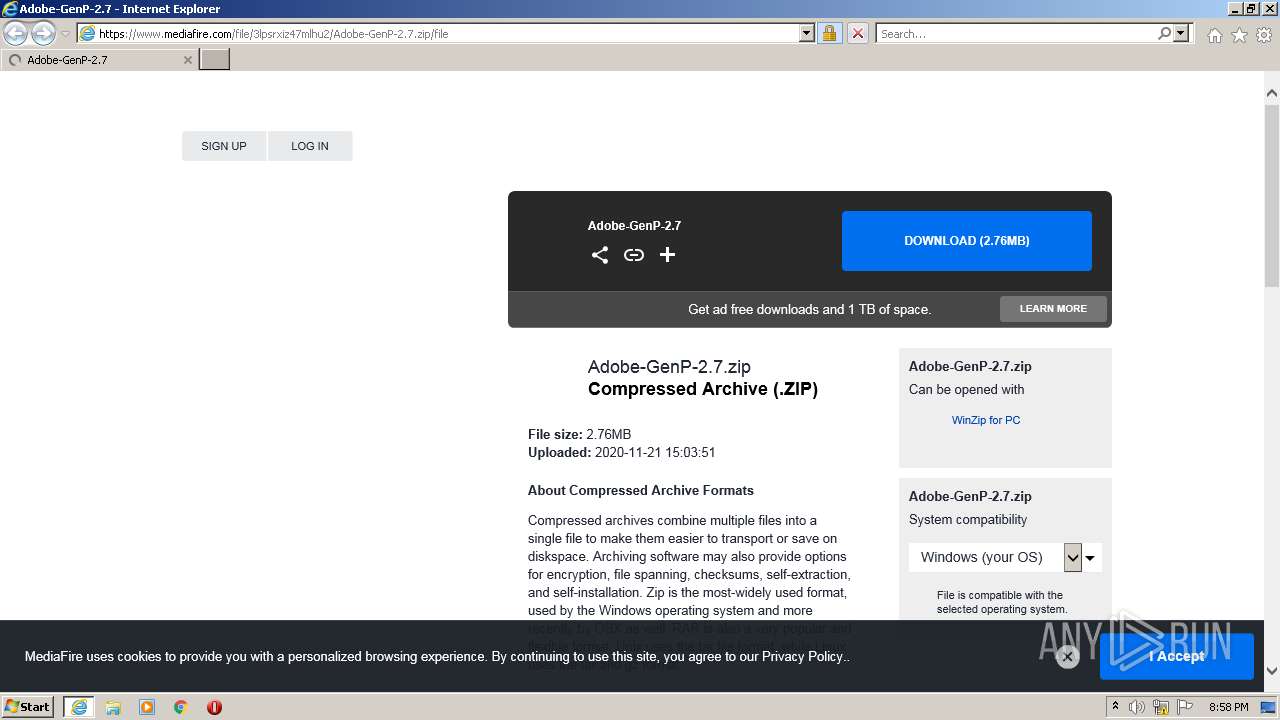
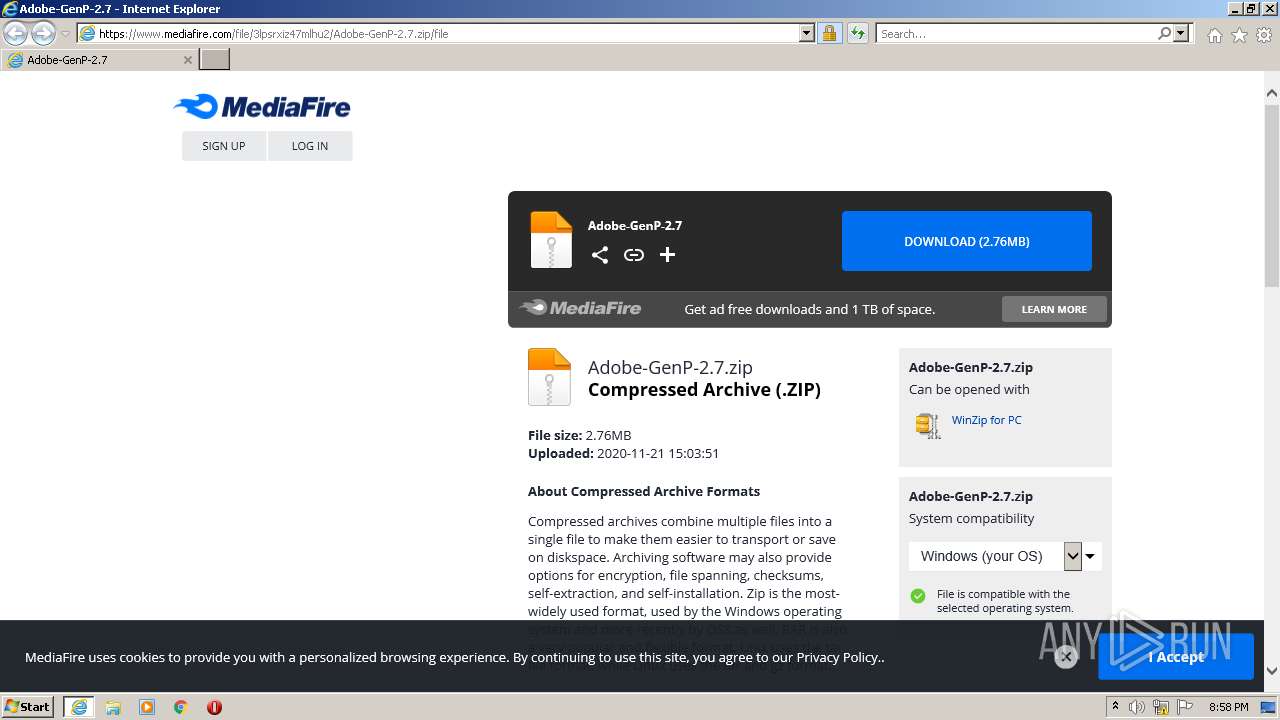
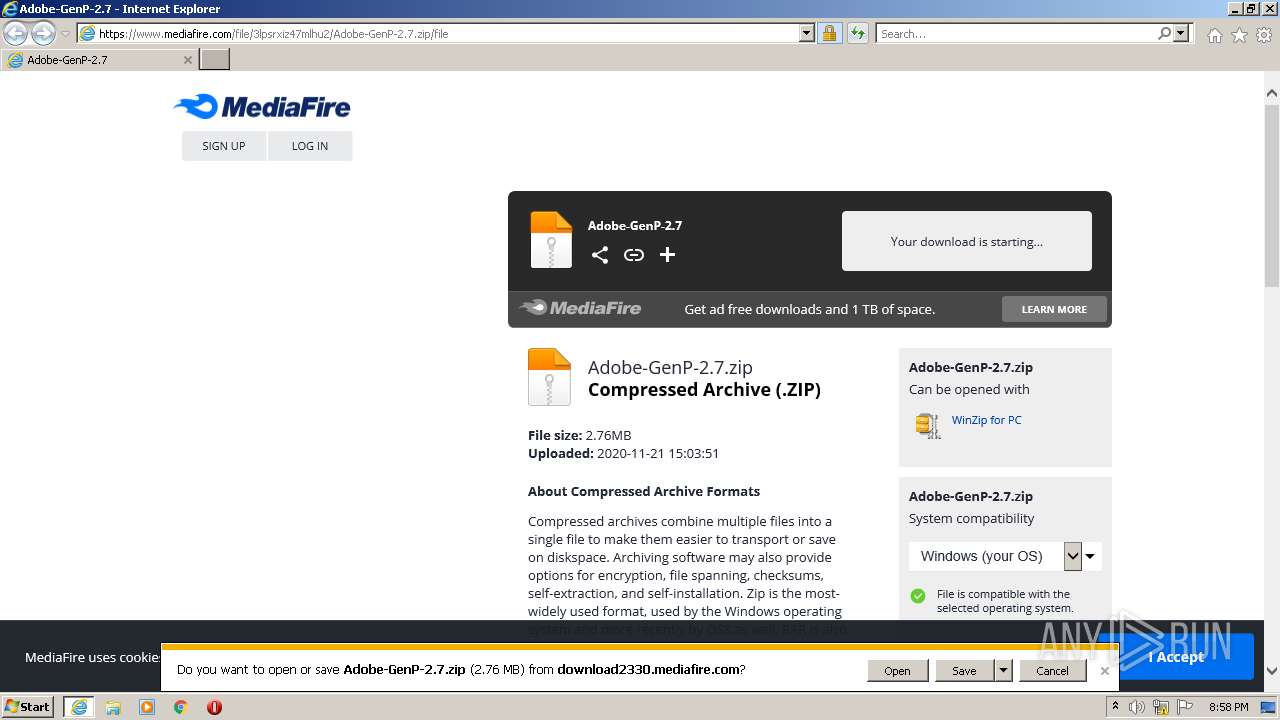
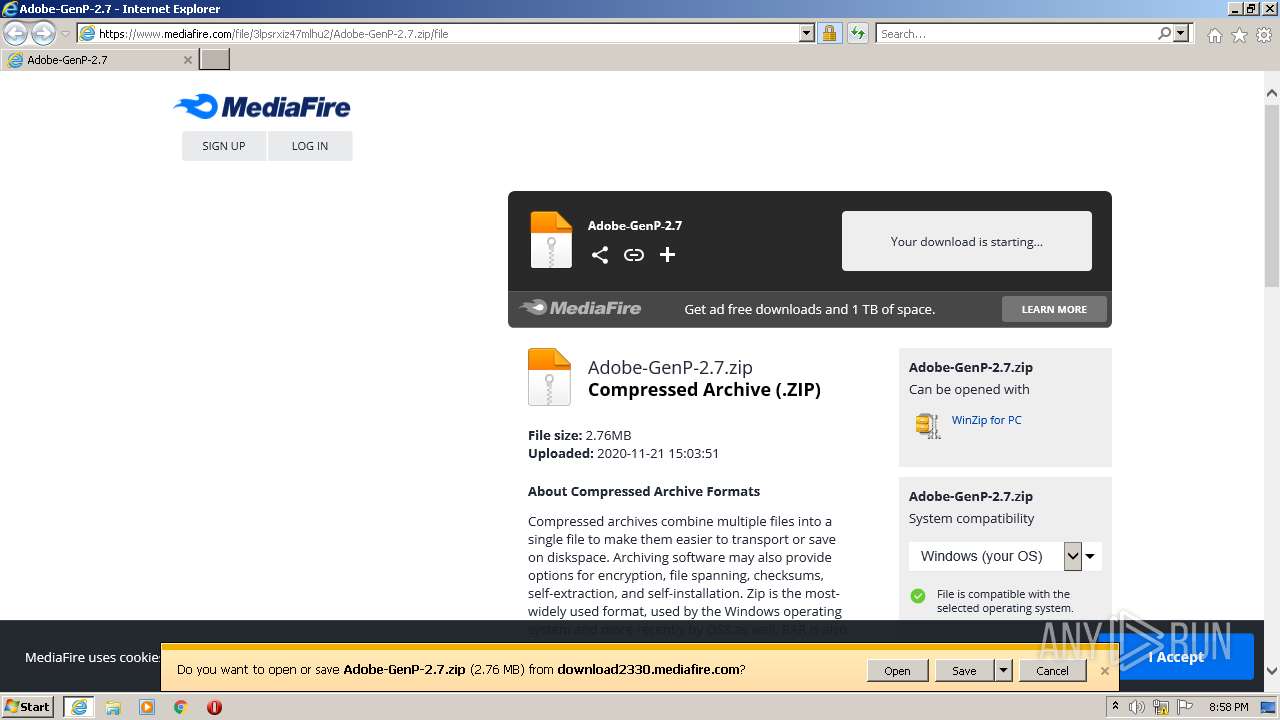
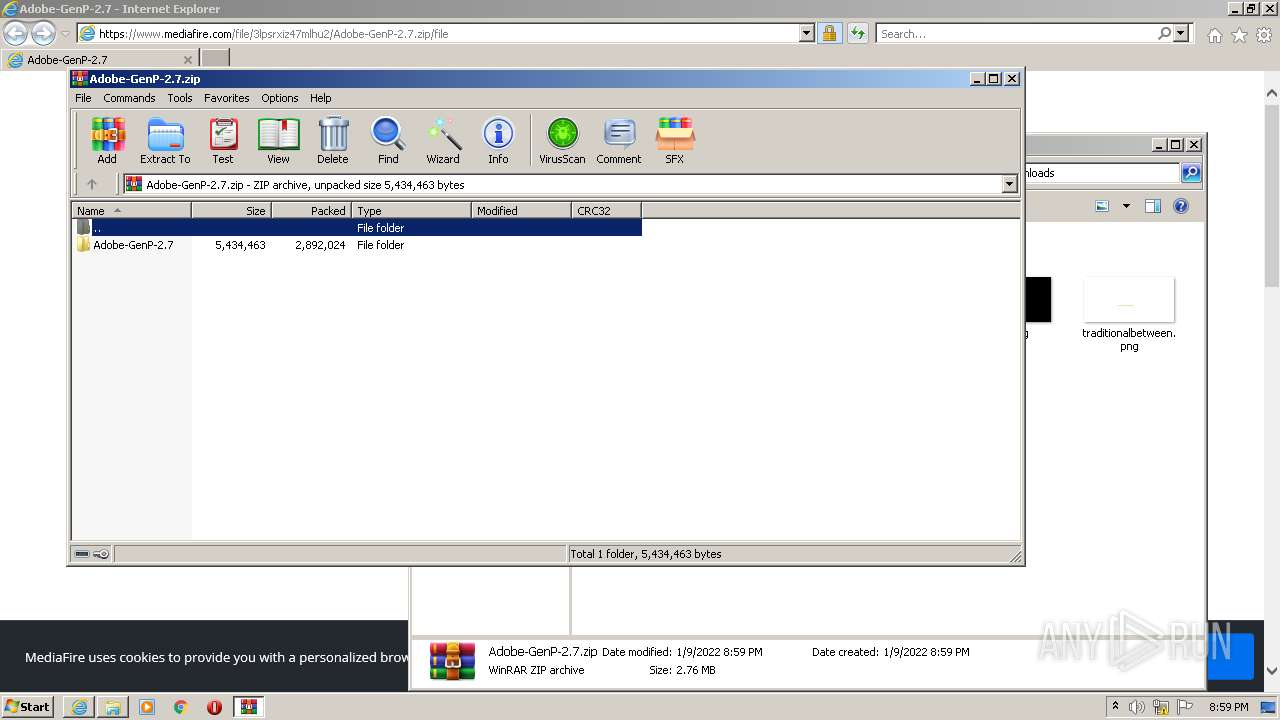
| URL: | https://www.mediafire.com/file/3lpsrxiz47mlhu2/Adobe-GenP-2.7.zip/file |
| Full analysis: | https://app.any.run/tasks/0eb27f66-9fd3-43b8-8605-f97b1bc4d224 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2022, 20:58:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3F7B16CC2E897813179437F47934D0C1 |
| SHA1: | A9EDDBD021BE0512F721A006CEB25014E1AEF5D7 |
| SHA256: | D0BDDFE81E8F4F15F0D42EB8DE35E40197DD3D1BD528B0680CD614891A1BFBDD |
| SSDEEP: | 3:N8DSLw3eGUoWbWNMJDCutiu1qO1:2OLw3eGeWNe11 |
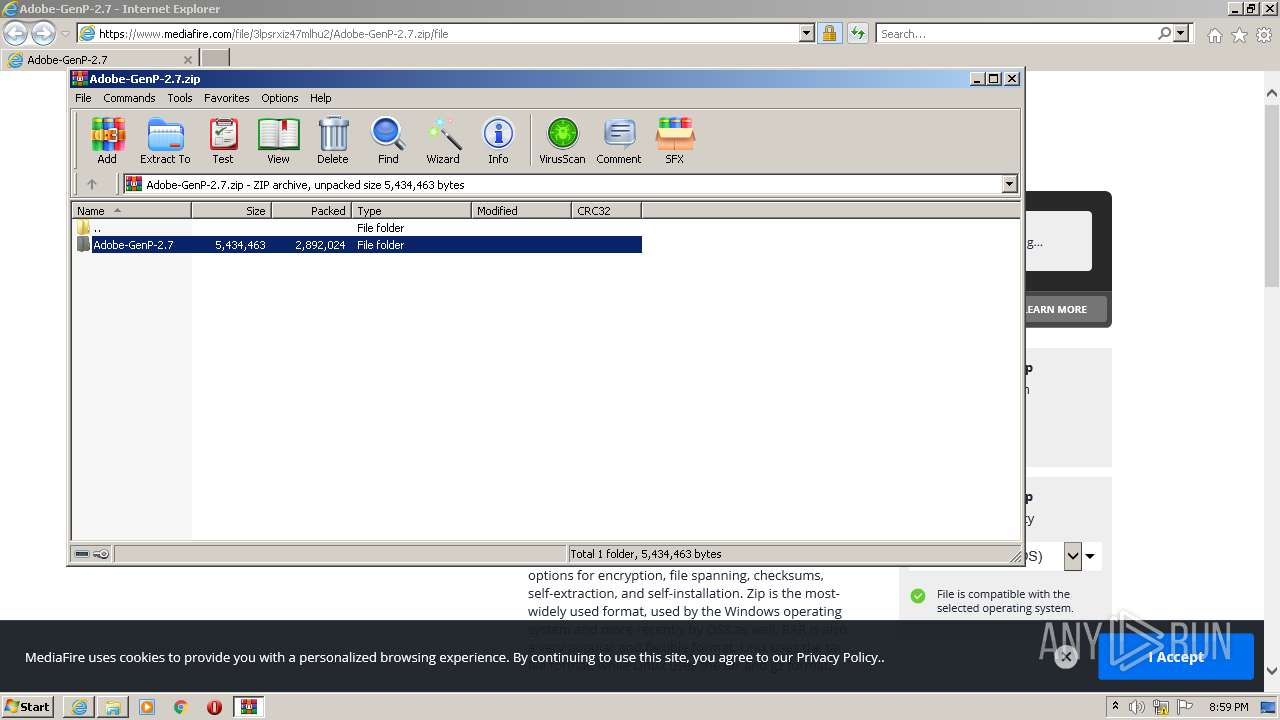
MALICIOUS
Drops executable file immediately after starts
- msdt.exe (PID: 2840)
- csc.exe (PID: 848)
- csc.exe (PID: 3820)
- csc.exe (PID: 3200)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2208)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2252)
Reads the computer name
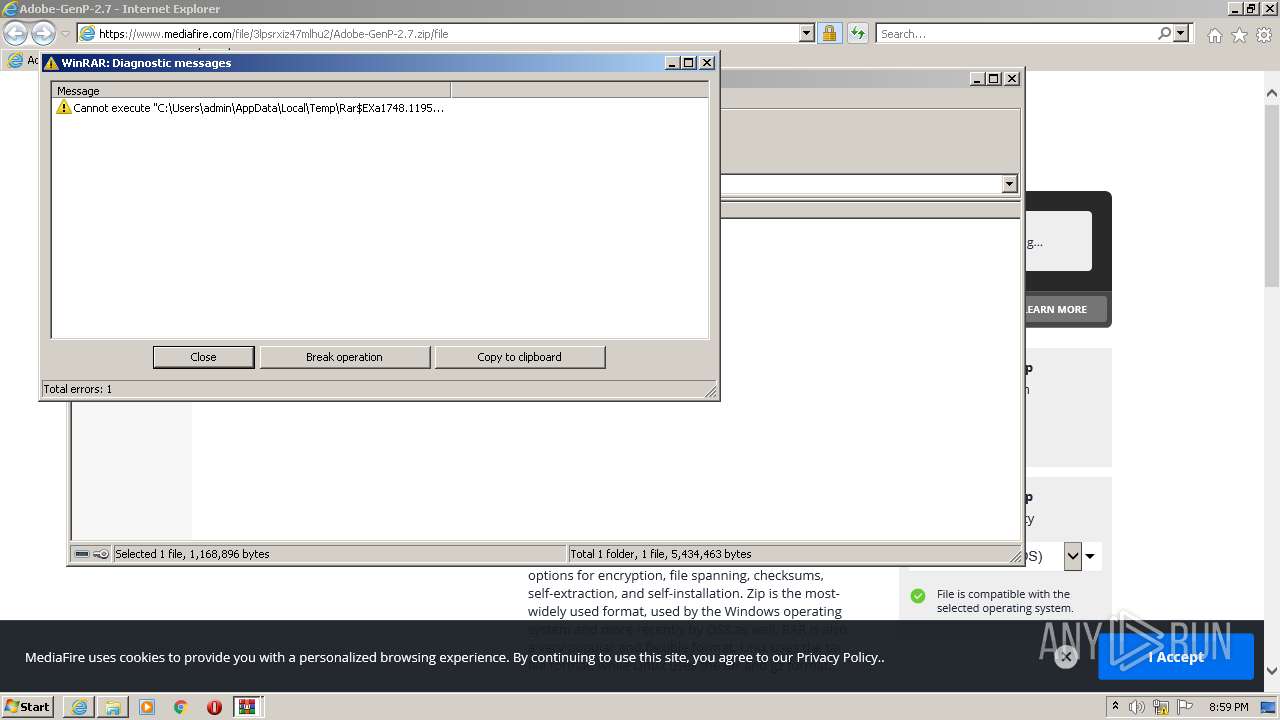
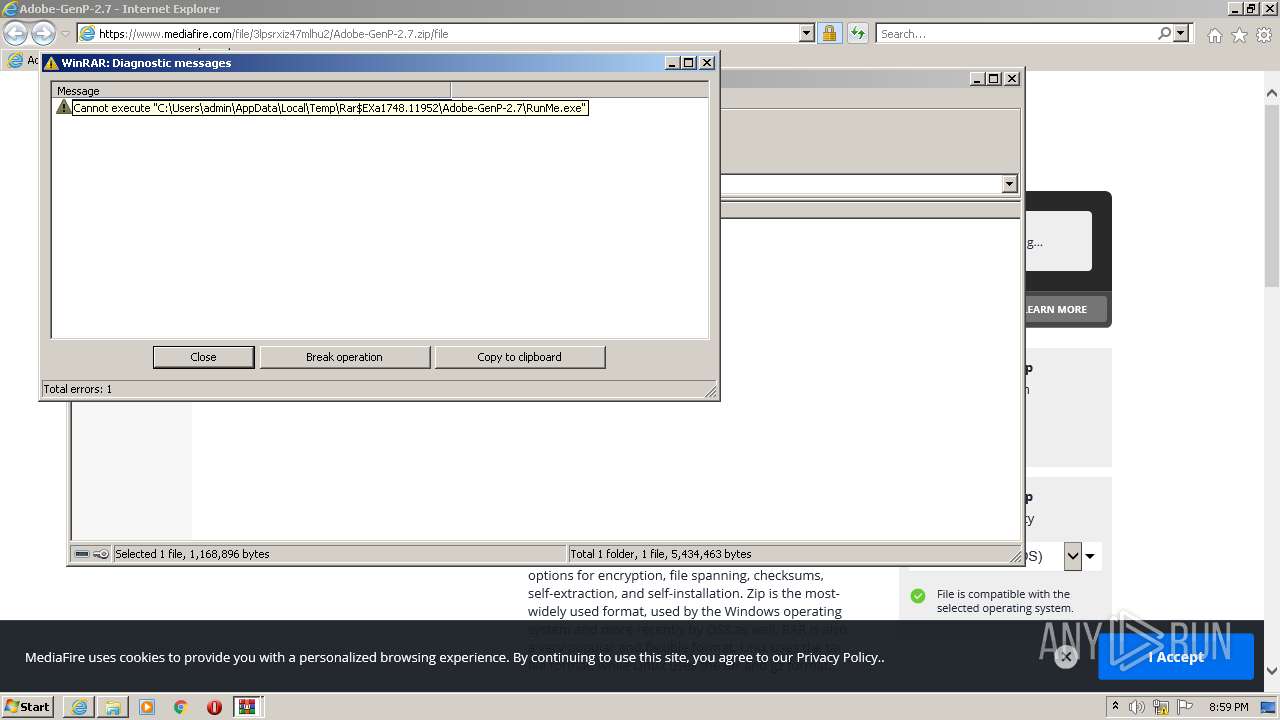
- WinRAR.exe (PID: 1748)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1748)
- csc.exe (PID: 3200)
- csc.exe (PID: 3820)
- csc.exe (PID: 848)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1748)
- msdt.exe (PID: 2840)
- csc.exe (PID: 848)
- csc.exe (PID: 3200)
- csc.exe (PID: 3820)
Checks supported languages
- WinRAR.exe (PID: 1748)
- csc.exe (PID: 848)
- cvtres.exe (PID: 3108)
- csc.exe (PID: 3820)
- csc.exe (PID: 3200)
- cvtres.exe (PID: 1252)
- cvtres.exe (PID: 3352)
Drops a file with too old compile date
- msdt.exe (PID: 2840)
Executed via COM
- sdiagnhost.exe (PID: 2208)
Drops a file with a compile date too recent
- csc.exe (PID: 848)
- csc.exe (PID: 3200)
- csc.exe (PID: 3820)
INFO
Checks supported languages
- iexplore.exe (PID: 612)
- iexplore.exe (PID: 2252)
- pcwrun.exe (PID: 3160)
- msdt.exe (PID: 2840)
- sdiagnhost.exe (PID: 2208)
Reads the computer name
- iexplore.exe (PID: 612)
- iexplore.exe (PID: 2252)
- msdt.exe (PID: 2840)
- sdiagnhost.exe (PID: 2208)
Creates files in the user directory
- iexplore.exe (PID: 2252)
- iexplore.exe (PID: 612)
Changes internet zones settings
- iexplore.exe (PID: 612)
Checks Windows Trust Settings
- iexplore.exe (PID: 612)
- iexplore.exe (PID: 2252)
- msdt.exe (PID: 2840)
- sdiagnhost.exe (PID: 2208)
Application launched itself
- iexplore.exe (PID: 612)
Reads settings of System Certificates
- iexplore.exe (PID: 2252)
- iexplore.exe (PID: 612)
- msdt.exe (PID: 2840)
Reads internet explorer settings
- iexplore.exe (PID: 2252)
Modifies the phishing filter of IE
- iexplore.exe (PID: 612)
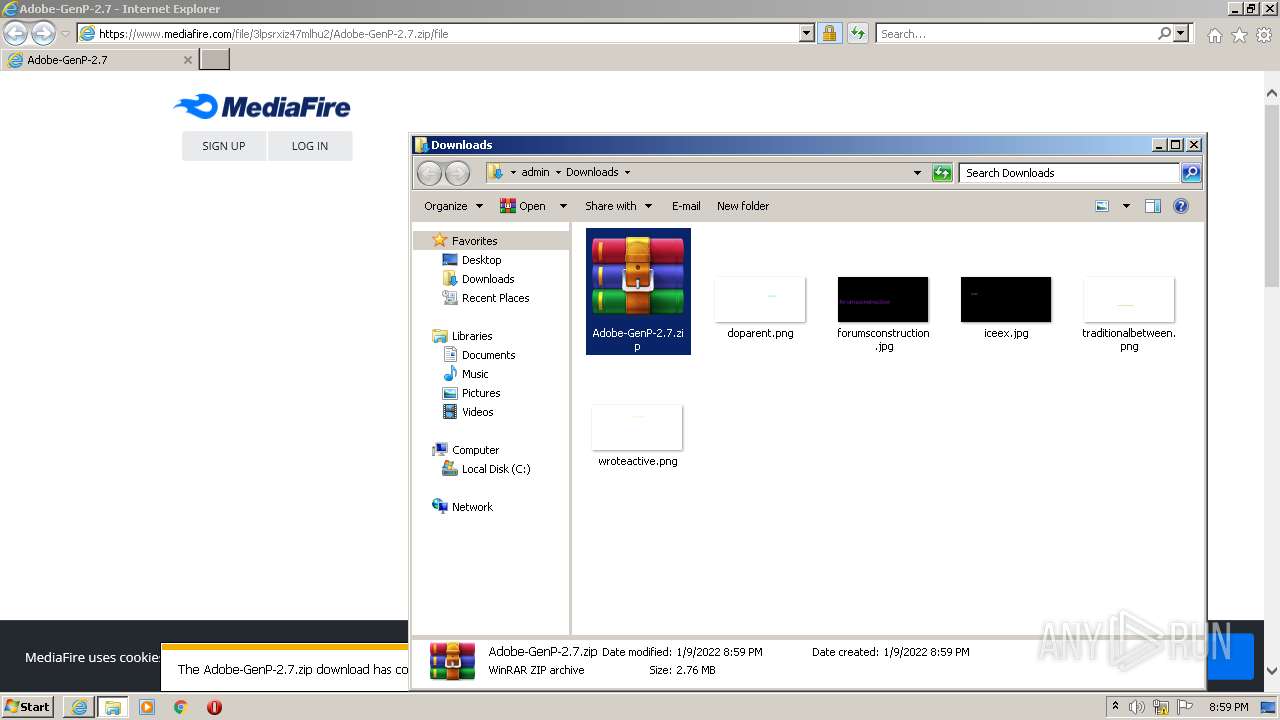
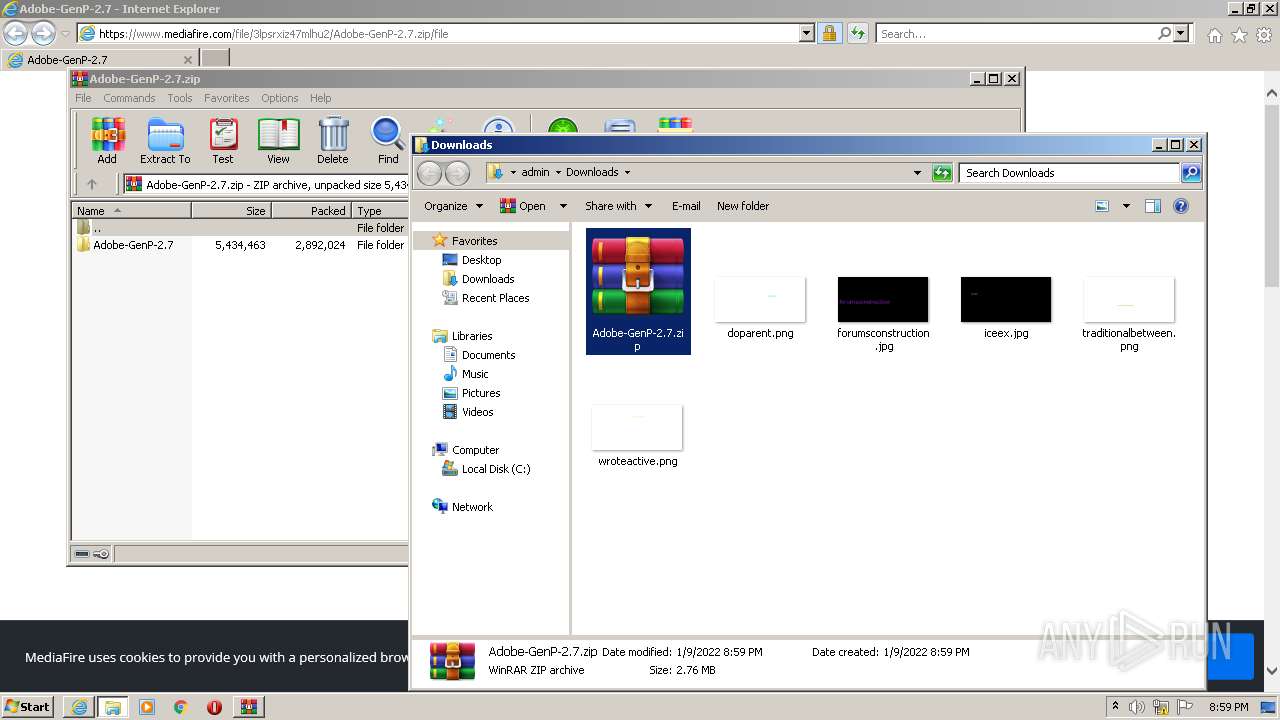
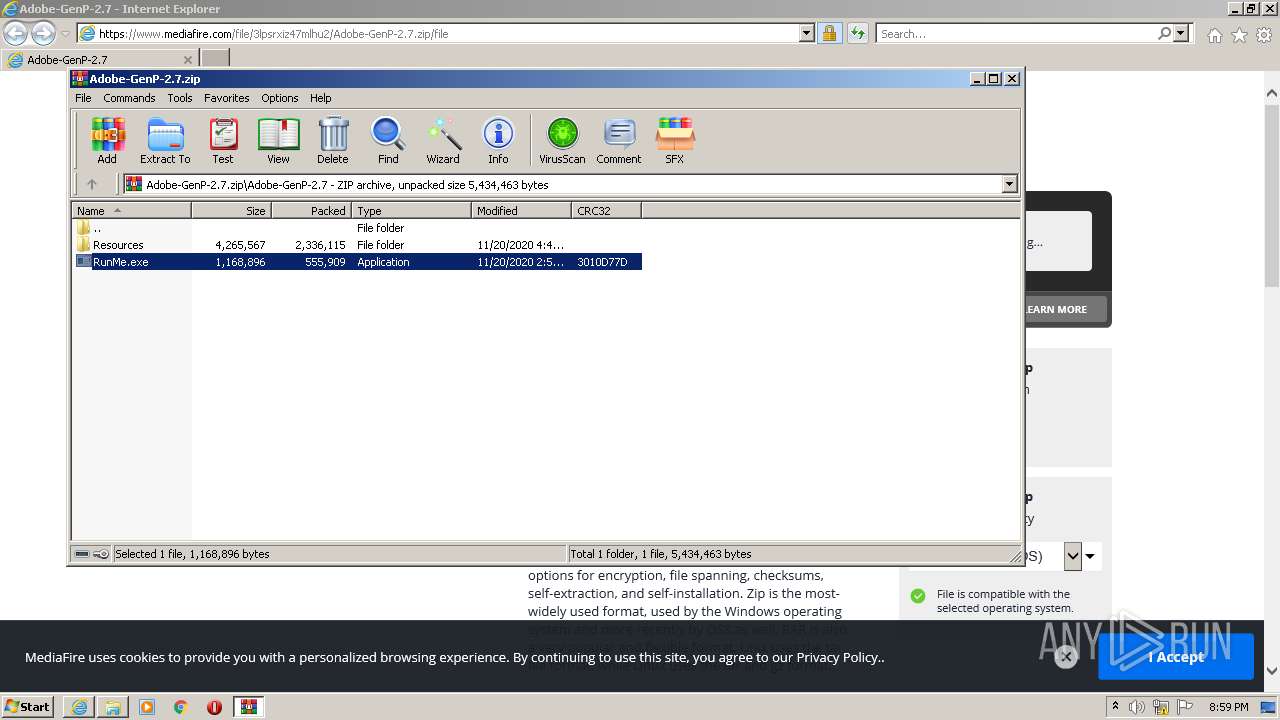
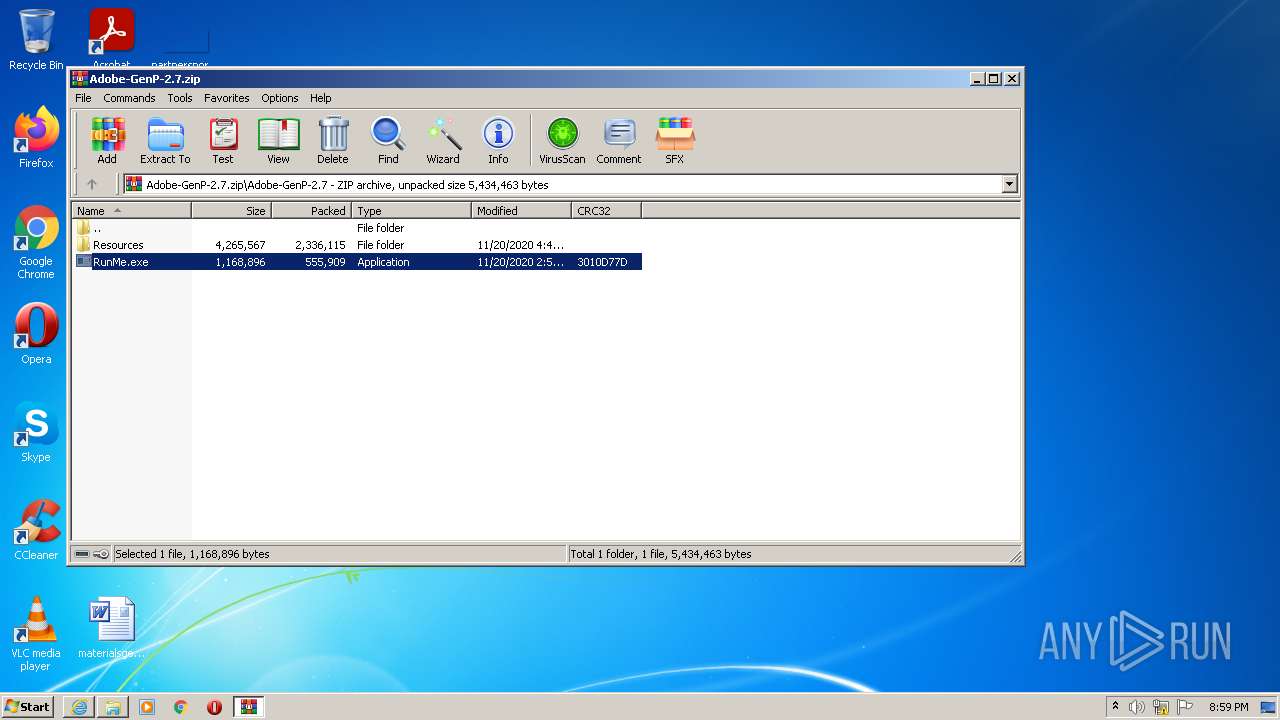
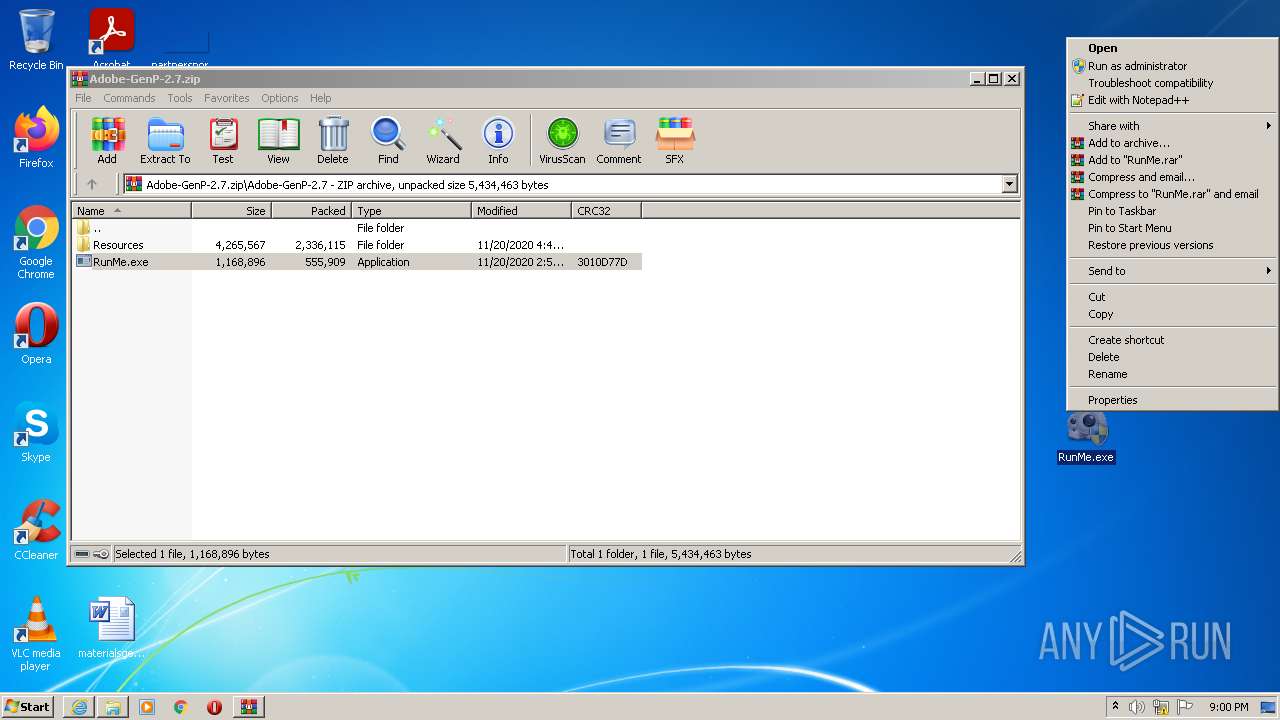
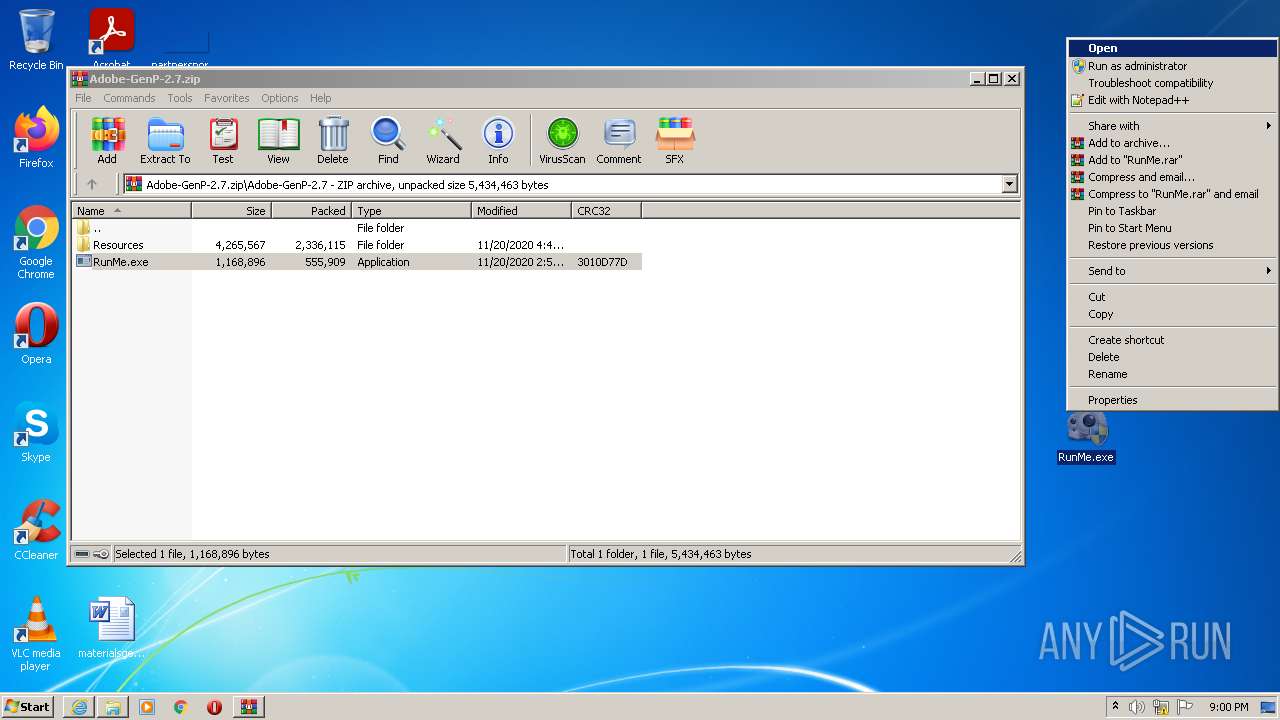
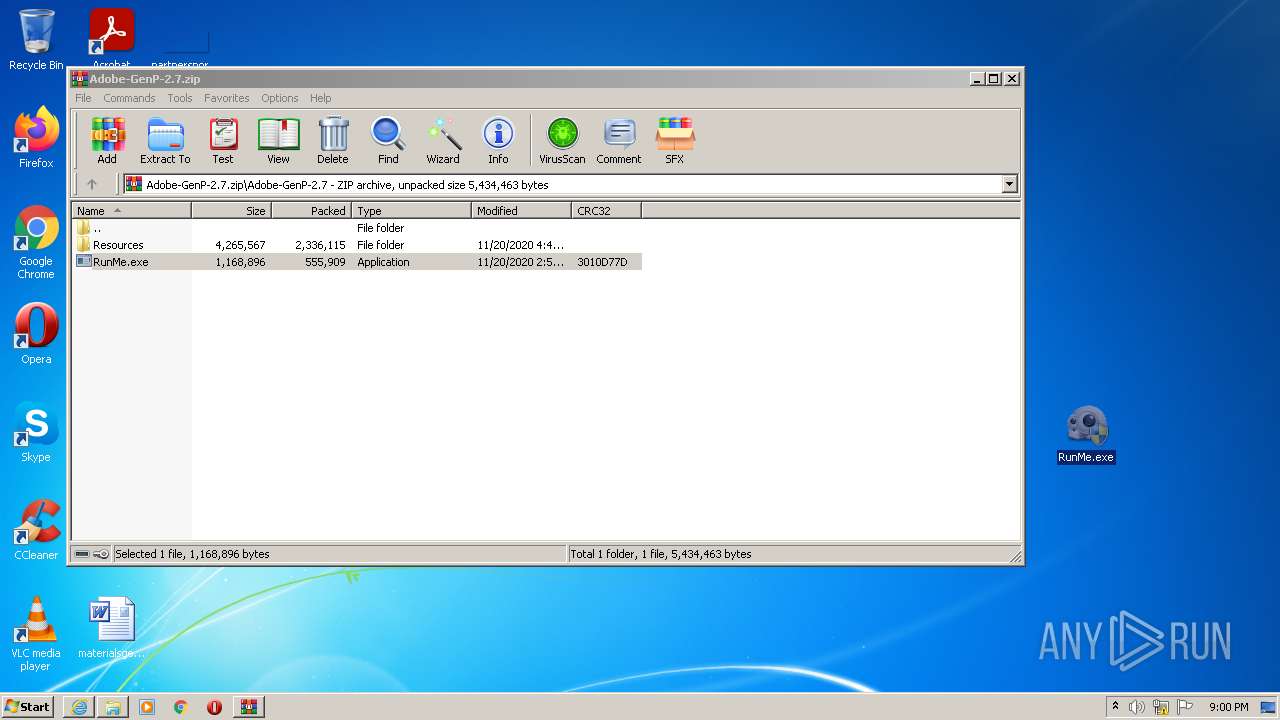
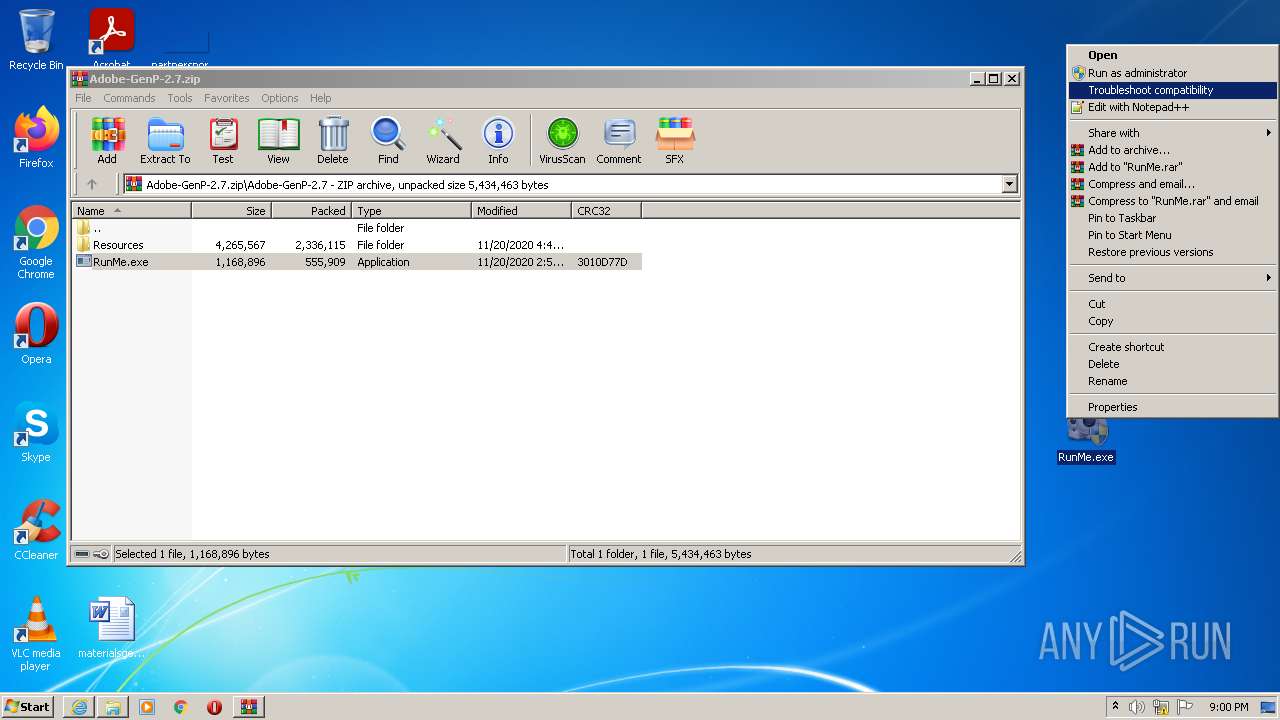
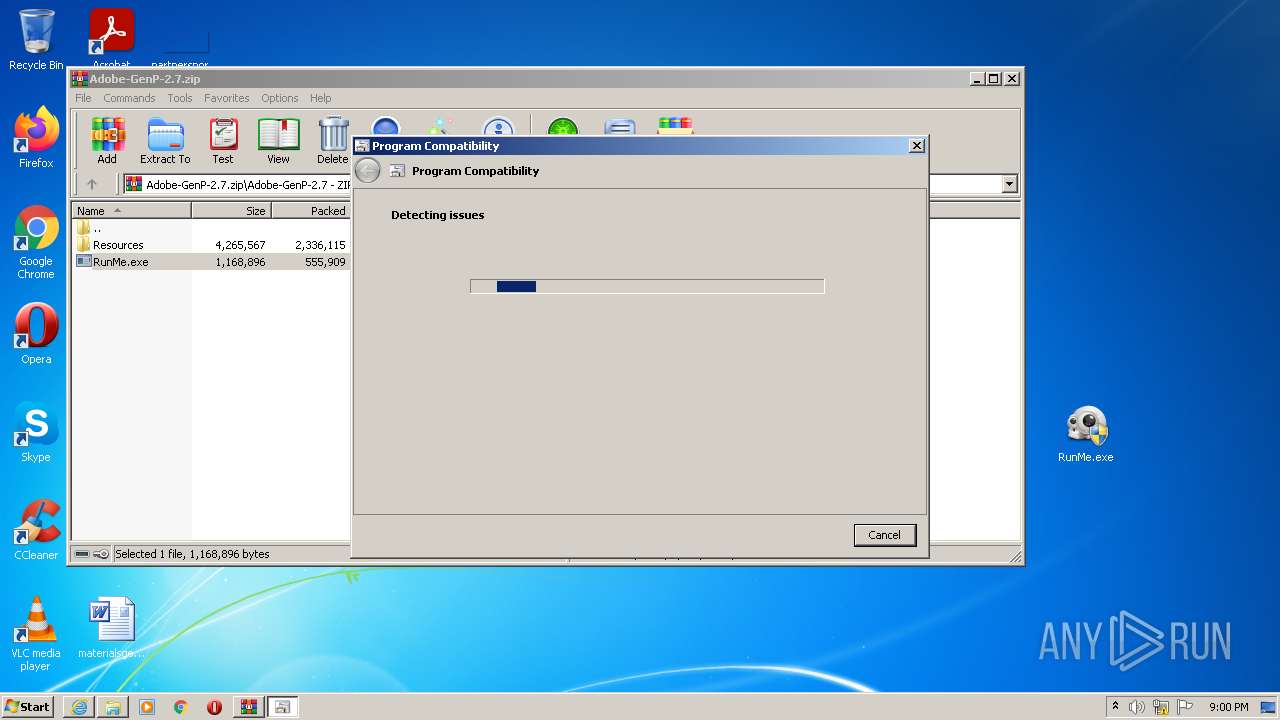
Manual execution by user
- WinRAR.exe (PID: 1748)
- pcwrun.exe (PID: 3160)
Adds / modifies Windows certificates
- iexplore.exe (PID: 612)
Changes settings of System certificates
- iexplore.exe (PID: 612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
12
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.mediafire.com/file/3lpsrxiz47mlhu2/Adobe-GenP-2.7.zip/file" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 848 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\oqu4e3e5.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1252 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES534B.tmp" "c:\Users\admin\AppData\Local\Temp\CSC534A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
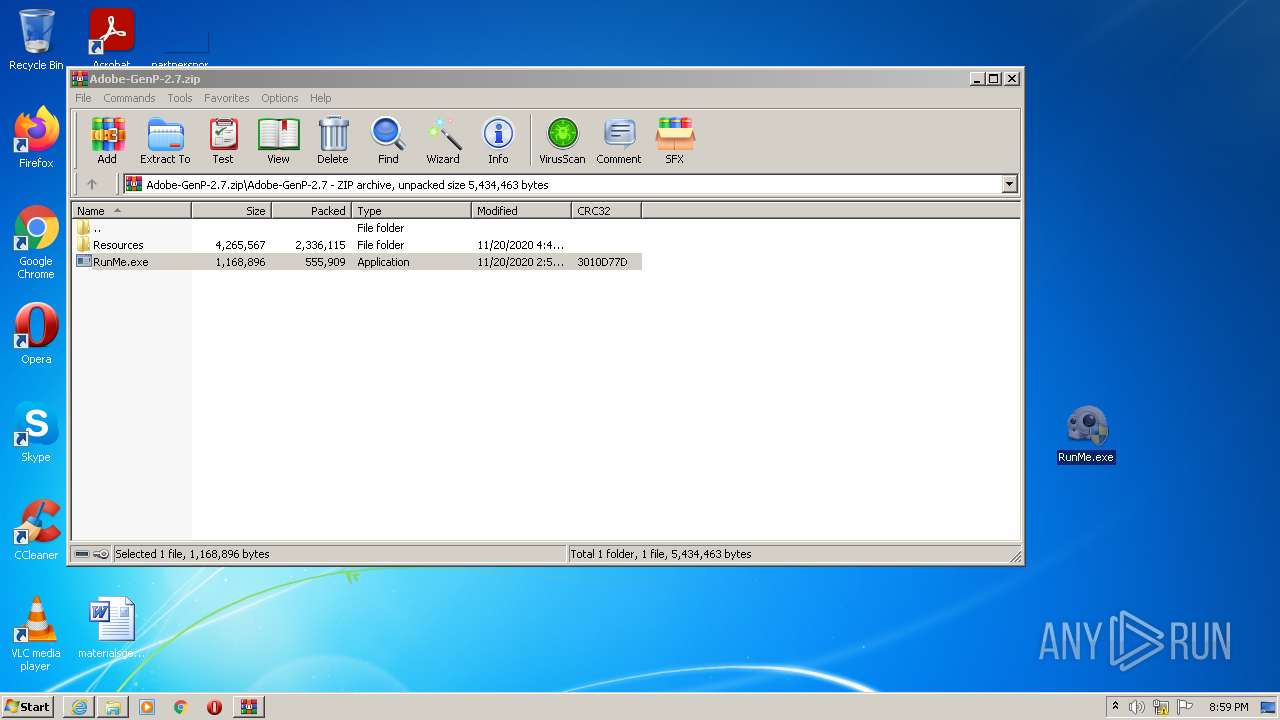
| 1748 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Adobe-GenP-2.7.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2208 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:612 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2840 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCW4EF4.xml /skip TRUE | C:\Windows\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3108 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES52BE.tmp" "c:\Users\admin\AppData\Local\Temp\CSC52BD.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
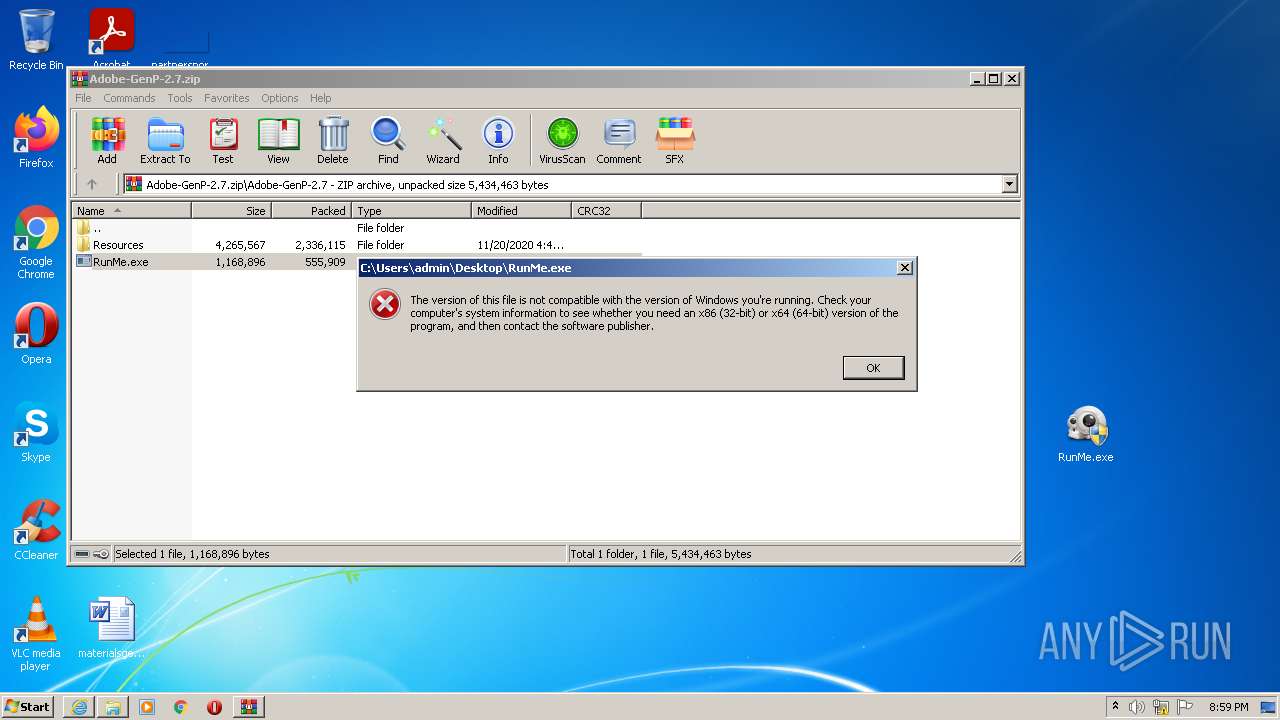
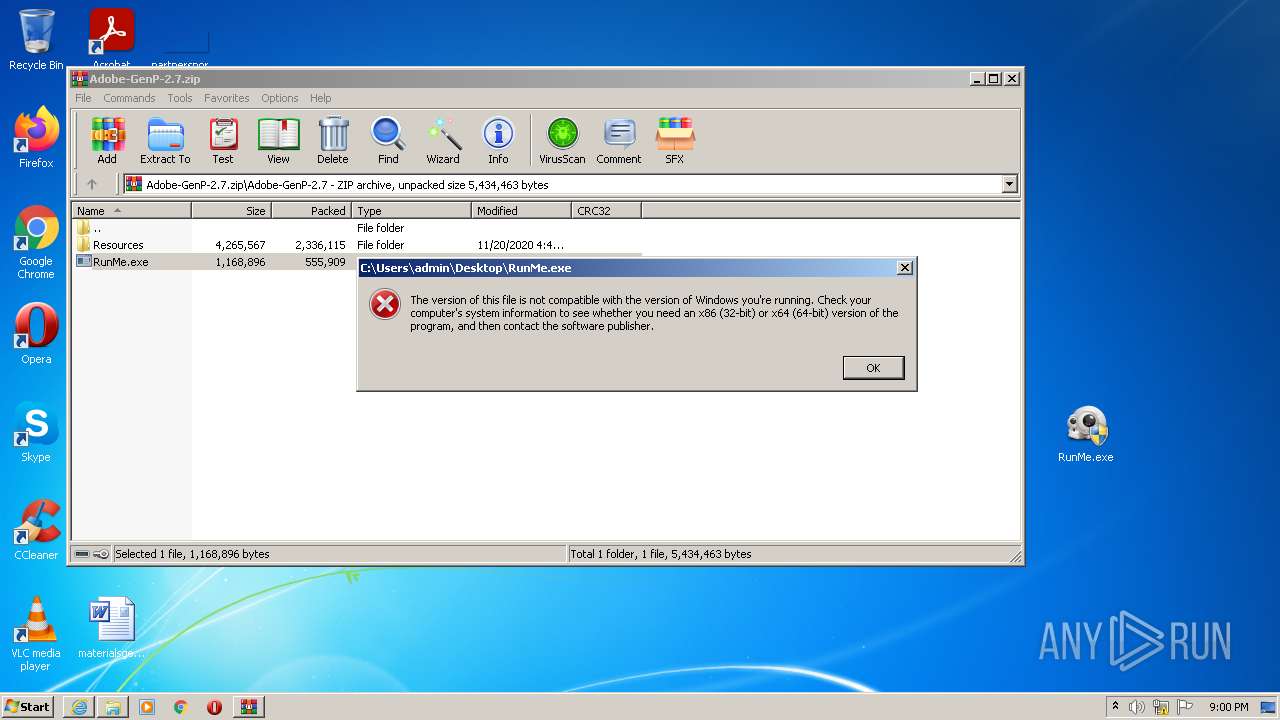
| 3160 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\Desktop\RunMe.exe" | C:\Windows\system32\pcwrun.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3200 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ff67k1nu.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
Total events
22 841
Read events
22 643
Write events
196
Delete events
2
Modification events
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30934427 | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30934427 | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
11
Suspicious files
33
Text files
96
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\OH7UAXI2.txt | text | |
MD5:3EBDE39DACE3BDAEE6C9A72A0B0F6467 | SHA256:6A3D5916EA5EF0E7345E7018691880063C21606089686B9BAB6F8DF665B9BD00 | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:D7DE9FDF72CB528C1346E89EDD109C5B | SHA256:C12920695A88D319510A844714BE4322388ACA5AA474D7A97FA553B61C12485D | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\O7E95N30.txt | text | |
MD5:066455D4A5F94421915FAD92DB028EEB | SHA256:86145E2156D4421D01388E0A23E028FBC1C1F32E2AF5E362F569DE30F87EA76C | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | der | |
MD5:1A5F5EB443D37481ED5C206A4AE9F184 | SHA256:2ACA905A66138AF0D6B5F6FD71CAAE4F4CF29F9FA395F7AC8F8BC213C1DFEFA7 | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\NYHY262I.txt | text | |
MD5:6F62947935D14B074D07F93B8B218B3D | SHA256:D626BB99048AB643AF6A0C46928578EE8339F446738714619C5BBB5C2F2FDD5A | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\file[1].htm | html | |
MD5:256671E3FE47BCF99FEB91430A7C925D | SHA256:44FE06E59AC280C5BE5C00670008CE0EE347F97FDB21626503794FDDE7365464 | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:07582E3CA36F6C506CB8A15D13D109DC | SHA256:835CFBF5D76652718825BD9D29ADB470FA1FC339E8A8E0F5FFA1F76FFBC420BE | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:1C7C668F43C6B441CFC588C76A8B1CDA | SHA256:4E4022A392AF782CDC429C25CAD09B00092B874EFA9B5900CAAF8ADCD6E6658E | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SDQNICUT.txt | text | |
MD5:29A5F255A9CBA73D45D494BDD27B9A67 | SHA256:31429938B33C97417A55BCC706558E56C11CB6F6034DA20B1D2DF7D25A95C816 | |||
| 2252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:64E9B8BB98E2303717538CE259BEC57D | SHA256:76BD459EC8E467EFC3E3FB94CB21B9C77A2AA73C9D4C0F3FAF823677BE756331 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
89
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2252 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?50539304c6442a1b | US | compressed | 4.70 Kb | whitelisted |
2252 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d8ce35b610dd58be | US | compressed | 4.70 Kb | whitelisted |
2252 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
2252 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2252 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2252 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2252 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2252 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD6vIn3vzMQlAoAAAABJf0y | US | der | 472 b | whitelisted |
2252 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECHMNwkPtKJCCgAAAAEl%2FQo%3D | US | der | 471 b | whitelisted |
2252 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAEC9RywYwyihLibdTfI1sk%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
612 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2252 | iexplore.exe | 173.194.76.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2252 | iexplore.exe | 104.16.203.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
2252 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
2252 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
2252 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2252 | iexplore.exe | 142.250.184.232:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2252 | iexplore.exe | 142.250.184.238:443 | translate.google.com | Google Inc. | US | whitelisted |
2252 | iexplore.exe | 142.250.186.174:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
2252 | iexplore.exe | 104.111.239.153:443 | c.aaxads.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
cdn.amplitude.com |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|