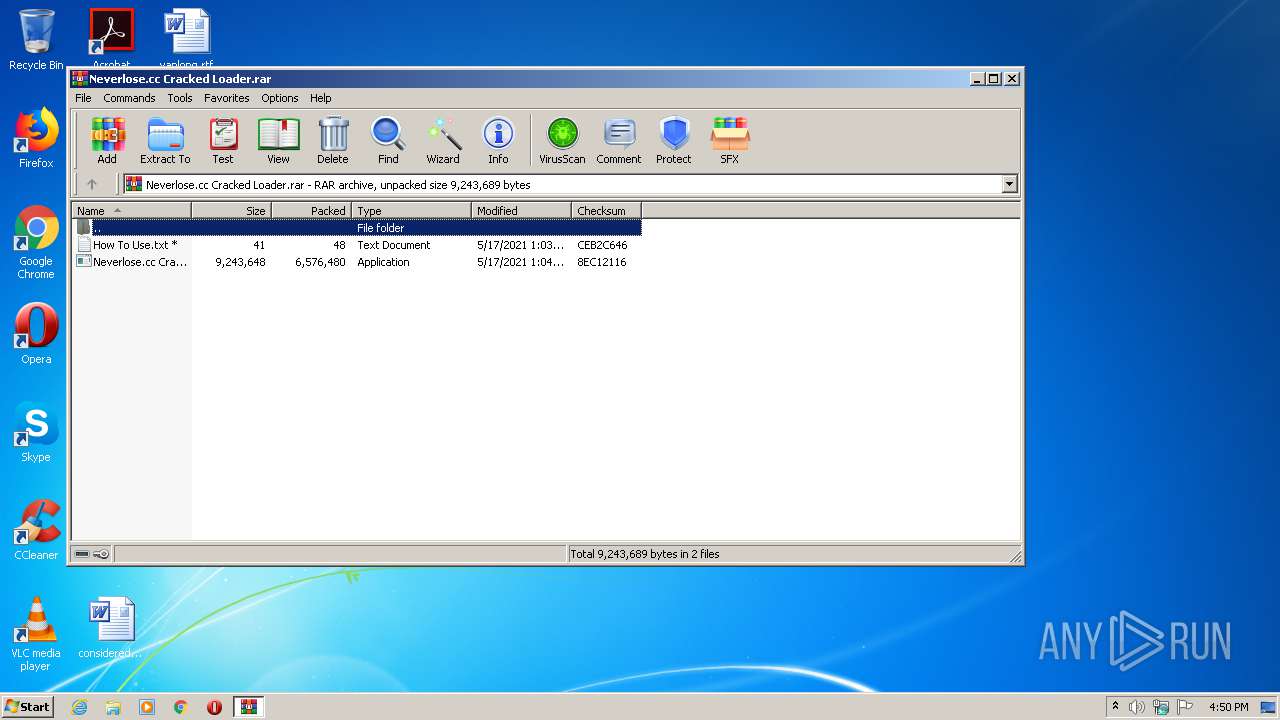
| File name: | Neverlose.cc Cracked Loader.rar |
| Full analysis: | https://app.any.run/tasks/36741049-6929-4c03-a171-f6c342d089b3 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2021, 15:50:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7994DDEBBFD7AFCBB00D421D968827B2 |
| SHA1: | A1A08EDCA359C442819742DE55A03E930205FC08 |
| SHA256: | D12C4158C844BF0AA5313332793D012733985E0CFE2EFB5381CFD67B73504367 |
| SSDEEP: | 196608:cebsi64awWa7XIetBAlyALR+4+wwy67r8/lrjKrrlNc3zw:9bsobttByyVxBr8/lolNmzw |
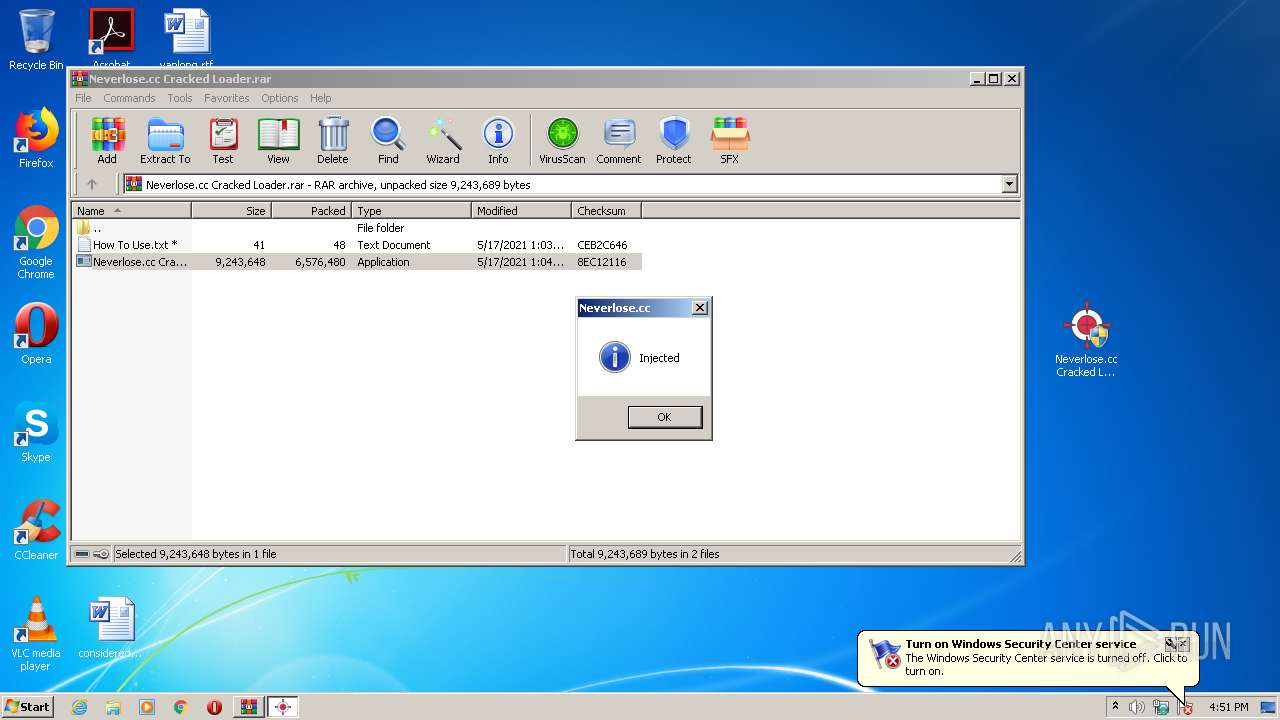
MALICIOUS
Application was dropped or rewritten from another process
- Neverlose.cc Cracked Loader.exe (PID: 1380)
- Neverlose.cc Cracked Loader.exe (PID: 2500)
- svchosts.exe (PID: 3512)
- detecterfn.exe (PID: 1688)
- crypted.exe (PID: 3888)
- AdvancedRun.exe (PID: 3452)
- d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe (PID: 3556)
- AdvancedRun.exe (PID: 3624)
Drops executable file immediately after starts
- Neverlose.cc Cracked Loader.exe (PID: 1380)
UAC/LUA settings modification
- reg.exe (PID: 996)
- crypted.exe (PID: 3888)
- d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe (PID: 3556)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2440)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 2932)
- cmd.exe (PID: 1548)
Modifies hosts file to block updates
- svchosts.exe (PID: 3512)
Writes to the hosts file
- svchosts.exe (PID: 3512)
Uses Task Scheduler to autorun other applications
- svchosts.exe (PID: 3512)
Changes settings of System certificates
- detecterfn.exe (PID: 1688)
Writes to a start menu file
- crypted.exe (PID: 3888)
Disables Windows Defender
- crypted.exe (PID: 3888)
Changes the autorun value in the registry
- crypted.exe (PID: 3888)
- d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe (PID: 3556)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 916)
- Neverlose.cc Cracked Loader.exe (PID: 1380)
- crypted.exe (PID: 3888)
- svchosts.exe (PID: 3512)
- d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe (PID: 3556)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 916)
- svchosts.exe (PID: 3512)
- Neverlose.cc Cracked Loader.exe (PID: 1380)
Drops a file with too old compile date
- Neverlose.cc Cracked Loader.exe (PID: 1380)
- crypted.exe (PID: 3888)
Drops a file that was compiled in debug mode
- Neverlose.cc Cracked Loader.exe (PID: 1380)
- crypted.exe (PID: 3888)
- svchosts.exe (PID: 3512)
- d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe (PID: 3556)
Executes PowerShell scripts
- svchosts.exe (PID: 3512)
- crypted.exe (PID: 3888)
- d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe (PID: 3556)
Creates files in the Windows directory
- svchosts.exe (PID: 3512)
- crypted.exe (PID: 3888)
Uses REG.EXE to modify Windows registry
- svchosts.exe (PID: 3512)
Low-level read access rights to disk partition
- reagentc.exe (PID: 960)
Creates files in the user directory
- powershell.exe (PID: 2800)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 2404)
- powershell.exe (PID: 3792)
- crypted.exe (PID: 3888)
- powershell.exe (PID: 2280)
- powershell.exe (PID: 4064)
- powershell.exe (PID: 2612)
- powershell.exe (PID: 4024)
- powershell.exe (PID: 2428)
- powershell.exe (PID: 256)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 840)
- powershell.exe (PID: 3964)
- powershell.exe (PID: 2980)
- powershell.exe (PID: 328)
- powershell.exe (PID: 3388)
Starts CMD.EXE for commands execution
- AdvancedRun.exe (PID: 3452)
- crypted.exe (PID: 3888)
- AdvancedRun.exe (PID: 3624)
- d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe (PID: 3556)
Starts SC.EXE for service management
- cmd.exe (PID: 2932)
- cmd.exe (PID: 1548)
Reads Environment values
- detecterfn.exe (PID: 1688)
Starts itself from another location
- crypted.exe (PID: 3888)
Adds / modifies Windows certificates
- detecterfn.exe (PID: 1688)
Creates executable files which already exist in Windows
- crypted.exe (PID: 3888)
INFO
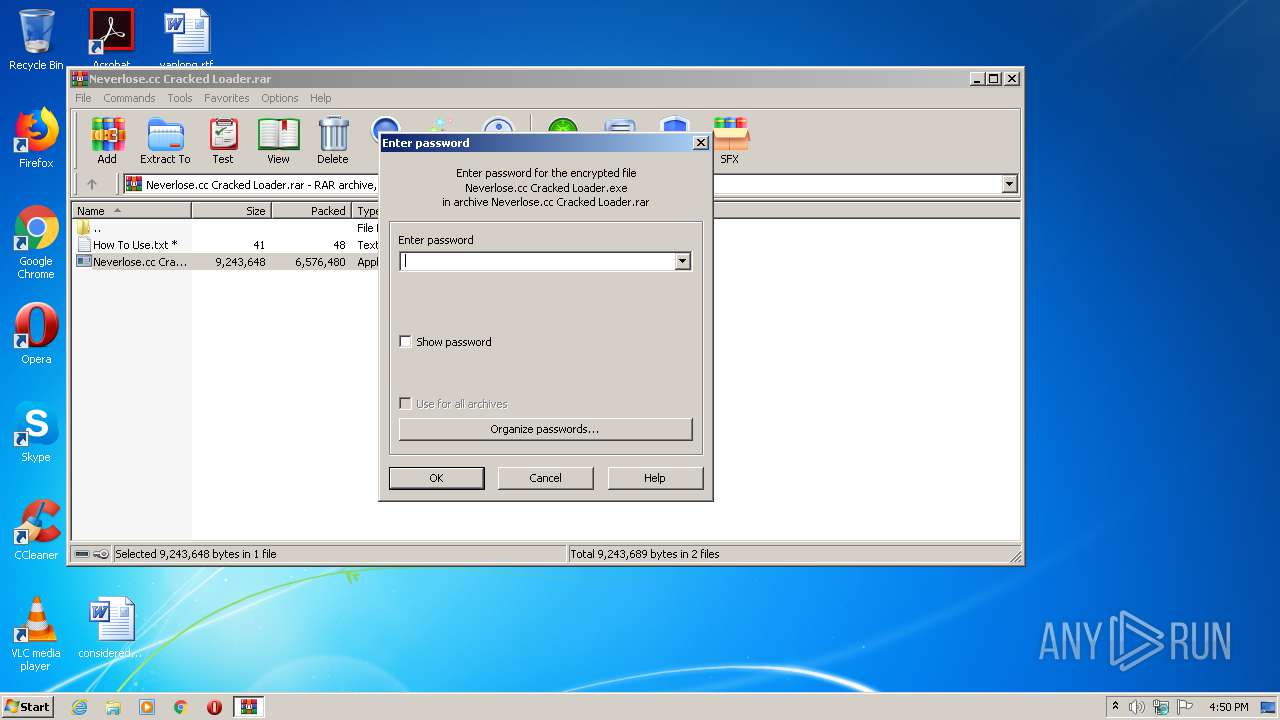
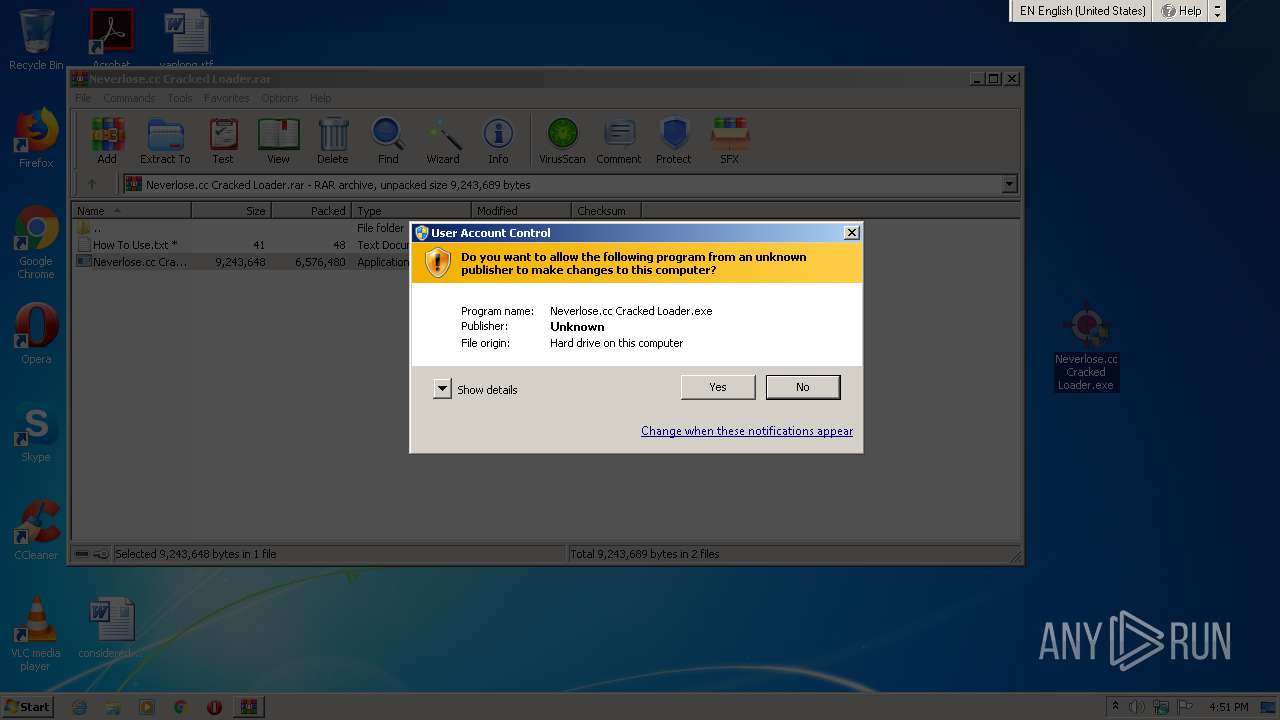
Manual execution by user
- Neverlose.cc Cracked Loader.exe (PID: 1380)
- Neverlose.cc Cracked Loader.exe (PID: 2500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
147
Monitored processes
81
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Windows\Resources\Themes\2d2b2I4080fffI7p989t\svchost.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | crypted.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Windows\Resources\Themes\2d2b2I4080fffI7p989t\svchost.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | sc config Sense start= disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | sc stop SecurityHealthService | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | sc stop WdiSystemHost | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | sc stop Sense | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 840 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | d9f4cza91c4aJb1eK154d1f3C3b8eQT34c7f444O1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | sc config wuauserv start= disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
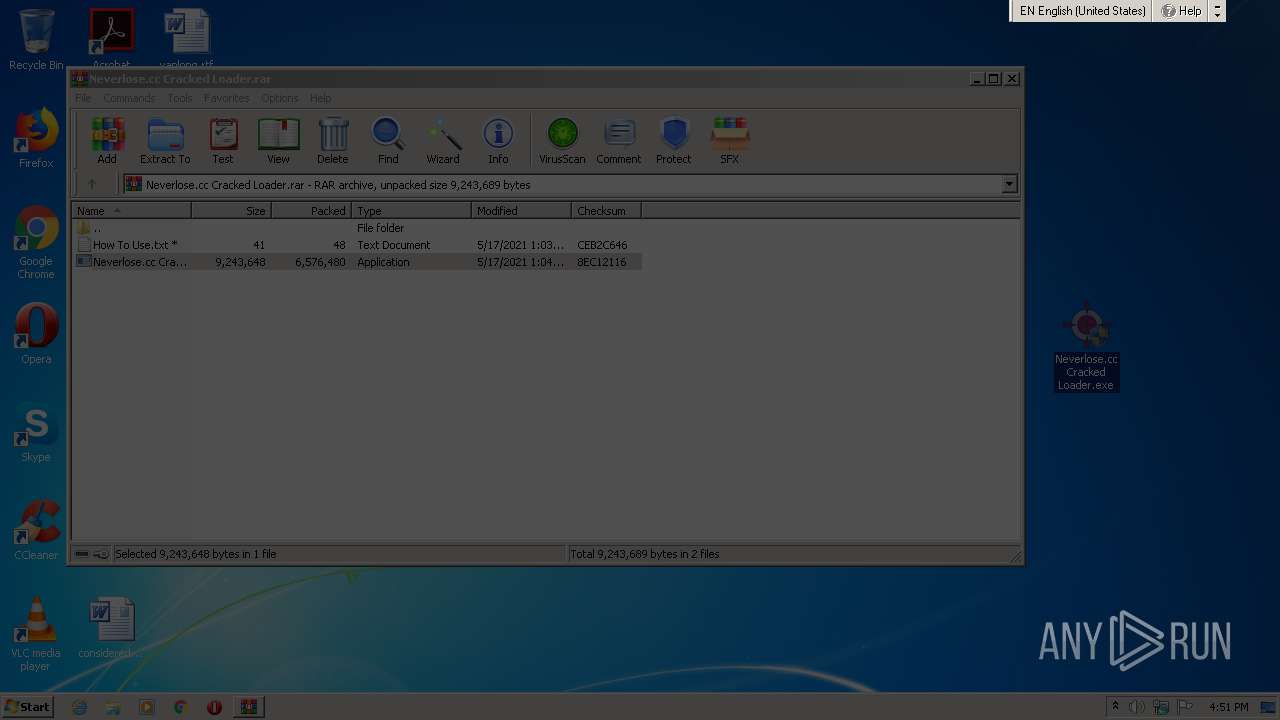
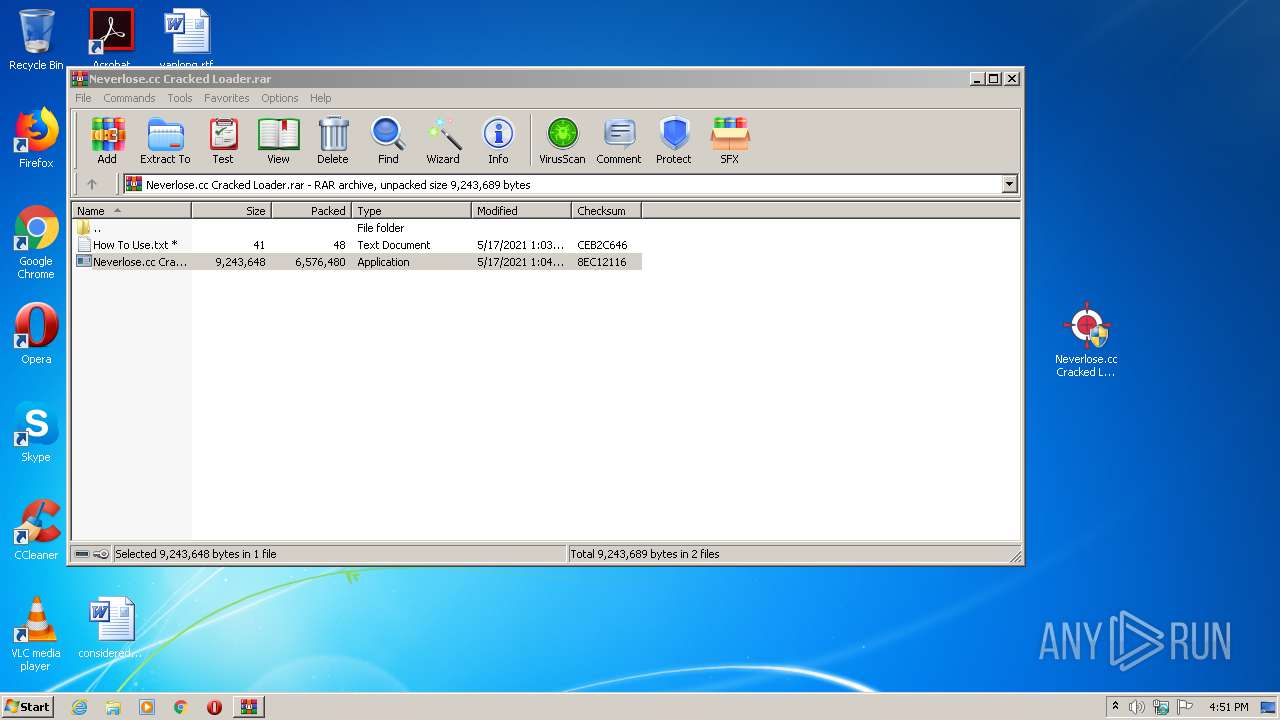
| 916 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Neverlose.cc Cracked Loader.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 960 | reagentc.exe /disable | C:\Windows\system32\reagentc.exe | — | svchosts.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Recovery Agent Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 486
Read events
5 402
Write events
1 064
Delete events
20
Modification events
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Neverlose.cc Cracked Loader.rar | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
12
Suspicious files
30
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | reagentc.exe | C:\Windows\system32\Recovery\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2404 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FM2ZH3001NQAYV706CTH.temp | — | |
MD5:— | SHA256:— | |||
| 2800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FH82ZM8DXBHNLBI3OD4J.temp | — | |
MD5:— | SHA256:— | |||
| 3612 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0MGIX2UIVK5TLJ9HMYEW.temp | — | |
MD5:— | SHA256:— | |||
| 4000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DJQME1KOZDB6ZT0LJG3P.temp | — | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NLGRMRZTBOECT797QCG7.temp | — | |
MD5:— | SHA256:— | |||
| 1380 | Neverlose.cc Cracked Loader.exe | C:\Users\admin\AppData\Local\Temp\xmr1.exe | executable | |
MD5:— | SHA256:— | |||
| 1380 | Neverlose.cc Cracked Loader.exe | C:\Users\admin\AppData\Local\Temp\svchosts.exe | executable | |
MD5:— | SHA256:— | |||
| 1380 | Neverlose.cc Cracked Loader.exe | C:\Users\admin\AppData\Local\Temp\crypted.exe | executable | |
MD5:— | SHA256:— | |||
| 1380 | Neverlose.cc Cracked Loader.exe | C:\Users\admin\AppData\Local\Temp\etc1.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | applaunch.exe | 78.180.177.193:6606 | geceler31.duckdns.org | Turk Telekom | TR | malicious |
1688 | detecterfn.exe | 162.159.136.232:443 | discord.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
discord.com |
| whitelisted |
geceler31.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
Process | Message |
|---|---|
crypted.exe | b67bf2cd-dfc8-4f8f-9b2c-7f4ec2cc81b3
|
crypted.exe | a8aab37a-50bb-446b-8bee-31afdbe2b214
|
crypted.exe | c278d2a6-fe19-4d32-95bc-bc88a192813e
|
crypted.exe | dd24cde0-1548-4e04-9199-a5f3793b5f65
|
crypted.exe | f686fcd4-611e-4e70-ad5b-bda036ecb1d2
|
crypted.exe | 8f6948da-772a-457a-b19d-3130e3181219
|
crypted.exe | 435be3c8-0426-41d5-824d-bf5ad6520ca8
|
crypted.exe | 291a2b98-81f8-4641-81fc-52e5d2fb2fba
|
crypted.exe | 505d616a-ae47-4f29-8f79-073d9595e17e
|
crypted.exe | f3aafd7c-12e5-42fe-ac26-bf650256bfae
|