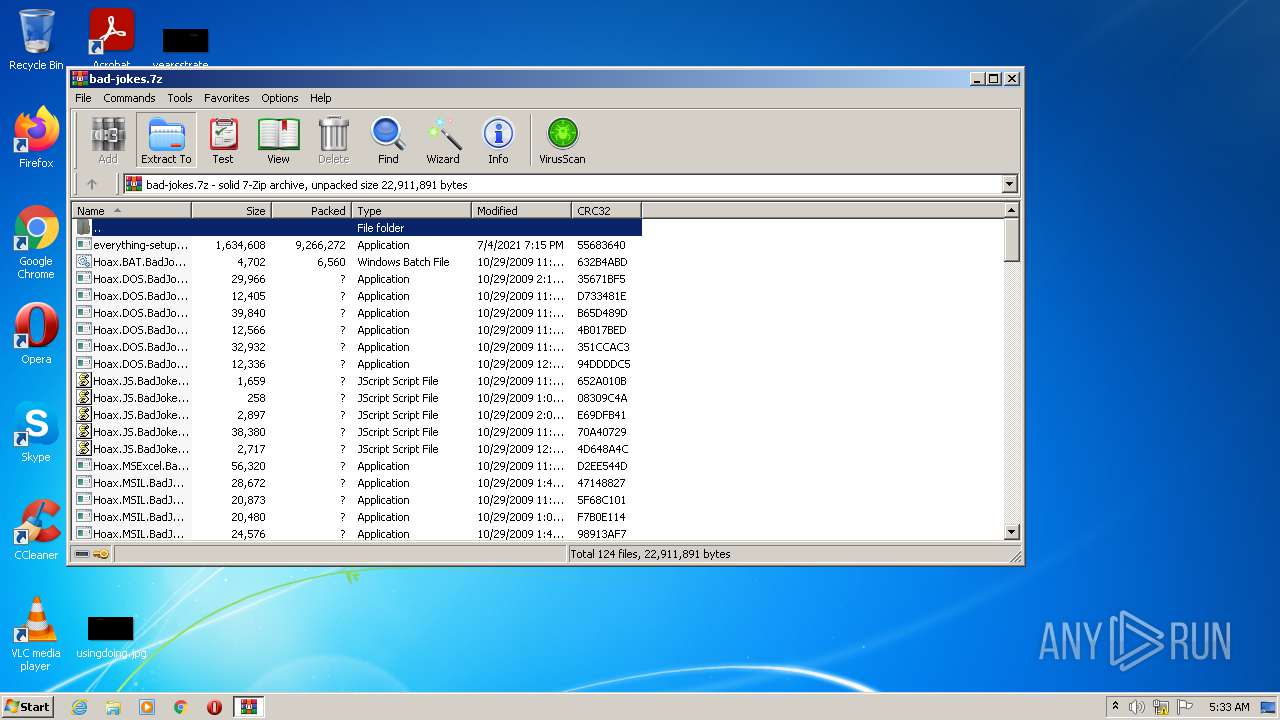
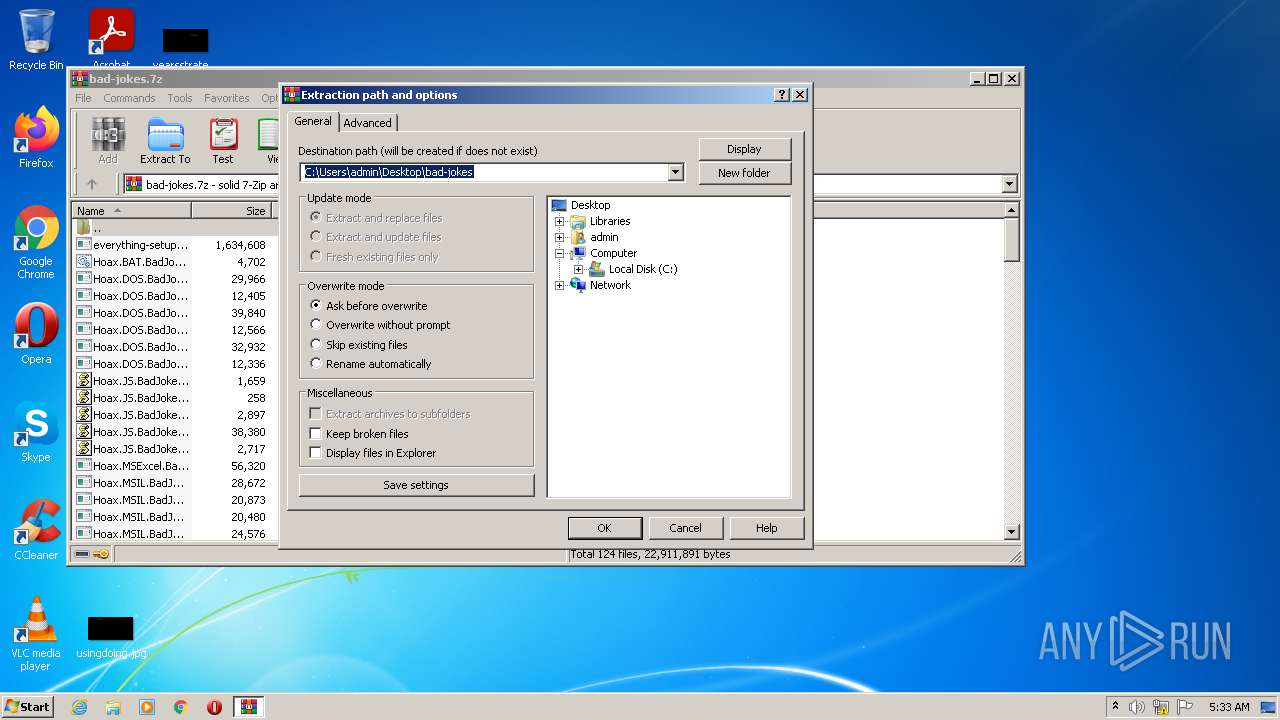
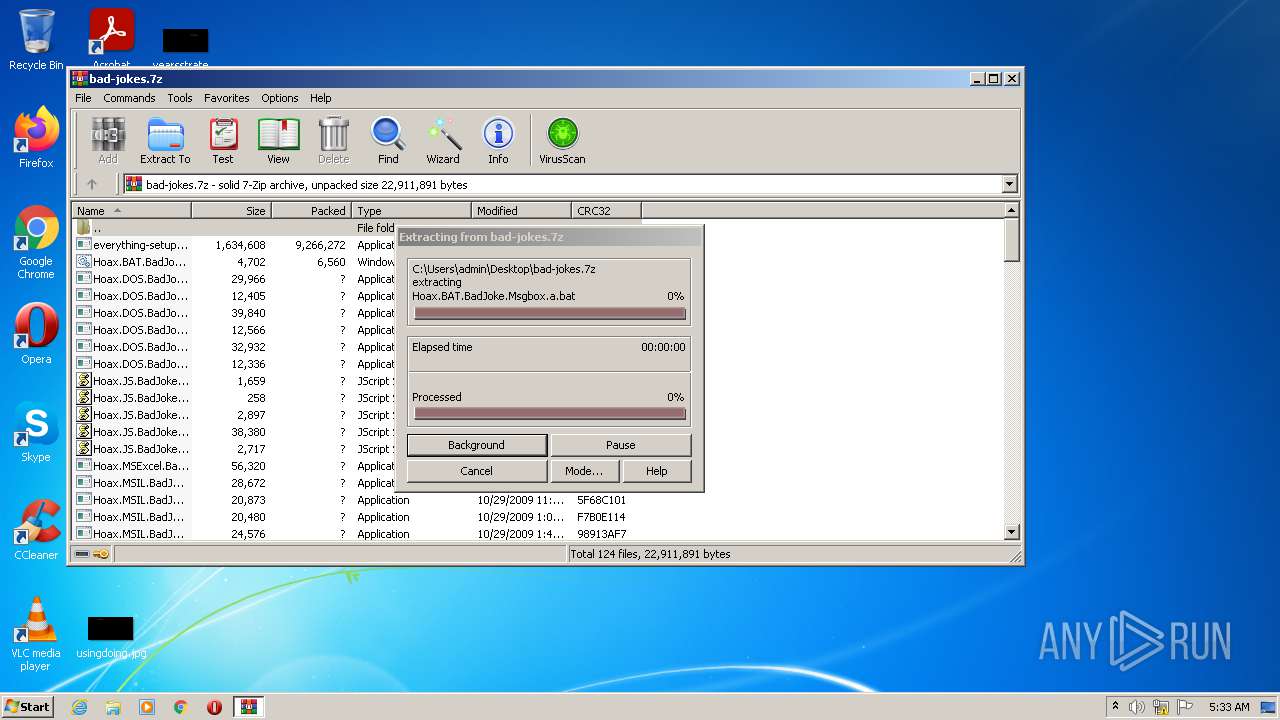
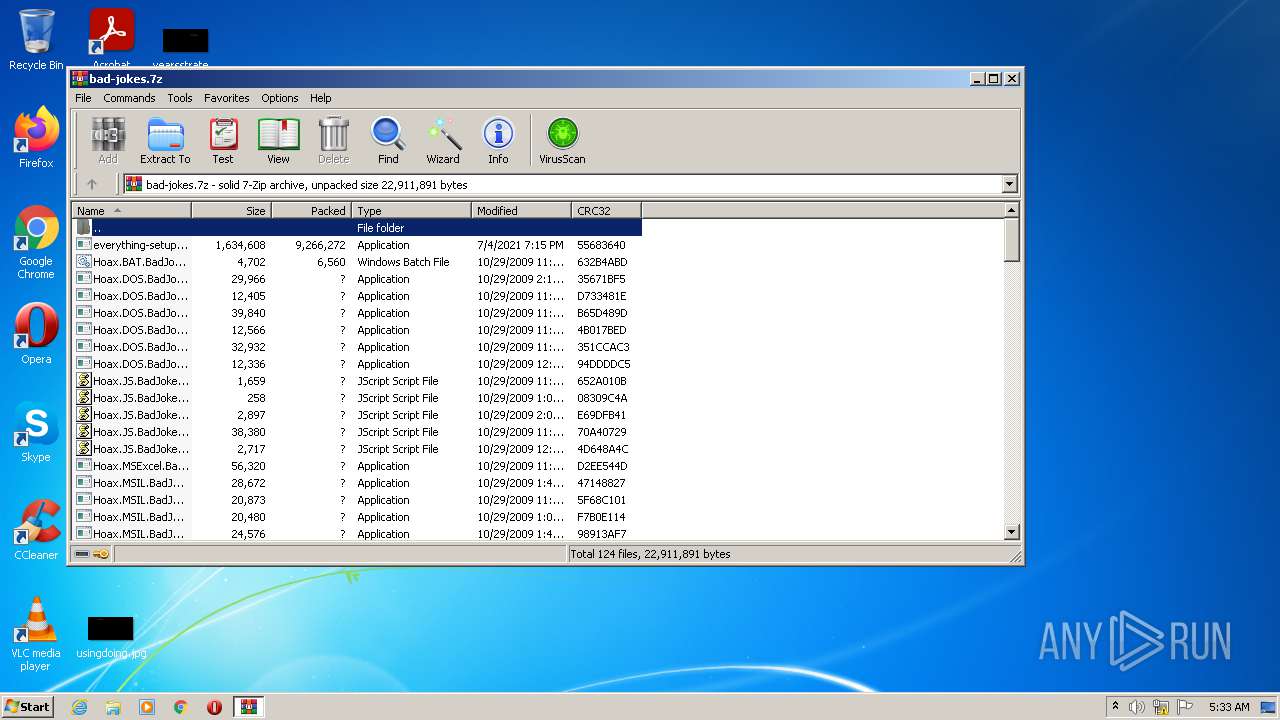
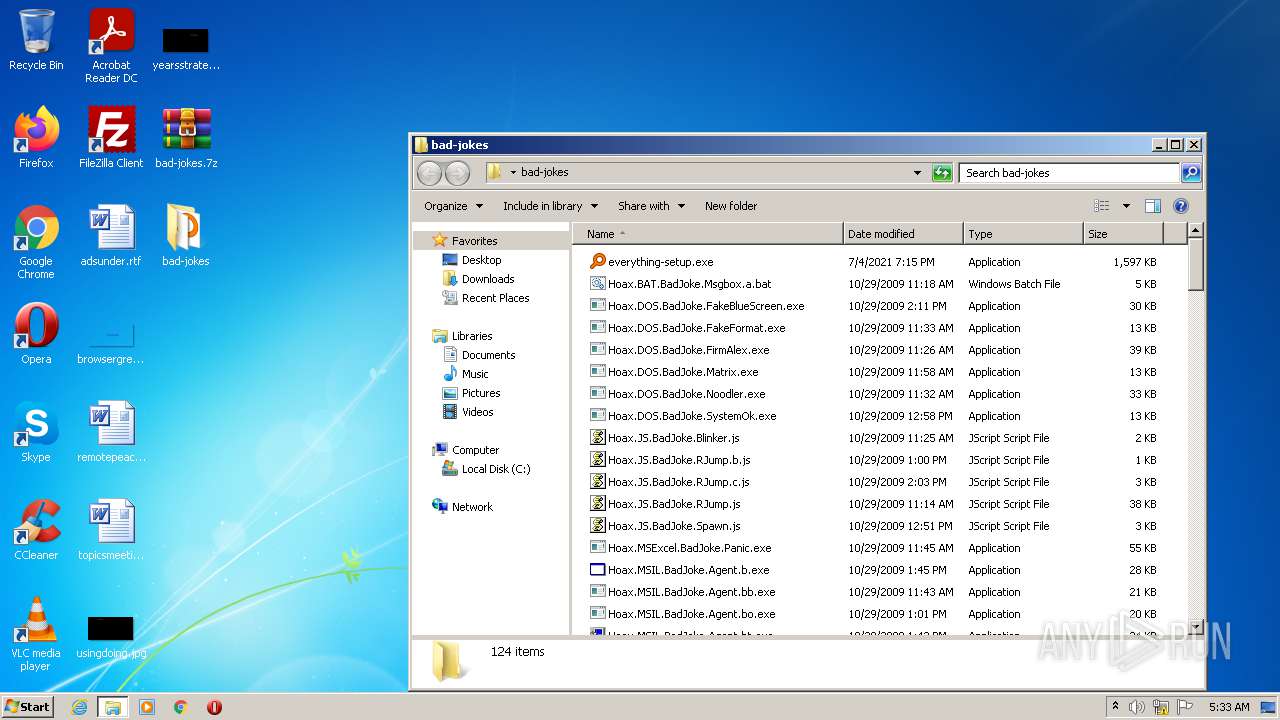
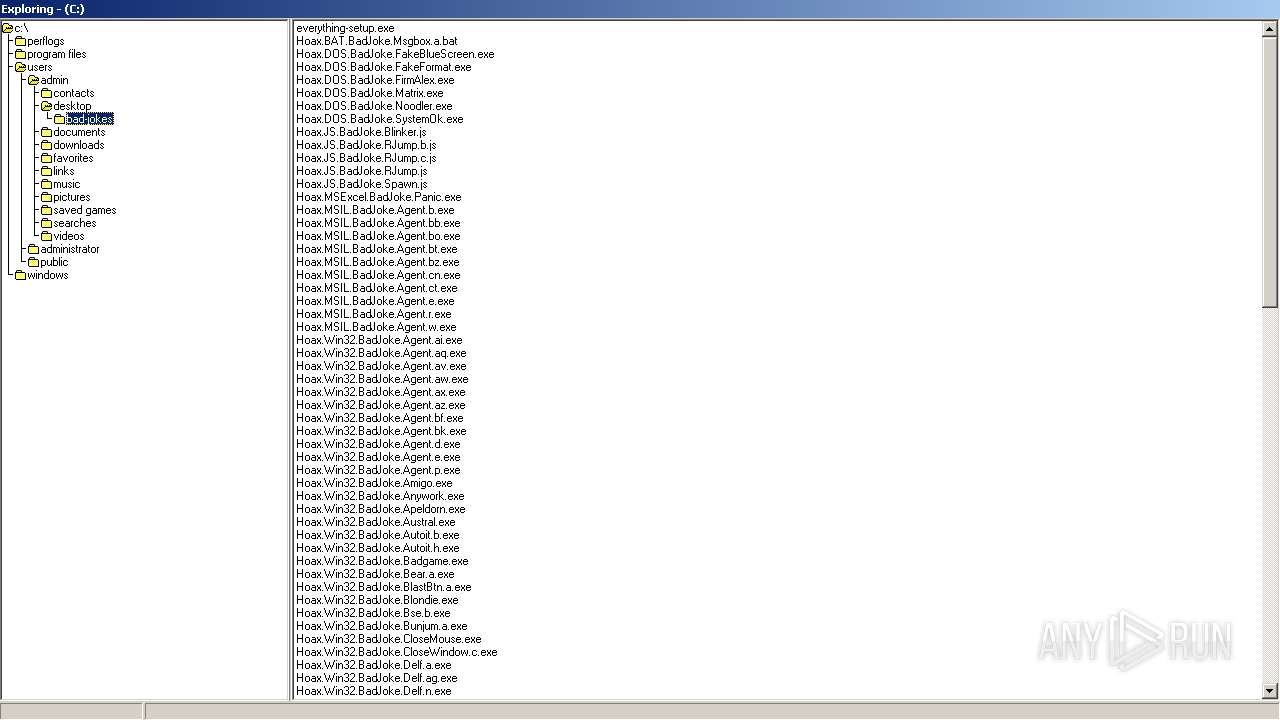
| File name: | bad-jokes.7z |
| Full analysis: | https://app.any.run/tasks/8b71c02c-9229-4d83-a2d8-bafb1e2a4b1d |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2021, 04:32:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
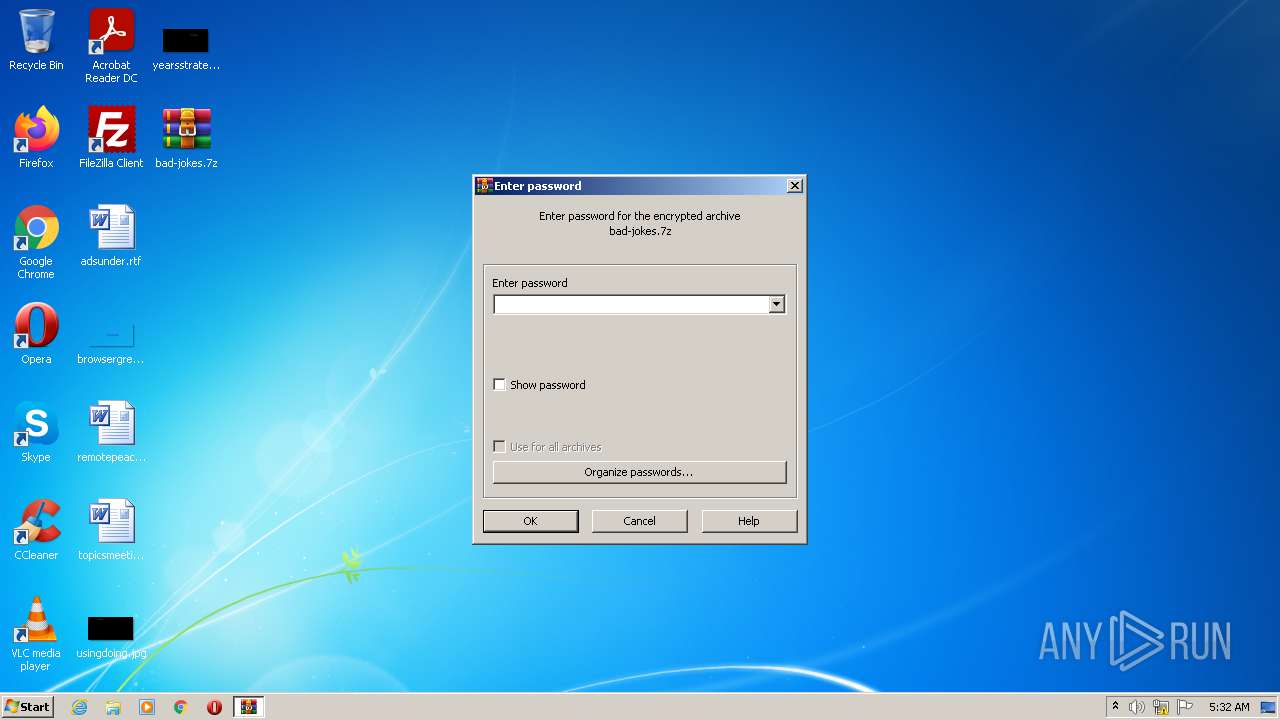
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | DAEDC9DEFCCD4D0B99F9C4FFCDDCE889 |
| SHA1: | FEF127B272223FC130FF3827DE455F7B5943F690 |
| SHA256: | D0A5CFB036B6C13ABF60CB43A2923D569E23C062807A0E441ED2ABEA022A406C |
| SSDEEP: | 196608:17oH6AxNkvcyf4n0sJlhDRSs+/1v0B00XMAiN7myiGBsM6hpTi:1sH6AQ3rq658BNXfeK3GBszi |
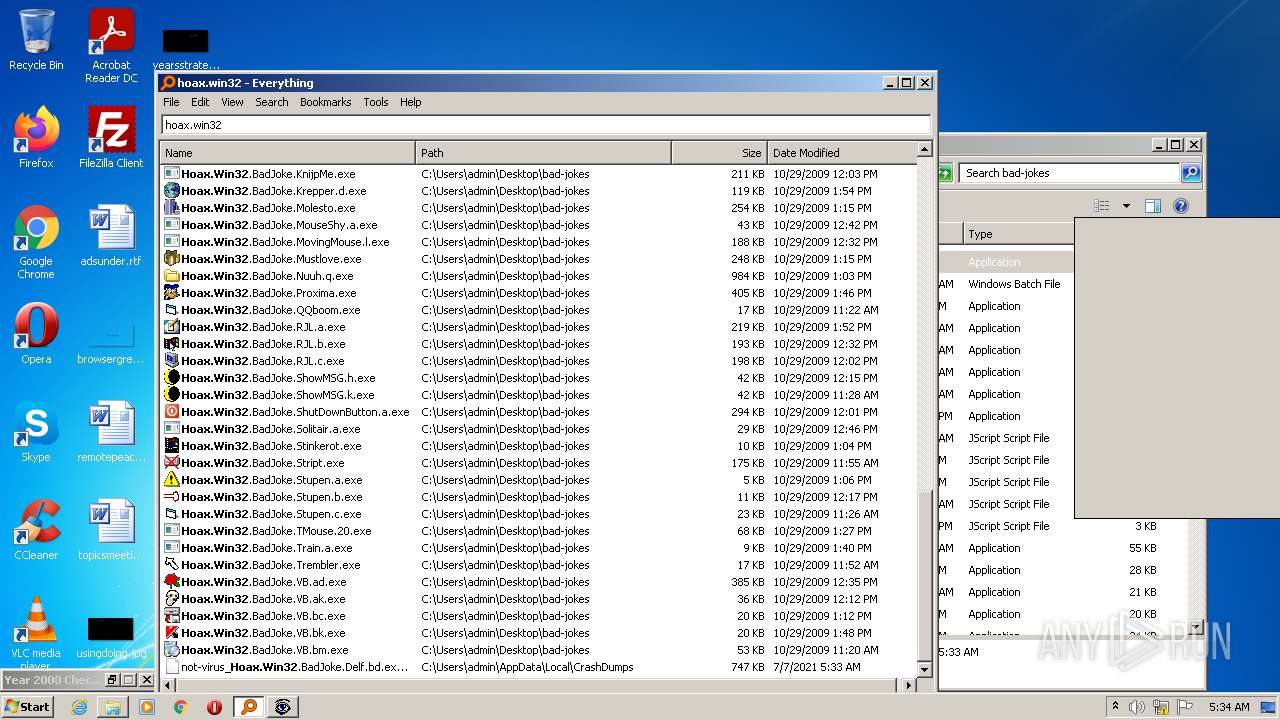
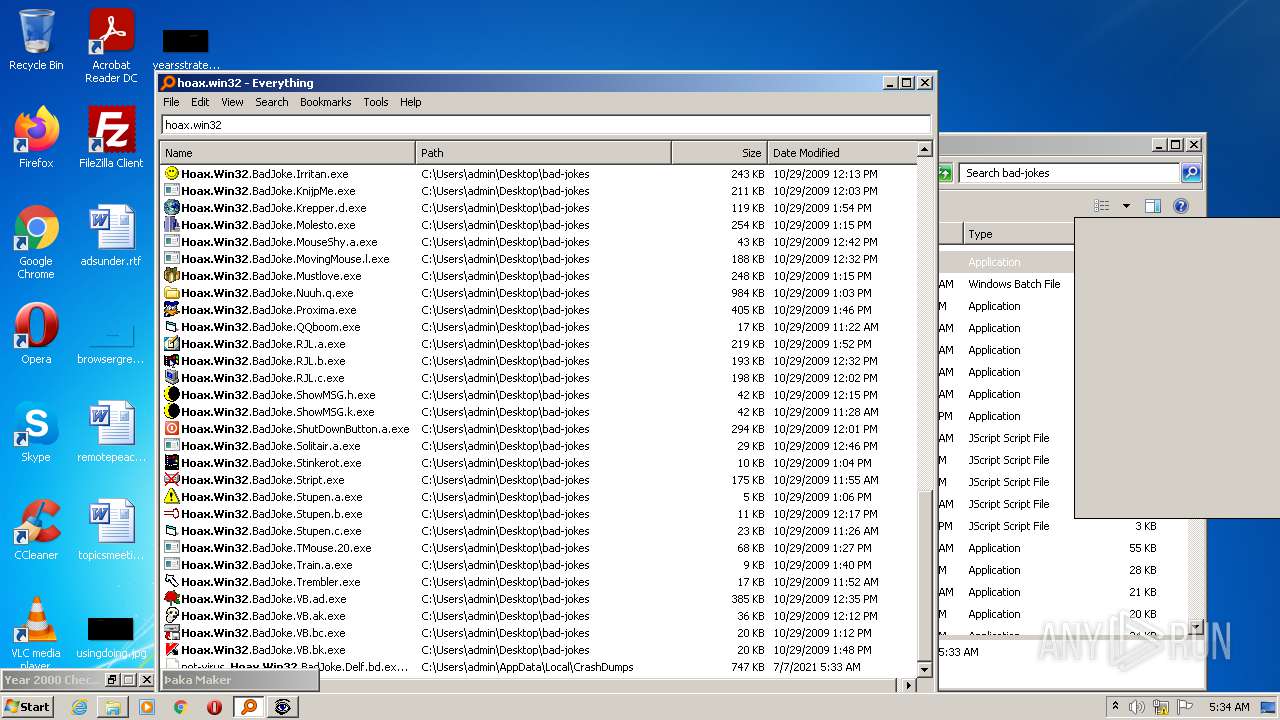
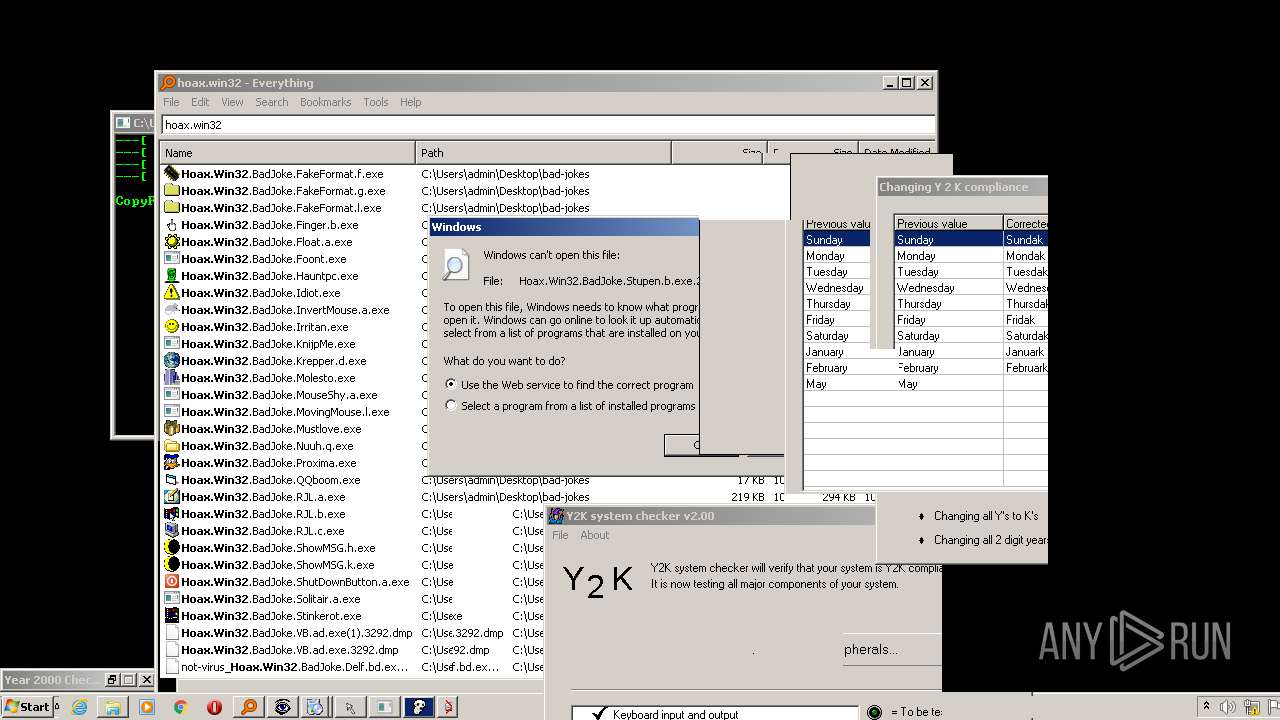
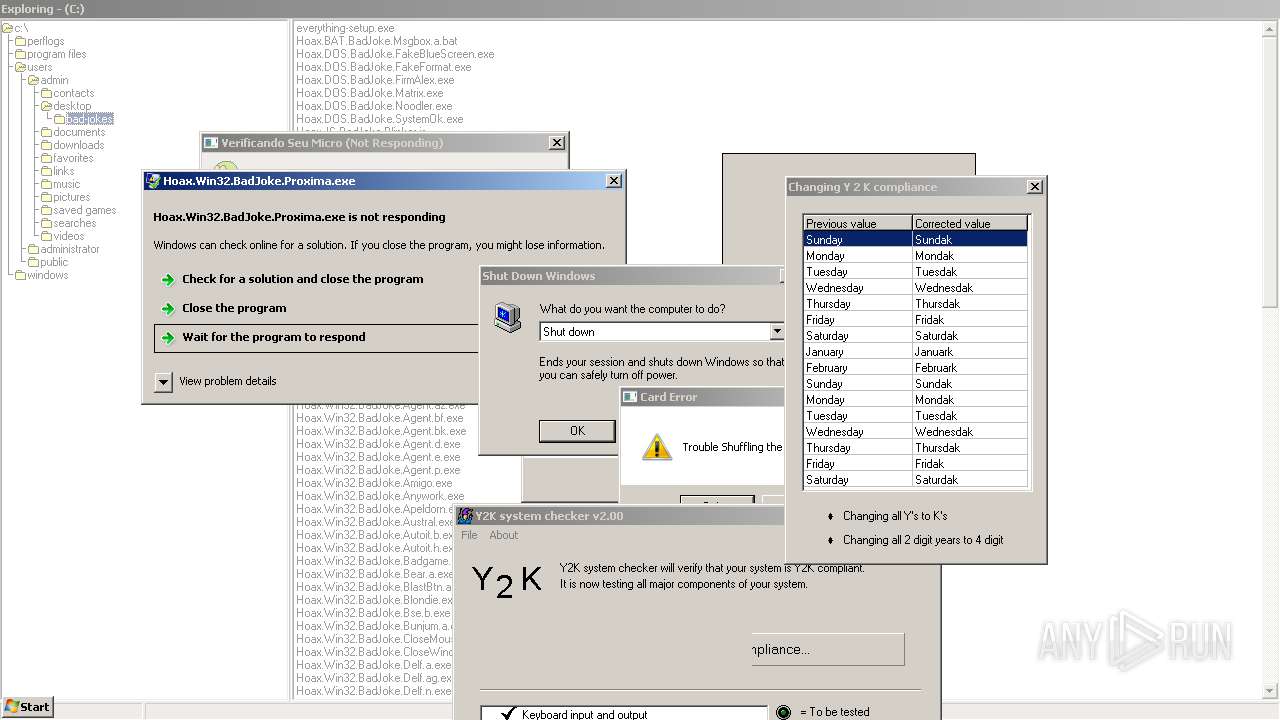
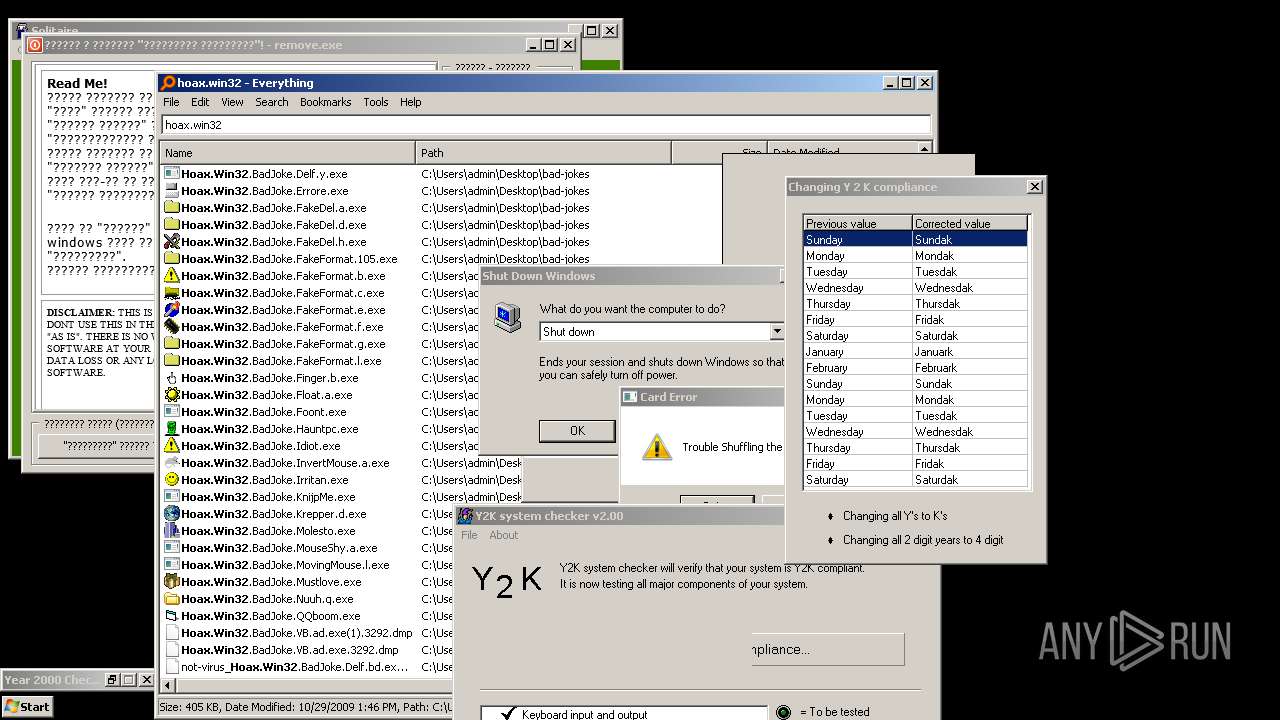
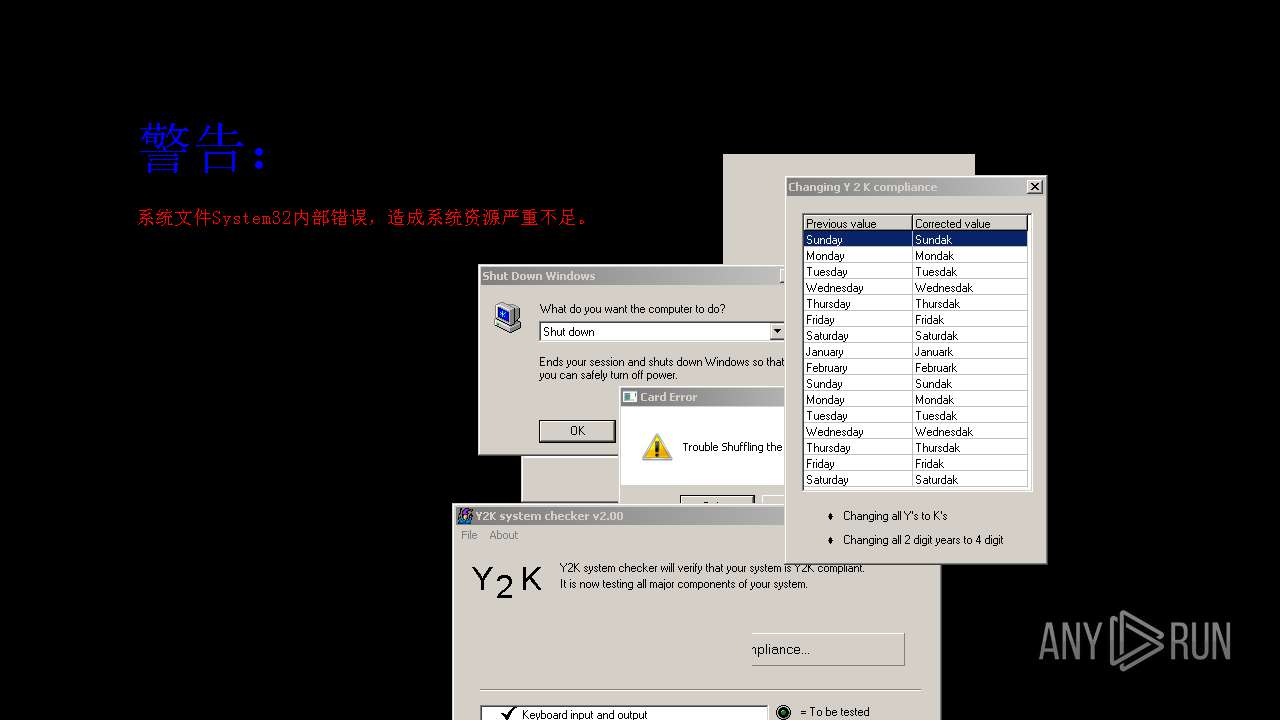
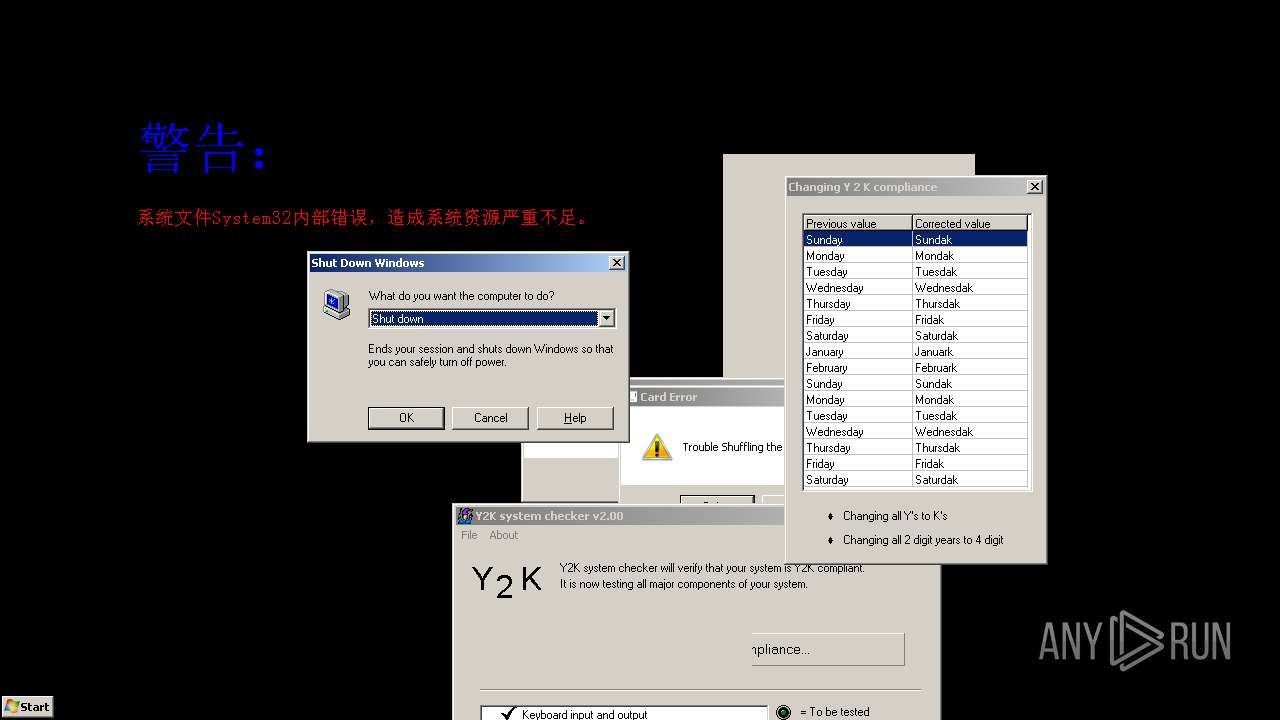
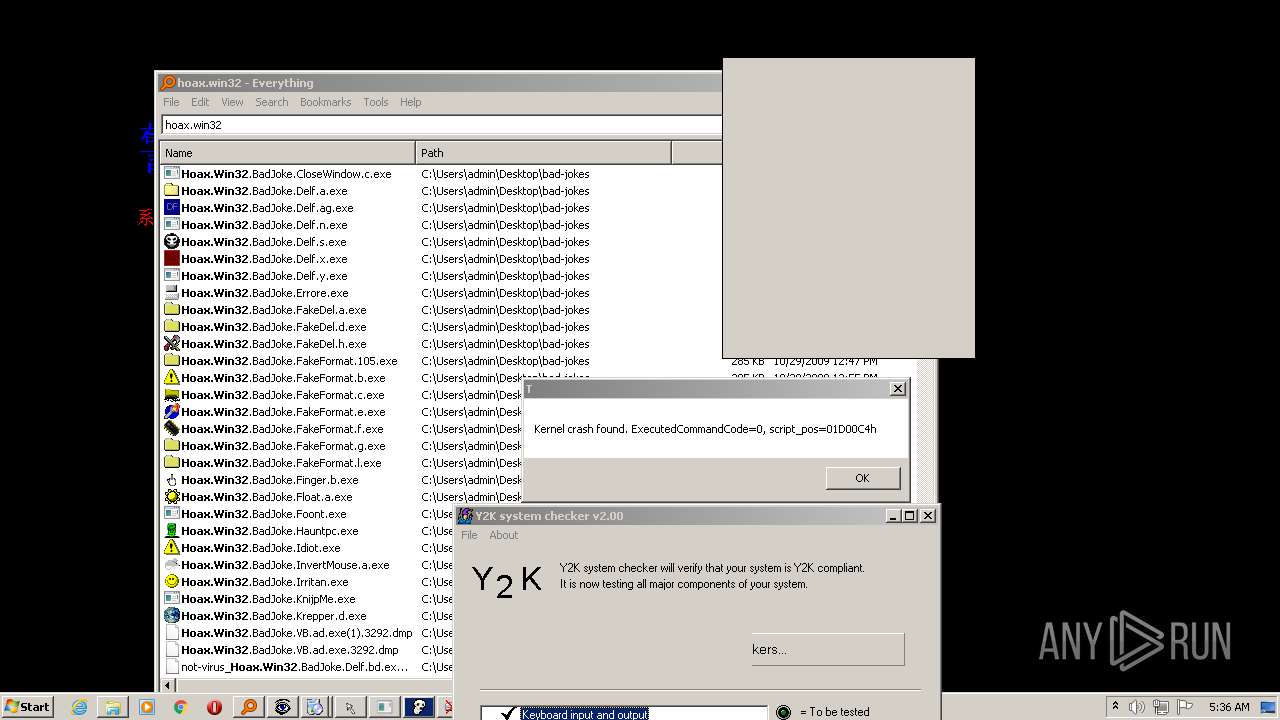
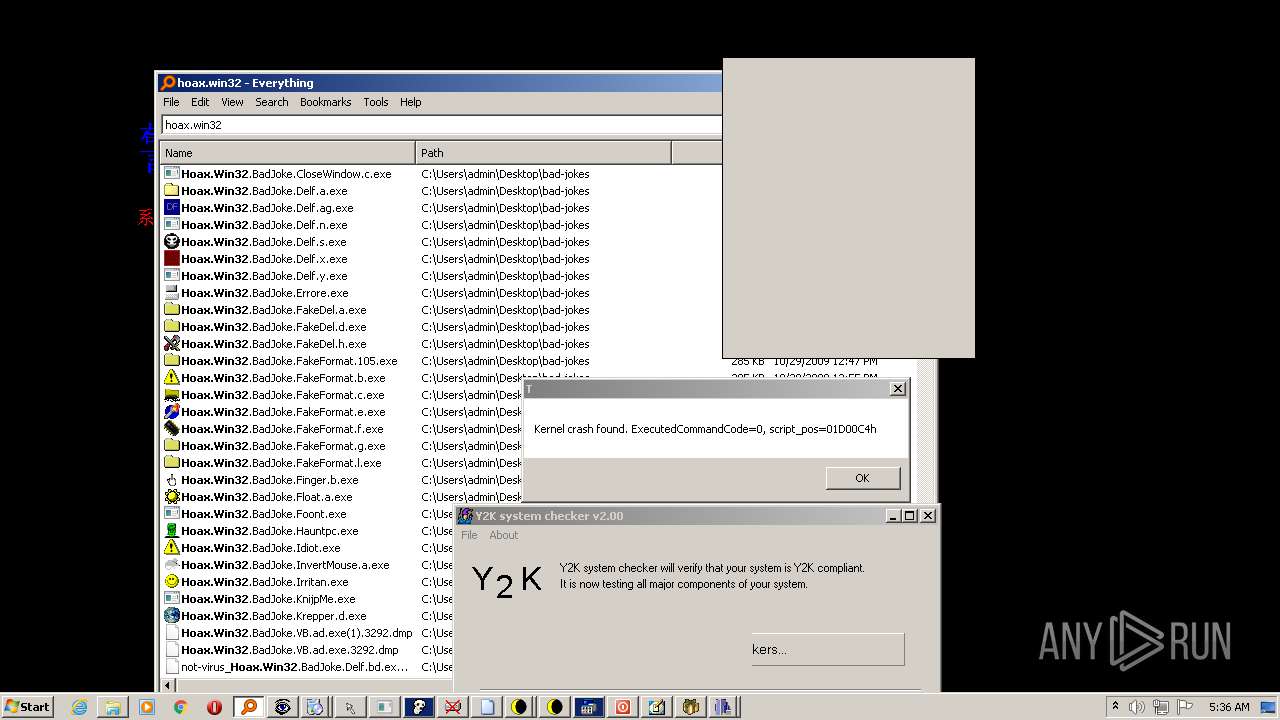
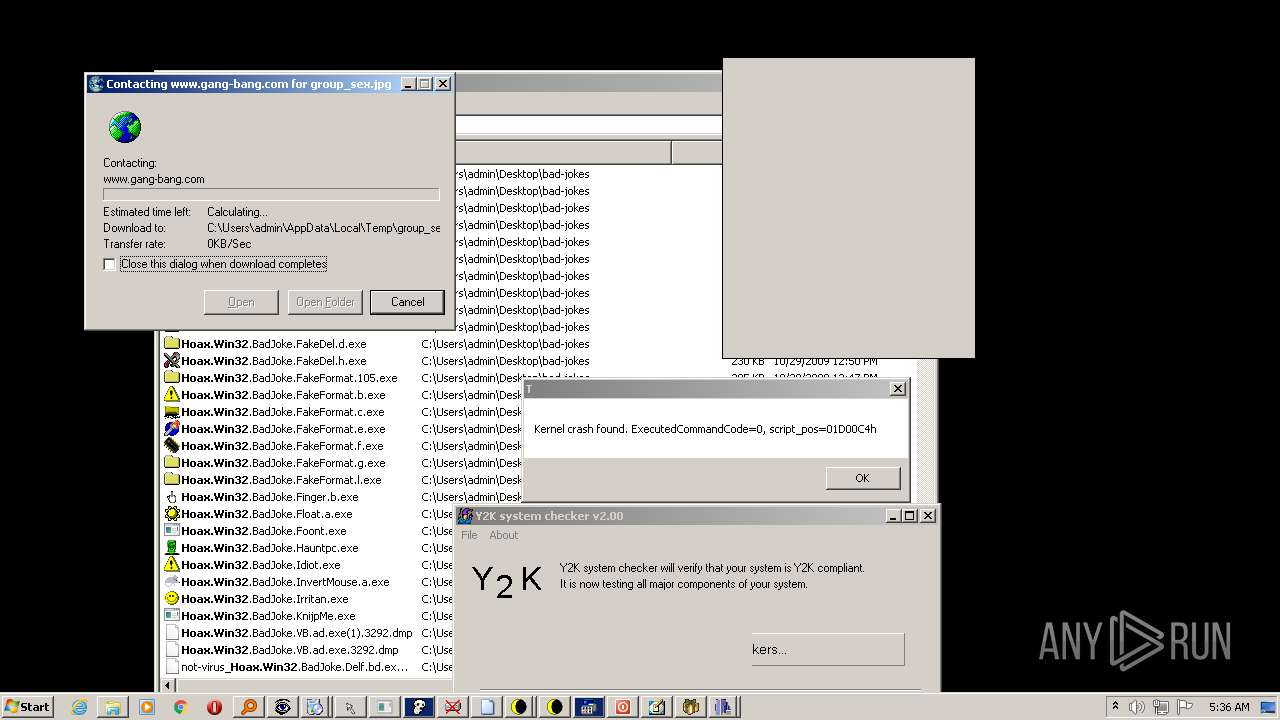
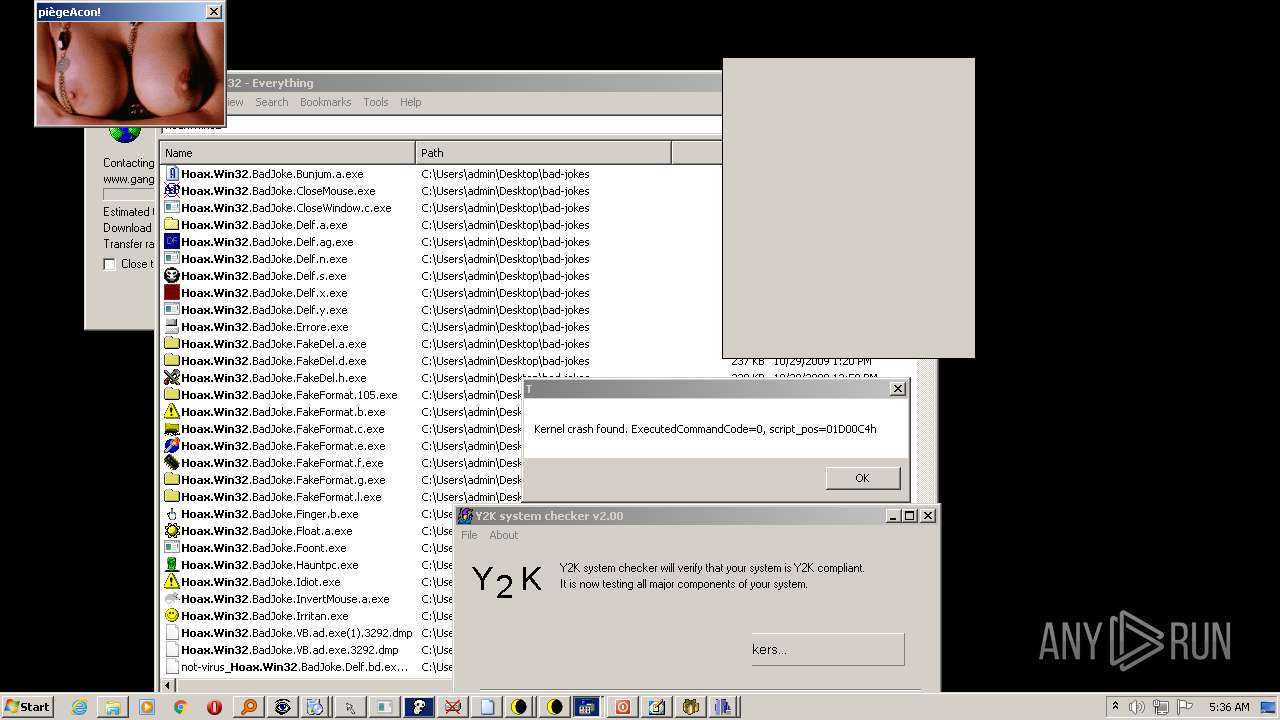
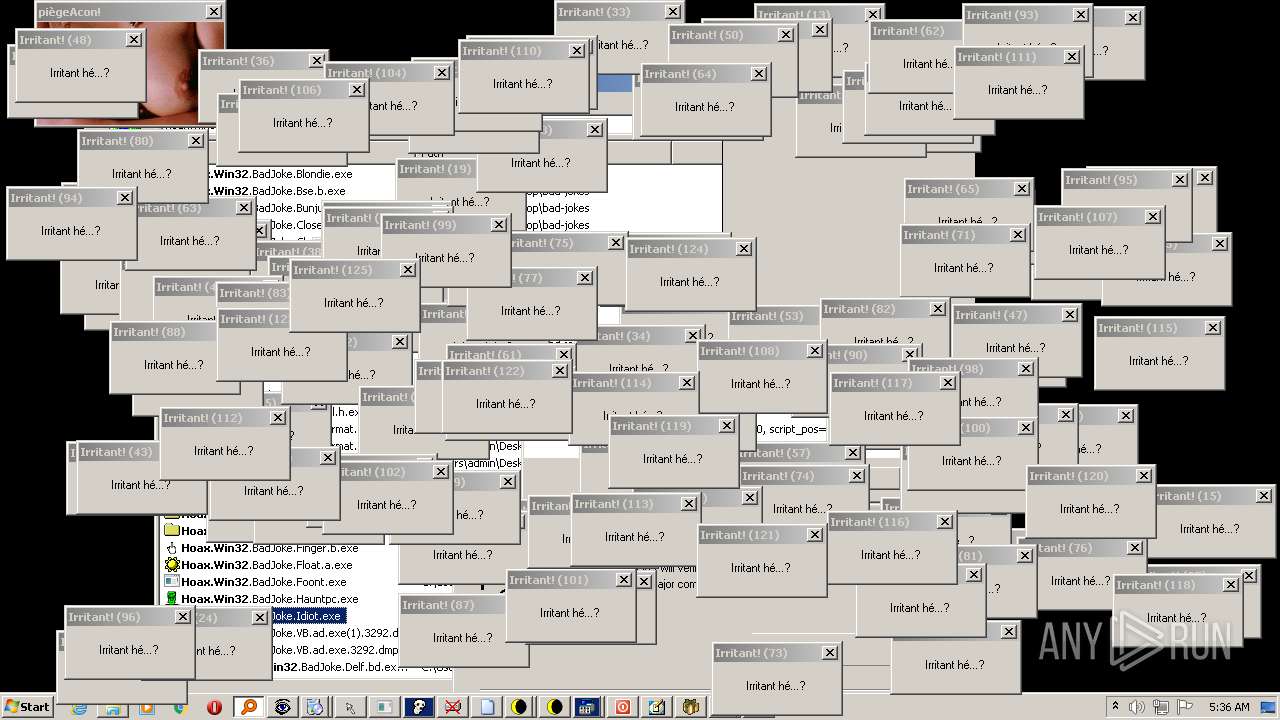
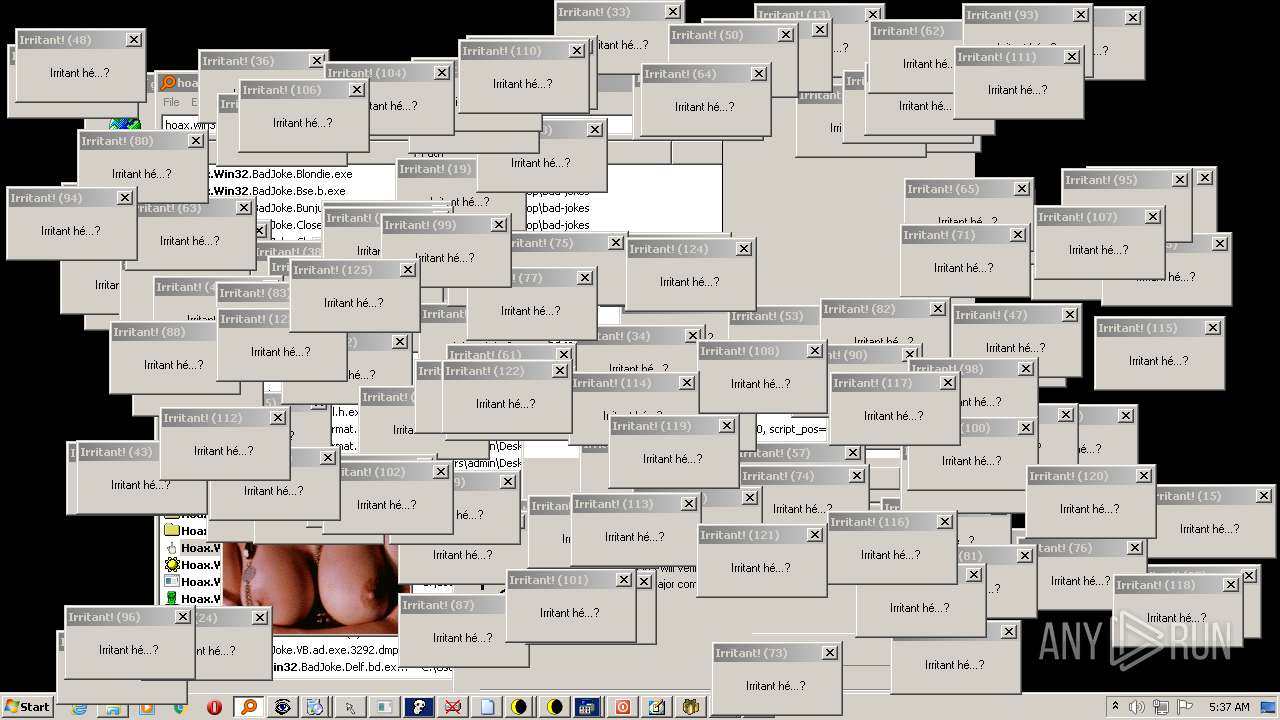
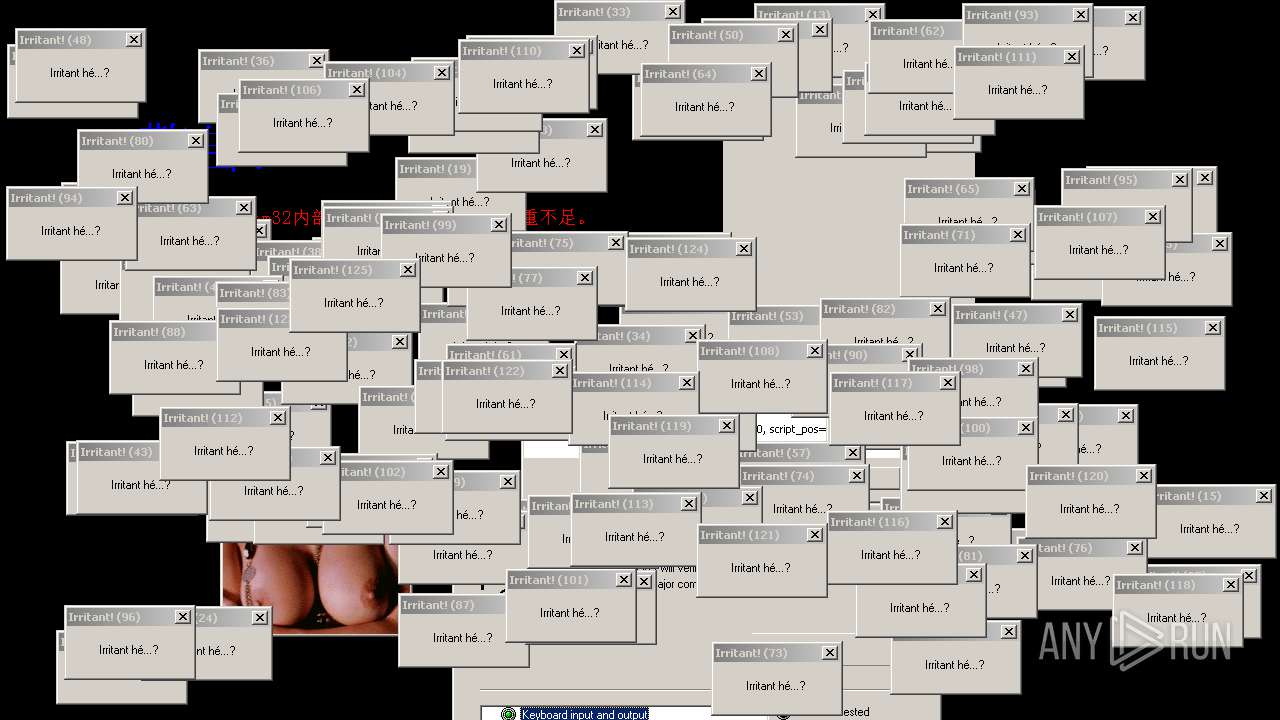
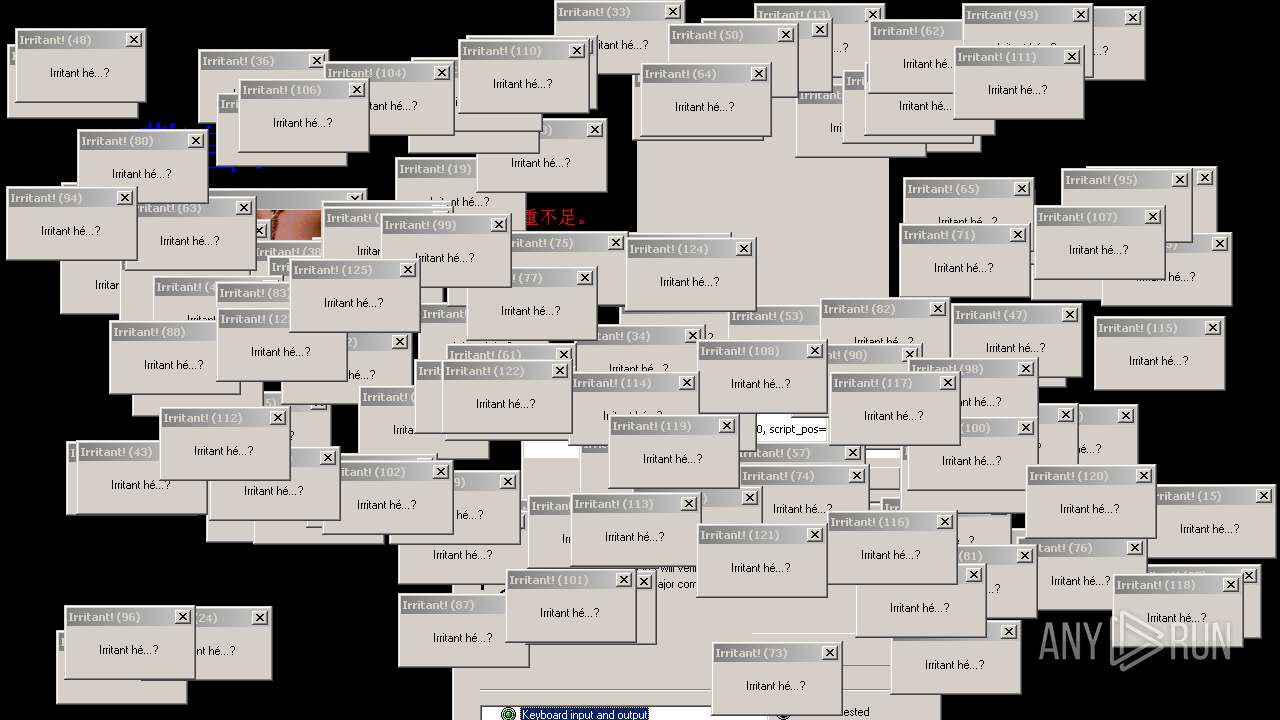
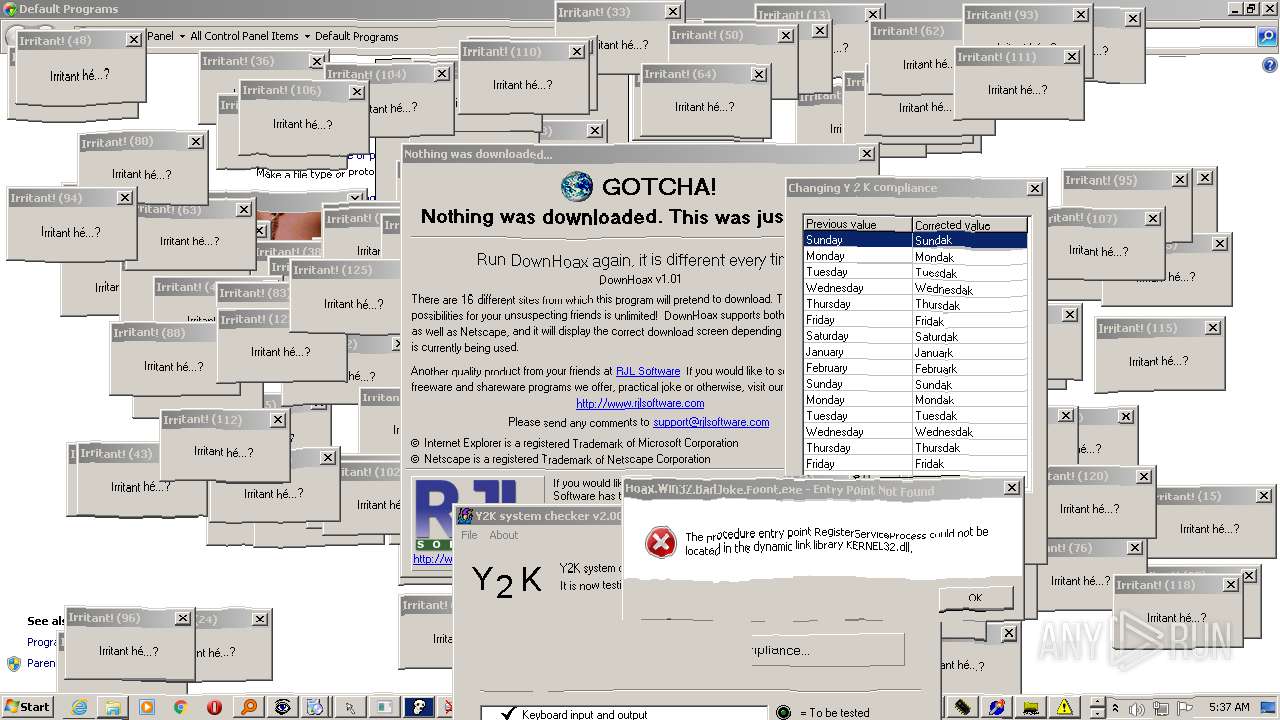
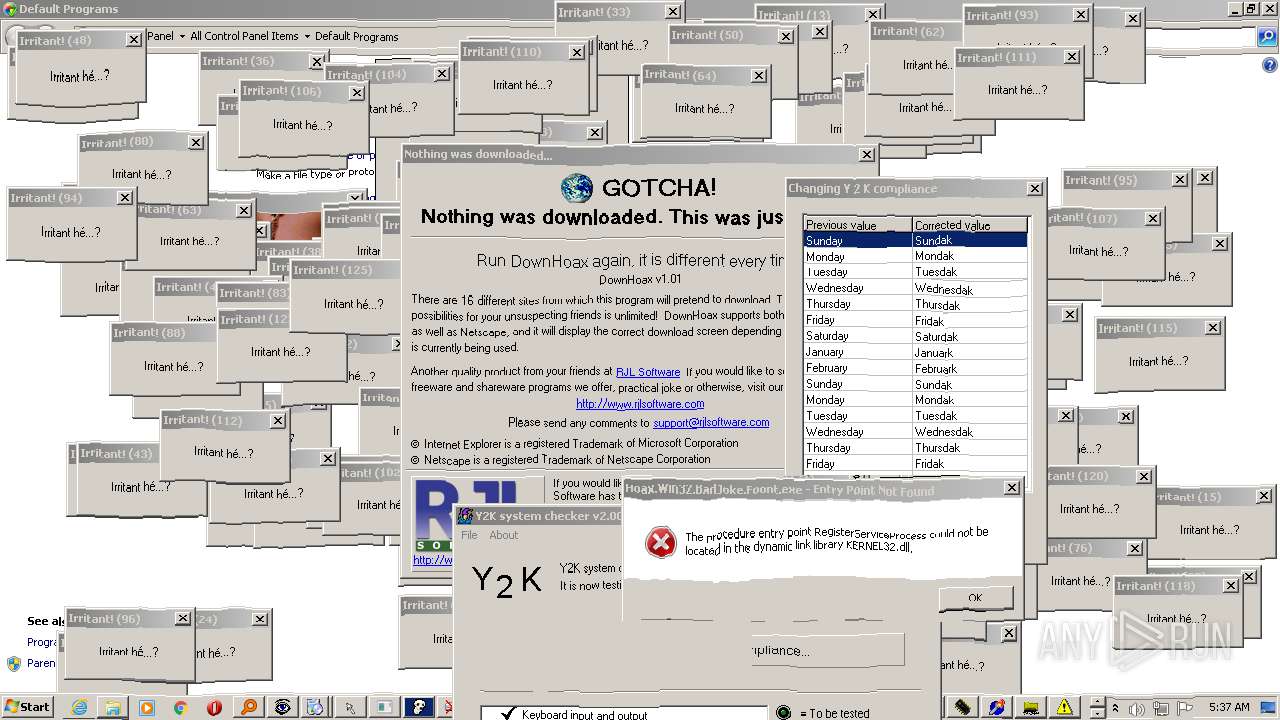
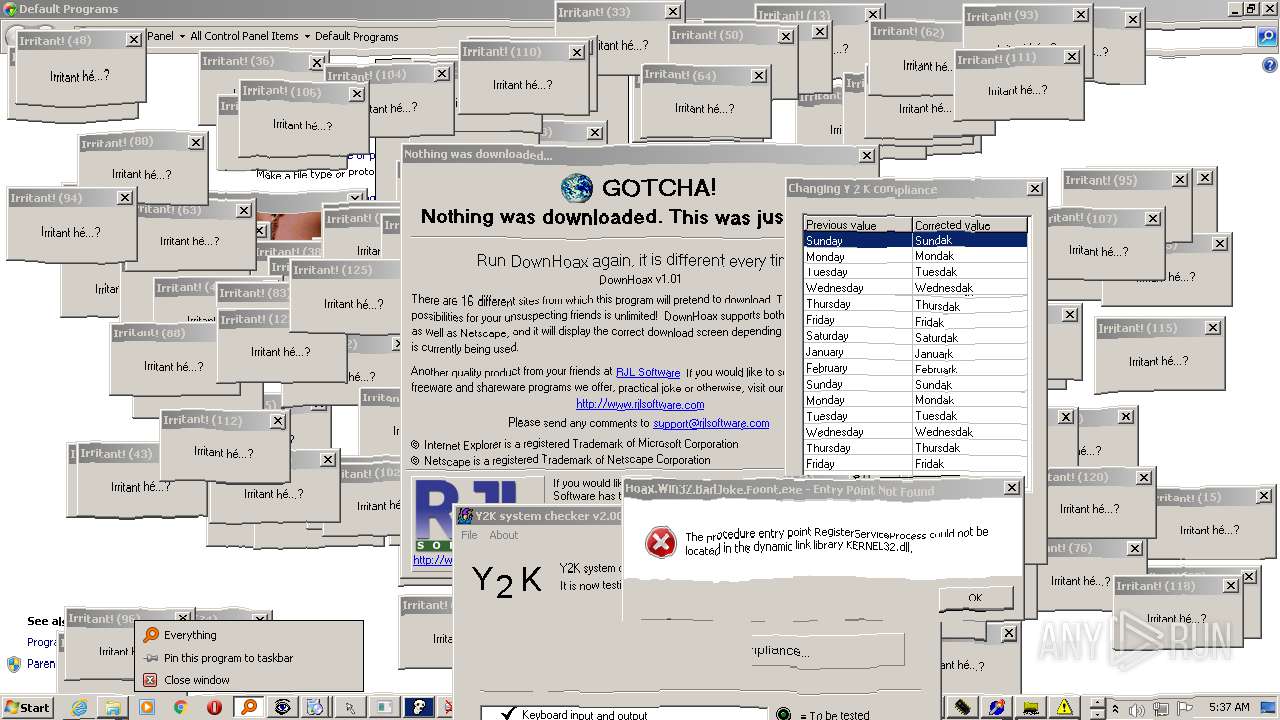
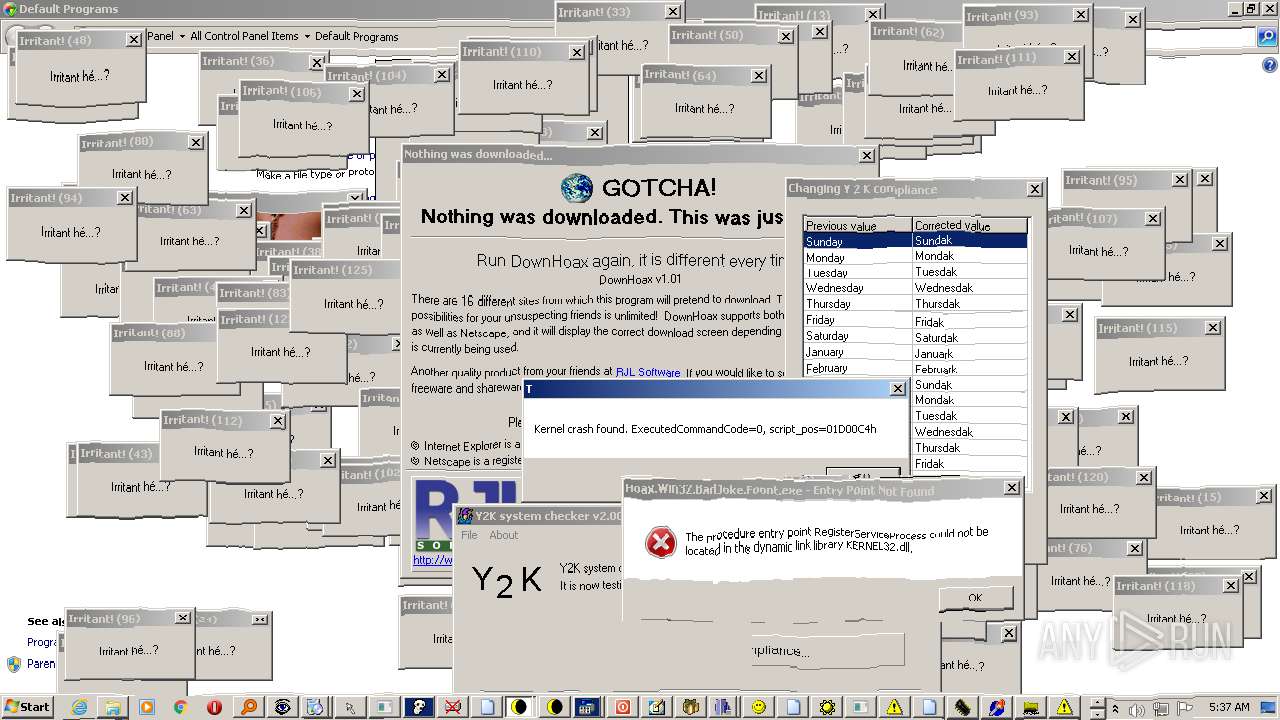
MALICIOUS
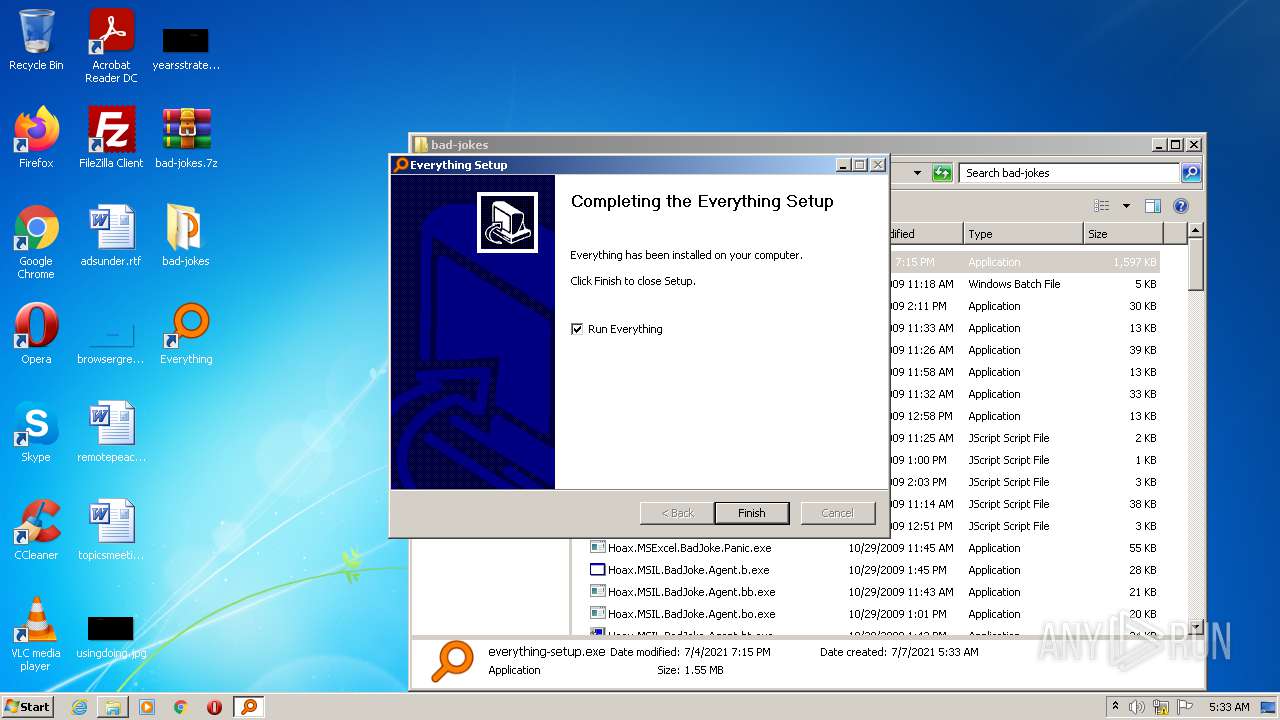
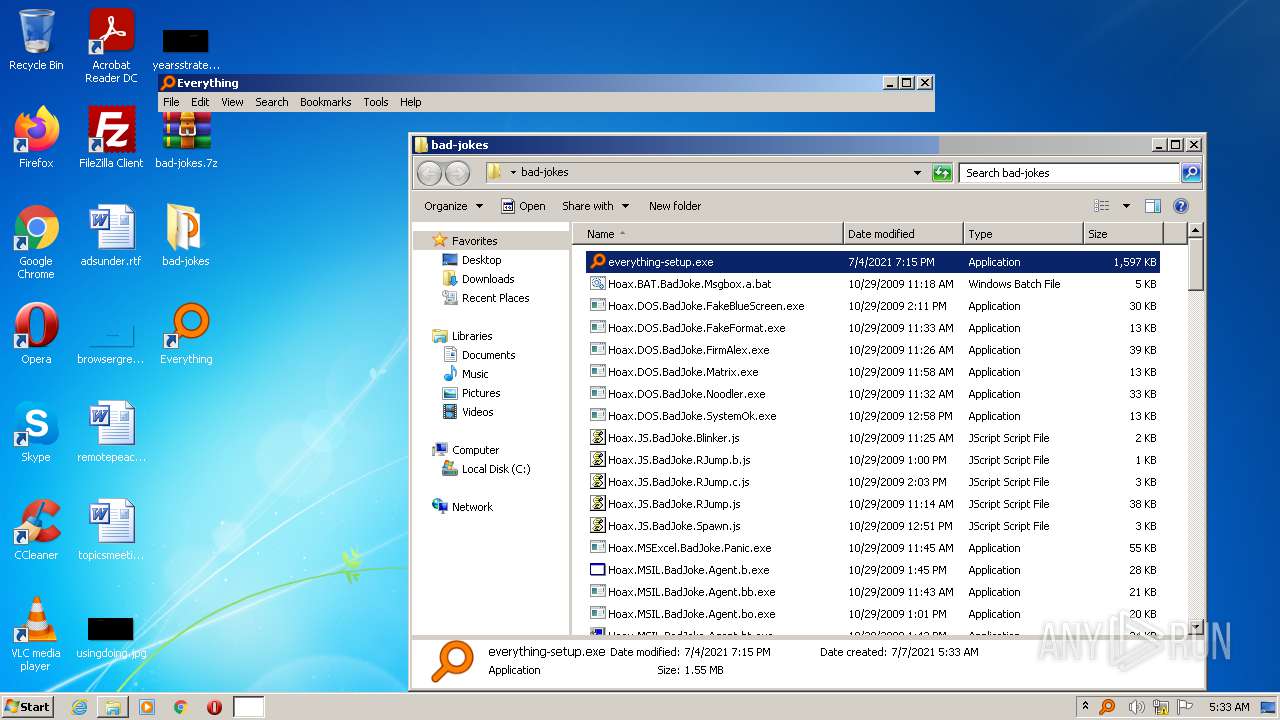
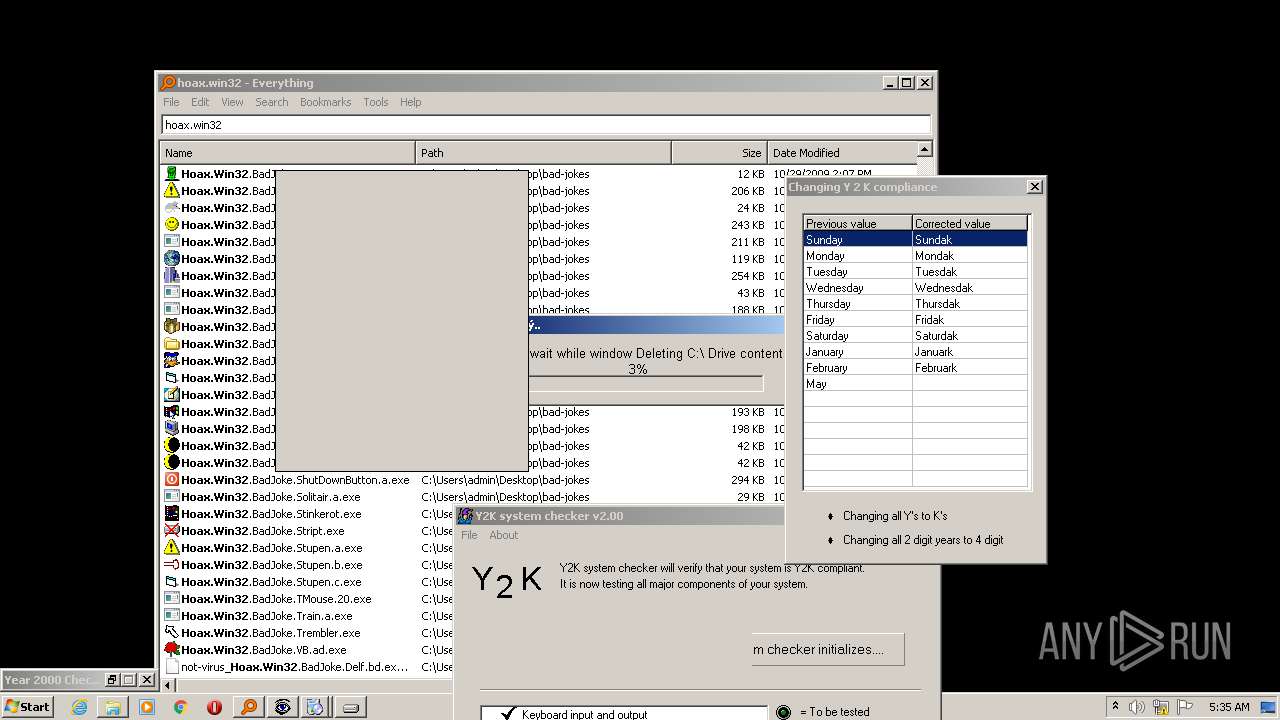
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1888)
- everything-setup.exe (PID: 3424)
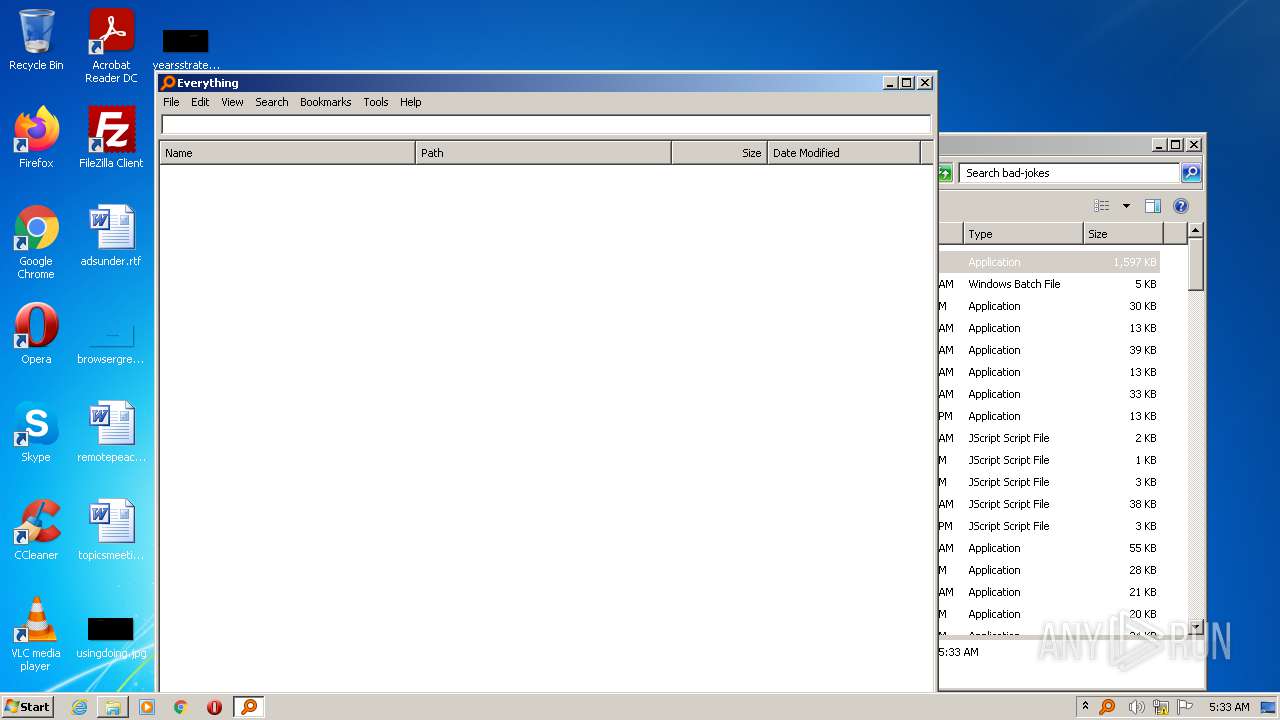
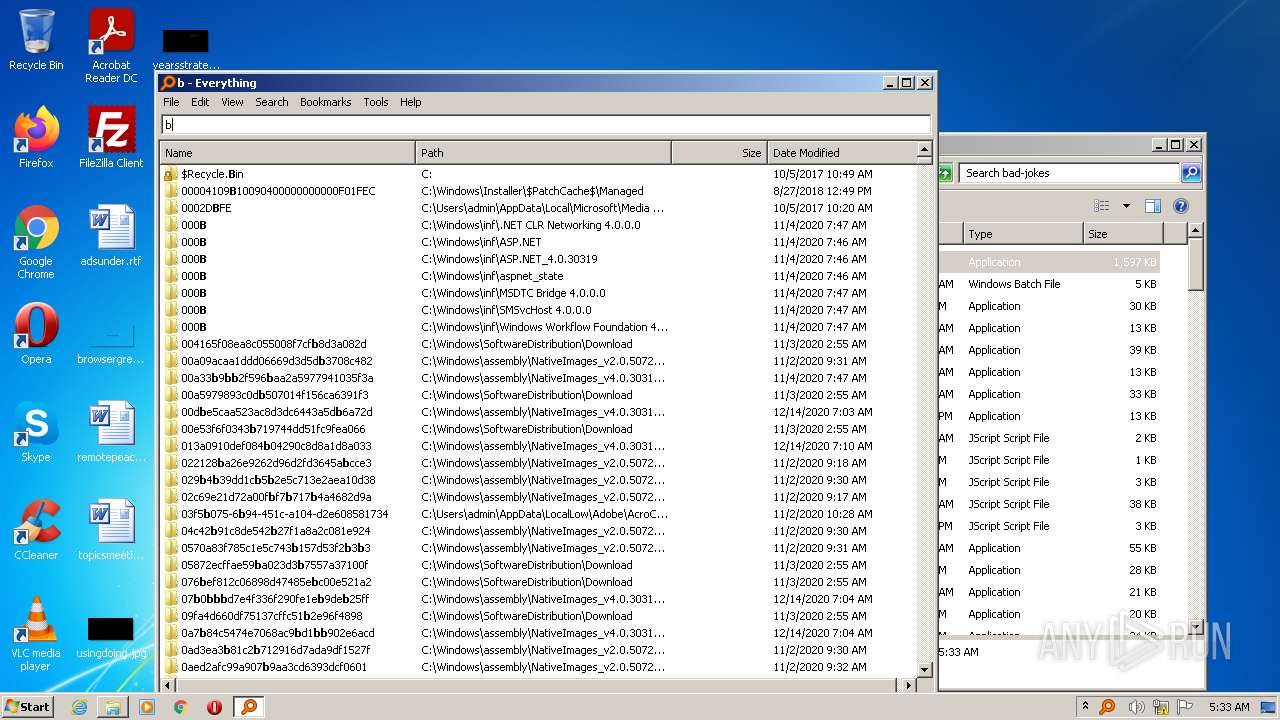
- Everything.exe (PID: 724)
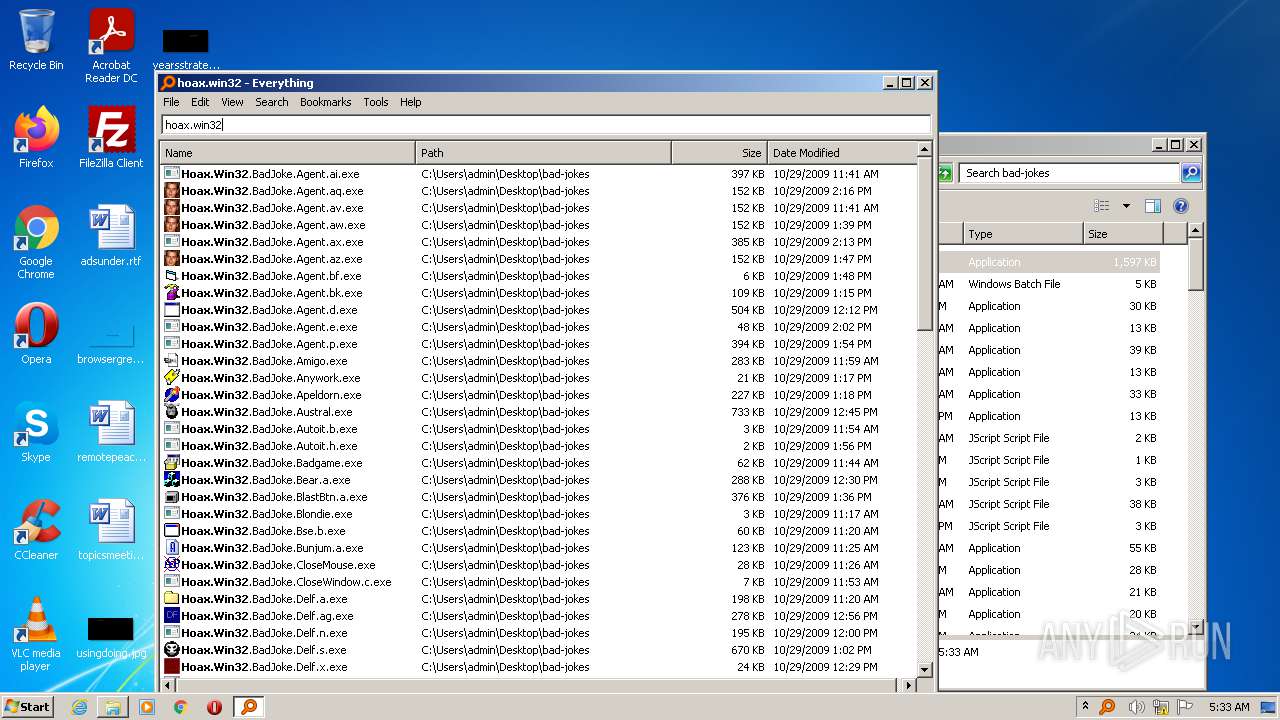
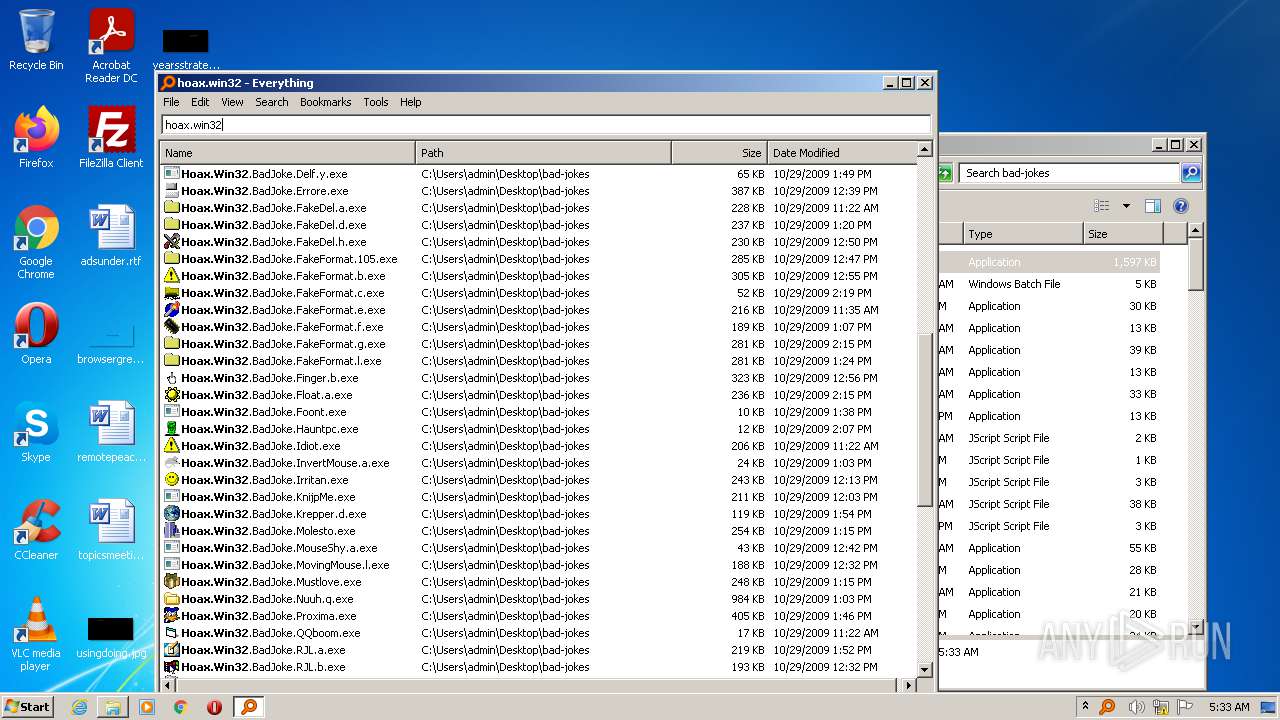
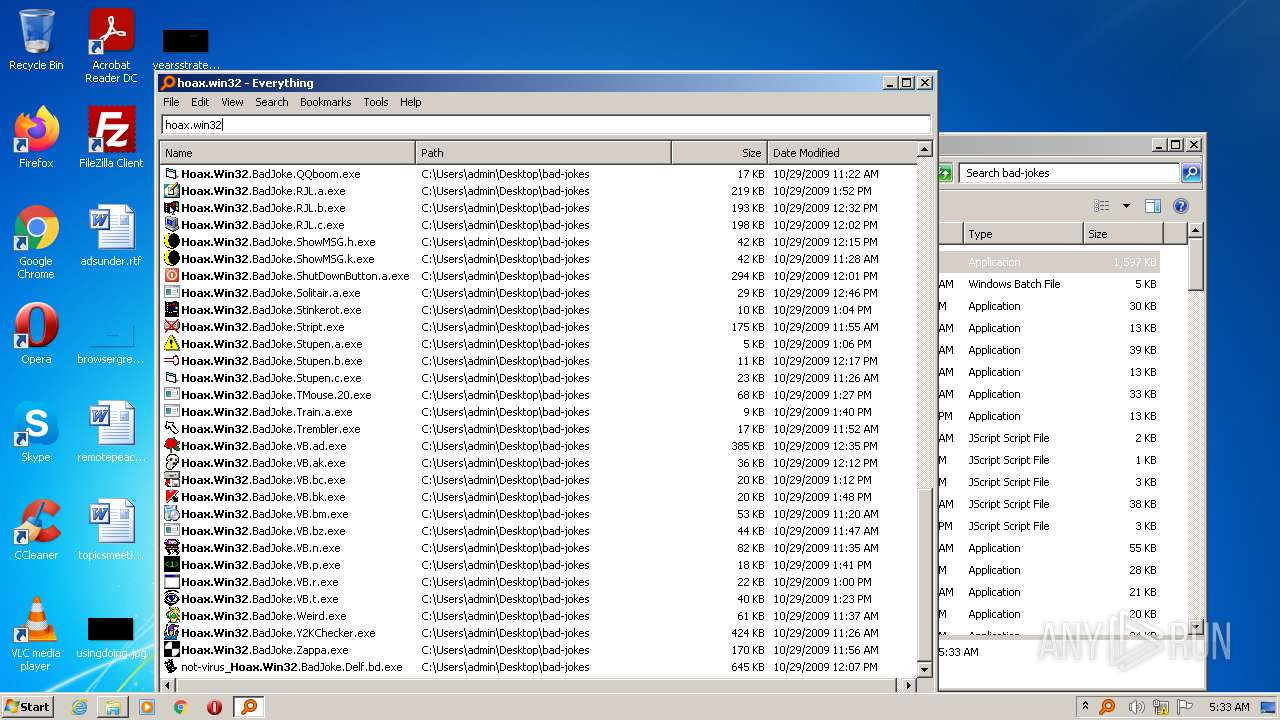
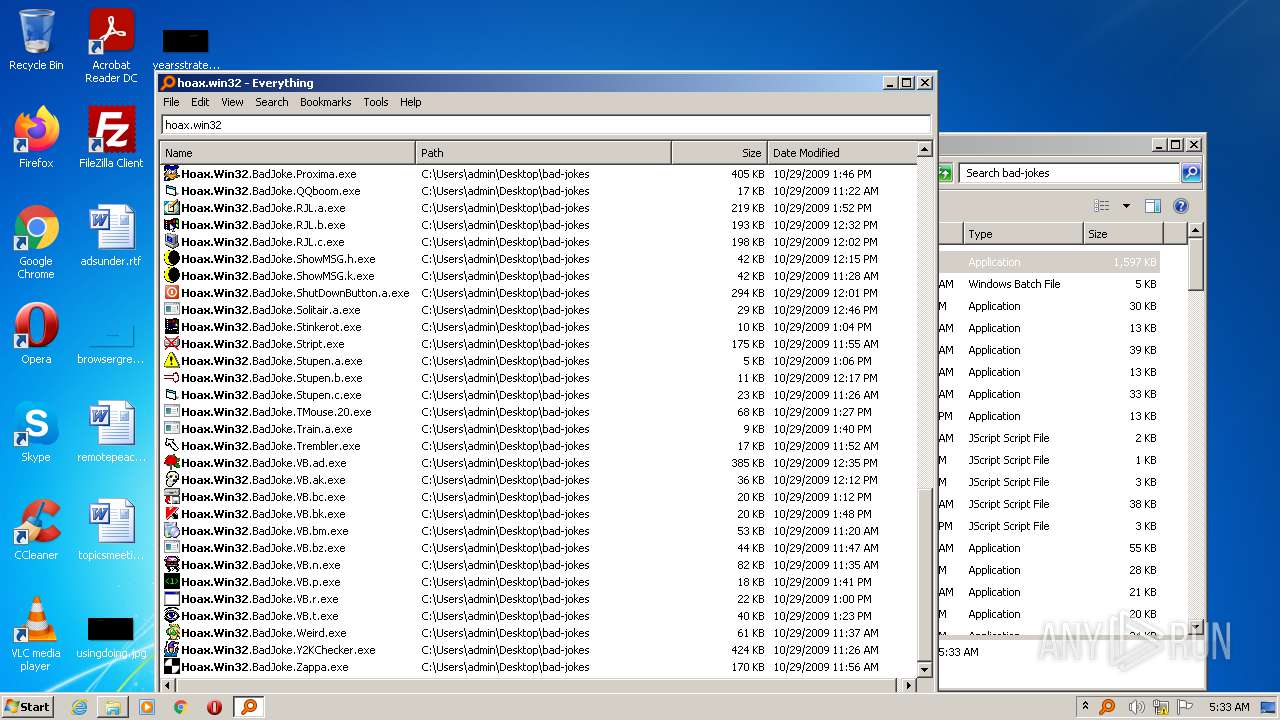
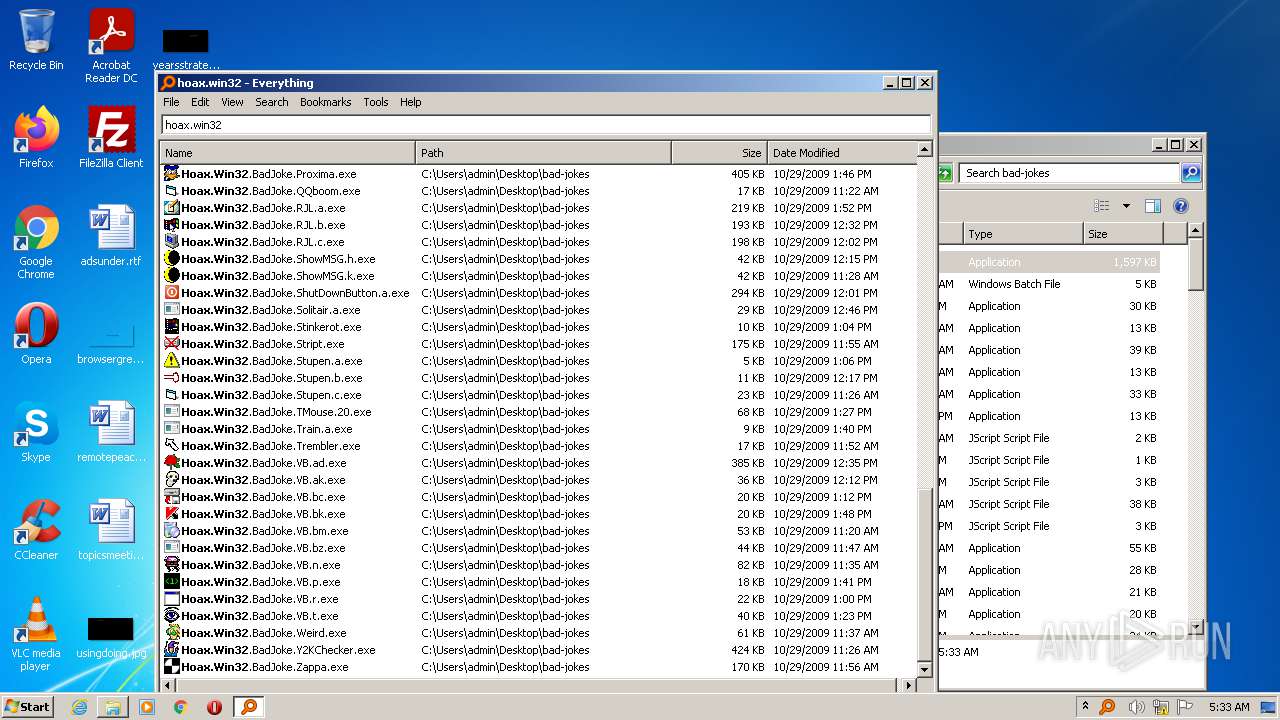
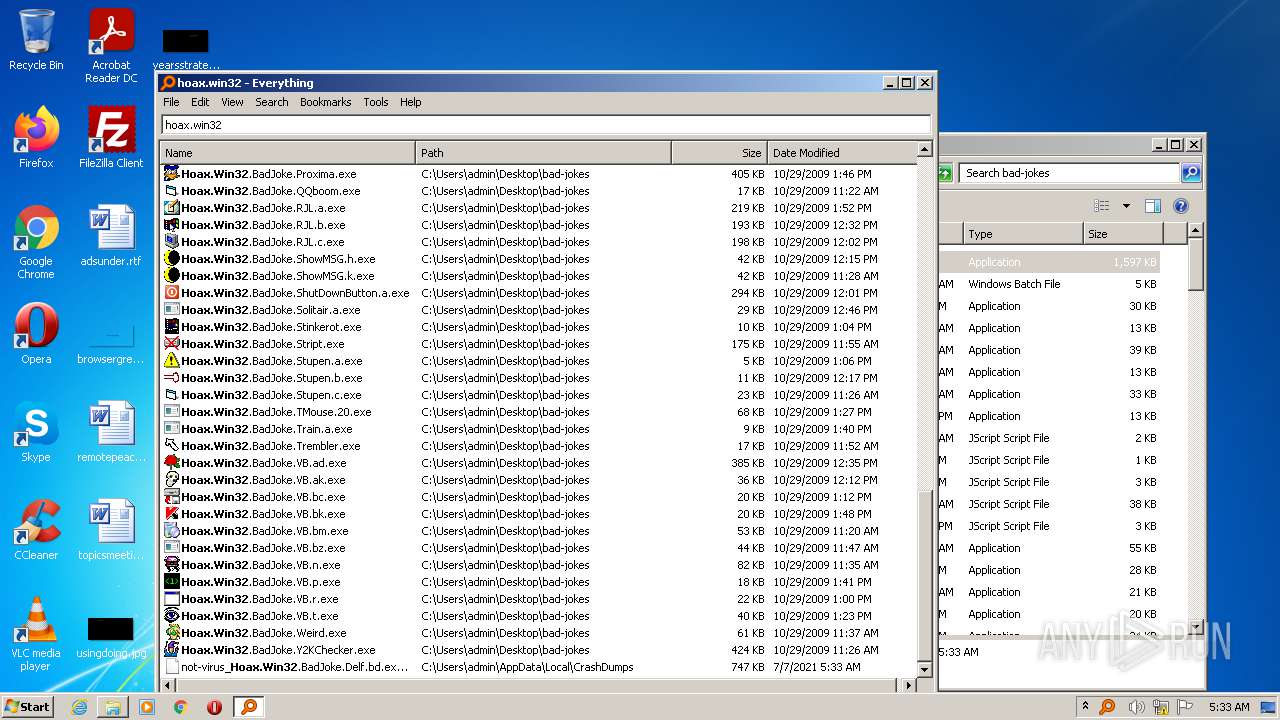
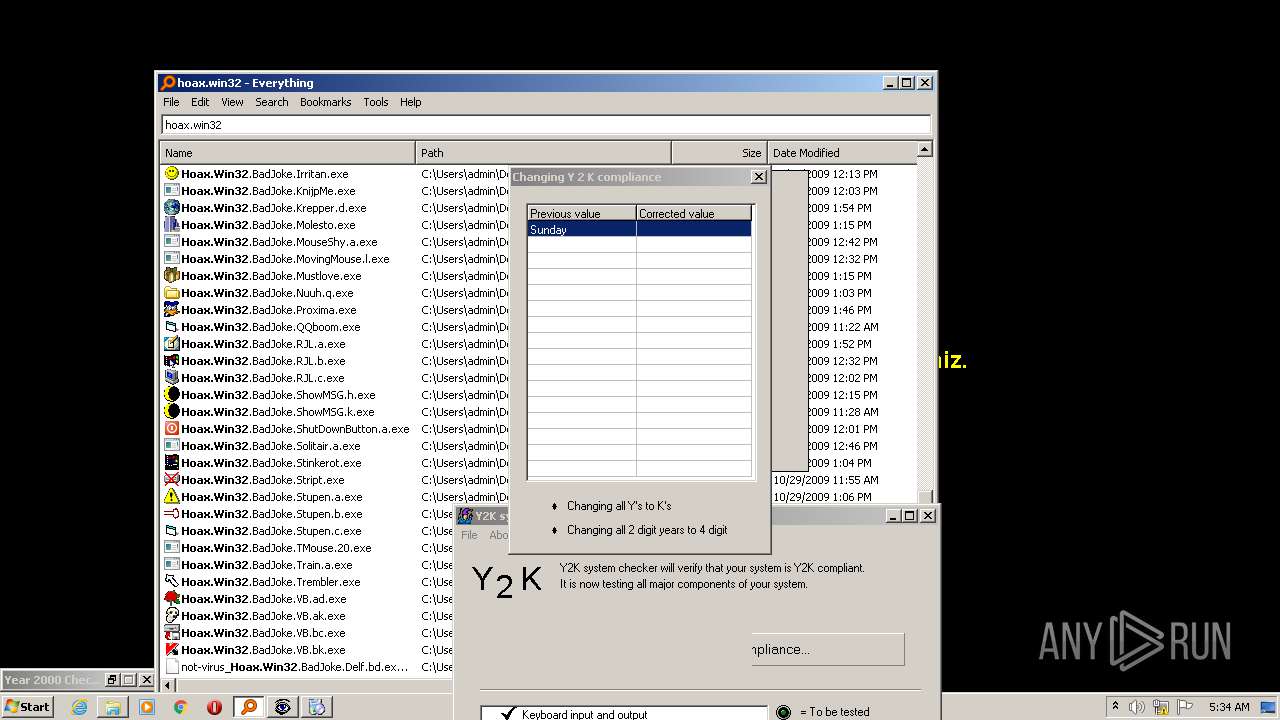
Application was dropped or rewritten from another process
- everything-setup.exe (PID: 3424)
- Everything.exe (PID: 3796)
- Everything.exe (PID: 2948)
- Everything.exe (PID: 3612)
- Everything.exe (PID: 2360)
- Everything.exe (PID: 3912)
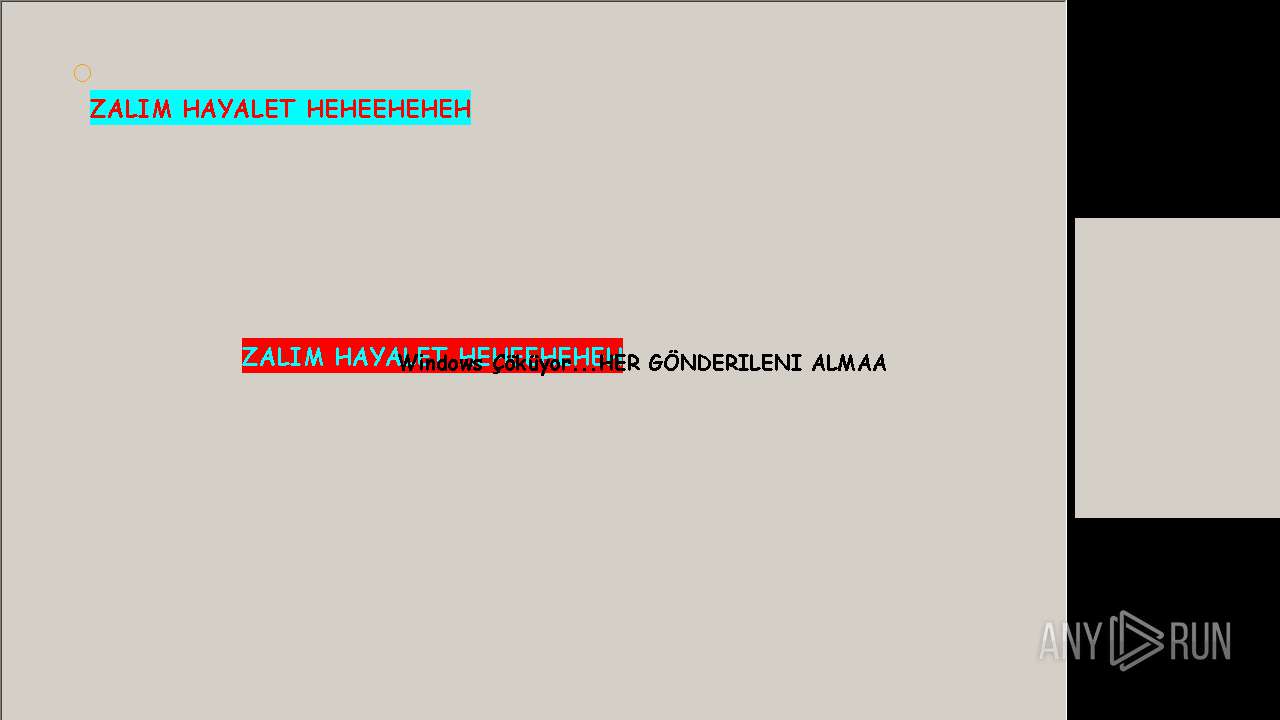
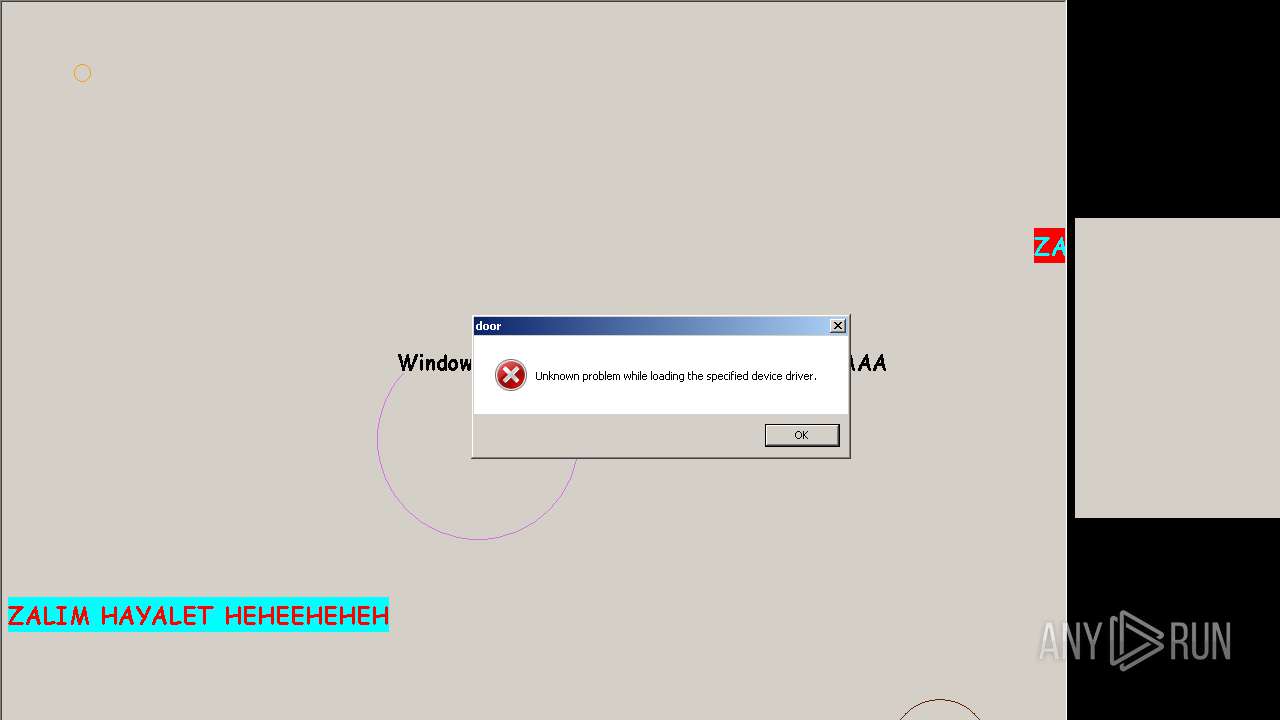
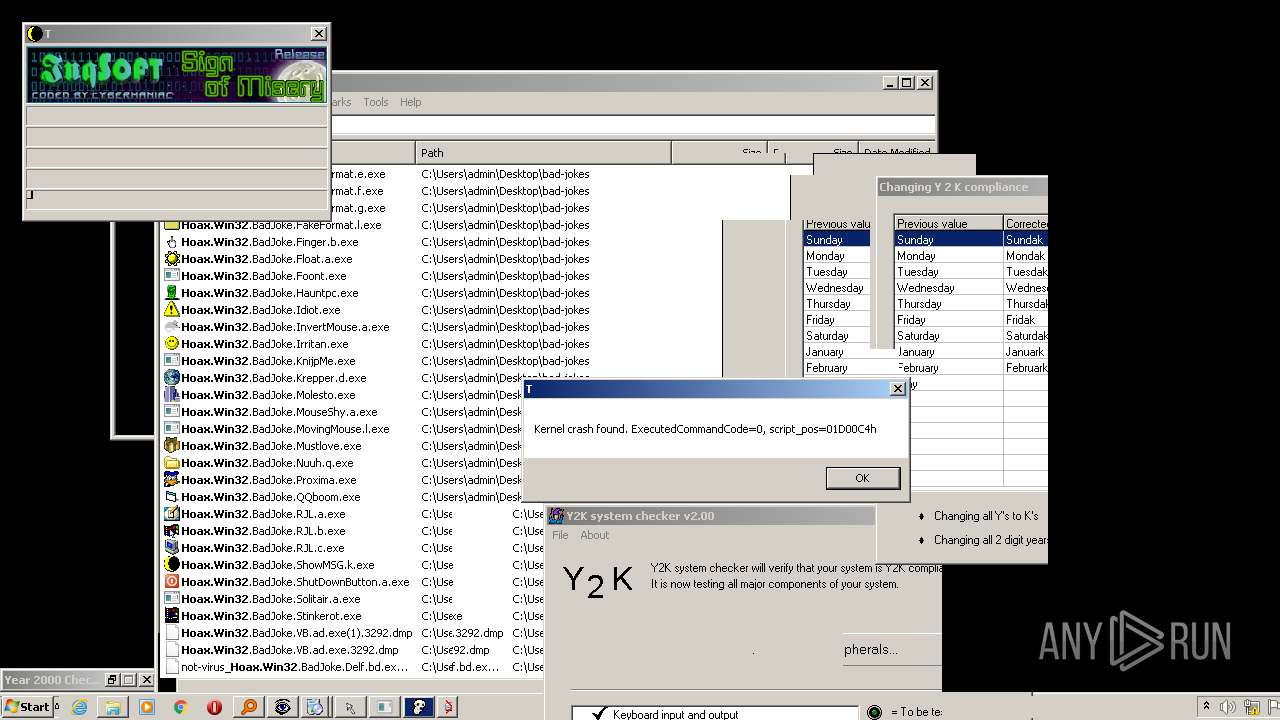
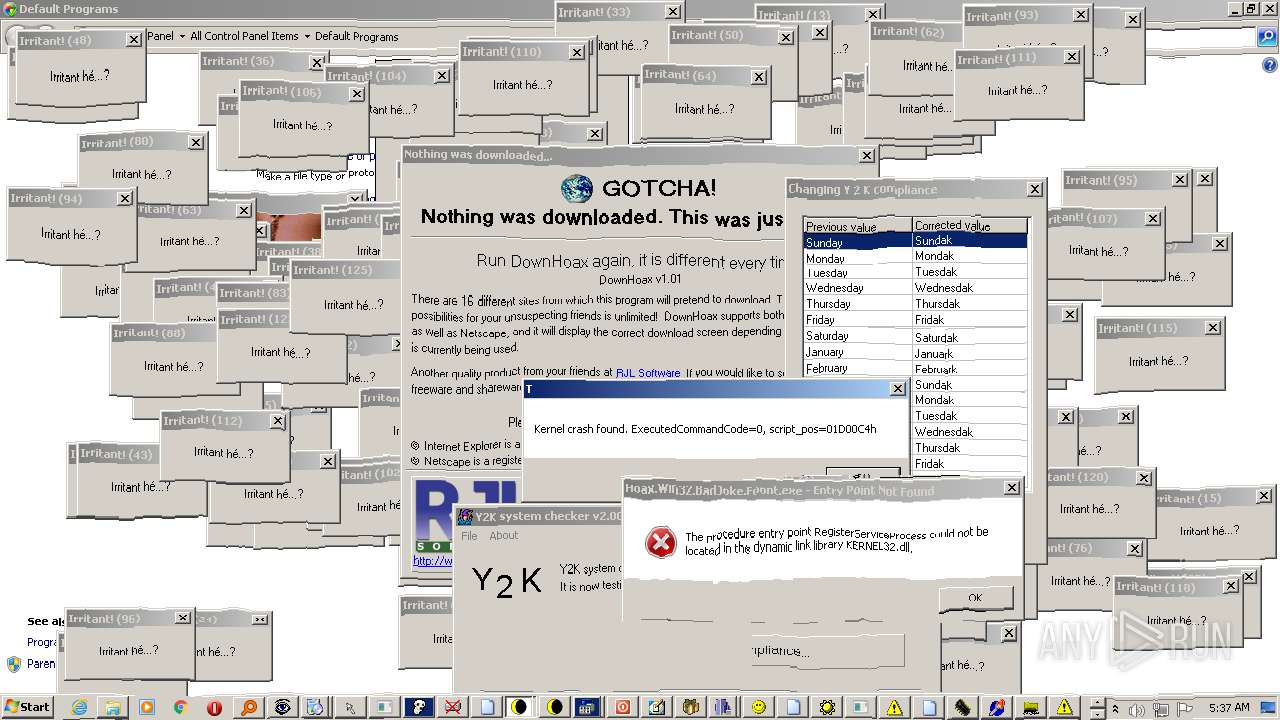
- Hoax.Win32.BadJoke.Weird.exe (PID: 2816)
- Everything.exe (PID: 724)
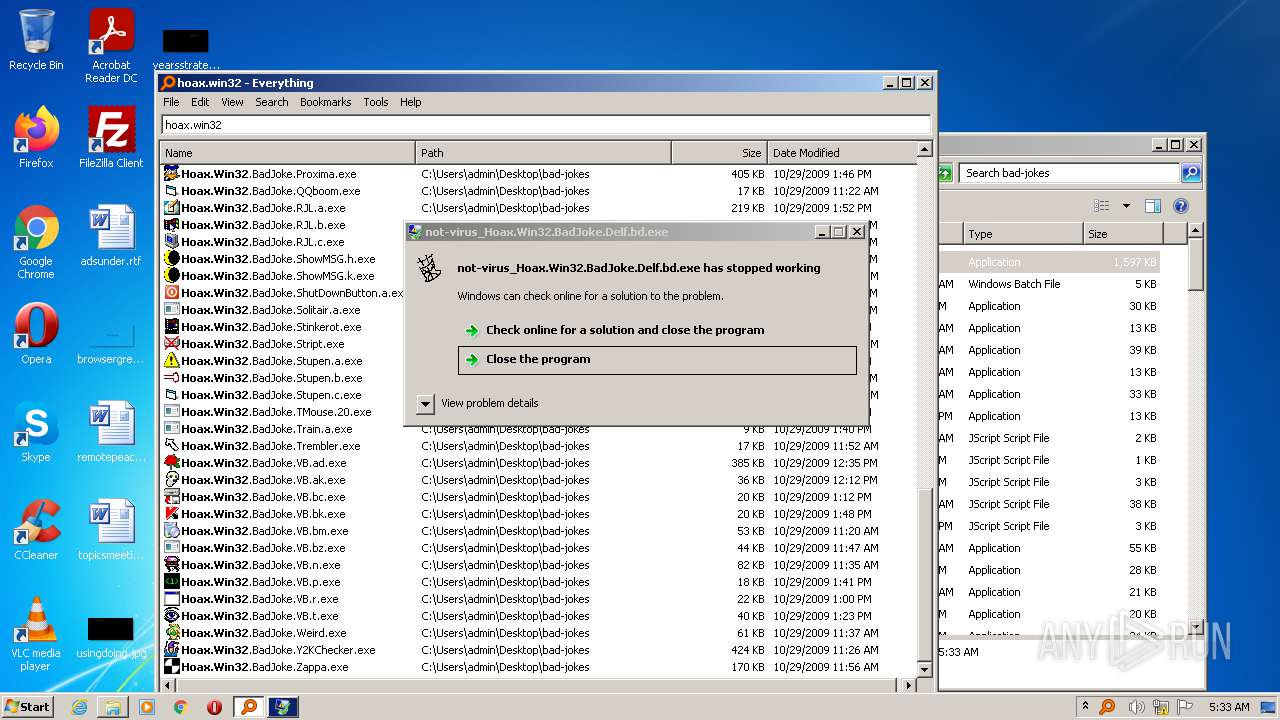
- not-virus_Hoax.Win32.BadJoke.Delf.bd.exe (PID: 3940)
- Hoax.Win32.BadJoke.Zappa.exe (PID: 2556)
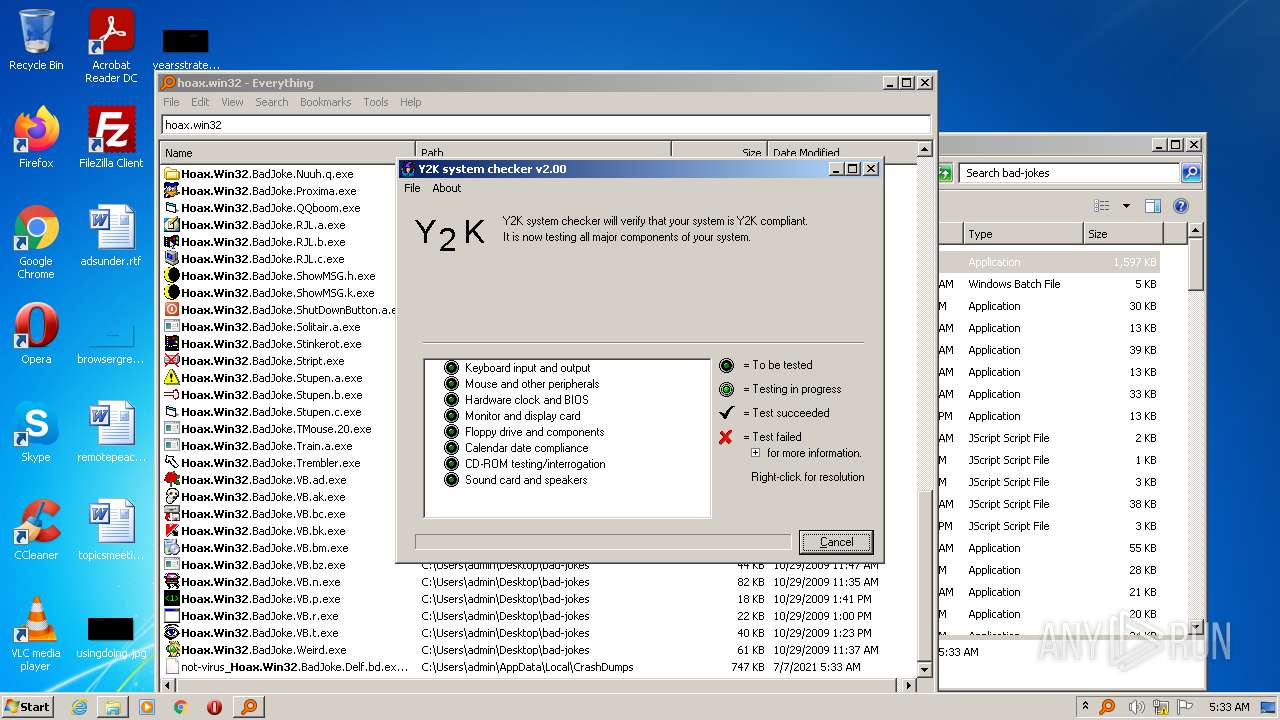
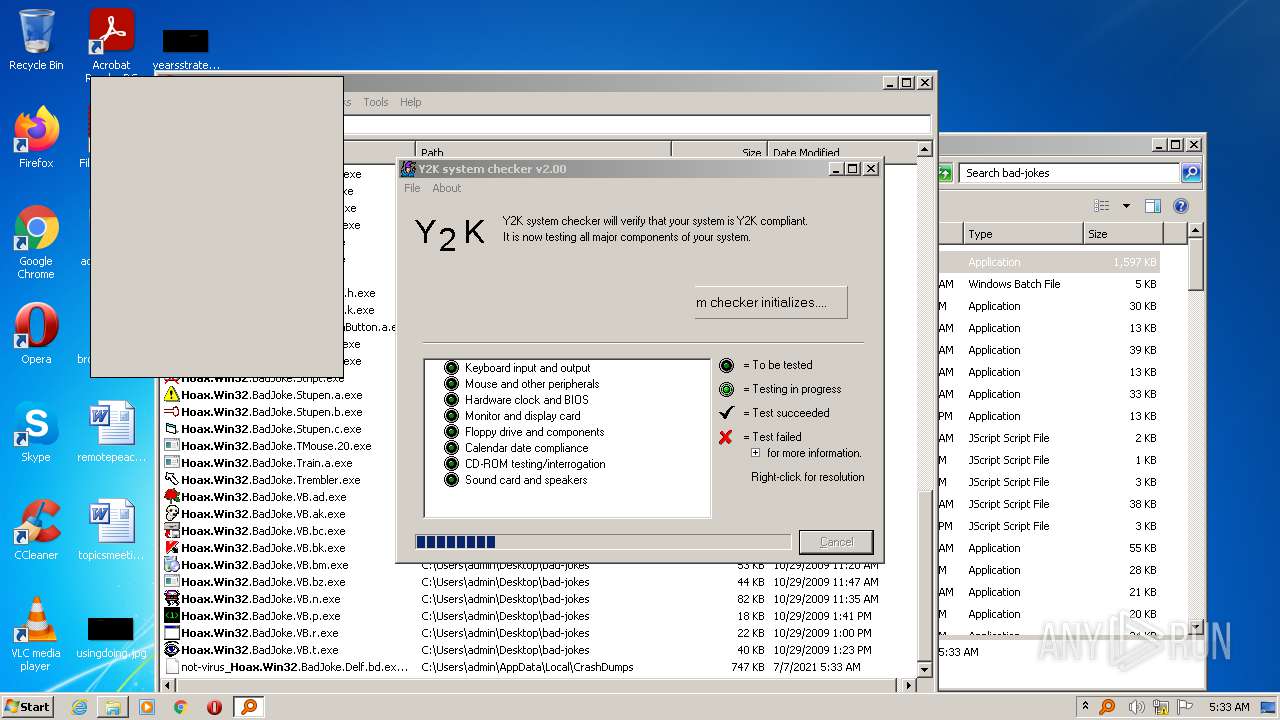
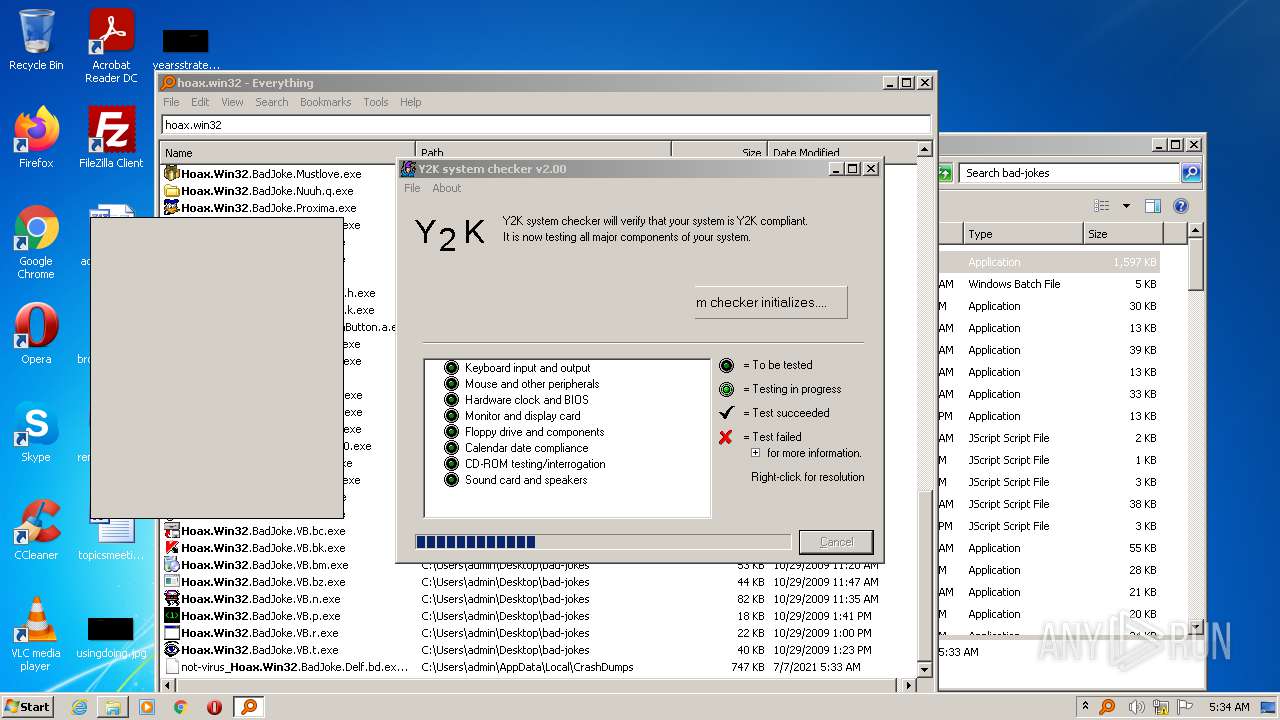
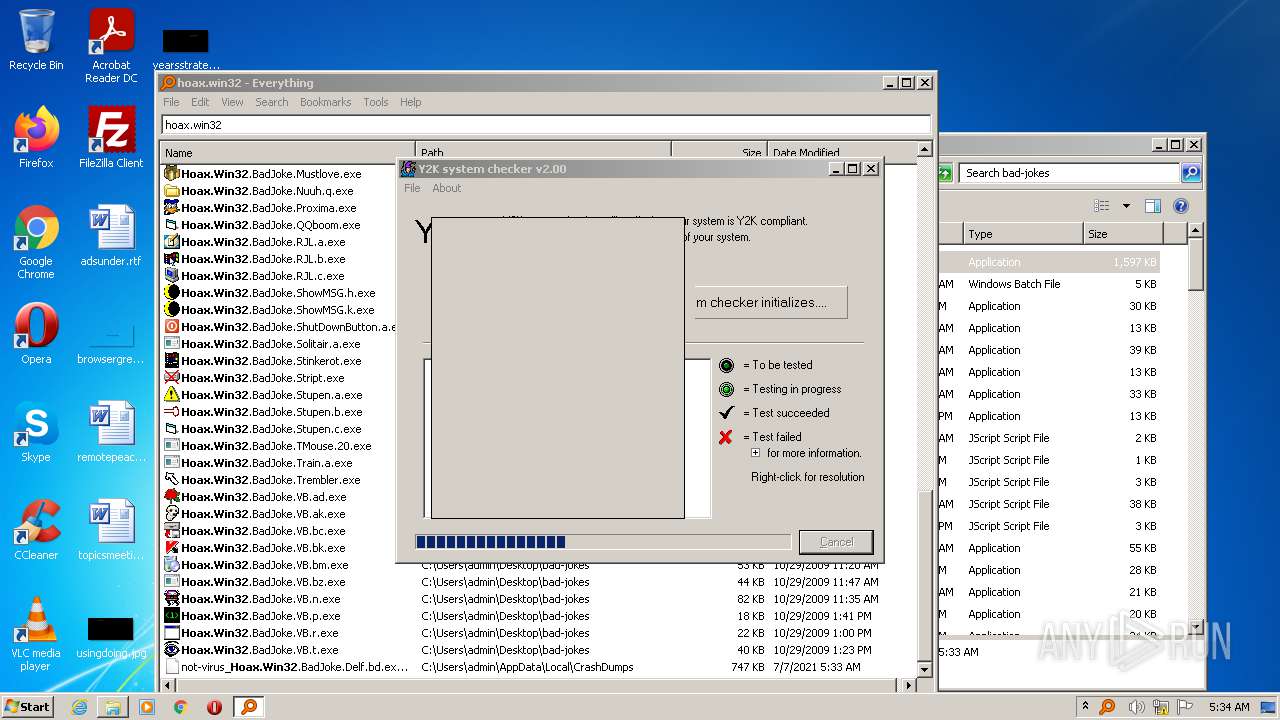
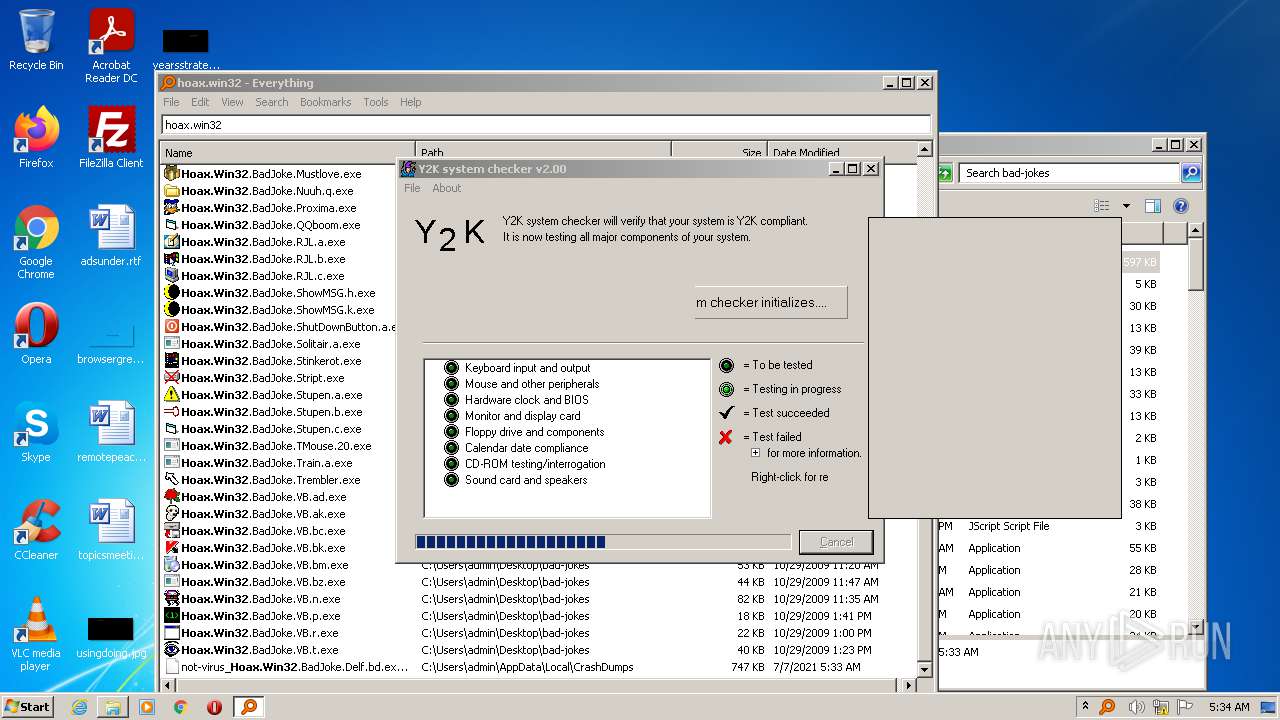
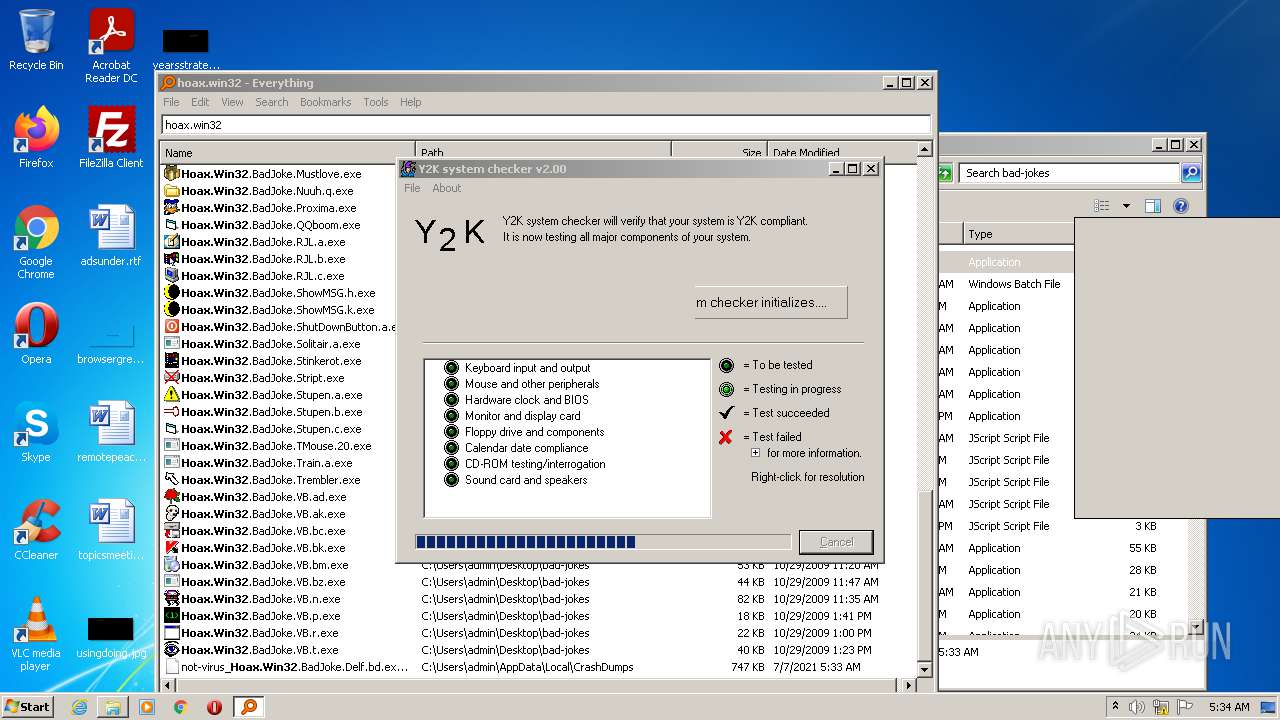
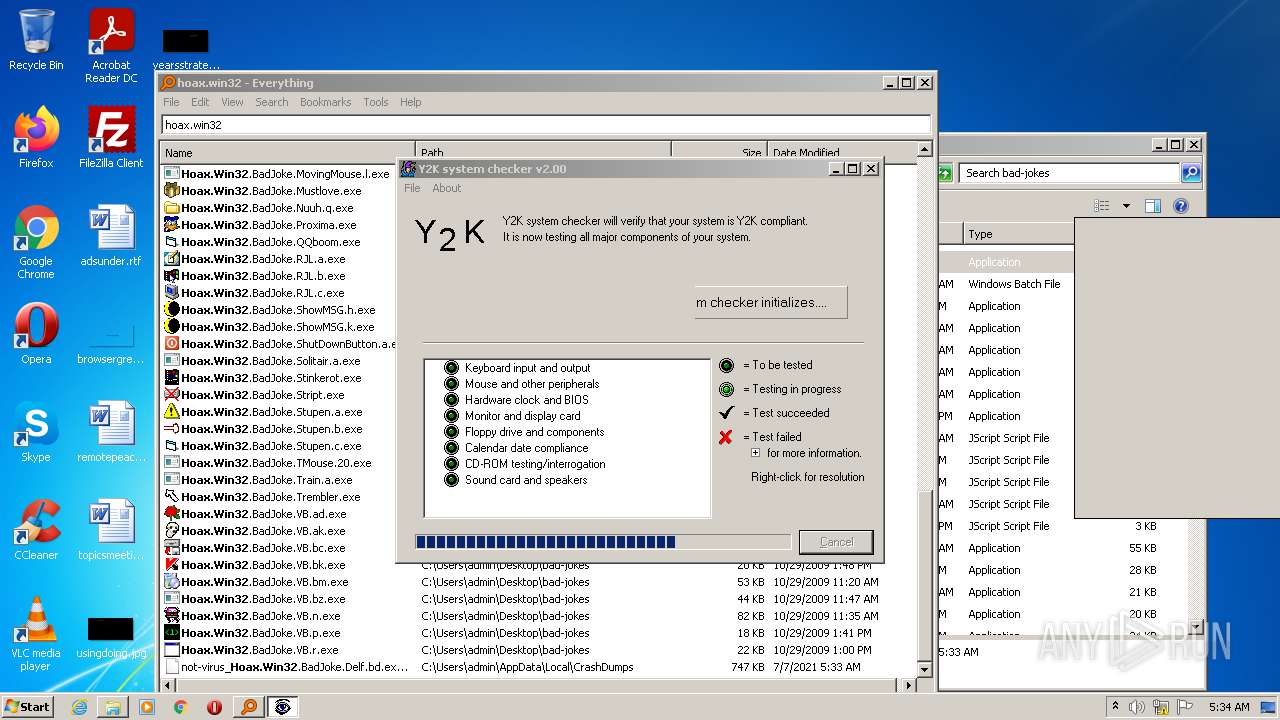
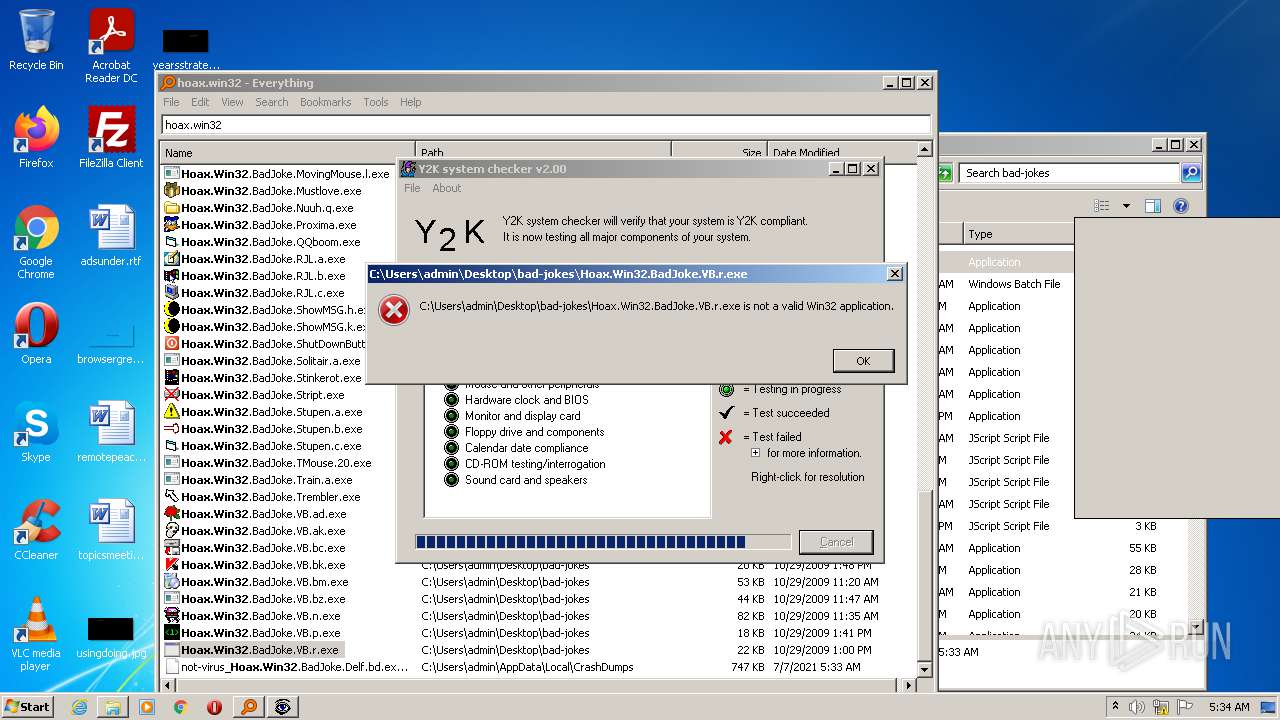
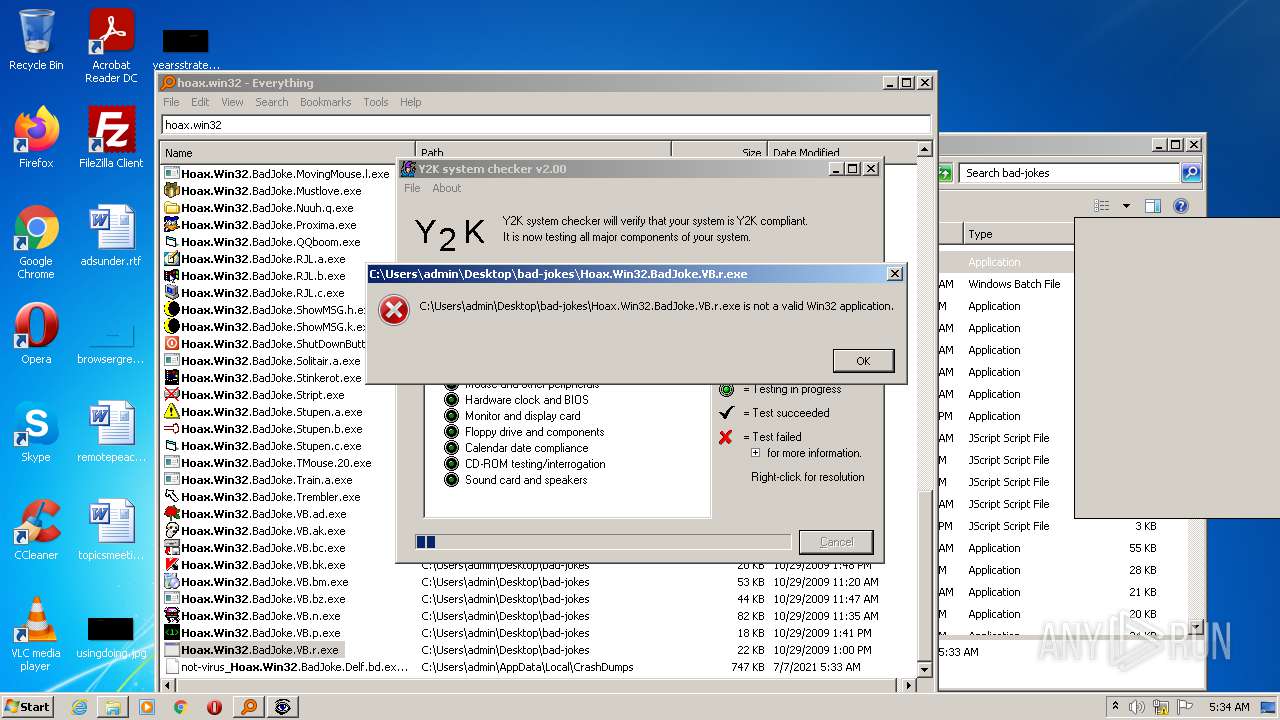
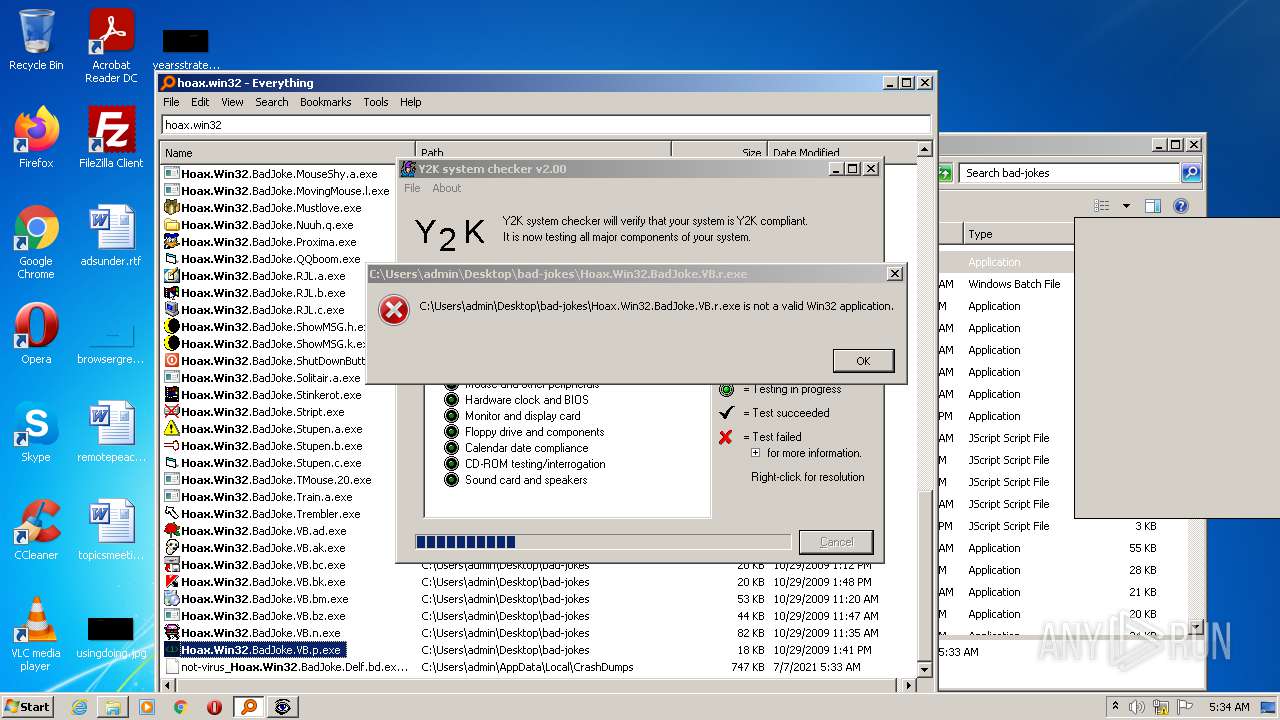
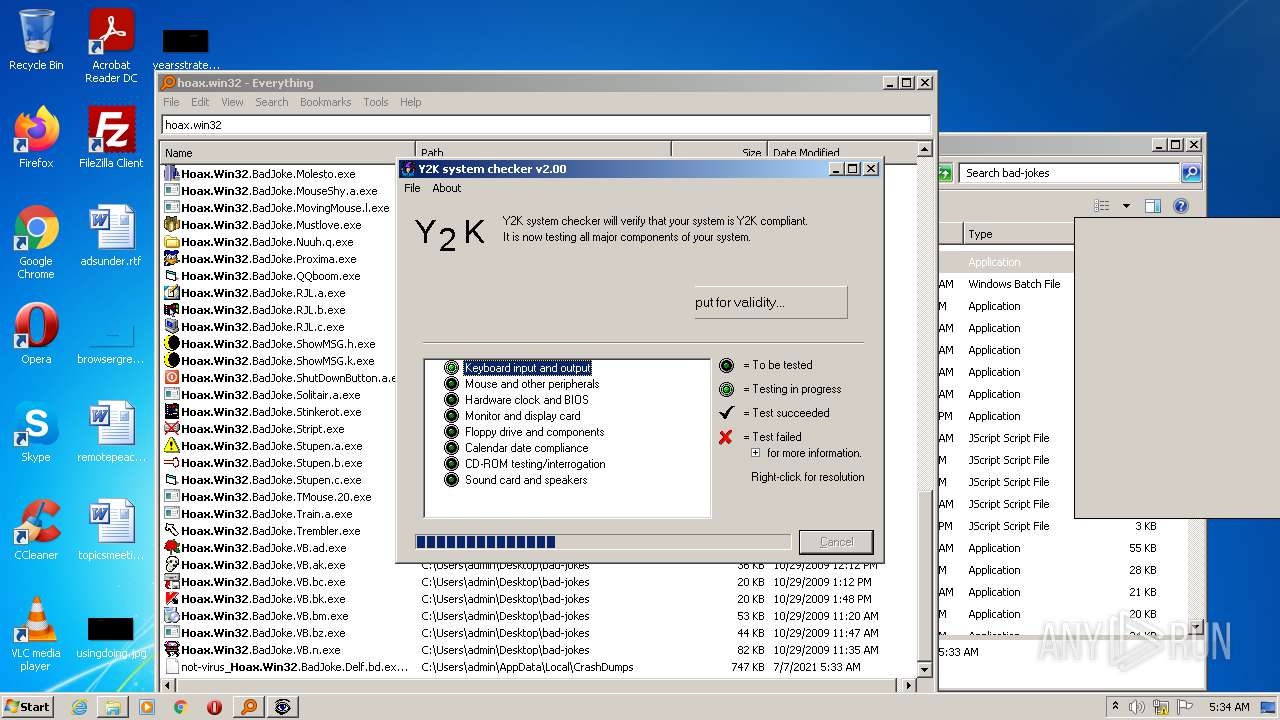
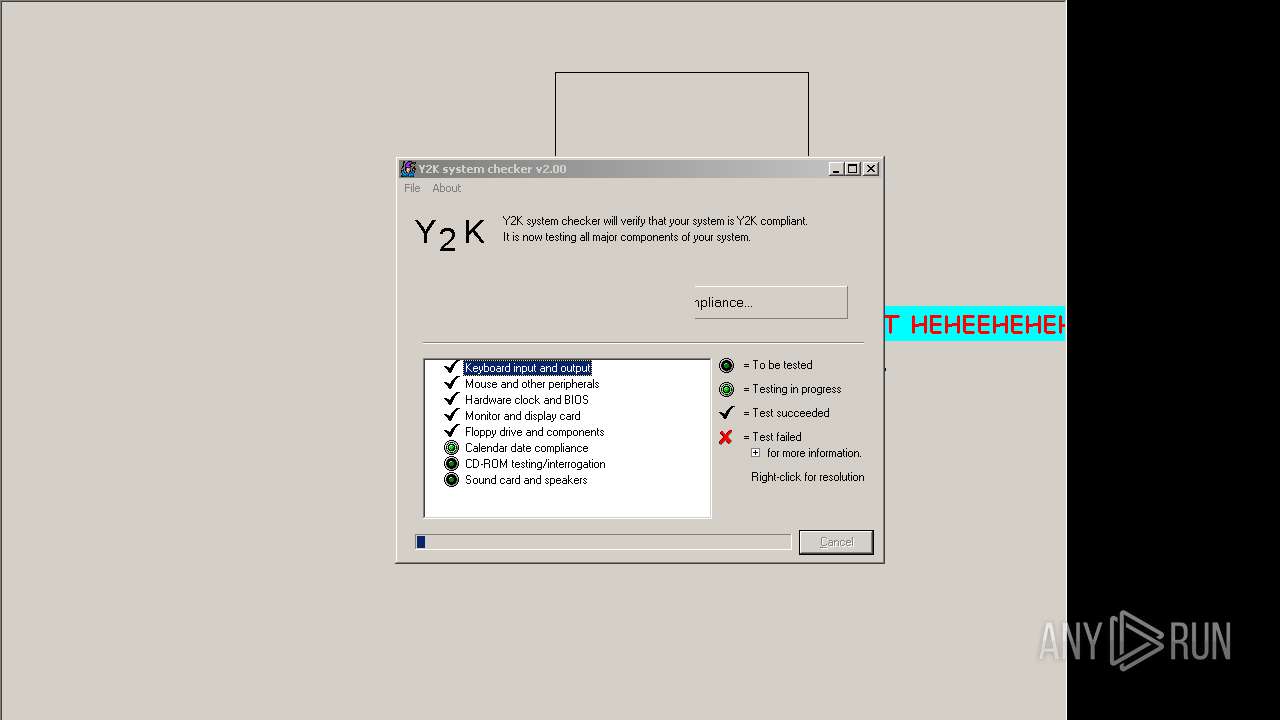
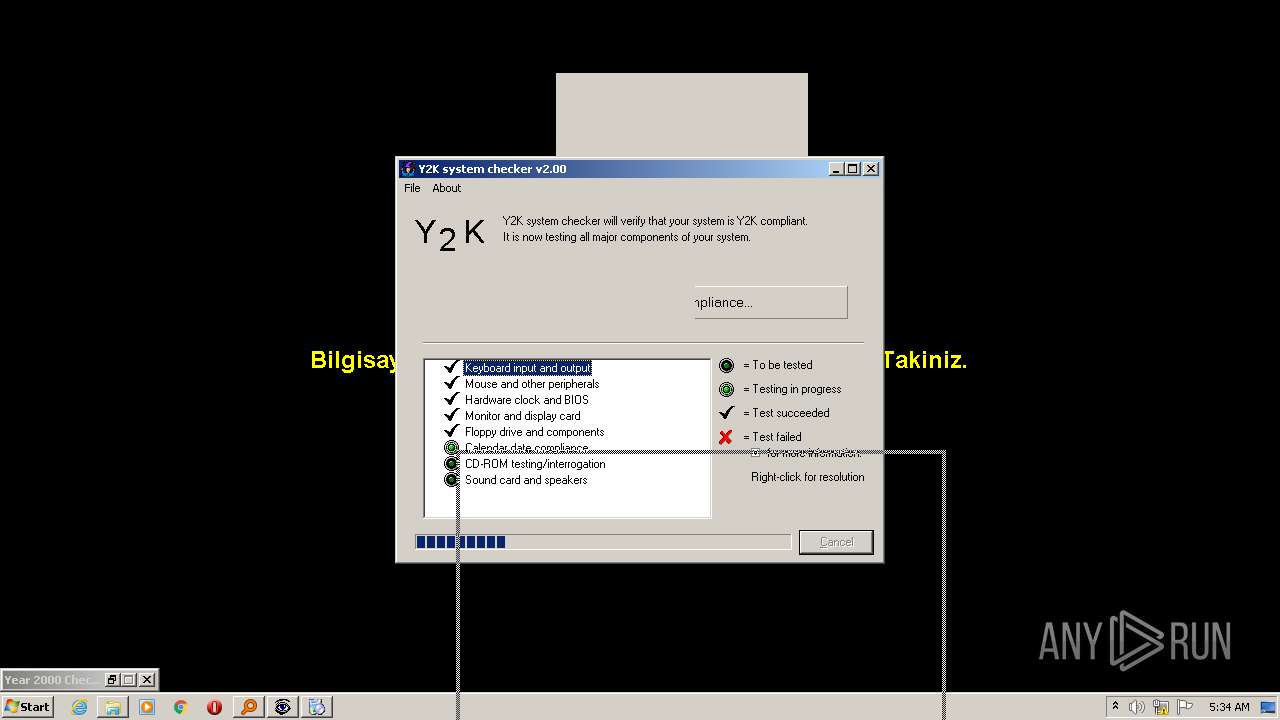
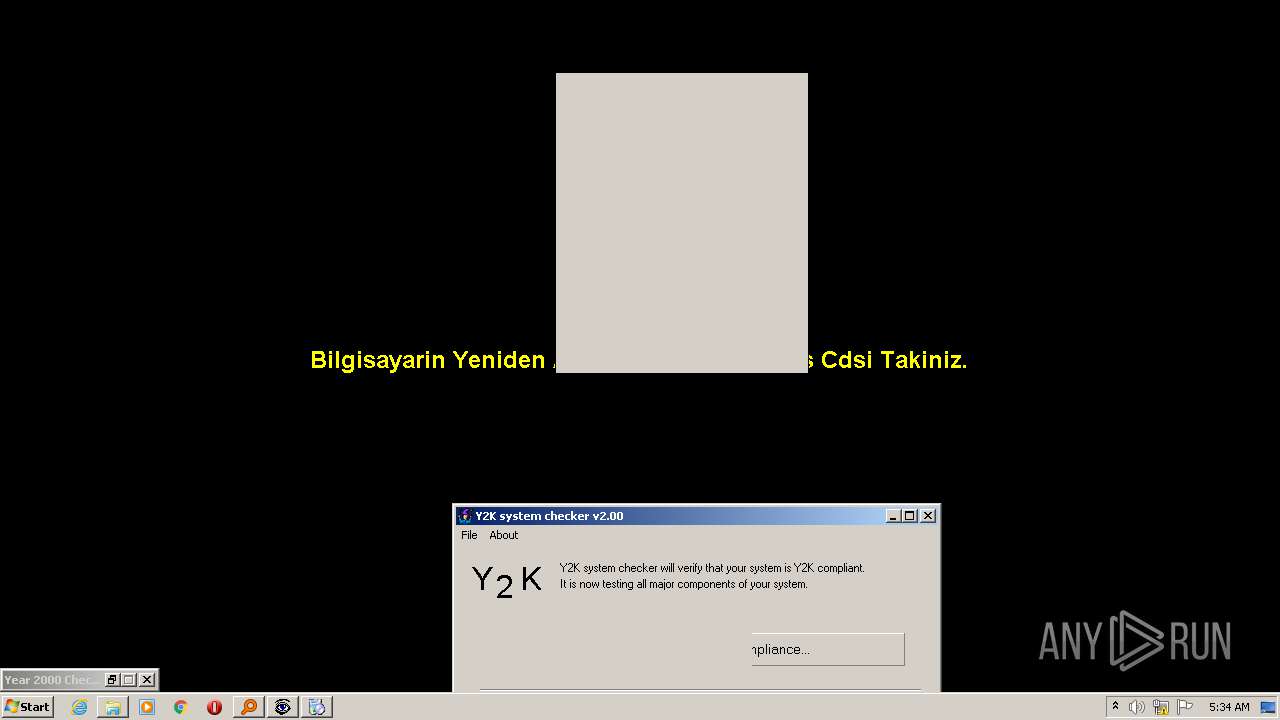
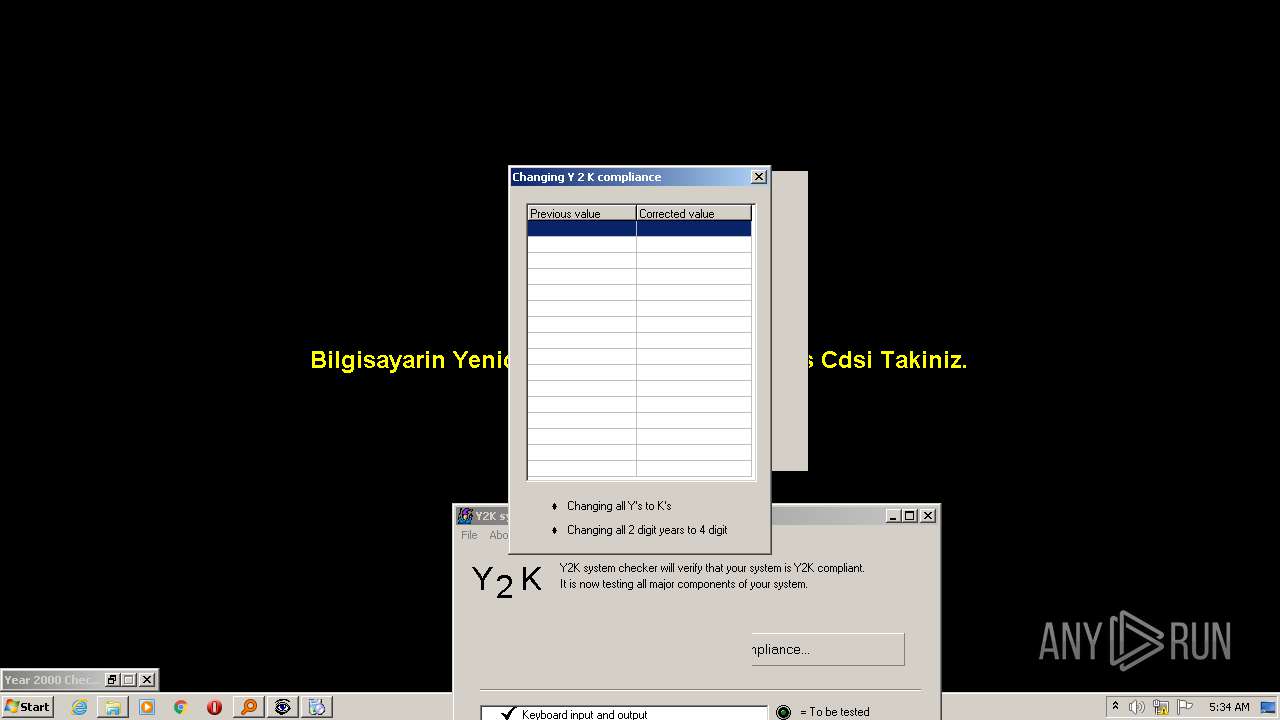
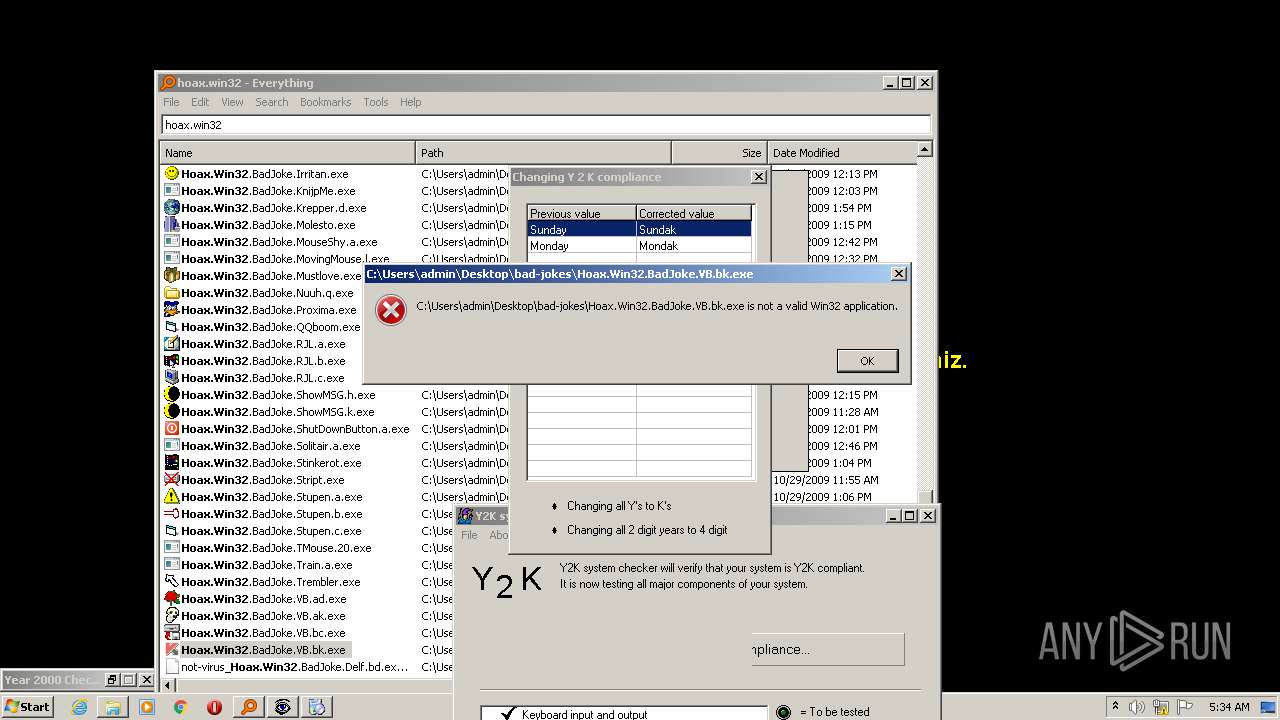
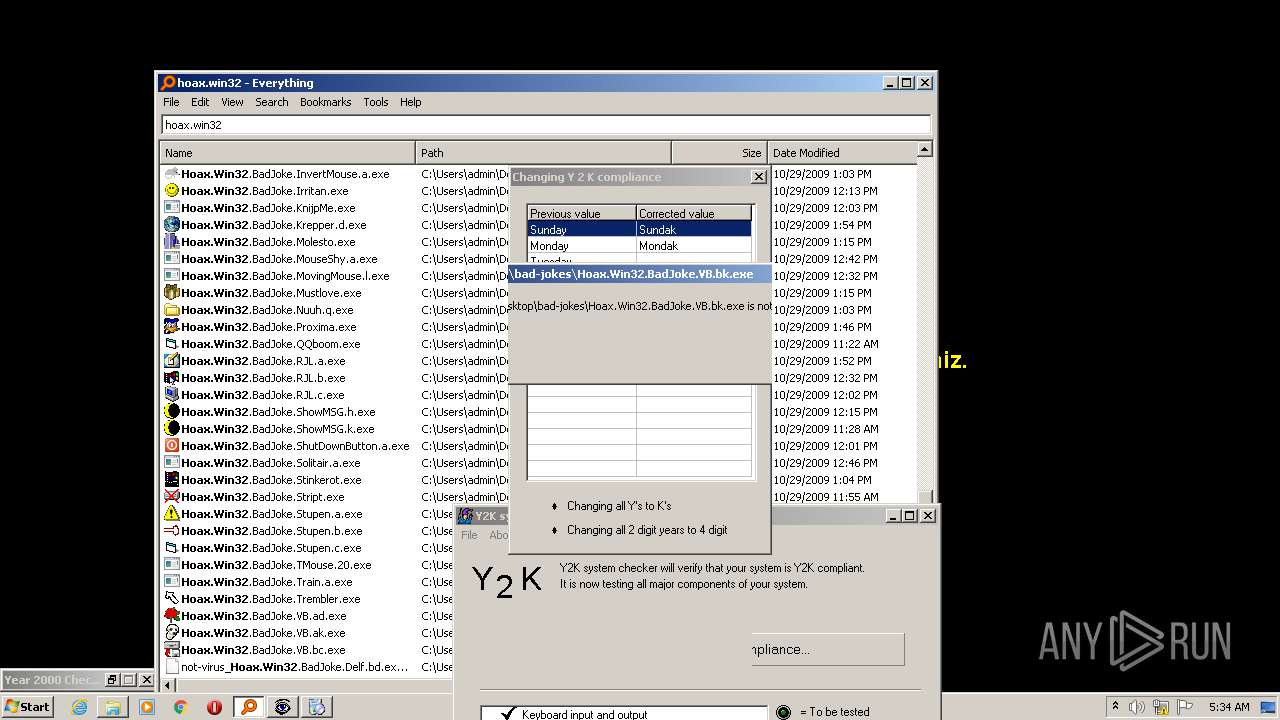
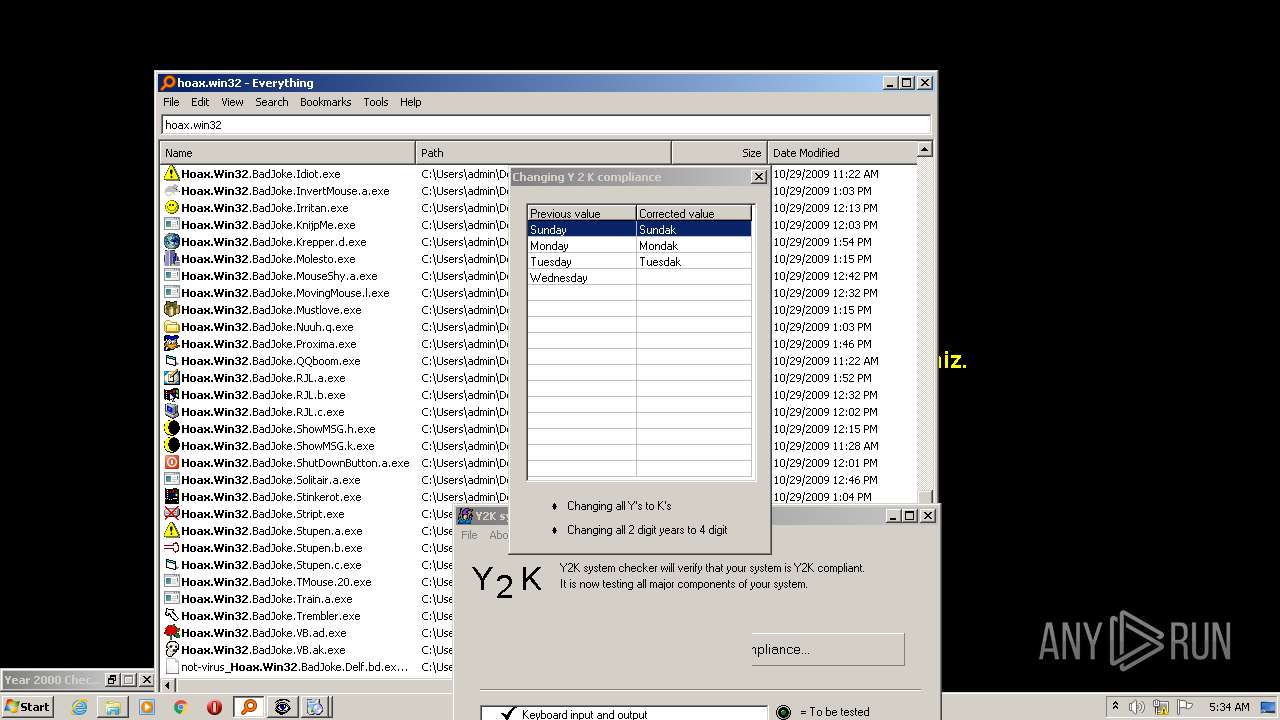
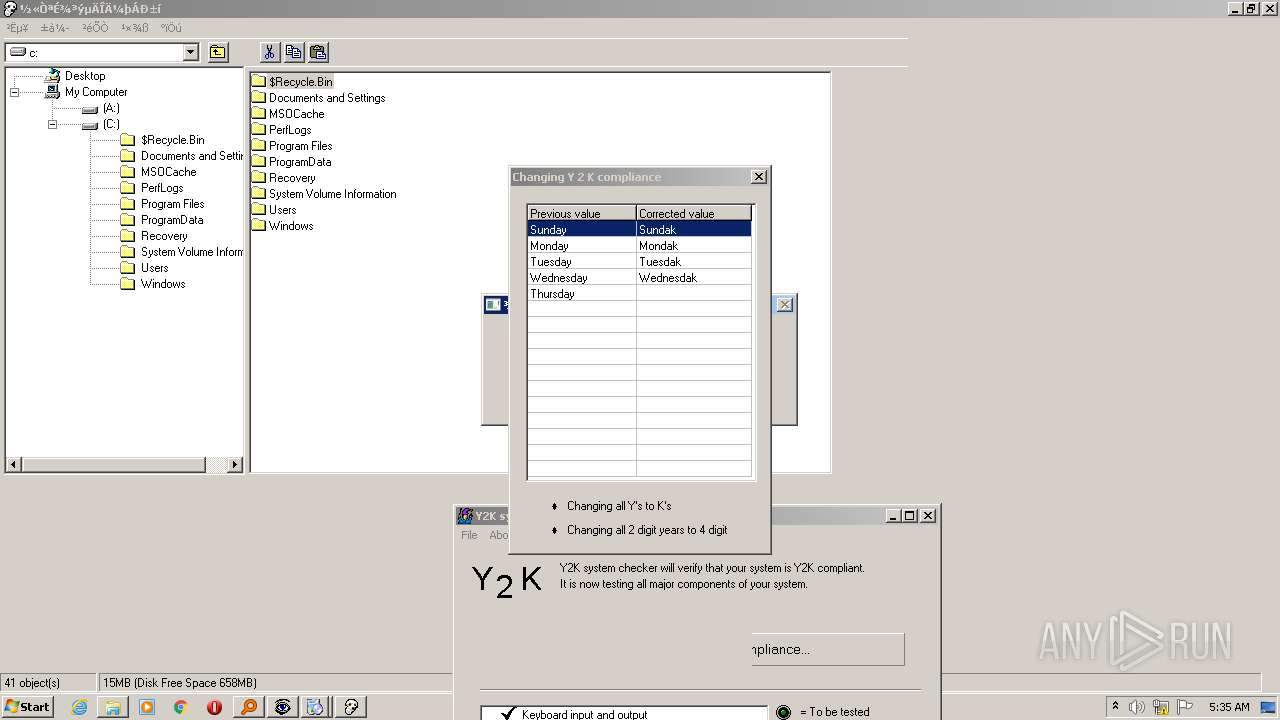
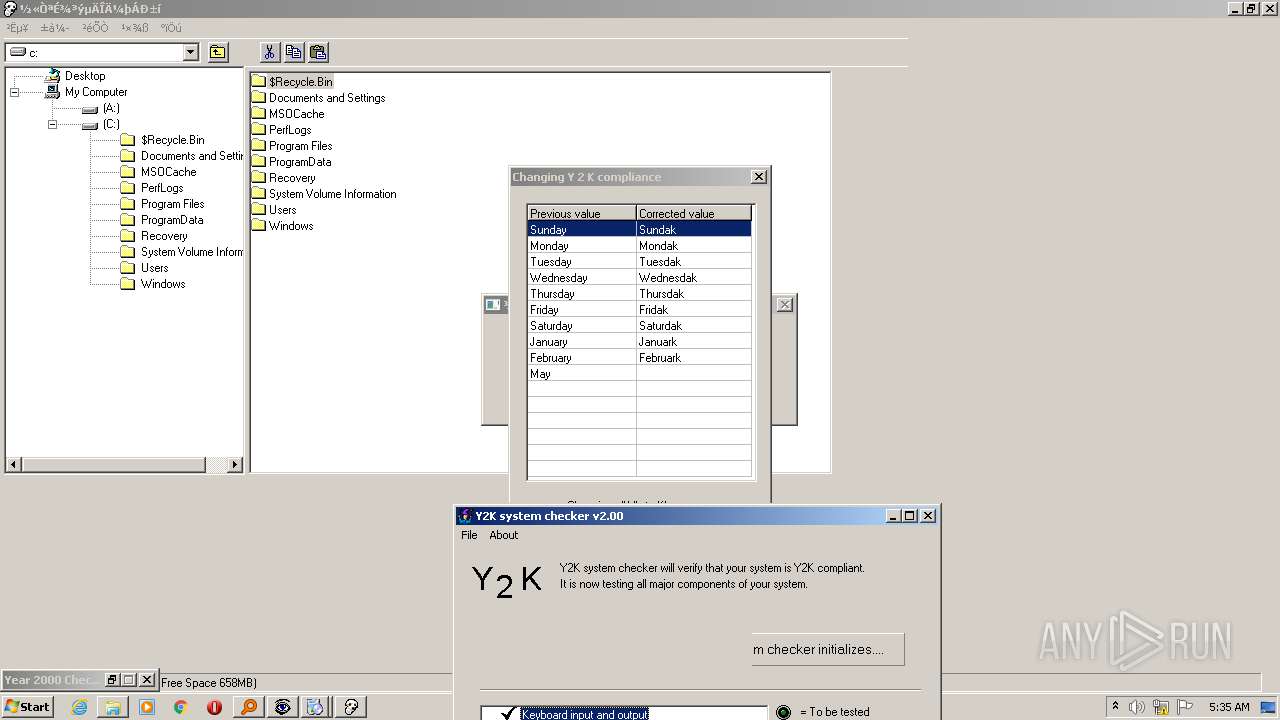
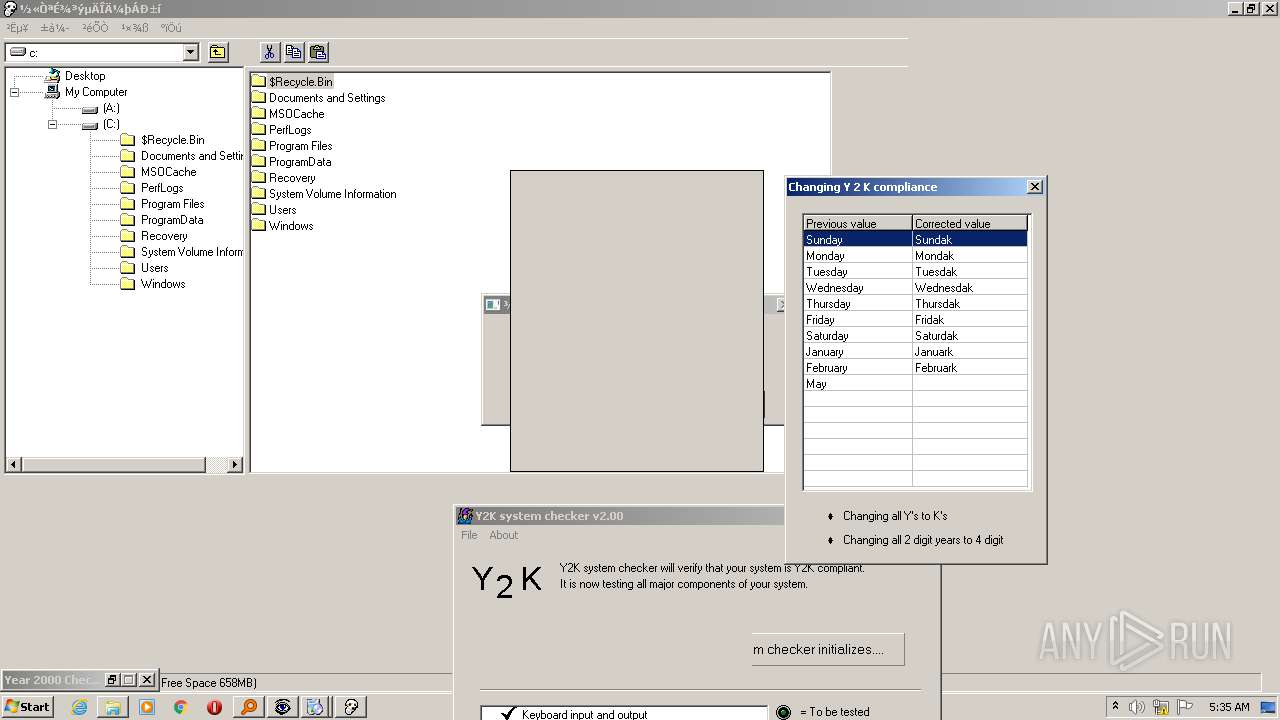
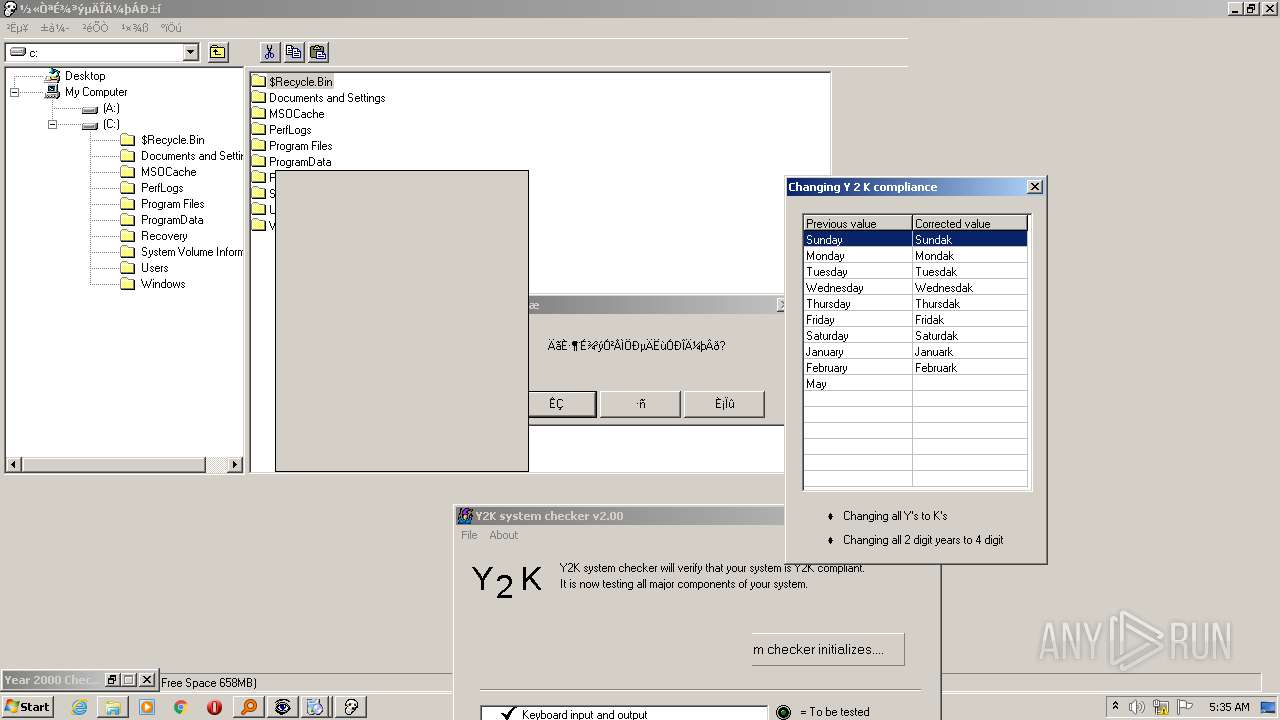
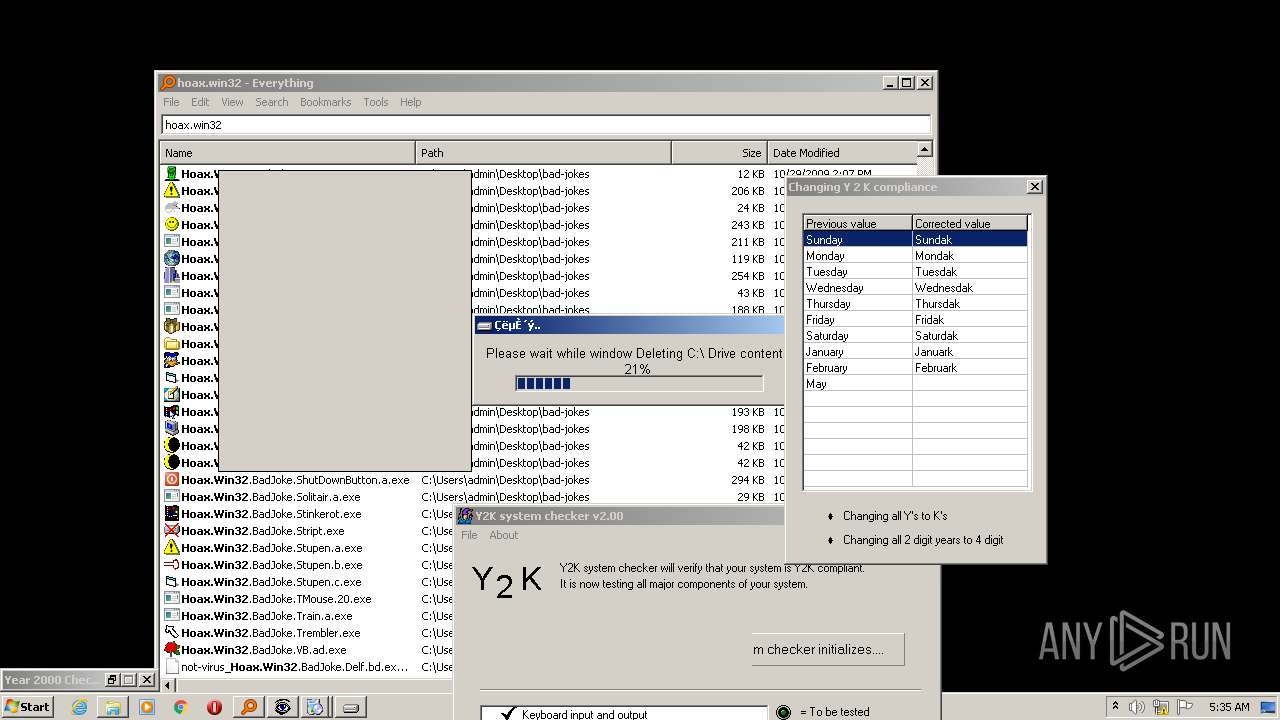
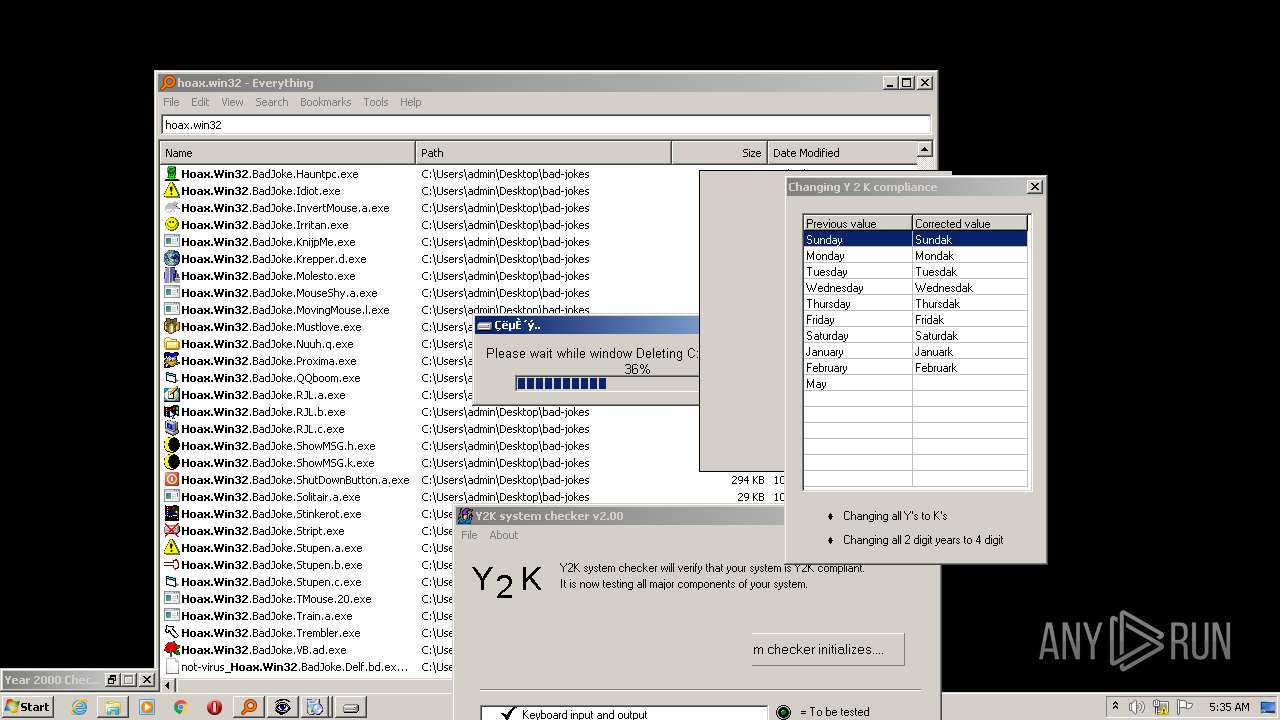
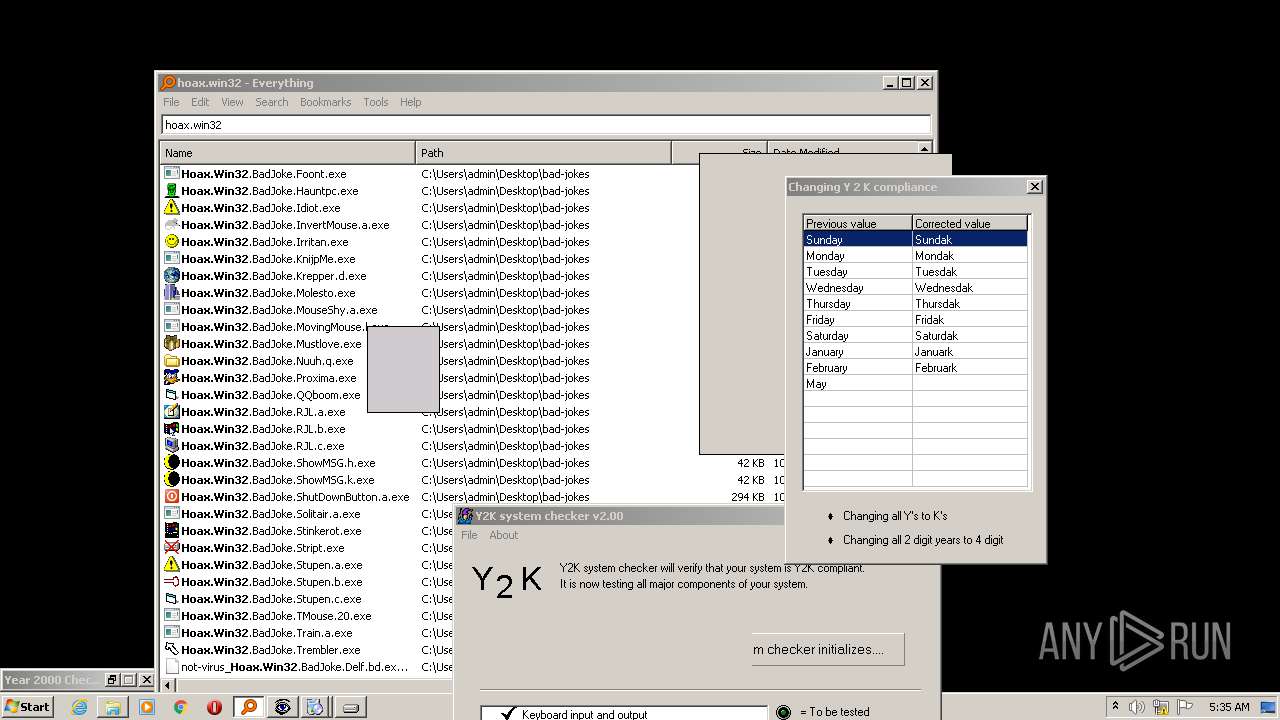
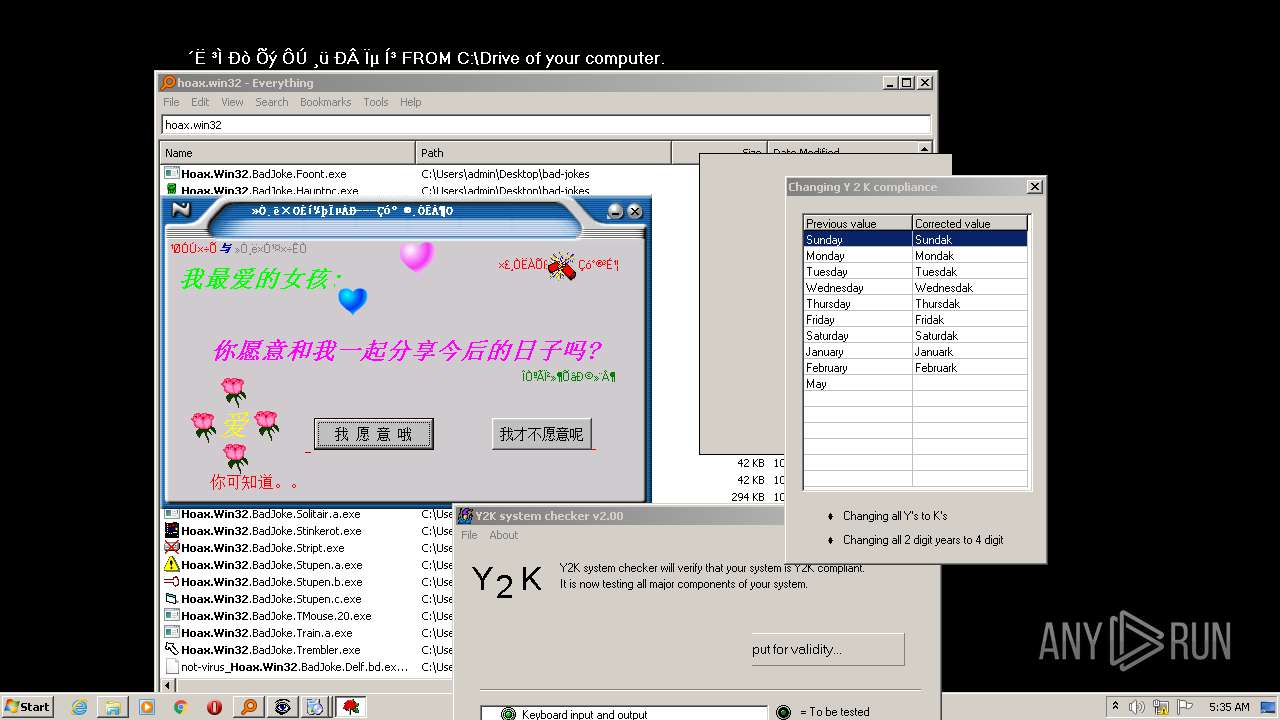
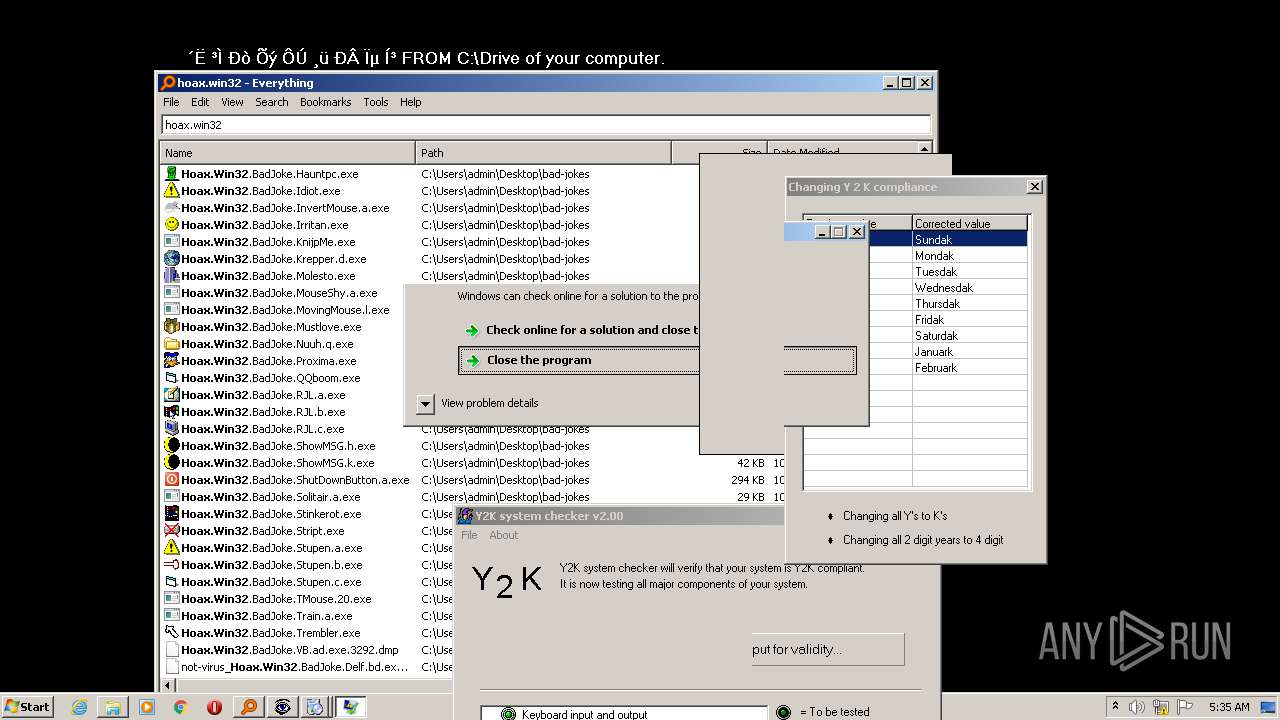
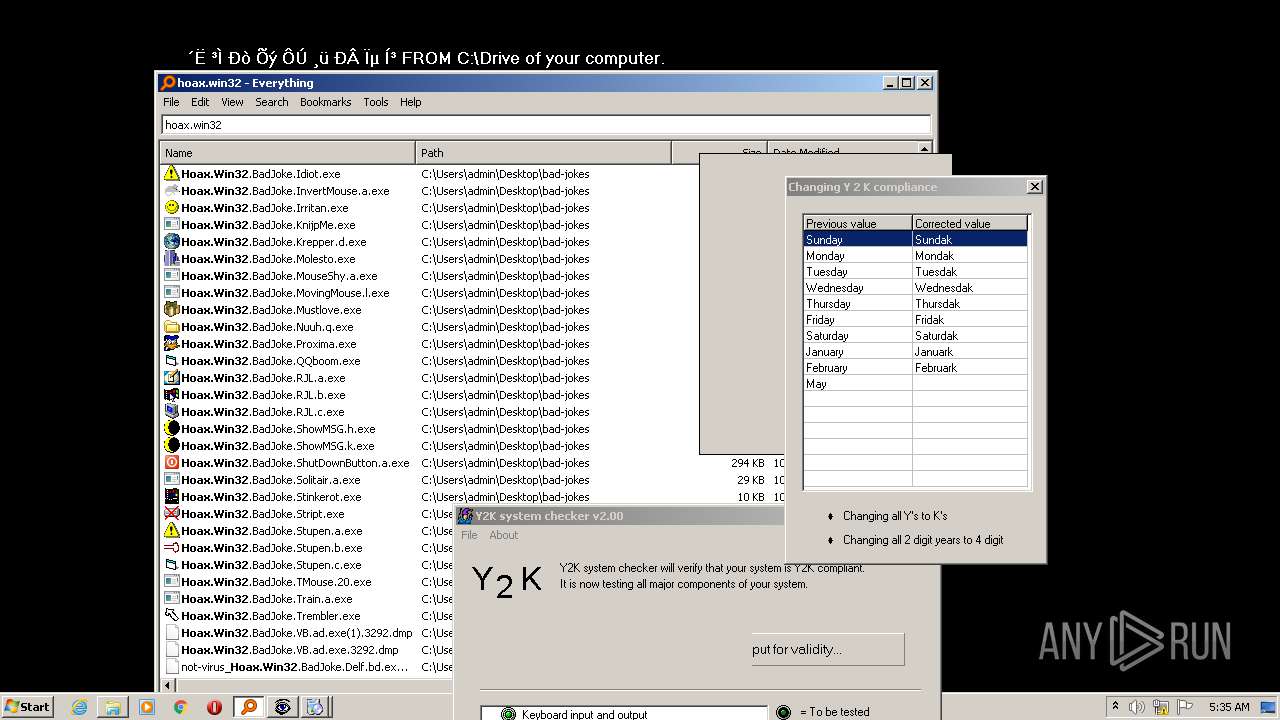
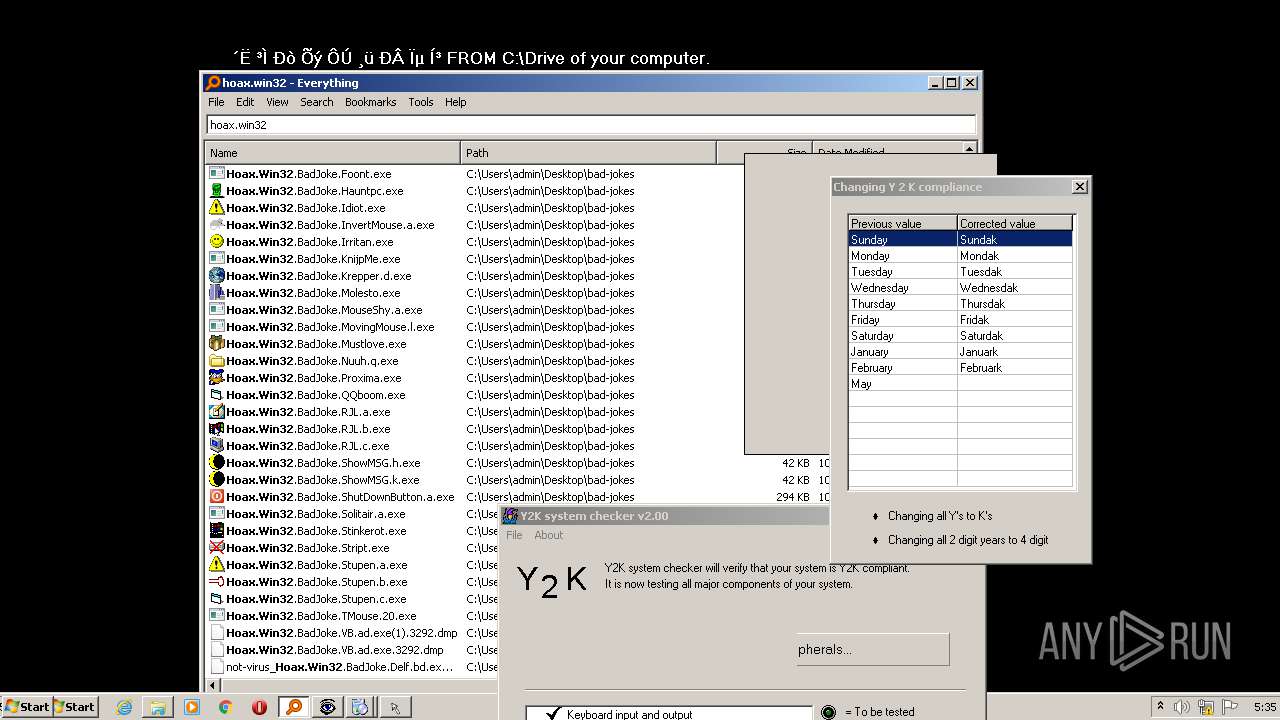
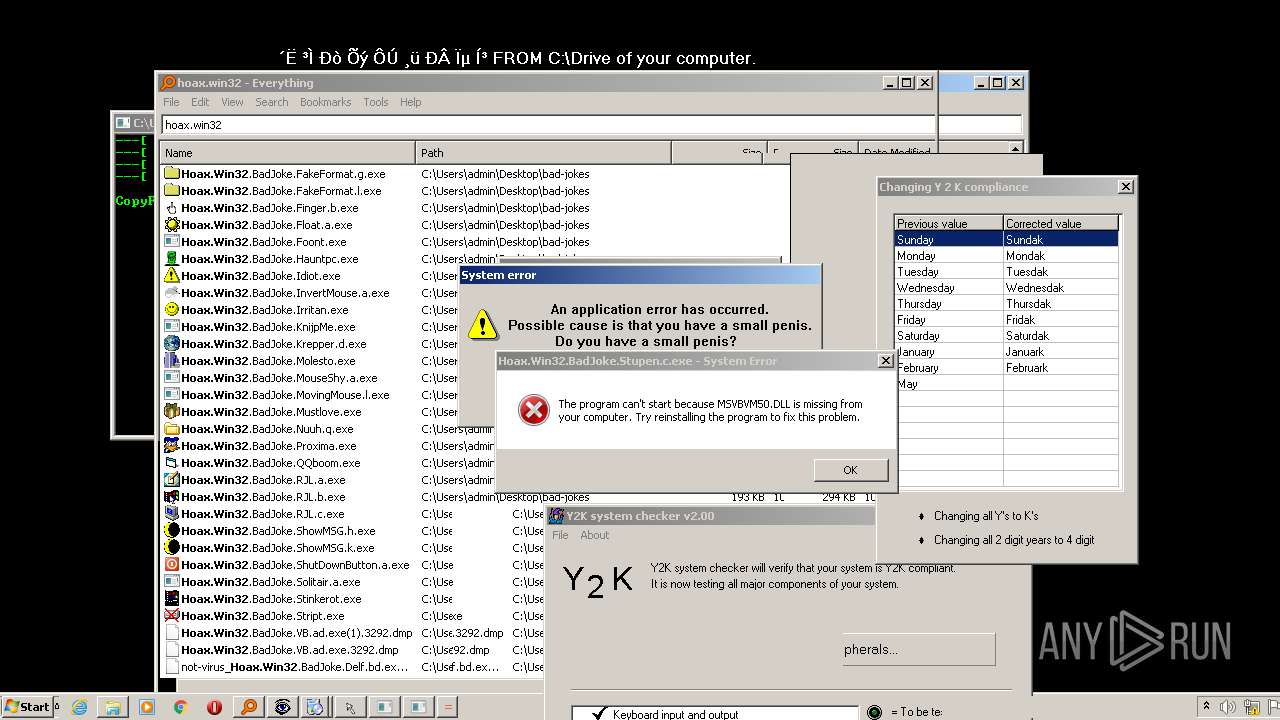
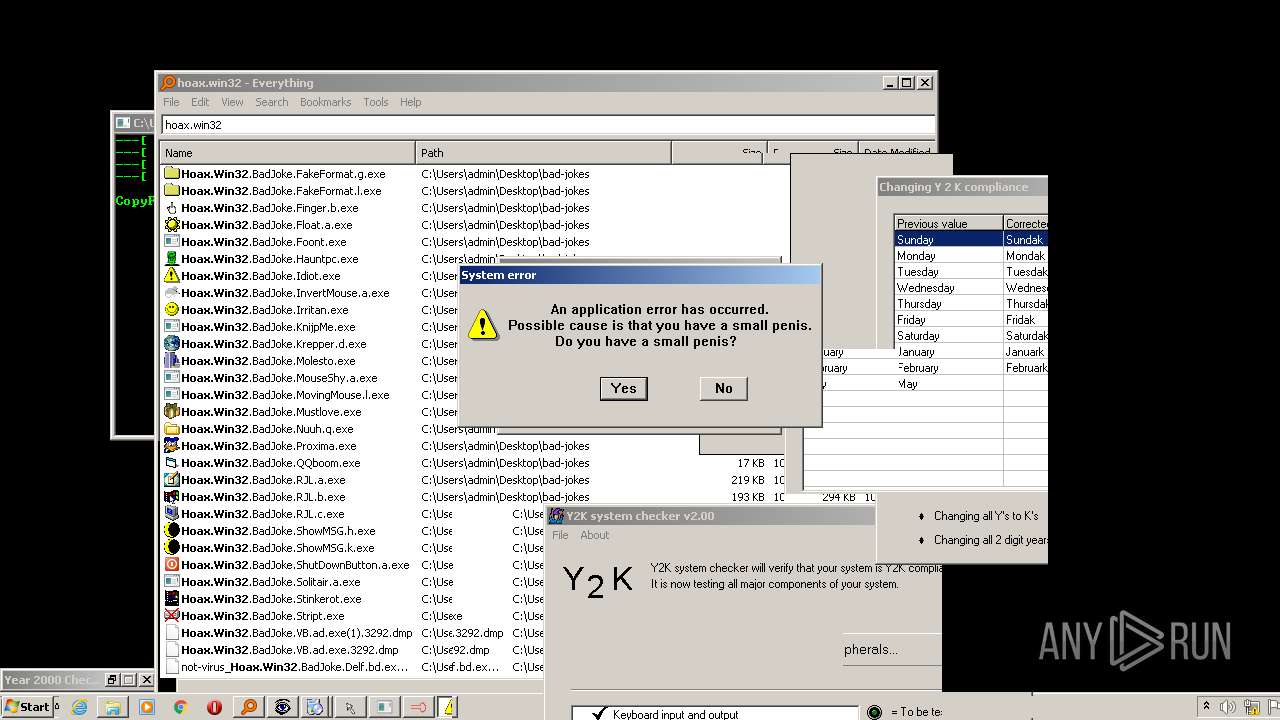
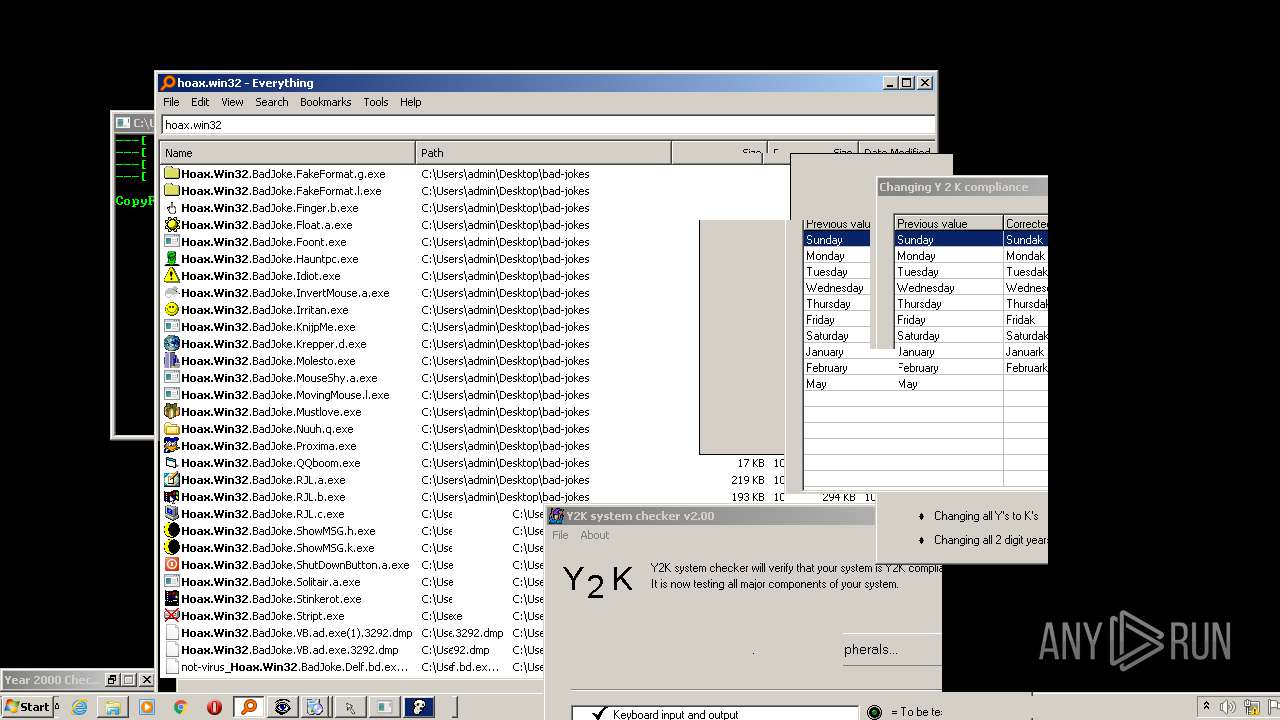
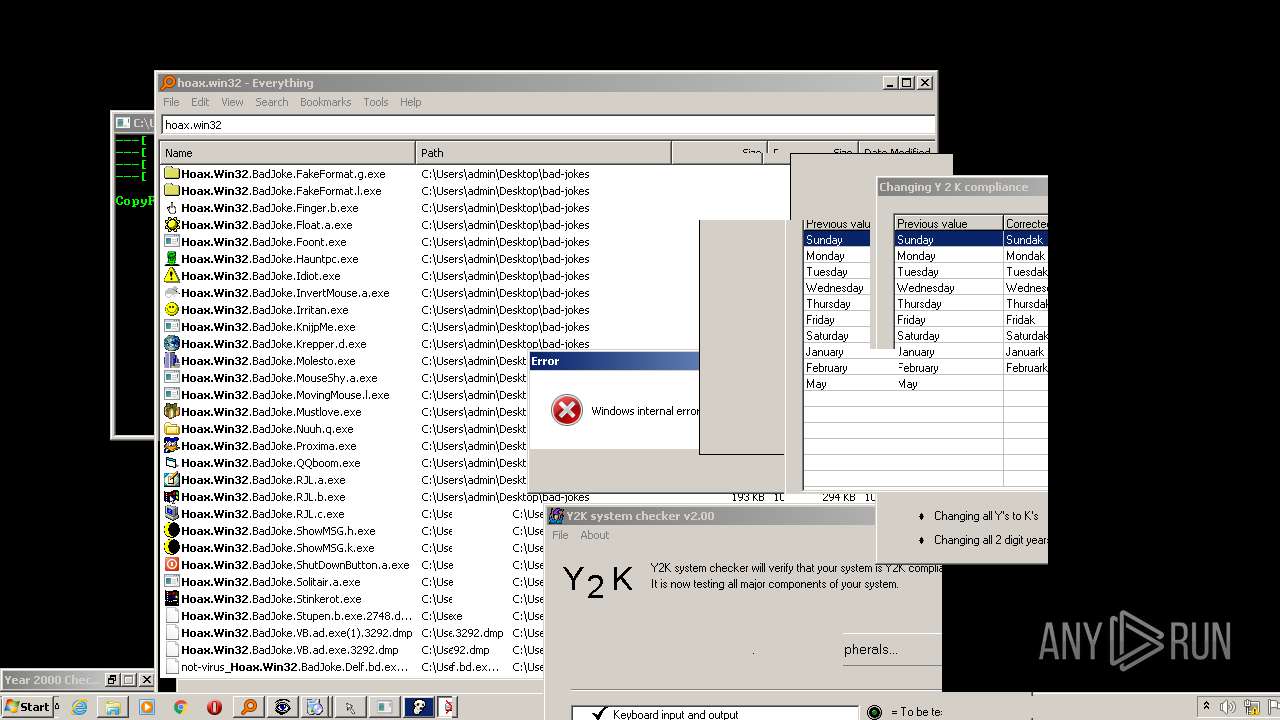
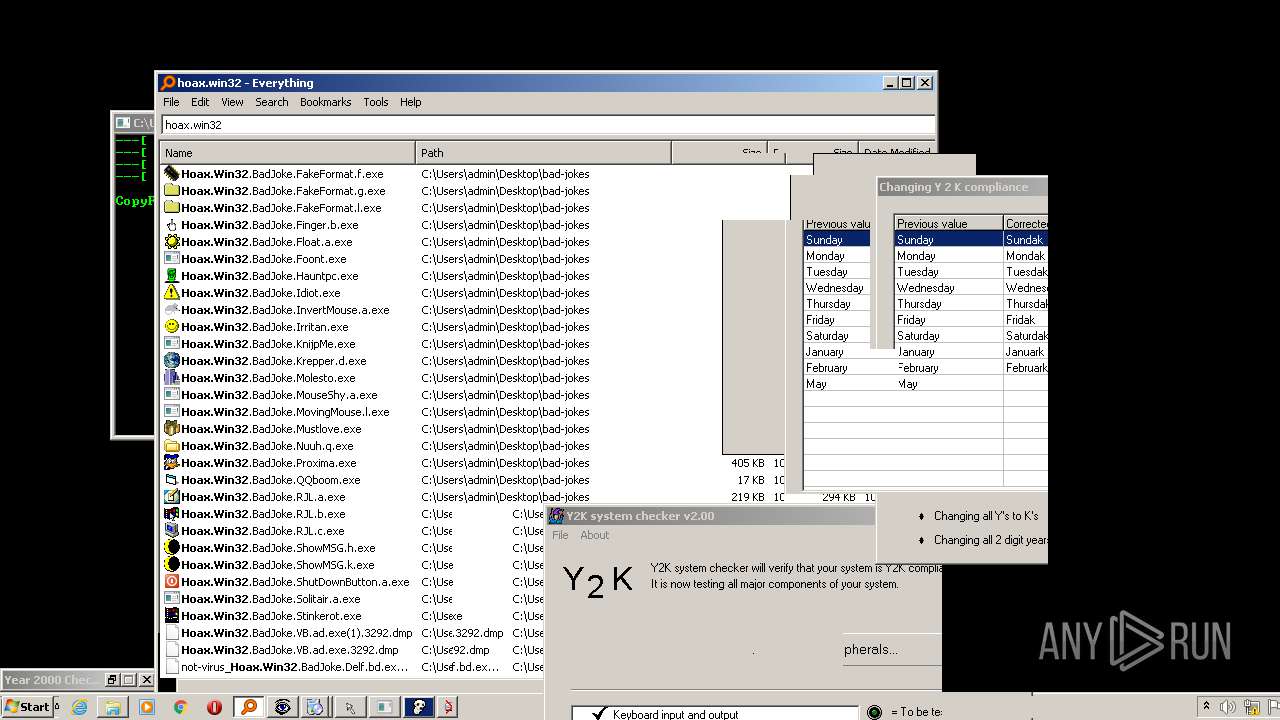
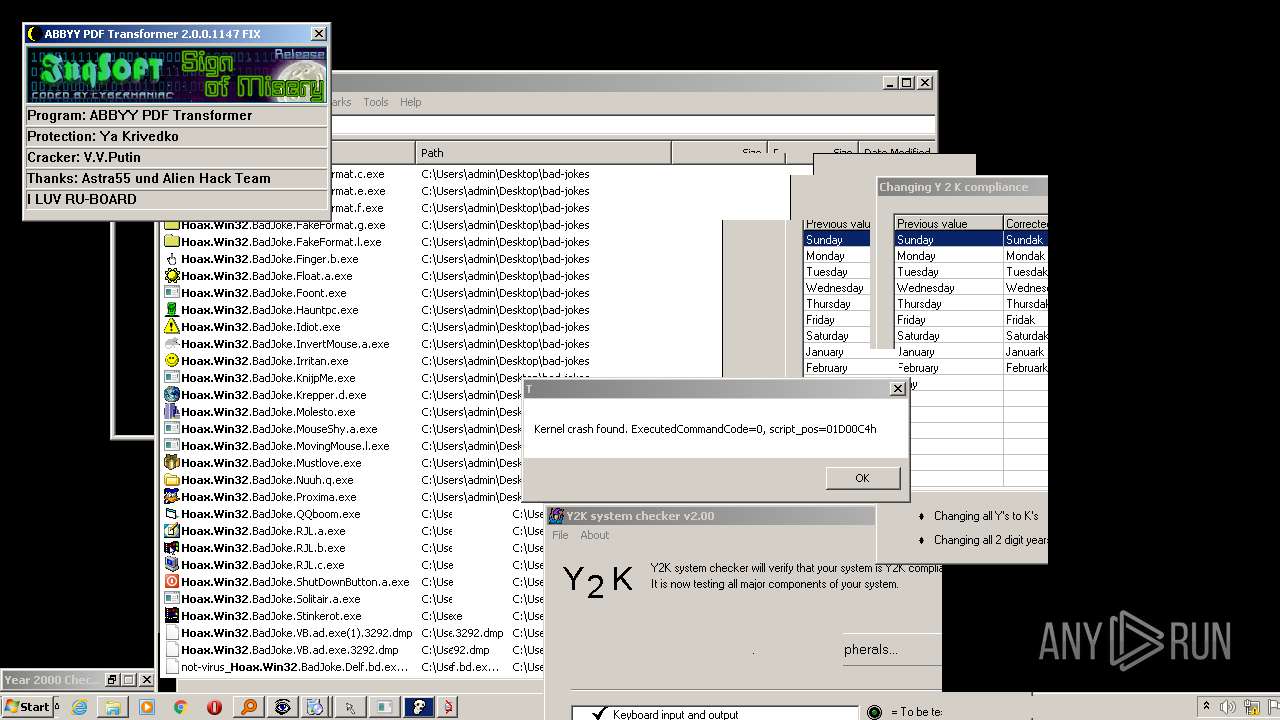
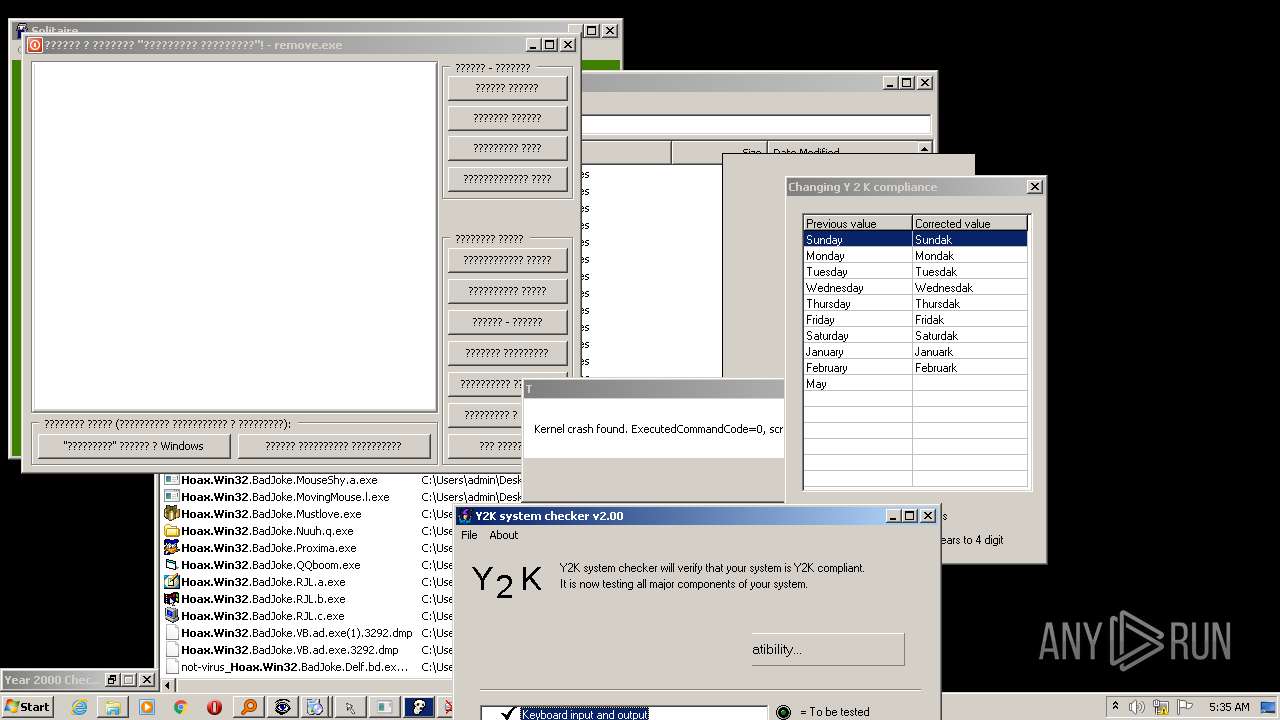
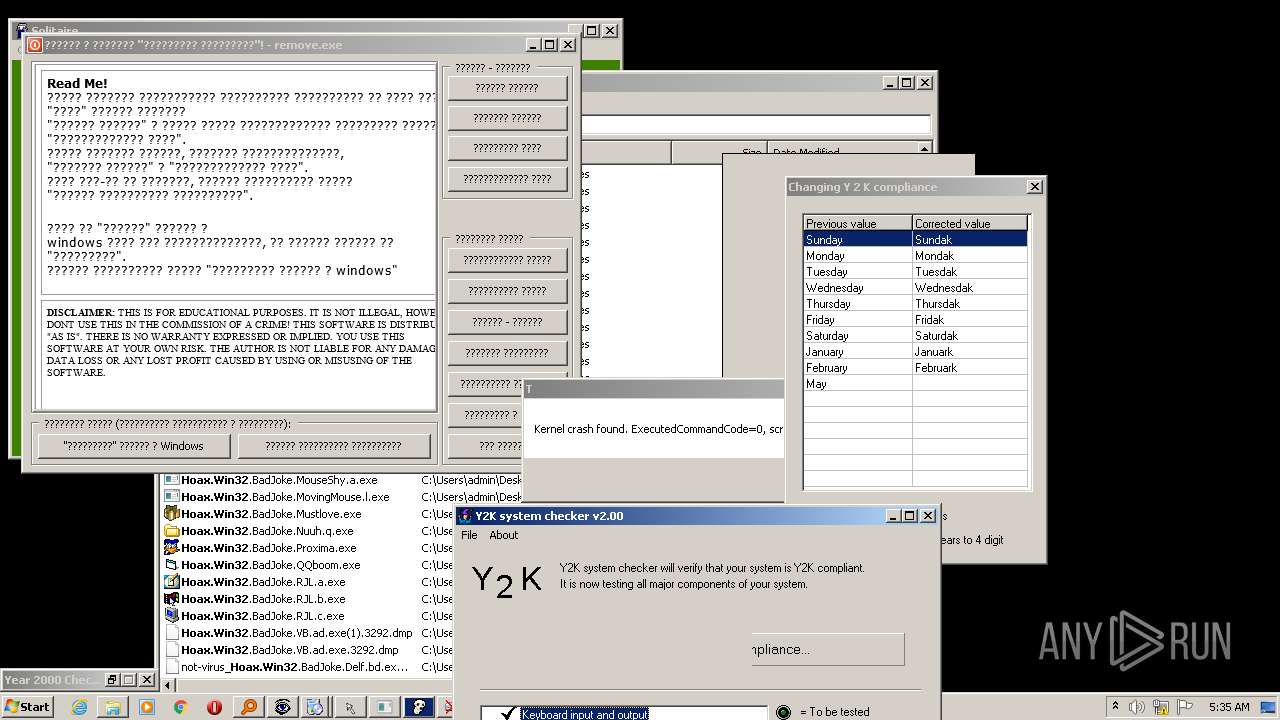
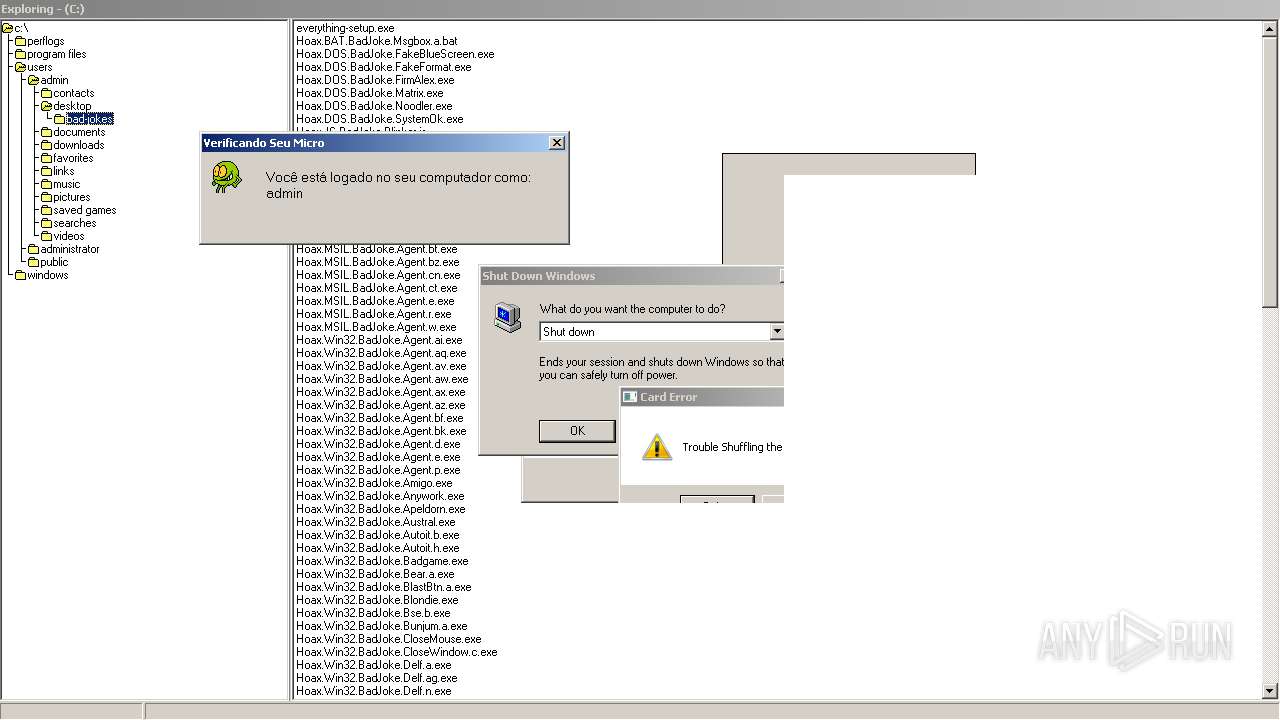
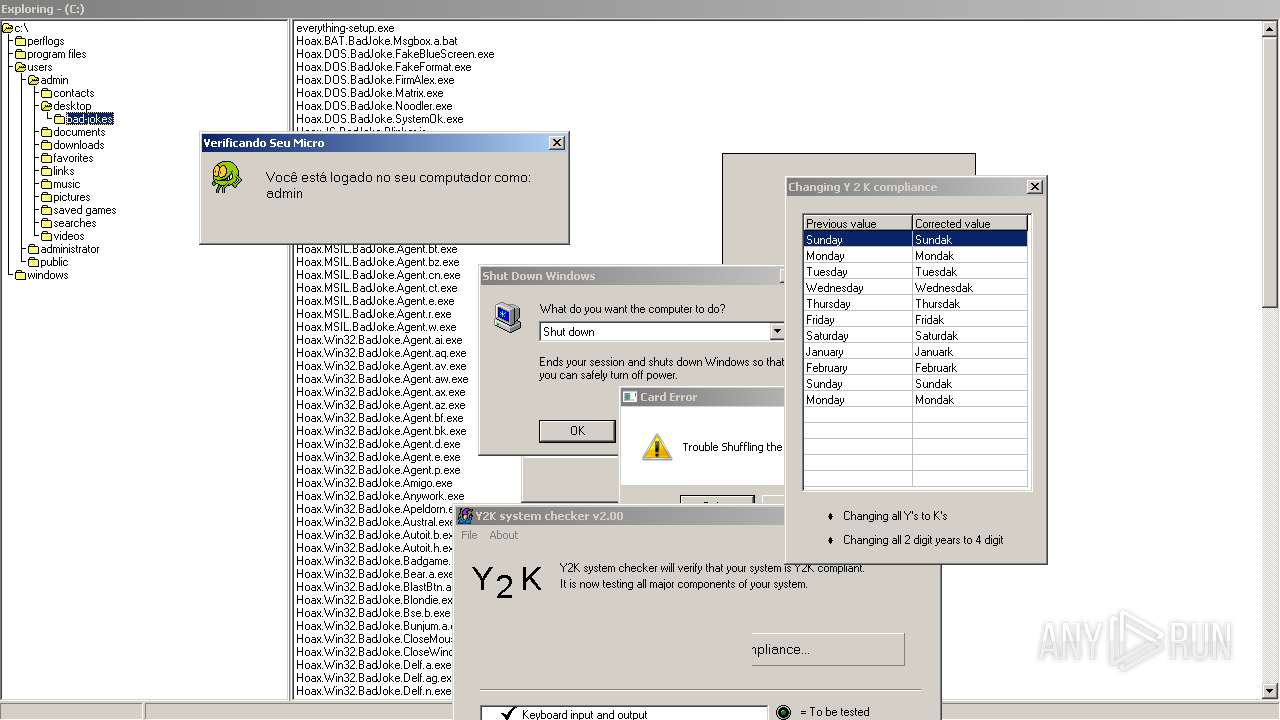
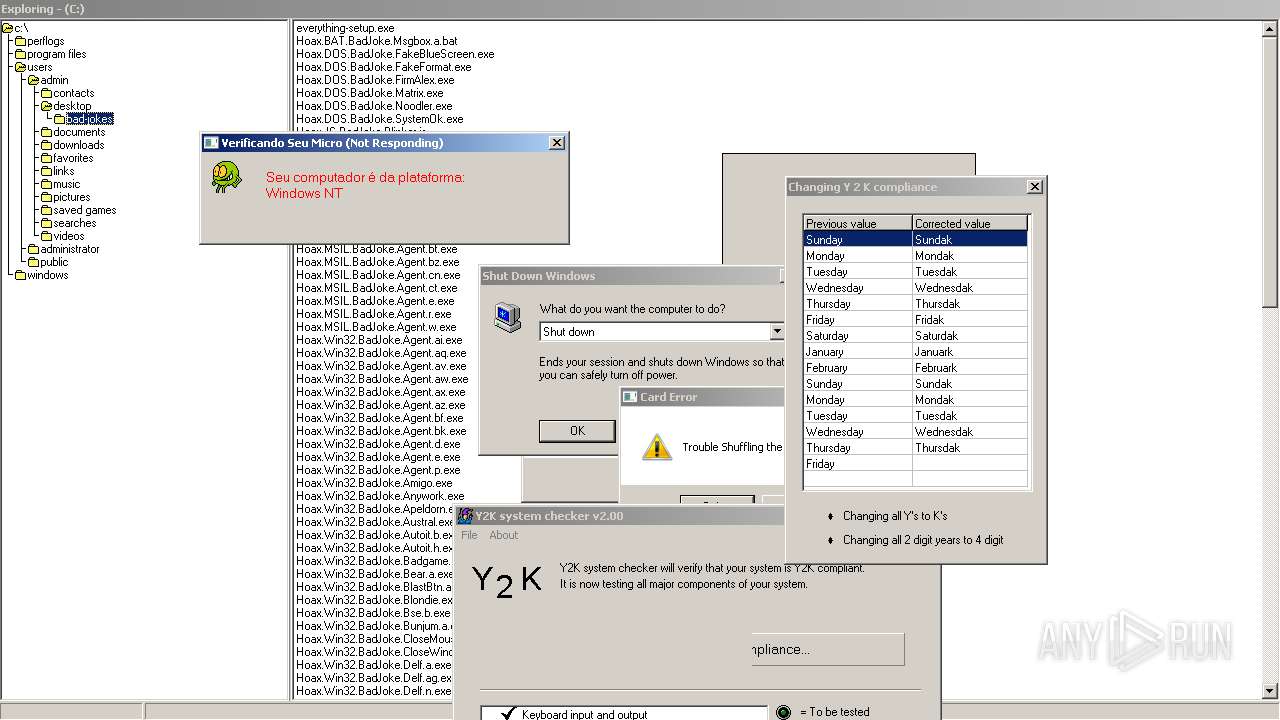
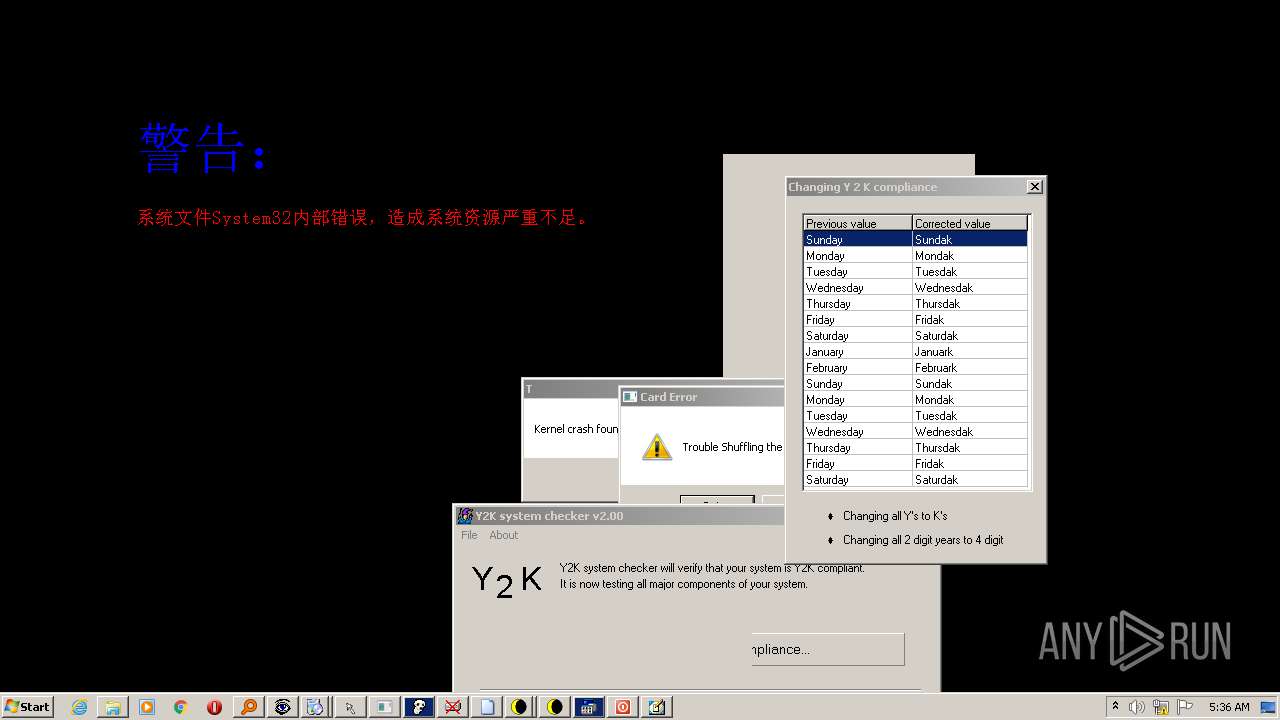
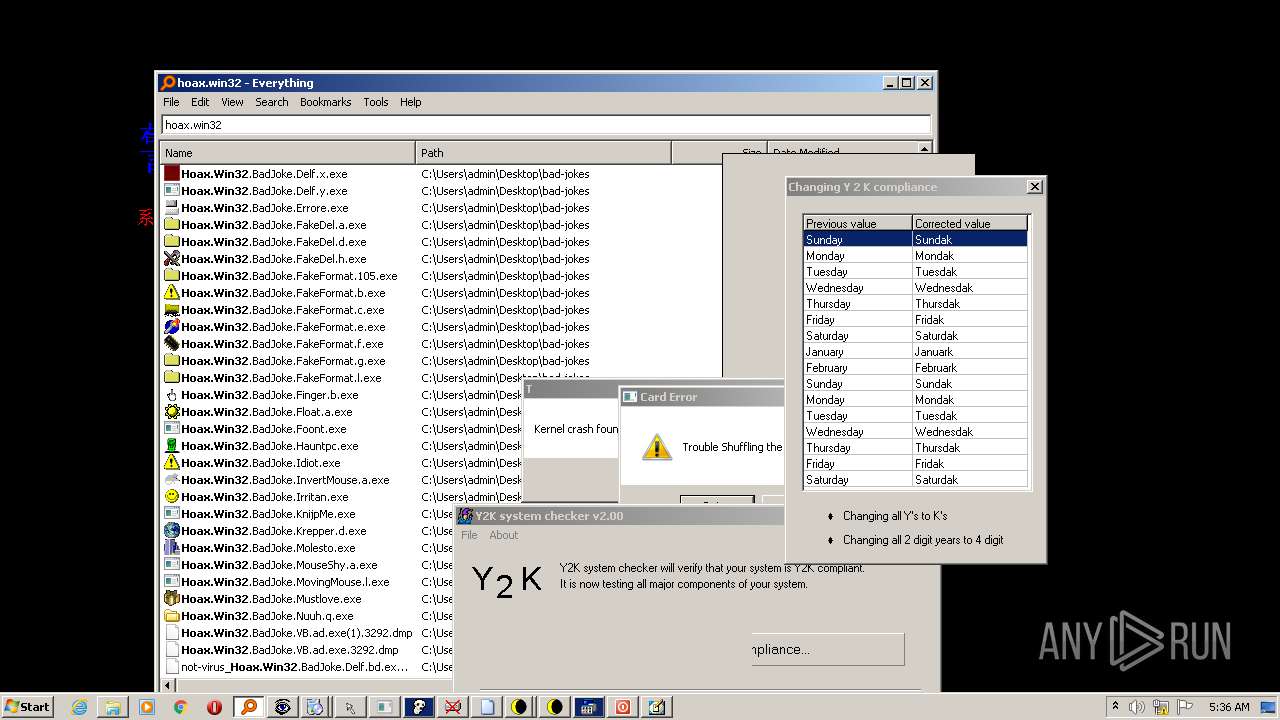
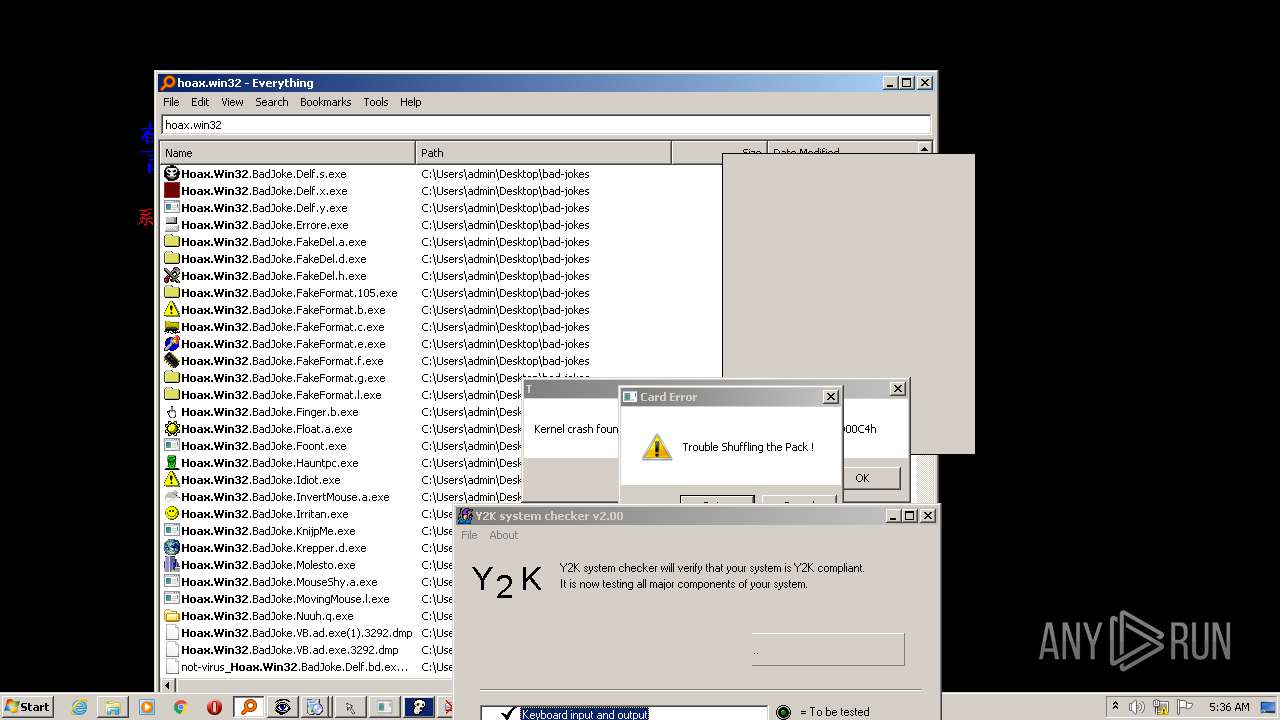
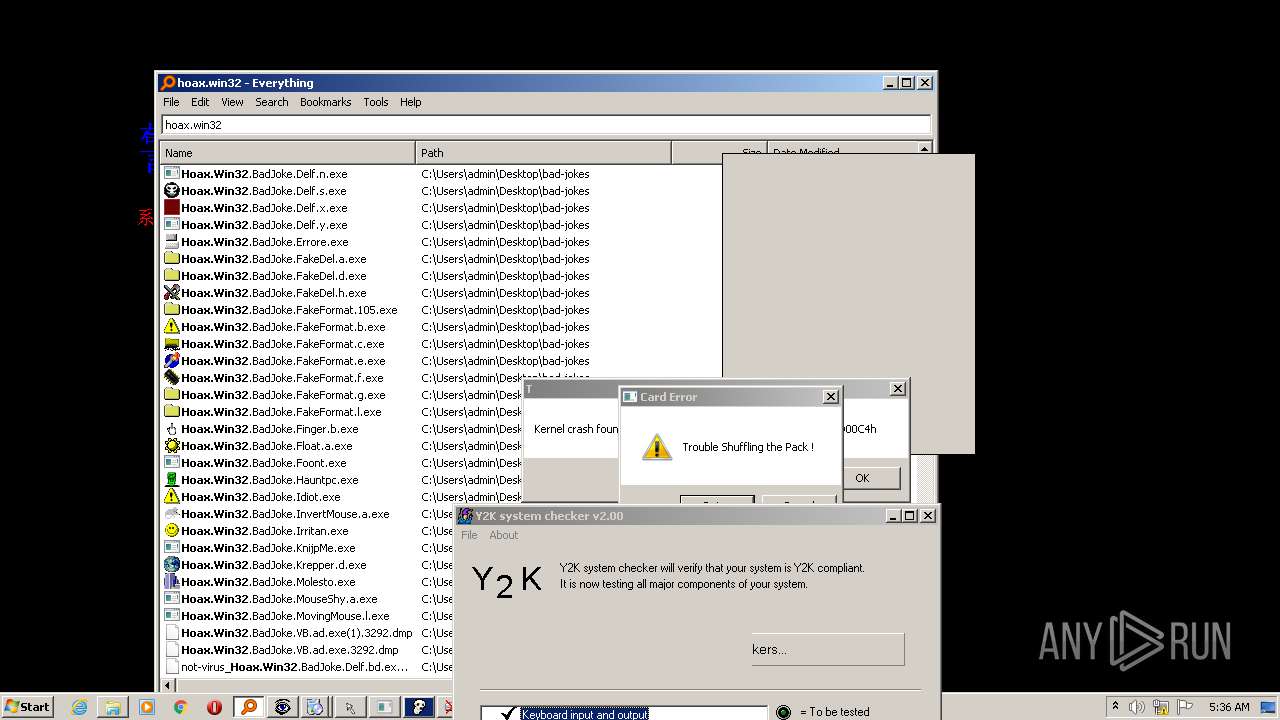
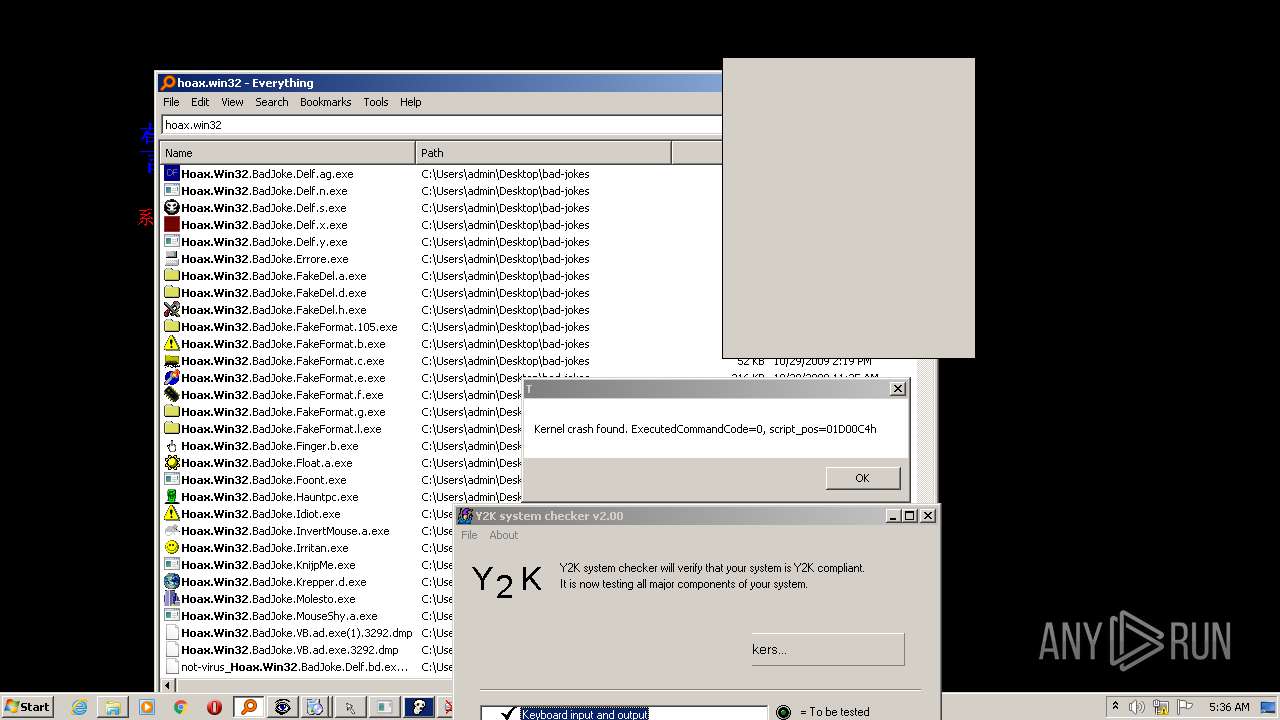
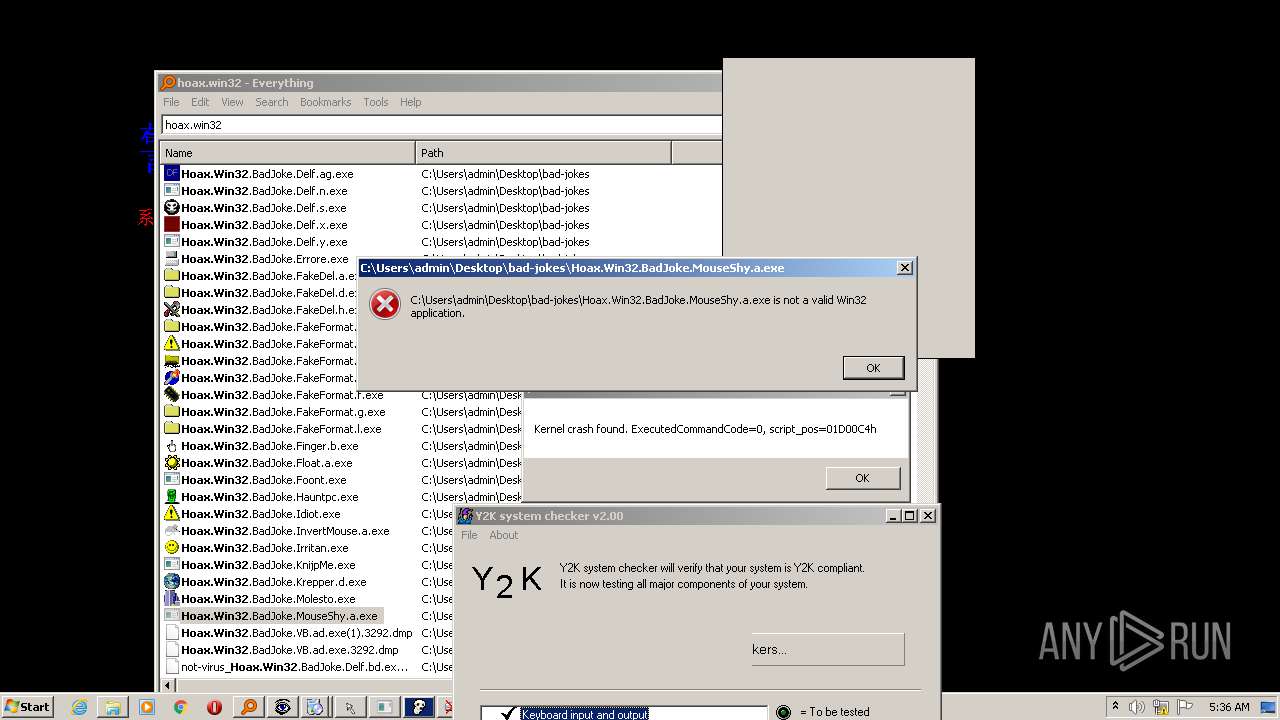
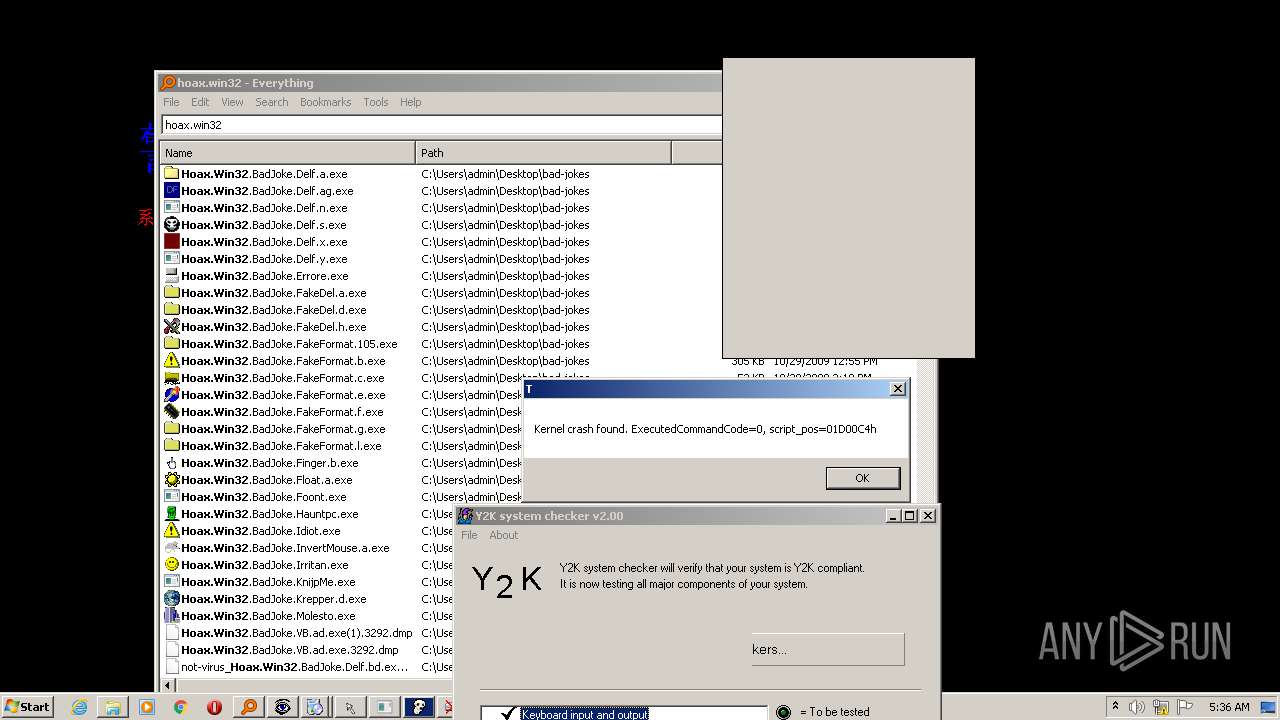
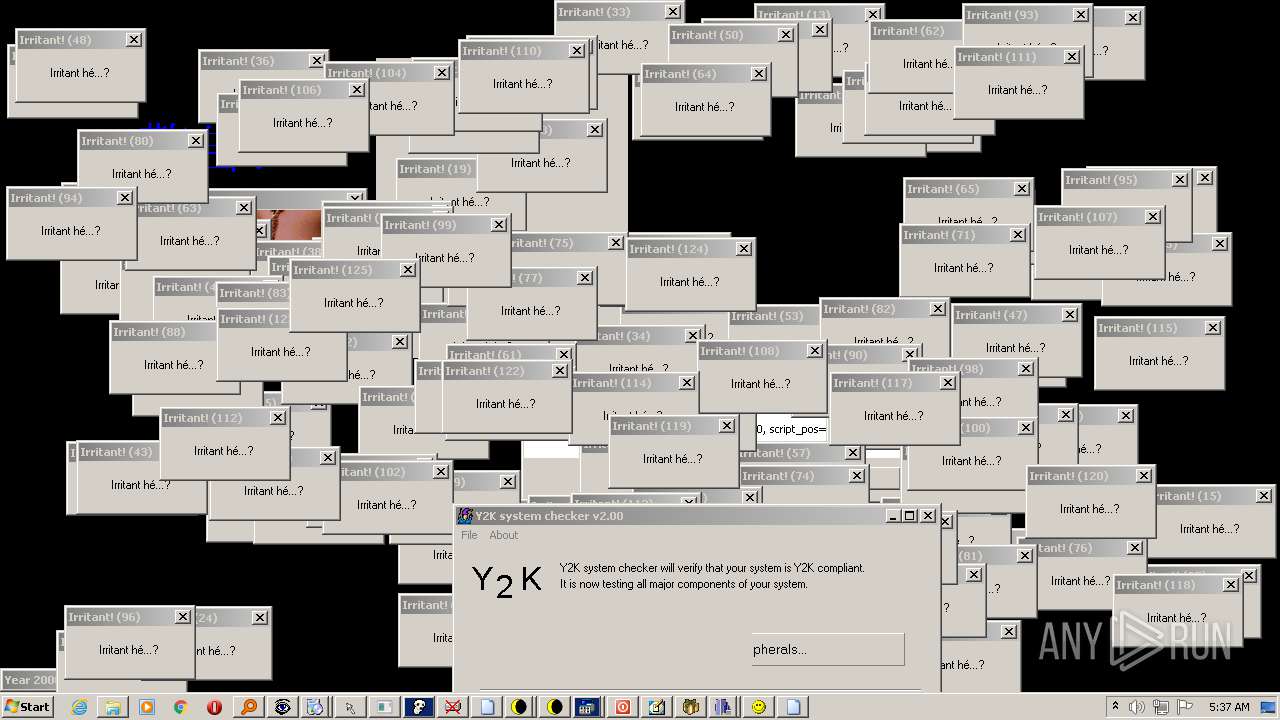
- Hoax.Win32.BadJoke.Y2KChecker.exe (PID: 312)
- Hoax.Win32.BadJoke.VB.t.exe (PID: 3492)
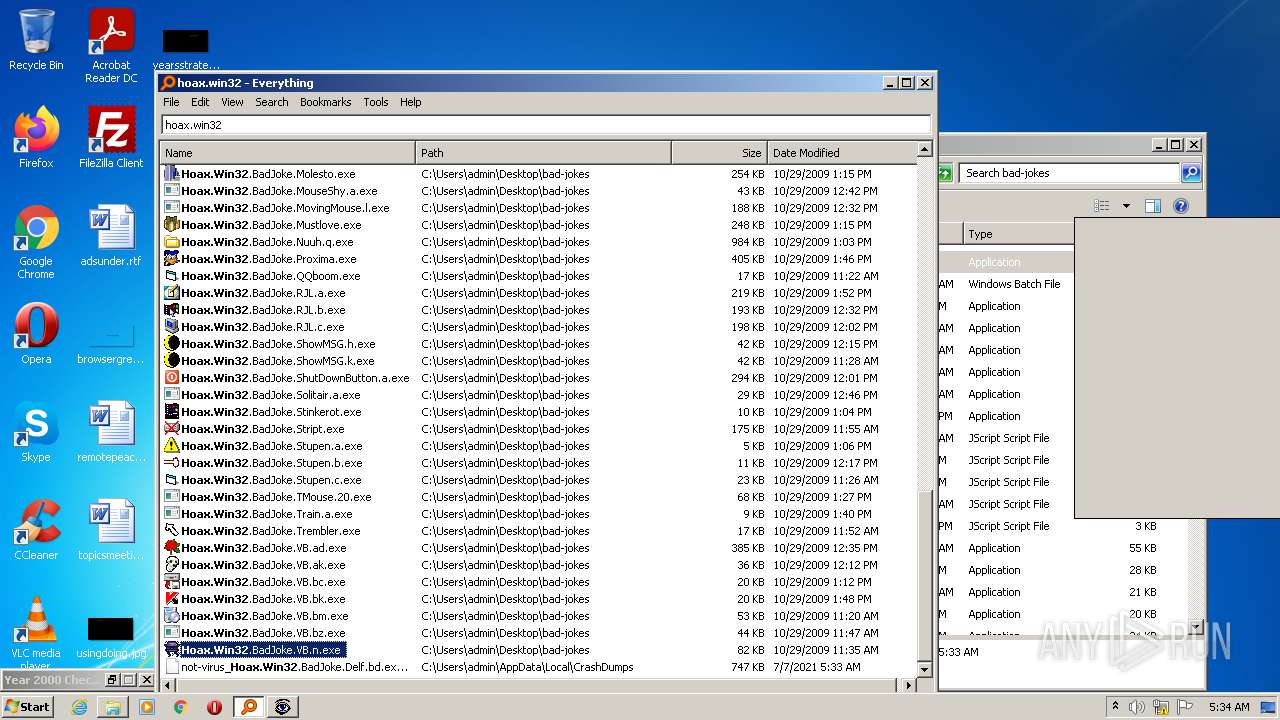
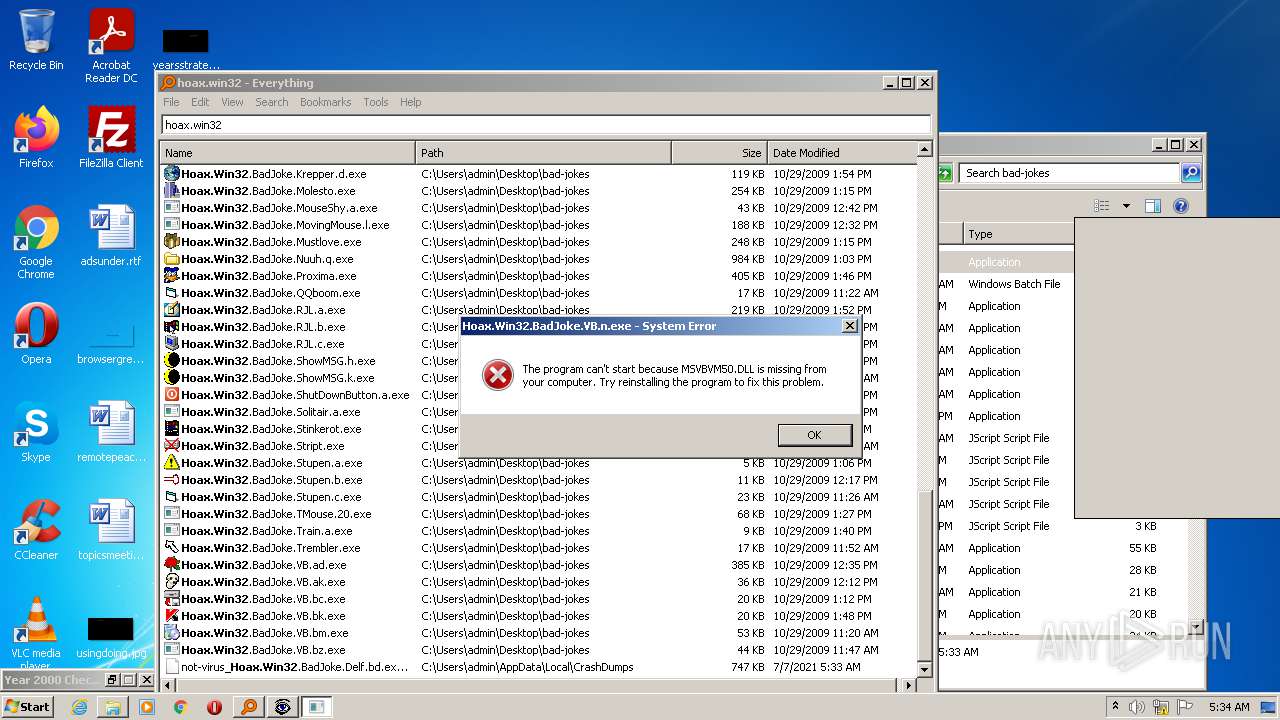
- Hoax.Win32.BadJoke.VB.n.exe (PID: 756)
- Hoax.Win32.BadJoke.VB.bm.exe (PID: 3740)
- Hoax.Win32.BadJoke.VB.bc.exe (PID: 468)
- Hoax.Win32.BadJoke.VB.ak.exe (PID: 3520)
- Hoax.Win32.BadJoke.VB.ad.exe (PID: 3292)
- Hoax.Win32.BadJoke.TMouse.20.exe (PID: 1592)
- Hoax.Win32.BadJoke.Trembler.exe (PID: 2724)
- Hoax.Win32.BadJoke.Train.a.exe (PID: 3040)
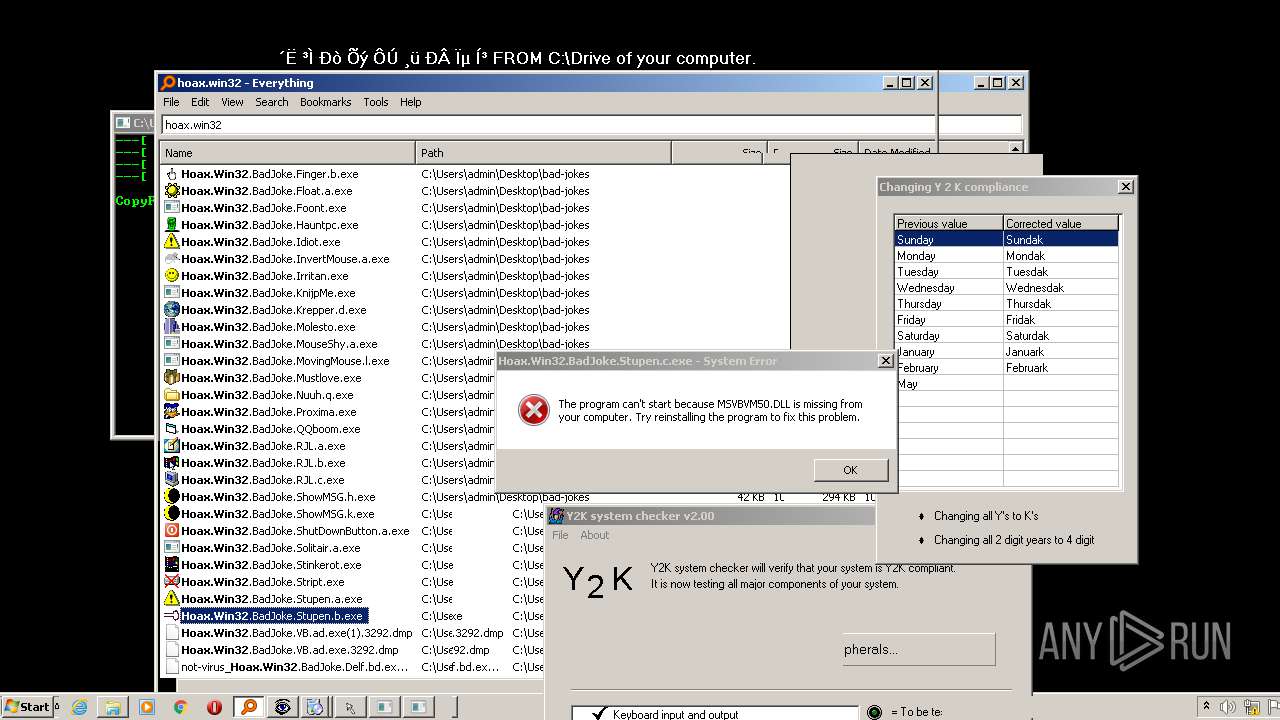
- Hoax.Win32.BadJoke.Stupen.c.exe (PID: 2692)
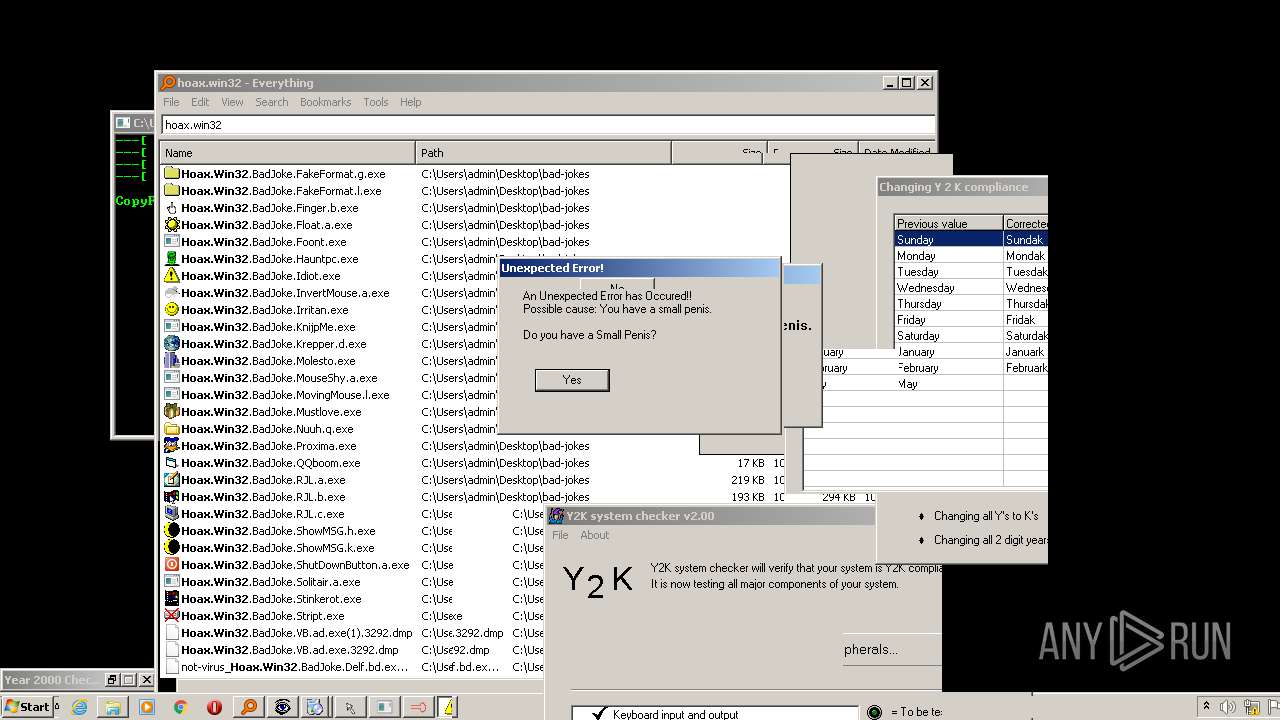
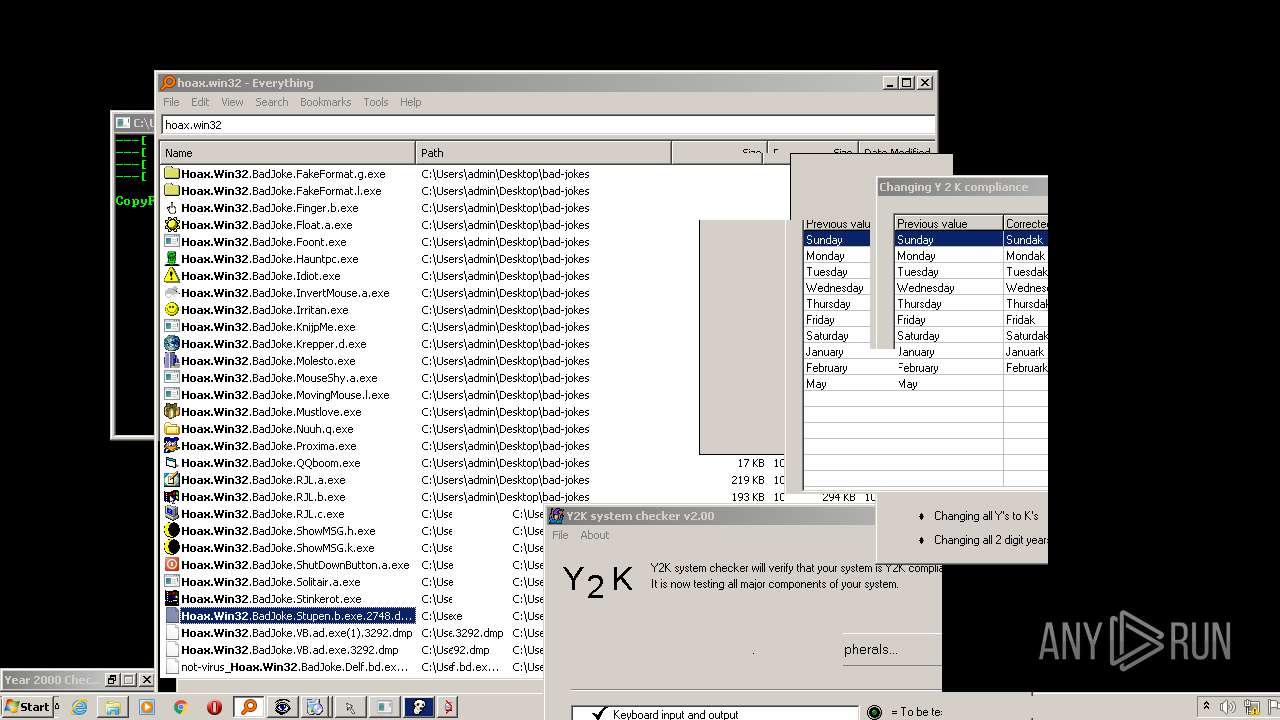
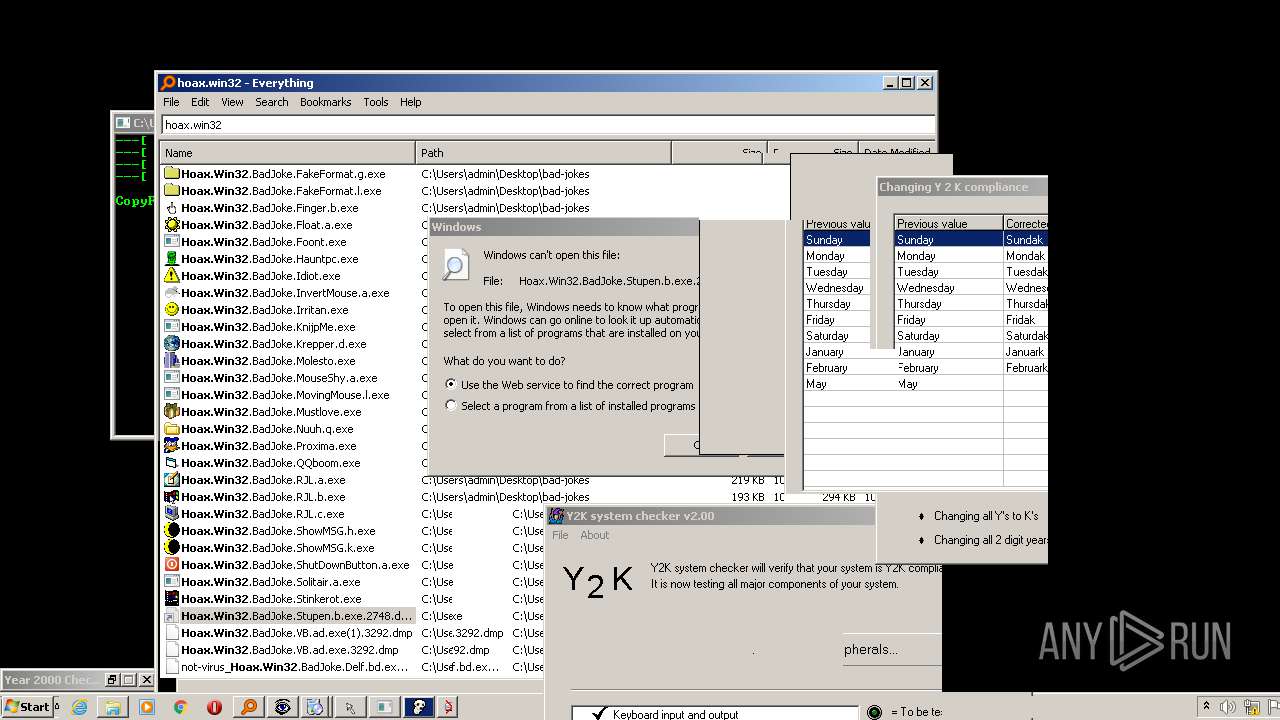
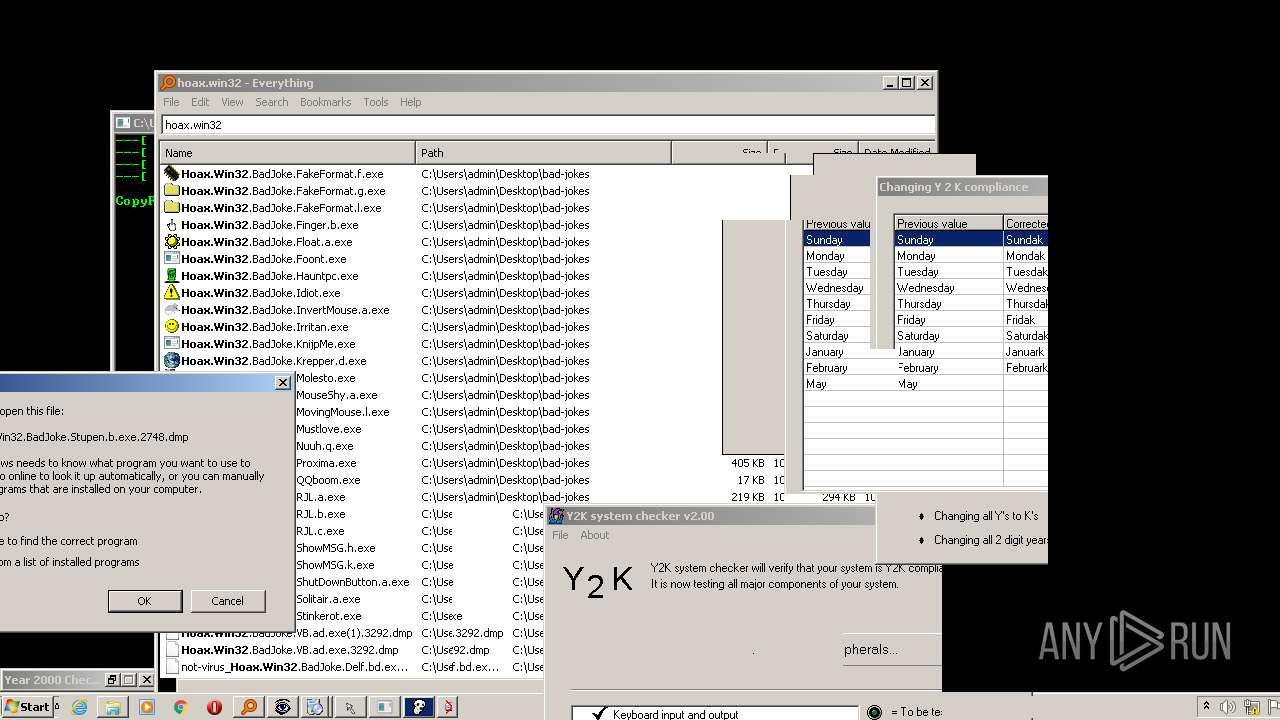
- Hoax.Win32.BadJoke.Stupen.b.exe (PID: 2748)
- Hoax.Win32.BadJoke.Stupen.a.exe (PID: 3392)
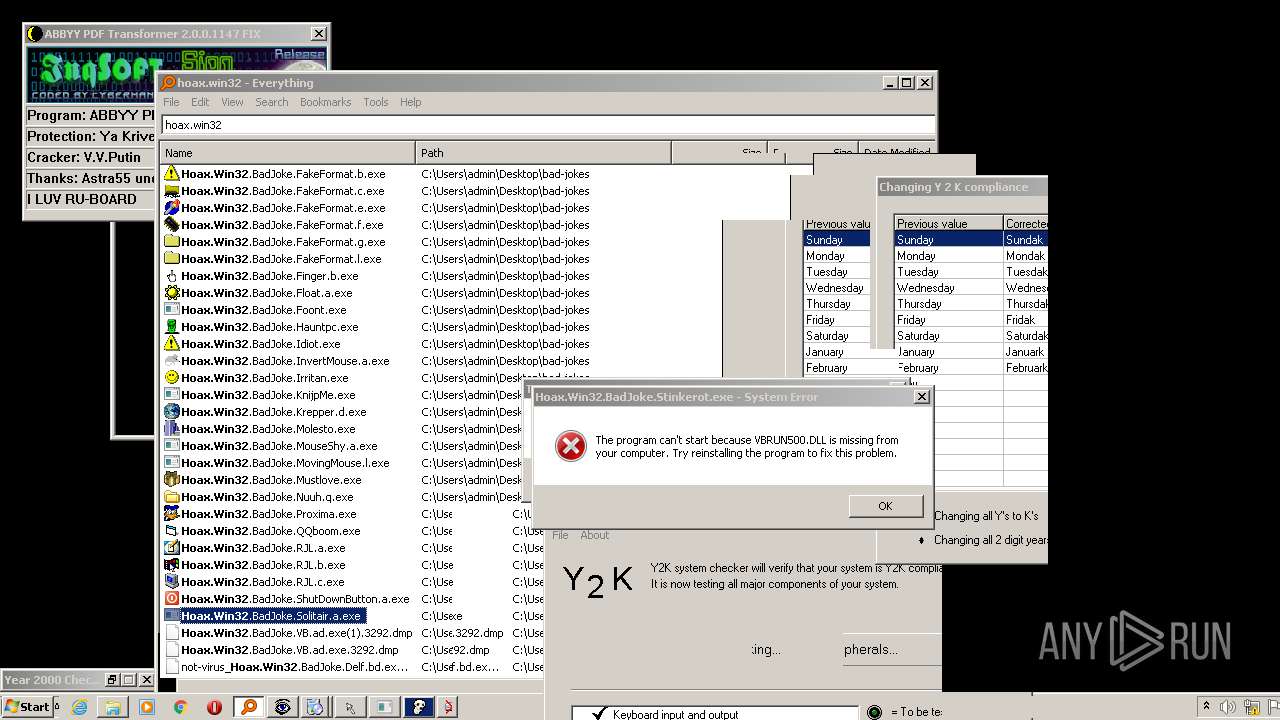
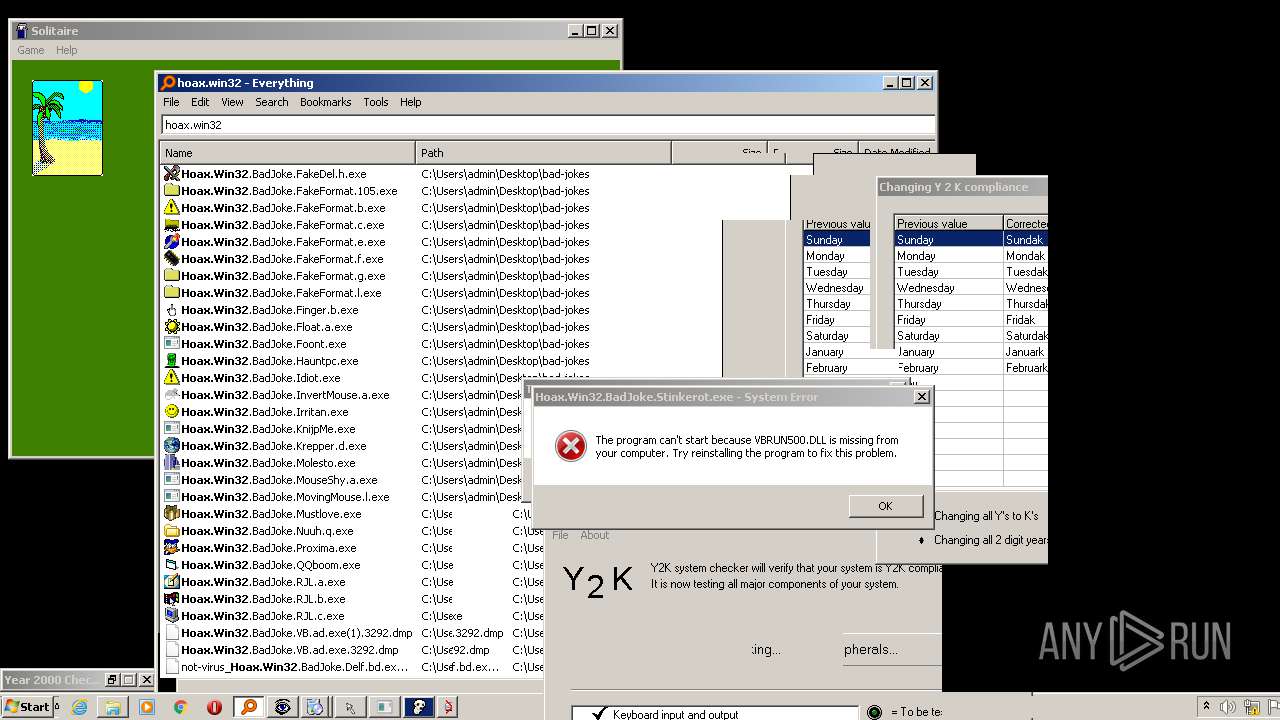
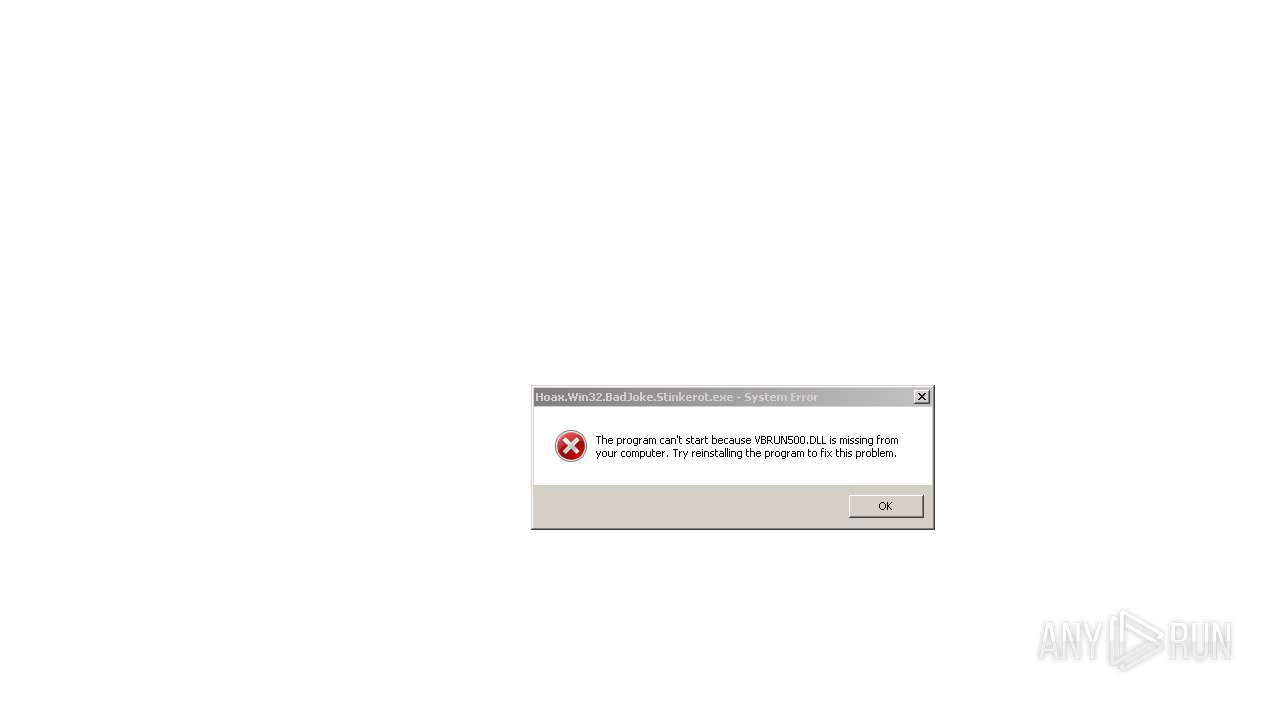
- Hoax.Win32.BadJoke.Stinkerot.exe (PID: 2148)
- Hoax.Win32.BadJoke.Stript.exe (PID: 2668)
- Hoax.Win32.BadJoke.ShowMSG.h.exe (PID: 3604)
- Hoax.Win32.BadJoke.ShowMSG.k.exe (PID: 4032)
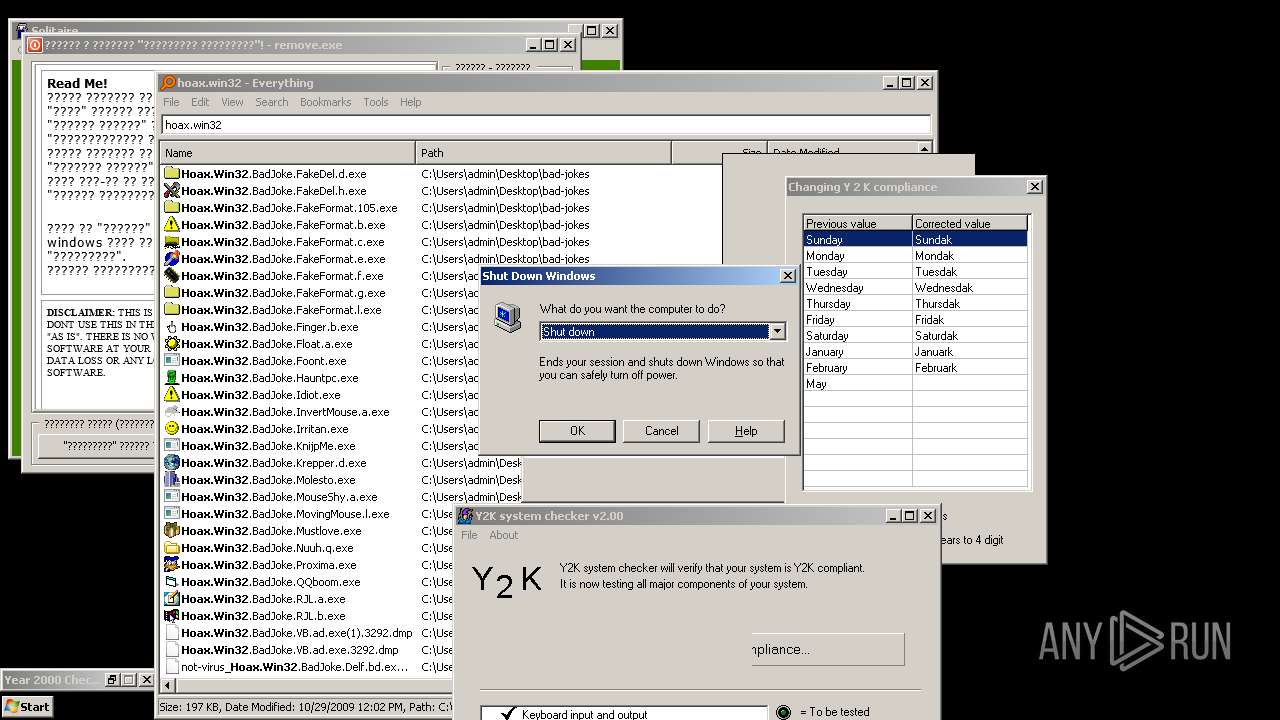
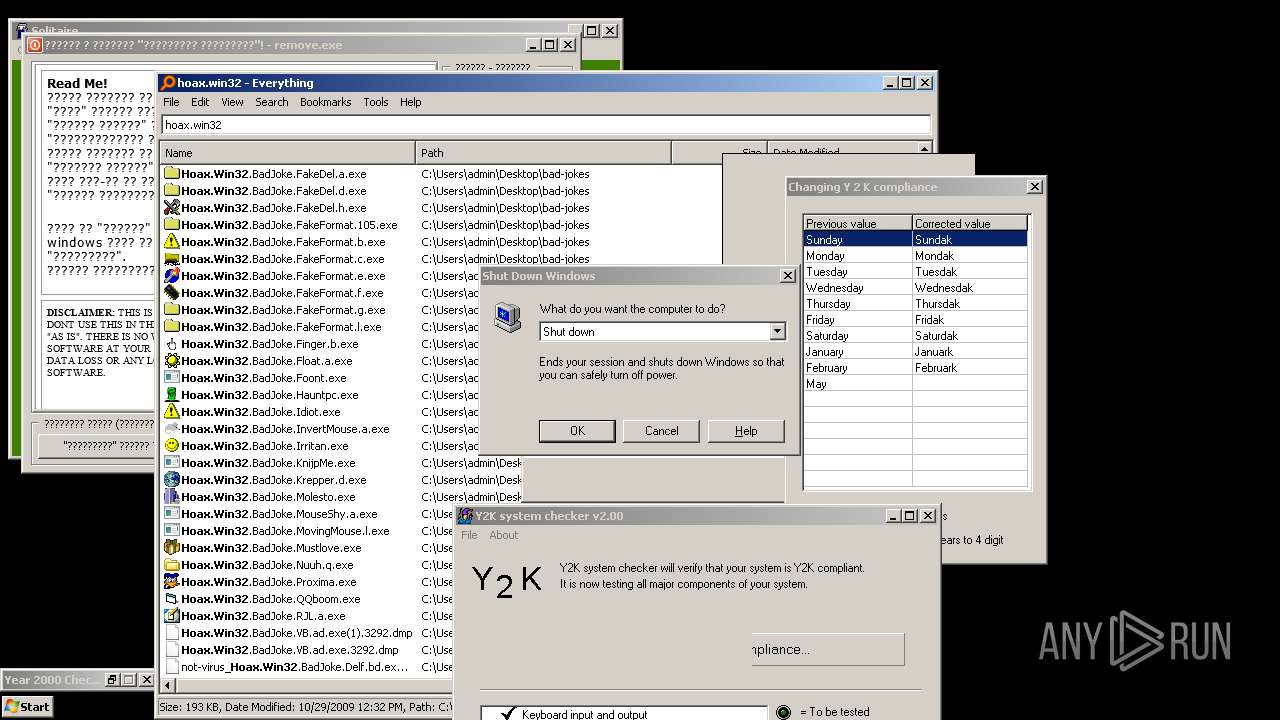
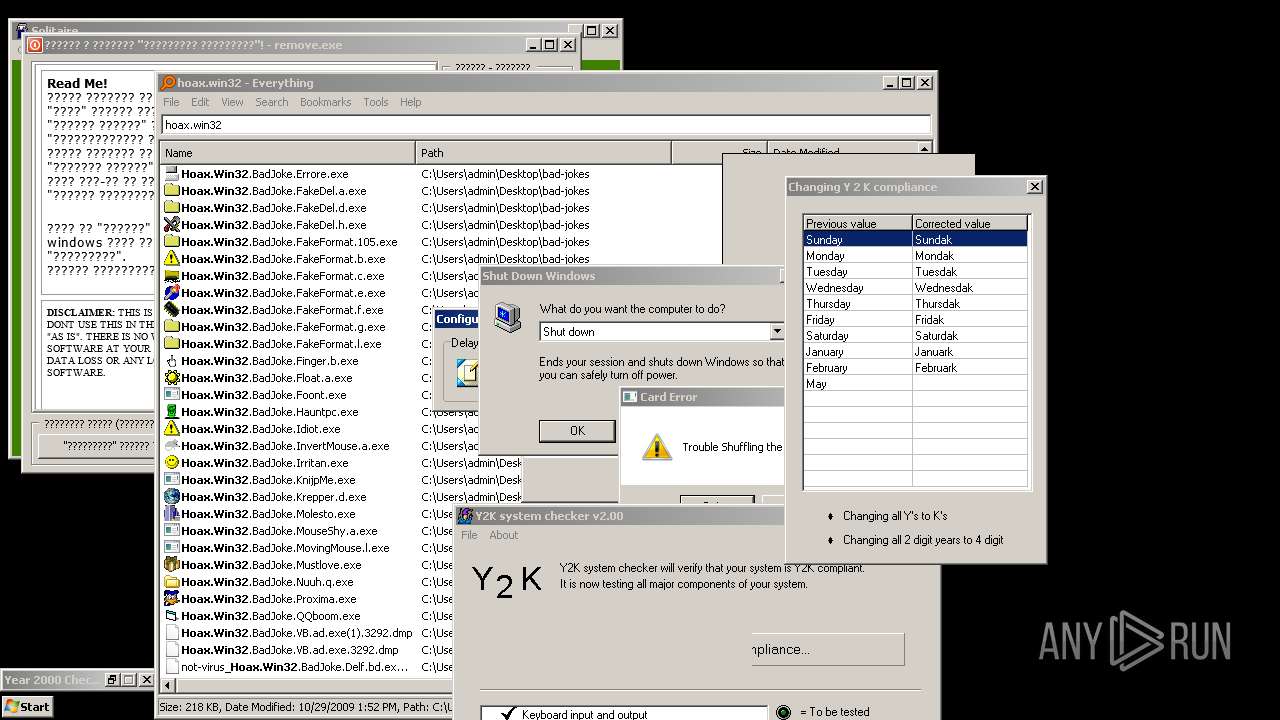
- Hoax.Win32.BadJoke.ShutDownButton.a.exe (PID: 2244)
- Hoax.Win32.BadJoke.ShutDownButton.a.exe (PID: 1064)
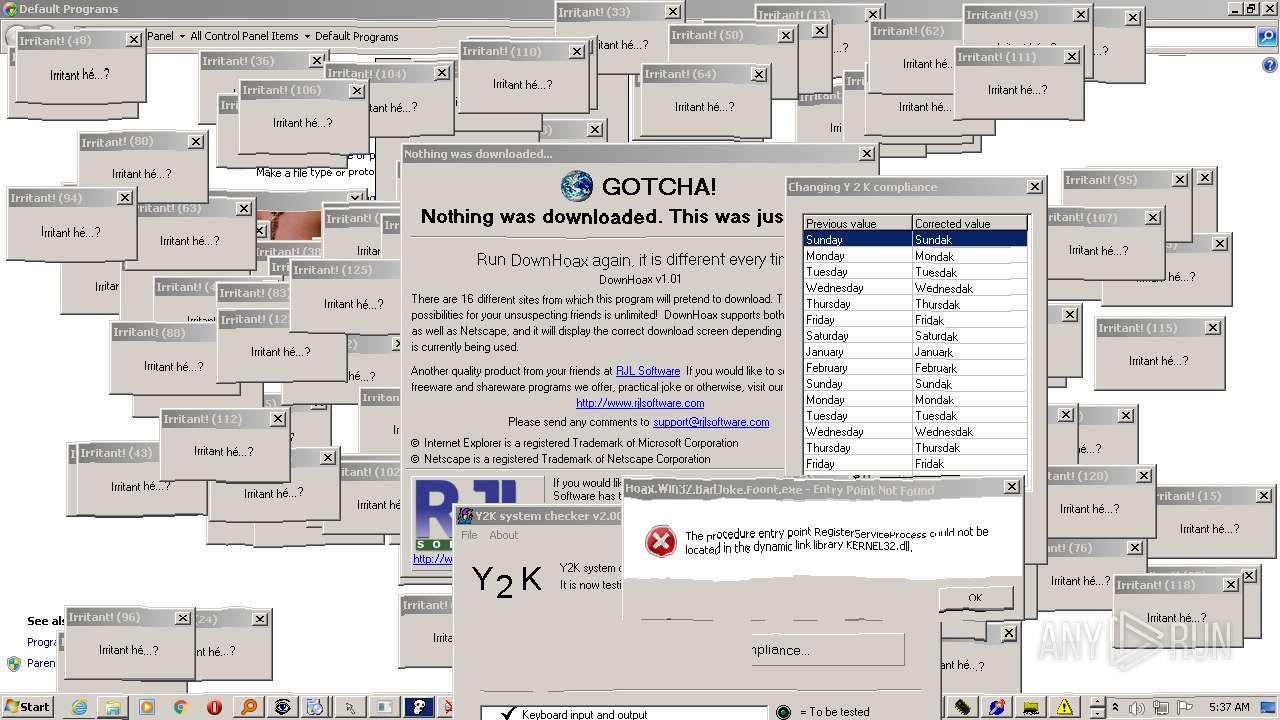
- Hoax.Win32.BadJoke.RJL.a.exe (PID: 2592)
- Hoax.Win32.BadJoke.RJL.b.exe (PID: 2312)
- Hoax.Win32.BadJoke.RJL.c.exe (PID: 2204)
- Hoax.Win32.BadJoke.Proxima.exe (PID: 536)
- Hoax.Win32.BadJoke.QQboom.exe (PID: 3968)
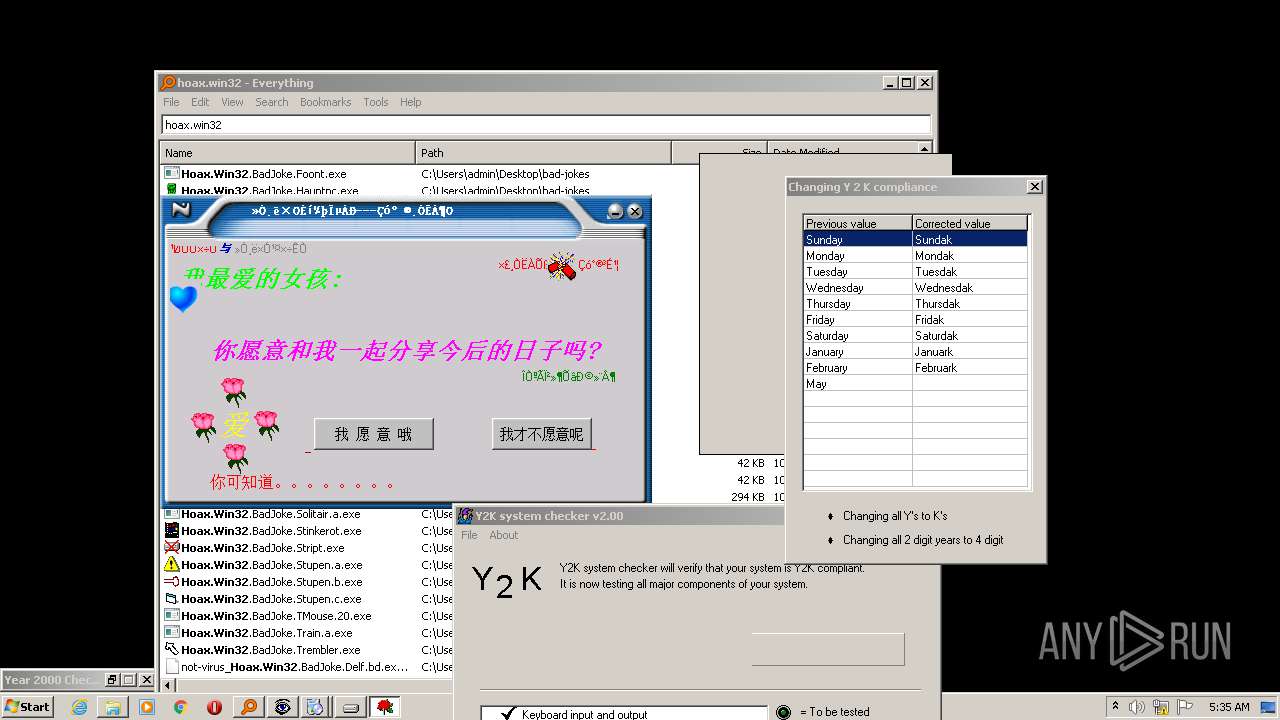
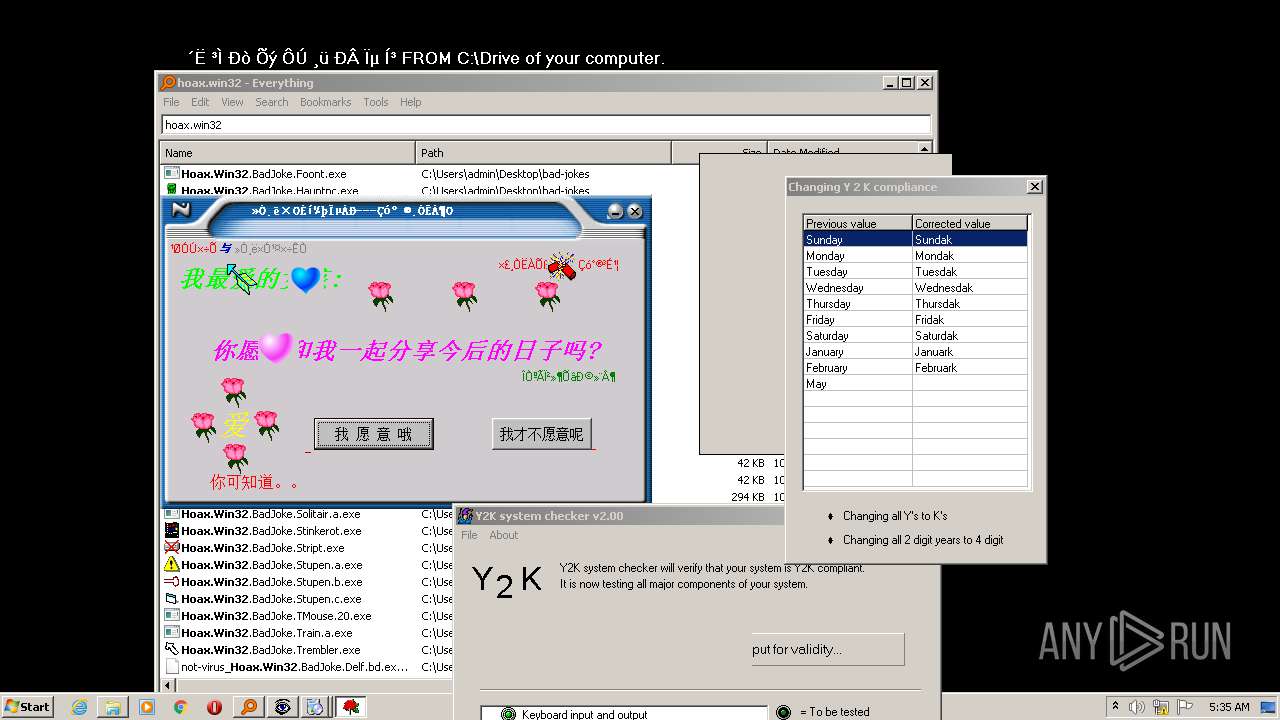
- Hoax.Win32.BadJoke.Mustlove.exe (PID: 572)
- Everything.exe (PID: 3236)
- Hoax.Win32.BadJoke.Krepper.d.exe (PID: 2528)
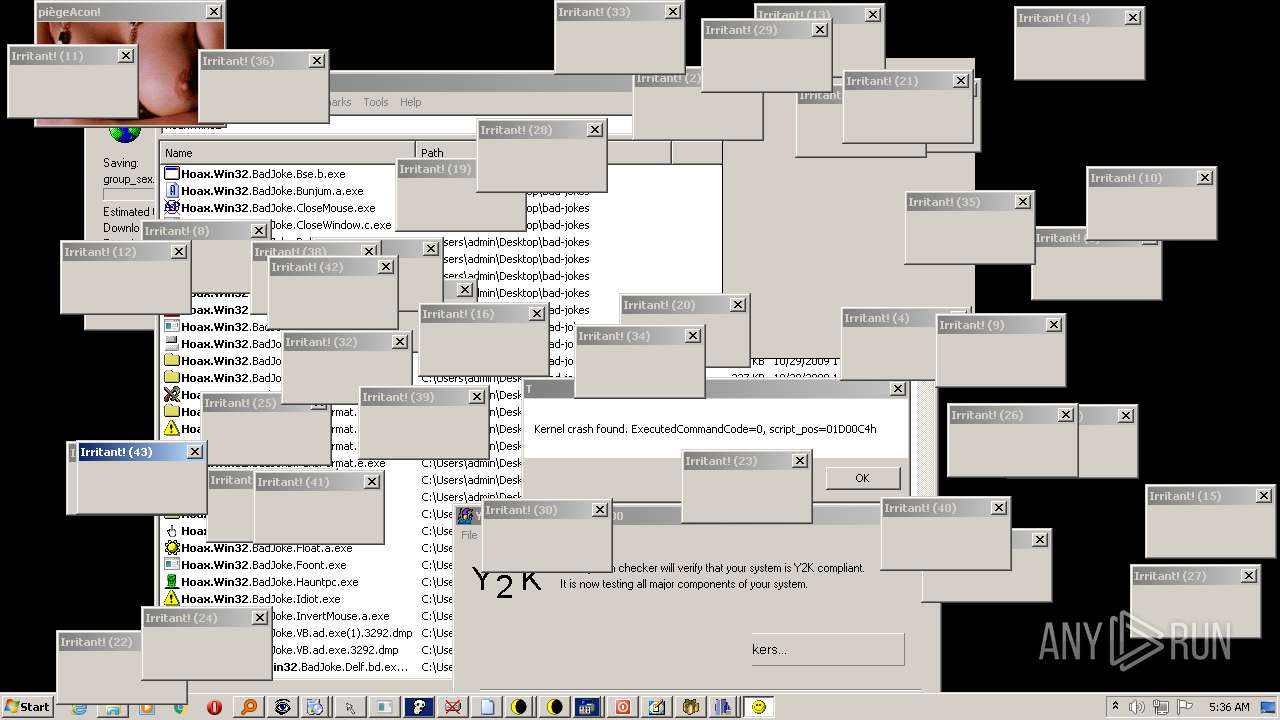
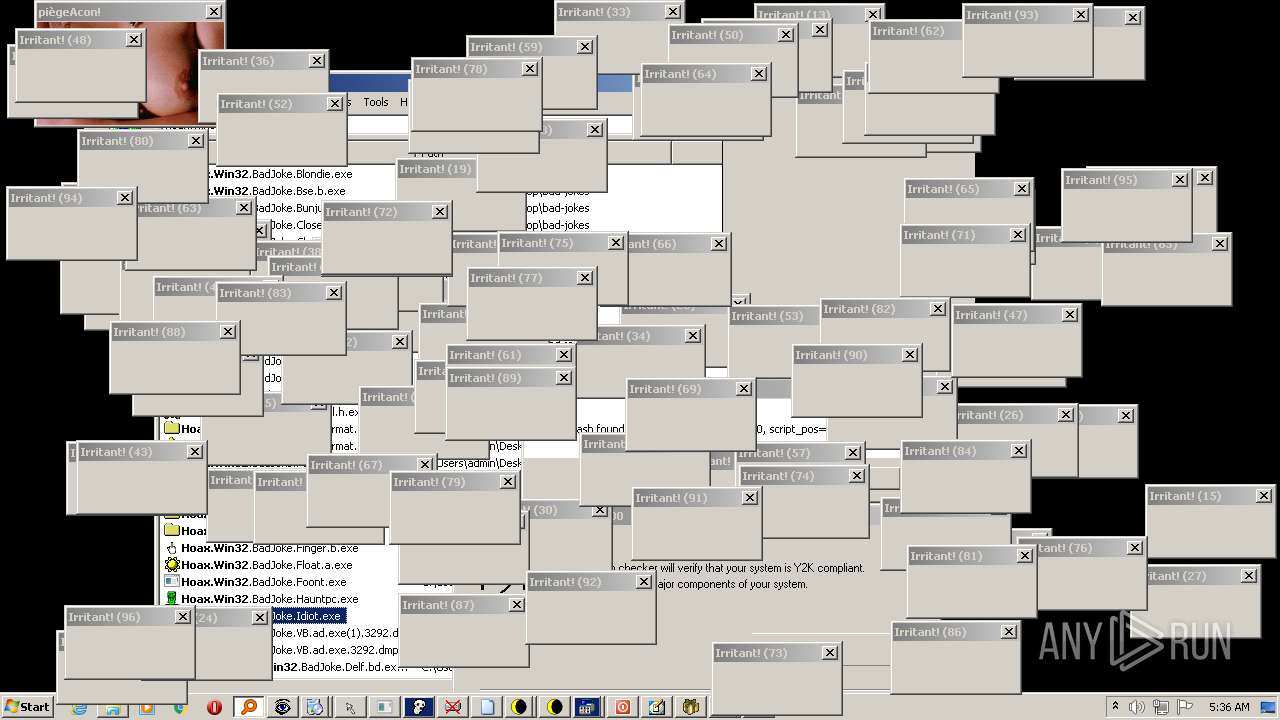
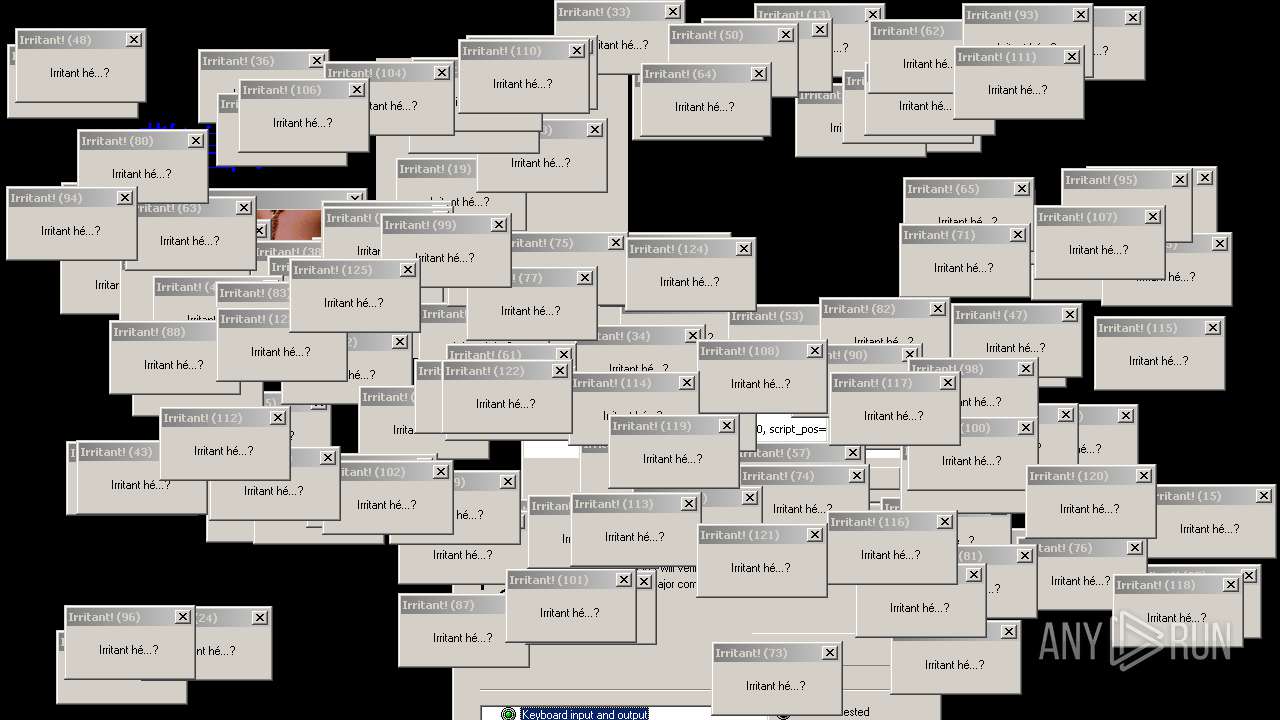
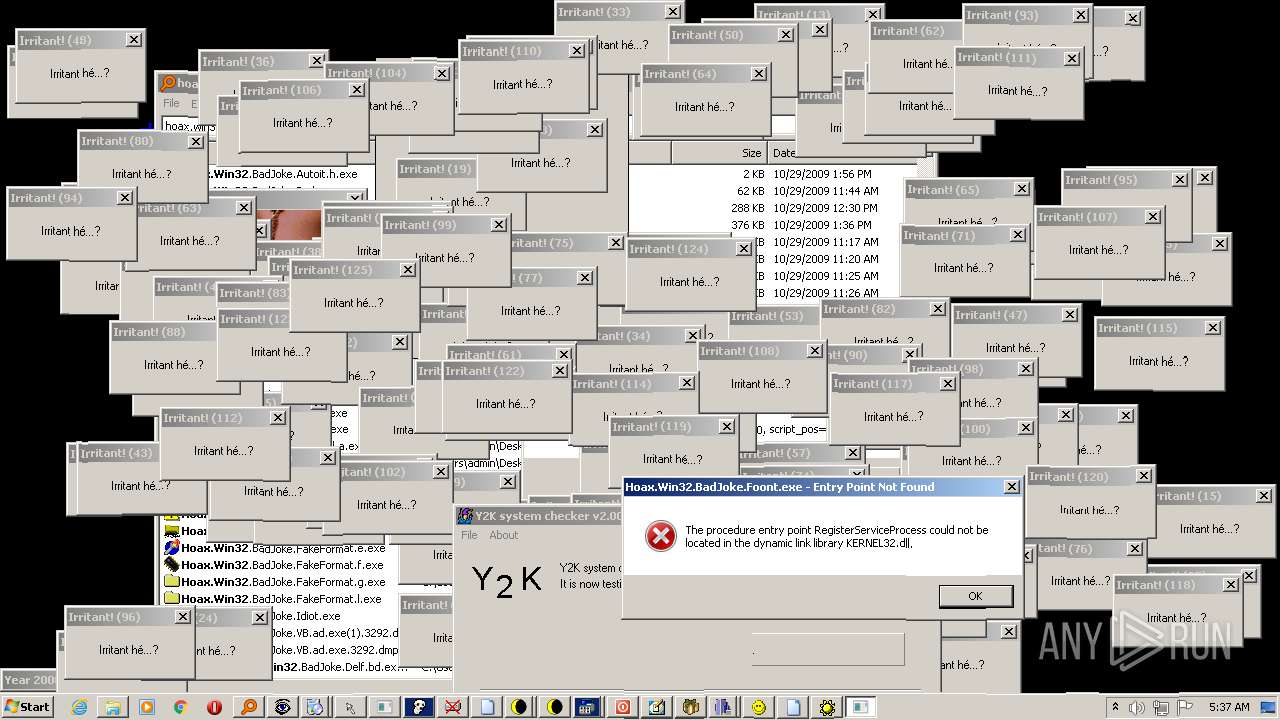
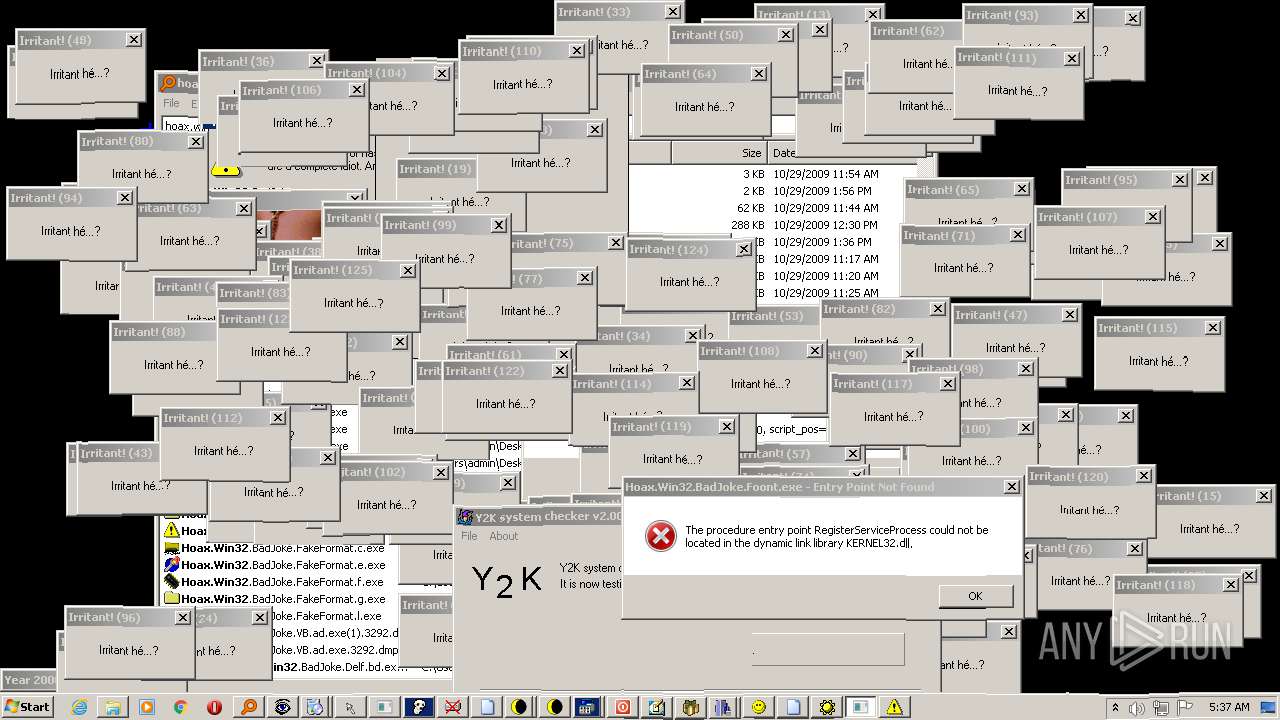
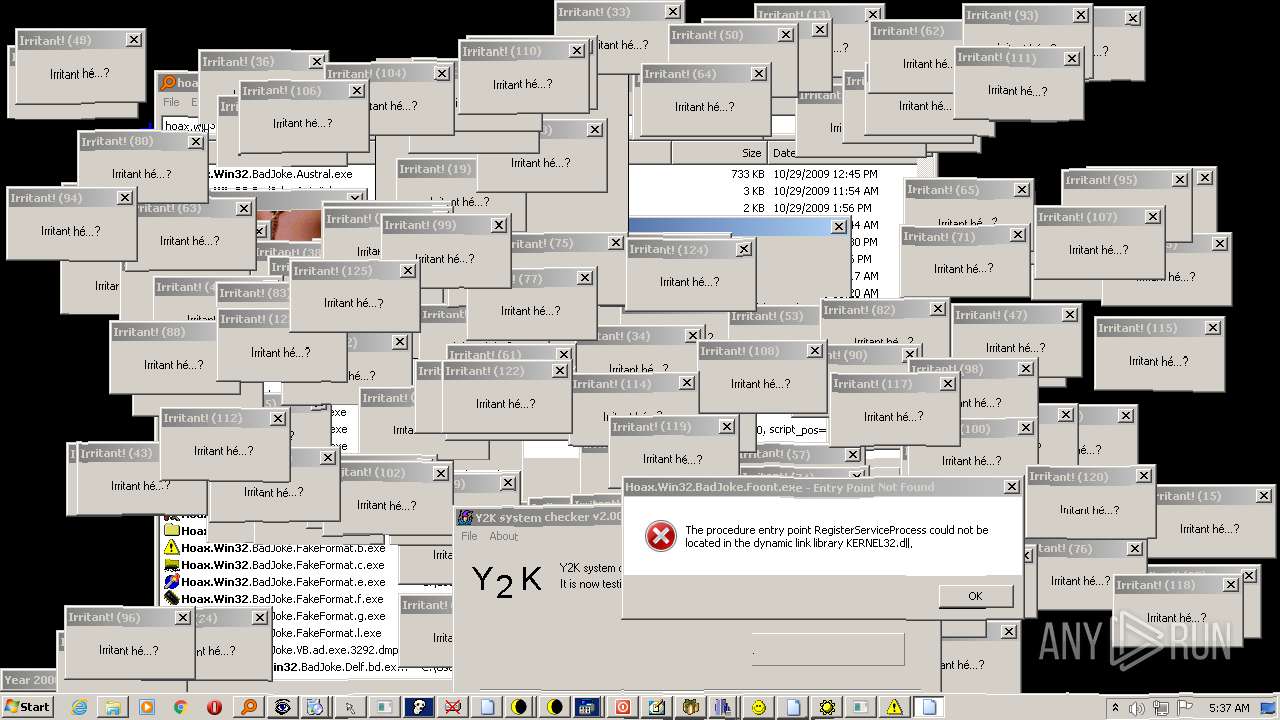
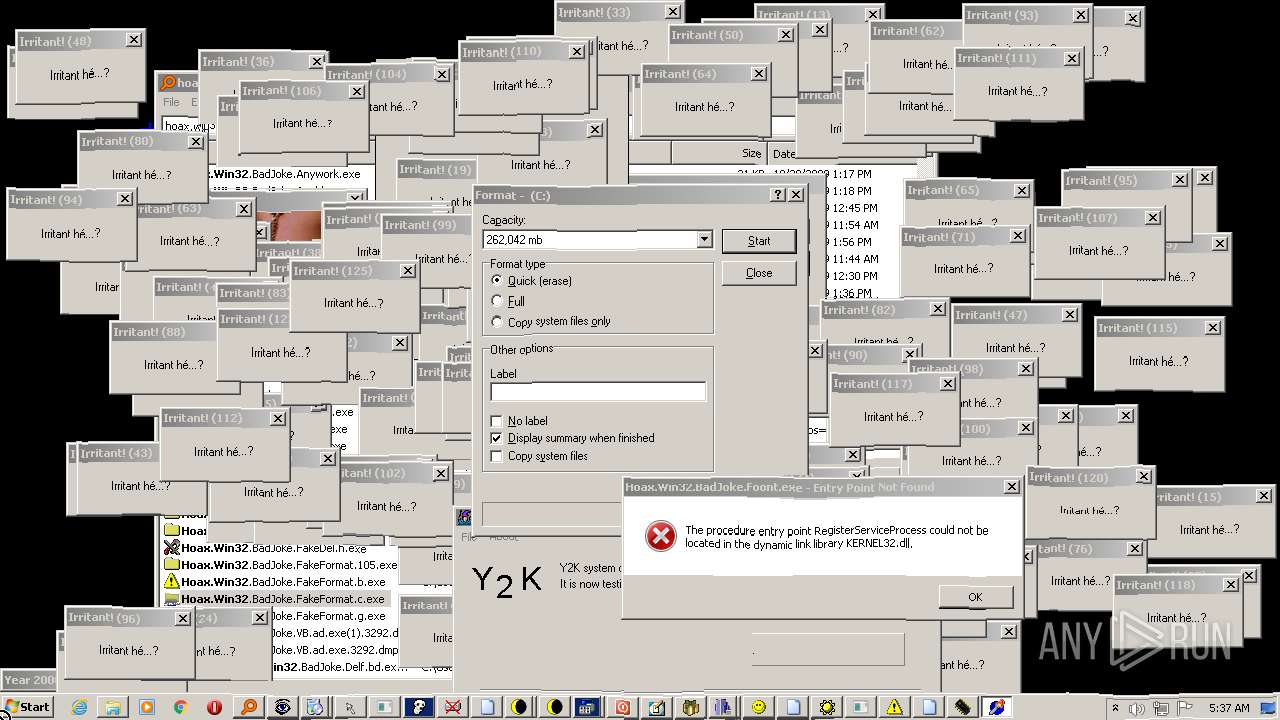
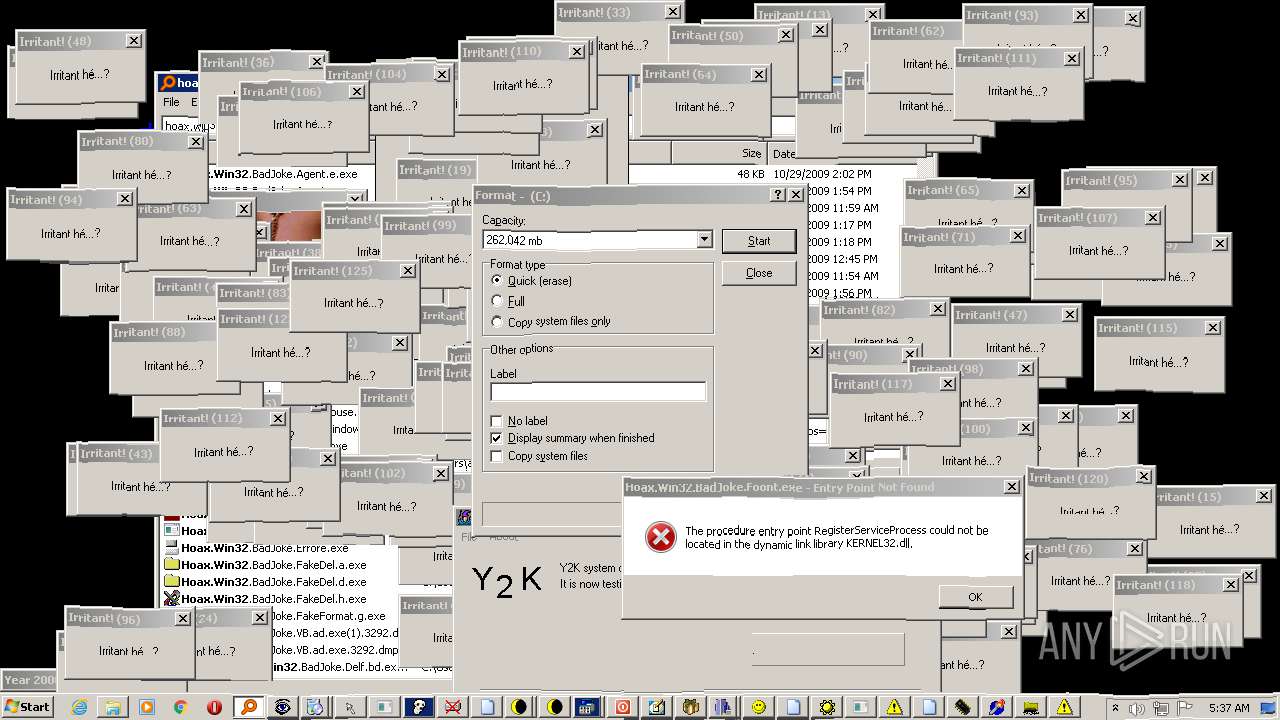
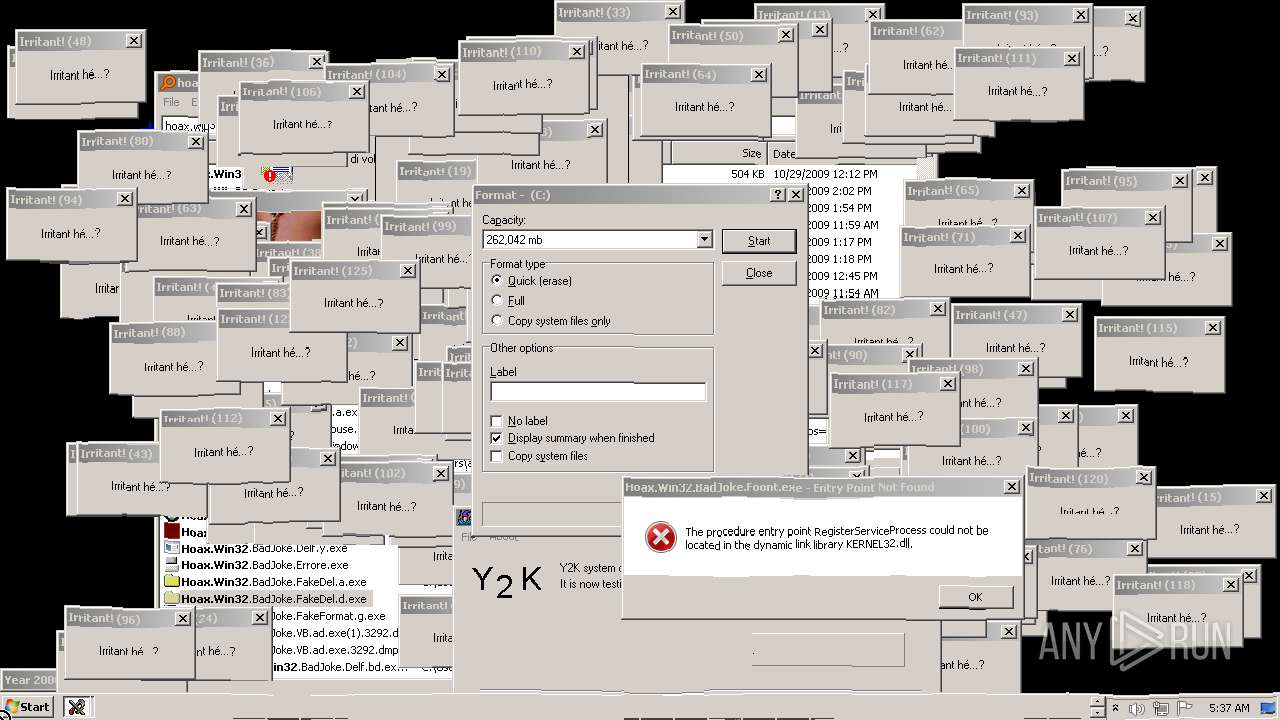
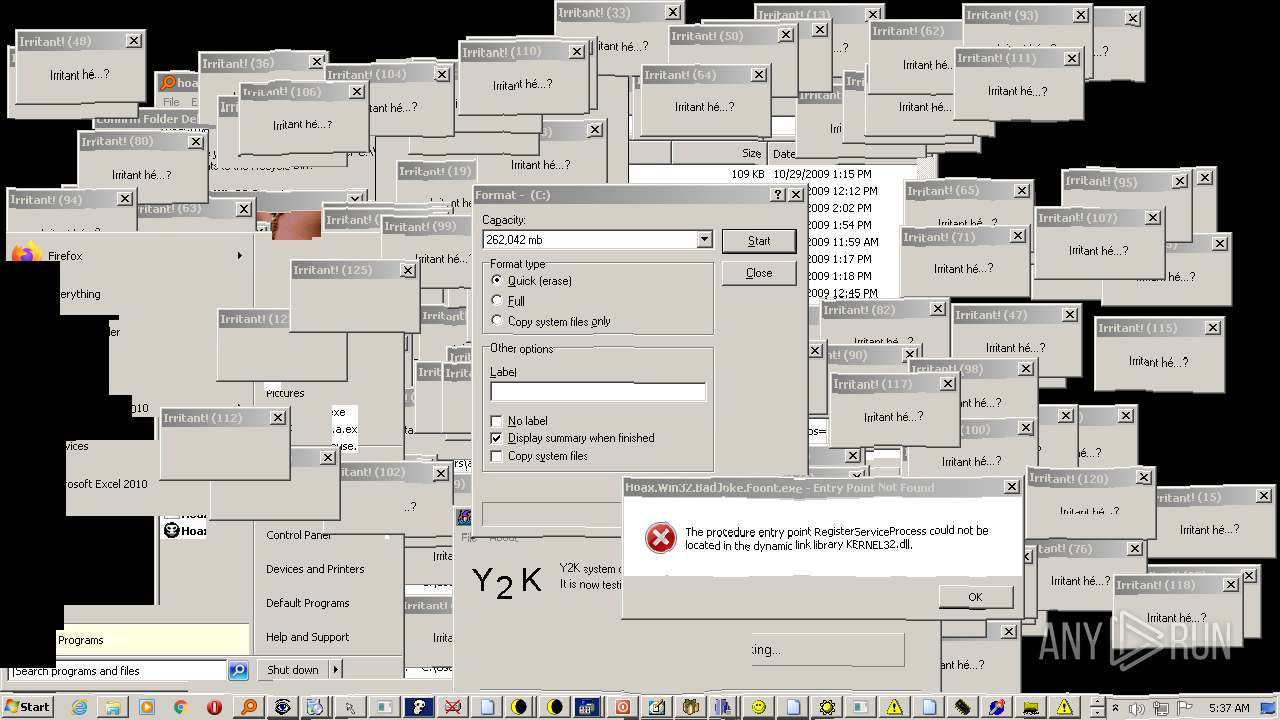
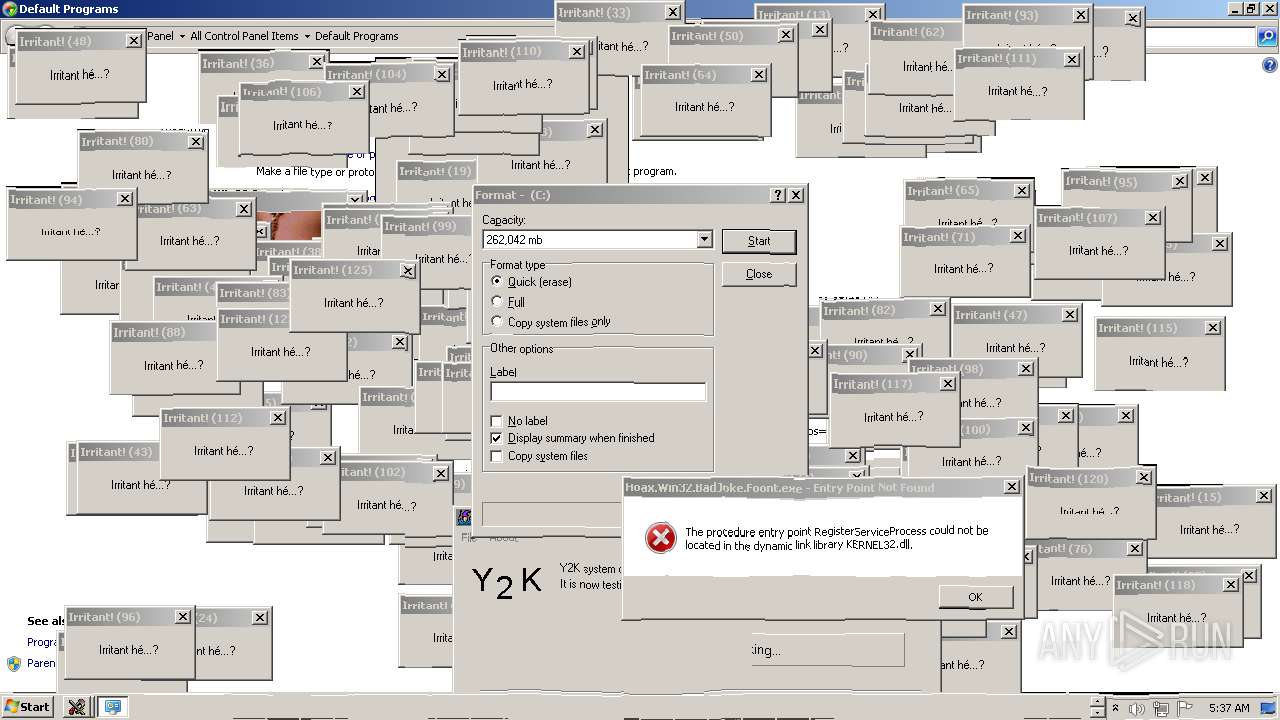
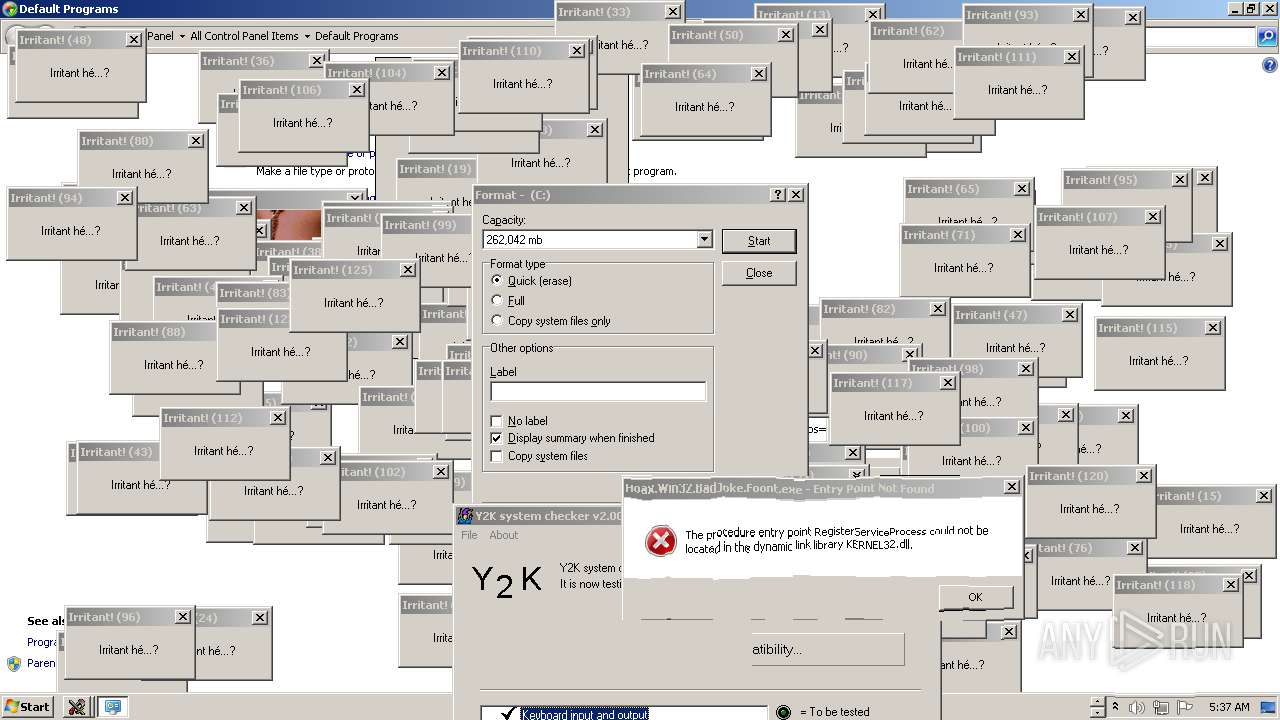
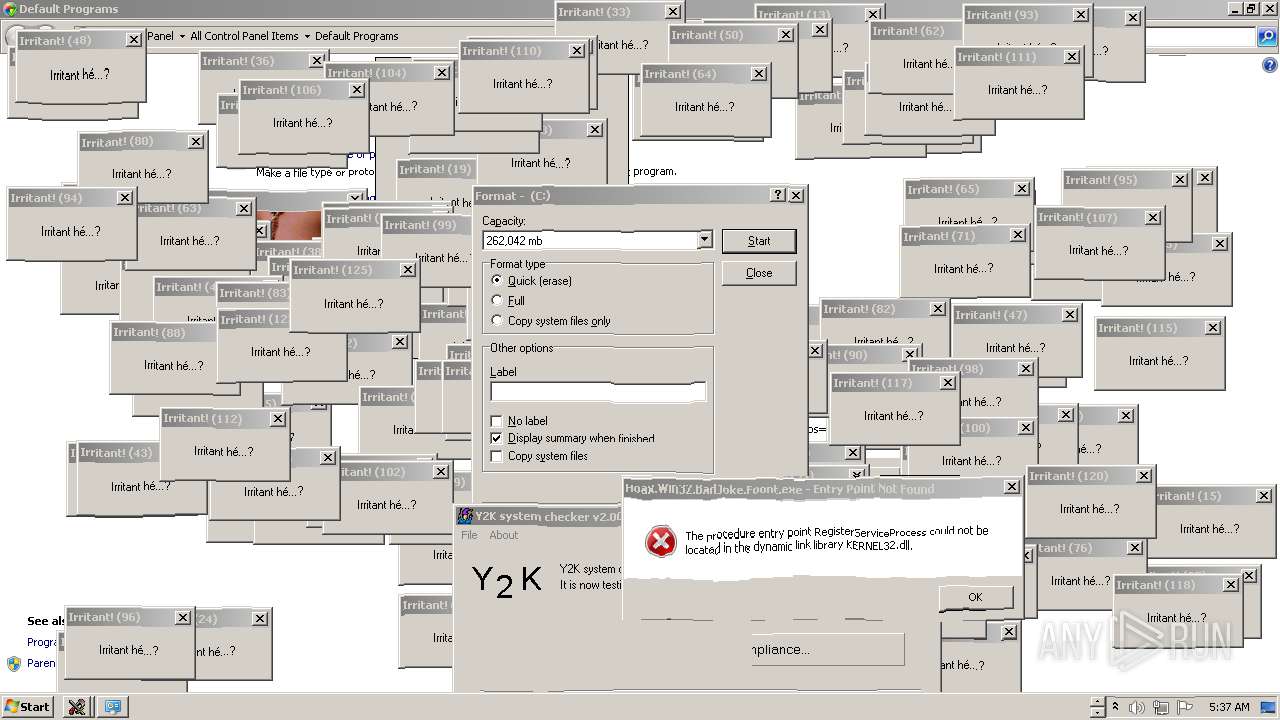
- Hoax.Win32.BadJoke.Irritan.exe (PID: 2148)
- Hoax.Win32.BadJoke.InvertMouse.a.exe (PID: 2684)
- Hoax.Win32.BadJoke.Nuuh.q.exe (PID: 924)
- Hoax.Win32.BadJoke.Molesto.exe (PID: 528)
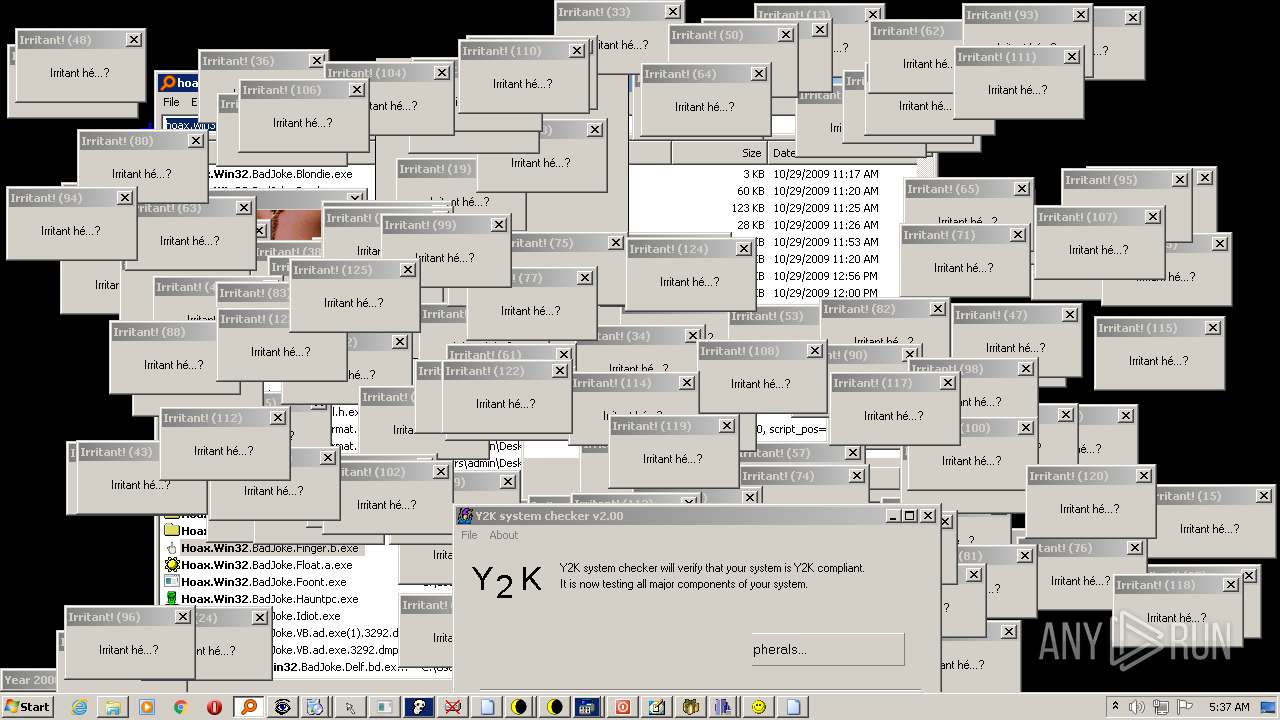
- Hoax.Win32.BadJoke.Finger.b.exe (PID: 1844)
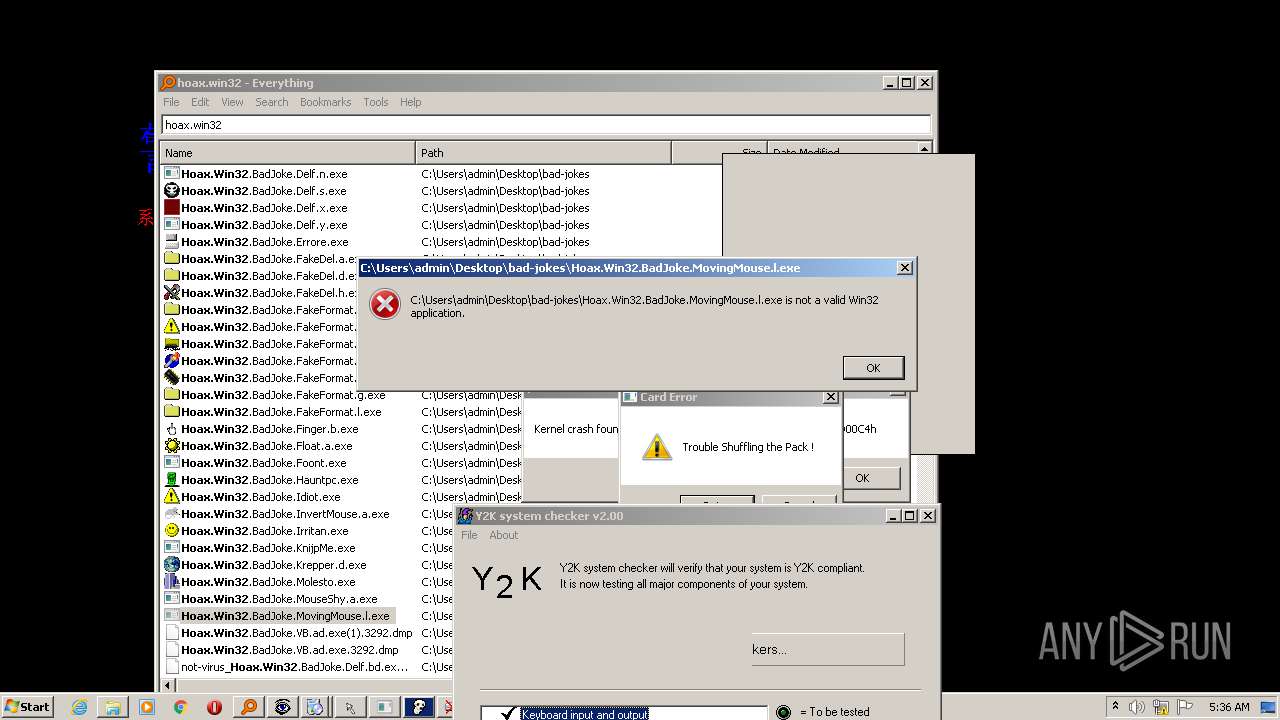
- Hoax.Win32.BadJoke.Float.a.exe (PID: 3160)
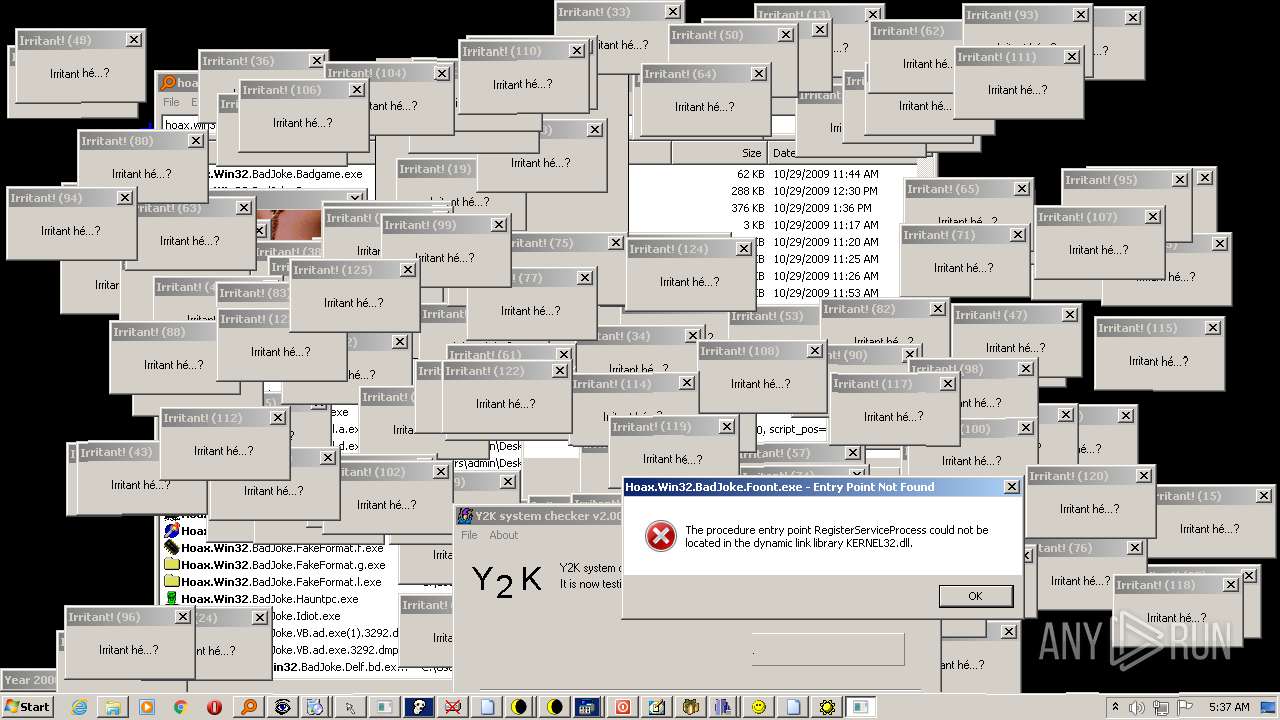
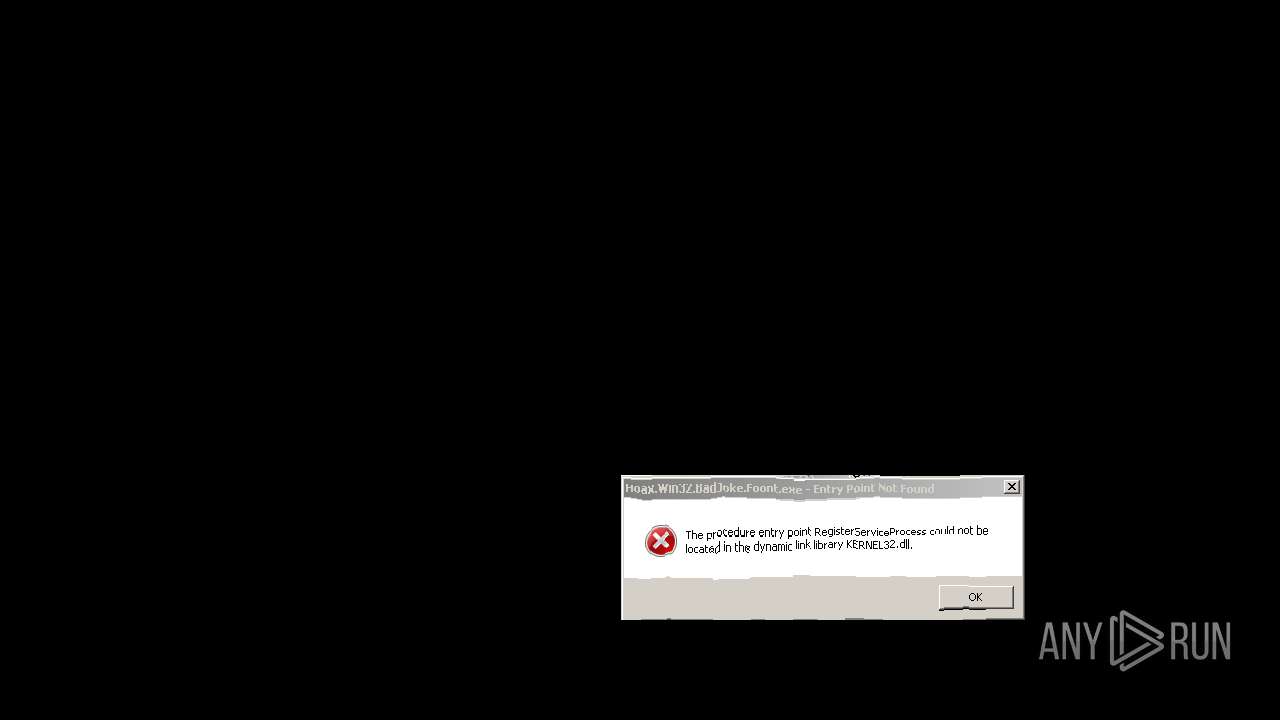
- Hoax.Win32.BadJoke.Foont.exe (PID: 1408)
- Hoax.Win32.BadJoke.Hauntpc.exe (PID: 3268)
- Hoax.Win32.BadJoke.Idiot.exe (PID: 3848)
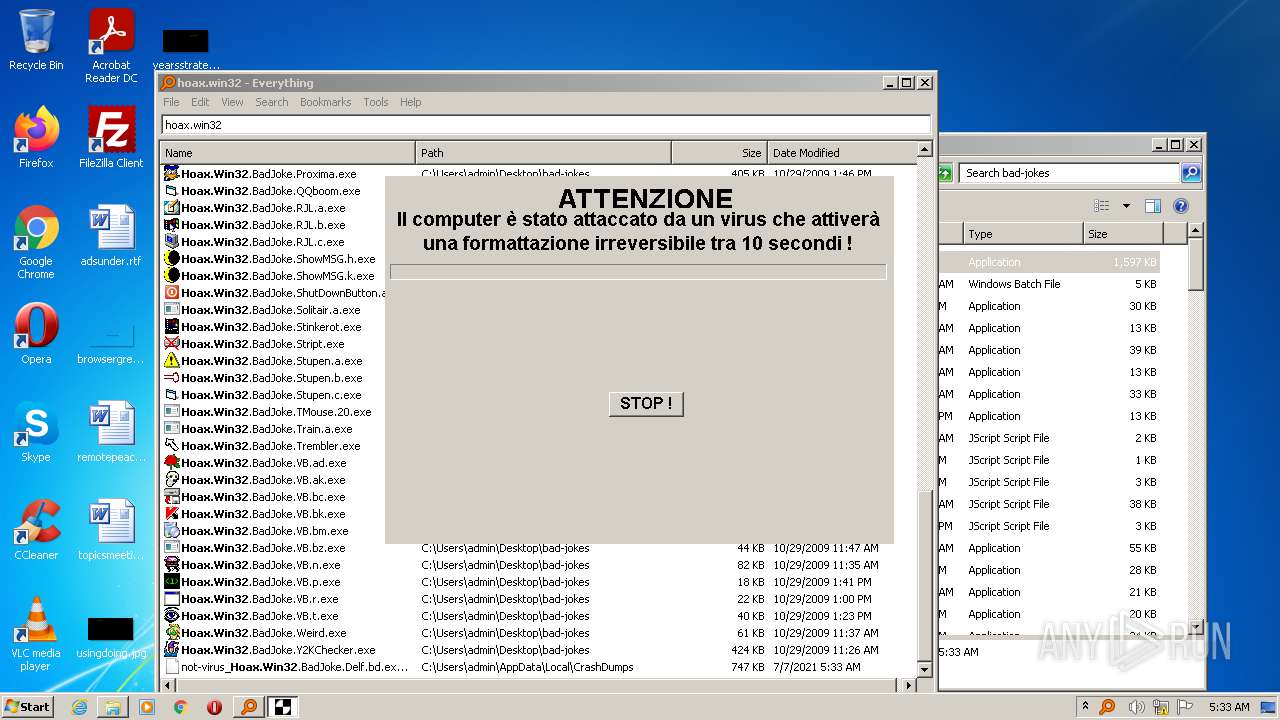
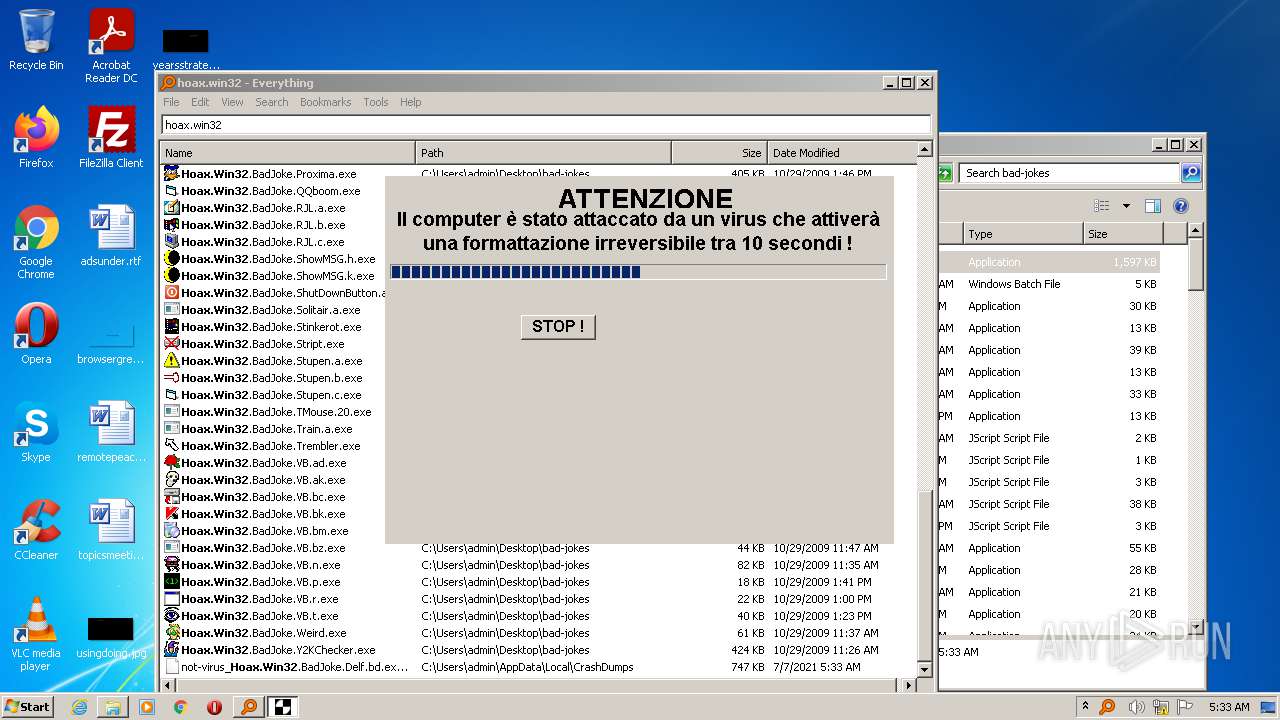
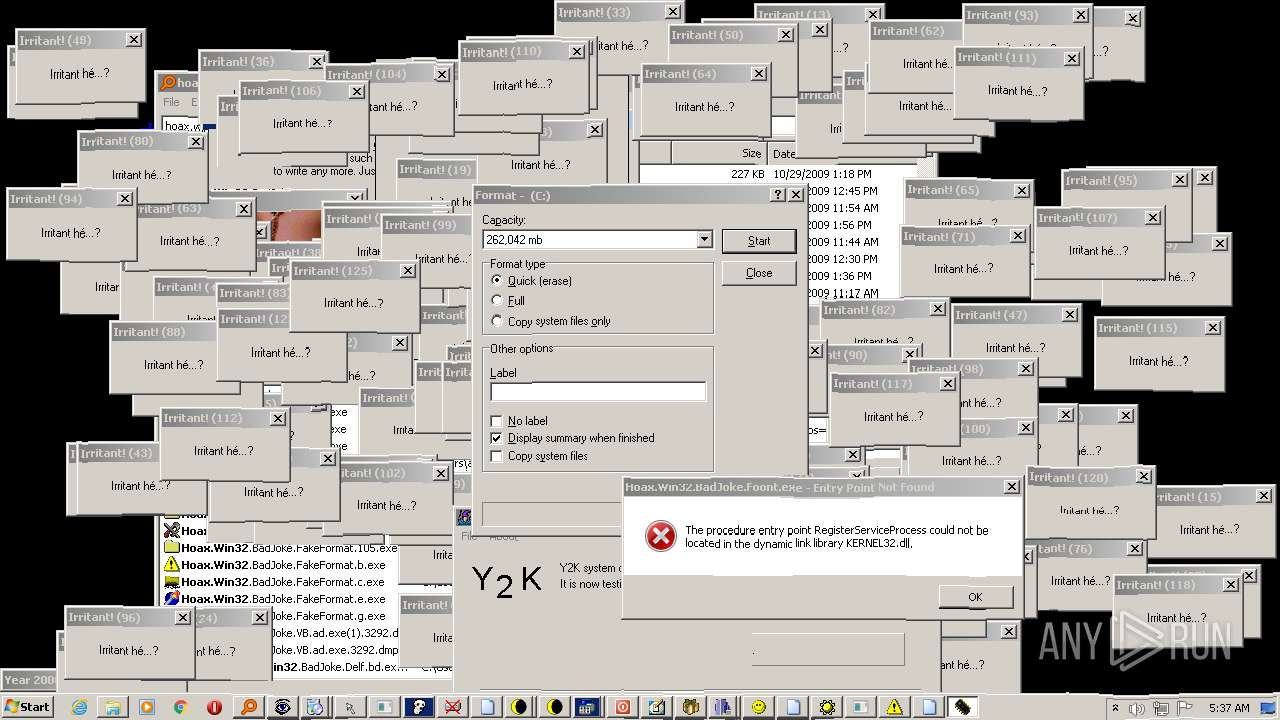
- Hoax.Win32.BadJoke.FakeFormat.l.exe (PID: 3988)
- Hoax.Win32.BadJoke.FakeFormat.f.exe (PID: 2744)
- Hoax.Win32.BadJoke.FakeFormat.e.exe (PID: 3136)
- Hoax.Win32.BadJoke.FakeFormat.c.exe (PID: 2780)
- Hoax.Win32.BadJoke.FakeFormat.105.exe (PID: 3724)
- Hoax.Win32.BadJoke.FakeDel.h.exe (PID: 3156)
- Hoax.Win32.BadJoke.FakeDel.h.exe (PID: 2464)
- Hoax.Win32.BadJoke.FakeDel.d.exe (PID: 1616)
- Hoax.Win32.BadJoke.FakeDel.d.exe (PID: 2296)
- Hoax.Win32.BadJoke.FakeFormat.b.exe (PID: 2868)
Drops executable file immediately after starts
- everything-setup.exe (PID: 3424)
- Everything.exe (PID: 2948)
- Hoax.Win32.BadJoke.Nuuh.q.exe (PID: 924)
Changes the autorun value in the registry
- Everything.exe (PID: 2360)
- Hoax.Win32.BadJoke.Stupen.b.exe (PID: 2748)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 1116)
- everything-setup.exe (PID: 3424)
- Everything.exe (PID: 3796)
- Everything.exe (PID: 2948)
- Everything.exe (PID: 2360)
- Everything.exe (PID: 3612)
- Everything.exe (PID: 3912)
- Everything.exe (PID: 724)
- Hoax.Win32.BadJoke.VB.bm.exe (PID: 3740)
- Hoax.Win32.BadJoke.VB.ak.exe (PID: 3520)
- Hoax.Win32.BadJoke.ShowMSG.k.exe (PID: 4032)
- Hoax.Win32.BadJoke.ShowMSG.h.exe (PID: 3604)
- Hoax.Win32.BadJoke.ShutDownButton.a.exe (PID: 1064)
- Hoax.Win32.BadJoke.Proxima.exe (PID: 536)
- Hoax.Win32.BadJoke.Y2KChecker.exe (PID: 312)
- Hoax.Win32.BadJoke.Nuuh.q.exe (PID: 924)
- Everything.exe (PID: 3236)
- Hoax.Win32.BadJoke.FakeDel.d.exe (PID: 1616)
- Hoax.Win32.BadJoke.FakeDel.d.exe (PID: 2296)
Checks supported languages
- WinRAR.exe (PID: 1116)
- everything-setup.exe (PID: 3424)
- Everything.exe (PID: 3796)
- Everything.exe (PID: 2948)
- Everything.exe (PID: 3612)
- Everything.exe (PID: 2360)
- Everything.exe (PID: 3912)
- Everything.exe (PID: 724)
- Hoax.Win32.BadJoke.Zappa.exe (PID: 2556)
- Hoax.Win32.BadJoke.Y2KChecker.exe (PID: 312)
- Hoax.Win32.BadJoke.Weird.exe (PID: 2816)
- Hoax.Win32.BadJoke.VB.t.exe (PID: 3492)
- Hoax.Win32.BadJoke.VB.bm.exe (PID: 3740)
- Hoax.Win32.BadJoke.VB.bc.exe (PID: 468)
- Hoax.Win32.BadJoke.VB.ak.exe (PID: 3520)
- Hoax.Win32.BadJoke.VB.ad.exe (PID: 3292)
- Hoax.Win32.BadJoke.Trembler.exe (PID: 2724)
- Hoax.Win32.BadJoke.Train.a.exe (PID: 3040)
- Hoax.Win32.BadJoke.TMouse.20.exe (PID: 1592)
- cmd.exe (PID: 1512)
- Hoax.Win32.BadJoke.Stupen.b.exe (PID: 2748)
- Hoax.Win32.BadJoke.Stupen.a.exe (PID: 3392)
- Hoax.Win32.BadJoke.Stript.exe (PID: 2668)
- Hoax.Win32.BadJoke.ShowMSG.h.exe (PID: 3604)
- Hoax.Win32.BadJoke.ShowMSG.k.exe (PID: 4032)
- Hoax.Win32.BadJoke.ShutDownButton.a.exe (PID: 1064)
- Hoax.Win32.BadJoke.RJL.c.exe (PID: 2204)
- Hoax.Win32.BadJoke.RJL.b.exe (PID: 2312)
- Hoax.Win32.BadJoke.RJL.a.exe (PID: 2592)
- Hoax.Win32.BadJoke.Proxima.exe (PID: 536)
- Hoax.Win32.BadJoke.QQboom.exe (PID: 3968)
- Hoax.Win32.BadJoke.Molesto.exe (PID: 528)
- Hoax.Win32.BadJoke.Krepper.d.exe (PID: 2528)
- Hoax.Win32.BadJoke.Irritan.exe (PID: 2148)
- Hoax.Win32.BadJoke.InvertMouse.a.exe (PID: 2684)
- Hoax.Win32.BadJoke.Mustlove.exe (PID: 572)
- Hoax.Win32.BadJoke.Nuuh.q.exe (PID: 924)
- Everything.exe (PID: 3236)
- Hoax.Win32.BadJoke.Idiot.exe (PID: 3848)
- Hoax.Win32.BadJoke.Finger.b.exe (PID: 1844)
- Hoax.Win32.BadJoke.Float.a.exe (PID: 3160)
- Hoax.Win32.BadJoke.FakeFormat.l.exe (PID: 3988)
- Hoax.Win32.BadJoke.FakeFormat.f.exe (PID: 2744)
- Hoax.Win32.BadJoke.FakeFormat.e.exe (PID: 3136)
- Hoax.Win32.BadJoke.FakeFormat.c.exe (PID: 2780)
- Hoax.Win32.BadJoke.FakeFormat.b.exe (PID: 2868)
- Hoax.Win32.BadJoke.FakeFormat.105.exe (PID: 3724)
- Hoax.Win32.BadJoke.FakeDel.h.exe (PID: 3156)
- Hoax.Win32.BadJoke.FakeDel.h.exe (PID: 2464)
- Hoax.Win32.BadJoke.FakeDel.d.exe (PID: 1616)
- Hoax.Win32.BadJoke.FakeDel.d.exe (PID: 2296)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1116)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1116)
Executable content was dropped or overwritten
- everything-setup.exe (PID: 3424)
- Everything.exe (PID: 2948)
- WinRAR.exe (PID: 1116)
- Hoax.Win32.BadJoke.Nuuh.q.exe (PID: 924)
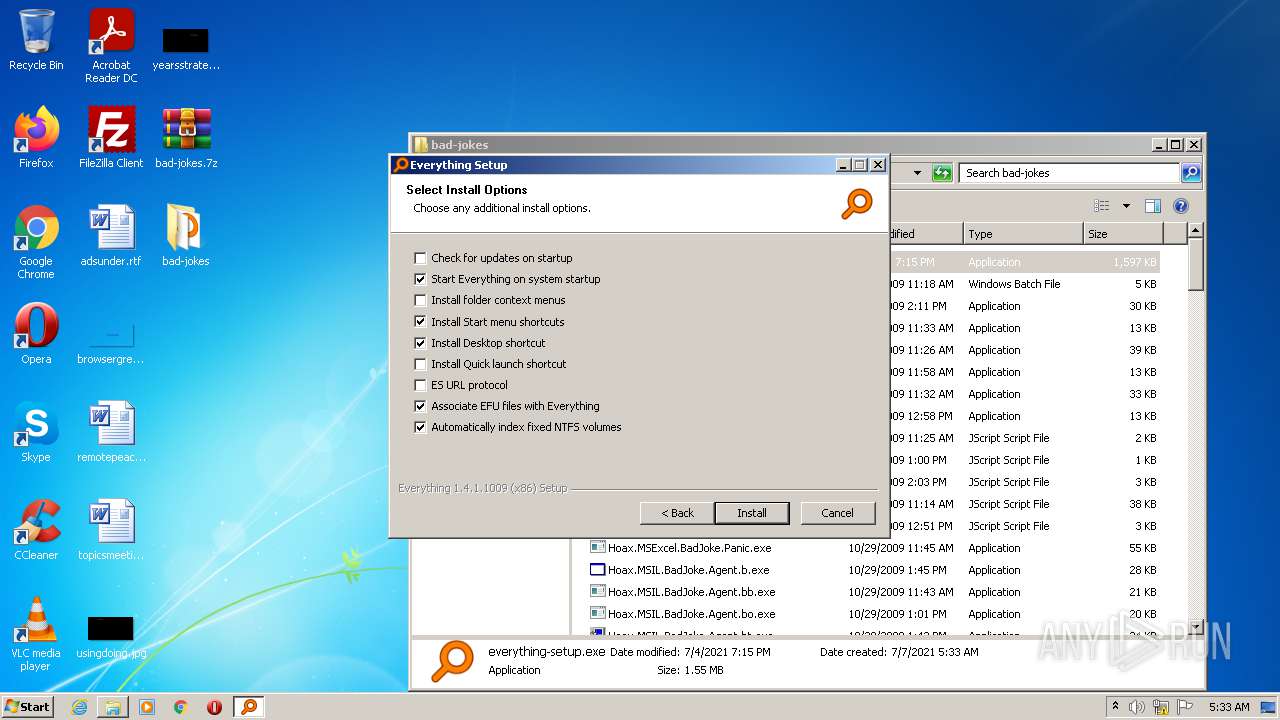
Application launched itself
- Everything.exe (PID: 3796)
Creates a directory in Program Files
- Everything.exe (PID: 2948)
Creates files in the program directory
- Everything.exe (PID: 2948)
- Everything.exe (PID: 2360)
Creates a software uninstall entry
- Everything.exe (PID: 2948)
Starts itself from another location
- Everything.exe (PID: 2948)
Drops a file with too old compile date
- WinRAR.exe (PID: 1116)
- Hoax.Win32.BadJoke.Nuuh.q.exe (PID: 924)
Changes default file association
- Everything.exe (PID: 2360)
Executed as Windows Service
- Everything.exe (PID: 3612)
Creates files in the user directory
- Everything.exe (PID: 3912)
Reads mouse settings
- Hoax.Win32.BadJoke.VB.ak.exe (PID: 3520)
Starts CMD.EXE for commands execution
- Hoax.Win32.BadJoke.TMouse.20.exe (PID: 1592)
Uses RUNDLL32.EXE to load library
- Everything.exe (PID: 724)
- Hoax.Win32.BadJoke.Train.a.exe (PID: 3040)
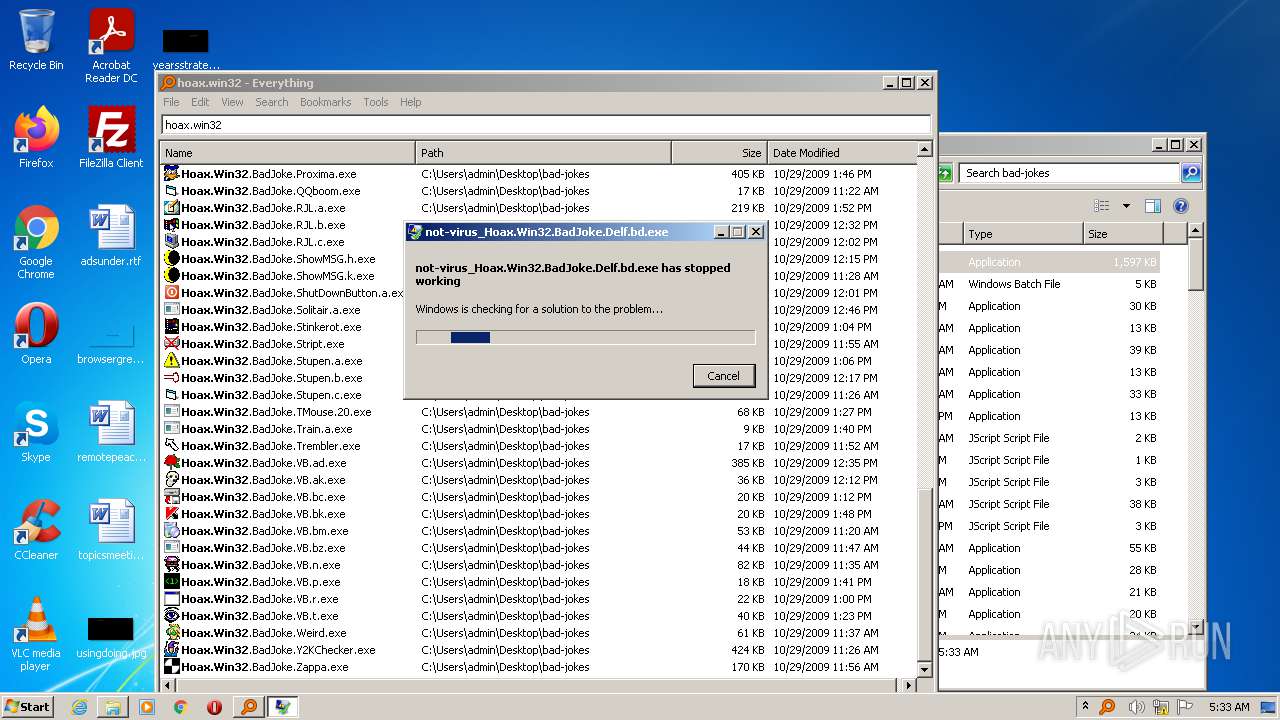
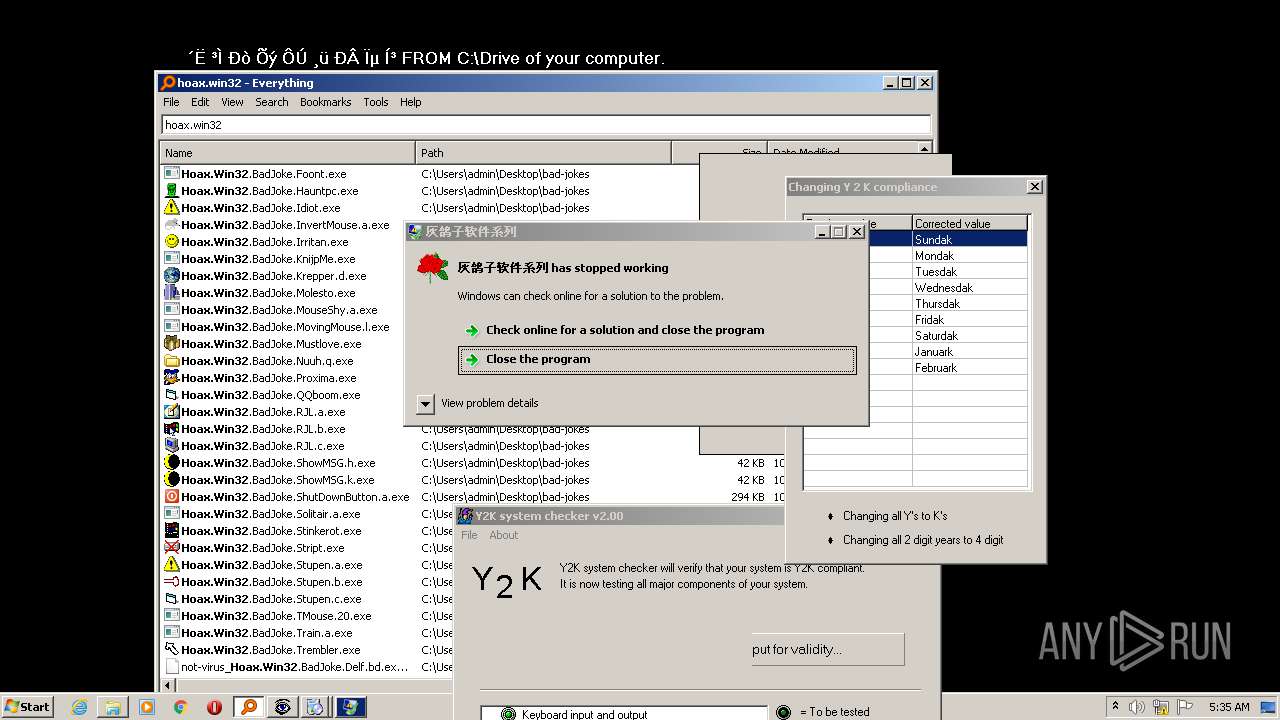
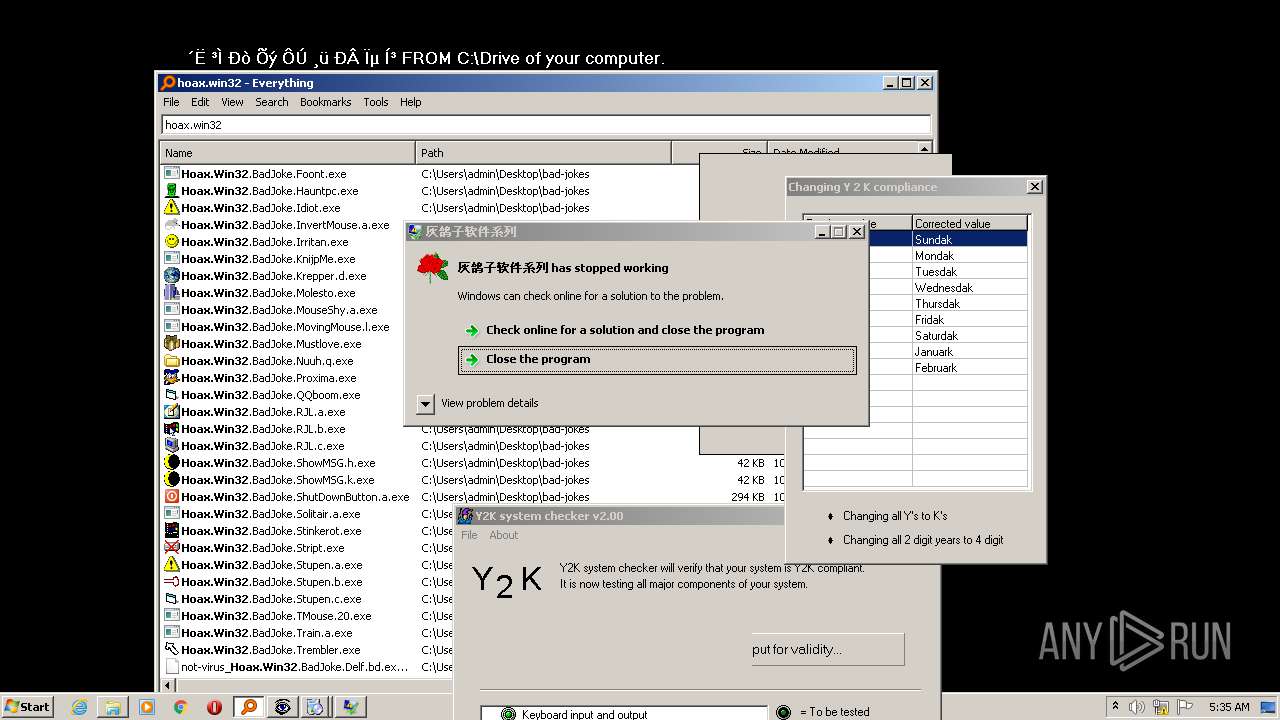
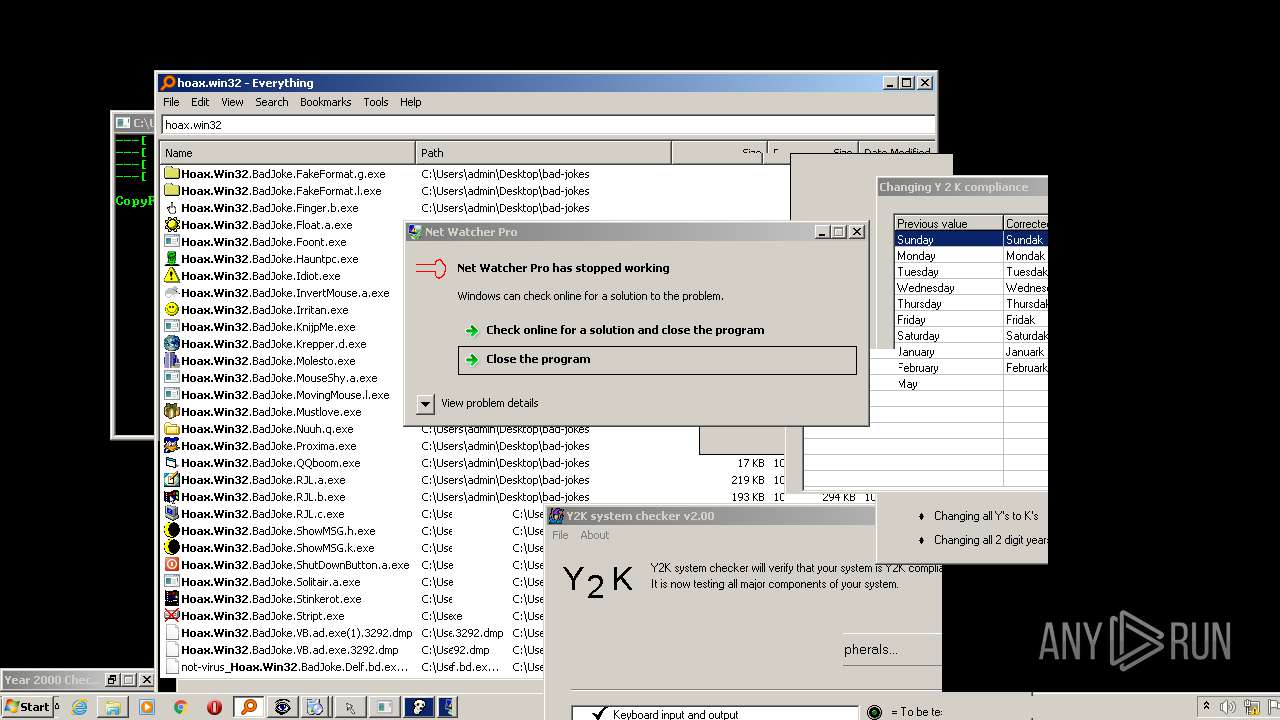
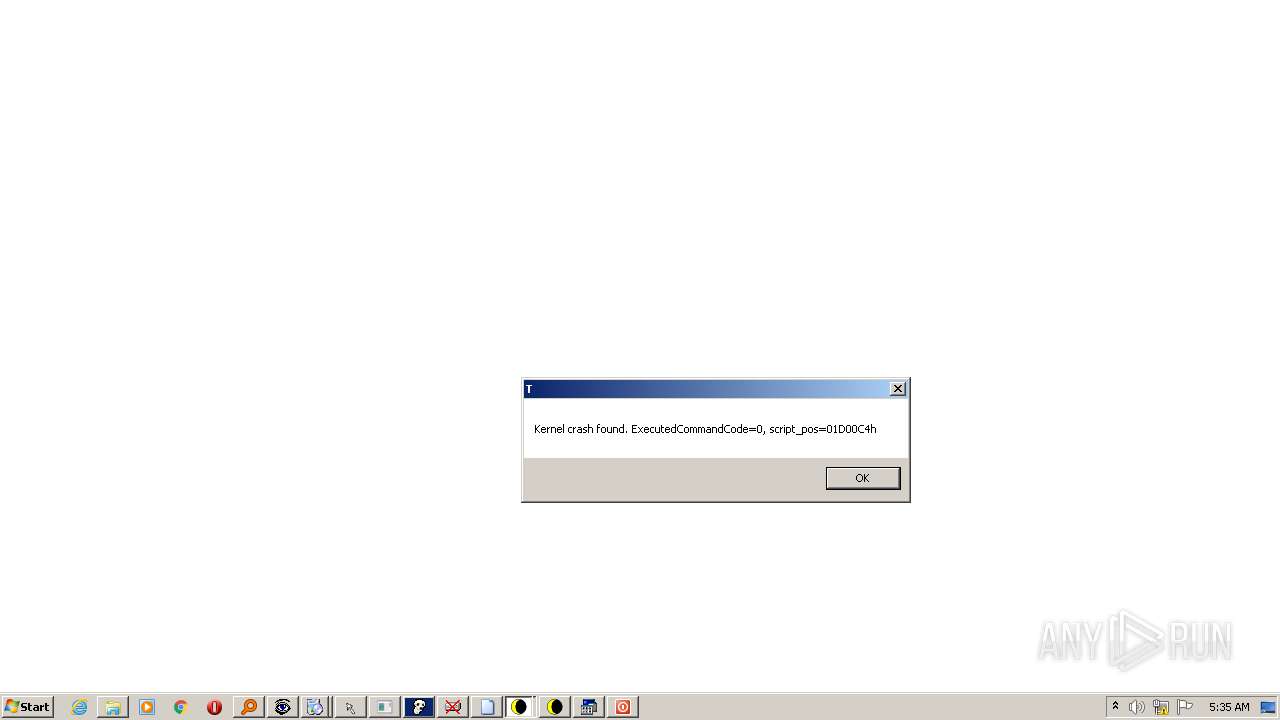
Executes application which crashes
- Everything.exe (PID: 724)
Reads Microsoft Outlook installation path
- Hoax.Win32.BadJoke.ShutDownButton.a.exe (PID: 1064)
Reads internet explorer settings
- Hoax.Win32.BadJoke.ShutDownButton.a.exe (PID: 1064)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 1116)
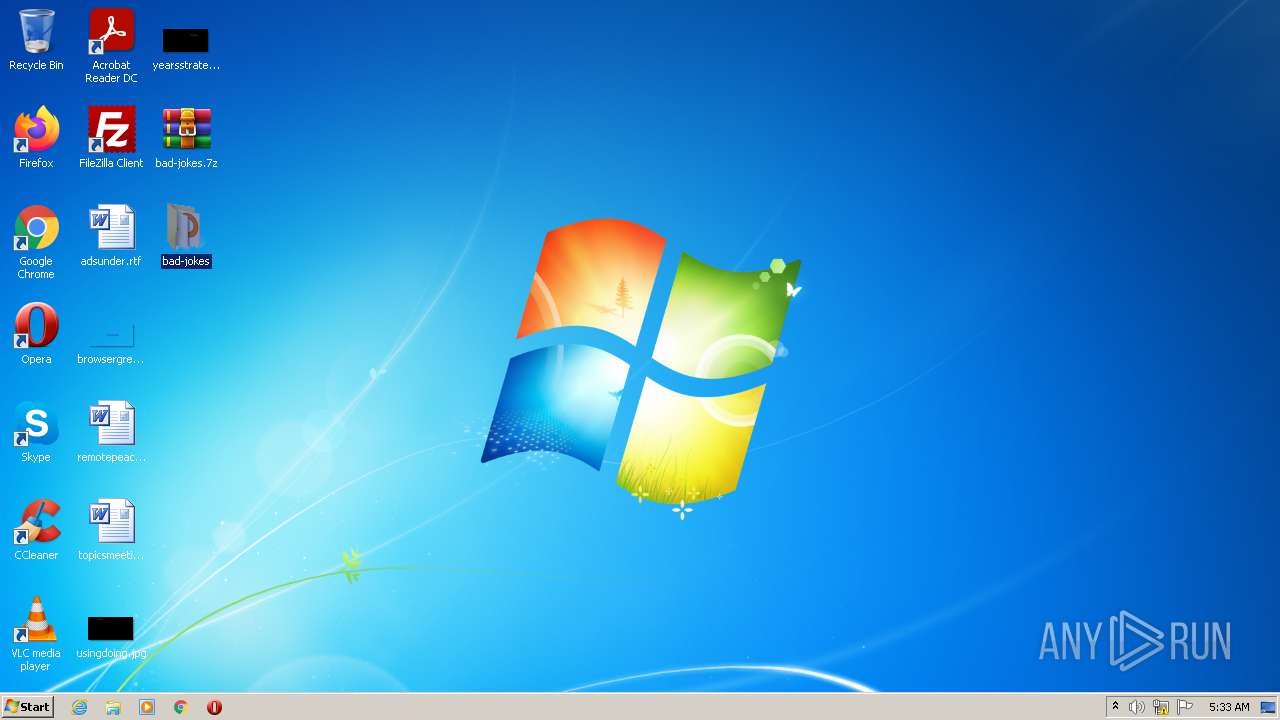
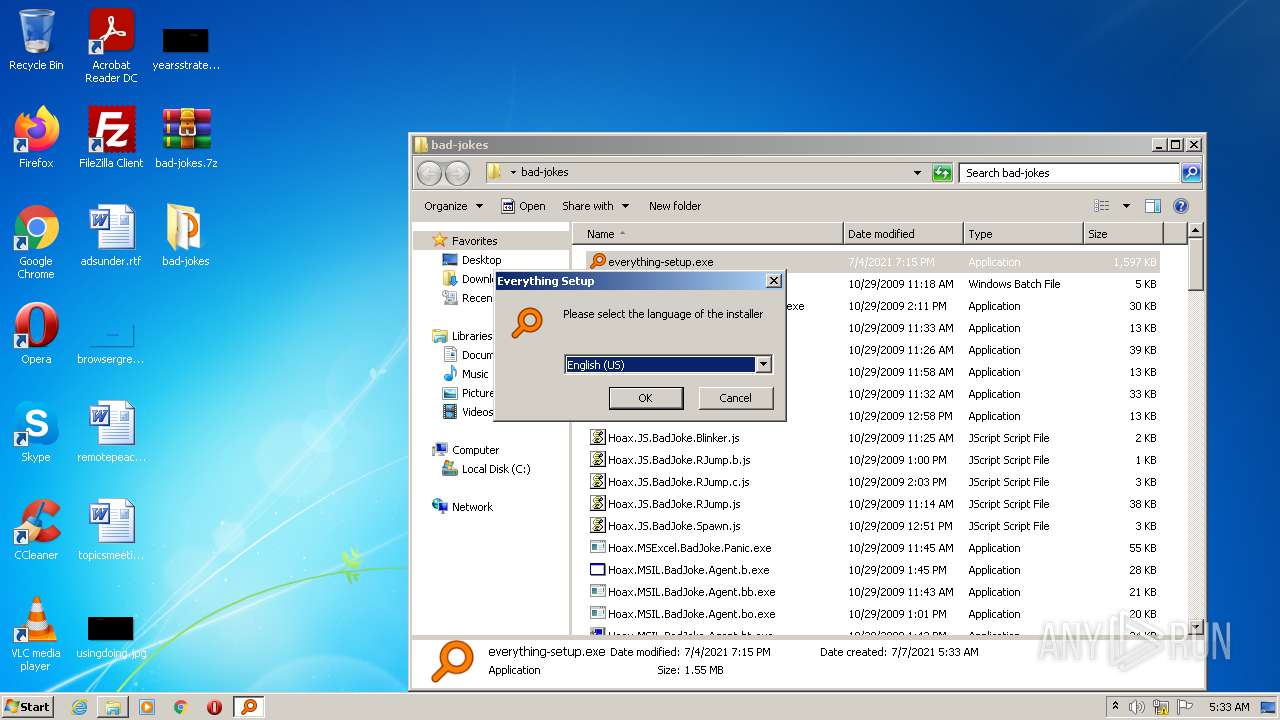
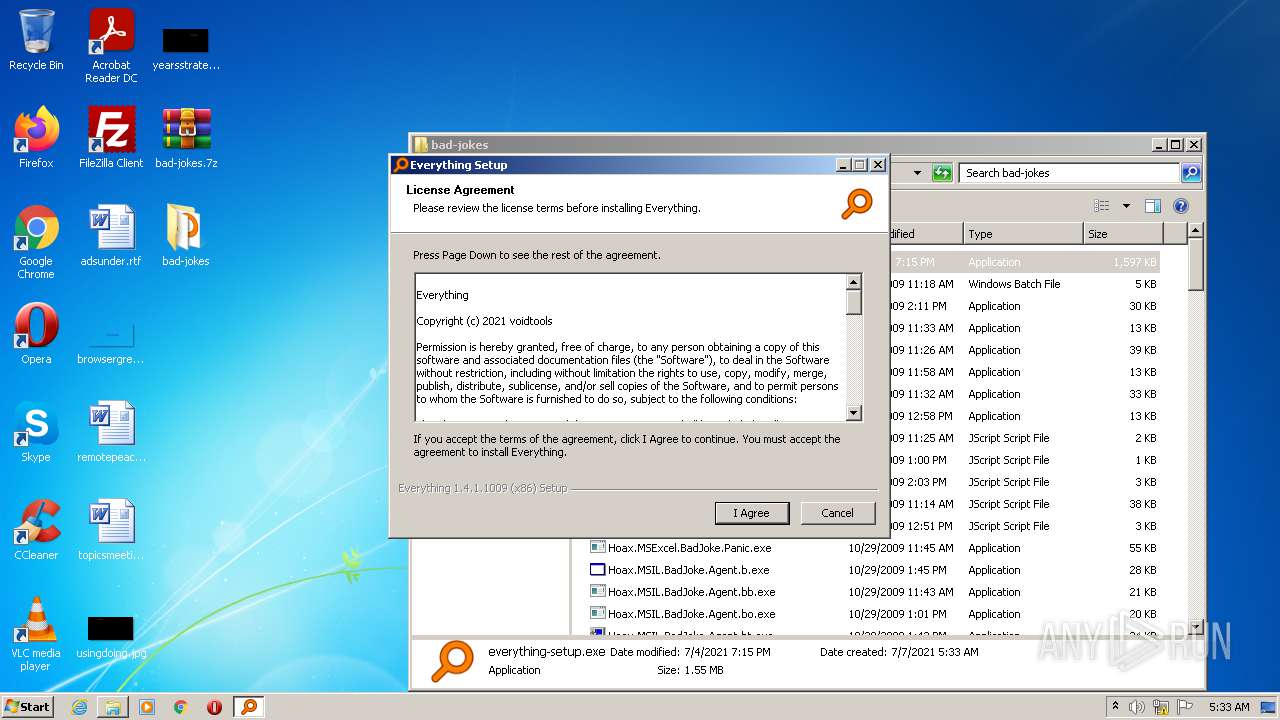
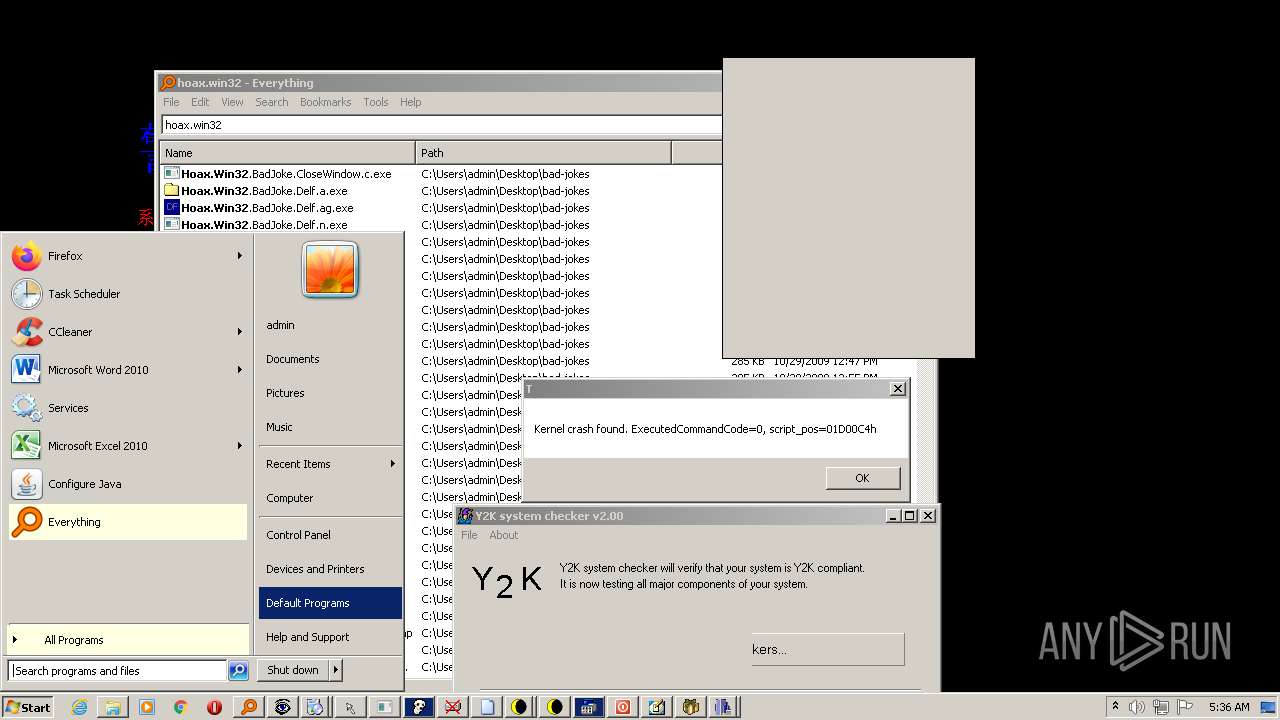
Manual execution by user
- everything-setup.exe (PID: 3424)
- Everything.exe (PID: 3236)
- control.exe (PID: 756)
Reads Microsoft Office registry keys
- Hoax.Win32.BadJoke.VB.ak.exe (PID: 3520)
Checks supported languages
- rundll32.exe (PID: 3928)
- rundll32.exe (PID: 1880)
- ntvdm.exe (PID: 1708)
- ntvdm.exe (PID: 3036)
- rundll32.exe (PID: 3888)
- rundll32.exe (PID: 3040)
- control.exe (PID: 756)
Reads the computer name
- control.exe (PID: 756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
117
Monitored processes
66
Malicious processes
51
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
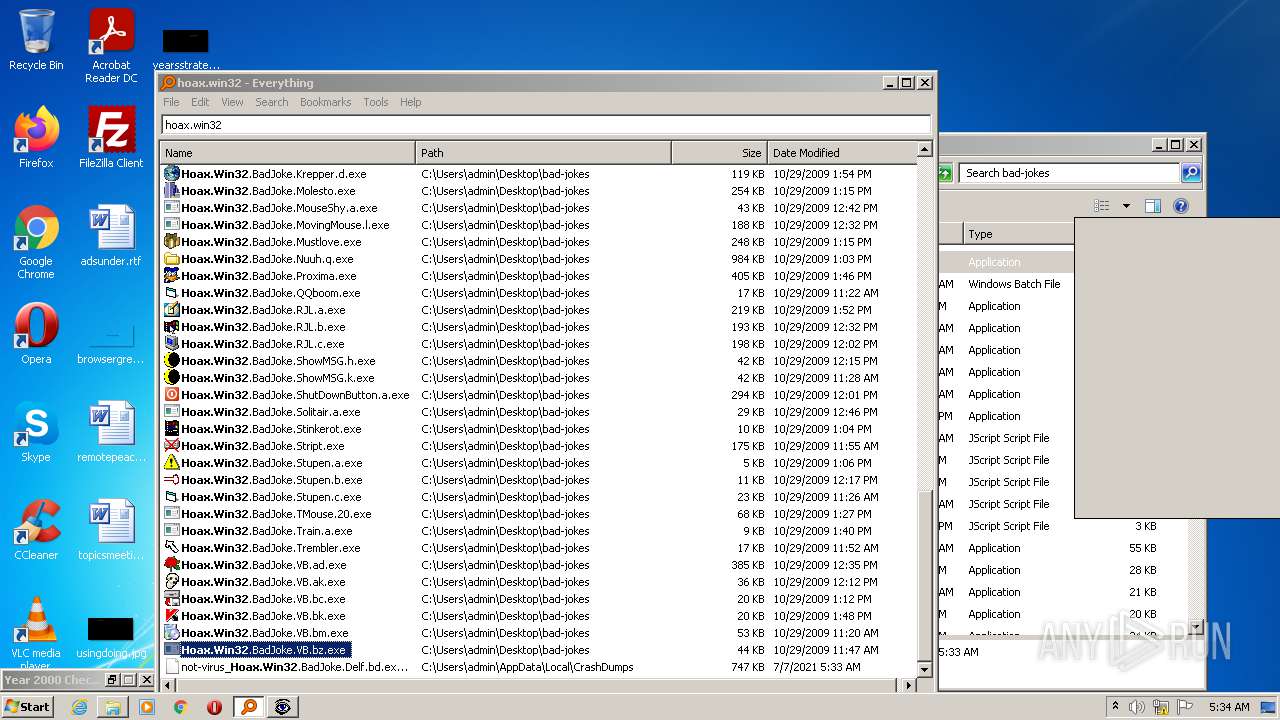
| 312 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Y2KChecker.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Y2KChecker.exe | — | Everything.exe | |||||||||||
User: admin Company: R.J.L. Software Integrity Level: MEDIUM Description: Y 2 K Joke - www.rjlsoftware.com Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 468 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.VB.bc.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.VB.bc.exe | — | Everything.exe | |||||||||||
User: admin Company: Microsoft Cooperation Integrity Level: MEDIUM Description: Microsoft Rom File Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
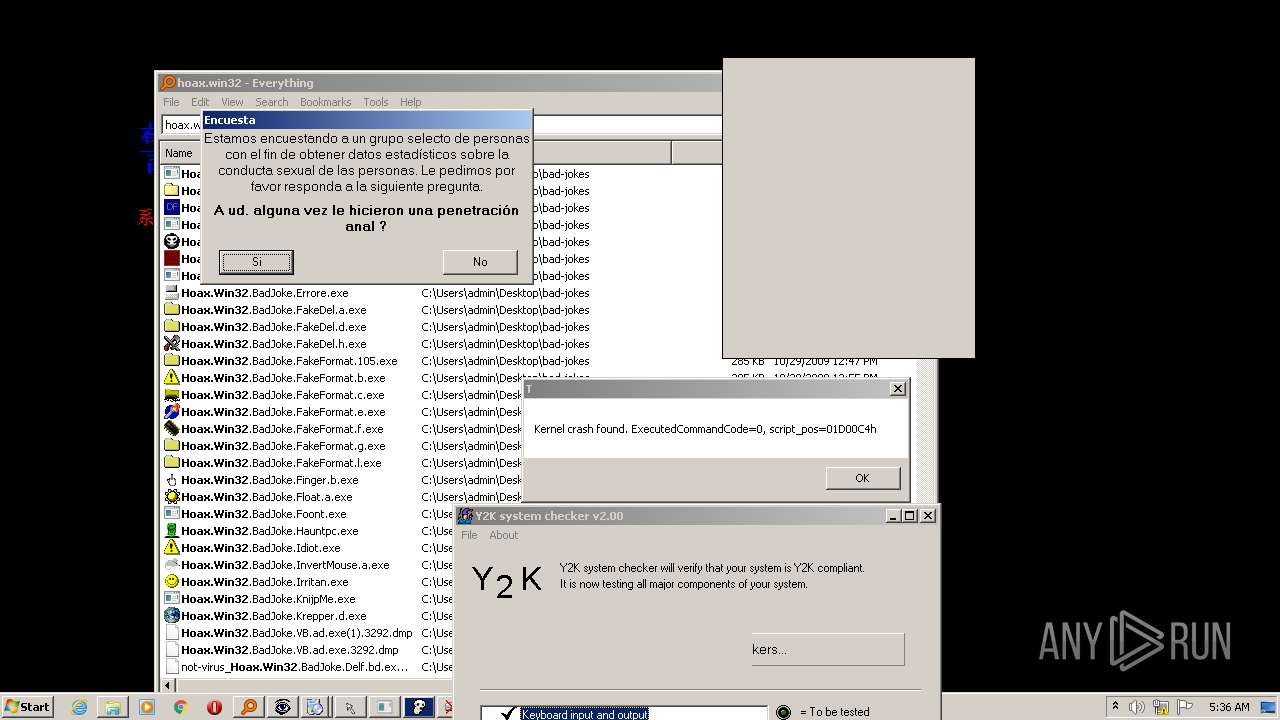
| 528 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Molesto.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Molesto.exe | — | Everything.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 536 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Proxima.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Proxima.exe | — | Everything.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3489660927 Modules
| |||||||||||||||
| 572 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Mustlove.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Mustlove.exe | — | Everything.exe | |||||||||||
User: admin Company: RICKY??? Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Everything\Everything.exe" | C:\Program Files\Everything\Everything.exe | — | everything-setup.exe | |||||||||||
User: admin Company: voidtools Integrity Level: MEDIUM Description: Everything Exit code: 0 Version: 1.4.1.1009 Modules
| |||||||||||||||
| 756 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.VB.n.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.VB.n.exe | — | Everything.exe | |||||||||||
User: admin Company: Taiwan Integrity Level: MEDIUM Exit code: 3221225781 Version: 1.00 Modules
| |||||||||||||||
| 756 | "C:\Windows\system32\control.exe" /name Microsoft.DefaultPrograms | C:\Windows\system32\control.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Nuuh.q.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.Nuuh.q.exe | Everything.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.ShutDownButton.a.exe" | C:\Users\admin\Desktop\bad-jokes\Hoax.Win32.BadJoke.ShutDownButton.a.exe | Everything.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
9 434
Read events
9 315
Write events
118
Delete events
1
Modification events
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\bad-jokes.7z | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
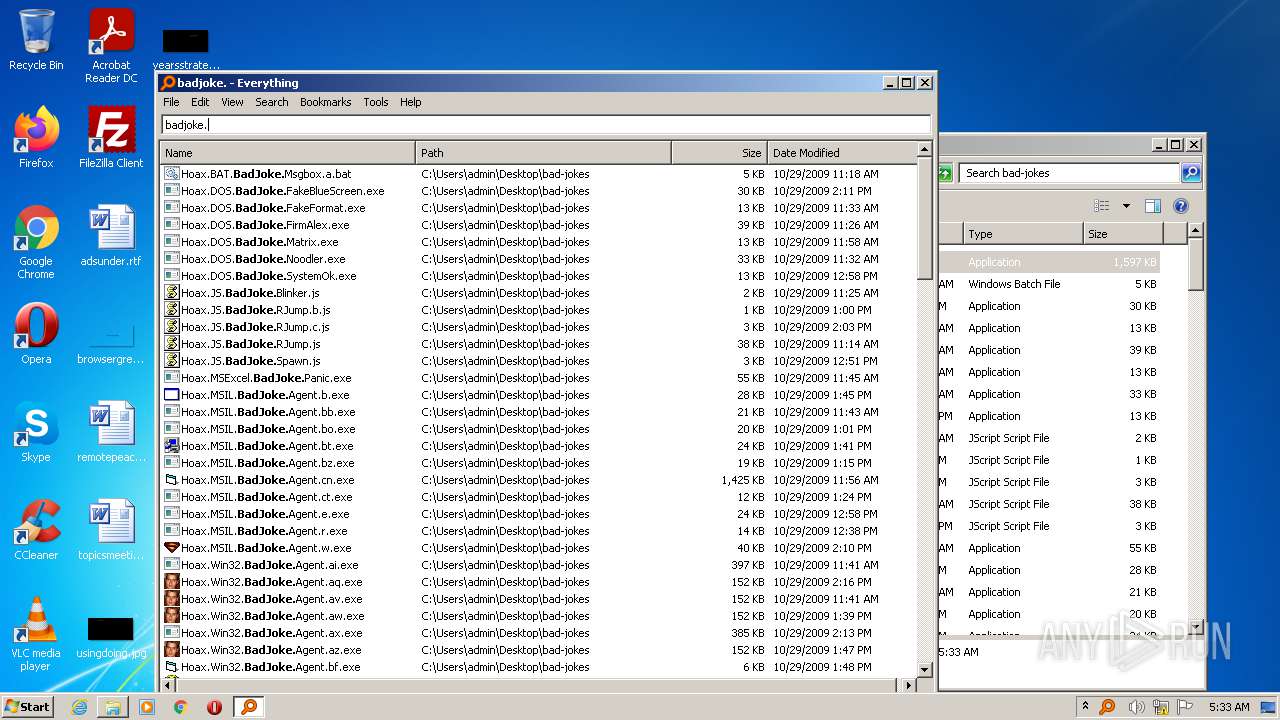
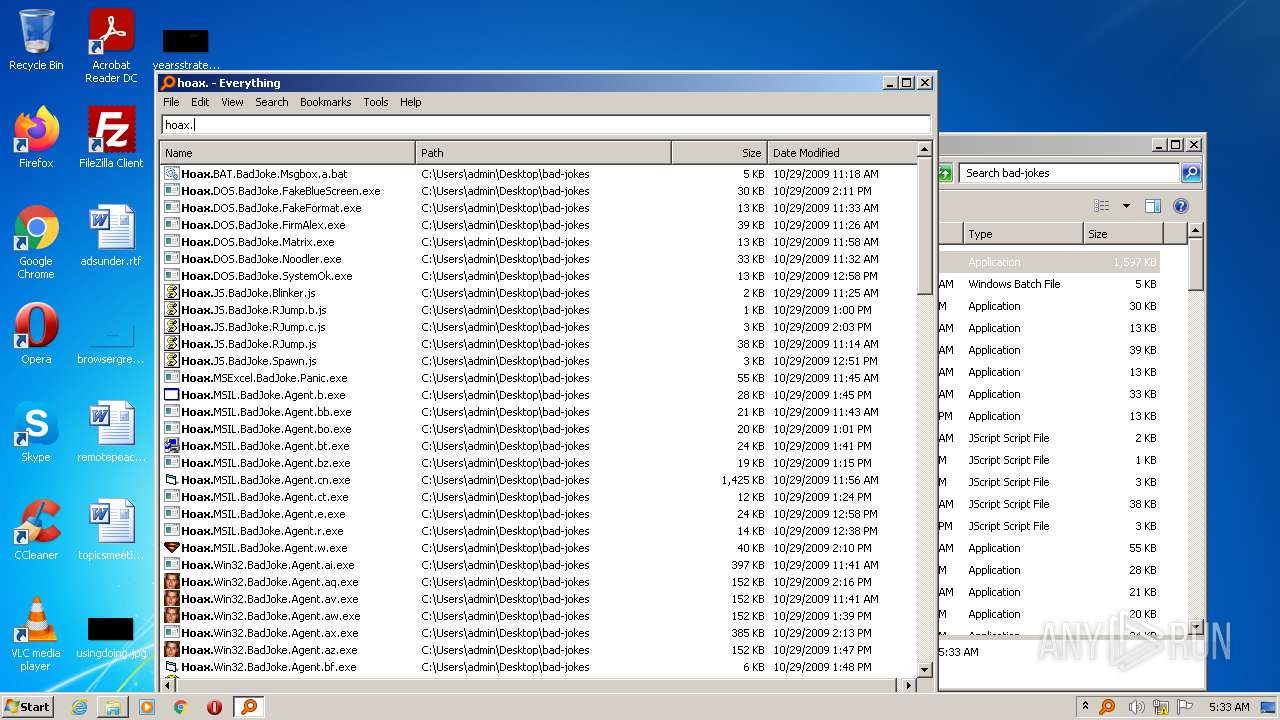
Executable files
126
Suspicious files
8
Text files
26
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.JS.BadJoke.RJump.js | html | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.JS.BadJoke.Spawn.js | html | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.BAT.BadJoke.Msgbox.a.bat | text | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.JS.BadJoke.Blinker.js | html | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.MSIL.BadJoke.Agent.bt.exe | executable | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.MSIL.BadJoke.Agent.bb.exe | executable | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.DOS.BadJoke.SystemOk.exe | binary | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.MSIL.BadJoke.Agent.b.exe | executable | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.MSIL.BadJoke.Agent.bo.exe | executable | |
MD5:— | SHA256:— | |||
| 1116 | WinRAR.exe | C:\Users\admin\Desktop\bad-jokes\Hoax.MSIL.BadJoke.Agent.bz.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
30
DNS requests
4
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | WerFault.exe | 104.43.193.48:443 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
924 | Hoax.Win32.BadJoke.Nuuh.q.exe | 183.236.2.18:52113 | qqw77.3322.org | Guangdong Mobile Communication Co.Ltd. | CN | malicious |
— | — | 183.236.2.18:52113 | qqw77.3322.org | Guangdong Mobile Communication Co.Ltd. | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
qqw77.3322.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to 3322.org Domain |
924 | Hoax.Win32.BadJoke.Nuuh.q.exe | Generic Protocol Command Decode | SURICATA STREAM suspected RST injection |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to 3322.org Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to 3322.org Domain |