| File name: | Procmon.exe |
| Full analysis: | https://app.any.run/tasks/991f594a-82f2-4c9d-a46c-26b6530c1017 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 16:13:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 652F80CE1A330C44F2852F9C1A640649 |
| SHA1: | C96E0153F75823FFDEF961A0BBDFCE923F70F48E |
| SHA256: | D0FA2CFF4E2862F982671CDD1A2967E159BF6ECC4644A3C259AC48EC29496670 |
| SSDEEP: | 12288:sIOAbhkGOMvb2Owb6GPgOlUtpaIRGcE9fURBbeKWKKNFNutSa+WW635Qu94FkNM7:s3yPvCOwGGgOlktROlURBblWKKn8Dugk |
MALICIOUS
Drops executable file immediately after starts
- Procmon.exe (PID: 2484)
Loads the Task Scheduler COM API
- Procmon.exe (PID: 2484)
SUSPICIOUS
Reads the computer name
- Procmon.exe (PID: 2840)
- Procmon.exe (PID: 2484)
Checks supported languages
- Procmon.exe (PID: 2840)
- Procmon.exe (PID: 2484)
Application launched itself
- Procmon.exe (PID: 2840)
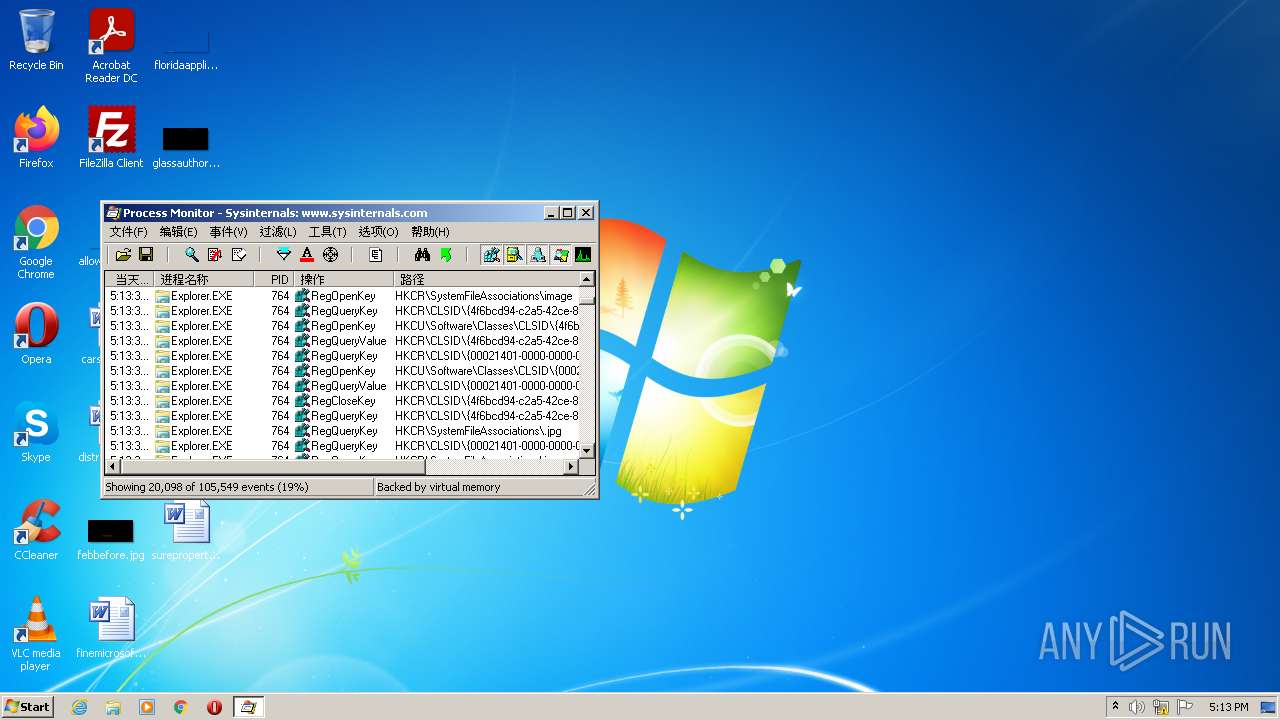
Changes default file association
- Procmon.exe (PID: 2484)
Creates files in the driver directory
- Procmon.exe (PID: 2484)
Creates files in the Windows directory
- Procmon.exe (PID: 2484)
Creates or modifies windows services
- Procmon.exe (PID: 2484)
Executable content was dropped or overwritten
- Procmon.exe (PID: 2484)
Drops a file with a compile date too recent
- Procmon.exe (PID: 2484)
Removes files from Windows directory
- Procmon.exe (PID: 2484)
Reads CPU info
- Procmon.exe (PID: 2484)
Reads the time zone
- Procmon.exe (PID: 2484)
Loads DLL from Mozilla Firefox
- Procmon.exe (PID: 2484)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| ProductVersion: | 3.1 |
|---|---|
| ProductName: | Sysinternals Procmon |
| OriginalFileName: | Procmon.exe |
| LegalCopyright: | Copyright © 1996-2014 Mark Russinovich |
| InternalName: | Procmon |
| FileVersion: | 3.1 |
| FileDescription: | Process Monitor |
| CompanyName: | Sysinternals - www.sysinternals.com |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.10.0.0 |
| FileVersionNumber: | 3.10.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x26d190 |
| UninitializedDataSize: | 1859584 |
| InitializedDataSize: | 40960 |
| CodeSize: | 684032 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2014:02:21 19:53:31+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2014 18:53:31 |
| Detected languages: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Process Monitor |
| FileVersion: | 3.10 |
| InternalName: | Procmon |
| LegalCopyright: | Copyright © 1996-2014 Mark Russinovich |
| OriginalFilename: | Procmon.exe |
| ProductName: | Sysinternals Procmon |
| ProductVersion: | 3.10 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 21-Feb-2014 18:53:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x001C6000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x001C7000 | 0x000A7000 | 0x000A6E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99958 |
.rsrc | 0x0026E000 | 0x0000A000 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98742 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08051 | 1543 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 4.26098 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.09301 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.41795 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.17862 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 4.26977 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 1.57156 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
8 | 1.61781 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 1.77545 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
10 | 1.88589 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
FLTLIB.DLL |
GDI32.dll |
KERNEL32.DLL |
NETAPI32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
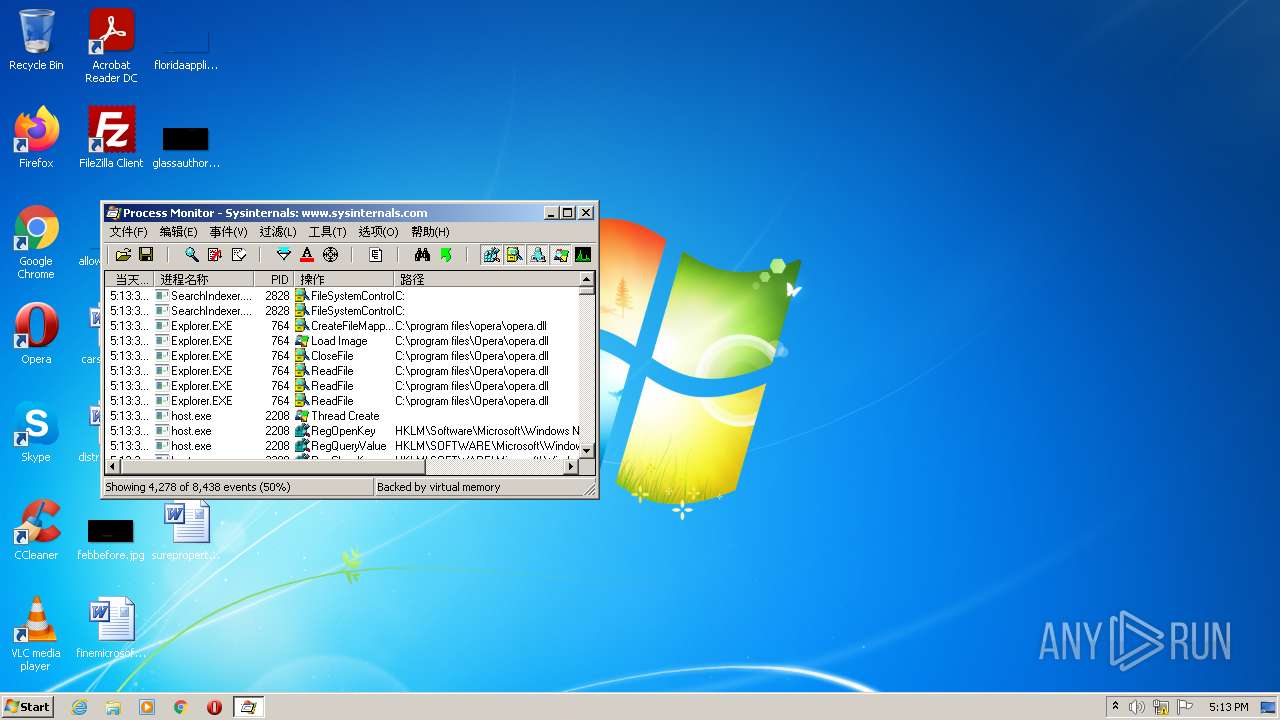
Total processes
39
Monitored processes
2
Malicious processes
2
Suspicious processes
0
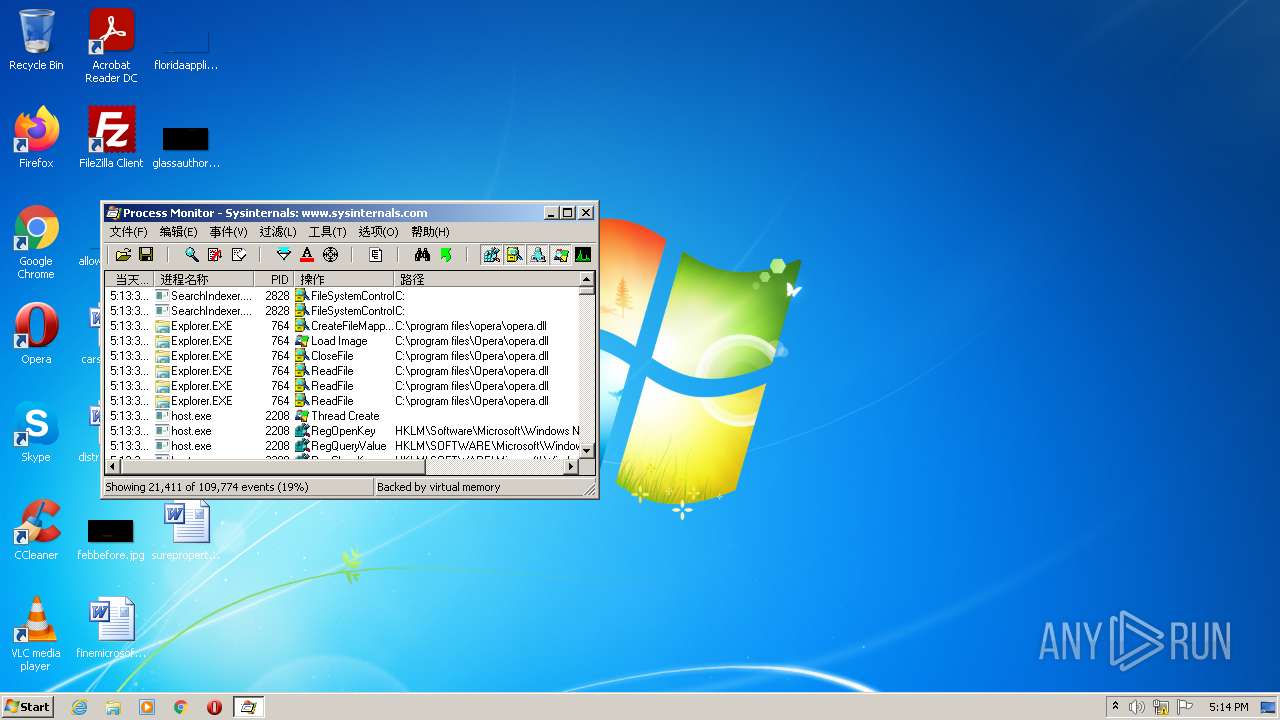
Behavior graph
Click at the process to see the details
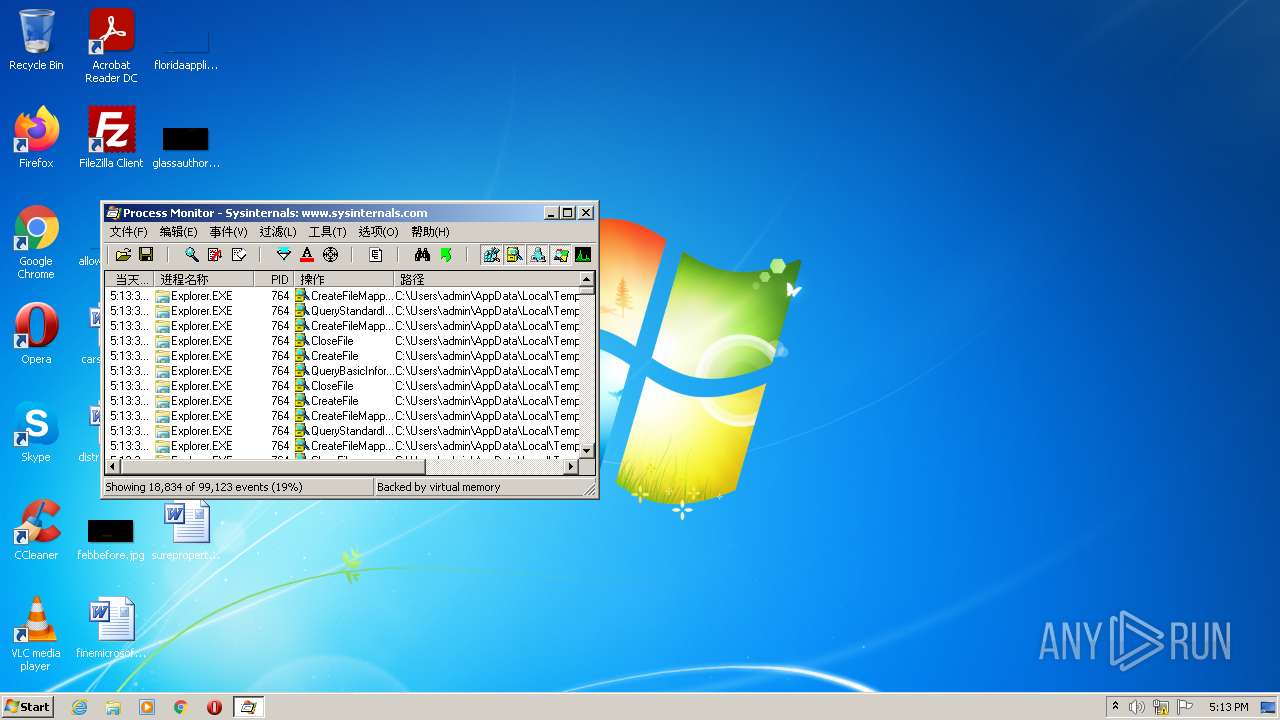
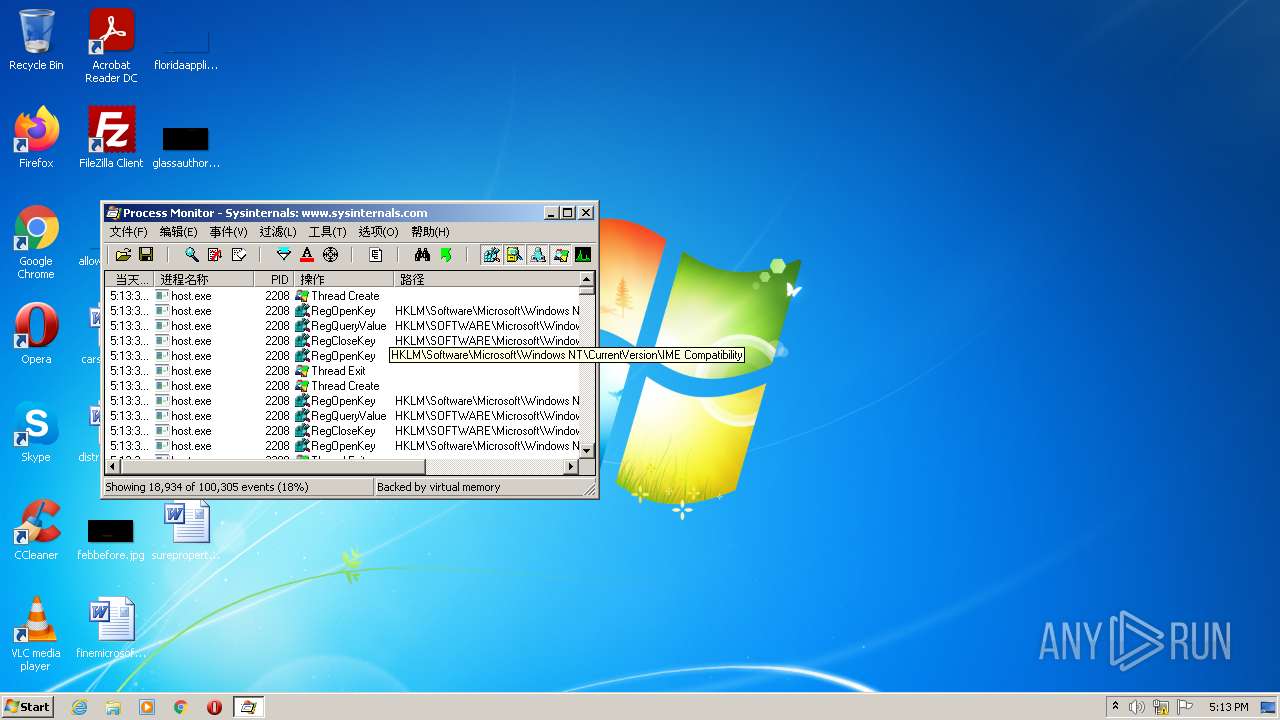
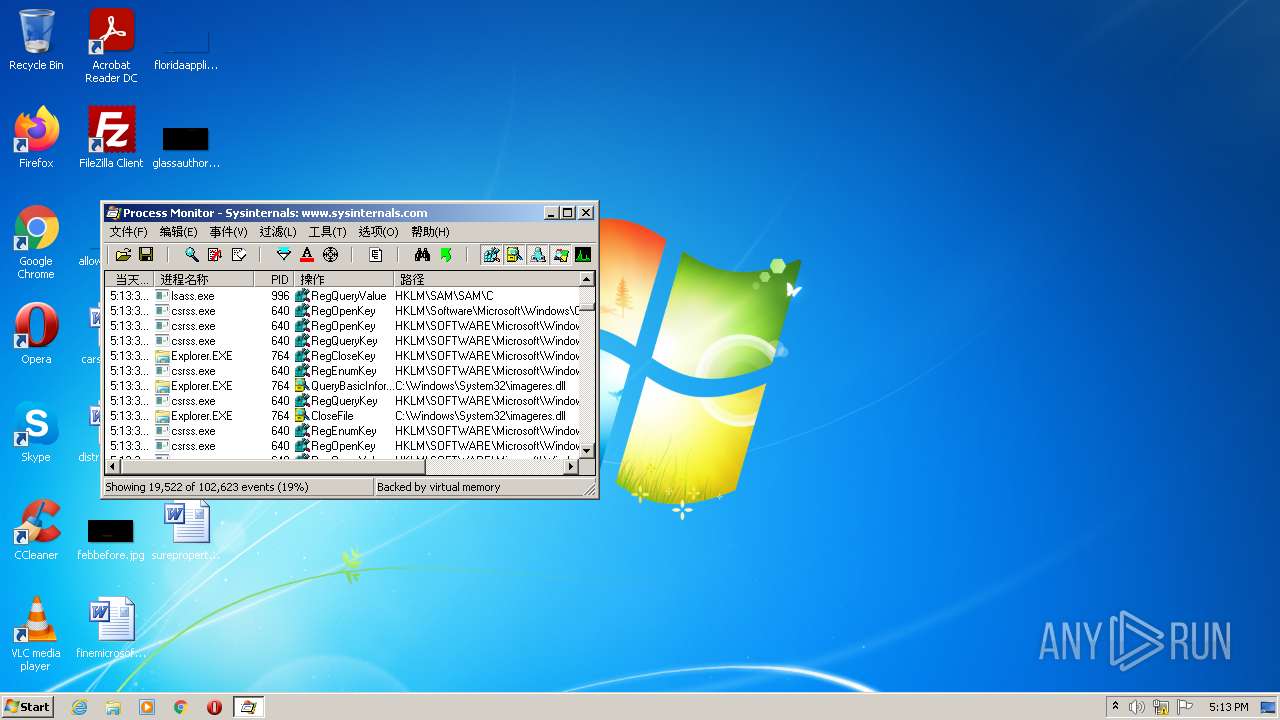
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2484 | "C:\Users\admin\AppData\Local\Temp\Procmon.exe" | C:\Users\admin\AppData\Local\Temp\Procmon.exe | Procmon.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Process Monitor Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 2840 | "C:\Users\admin\AppData\Local\Temp\Procmon.exe" | C:\Users\admin\AppData\Local\Temp\Procmon.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Process Monitor Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
Total events
1 863
Read events
1 835
Write events
23
Delete events
5
Modification events
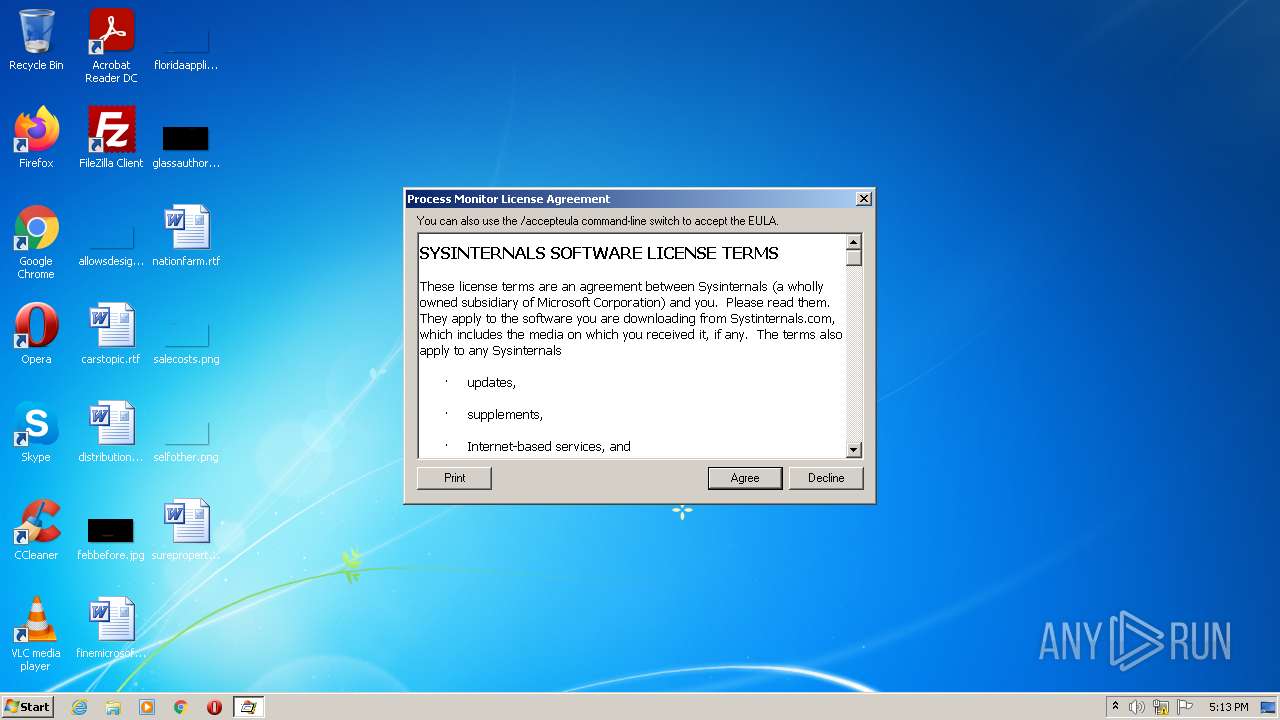
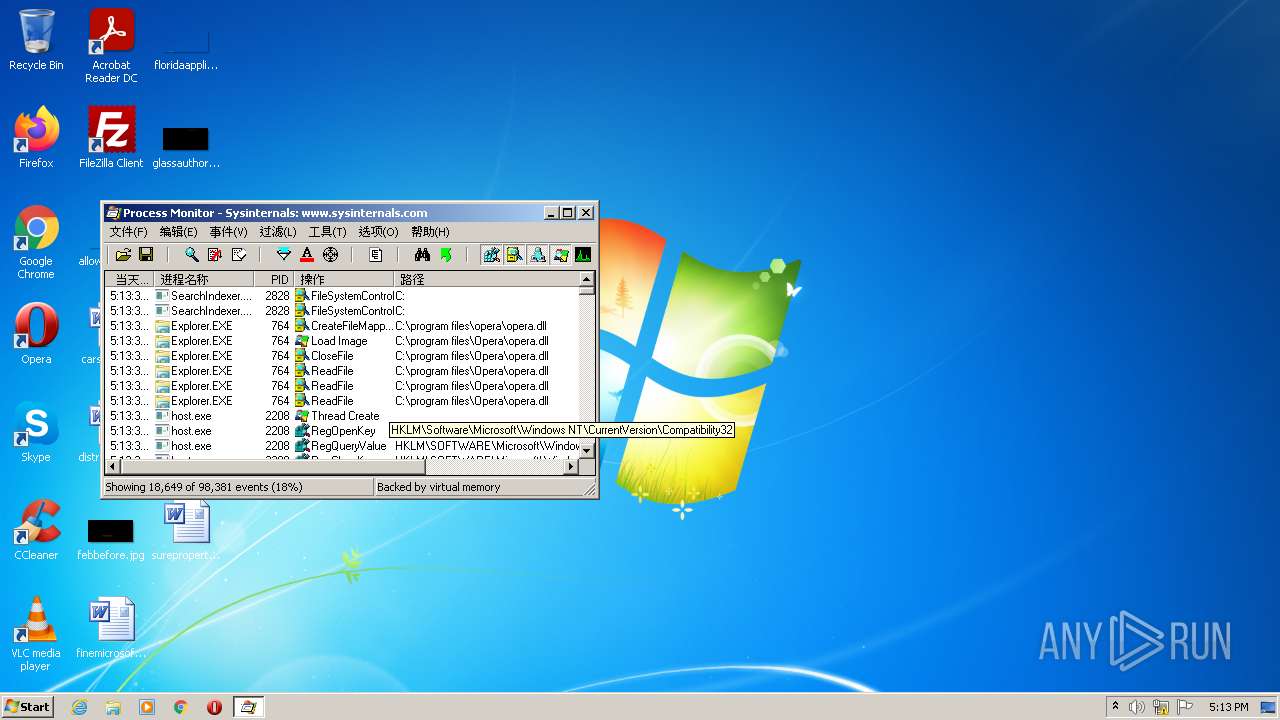
| (PID) Process: | (2840) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Process Monitor |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (2840) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2840) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2840) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2840) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2484) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Process Monitor |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (2484) Procmon.exe | Key: | HKEY_CLASSES_ROOT\.PML |
| Operation: | write | Name: | (default) |
Value: ProcMon.Logfile.1 | |||
| (PID) Process: | (2484) Procmon.exe | Key: | HKEY_CLASSES_ROOT\ProcMon.Logfile.1 |
| Operation: | write | Name: | (default) |
Value: ProcMon Log File | |||
| (PID) Process: | (2484) Procmon.exe | Key: | HKEY_CLASSES_ROOT\ProcMon.Logfile.1\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\AppData\Local\Temp\Procmon.exe" /OpenLog "%1" | |||
| (PID) Process: | (2484) Procmon.exe | Key: | HKEY_CLASSES_ROOT\ProcMon.Logfile.1\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\AppData\Local\Temp\Procmon.exe",0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | Procmon.exe | C:\Windows\system32\Drivers\PROCMON23.SYS | executable | |
MD5:D503B4F5ED38E688AFD5C1DBFEE530C8 | SHA256:718FFAC584A5E30AD7350BB35E6492F80045DE14123DC820B71EBC7298513FA6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
255.100.168.192.in-addr.arpa |
| unknown |
2.100.168.192.in-addr.arpa |
| whitelisted |
3.0.0.0.1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.2.0.f.f.ip6.arpa |
| unknown |
252.0.0.224.in-addr.arpa |
| unknown |
2.0.0.0.1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.2.0.f.f.ip6.arpa |
| unknown |