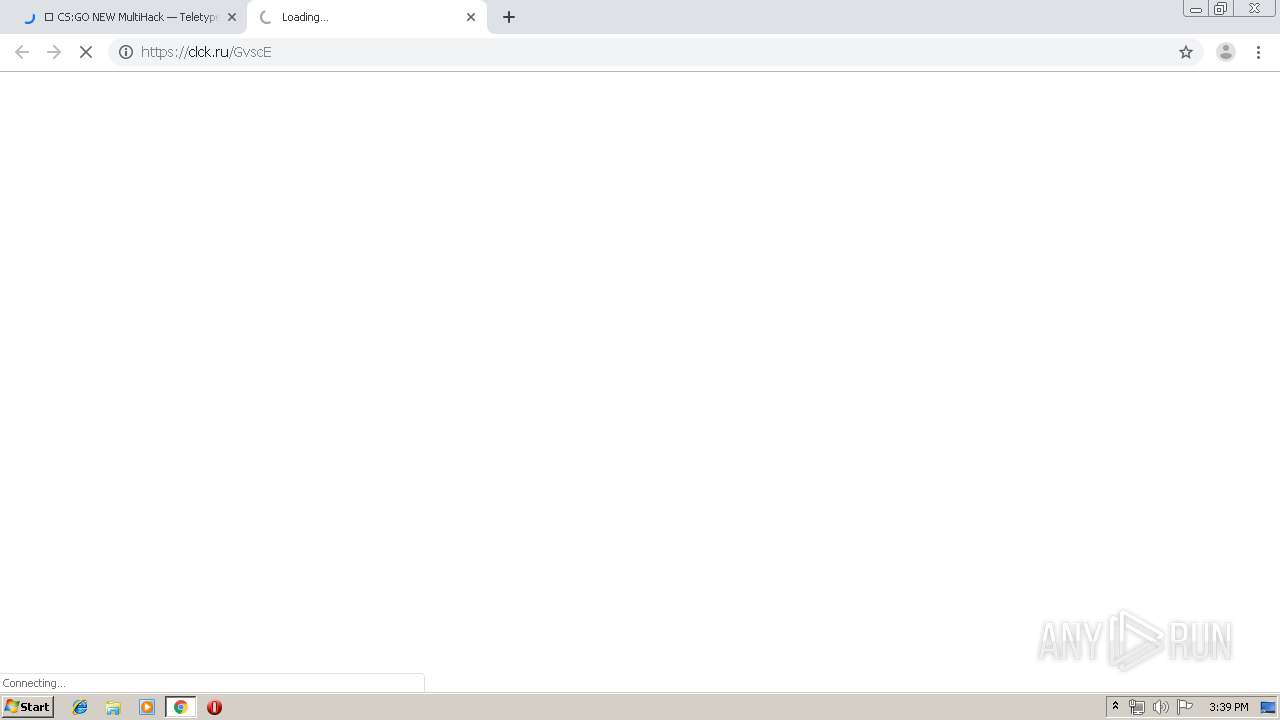
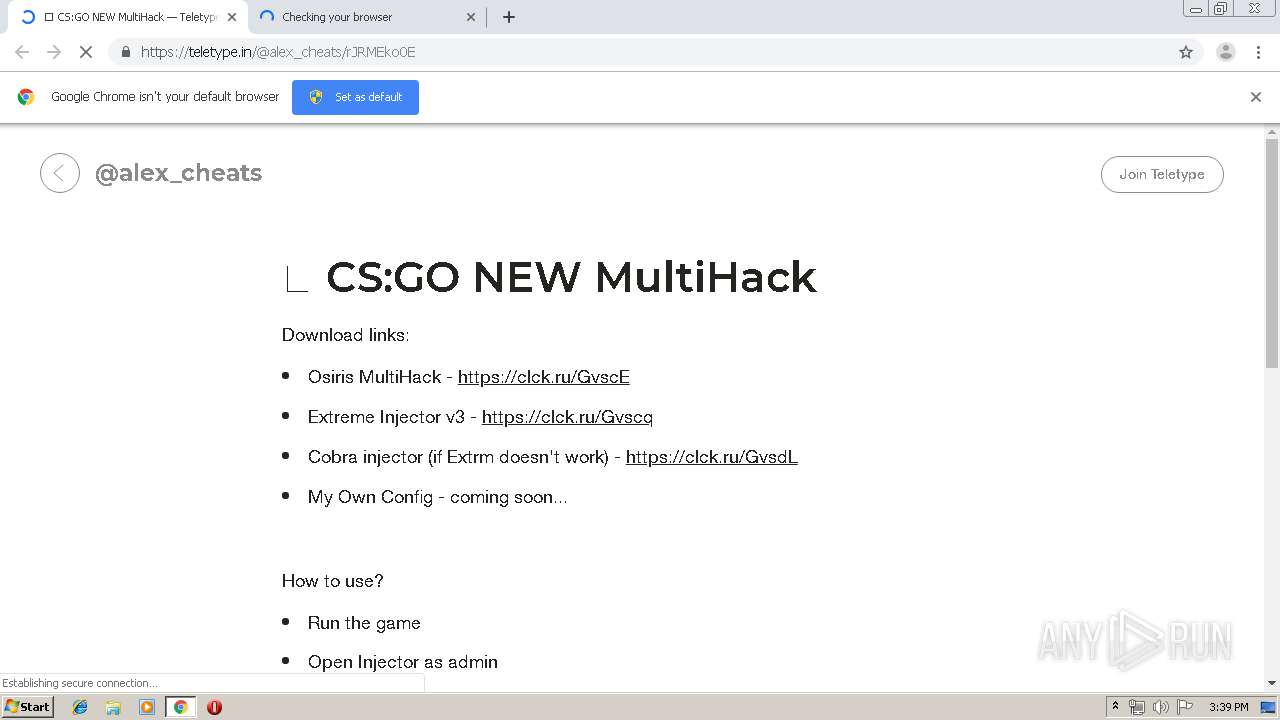
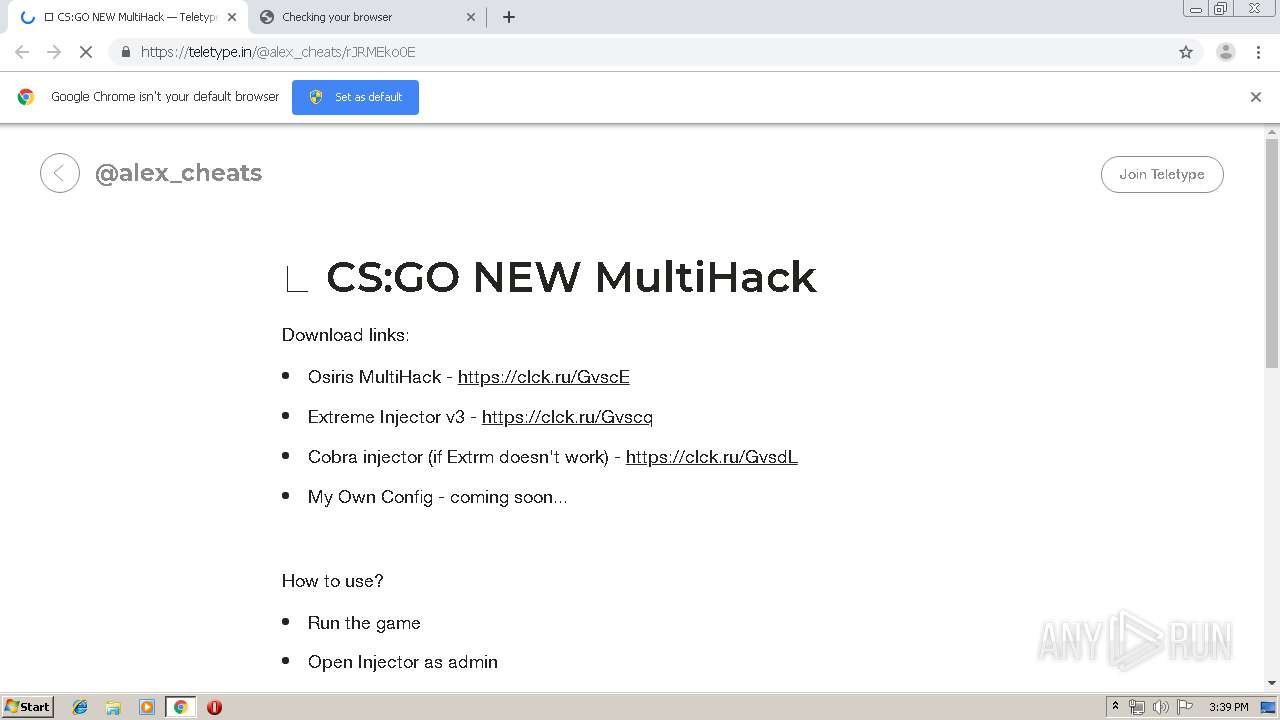
| URL: | https://clck.ru/Gvsdz |
| Full analysis: | https://app.any.run/tasks/c25b22c1-d0df-4376-9375-7c3e043001c4 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2019, 14:38:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6D47EE9C236A2440EE17C306130E1A24 |
| SHA1: | E94B15942BB5BC88E5DC99CCD85BB1E8AE7D2C2B |
| SHA256: | D0C738AC6D429F34F6BB43A72ABD88C47E3B06C856D59DFBFD682CCD5FD69B4F |
| SSDEEP: | 3:N8UZLXQKjBfn:2U59fn |
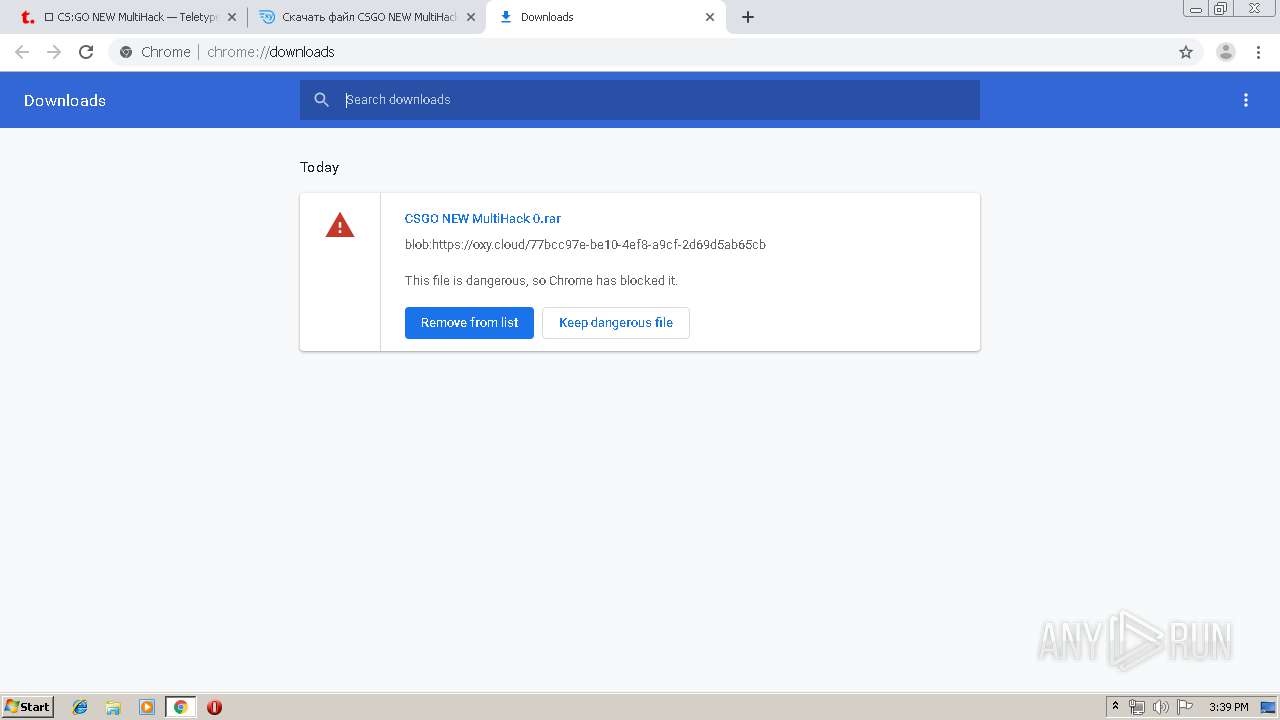
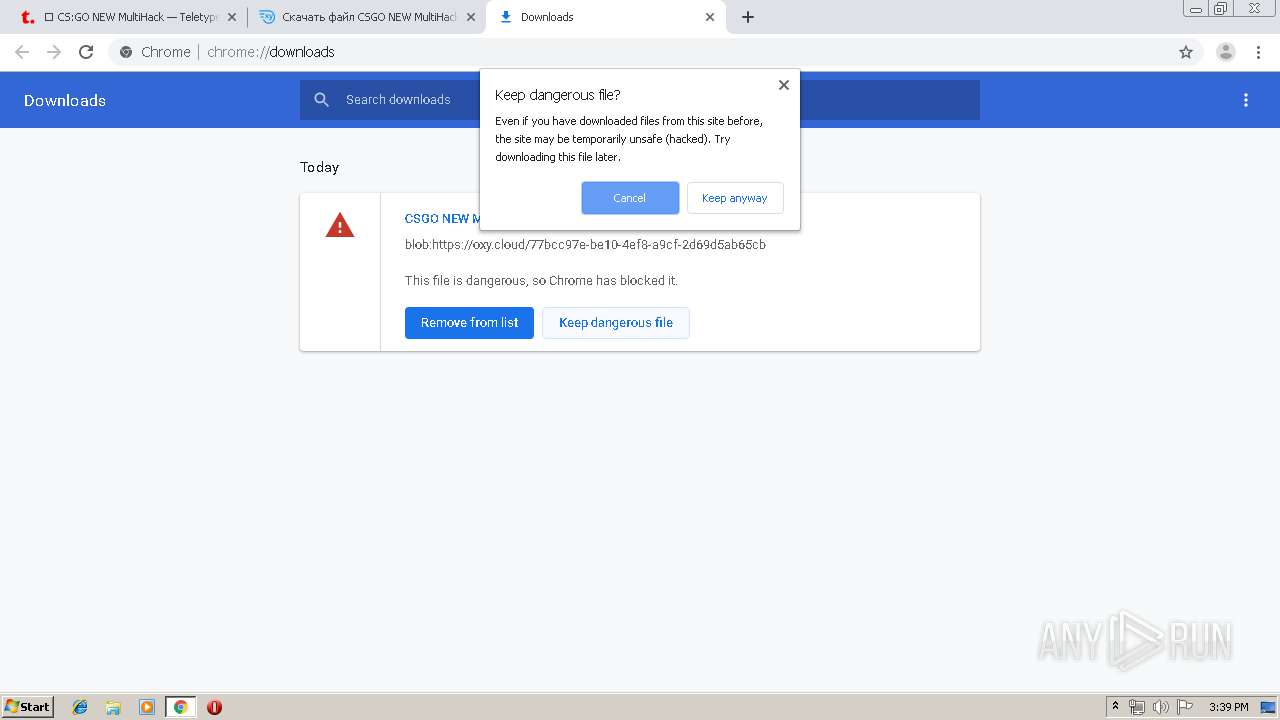
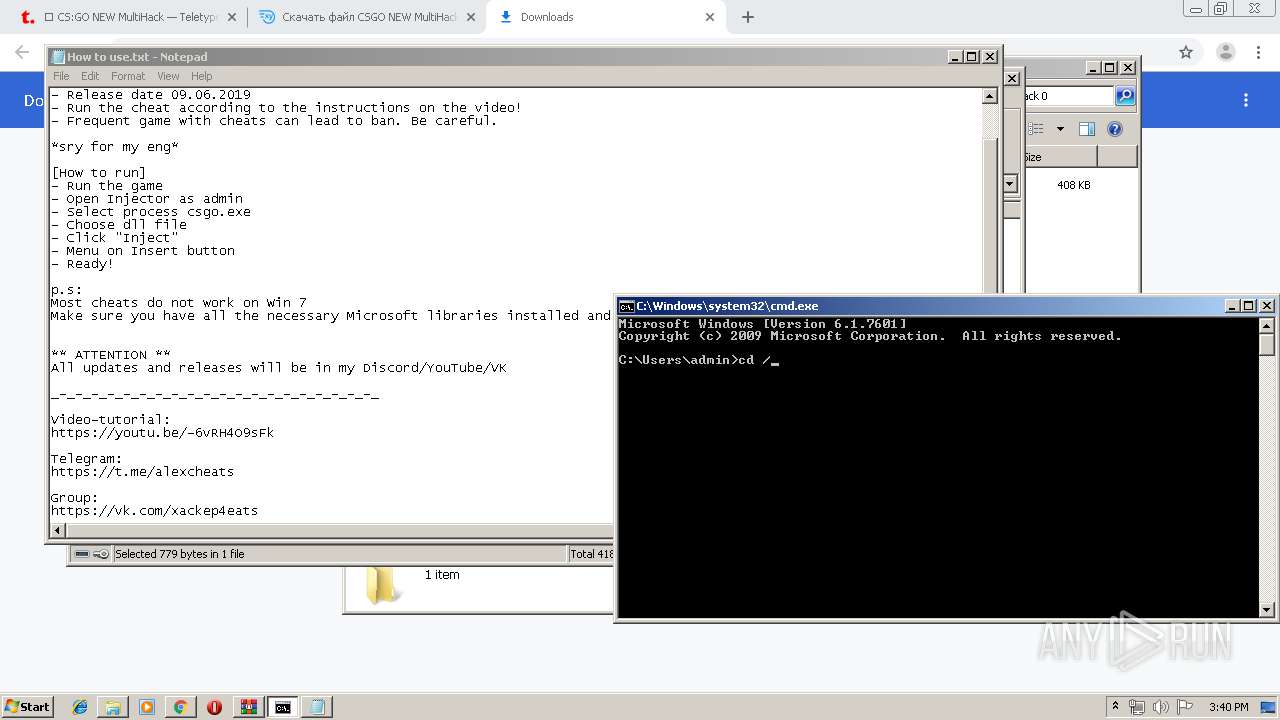
MALICIOUS
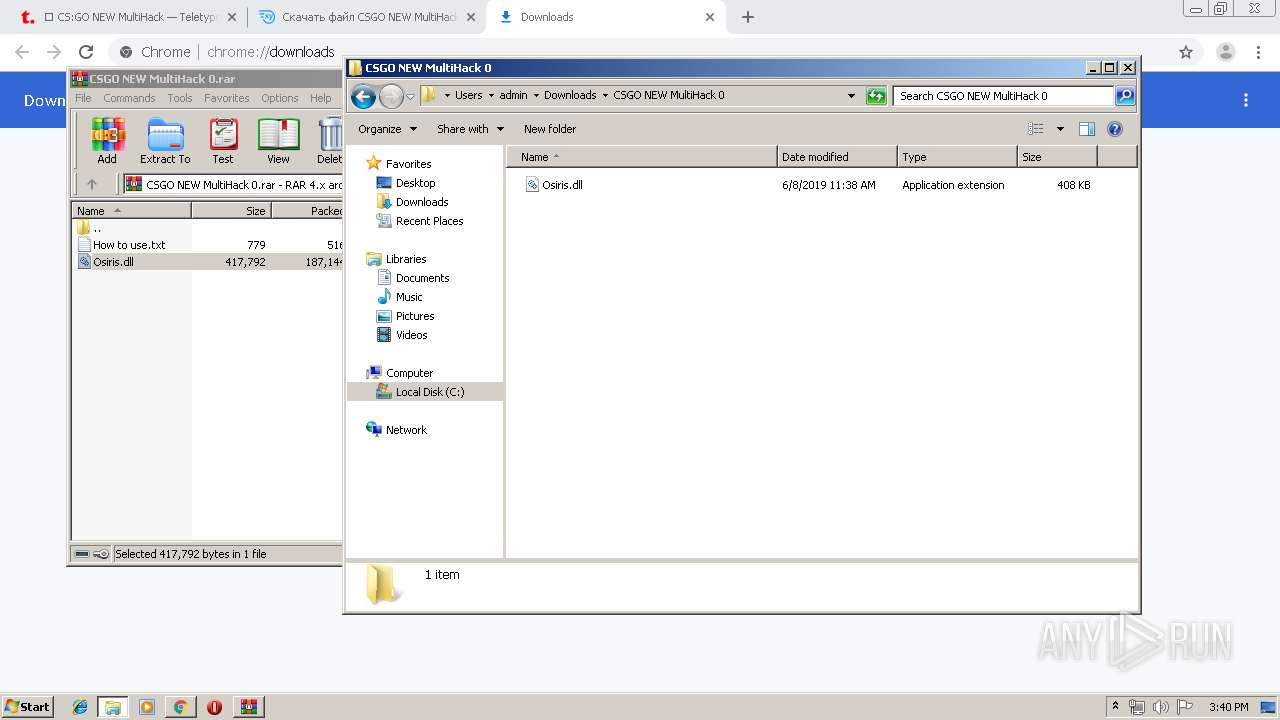
Loads dropped or rewritten executable
- explorer.exe (PID: 128)
- SearchProtocolHost.exe (PID: 592)
Runs app for hidden code execution
- explorer.exe (PID: 128)
SUSPICIOUS
Reads Internet Cache Settings
- explorer.exe (PID: 128)
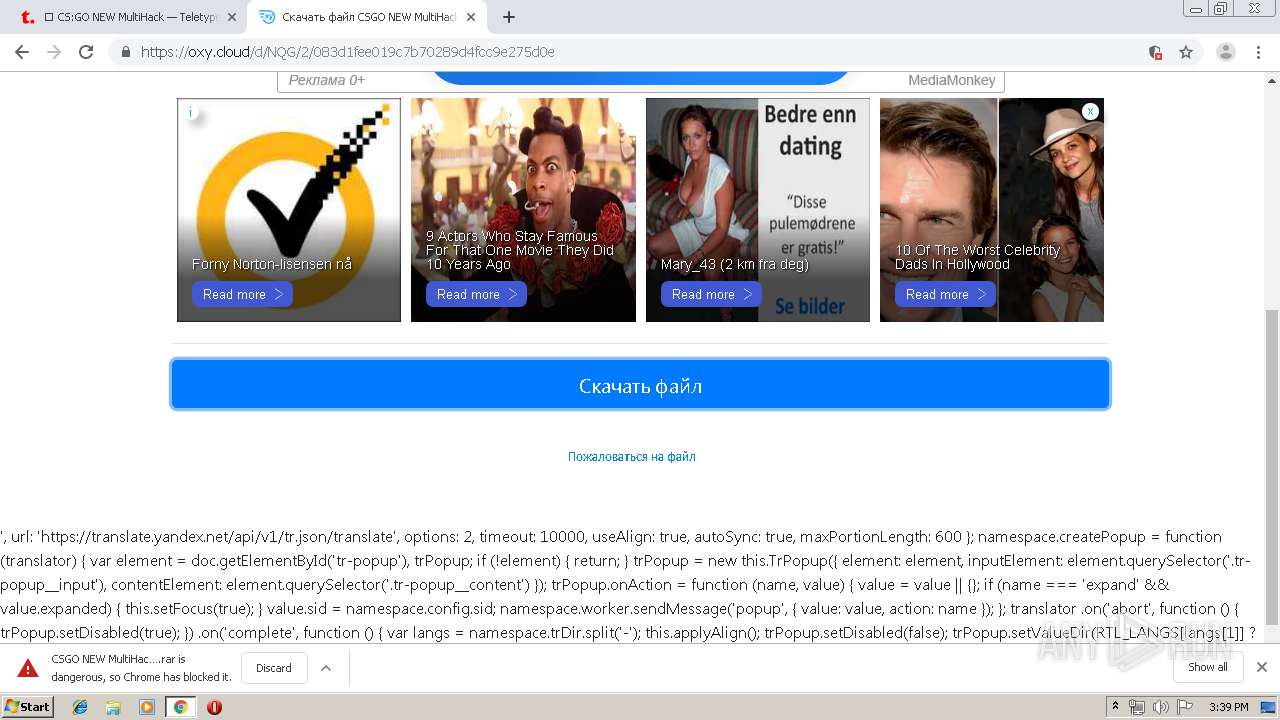
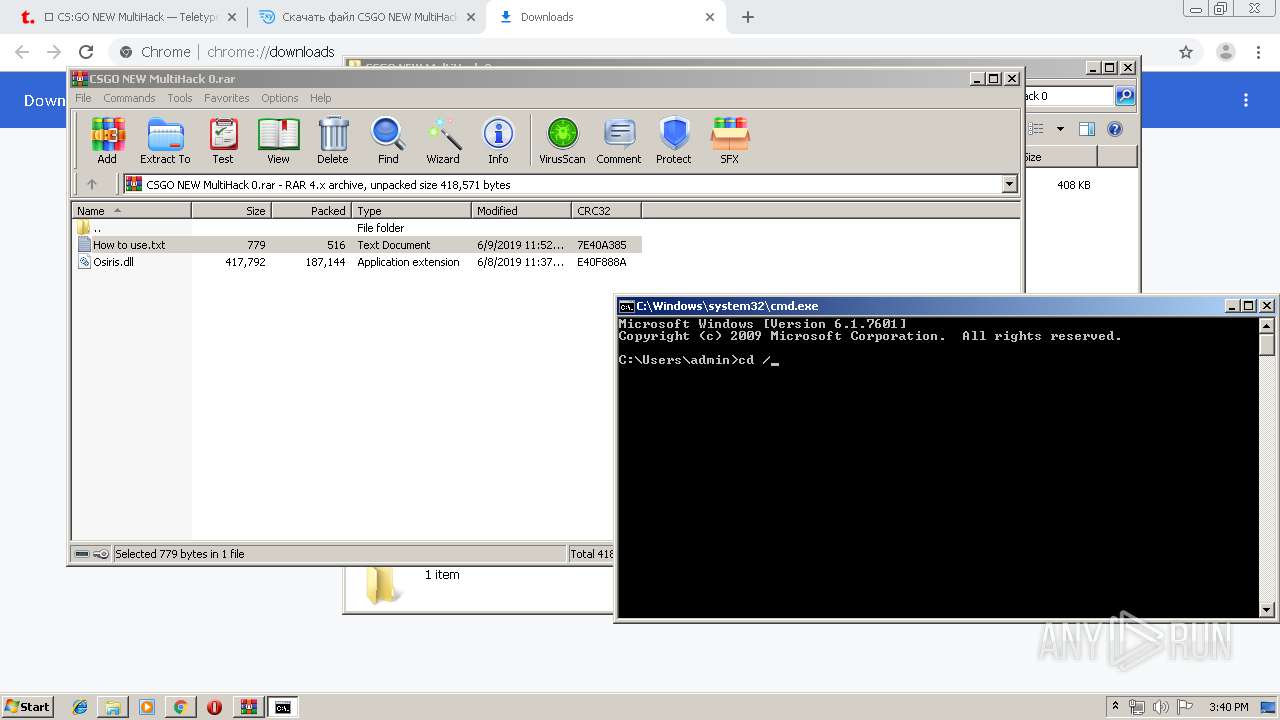
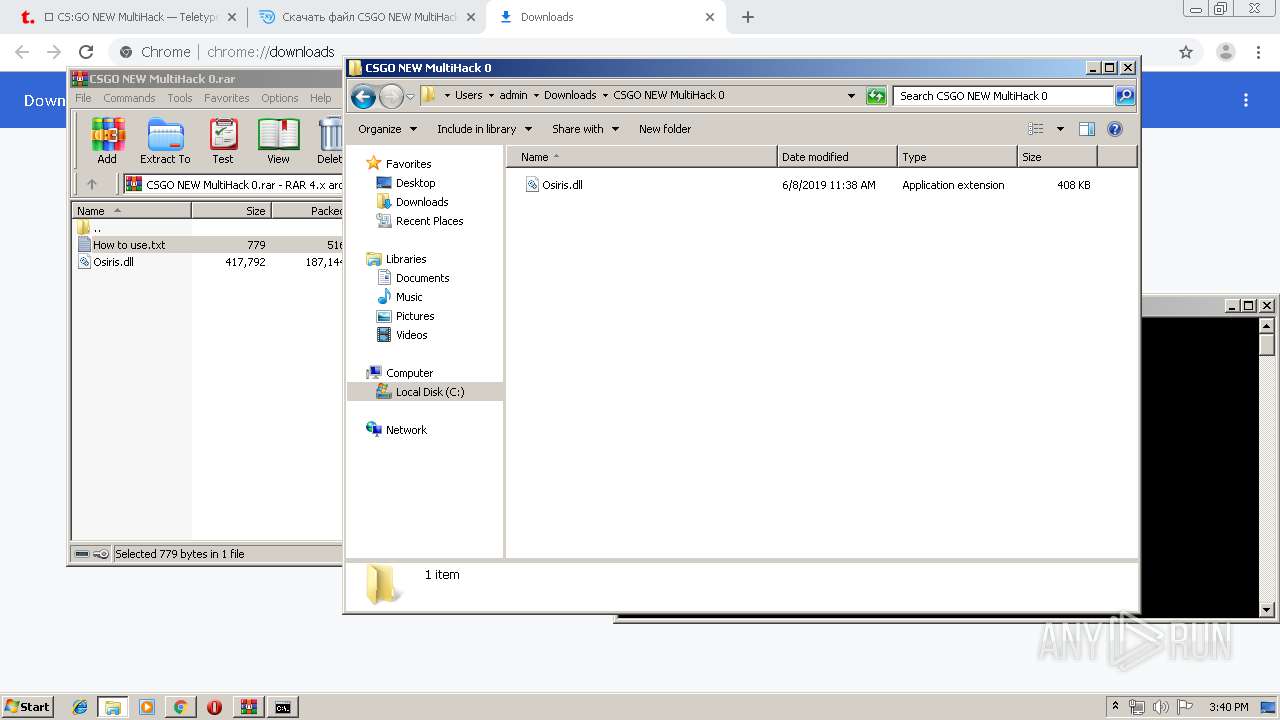
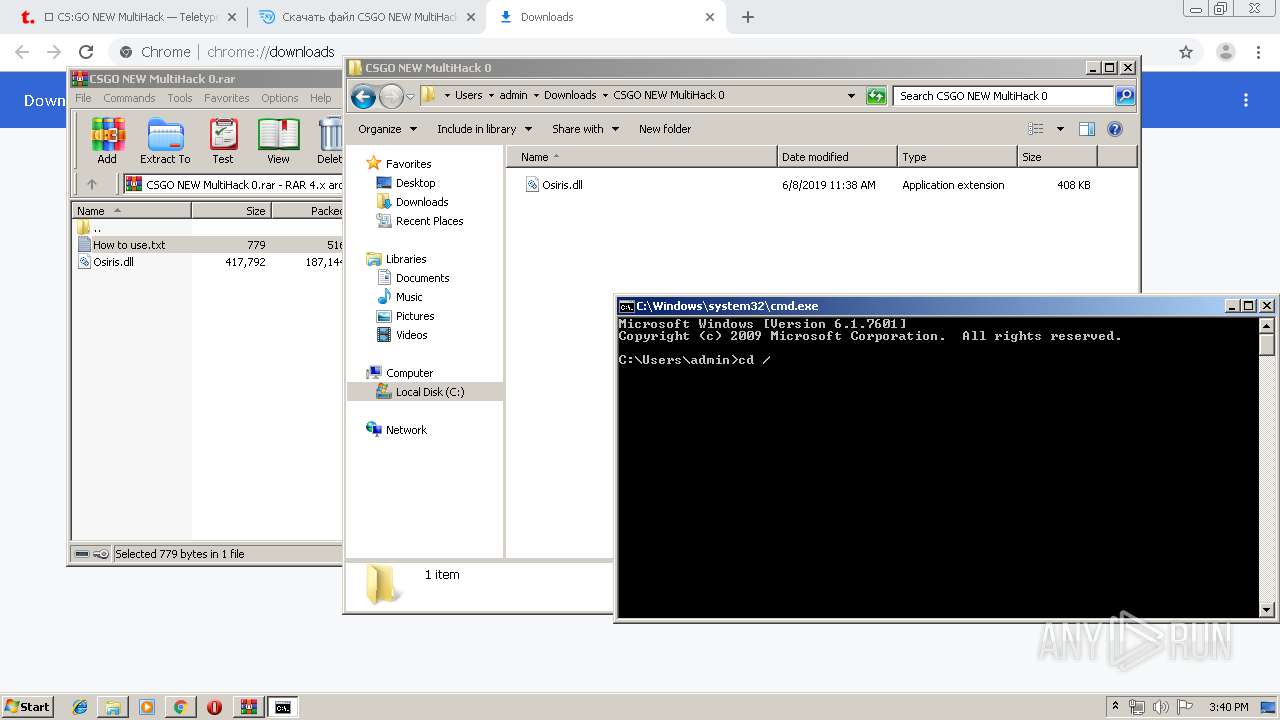
Executable content was dropped or overwritten
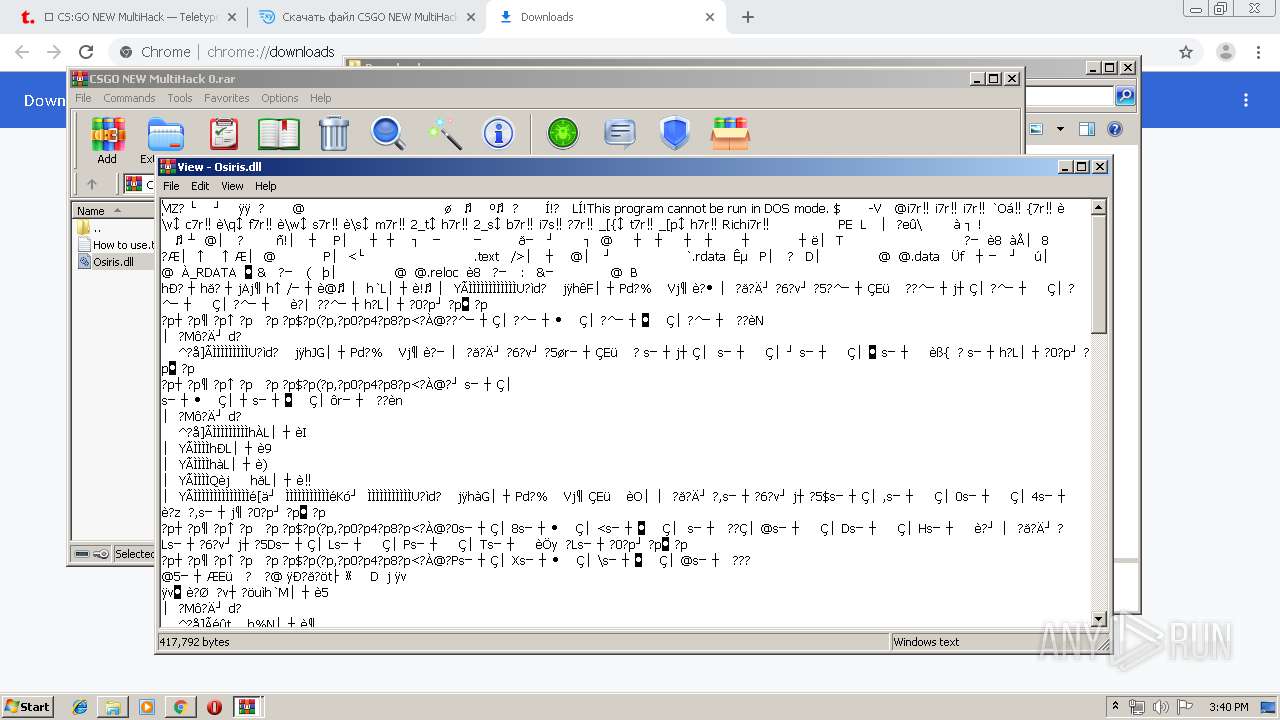
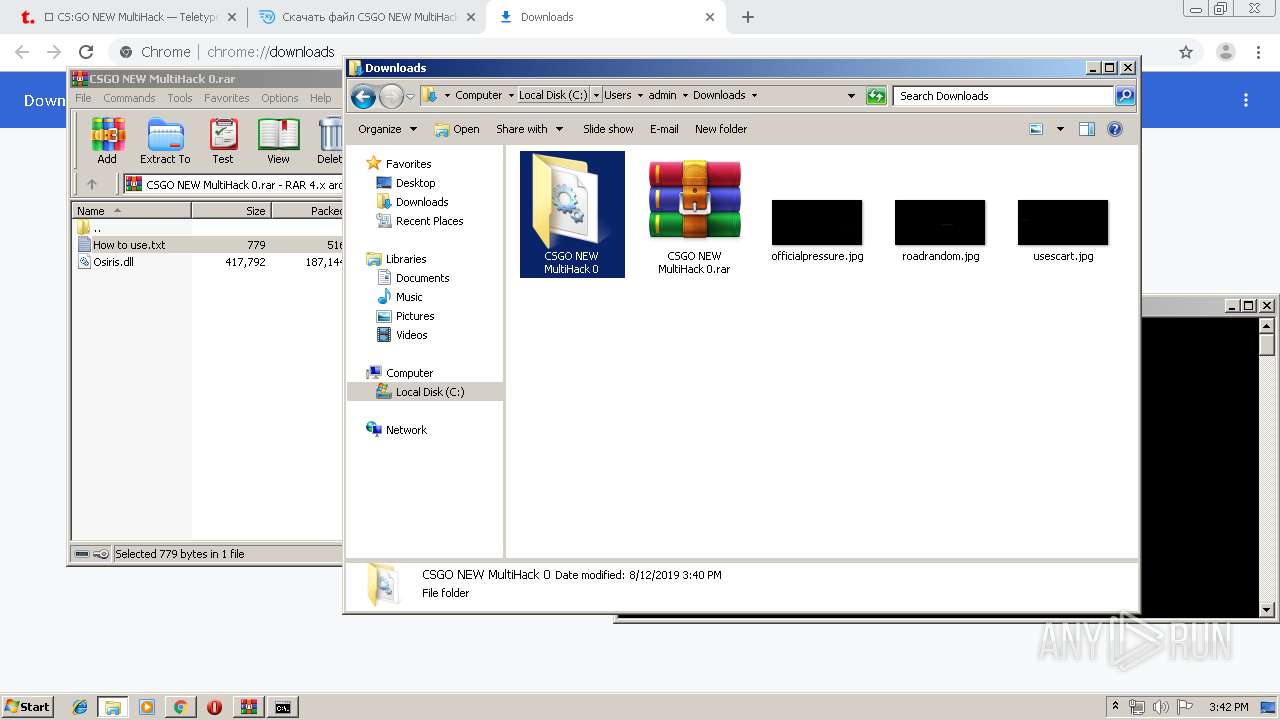
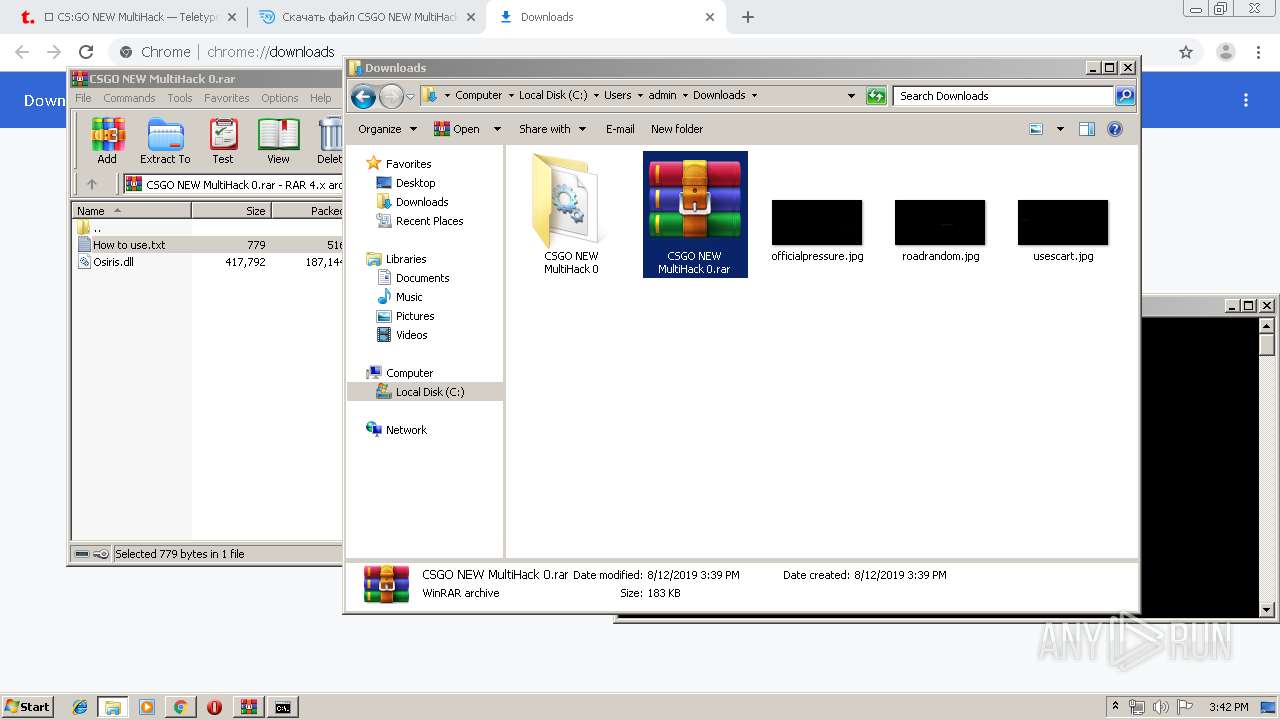
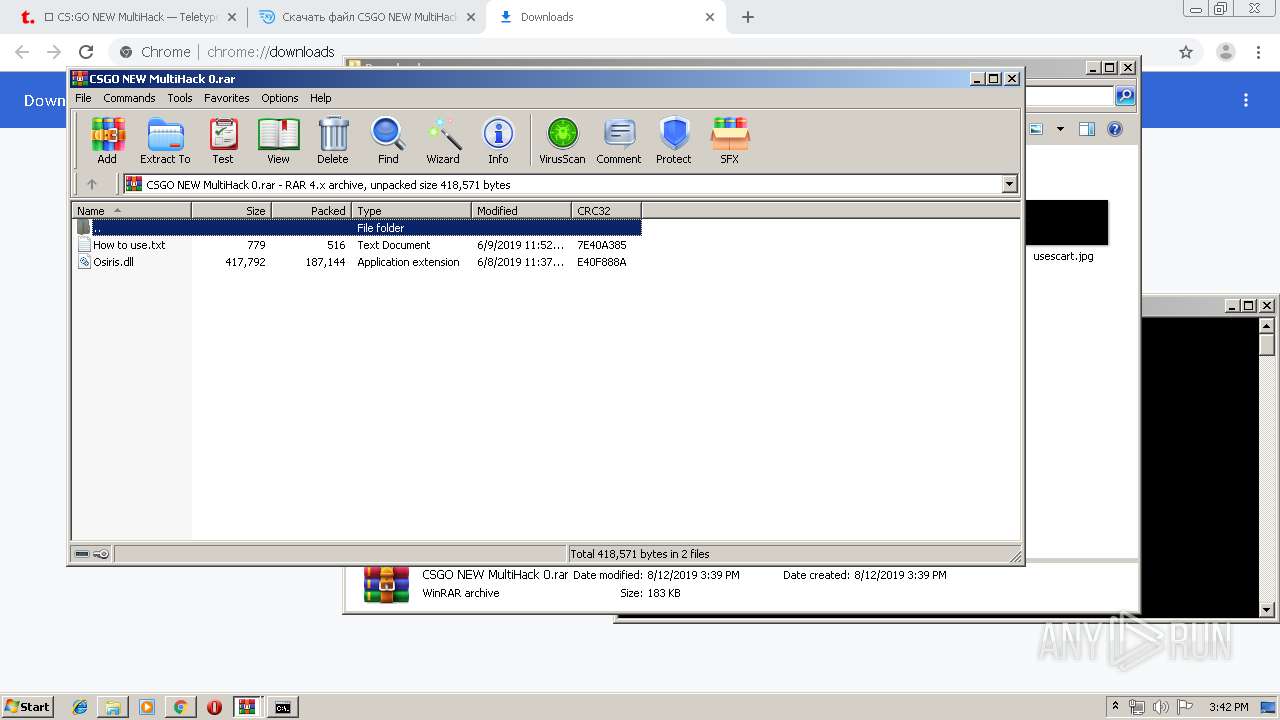
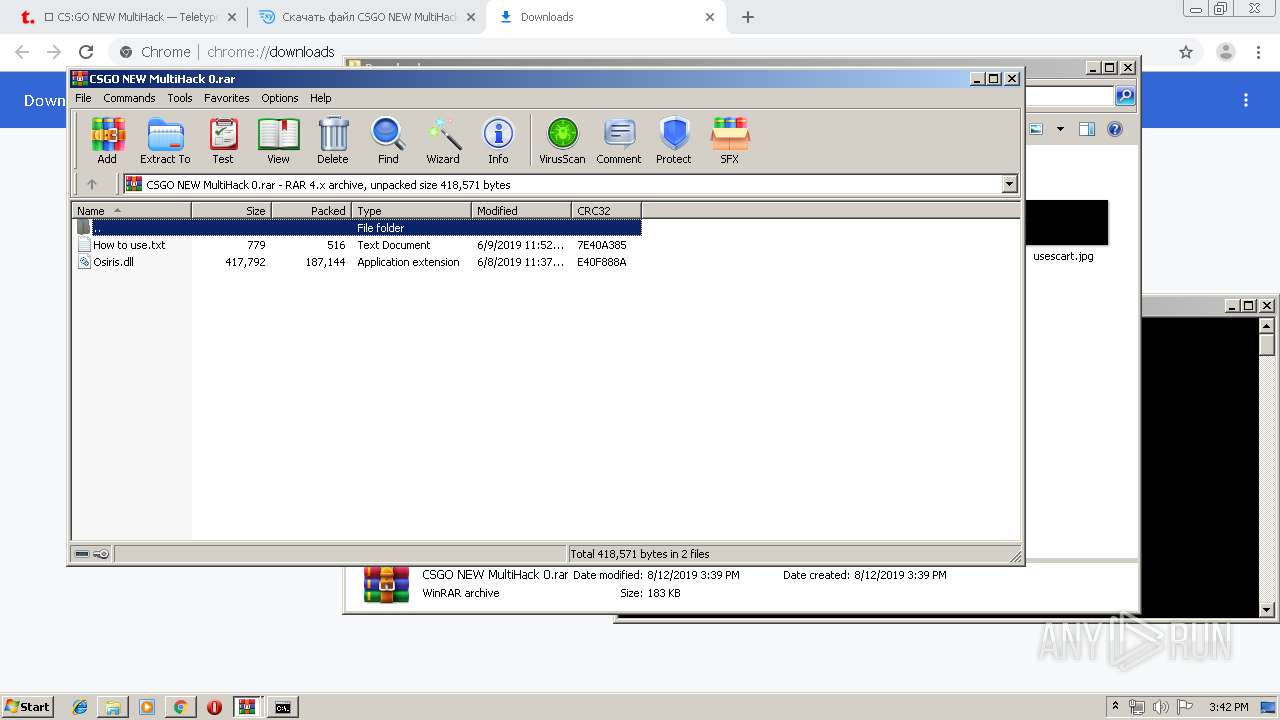
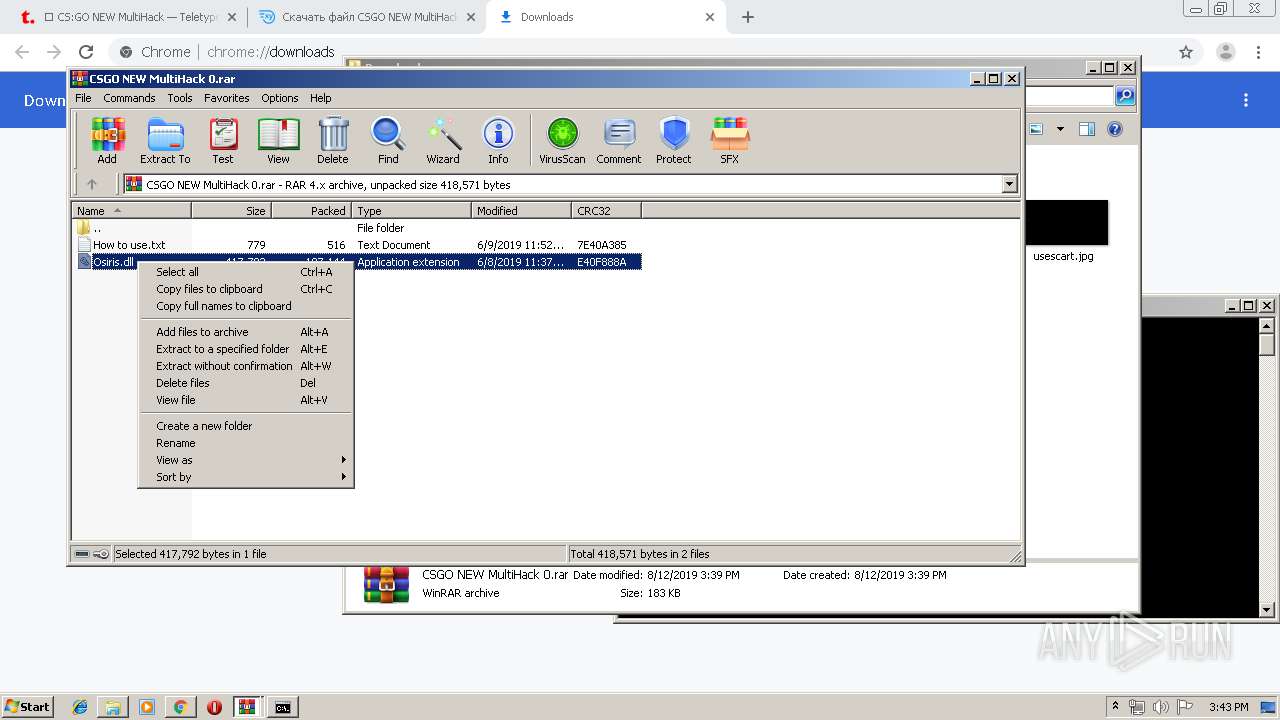
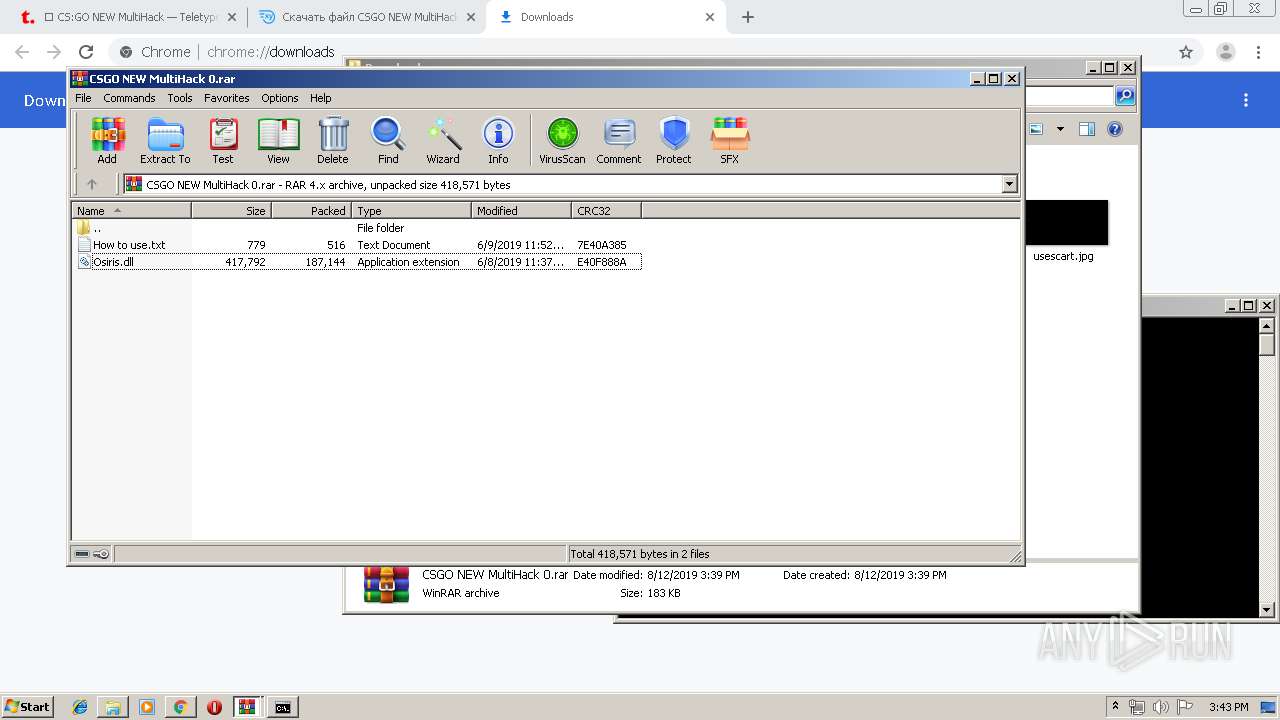
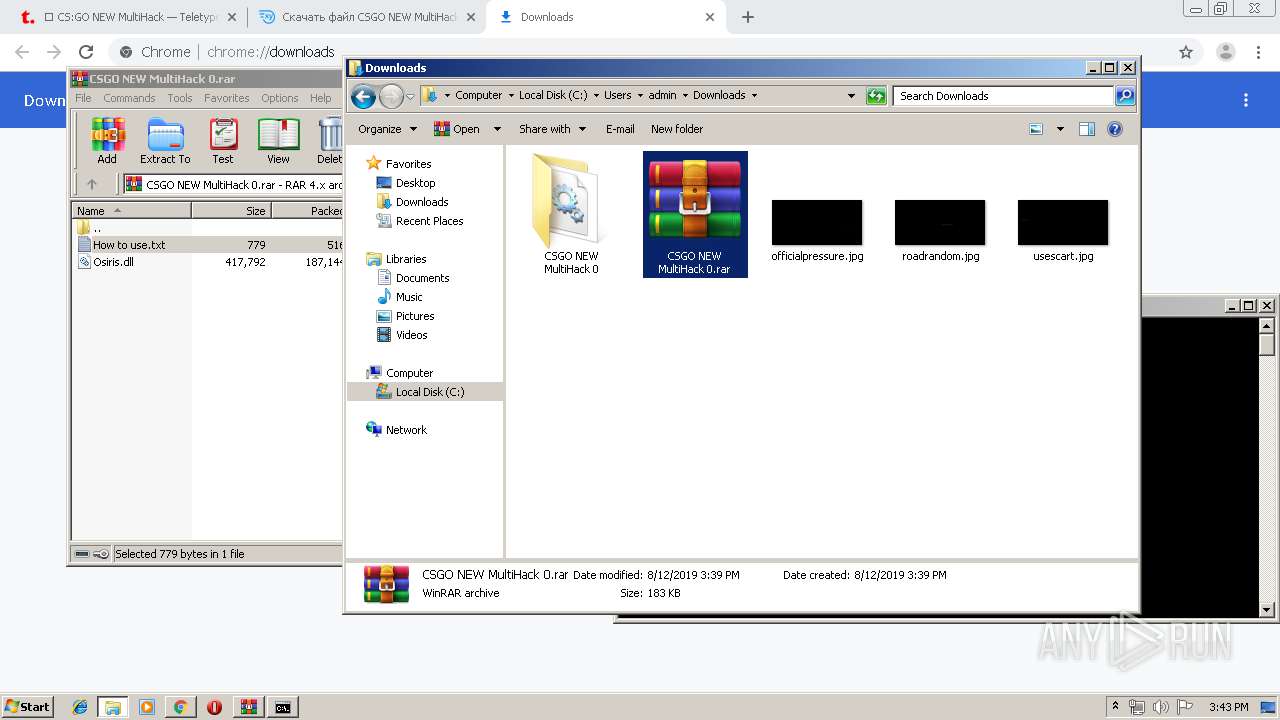
- WinRAR.exe (PID: 3488)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3016)
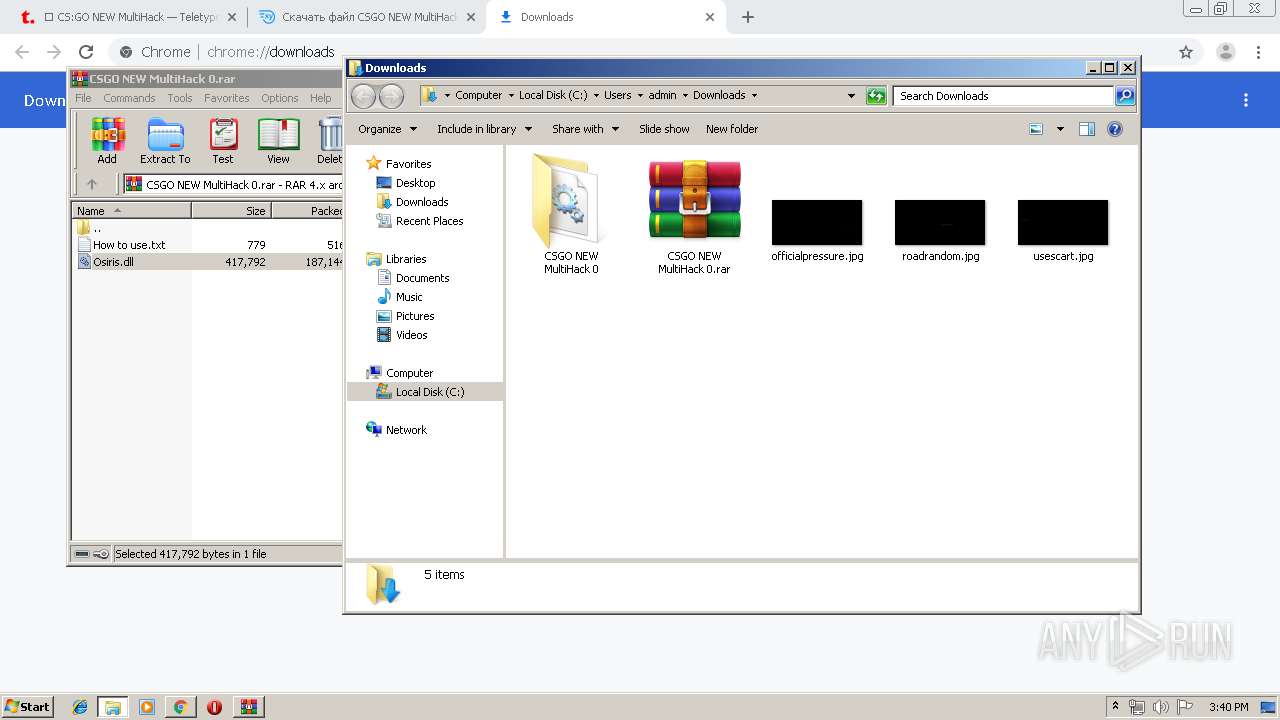
Creates files in the user directory
- explorer.exe (PID: 128)
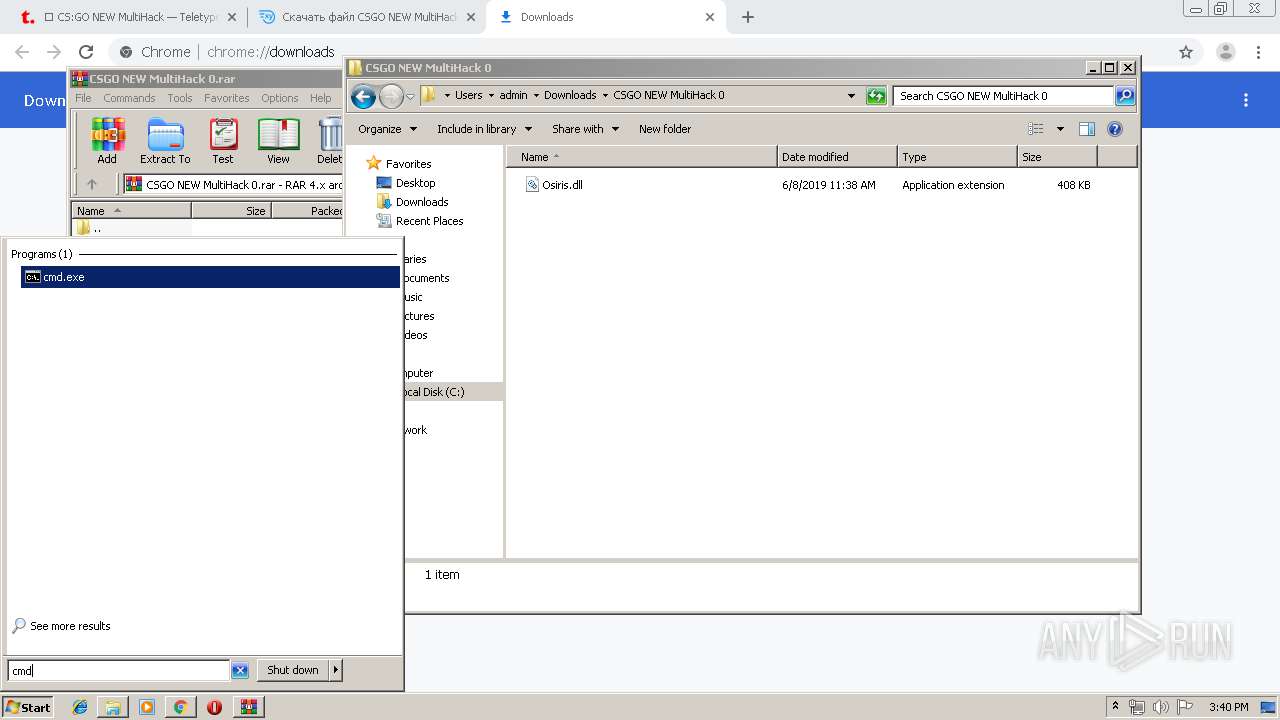
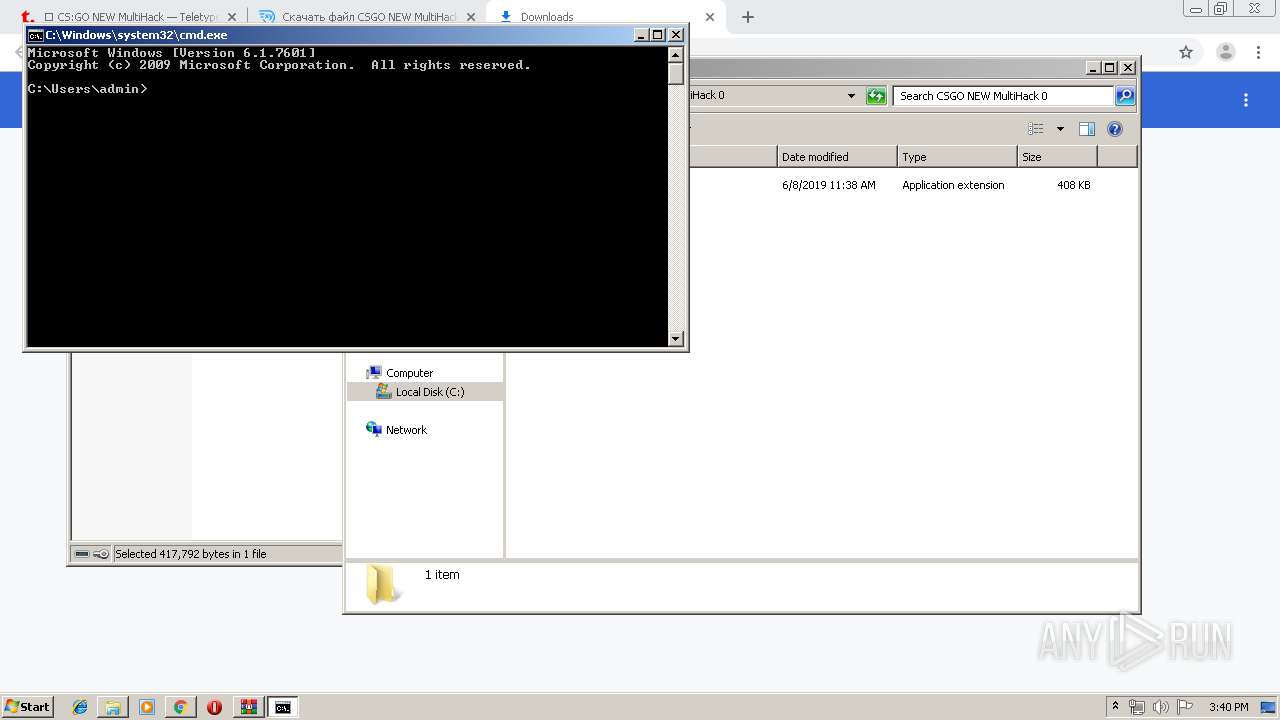
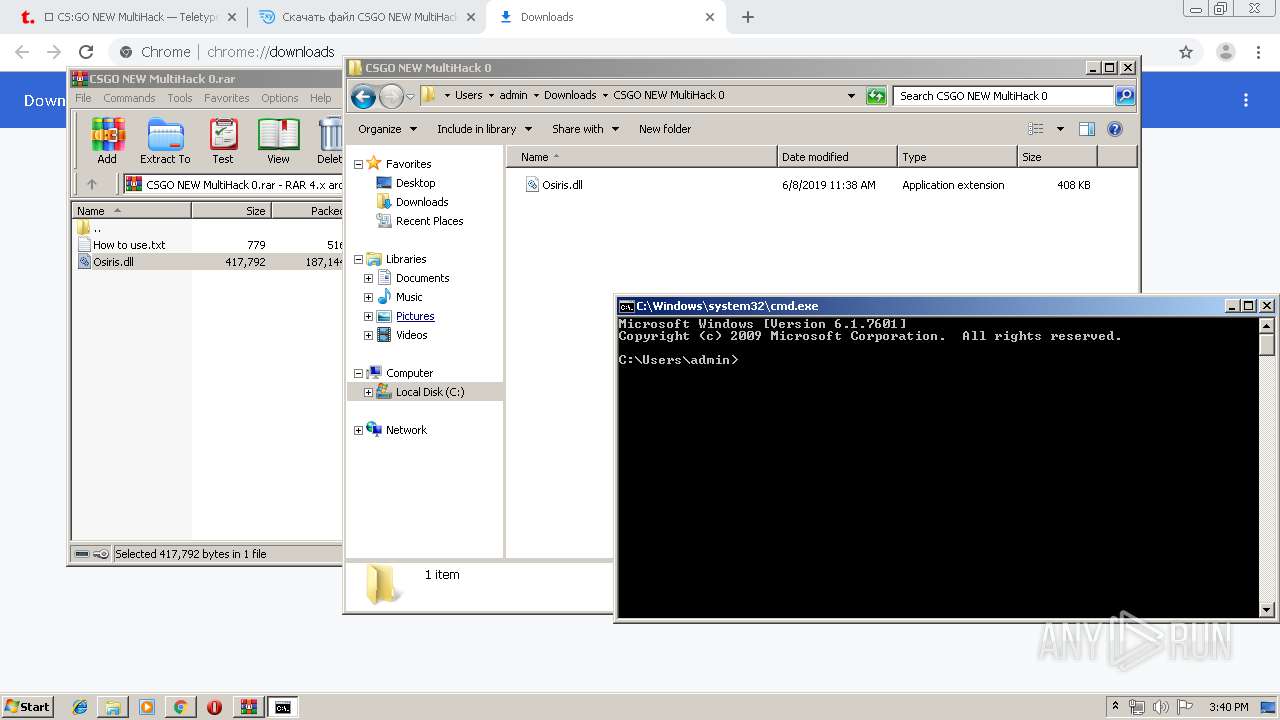
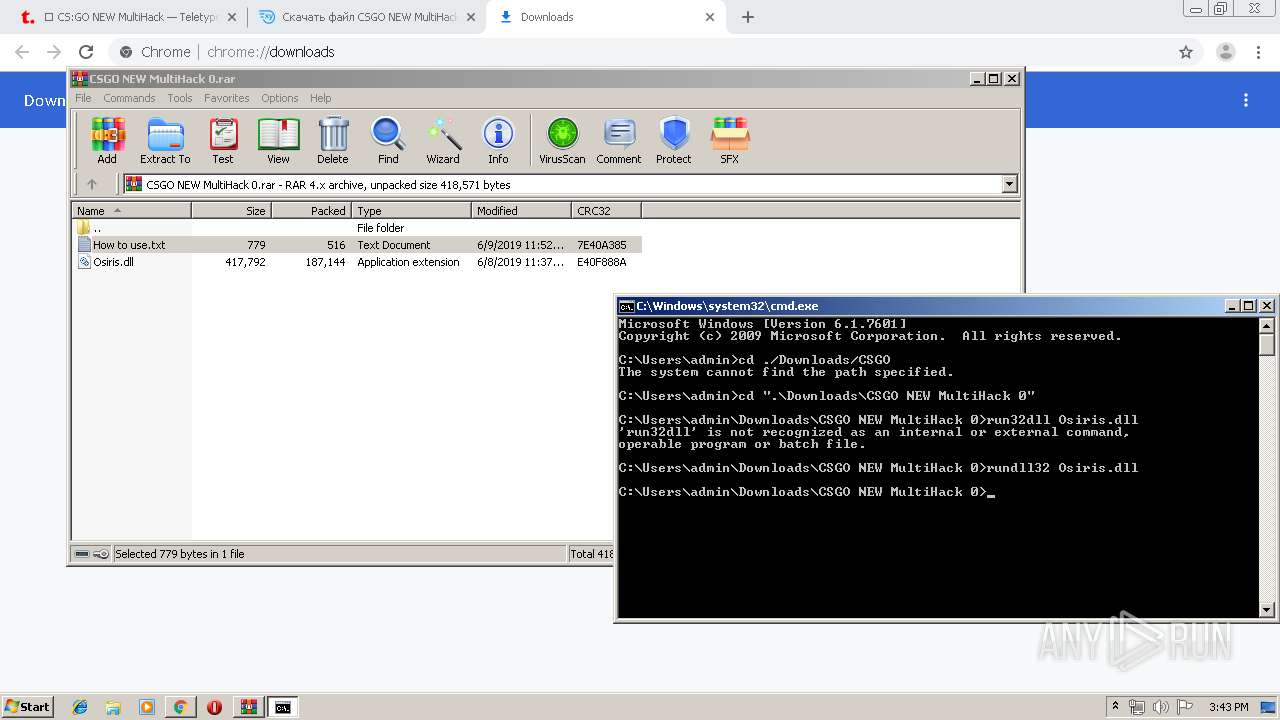
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2612)
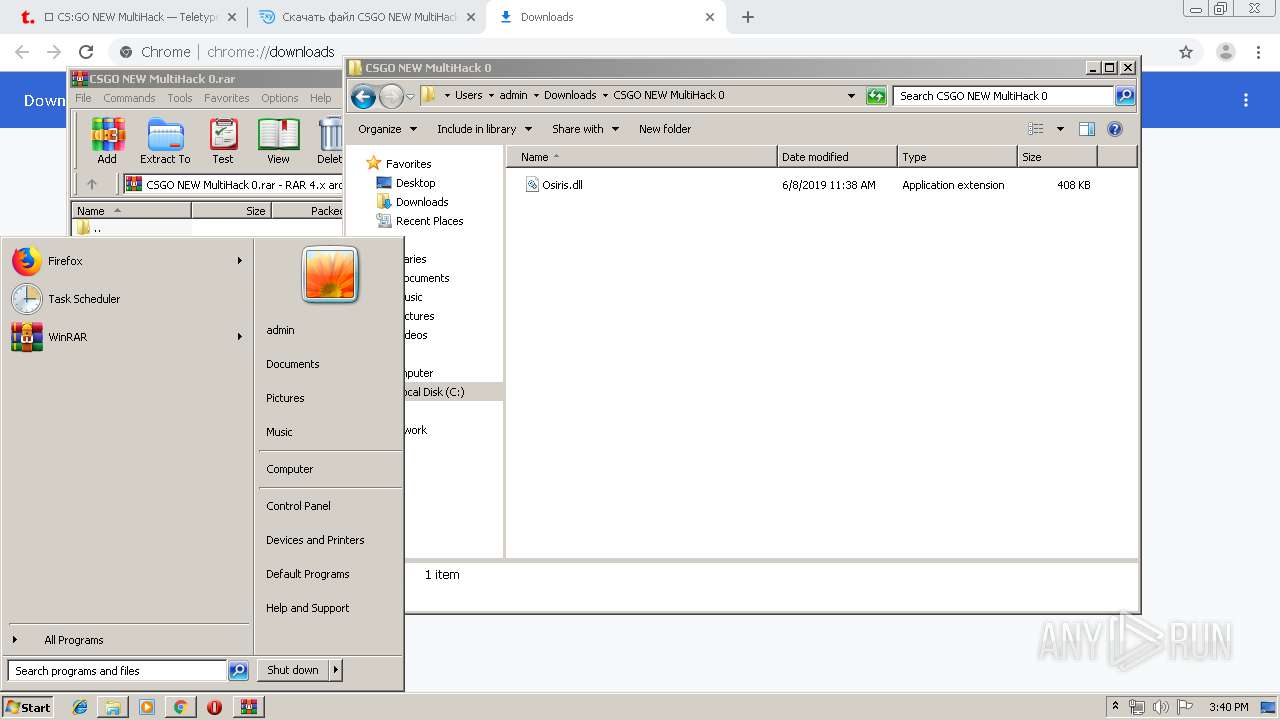
Starts CMD.EXE for commands execution
- explorer.exe (PID: 128)
INFO
Application launched itself
- chrome.exe (PID: 3016)
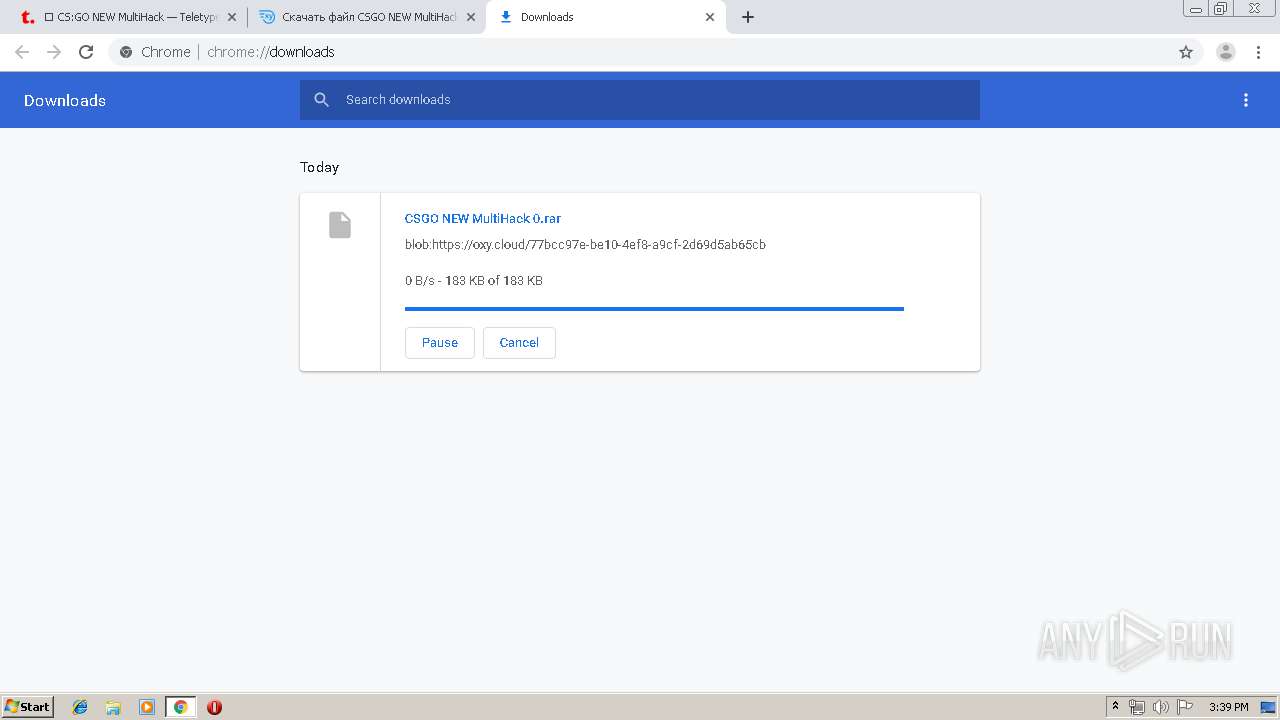
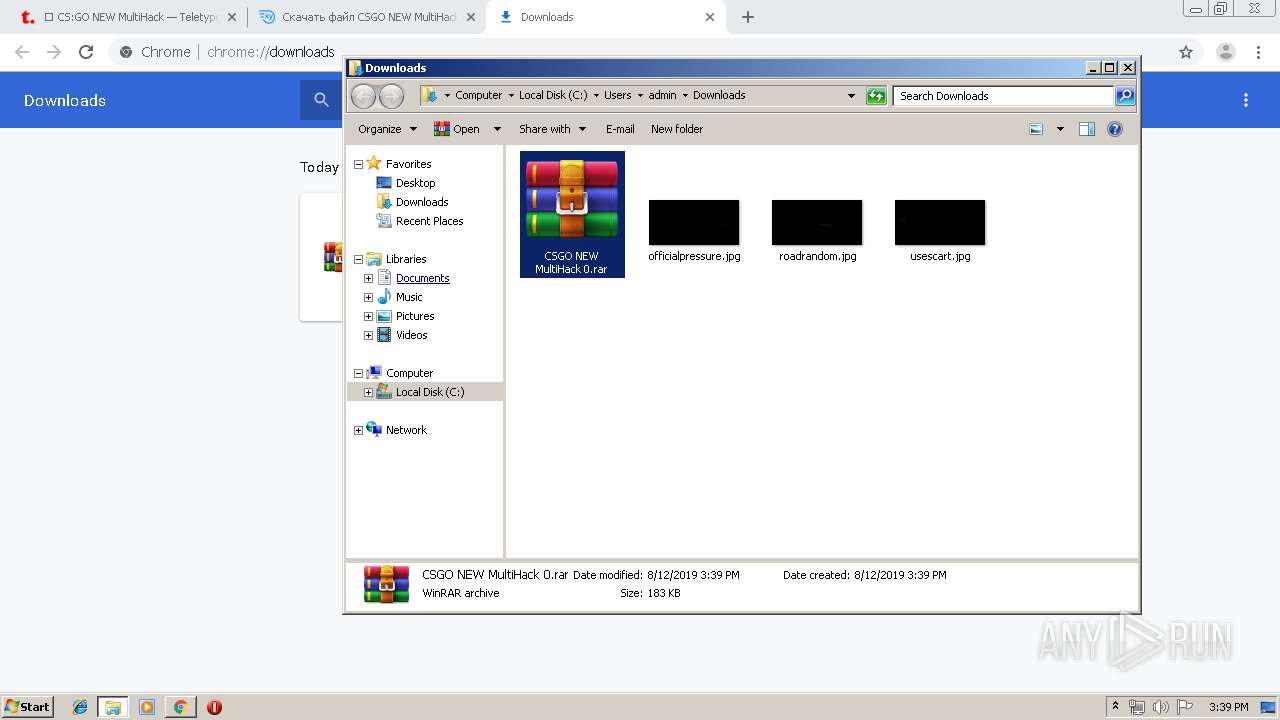
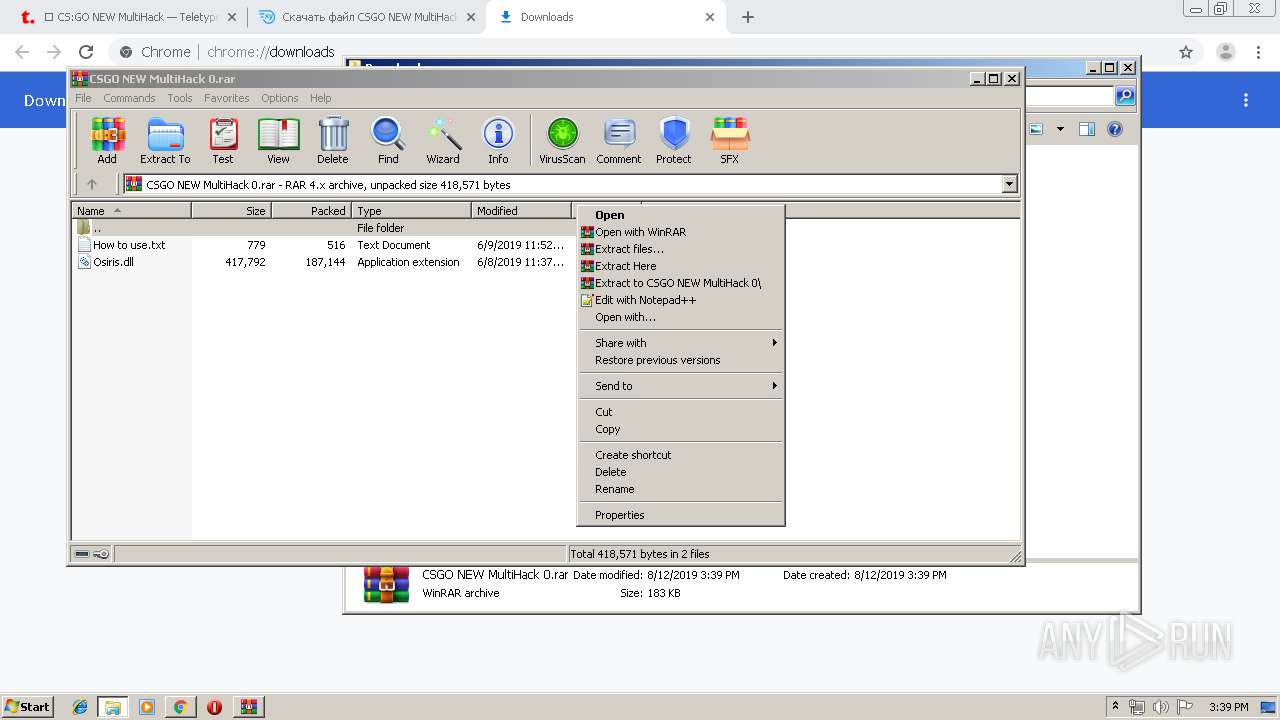
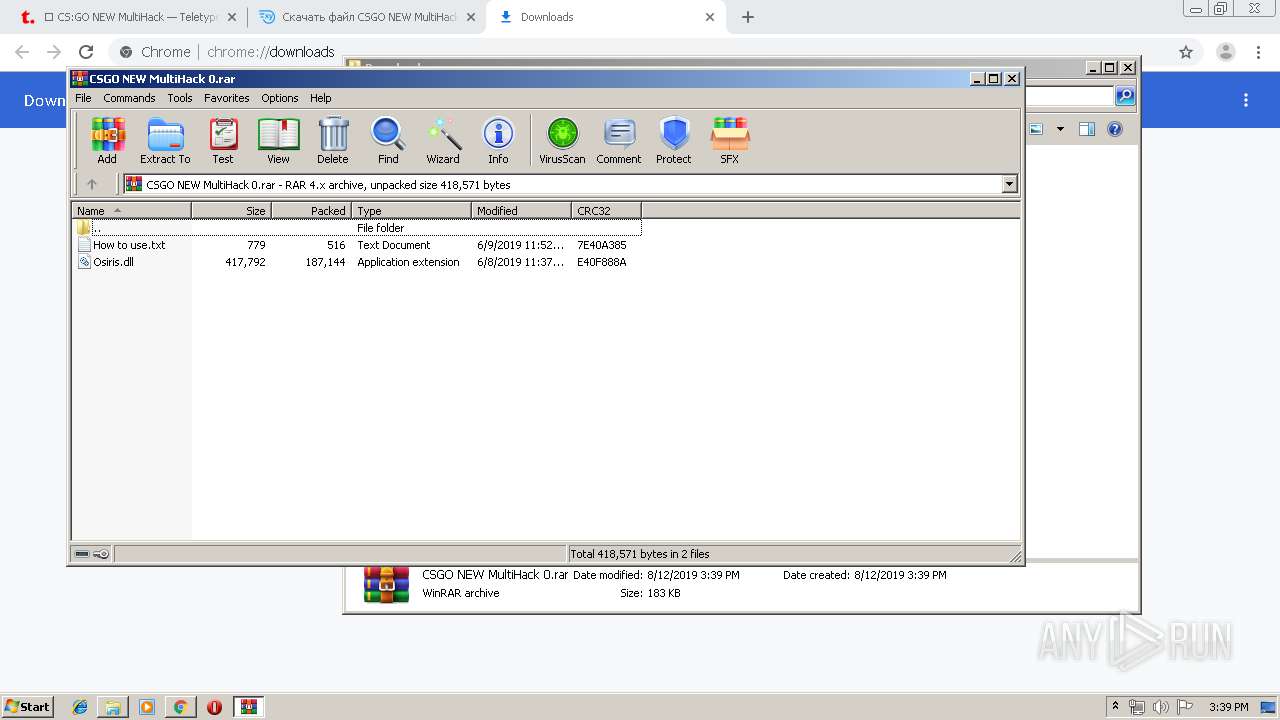
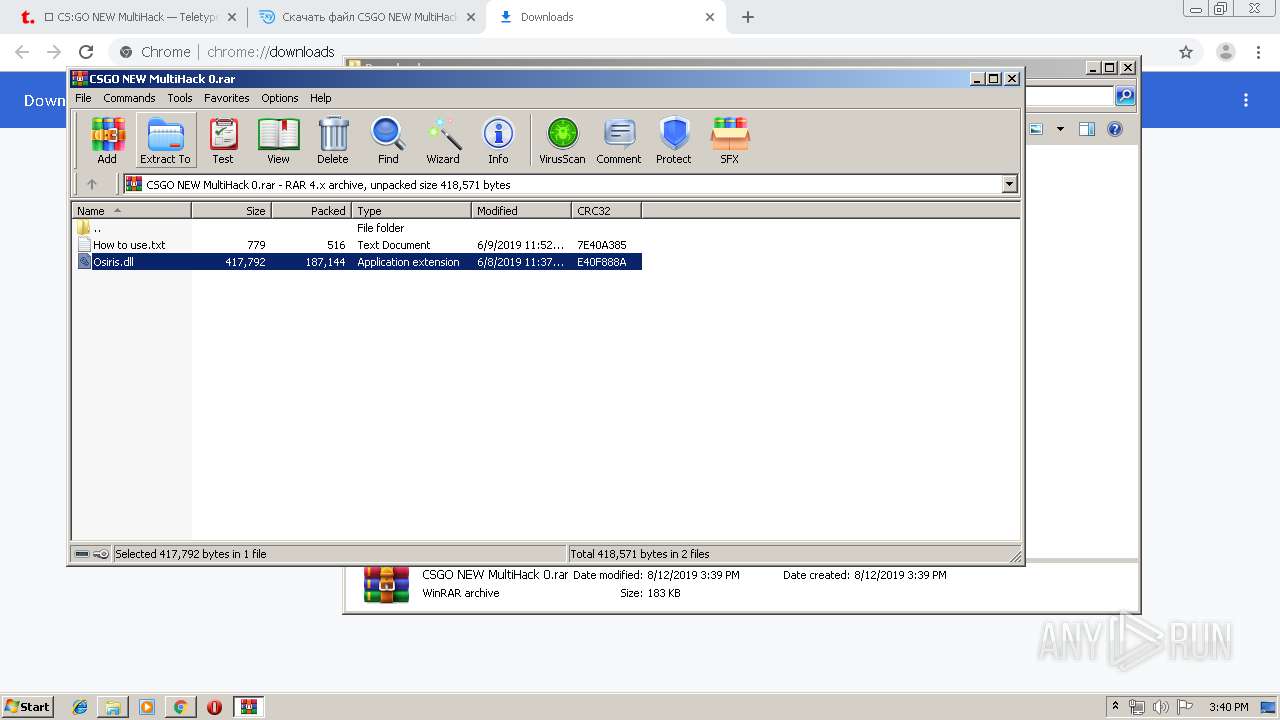
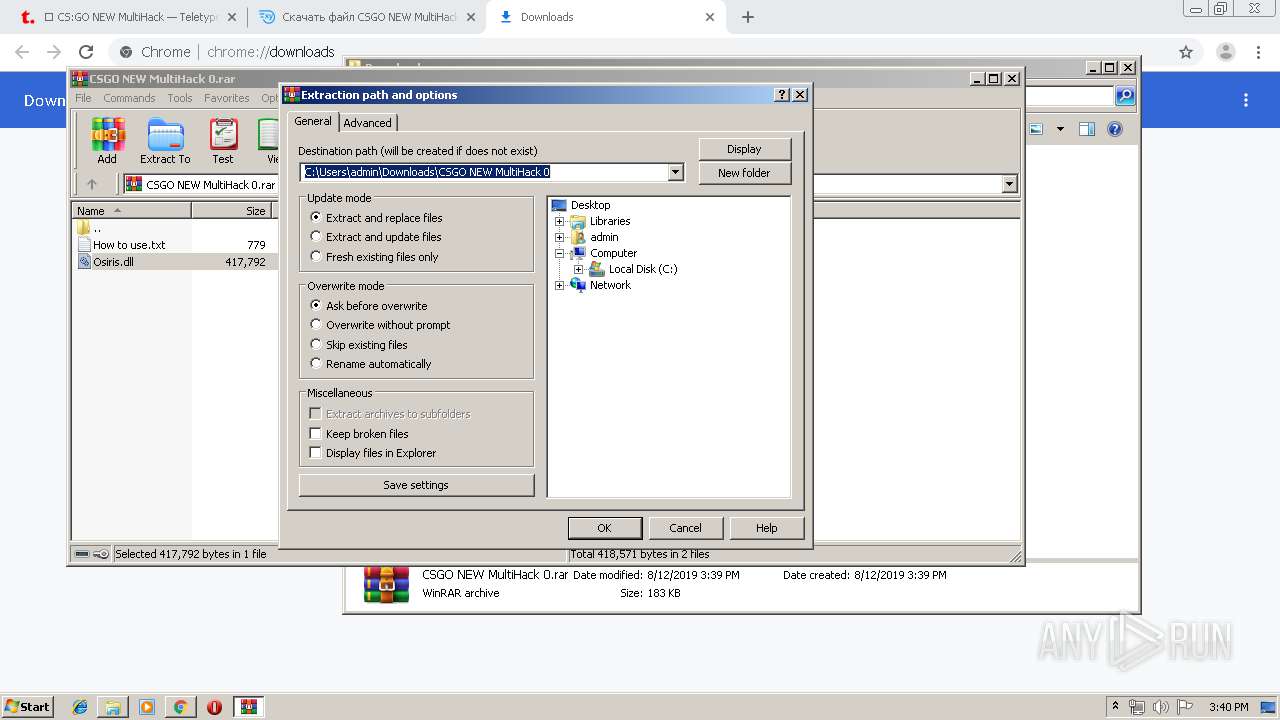
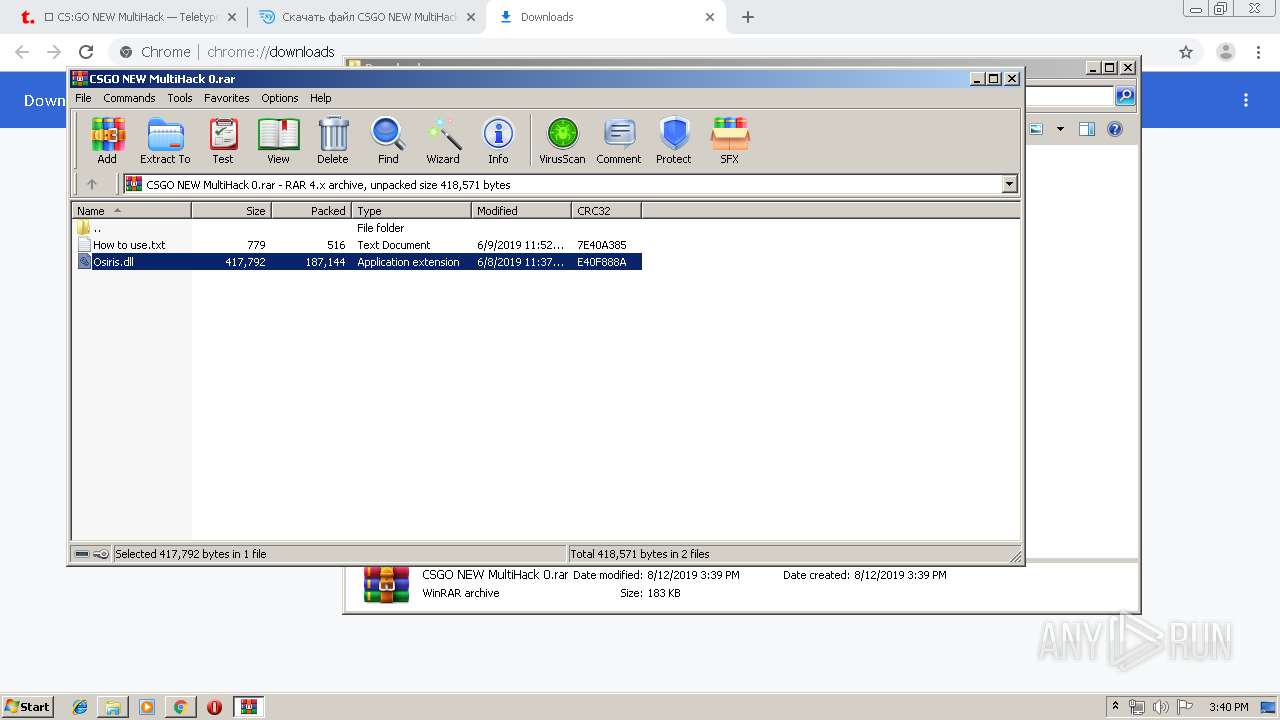
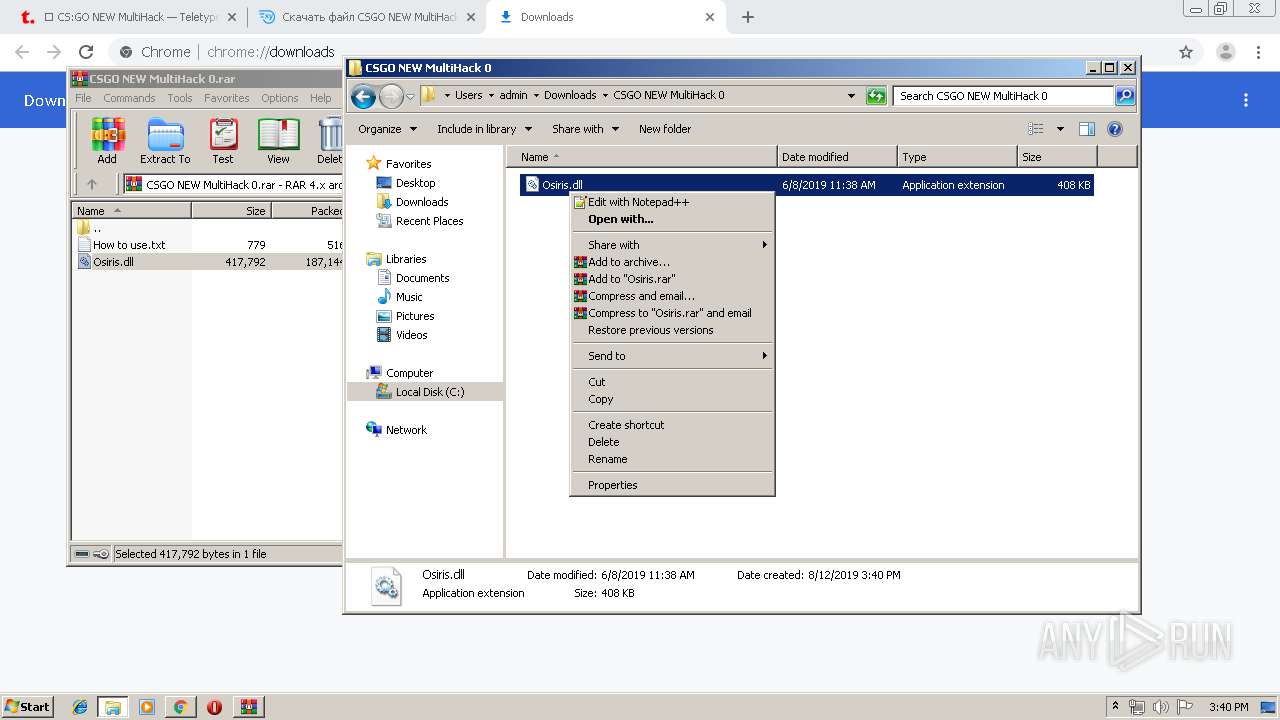
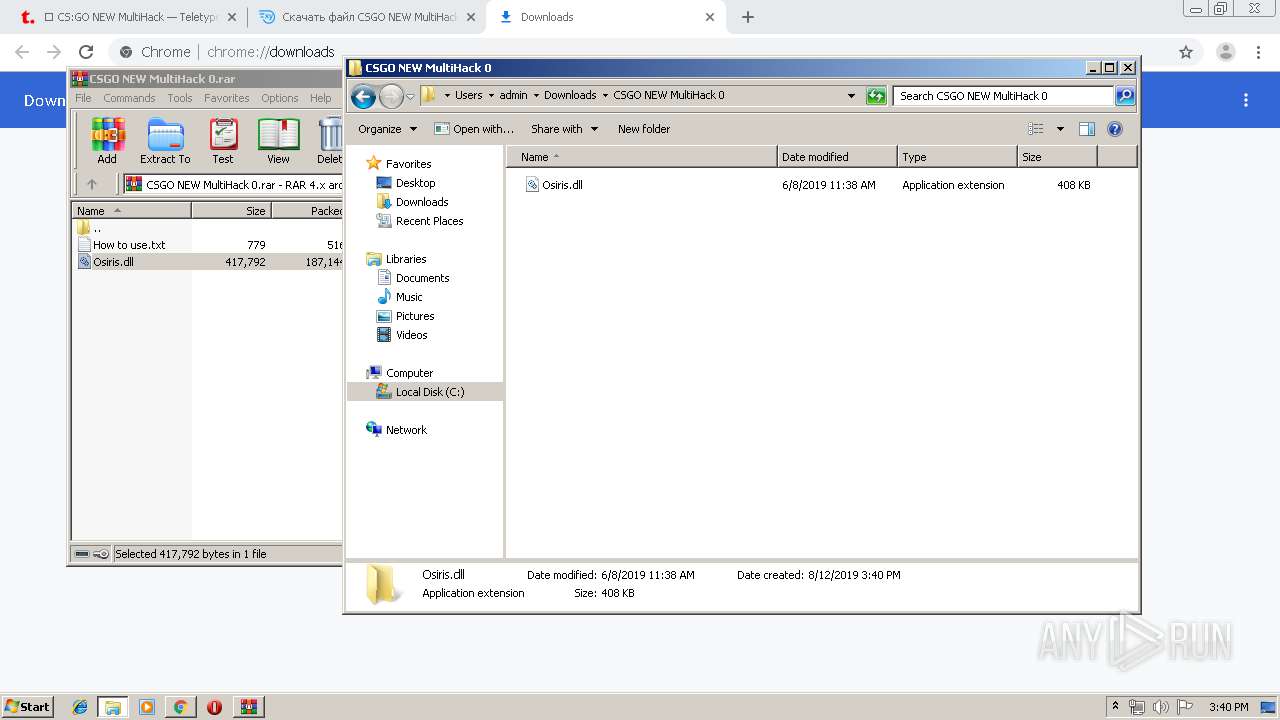
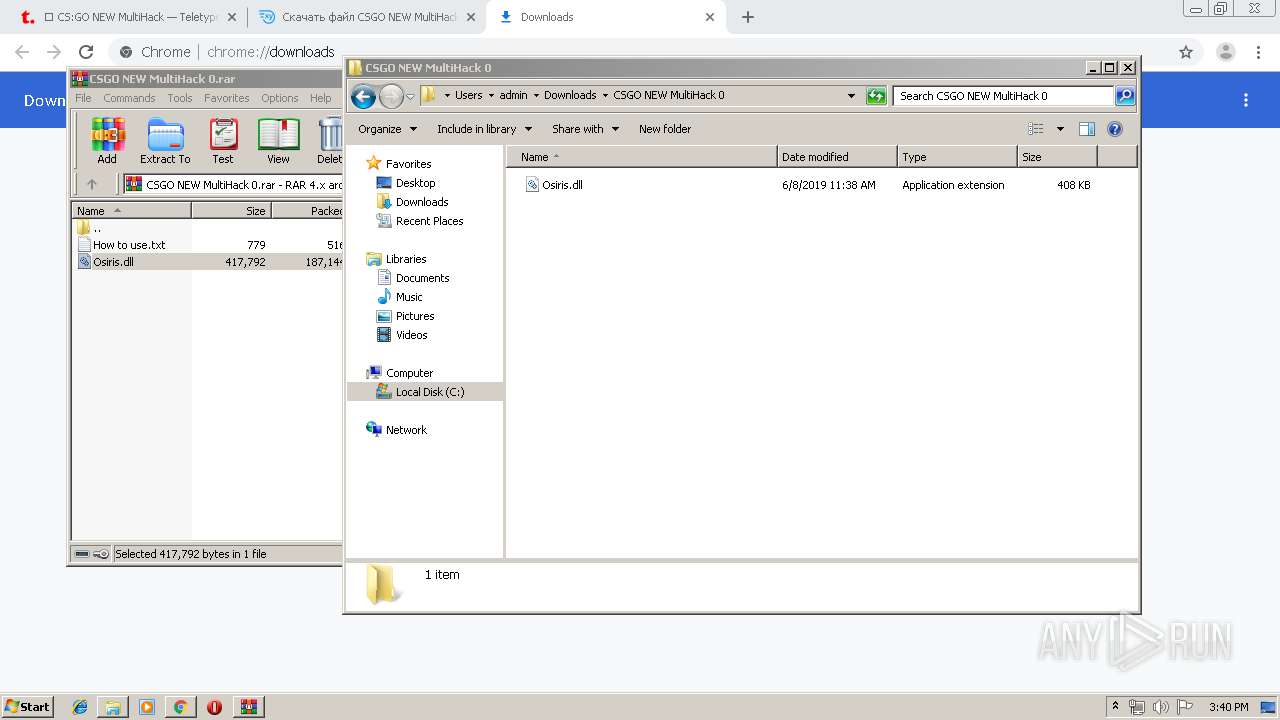
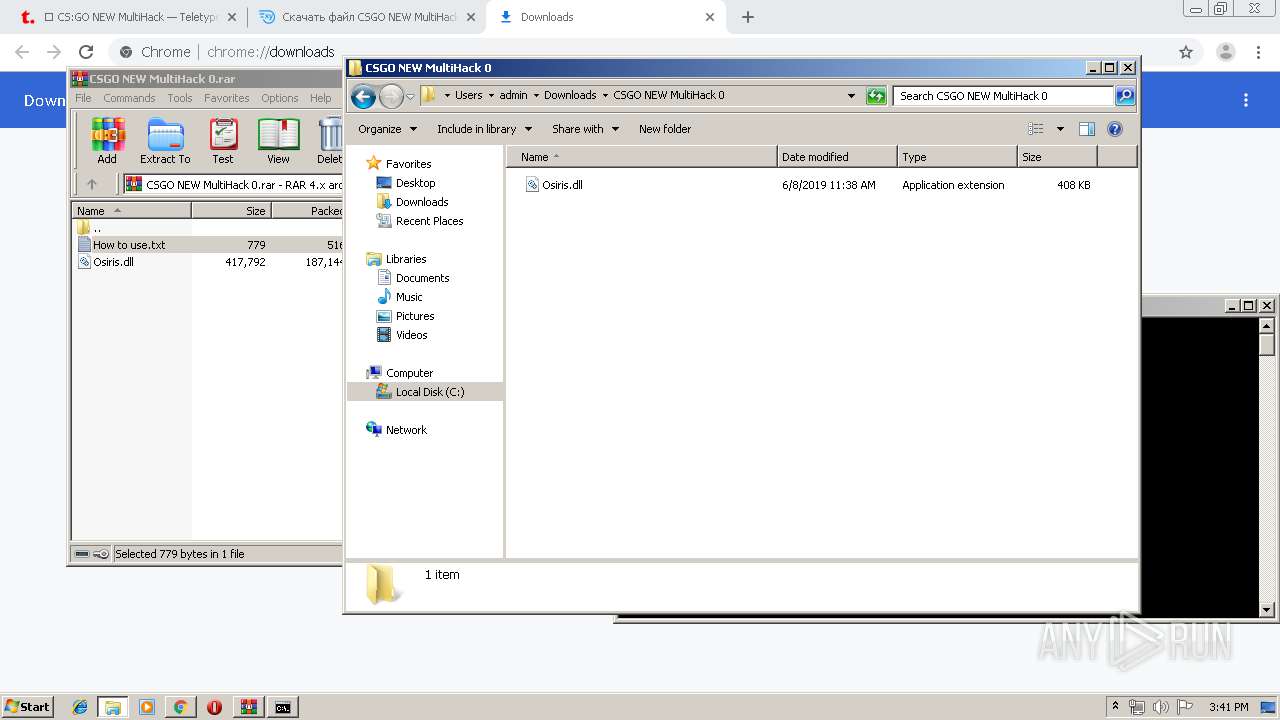
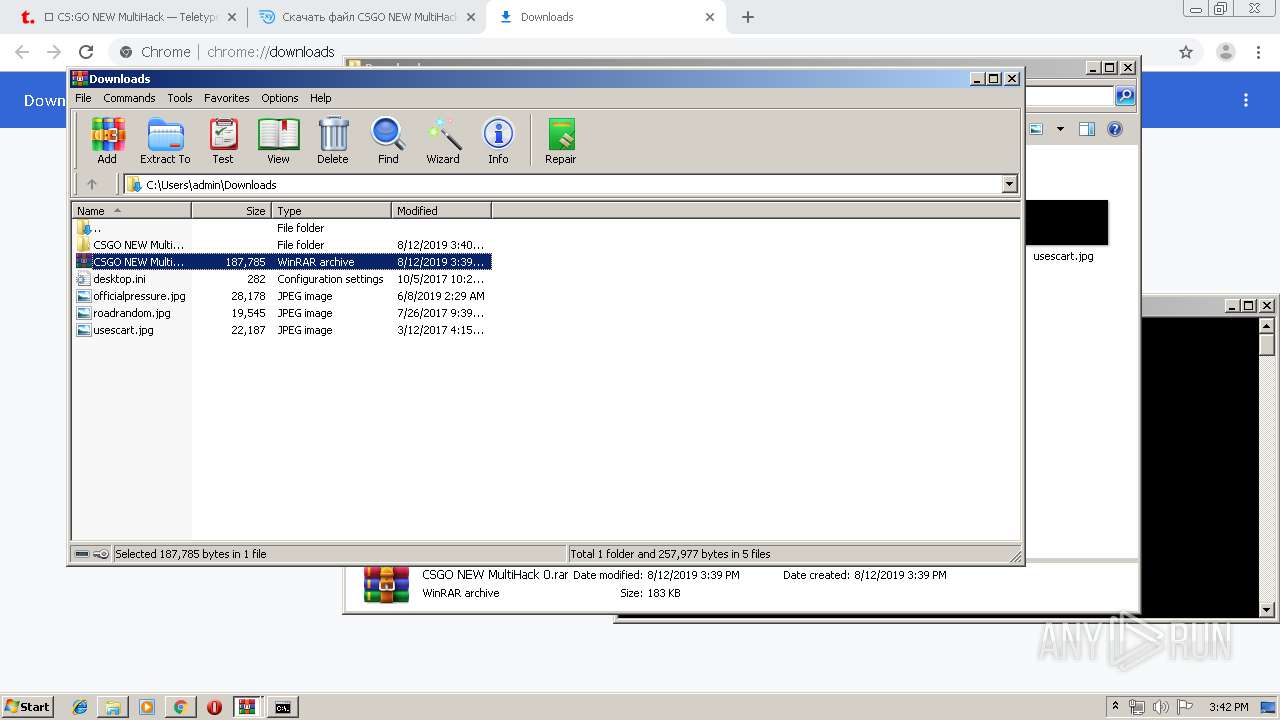
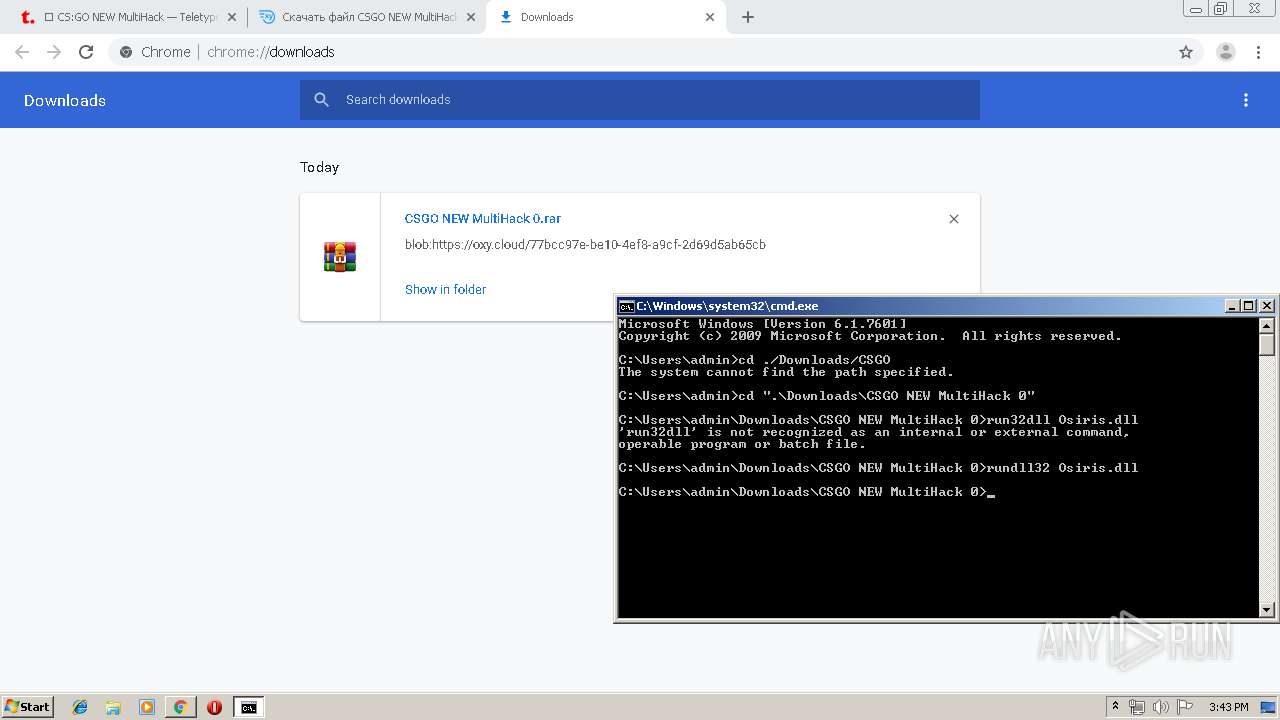
Manual execution by user
- WinRAR.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
47
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe13_ Global\UsGthrCtrlFltPipeMssGthrPipe13 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14392604218662011632 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8286588590027378277 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14008767989332398435 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=916 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4167019223094353510 --mojo-platform-channel-handle=1896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12379037829015354710 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1946406701209597582 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9213235211781821083 --mojo-platform-channel-handle=5416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 328
Read events
2 681
Write events
638
Delete events
9
Modification events
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3016-13210094334712375 |
Value: 259 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3016-13210094334712375 |
Value: 259 | |||
Executable files
2
Suspicious files
147
Text files
238
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\24e8a929-4bbc-41d5-9069-326ca3a7437c.tmp | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF36d4dd.TMP | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF36d49f.TMP | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF36d49f.TMP | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF36d51c.TMP | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
96
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
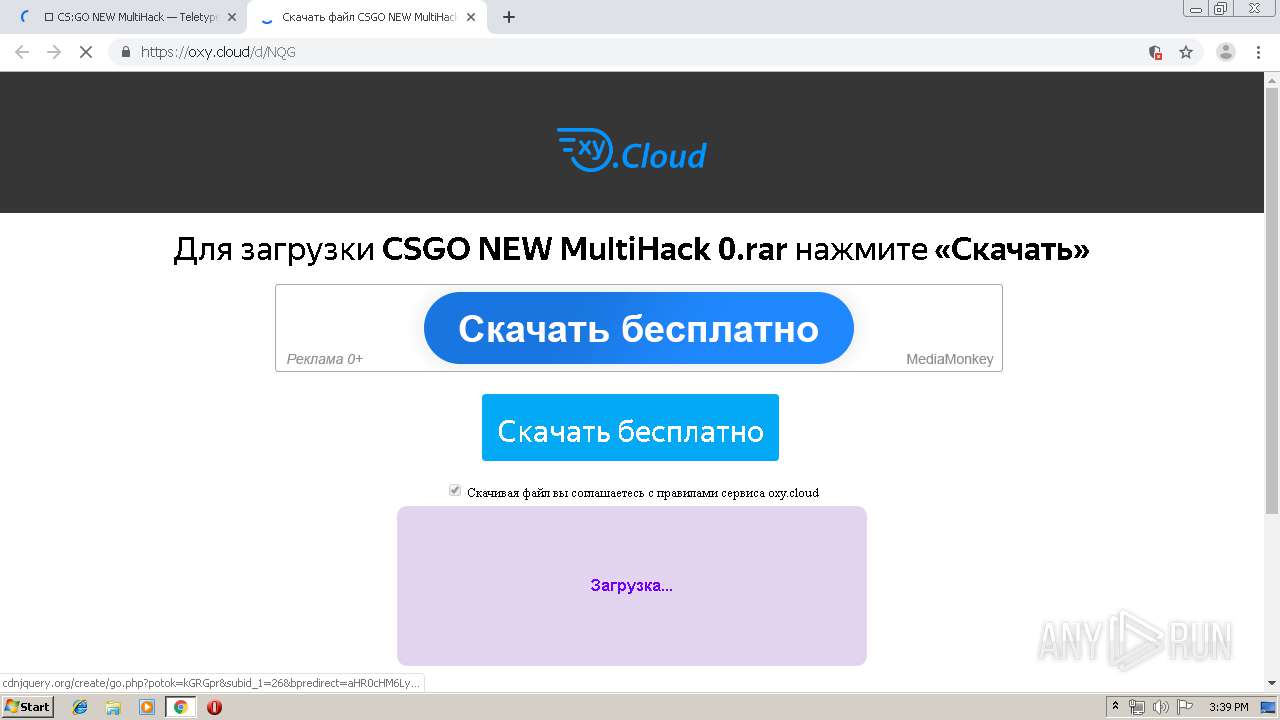
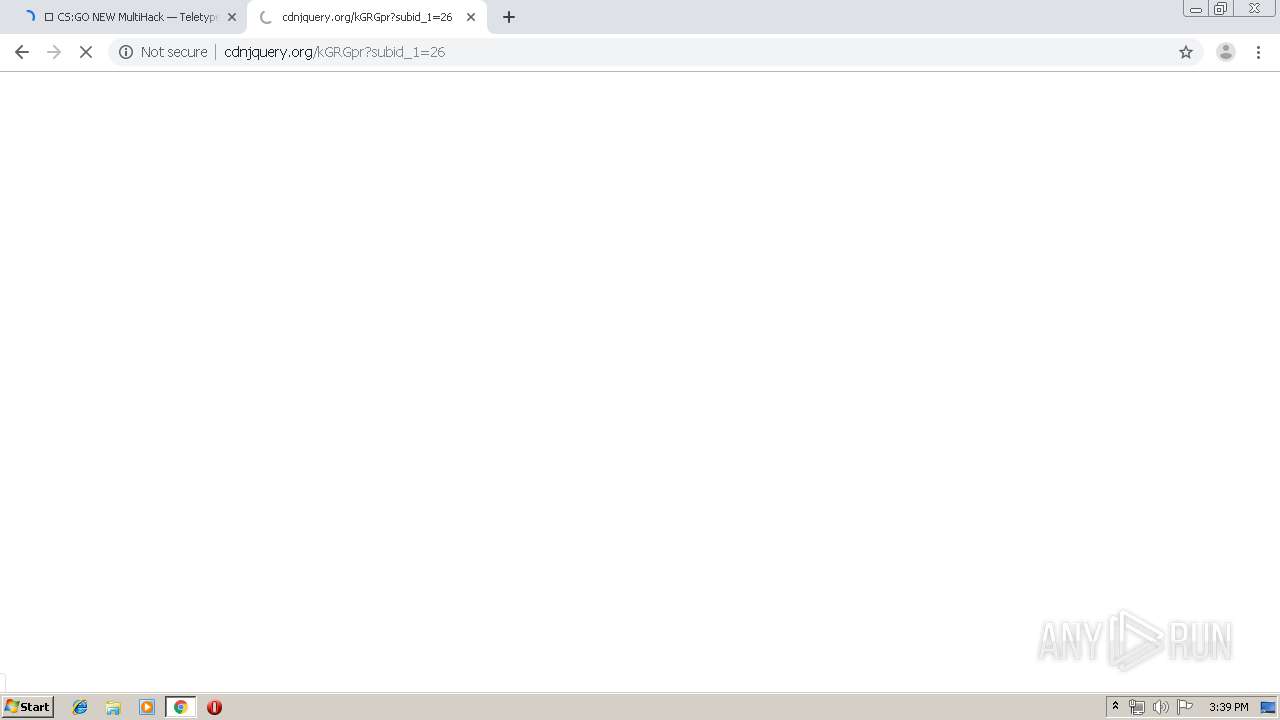
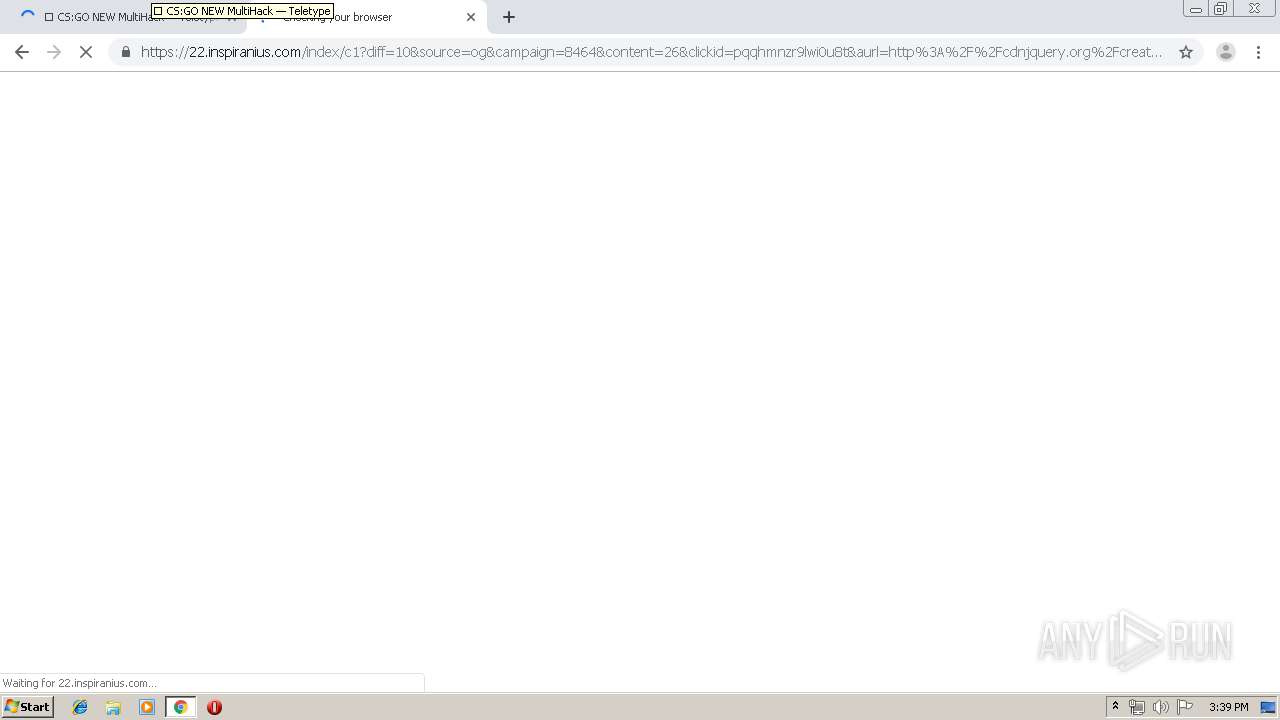
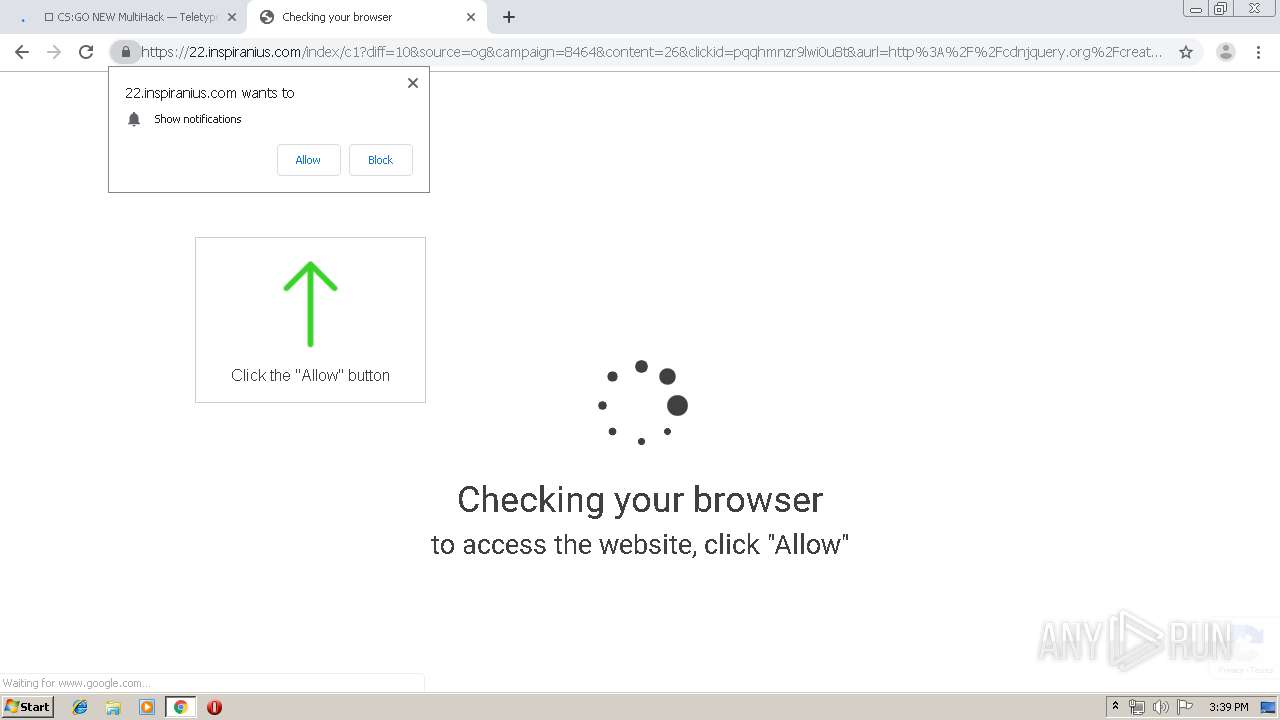
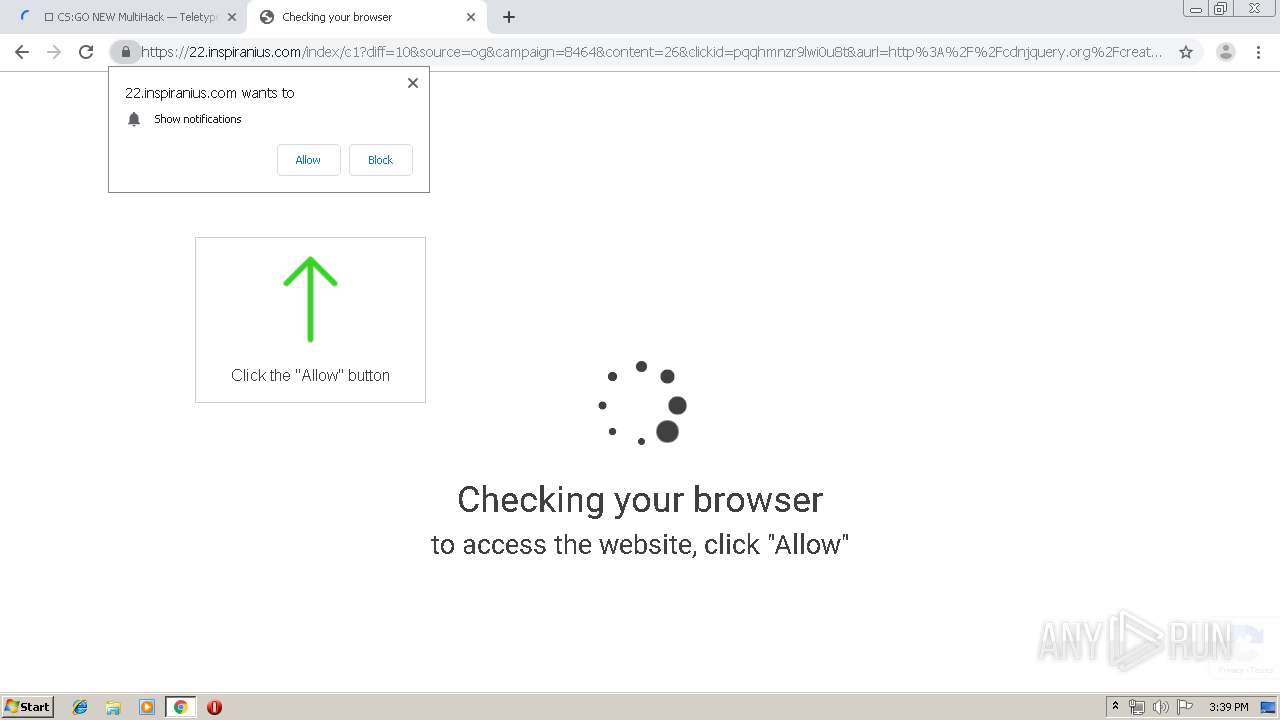
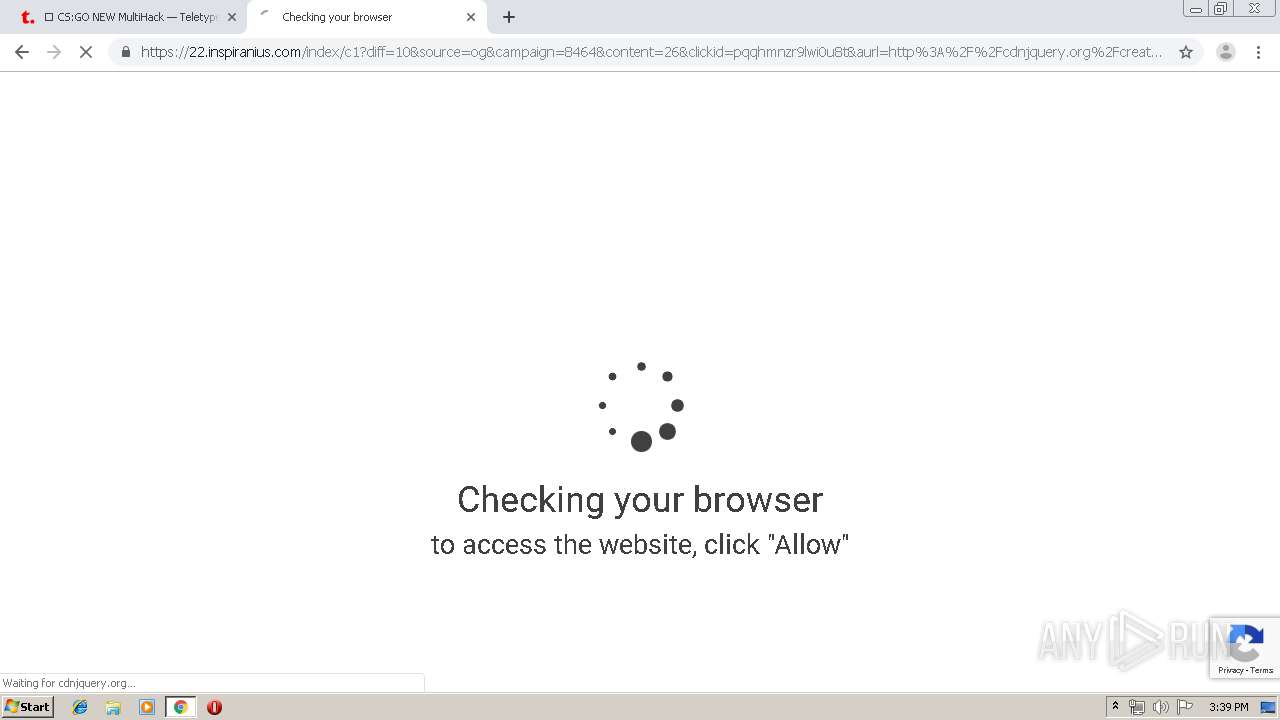
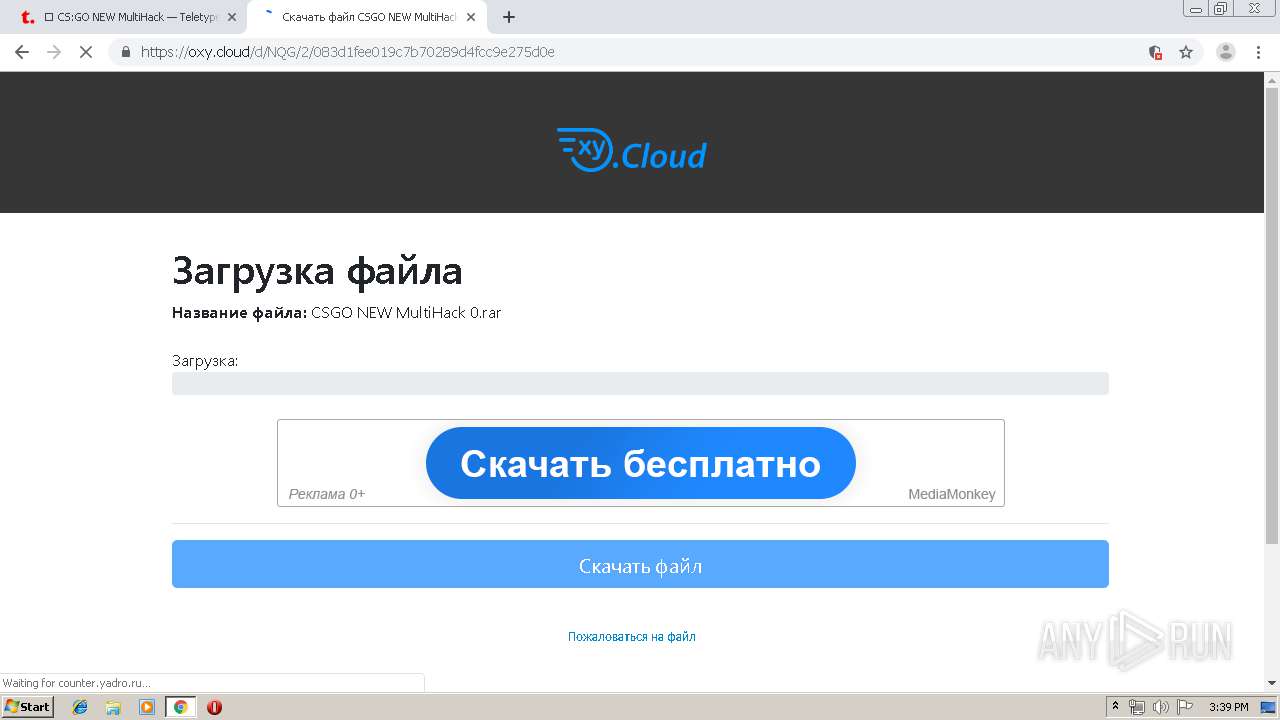
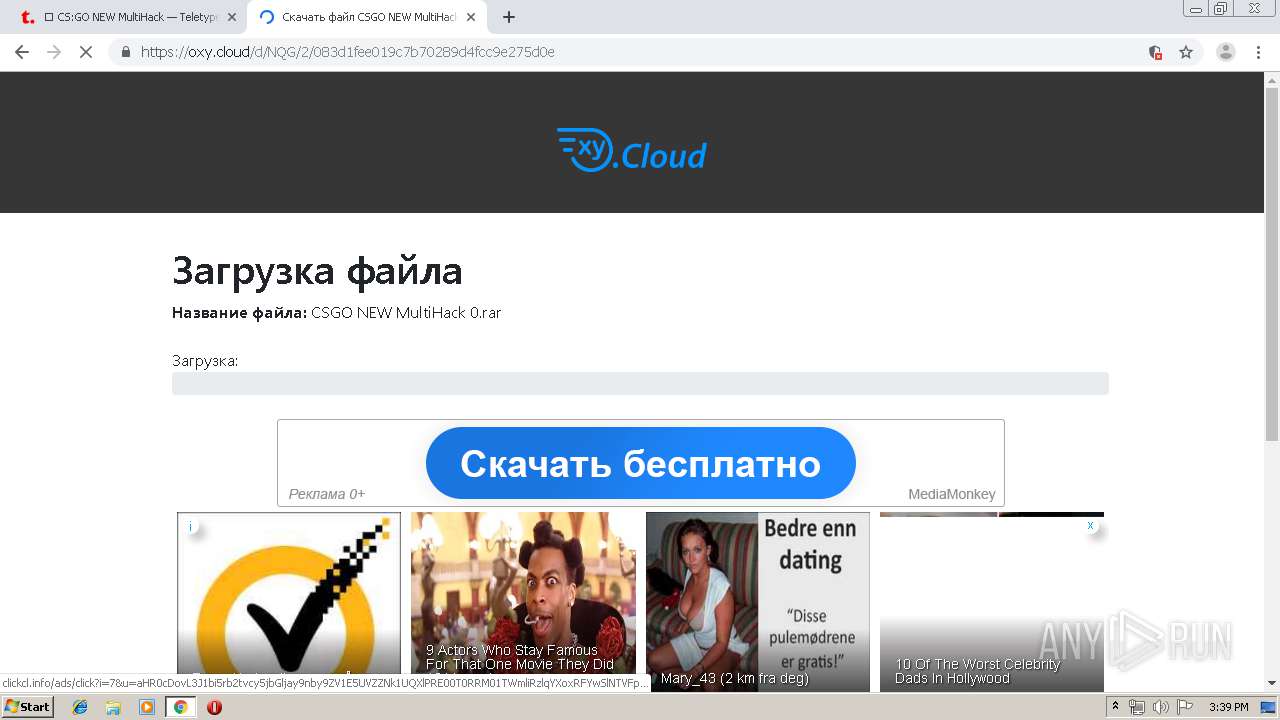
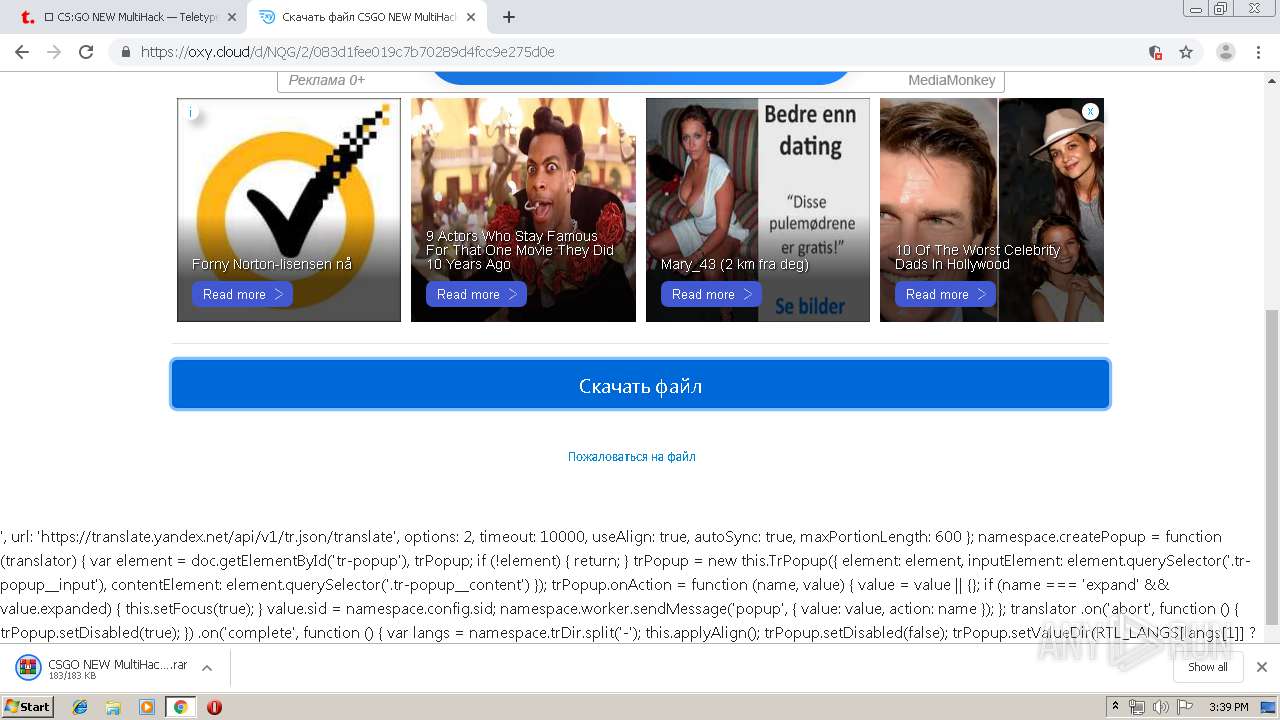
3244 | chrome.exe | GET | 302 | 104.28.3.72:80 | http://cdnjquery.org/create/go.php?potok=kGRGpr&subid_1=26&bpredirect=aHR0cHM6Ly9veHkuY2xvdWQvZC9OUUcvMi8wODNkMWZlZTAxOWM3YjcwMjg5ZDRmY2M5ZTI3NWQwZQ%3D%3D | US | — | — | shared |
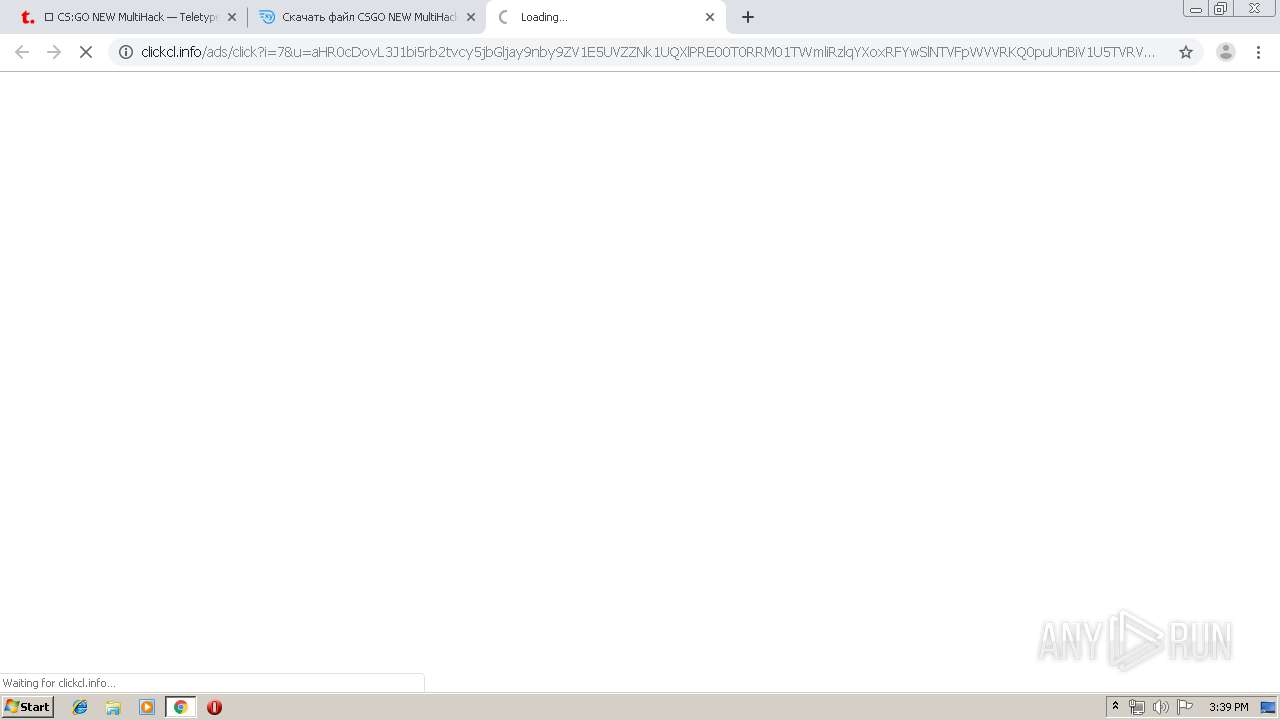
3244 | chrome.exe | GET | — | 104.27.170.15:80 | http://clickcl.info/ads/click?i=7&u=aHR0cDovL3J1bi5rb2tvcy5jbGljay9nby9ZV1E5UVZZNk1UQXlPRE00T0RRM01TWmliRzlqYXoxRFYwSlNTVFpWVVRKQ0puUnBiV1U5TVRVMk5UWXlNRGMyTlNaMGVYQmxQVlJGUVZORlVnLzQzNWNjODBlY2YwZmYxYzBlODE4NWI2Y2Q5ZTgyY2YyY2M3MTEzNmE=&n=kokos&b=AV:1028388471&p=0.1918280136&c=rub&s=0.8&f=0.85 | US | — | — | shared |
3244 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEHbYt4bR81JP7pU%2BcUA9mdU%3D | US | der | 471 b | whitelisted |
3244 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3244 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQCA9WBtOhYrFDrcEvvowgZv | US | der | 314 b | whitelisted |
3244 | chrome.exe | GET | 200 | 173.194.150.220:80 | http://r6---sn-5goeen7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.22.104&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1565620705&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3244 | chrome.exe | GET | 404 | 104.28.3.72:80 | http://cdnjquery.org/favicon.ico | US | html | 167 b | shared |
3244 | chrome.exe | GET | 200 | 104.28.3.72:80 | http://cdnjquery.org/kGRGpr?subid_1=26 | US | html | 321 b | shared |
3244 | chrome.exe | GET | 302 | 104.28.3.72:80 | http://cdnjquery.org/create/g.php | US | compressed | 167 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
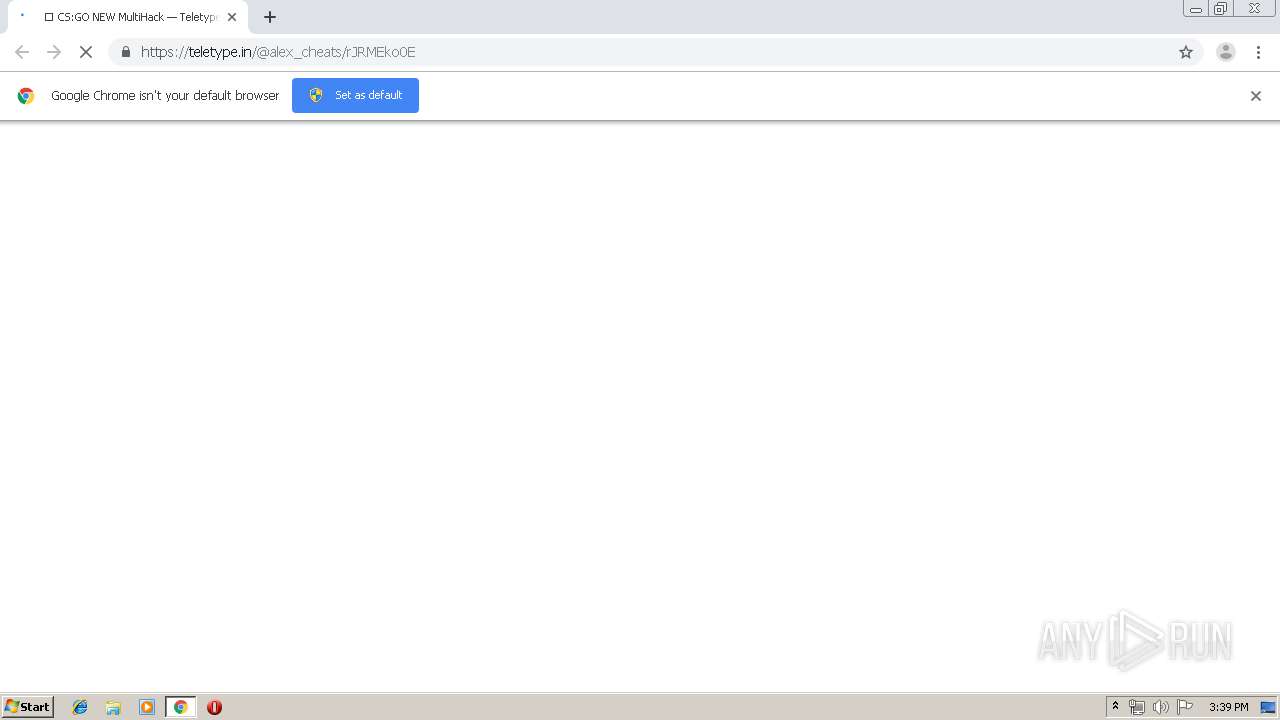
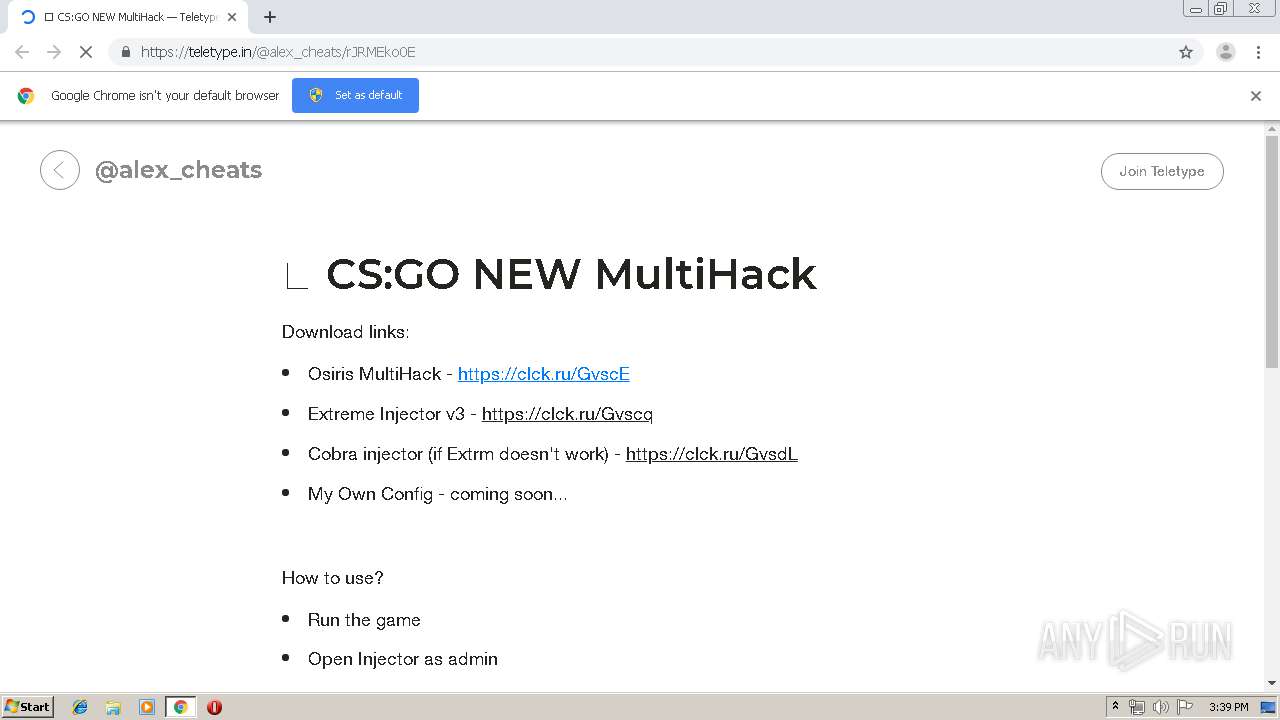
3244 | chrome.exe | 213.180.204.221:443 | clck.ru | YANDEX LLC | RU | whitelisted |
3244 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 87.250.250.232:443 | sba.yandex.net | YANDEX LLC | RU | whitelisted |
3244 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 172.217.23.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 104.16.35.63:443 | cdn.onesignal.com | Cloudflare Inc | US | shared |
3244 | chrome.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
3244 | chrome.exe | 172.217.22.104:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 104.244.42.8:443 | syndication.twitter.com | Twitter Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clck.ru |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sba.yandex.net |
| whitelisted |
teletype.in |
| whitelisted |
www.google.com |
| malicious |
www.youtube.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
connect.facebook.net |
| whitelisted |
apis.google.com |
| whitelisted |