| File name: | met.exe |
| Full analysis: | https://app.any.run/tasks/80a51d9d-8147-41f9-89af-9ef82849aacc |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 20:33:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | BD8DF2CB8307DEC1C29D041A1AA230D2 |
| SHA1: | F5044E00DA2D9BEA4FDEAE547BBE09F3205E32BC |
| SHA256: | D09AEB791EB04391B379F44E5D2FC6DE7471951D523AECE5D93E1030A222E675 |
| SSDEEP: | 768:Dz1kbkNtE3gO1ll0S3jNe/6WimzNqhlMsnD6hzVp9ckaDKfJwOPSFow:Dz18mEwO1bP3hezDzNZsnYzxZ2KfT0 |
MALICIOUS
Writes to a start menu file
- Jhon.exe (PID: 1444)
SUSPICIOUS
Connects to unusual port
- met.exe (PID: 1660)
- Jhon.exe (PID: 1444)
Executable content was dropped or overwritten
- met.exe (PID: 1660)
Creates files in the user directory
- Jhon.exe (PID: 1444)
Starts itself from another location
- met.exe (PID: 1660)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:19 16:37:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 46592 |
| InitializedDataSize: | 13312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd43e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | met |
| FileVersion: | 1.0.0.0 |
| InternalName: | met.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFileName: | met.exe |
| ProductName: | met |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Mar-2019 15:37:01 |
| Debug artifacts: |
|
| FileDescription: | met |
| FileVersion: | 1.0.0.0 |
| InternalName: | met.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFilename: | met.exe |
| ProductName: | met |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 19-Mar-2019 15:37:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000B444 | 0x0000B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48033 |
.sdata | 0x0000E000 | 0x00000138 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.87565 |
.rsrc | 0x00010000 | 0x00002E20 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.27689 |
.reloc | 0x00014000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.0843 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 1.04772 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.76148 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 1.71396 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 1.72071 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.72257 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.71964 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
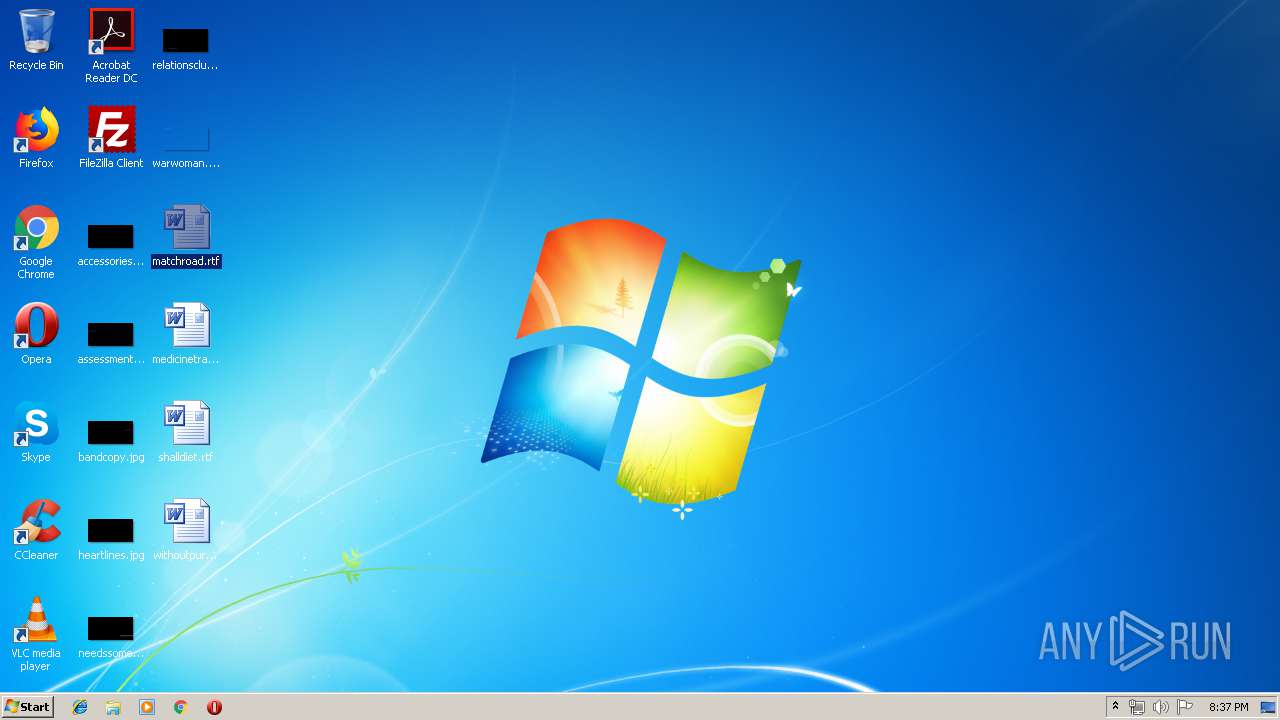
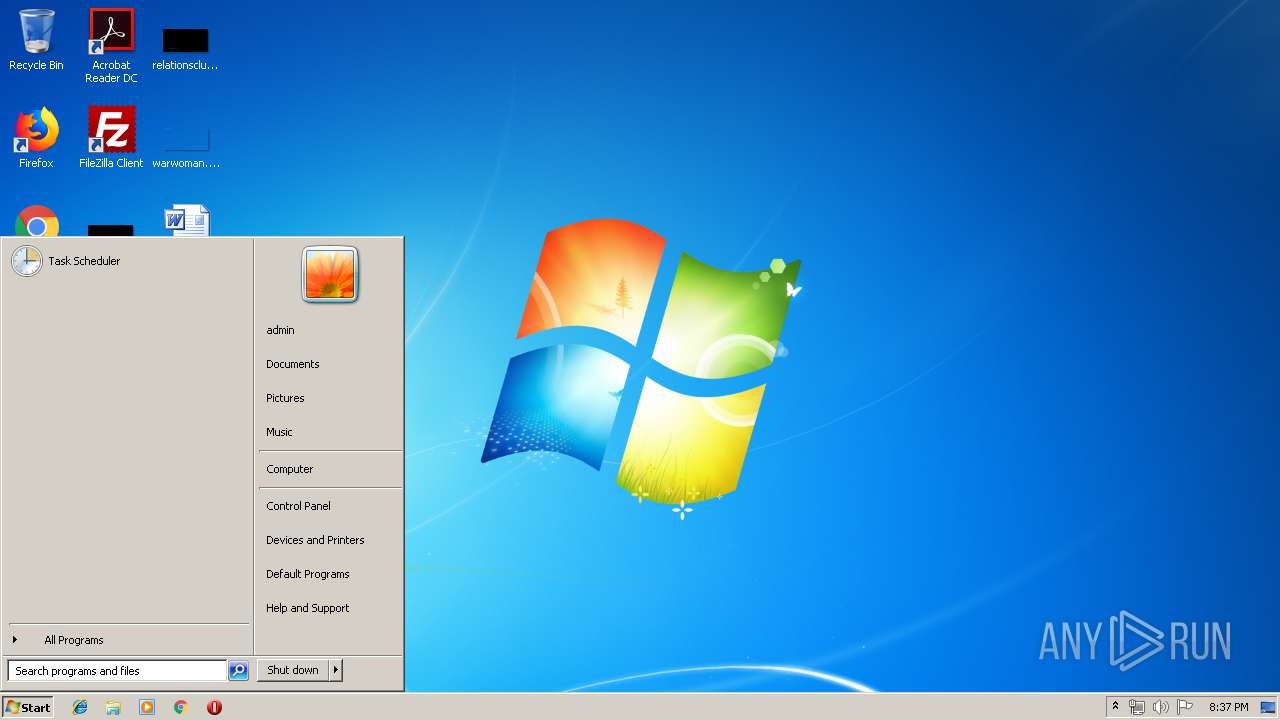
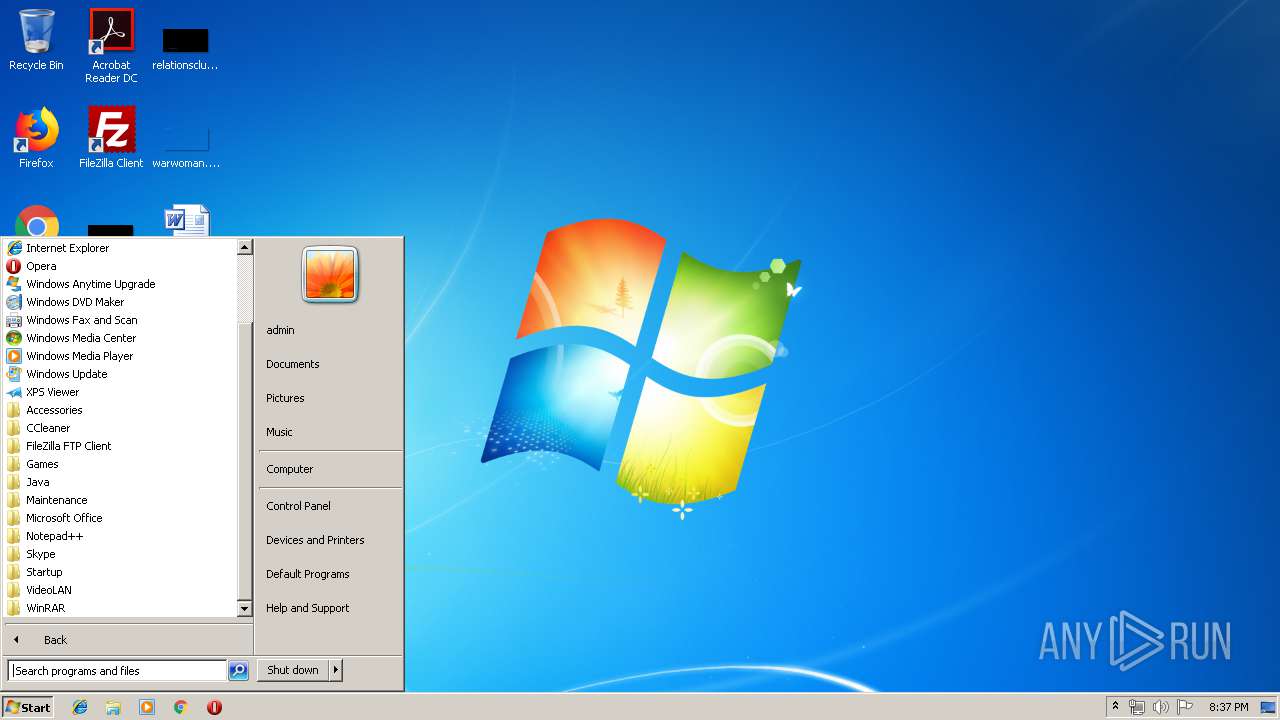
Total processes
31
Monitored processes
3
Malicious processes
0
Suspicious processes
2
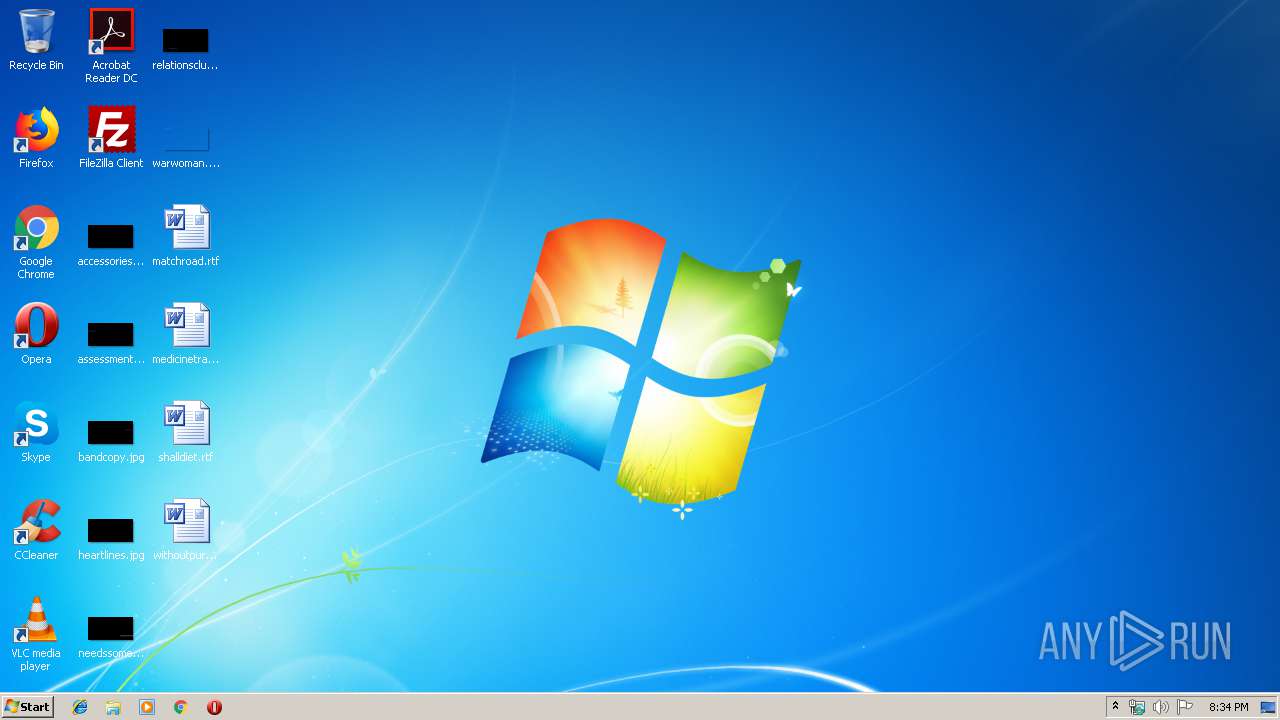
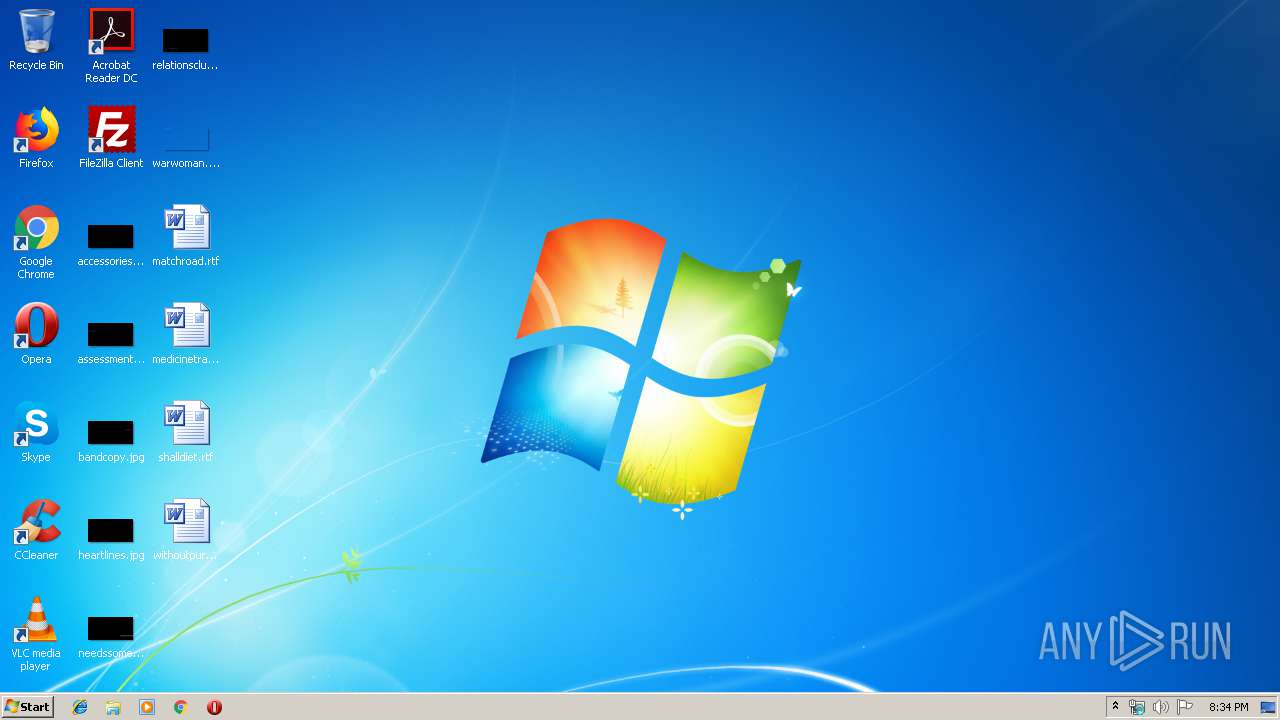
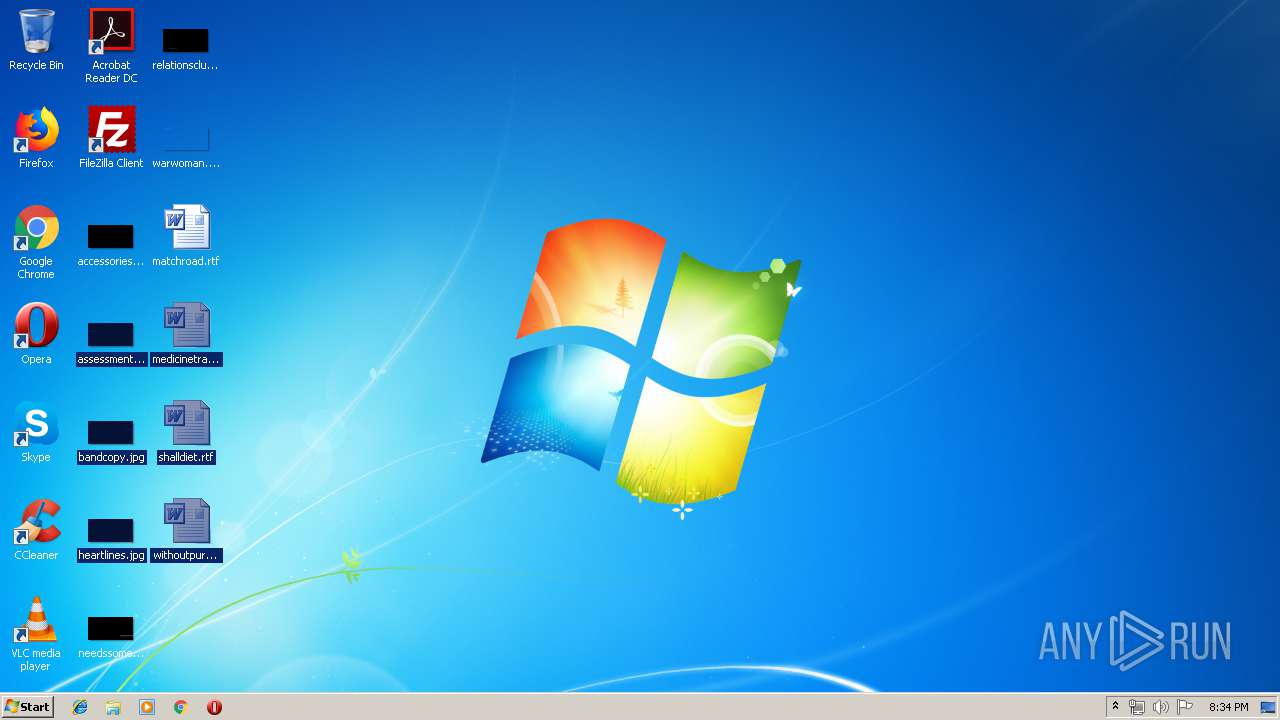
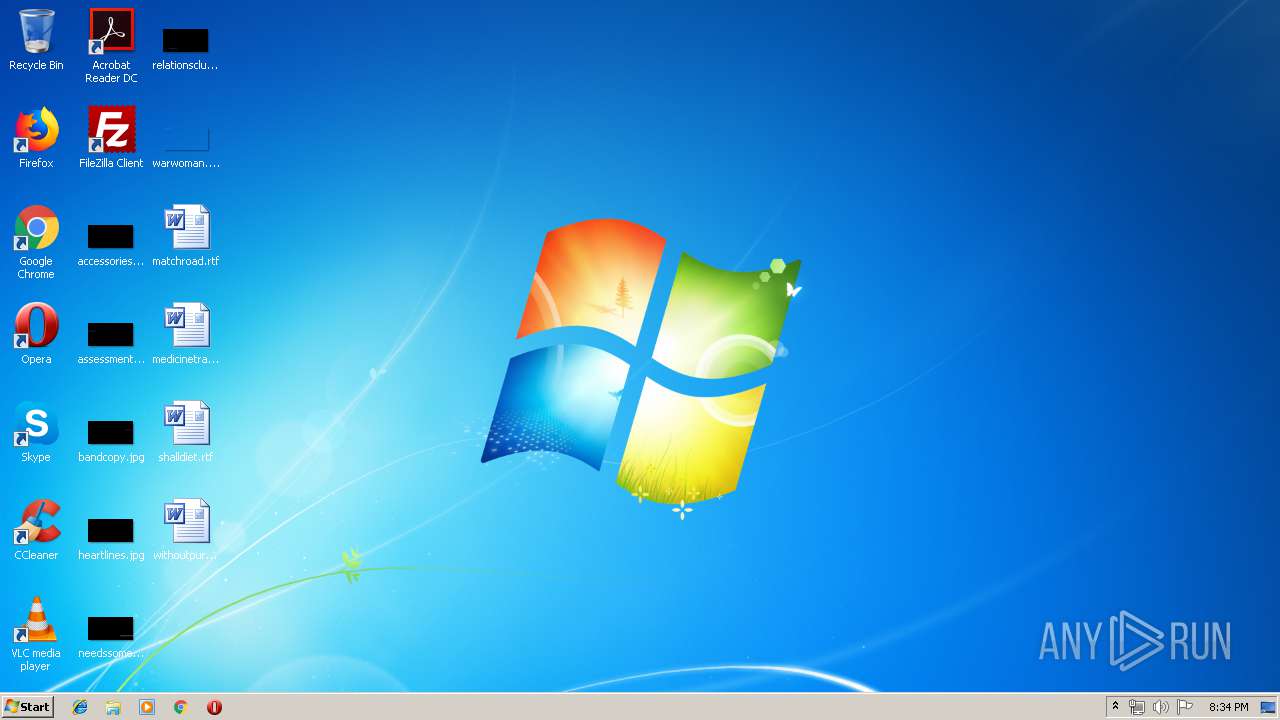
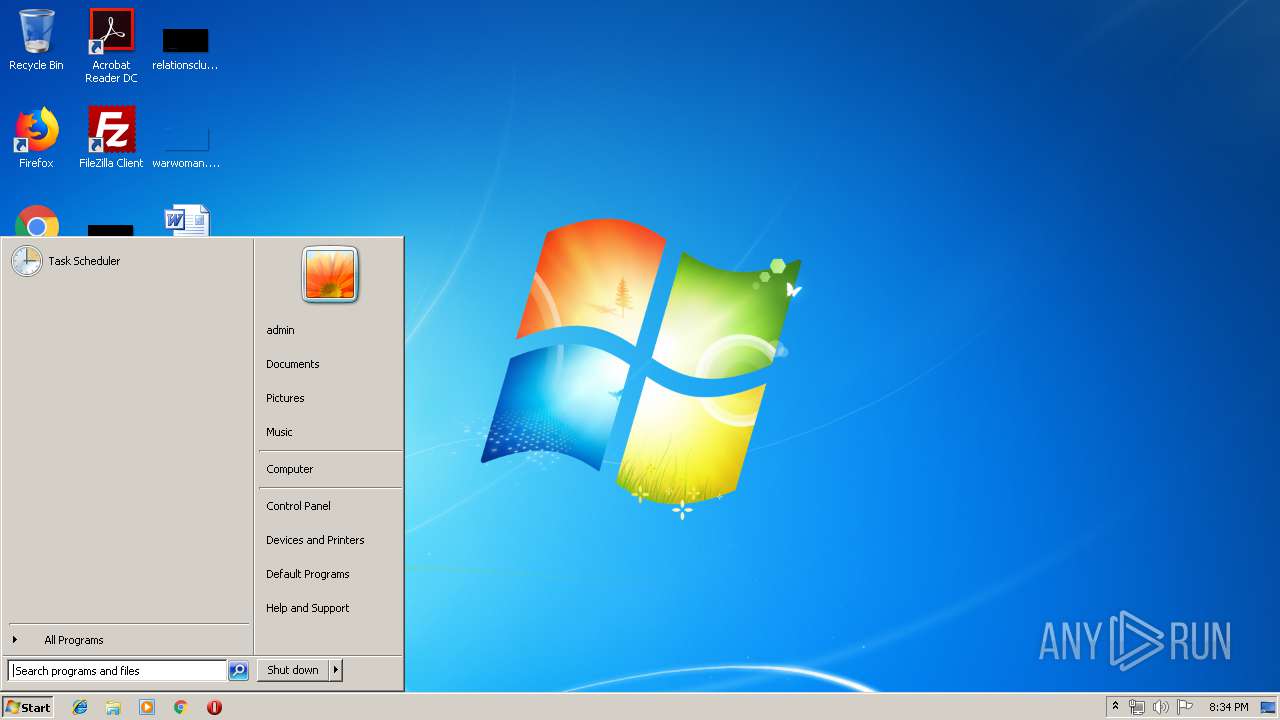
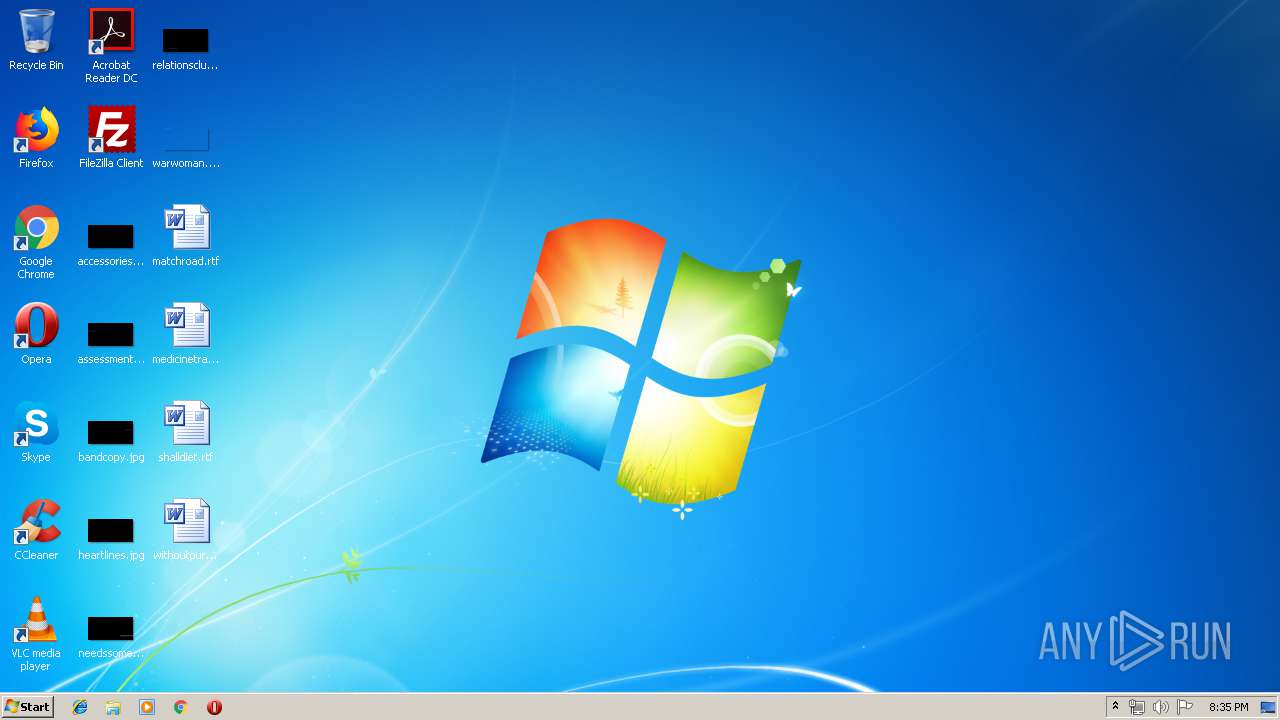
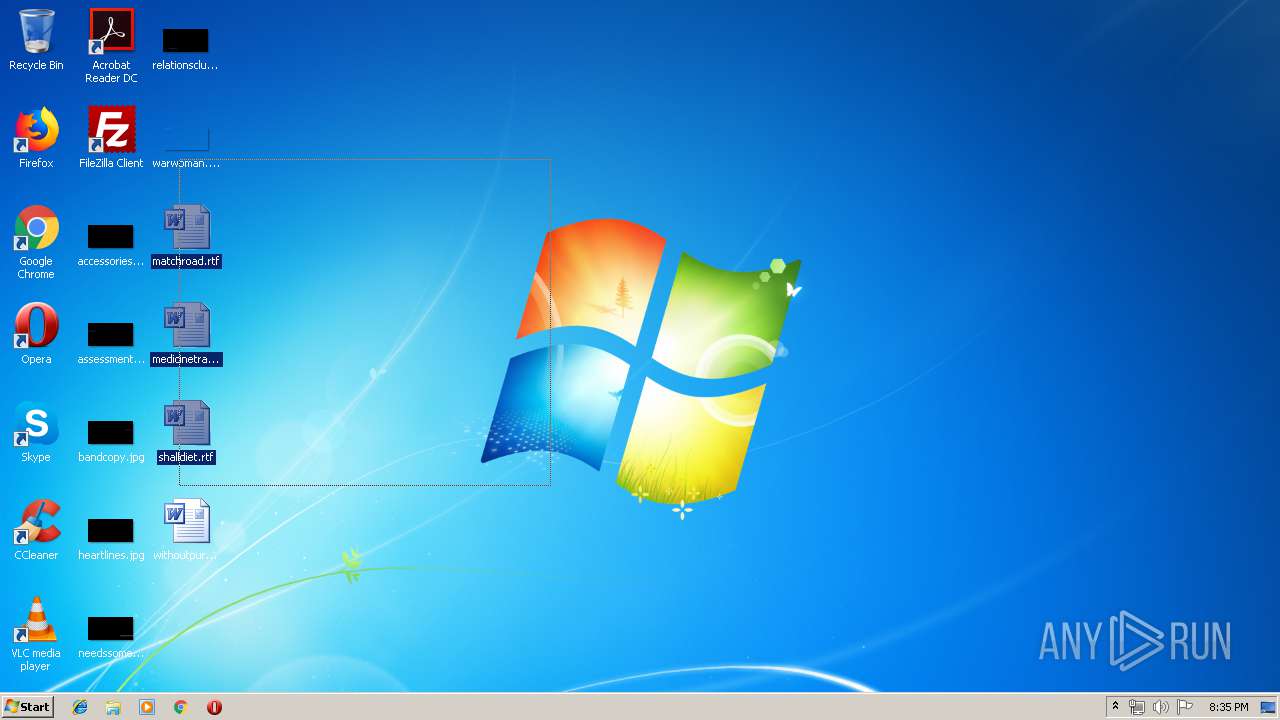
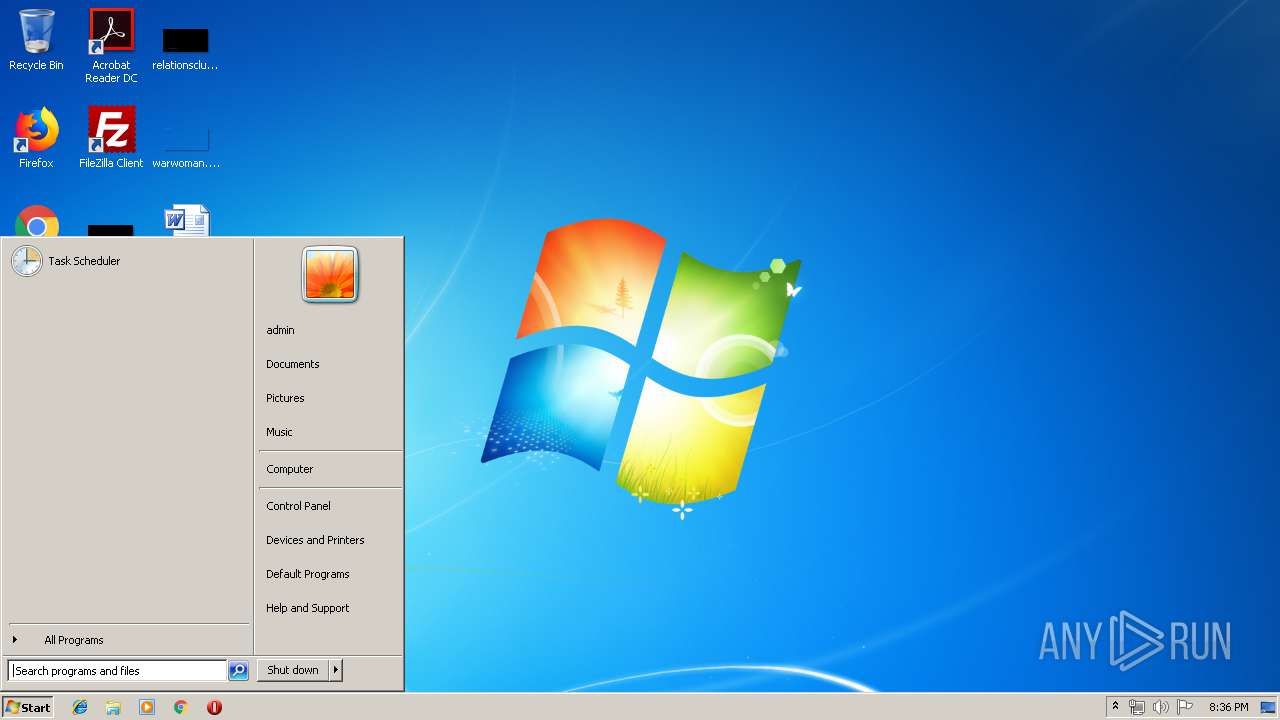
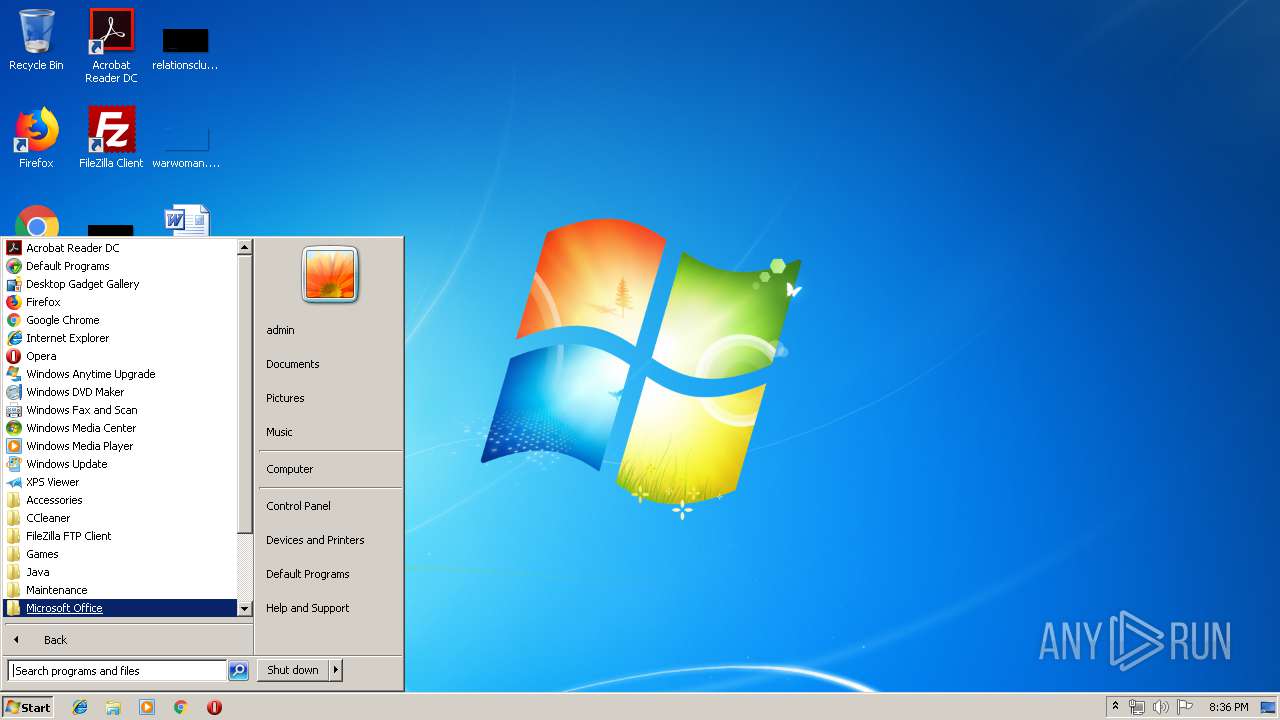
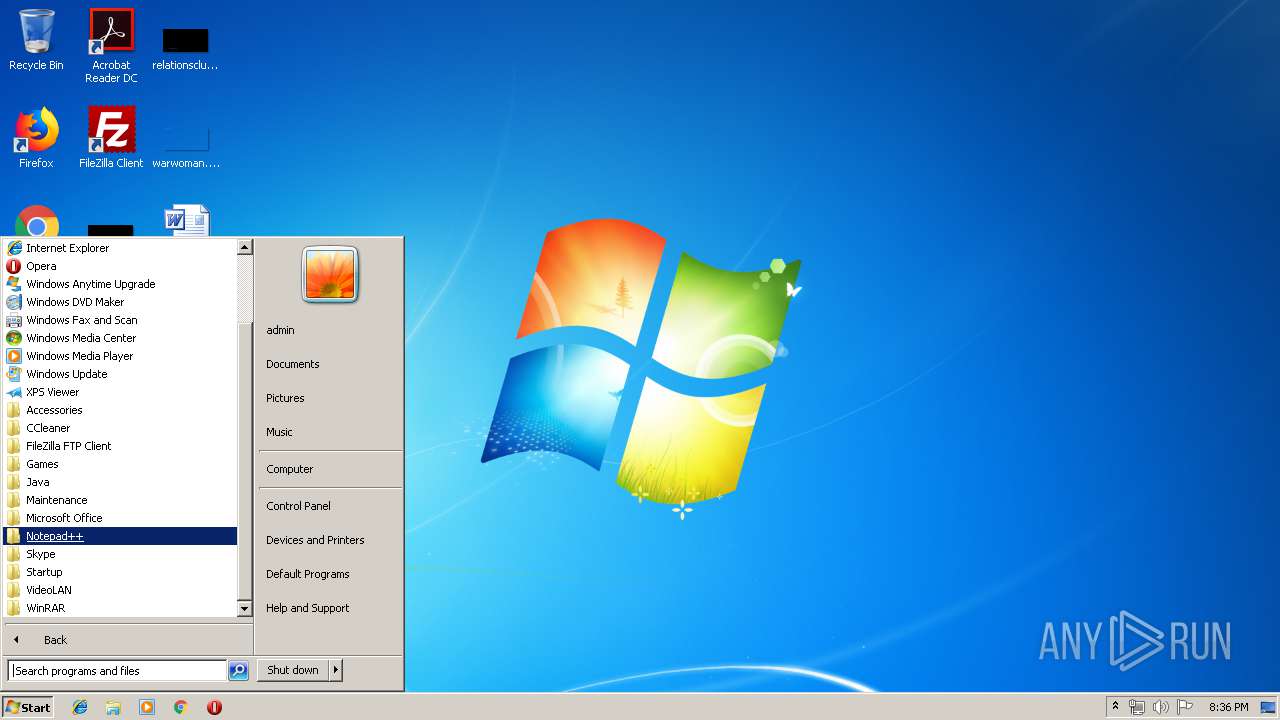
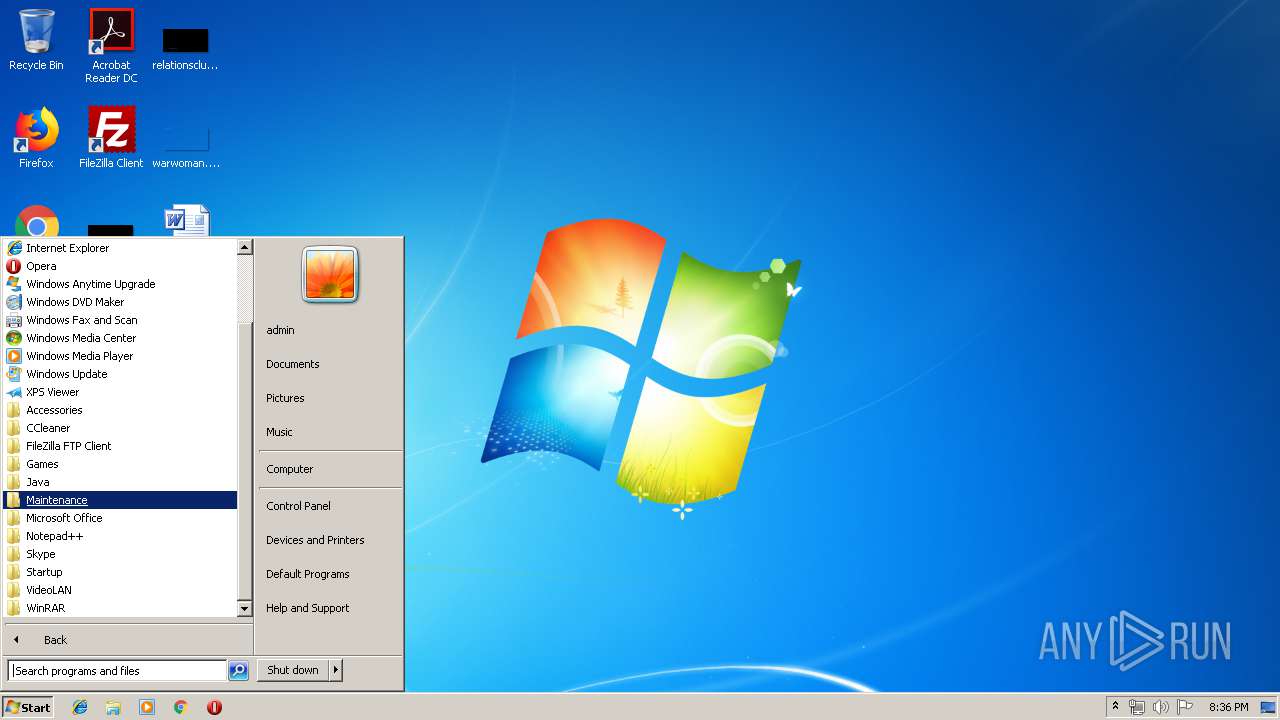
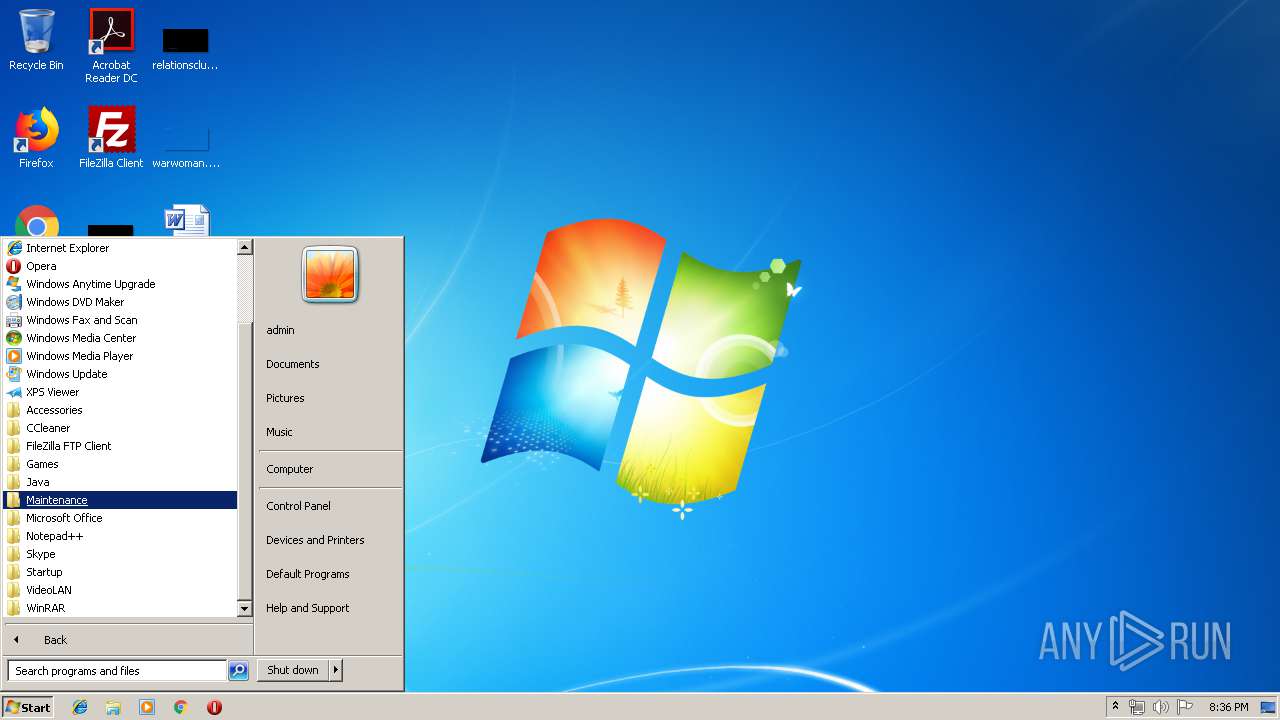
Behavior graph
Click at the process to see the details
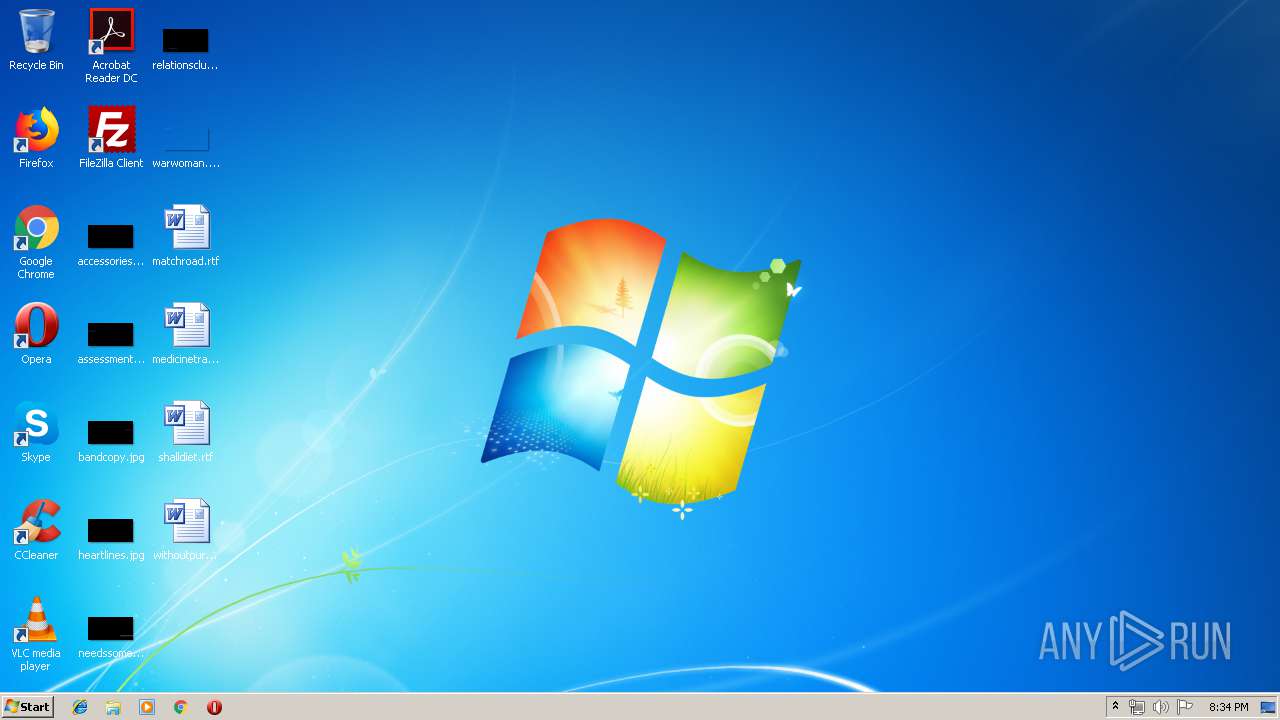
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1444 | "C:\Users\admin\Documents\Jhon.exe" | C:\Users\admin\Documents\Jhon.exe | met.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: met Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1660 | "C:\Users\admin\AppData\Local\Temp\met.exe" | C:\Users\admin\AppData\Local\Temp\met.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: met Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\Documents\Jhon.exe" | C:\Users\admin\Documents\Jhon.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: met Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
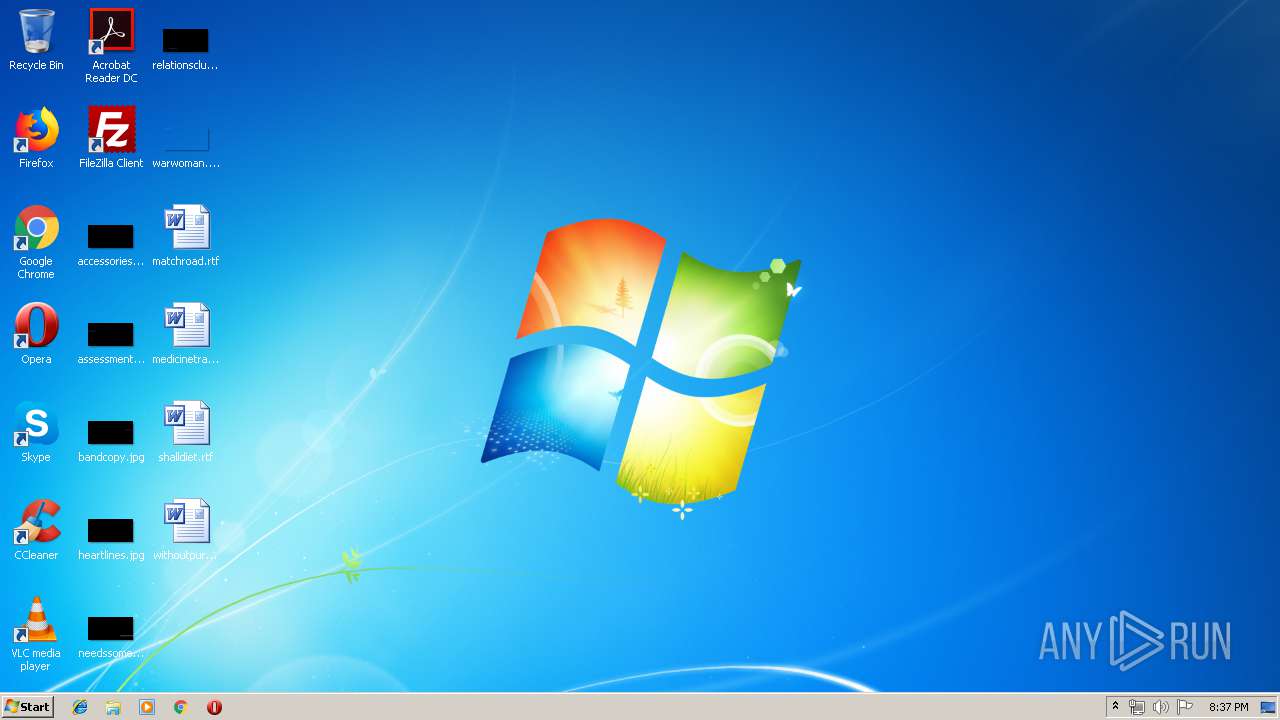
Total events
851
Read events
847
Write events
4
Delete events
0
Modification events
| (PID) Process: | (1660) met.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1660) met.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1660 | met.exe | C:\Users\admin\Documents\Jhon.exe | executable | |
MD5:— | SHA256:— | |||
| 1444 | Jhon.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Jhon.exe.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
37
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1660 | met.exe | 177.95.90.246:1000 | rua7.ddns.net | TELEFÔNICA BRASIL S.A | BR | unknown |
1444 | Jhon.exe | 177.95.90.246:1000 | rua7.ddns.net | TELEFÔNICA BRASIL S.A | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rua7.ddns.net |
| malicious |