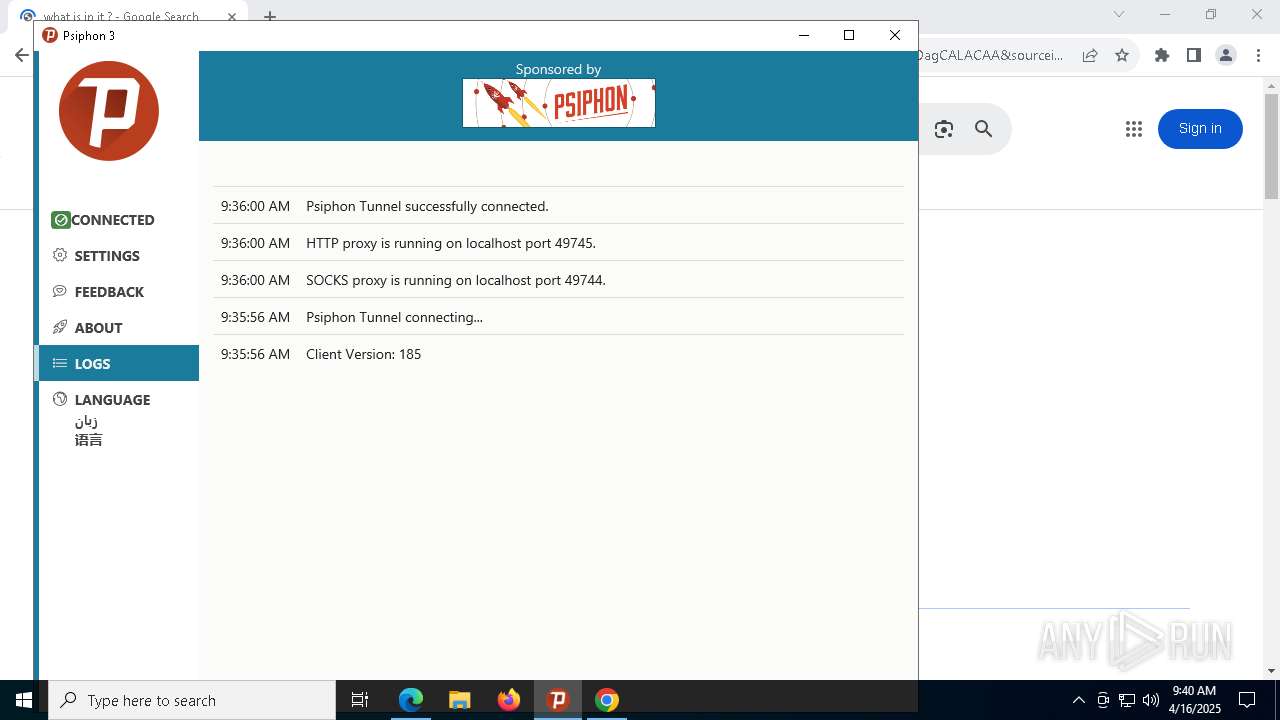
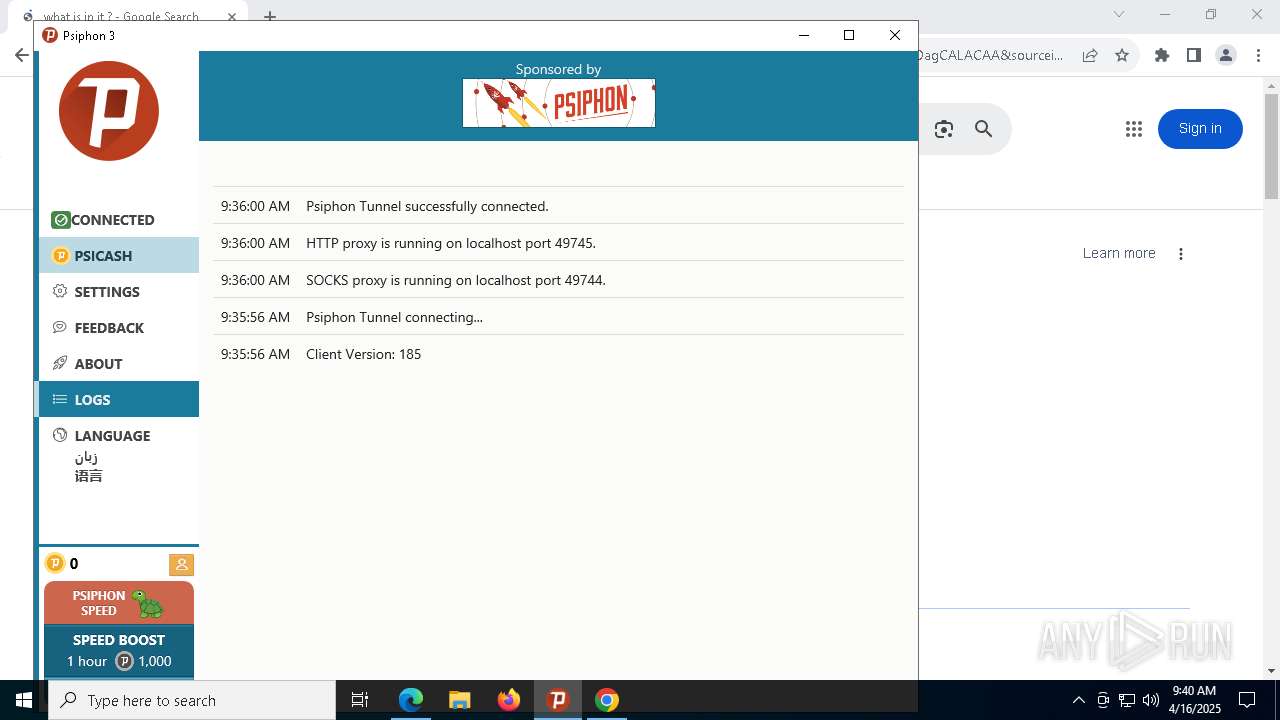
Attempting to connect via SSH
- psiphon-tunnel-core.exe (PID: 920)
SUSPICIOUS
Reads Internet Explorer settings
- psiphon3 (3).exe (PID: 5072)
Reads security settings of Internet Explorer
- psiphon3 (3).exe (PID: 5072)
Reads Microsoft Outlook installation path
- psiphon3 (3).exe (PID: 5072)
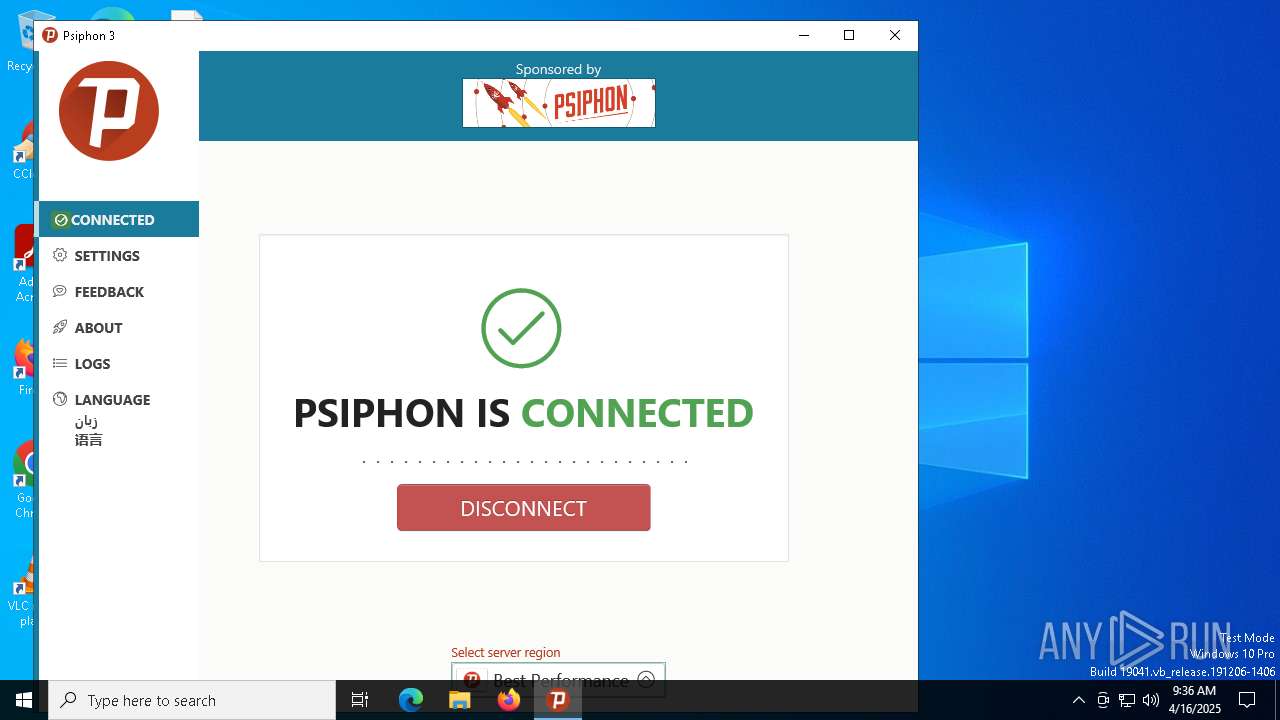
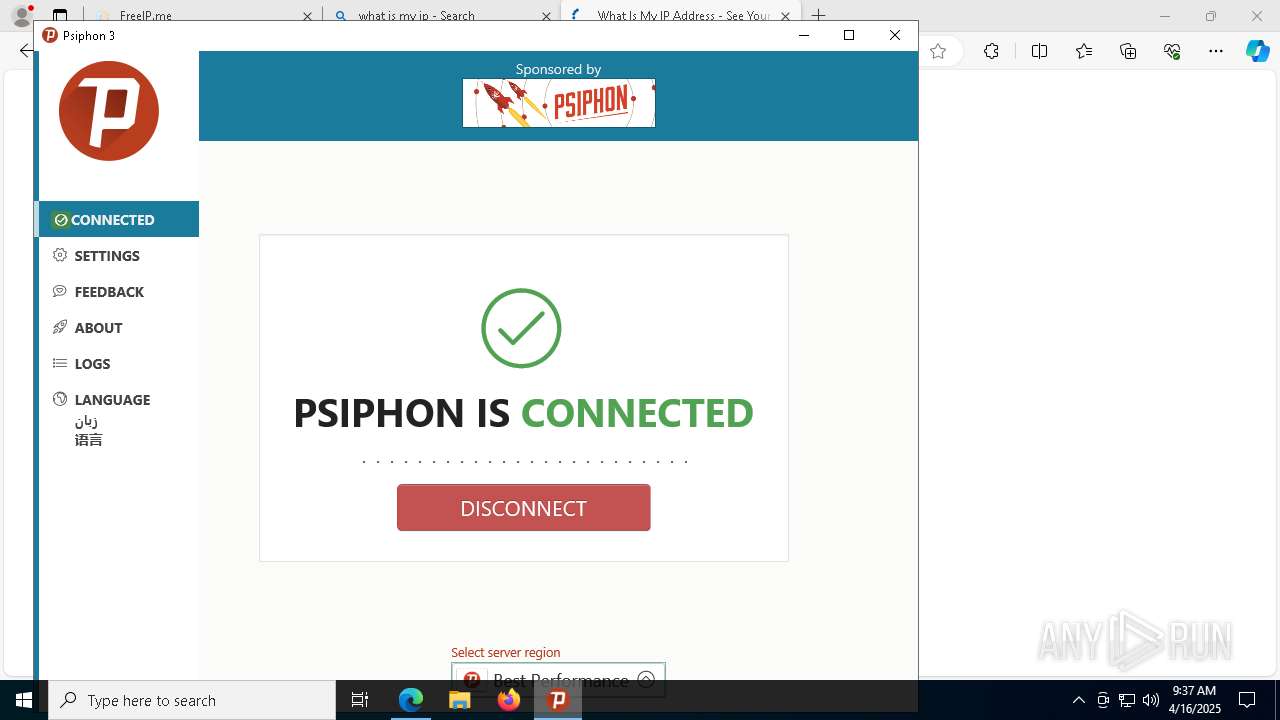
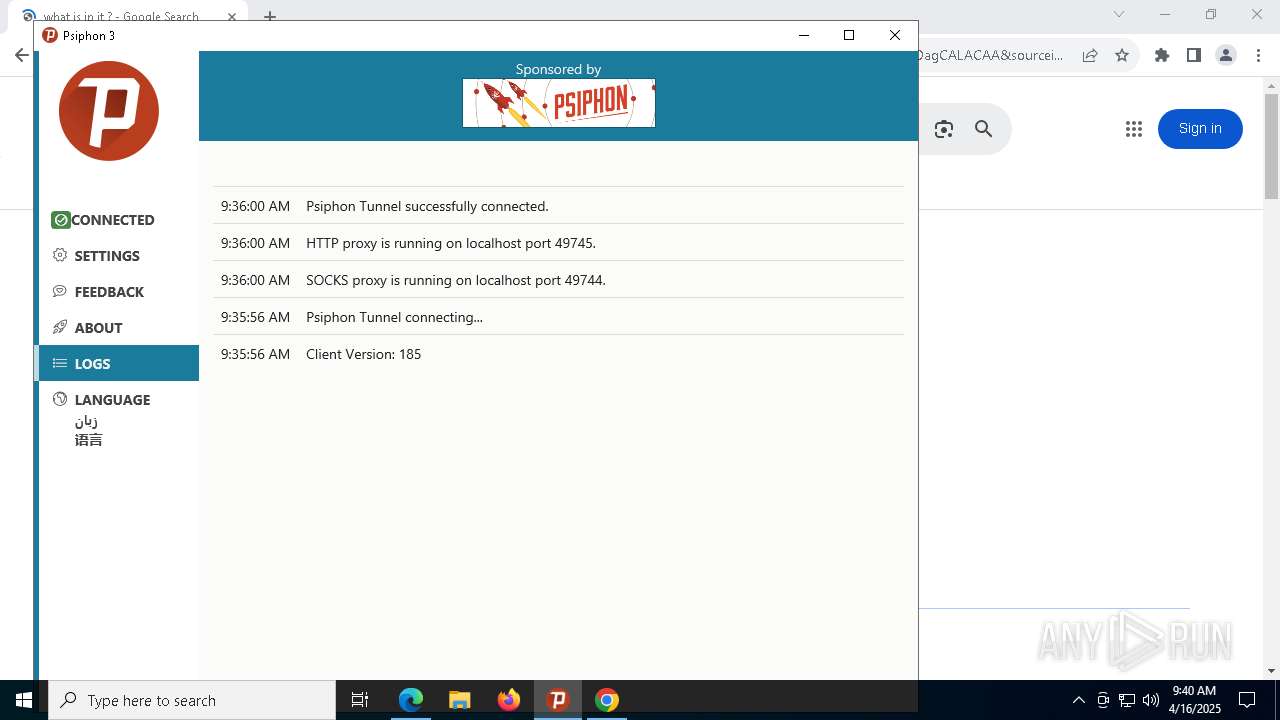
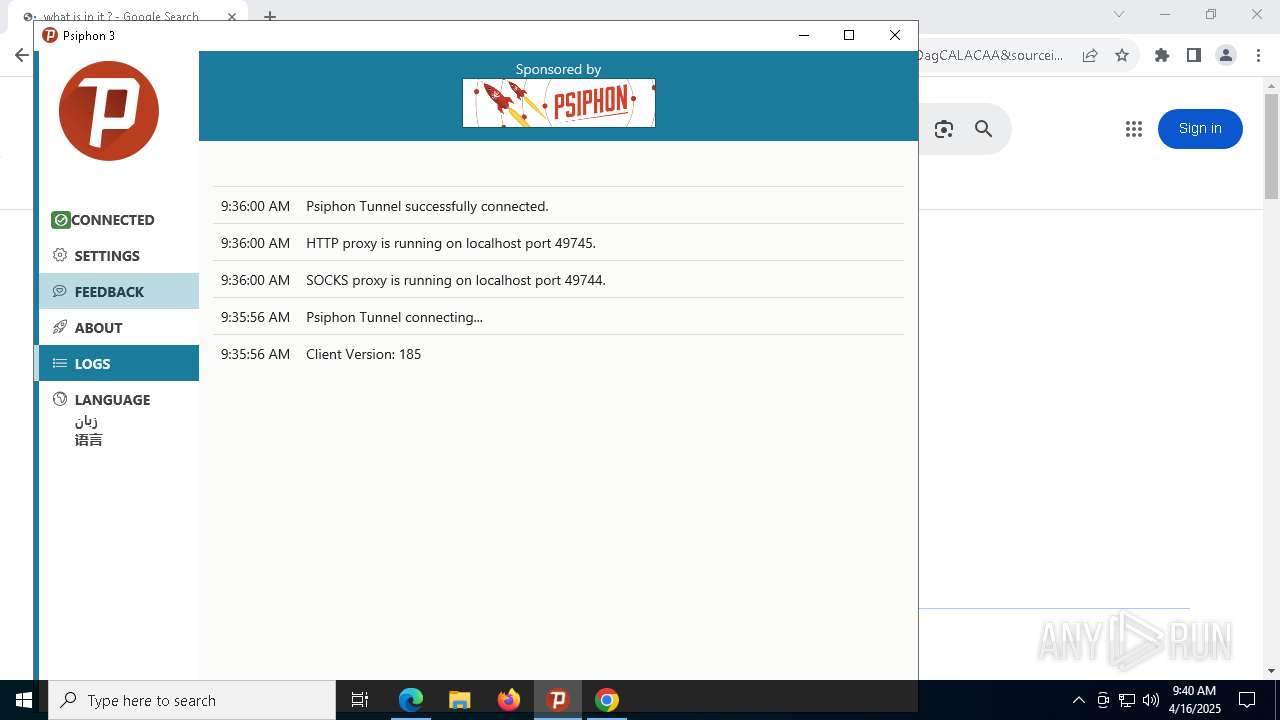
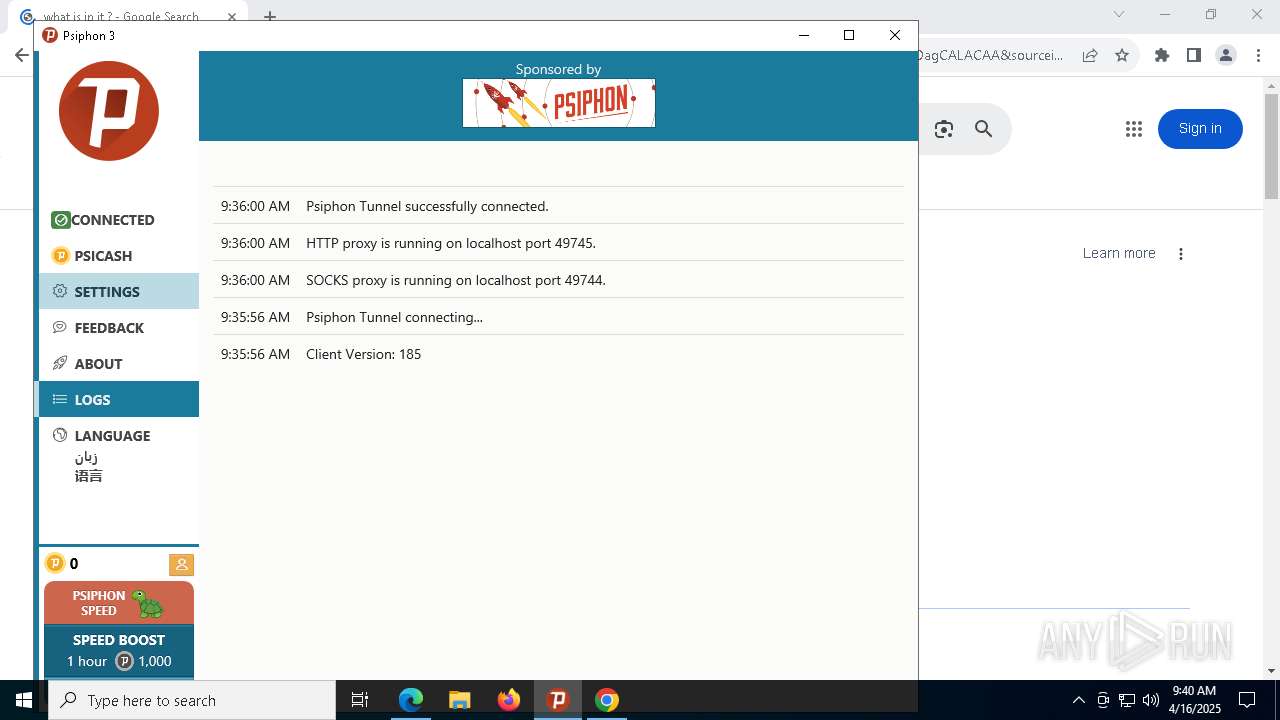
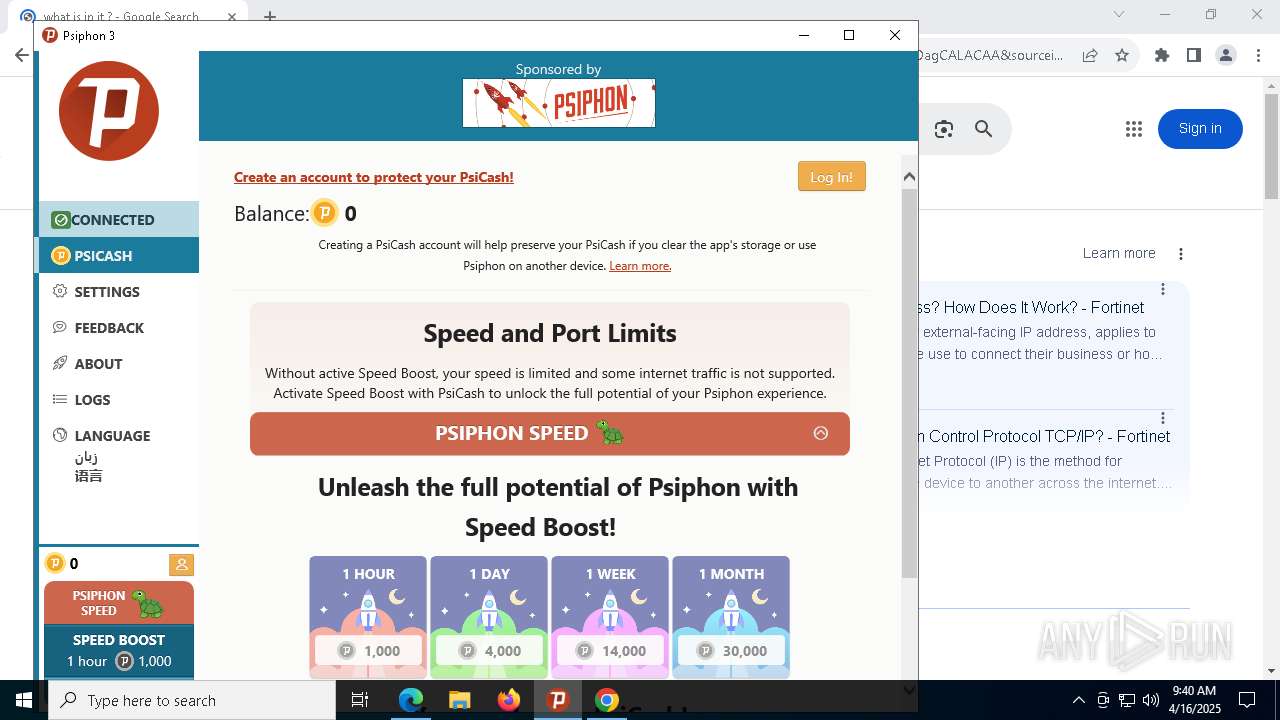
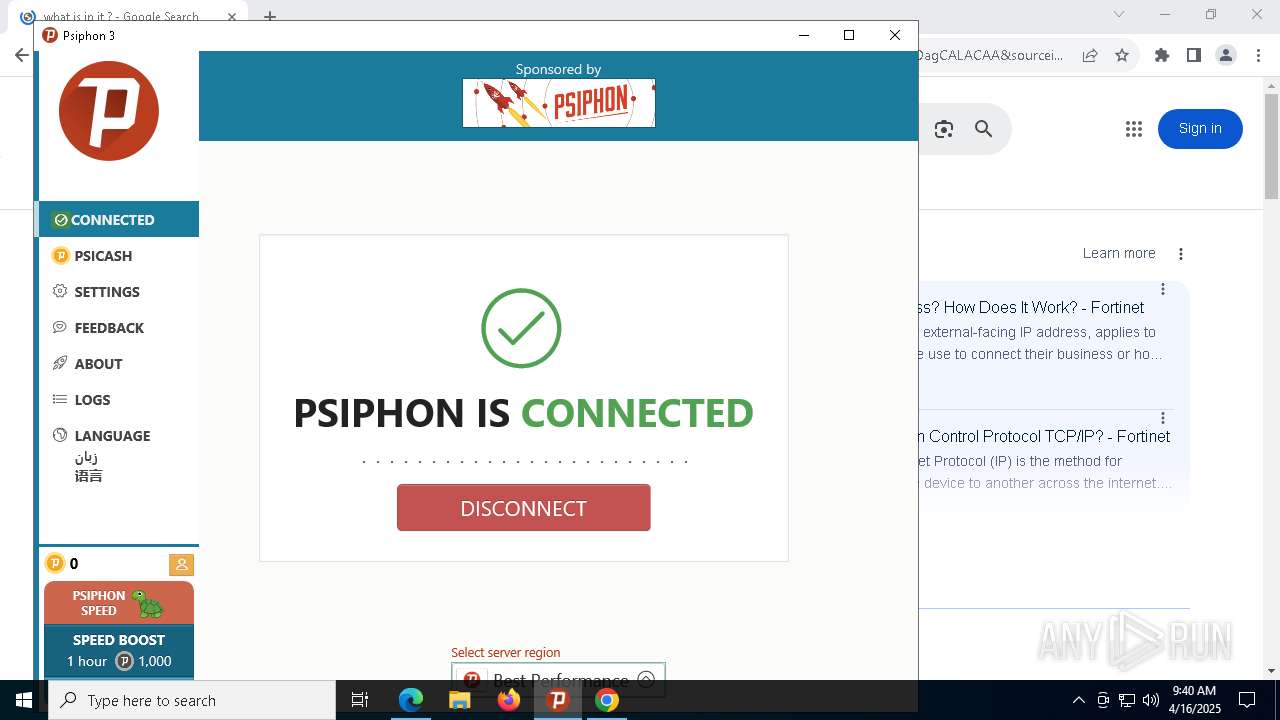
Psiphon VPN has been detected
- psiphon3 (3).exe (PID: 5072)
Executable content was dropped or overwritten
- psiphon3 (3).exe (PID: 5072)
Potential Corporate Privacy Violation
- psiphon-tunnel-core.exe (PID: 920)
Connects to unusual port
- psiphon-tunnel-core.exe (PID: 920)
Connects to SSH
- psiphon-tunnel-core.exe (PID: 920)
There is functionality for taking screenshot (YARA)
- psiphon3 (3).exe (PID: 5072)
INFO
Checks supported languages
- psiphon3 (3).exe (PID: 5072)
- psiphon-tunnel-core.exe (PID: 920)
- identity_helper.exe (PID: 7748)
Reads the computer name
- psiphon3 (3).exe (PID: 5072)
- psiphon-tunnel-core.exe (PID: 920)
- identity_helper.exe (PID: 7748)
Checks proxy server information
- psiphon3 (3).exe (PID: 5072)
- slui.exe (PID: 2644)
Disables trace logs
- psiphon3 (3).exe (PID: 5072)
Creates files or folders in the user directory
- psiphon3 (3).exe (PID: 5072)
- psiphon-tunnel-core.exe (PID: 920)
Create files in a temporary directory
- psiphon3 (3).exe (PID: 5072)
Application launched itself
- msedge.exe (PID: 728)
- chrome.exe (PID: 2568)
UPX packer has been detected
- psiphon3 (3).exe (PID: 5072)
Detects GO elliptic curve encryption (YARA)
- psiphon3 (3).exe (PID: 5072)
- psiphon-tunnel-core.exe (PID: 920)
Reads the software policy settings
- psiphon3 (3).exe (PID: 5072)
- slui.exe (PID: 1764)
- psiphon-tunnel-core.exe (PID: 920)
- slui.exe (PID: 2644)
Application based on Golang
- psiphon-tunnel-core.exe (PID: 920)
- psiphon3 (3).exe (PID: 5072)
Manual execution by a user
- chrome.exe (PID: 2568)
Reads the machine GUID from the registry
- psiphon-tunnel-core.exe (PID: 920)
Reads Environment values
- identity_helper.exe (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:01:19 23:15:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 10149888 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 20512768 |
| EntryPoint: | 0x1d3c2b0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
204
Monitored processes
65
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
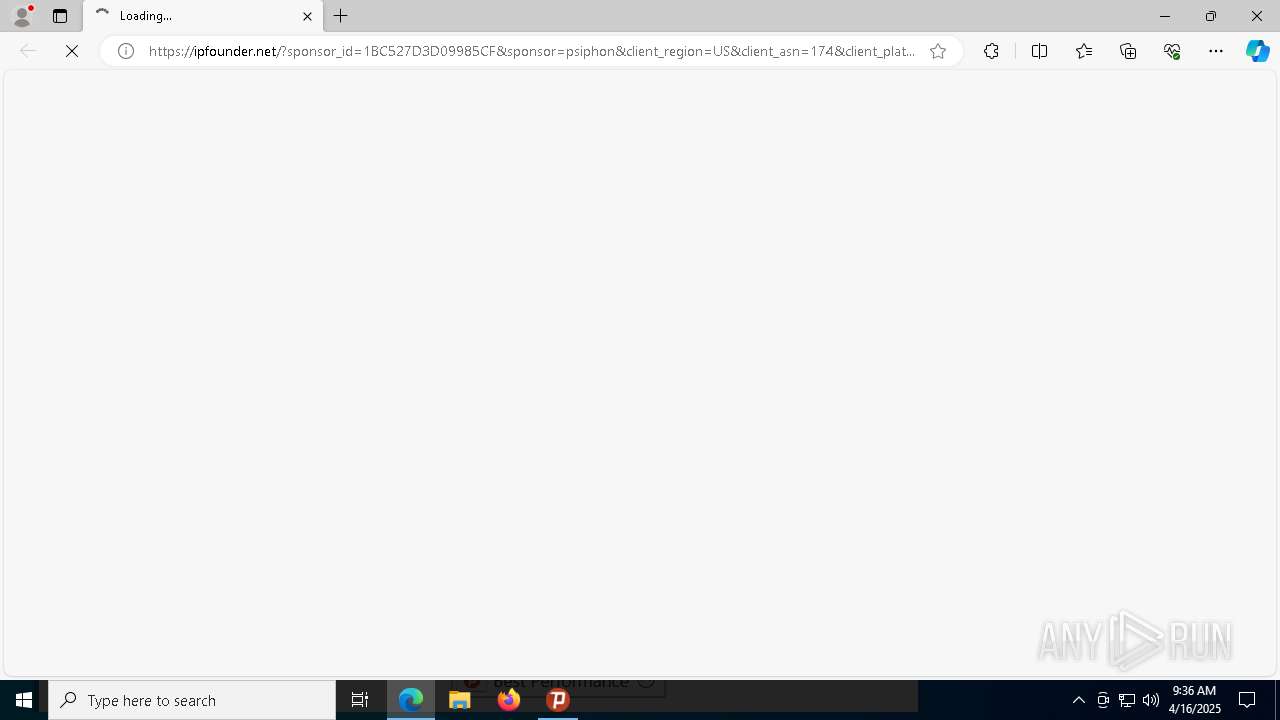
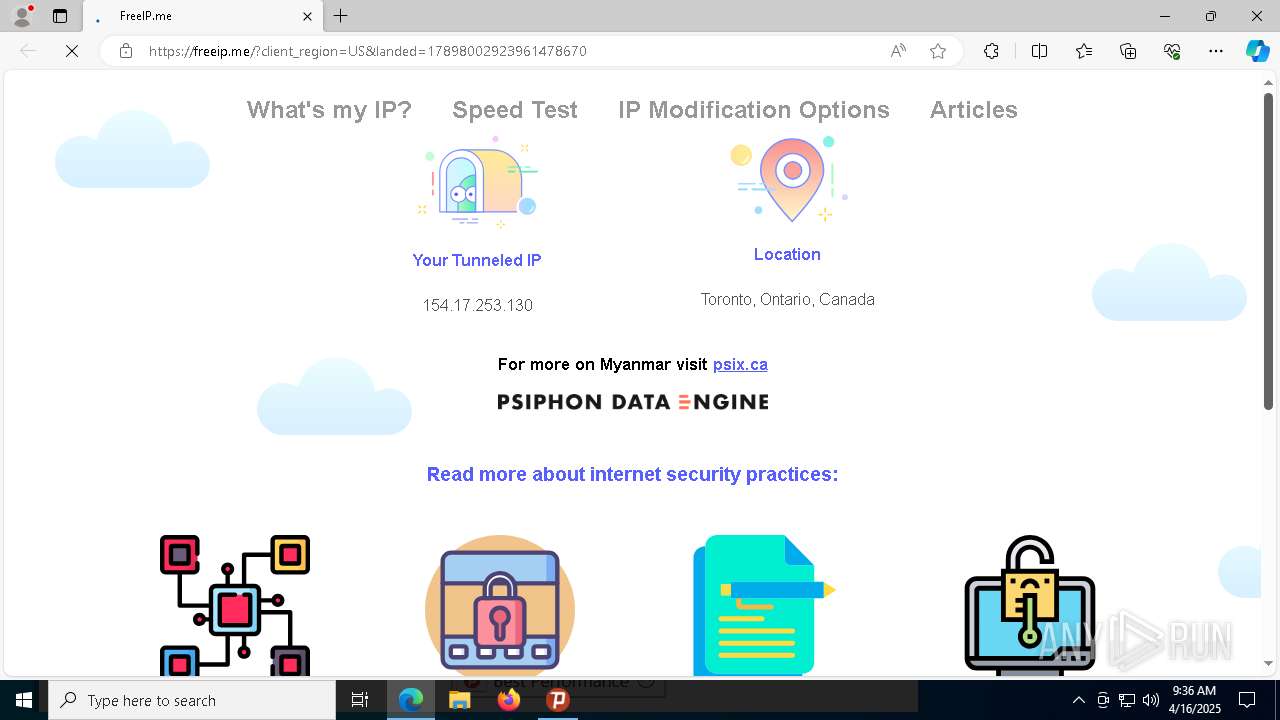
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://ipfounder.net/?sponsor_id=1BC527D3D09985CF&sponsor=psiphon&client_region=US&client_asn=174&client_platform=windows&secret=580EfjEI29xL3hoyU6dgP4vSEVxdcGI7JDFkxgjds7PHulSEF0wmORpvzbqxyTwYtpowsY4xMFnfWEnTghe6l8jiV9K5QSZoir2i6fDeKJD6EhL6DkoYTEMu2EE9YJvy3LdCUZ7ncdVC6ipgWx06wznvDLbY1ajfcfRGCpfsQJei2q6tb0GSFh1QK3x3qXKwyjmNPc5J&psireason=connect&psicash=eyJtZXRhZGF0YSI6eyJjbGllbnRfcmVnaW9uIjoiVVMiLCJjbGllbnRfdmVyc2lvbiI6IjE4NSIsInByb3BhZ2F0aW9uX2NoYW5uZWxfaWQiOiJBNTIwQ0NERTJBQzYyNkQ2Iiwic3BvbnNvcl9pZCI6IkJDQTBCN0I2RDk0NDVGNzMiLCJ1c2VyX2FnZW50IjoiUHNpcGhvbi1Qc2lDYXNoLVdpbmRvd3MiLCJ2IjoxfSwidGltZXN0YW1wIjoiMjAyNS0wNC0xNlQwOTozNjowMC4wODVaIiwidG9rZW5zIjpudWxsLCJ2IjoxfQ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | psiphon3 (3).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=3816 --field-trial-handle=2528,i,12114701421874528247,6050128982391739095,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe --config "C:\Users\admin\AppData\Local\Psiphon3\psiphon.config" --serverList "C:\Users\admin\AppData\Local\Psiphon3\server_list.dat" | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe | psiphon3 (3).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1764 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3724 --field-trial-handle=1884,i,11808505890401066552,13840847664799426204,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6500 --field-trial-handle=2528,i,12114701421874528247,6050128982391739095,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2644 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4620 --field-trial-handle=1884,i,11808505890401066552,13840847664799426204,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3164 --field-trial-handle=1884,i,11808505890401066552,13840847664799426204,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
17 847
Read events
17 768
Write events
73
Delete events
6
Modification events
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Psiphon3 |
| Operation: | write | Name: | SkipProxySettings |
Value: 0 | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Psiphon3 |
| Operation: | write | Name: | SkipAutoConnect |
Value: 0 | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CLASSES_ROOT\psiphon |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyHost |
Value: | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyUsername |
Value: | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyPassword |
Value: | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyDomain |
Value: | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5072) psiphon3 (3).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
24
Suspicious files
361
Text files
146
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10dbac.TMP | — | |
MD5:— | SHA256:— | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10dbac.TMP | — | |
MD5:— | SHA256:— | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10dbac.TMP | — | |
MD5:— | SHA256:— | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | psiphon3 (3).exe | C:\Users\admin\AppData\Local\Psiphon3\psicash\psicashdatastore.prod.2.temp | binary | |
MD5:5AD5CC4D26869082EFD29C436B57384A | SHA256:C5C24F7CA1C946FA4DFD44407409C8E11EC6E41F0E1C7C45BF8381B42AFB31F1 | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10dcc5.TMP | — | |
MD5:— | SHA256:— | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10dcc5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
36
DNS requests
14
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
920 | psiphon-tunnel-core.exe | 104.18.164.46:443 | — | CLOUDFLARENET | — | unknown |
920 | psiphon-tunnel-core.exe | 5.254.60.251:443 | — | — | — | unknown |
920 | psiphon-tunnel-core.exe | 37.46.116.44:53 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
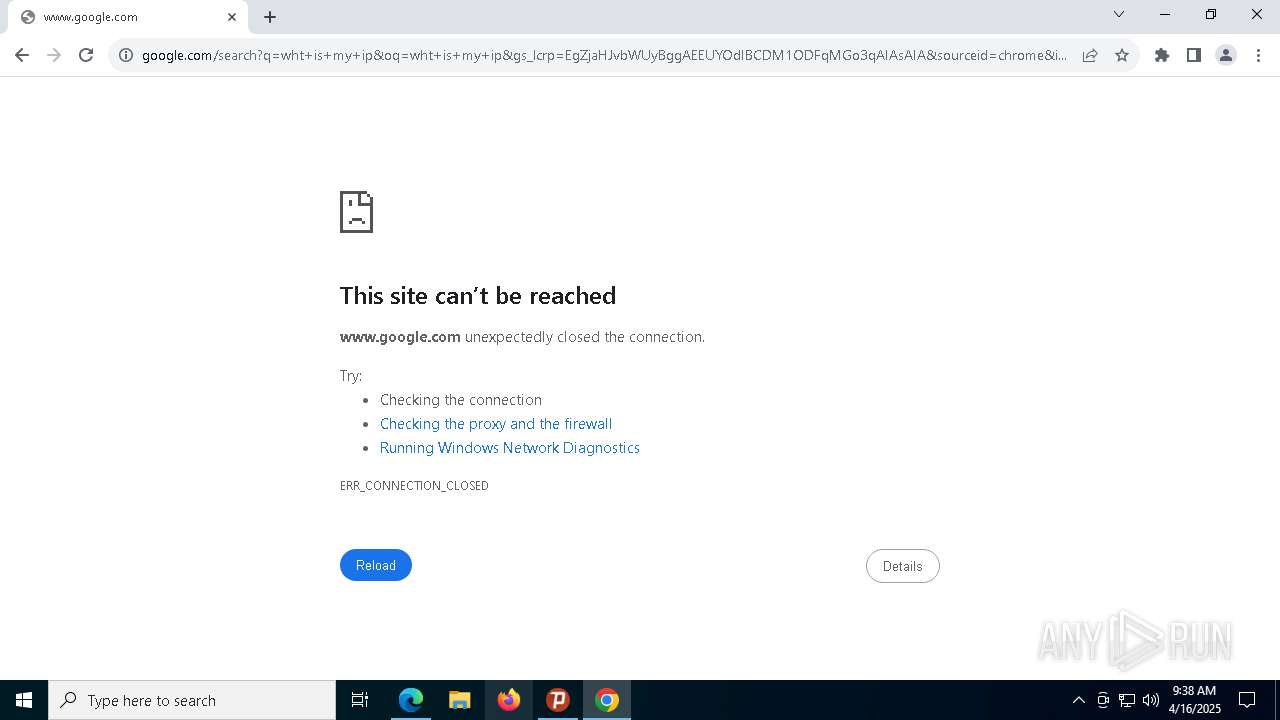
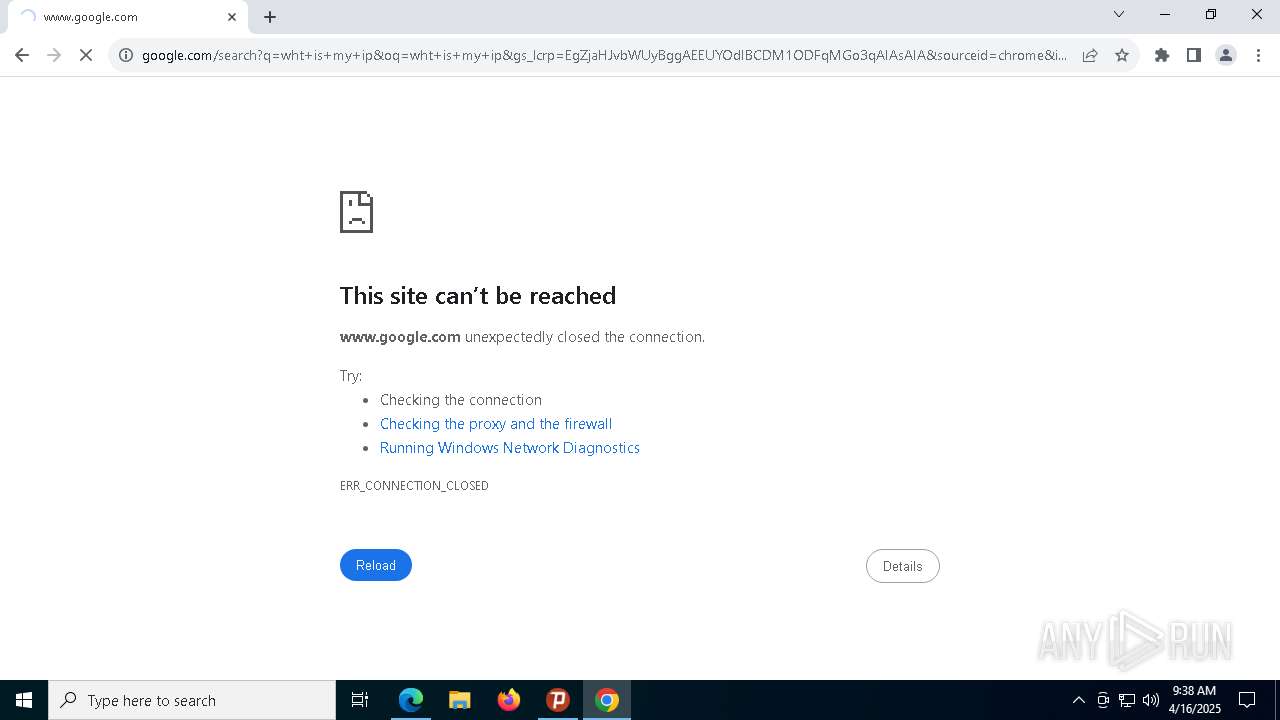
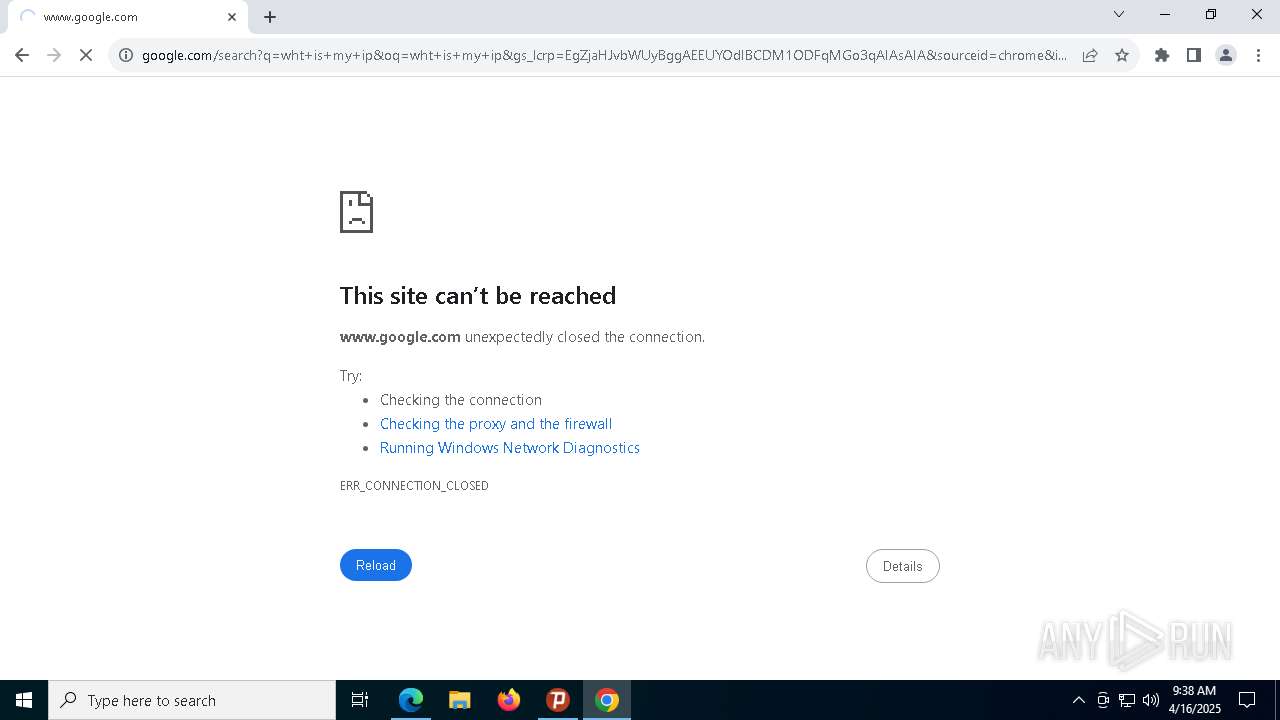
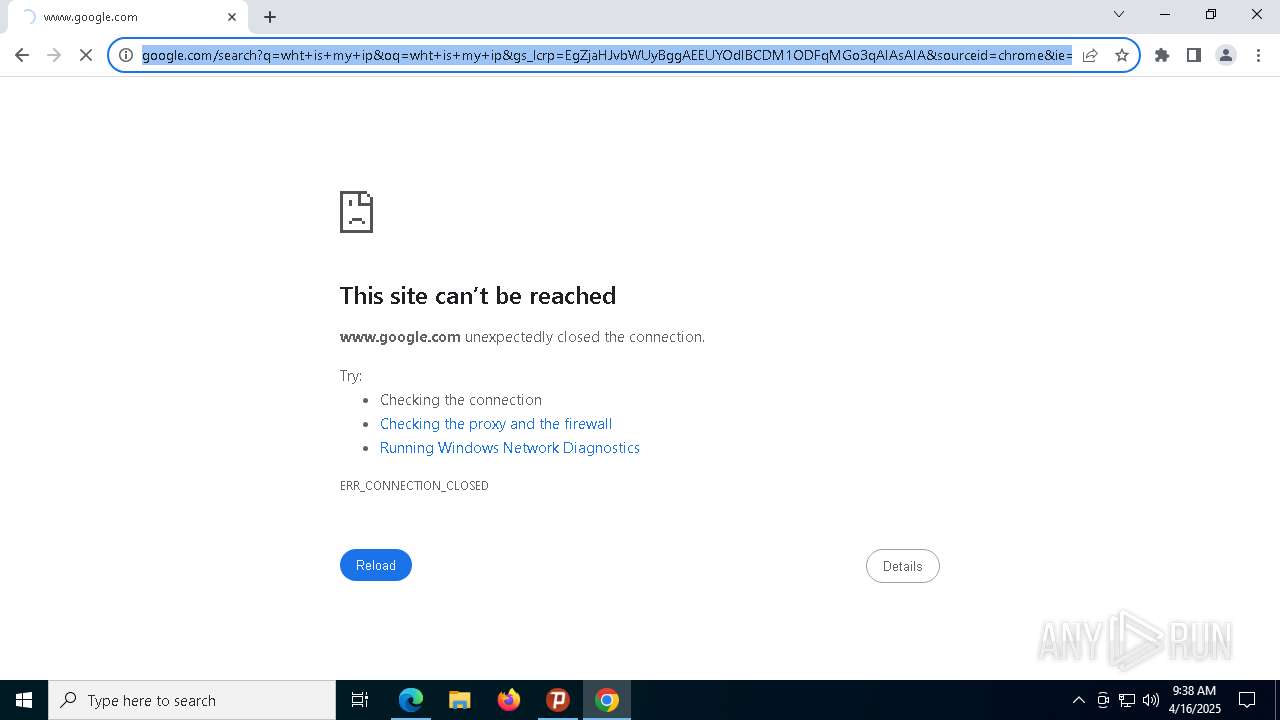
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] A SSH banner has been detected |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
920 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |