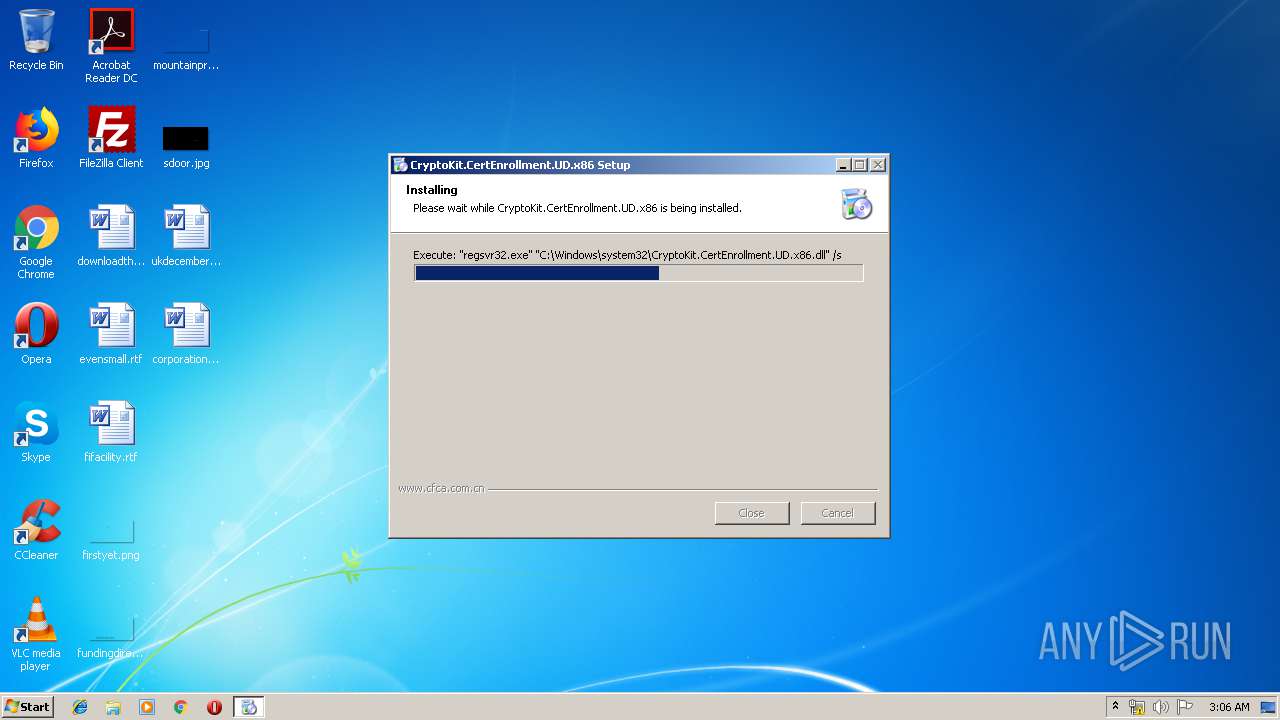
| download: | CryptoKit.CertEnrollment.UD.x86.exe |
| Full analysis: | https://app.any.run/tasks/c288f119-ac08-4adb-afd1-50608e153d99 |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2019, 02:05:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 577F6E89AD89853822930AC3A2F1FCFC |
| SHA1: | 60F6E137BC7664B4C9EA10ADD843AB1949136356 |
| SHA256: | D0BBD1AAC63C8E5C38E9093DCBF8CA15B4534EA99894BFB4DEE0A9AA4FB2407B |
| SSDEEP: | 6144:3zZZWUjD5cZS9/x6k/ec8s9MeR2r81uhqPxVthYX52v2mQkrkvuRLso+tfoxF/KM:3zZMUjD5co/Ik2c8s9Mewr81uQTS2qkT |
MALICIOUS
Loads dropped or rewritten executable
- CryptoKit.CertEnrollment.UD.x86.exe (PID: 3388)
- regsvr32.exe (PID: 620)
Registers / Runs the DLL via REGSVR32.EXE
- CryptoKit.CertEnrollment.UD.x86.exe (PID: 3388)
Changes settings of System certificates
- regsvr32.exe (PID: 620)
Changes internet zones settings
- regsvr32.exe (PID: 620)
SUSPICIOUS
Creates COM task schedule object
- regsvr32.exe (PID: 620)
Creates files in the Windows directory
- CryptoKit.CertEnrollment.UD.x86.exe (PID: 3388)
Creates files in the user directory
- CryptoKit.CertEnrollment.UD.x86.exe (PID: 3388)
- regsvr32.exe (PID: 620)
Executable content was dropped or overwritten
- CryptoKit.CertEnrollment.UD.x86.exe (PID: 3388)
Reads Internet Cache Settings
- regsvr32.exe (PID: 620)
Creates files in the program directory
- CryptoKit.CertEnrollment.UD.x86.exe (PID: 3388)
Creates a software uninstall entry
- CryptoKit.CertEnrollment.UD.x86.exe (PID: 3388)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 14:19:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 26624 |
| InitializedDataSize: | 475136 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3415 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.0.3 |
| ProductVersionNumber: | 3.2.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | CFCA |
| FileDescription: | CFCA Crypto Kit IE ActiveX |
| FileVersion: | 3.2.0.3 |
| LegalCopyright: | Copyright(C) 2011 CFCA |
| ProductName: | CryptoKit.CertEnrollment.UD.x86 |
| ProductVersion: | 3.2.0.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Apr-2010 12:19:38 |
| Detected languages: |
|
| CompanyName: | CFCA |
| FileDescription: | CFCA Crypto Kit IE ActiveX |
| FileVersion: | 3.2.0.3 |
| LegalCopyright: | Copyright(C) 2011 CFCA |
| ProductName: | CryptoKit.CertEnrollment.UD.x86 |
| ProductVersion: | 3.2.0.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Apr-2010 12:19:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000671C | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50461 |
.rdata | 0x00008000 | 0x000019D6 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02684 |
.data | 0x0000A000 | 0x0007139C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.73601 |
.ndata | 0x0007C000 | 0x000D1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0014D000 | 0x00007448 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70289 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21494 | 966 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.6303 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 6.5168 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.72637 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.68656 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.62942 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 6.07002 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.89724 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.70745 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
43
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "regsvr32.exe" "C:\Windows\system32\CryptoKit.CertEnrollment.UD.x86.dll" /s | C:\Windows\system32\regsvr32.exe | — | CryptoKit.CertEnrollment.UD.x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\AppData\Local\Temp\CryptoKit.CertEnrollment.UD.x86.exe" | C:\Users\admin\AppData\Local\Temp\CryptoKit.CertEnrollment.UD.x86.exe | — | explorer.exe | |||||||||||
User: admin Company: CFCA Integrity Level: MEDIUM Description: CFCA Crypto Kit IE ActiveX Exit code: 3221226540 Version: 3.2.0.3 Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\Temp\CryptoKit.CertEnrollment.UD.x86.exe" | C:\Users\admin\AppData\Local\Temp\CryptoKit.CertEnrollment.UD.x86.exe | explorer.exe | ||||||||||||
User: admin Company: CFCA Integrity Level: HIGH Description: CFCA Crypto Kit IE ActiveX Exit code: 0 Version: 3.2.0.3 Modules
| |||||||||||||||
Total events
1 218
Read events
356
Write events
862
Delete events
0
Modification events
| (PID) Process: | (3388) CryptoKit.CertEnrollment.UD.x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\@cfca.com/CryptoKit.CertEnrollment.UD.x86,version=3.2.0.3 |
| Operation: | write | Name: | Description |
Value: CFCA Crypto Kit IE ActiveX | |||
| (PID) Process: | (3388) CryptoKit.CertEnrollment.UD.x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\@cfca.com/CryptoKit.CertEnrollment.UD.x86,version=3.2.0.3 |
| Operation: | write | Name: | Path |
Value: C:\Windows\system32\CryptoKit.CertEnrollment.UD.x86.dll | |||
| (PID) Process: | (3388) CryptoKit.CertEnrollment.UD.x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\@cfca.com/CryptoKit.CertEnrollment.UD.x86,version=3.2.0.3 |
| Operation: | write | Name: | Vender |
Value: CFCA Technologies. | |||
| (PID) Process: | (3388) CryptoKit.CertEnrollment.UD.x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\@cfca.com/CryptoKit.CertEnrollment.UD.x86,version=3.2.0.3 |
| Operation: | write | Name: | GeckoVersion |
Value: 1.9.0 | |||
| (PID) Process: | (3388) CryptoKit.CertEnrollment.UD.x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\@cfca.com/CryptoKit.CertEnrollment.UD.x86,version=3.2.0.3 |
| Operation: | write | Name: | ProductName |
Value: CryptoKit.CertEnrollment.UD.x86 | |||
| (PID) Process: | (3388) CryptoKit.CertEnrollment.UD.x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\@cfca.com/CryptoKit.CertEnrollment.UD.x86,version=3.2.0.3 |
| Operation: | write | Name: | Version |
Value: 3.2.0.3 | |||
| (PID) Process: | (3388) CryptoKit.CertEnrollment.UD.x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\@cfca.com/CryptoKit.CertEnrollment.UD.x86,version=3.2.0.3\MimeTypes\application/CryptoKit.CertEnrollment.UD.x86 |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (620) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CryptoKit.CryptoAgent.CertEnrollment.UD.X86.1 |
| Operation: | write | Name: | |
Value: CryptoAgent Class | |||
| (PID) Process: | (620) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CryptoKit.CryptoAgent.CertEnrollment.UD.X86.1\CLSID |
| Operation: | write | Name: | |
Value: {049A930E-C769-4AEA-87F8-0FFEA7849487} | |||
| (PID) Process: | (620) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CryptoKit.CryptoAgent.CertEnrollment.UD.X86 |
| Operation: | write | Name: | |
Value: CryptoAgent Class | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 620 | regsvr32.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 3388 | CryptoKit.CertEnrollment.UD.x86.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\CFCA\CryptoKit.CertEnrollment.UD.x86\Uninstall CryptoKit.CertEnrollment.UD.x86.lnk | lnk | |
MD5:CE28CE49914B59C3F989BD04EF7C3F07 | SHA256:07C38E5561756635BDE7BFA24E8A42548240E1530041DA0035F332F0B648F3B5 | |||
| 3388 | CryptoKit.CertEnrollment.UD.x86.exe | C:\Users\admin\AppData\Local\Temp\nsn6DF8.tmp\System.dll | executable | |
MD5:959EA64598B9A3E494C00E8FA793BE7E | SHA256:03CD57AB00236C753E7DDEEE8EE1C10839ACE7C426769982365531042E1F6F8B | |||
| 3388 | CryptoKit.CertEnrollment.UD.x86.exe | C:\Program Files\CFCA\CryptoKit.CertEnrollment.UD.x86\uninst.exe | executable | |
MD5:57AA0E3716EF02FAE721C53D668C9620 | SHA256:16A4412EAADE49668D49F937EDB008B90F7F145F068526A7E2E4A5F64C599240 | |||
| 3388 | CryptoKit.CertEnrollment.UD.x86.exe | C:\Windows\system32\CryptoKit.CertEnrollment.UD.x86.dll | executable | |
MD5:86A62A2548E82FCEE2BEB6404454147F | SHA256:69901DE4176AD979F1161DB37ED565AC77626C7235E96DD1B14BD29868B74AC9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report