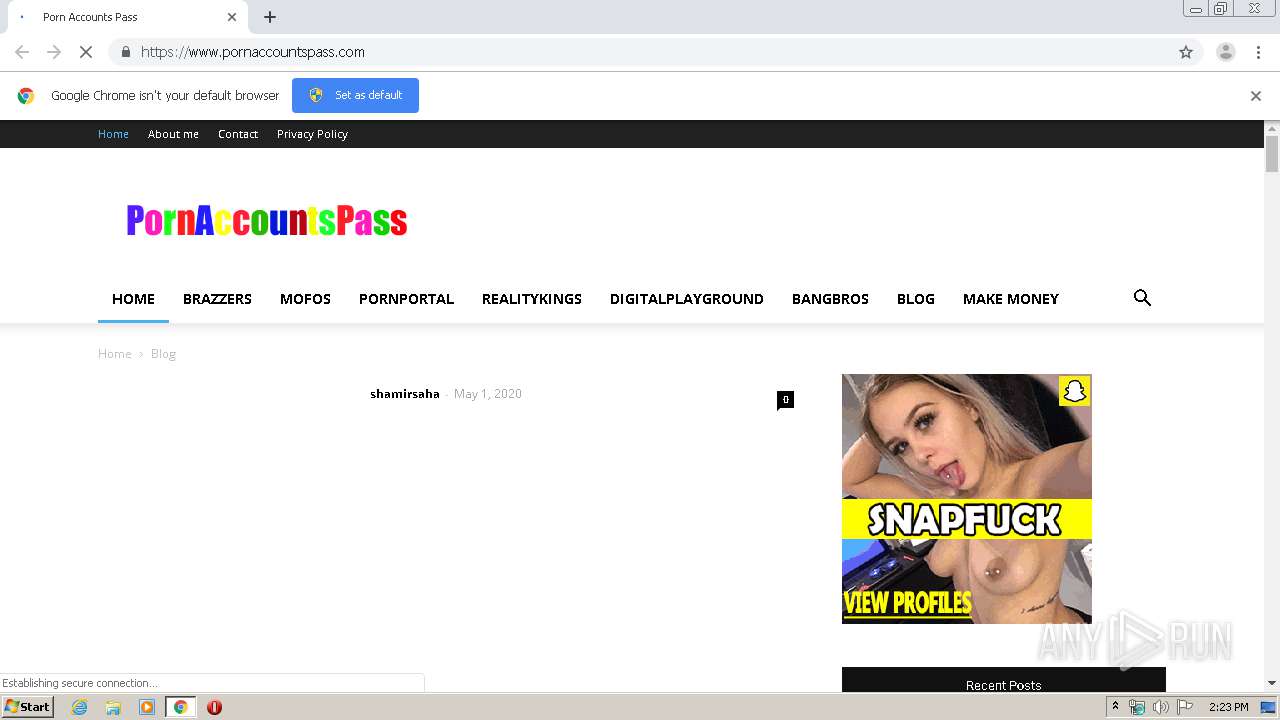
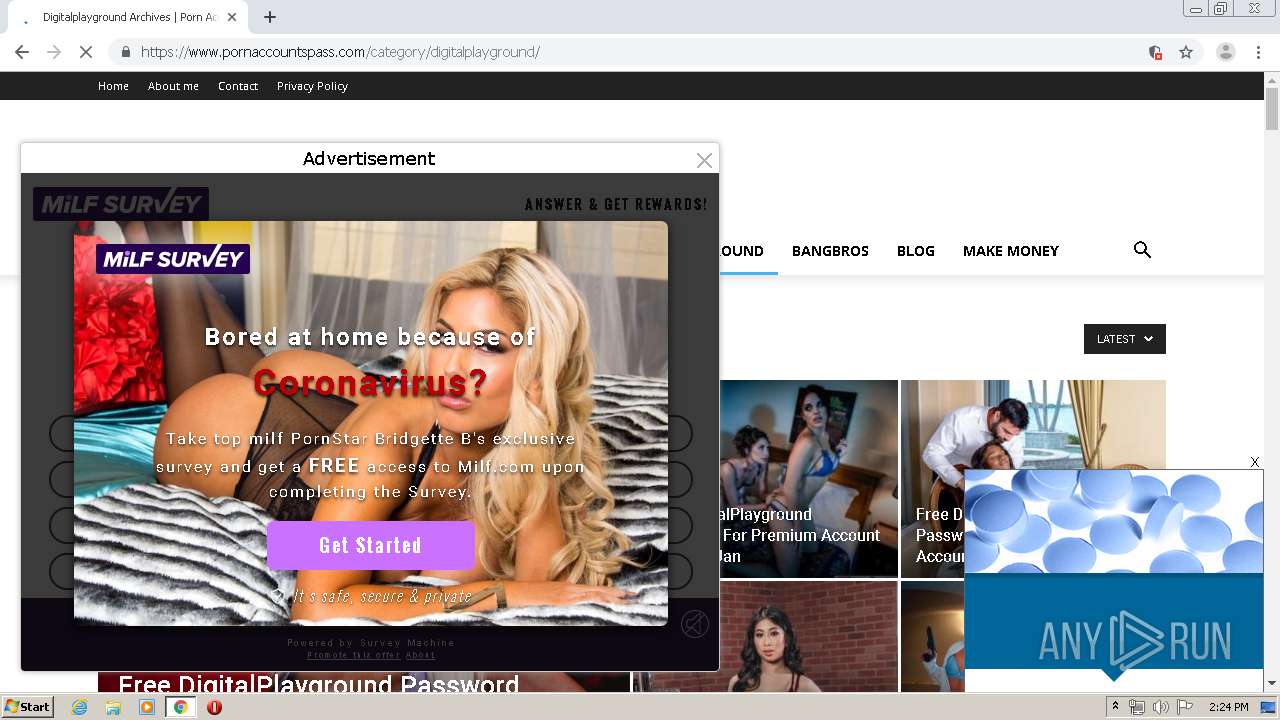
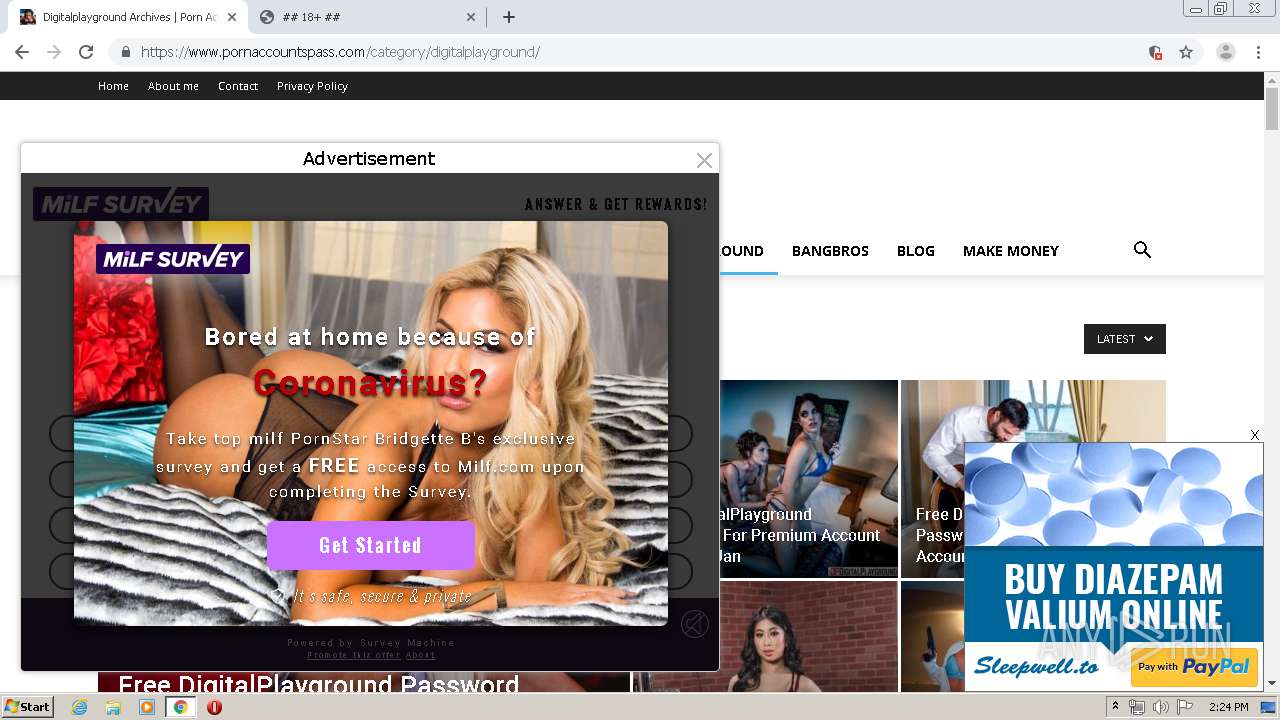
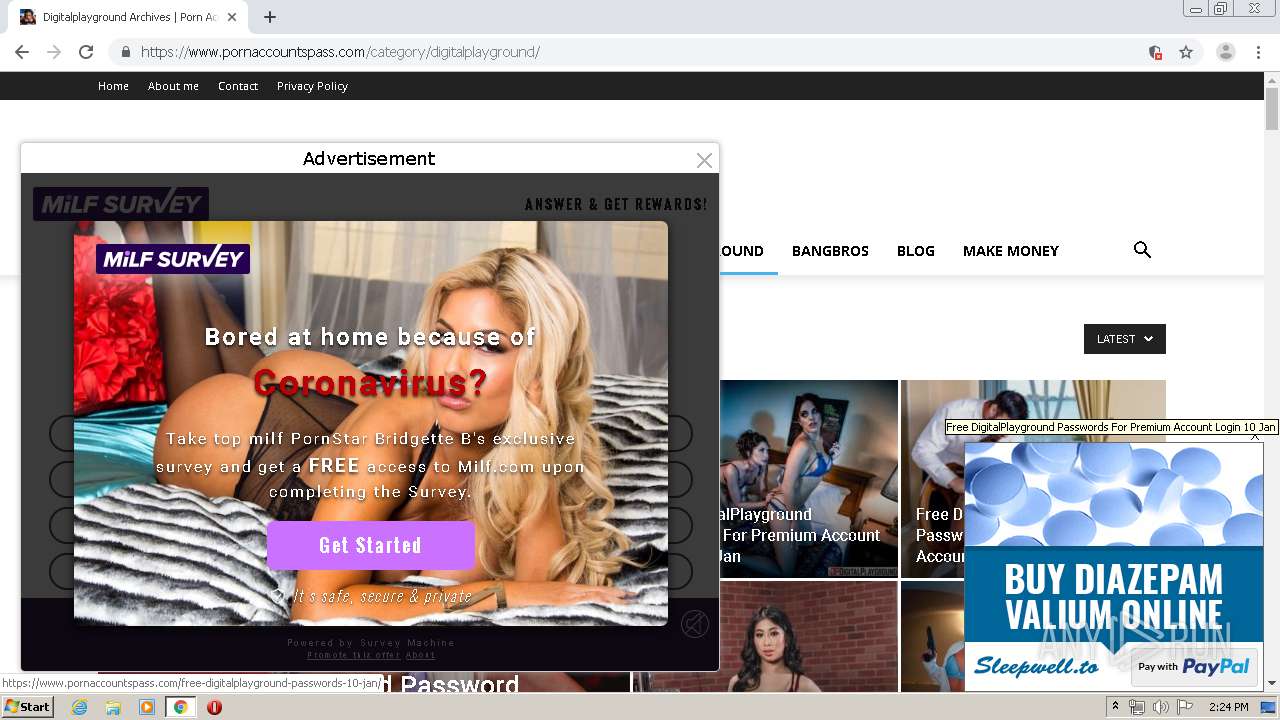
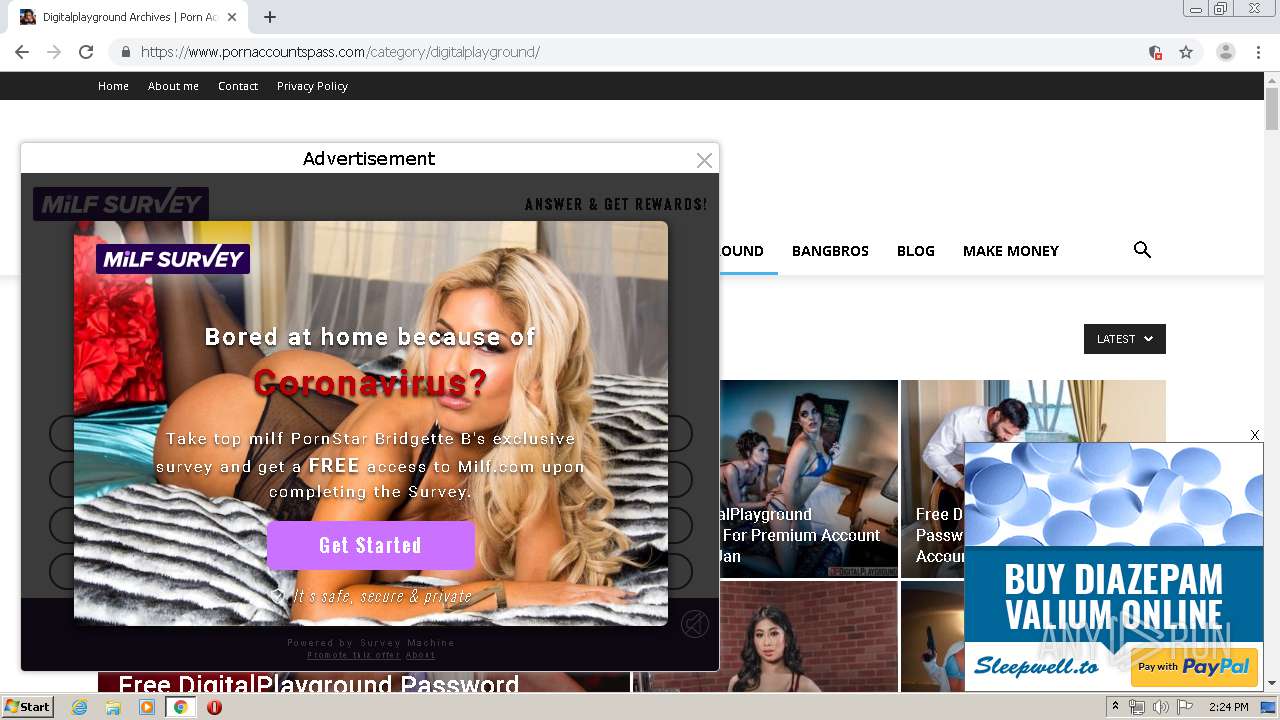
| URL: | https://www.pornaccountspass.com/ |
| Full analysis: | https://app.any.run/tasks/0fe96463-b60e-4f27-872b-1f8f6465eb29 |
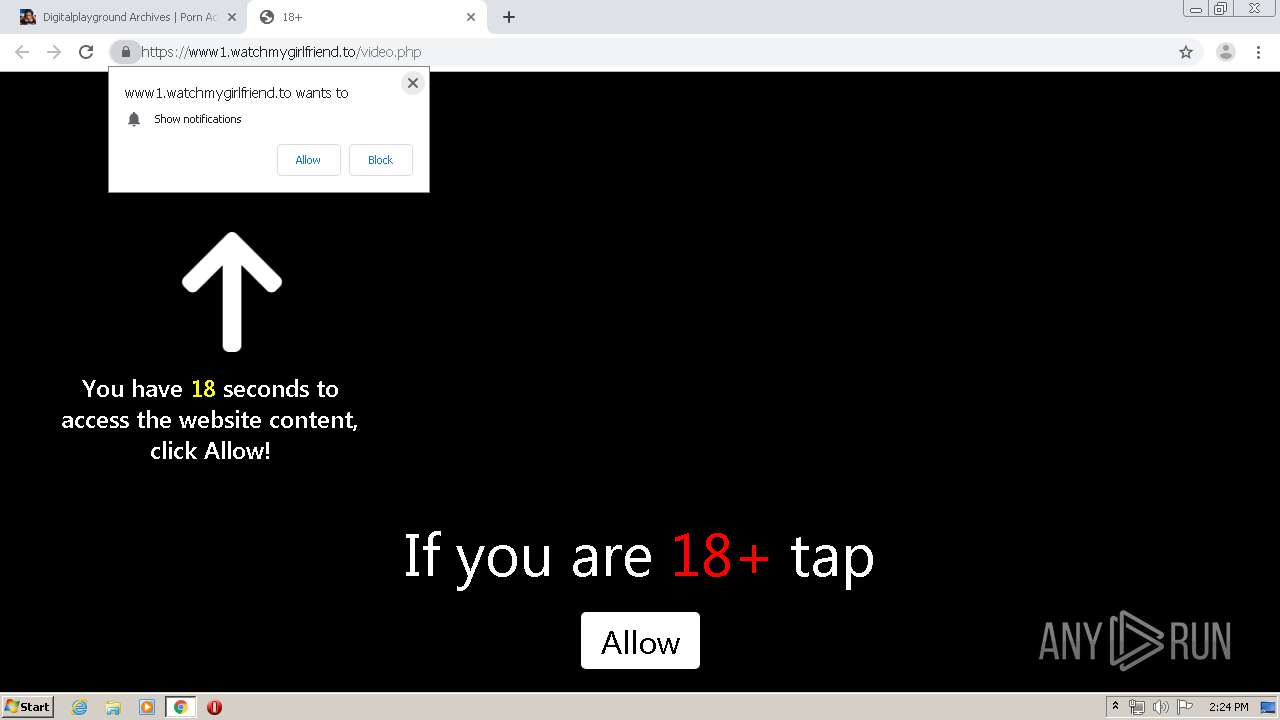
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2020, 13:23:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5672BC557CC0A4A854C33B8E9C9F6290 |
| SHA1: | ECA0AF02BE29681A489097512FC6E390716304D6 |
| SHA256: | D10CA8053202E661F925835681DA58F0BA4455414B8000FB361E9704145D4B19 |
| SSDEEP: | 3:N8DSLDBRLGKIK:2OLDHKK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2808)
INFO
Application launched itself
- chrome.exe (PID: 2808)
Reads the hosts file
- chrome.exe (PID: 2808)
- chrome.exe (PID: 2184)
Creates files in the user directory
- chrome.exe (PID: 2808)
Reads settings of System Certificates
- chrome.exe (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
79
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9646475050839230609 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3635792656288525744 --mojo-platform-channel-handle=5928 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16900205576352869271 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4849106091803140506 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15917882517340633244 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7861369199309382982 --mojo-platform-channel-handle=5020 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13434285579850715737 --renderer-client-id=65 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13325751092775596131 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=598424295175777242 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13368416241192923481,5766464371782916216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1435851970893644386 --renderer-client-id=53 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
929
Read events
792
Write events
132
Delete events
5
Modification events
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2808-13233590617844125 |
Value: 259 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
156
Text files
304
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EB8005A-AF8.pma | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d3686922-6e47-4f50-a3d3-8fda979a19a2.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa87379.TMP | text | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa87369.TMP | text | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa875cb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
177
DNS requests
84
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2184 | chrome.exe | GET | 302 | 174.137.155.139:80 | http://clk.rtpdn11.com/click?i=zo98HExVPrw_0 | US | — | — | malicious |
2184 | chrome.exe | GET | 302 | 174.137.155.139:80 | http://clk.rtpdn11.com/click2?i=zo98HExVPrw_0&j=rv%3Db%26ss%3D1280x720%26ws%3D1280x620%26wp%3D0x0%26ce%3D1%26ck%3Djc%26cv%3D9537%26cs%3D1%26fr%3D0%26hc%3D0%26fl%3Dnull%26jv%3Dnull%26sc%3D24%26hr%3D3%26rf%3Dsp.popcash.net%26lo%3Dtq.adventurefeeds.com%26mb%3D0%26hb%3D0%26pl%3DWin32%26ua%3DMozilla%252F5.0%2B%28Windows%2BNT%2B6.1%29%2BAppleWebKit%252F537.36%2B%28KHTML%252C%2Blike%2BGecko%29%2BChrome%252F75.0.3770.100%2BSafari%252F537.36%26tp%3D597%26nd%3D0%26to%3Dnull%26er%3D%26pm%3D100 | US | — | — | malicious |
2184 | chrome.exe | GET | 302 | 23.235.244.225:80 | http://prpops.com/p/o26g/direct/t:source-41?prc_c=1589117068&prc_r=eyJIVFRQX1VTRVJfQUdFTlQiOiJNb3ppbGxhXC81LjAgKFdpbmRvd3MgTlQgNi4xKSBBcHBsZVdlYktpdFwvNTM3LjM2IChLSFRNTCwgbGlrZSBHZWNrbykgQ2hyb21lXC83NS4wLjM3NzAuMTAwIFNhZmFyaVwvNTM3LjM2In0=&prc_h=3583caa7f35607cc1a6579cdf7e99a66df14aba0be8edc8f175e16dc3b4e8dee&pr_tsid=0d5a5cb697d7592f8af9c5318865b151d861150b5ecc16307a8e829f09fba3e8&pr_tsids=1b30dce71318fe3aa7531b01ab903785efe52cfbdb91e97c84c97a76ddafd490&prc_obfjs=f5ef35210db14fb974879a00a7bb36fb340e22ada105a2af2d3d3dec01c8655a&prc_isIframe1=false&prc_jw=1280&prc_jh=620&prc_jow=1280&prc_joh=692&prc_jsw=1280&prc_jsh=720&prc_jwaw=1280&prc_jwah=692&prc_jnp=Win32&prc_jnv=Google%20Inc.&prc_jcp=0&prc_jp=0&prc_jpc=3&prc_jfp=0&prc_bhl=1&prc_erf=1&prc_isPhantomJS=0&prc_PhantomJSDetail=0&prc_isHeadlessChrome=0&prc_HeadlessChromeDetail=0&prc_pnc=100&prc_pnd=3 | US | — | — | suspicious |
2184 | chrome.exe | GET | 302 | 23.235.244.225:80 | http://prpops.com/p/o26g/direct/t:source-41?prc_c=1589117056&prc_r=eyJIVFRQX1VTRVJfQUdFTlQiOiJNb3ppbGxhXC81LjAgKFdpbmRvd3MgTlQgNi4xKSBBcHBsZVdlYktpdFwvNTM3LjM2IChLSFRNTCwgbGlrZSBHZWNrbykgQ2hyb21lXC83NS4wLjM3NzAuMTAwIFNhZmFyaVwvNTM3LjM2In0=&prc_h=457dd2479b738399e9a3df2396f0455be563b6c6d4bf22311862c0165992623a&pr_tsid=e9fbe15a270dd3fa98df5e392cec105a237b430d9e1a9be85935970249eff806&pr_tsids=4b2080285e13104fd91f3abb30e3d1aec19fa2a5b4169765365168765bc5119b&prc_obfjs=f5ef35210db14fb974879a00a7bb36fb340e22ada105a2af2d3d3dec01c8655a&prc_isIframe1=false&prc_jw=1280&prc_jh=620&prc_jow=0&prc_joh=0&prc_jsw=1280&prc_jsh=720&prc_jwaw=1280&prc_jwah=692&prc_jnp=Win32&prc_jnv=Google%20Inc.&prc_jcp=0&prc_jp=0&prc_jpc=3&prc_jfp=0&prc_bhl=1&prc_erf=1&prc_isPhantomJS=0&prc_PhantomJSDetail=0&prc_isHeadlessChrome=0&prc_HeadlessChromeDetail=0&prc_pnc=100&prc_pnd=3 | US | — | — | suspicious |
2184 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
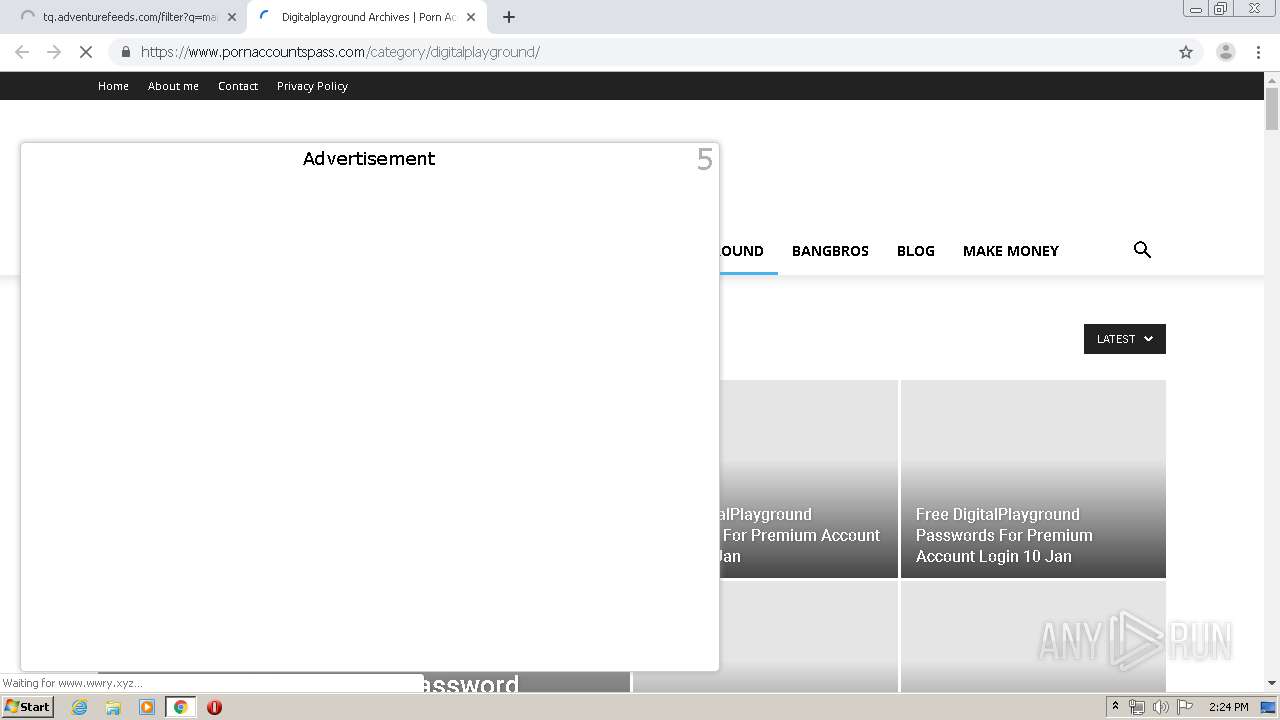
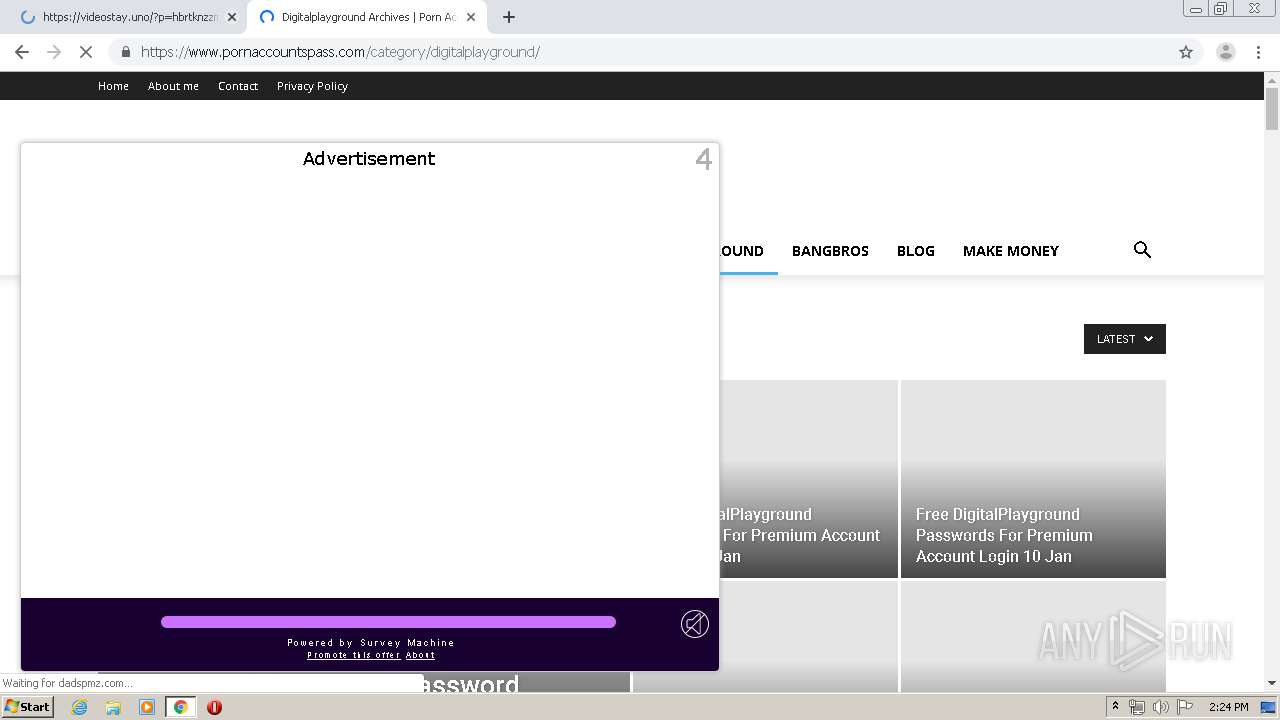
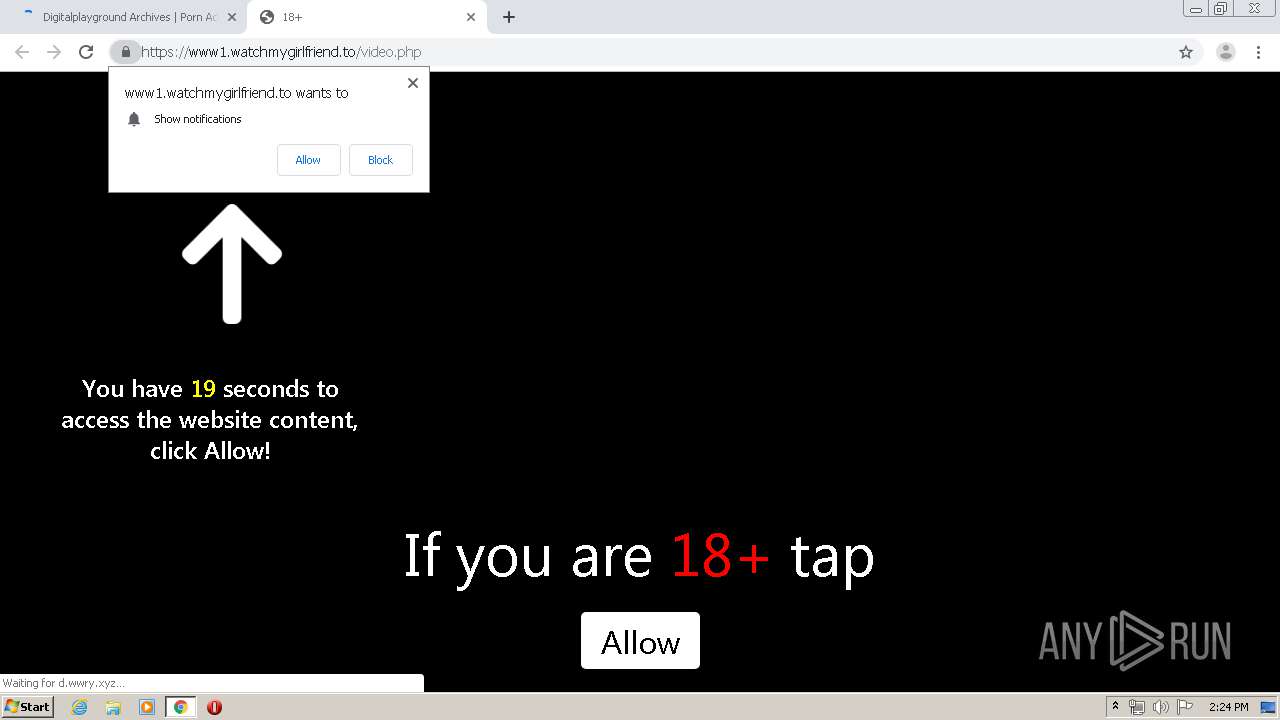
2184 | chrome.exe | GET | 303 | 107.23.28.17:80 | http://sp.popcash.net/ad/ad?p=223901&w=465801&t=3840bd0d6620e171&r=aHR0cHMlM0EvL3d3dy5wb3JuYWNjb3VudHNwYXNzLmNvbS9jYXRlZ29yeS9kaWdpdGFscGxheWdyb3VuZC8=&vw=1280&vh=620 | US | html | 468 b | suspicious |
2184 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEA96F1Rsa9jjw5yJodY%2Fbhg%3D | US | der | 471 b | whitelisted |
2184 | chrome.exe | GET | 404 | 174.137.155.139:80 | http://tq.adventurefeeds.com/favicon.ico | US | html | 339 b | suspicious |
2184 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
2184 | chrome.exe | GET | 200 | 174.137.155.139:80 | http://tq.adventurefeeds.com/filter?q=mainstream%2Cadult&i=zo98HExVPrw_0&t=700869672 | US | html | 8.25 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2184 | chrome.exe | 216.58.208.35:443 | — | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2184 | chrome.exe | 162.213.253.35:443 | www.pornaccountspass.com | Namecheap, Inc. | US | malicious |
2184 | chrome.exe | 216.58.207.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 2.21.36.164:443 | s7.addthis.com | GTT Communications Inc. | FR | suspicious |
2184 | chrome.exe | 205.185.216.42:443 | clientservices.googleapis.com | Highwinds Network Group, Inc. | US | whitelisted |
2184 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 216.58.206.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 151.139.128.11:443 | cdn.popcash.net | Highwinds Network Group, Inc. | US | malicious |
2184 | chrome.exe | 104.22.70.197:443 | static.addtoany.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.pornaccountspass.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
ads.exosrv.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn.popcash.net |
| whitelisted |
s.w.org |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
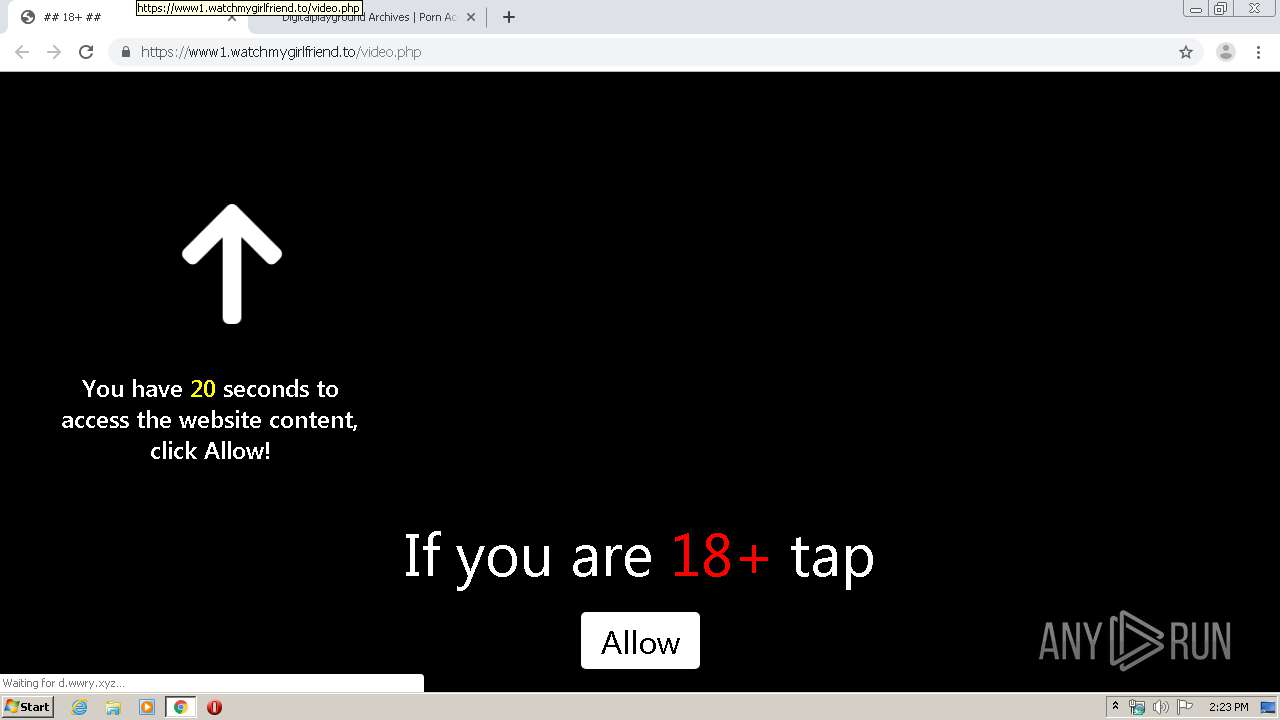
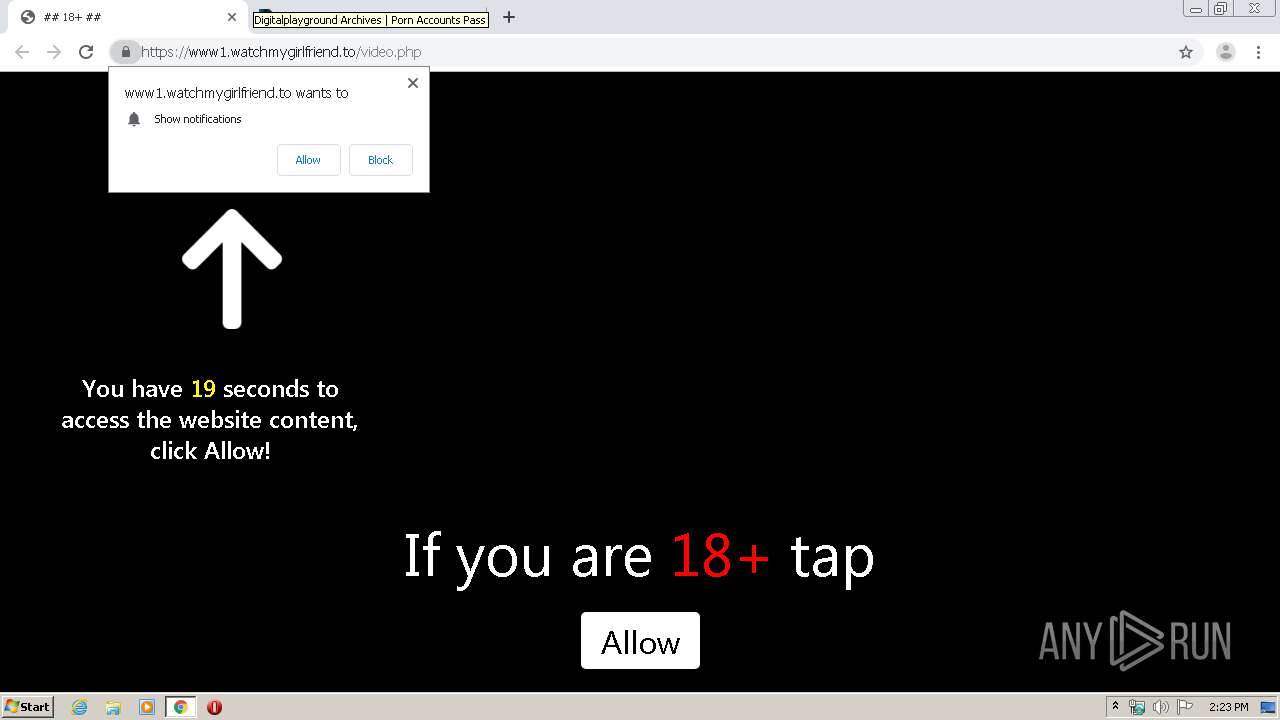
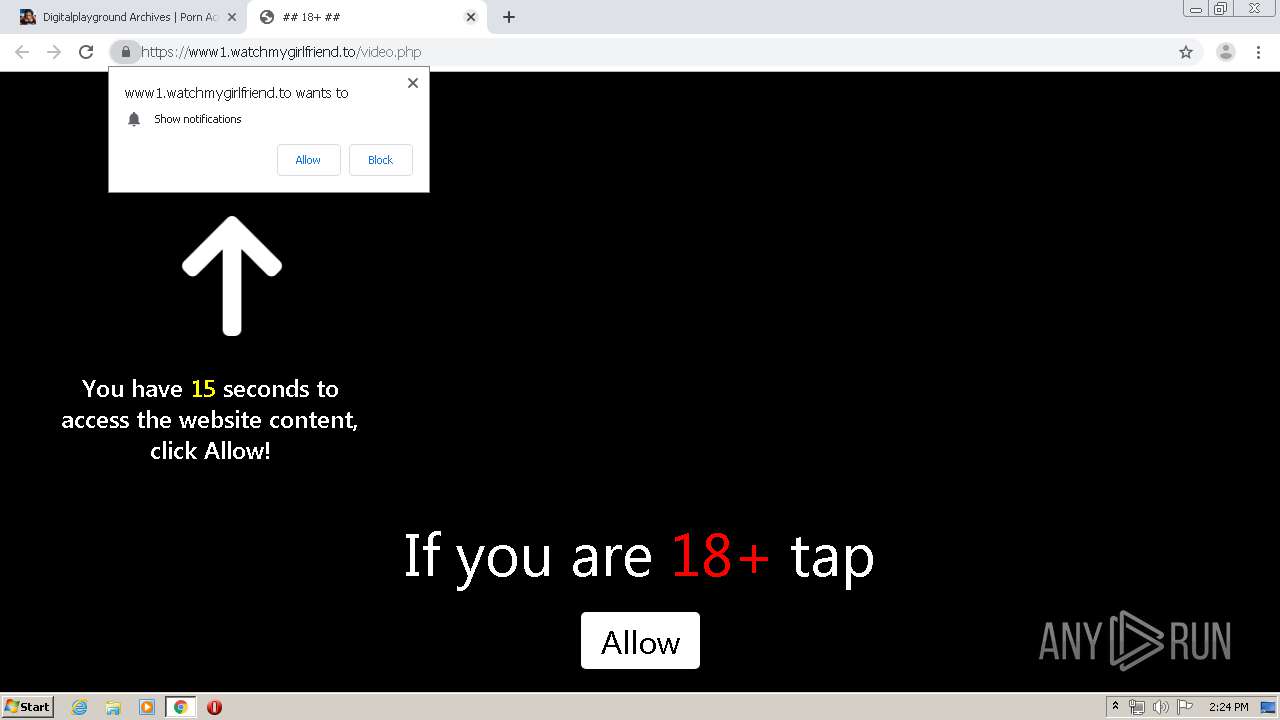
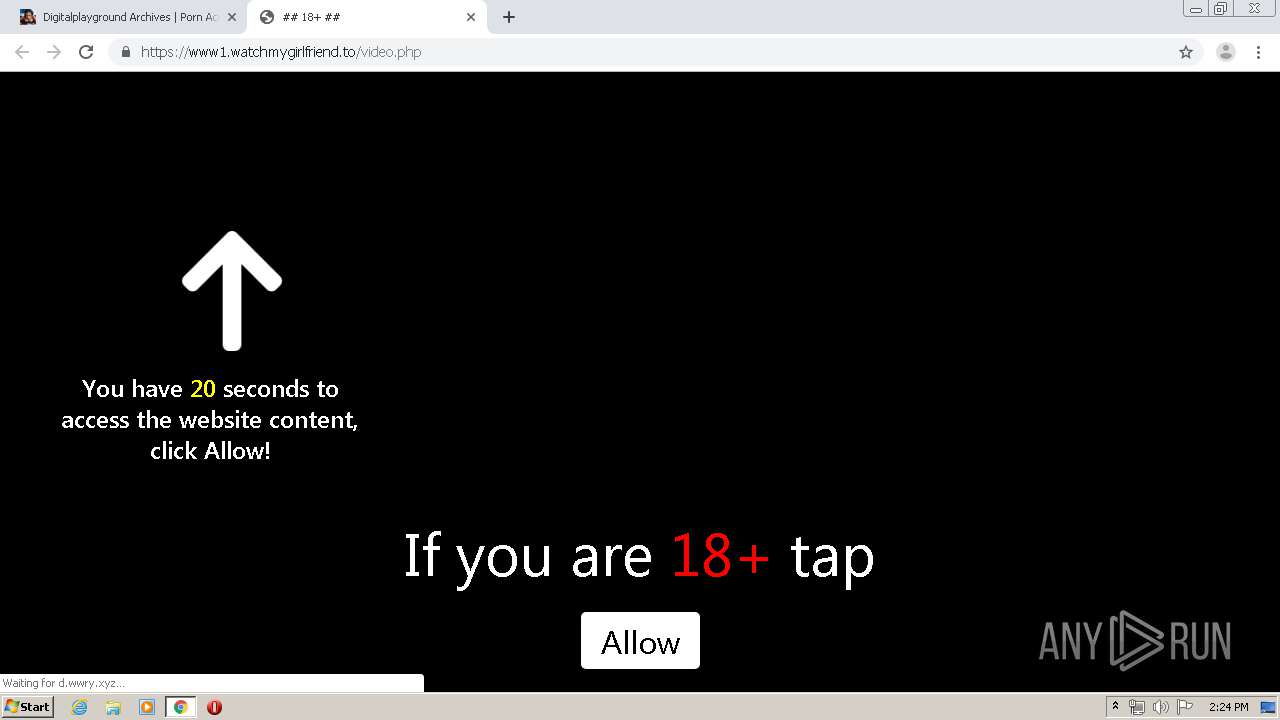
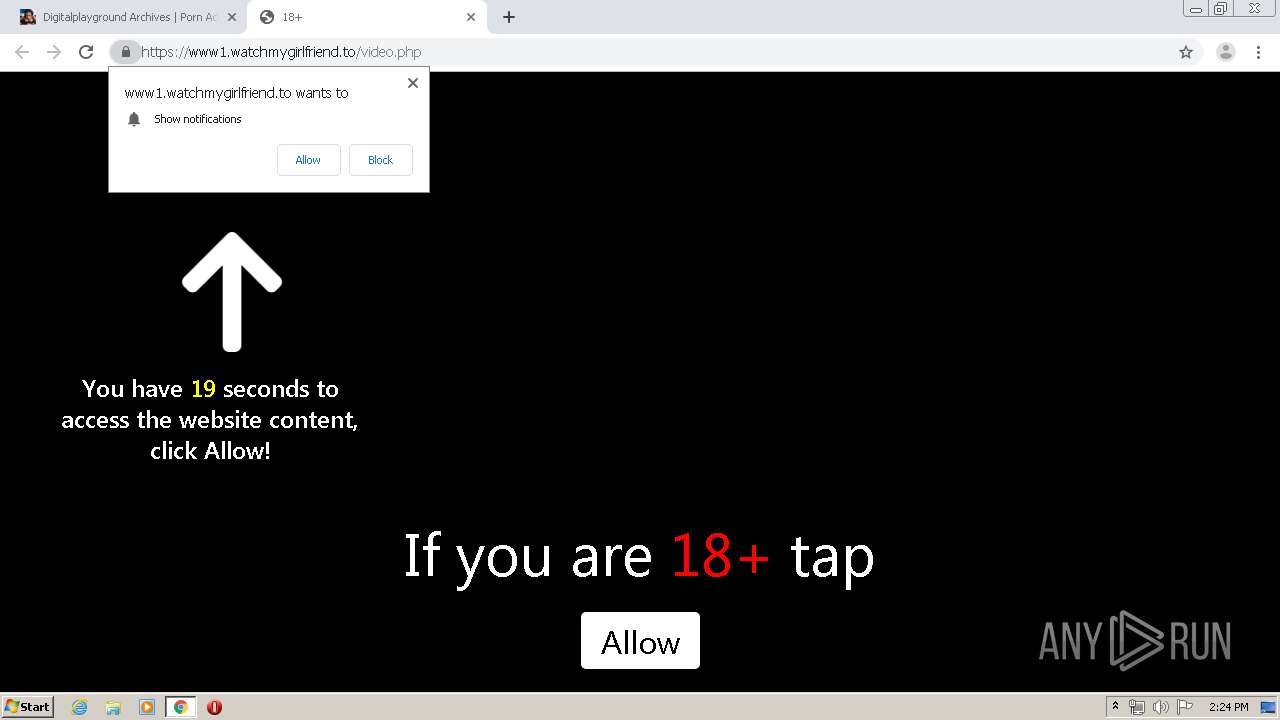
2184 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2184 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2184 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
2184 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2184 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |