| File name: | C49RG9xSS.exe |
| Full analysis: | https://app.any.run/tasks/7de07bc4-5dcf-461d-9204-b0bc4229d7b1 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2020, 00:23:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 140D164878C160B5D8D64095BA0DA289 |
| SHA1: | BDCB33C3BCF0EF089ADB0E86E46285DCF5FB9D8B |
| SHA256: | D13FCBFC7CF4A356FA0E76C6E817E4E25C6422293F767941A9CCB49E61BA57C8 |
| SSDEEP: | 196608:XzOcv7TBNKEsYaRccf/mster2BCoUFWt2X9CkbH5zq3HIR:XKC7Fo3Y+vmQei3KWt2X9hbZzbR |
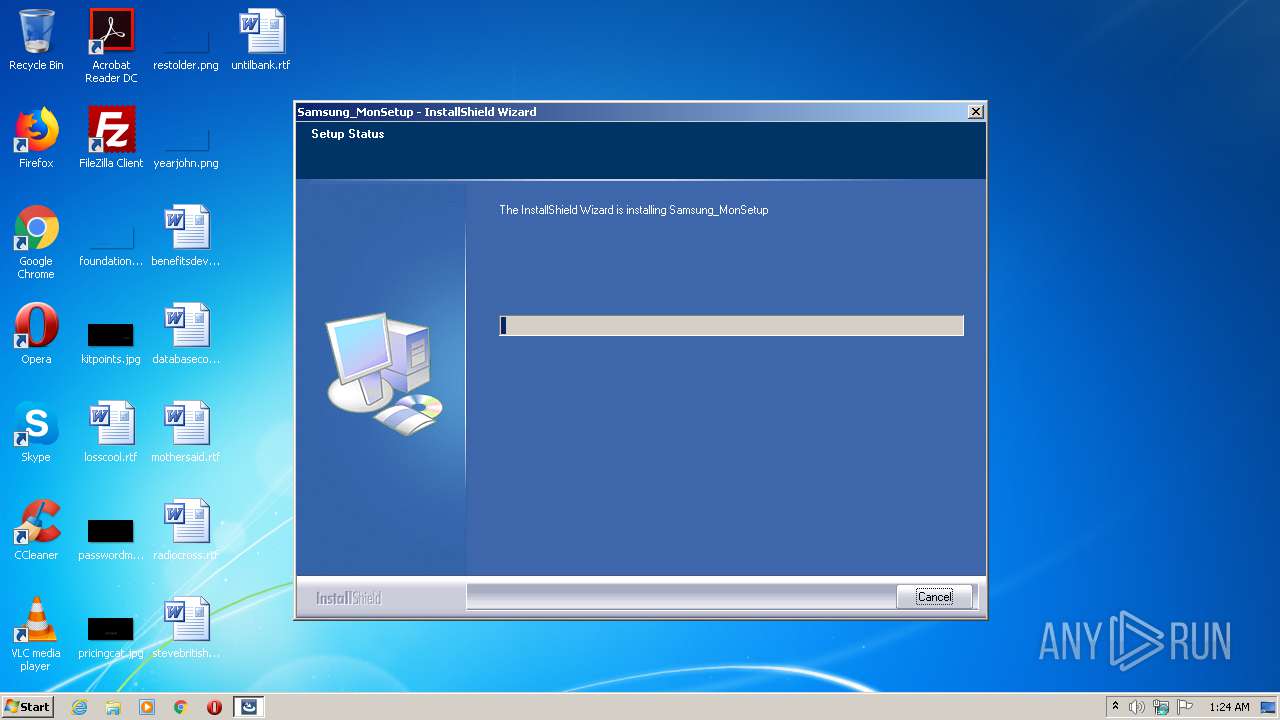
MALICIOUS
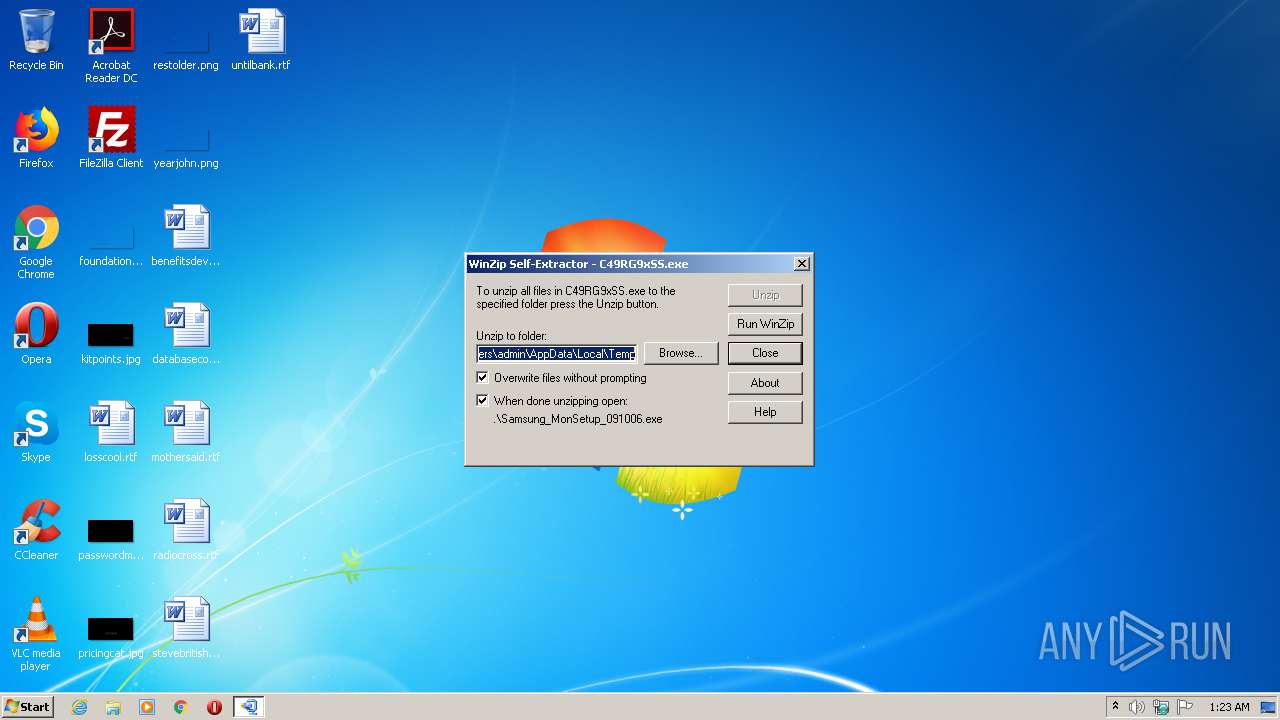
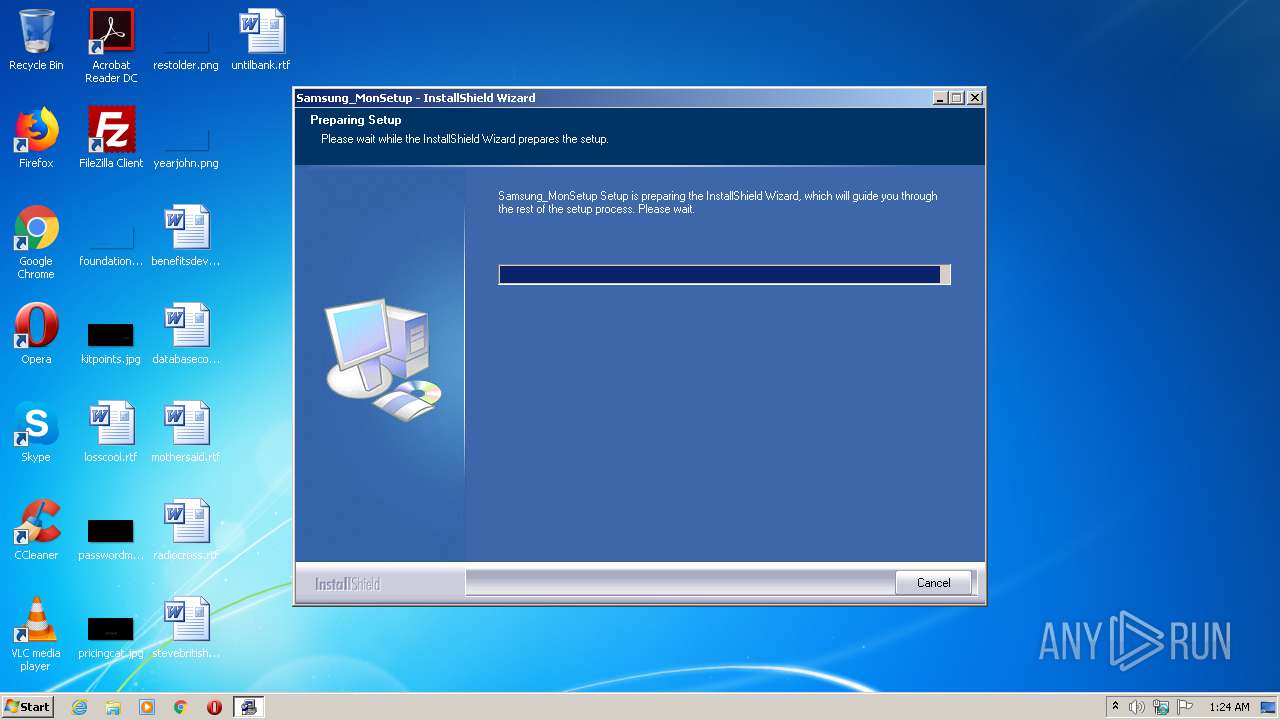
Application was dropped or rewritten from another process
- Samsung_MonSetup_091006.exe (PID: 324)
- Samsung_MonSetup_091006.exe (PID: 2768)
- install.exe (PID: 2140)
- vcredist_x86.exe (PID: 2816)
- MonSetup.exe (PID: 3944)
Loads dropped or rewritten executable
- Samsung_MonSetup_091006.exe (PID: 2768)
- install.exe (PID: 2140)
Changes settings of System certificates
- MonSetup.exe (PID: 3944)
- msiexec.exe (PID: 2460)
SUSPICIOUS
Executable content was dropped or overwritten
- C49RG9xSS.exe (PID: 2476)
- C49RG9xSS.exe (PID: 2872)
- vcredist_x86.exe (PID: 2816)
- Samsung_MonSetup_091006.exe (PID: 2768)
- msiexec.exe (PID: 2460)
Creates files in the user directory
- Samsung_MonSetup_091006.exe (PID: 2768)
Executed as Windows Service
- vssvc.exe (PID: 1728)
Executed via COM
- DllHost.exe (PID: 2684)
Starts itself from another location
- C49RG9xSS.exe (PID: 2476)
Creates files in the program directory
- Samsung_MonSetup_091006.exe (PID: 2768)
Searches for installed software
- Samsung_MonSetup_091006.exe (PID: 2768)
Creates a software uninstall entry
- Samsung_MonSetup_091006.exe (PID: 2768)
Adds / modifies Windows certificates
- MonSetup.exe (PID: 3944)
- msiexec.exe (PID: 2460)
Creates files in the Windows directory
- msiexec.exe (PID: 2460)
Removes files from Windows directory
- msiexec.exe (PID: 2460)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 1728)
Reads settings of System Certificates
- msiexec.exe (PID: 2460)
Creates a software uninstall entry
- msiexec.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (30.7) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (22.2) |
| .exe | | | Win64 Executable (generic) (19.7) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (16.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:05 17:27:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 159744 |
| InitializedDataSize: | 143360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1669f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Aug-2016 15:27:39 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Aug-2016 15:27:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002601E | 0x00027000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56993 |
.rdata | 0x00028000 | 0x00007134 | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.31041 |
.data | 0x00030000 | 0x0001079C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23888 |
.rsrc | 0x00041000 | 0x00009CD8 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.37636 |
_winzip_ | 0x0004B000 | 0x007E1000 | 0x007E1000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99977 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04423 | 1492 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.03621 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.14459 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 5.56342 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.99214 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.69605 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.83382 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 6.01045 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 4.68735 | 1128 | UNKNOWN | English - United States | RT_ICON |
63 | 3.18826 | 764 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll (delay-loaded) |
Total processes
48
Monitored processes
10
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Users\admin\AppData\Local\Temp\Samsung_MonSetup_091006.exe" | C:\Users\admin\AppData\Local\Temp\Samsung_MonSetup_091006.exe | — | C49RG9xSS.exe | |||||||||||
User: admin Company: Macrovision Corporation Integrity Level: MEDIUM Description: Setup.exe Exit code: 3221226540 Version: 12.0.49974 Modules
| |||||||||||||||
| 1728 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | c:\b37b7890876487b2d128c17e\.\install.exe "/q:a" | c:\b37b7890876487b2d128c17e\install.exe | — | vcredist_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: External Installer Exit code: 0 Version: 9.0.21022.8 built by: RTM Modules
| |||||||||||||||
| 2460 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | "C:\Users\admin\AppData\Local\Temp\C49RG9xSS.exe" | C:\Users\admin\AppData\Local\Temp\C49RG9xSS.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2684 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\Samsung_MonSetup_091006.exe" | C:\Users\admin\AppData\Local\Temp\Samsung_MonSetup_091006.exe | C49RG9xSS.exe | ||||||||||||
User: admin Company: Macrovision Corporation Integrity Level: HIGH Description: Setup.exe Exit code: 0 Version: 12.0.49974 Modules
| |||||||||||||||
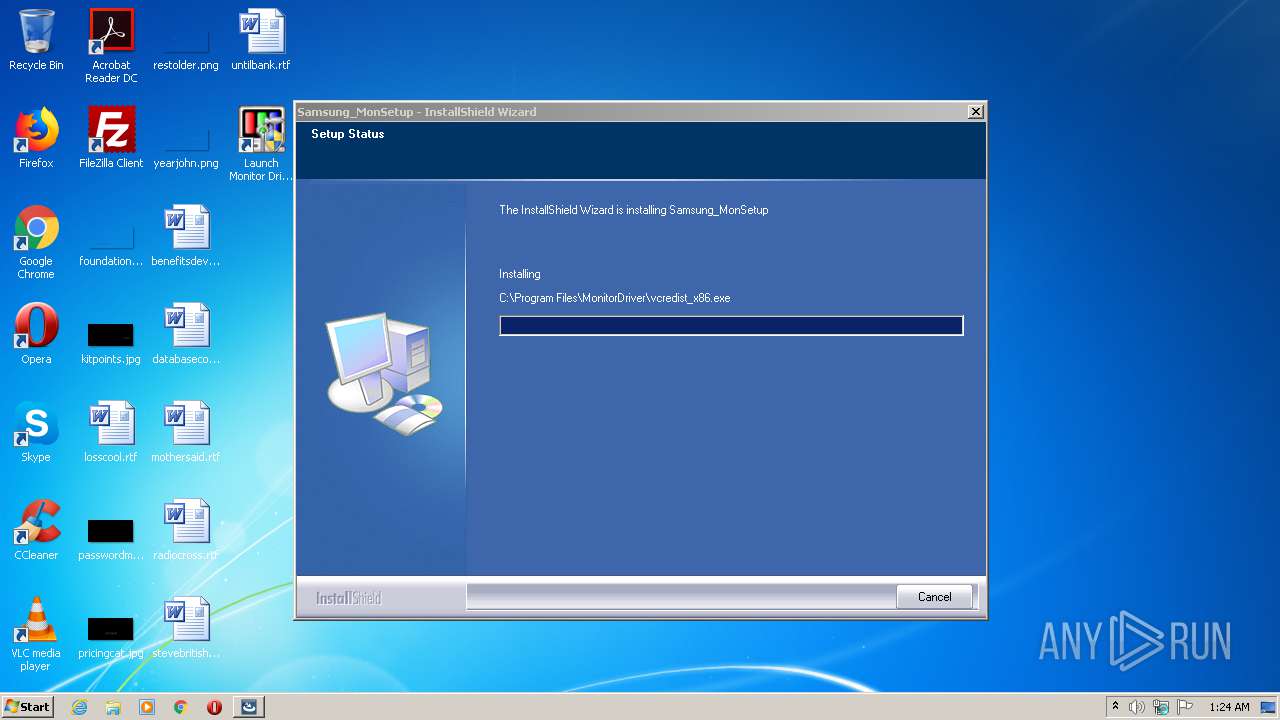
| 2816 | "C:\Program Files\MonitorDriver\vcredist_x86.exe" "/q:a" | C:\Program Files\MonitorDriver\vcredist_x86.exe | Samsung_MonSetup_091006.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2008 Redistributable Setup Exit code: 0 Version: 9.0.21022.08 Modules
| |||||||||||||||
| 2872 | run=1 shortcut="C:\Users\admin\AppData\Local\Temp\C49RG9xSS.exe" | C:\Users\admin\AppData\Local\Temp\108251\C49RG9xSS.exe | C49RG9xSS.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
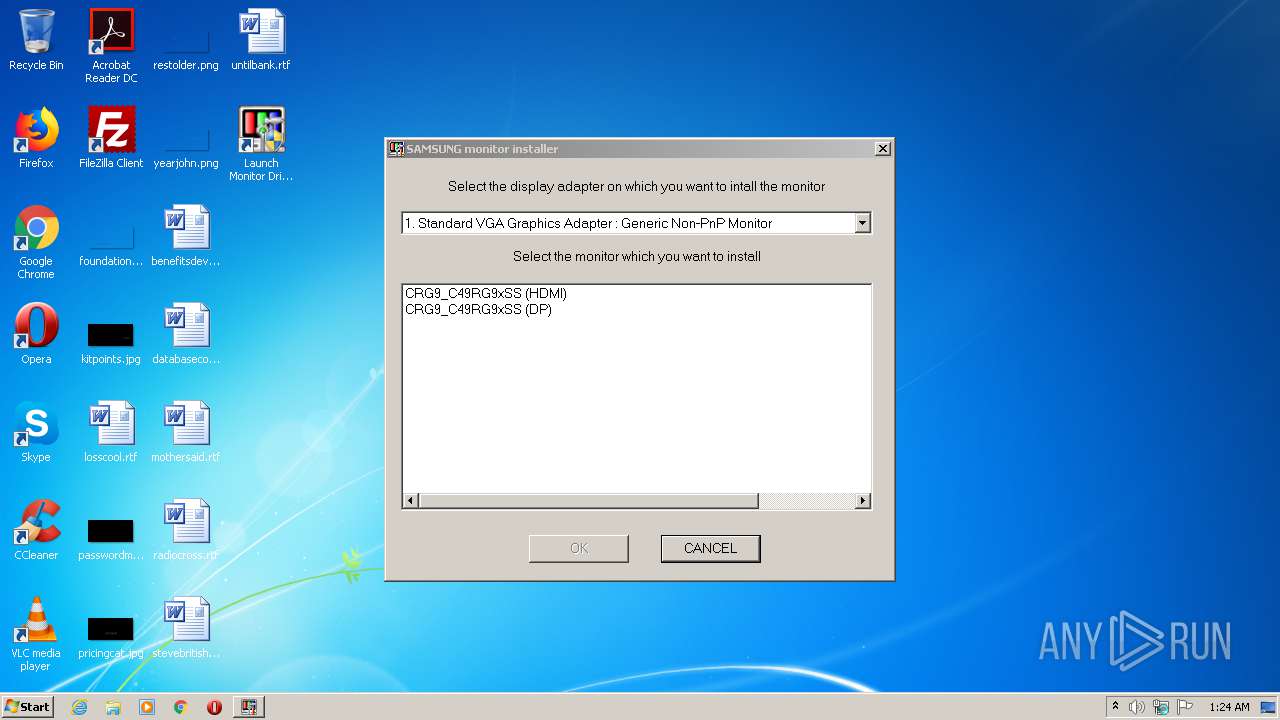
| 3944 | "C:\Program Files\MonitorDriver\MonSetup.exe" | C:\Program Files\MonitorDriver\MonSetup.exe | — | Samsung_MonSetup_091006.exe | |||||||||||
User: admin Company: Samsung Electronics Integrity Level: HIGH Description: MonSetup32 Exit code: 0 Version: 2, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 535
Read events
959
Write events
1 564
Delete events
12
Modification events
| (PID) Process: | (2872) C49RG9xSS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2872) C49RG9xSS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2684) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000AA43CFC40645D6017C0A00002C0D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2684) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 38 | |||
| (PID) Process: | (2684) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000005E08D4C40645D6017C0A00002C0D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2684) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B86AD6C40645D6017C0A0000600F0000E8030000010000000000000000000000798602FEC4C30B48BD6B914C774057490000000000000000 | |||
| (PID) Process: | (1728) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B0BBA6C40645D601C0060000F8090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1728) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B0BBA6C40645D601C00600003C0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1728) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B0BBA6C40645D601C00600001C0C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1728) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B0BBA6C40645D601C00600002C0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
59
Suspicious files
21
Text files
73
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | C49RG9xSS.exe | C:\Users\admin\AppData\Local\Temp\C49RG9xSS.inf | text | |
MD5:1BCE99BD9B452C55BA05DD9E815F6E5F | SHA256:96A03EB9507219AB8A920E2F200C8C0990A07C3D4B13537B069B70DE93213A55 | |||
| 2768 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\c0220f2d3cd6ed06f2a16534e989baee_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:— | SHA256:— | |||
| 2768 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{4A747939-4C21-42FF-AA90-34D70751958E}\{8EA79DBF-D637-448A-89D6-410A087A4493}\setu8bd7.rra | — | |
MD5:— | SHA256:— | |||
| 2872 | C49RG9xSS.exe | C:\Users\admin\AppData\Local\Temp\C49RG9xSS.icm | icc | |
MD5:451891E7F6B7EEB029B60212225C54EF | SHA256:CB449B7F780BDD2086F9263706F4694516611AB0AEE8DACFDF9BF375A1269014 | |||
| 2768 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{4A747939-4C21-42FF-AA90-34D70751958E}\{8EA79DBF-D637-448A-89D6-410A087A4493}\lice8bd7.rra | — | |
MD5:— | SHA256:— | |||
| 2768 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{ACA73998-E1A1-472D-B2F8-DA1F4805E4F1}\_ispackdel.ini | text | |
MD5:— | SHA256:— | |||
| 2768 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{4A747939-4C21-42FF-AA90-34D70751958E}\{8EA79DBF-D637-448A-89D6-410A087A4493}\_ISU8bd7.rra | — | |
MD5:— | SHA256:— | |||
| 2768 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{ACA73998-E1A1-472D-B2F8-DA1F4805E4F1}\Disk1\setup.exe | executable | |
MD5:2D111130C27C36C91EA57D0E88B68BD6 | SHA256:C793C2BBC622872E281C472A1C50CAC2DD567B3A40C13094C44982FB56DF0CD8 | |||
| 2768 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{4A747939-4C21-42FF-AA90-34D70751958E}\core8be6.rra | — | |
MD5:— | SHA256:— | |||
| 2872 | C49RG9xSS.exe | C:\Users\admin\AppData\Local\Temp\Samsung_MonSetup_091006.exe | executable | |
MD5:0924C3DFC4368C3DF1B8B42598D8D7AF | SHA256:0580B3FC29D2C76D2B758081CB288E28185D4CF95A7F7E49A6E75B175ABB5274 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report