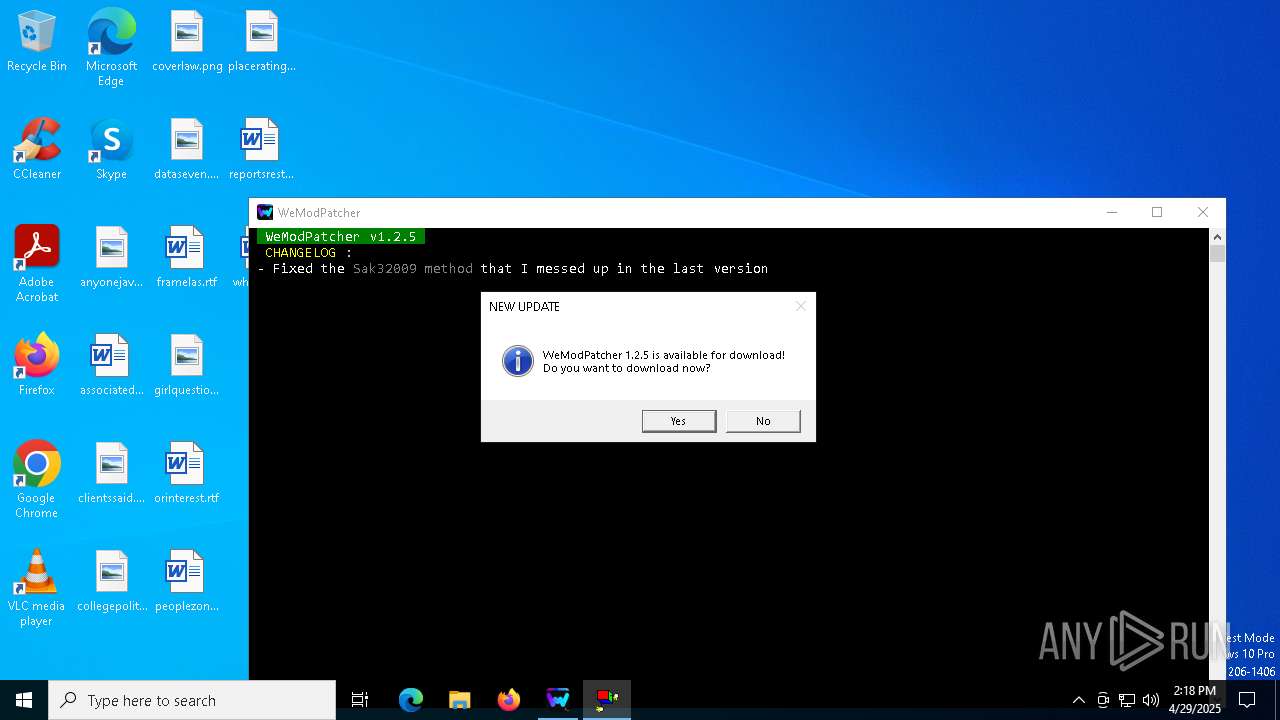
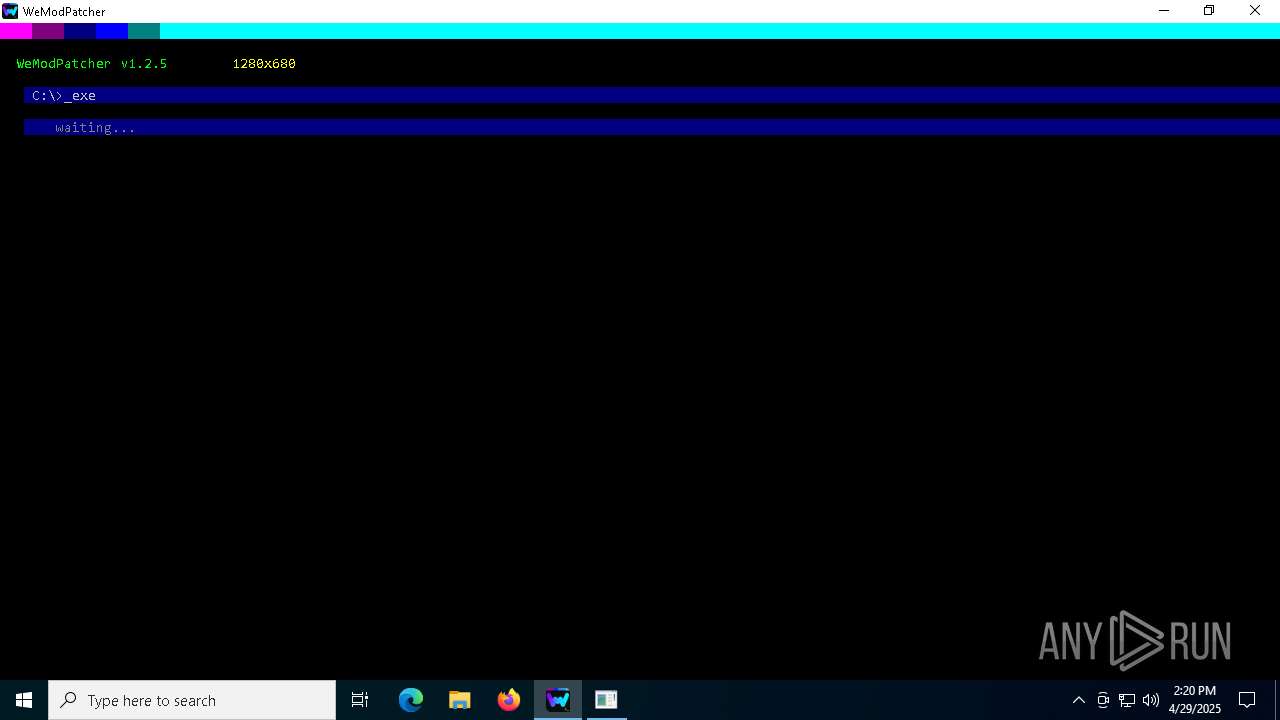
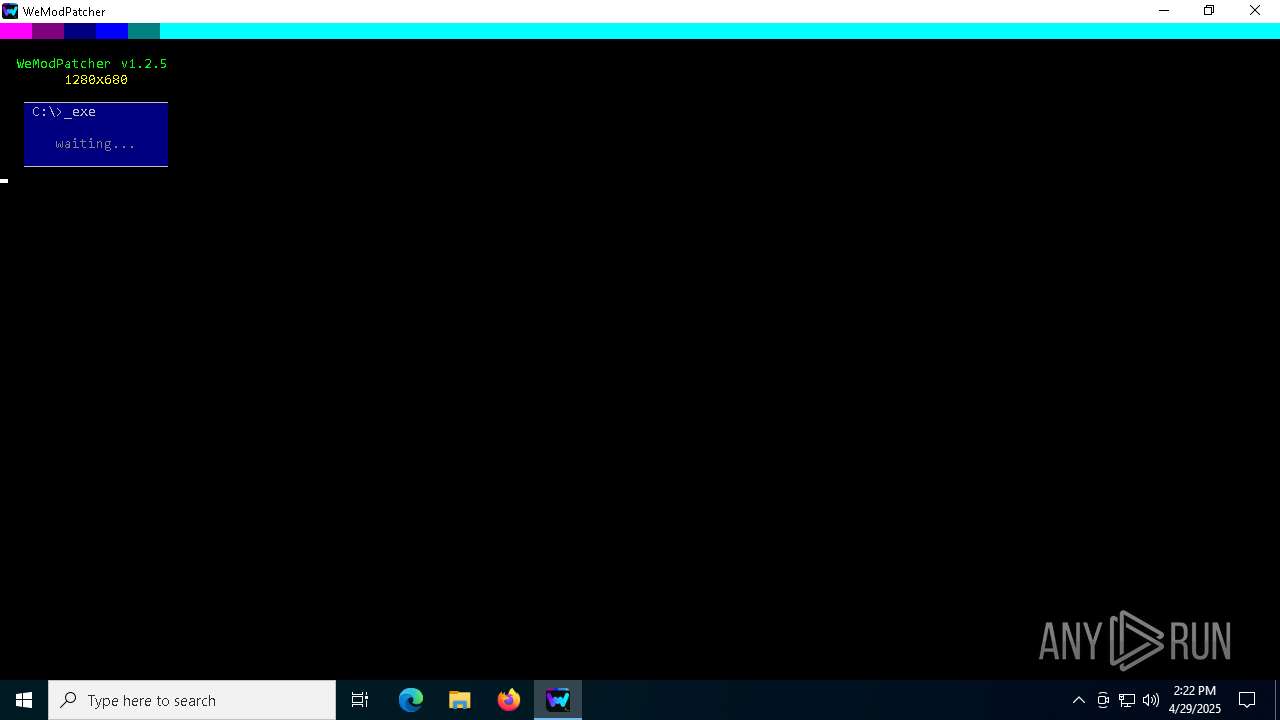
| File name: | WeModPatcher.exe |
| Full analysis: | https://app.any.run/tasks/c0482952-668e-4d75-a1b1-38dfe9025cb6 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 14:17:54 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | EE18B60674B7A614B32816AAFB0E221C |
| SHA1: | A2ACA23DA84AF4F7E6EF0095C1359A11B1AA4C47 |
| SHA256: | D0942C3A08B1AE16316283BAC0E386D50FB55C254C5AA4221850774BCFEEDF7D |
| SSDEEP: | 98304:00RXUTfCh2HVNYDq0S/oeM5++nFqSLsjFjmb90Bgni3tiFZIJFzj9FyAp83RRwyO:iNQs |
MALICIOUS
No malicious indicators.SUSPICIOUS
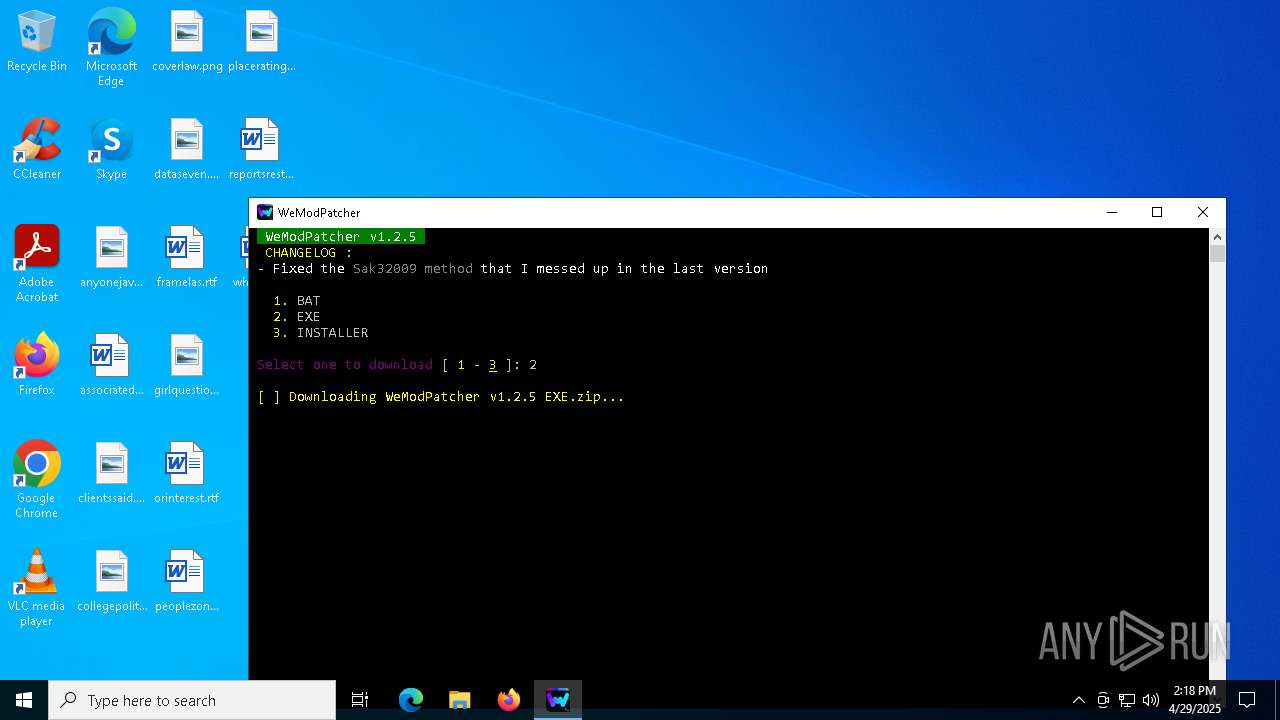
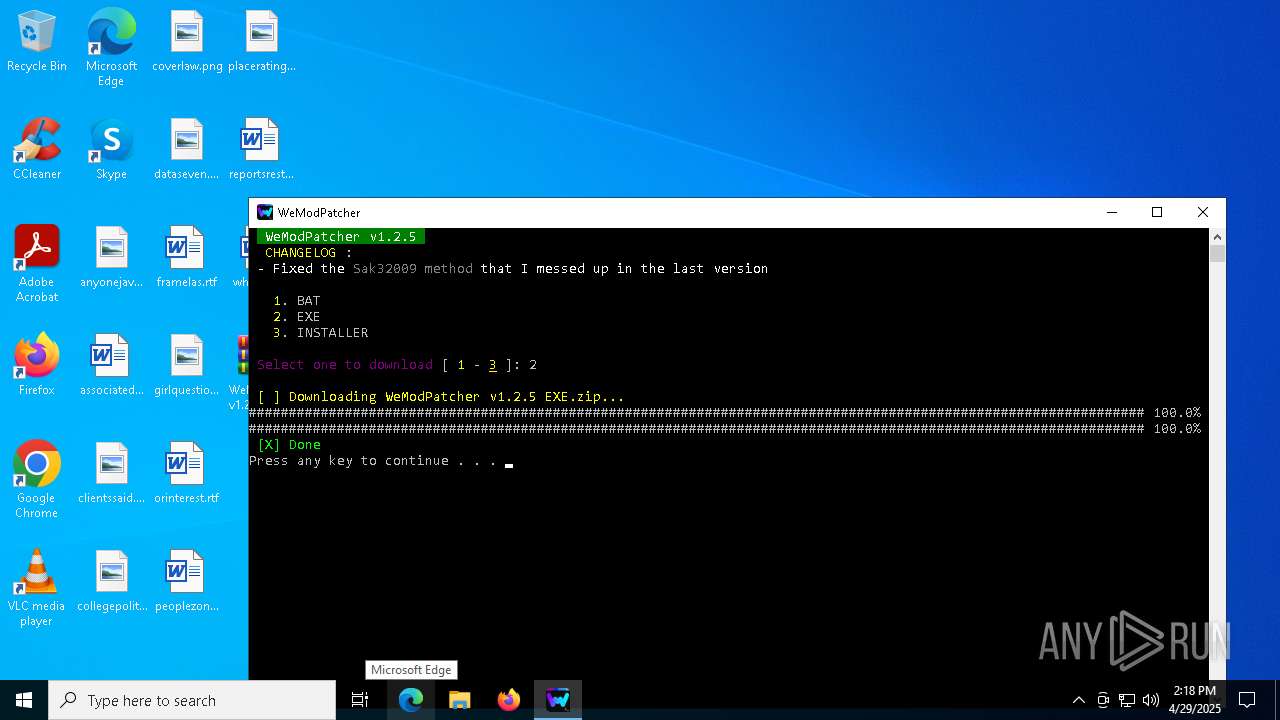
Drops 7-zip archiver for unpacking
- WeModPatcher.exe (PID: 7476)
- WeModPatcher.exe (PID: 7676)
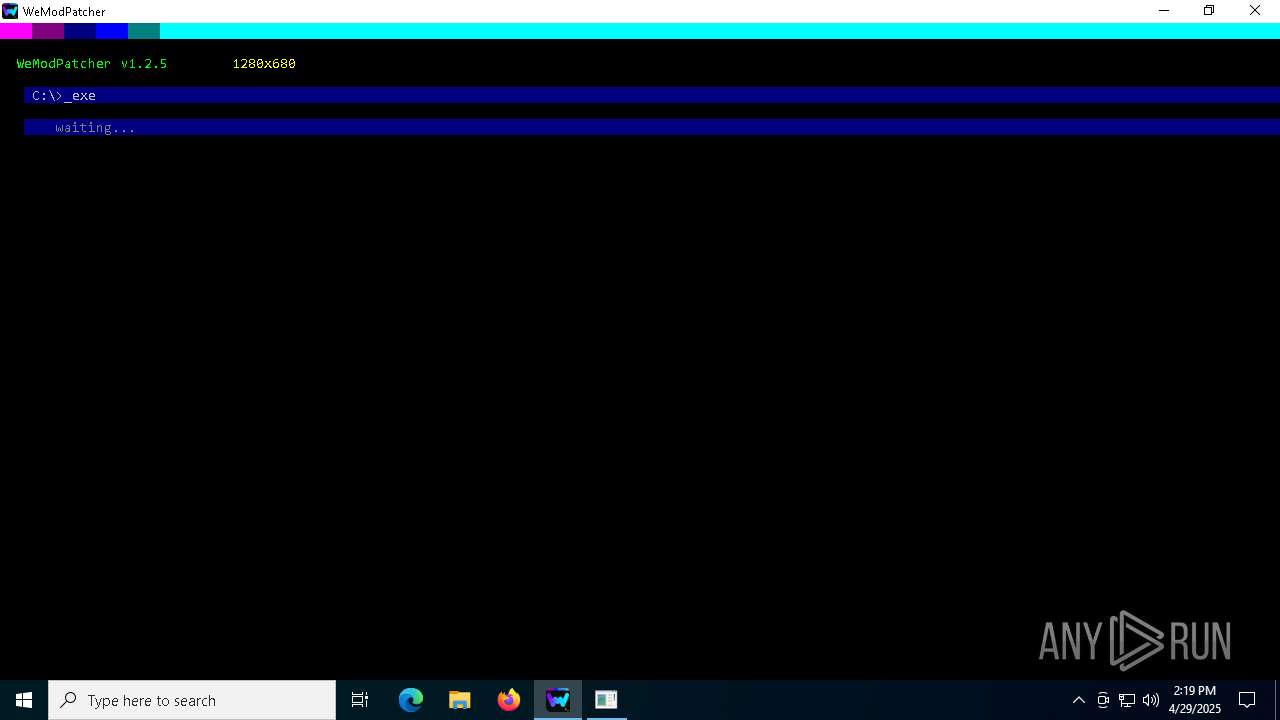
Starts CMD.EXE for commands execution
- WeModPatcher.exe (PID: 7476)
- cmd.exe (PID: 7556)
- WeModPatcher.exe (PID: 7676)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 896)
- WeModPatcher.exe (PID: 4996)
Executing commands from a ".bat" file
- WeModPatcher.exe (PID: 7476)
- WeModPatcher.exe (PID: 7676)
- WeModPatcher.exe (PID: 4996)
Execution of CURL command
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 896)
Application launched itself
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 896)
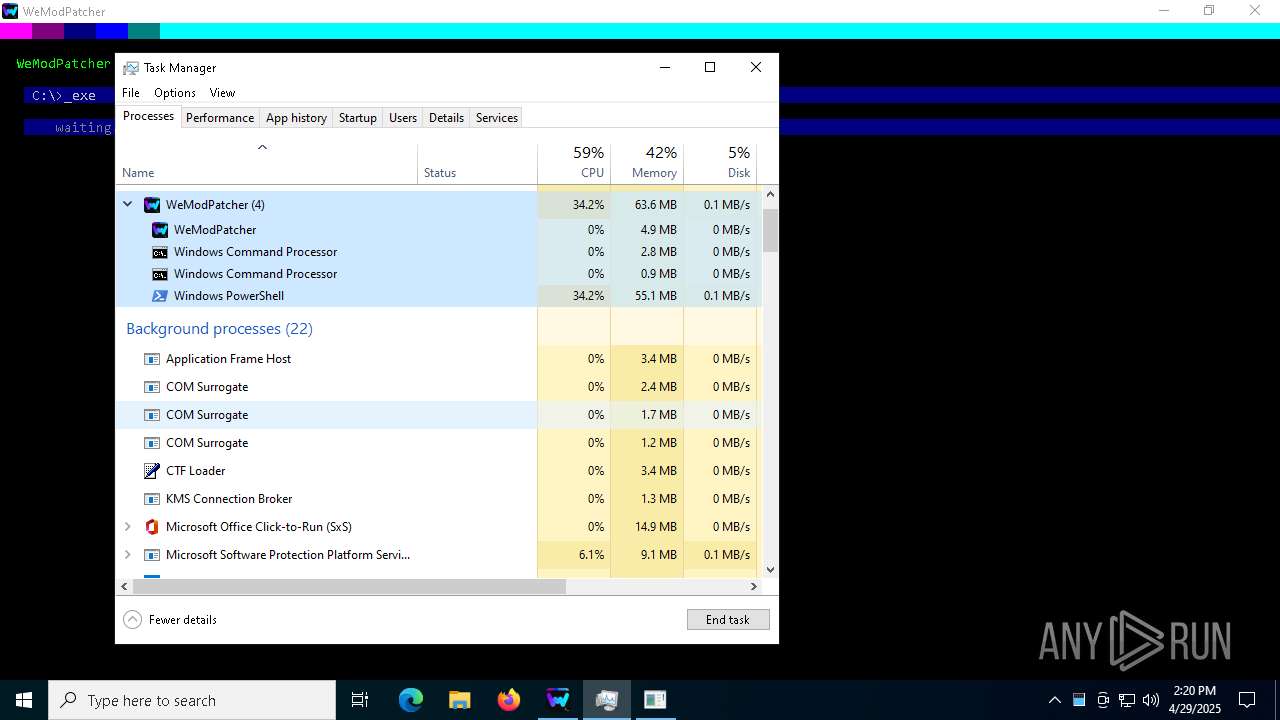
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7640)
- cmd.exe (PID: 300)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 664)
- cmd.exe (PID: 7192)
- cmd.exe (PID: 8128)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 6944)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 5404)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 6300)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 5428)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 5360)
- cmd.exe (PID: 232)
- cmd.exe (PID: 1676)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 6324)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 5596)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 7136)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 896)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 7552)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 232)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 680)
- cmd.exe (PID: 7520)
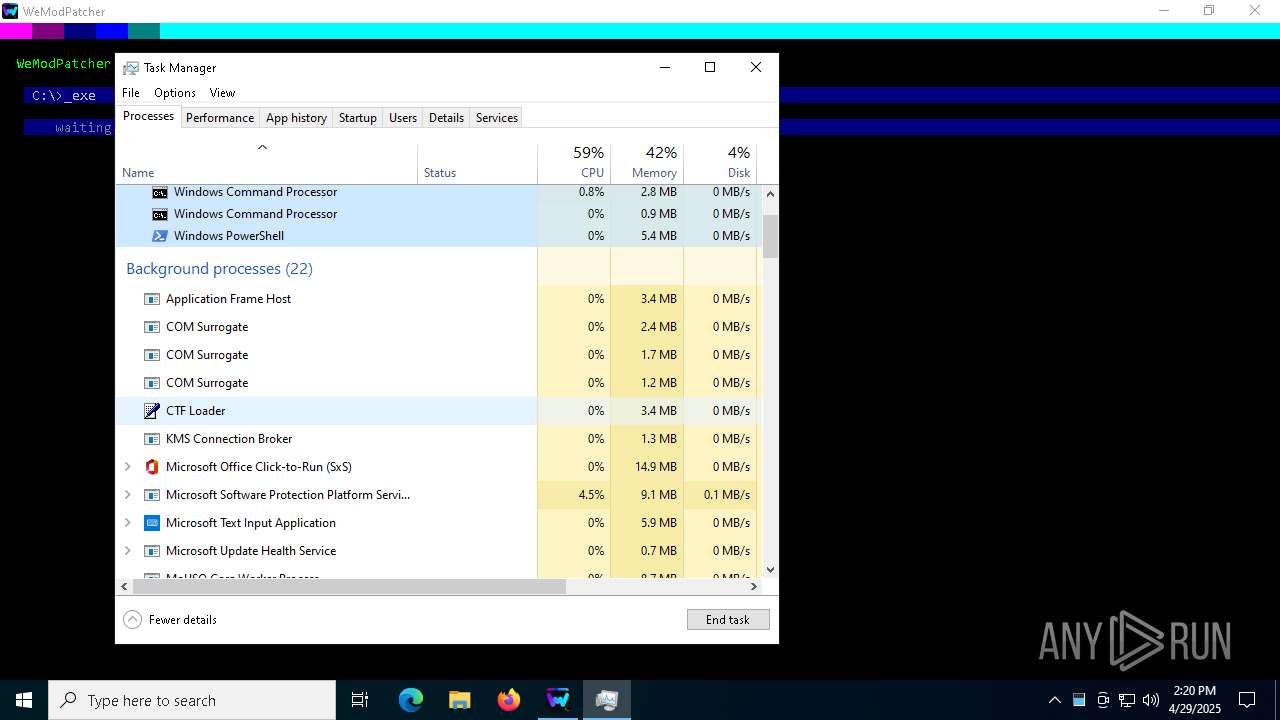
The process executes VB scripts
- cmd.exe (PID: 8064)
Creates file in the systems drive root
- powershell.exe (PID: 1244)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7648)
- net.exe (PID: 1040)
- cmd.exe (PID: 896)
- net.exe (PID: 6872)
Get information on the list of running processes
- cmd.exe (PID: 7236)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 5404)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 896)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 680)
Starts application with an unusual extension
- cmd.exe (PID: 4756)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 896)
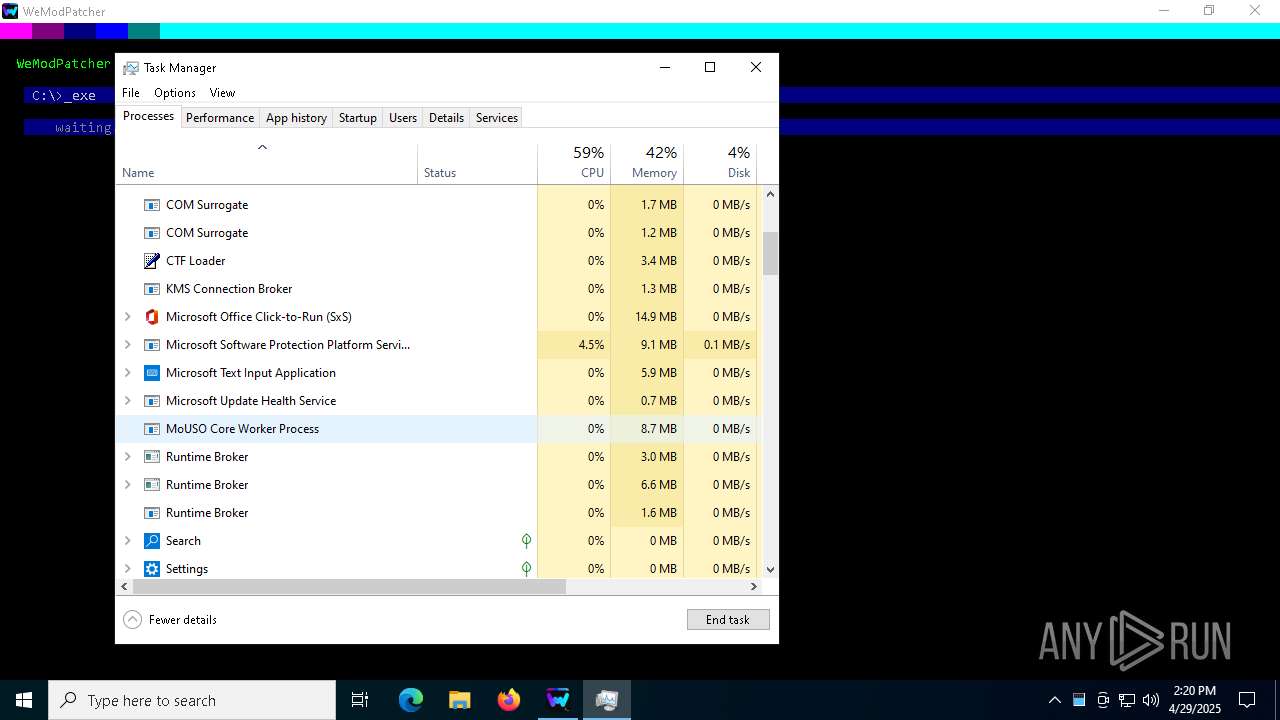
Executes application which crashes
- mshta.exe (PID: 6512)
- mshta.exe (PID: 4728)
- mshta.exe (PID: 7312)
- mshta.exe (PID: 7836)
- mshta.exe (PID: 7624)
- mshta.exe (PID: 7436)
- mshta.exe (PID: 4428)
- mshta.exe (PID: 6944)
- mshta.exe (PID: 2064)
- mshta.exe (PID: 5892)
- mshta.exe (PID: 3884)
- mshta.exe (PID: 8136)
- mshta.exe (PID: 8068)
- mshta.exe (PID: 7292)
- mshta.exe (PID: 6344)
- mshta.exe (PID: 2320)
- mshta.exe (PID: 5528)
- mshta.exe (PID: 7604)
- mshta.exe (PID: 2780)
- mshta.exe (PID: 7404)
- mshta.exe (PID: 8092)
- mshta.exe (PID: 4220)
- mshta.exe (PID: 6044)
- mshta.exe (PID: 7616)
- mshta.exe (PID: 744)
- mshta.exe (PID: 2776)
- mshta.exe (PID: 1676)
- mshta.exe (PID: 8116)
- mshta.exe (PID: 4244)
- mshta.exe (PID: 2644)
- mshta.exe (PID: 1568)
- mshta.exe (PID: 5640)
- mshta.exe (PID: 1748)
- mshta.exe (PID: 6800)
- mshta.exe (PID: 6028)
- mshta.exe (PID: 4380)
- mshta.exe (PID: 6148)
- mshta.exe (PID: 2244)
- mshta.exe (PID: 5728)
- mshta.exe (PID: 7480)
- mshta.exe (PID: 7660)
- mshta.exe (PID: 7504)
- mshta.exe (PID: 6676)
- mshta.exe (PID: 7736)
- mshta.exe (PID: 7896)
- mshta.exe (PID: 5376)
- mshta.exe (PID: 960)
INFO
Checks supported languages
- WeModPatcher.exe (PID: 7476)
- curl.exe (PID: 7588)
- curl.exe (PID: 7228)
- curl.exe (PID: 1760)
- curl.exe (PID: 8000)
- curl.exe (PID: 7632)
- curl.exe (PID: 3884)
- WeModPatcher.exe (PID: 7676)
- chcp.com (PID: 2384)
- mode.com (PID: 7360)
- chcp.com (PID: 5072)
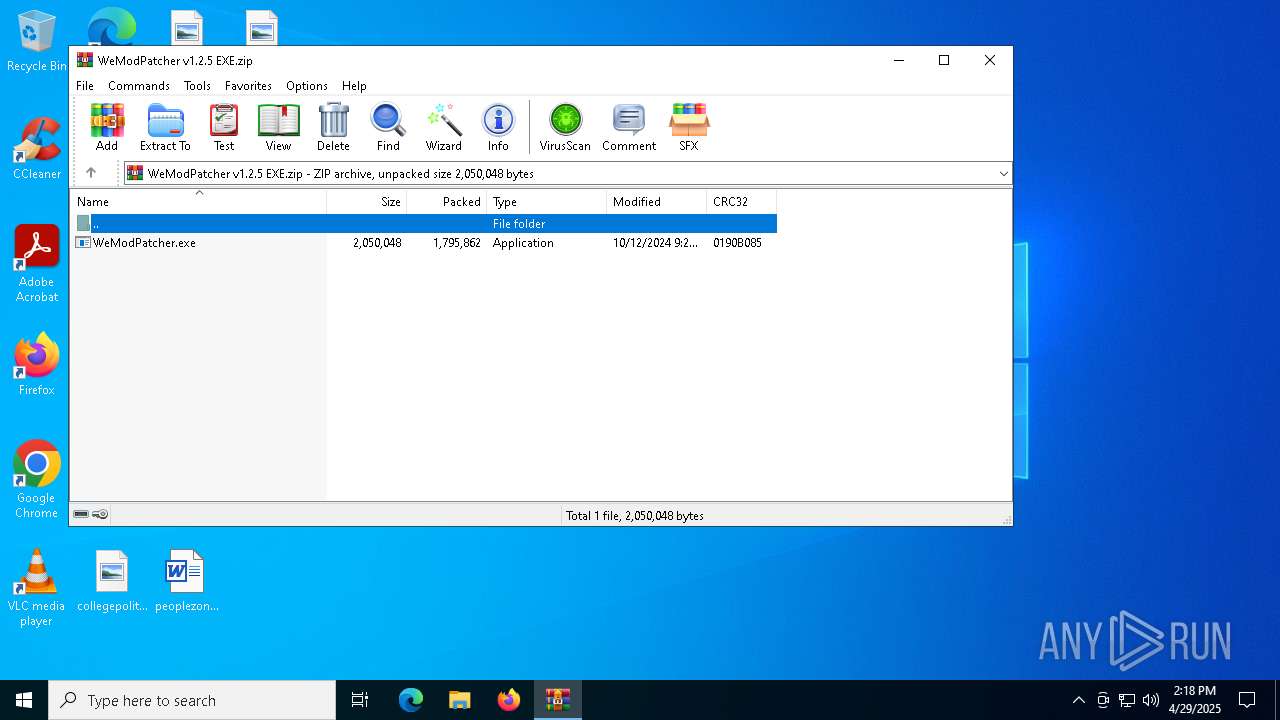
The sample compiled with english language support
- WeModPatcher.exe (PID: 7476)
- curl.exe (PID: 1760)
- WinRAR.exe (PID: 7944)
- WeModPatcher.exe (PID: 7676)
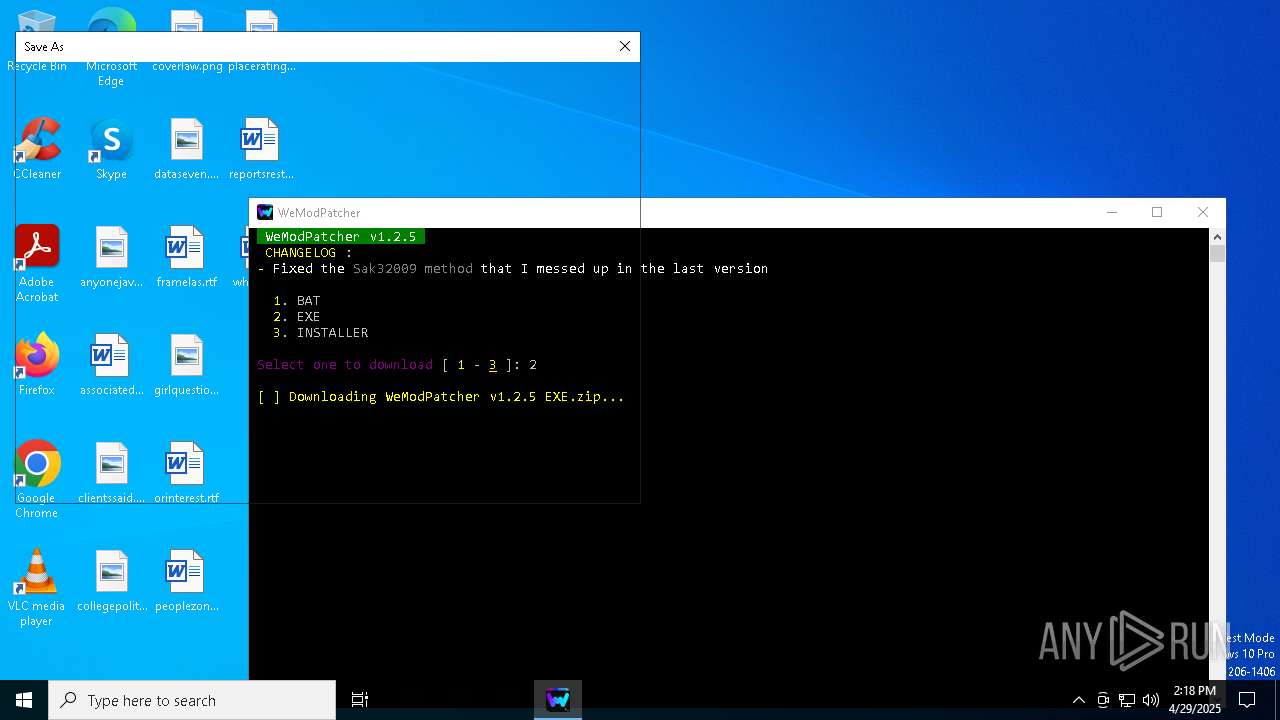
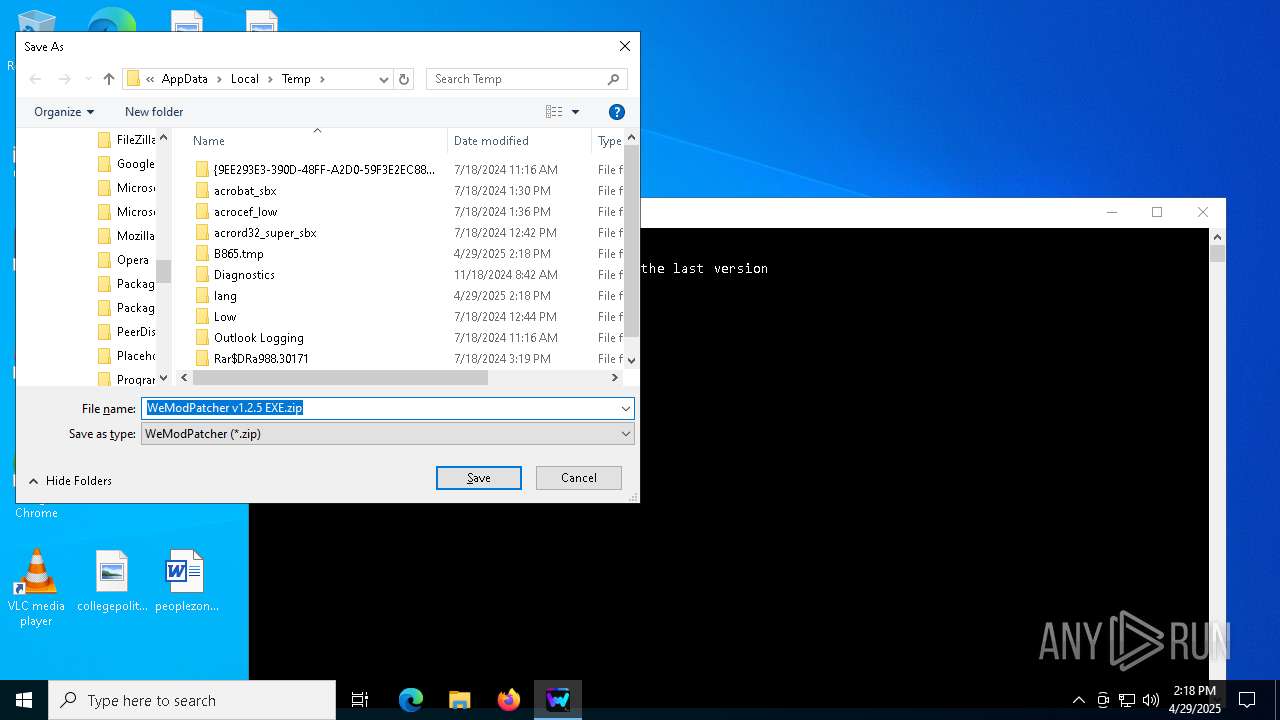
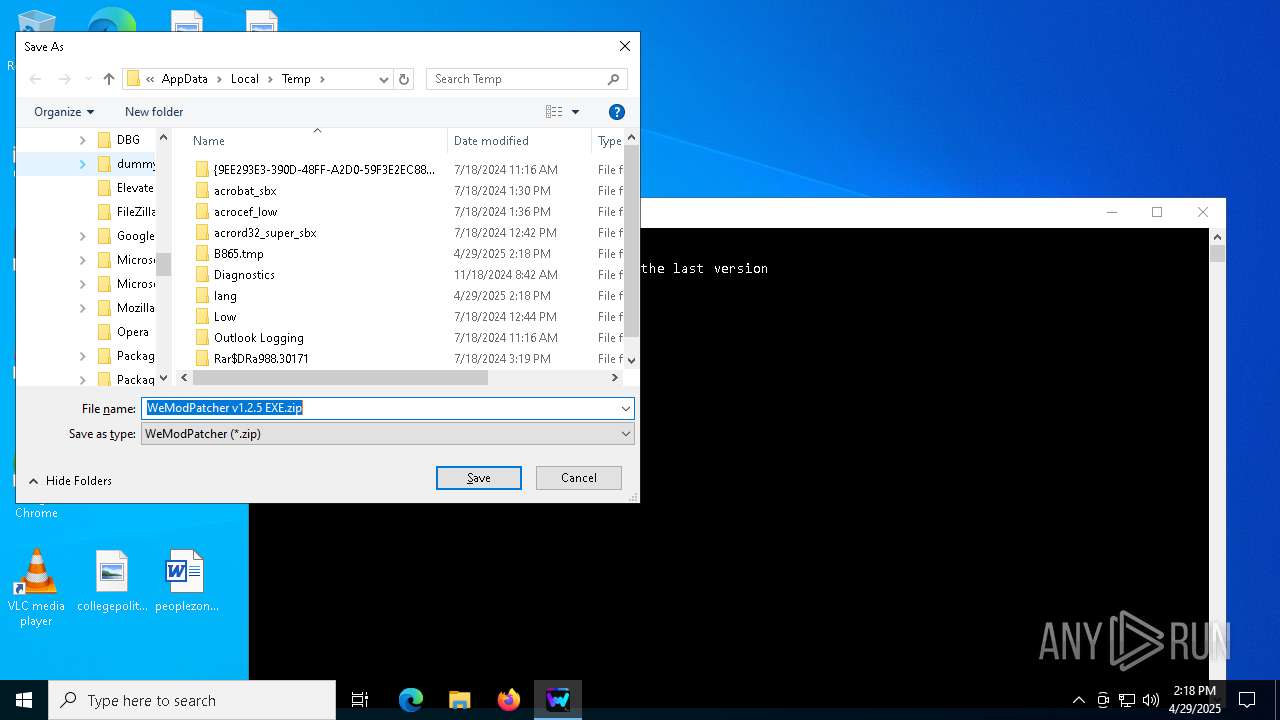
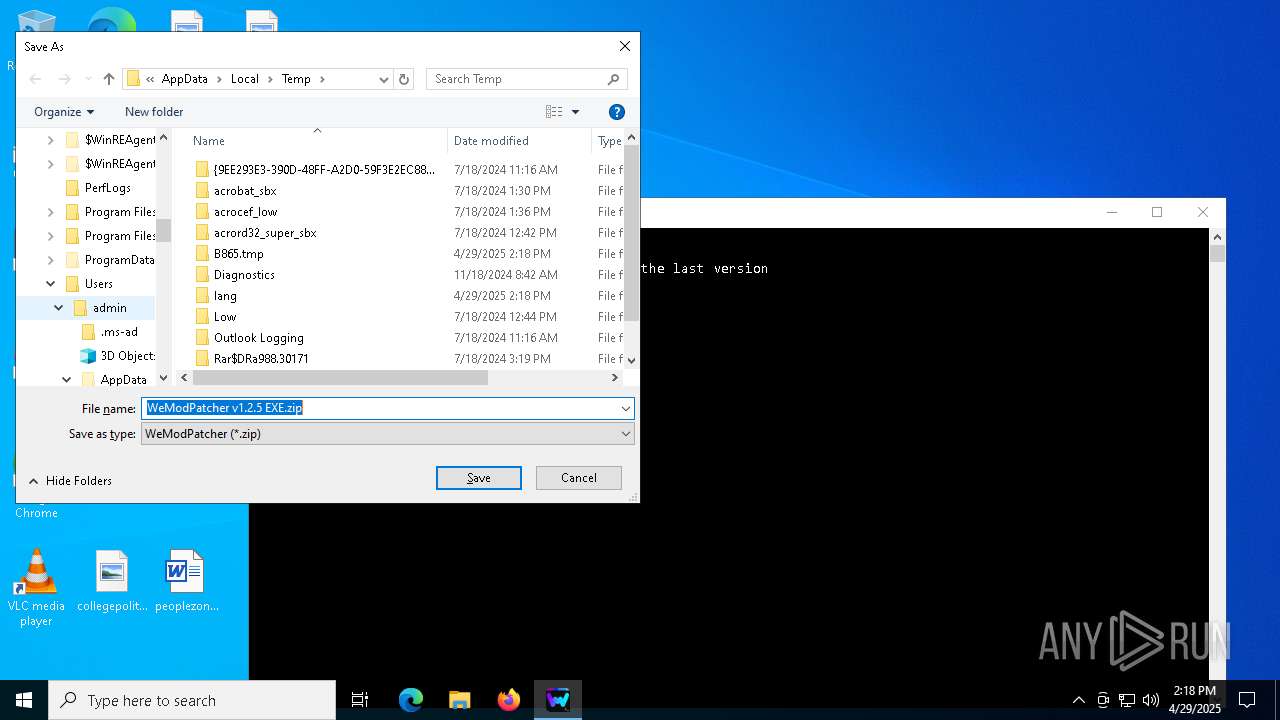
Create files in a temporary directory
- WeModPatcher.exe (PID: 7476)
- curl.exe (PID: 7632)
- WeModPatcher.exe (PID: 7676)
Execution of CURL command
- cmd.exe (PID: 7572)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 7932)
Reads the computer name
- curl.exe (PID: 7588)
- curl.exe (PID: 7228)
- curl.exe (PID: 1760)
- curl.exe (PID: 7632)
- curl.exe (PID: 8000)
- curl.exe (PID: 3884)
Reads security settings of Internet Explorer
- cscript.exe (PID: 8080)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7944)
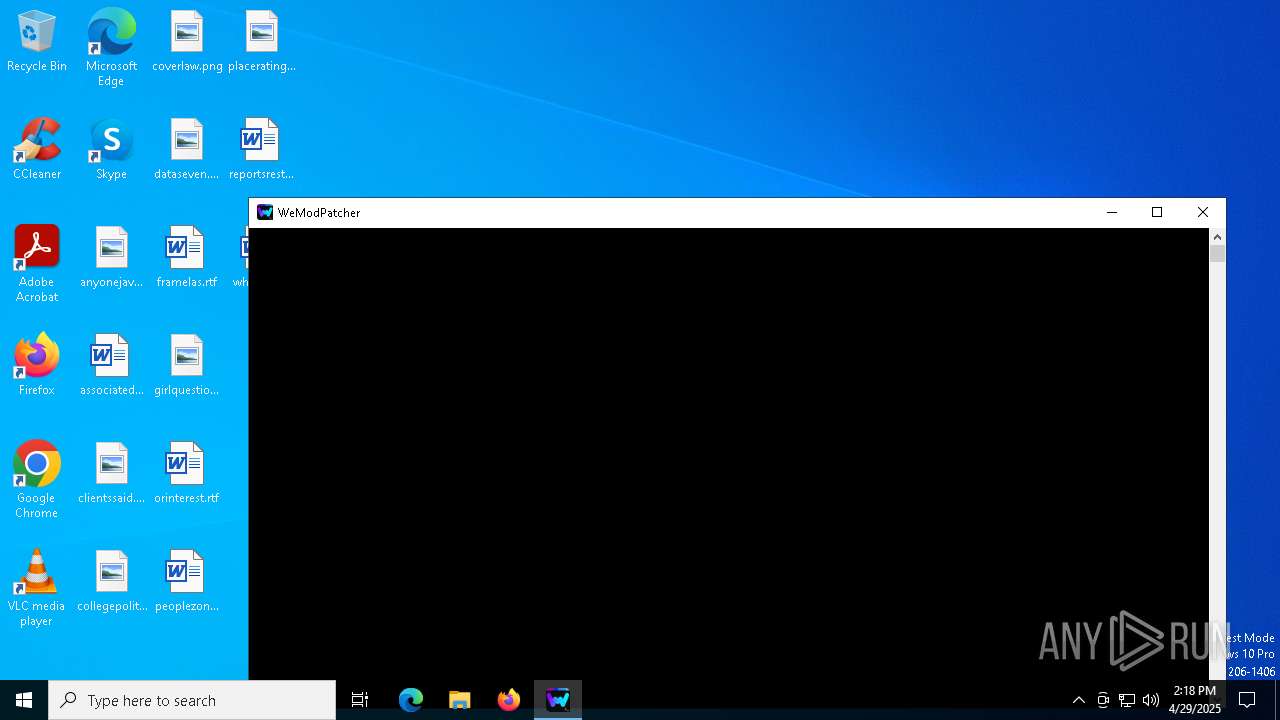
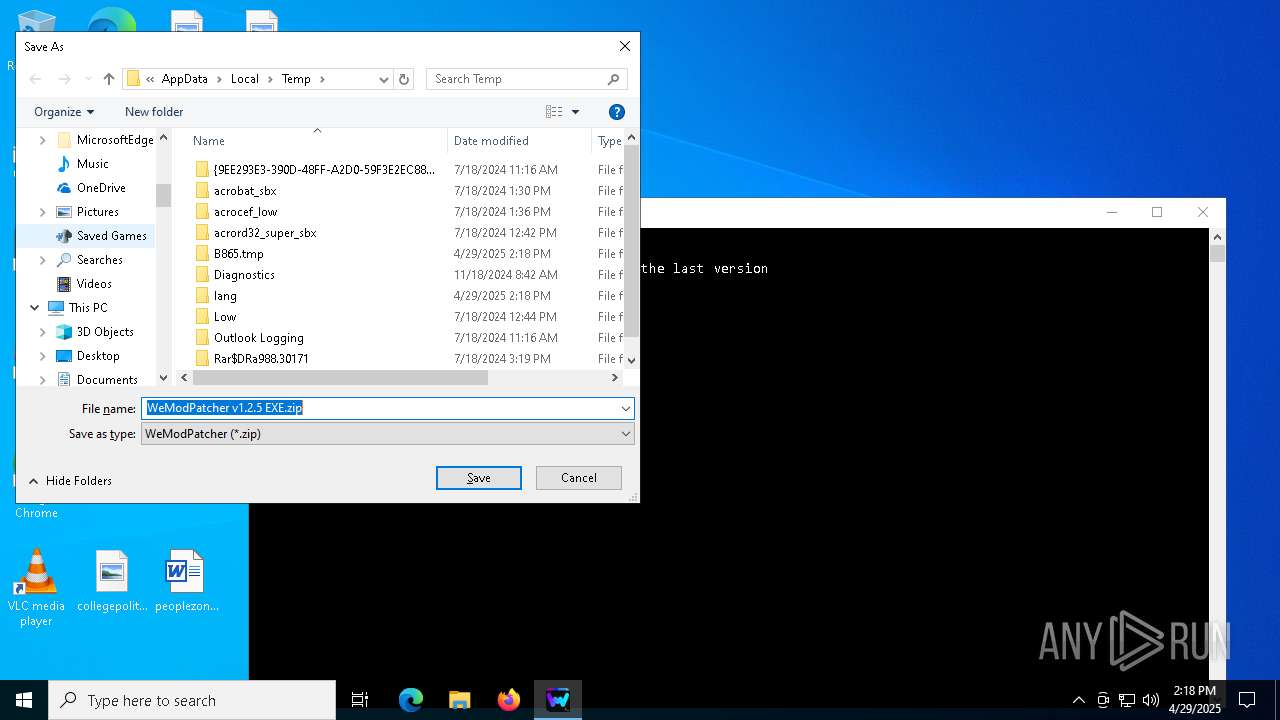
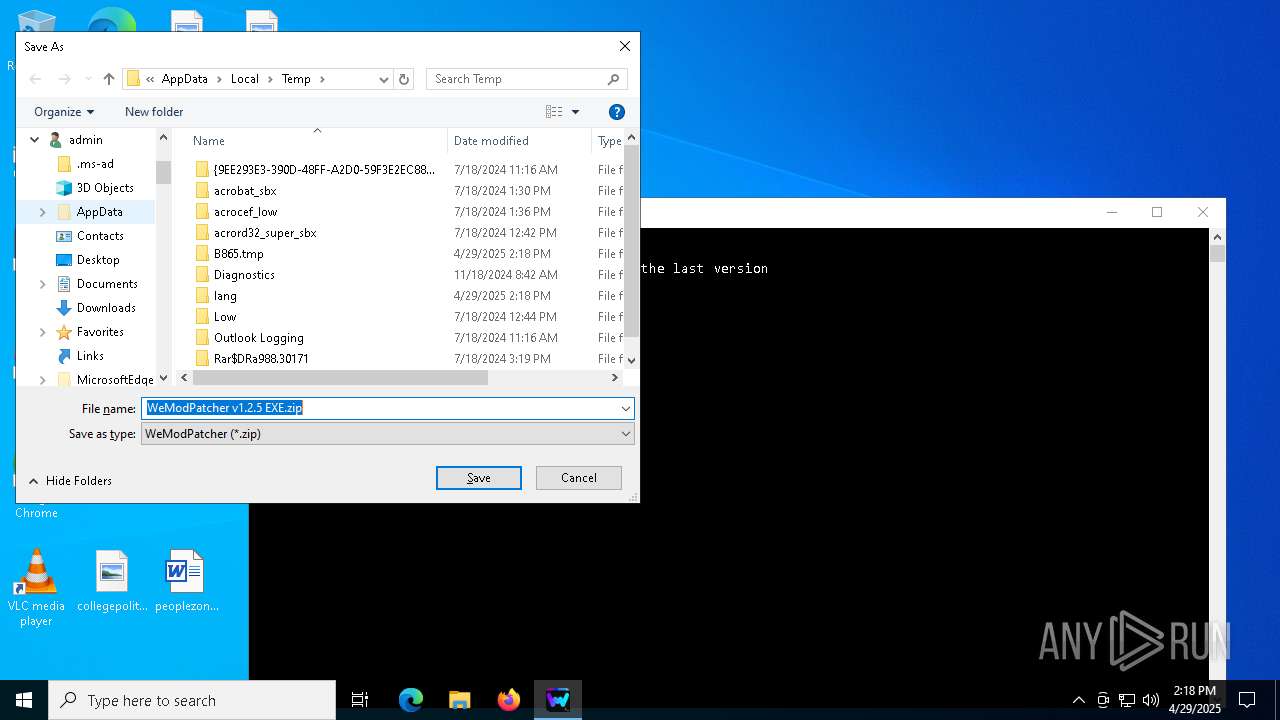
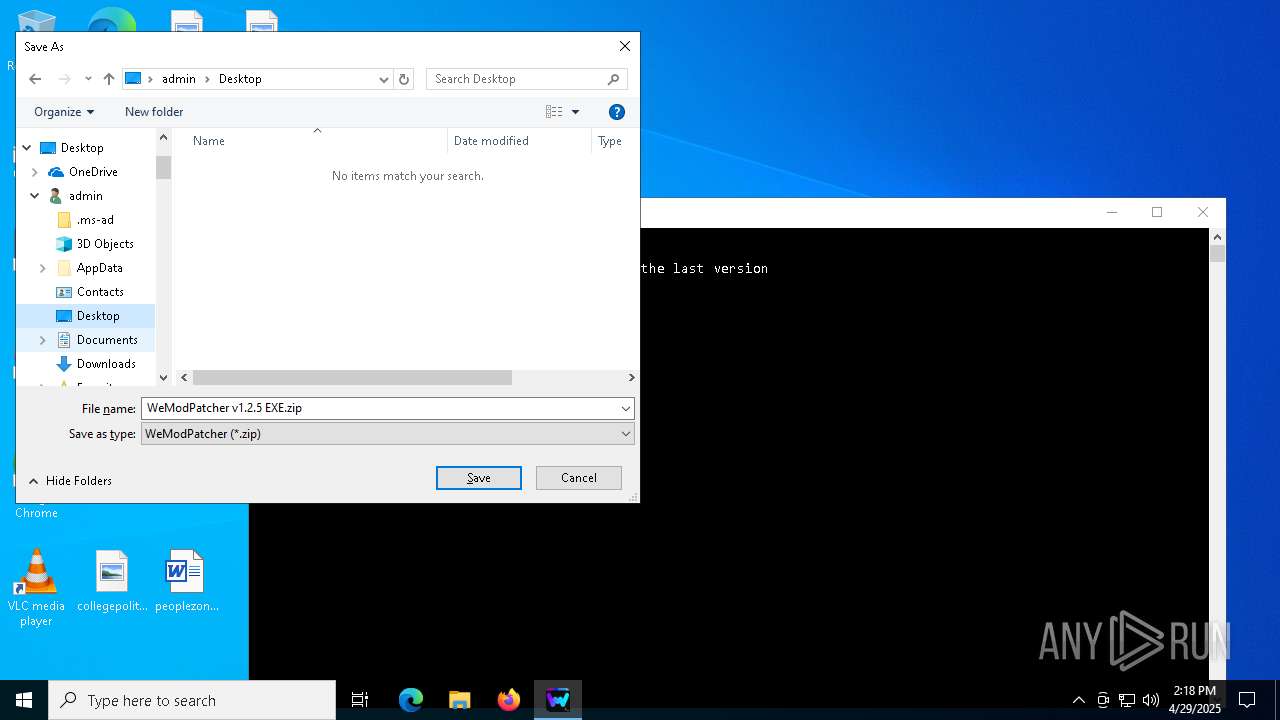
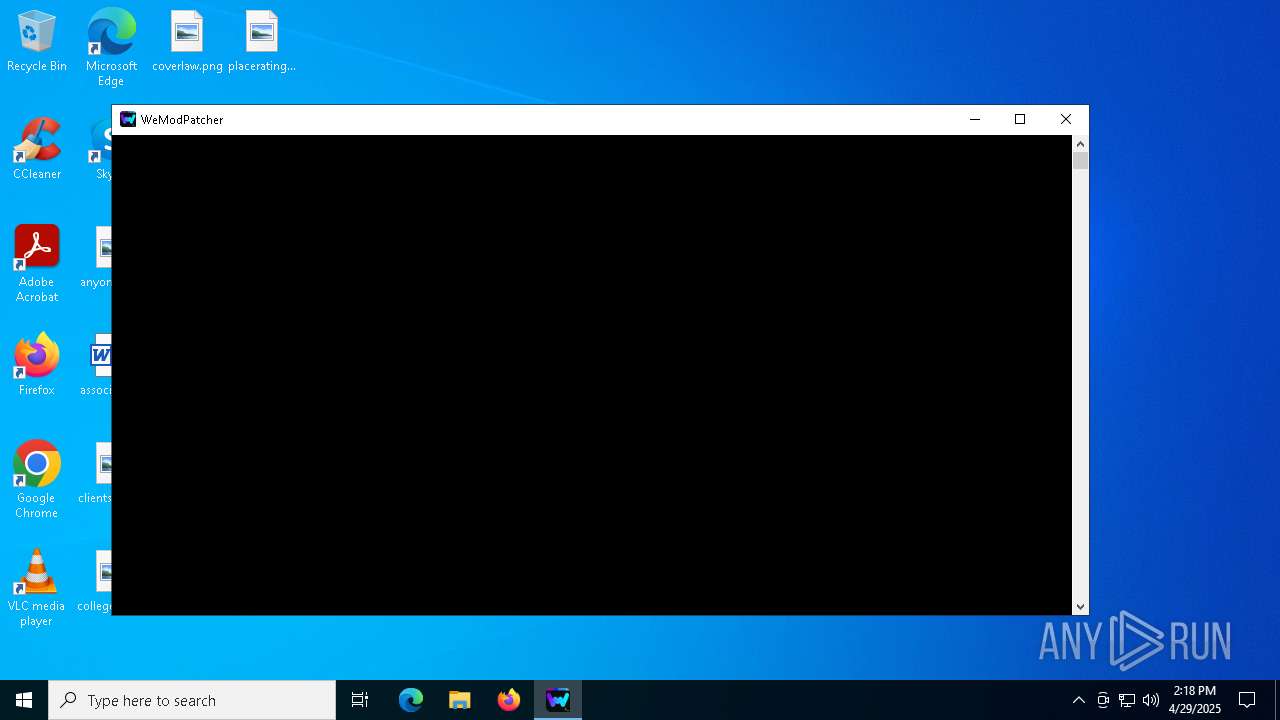
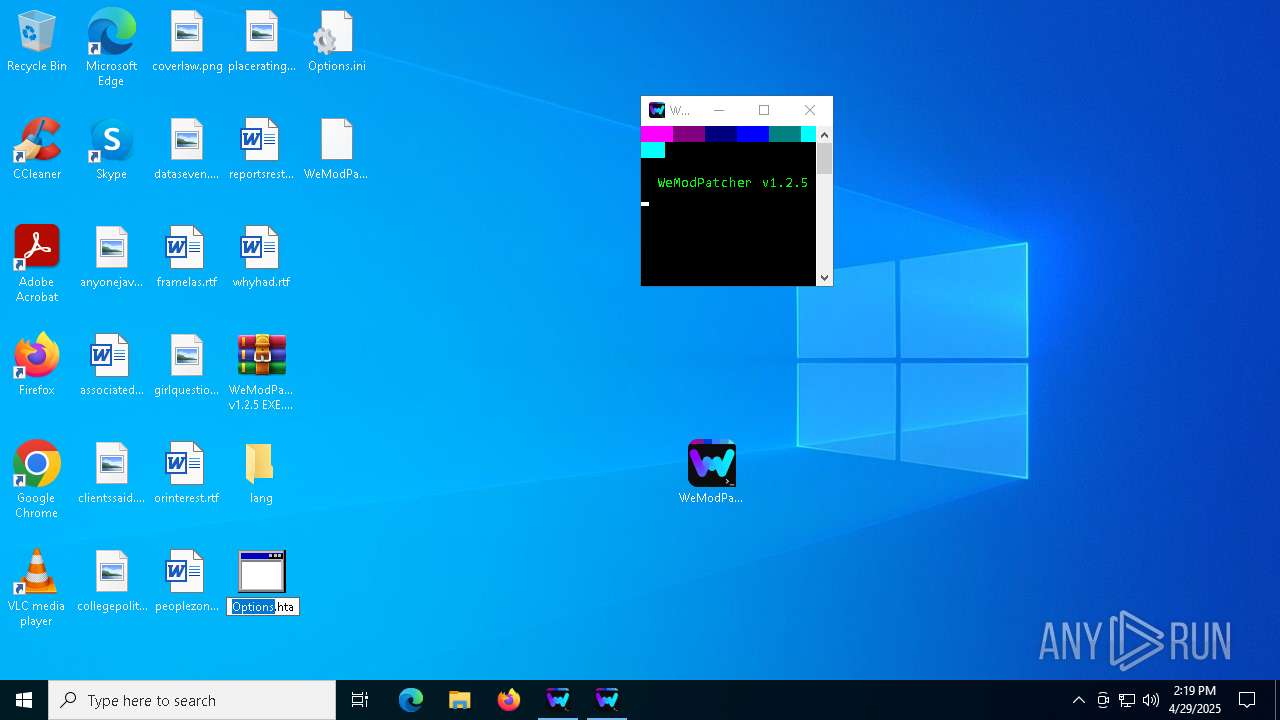
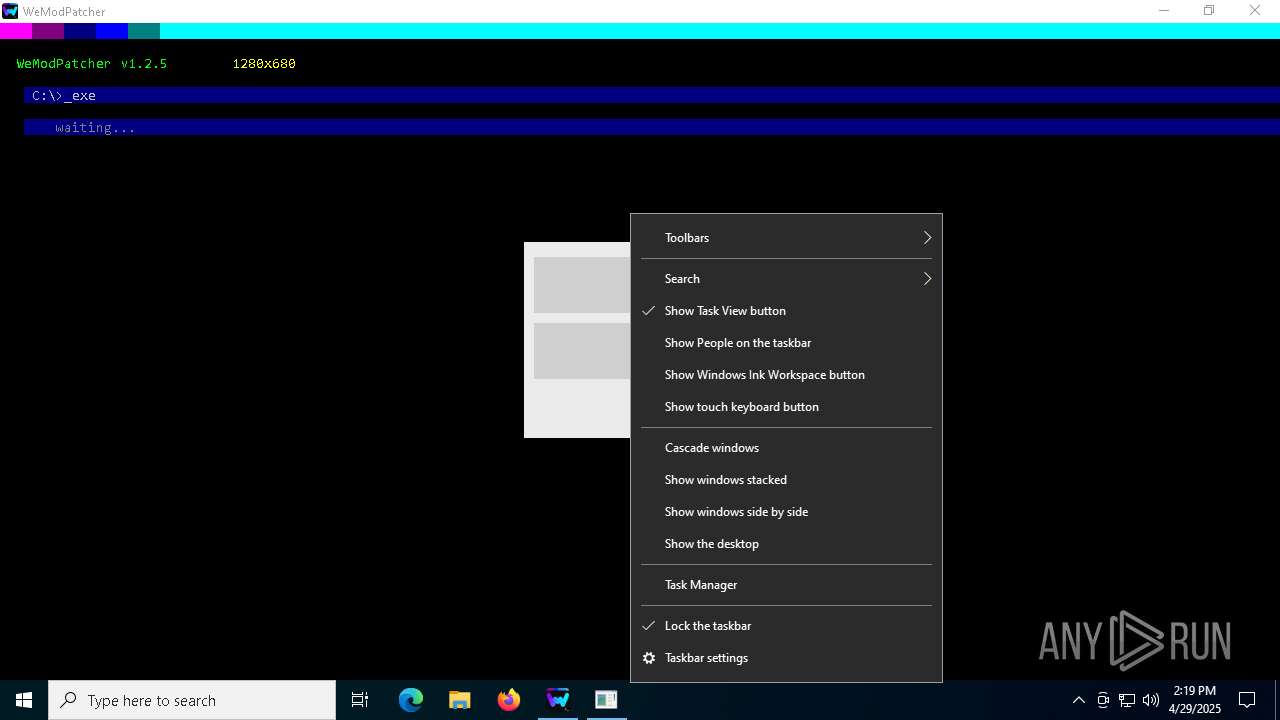
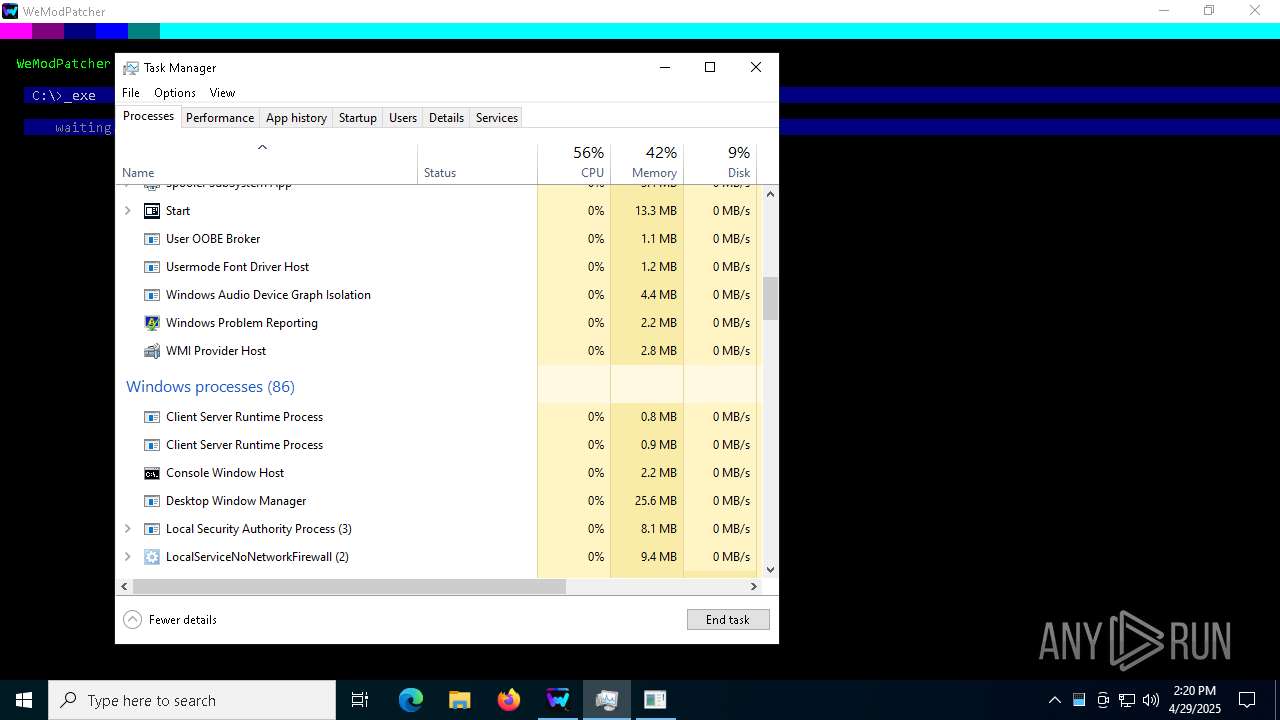
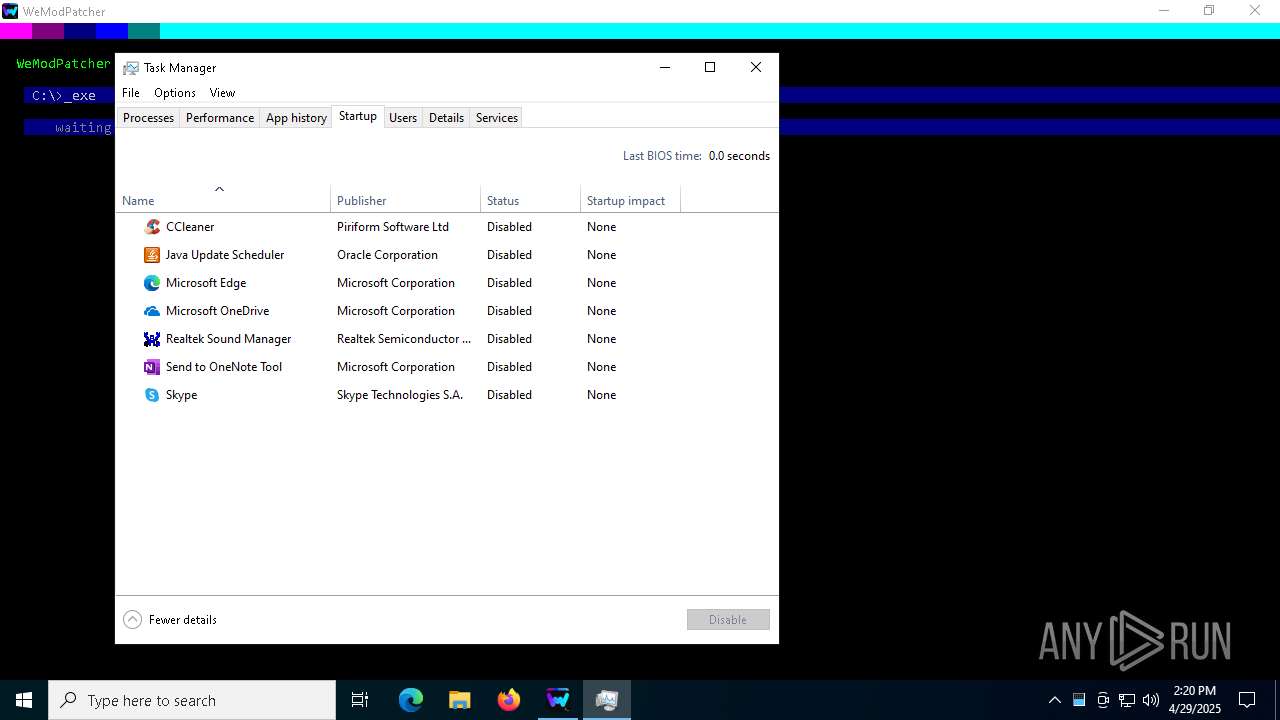
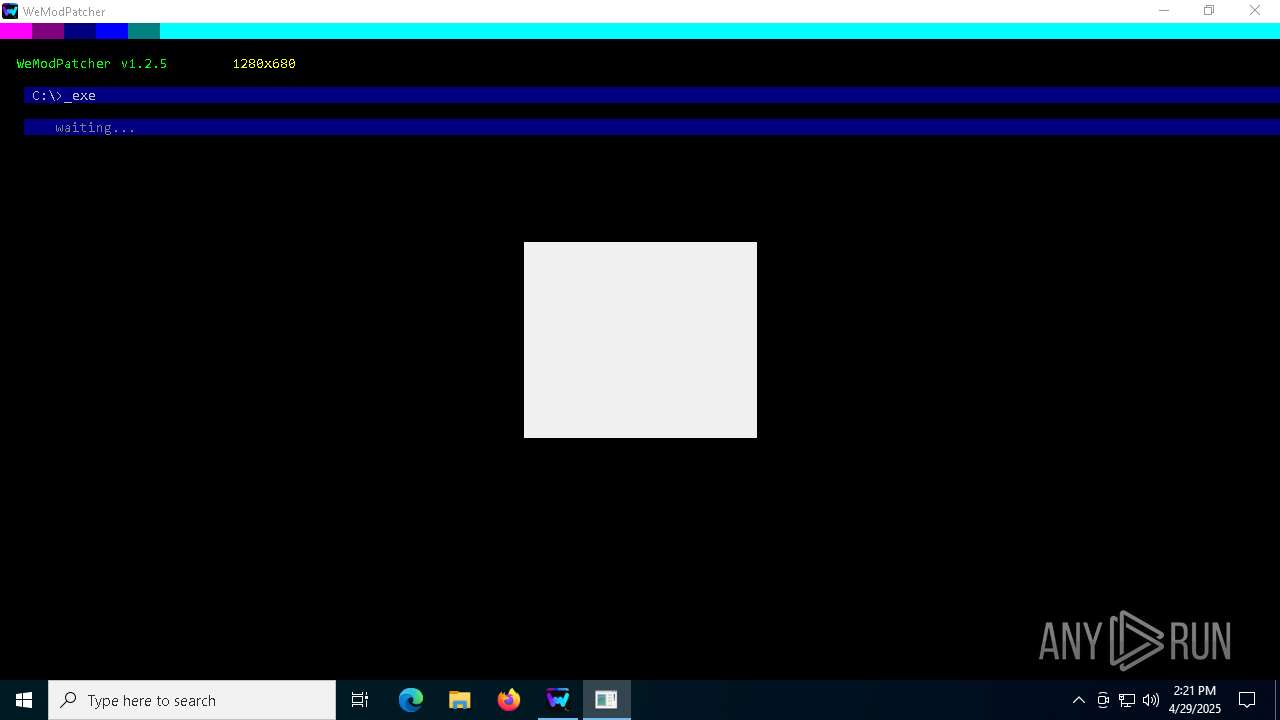
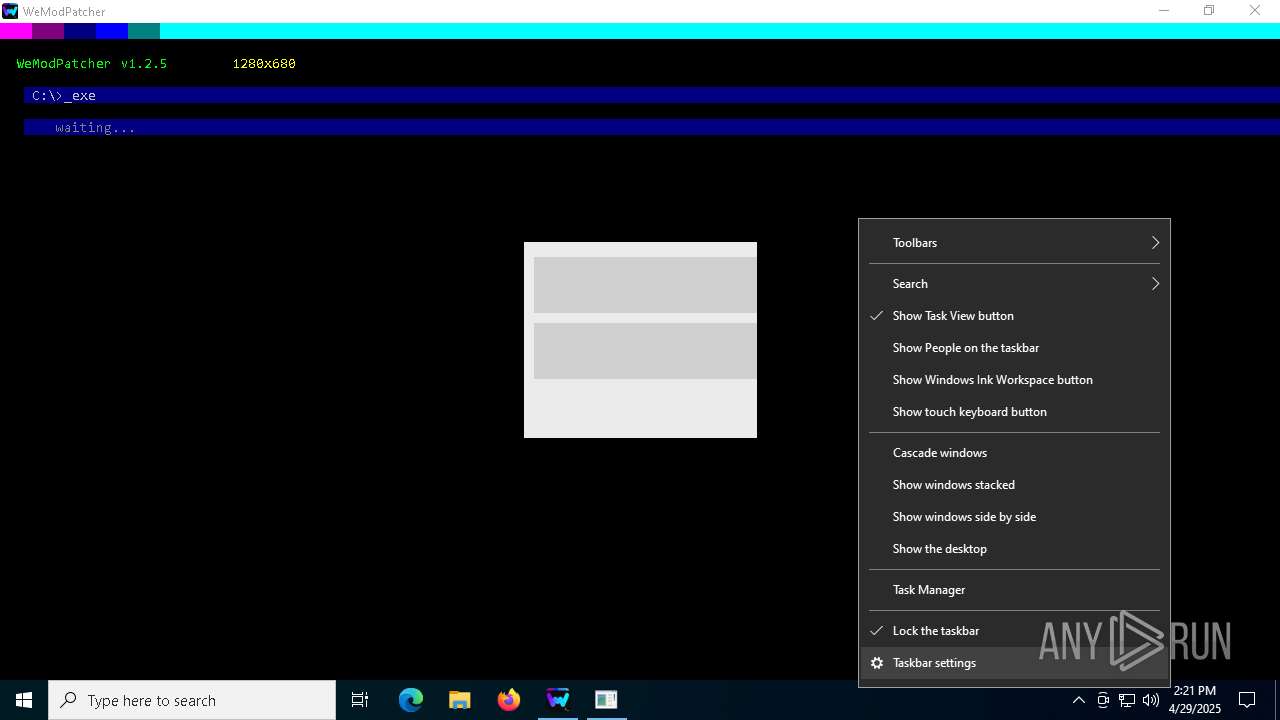
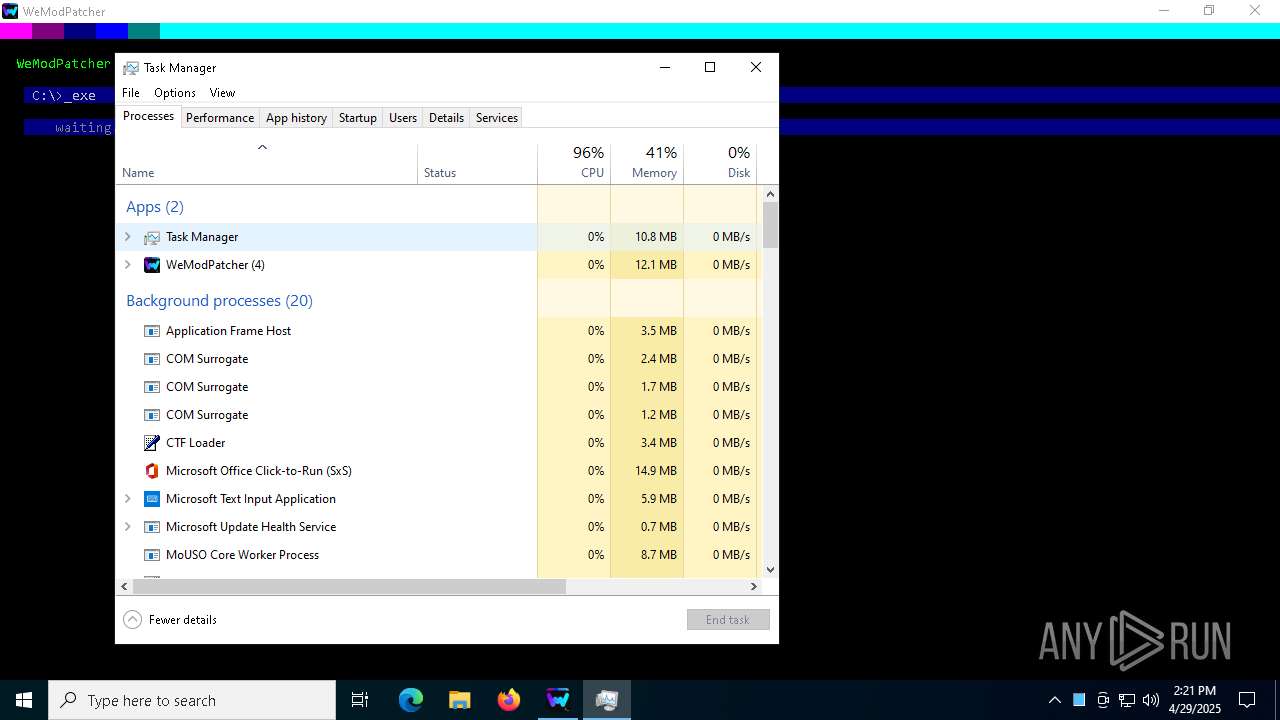
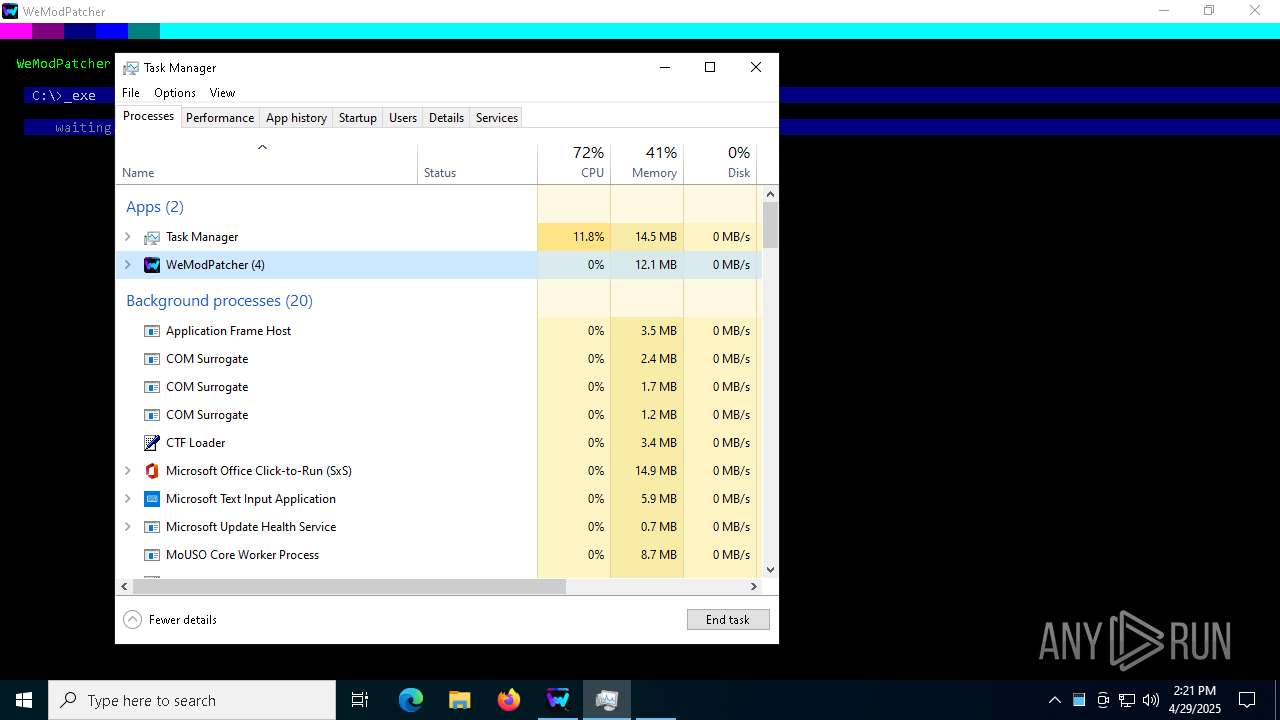
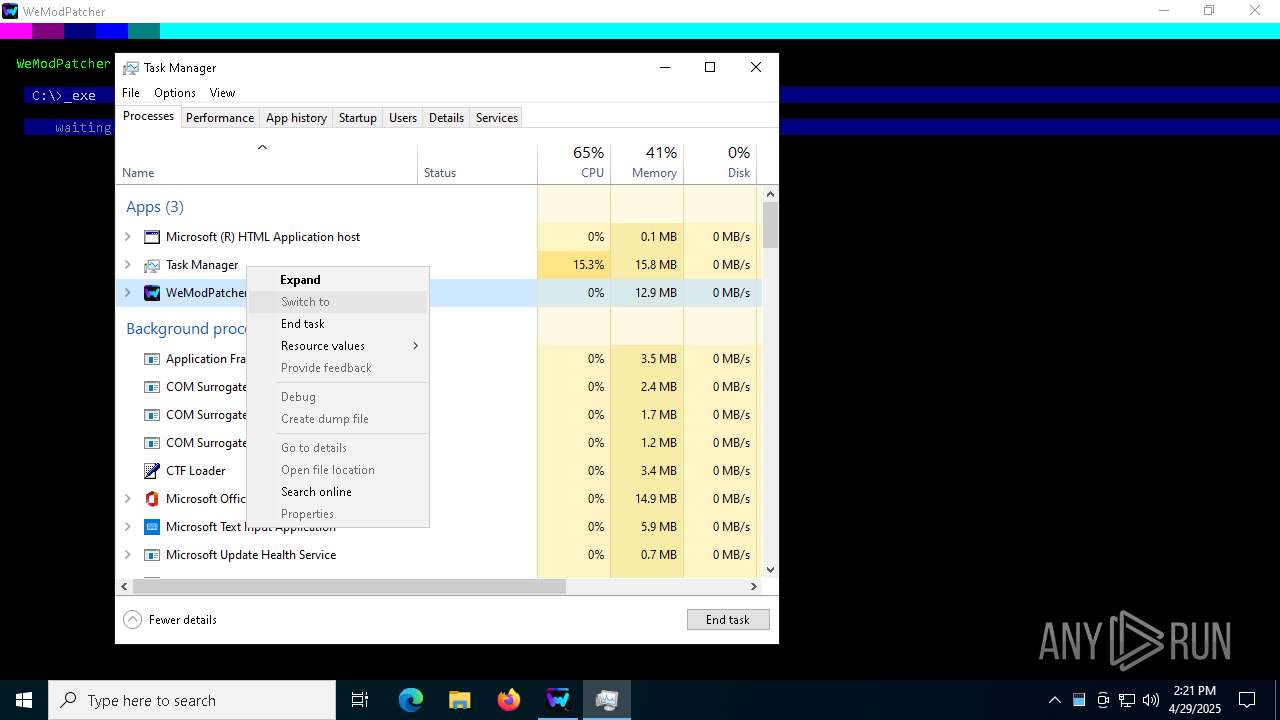
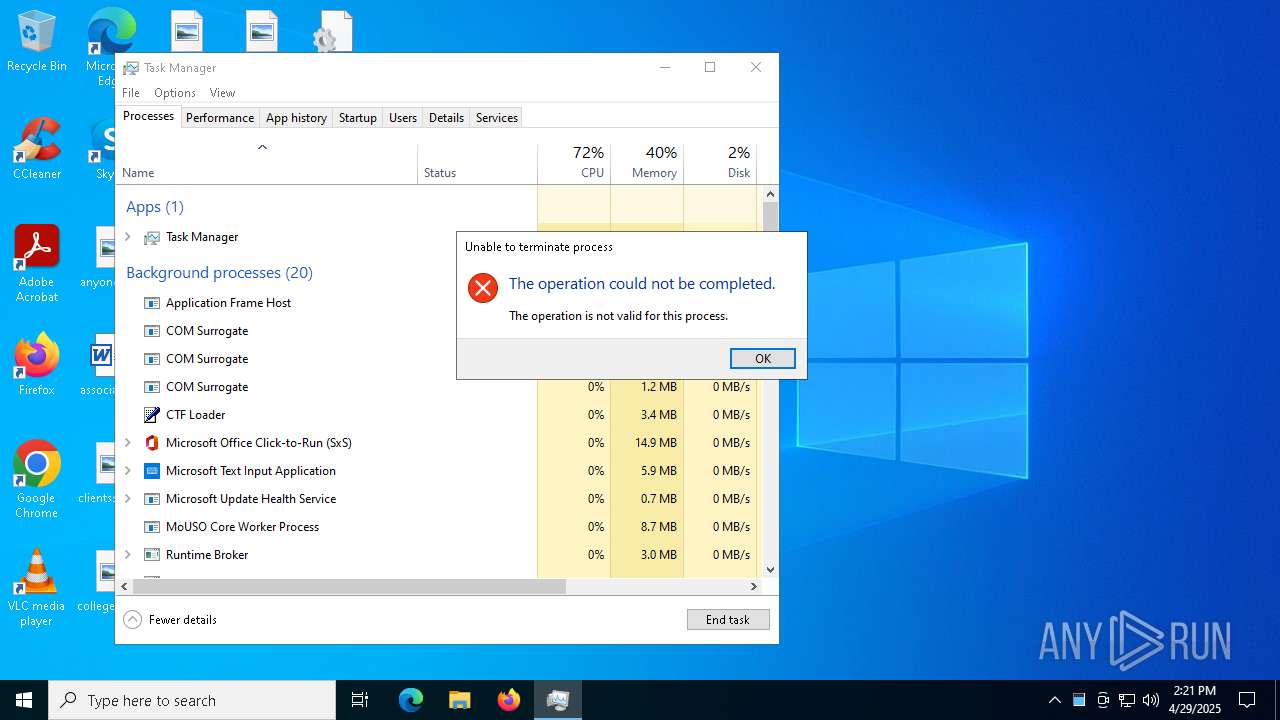
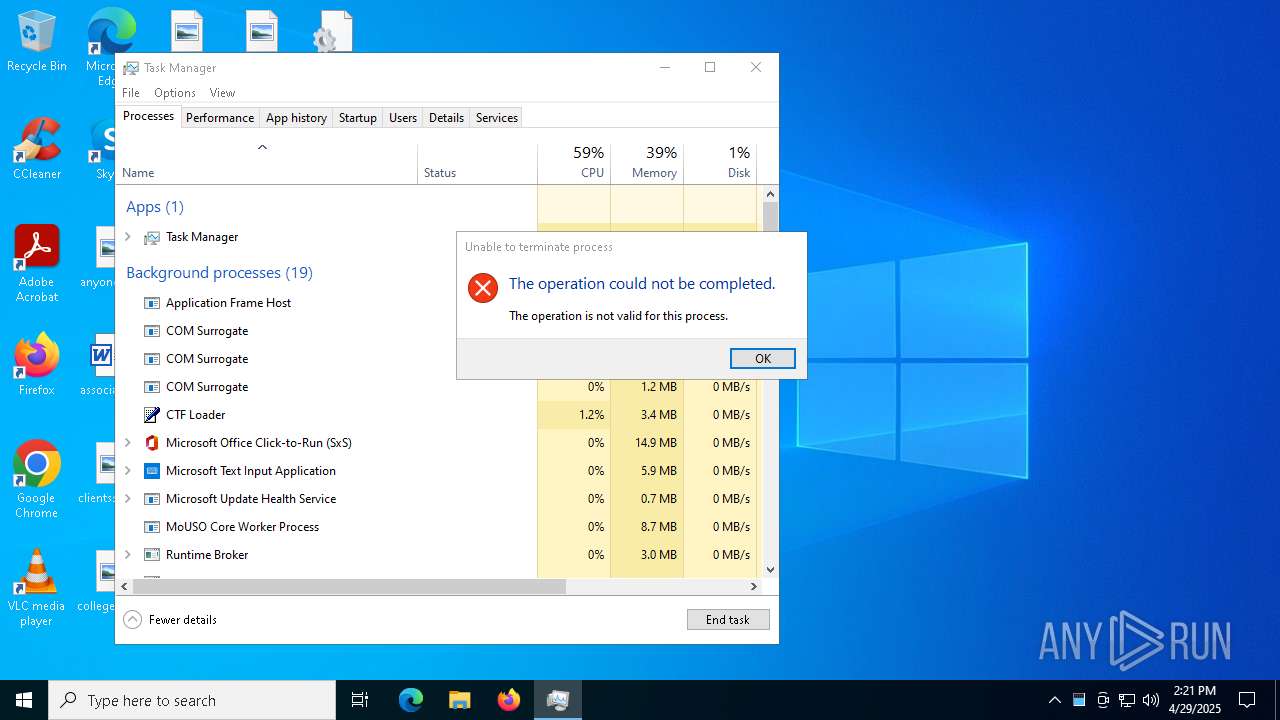
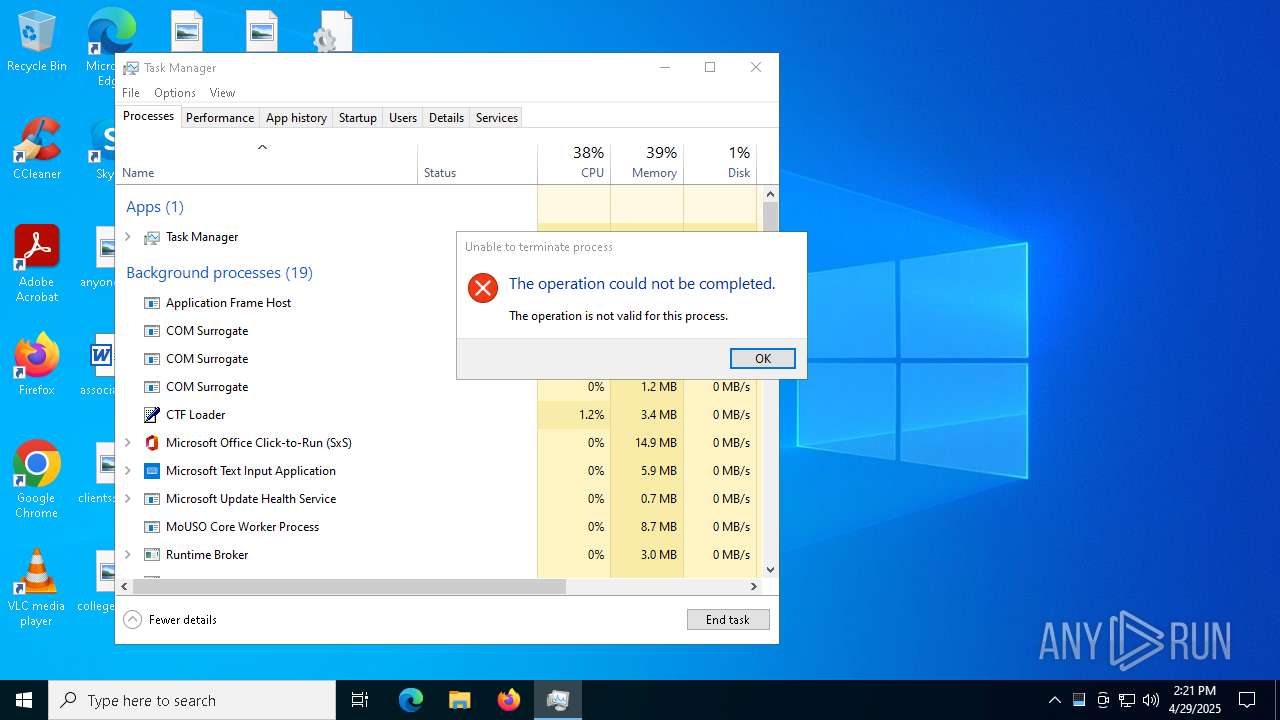
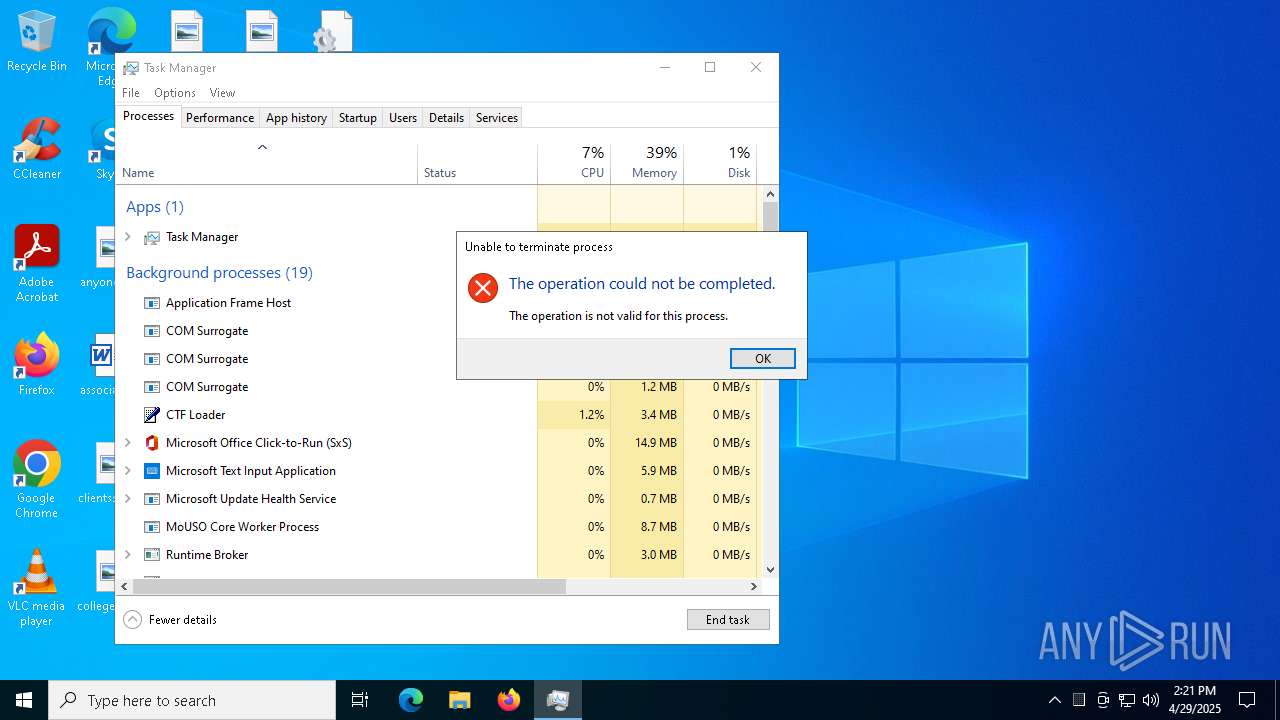
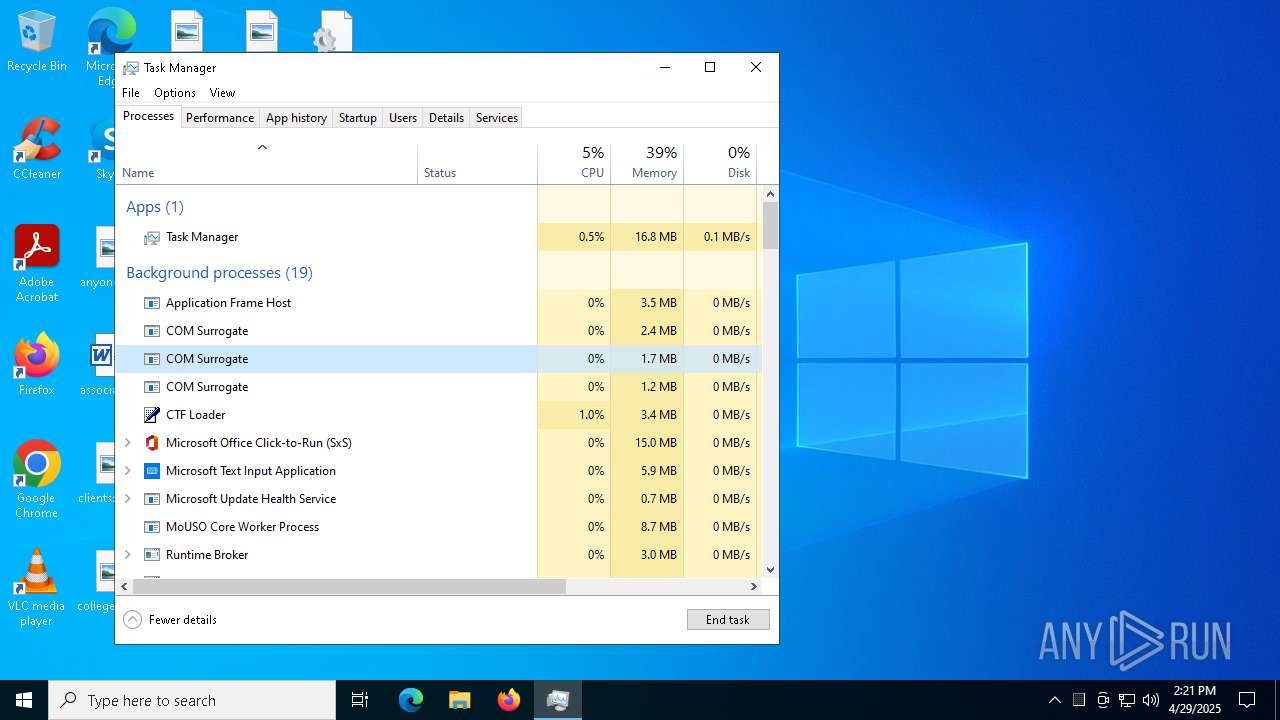
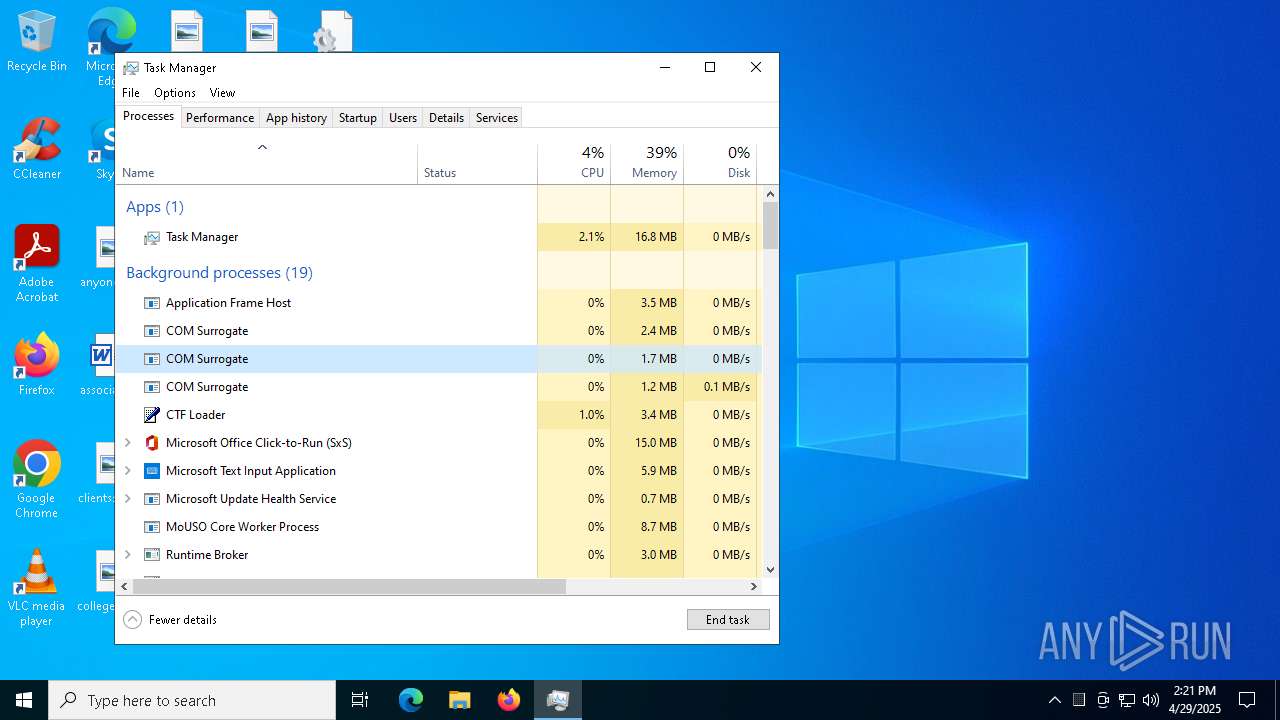
Manual execution by a user
- WeModPatcher.exe (PID: 7676)
- WinRAR.exe (PID: 7944)
- mshta.exe (PID: 4428)
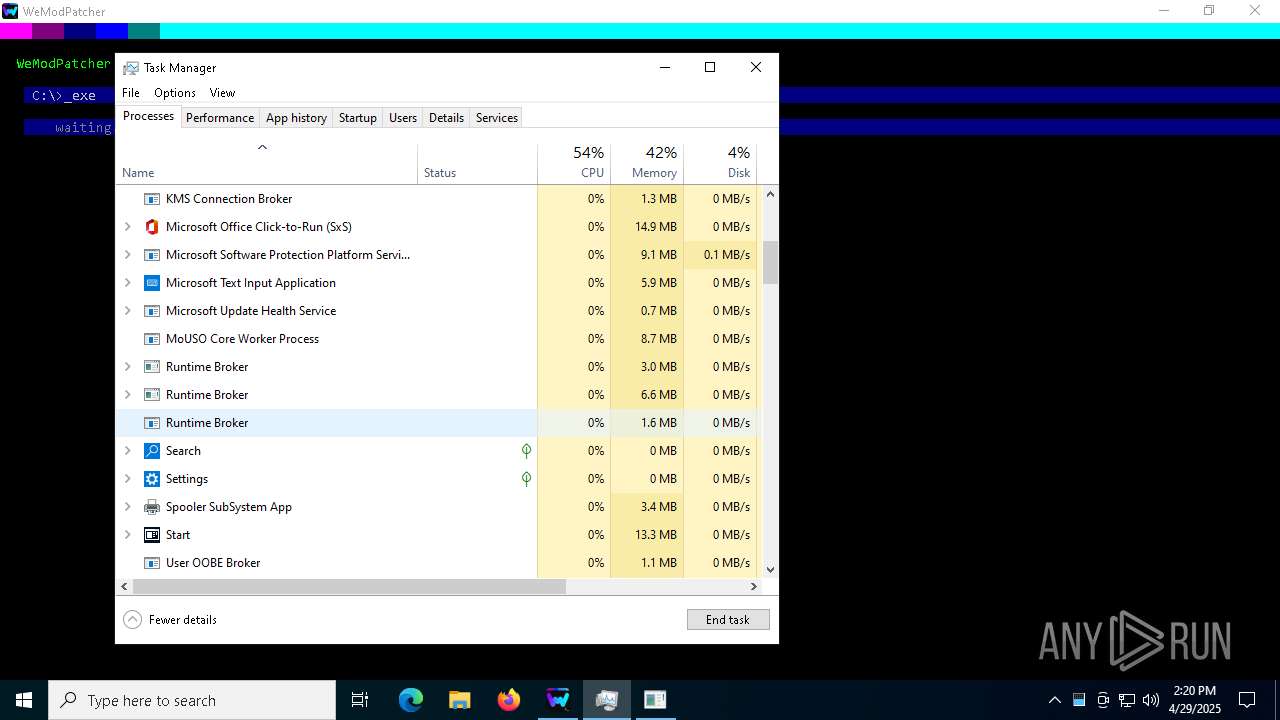
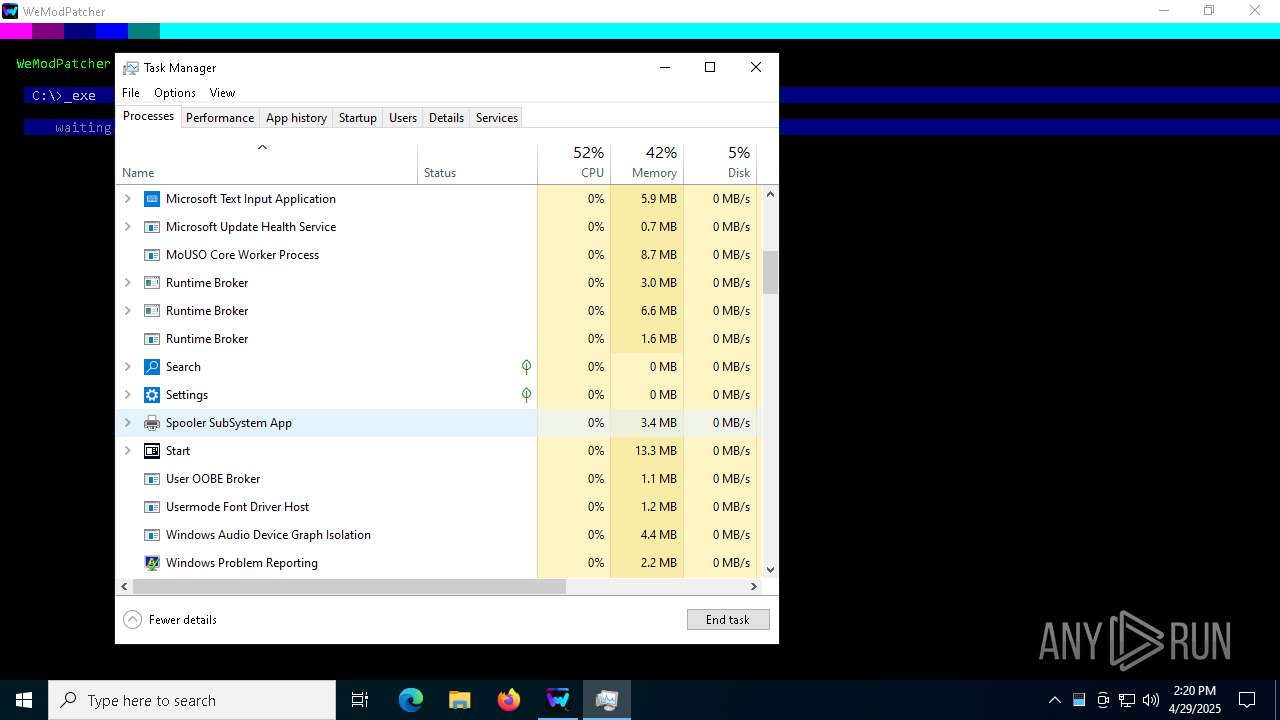
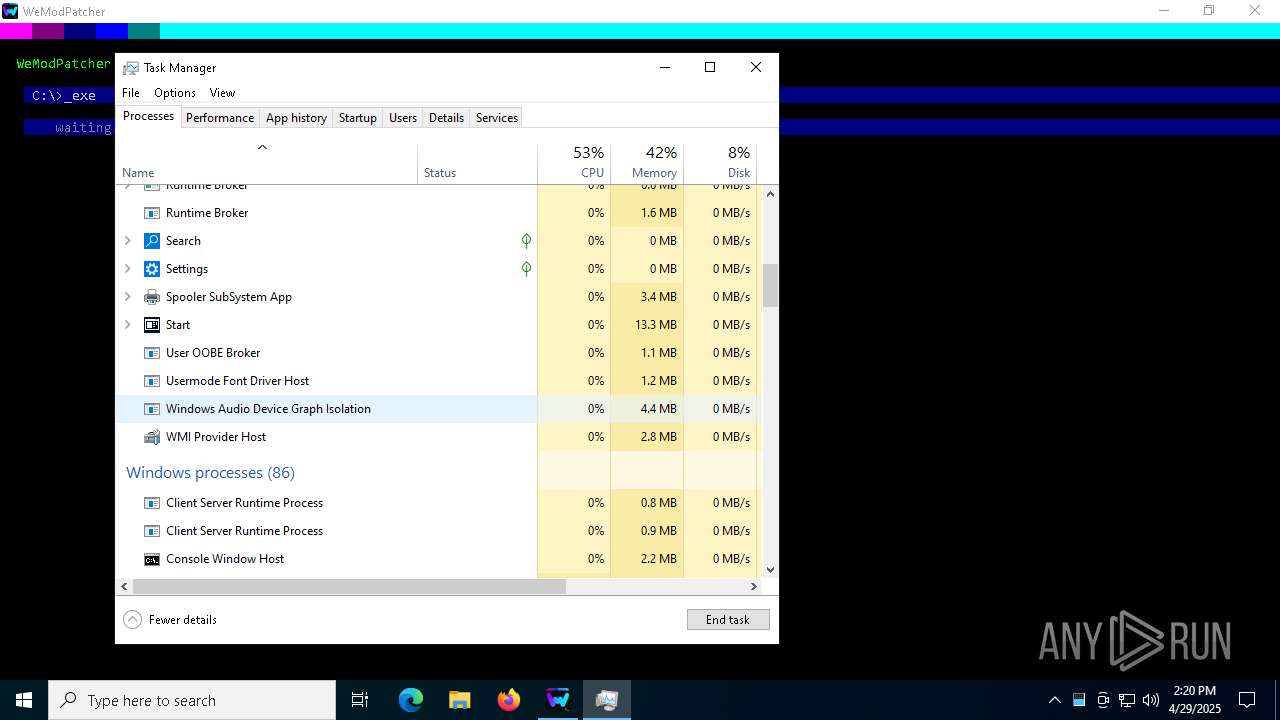
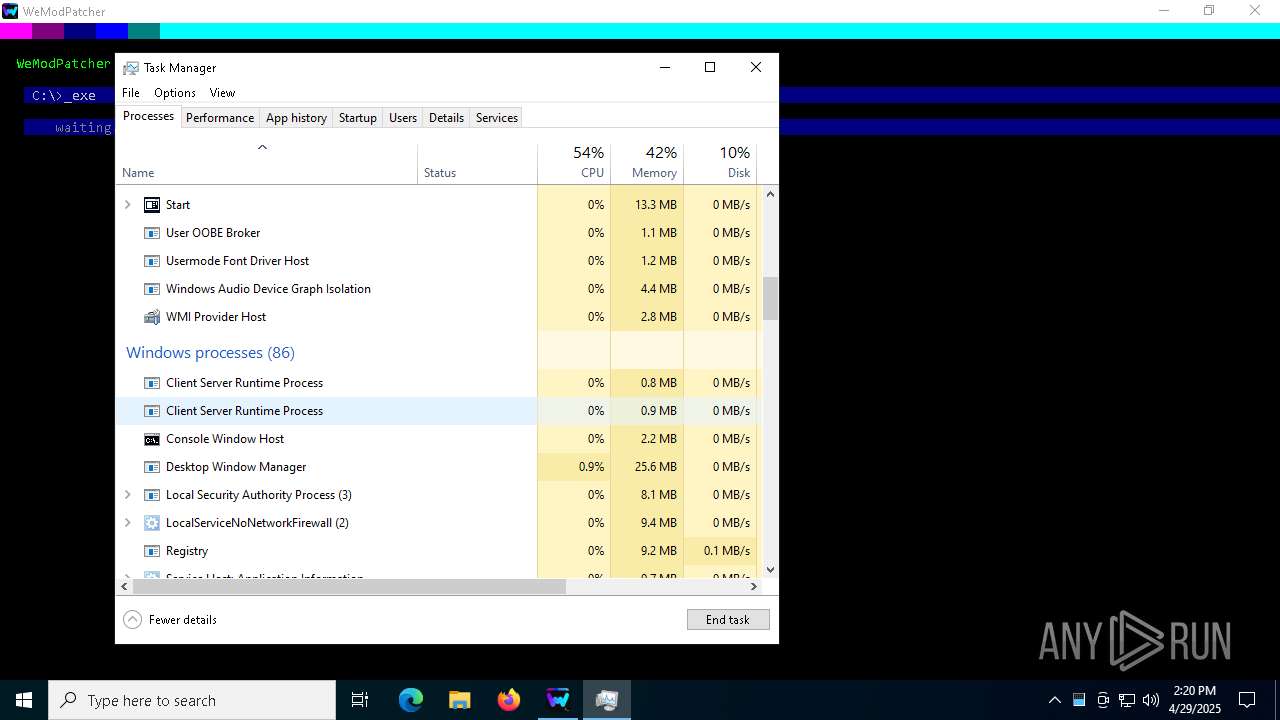
- Taskmgr.exe (PID: 7212)
- Taskmgr.exe (PID: 5436)
- Taskmgr.exe (PID: 6972)
- Taskmgr.exe (PID: 668)
- WeModPatcher.exe (PID: 4996)
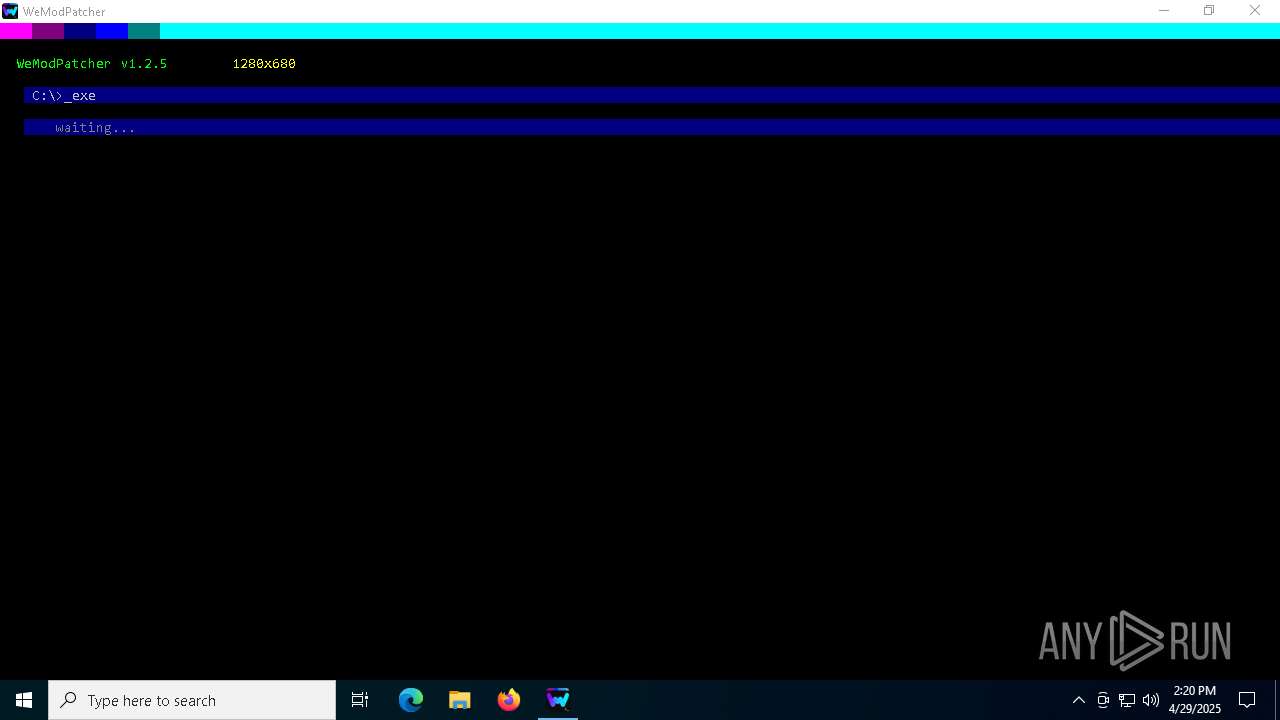
Changes the display of characters in the console
- cmd.exe (PID: 4756)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 896)
- cmd.exe (PID: 7436)
Starts MODE.COM to configure console settings
- mode.com (PID: 7360)
- mode.com (PID: 7464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:07:30 08:52:08+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 92672 |
| InitializedDataSize: | 1956352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.2.4.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
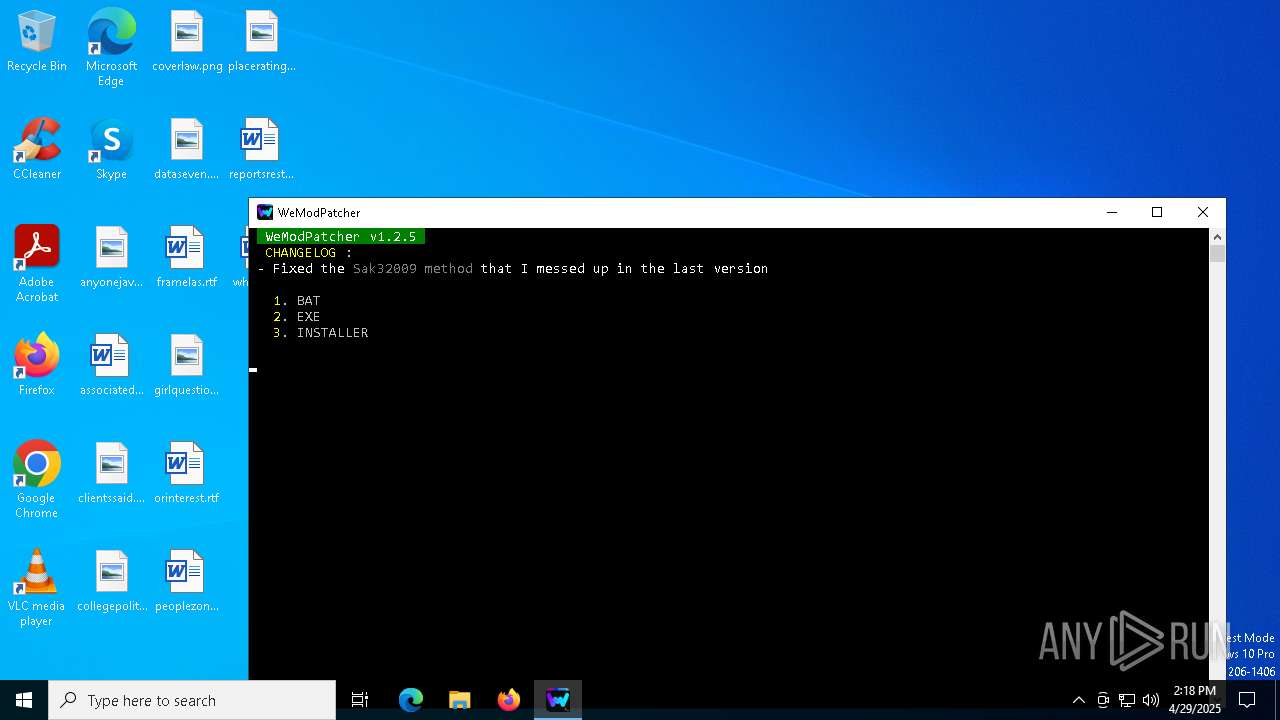
| FileVersion: | 1.2.4.0 |
| ProductVersion: | 1.2.4 |
| ProductName: | WeModPatcher |
| OriginalFileName: | WeModPatcher.bat |
| FileDescription: | WeModPatcher |
| LegalCopyright: | brunolee® |
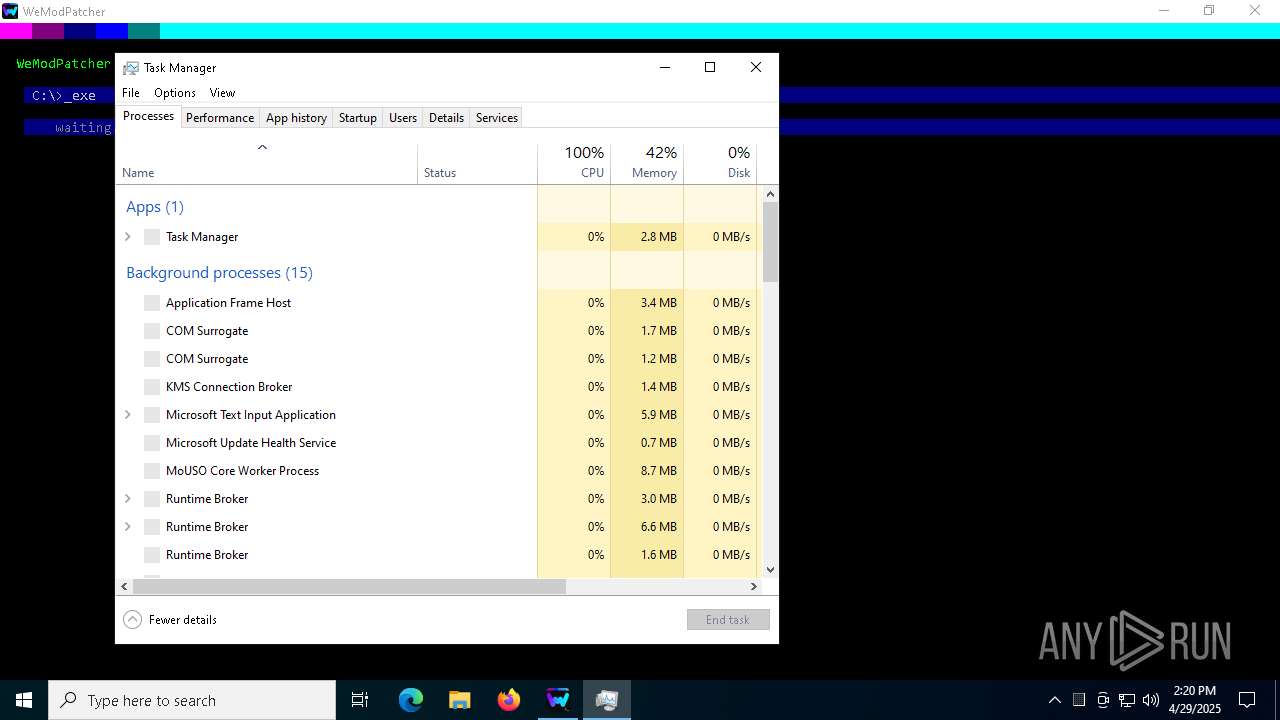
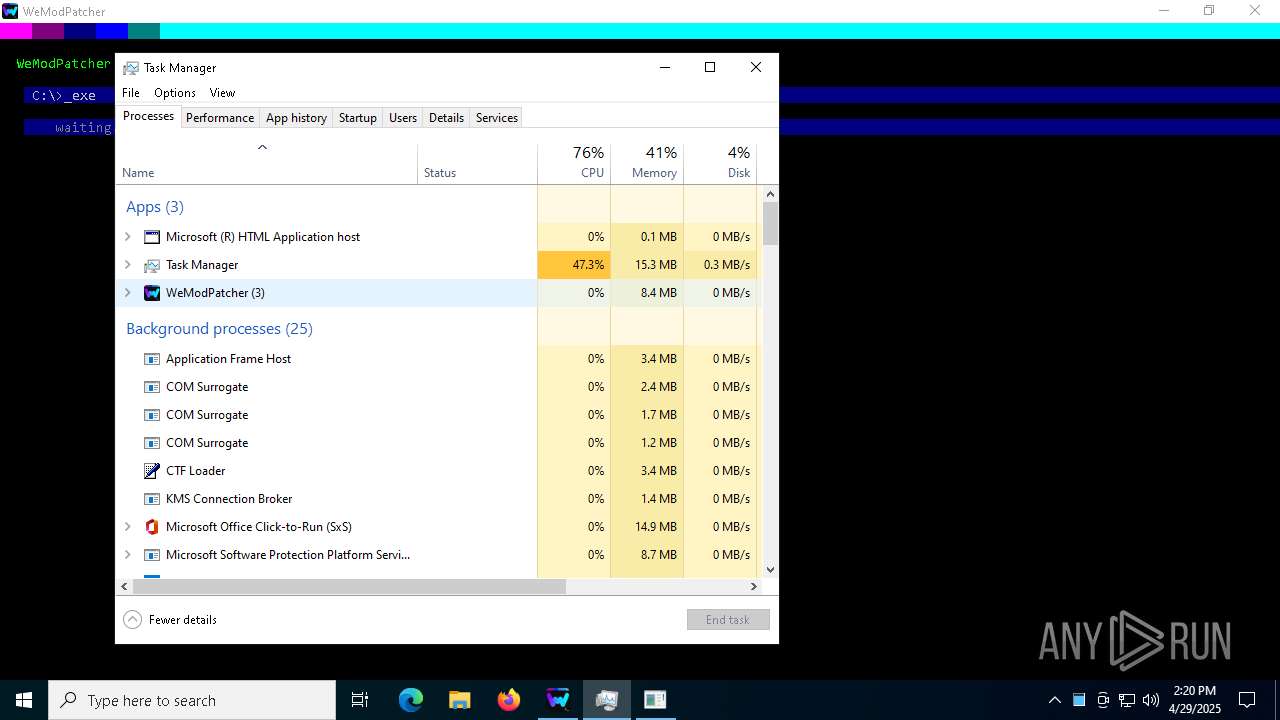
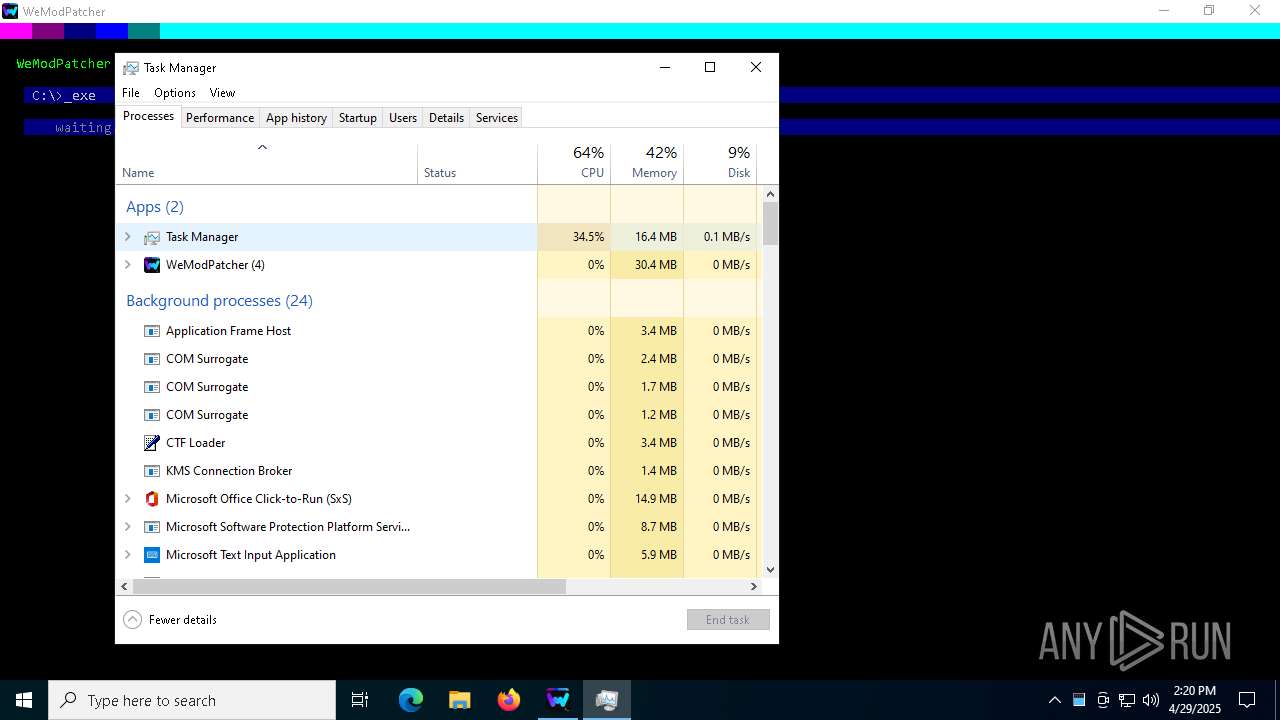
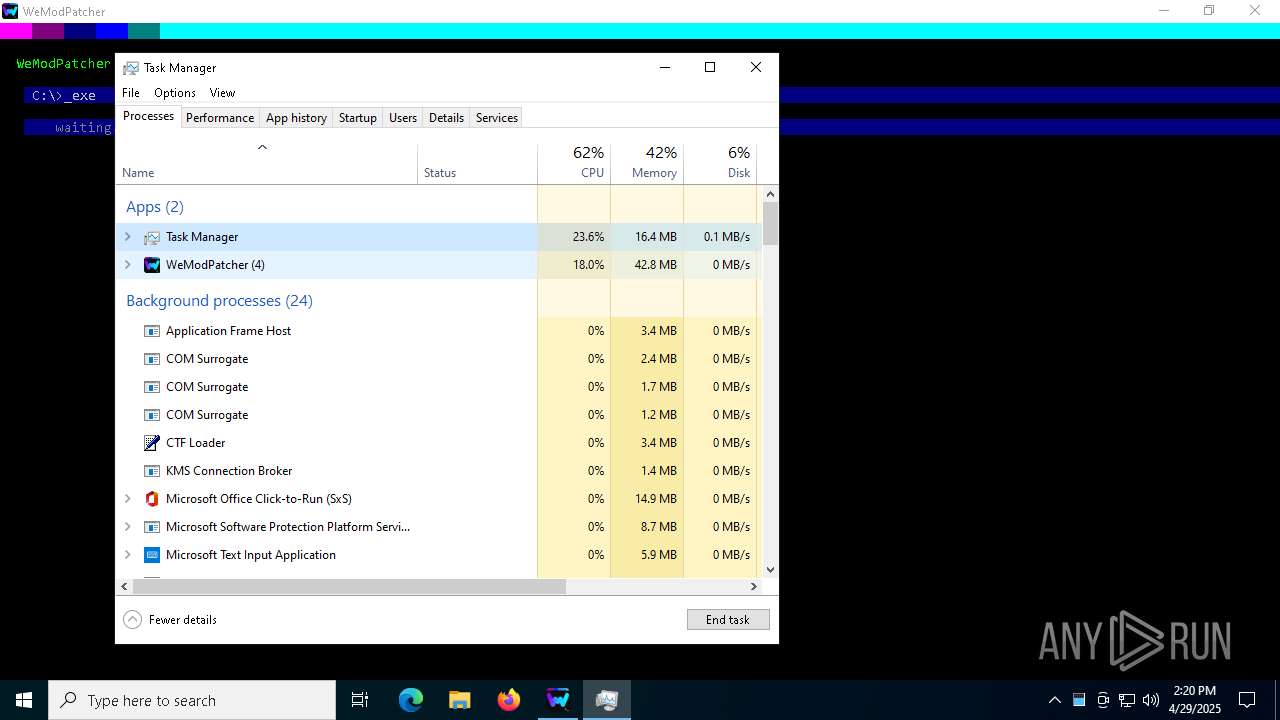
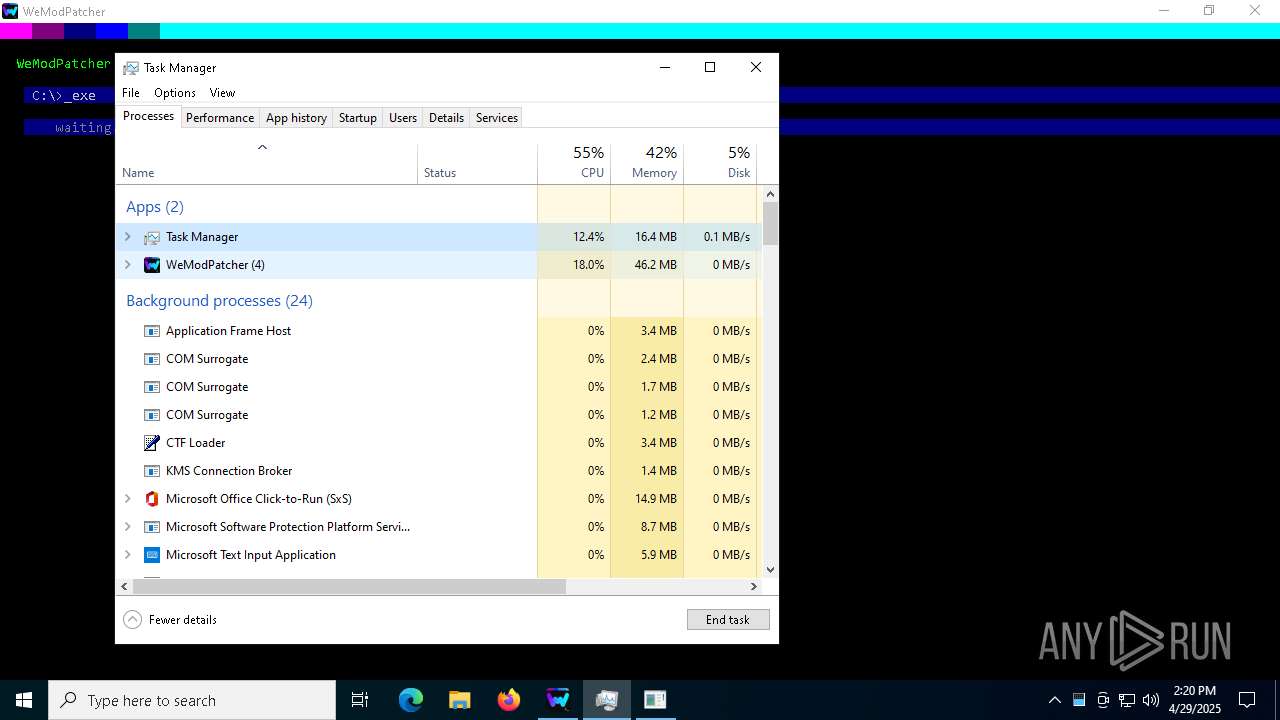
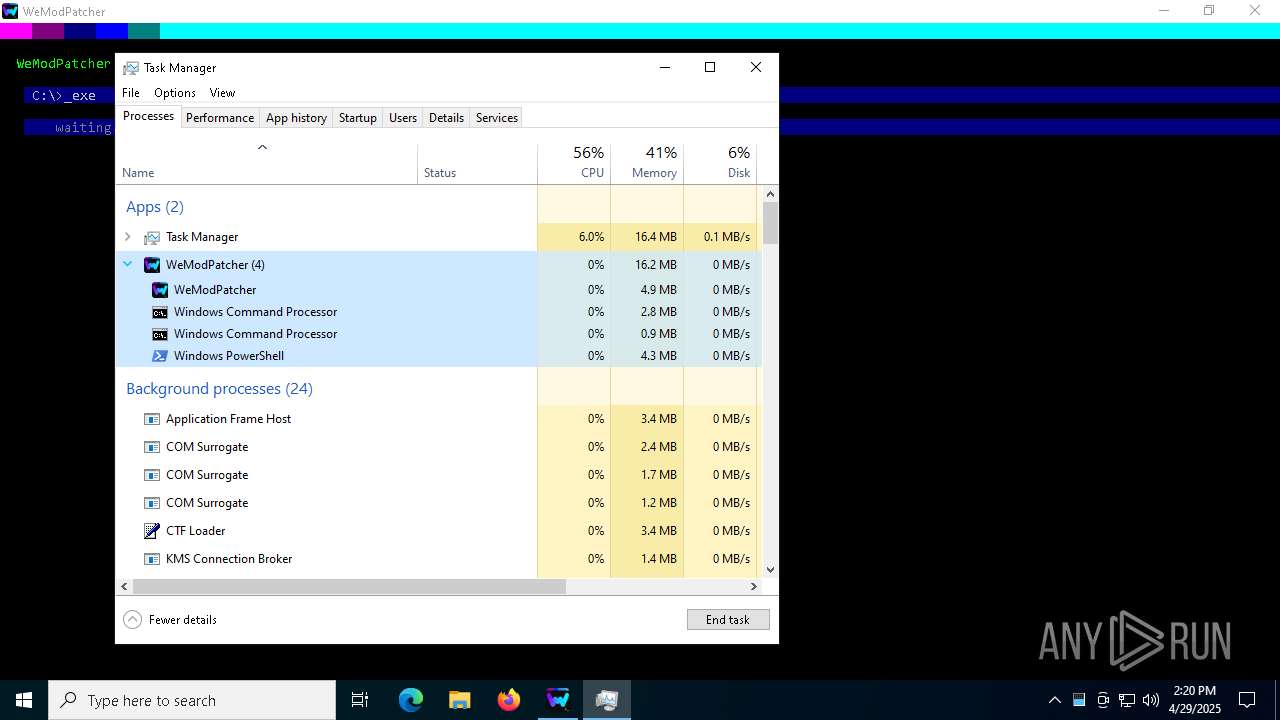
Total processes
566
Monitored processes
383
Malicious processes
6
Suspicious processes
51
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-Culture).DisplayName" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | reg query "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\Personalize" /V "AppsUseLightTheme" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "[Console]::CursorTop" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | chcp 850 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | C:\WINDOWS\system32\cmd.exe /c mshta.exe "C:\Users\admin\Desktop\Launcher.hta" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | C:\WINDOWS\system32\WerFault.exe -u -p 7480 -s 1904 | C:\Windows\System32\WerFault.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | powershell -Command "Add-Type -AssemblyName System.Windows.Forms;([System.Windows.Forms.Screen]::AllScreens).WorkingArea.Width" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
442 885
Read events
442 788
Write events
92
Delete events
5
Modification events
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0400000005000000060000000100000008000000020000000C0000000B0000000A00000009000000070000000000000003000000FFFFFFFF | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\4\0\0\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0000000004000000030000000200000001000000FFFFFFFF | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: AEDF106800000000 | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\39\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Modules\NavPane |
| Operation: | write | Name: | ExpandedState |
Value: 12000000160014001F80CB859F6720028040B29B5540CC05AAB60000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF00000000000000000000160014001F60983FFBB4EAC18D42A78AD1F5659CBA930000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF00000000000000000000160014001F7840F05F6481501B109F0800AA002F954E0000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000160014001F706806EE260AA0D7449371BEB064C986830000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF00000000000000000000160014001F580D1A2CF021BE504388B07367FC96EF3C0000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000160014001F5425481E03947BC34DB131E946B44C8DD50000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000160014001F50E04FD020EA3A6910A2D808002B30309D0000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF000000000000000000003C003A001F44471A0359723FA74489C55595FE6B30EE260001002600EFBE1000000034E9025AA9B7D80155EC262BAAB7D8018F3827B5B0B7D80114000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF000000000000000000003C003A001F42665C8D01334507439B53224DE2ED1FE6260001002600EFBE11000000A1C1E0E0AF27D301F77F6305B0B7D8019F22F307B0B7D80114000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000940092003200000080004658D1892000474F4F474C457E312E5A49500000760009000400EFBE4658D1894658D1892E000000F55D05000000090000000000000000000000000000001F47700047006F006F0067006C0065004300680072006F006D00650045006E0074006500720070007200690073006500420075006E0064006C006500360034002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B0000000000000000000000000000005C005A00320099030000F2588C582000657874312E7A69700000420009000400EFBEF2588C58F2588C582E000000A70D00000000160000000000000000000000000000003A91F90065007800740031002E007A0069007000000018000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B00000000000000000000000000000050004E00310000000000F258CE5810006578743100003A0009000400EFBEF258CE58F258CE582E000000DE0200000000170000000000000000000000000000001CB7E9006500780074003100000014000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF000000000000000000006E006C0032001EEC0500F258826620005052454645527E312E5A49500000500009000400EFBEF2588266F25882662E00000028D4000000001900000000000000000000000000000005A1250050007200650066006500720065006E006300650073002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B0000000000000000000000000000005800560032007E0D0000F258866620006578742E7A697000400009000400EFBEF2588666F25886662E0000002AD4000000001E0000000000000000000000000000005498DF006500780074002E007A0069007000000016000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B00000000000000000000000000000062006000310000000000F2588D6610005052454645527E310000480009000400EFBEF2588D66F2588F662E0000002E2F0100000017000000000000000000000000000000CF57130150007200650066006500720065006E00630065007300000018000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B0000000000000000000000000000004C004A00310000000000F2589066100065787400380009000400EFBEF2589066F25890662E000000E88D0100000007000000000000000000000000000000DE8B4100650078007400000012000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000780076003200C1862C03F258957920004F4D4E495F327E312E5A495000005A0009000400EFBEF258E578F25895792E0000007C600500000039000000000000000000000000000000DE6FED006F006D006E0069005F00320033005F00310030005F0032003000320034005F002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B00000000000000000000000000000070006E0032007E0D0000F2587B7920004348524F4D497E312E5A49500000520009000400EFBEF2587B79F2587B792E000000C260050000001800000000000000000000000000000028F586006300680072006F006D00690075006D005F006500780074002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000 | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0E000000040000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (1244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
1
Suspicious files
116
Text files
230
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\Options.ini | text | |
MD5:83503A2A8B9F78CFFA4ED444885C4959 | SHA256:E217B87EA4F57FA0FBF70BED27EDA1DA7FF3A4D3B7A989BF15B1261E6735387A | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\B865.tmp\B895.tmp\B896.bat | binary | |
MD5:FE03422746B1F8CC51702DCB74C4E7DC | SHA256:EDBBD519A21D40092E9C4E72783127772134B491D5B9CA0244AABAC5F9CEE9C1 | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\lang\lang_tr.ini | text | |
MD5:BC7CBB4ADA04CE76B890600EADBBA4D7 | SHA256:A85BD038A89BE70A95278E4C06980E89254EAEA8D3F6DA667F35A84749F10215 | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\Options.hta | html | |
MD5:C0826786D1B58B03C4C134865CD0A0A6 | SHA256:E4CDEA4433591103E4C416165B9B7EEBFF79C30B011EEE839064C0621FE0B209 | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\lang\lang_de.ini | text | |
MD5:56F718D833D85B64D368A746CEC7D311 | SHA256:9296A56AE3F33183E5DD78159EEDC14E7C55D58B6FF984D30480927F3491A0A6 | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\lang\lang_es.ini | text | |
MD5:EFE851D125CBF4EA90D87CF1F469E331 | SHA256:5D75679F3A5CD60EA5700C5F83AF9411D404B1A6077EB994D90597BDFE9855D9 | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\WeModPatcherTools | compressed | |
MD5:7D2DBEC2395D4CF262EAF10C9B944F4C | SHA256:43F2B4E8D63A62055E8A2CDF80C8809ED6A9FE1574141A9083CA998B65C7E082 | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\lang\lang_en.ini | text | |
MD5:DA7F78CEA561177B4593E43E472B8A61 | SHA256:5CE043FA53863E2FC94E42D72D870DA746D94CA5CDBC1E1F6FBD364681D69F26 | |||
| 7476 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\lang\lang_fr.ini | text | |
MD5:EA19B7BB4D40D45A8F8A7DD1AC50F71B | SHA256:1C7F187AED0221D27937884A433425D351AA85CEB907F2CBD59794F2437E5801 | |||
| 7656 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nunqgfra.i2i.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
37
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
756 | lsass.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
1628 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCrZoa1YnvoBZaCEzAShkn1 | unknown | — | — | whitelisted |
1628 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.216.77.36:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7588 | curl.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
756 | lsass.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
756 | lsass.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |