| File name: | sample.bin |
| Full analysis: | https://app.any.run/tasks/f9d0ca47-0d8a-4132-a33d-671e6c1de171 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 13:59:23 |
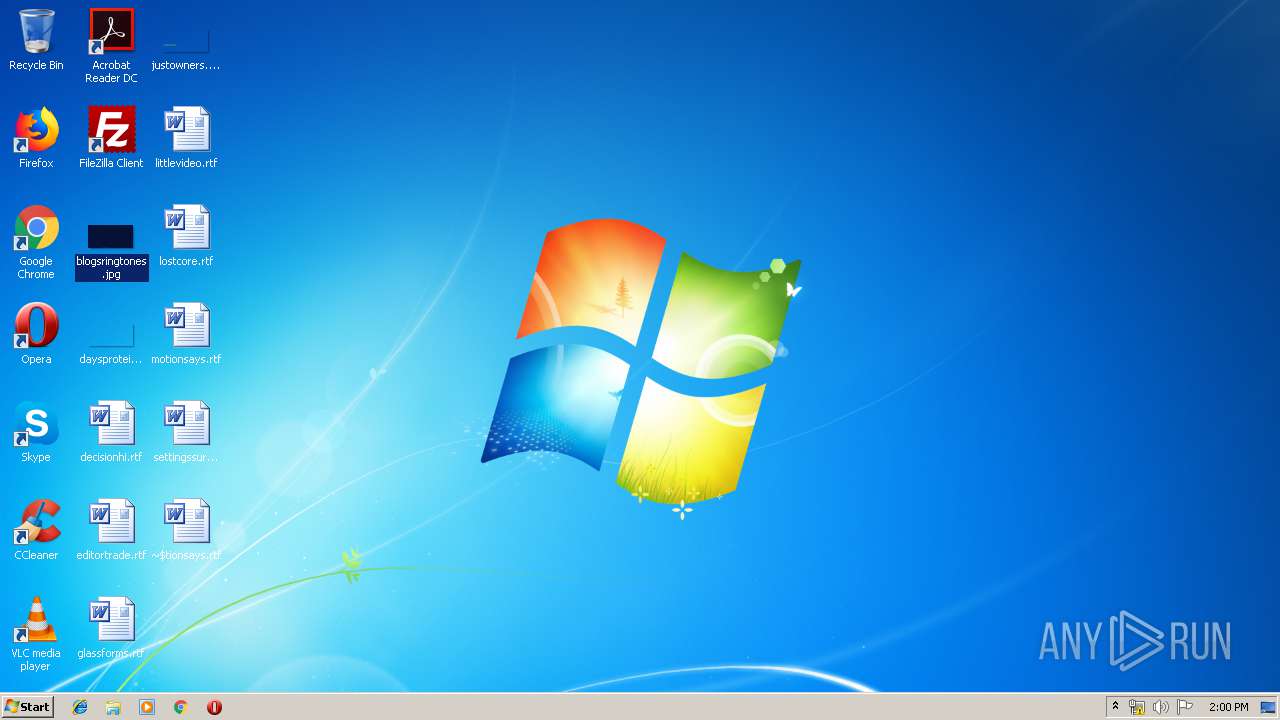
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | C41A0E1DDEB85B6326A3DC403A5FD0FA |
| SHA1: | 3C8E60CE5FF0CB21BE39D1176D1056F9EF9438FA |
| SHA256: | D0CDE86D47219E9C56B717F55DCDB01B0566344C13AA671613598CAB427345B9 |
| SSDEEP: | 6144:MqT9DnJsEEyhxbPL73veqySdCNivJo0v6e:F7jxzL732qyeuivC0y |
MALICIOUS
Actions looks like stealing of personal data
- sample.bin.exe (PID: 3108)
SUSPICIOUS
Creates files in the program directory
- sample.bin.exe (PID: 3108)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 4072)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:05 20:00:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 229376 |
| InitializedDataSize: | 13824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x24936 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Feb-2019 19:00:34 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Feb-2019 19:00:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00037F5A | 0x00038000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5978 |
.data | 0x00039000 | 0x00002B80 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.04014 |
.rsrc | 0x0003C000 | 0x00000970 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.17363 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.18966 | 2216 | UNKNOWN | English - United States | RT_ICON |
C | 1.81924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2388 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\sample.bin.exe" | C:\Users\admin\AppData\Local\Temp\sample.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4072 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\motionsays.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
539
Read events
497
Write events
31
Delete events
11
Modification events
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "0 |
Value: 22302000E80F0000010000000000000000000000 | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1316290591 | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290704 | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290705 | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: E80F00003A19F76AEEDFD40100000000 | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | )1 |
Value: 29312000E80F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | )1 |
Value: 29312000E80F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (4072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
494
Text files
61
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | sample.bin.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini.Clop | binary | |
MD5:— | SHA256:— | |||
| 3108 | sample.bin.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 3108 | sample.bin.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.Clop | binary | |
MD5:— | SHA256:— | |||
| 3108 | sample.bin.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr65536.dat.Clop | binary | |
MD5:— | SHA256:— | |||
| 3108 | sample.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\ClopReadMe.txt | text | |
MD5:DA76CDBC83863176E9DA51B1C9224139 | SHA256:E79DFC0BBDEFCA3815FFB349139A512E7090403A1E4D80414B97B3E567C7C1AD | |||
| 3108 | sample.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\ClopReadMe.txt | text | |
MD5:DA76CDBC83863176E9DA51B1C9224139 | SHA256:E79DFC0BBDEFCA3815FFB349139A512E7090403A1E4D80414B97B3E567C7C1AD | |||
| 3108 | sample.bin.exe | C:\Users\admin\.oracle_jre_usage\ClopReadMe.txt | text | |
MD5:DA76CDBC83863176E9DA51B1C9224139 | SHA256:E79DFC0BBDEFCA3815FFB349139A512E7090403A1E4D80414B97B3E567C7C1AD | |||
| 3108 | sample.bin.exe | C:\Users\admin\ClopReadMe.txt | text | |
MD5:DA76CDBC83863176E9DA51B1C9224139 | SHA256:E79DFC0BBDEFCA3815FFB349139A512E7090403A1E4D80414B97B3E567C7C1AD | |||
| 3108 | sample.bin.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\ClopReadMe.txt | text | |
MD5:DA76CDBC83863176E9DA51B1C9224139 | SHA256:E79DFC0BBDEFCA3815FFB349139A512E7090403A1E4D80414B97B3E567C7C1AD | |||
| 3108 | sample.bin.exe | C:\ProgramData\ClopReadMe.txt | text | |
MD5:DA76CDBC83863176E9DA51B1C9224139 | SHA256:E79DFC0BBDEFCA3815FFB349139A512E7090403A1E4D80414B97B3E567C7C1AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report