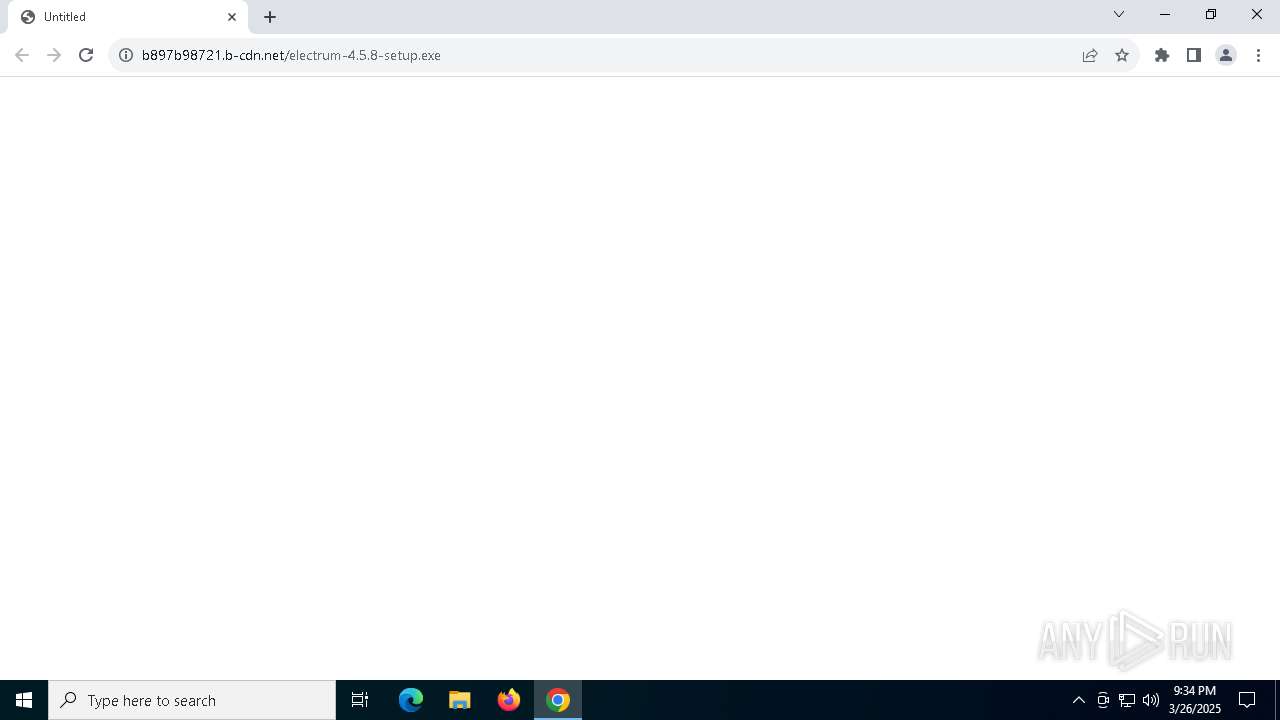
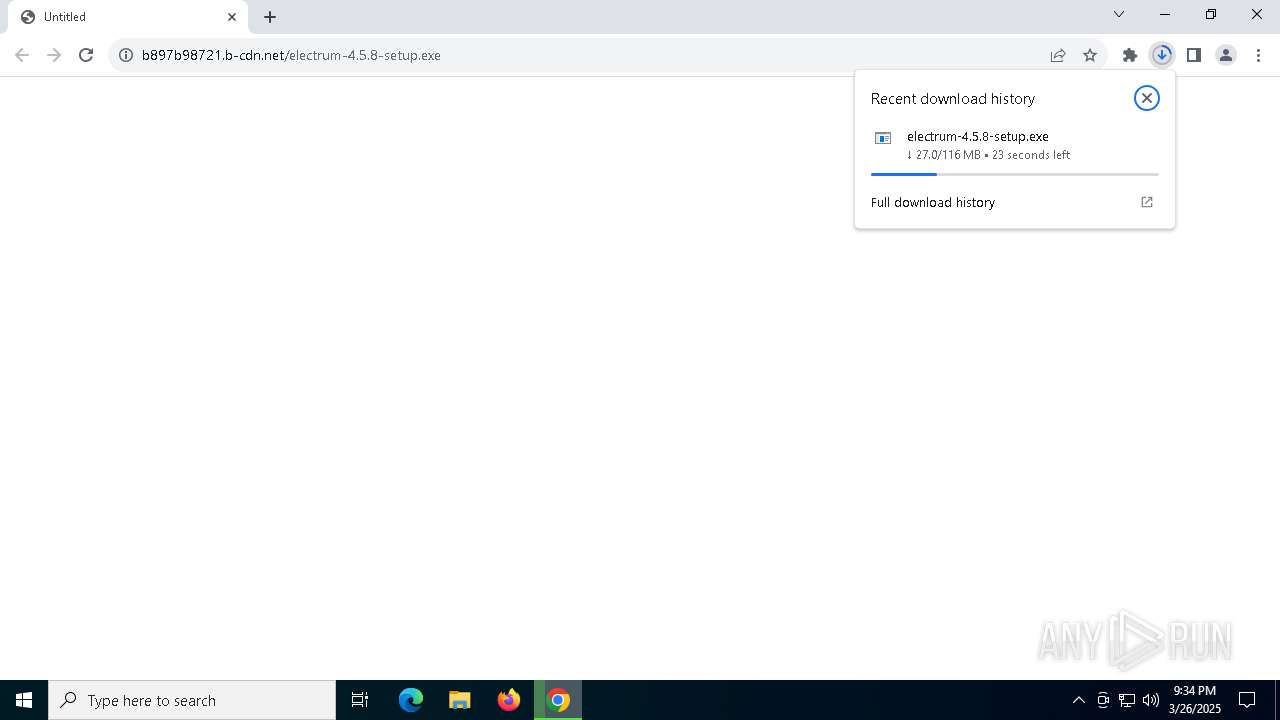
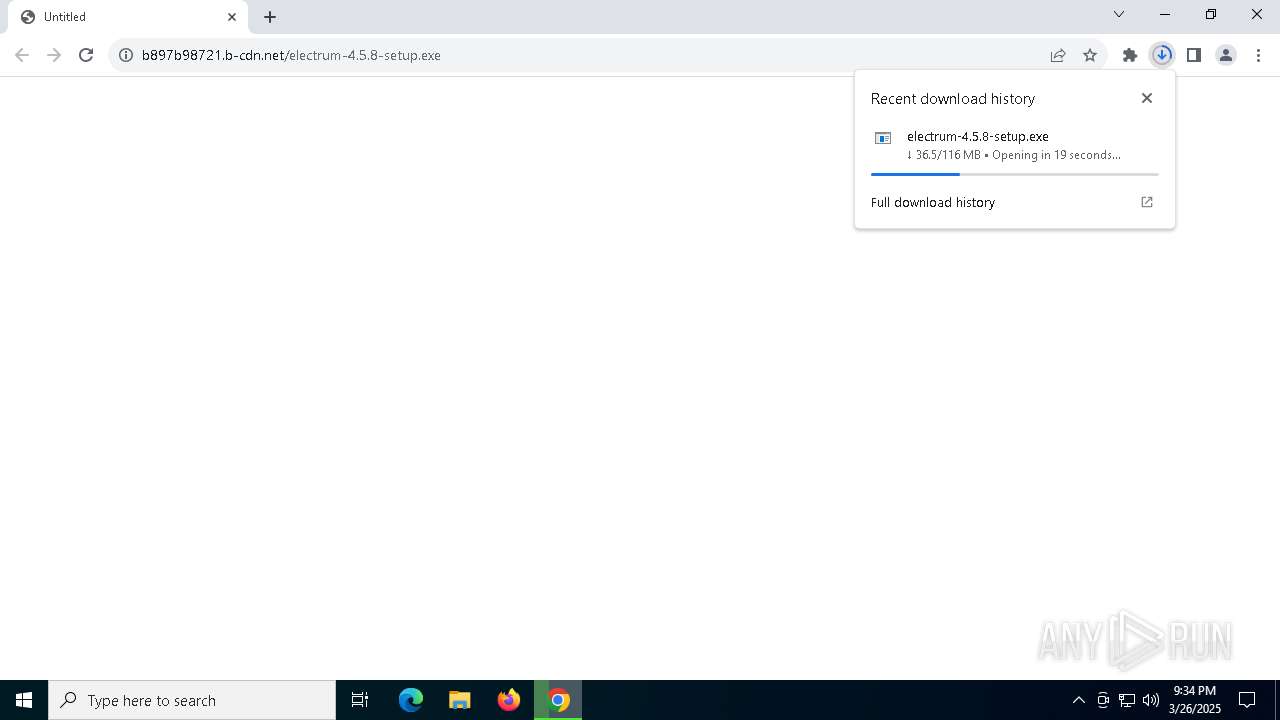
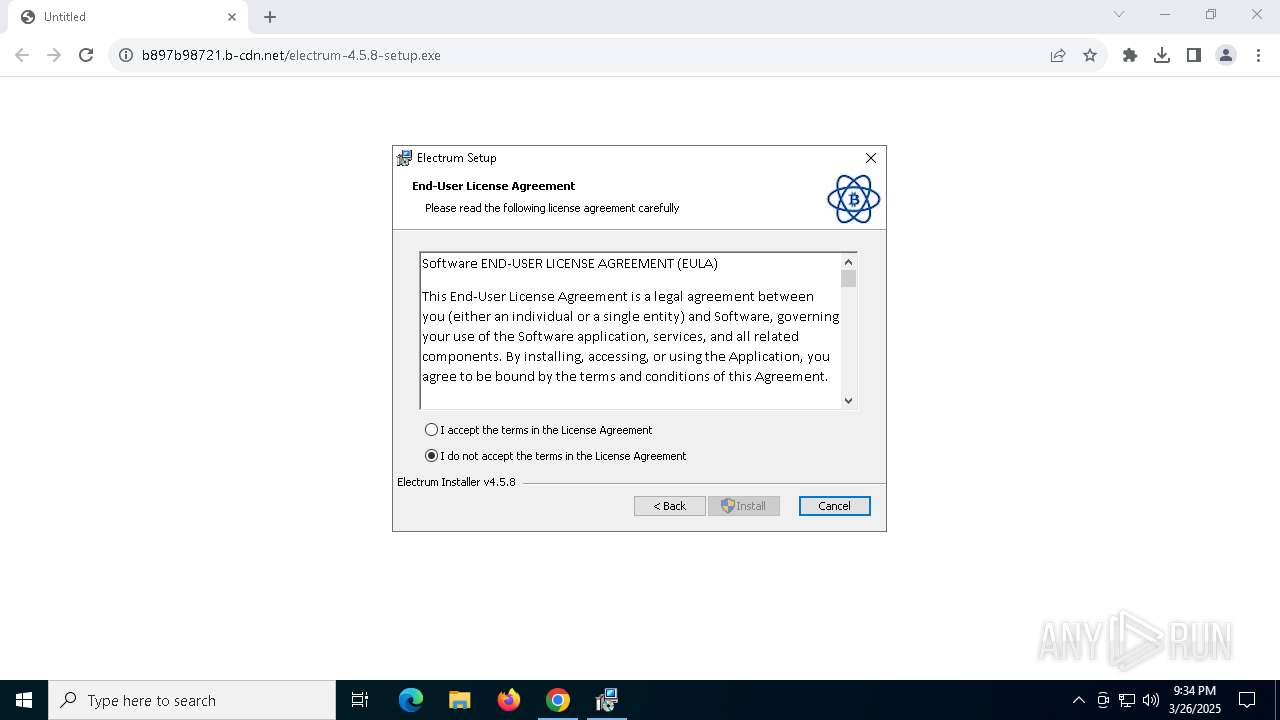
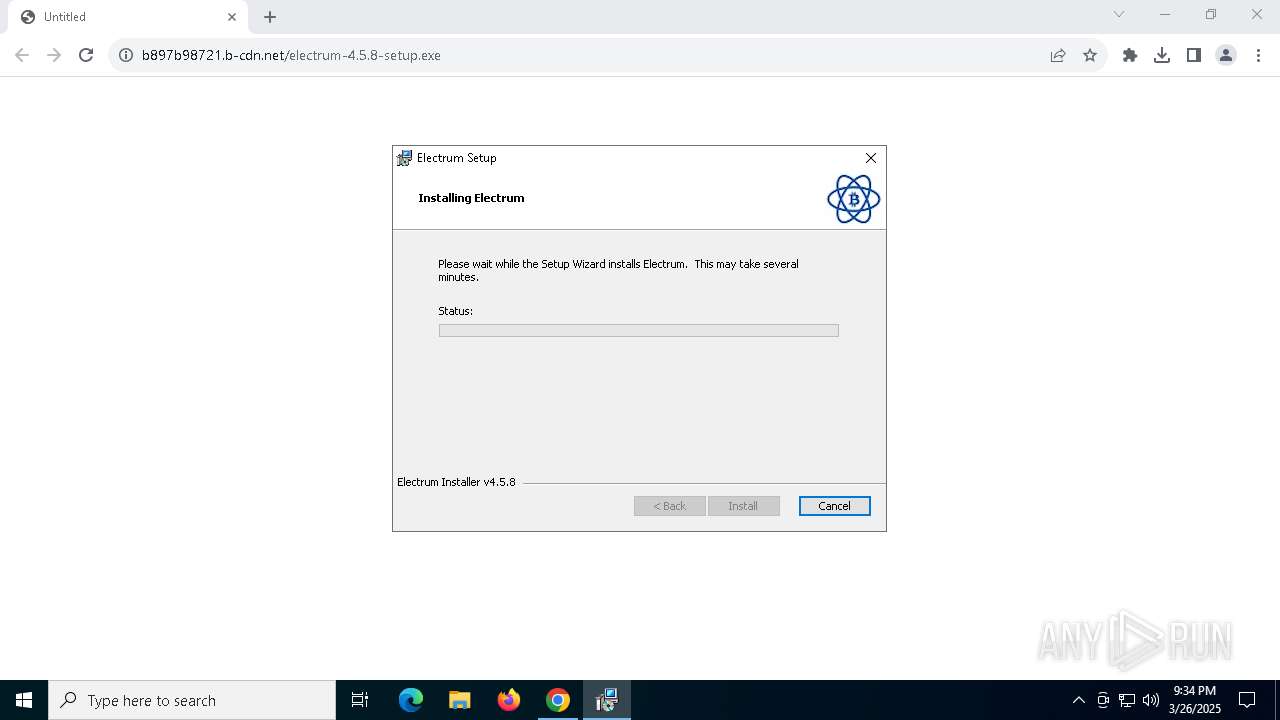
| URL: | https://b897b98721.b-cdn.net/electrum-4.5.8-setup.exe |
| Full analysis: | https://app.any.run/tasks/ced4950c-ef79-4a75-8c8a-7abcaae4ef58 |
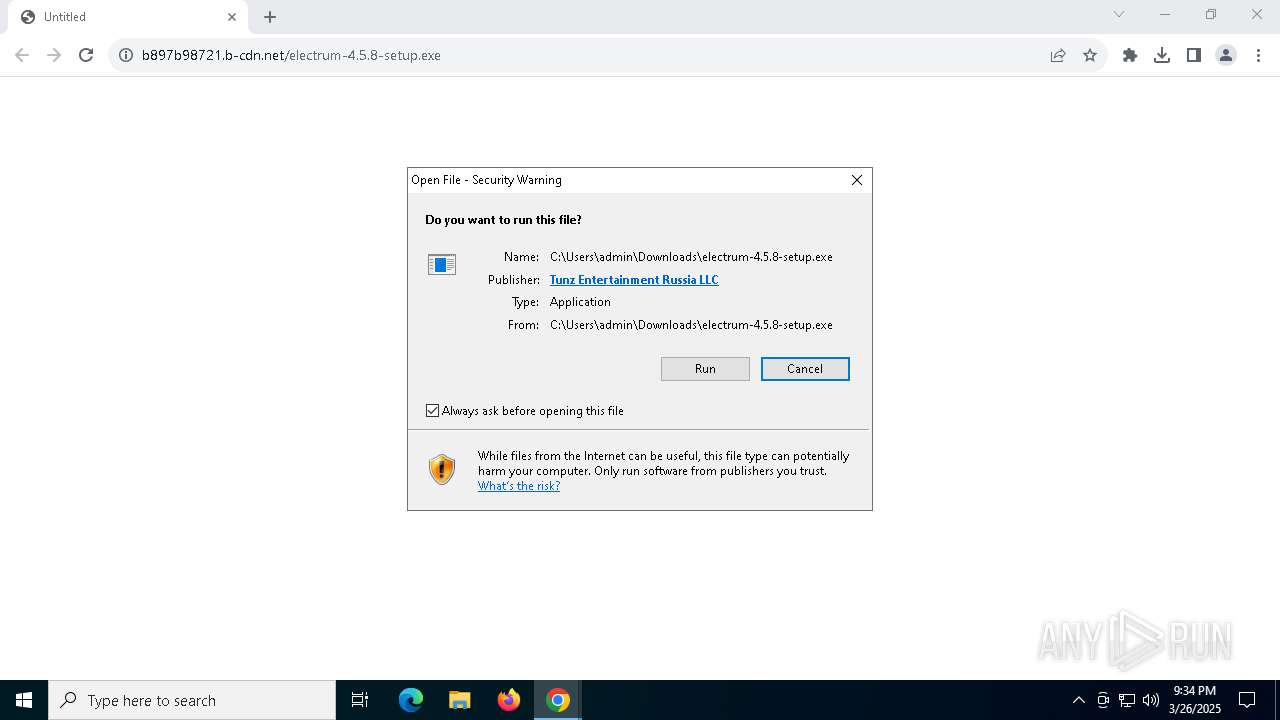
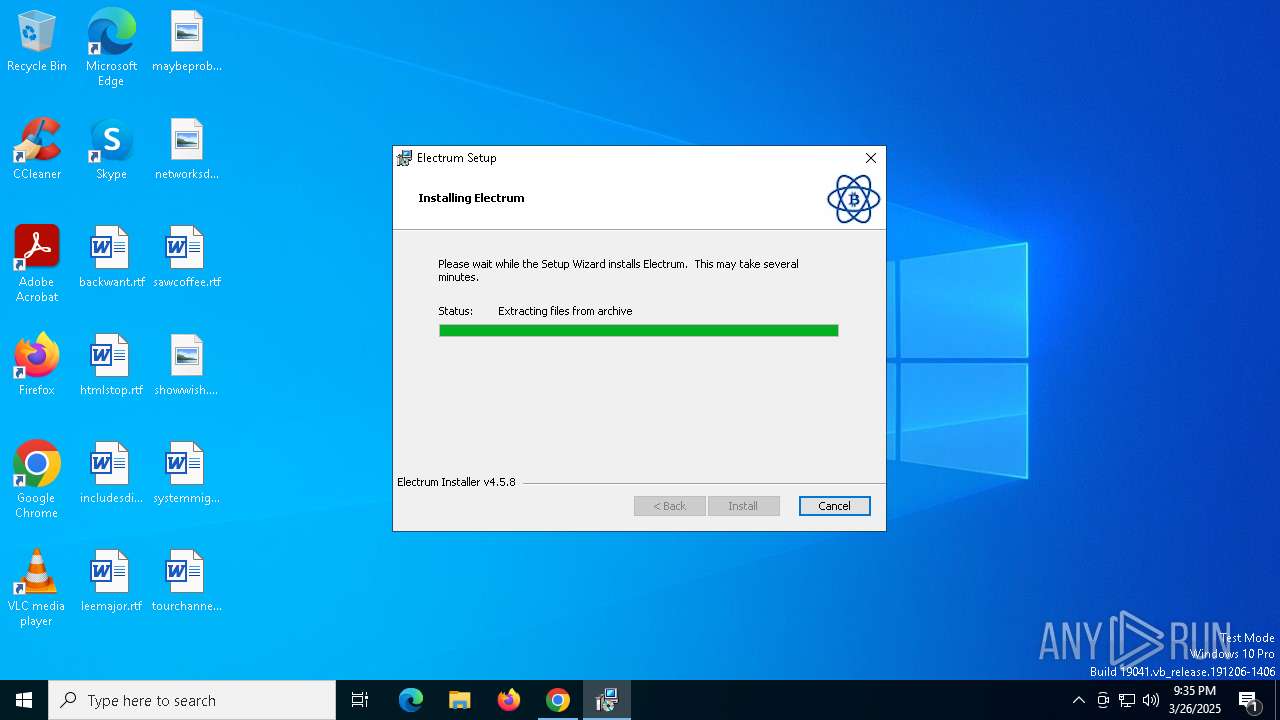
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2025, 21:33:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B277158D7349E73F61EDED6BE9BD25A3 |
| SHA1: | 155E744D6908E032E9293C65C806ED27E7280804 |
| SHA256: | D14084D1A12D2A20200937E744508988377FC42D92706514516B2AF64047CB8F |
| SSDEEP: | 3:N8zcSTXUzFgyGxQ1oKW0lA:2nbUSyGwtA |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 4652)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 8044)
SUSPICIOUS
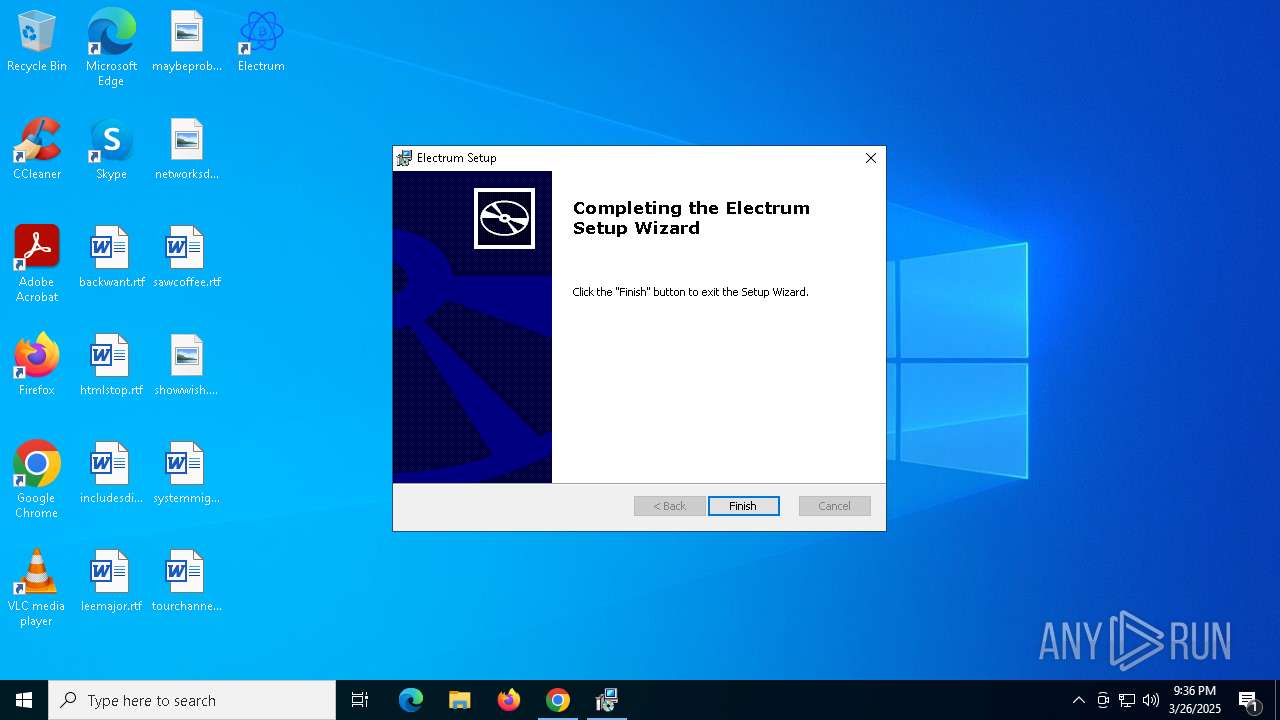
ADVANCEDINSTALLER mutex has been found
- electrum-4.5.8-setup.exe (PID: 3784)
Process drops legitimate windows executable
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
Reads security settings of Internet Explorer
- electrum-4.5.8-setup.exe (PID: 3784)
- ShellExperienceHost.exe (PID: 7996)
Executable content was dropped or overwritten
- electrum-4.5.8-setup.exe (PID: 3784)
Reads the Windows owner or organization settings
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
Executes as Windows Service
- VSSVC.exe (PID: 2960)
There is functionality for taking screenshot (YARA)
- electrum-4.5.8-setup.exe (PID: 3784)
Detects AdvancedInstaller (YARA)
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
- msiexec.exe (PID: 7988)
Process drops python dynamic module
- msiexec.exe (PID: 6872)
- electrum-4.5.8-setup.exe (PID: 3784)
The process drops C-runtime libraries
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 8044)
The process executes Powershell scripts
- msiexec.exe (PID: 8044)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 8044)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 8044)
Loads Python modules
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
Starts CMD.EXE for commands execution
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
Potential Corporate Privacy Violation
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
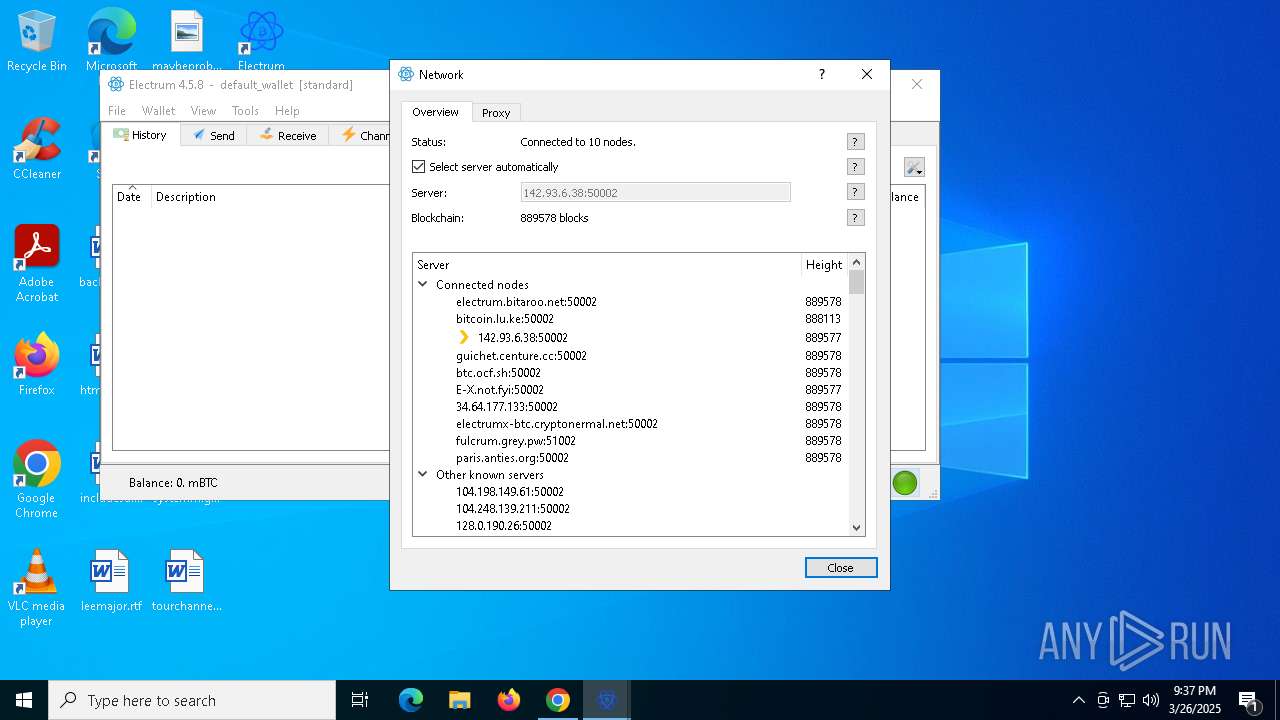
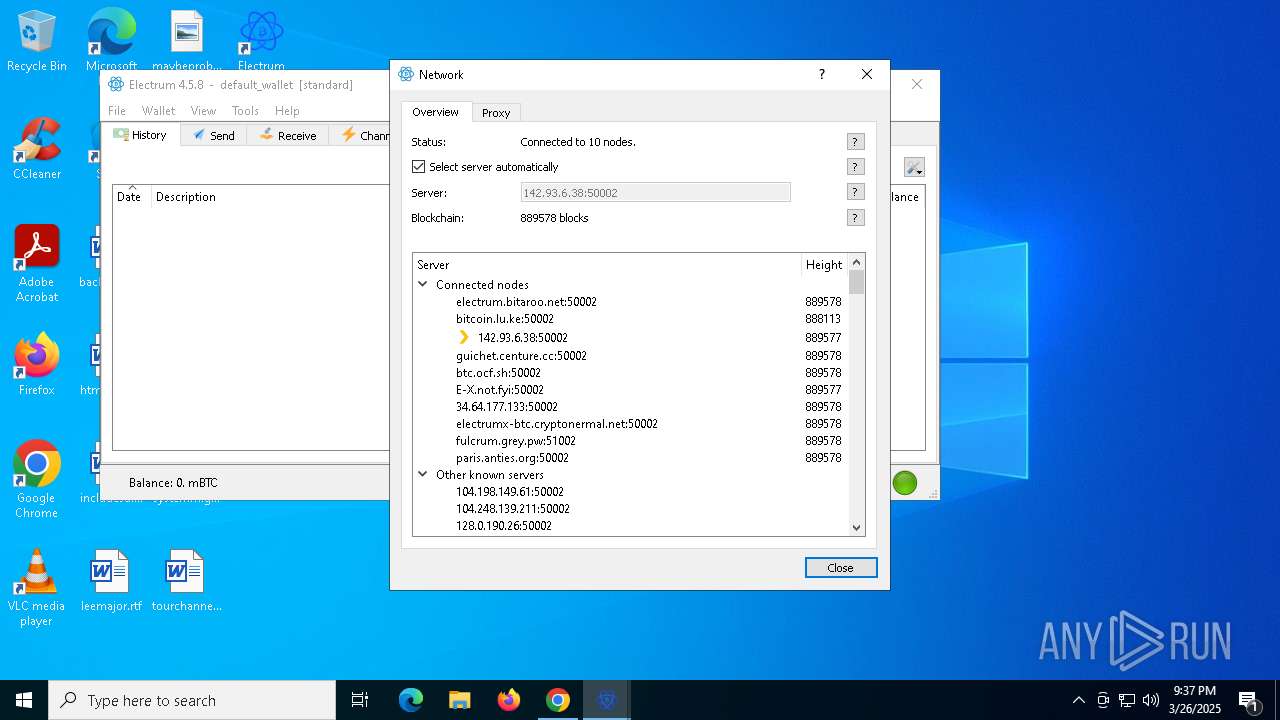
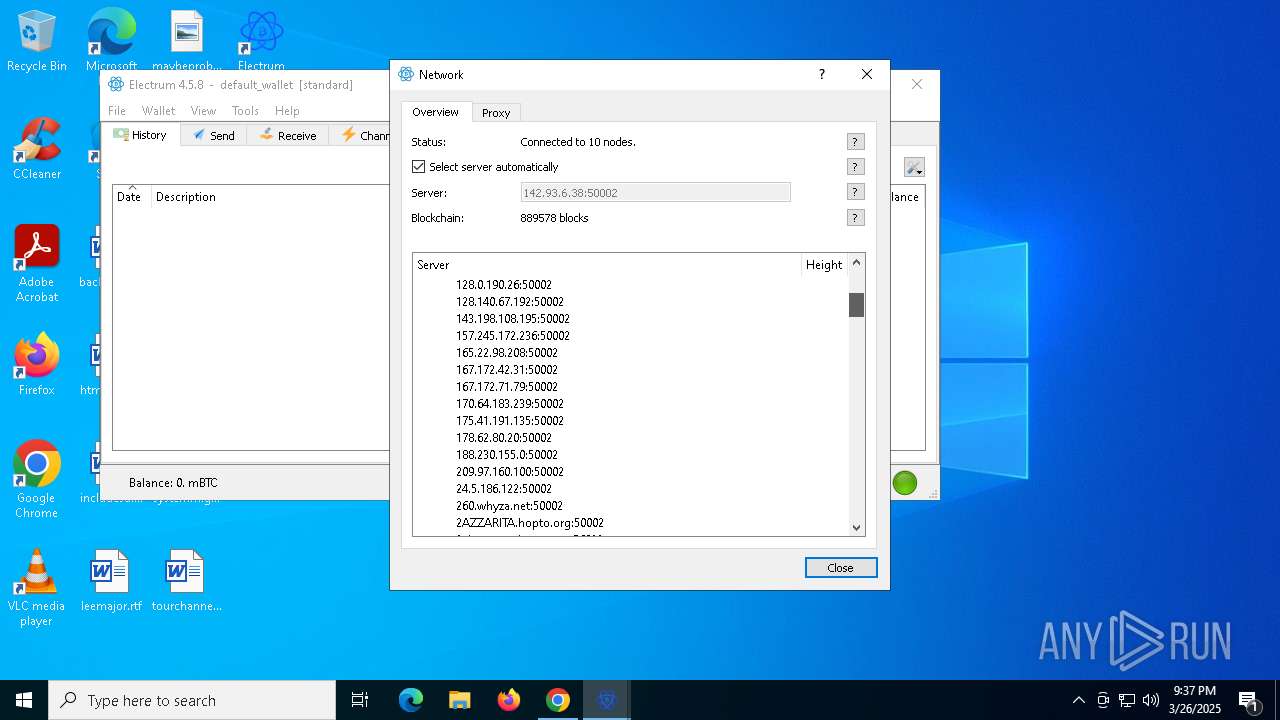
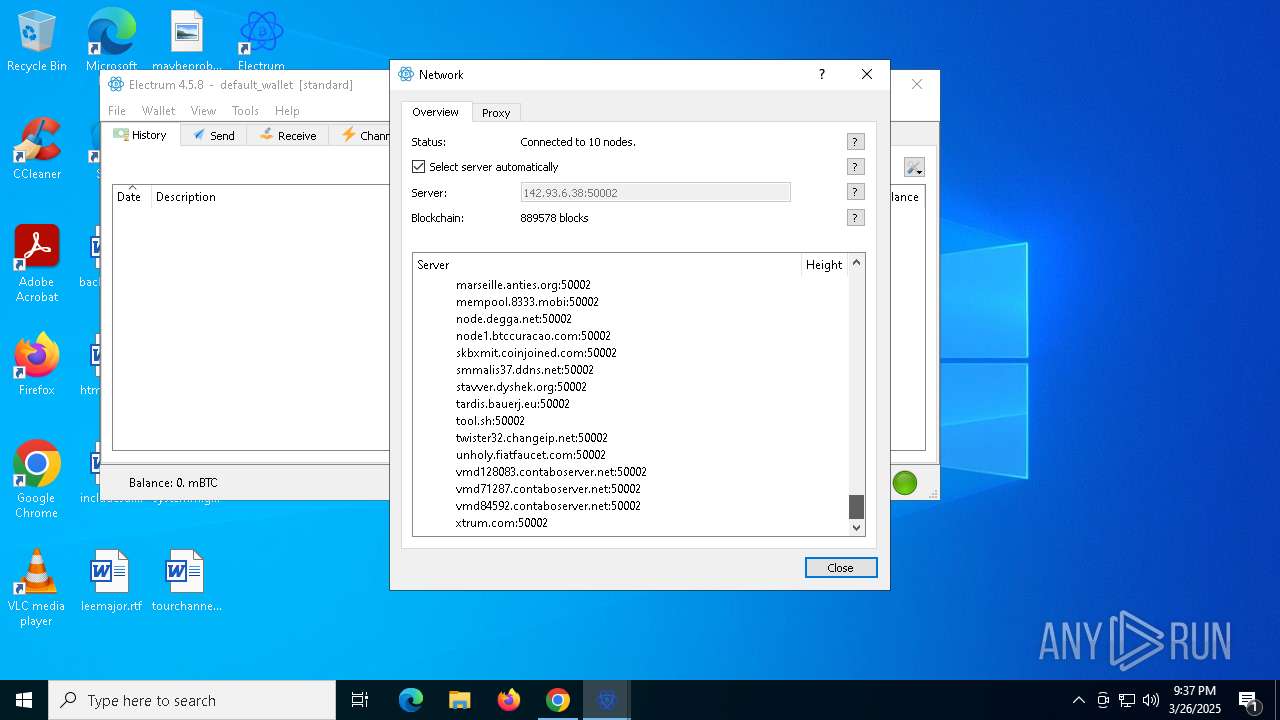
Connects to unusual port
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5548)
- BackgroundTransferHost.exe (PID: 6436)
- BackgroundTransferHost.exe (PID: 4068)
- BackgroundTransferHost.exe (PID: 6228)
- BackgroundTransferHost.exe (PID: 8028)
- msiexec.exe (PID: 7988)
- powershell.exe (PID: 4652)
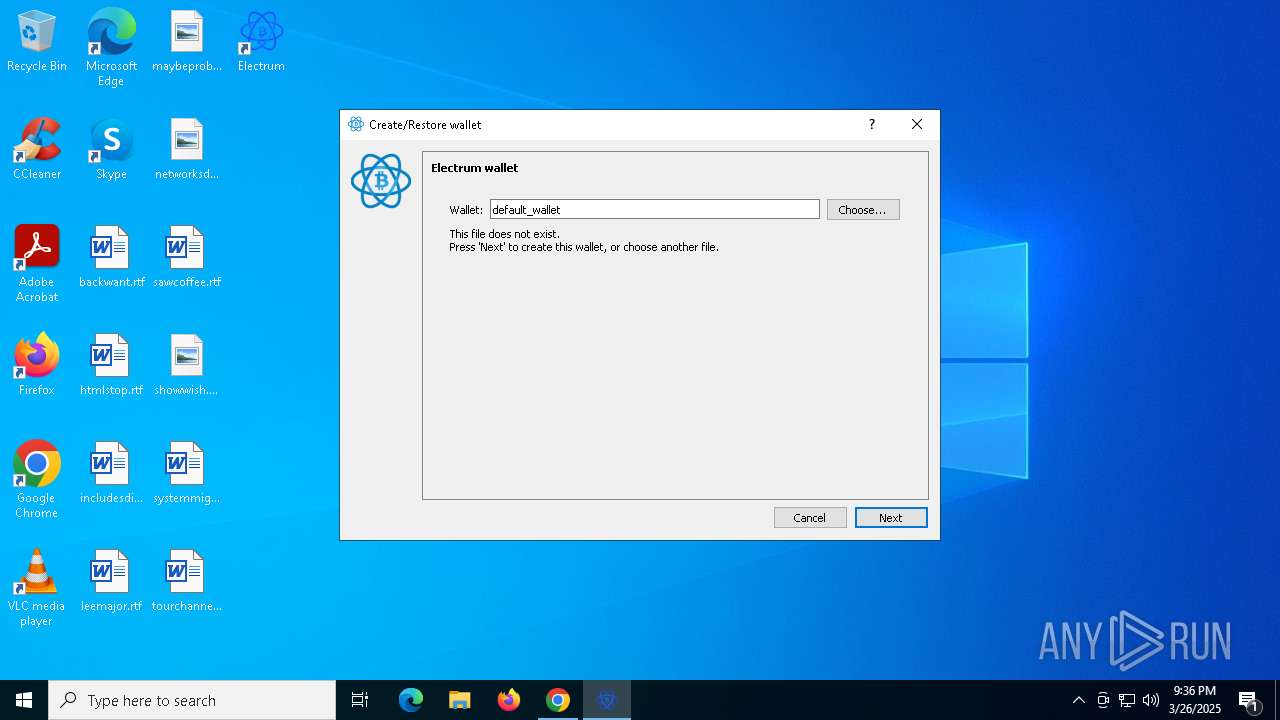
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5548)
- electrum-4.5.8-setup.exe (PID: 3784)
- electrum-4.5.8.exe (PID: 5260)
- electrum-4.5.8.exe (PID: 7972)
Executable content was dropped or overwritten
- chrome.exe (PID: 6620)
- msiexec.exe (PID: 7988)
- msiexec.exe (PID: 6872)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5548)
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 7988)
- msiexec.exe (PID: 6872)
- slui.exe (PID: 7812)
- slui.exe (PID: 1196)
- powershell.exe (PID: 4652)
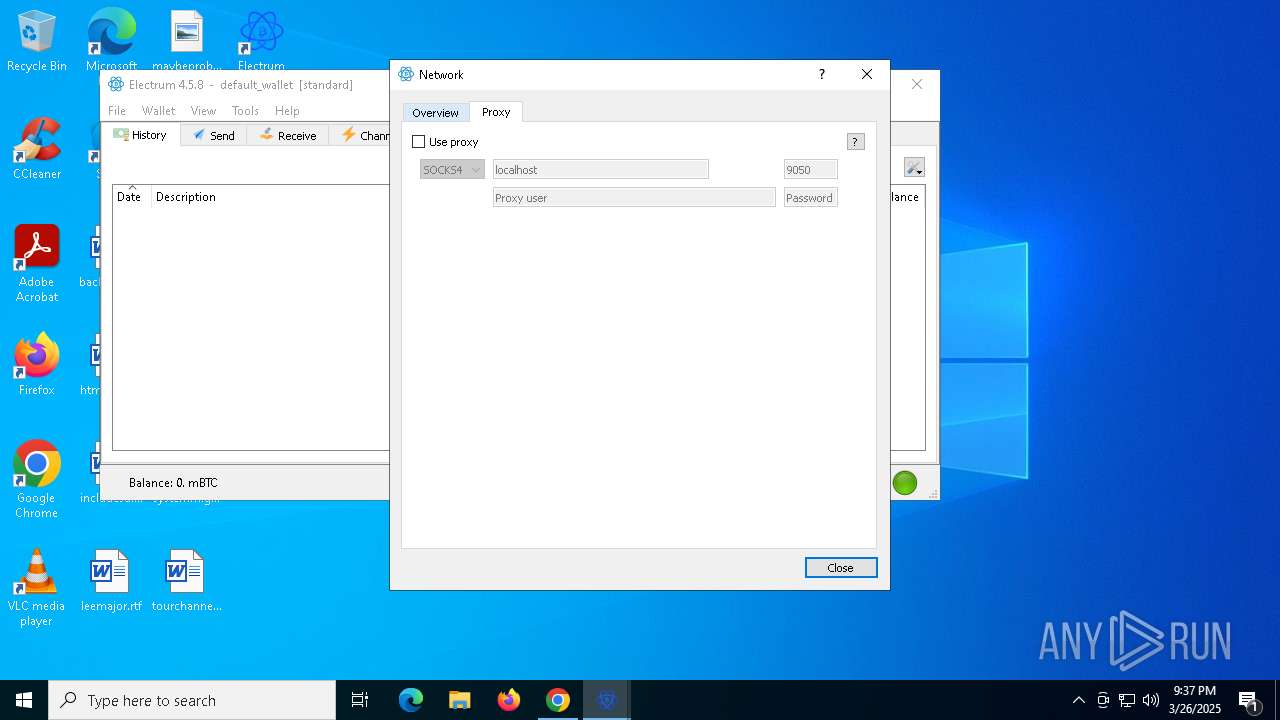
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5548)
- slui.exe (PID: 1196)
- powershell.exe (PID: 4652)
Autorun file from Downloads
- chrome.exe (PID: 7876)
Reads the computer name
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
- msiexec.exe (PID: 2096)
- msiexec.exe (PID: 7584)
- ShellExperienceHost.exe (PID: 7996)
- msiexec.exe (PID: 8044)
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
Checks supported languages
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
- msiexec.exe (PID: 2096)
- msiexec.exe (PID: 7584)
- ShellExperienceHost.exe (PID: 7996)
- msiexec.exe (PID: 8044)
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
Application launched itself
- chrome.exe (PID: 6620)
Reads Environment values
- msiexec.exe (PID: 2096)
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 7584)
- msiexec.exe (PID: 8044)
Reads the machine GUID from the registry
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
The sample compiled with english language support
- msiexec.exe (PID: 7988)
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 6872)
Create files in a temporary directory
- electrum-4.5.8-setup.exe (PID: 3784)
- msiexec.exe (PID: 8044)
- powershell.exe (PID: 4652)
Manages system restore points
- SrTasks.exe (PID: 3888)
Creates a software uninstall entry
- msiexec.exe (PID: 6872)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4652)
Disables trace logs
- powershell.exe (PID: 4652)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 4652)
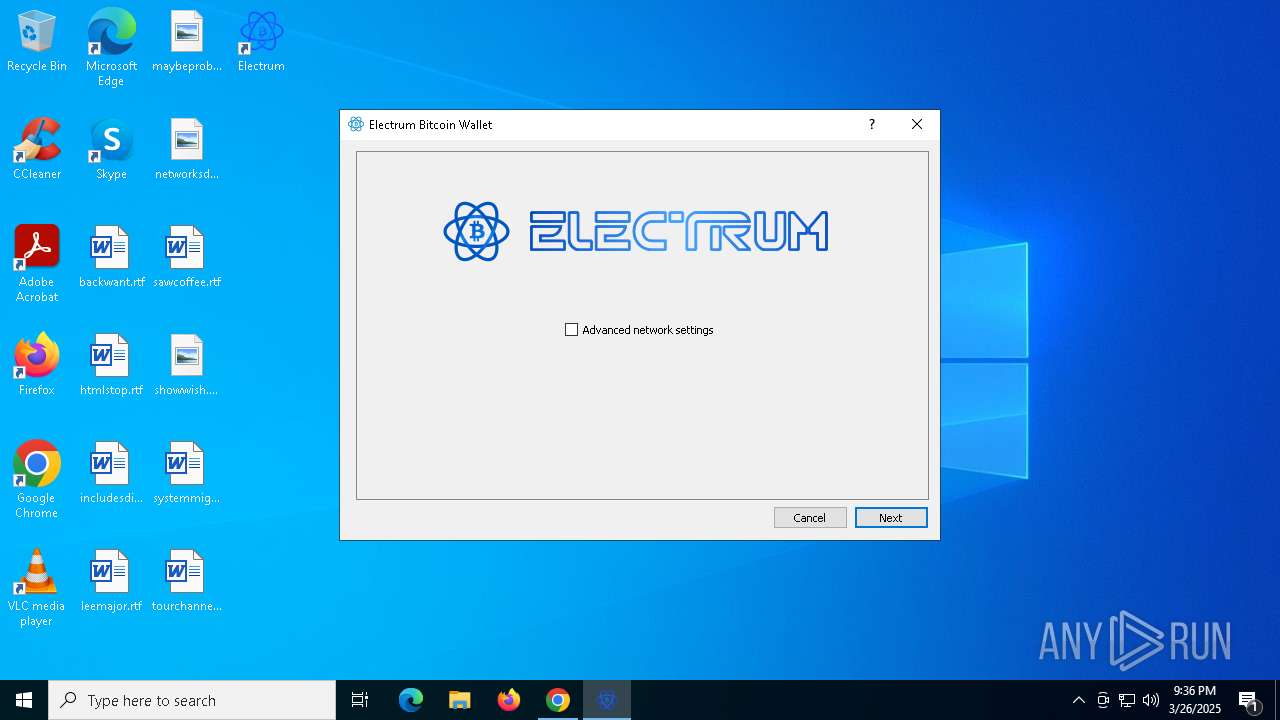
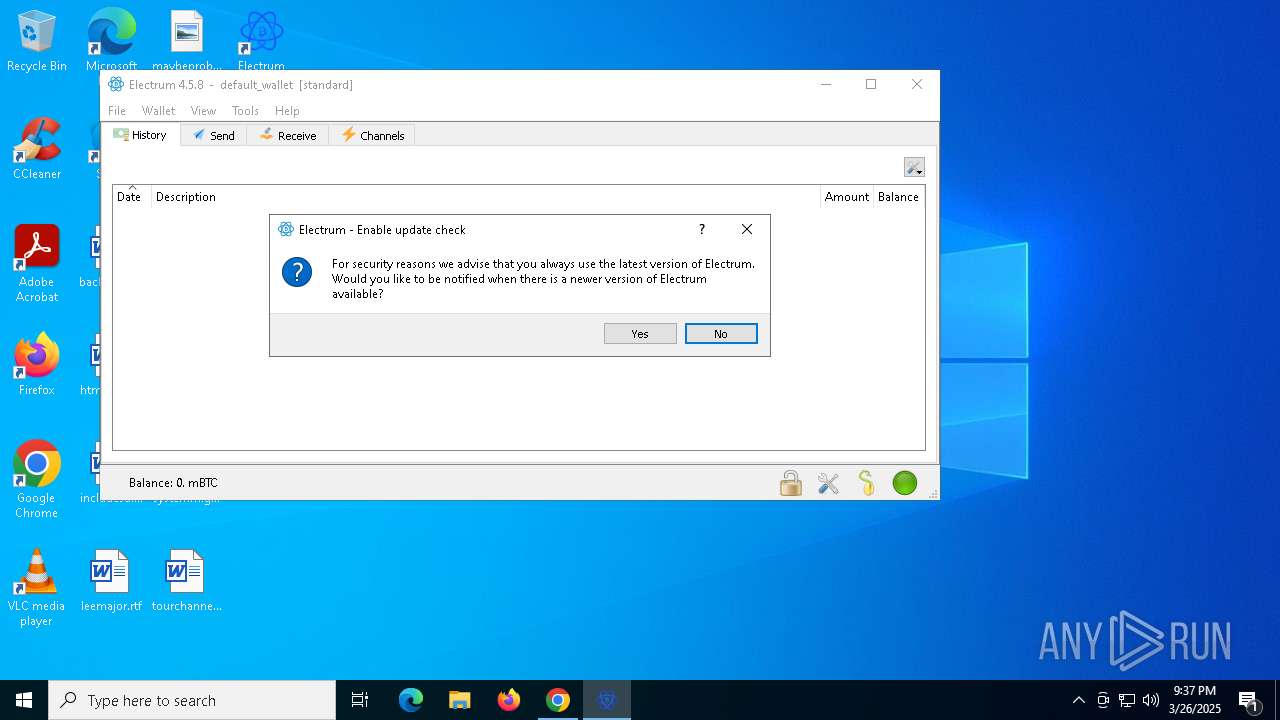
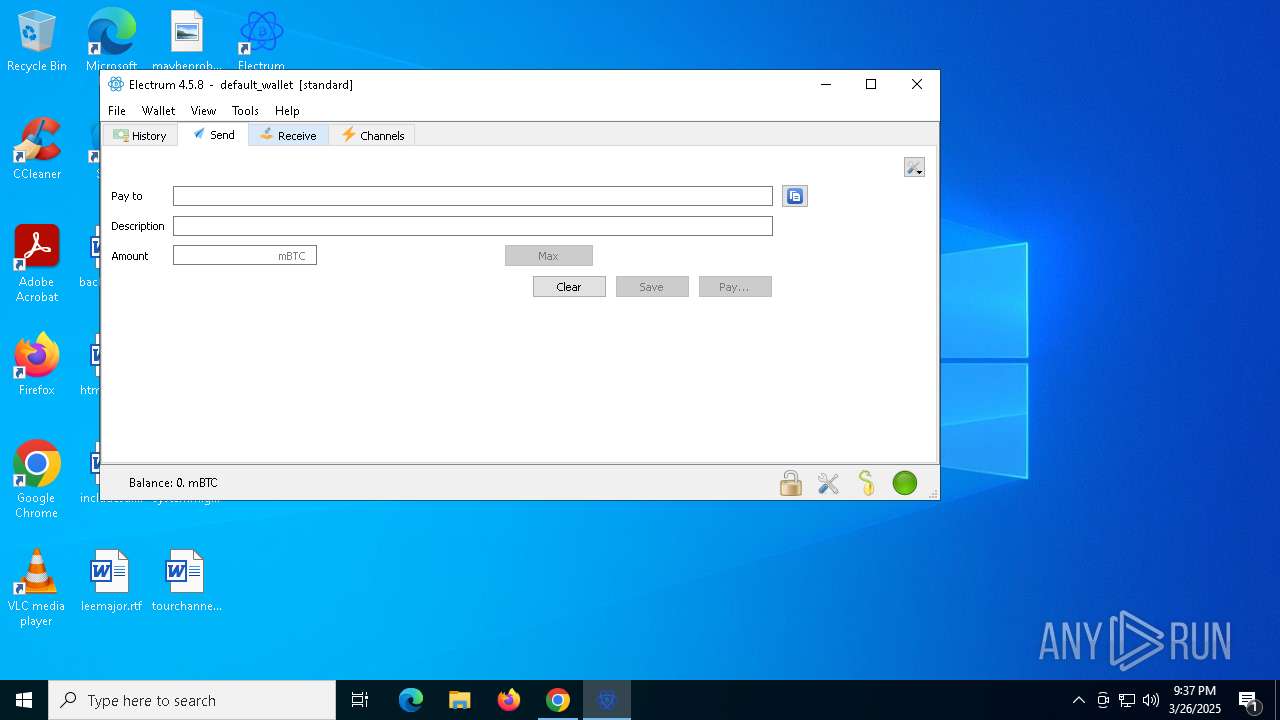
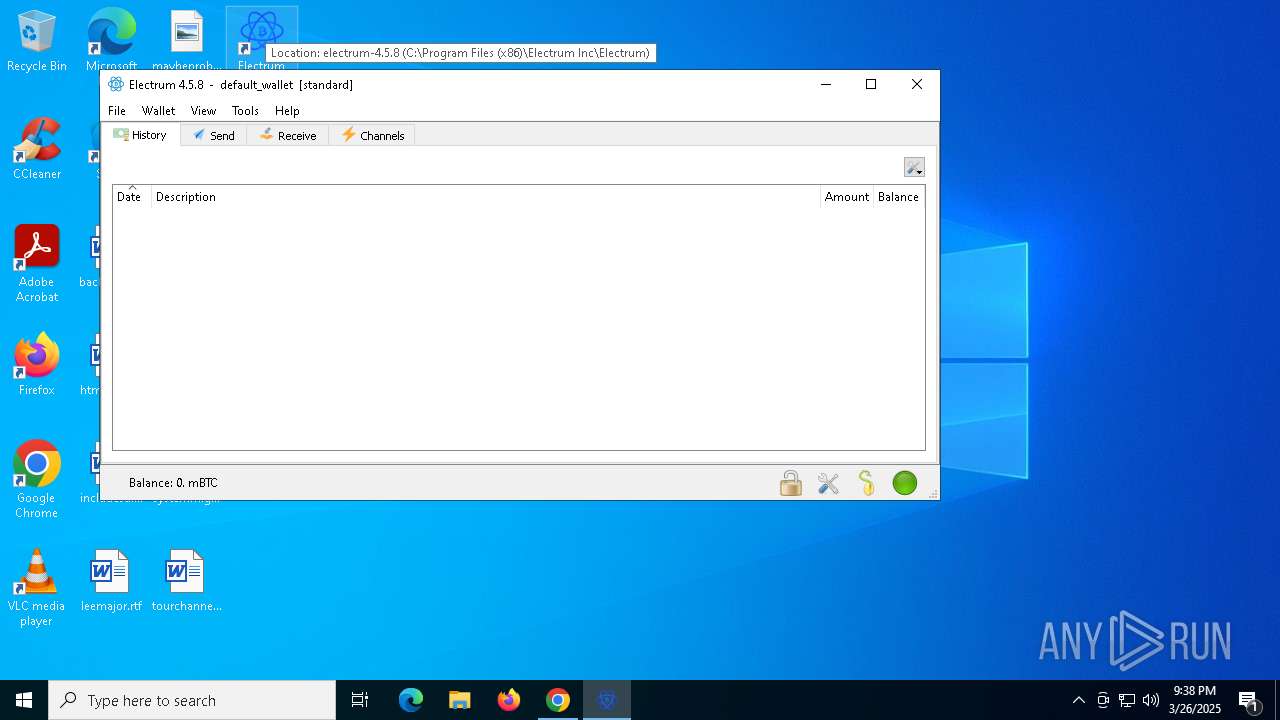
Manual execution by a user
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
Checks operating system version
- electrum-4.5.8.exe (PID: 7972)
- electrum-4.5.8.exe (PID: 5260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
53
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\SysWOW64\cmd.exe | — | electrum-4.5.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | C:\WINDOWS\system32\cmd.exe /c fsutil sparse setflag "C:\Users\admin\AppData\Roaming\Electrum\blockchain_headers" 1 | C:\Windows\SysWOW64\cmd.exe | — | electrum-4.5.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6112 --field-trial-handle=1988,i,13255500270493586866,17729285769535627053,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3348 --field-trial-handle=1988,i,13255500270493586866,17729285769535627053,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2064 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3612 --field-trial-handle=1988,i,13255500270493586866,17729285769535627053,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2096 | C:\Windows\syswow64\MsiExec.exe -Embedding 1ED188C60B37F0645F1E371E7C6E1C9E C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2960 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 137
Read events
33 408
Write events
703
Delete events
26
Modification events
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6436) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6436) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6436) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5548) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5548) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
210
Suspicious files
532
Text files
1 342
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c42c.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
121
DNS requests
86
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7548 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5548 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5324 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6676 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrljlfa5ixcx3xxfxlxc7wb5vja_1259/efniojlnjndmcbiieegkicadnoecjjef_1259_all_mqpwdvyz2xzad3i2vp4bsi6fbe.crx3 | unknown | — | — | whitelisted |
6676 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
6676 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrljlfa5ixcx3xxfxlxc7wb5vja_1259/efniojlnjndmcbiieegkicadnoecjjef_1259_all_mqpwdvyz2xzad3i2vp4bsi6fbe.crx3 | unknown | — | — | whitelisted |
6676 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrljlfa5ixcx3xxfxlxc7wb5vja_1259/efniojlnjndmcbiieegkicadnoecjjef_1259_all_mqpwdvyz2xzad3i2vp4bsi6fbe.crx3 | unknown | — | — | whitelisted |
6676 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrljlfa5ixcx3xxfxlxc7wb5vja_1259/efniojlnjndmcbiieegkicadnoecjjef_1259_all_mqpwdvyz2xzad3i2vp4bsi6fbe.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6620 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7268 | chrome.exe | 138.199.37.231:443 | b897b98721.b-cdn.net | Datacamp Limited | DE | whitelisted |
7268 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.172.255.216:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
b897b98721.b-cdn.net |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
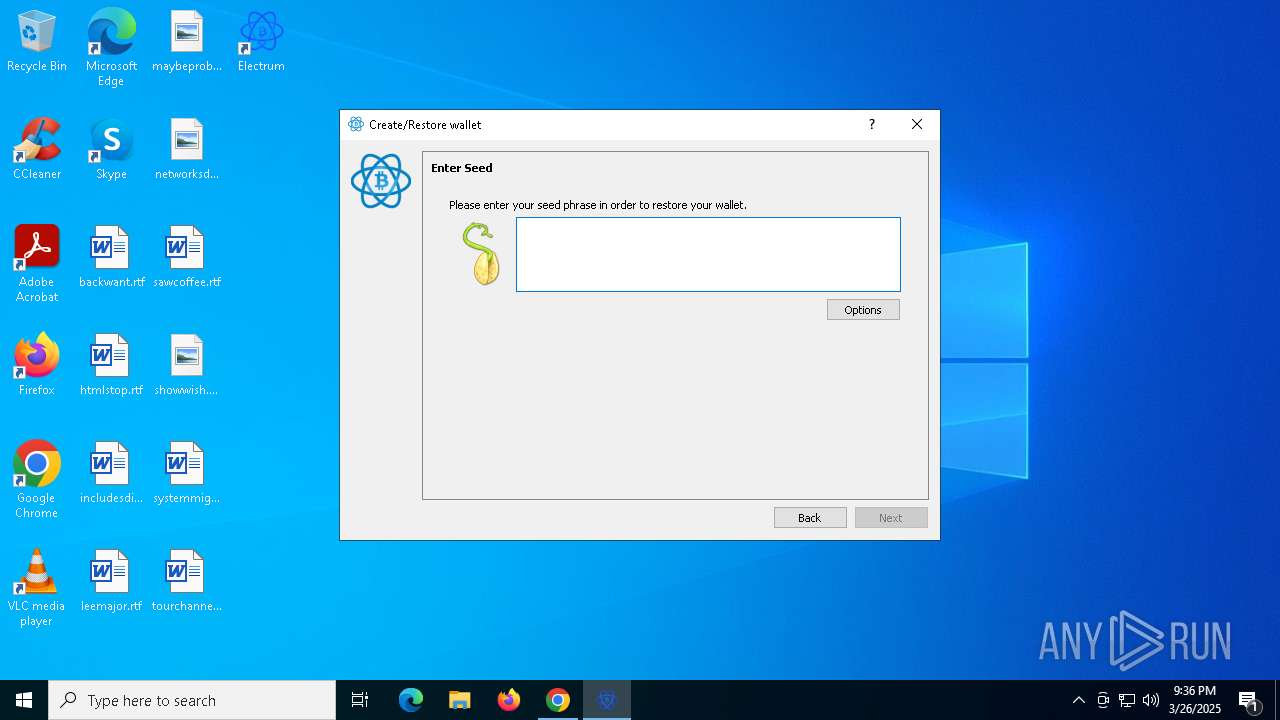
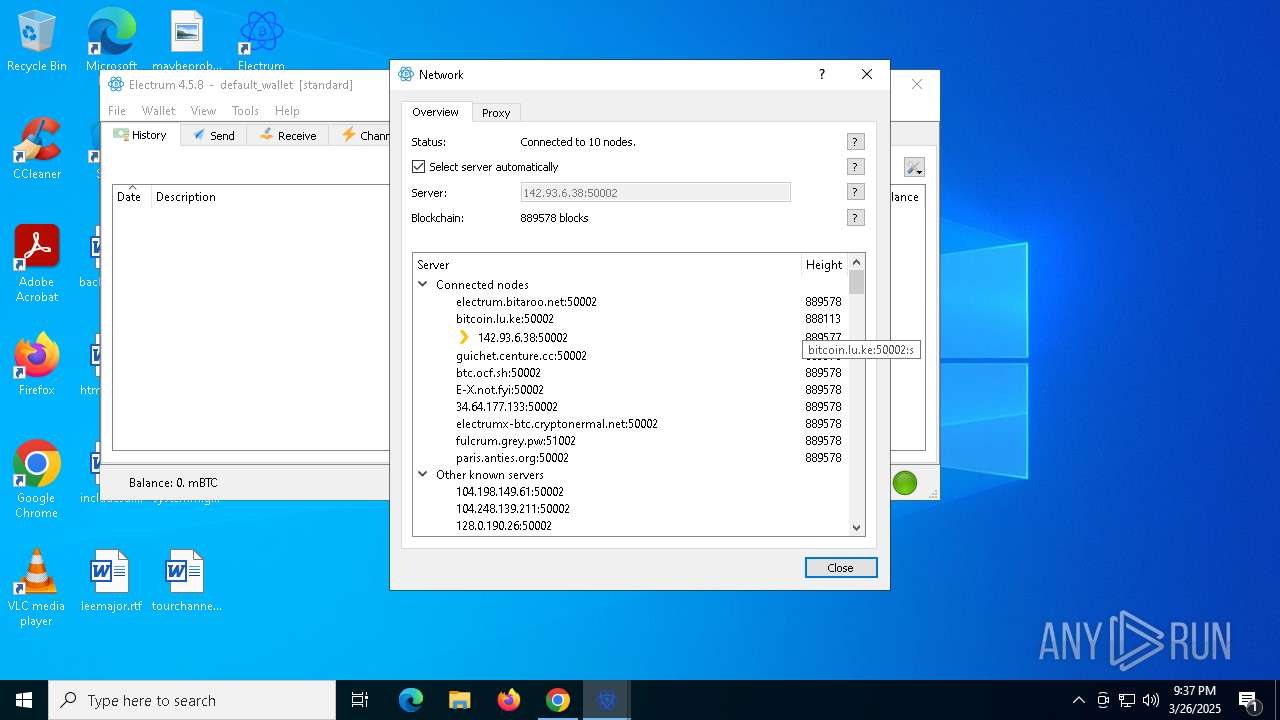
7972 | electrum-4.5.8.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
7972 | electrum-4.5.8.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
7972 | electrum-4.5.8.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
7972 | electrum-4.5.8.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.hopto .org |
7972 | electrum-4.5.8.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.hopto .org |
7972 | electrum-4.5.8.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
7972 | electrum-4.5.8.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 151 |
7972 | electrum-4.5.8.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
7972 | electrum-4.5.8.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
7972 | electrum-4.5.8.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |