| File name: | challenge_1.bat |
| Full analysis: | https://app.any.run/tasks/27b3bb0e-4a26-440c-85b5-c343930140b3 |
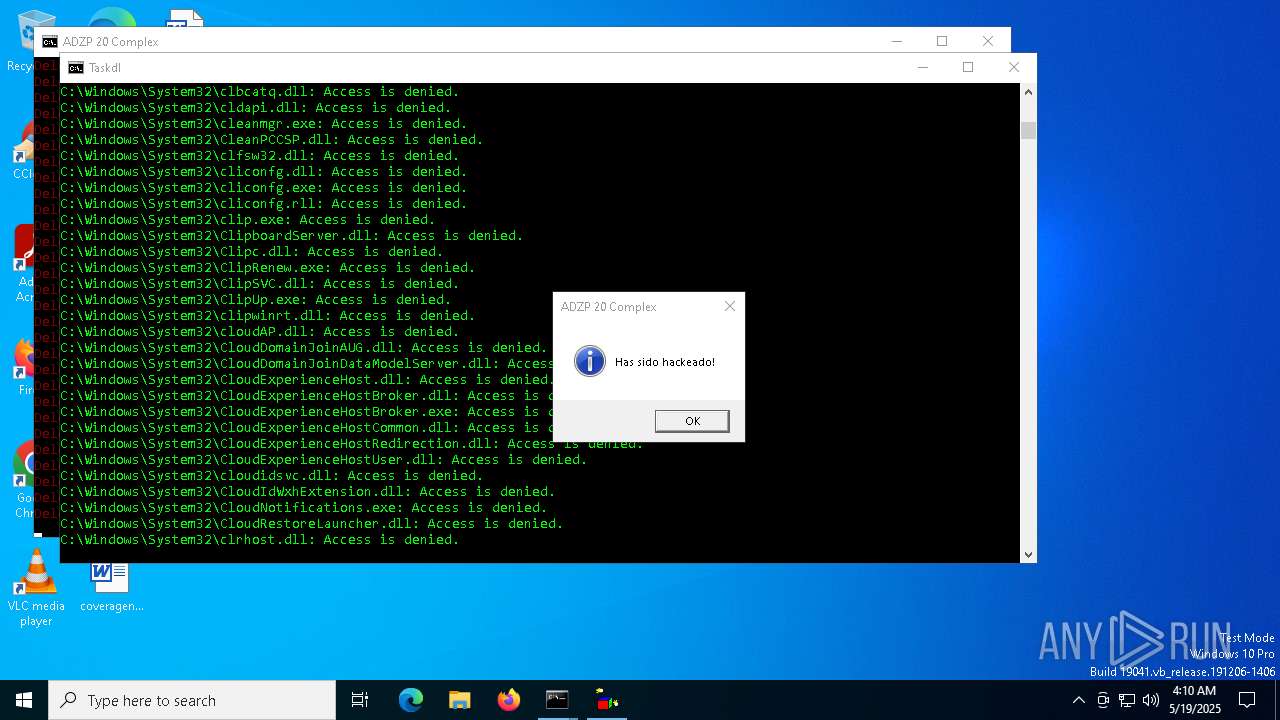
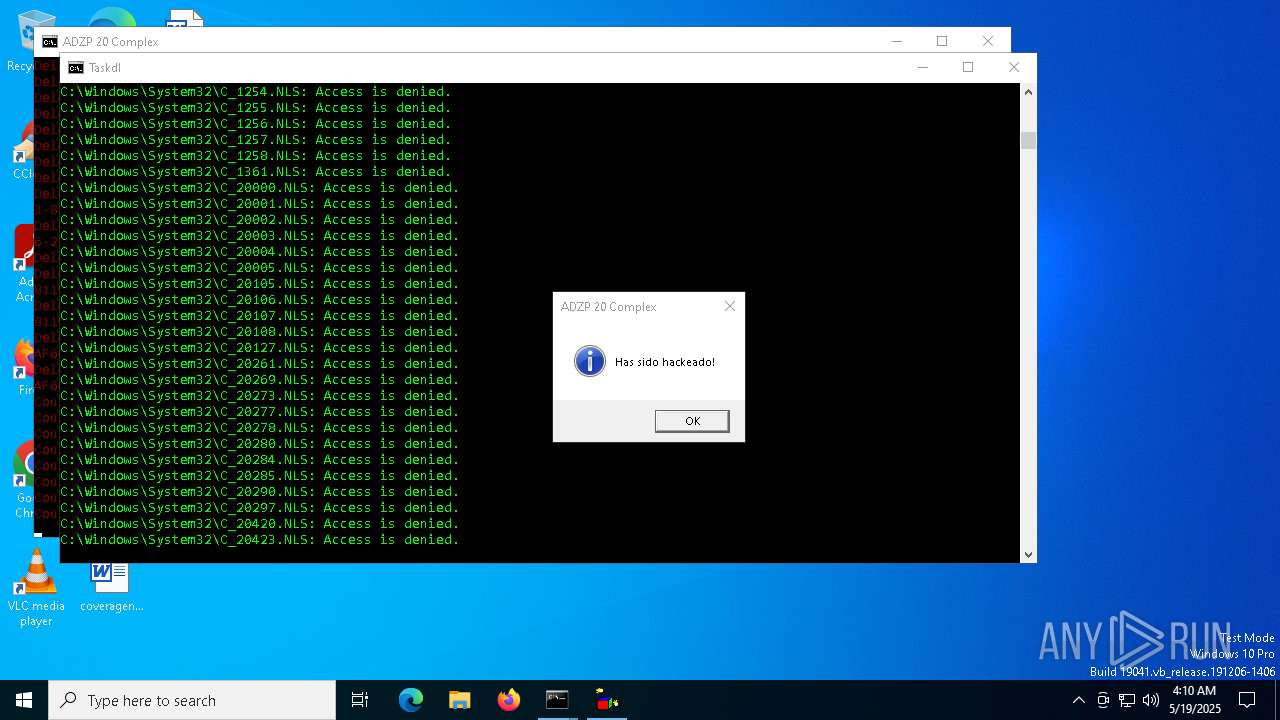
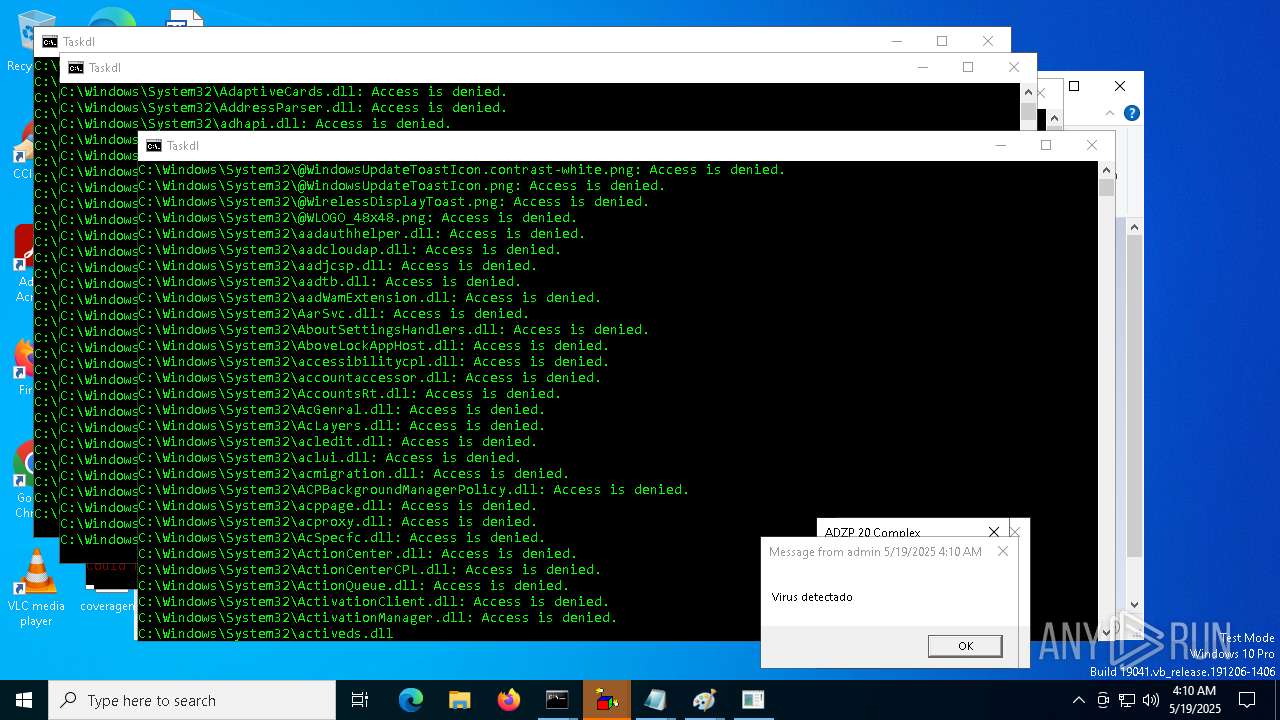
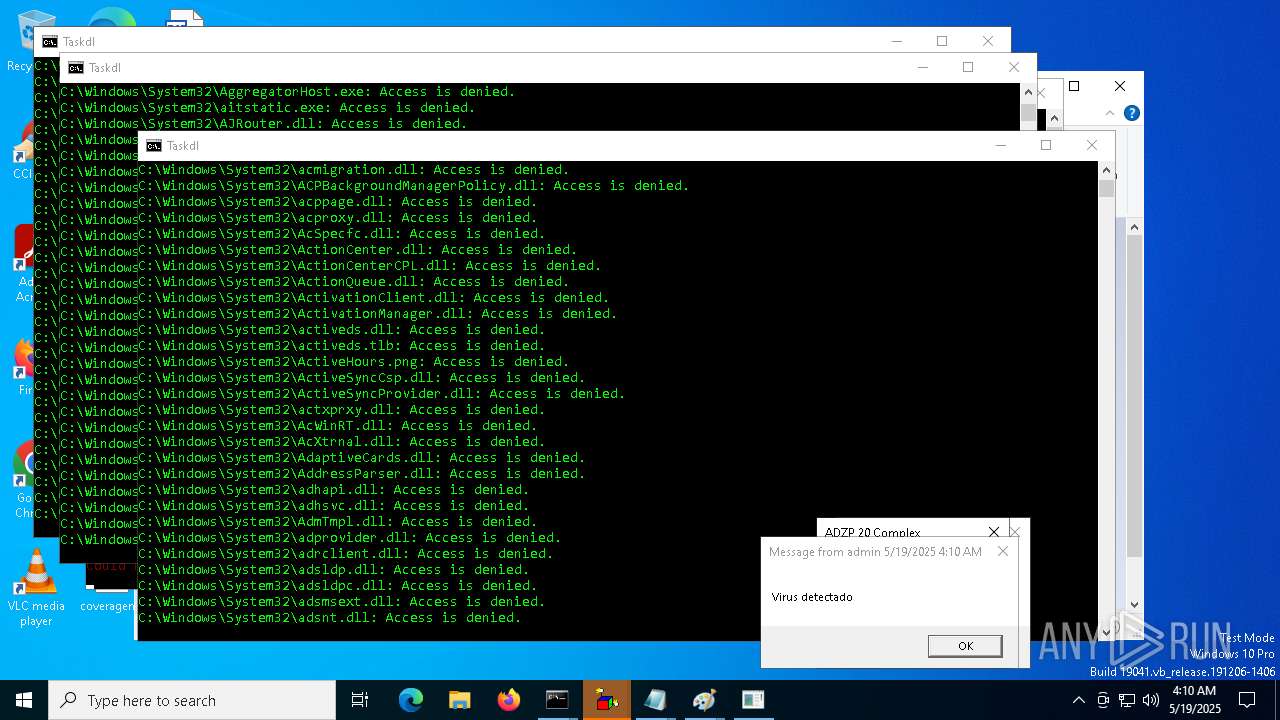
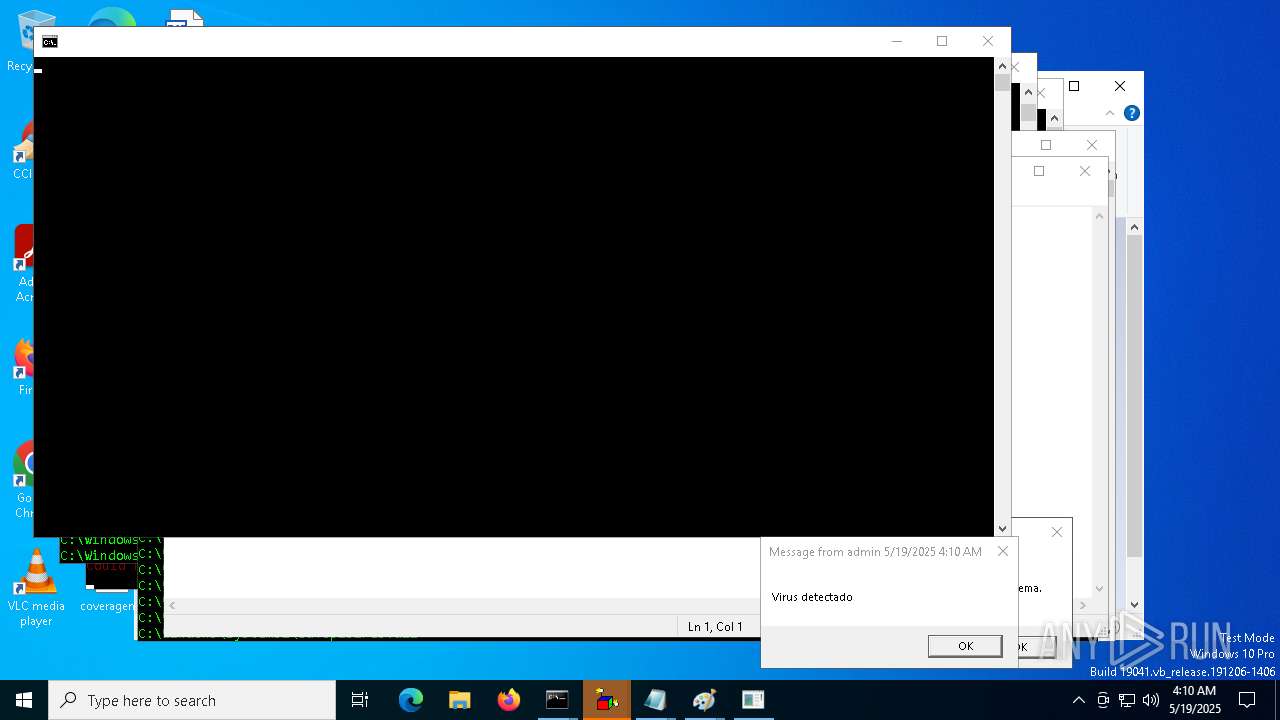
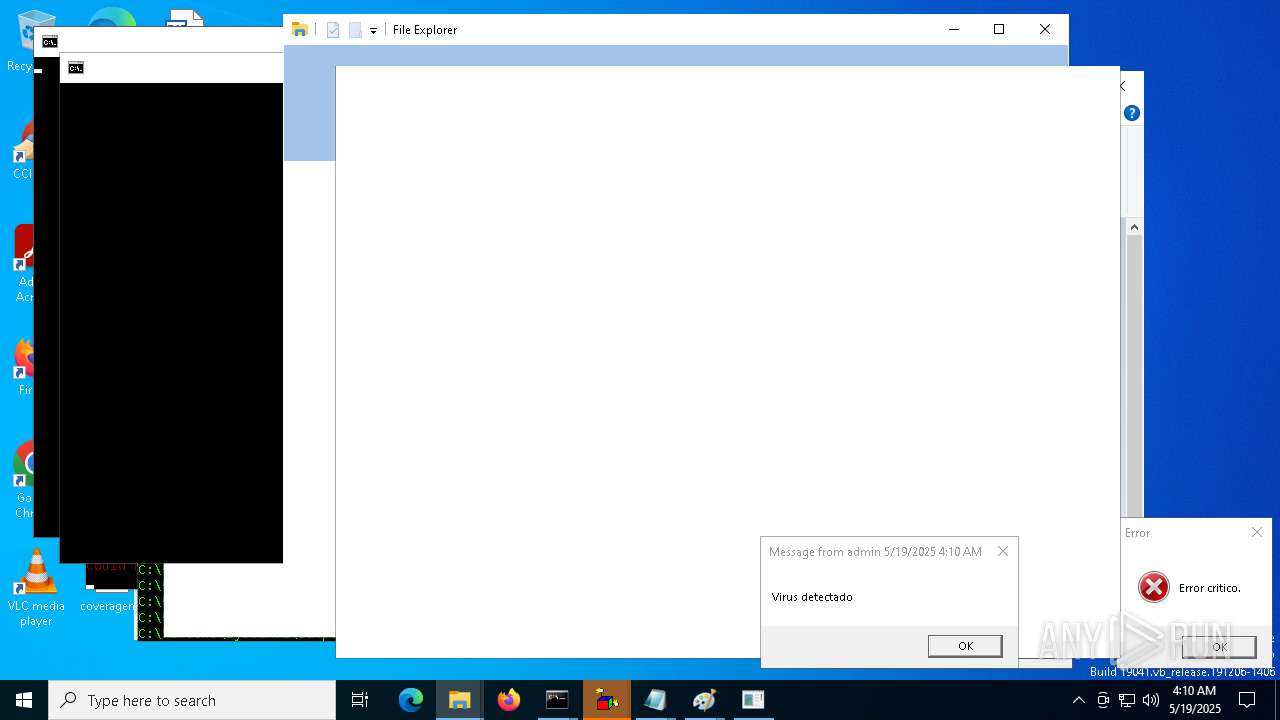
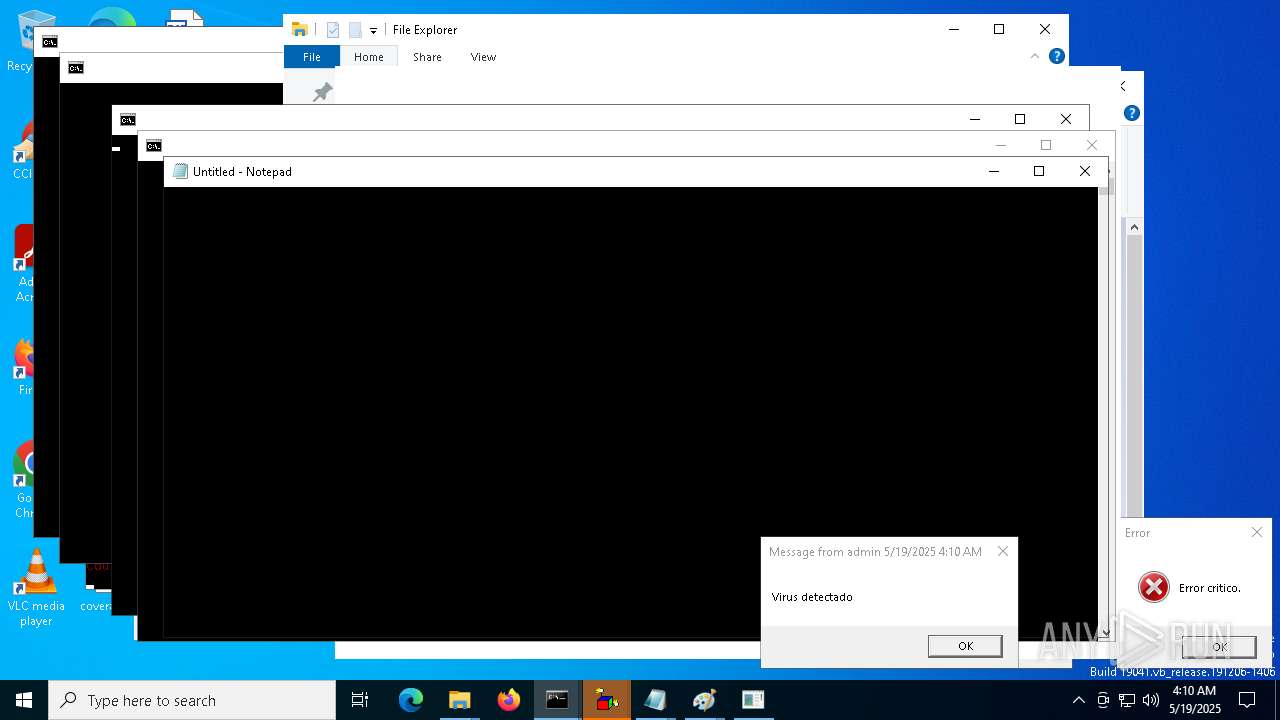
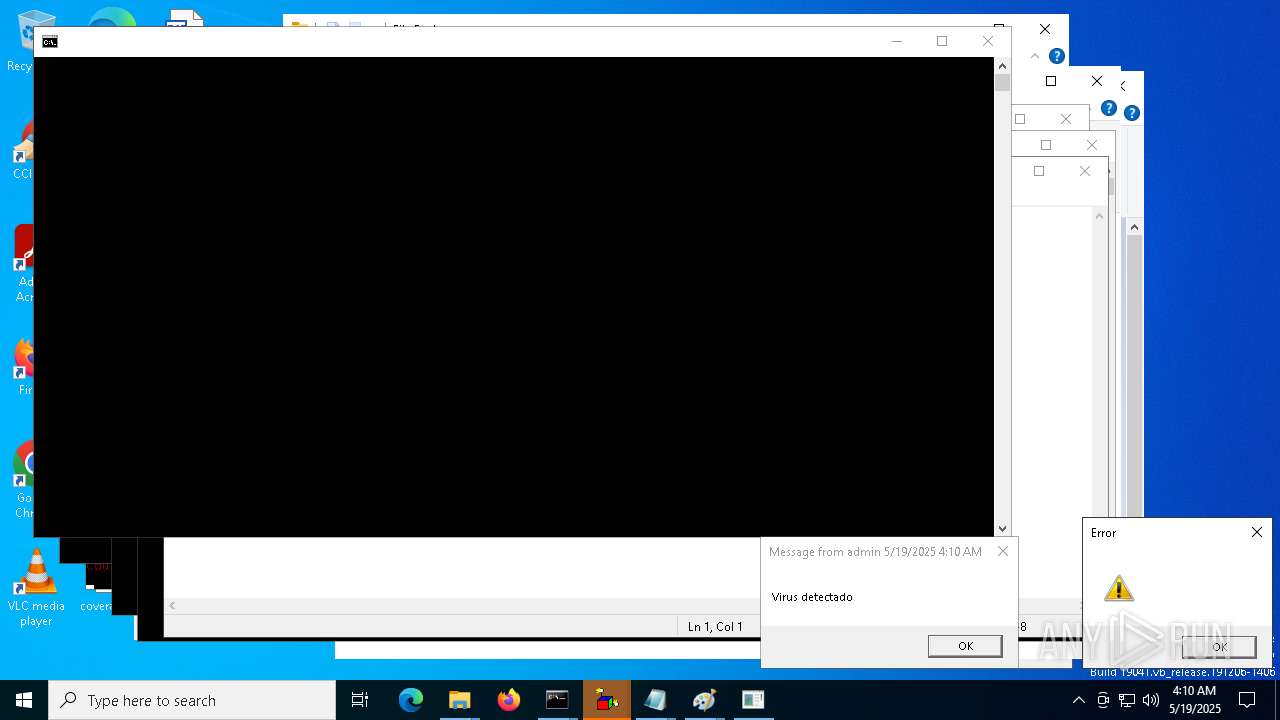
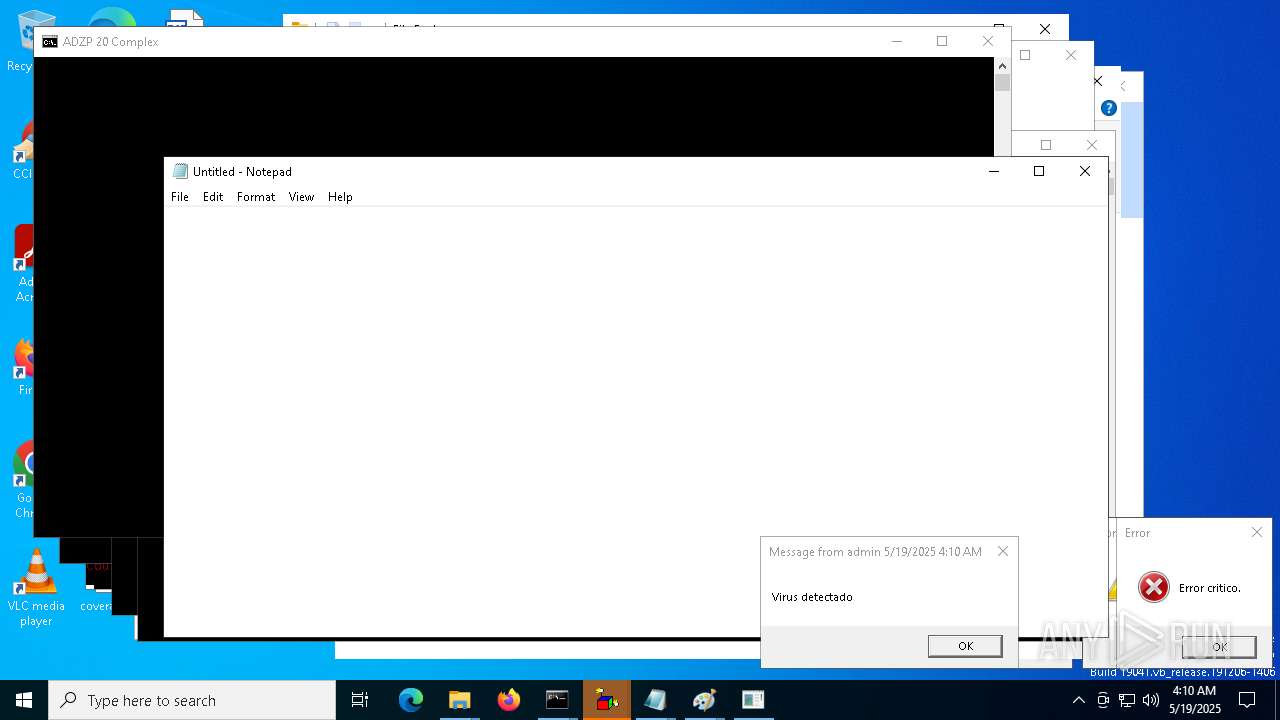
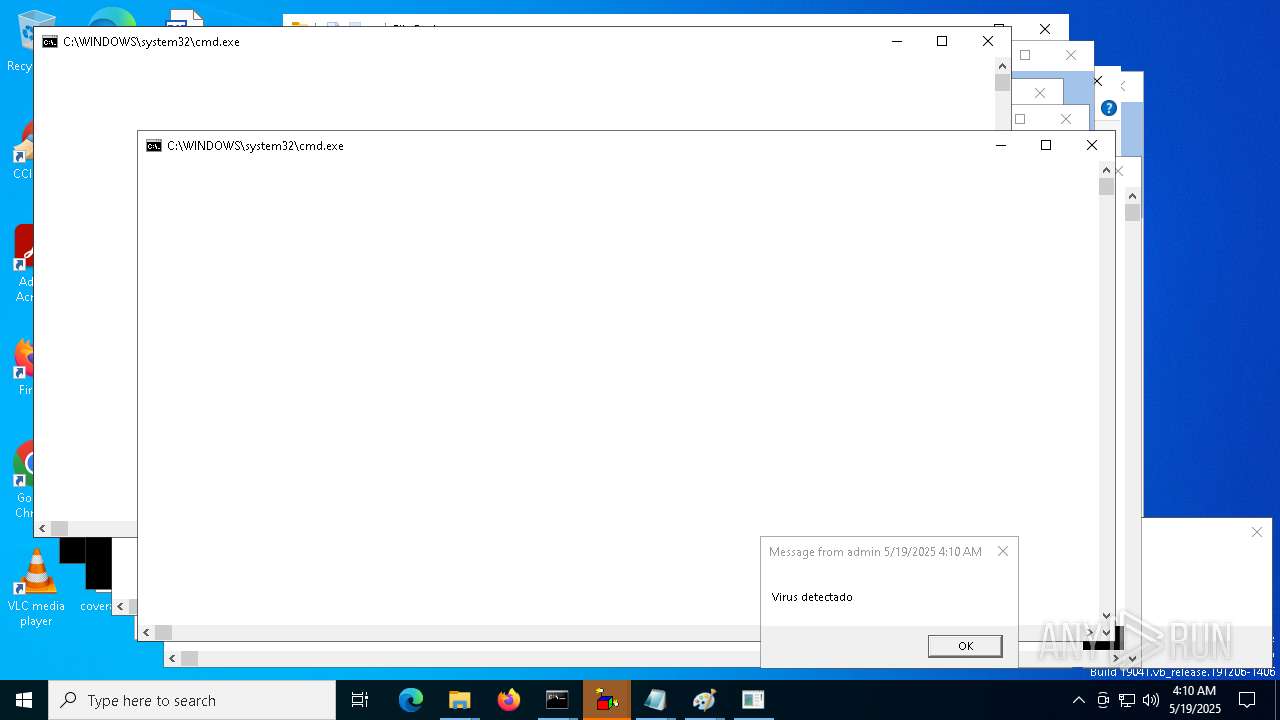
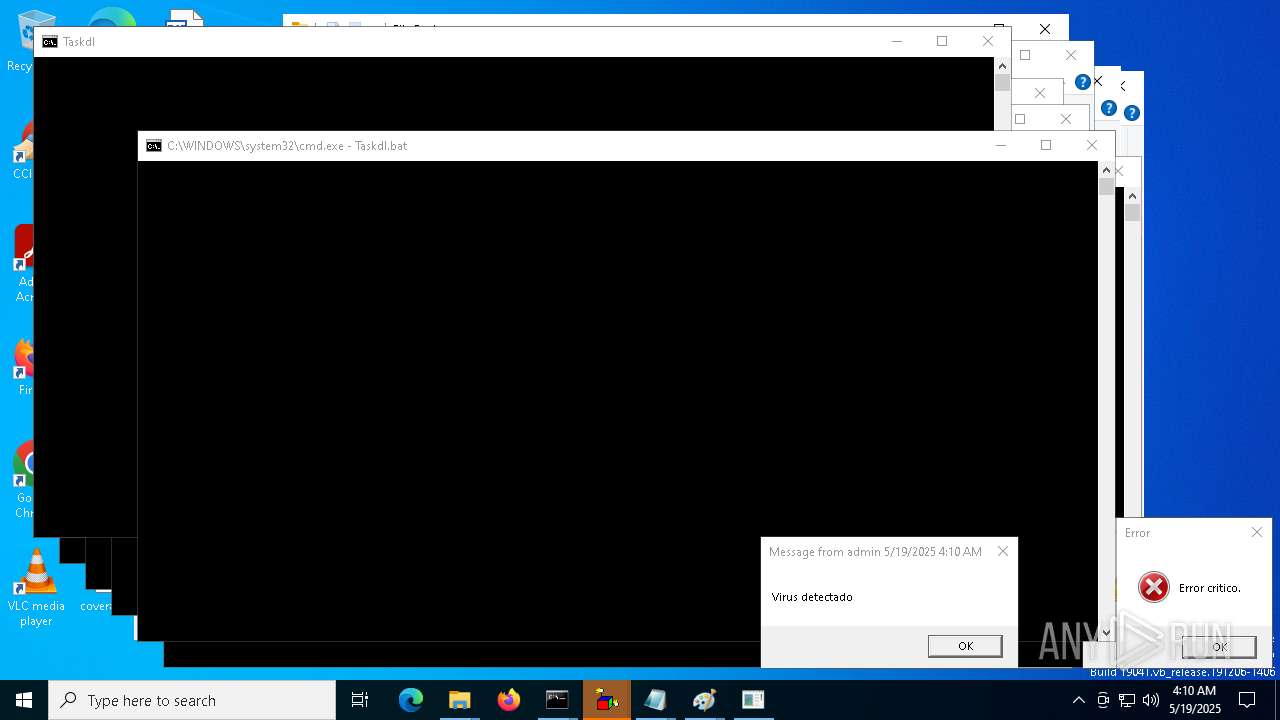
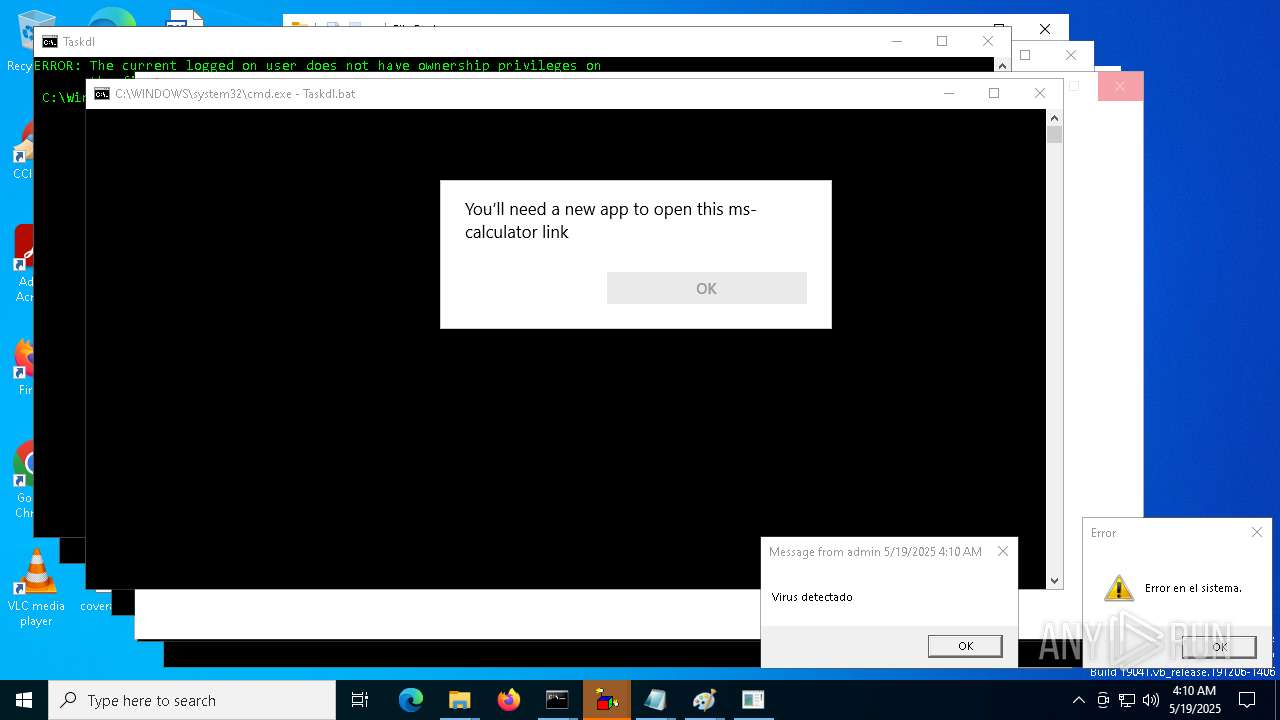
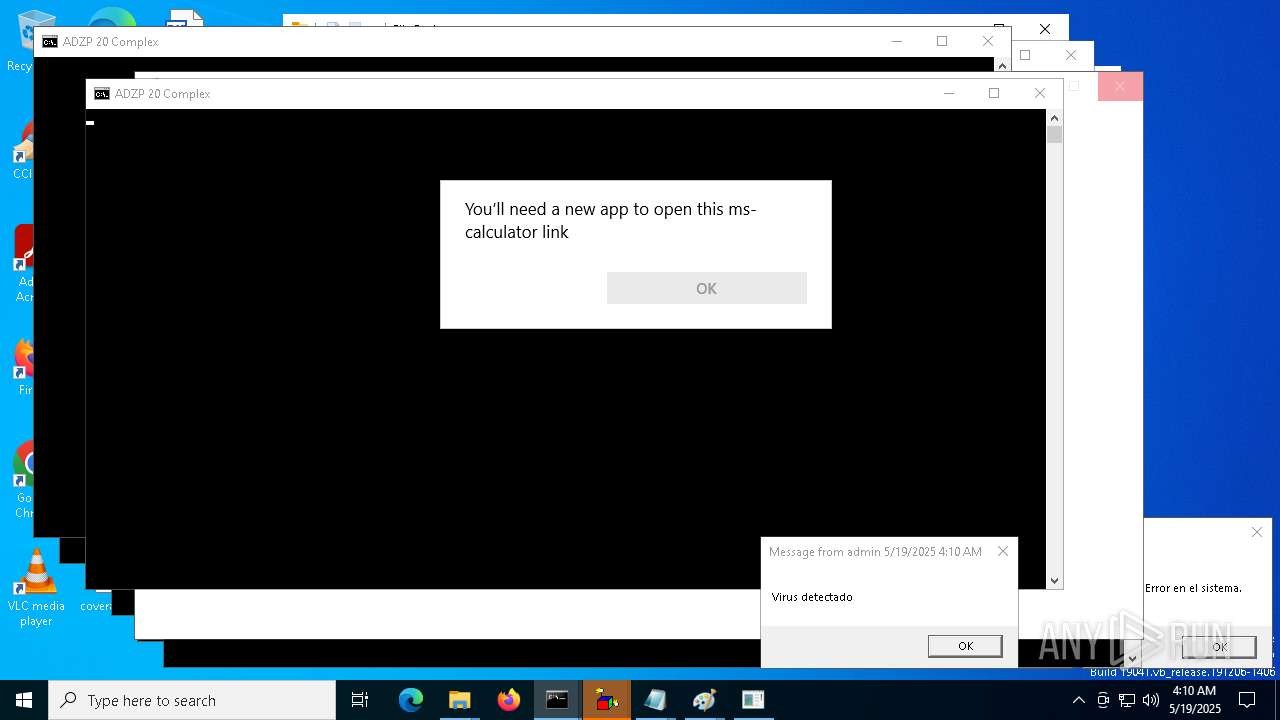
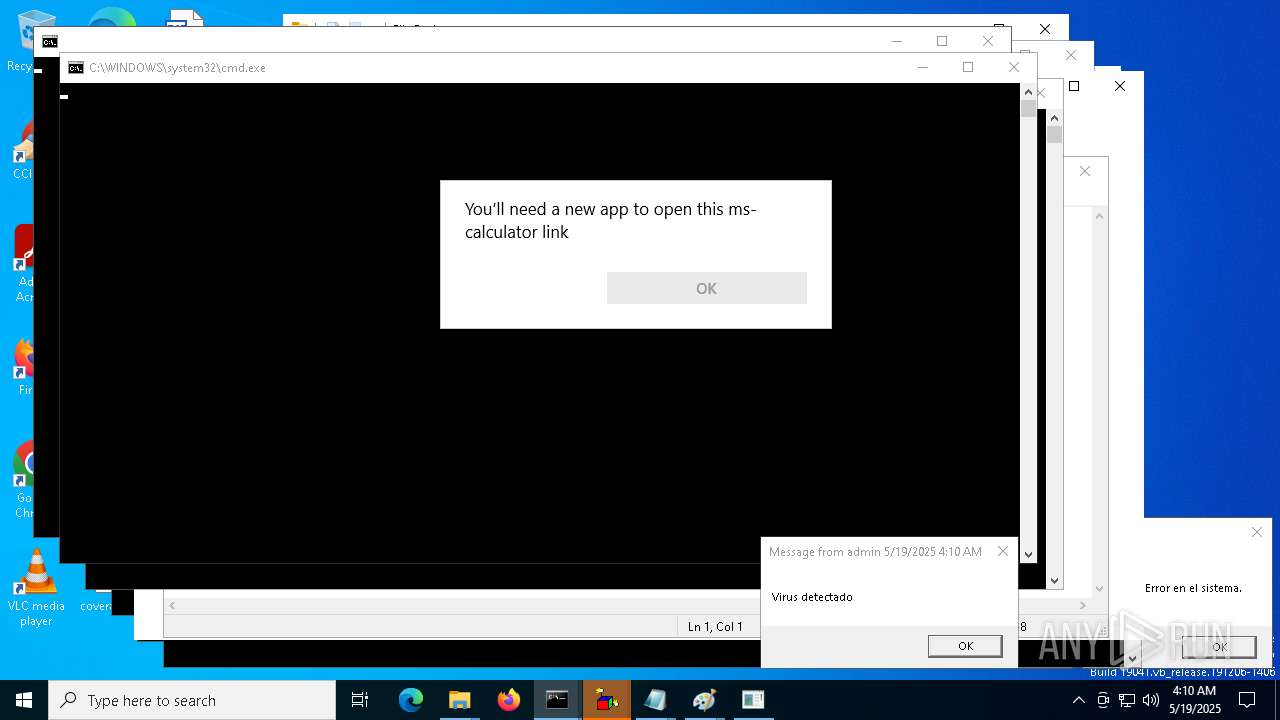
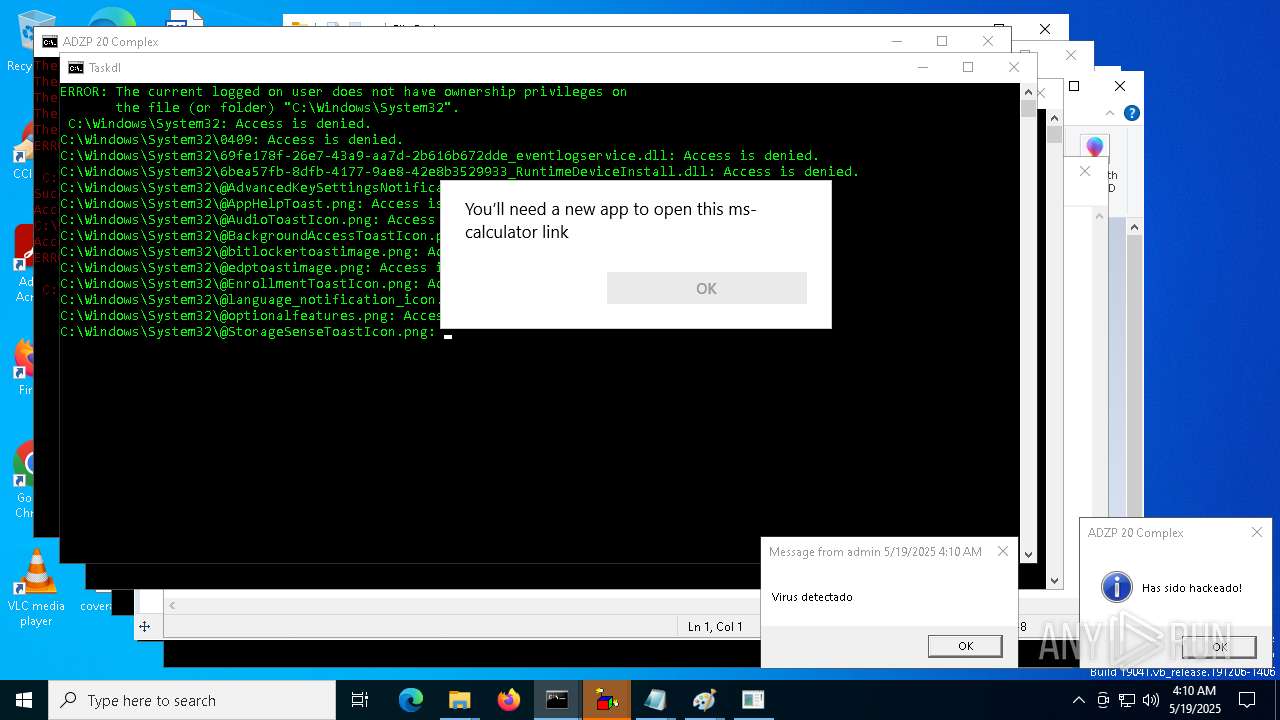
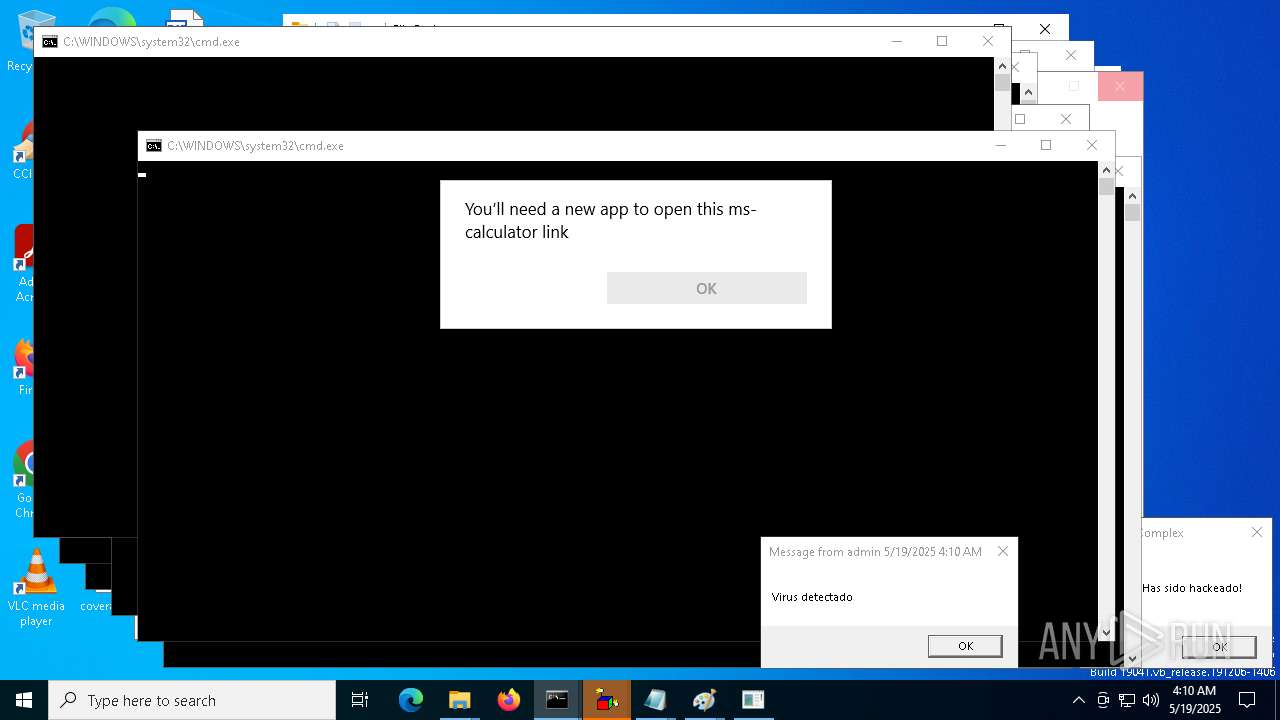
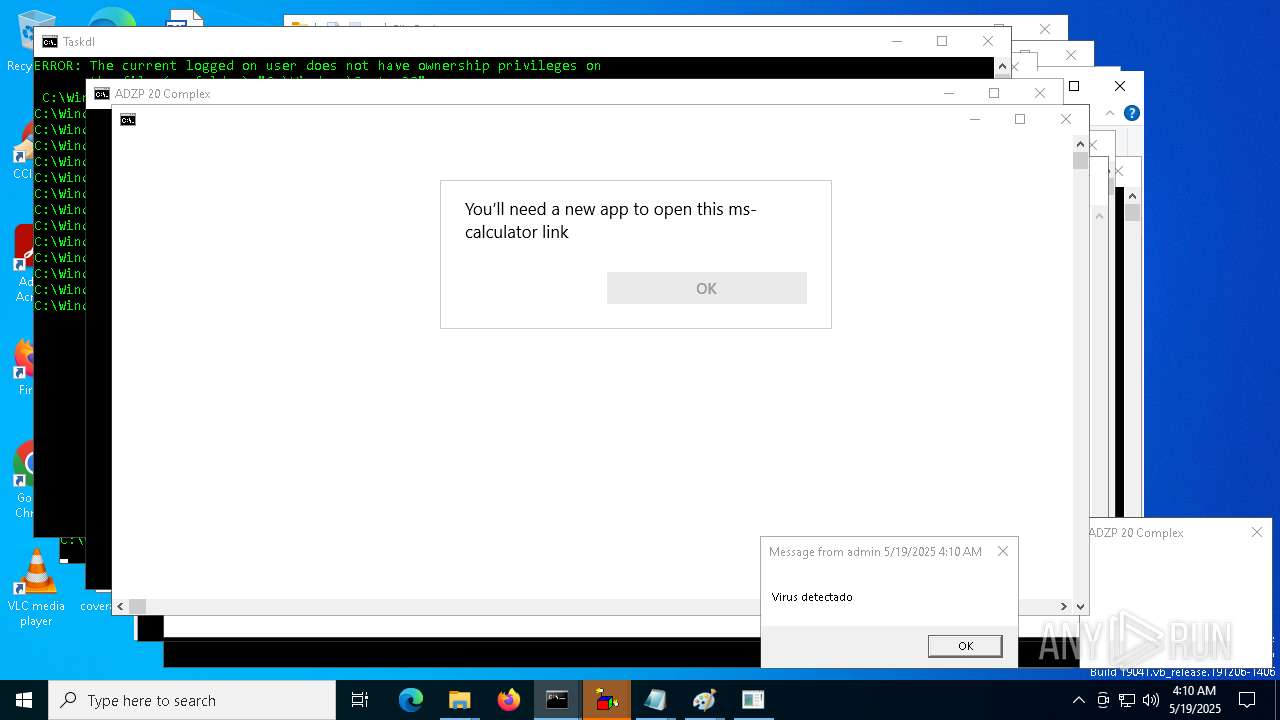
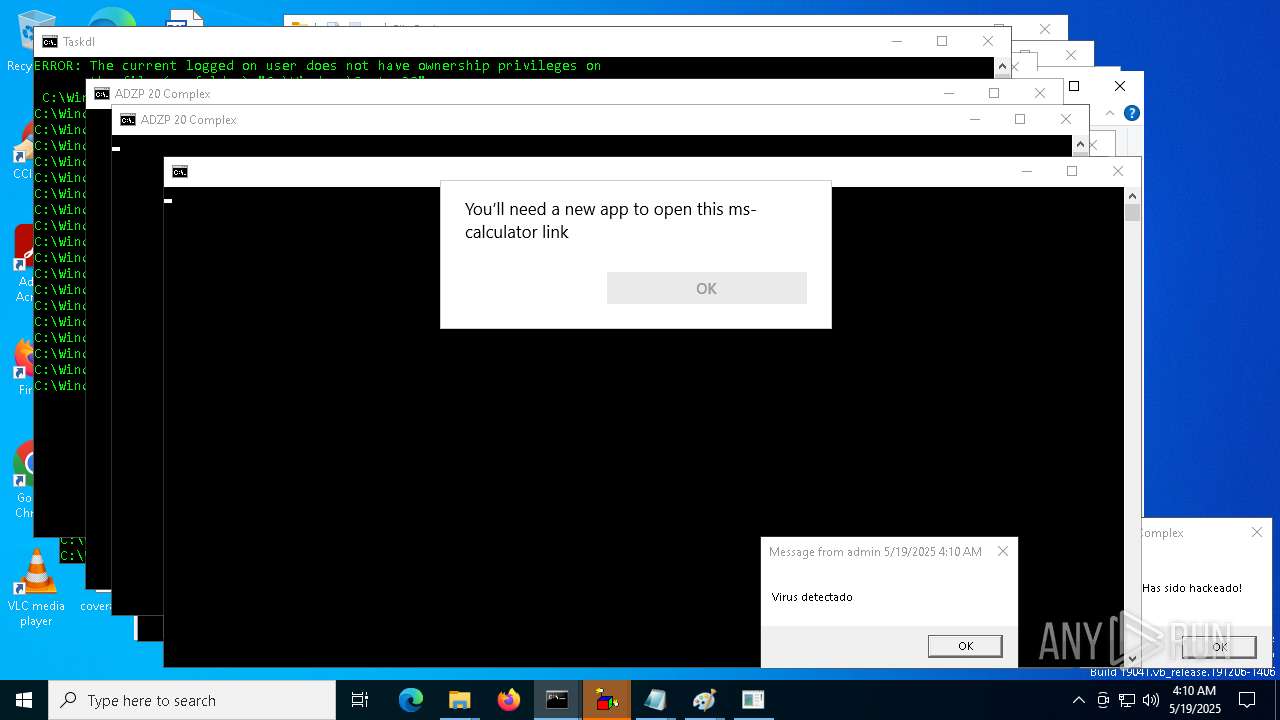
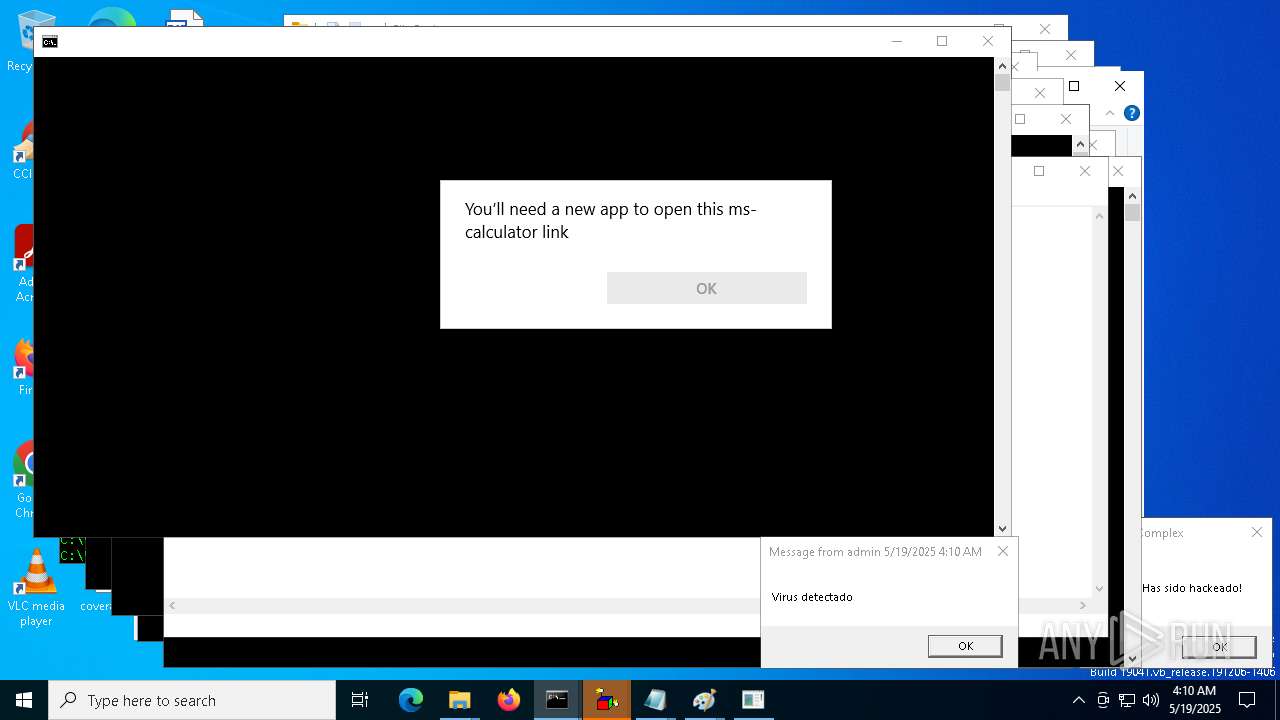
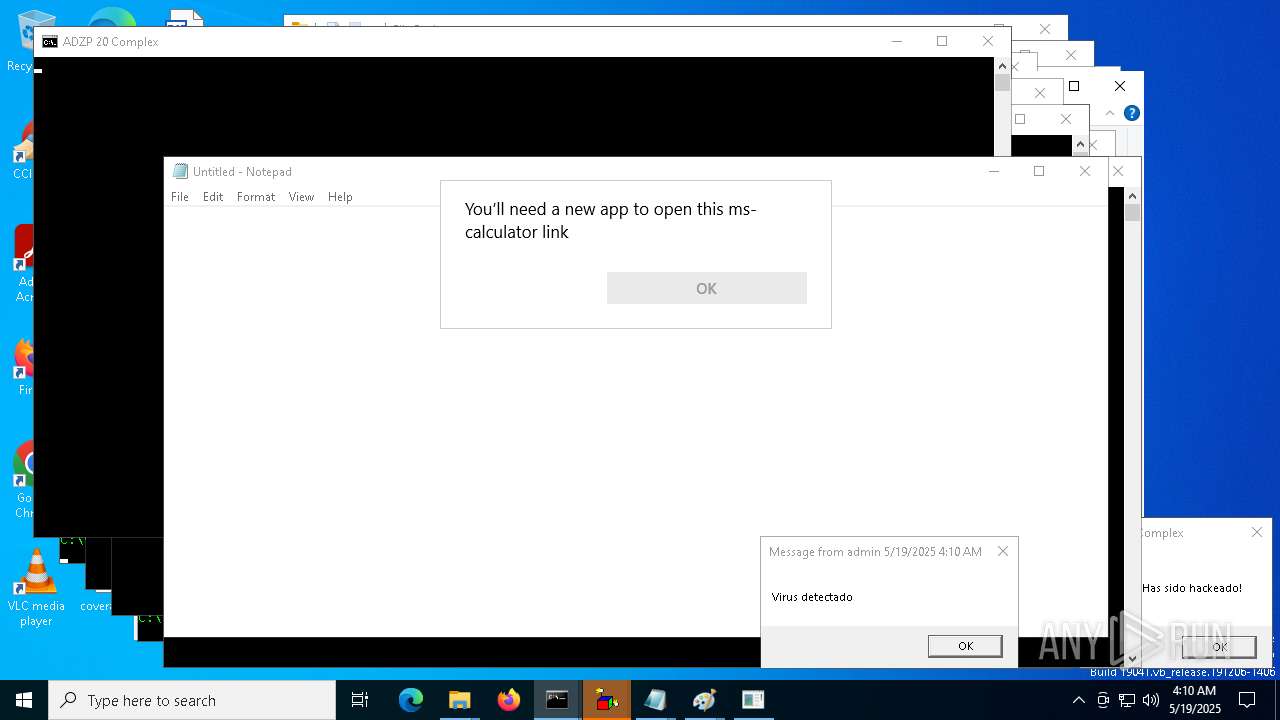
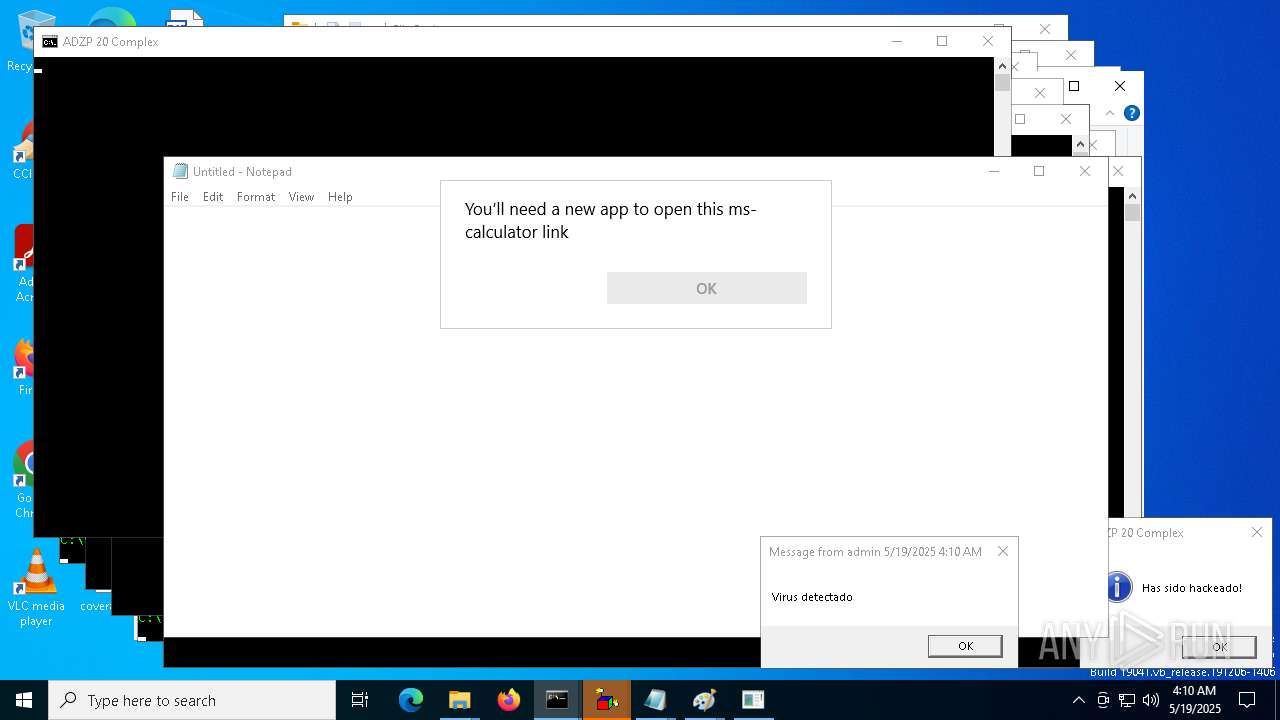
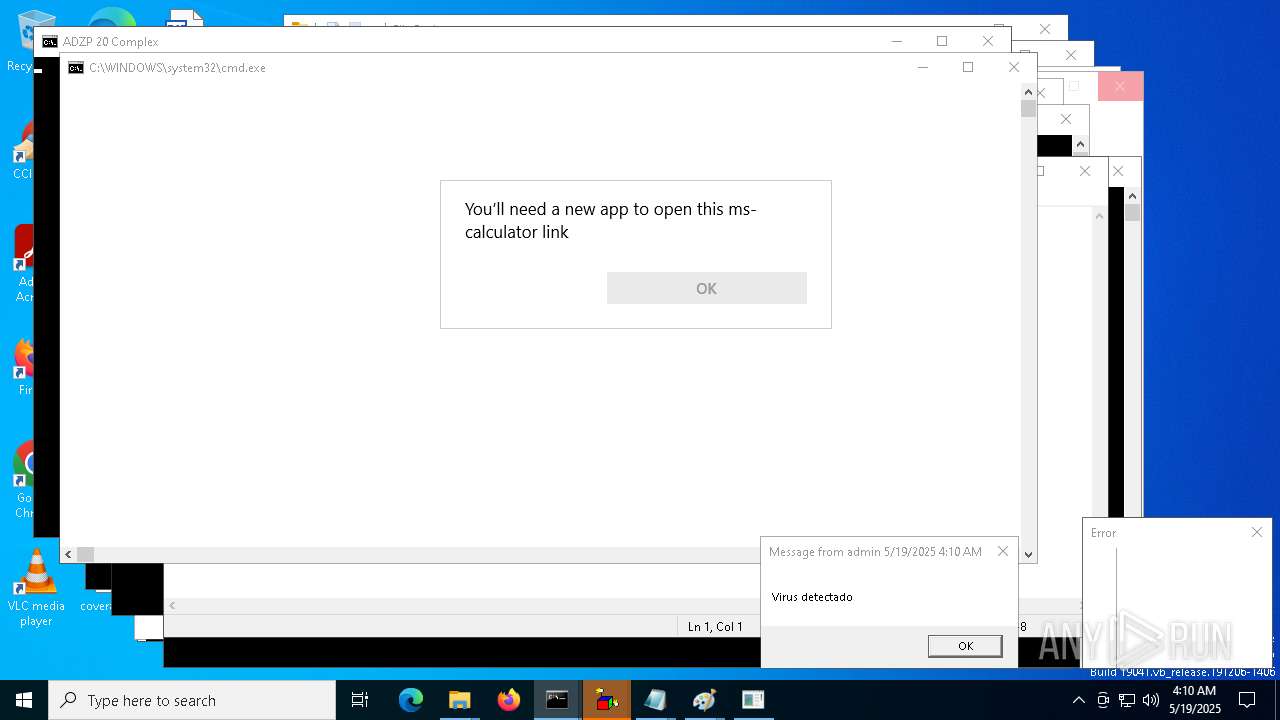
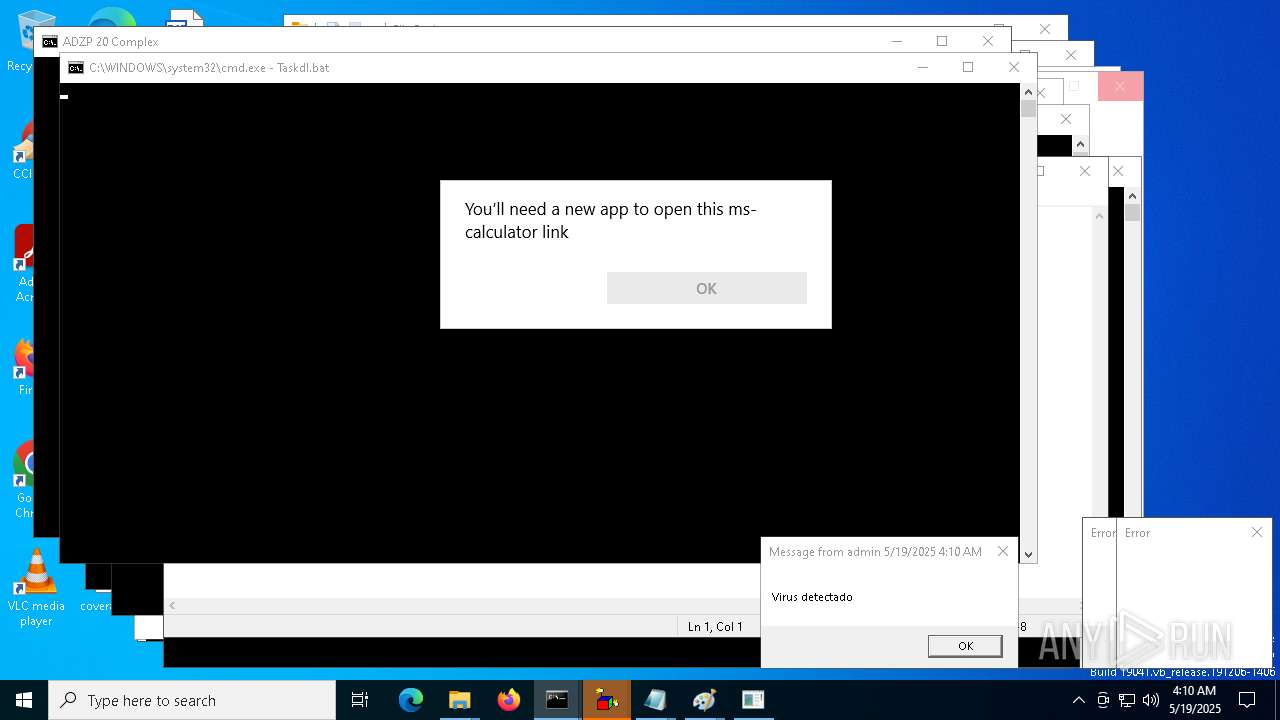
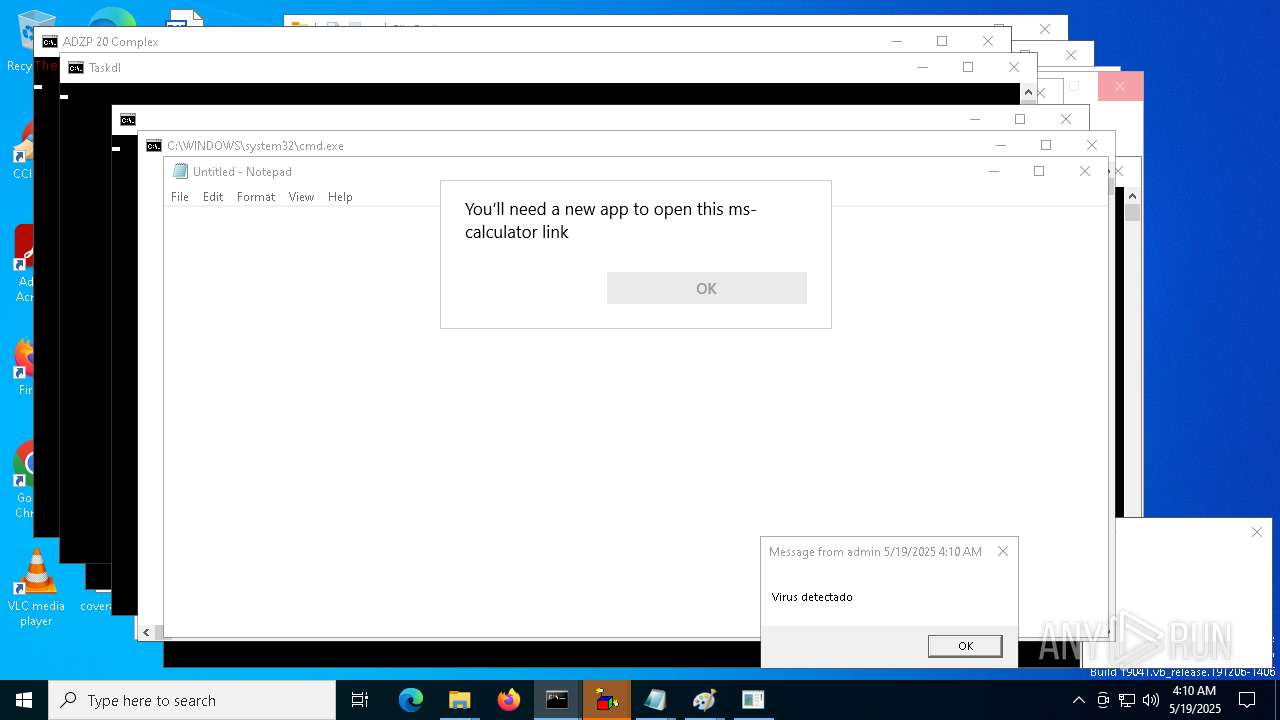
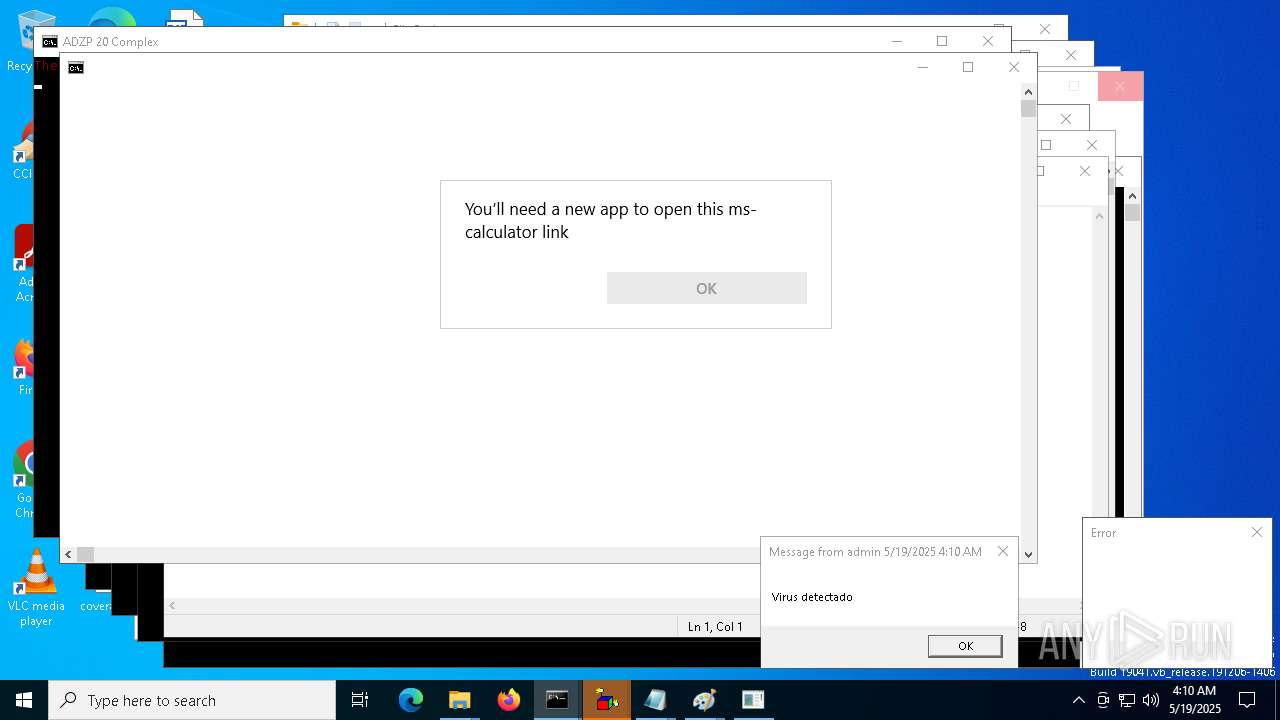
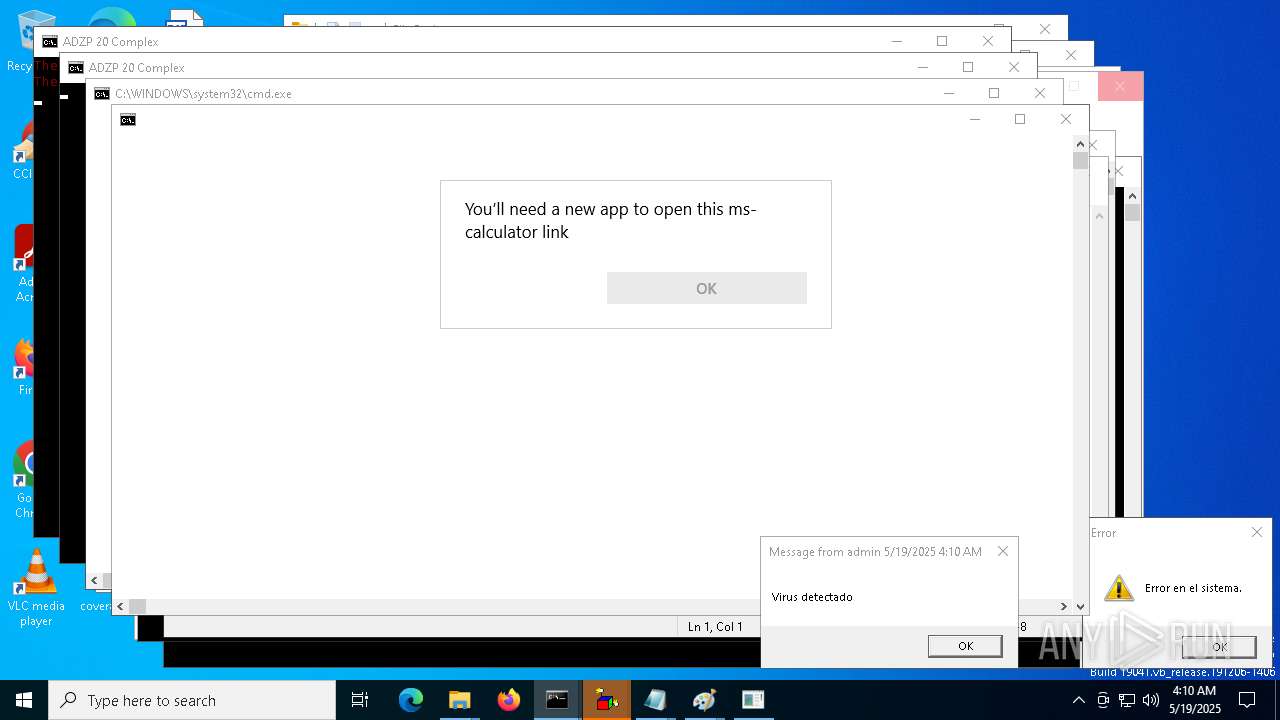
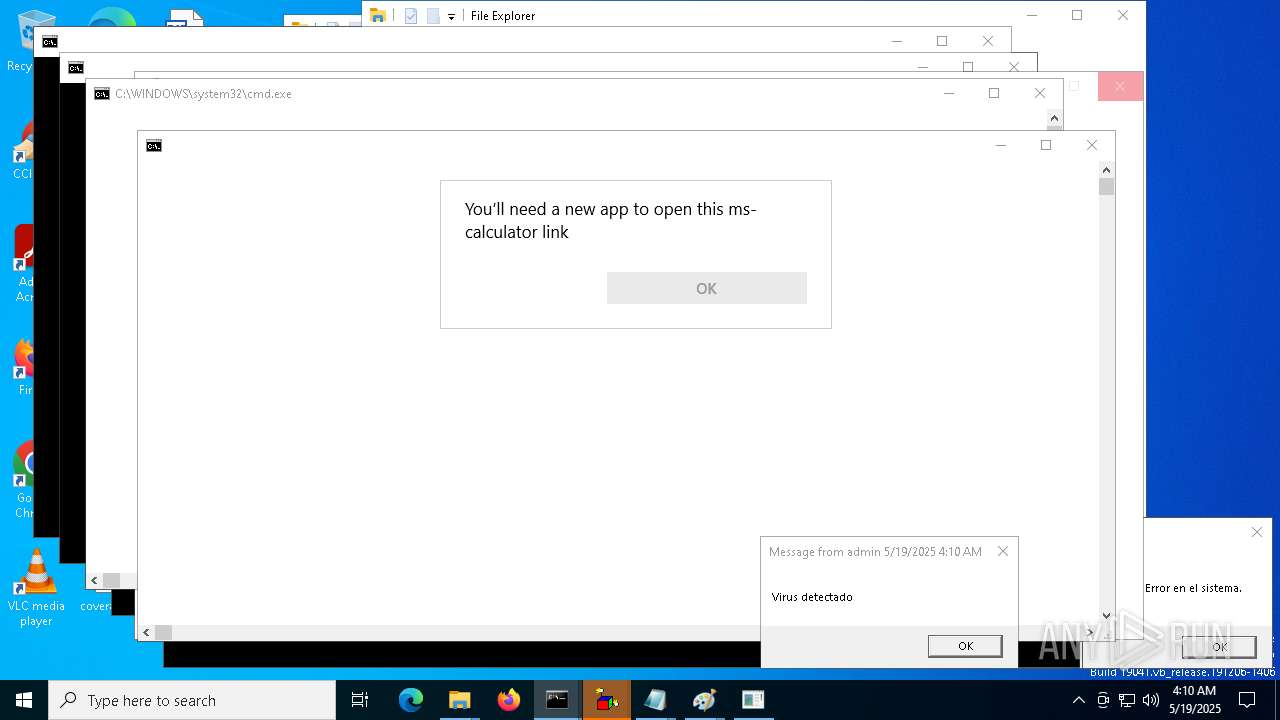
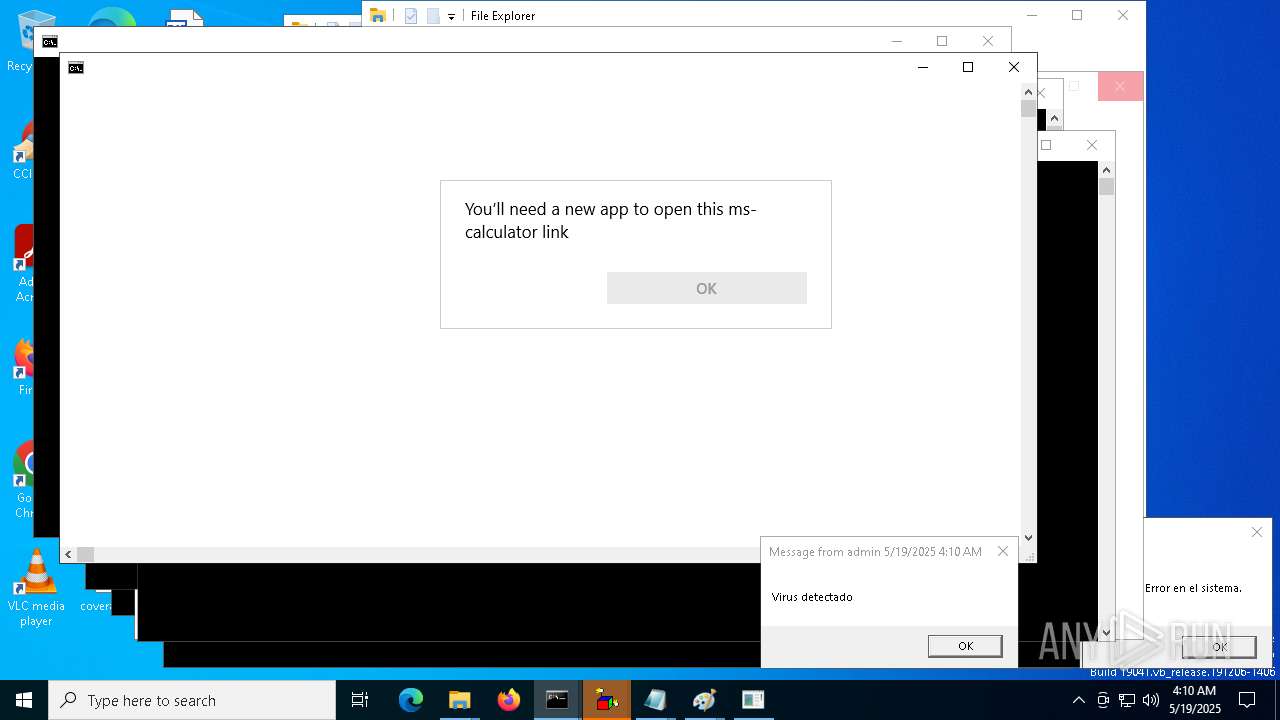
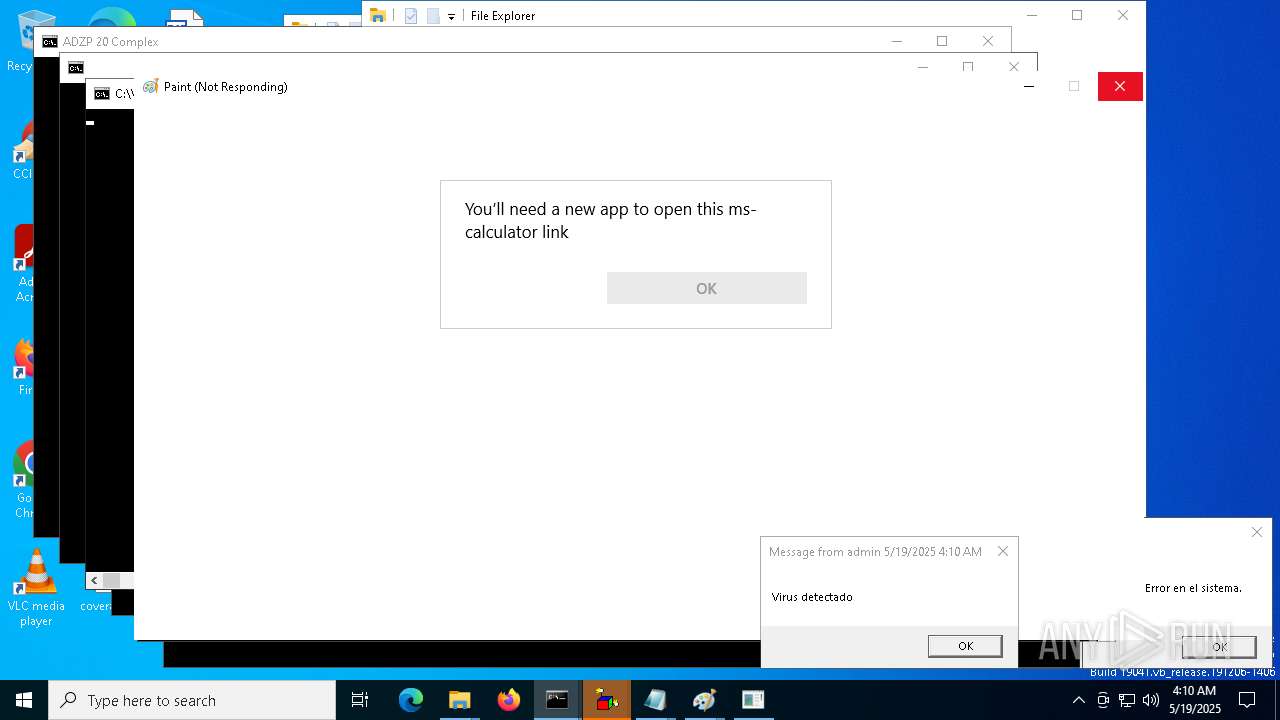
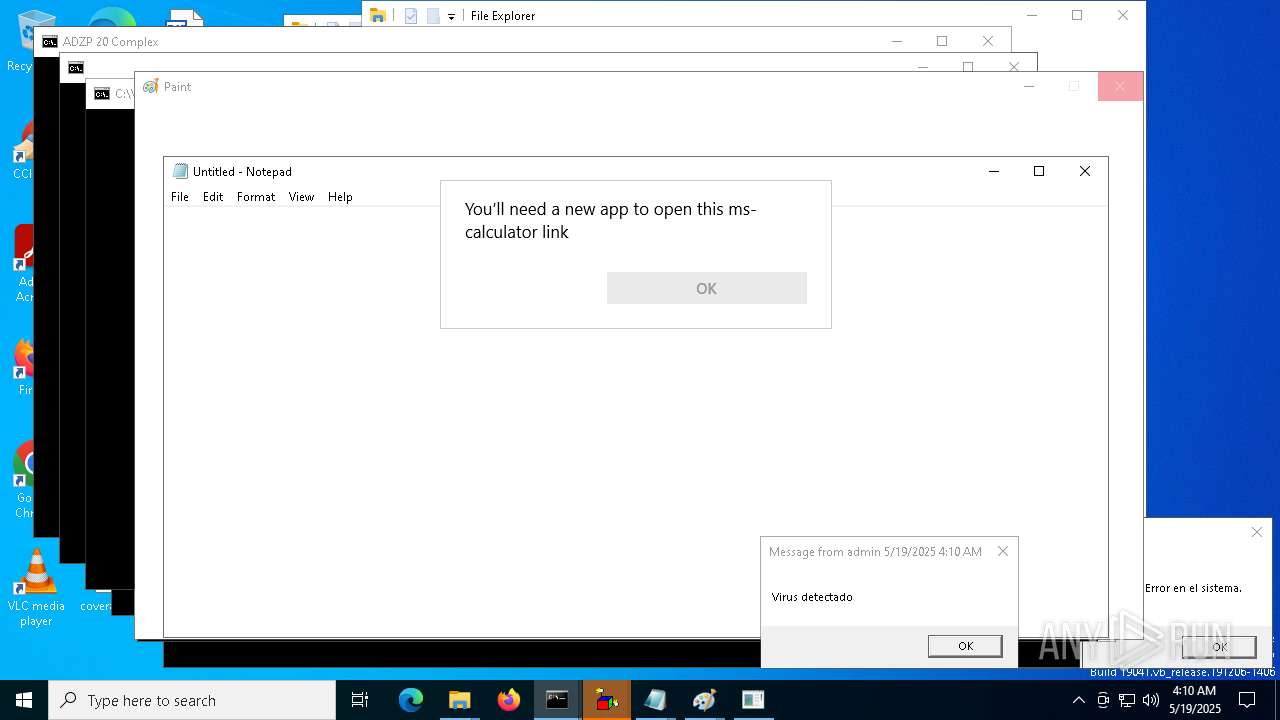
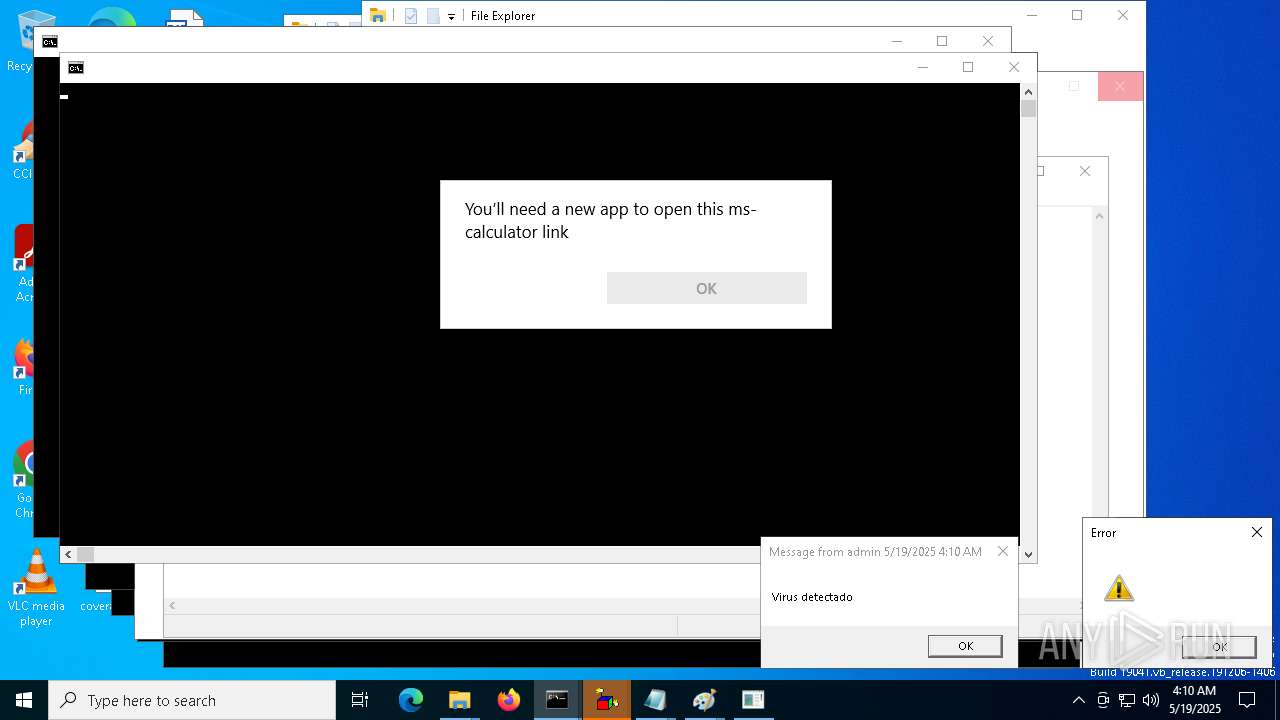
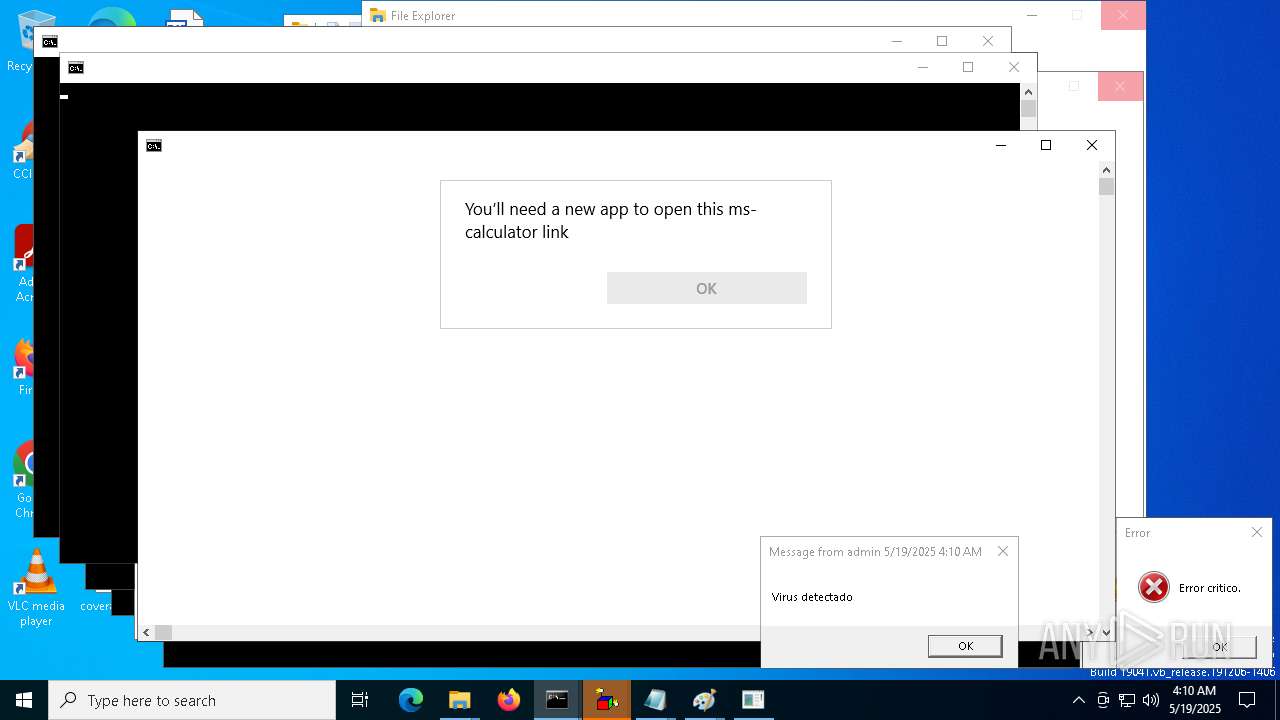
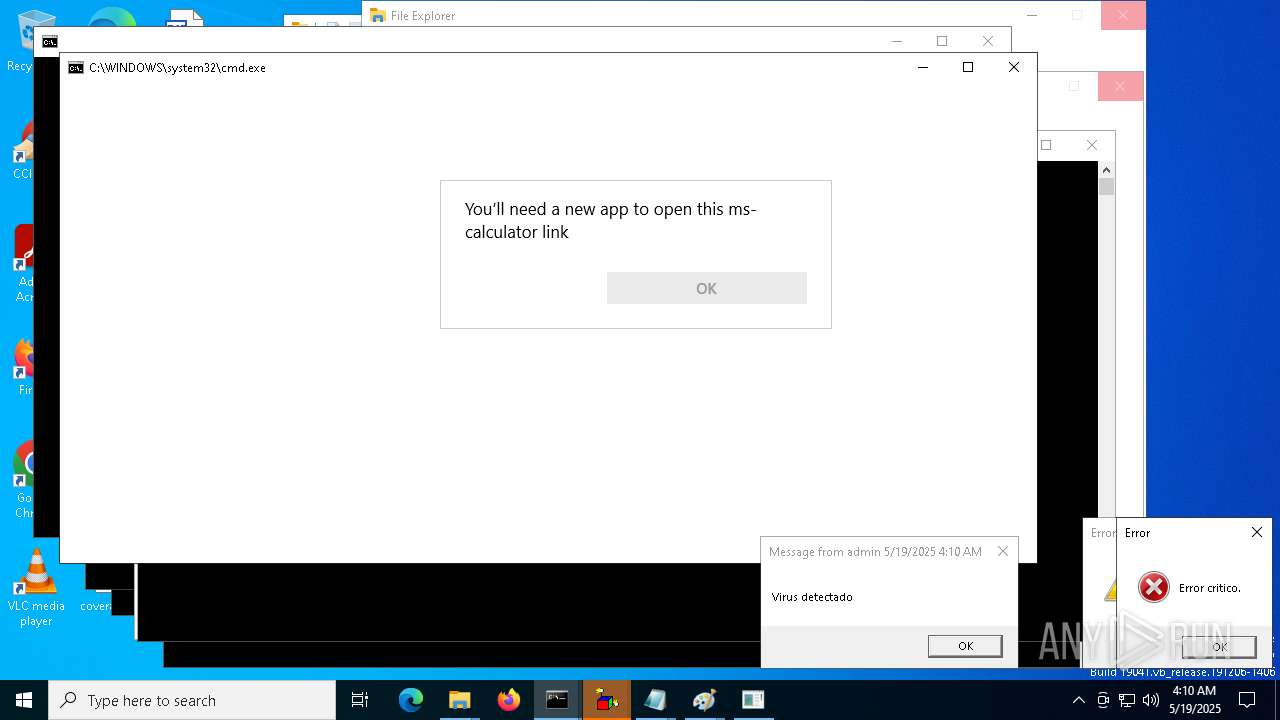
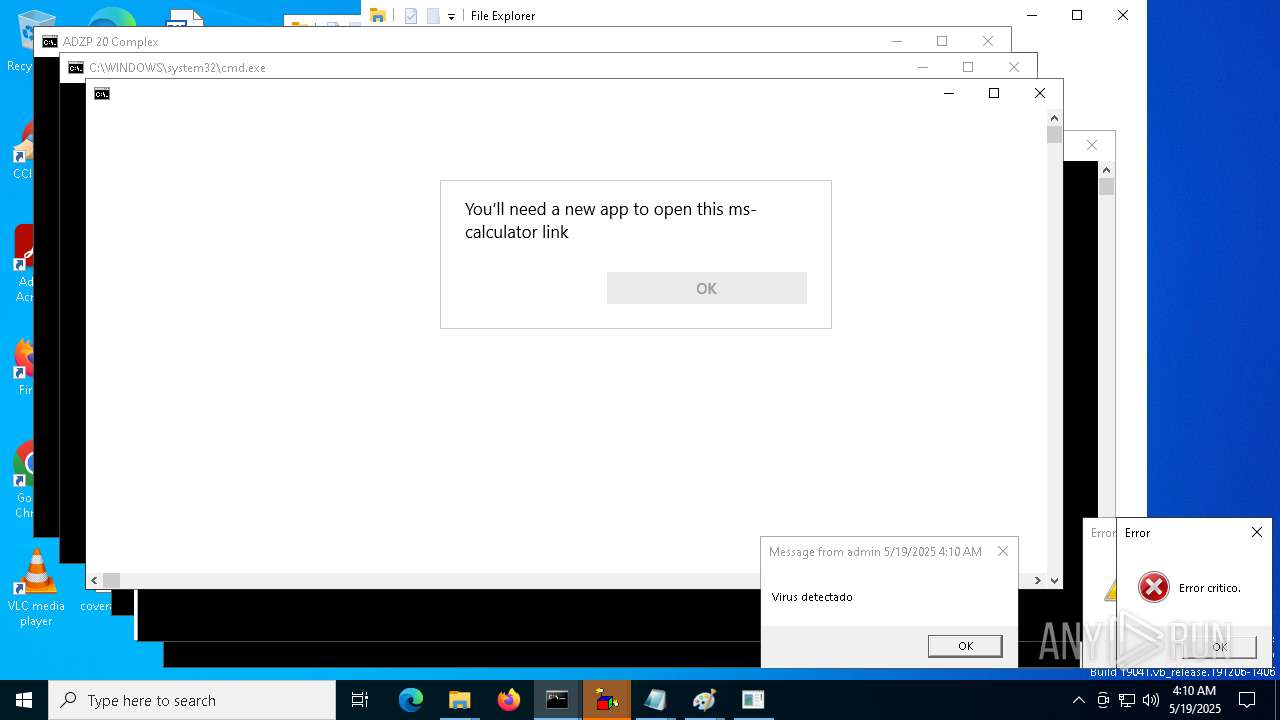
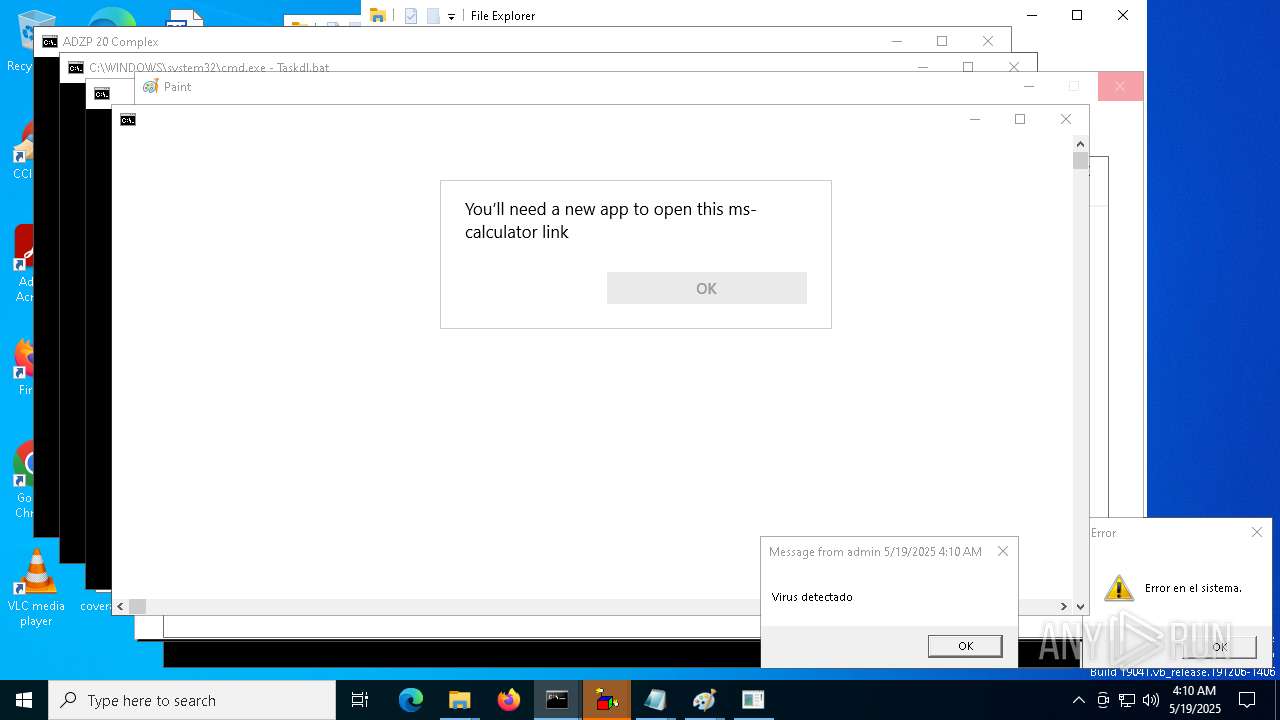
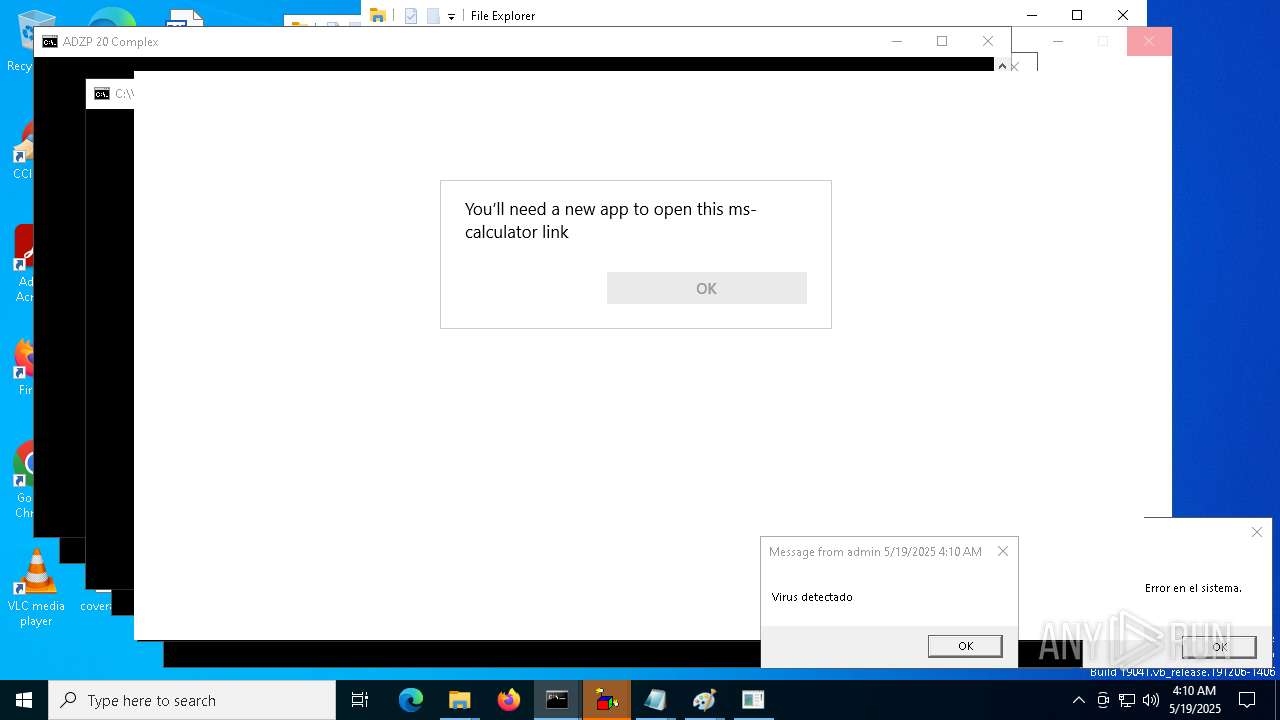
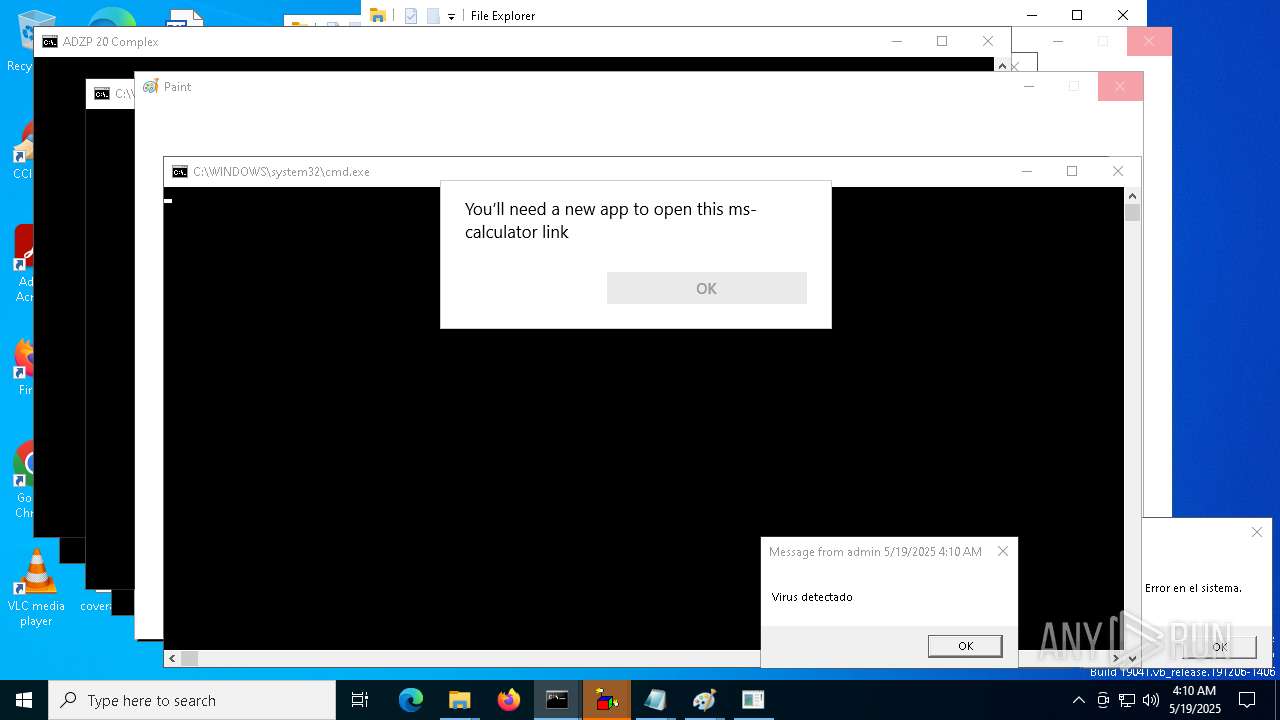
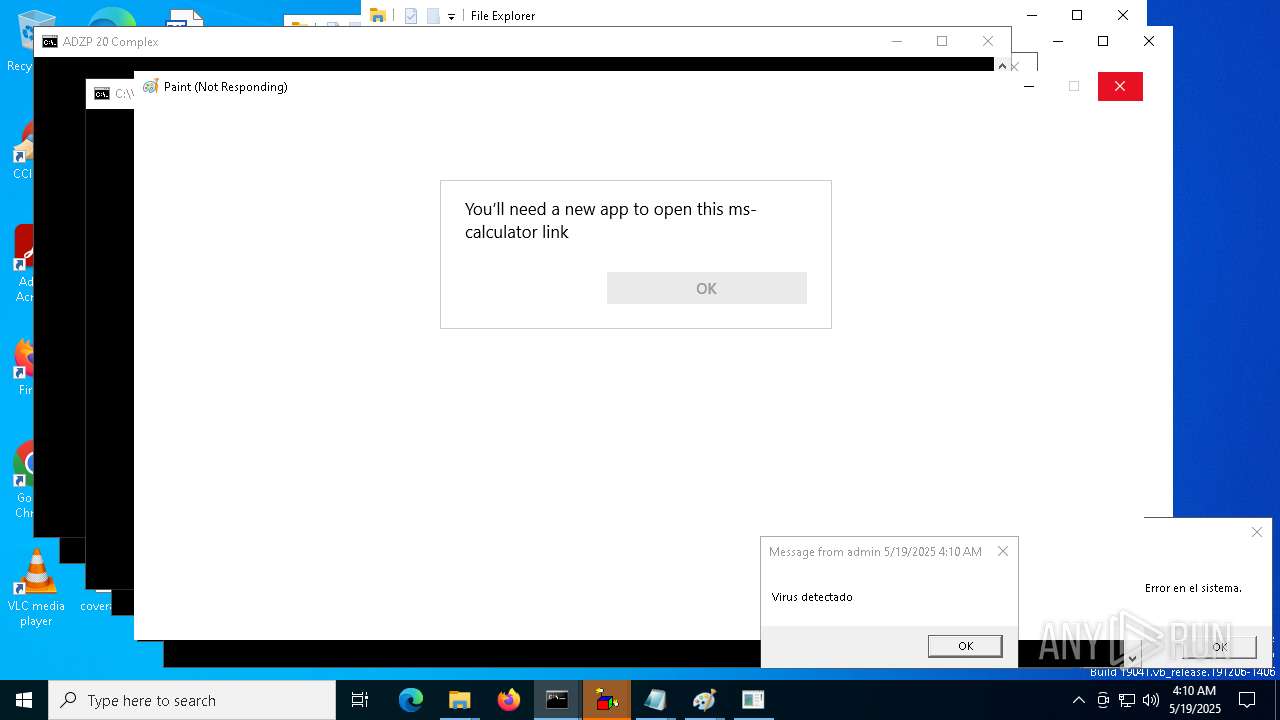
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 04:10:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (841), with CRLF line terminators |
| MD5: | 39830FCB4FFB54FEAAF9A659C07ACED3 |
| SHA1: | 2A68399C0B0D229CE12642B3C1828BF5A78D8521 |
| SHA256: | D13E2C505021D99FD969A85F1FD530066E48ABDCA9161166D38D7593C8EF275D |
| SSDEEP: | 384:8OJWlo3yzLK+qPXPtTGcJdAbrM21q0j0L1qEzdQ8PigfwTxX8j2x:8FqPFTGcbAUAW17JQrgodXG2x |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 1628)
- reg.exe (PID: 9148)
- reg.exe (PID: 9192)
- reg.exe (PID: 7620)
Create files in the Startup directory
- cmd.exe (PID: 1452)
SONIC has been detected
- cmd.exe (PID: 1452)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7800)
SUSPICIOUS
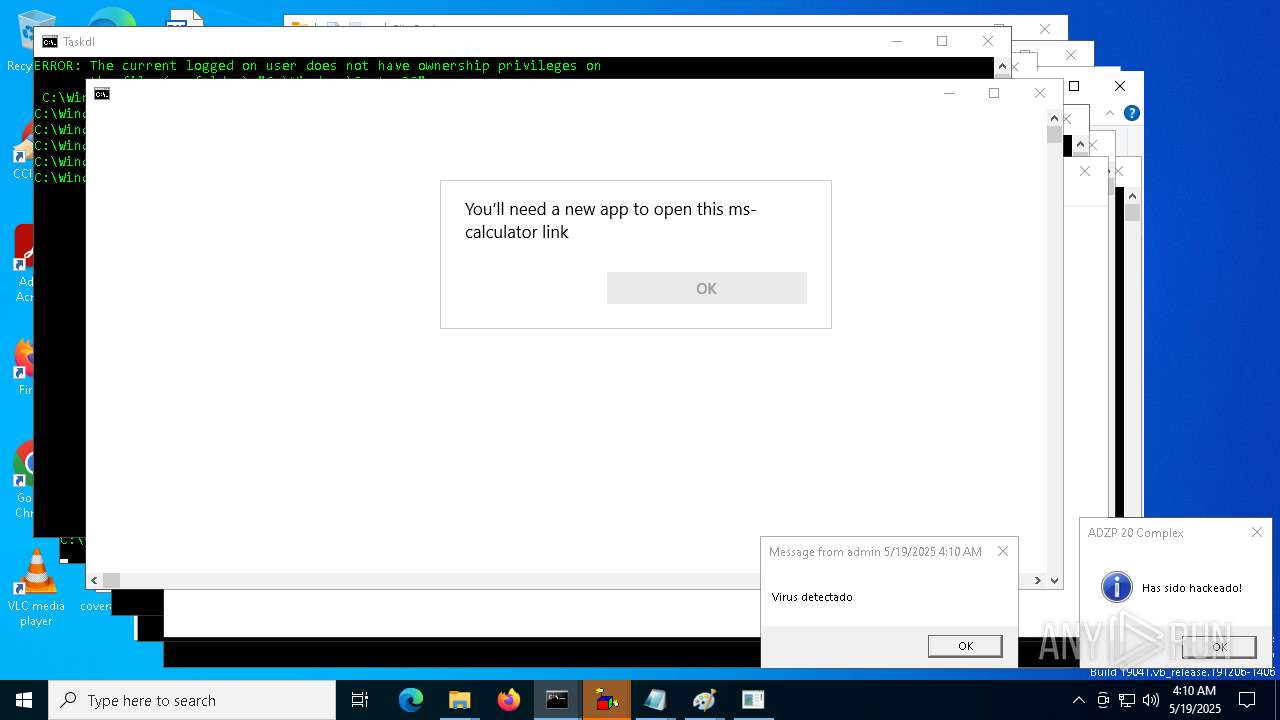
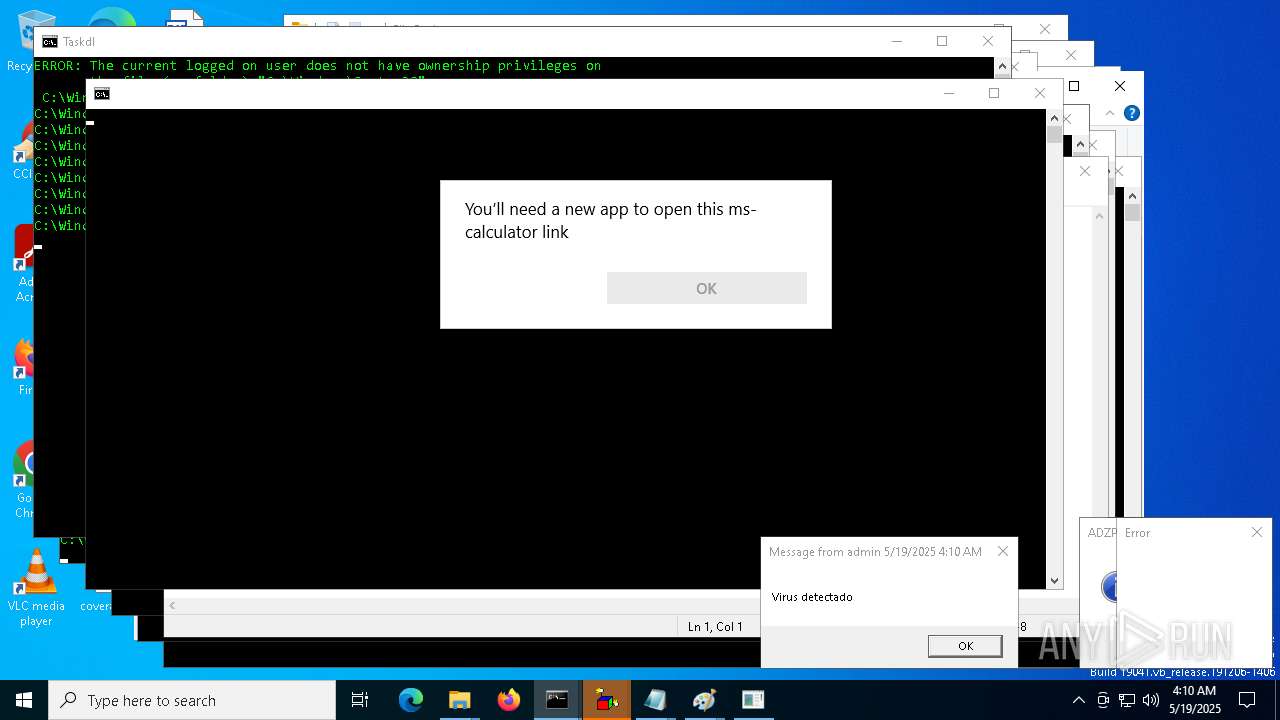
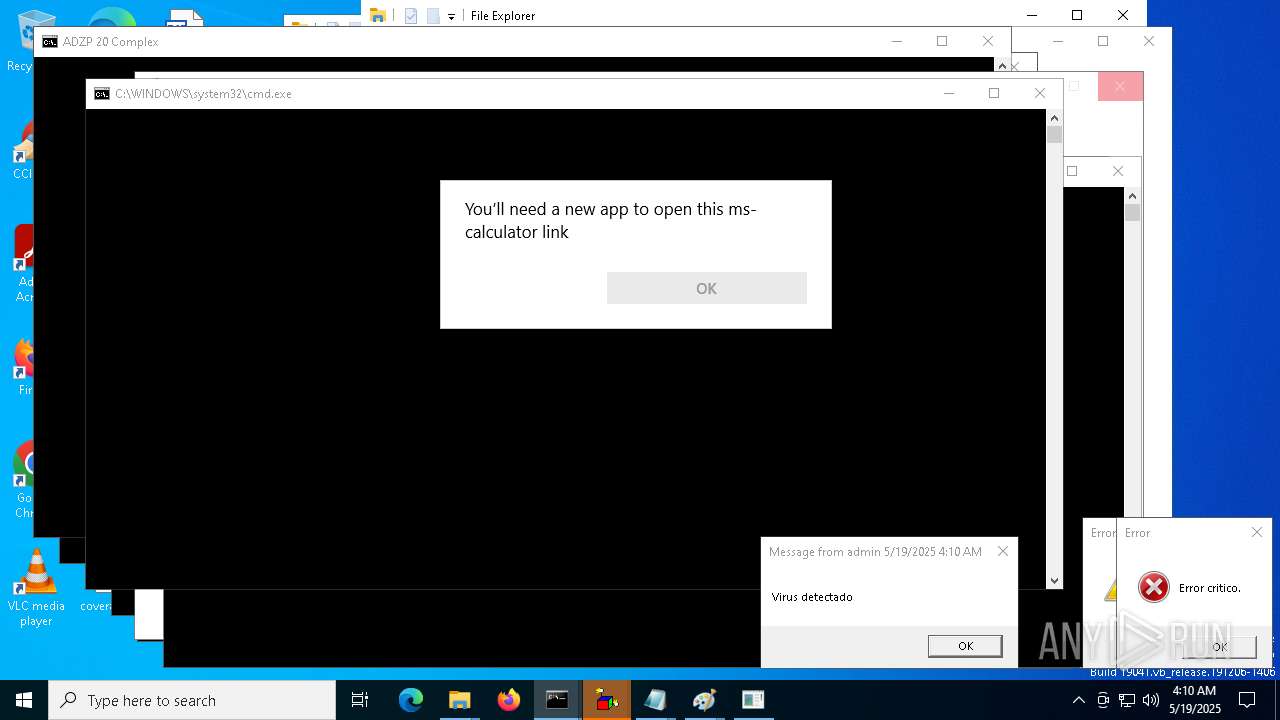
Application launched itself
- cmd.exe (PID: 1452)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 13028)
- cmd.exe (PID: 13264)
- cmd.exe (PID: 13996)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 13808)
- cmd.exe (PID: 14284)
- cmd.exe (PID: 14664)
- cmd.exe (PID: 15684)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 16380)
- cmd.exe (PID: 14932)
- cmd.exe (PID: 16632)
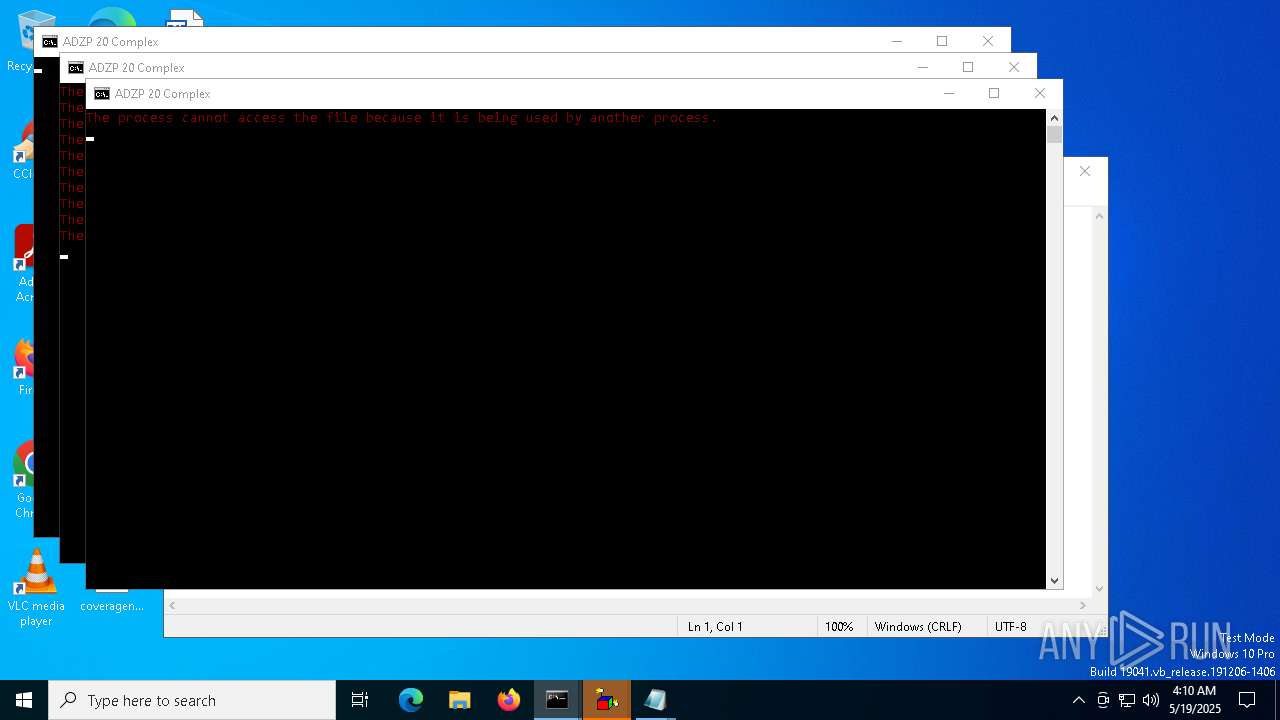
Executable content was dropped or overwritten
- certutil.exe (PID: 2140)
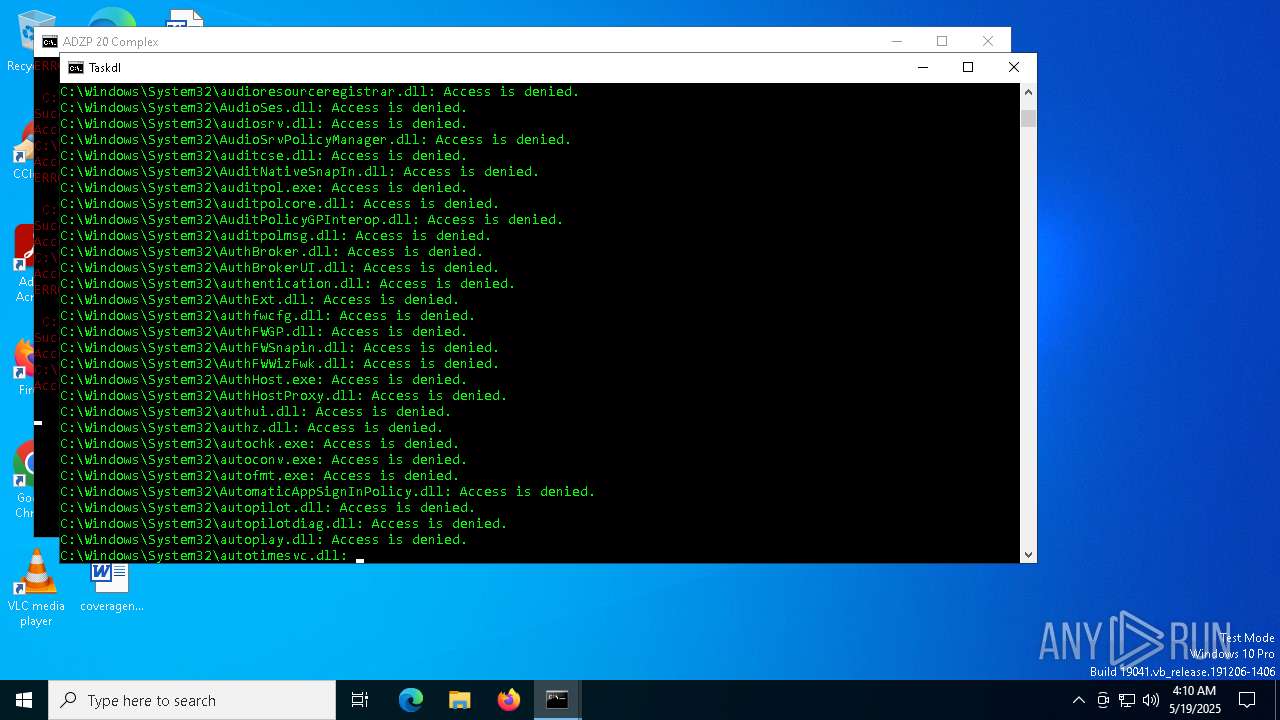
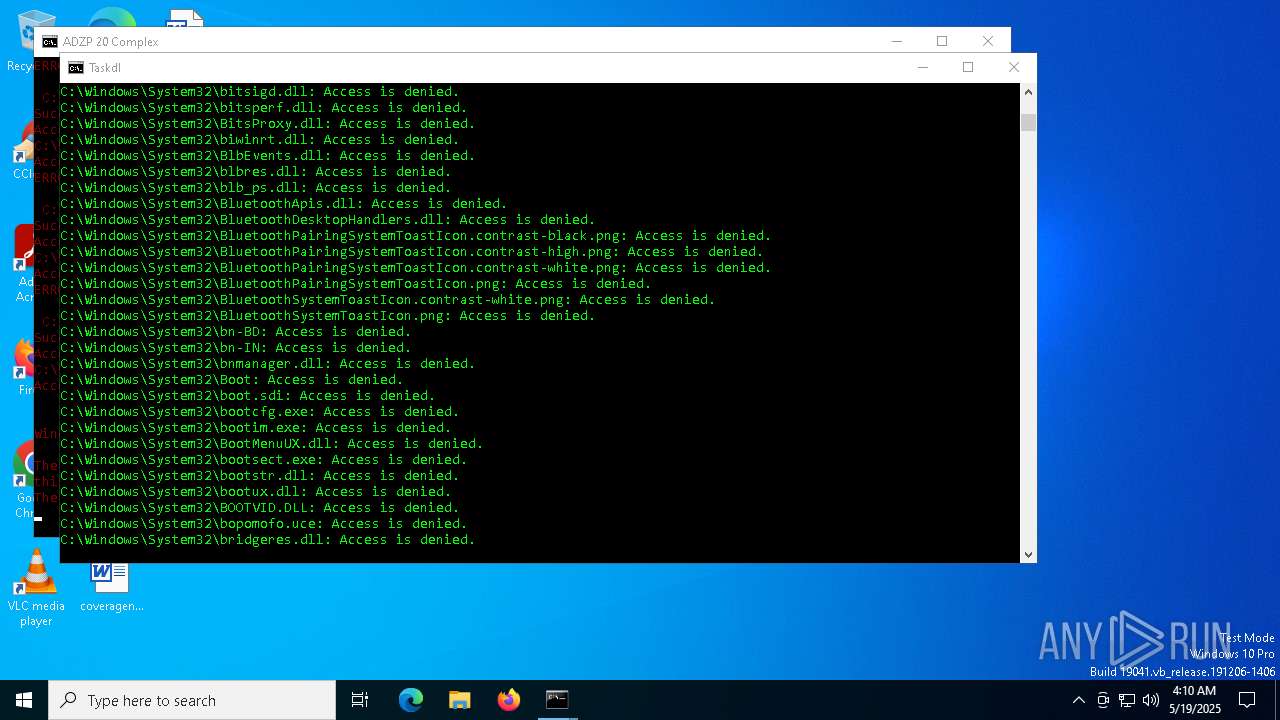
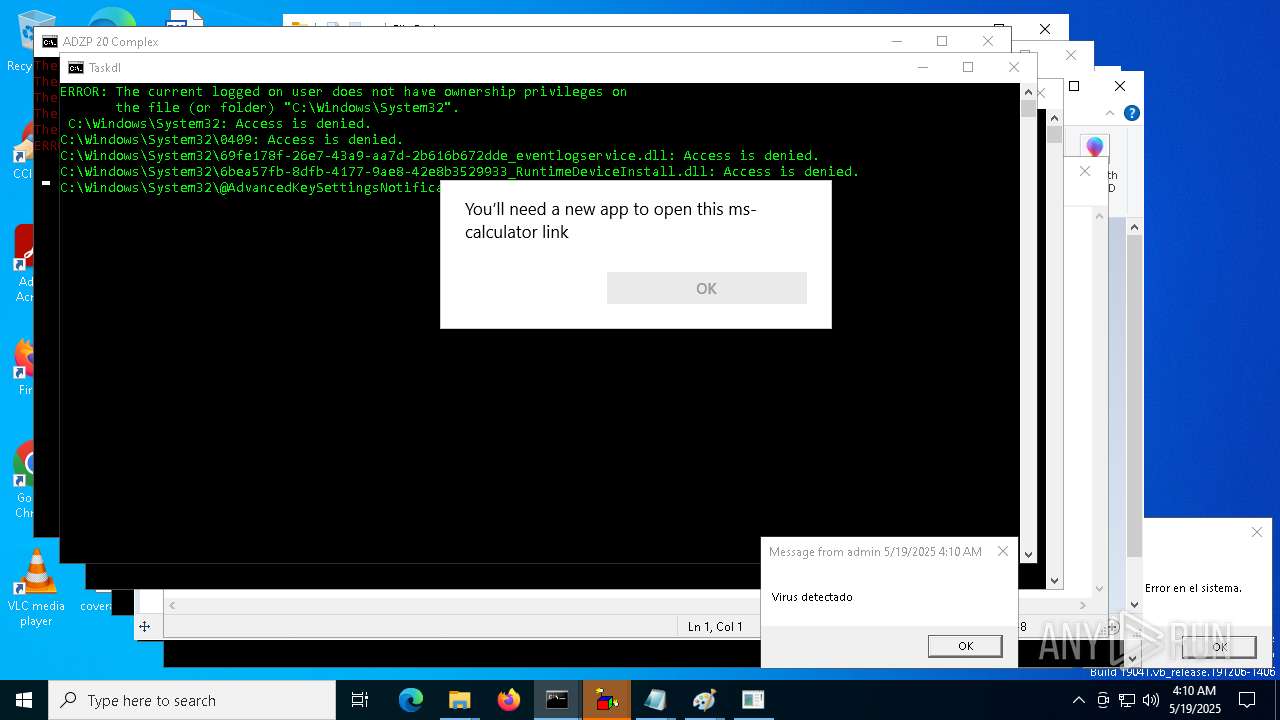
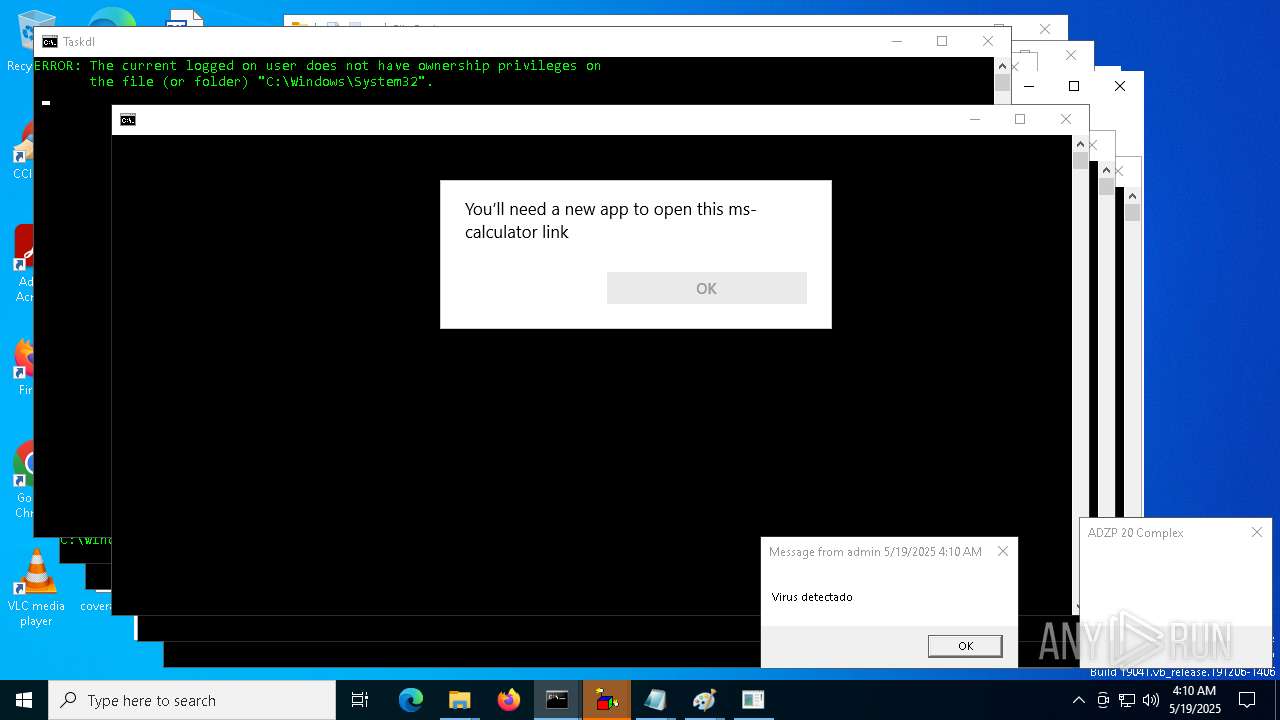
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6028)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 9724)
- cmd.exe (PID: 9776)
- cmd.exe (PID: 9716)
- cmd.exe (PID: 10424)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 12108)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 12320)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 10528)
- cmd.exe (PID: 11168)
- cmd.exe (PID: 11424)
- cmd.exe (PID: 12092)
- cmd.exe (PID: 12276)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 13028)
- cmd.exe (PID: 13996)
- cmd.exe (PID: 15192)
- cmd.exe (PID: 13808)
- cmd.exe (PID: 13264)
- cmd.exe (PID: 14780)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 16356)
- cmd.exe (PID: 8624)
- cmd.exe (PID: 15684)
- cmd.exe (PID: 14284)
- cmd.exe (PID: 17400)
- cmd.exe (PID: 14664)
- cmd.exe (PID: 18112)
- cmd.exe (PID: 8616)
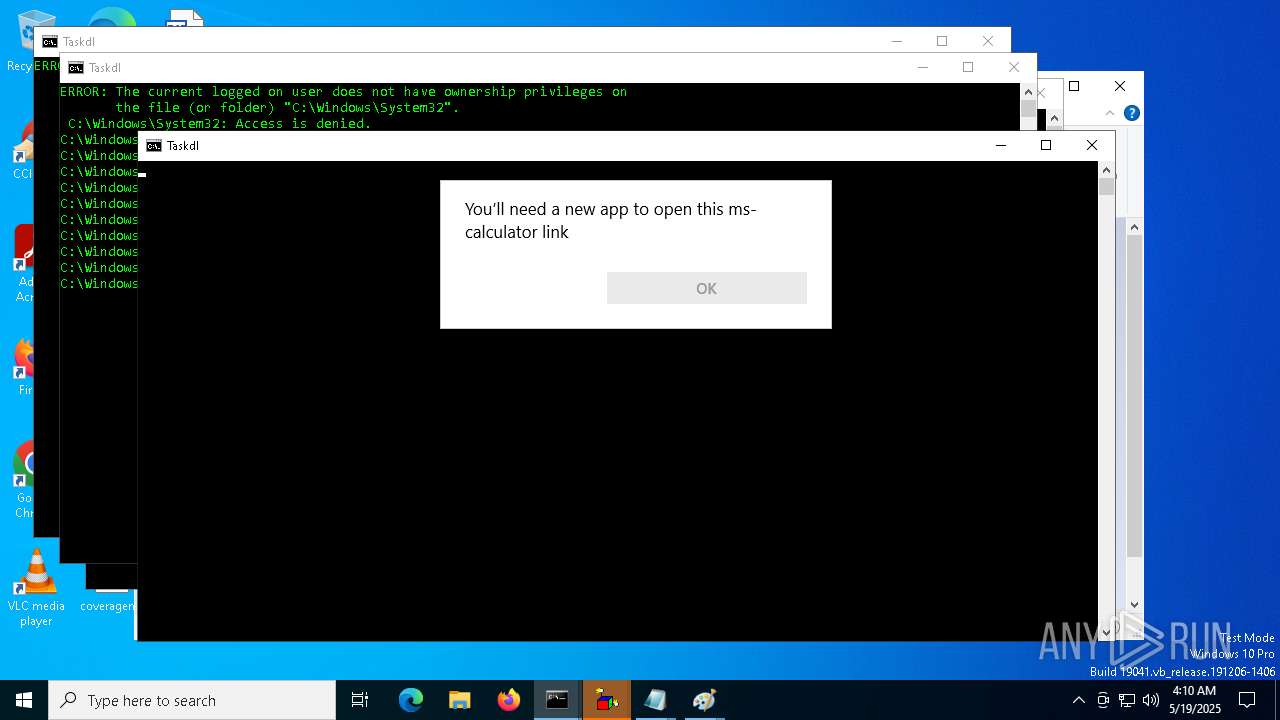
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 9724)
- cmd.exe (PID: 9776)
- cmd.exe (PID: 9716)
- cmd.exe (PID: 10424)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 12108)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 10528)
- cmd.exe (PID: 12320)
- cmd.exe (PID: 12092)
- cmd.exe (PID: 12276)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 11168)
- cmd.exe (PID: 11424)
- cmd.exe (PID: 13028)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 13264)
- cmd.exe (PID: 15192)
- cmd.exe (PID: 13808)
- cmd.exe (PID: 14780)
- cmd.exe (PID: 13996)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 16356)
- cmd.exe (PID: 8624)
- cmd.exe (PID: 14284)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 18112)
- cmd.exe (PID: 15684)
- cmd.exe (PID: 14664)
- cmd.exe (PID: 17400)
- cmd.exe (PID: 16380)
- cmd.exe (PID: 19868)
- cmd.exe (PID: 8616)
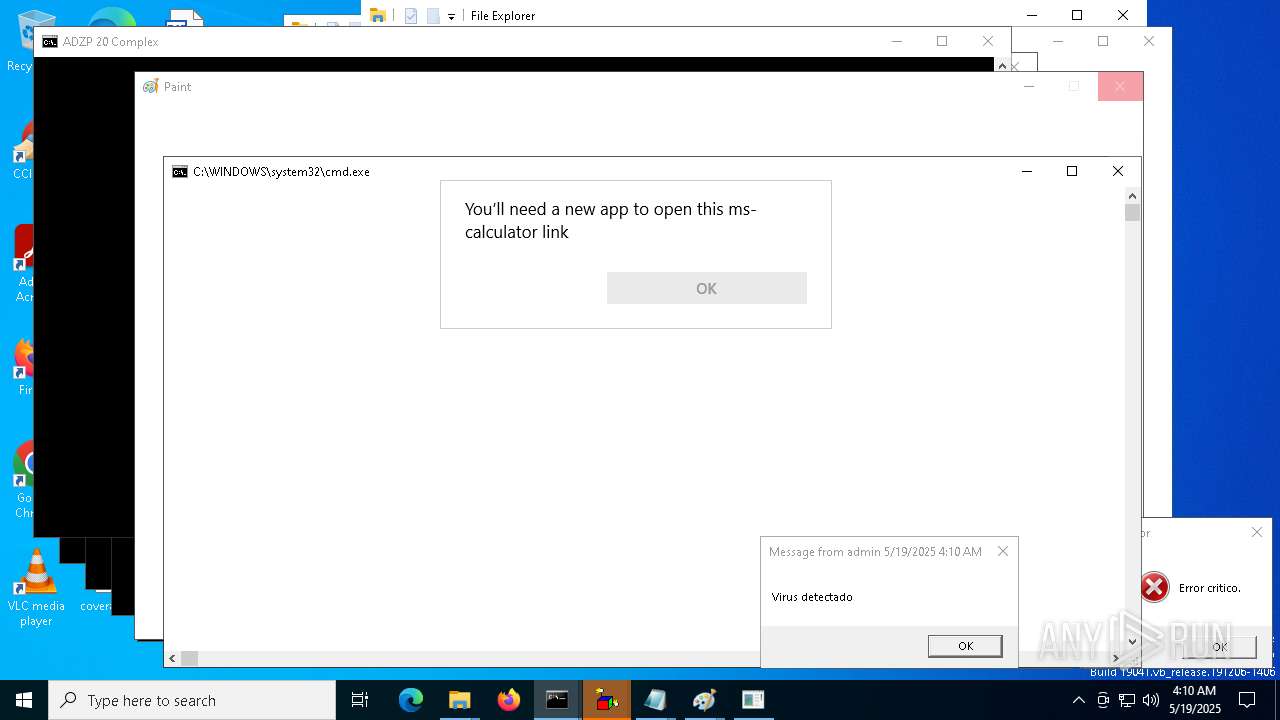
Executing commands from a ".bat" file
- cmd.exe (PID: 1452)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 13028)
- cmd.exe (PID: 13264)
- cmd.exe (PID: 13808)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 13996)
- cmd.exe (PID: 14284)
- cmd.exe (PID: 15684)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 14664)
- cmd.exe (PID: 14932)
- cmd.exe (PID: 16380)
- cmd.exe (PID: 16632)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 1452)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 9744)
The executable file from the user directory is run by the CMD process
- Tasksvc.exe (PID: 2516)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7800)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 13028)
- cmd.exe (PID: 13264)
- cmd.exe (PID: 13996)
- cmd.exe (PID: 13808)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 14284)
- cmd.exe (PID: 15684)
- cmd.exe (PID: 14664)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 16380)
- cmd.exe (PID: 14932)
- cmd.exe (PID: 16632)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 13028)
- cmd.exe (PID: 13264)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 13996)
- cmd.exe (PID: 13808)
- cmd.exe (PID: 14284)
- cmd.exe (PID: 14664)
- cmd.exe (PID: 15684)
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 1452)
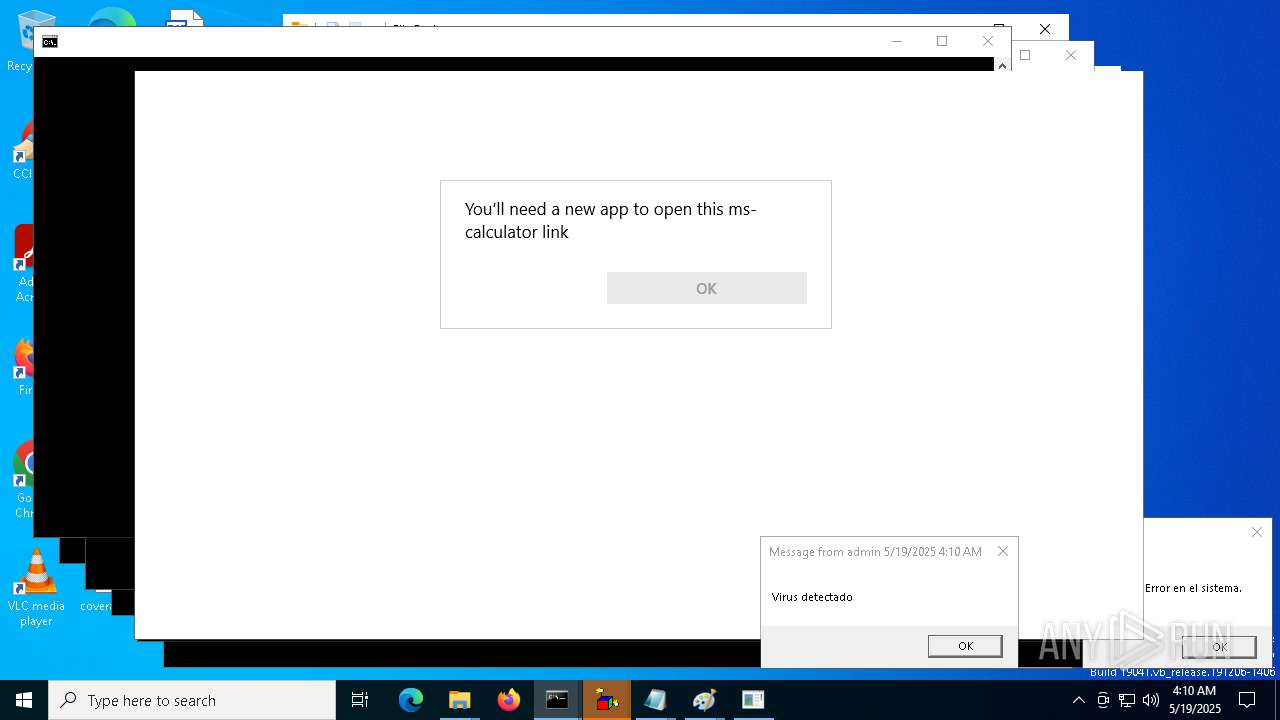
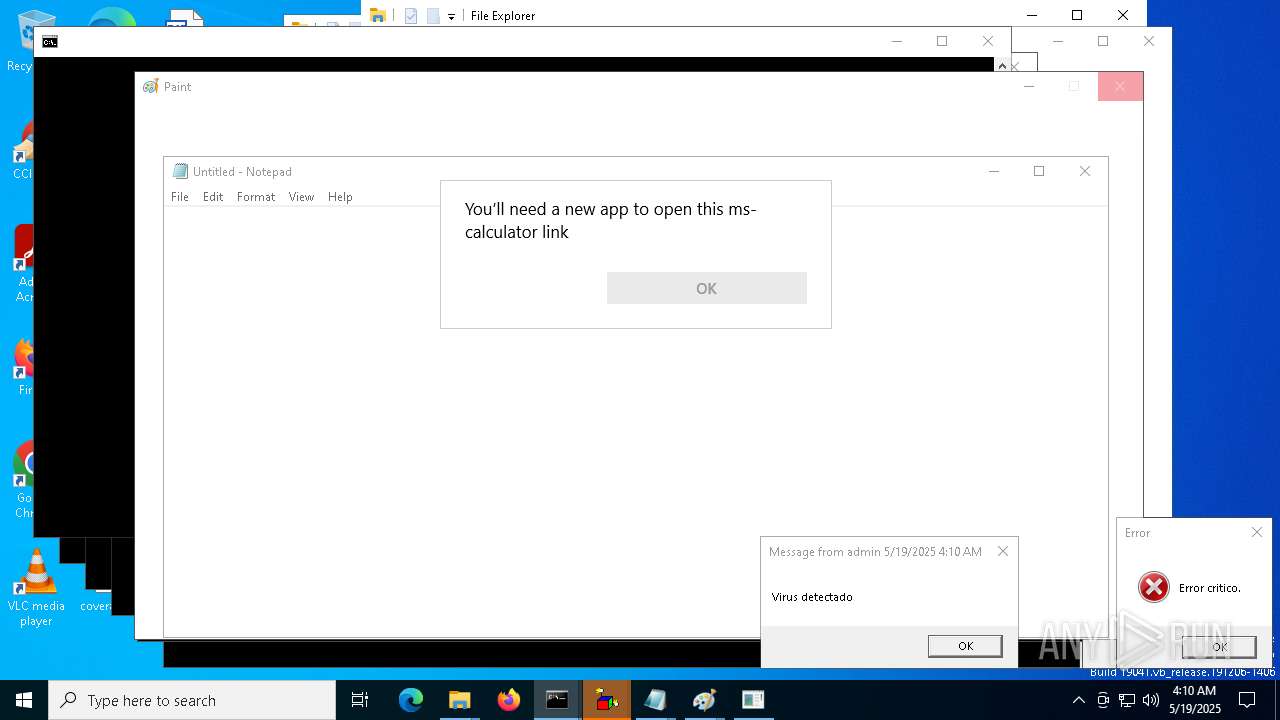
The process executes VB scripts
- cmd.exe (PID: 1452)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 9220)
- cmd.exe (PID: 12008)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 9256)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 1452)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 8288)
The process checks if it is being run in the virtual environment
- icacls.exe (PID: 8980)
- attrib.exe (PID: 8196)
Starts application with an unusual extension
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7392)
INFO
Create files in a temporary directory
- certutil.exe (PID: 2140)
Checks supported languages
- Tasksvc.exe (PID: 2516)
Reads security settings of Internet Explorer
- calc.exe (PID: 7480)
- calc.exe (PID: 7880)
- calc.exe (PID: 8128)
- OpenWith.exe (PID: 6652)
- OpenWith.exe (PID: 8164)
- OpenWith.exe (PID: 812)
- calc.exe (PID: 644)
- calc.exe (PID: 8168)
- calc.exe (PID: 8972)
- calc.exe (PID: 9152)
- calc.exe (PID: 9600)
- calc.exe (PID: 9612)
Reads the computer name
- Tasksvc.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
1 046
Monitored processes
919
Malicious processes
19
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | attrib -r -a -s -h "C:\WINDOWS\System32\winload.exe" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | attrib -r -a -s -h *.* | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | calc | C:\Windows\System32\calc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableLockWorkstation /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | netsh advfirewall set allprofiles state off | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | takeown /f "C:\WINDOWS\System32\winload.exe" | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | rundll32 user32.dll, SetCursorPos | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | takeown /f "C:\WINDOWS\System32\winresume.exe" | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | WScript Informacion.vbs | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
91 457
Read events
91 111
Write events
346
Delete events
0
Modification events
| (PID) Process: | (1628) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | EthernetKill |
Value: C:\Users\admin\AppData\Local\Temp\EthernetKiller.cmd | |||
| (PID) Process: | (7480) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7480) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7480) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7480) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7404) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7880) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8128) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8128) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8128) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
2
Suspicious files
0
Text files
42
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
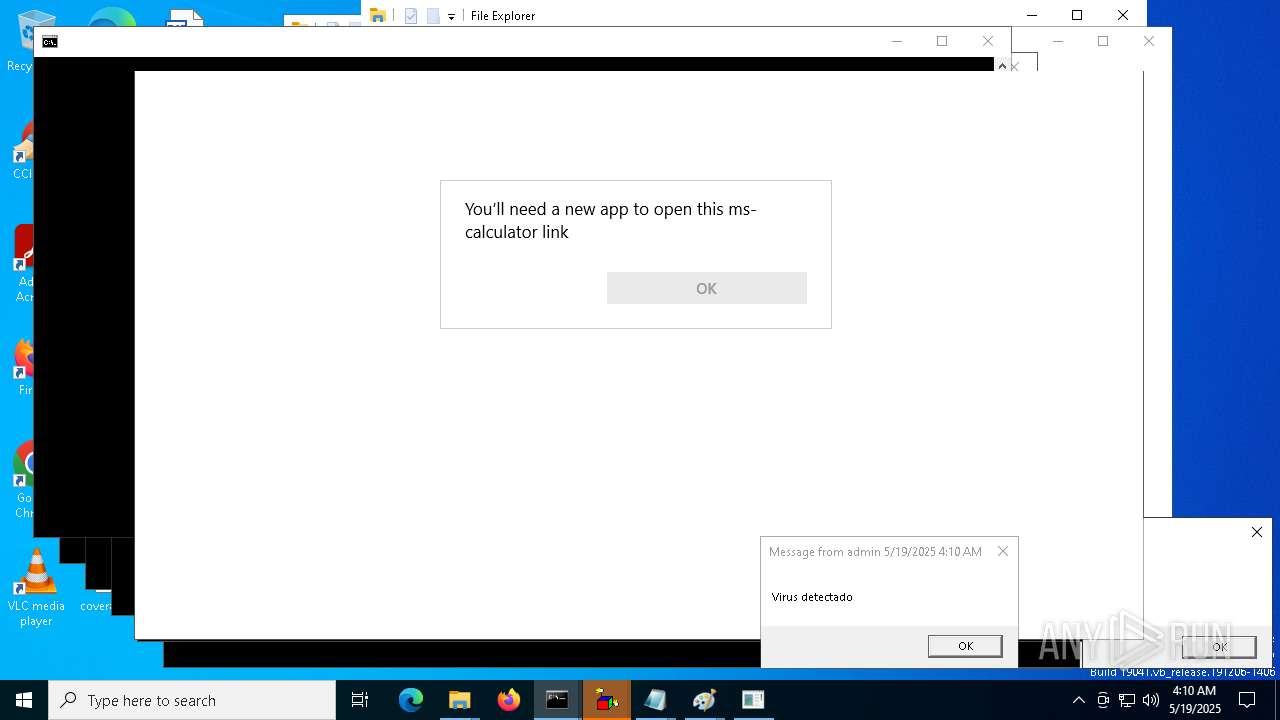
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Advertencia.vbs | text | |
MD5:08121EA7E3B2EB7EDFC85252B937AAEB | SHA256:31CD4463ECC62DC846DBAEE0A5446D4BF11100BEFF1B01AE88E234B6C29329C2 | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Virus.rar | text | |
MD5:BAEB8FE7AB37CF5641B40448121314C1 | SHA256:06ACAC09633EECD11E6F633977EE821E7D614B9953D1FE1A193133C41A46025C | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ErrorCritico.vbs | text | |
MD5:08121EA7E3B2EB7EDFC85252B937AAEB | SHA256:31CD4463ECC62DC846DBAEE0A5446D4BF11100BEFF1B01AE88E234B6C29329C2 | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Virus.sys | text | |
MD5:9E04B2A5495B7B8E01D2A0A5E496ABC6 | SHA256:88E21213C9ACDC37907809B64A8FB0264010DD9470E737E24030159FE3DCCC91 | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Autorun.inf | text | |
MD5:9A9FED65AE5AECB2E2723DCCF0F0B34E | SHA256:B9EB9A01994285B8A10189321D0CF6055AD92AE659D6603F7D1FE835F39CA1D2 | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\EthernetKiller.cmd | text | |
MD5:9905E5A33C6EDD8EB5F59780AFBF74DE | SHA256:C134B2F85415BA5CFCE3E3FE4745688335745A9BB22152AC8F5C77F190D8AEE3 | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Bytebeat.Shingapi.tmp | text | |
MD5:0BF50EA68E7B825549C09F0E81EA1E41 | SHA256:54530C881B0D32EA17870D396712ABF94589F906AC294C1D1893A68DE4E522F4 | |||
| 2140 | certutil.exe | C:\Users\admin\AppData\Local\Temp\Tasksvc.exe | executable | |
MD5:3A5168287A2BED6D6D26737DA9AF294B | SHA256:01ADE58CEB0B9442A0C5C5BB27B781E748A86347FE0708ED9DE26B337829E294 | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Virus.ini | text | |
MD5:9BD39A78B4FA9ADF21BFE2020B476F30 | SHA256:2D55884D3C9DDA7C90866755DEF378BA5437CA731B9D1D1EB3495188B79D5D8B | |||
| 1452 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Virus.exe | text | |
MD5:0E4E4DAD9B6D7FEBA8BC3A096293F5A5 | SHA256:A93DD2C40E523577E9FEA9609CA5C4745CEAE7D95205B9C960B32AF1A4F49735 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
15
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
12432 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
12432 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
12432 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
12432 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
12432 | SIHClient.exe | 40.69.42.241:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |