| File name: | 02478570_4 |
| Full analysis: | https://app.any.run/tasks/18711756-5bc9-4ad2-a0e1-c82d871f0b87 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2021, 00:05:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 0196A16234AC25574A7A7E7D7A7D9685 |
| SHA1: | 6C5F952EC75D9516CB28CED9878AE24421028346 |
| SHA256: | D0A4A0C4EB473C7A6233135B31383E2D1C70B66211460F43C39FFB434A8191C2 |
| SSDEEP: | 196608:5wium9ZeEzqZWIc/ANC9TFfPF9sti7A95hVxms+IT030HyKdYxB/cqfp:ml9EqWPINC92E7Abws+IT0IdYxB/cqfp |
MALICIOUS
Loads dropped or rewritten executable
- 02478570_4.exe (PID: 2304)
- CagService.exe (PID: 2272)
- Gui.exe (PID: 2884)
- MsiExec.exe (PID: 2384)
- svchost.exe (PID: 764)
- Splashtop_Software_Updater.exe (PID: 3388)
- SRManager.exe (PID: 3200)
Changes the autorun value in the registry
- 02478570_4.exe (PID: 2304)
Drops executable file immediately after starts
- 02478570_4.exe (PID: 2304)
- MsiExec.exe (PID: 2384)
- Splashtop_Software_Updater.exe (PID: 3388)
Application was dropped or rewritten from another process
- CagService.exe (PID: 2272)
- Gui.exe (PID: 2884)
- winvnc.exe (PID: 3788)
- AEMAgent.exe (PID: 2448)
- AEMAgent.exe (PID: 1356)
- PreVerCheck.exe (PID: 2840)
- Splashtop_Streamer.exe (PID: 1804)
- SetupUtil.exe (PID: 2040)
- SetupUtil.exe (PID: 3984)
- SetupUtil.exe (PID: 1404)
- SRSelfSignCertUtil.exe (PID: 3136)
- SSU_Clean.exe (PID: 3224)
- Splashtop_Software_Updater.exe (PID: 3388)
- SRService.exe (PID: 1120)
- SSUService.exe (PID: 4044)
- SRService.exe (PID: 1244)
- SRManager.exe (PID: 3200)
- SRService.exe (PID: 3104)
Registers / Runs the DLL via REGSVR32.EXE
- CagService.exe (PID: 2272)
SUSPICIOUS
Reads the computer name
- 02478570_4.exe (PID: 2304)
- CagService.exe (PID: 2272)
- winvnc.exe (PID: 3788)
- Gui.exe (PID: 2884)
- AEMAgent.exe (PID: 1356)
- AEMAgent.exe (PID: 2448)
- Splashtop_Streamer.exe (PID: 1804)
- SetupUtil.exe (PID: 2040)
- SetupUtil.exe (PID: 3984)
- SetupUtil.exe (PID: 1404)
- SRSelfSignCertUtil.exe (PID: 3136)
- SSU_Clean.exe (PID: 3224)
- Splashtop_Software_Updater.exe (PID: 3388)
- SSUService.exe (PID: 4044)
- SRService.exe (PID: 1120)
- SRService.exe (PID: 1244)
- SRService.exe (PID: 3104)
- SRManager.exe (PID: 3200)
Checks supported languages
- 02478570_4.exe (PID: 2304)
- CagService.exe (PID: 2272)
- nsD0A2.tmp (PID: 2892)
- nsD1FB.tmp (PID: 2300)
- winvnc.exe (PID: 3788)
- Gui.exe (PID: 2884)
- AEMAgent.exe (PID: 2448)
- AEMAgent.exe (PID: 1356)
- Splashtop_Streamer.exe (PID: 1804)
- PreVerCheck.exe (PID: 2840)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 3660)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 3608)
- cmd.exe (PID: 696)
- cmd.exe (PID: 2972)
- SetupUtil.exe (PID: 2040)
- SetupUtil.exe (PID: 3984)
- SetupUtil.exe (PID: 1404)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 2476)
- SSU_Clean.exe (PID: 3224)
- Splashtop_Software_Updater.exe (PID: 3388)
- SRSelfSignCertUtil.exe (PID: 3136)
- SSUService.exe (PID: 4044)
- SRService.exe (PID: 1120)
- SRService.exe (PID: 3104)
- SRService.exe (PID: 1244)
- SRManager.exe (PID: 3200)
Creates a directory in Program Files
- 02478570_4.exe (PID: 2304)
- msiexec.exe (PID: 3528)
- Splashtop_Software_Updater.exe (PID: 3388)
- SRService.exe (PID: 1120)
Reads Environment values
- 02478570_4.exe (PID: 2304)
- CagService.exe (PID: 2272)
Drops a file with too old compile date
- 02478570_4.exe (PID: 2304)
- CagService.exe (PID: 2272)
- MsiExec.exe (PID: 2384)
- msiexec.exe (PID: 3528)
- Splashtop_Software_Updater.exe (PID: 3388)
Drops a file that was compiled in debug mode
- 02478570_4.exe (PID: 2304)
- Splashtop_Streamer.exe (PID: 1804)
- CagService.exe (PID: 2272)
- MsiExec.exe (PID: 2384)
- msiexec.exe (PID: 3528)
- Splashtop_Software_Updater.exe (PID: 3388)
Executable content was dropped or overwritten
- 02478570_4.exe (PID: 2304)
- Splashtop_Streamer.exe (PID: 1804)
- CagService.exe (PID: 2272)
- MsiExec.exe (PID: 2384)
- msiexec.exe (PID: 3528)
- SetupUtil.exe (PID: 1404)
- Splashtop_Software_Updater.exe (PID: 3388)
Executed as Windows Service
- CagService.exe (PID: 2272)
- winvnc.exe (PID: 3788)
- msiexec.exe (PID: 3528)
- SSUService.exe (PID: 4044)
- SRService.exe (PID: 1244)
Creates a software uninstall entry
- 02478570_4.exe (PID: 2304)
- CagService.exe (PID: 2272)
- msiexec.exe (PID: 3528)
- Splashtop_Software_Updater.exe (PID: 3388)
Starts application with an unusual extension
- 02478570_4.exe (PID: 2304)
Uses TASKKILL.EXE to kill process
- nsD0A2.tmp (PID: 2892)
- nsD1FB.tmp (PID: 2300)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 3660)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 3608)
- cmd.exe (PID: 696)
- cmd.exe (PID: 2972)
Creates files in the program directory
- 02478570_4.exe (PID: 2304)
- CagService.exe (PID: 2272)
- MsiExec.exe (PID: 2384)
- SetupUtil.exe (PID: 1404)
- SRSelfSignCertUtil.exe (PID: 3136)
- msiexec.exe (PID: 3528)
- Splashtop_Software_Updater.exe (PID: 3388)
- SRService.exe (PID: 1120)
- SRManager.exe (PID: 3200)
Changes default file association
- CagService.exe (PID: 2272)
- MsiExec.exe (PID: 2384)
Removes files from Windows directory
- CagService.exe (PID: 2272)
- MsiExec.exe (PID: 2384)
- SetupUtil.exe (PID: 3984)
- SSU_Clean.exe (PID: 3224)
- Splashtop_Software_Updater.exe (PID: 3388)
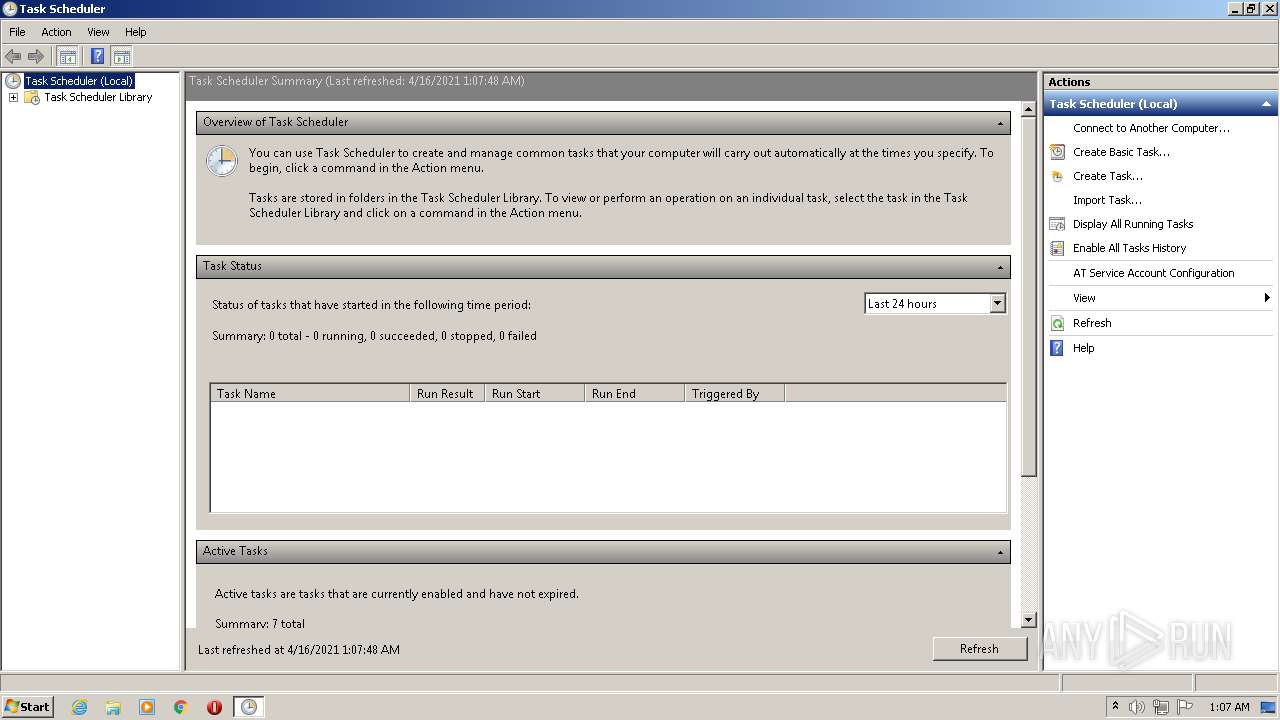
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3116)
- reg.exe (PID: 3864)
- SRService.exe (PID: 1120)
Creates or modifies windows services
- CagService.exe (PID: 2272)
- Splashtop_Software_Updater.exe (PID: 3388)
- SRManager.exe (PID: 3200)
Creates files in the Windows directory
- Splashtop_Streamer.exe (PID: 1804)
- msiexec.exe (PID: 1984)
- PreVerCheck.exe (PID: 2840)
- CagService.exe (PID: 2272)
- MsiExec.exe (PID: 2384)
- msiexec.exe (PID: 3528)
- SetupUtil.exe (PID: 2040)
- SetupUtil.exe (PID: 3984)
- svchost.exe (PID: 764)
- SSU_Clean.exe (PID: 3224)
- Splashtop_Software_Updater.exe (PID: 3388)
- SSUService.exe (PID: 4044)
- SRManager.exe (PID: 3200)
Reads the Windows organization settings
- msiexec.exe (PID: 3528)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3528)
Application launched itself
- msiexec.exe (PID: 3528)
Reads the time zone
- svchost.exe (PID: 764)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 2384)
- SetupUtil.exe (PID: 1404)
Searches for installed software
- CagService.exe (PID: 2272)
Uses REG.EXE to modify Windows registry
- MsiExec.exe (PID: 2384)
INFO
Reads the computer name
- taskkill.exe (PID: 2508)
- taskkill.exe (PID: 3288)
- msiexec.exe (PID: 3528)
- MsiExec.exe (PID: 2384)
- msiexec.exe (PID: 1984)
- taskkill.exe (PID: 4012)
- taskkill.exe (PID: 2296)
- taskkill.exe (PID: 3780)
- taskkill.exe (PID: 3964)
- taskkill.exe (PID: 904)
- taskkill.exe (PID: 3232)
- taskkill.exe (PID: 336)
- wevtutil.exe (PID: 2640)
- wevtutil.exe (PID: 3844)
Checks supported languages
- taskkill.exe (PID: 3288)
- taskkill.exe (PID: 2508)
- regsvr32.exe (PID: 3116)
- msiexec.exe (PID: 1984)
- msiexec.exe (PID: 3528)
- MsiExec.exe (PID: 2384)
- taskkill.exe (PID: 4012)
- taskkill.exe (PID: 3780)
- taskkill.exe (PID: 2296)
- taskkill.exe (PID: 3964)
- taskkill.exe (PID: 904)
- taskkill.exe (PID: 3232)
- taskkill.exe (PID: 336)
- regedit.exe (PID: 2292)
- regedit.exe (PID: 324)
- reg.exe (PID: 3864)
- wevtutil.exe (PID: 3844)
- wevtutil.exe (PID: 2640)
Reads settings of System Certificates
- Gui.exe (PID: 2884)
- CagService.exe (PID: 2272)
- SRManager.exe (PID: 3200)
Checks Windows Trust Settings
- Gui.exe (PID: 2884)
- SRManager.exe (PID: 3200)
Reads CPU info
- svchost.exe (PID: 764)
Manual execution by user
- mmc.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x4167 |
| UninitializedDataSize: | 154112 |
| InitializedDataSize: | 38912 |
| CodeSize: | 35328 |
| LinkerVersion: | 2.26 |
| PEType: | PE32 |
| TimeStamp: | 2016:04:27 03:27:51+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2016 01:27:51 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 27-Apr-2016 01:27:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008970 | 0x00008A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.02723 |
.data | 0x0000A000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.63061 |
.rdata | 0x0000B000 | 0x00006B04 | 0x00006C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.23063 |
.bss | 0x00012000 | 0x00025A00 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00038000 | 0x0000127C | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.18033 |
.ndata | 0x0003A000 | 0x0000C000 | 0x00000400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00046000 | 0x00008220 | 0x00008400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.41456 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19461 | 729 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.84101 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.52982 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.23377 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.62308 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
107
Monitored processes
52
Malicious processes
16
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | regedit.exe /s "C:\Windows\TEMP\{B7C5EA94-B96A-41F5-BE95-25D78B486678}\InstRegExp.reg" | C:\Windows\regedit.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 336 | taskkill.exe /F /IM SRChat.exe /T | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | C:\Windows\System32\cmd.exe /C "taskkill.exe /F /IM SRAgent.exe /T" | C:\Windows\System32\cmd.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 764 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | "C:\Users\admin\AppData\Local\Temp\02478570_4.exe" | C:\Users\admin\AppData\Local\Temp\02478570_4.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 904 | taskkill.exe /F /IM SRManager.exe /T | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 1120 | "C:\Program Files\Splashtop\Splashtop Remote\Server\SRService.exe" -i | C:\Program Files\Splashtop\Splashtop Remote\Server\SRService.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Splashtop Inc. Integrity Level: SYSTEM Description: Splashtop� Streamer Service Exit code: 1066 Version: 3.42.9.6740 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Splashtop\Splashtop Remote\Server\SRService.exe" | C:\Program Files\Splashtop\Splashtop Remote\Server\SRService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Splashtop Inc. Integrity Level: SYSTEM Description: Splashtop� Streamer Service Exit code: 0 Version: 3.42.9.6740 Modules
| |||||||||||||||
| 1356 | "C:\ProgramData\CentraStage\AEMAgent\AEMAgent.exe" | C:\ProgramData\CentraStage\AEMAgent\AEMAgent.exe | CagService.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: AEMAgent Exit code: 2147516547 Version: 9.3.0.2 Modules
| |||||||||||||||
Total events
27 784
Read events
26 808
Write events
964
Delete events
12
Modification events
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CentraStage |
Value: C:\Program Files\CentraStage\Gui.exe | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\CagService |
| Operation: | write | Name: | (default) |
Value: Service | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\uvnc_service |
| Operation: | write | Name: | (default) |
Value: Service | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\CagService.exe |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\CentraStage\CagService.exe | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | DisplayName |
Value: CentraStage | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\CentraStage\uninst.exe | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\CentraStage\CSIcon.ico | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.centrastage.com | |||
| (PID) Process: | (2304) 02478570_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | Publisher |
Value: CentraStage Limited | |||
| (PID) Process: | (2272) CagService.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
352
Suspicious files
42
Text files
206
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\defaultbrand.zip | compressed | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\Core.dll | executable | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\CSIcon.ico | image | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\CagService.exe | executable | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\CagService.exe.config | xml | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\Common.dll | executable | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\Core.XmlSerializers.dll | executable | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\Gui.exe | executable | |
MD5:— | SHA256:— | |||
| 2304 | 02478570_4.exe | C:\Users\admin\AppData\Local\Temp\nstA53C.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 2304 | 02478570_4.exe | C:\Program Files\CentraStage\AxInterop.MSTSCLib.dll | executable | |
MD5:0F581E56ED5BA500CE5D98D105B04A37 | SHA256:F041747B5B6B20B6620CA13A7B276C9E9070E54CDA8C29F6ADD54CBA9A42A2F5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3200 | SRManager.exe | GET | 200 | 23.51.123.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
— | — | POST | — | 107.22.247.100:80 | http://ds1.devicevm.com/ | US | — | — | suspicious |
3200 | SRManager.exe | GET | 200 | 23.51.123.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEHhvSYT5N0gvTTb3x7RJTGs%3D | NL | der | 1.48 Kb | shared |
— | — | GET | 200 | 54.164.16.142:80 | http://sn.splashtop.com/file_system/apt_repository/dists/ProtoSSU01/released/binary-i386/Packages.gz | US | compressed | 830 b | unknown |
3200 | SRManager.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?897fda51faa1a9a0 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2272 | CagService.exe | 52.7.54.43:443 | concordcc.centrastage.net | Amazon.com, Inc. | US | unknown |
2272 | CagService.exe | 34.195.169.6:443 | concord-agent.centrastage.net | Amazon.com, Inc. | US | unknown |
2272 | CagService.exe | 13.32.25.88:443 | update-concord.centrastage.net | Amazon.com, Inc. | US | suspicious |
— | — | 8.248.141.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3200 | SRManager.exe | 23.51.123.27:80 | s2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
— | — | 54.164.16.142:80 | sn.splashtop.com | Amazon.com, Inc. | US | unknown |
— | — | 107.22.247.100:80 | ds1.devicevm.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
concordcc.centrastage.net |
| unknown |
concord-agent.centrastage.net |
| unknown |
update-concord.centrastage.net |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
s2.symcb.com |
| whitelisted |
sv.symcd.com |
| shared |
sn.splashtop.com |
| unknown |
ds1.devicevm.com |
| suspicious |
Threats
Process | Message |
|---|---|
AEMAgent.exe | A fatal error occurred. The required library hostfxr.dll could not be found.
If this is a self-contained application, that library should exist in [C:\ProgramData\CentraStage\AEMAgent\].
If this is a framework-dependent application, install the runtime in the global location [C:\Program Files\dotnet] or use the DOTNET_ROOT environment variable to specify the runtime location or register the runtime location in [HKLM\SOFTWARE\dotnet\Setup\InstalledVersions\x86\InstallLocation]. |
AEMAgent.exe | The .NET Core runtime can be found at: |
AEMAgent.exe | - https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x86&rid=win7-x86 |
AEMAgent.exe | A fatal error occurred. The required library hostfxr.dll could not be found.
If this is a self-contained application, that library should exist in [C:\ProgramData\CentraStage\AEMAgent\].
If this is a framework-dependent application, install the runtime in the global location [C:\Program Files\dotnet] or use the DOTNET_ROOT environment variable to specify the runtime location or register the runtime location in [HKLM\SOFTWARE\dotnet\Setup\InstalledVersions\x86\InstallLocation]. |
AEMAgent.exe | The .NET Core runtime can be found at: |
AEMAgent.exe | - https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x86&rid=win7-x86 |
Splashtop_Streamer.exe | [1804]2021-04-16 01:07:30 [CUtility::OSInfo] OS 6.1(7601) Service Pack 1 x64:0 (Last=0) |
Splashtop_Streamer.exe | [1804]2021-04-16 01:07:30 [CUnPack::FindHeader] Name:C:\ProgramData\CentraStage\Splashtop\Splashtop_Streamer.exe (Last=0) |
Splashtop_Streamer.exe | [1804]2021-04-16 01:07:30 [CUnPack::FindHeader] Sign Size:6096 (Last=0) |
Splashtop_Streamer.exe | [1804]2021-04-16 01:07:30 [CUnPack::FindHeader] Header offset:426496 (Last=183) |