| File name: | Spectrasonics_2048_KeyGen.exe |
| Full analysis: | https://app.any.run/tasks/496d5530-54eb-4834-8b2c-b9f0bde6970a |
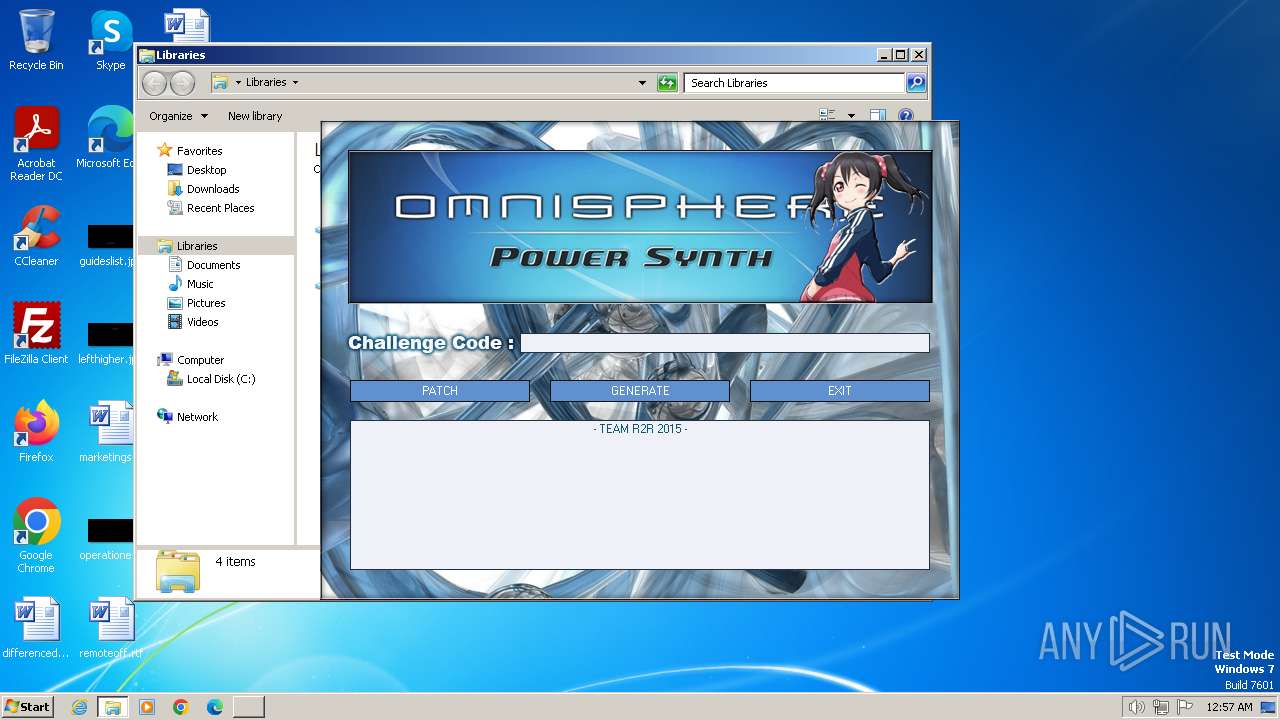
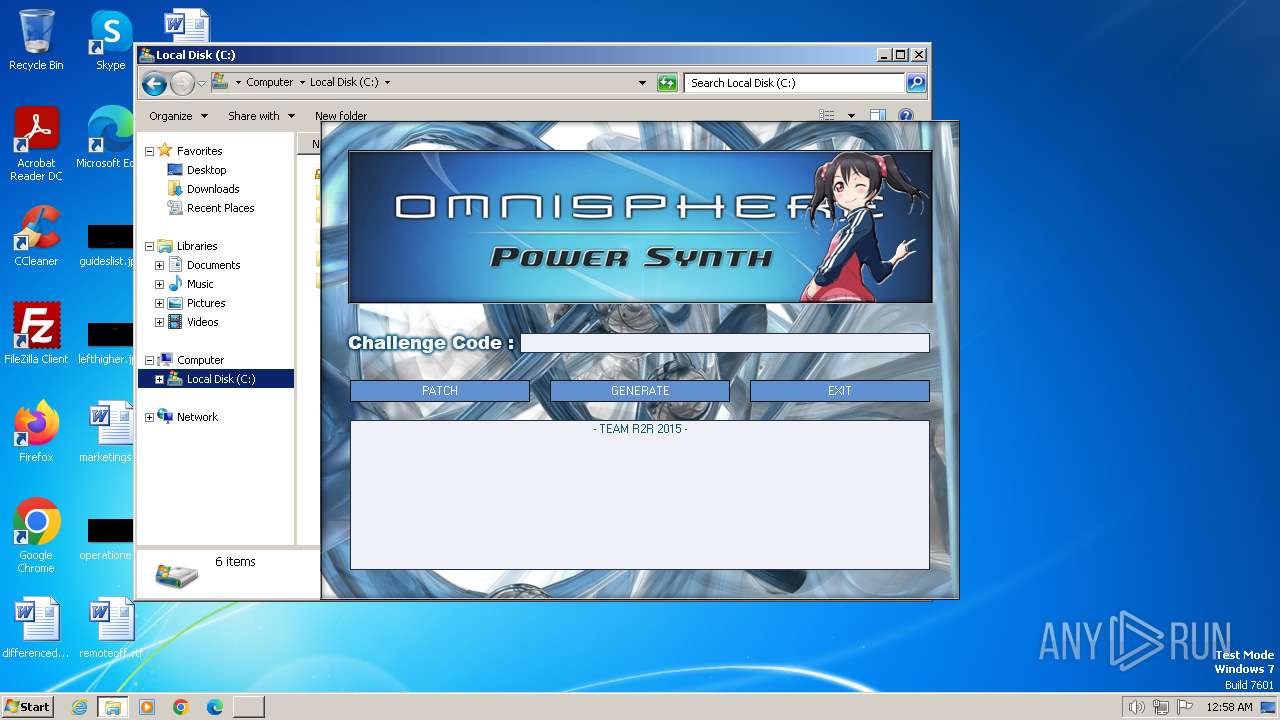
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2024, 00:57:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 17174BC990FCFD50BD3F2E00A2D82ED4 |
| SHA1: | 932CA7164760D452BA89F00E4B58DE79A2C9DF67 |
| SHA256: | D1436AAE15D42FFFE91BB0E77114BB66B4C97E58111E09AF2A10166790FE6EA1 |
| SSDEEP: | 24576:4cLwbUNL3di0CQki5R5uUO5qgd6fBn6DjPzs0Hjr3HwXBEBSllJ8NY6G:4AwbUNLdrRT5RsR5rd6J6DLXfHwRE075 |
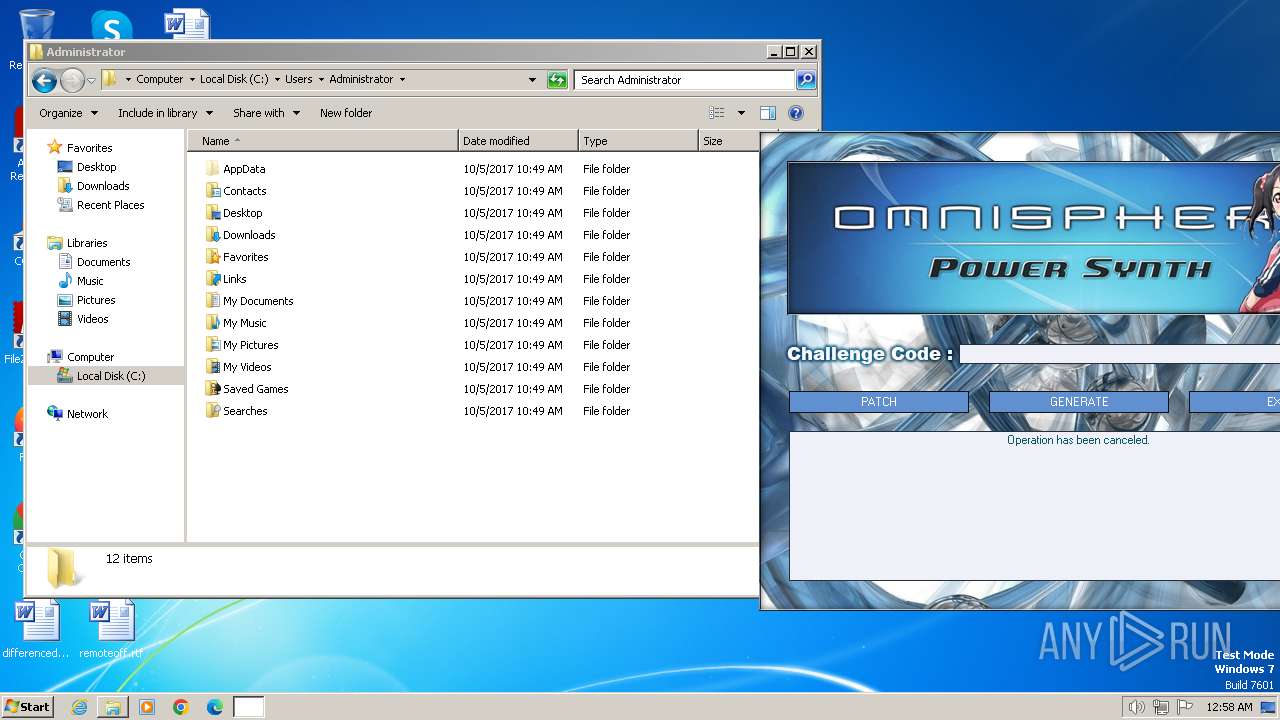
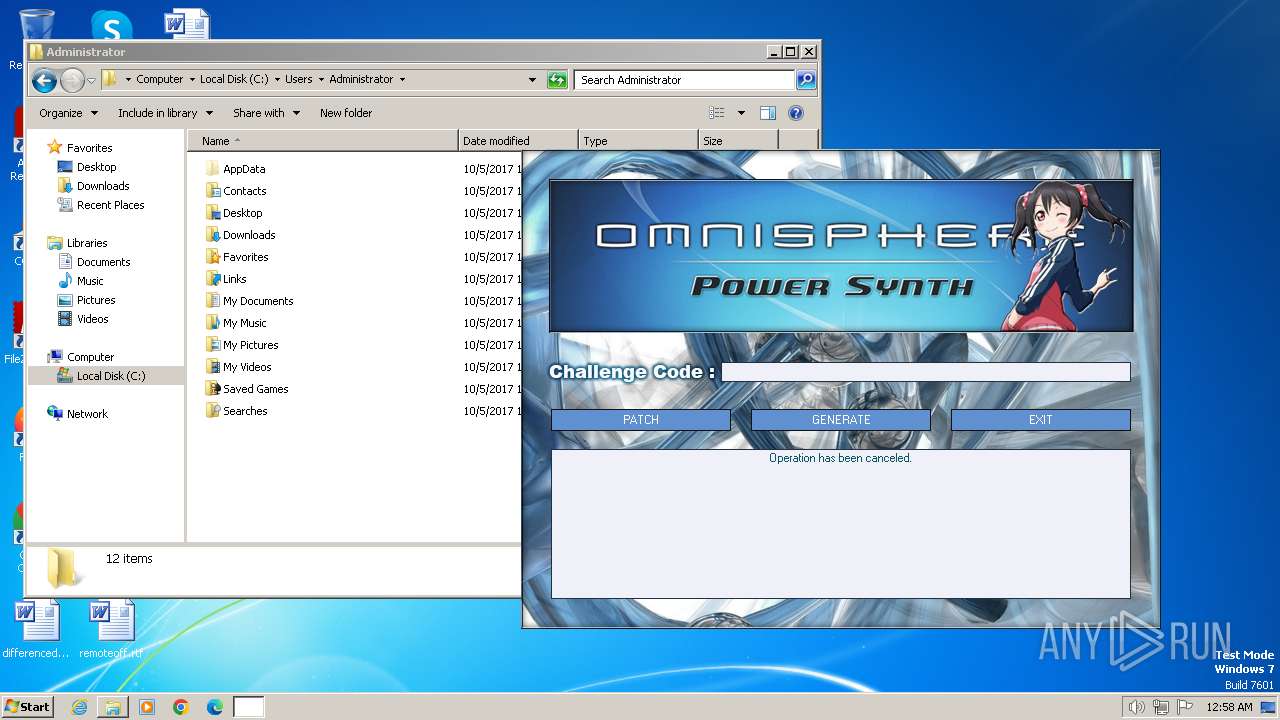
MALICIOUS
Drops the executable file immediately after the start
- Spectrasonics_2048_KeyGen.exe (PID: 1388)
SUSPICIOUS
Executable content was dropped or overwritten
- Spectrasonics_2048_KeyGen.exe (PID: 1388)
INFO
Create files in a temporary directory
- keygen.exe (PID: 1268)
- Spectrasonics_2048_KeyGen.exe (PID: 1388)
Reads the computer name
- Spectrasonics_2048_KeyGen.exe (PID: 1388)
- keygen.exe (PID: 1268)
Checks supported languages
- Spectrasonics_2048_KeyGen.exe (PID: 1388)
- keygen.exe (PID: 1268)
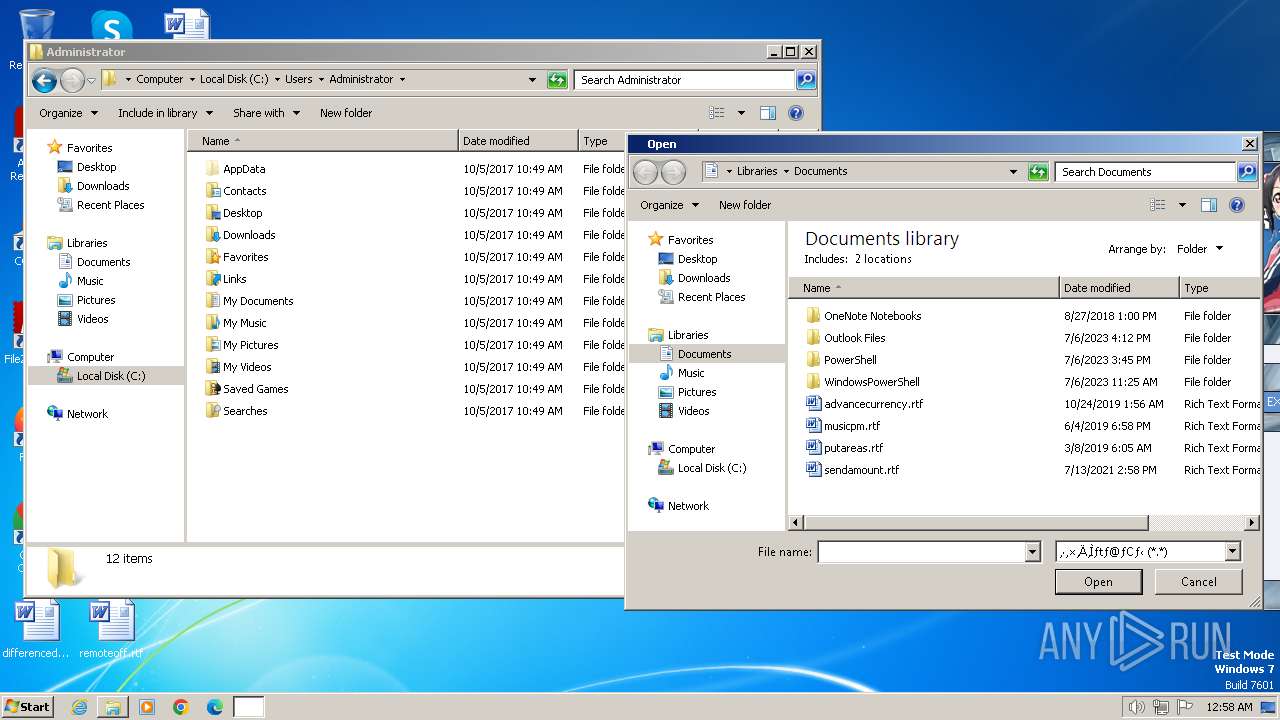
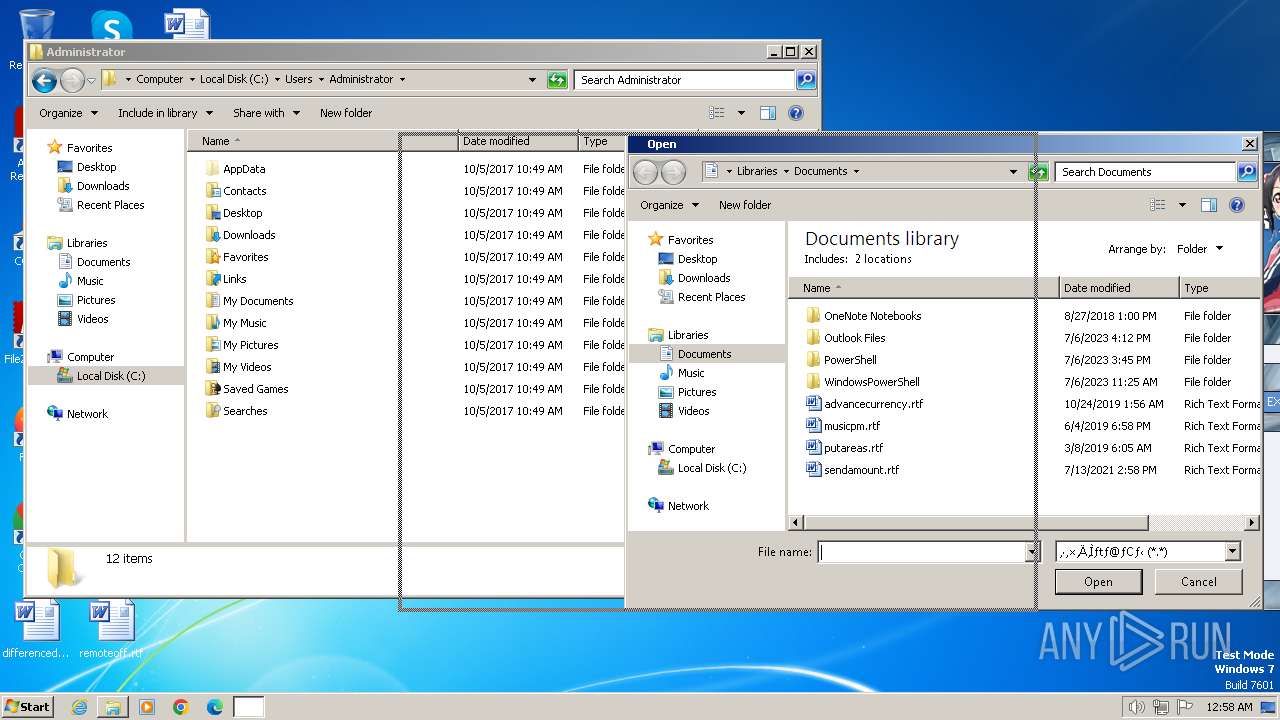
Reads the machine GUID from the registry
- keygen.exe (PID: 1268)
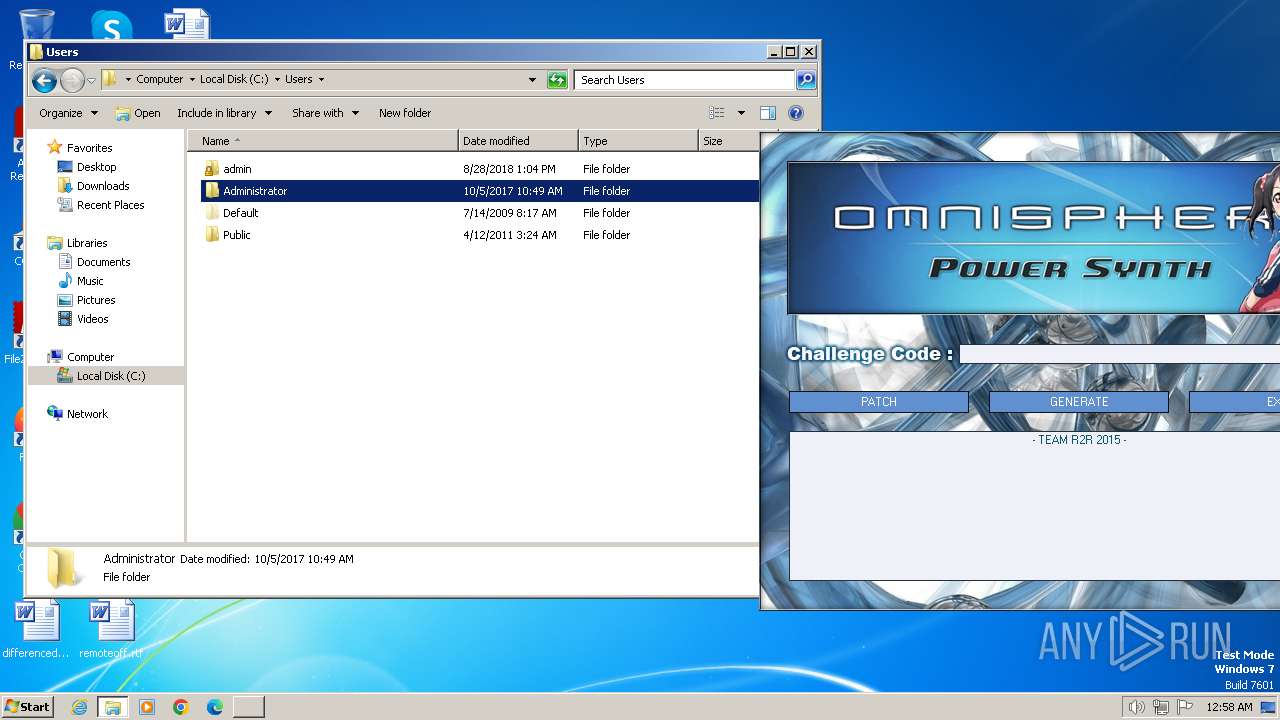
Manual execution by a user
- explorer.exe (PID: 1860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
47
Monitored processes
5
Malicious processes
1
Suspicious processes
0
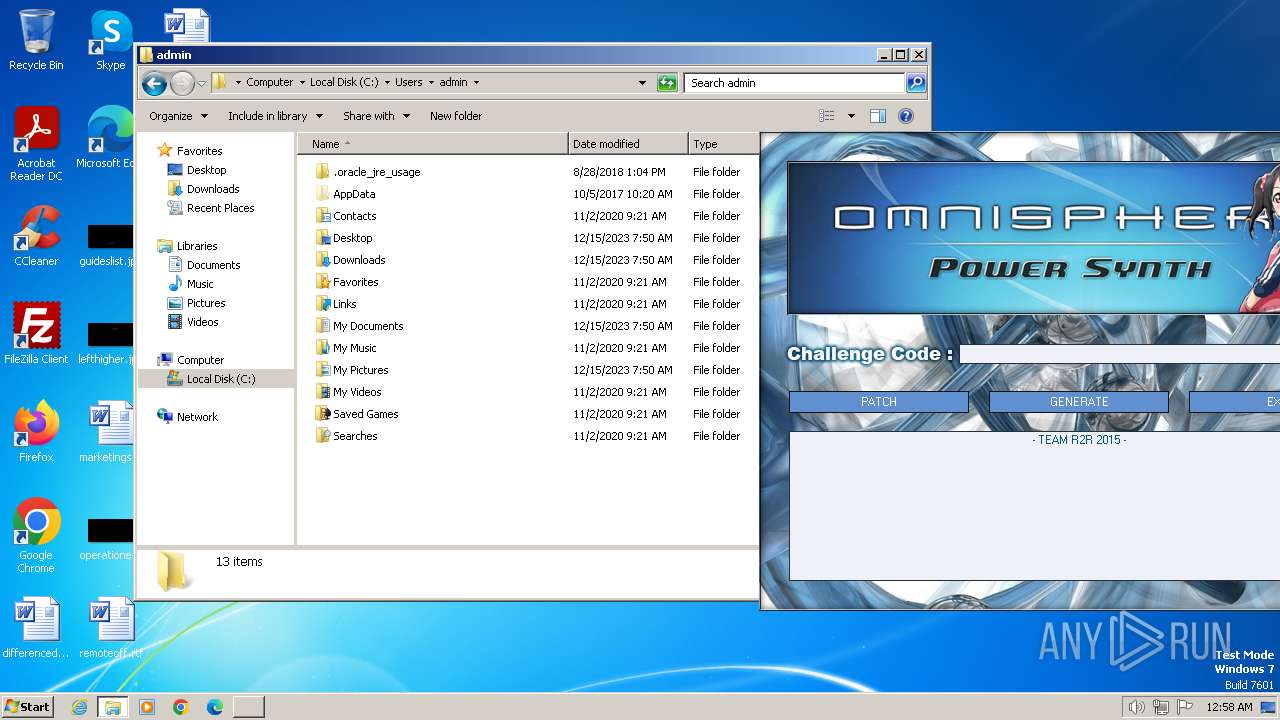
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
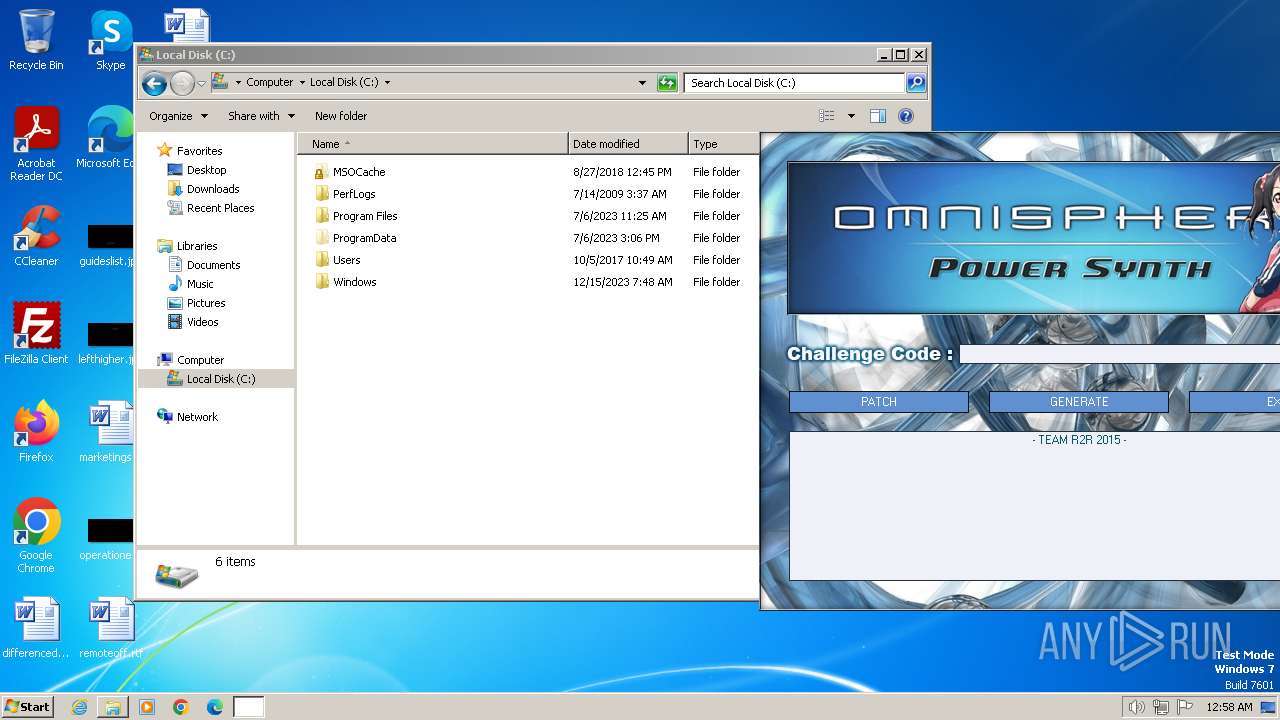
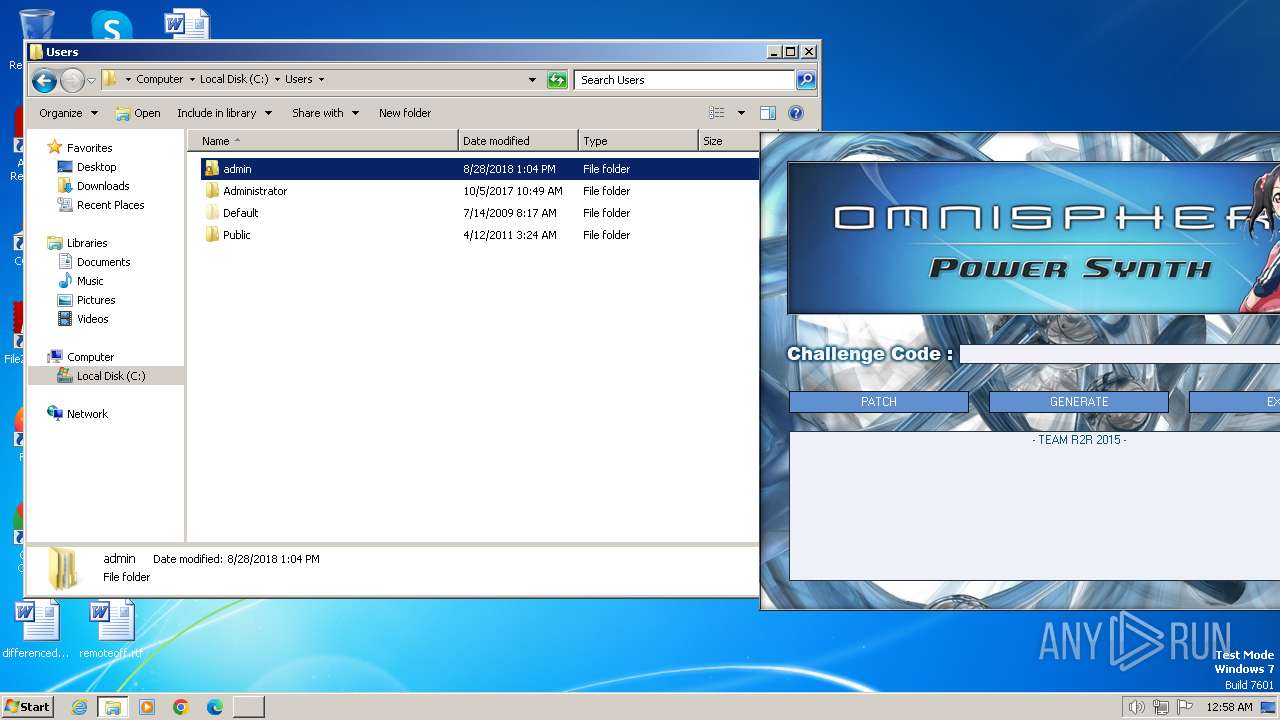
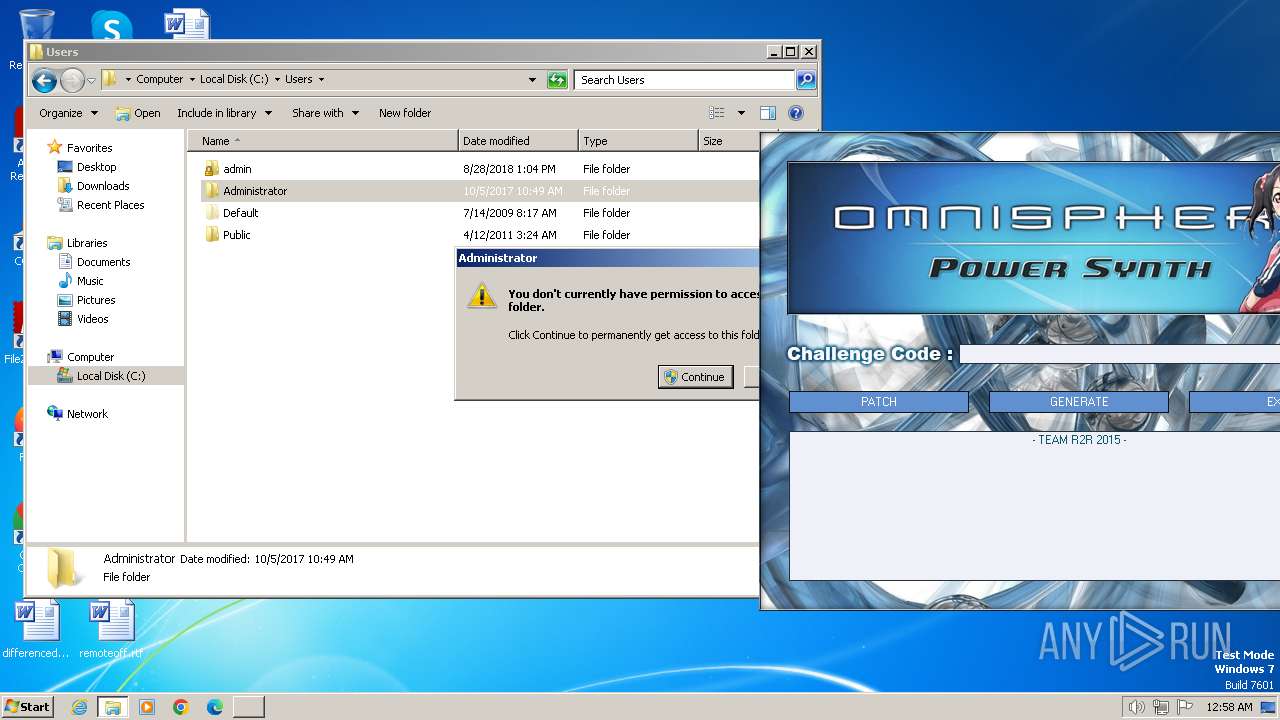
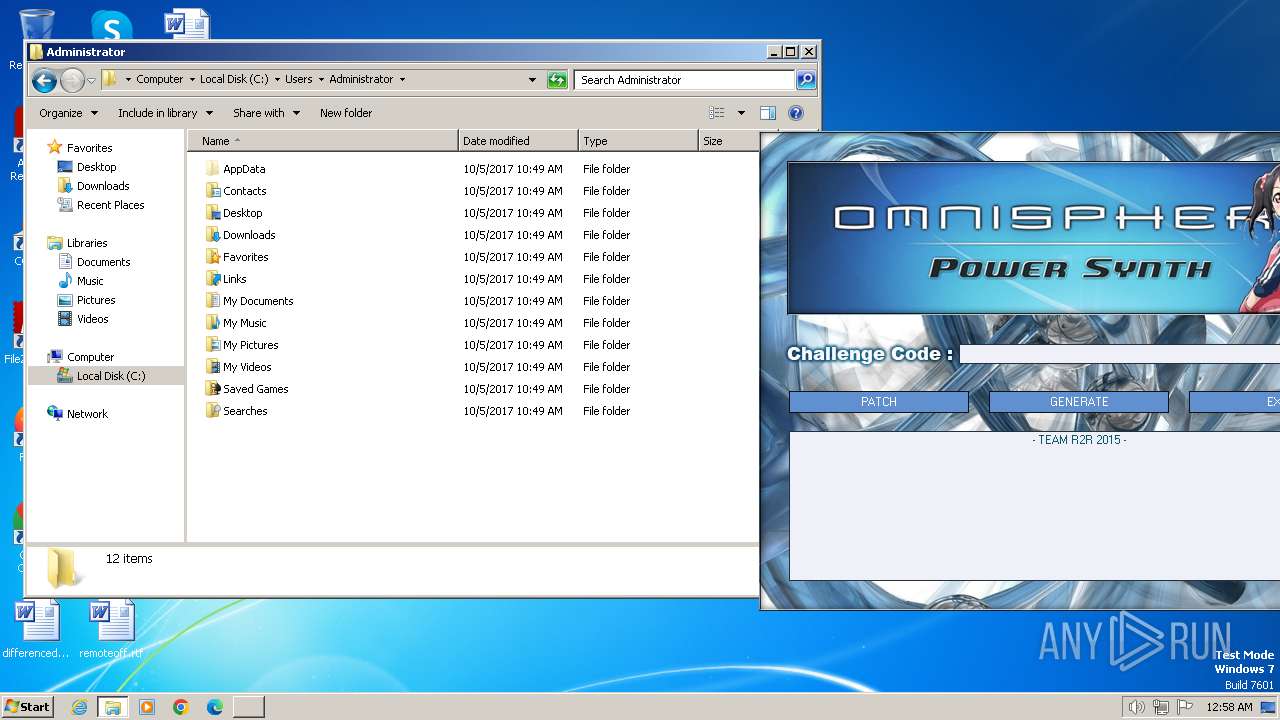
| 984 | "C:\Users\admin\AppData\Local\Temp\Spectrasonics_2048_KeyGen.exe" | C:\Users\admin\AppData\Local\Temp\Spectrasonics_2048_KeyGen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1268 | C:\Users\admin\AppData\Local\Temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | Spectrasonics_2048_KeyGen.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1388 | "C:\Users\admin\AppData\Local\Temp\Spectrasonics_2048_KeyGen.exe" | C:\Users\admin\AppData\Local\Temp\Spectrasonics_2048_KeyGen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1860 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 222
Read events
2 197
Write events
24
Delete events
1
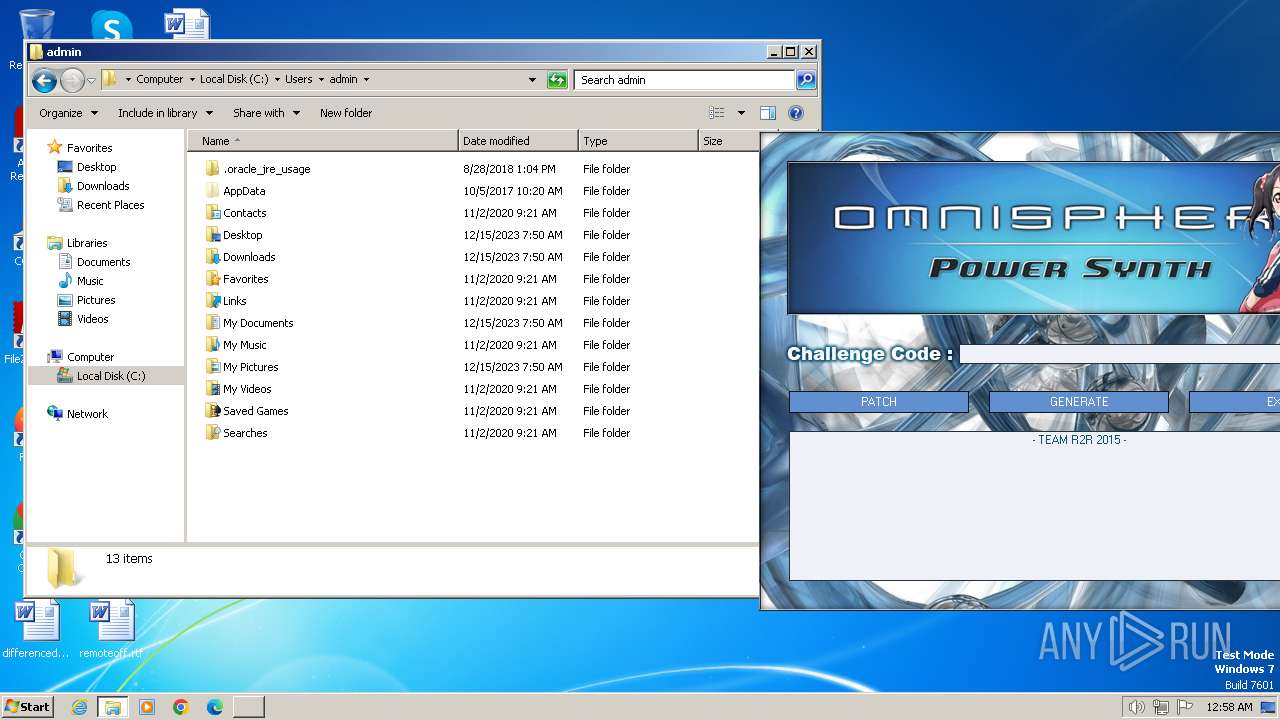
Modification events
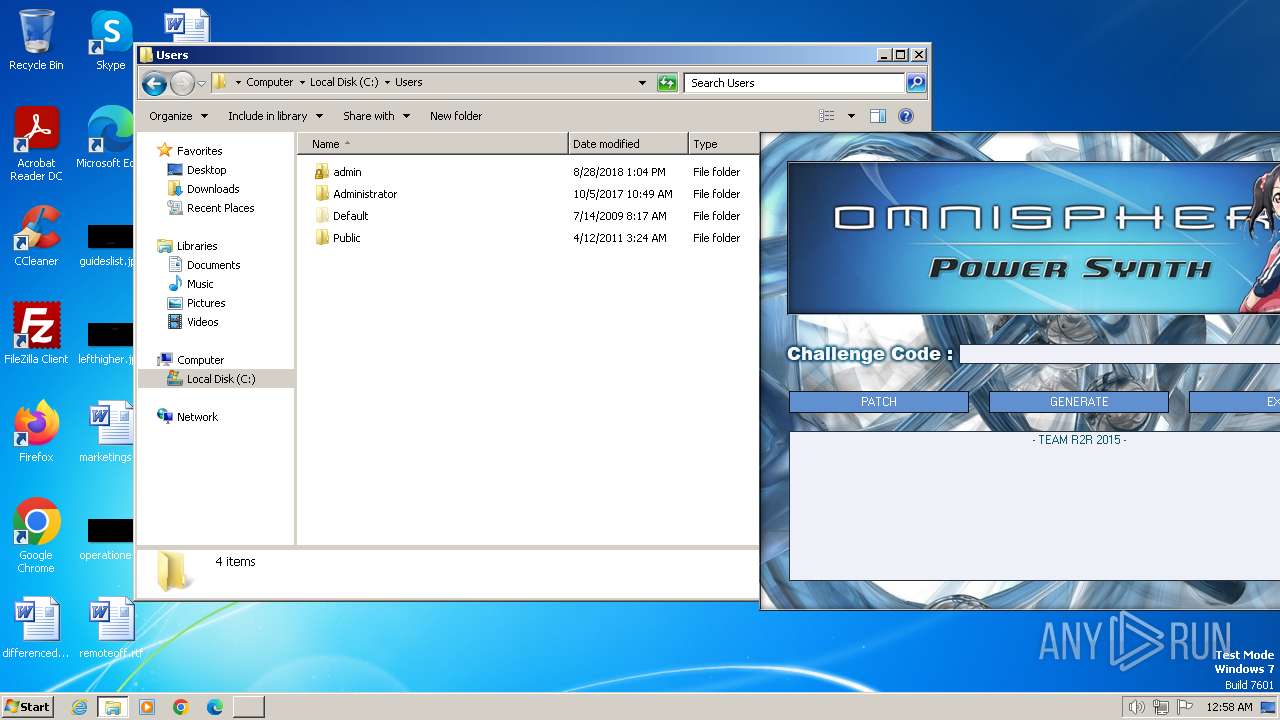
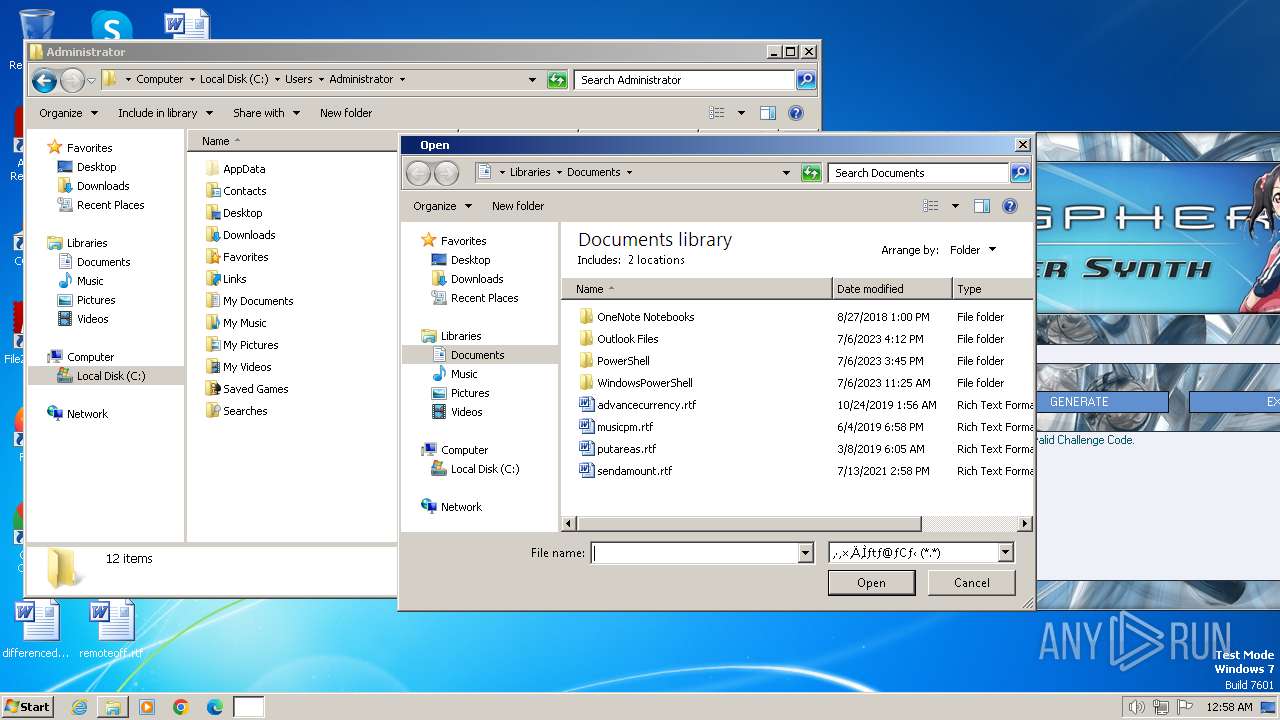
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 010000000200000006000000000000000B000000070000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000006000000000000000B000000070000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 4 |
Value: 6B0065007900670065006E002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000008D010000840000000D04000064020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 00000000020000000300000001000000FFFFFFFF | |||
| (PID) Process: | (1268) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
Executable files
4
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1388 | Spectrasonics_2048_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\R2RSS2048.dll | executable | |
MD5:4D97354487A74D33552AFC93A7A8E1B9 | SHA256:762548049D64380584D2E77B5499F4BEA16693308EE156618C83F0F0B847B064 | |||
| 1388 | Spectrasonics_2048_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\bgm.it | binary | |
MD5:31F24C0967530394A64CB82AC06A1E2F | SHA256:E66ACF2363DAB9A21265651887799B00DC1413B2F70155B9B94A4BB9CFF045BB | |||
| 1388 | Spectrasonics_2048_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 1388 | Spectrasonics_2048_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\R2RTOOL.dll | executable | |
MD5:0B0214CDF2577A43AF135B741D98BC0C | SHA256:D224BED5BBA63C1B222E6628E19615278490C1139804AAFEDE4627DA5BE655CC | |||
| 1388 | Spectrasonics_2048_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:F1F1B28254FC2816DF83BC4432A6D7CF | SHA256:62287A6C233820F45E7250CAAE8EE068425ECF1D229E29316D9F0038401A3751 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |