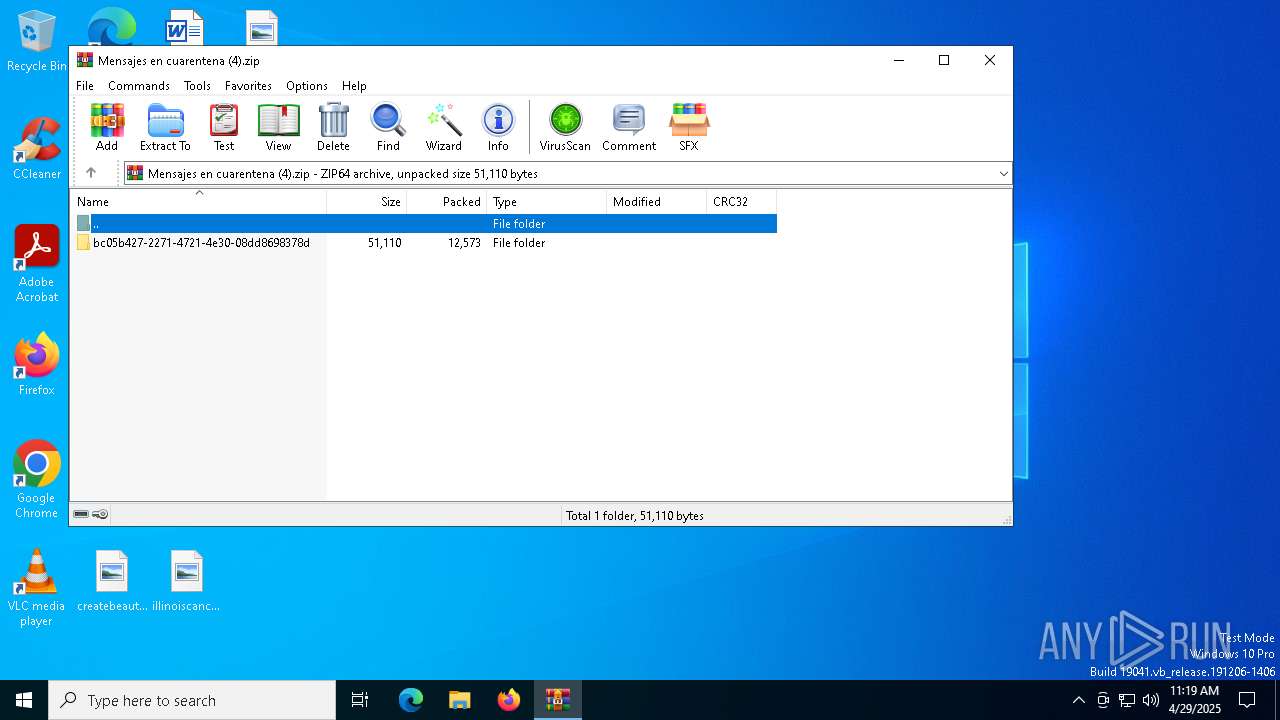
| File name: | Mensajes en cuarentena (4).zip |
| Full analysis: | https://app.any.run/tasks/ef37fcd7-3e8d-424d-a493-b259d71c1f76 |
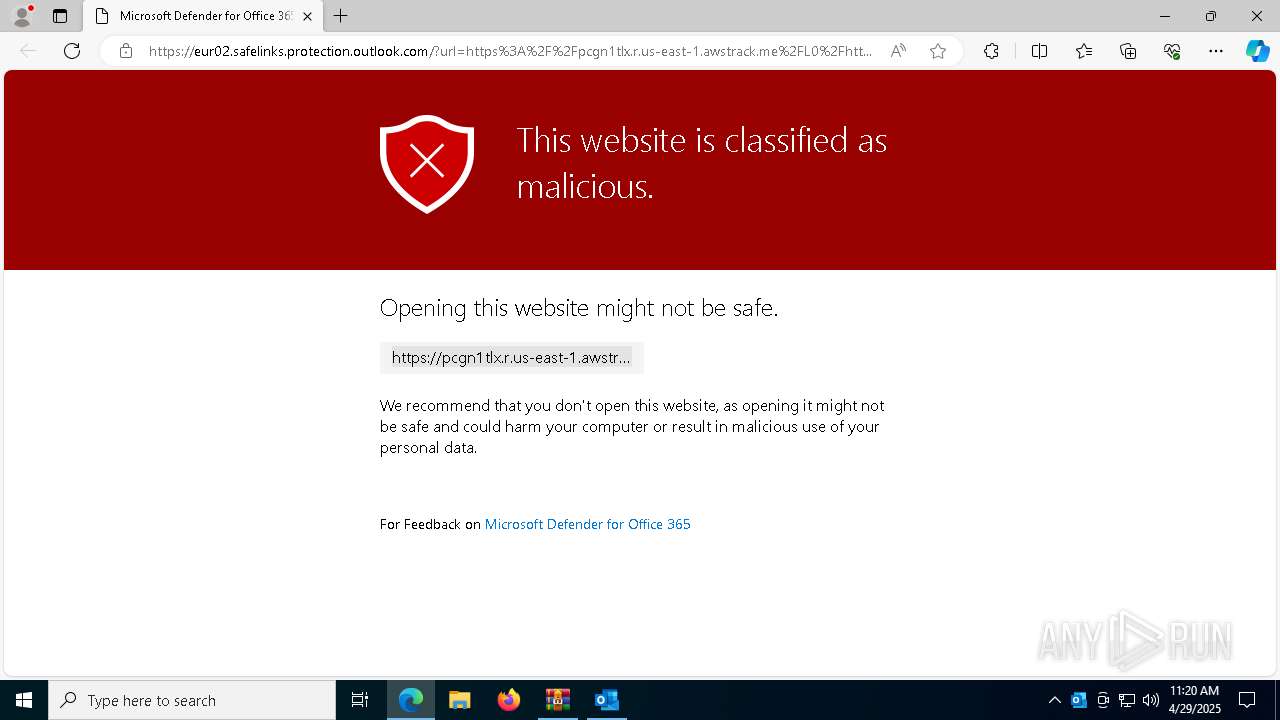
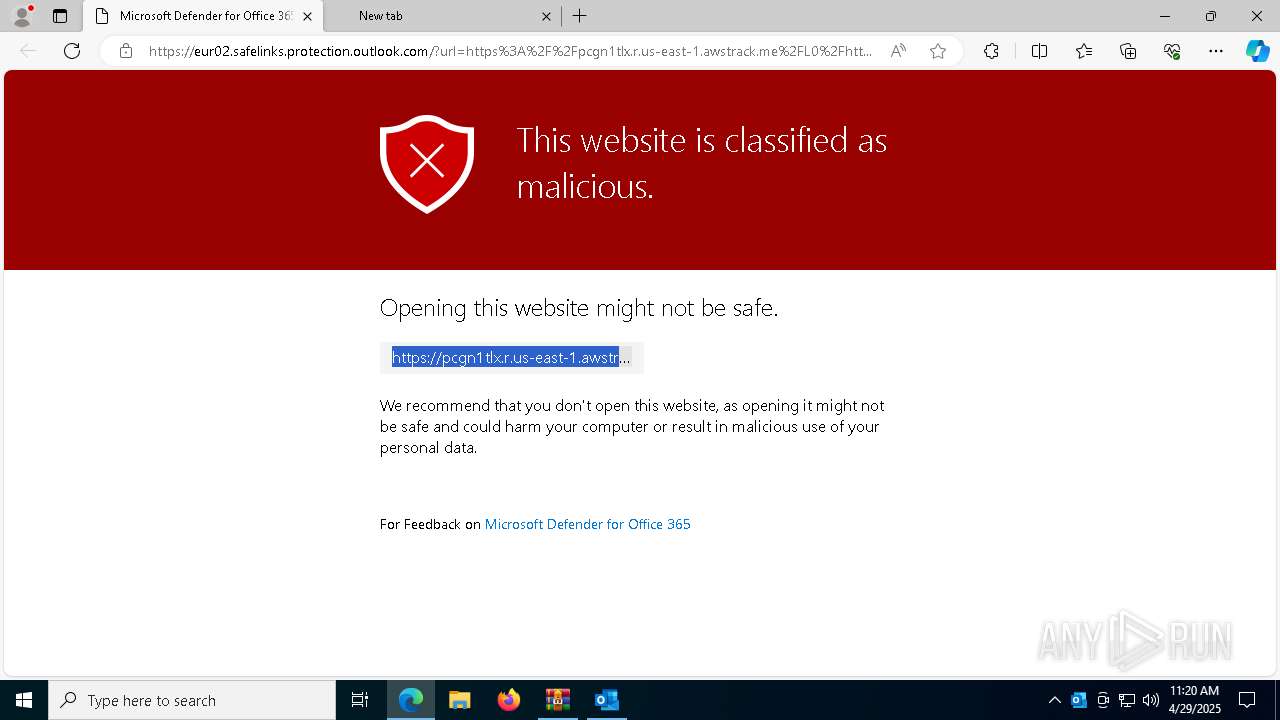
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 11:19:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 43CA008C3279A2C102E849F25F9D0ADE |
| SHA1: | 0323C959368FBC6566300F8BB1D87A70C01CB784 |
| SHA256: | D0DCA347F3BC5BA45309579B81E4CC0765249C1D47B44254A871DD4D64149508 |
| SSDEEP: | 384:esZcX7Ktuhmk8isrhbXi73wJYFKzCr2sa1j++YKMIy:esZcX7KKorhbXi7gKwybcjjxy |
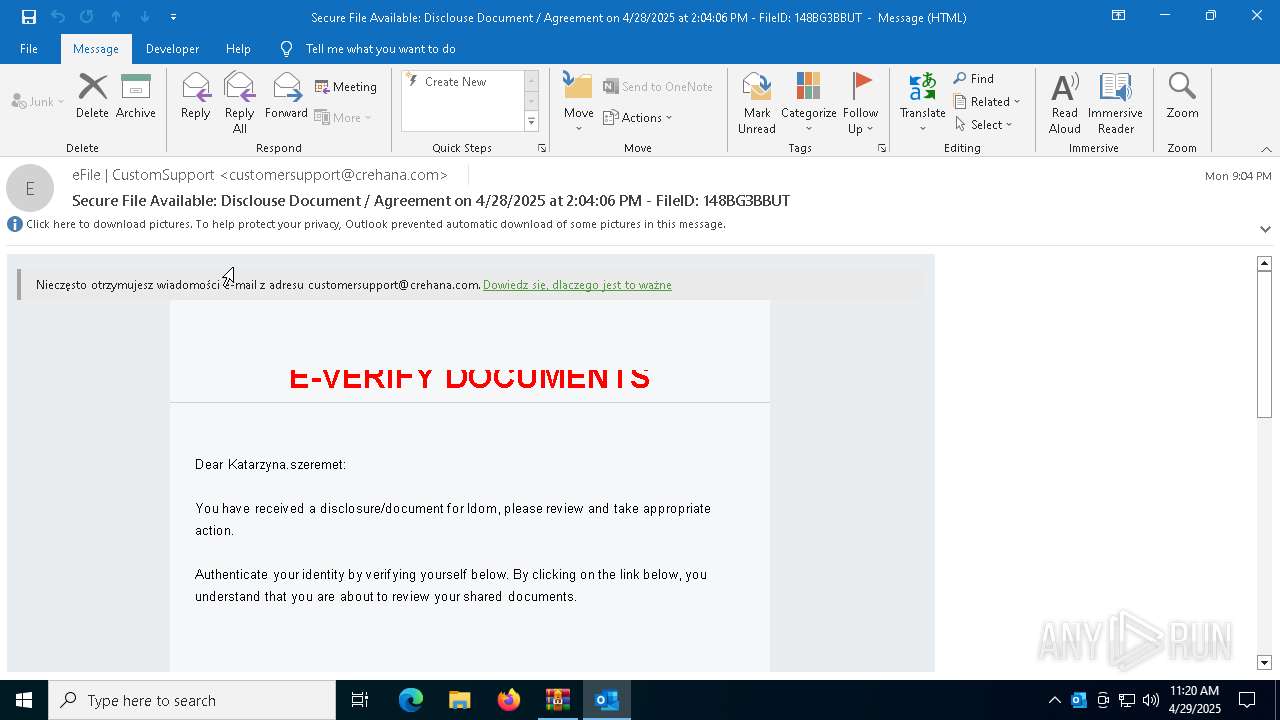
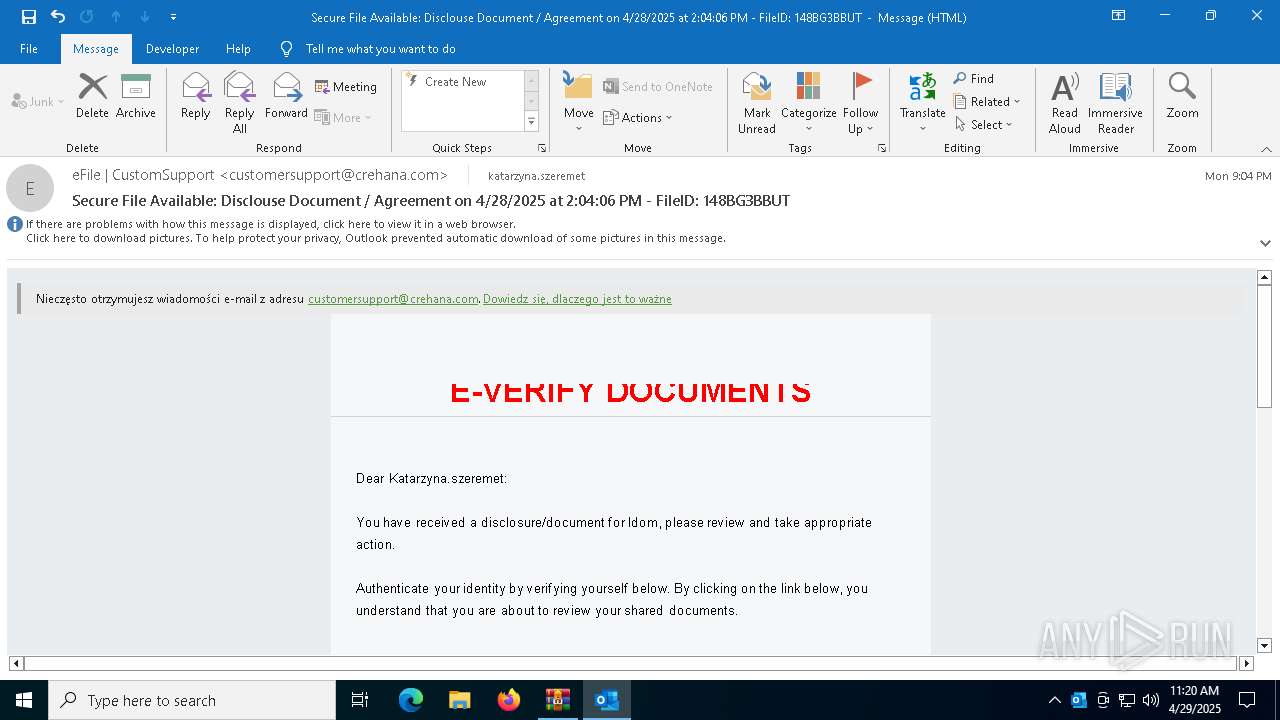
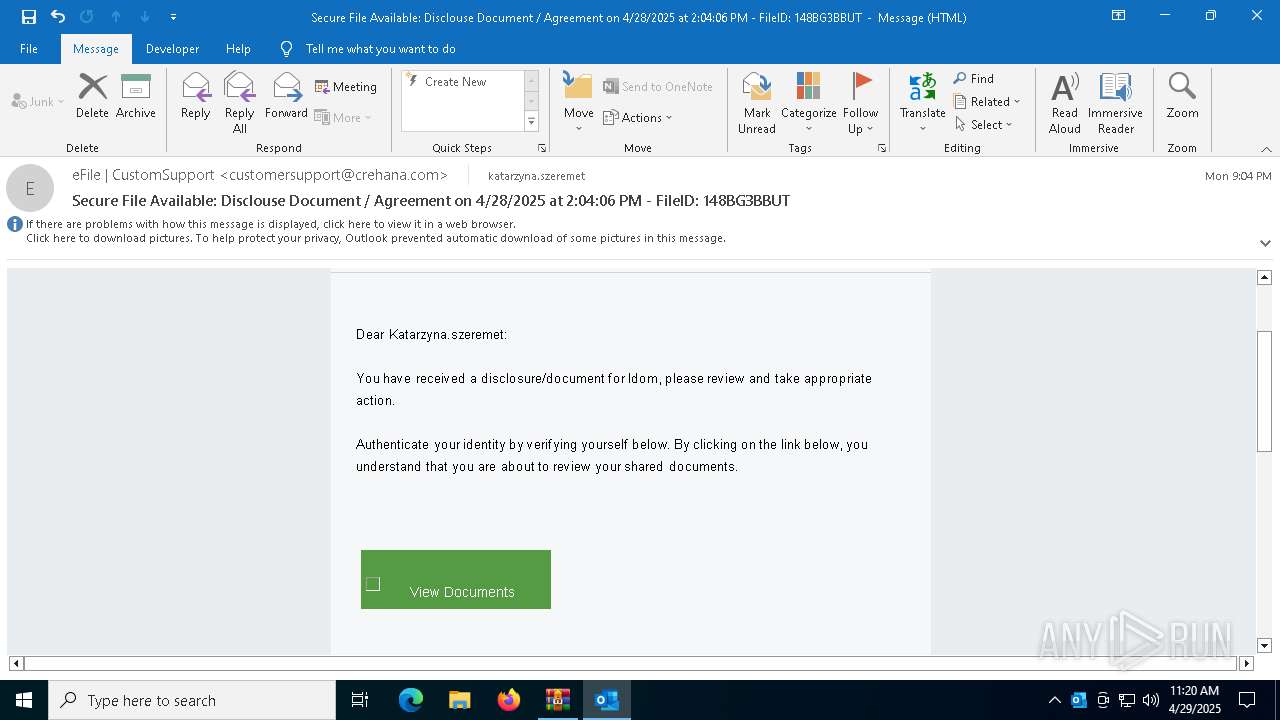
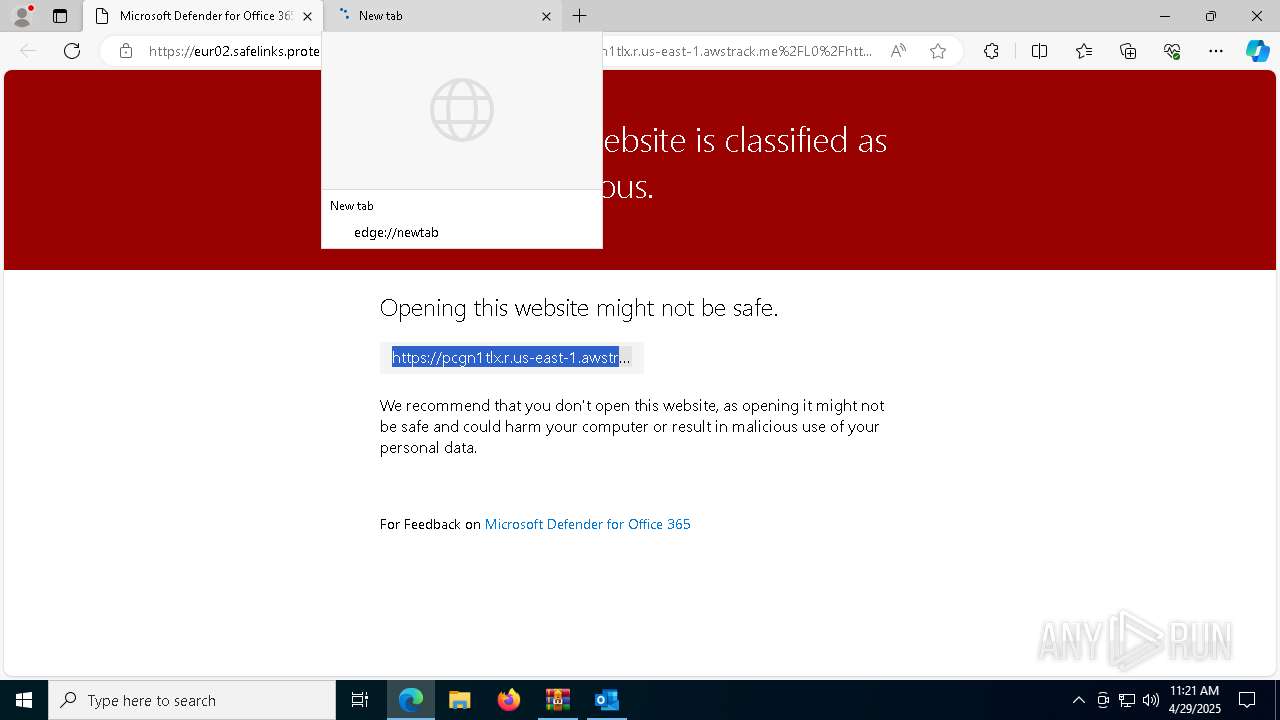
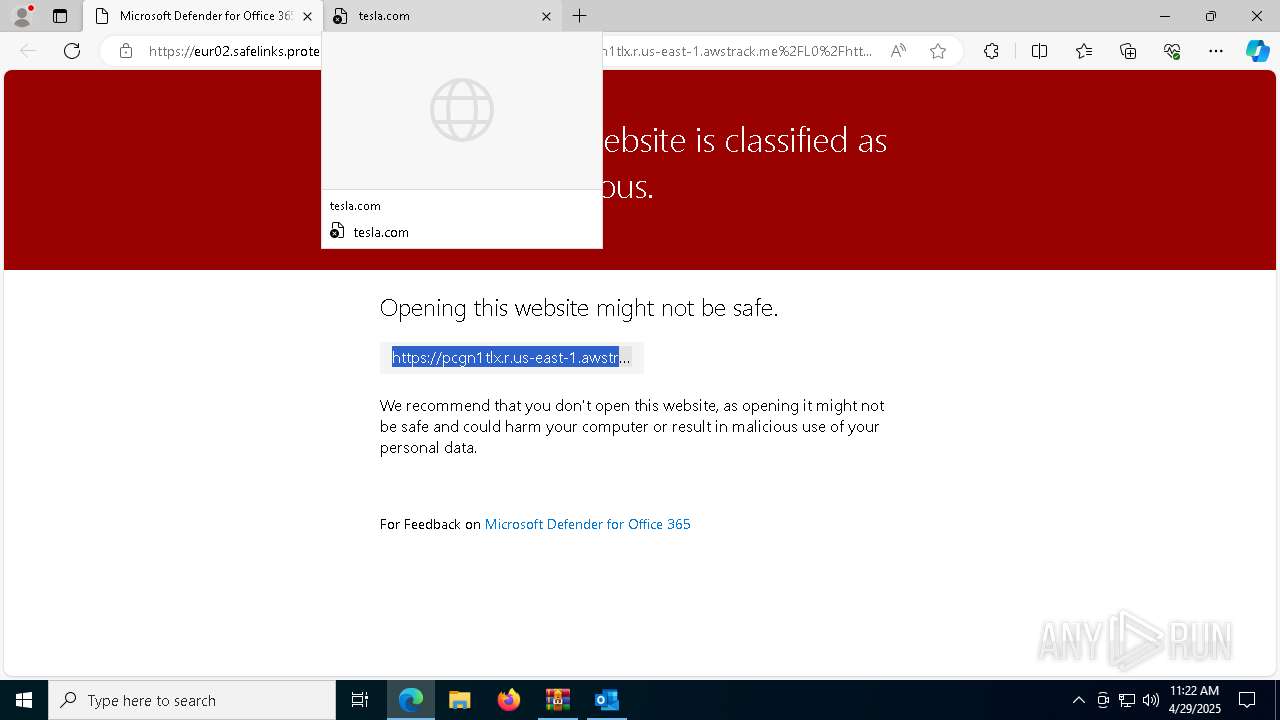
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6132)
SUSPICIOUS
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 7336)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7336)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7336)
Reads the computer name
- identity_helper.exe (PID: 1180)
Reads Environment values
- identity_helper.exe (PID: 1180)
Checks supported languages
- identity_helper.exe (PID: 1180)
Application launched itself
- msedge.exe (PID: 1324)
Reads the software policy settings
- slui.exe (PID: 7516)
- slui.exe (PID: 6644)
Checks proxy server information
- slui.exe (PID: 6644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:29 11:19:00 |
| ZipCRC: | 0xeed6f183 |
| ZipCompressedSize: | 4294967295 |
| ZipUncompressedSize: | 4294967295 |
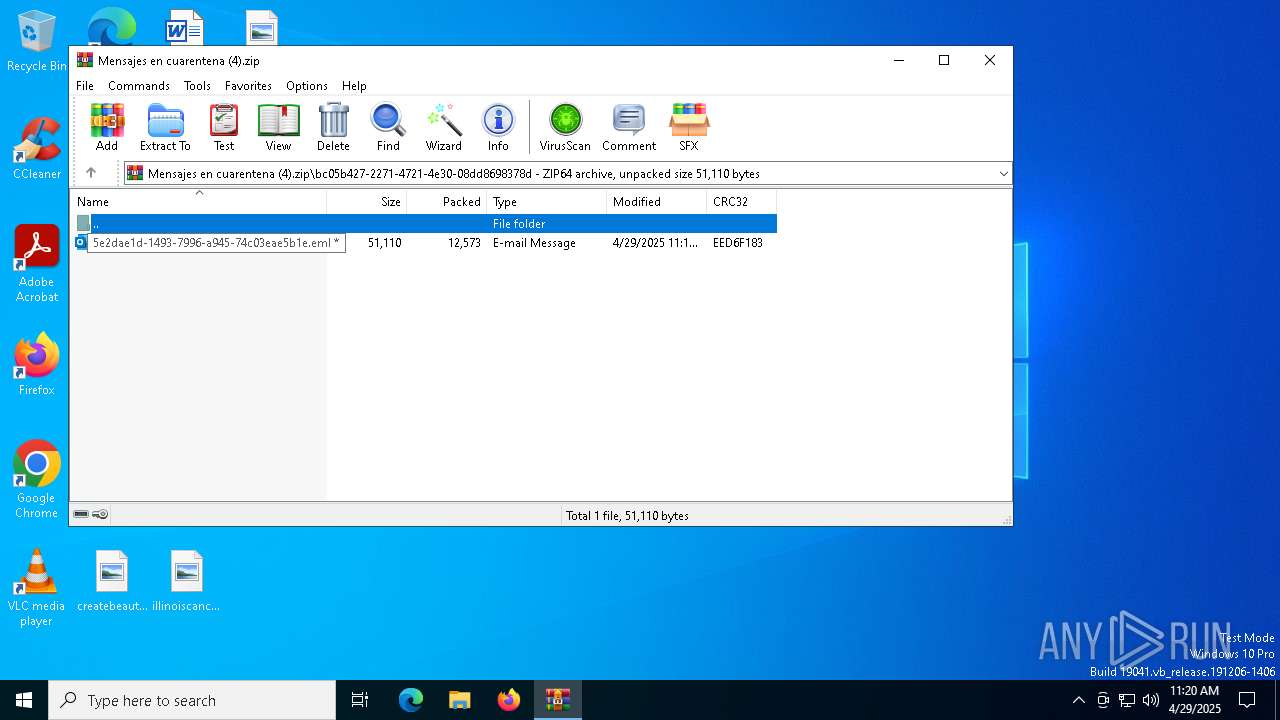
| ZipFileName: | bc05b427-2271-4721-4e30-08dd8698378d/5e2dae1d-1493-7996-a945-74c03eae5b1e.eml |
Total processes
197
Monitored processes
59
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6788 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6616 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7024 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5740 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4492 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4532 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
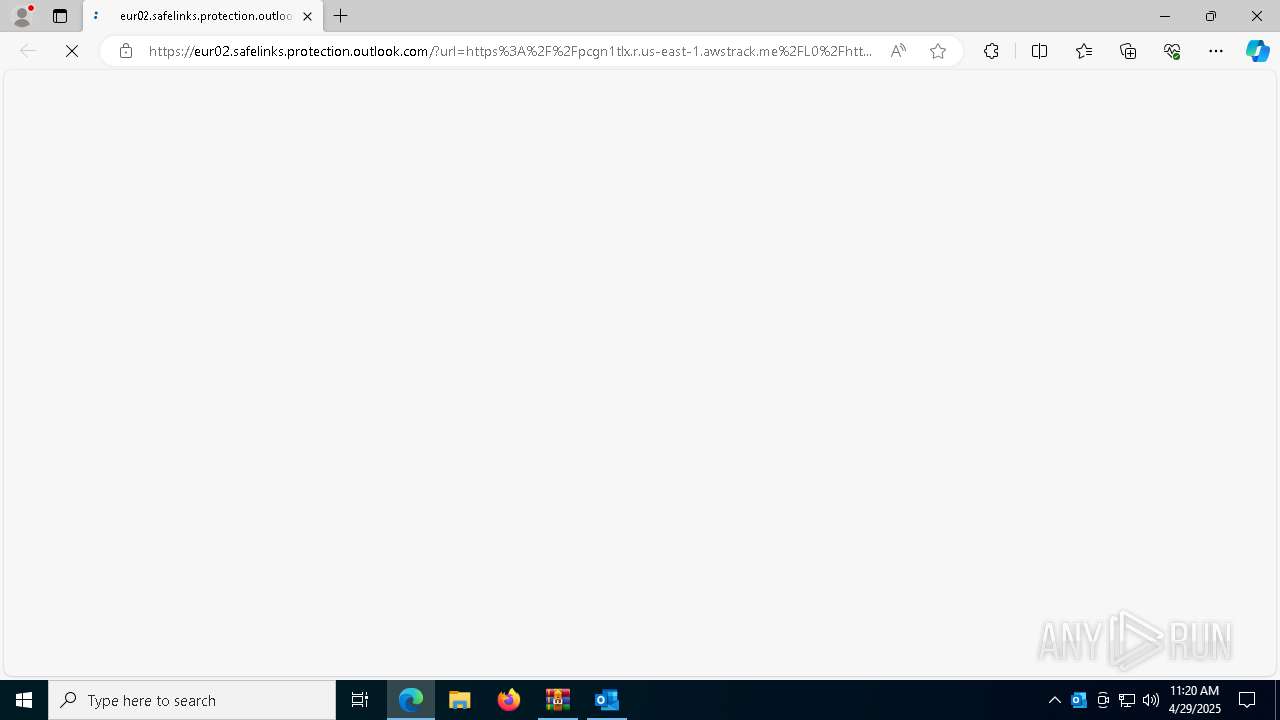
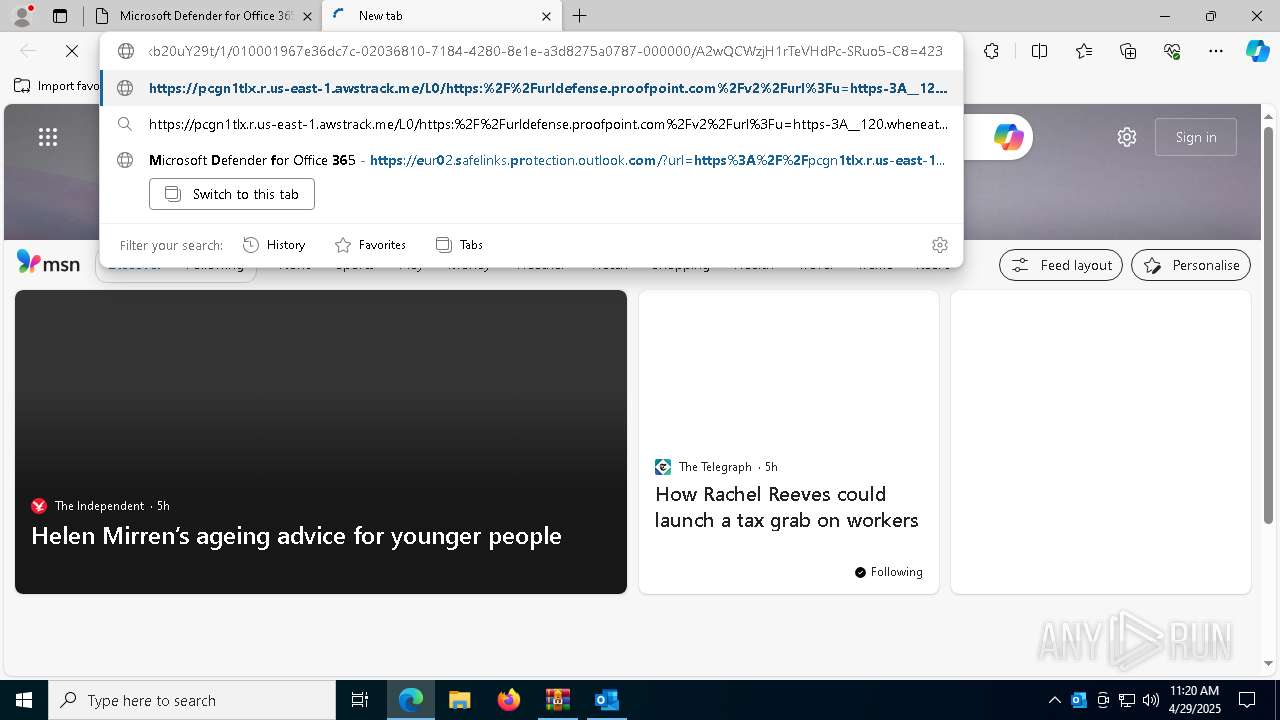
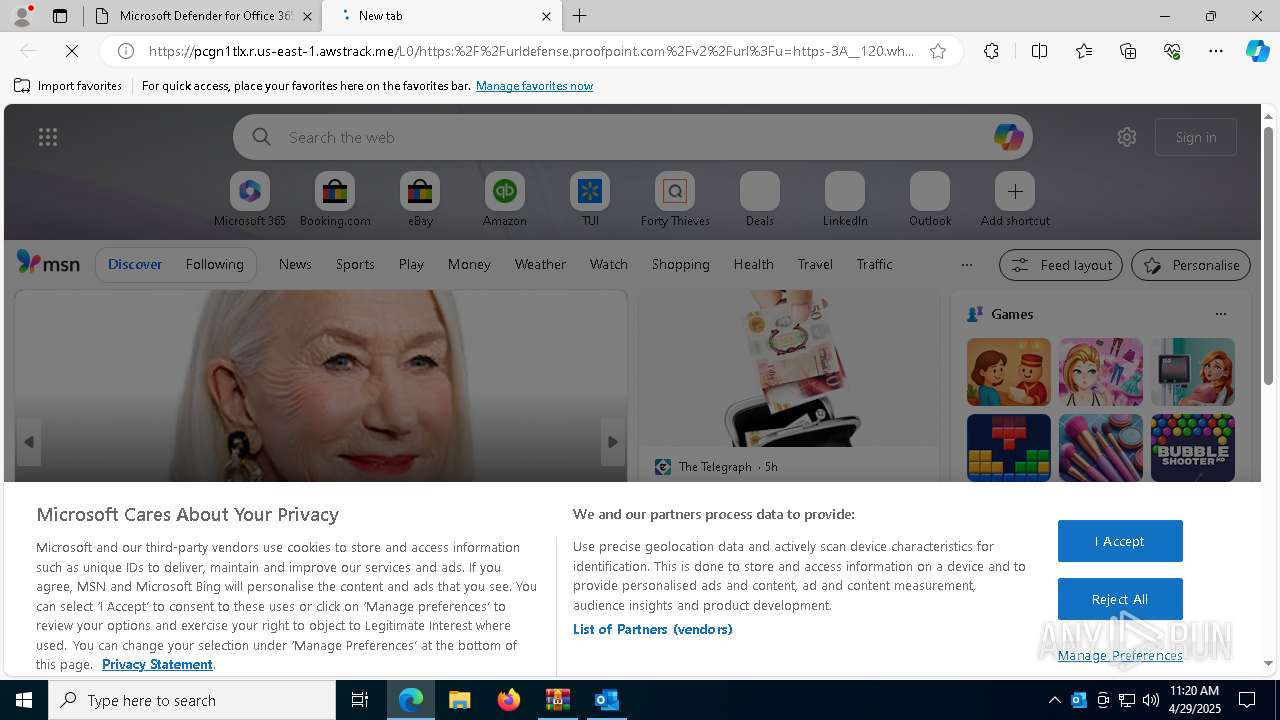
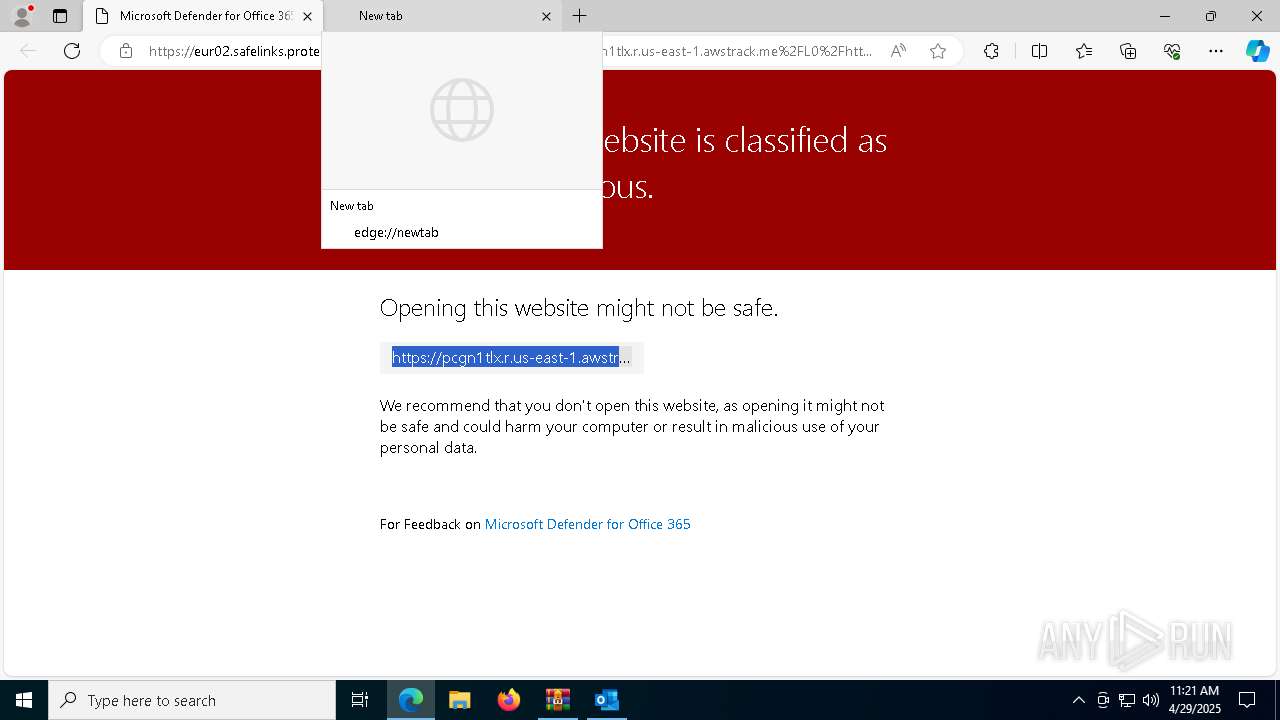
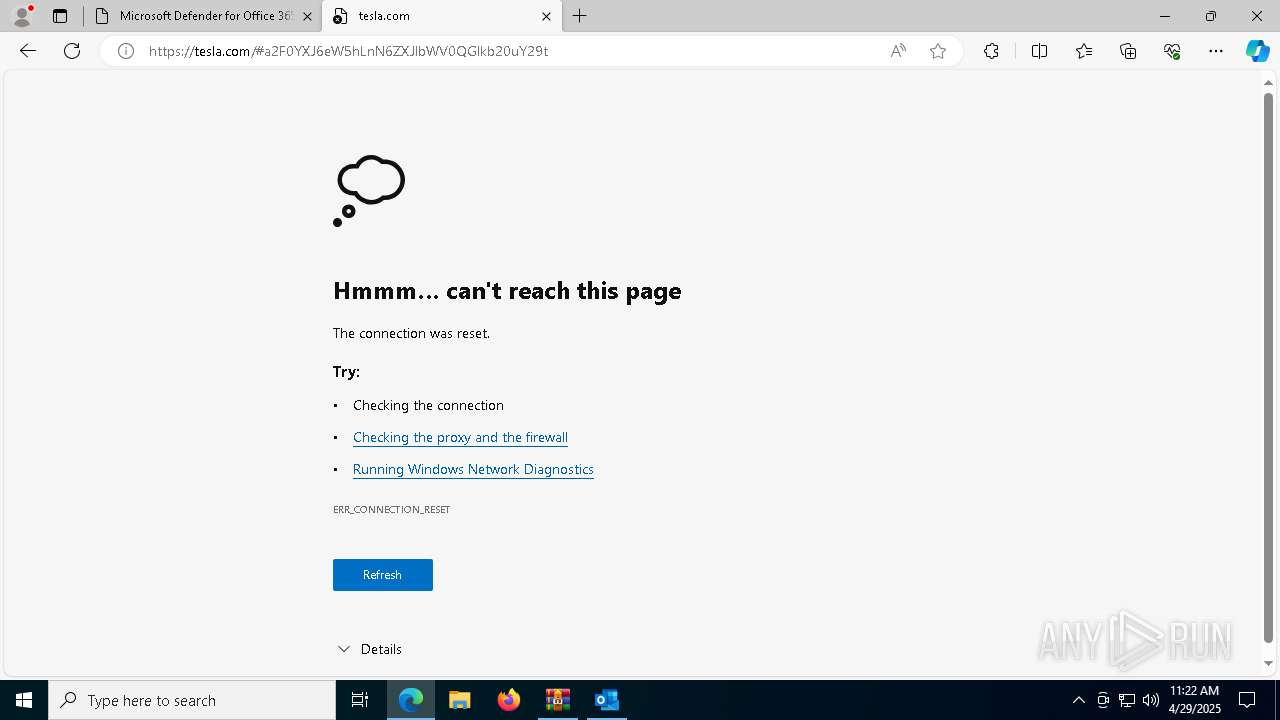
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://eur02.safelinks.protection.outlook.com/?url=https%3A%2F%2Fpcgn1tlx.r.us-east-1.awstrack.me%2FL0%2Fhttps%3A%252F%252Furldefense.proofpoint.com%252Fv2%252Furl%253Fu%3Dhttps-3A__120.wheneatingawolf.net%2526d%3DDwMFAw%2526c%3DeuGZstcaTDllvimEN8b7jXrwqOf-v5A_CdpgnVfiiMM%2526r%3DUoROyWS-6Zw04uqcZ6yhD9yFmC9e2PR4wXRTZWOoqVA%2526m%3Drjtehxu_Ya1EFd4cwshi9M4OYCiRNY899aU27DhoAlyW6ye0QZ4iGB7ghJGODwvC%2526s%3DvPCxPusw6Tu-UPI_wXAZZMma036GZgm2dwxYLNVUWiQ%2526e%3D%2523a2F0YXJ6eW5hLnN6ZXJlbWV0QGlkb20uY29t%2F1%2F010001967e36dc7c-02036810-7184-4280-8e1e-a3d8275a0787-000000%2FA2wQCWzjH1rTeVHdPc-SRuo5-C8%3D423&data=05%7C02%7Ckatarzyna.szeremet%40idom.com%7Cbc05b427227147214e3008dd8698378d%7Cb853f9774183428f855cffe7328b6f13%7C0%7C0%7C638814712431675352%7CUnknown%7CTWFpbGZsb3d8eyJFbXB0eU1hcGkiOnRydWUsIlYiOiIwLjAuMDAwMCIsIlAiOiJXaW4zMiIsIkFOIjoiTWFpbCIsIldUIjoyfQ%3D%3D%7C60000%7C%7C%7C&sdata=gfmjYdiVBrNlMuvh7Ud5mXbOKtKmxiFDEQs9a5xFwwM%3D&reserved=0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6148 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6812 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5608 --field-trial-handle=2432,i,211660522883225256,2093885996824265305,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
18 593
Read events
18 072
Write events
436
Delete events
85
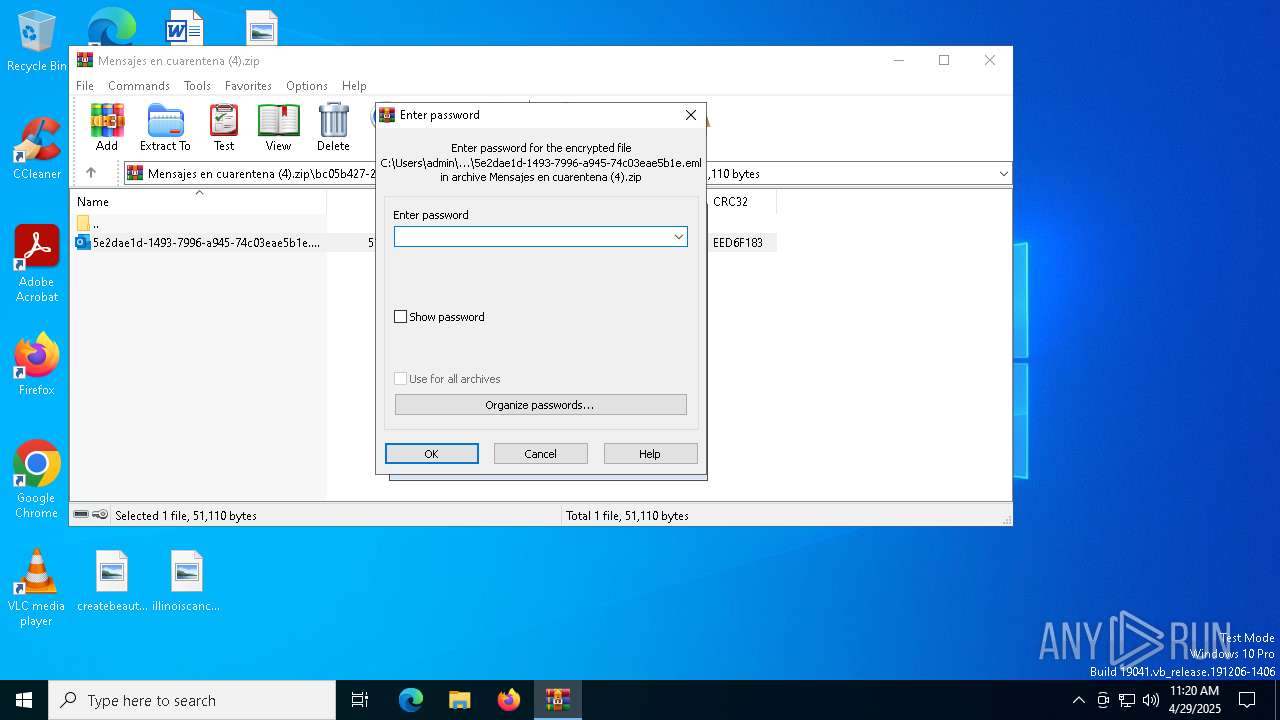
Modification events
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Mensajes en cuarentena (4).zip | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
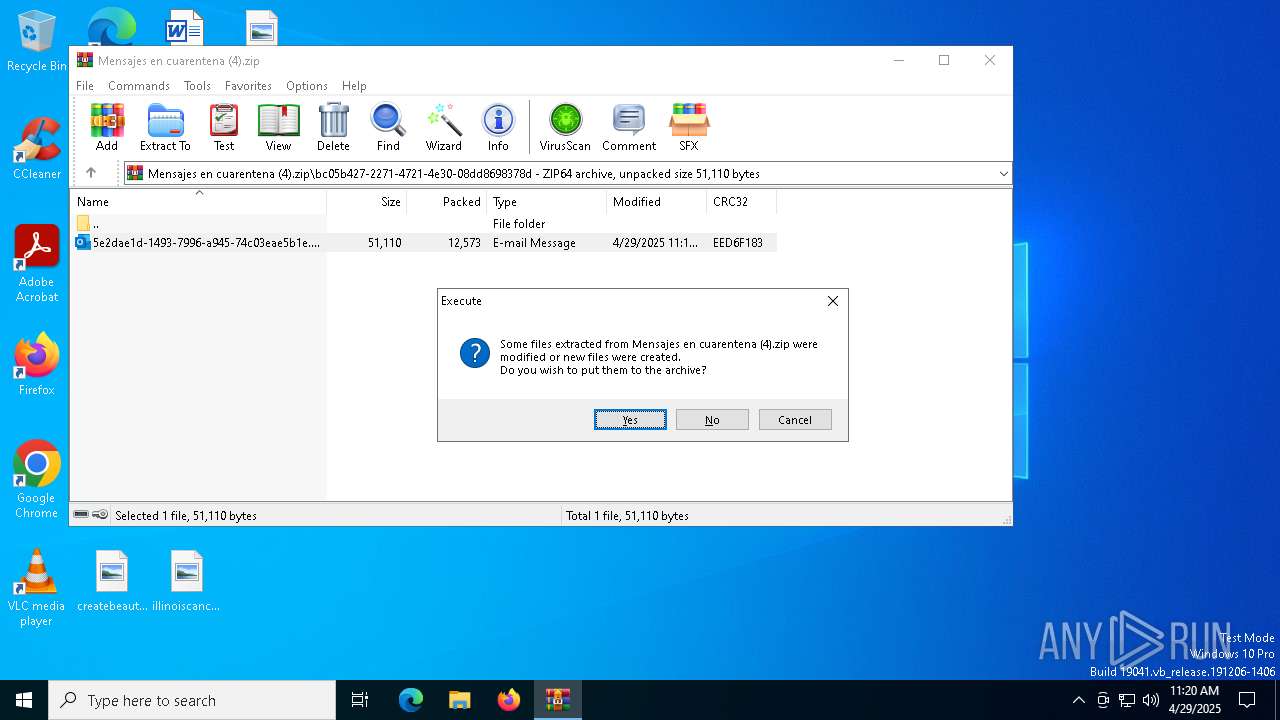
| (PID) Process: | (7336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.eml\OpenWithProgids |
| Operation: | write | Name: | Outlook.File.eml.15 |
Value: | |||
Executable files
34
Suspicious files
741
Text files
137
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7928 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\089C411E-C08A-4956-8793-11EF32F1884C | xml | |
MD5:86F8DCAE70CA1B5A3B3A8DD82AFCA4A3 | SHA256:20583F800C8FD29B4B448B0445922862EBF7889BF422594048612165DA547748 | |||
| 7336 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7336.41459\5e2dae1d-1493-7996-a945-74c03eae5b1e.eml | binary | |
MD5:DC8C69600C3B109AE6F39A5EEC6233A2 | SHA256:BD47B43E731D2BA54BDEADB0132544BB6274956B1ABD4230EA0D8F2A3ED93245 | |||
| 1324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11442a.TMP | — | |
MD5:— | SHA256:— | |||
| 7928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:604C16BF7A7181C03067AB1BCEBD7F57 | SHA256:B4415B2CFED401D774A4751CD1D48757FEC6B5615EBB4910B56746CED6972067 | |||
| 1324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7928 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:FB60FF789C58BC6CDCCF1F388665810F | SHA256:D0D379988D4ED6E4ACBE57E83246B62FE36DACBF96793173F626B7E31FDFB8E4 | |||
| 1324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11442a.TMP | — | |
MD5:— | SHA256:— | |||
| 1324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11442a.TMP | — | |
MD5:— | SHA256:— | |||
| 1324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
114
DNS requests
125
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 23.48.23.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7928 | OUTLOOK.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7928 | OUTLOOK.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
1164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
1164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
7500 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1746407434&P2=404&P3=2&P4=cjfHSGDM899kcUHSiDbI70teC1zt4DIx8imbQCBRvnvlkx%2bSztBaNgdGmIHjwmIikGVhO3jFkfEnLBOtd9S%2bLg%3d%3d | US | — | — | whitelisted |
7500 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1746407434&P2=404&P3=2&P4=cjfHSGDM899kcUHSiDbI70teC1zt4DIx8imbQCBRvnvlkx%2bSztBaNgdGmIHjwmIikGVhO3jFkfEnLBOtd9S%2bLg%3d%3d | US | binary | 2.05 Kb | whitelisted |
7500 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1746407434&P2=404&P3=2&P4=cjfHSGDM899kcUHSiDbI70teC1zt4DIx8imbQCBRvnvlkx%2bSztBaNgdGmIHjwmIikGVhO3jFkfEnLBOtd9S%2bLg%3d%3d | US | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.170:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7928 | OUTLOOK.EXE | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6132 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (wheneatingawolf .net) |
6132 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (wheneatingawolf .net) |