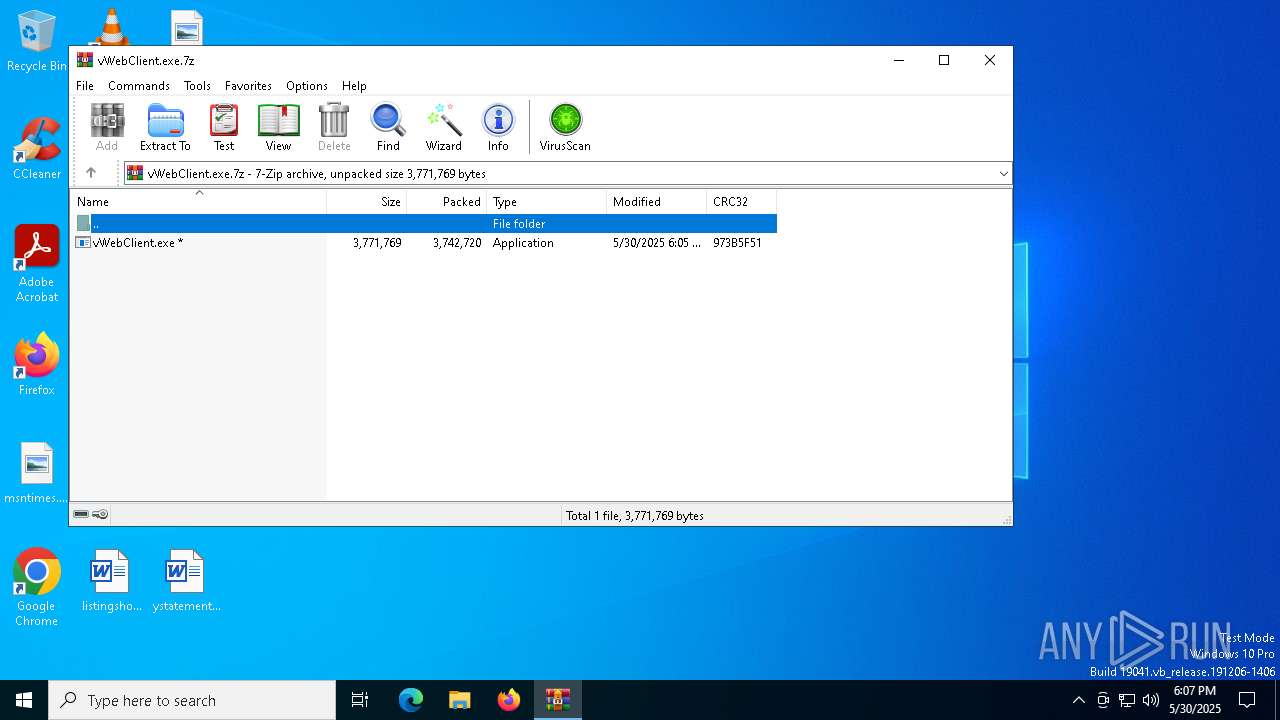
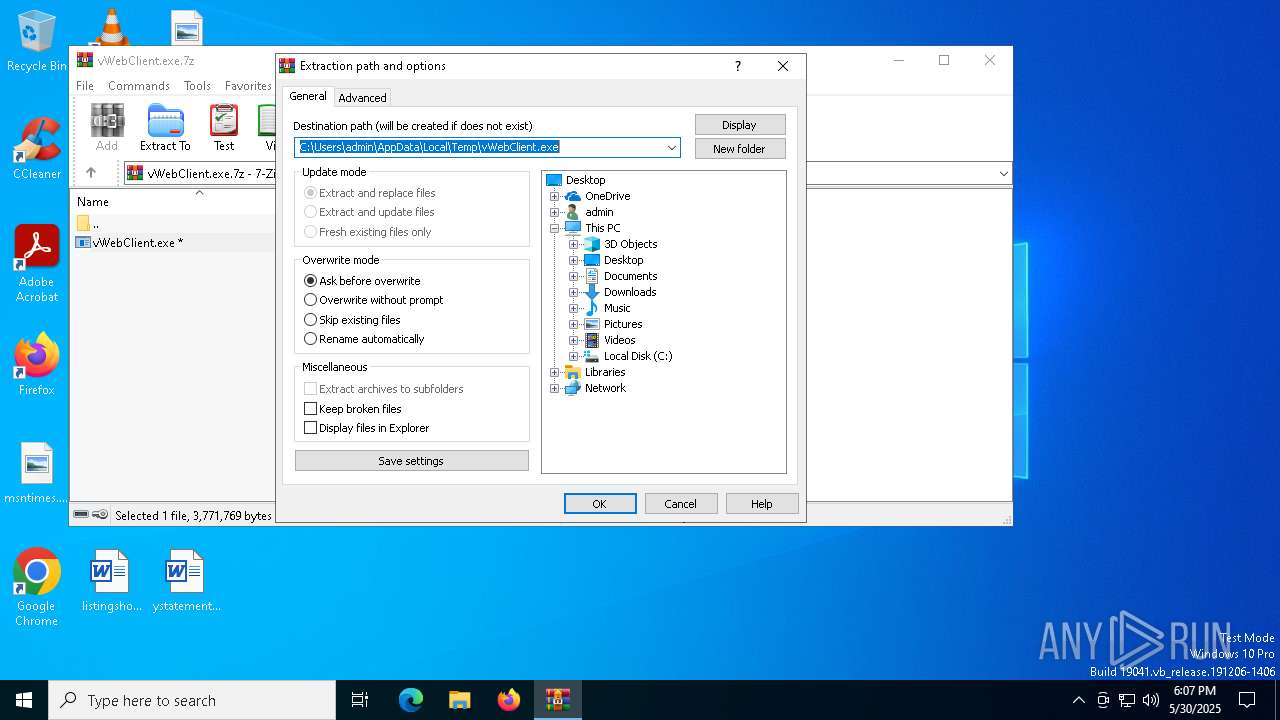
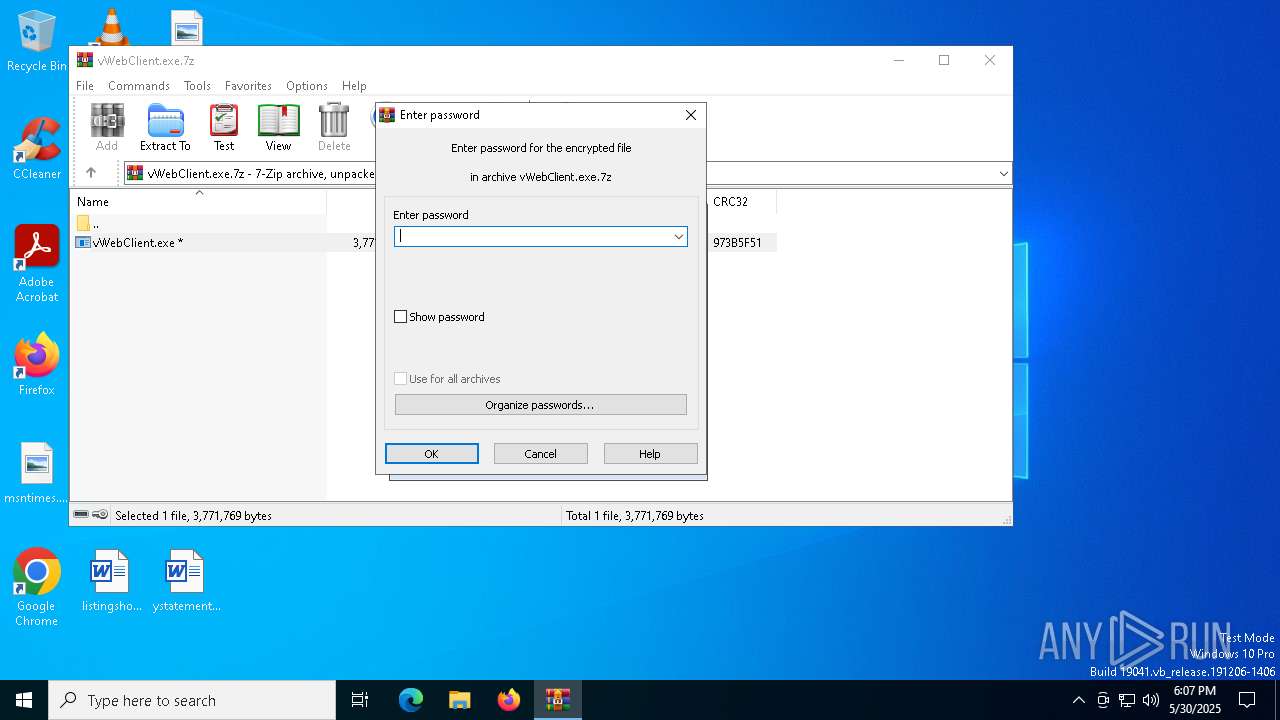
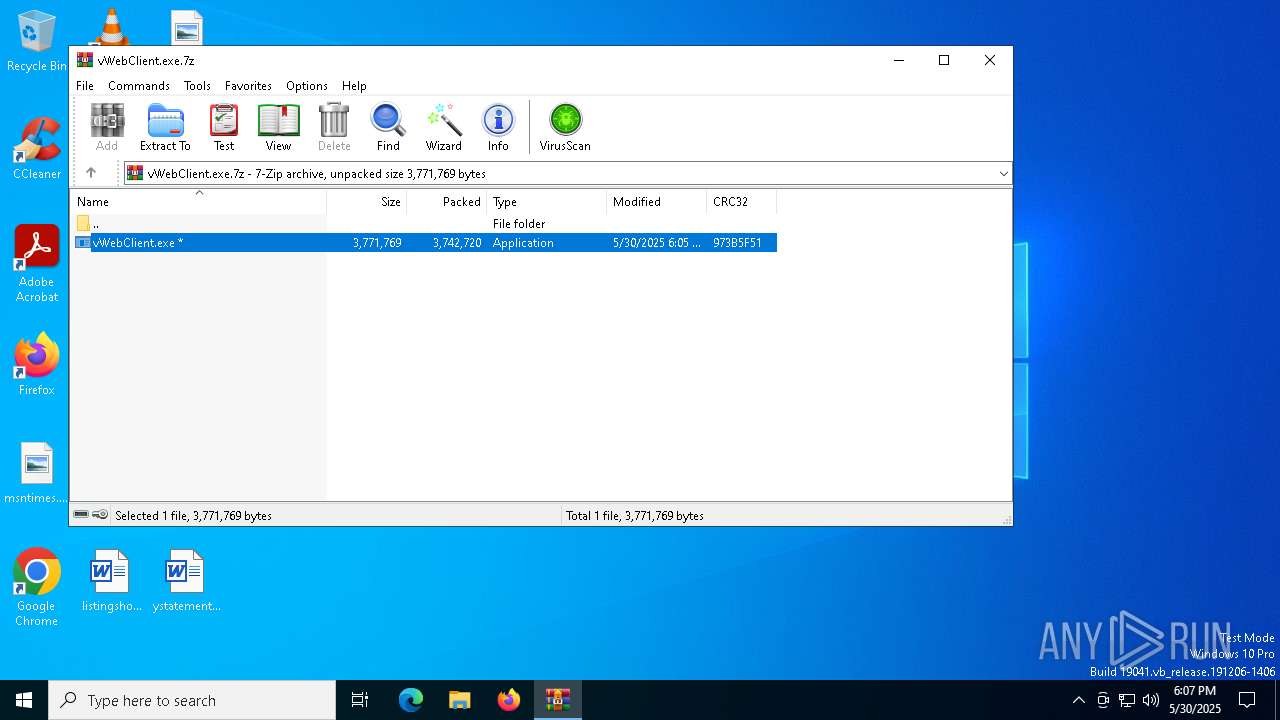
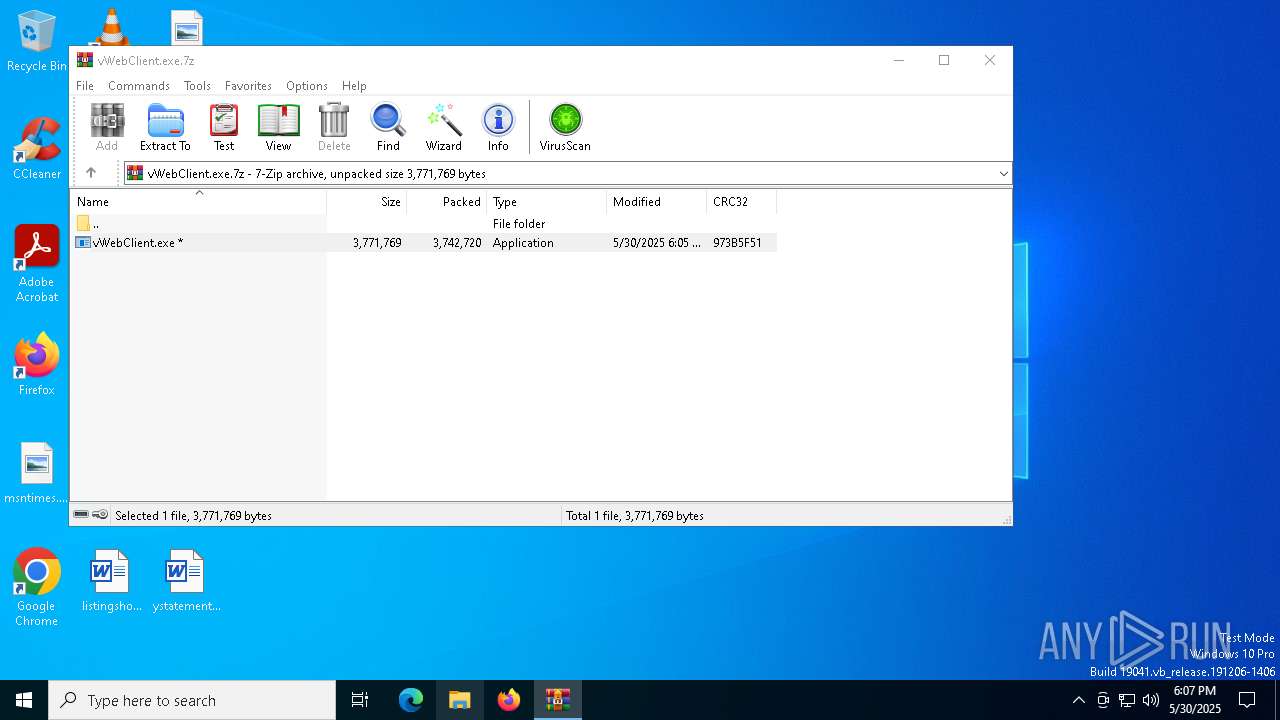
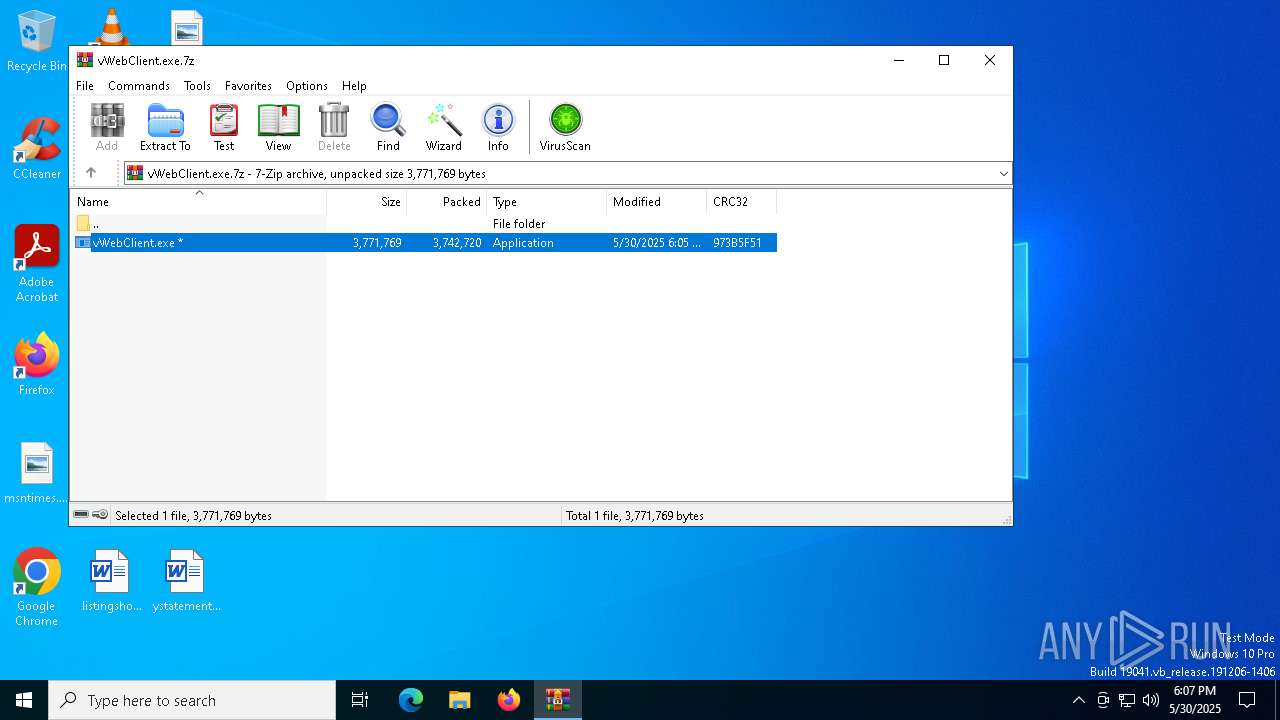
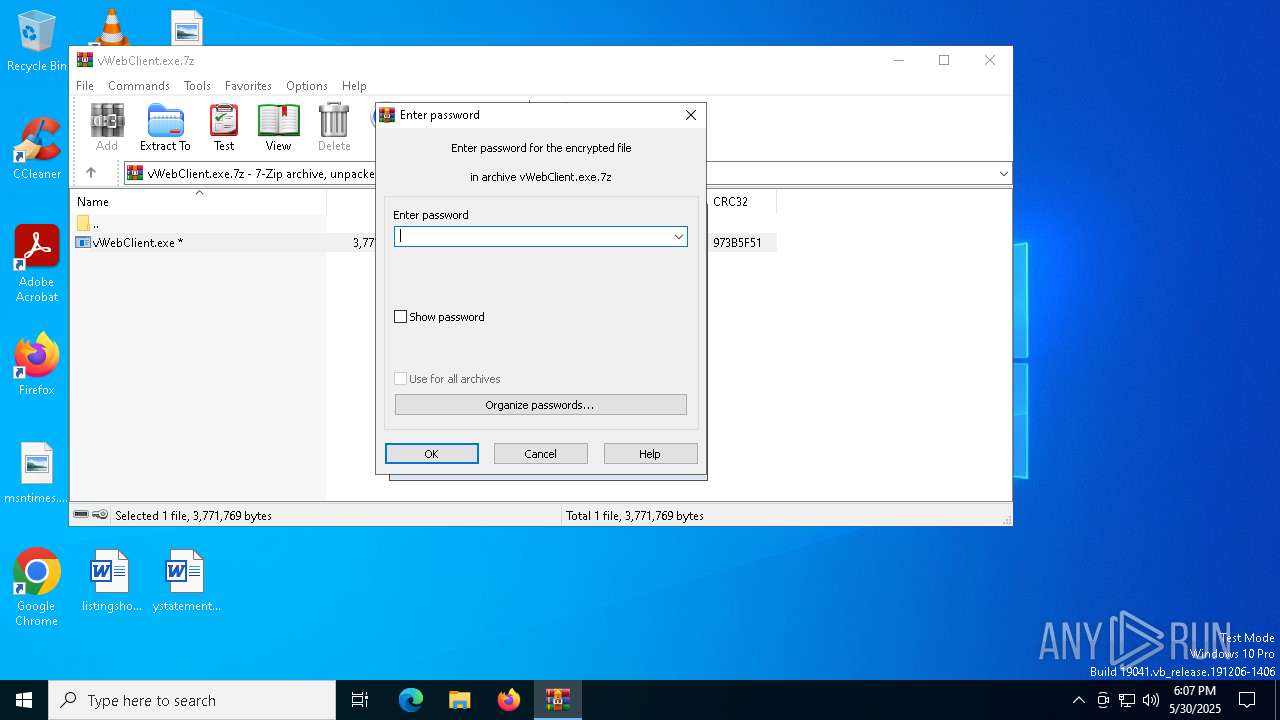
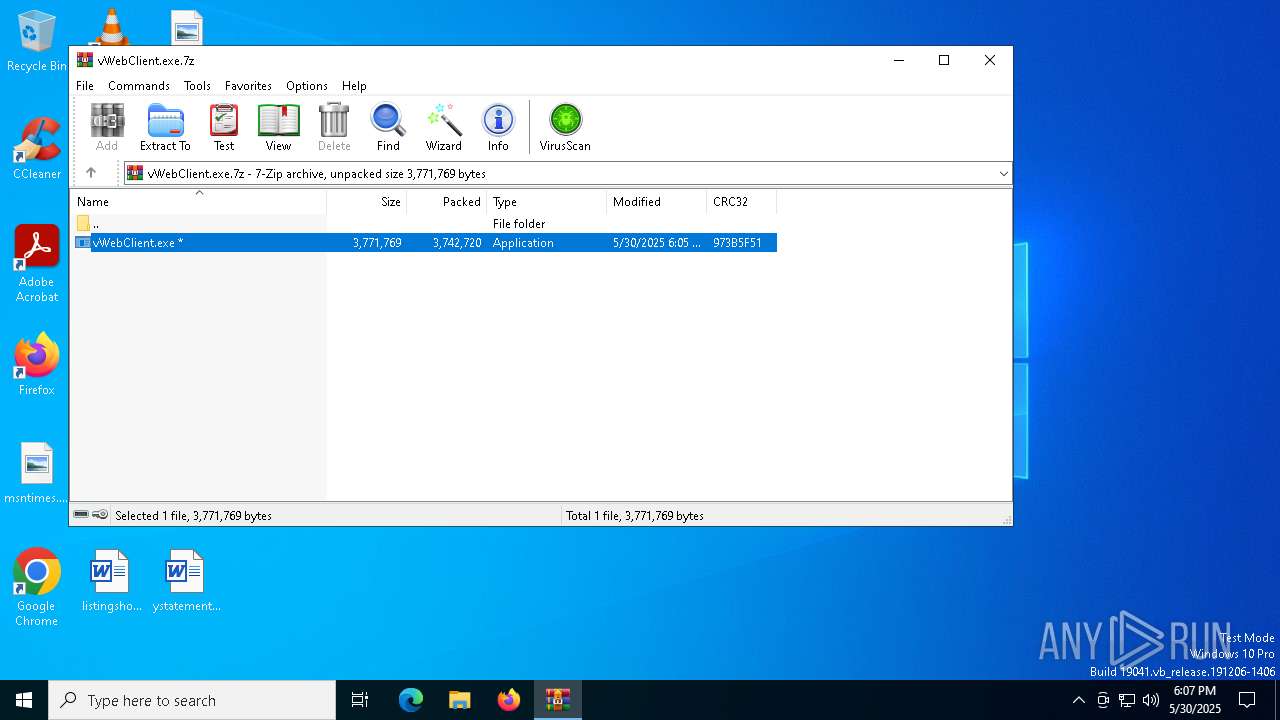
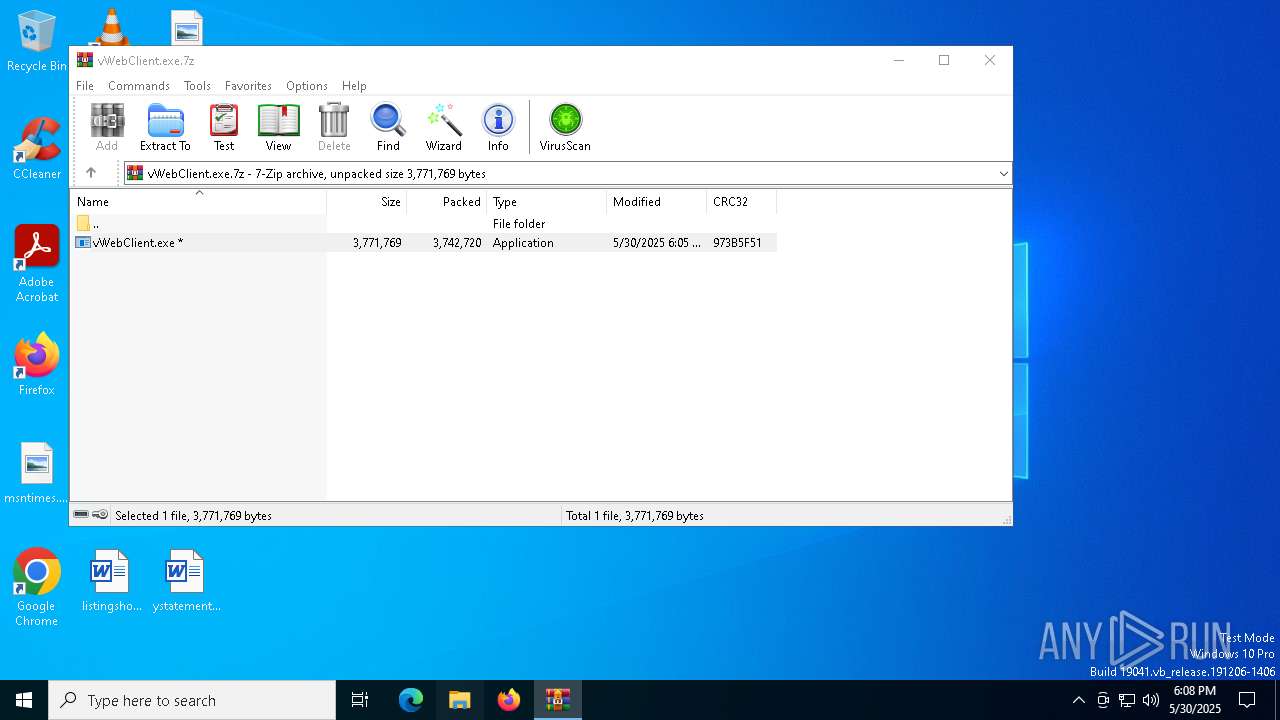
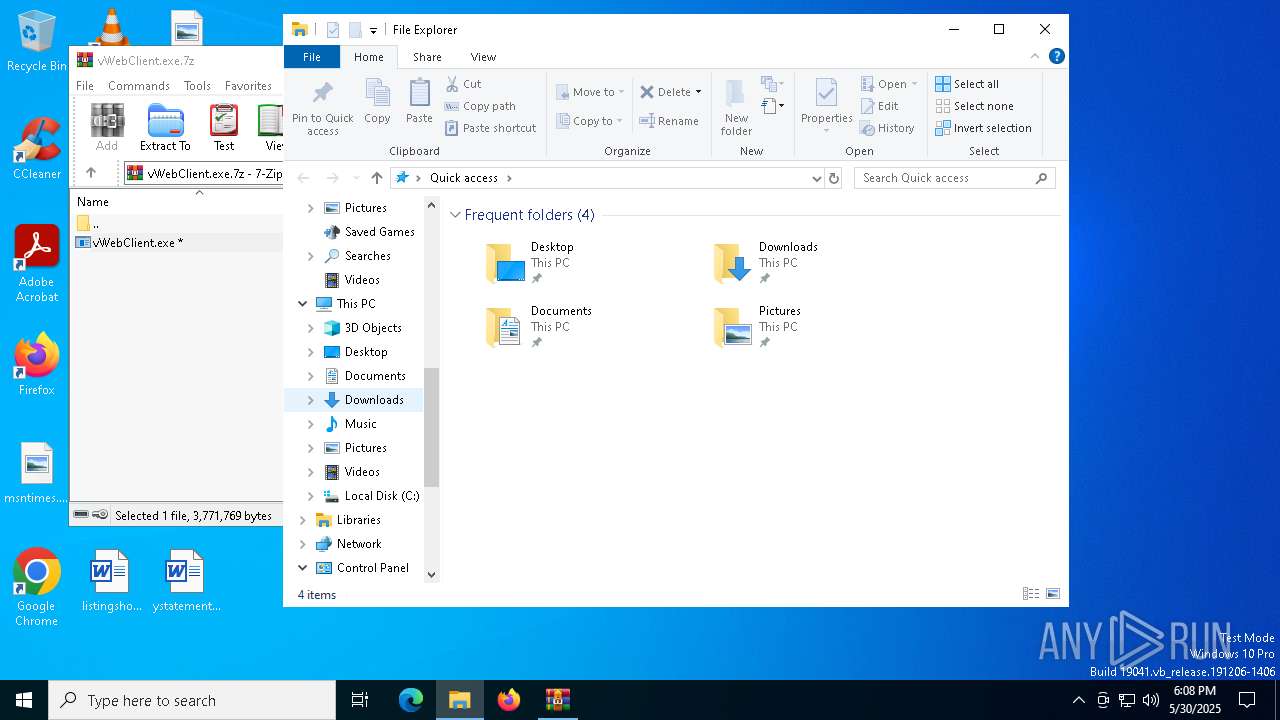
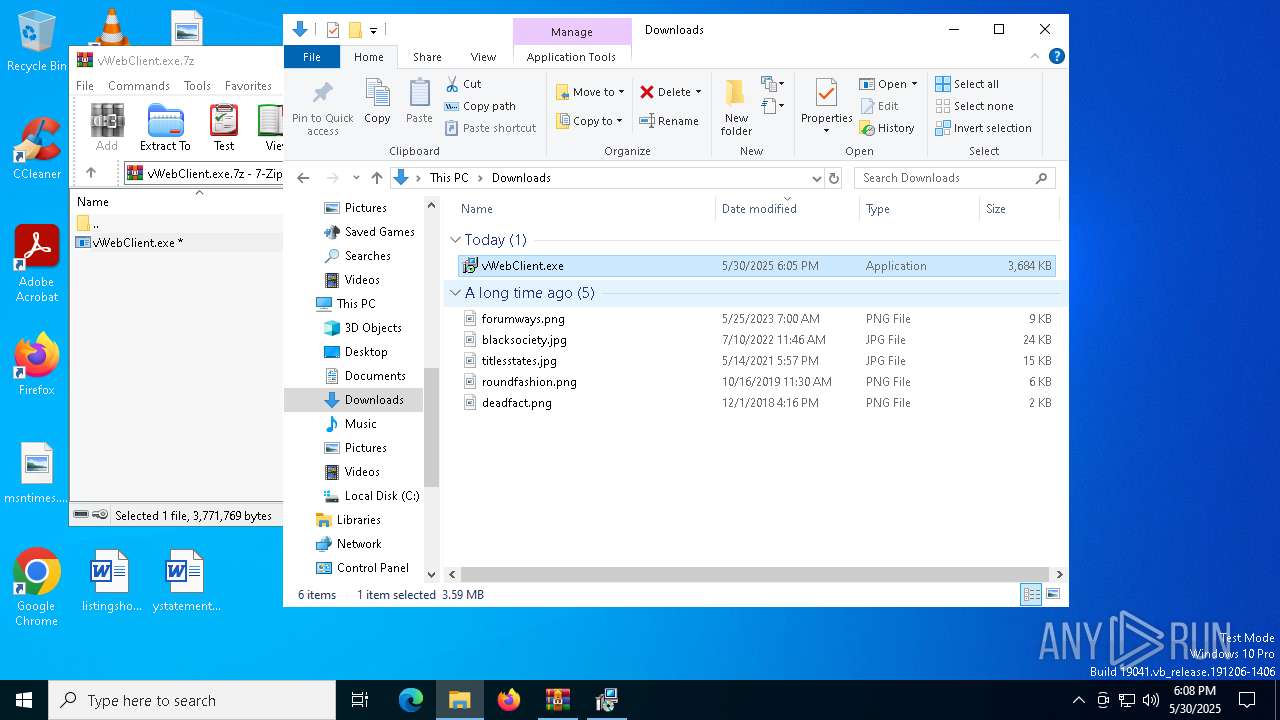
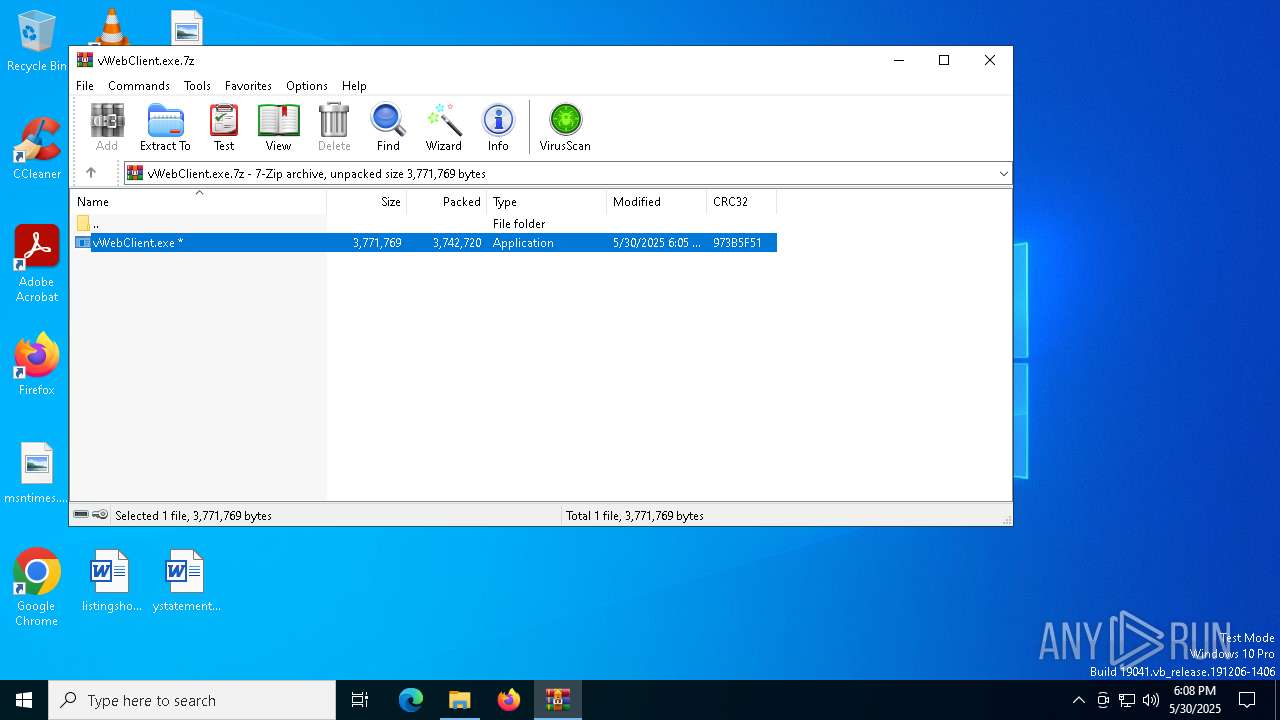
| File name: | vWebClient.exe.7z |
| Full analysis: | https://app.any.run/tasks/c94c7f30-6b57-49af-98b9-074c6ee4d046 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 18:06:56 |
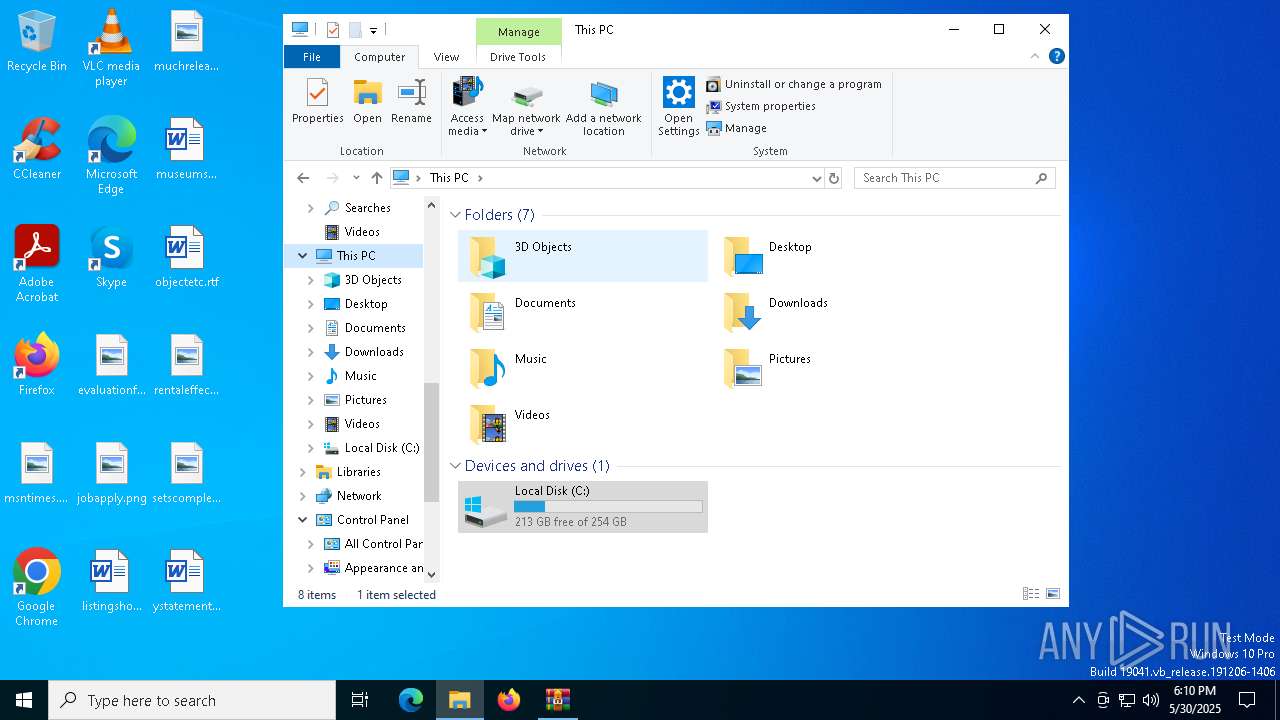
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 186FE042F4C93DFD3E7FFA90D8A3A3CC |
| SHA1: | 303E9231DE57A9BF187035ACCE504B50D293046D |
| SHA256: | D10B22E3D1A7E4F36D7289C1727D1A8E406378E71445147DD03C9FB94D157D88 |
| SSDEEP: | 98304:imbnBmImb+bgFn2Onge8pLV+UOgIp013CSgFg9COCApRX565hhVdhbaVV//6EZDR:HxRhNO0 |
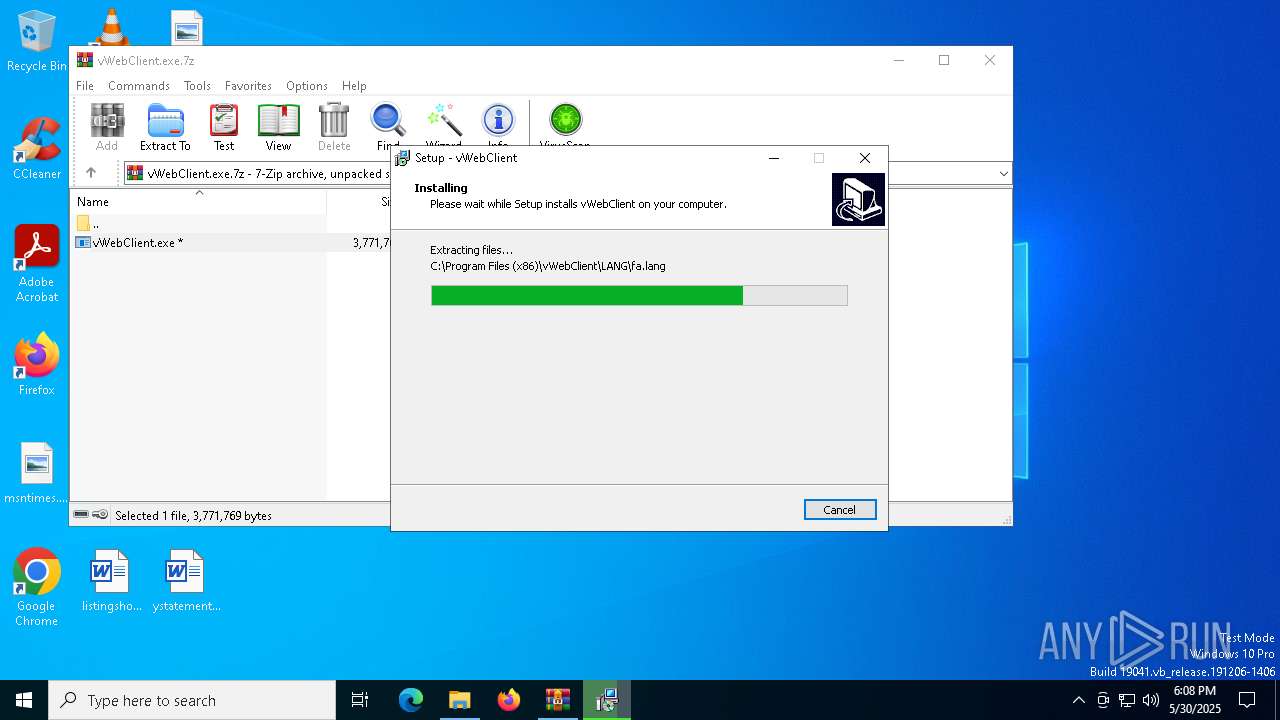
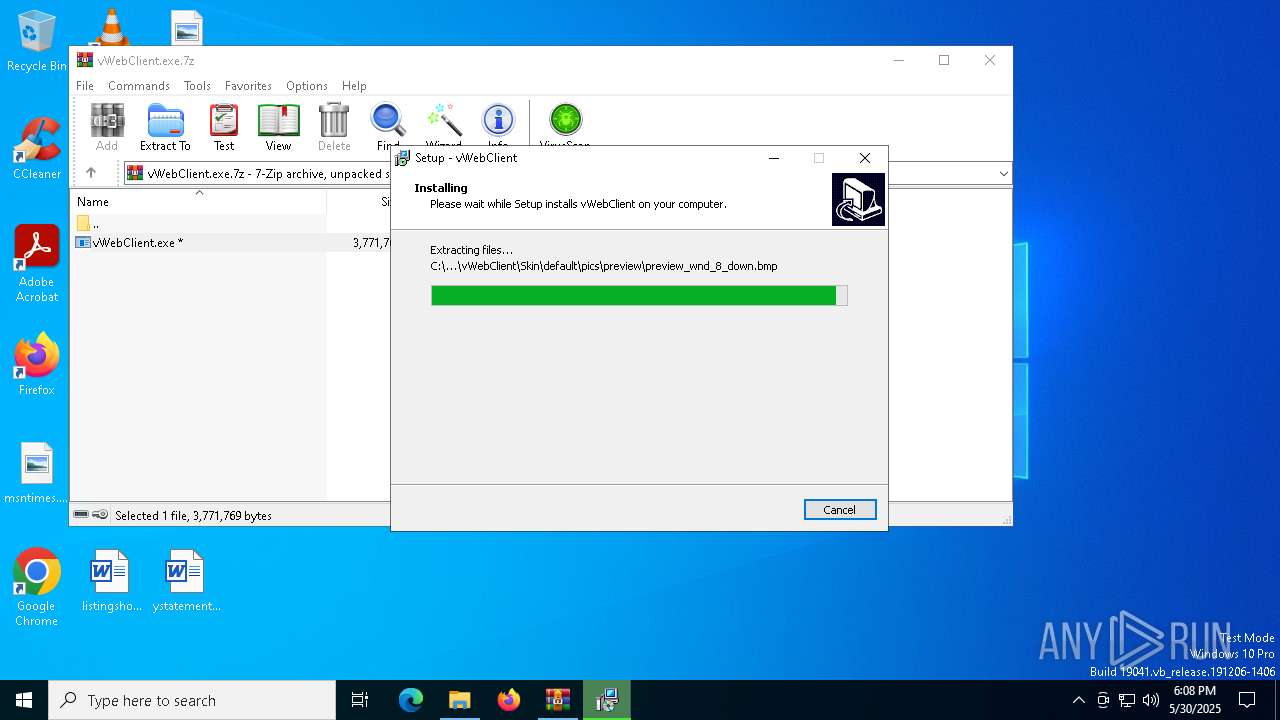
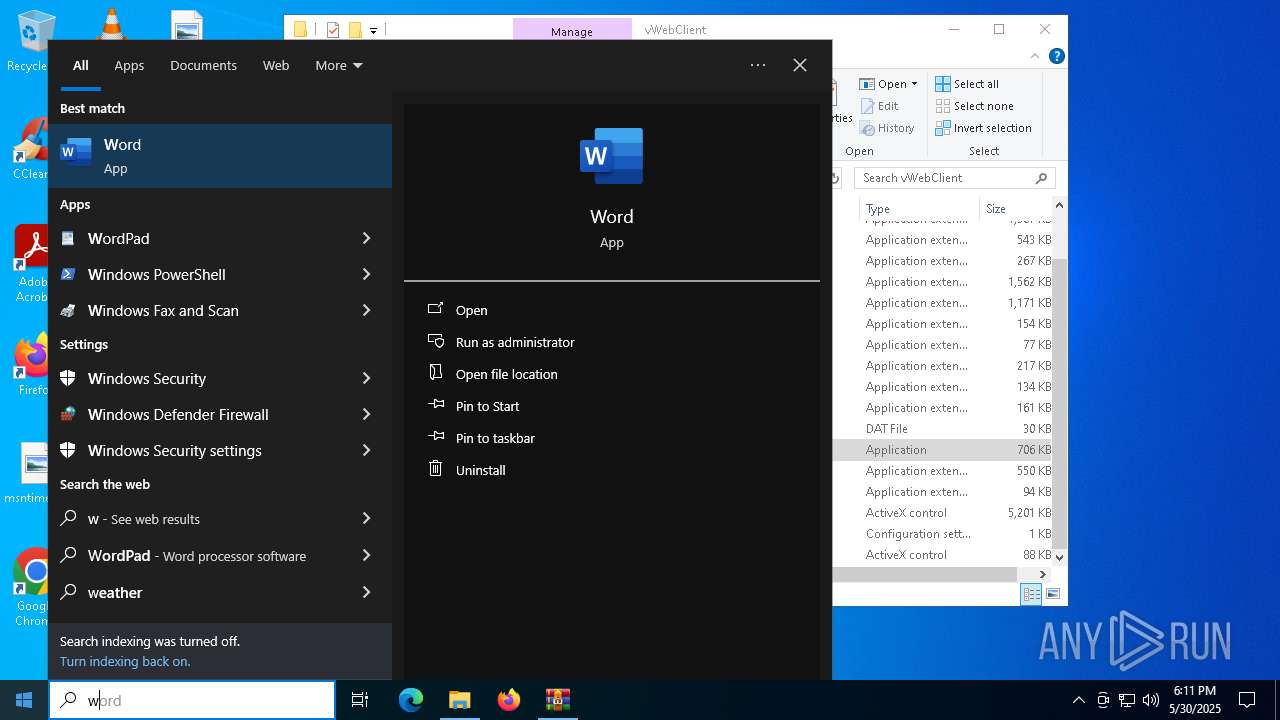
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6044)
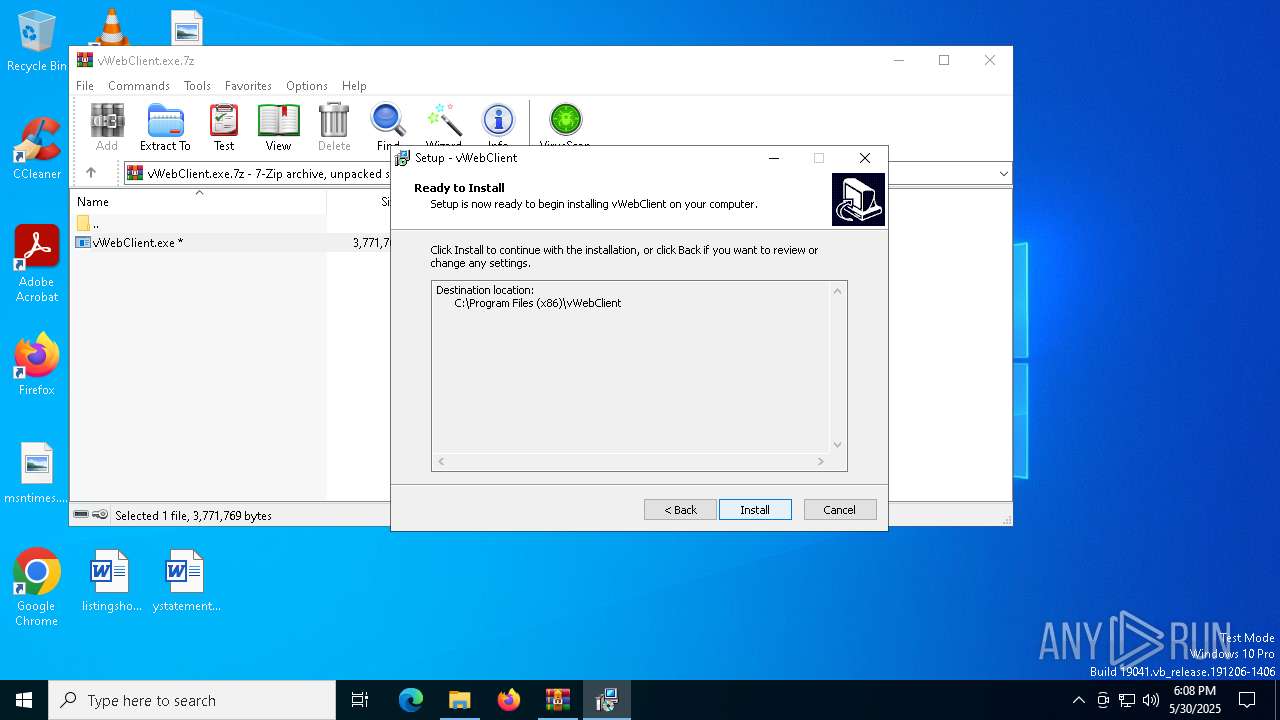
Registers / Runs the DLL via REGSVR32.EXE
- vWebClient.tmp (PID: 7752)
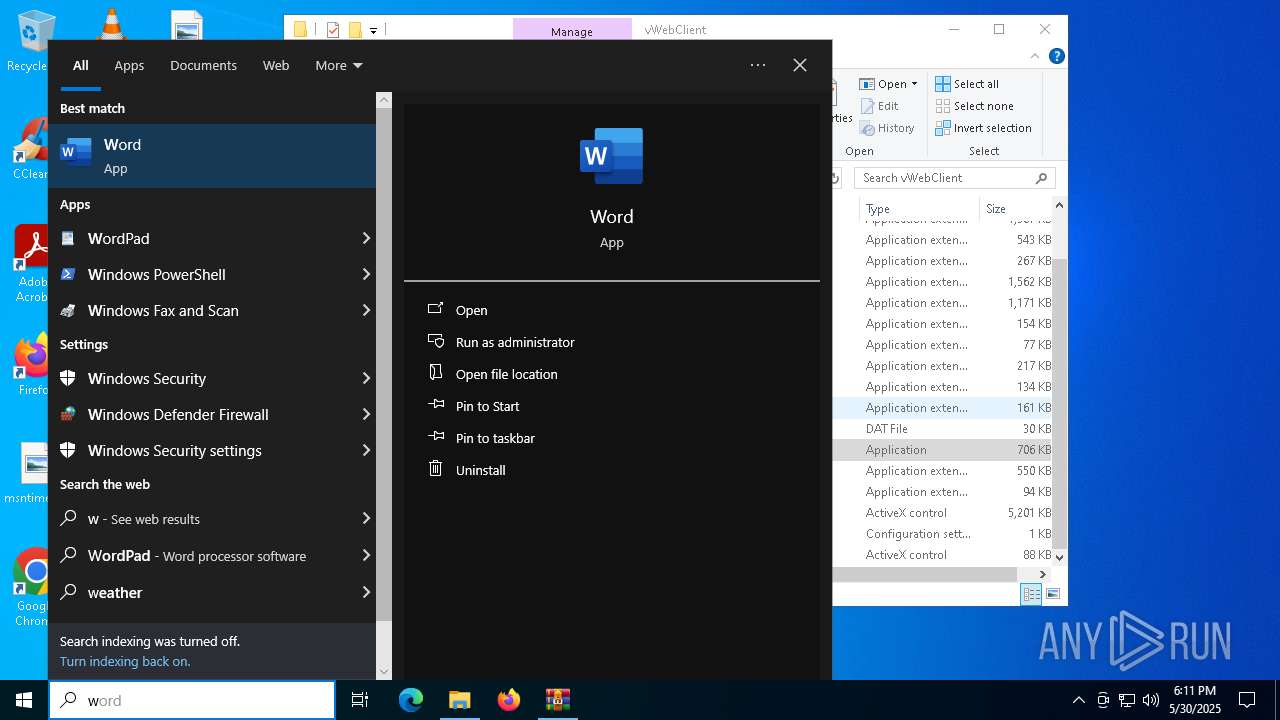
SUSPICIOUS
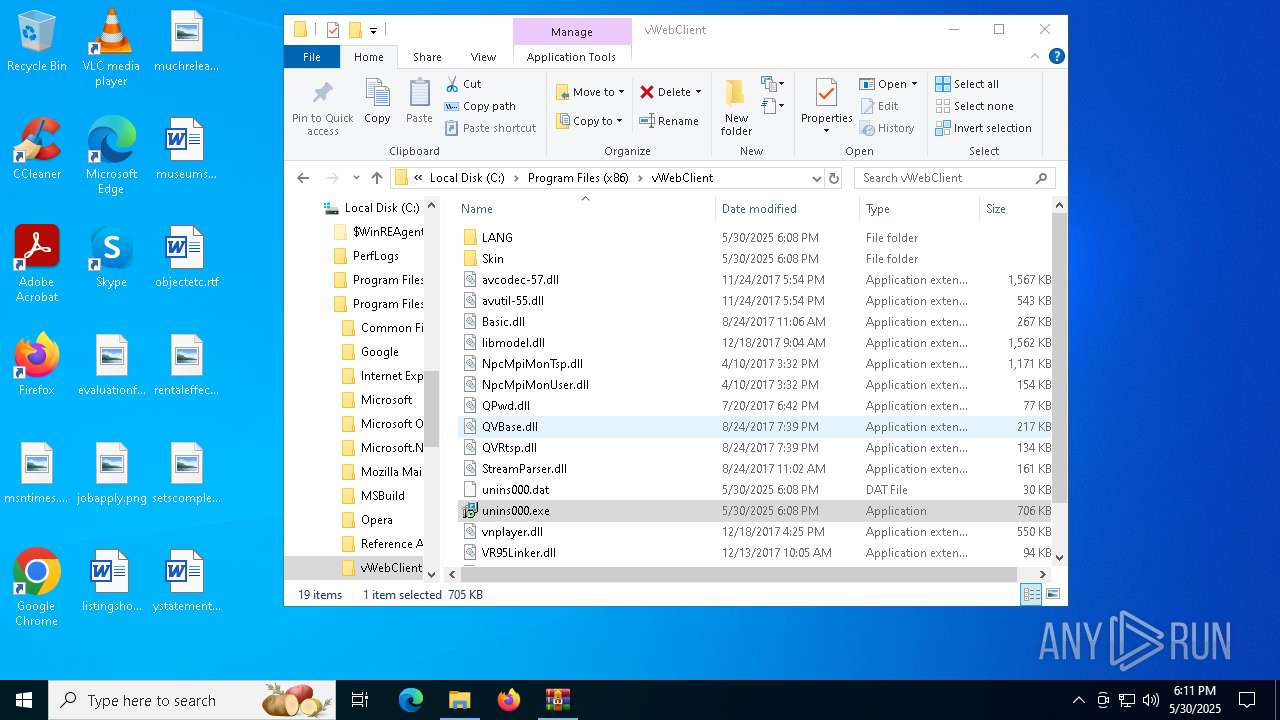
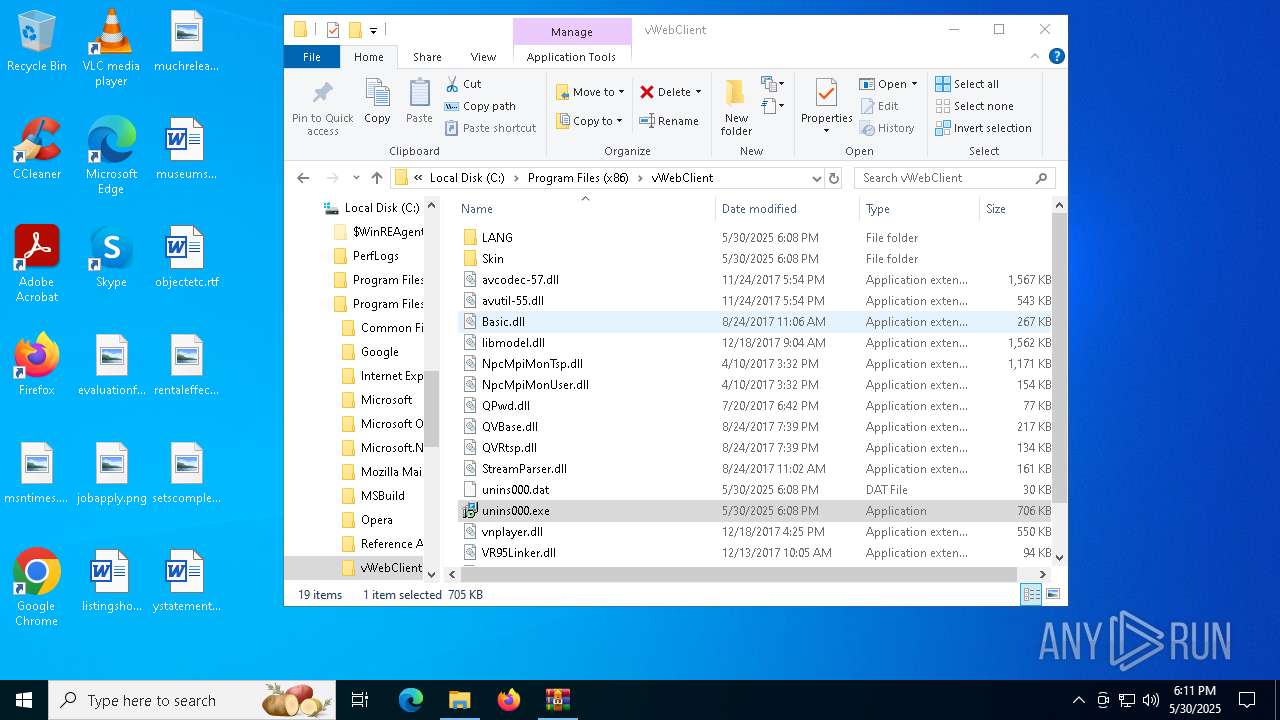
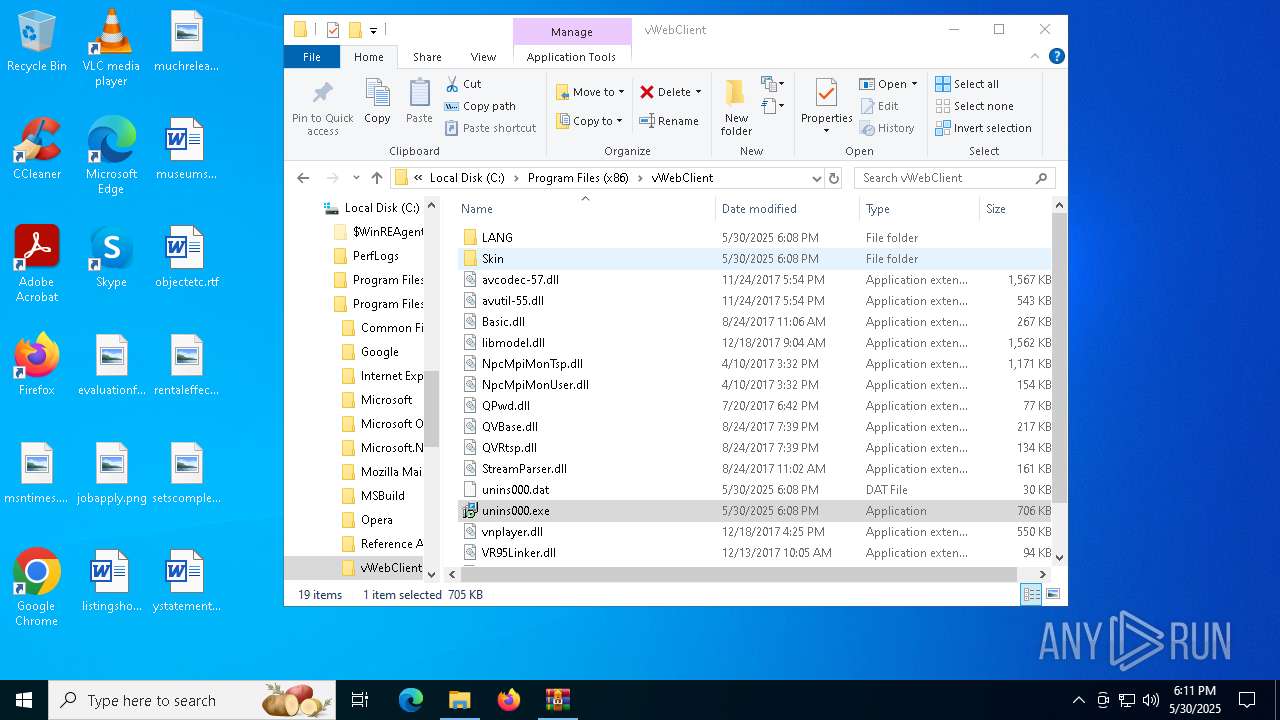
Executable content was dropped or overwritten
- vWebClient.exe (PID: 7856)
- vWebClient.tmp (PID: 7752)
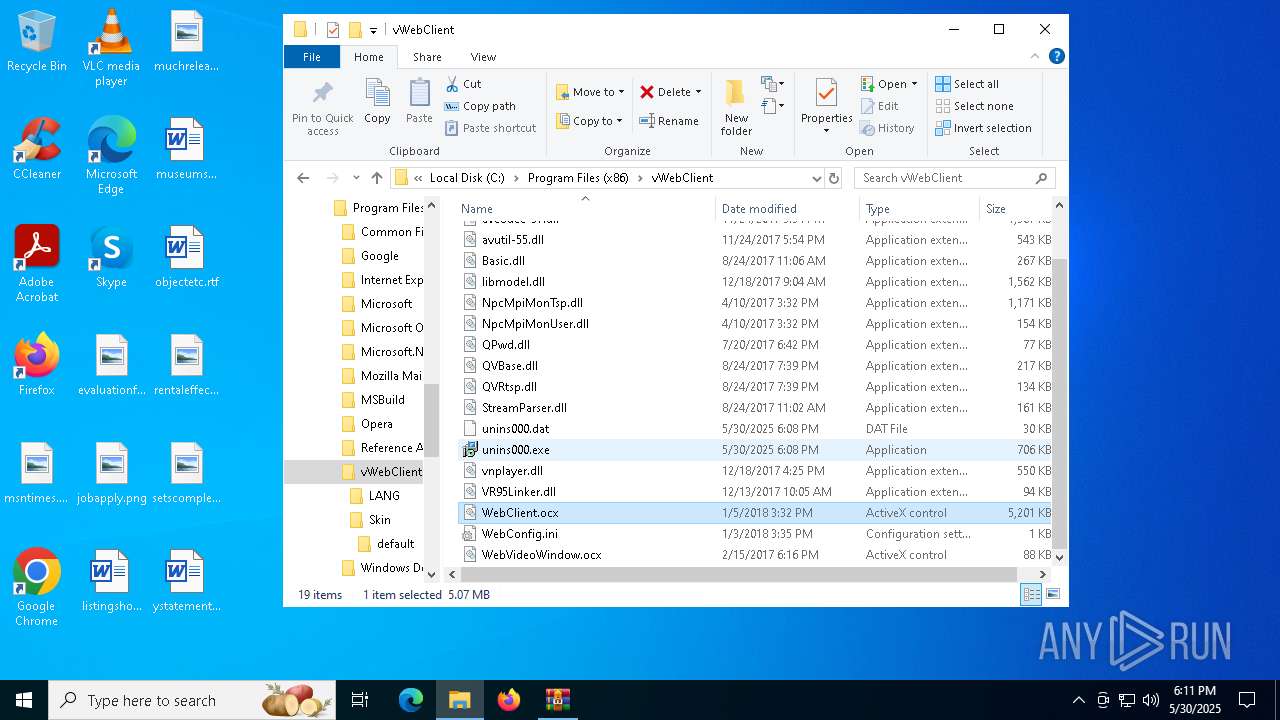
- unins000.exe (PID: 6892)
- _iu14D2N.tmp (PID: 5176)
- vWebClient.exe (PID: 4728)
Reads security settings of Internet Explorer
- vWebClient.tmp (PID: 8028)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2432)
- regsvr32.exe (PID: 2136)
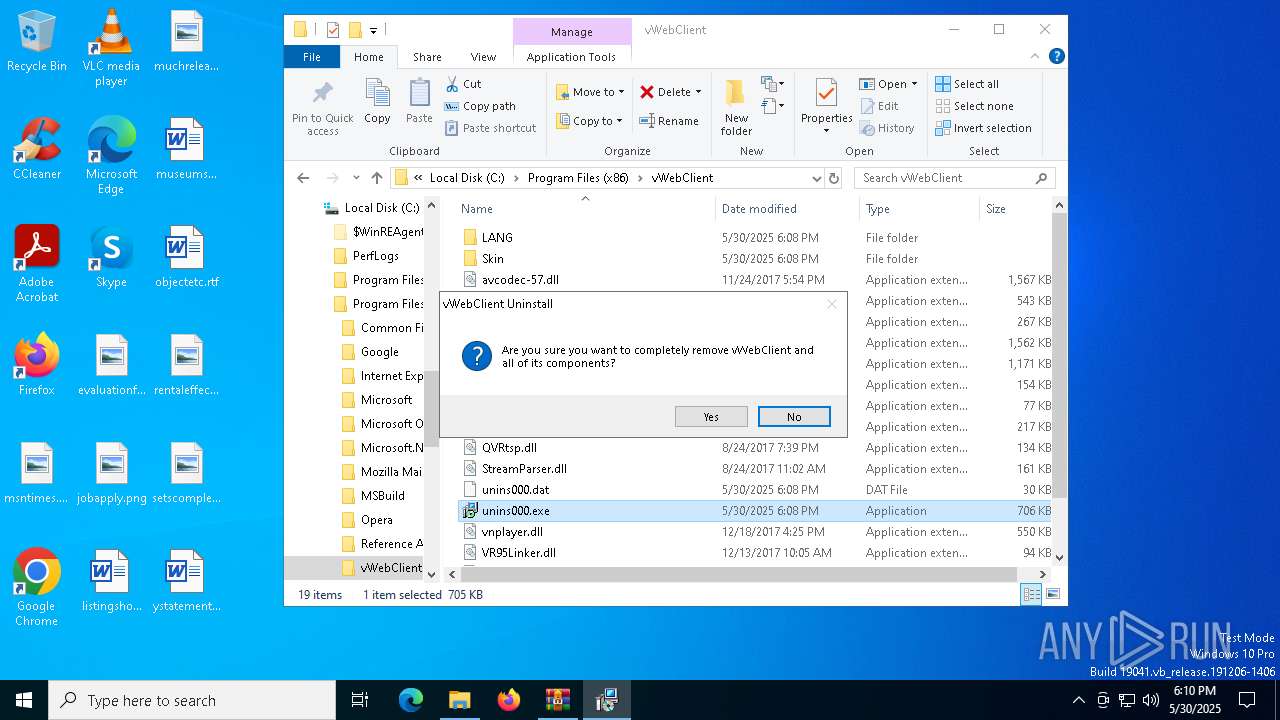
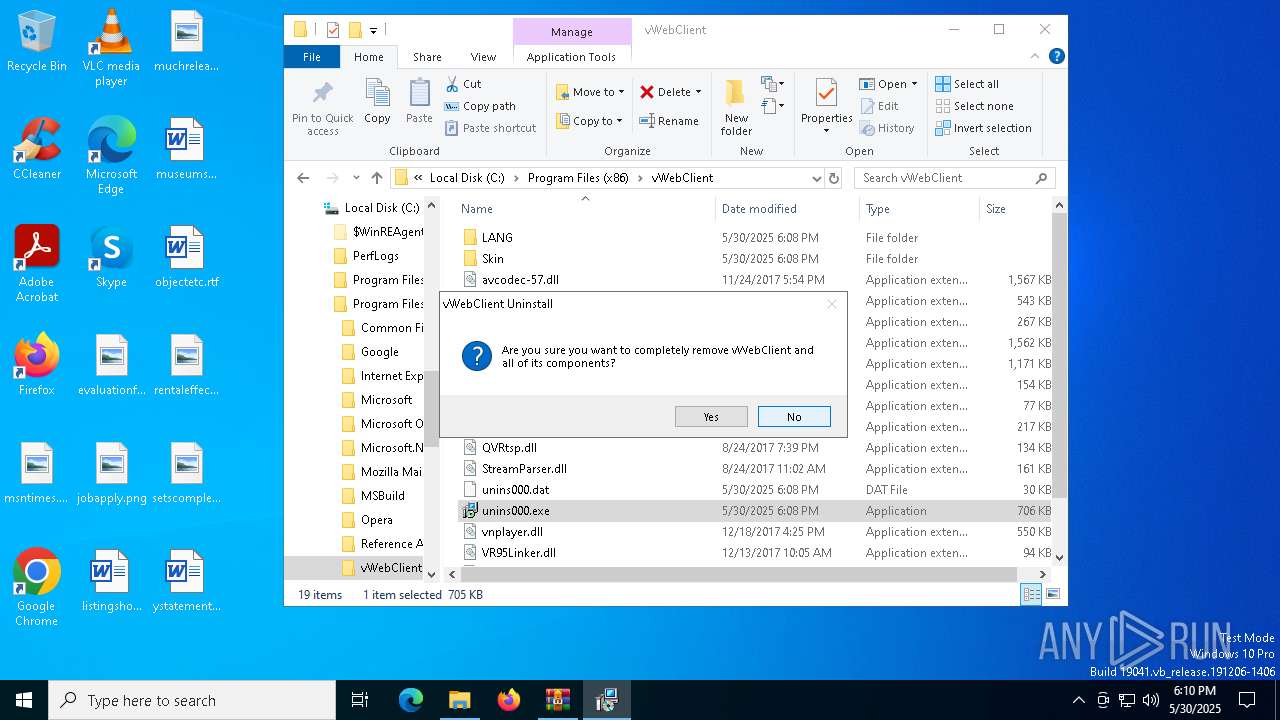
Application launched itself
- unins000.exe (PID: 4696)
Starts itself from another location
- unins000.exe (PID: 6892)
Starts application with an unusual extension
- unins000.exe (PID: 6892)
Reads the Windows owner or organization settings
- vWebClient.tmp (PID: 7752)
Process drops legitimate windows executable
- vWebClient.tmp (PID: 7752)
INFO
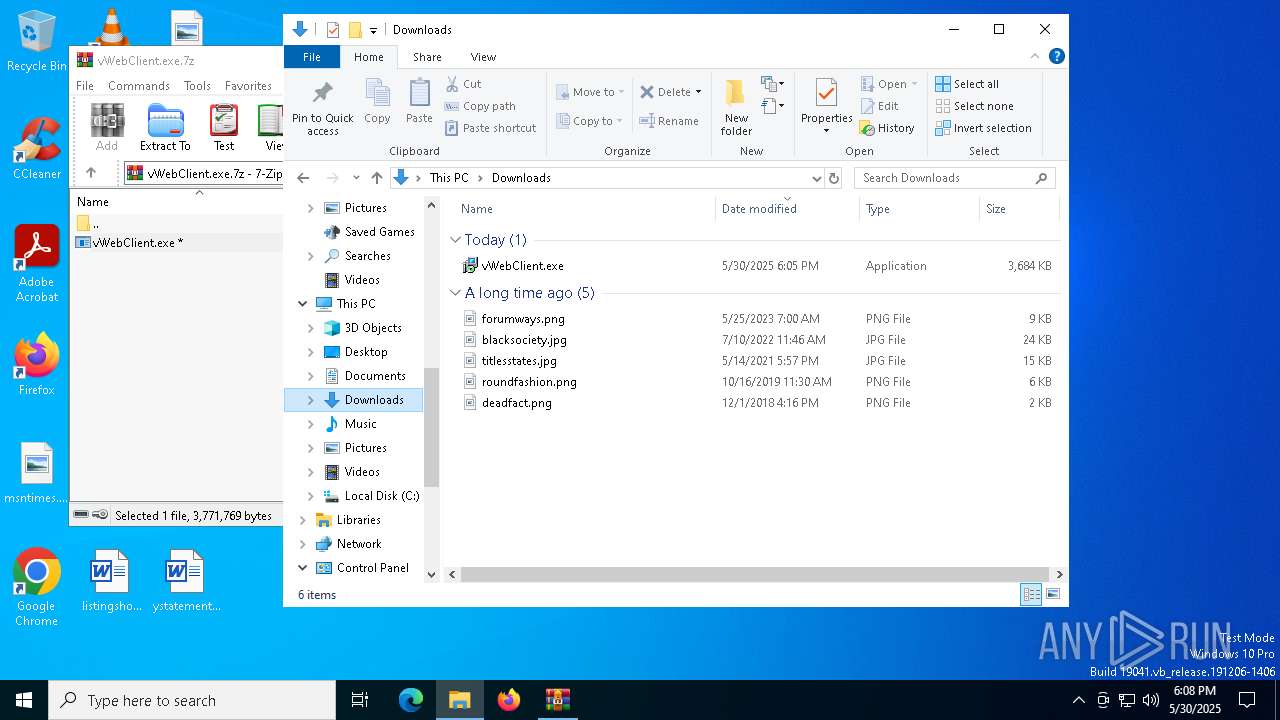
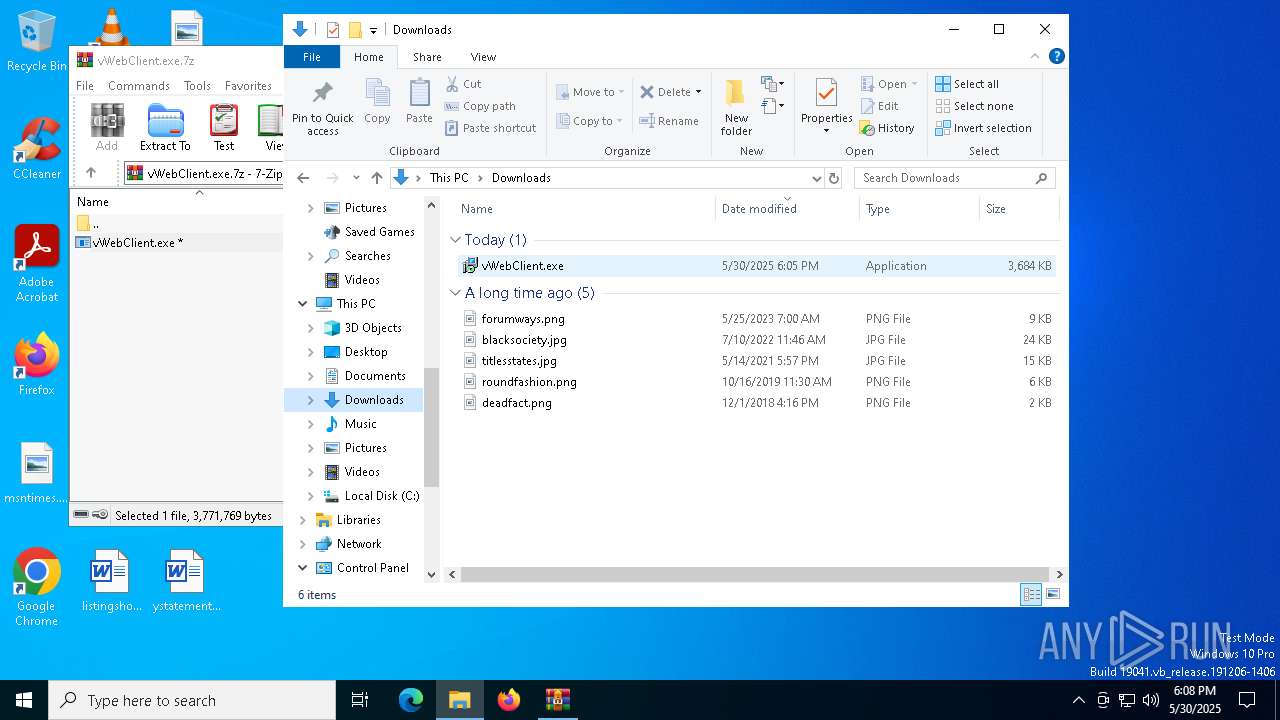
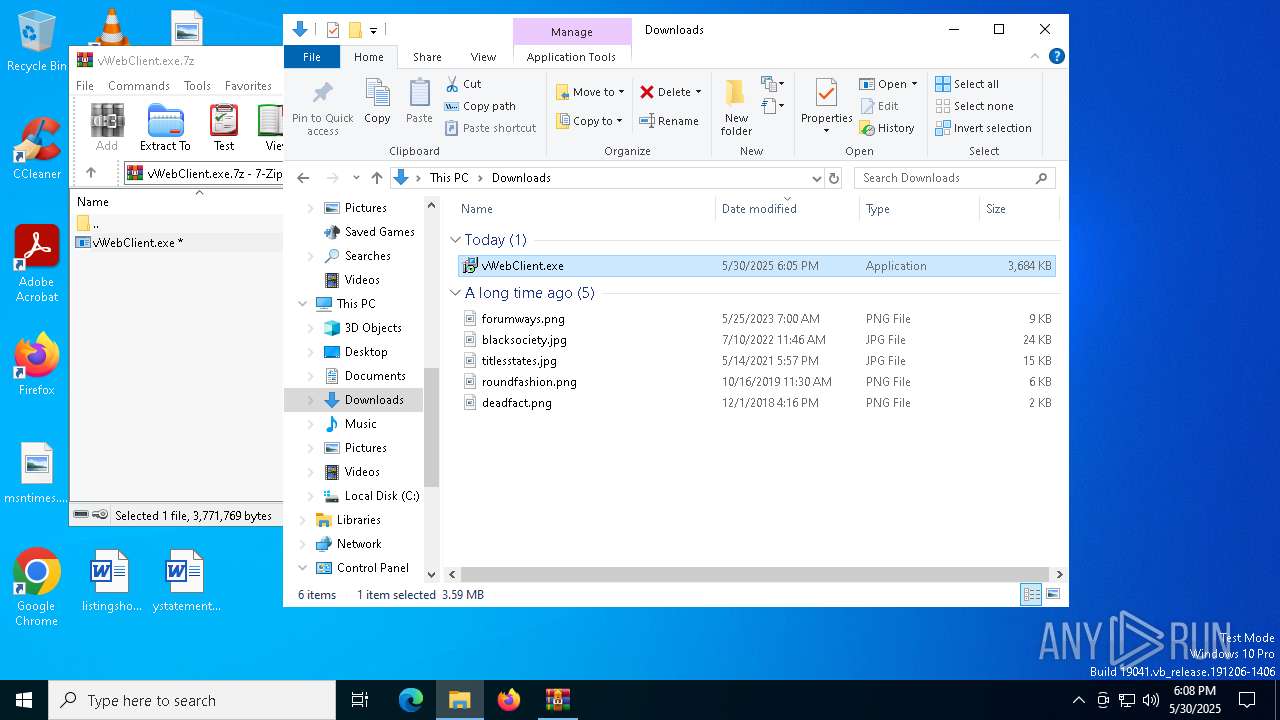
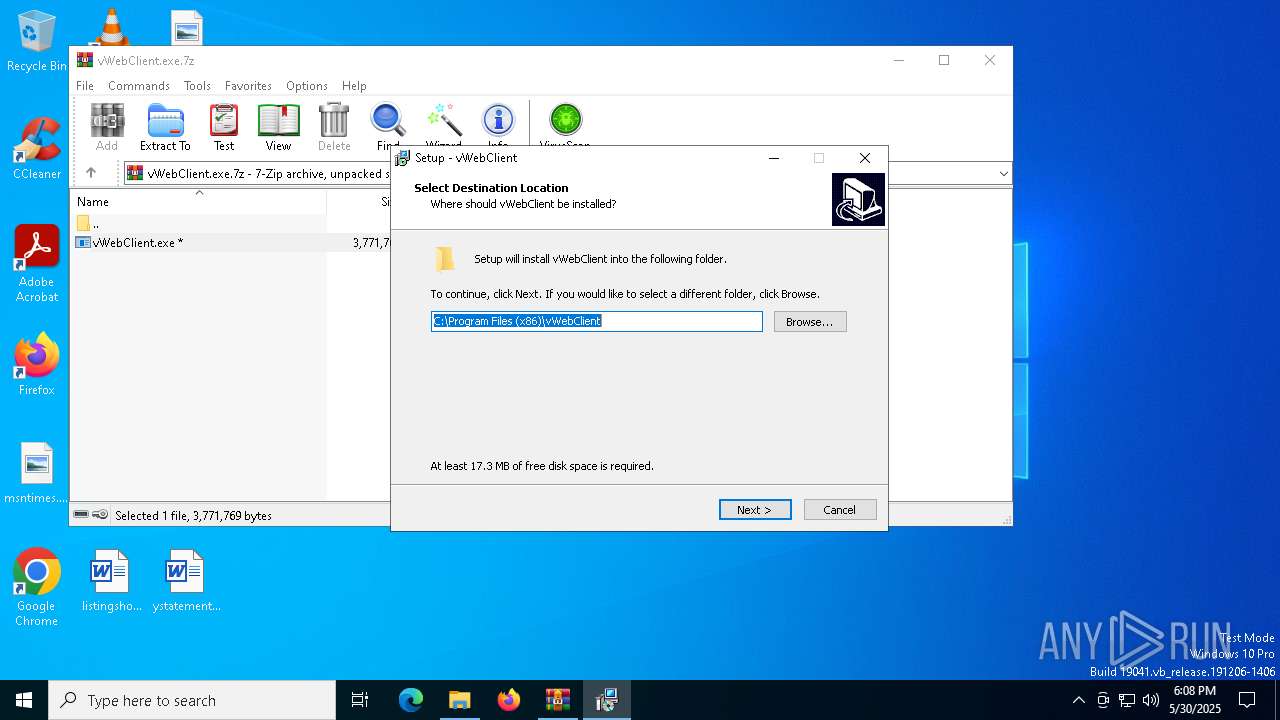
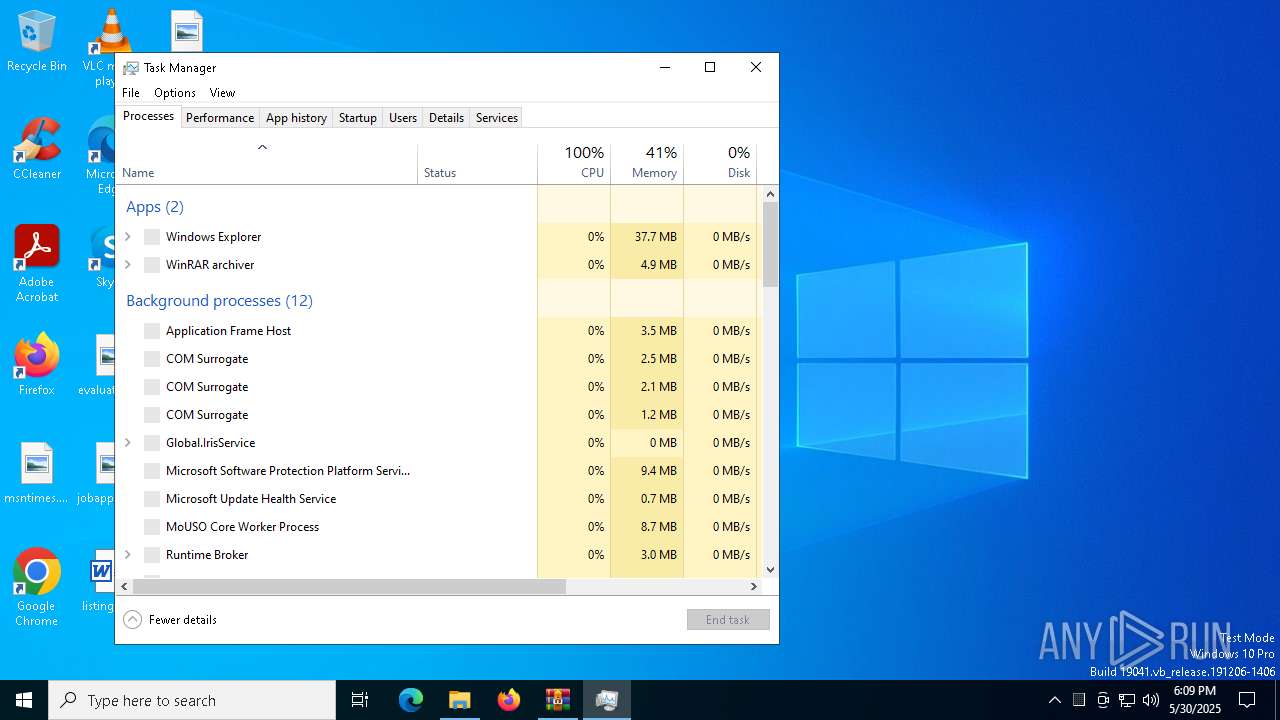
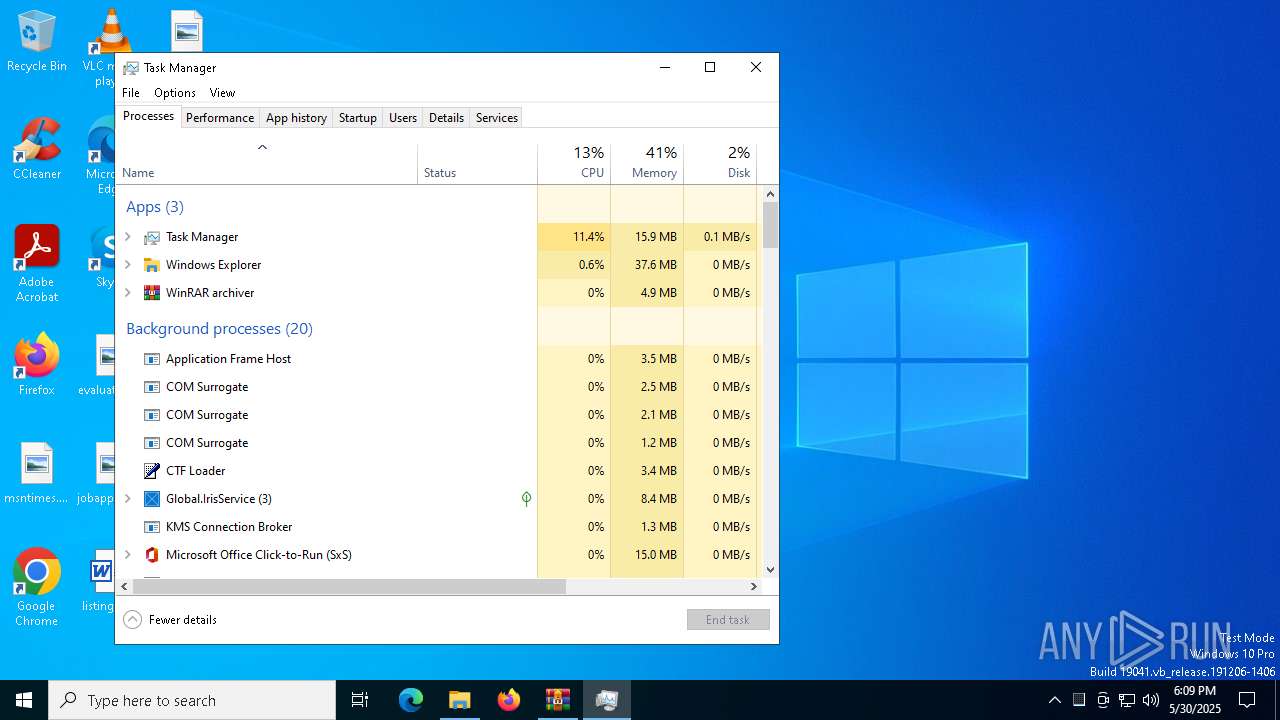
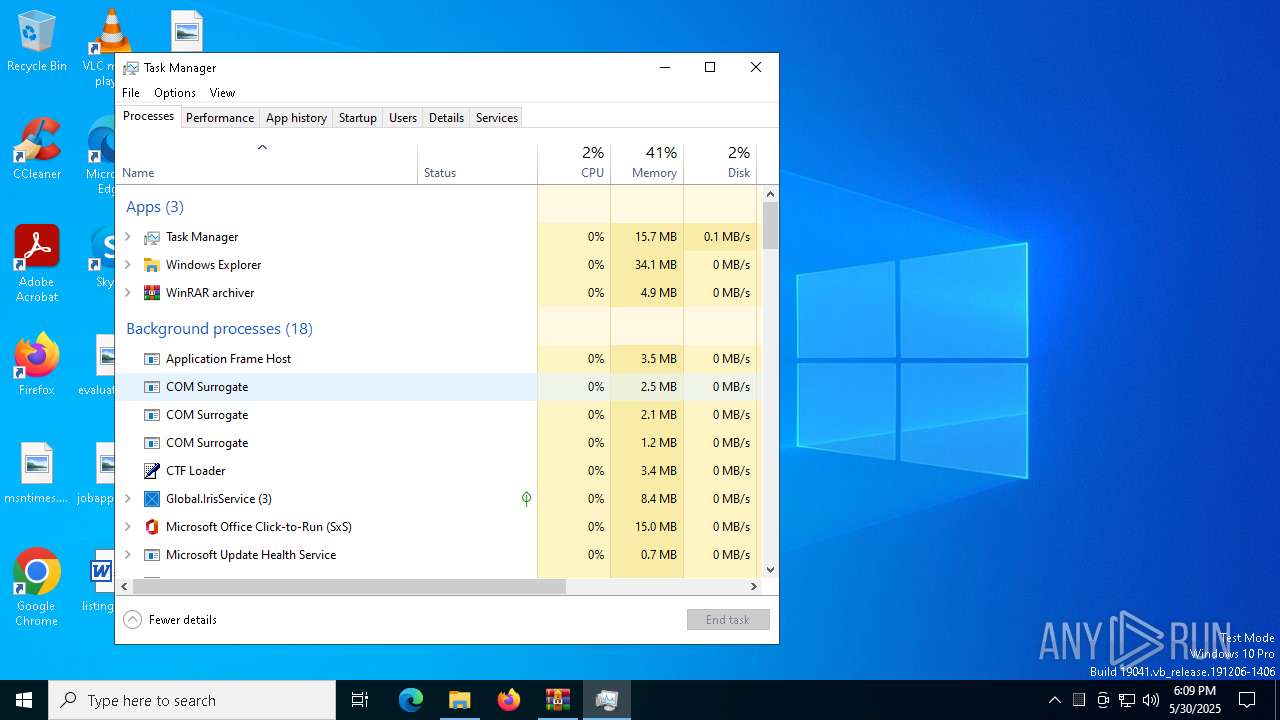
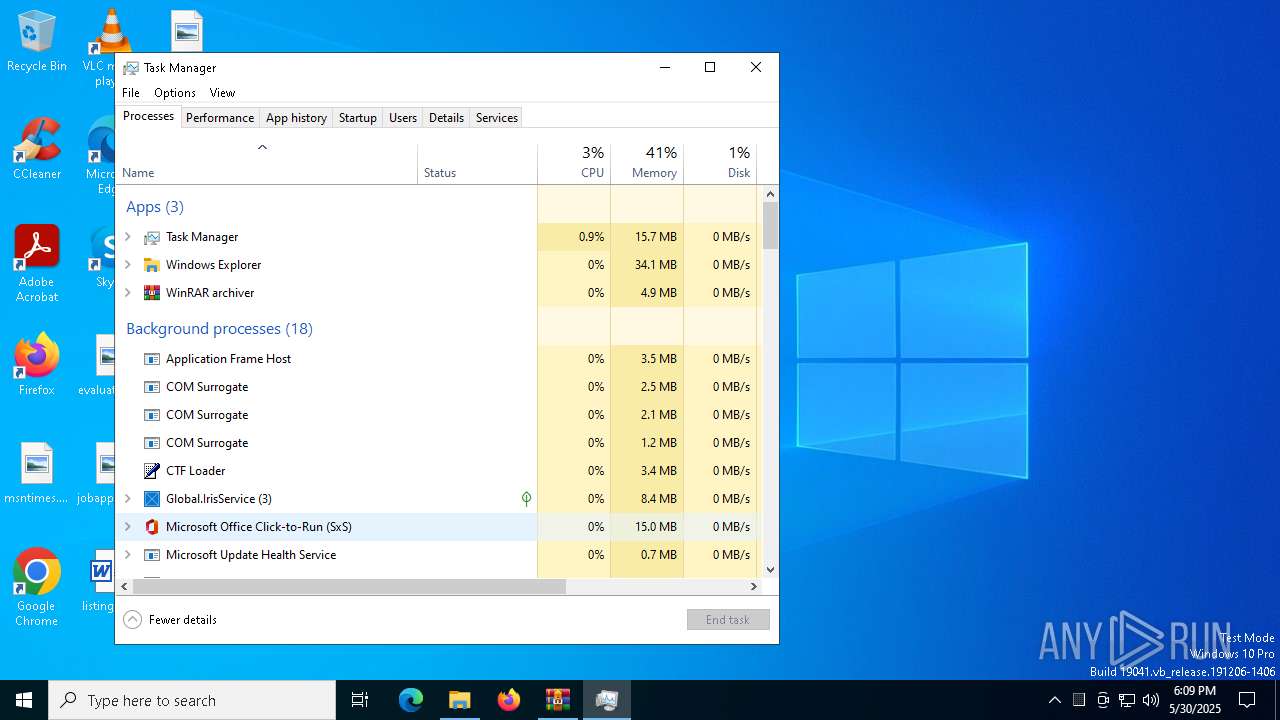
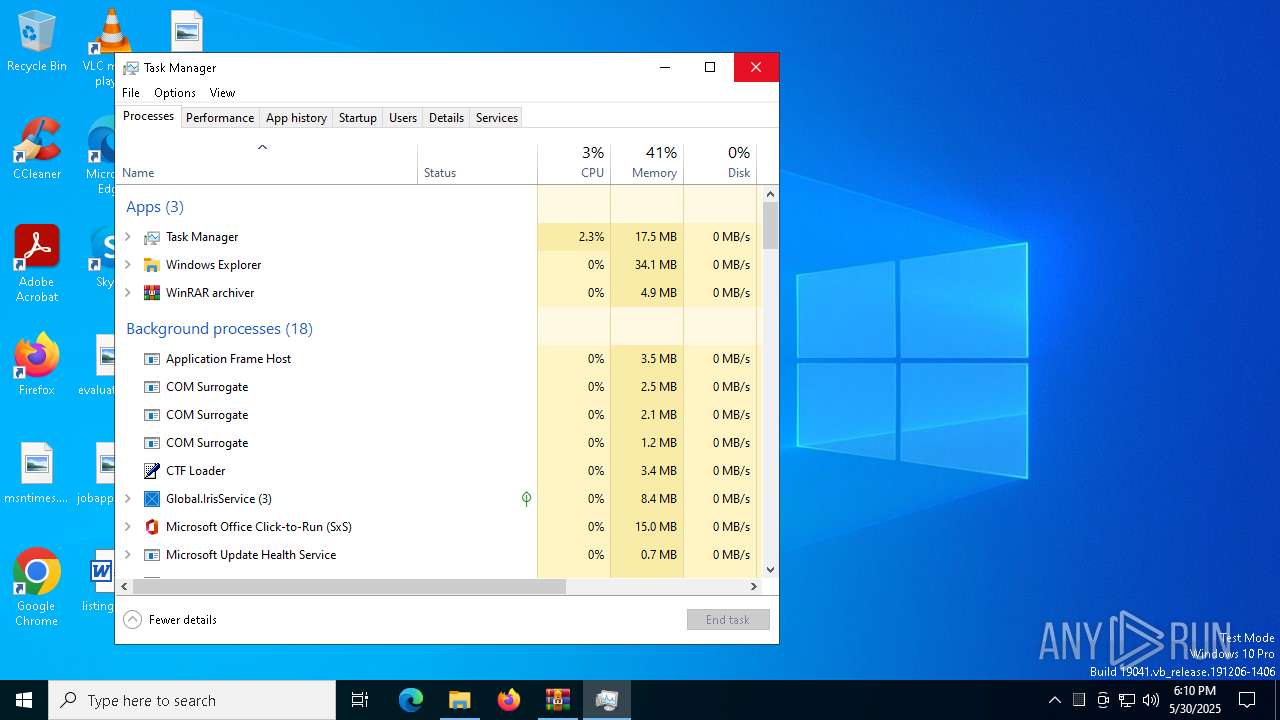
Manual execution by a user
- vWebClient.exe (PID: 7856)
- Taskmgr.exe (PID: 3868)
- Taskmgr.exe (PID: 3156)
- unins000.exe (PID: 4696)
Process checks computer location settings
- vWebClient.tmp (PID: 8028)
Checks supported languages
- vWebClient.tmp (PID: 8028)
- vWebClient.exe (PID: 4728)
- vWebClient.tmp (PID: 7752)
- vWebClient.exe (PID: 7856)
Reads the computer name
- vWebClient.tmp (PID: 8028)
- vWebClient.tmp (PID: 7752)
Create files in a temporary directory
- vWebClient.exe (PID: 7856)
- vWebClient.exe (PID: 4728)
- vWebClient.tmp (PID: 7752)
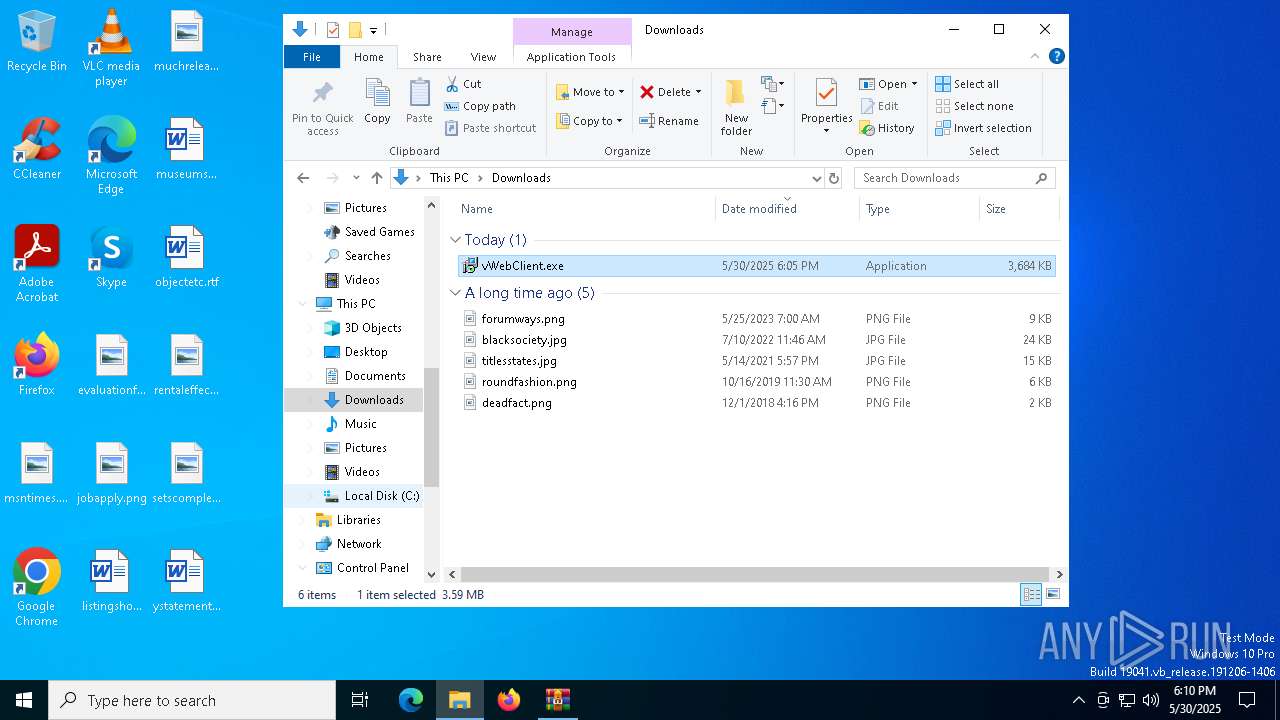
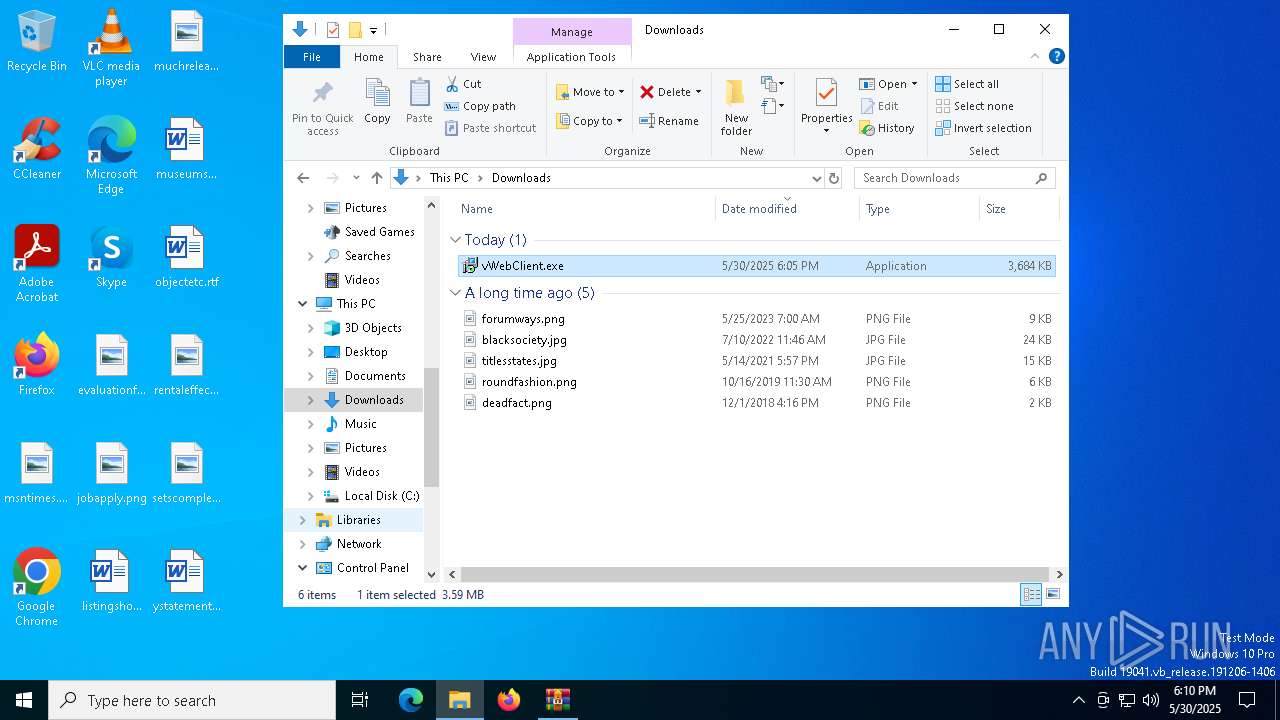
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6044)
The sample compiled with english language support
- vWebClient.tmp (PID: 7752)
Detects InnoSetup installer (YARA)
- vWebClient.tmp (PID: 8028)
- vWebClient.exe (PID: 7856)
- vWebClient.tmp (PID: 7752)
- vWebClient.exe (PID: 4728)
Compiled with Borland Delphi (YARA)
- vWebClient.tmp (PID: 8028)
- vWebClient.tmp (PID: 7752)
The sample compiled with chinese language support
- vWebClient.tmp (PID: 7752)
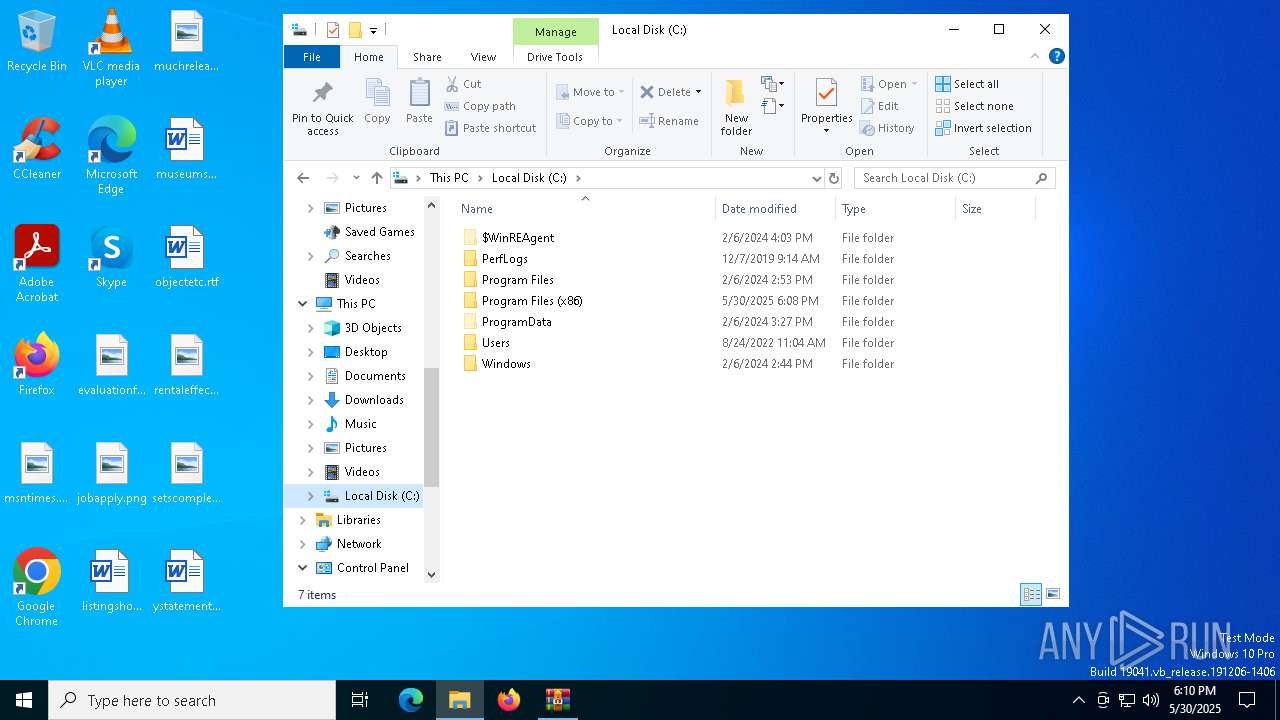
Creates files or folders in the user directory
- vWebClient.tmp (PID: 7752)
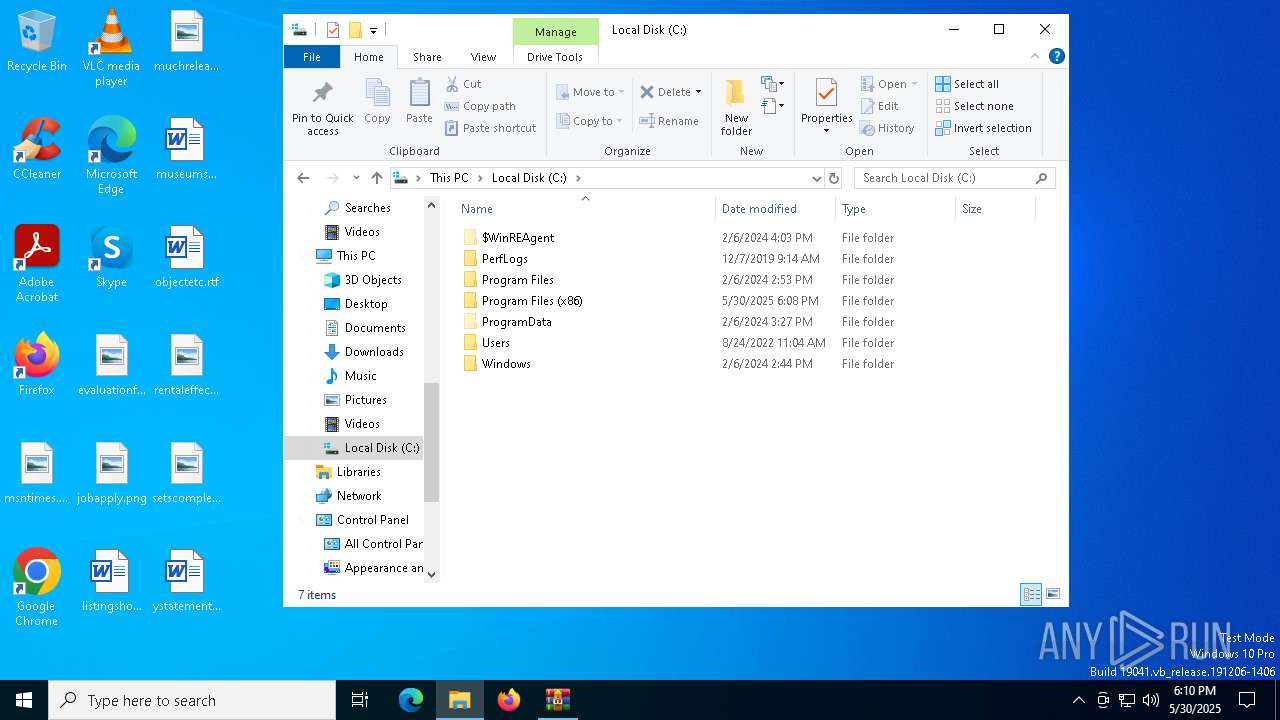
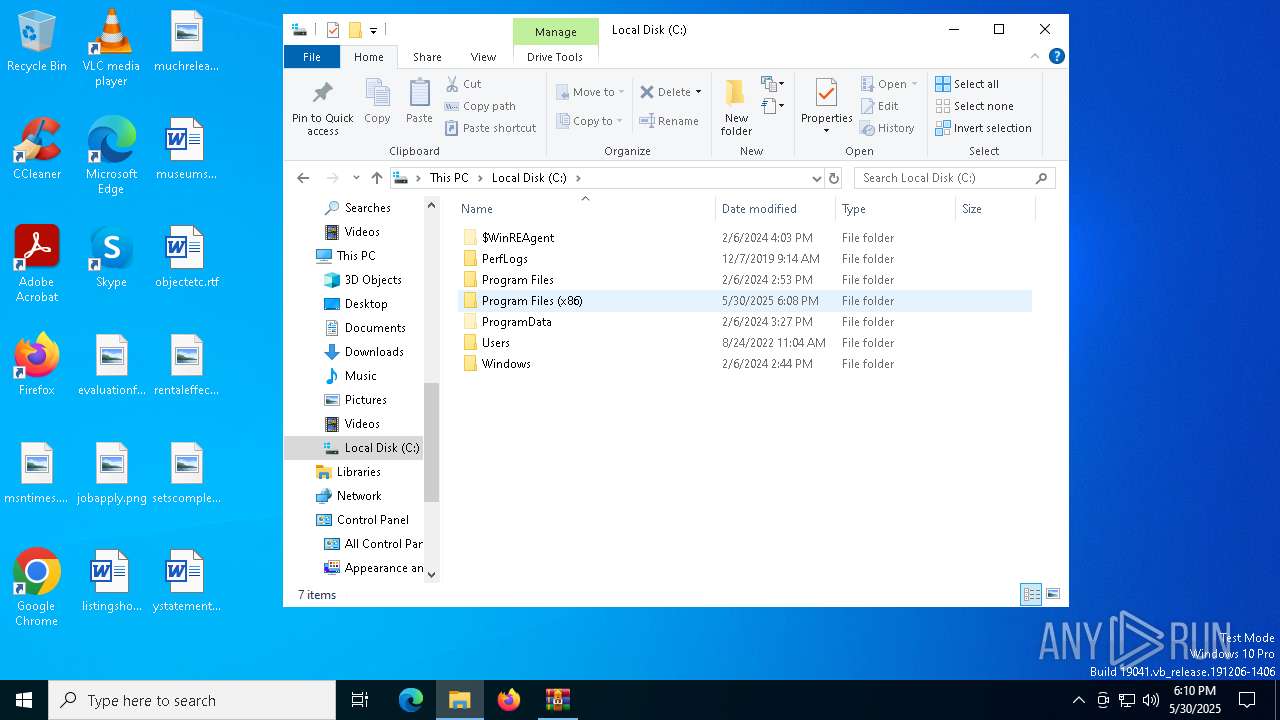
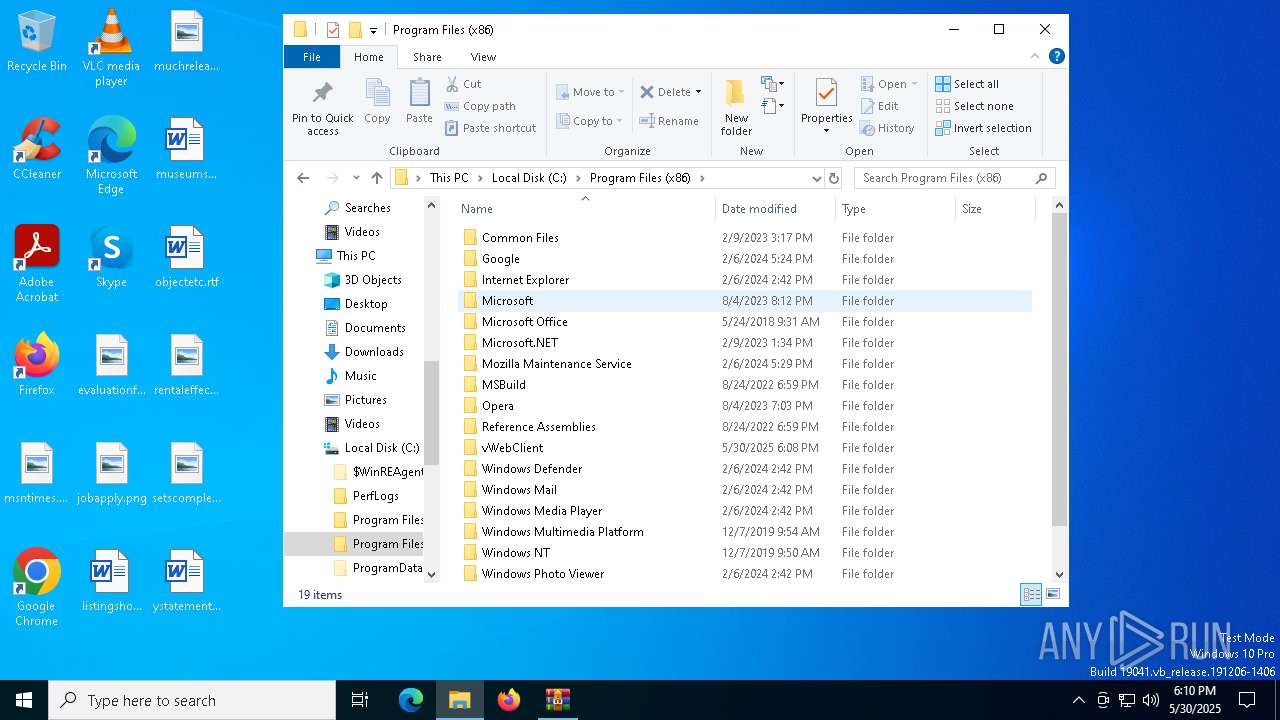
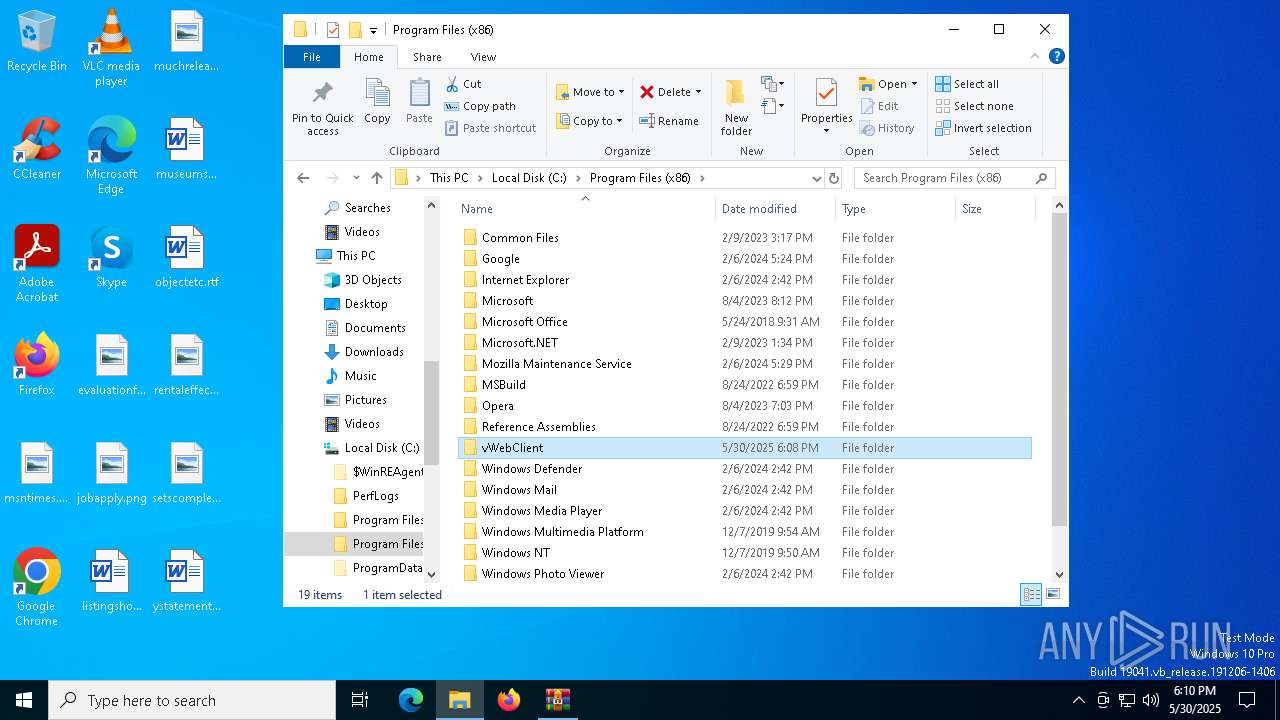
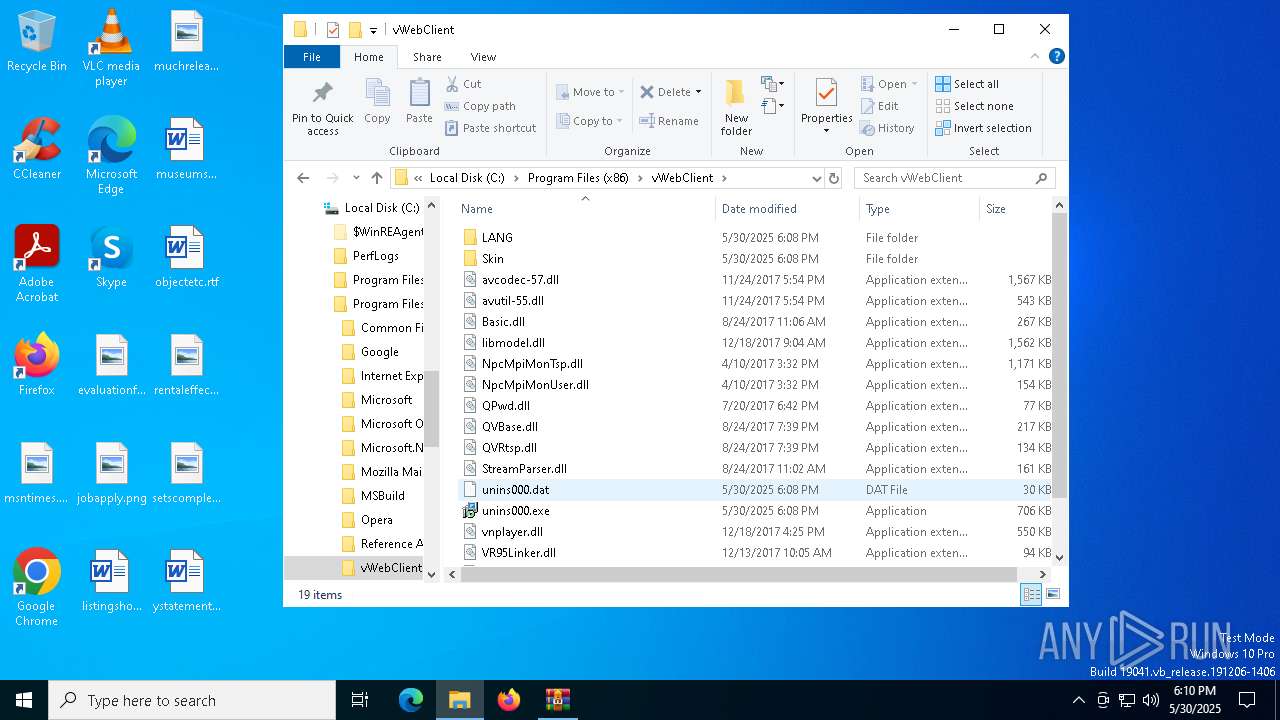
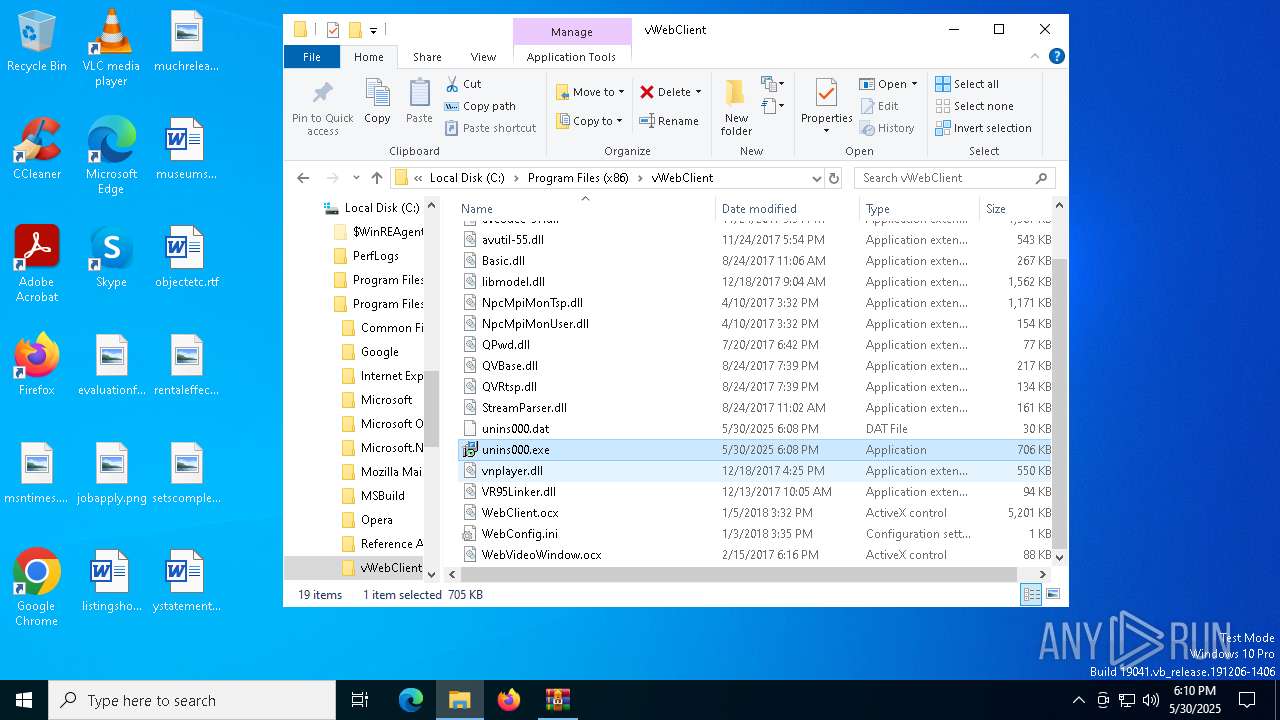
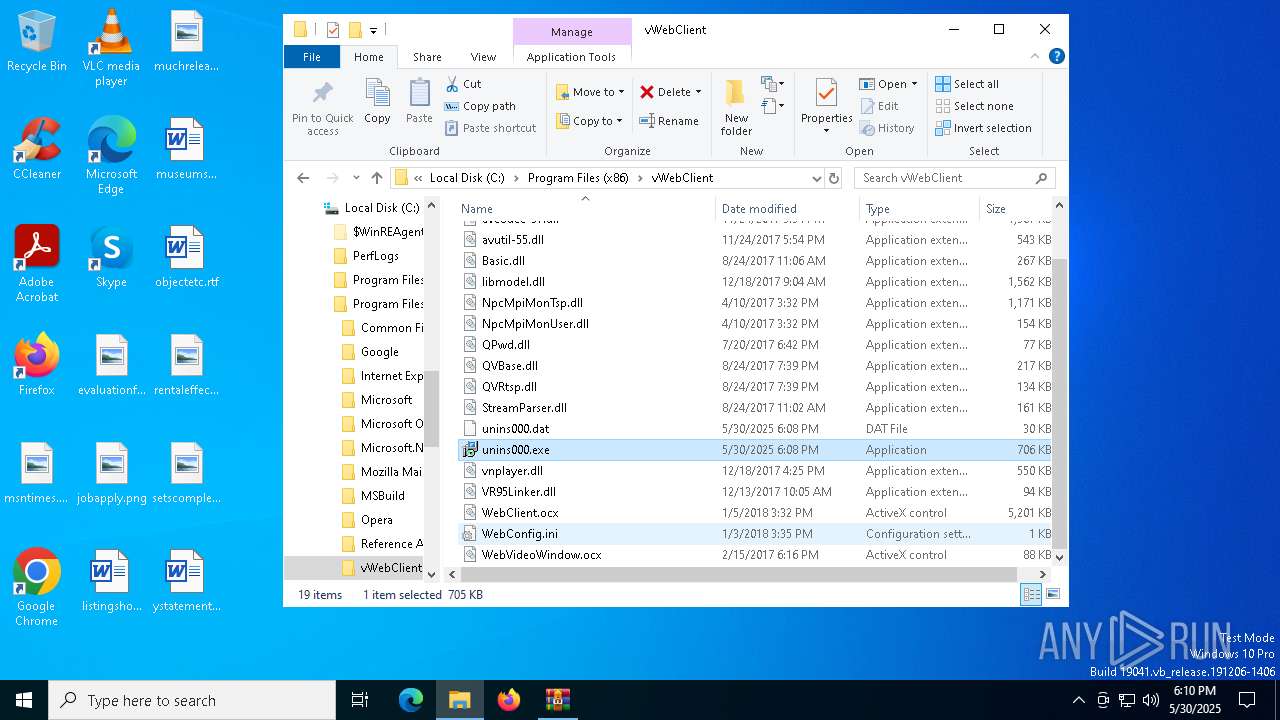
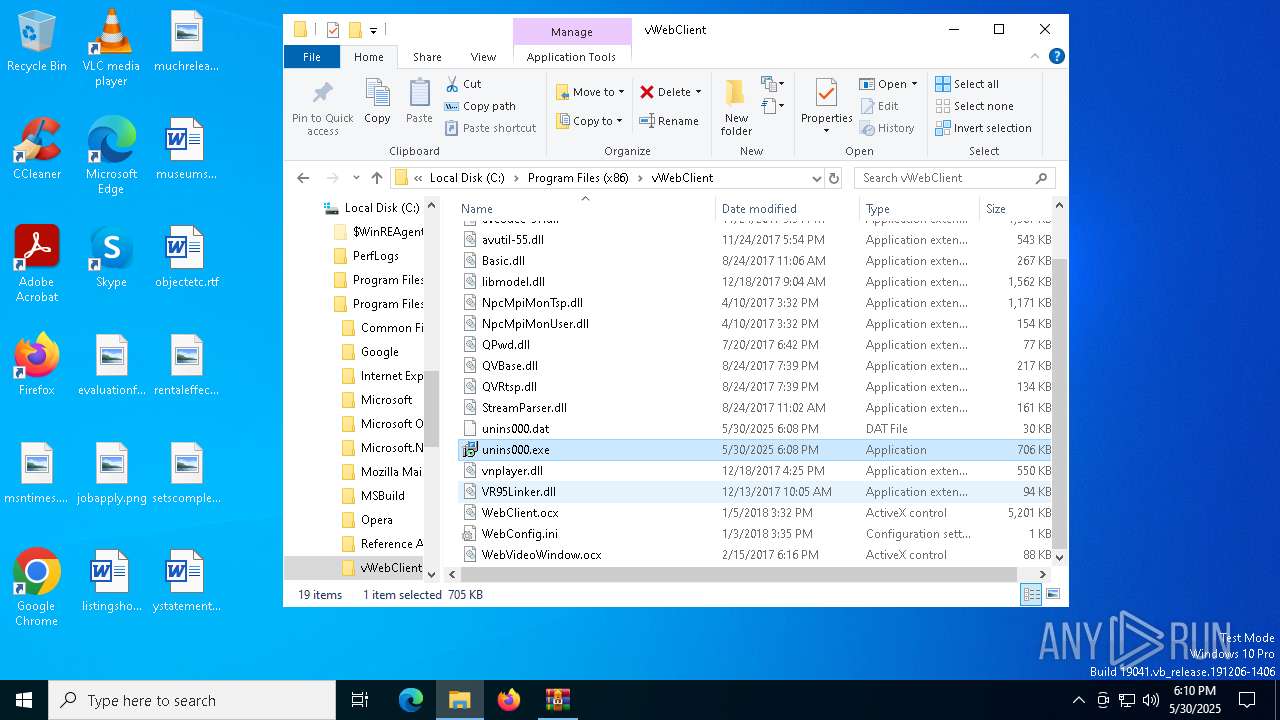
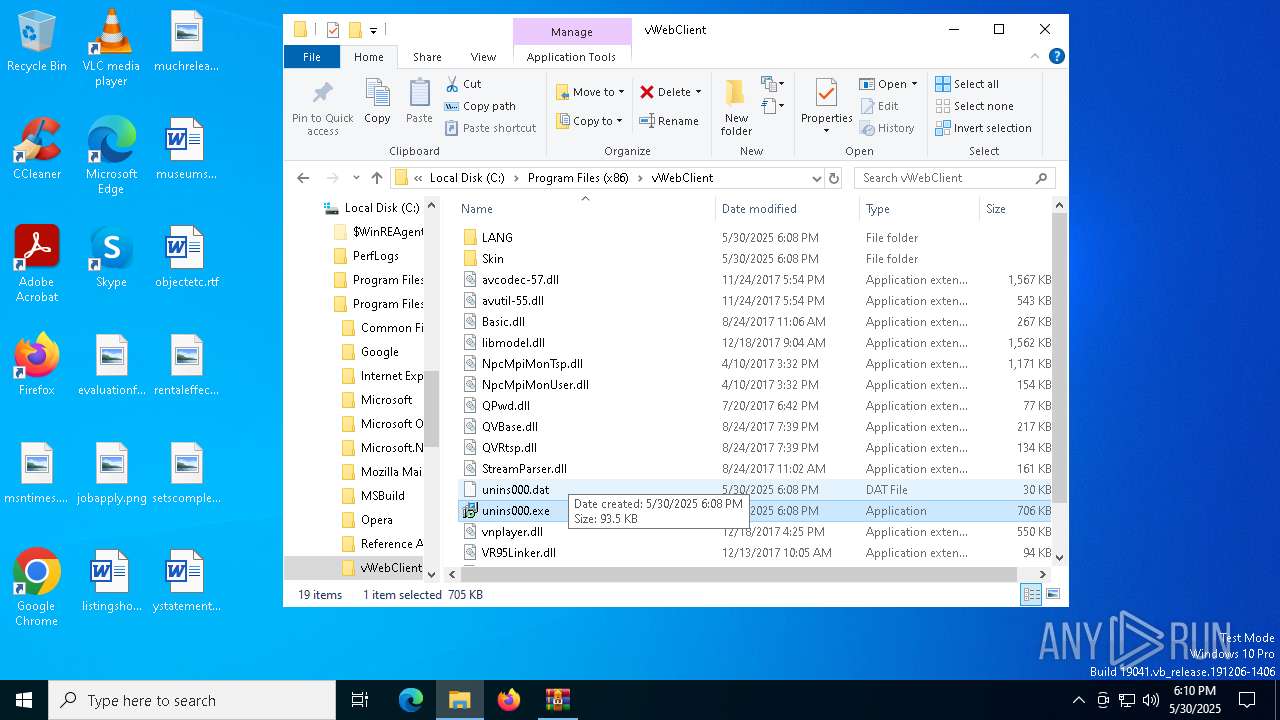
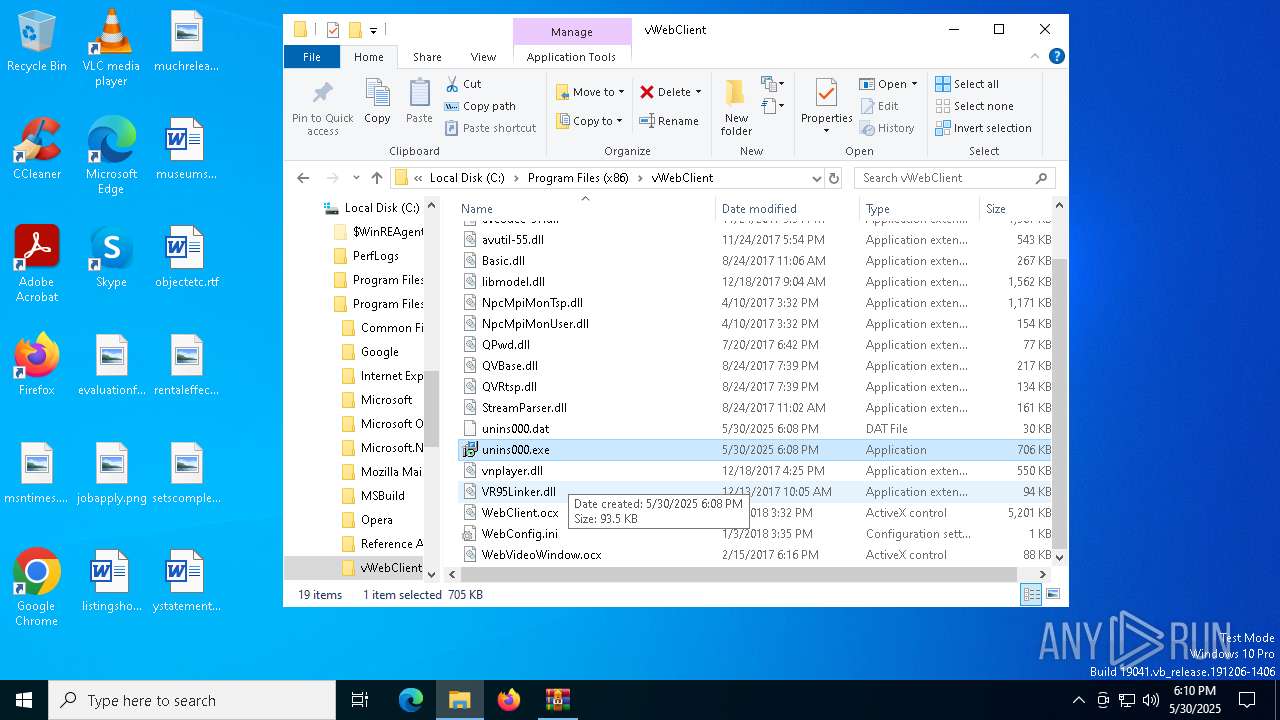
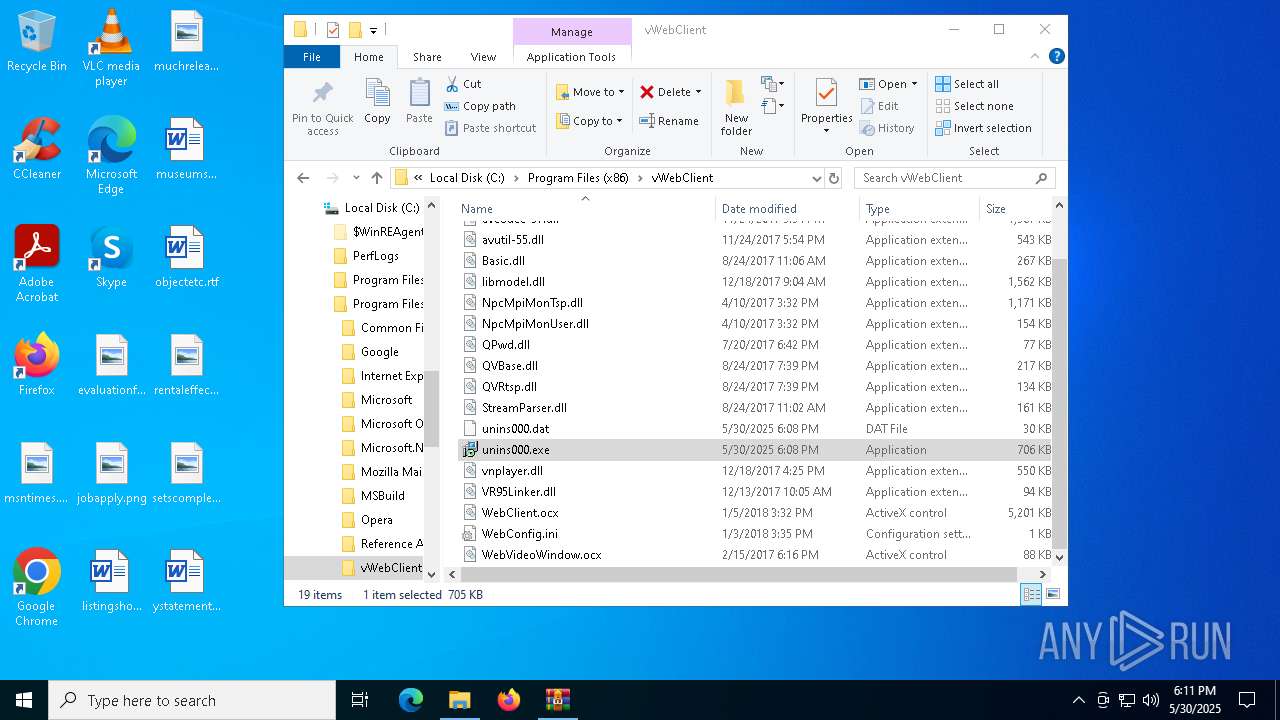
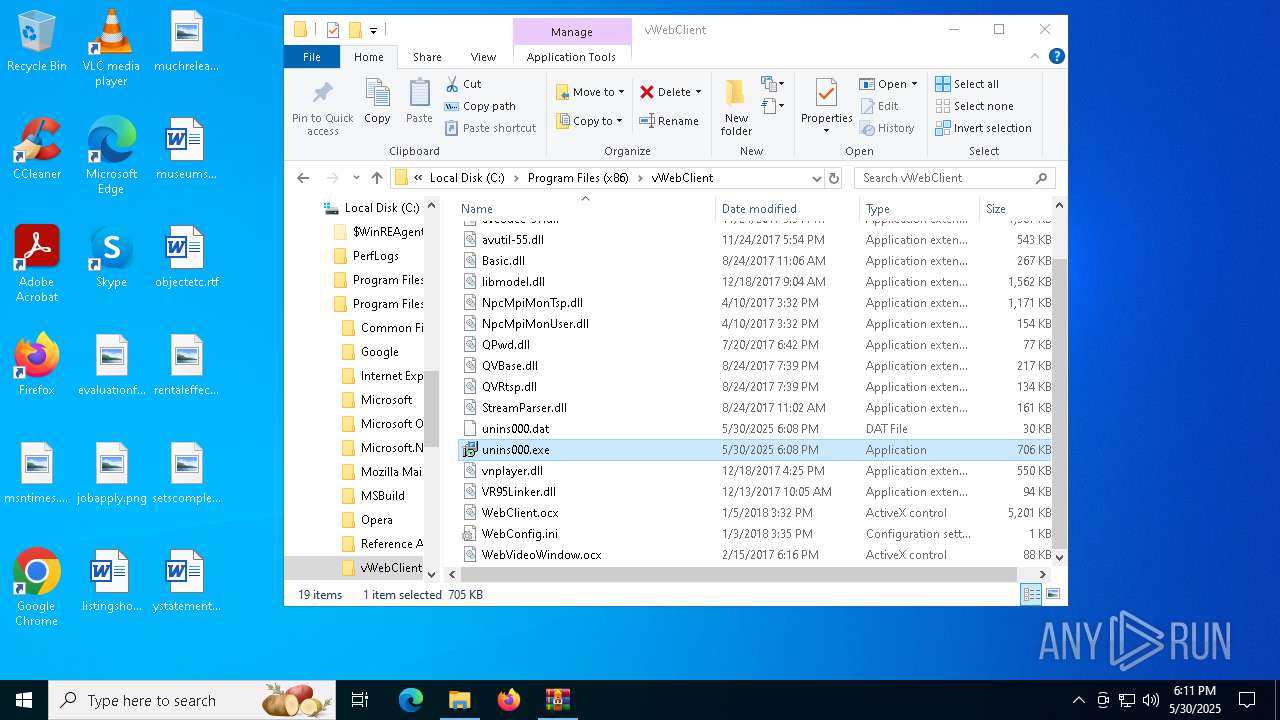
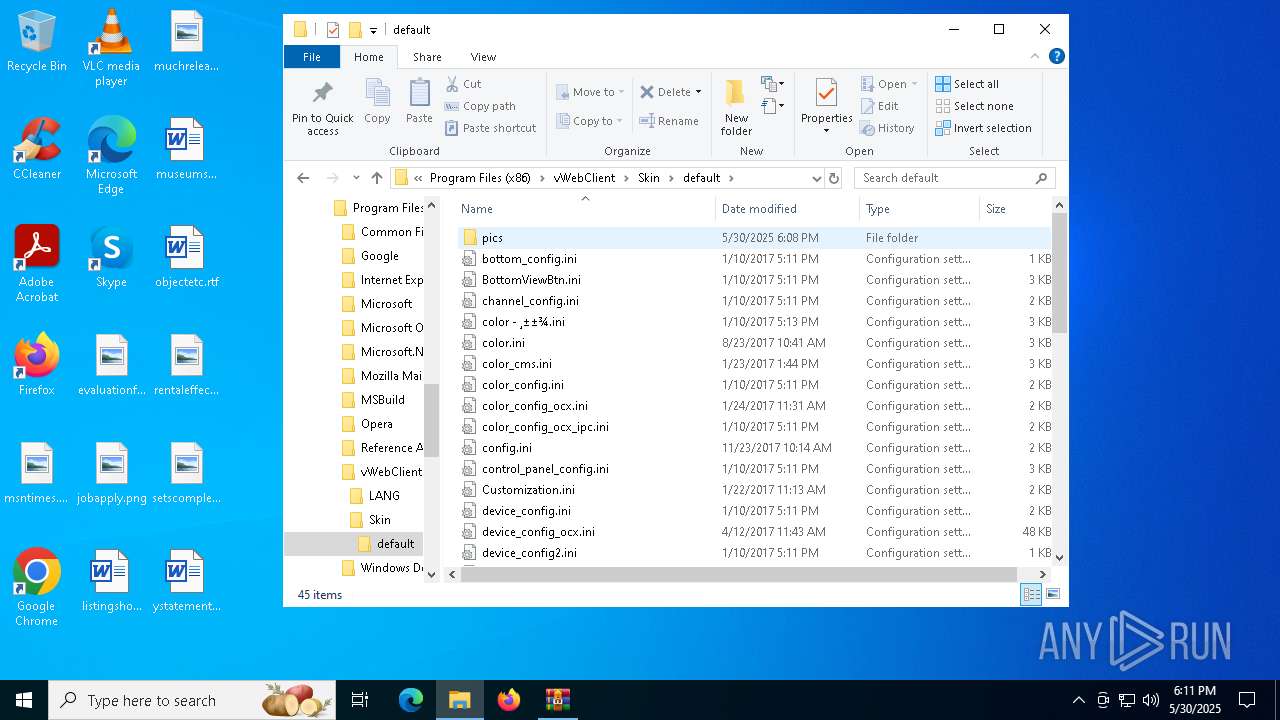
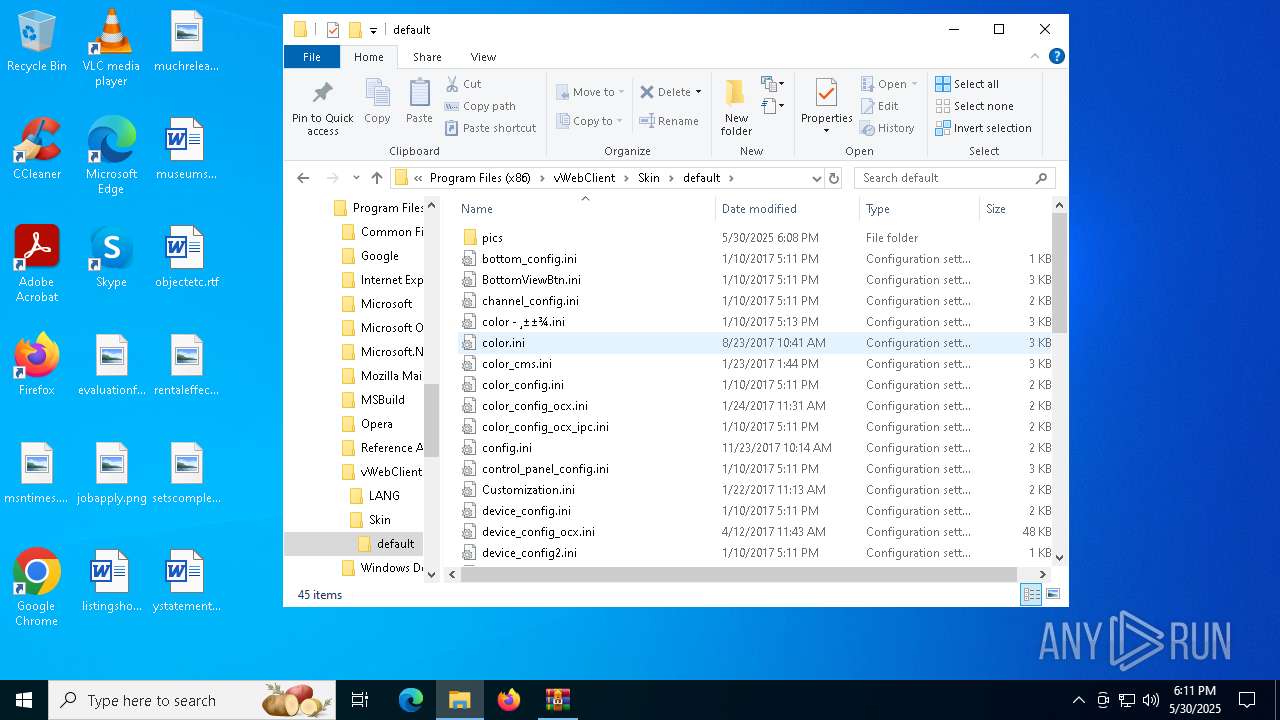
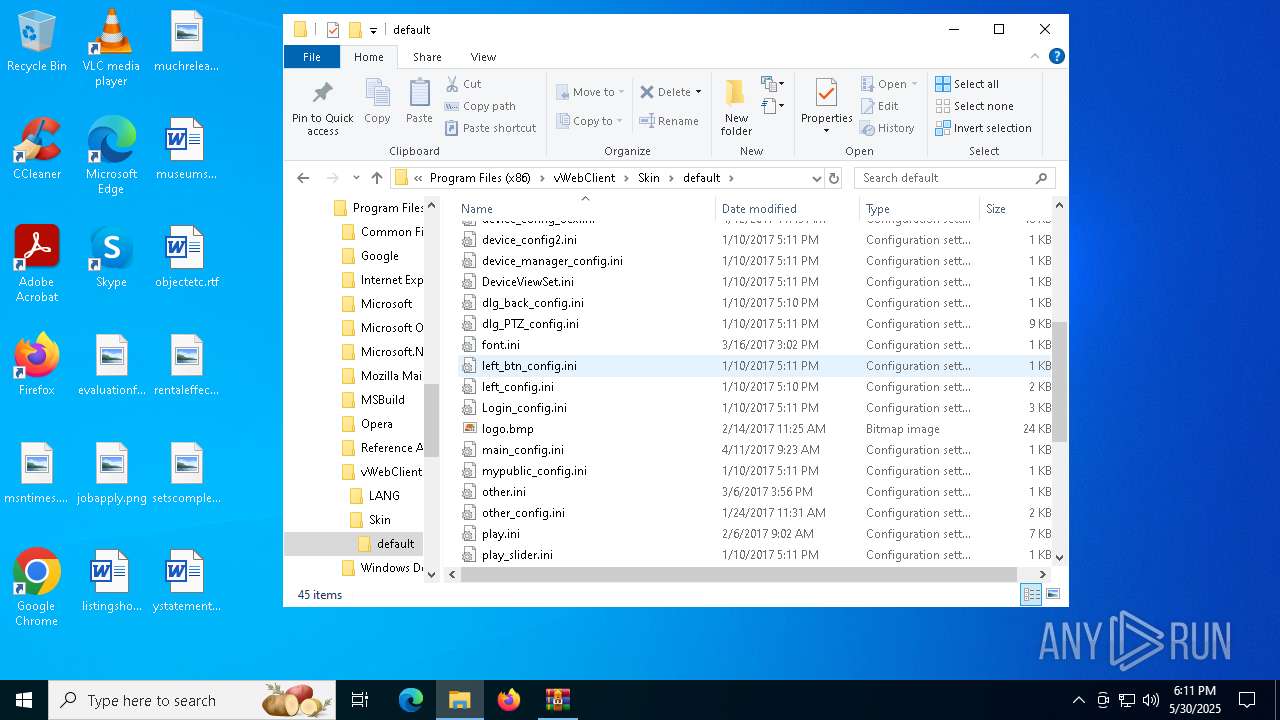
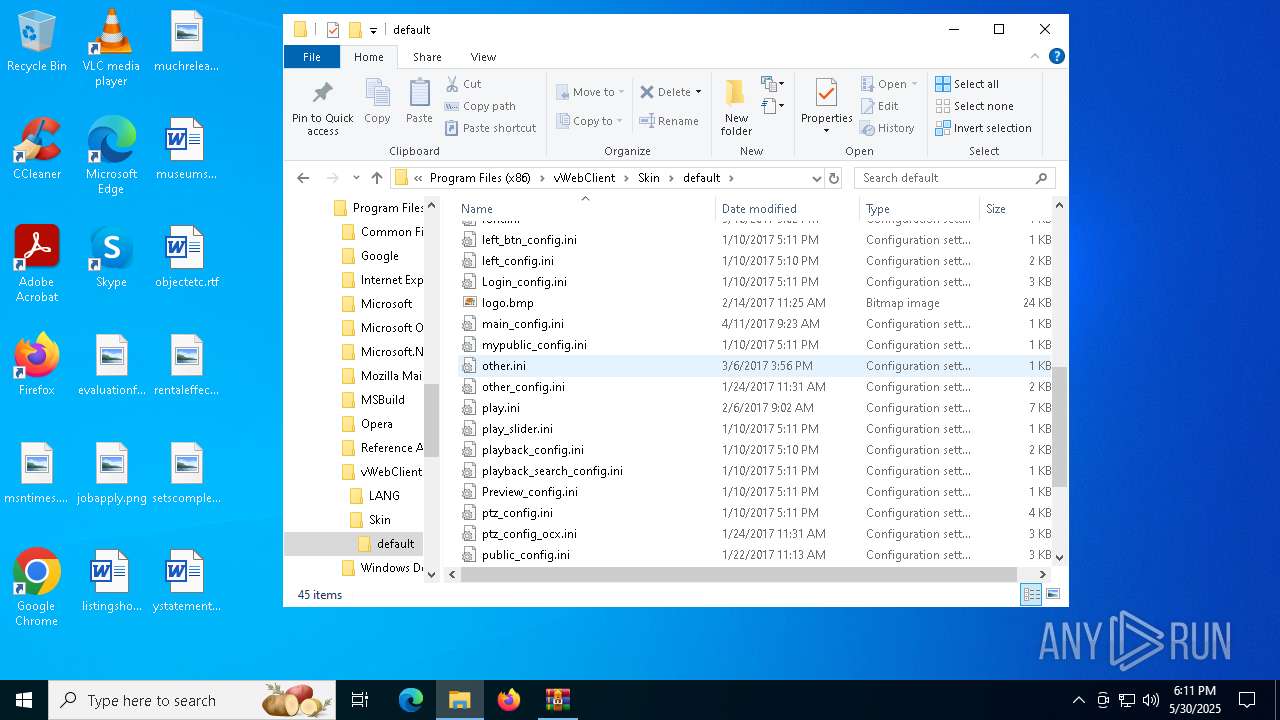
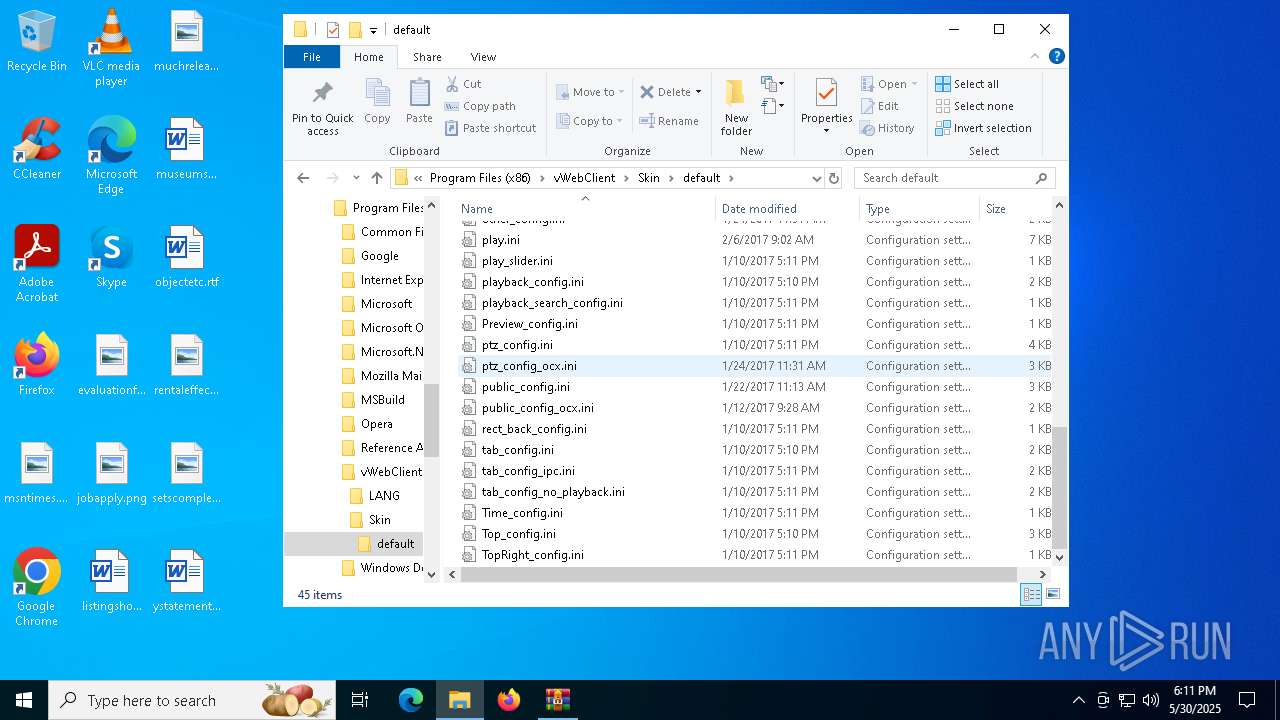
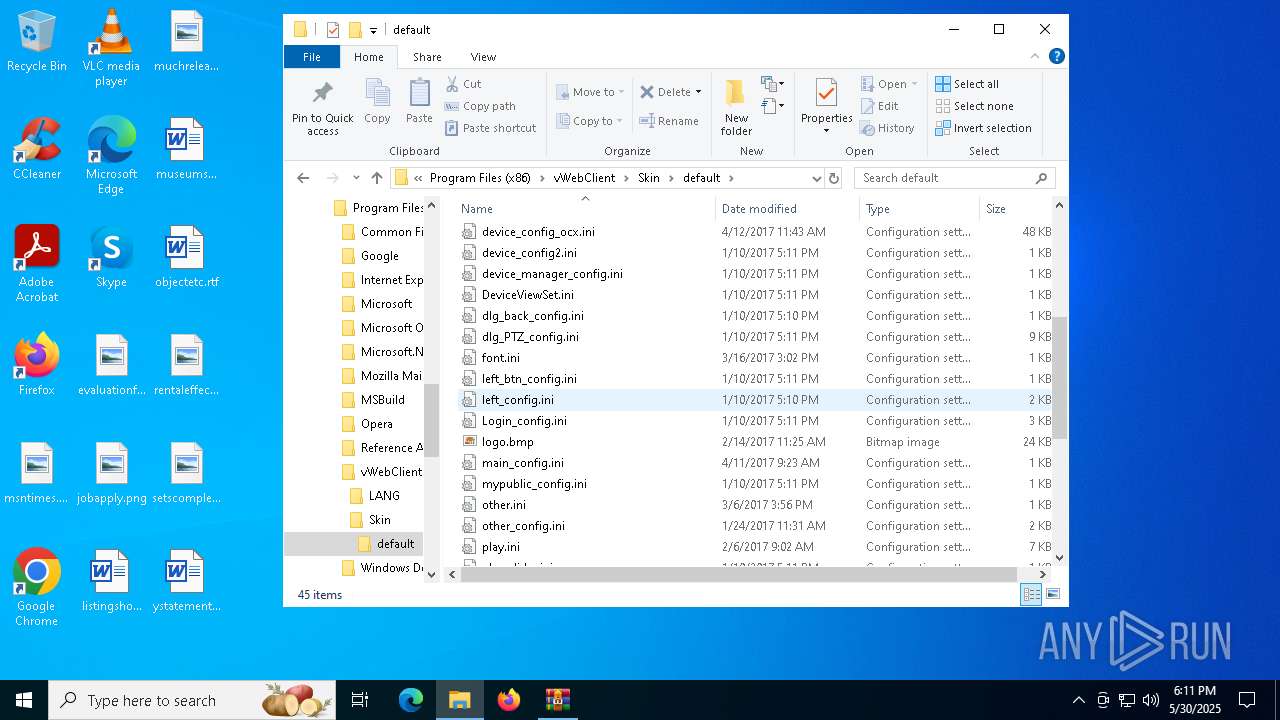
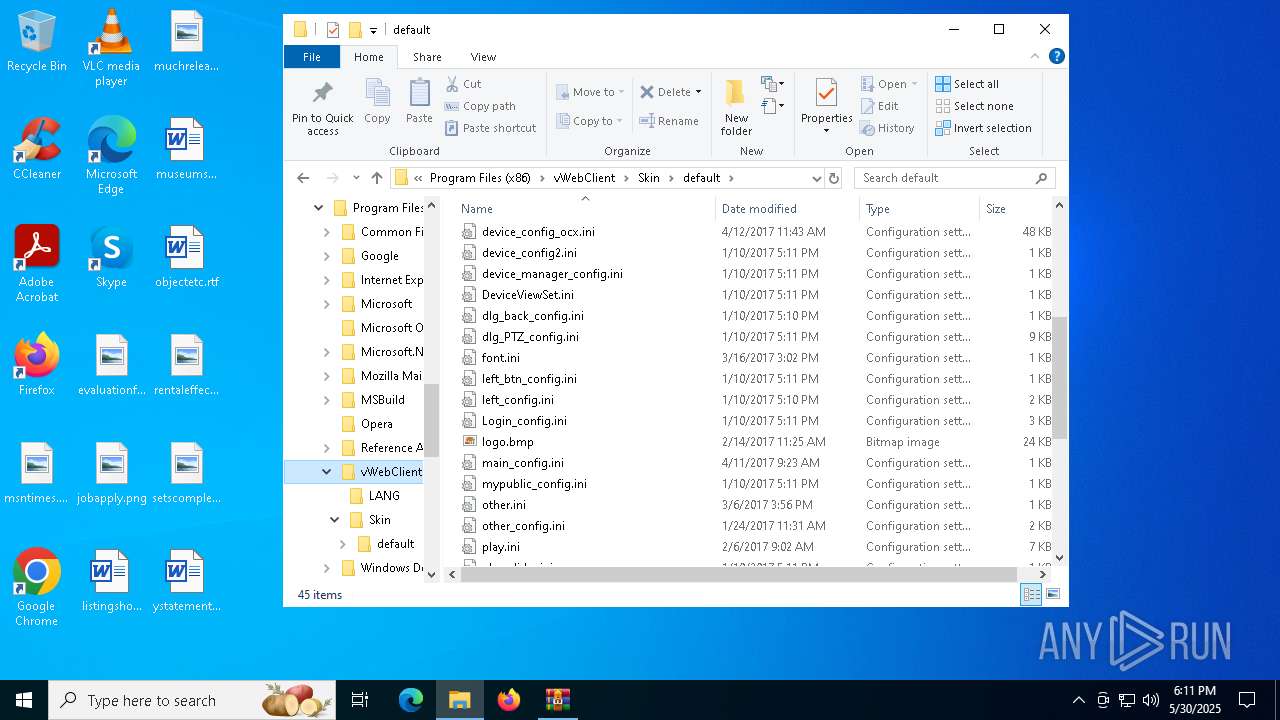
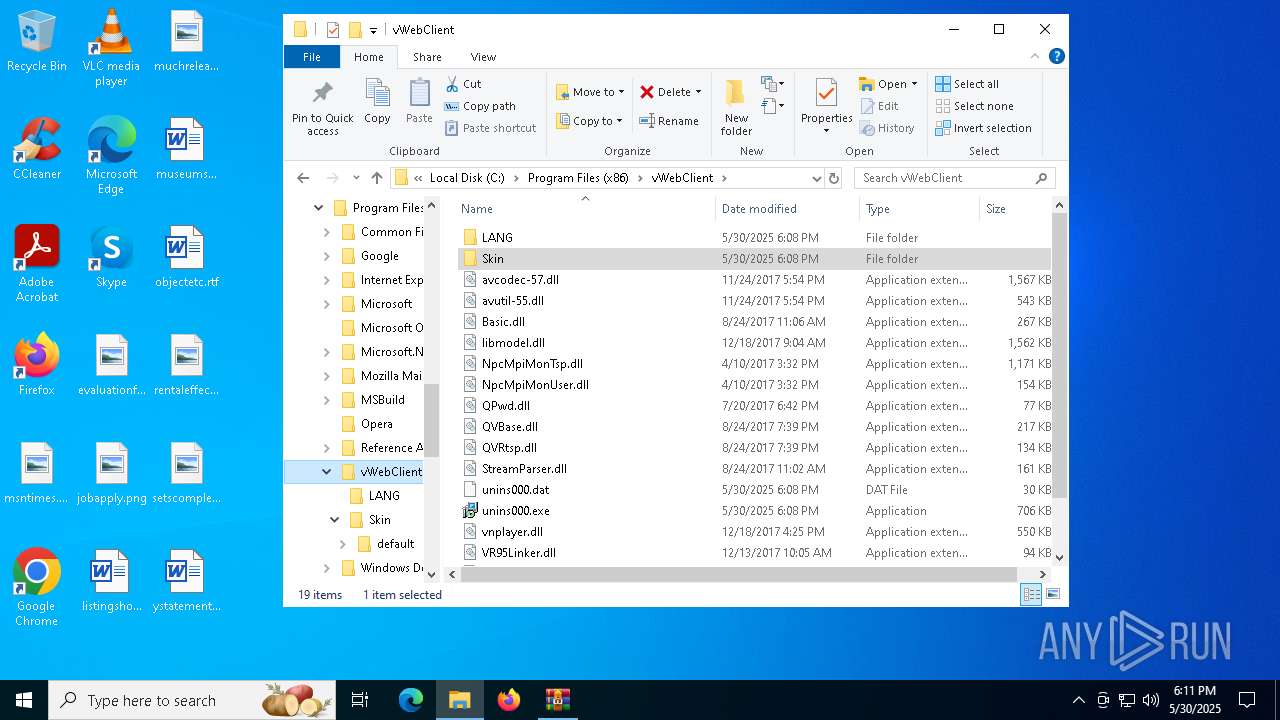
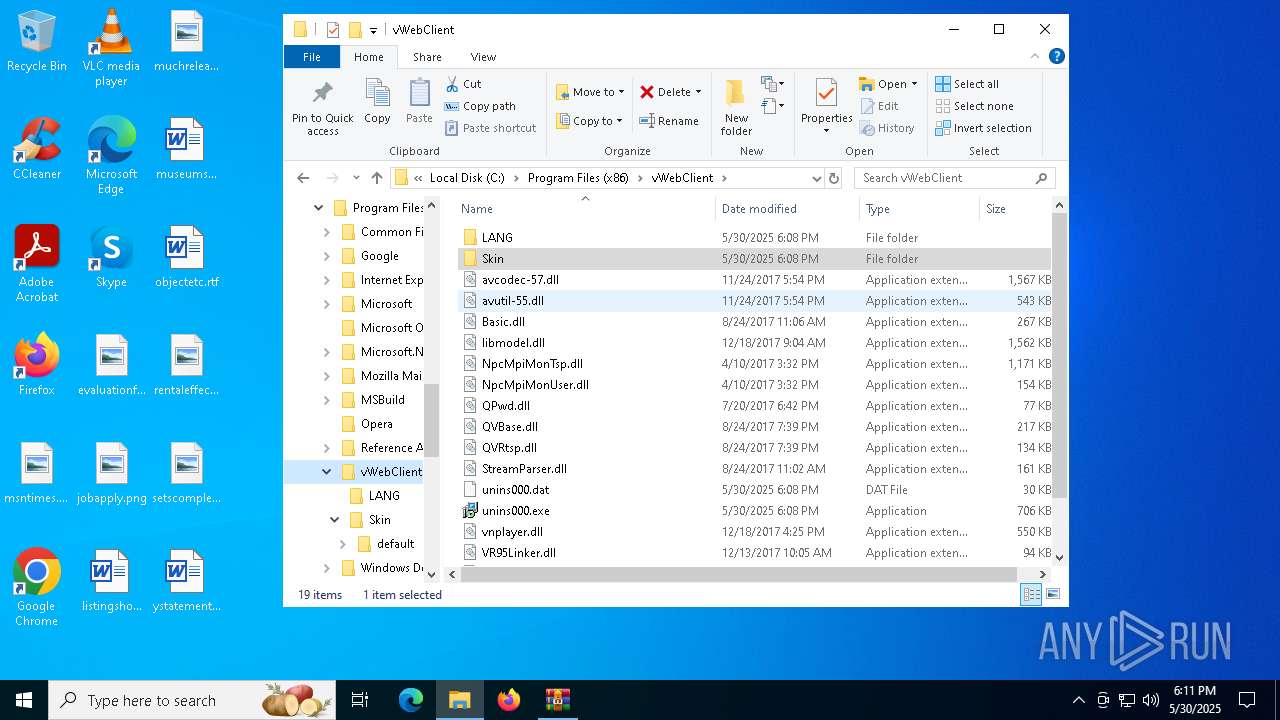
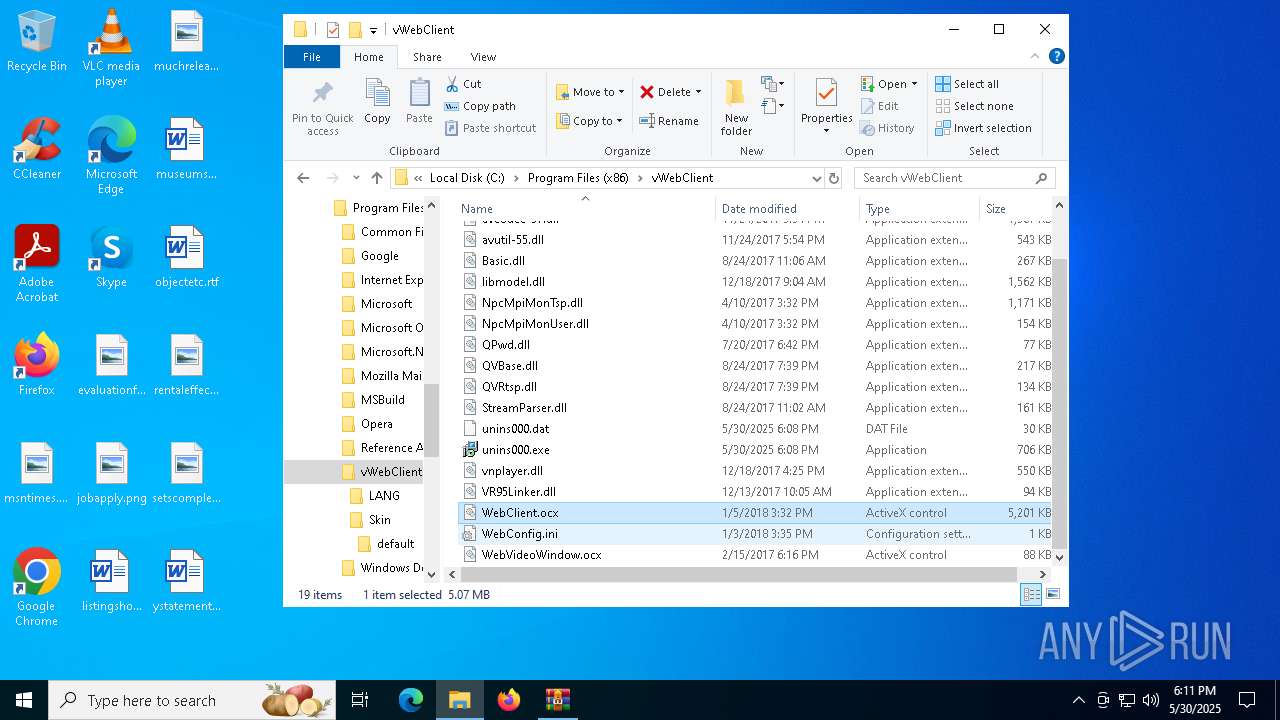
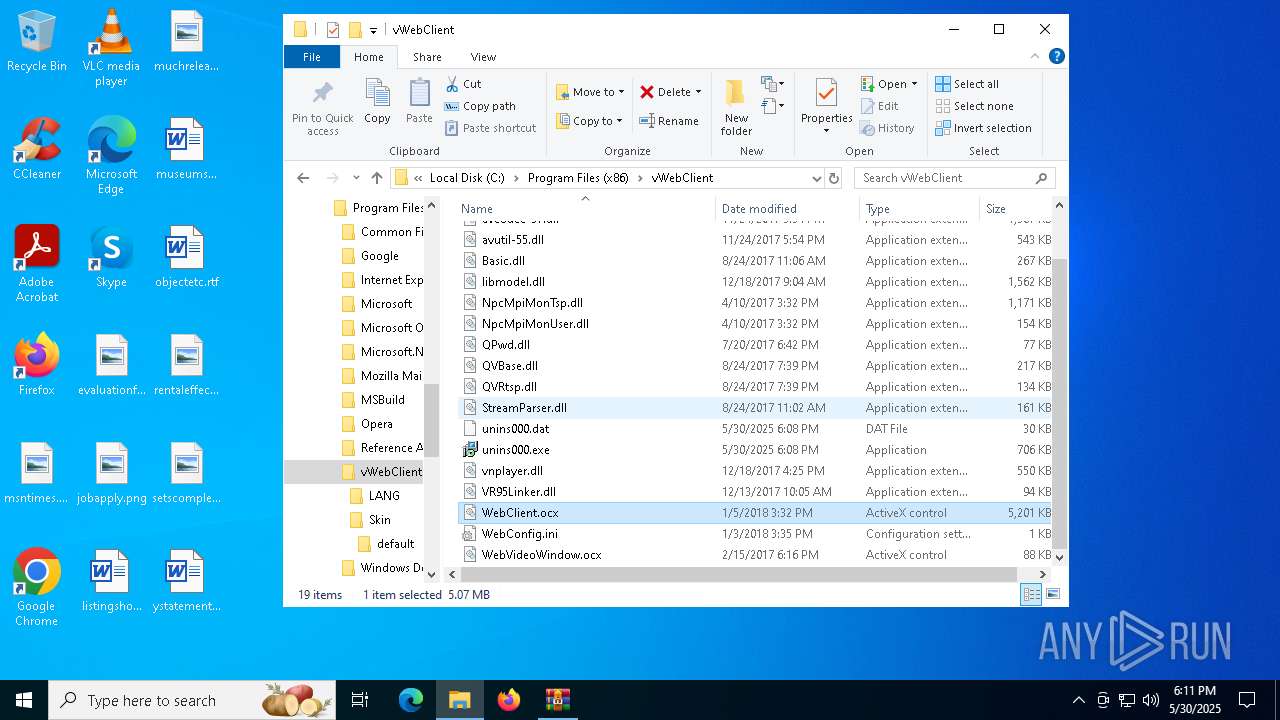
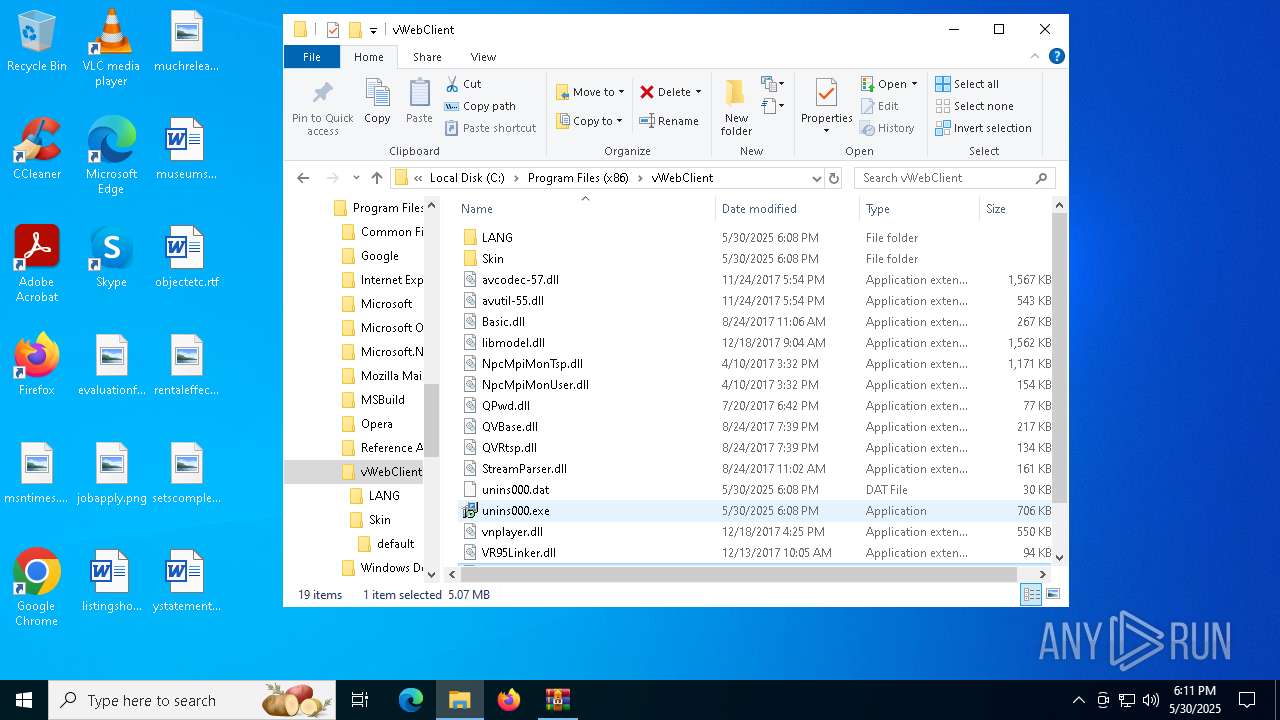
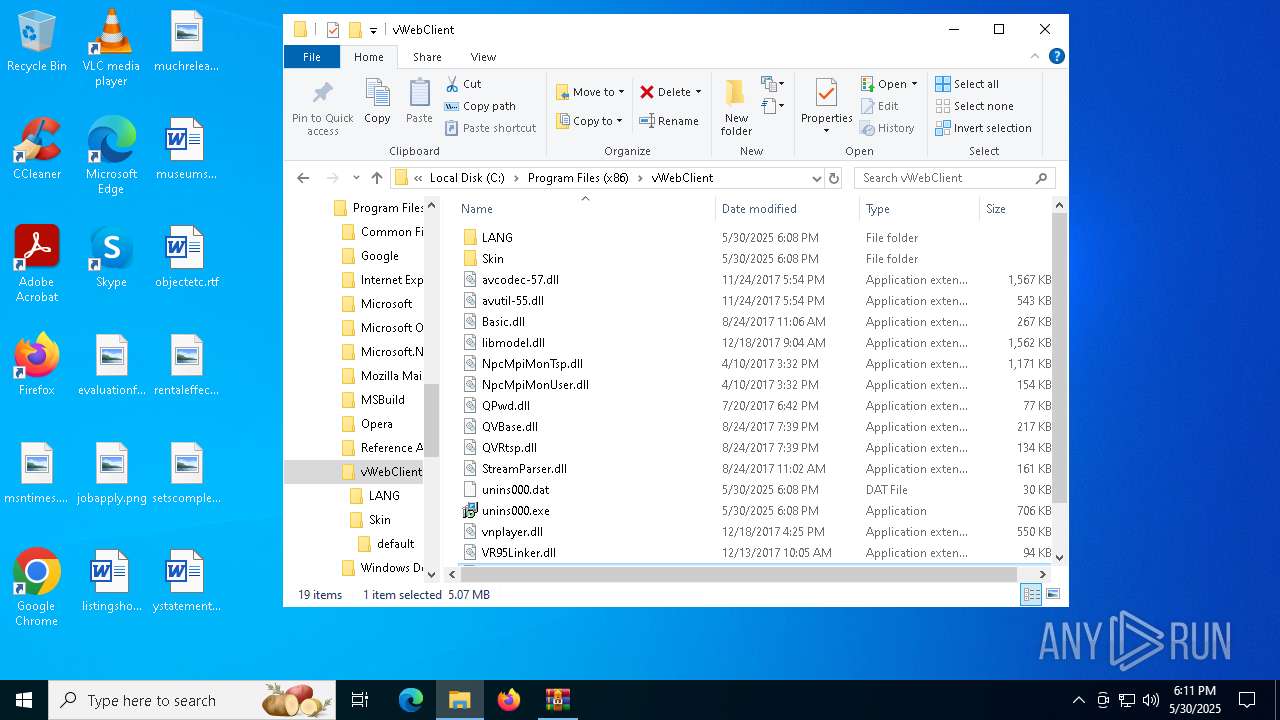
Creates files in the program directory
- vWebClient.tmp (PID: 7752)
Creates a software uninstall entry
- vWebClient.tmp (PID: 7752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:05:30 18:05:35+00:00 |
| ArchivedFileName: | vWebClient.exe |
Total processes
153
Monitored processes
15
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
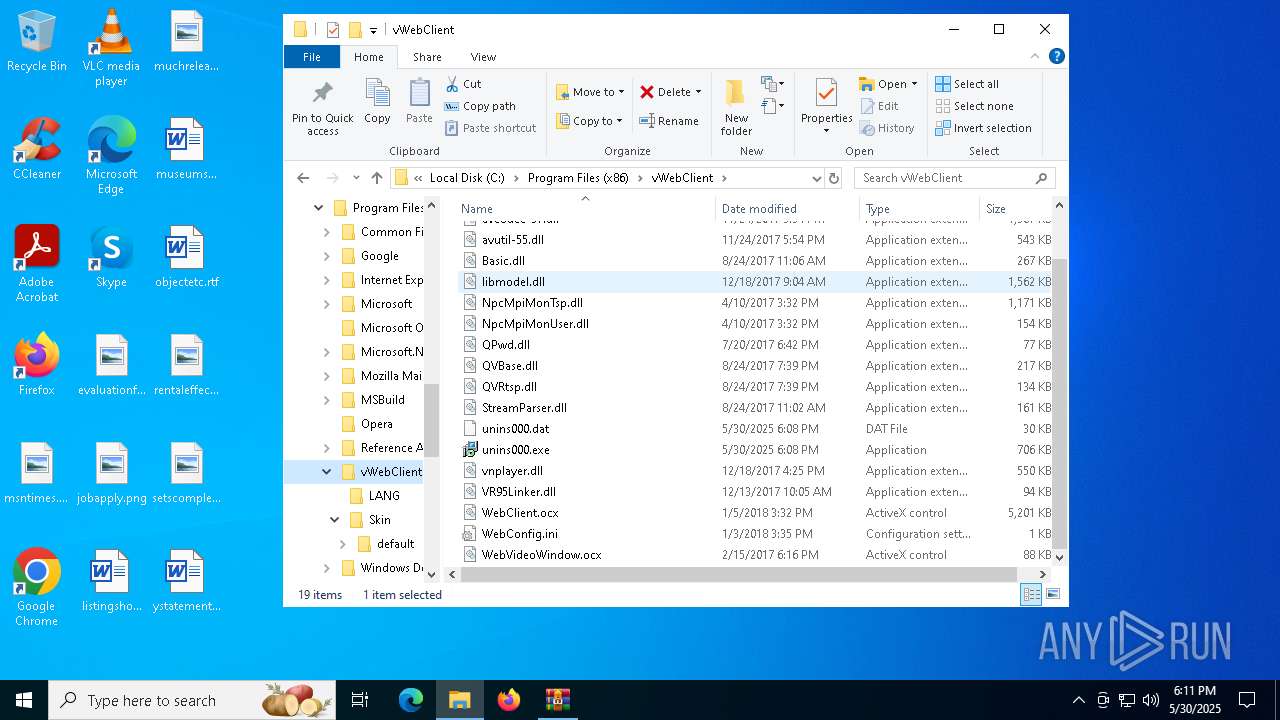
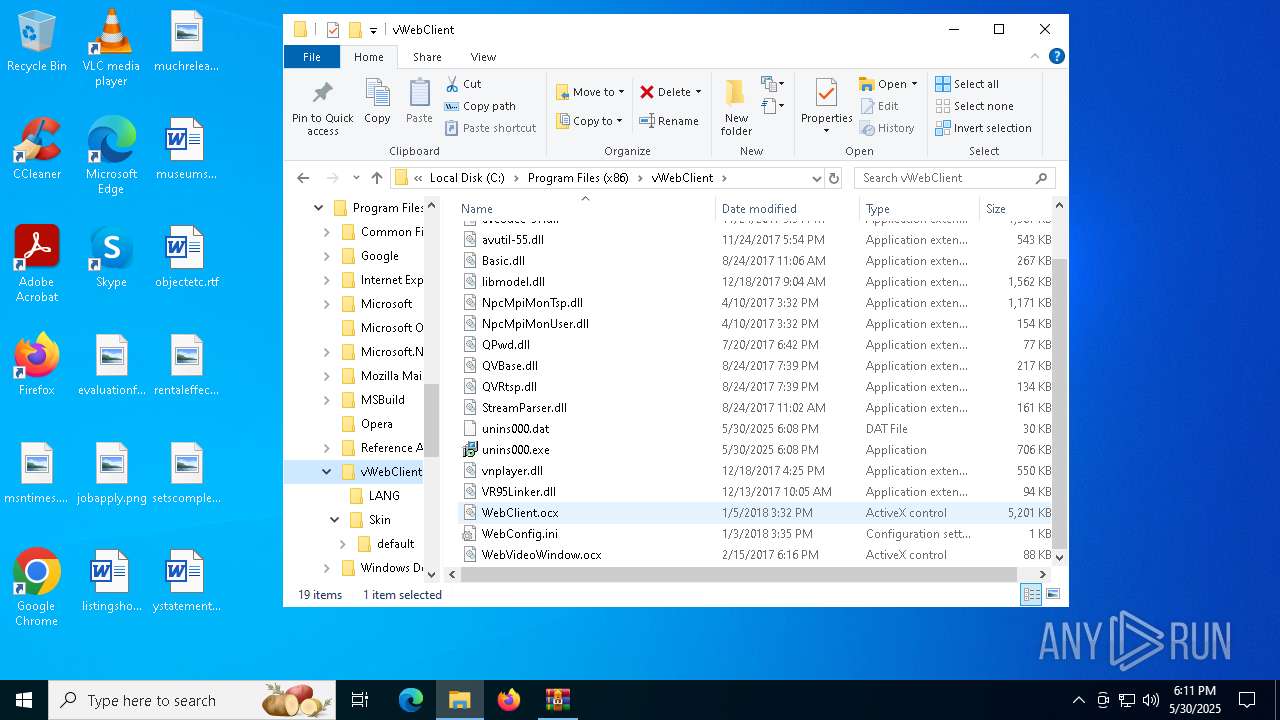
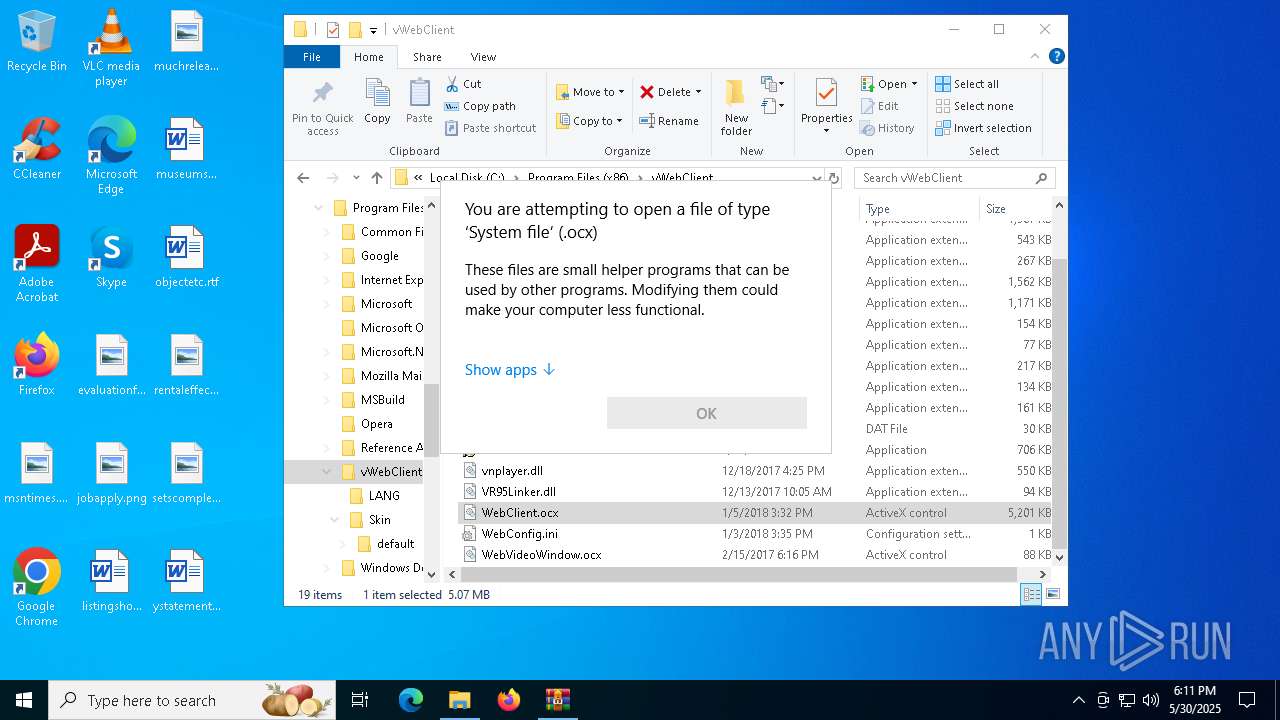
| 2136 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\vWebClient\WebClient.ocx" | C:\Windows\SysWOW64\regsvr32.exe | — | vWebClient.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\vWebClient\WebVideoWindow.ocx" | C:\Windows\SysWOW64\regsvr32.exe | — | vWebClient.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3156 | "C:\WINDOWS\system32\taskmgr.exe" /0 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3868 | "C:\WINDOWS\system32\taskmgr.exe" /0 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4696 | "C:\Program Files (x86)\vWebClient\unins000.exe" | C:\Program Files (x86)\vWebClient\unins000.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.52.0.0 Modules
| |||||||||||||||
| 4728 | "C:\Users\admin\Downloads\vWebClient.exe" /SPAWNWND=$203CA /NOTIFYWND=$403A0 | C:\Users\admin\Downloads\vWebClient.exe | vWebClient.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: vWebClient Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 5176 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files (x86)\vWebClient\unins000.exe" /FIRSTPHASEWND=$50256 /INITPROCWND=$6025A | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.52.0.0 Modules
| |||||||||||||||
| 6044 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\vWebClient.exe.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6808 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6892 | "C:\Program Files (x86)\vWebClient\unins000.exe" /INITPROCWND=$6025A | C:\Program Files (x86)\vWebClient\unins000.exe | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
6 127
Read events
6 055
Write events
46
Delete events
26
Modification events
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\vWebClient.exe.7z | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
44
Suspicious files
70
Text files
487
Unknown types
0
Dropped files
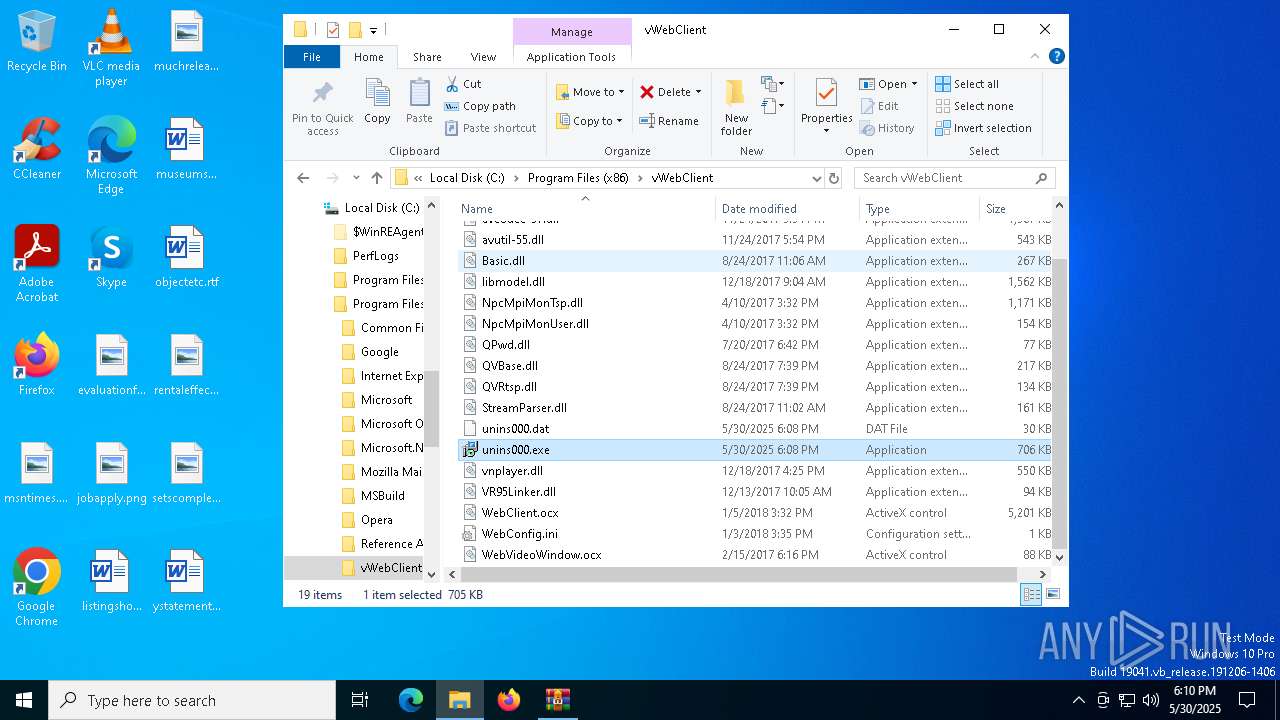
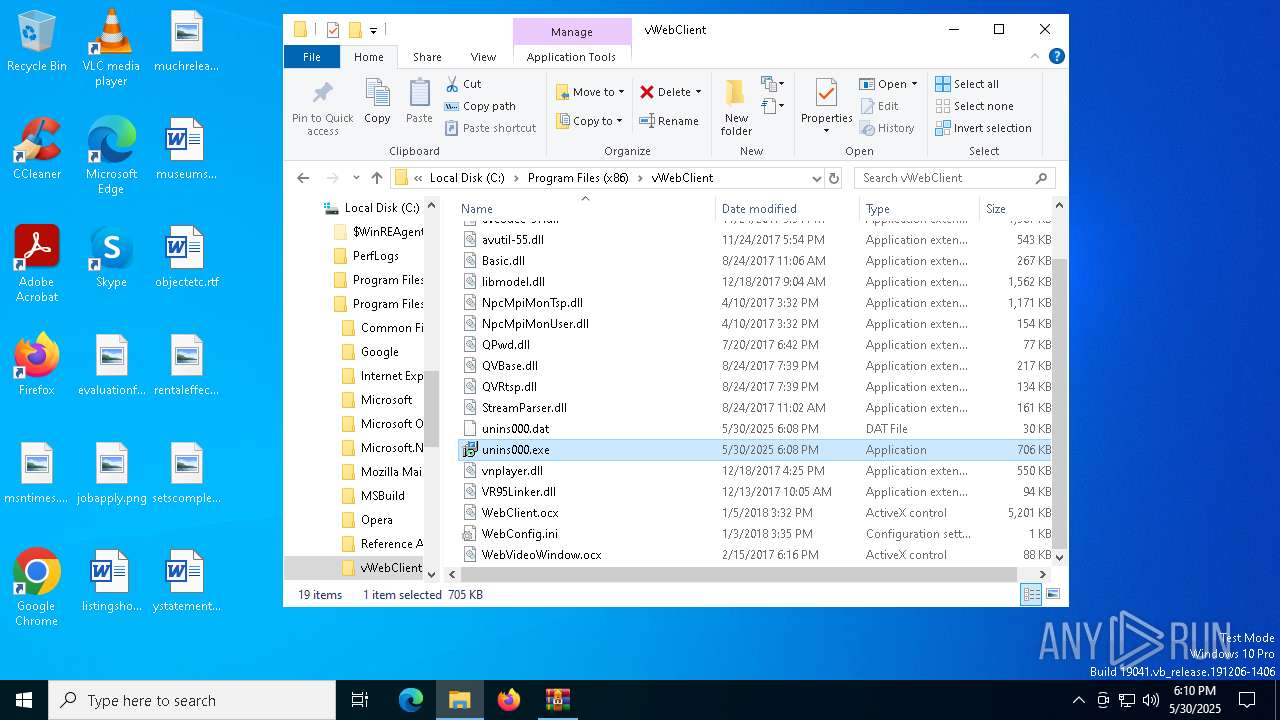
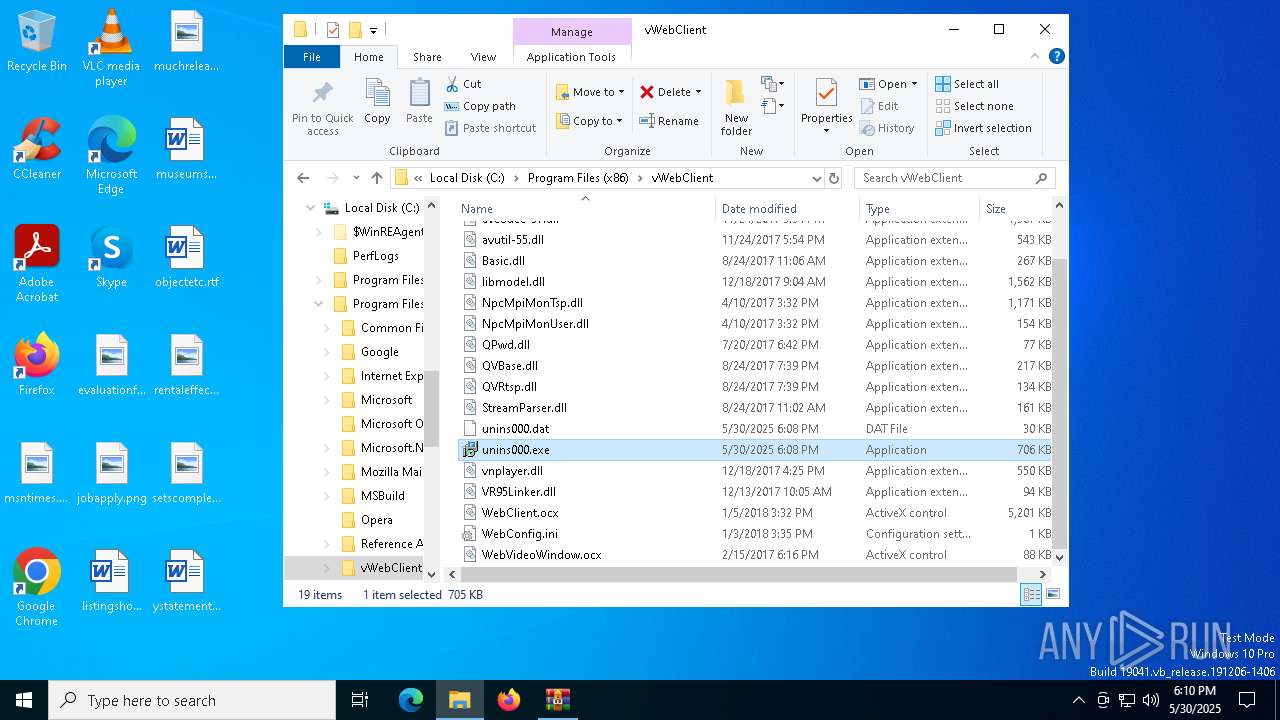
PID | Process | Filename | Type | |
|---|---|---|---|---|
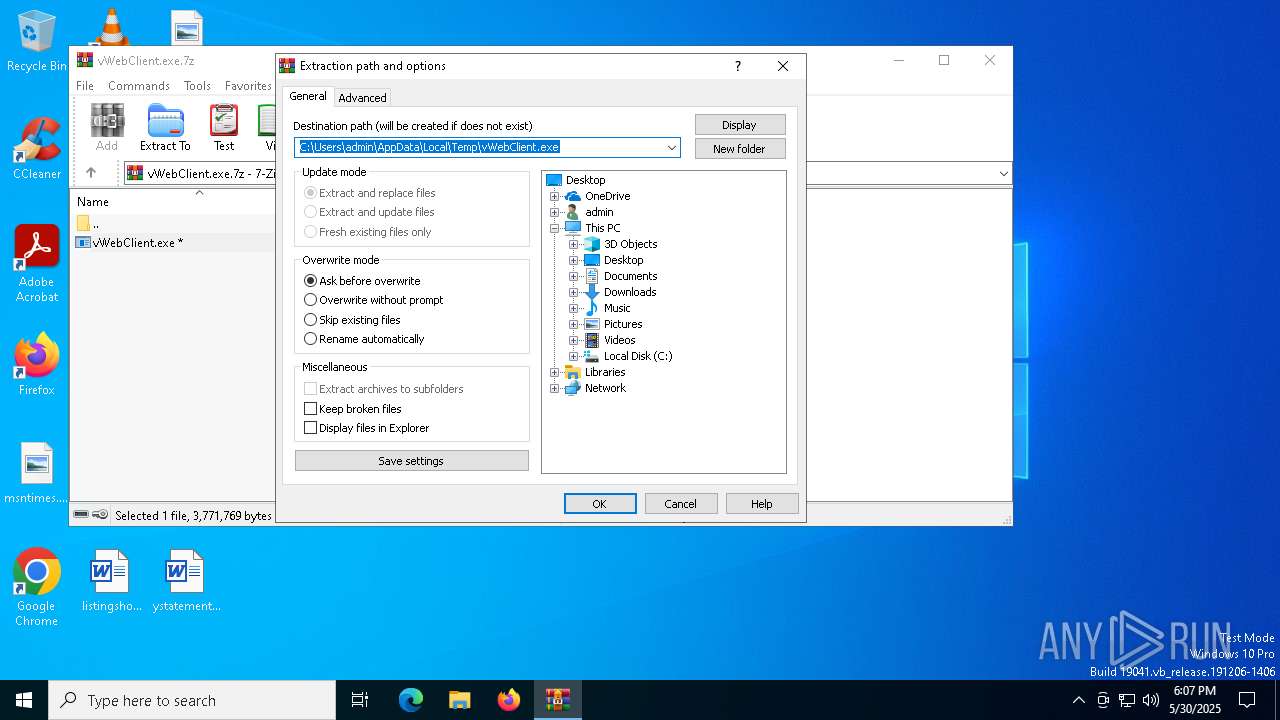
| 4728 | vWebClient.exe | C:\Users\admin\AppData\Local\Temp\is-RNLSI.tmp\vWebClient.tmp | executable | |
MD5:FFCF263A020AA7794015AF0EDEE5DF0B | SHA256:1D07CFB7104B85FC0DFFD761F6848AD176117E146BBB4079FE993EFA06B94C64 | |||
| 7752 | vWebClient.tmp | C:\Users\admin\AppData\Local\Temp\is-A6A86.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
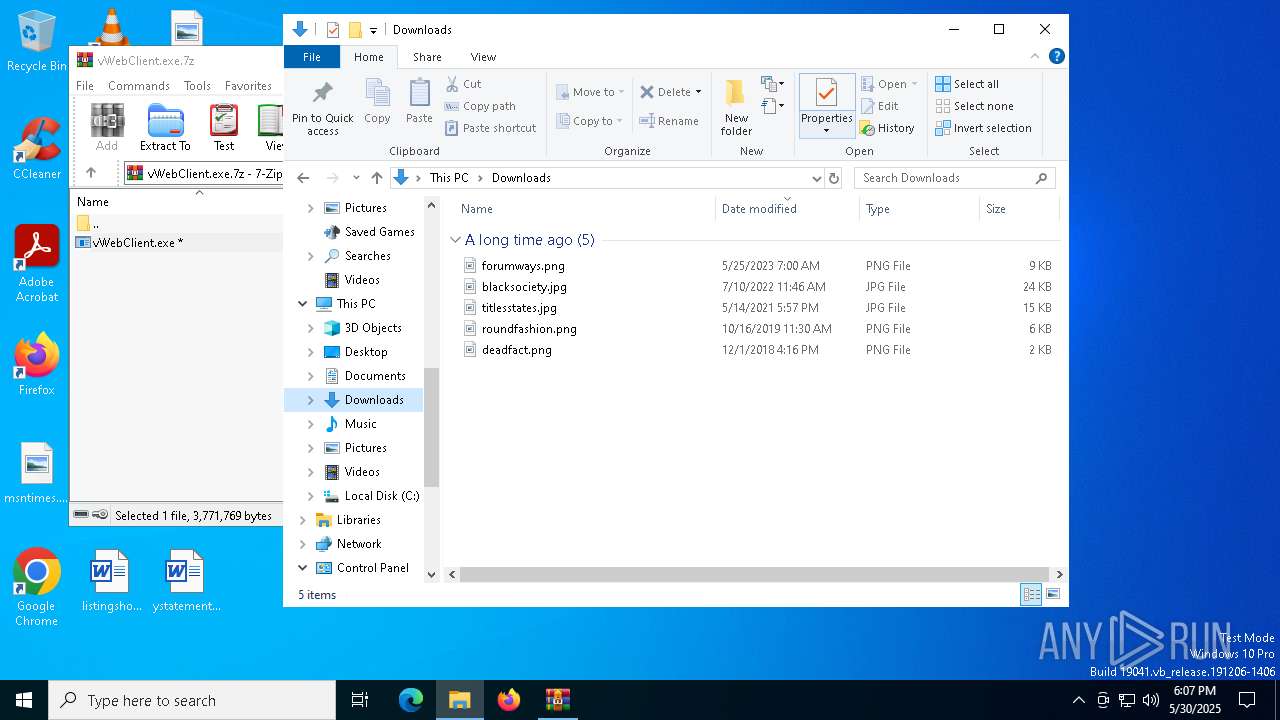
| 6044 | WinRAR.exe | C:\Users\admin\Downloads\vWebClient.exe | executable | |
MD5:BBD4DC59A3D969C96AD97BCD7DBF9A0E | SHA256:BE5EBE39FAF4067AAE49255C232C376B63960EFF9DB398508727B50213C12D26 | |||
| 7856 | vWebClient.exe | C:\Users\admin\AppData\Local\Temp\is-88OVJ.tmp\vWebClient.tmp | executable | |
MD5:FFCF263A020AA7794015AF0EDEE5DF0B | SHA256:1D07CFB7104B85FC0DFFD761F6848AD176117E146BBB4079FE993EFA06B94C64 | |||
| 7752 | vWebClient.tmp | C:\Users\admin\AppData\Local\Temp\is-A6A86.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
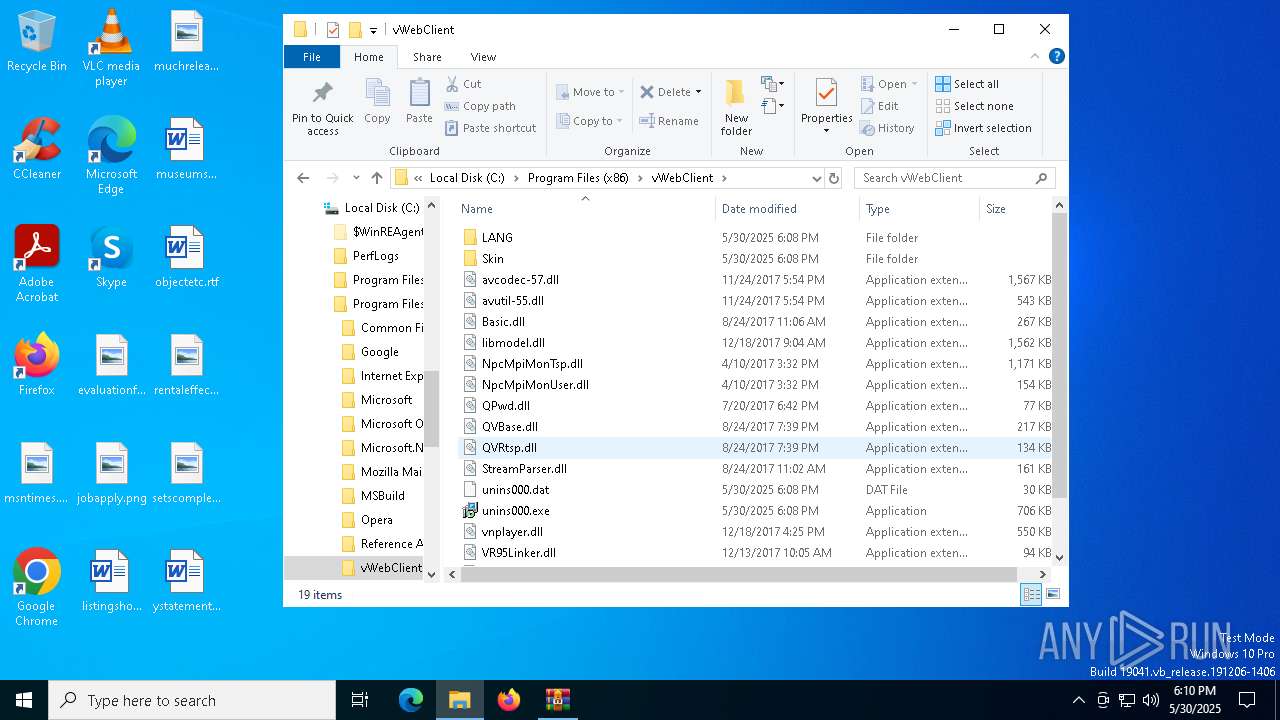
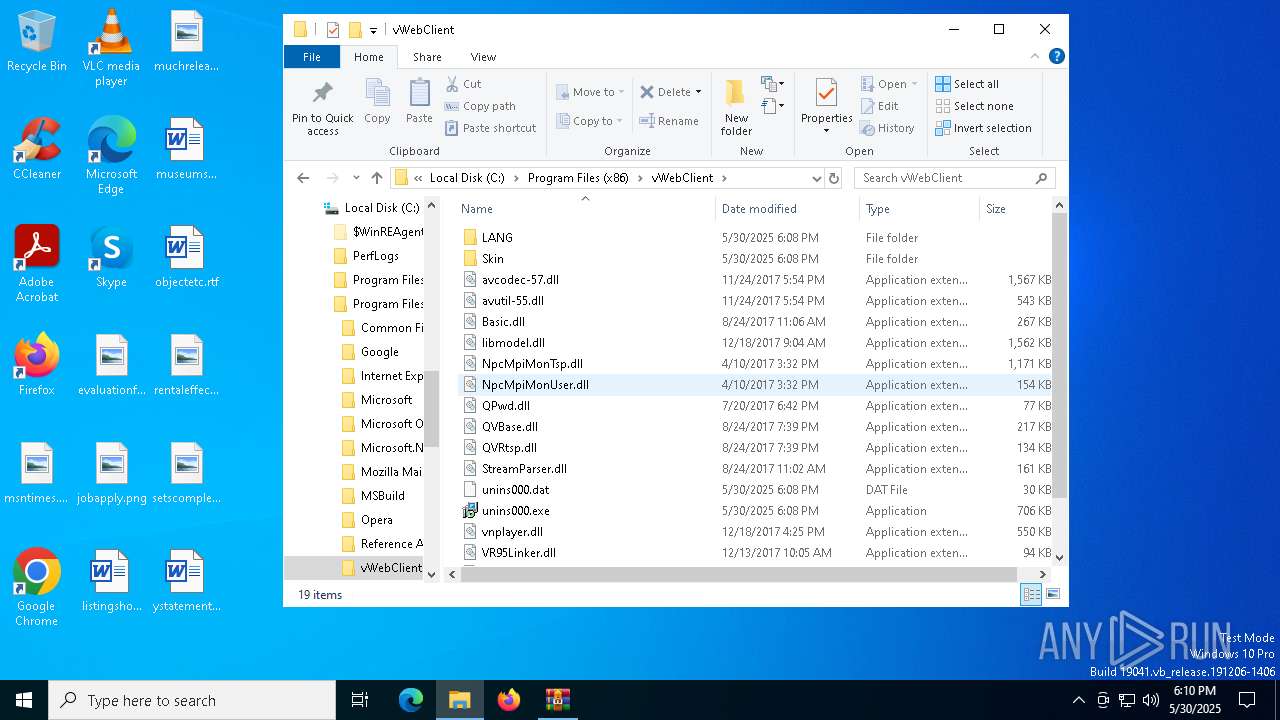
| 7752 | vWebClient.tmp | C:\Program Files (x86)\vWebClient\is-NK80I.tmp | executable | |
MD5:C9C209ACB1762938E225FCD735FFEDEB | SHA256:DB17EC03FEC5226FD09679A8E2015D415D49AB0DE54572ACB621494DA90485D8 | |||
| 7752 | vWebClient.tmp | C:\Program Files (x86)\vWebClient\is-NJNVS.tmp | executable | |
MD5:9D5005E8BAE1D452C8D61B635283524A | SHA256:22FBC5E272574A500D71BB2EDD85E2A74DDFA9B0CB89F344FB6FD80045F8203F | |||
| 7752 | vWebClient.tmp | C:\Program Files (x86)\vWebClient\Basic.dll | executable | |
MD5:545EC6A81207F4A5308E8844F0D7773C | SHA256:F405A3D879C281A74C1F1B84265499869C9DA7FED58042619E71C1F29FD5B0BF | |||
| 7752 | vWebClient.tmp | C:\Program Files (x86)\vWebClient\NpcMpiMonUser.dll | executable | |
MD5:C9C209ACB1762938E225FCD735FFEDEB | SHA256:DB17EC03FEC5226FD09679A8E2015D415D49AB0DE54572ACB621494DA90485D8 | |||
| 7752 | vWebClient.tmp | C:\Program Files (x86)\vWebClient\unins000.exe | executable | |
MD5:F874DAAA103E68FD9AF46DC71614658E | SHA256:E387393D94D6E302491EA0B5A225A2762126DF6635683C04FB9984B8C1D65EC4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
45
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8104 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5608 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1328 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.122:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5608 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |