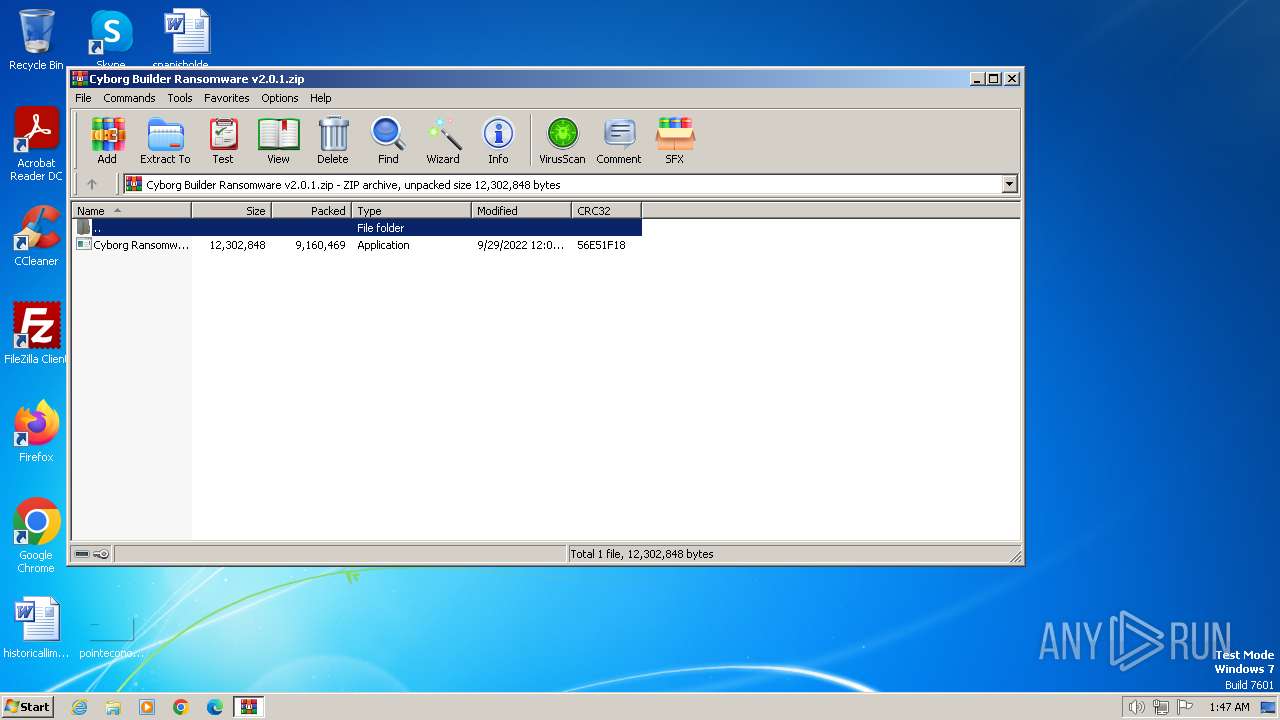
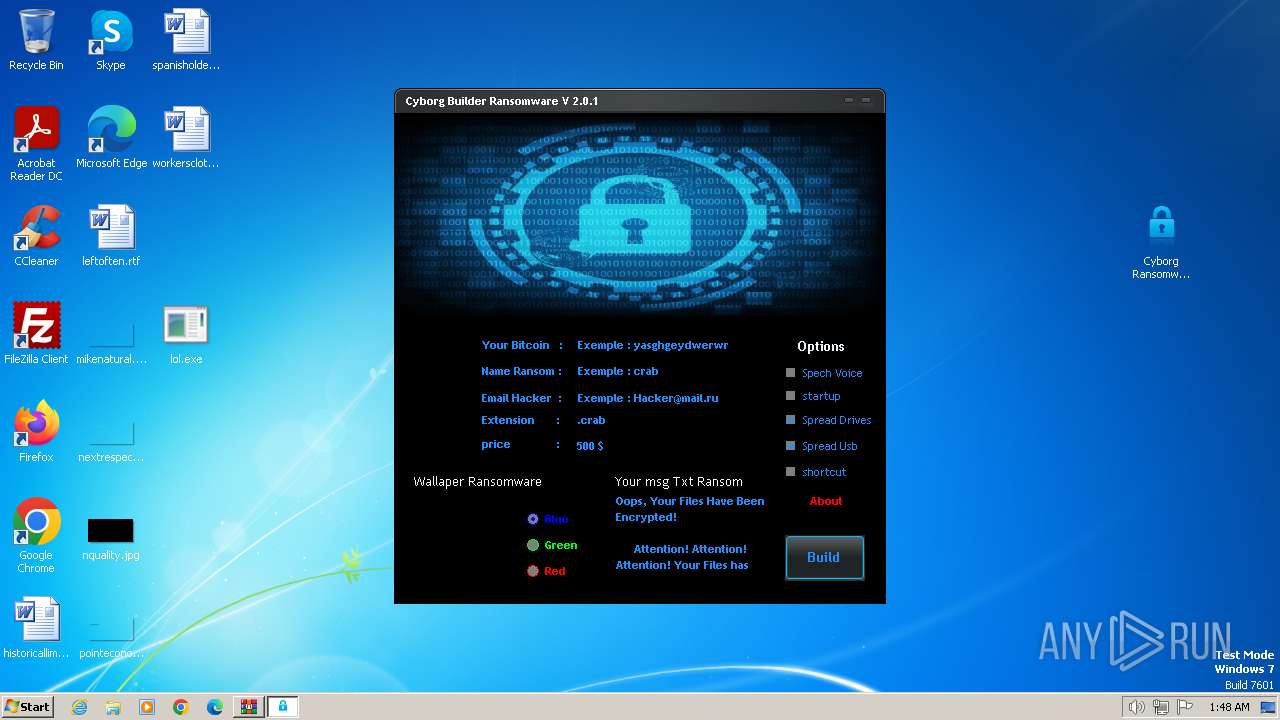
| File name: | Cyborg Builder Ransomware v2.0.1.zip |
| Full analysis: | https://app.any.run/tasks/a7d329ce-26ec-4ea8-9981-cc32632eac07 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 01:47:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 2976FA1365AA2507A60FE063CE9592D7 |
| SHA1: | E44E744944F42D735A091B692AA36DE66615902C |
| SHA256: | D06FD108F4F1CA2B928C33962A8BA5917A21E915F24BEE7E421CBFBF713FD5D8 |
| SSDEEP: | 98304:SVAKQ1PHaA1FvyaBjJ5iQQDj5f4qU7Mx4iwBDwXovVrzF1EBfmoX1cMw1gl4O3Au:+fl5i7Z+NuyW4m/4 |
MALICIOUS
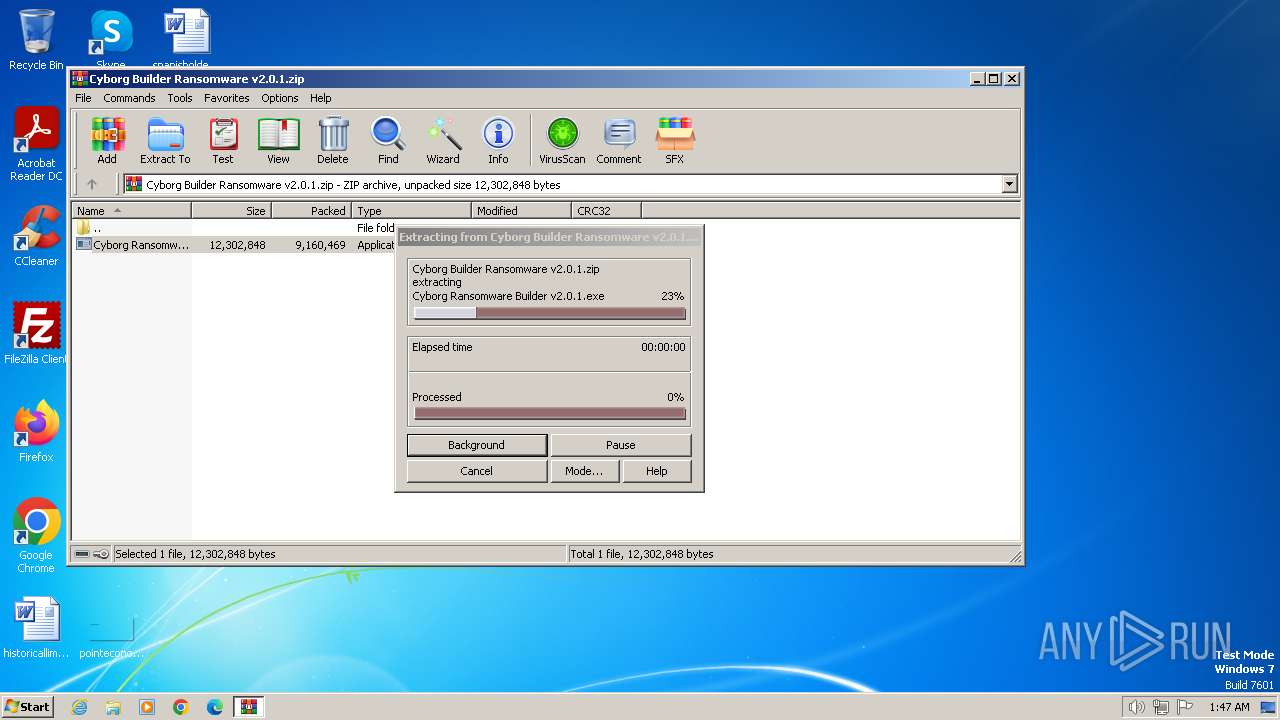
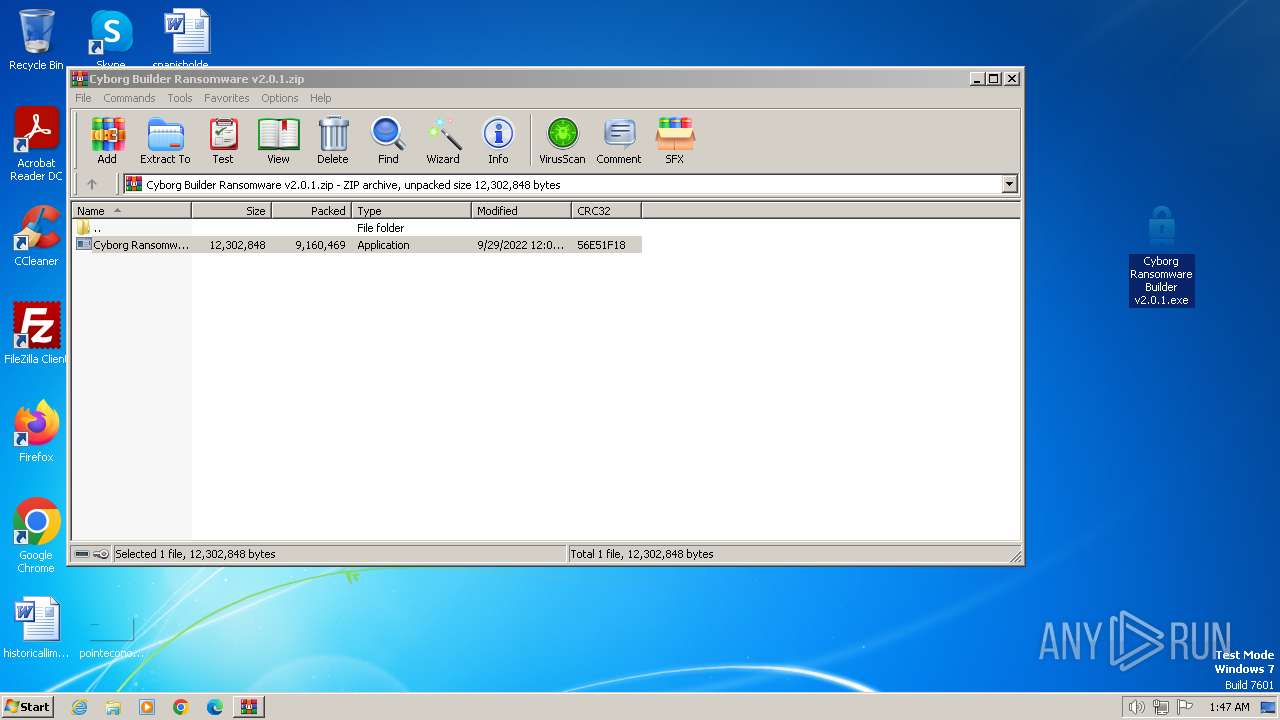
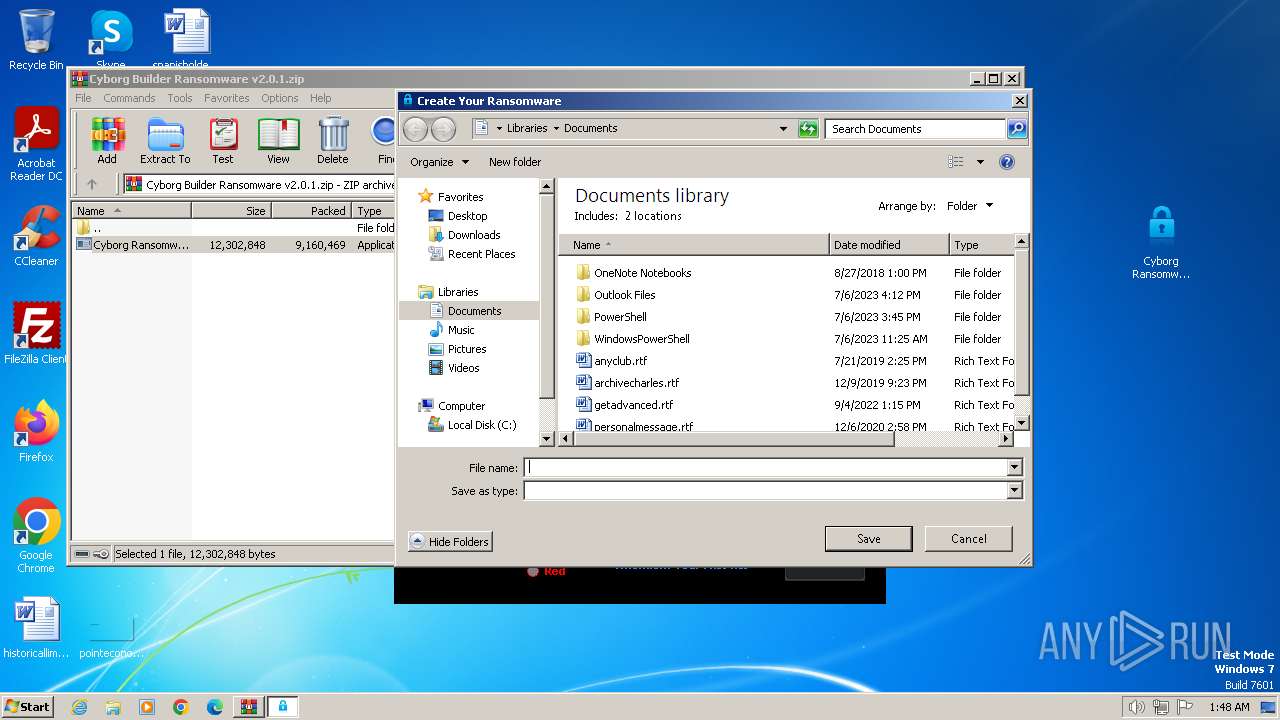
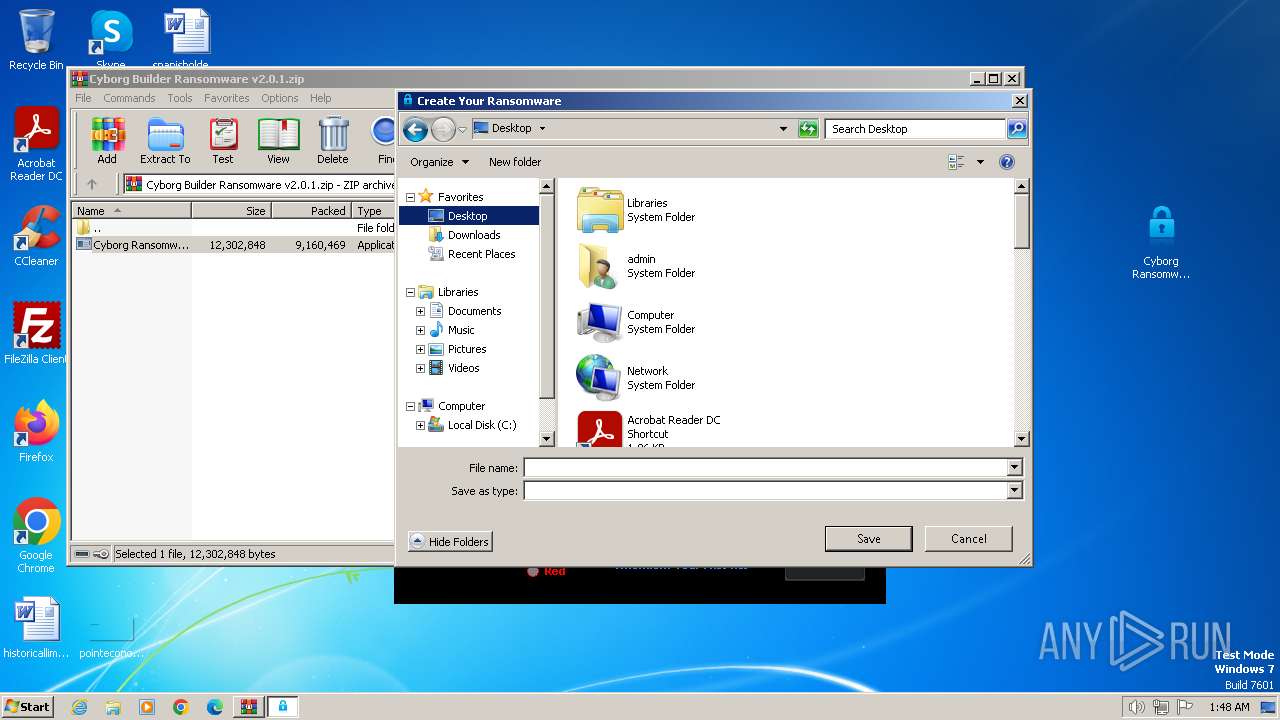
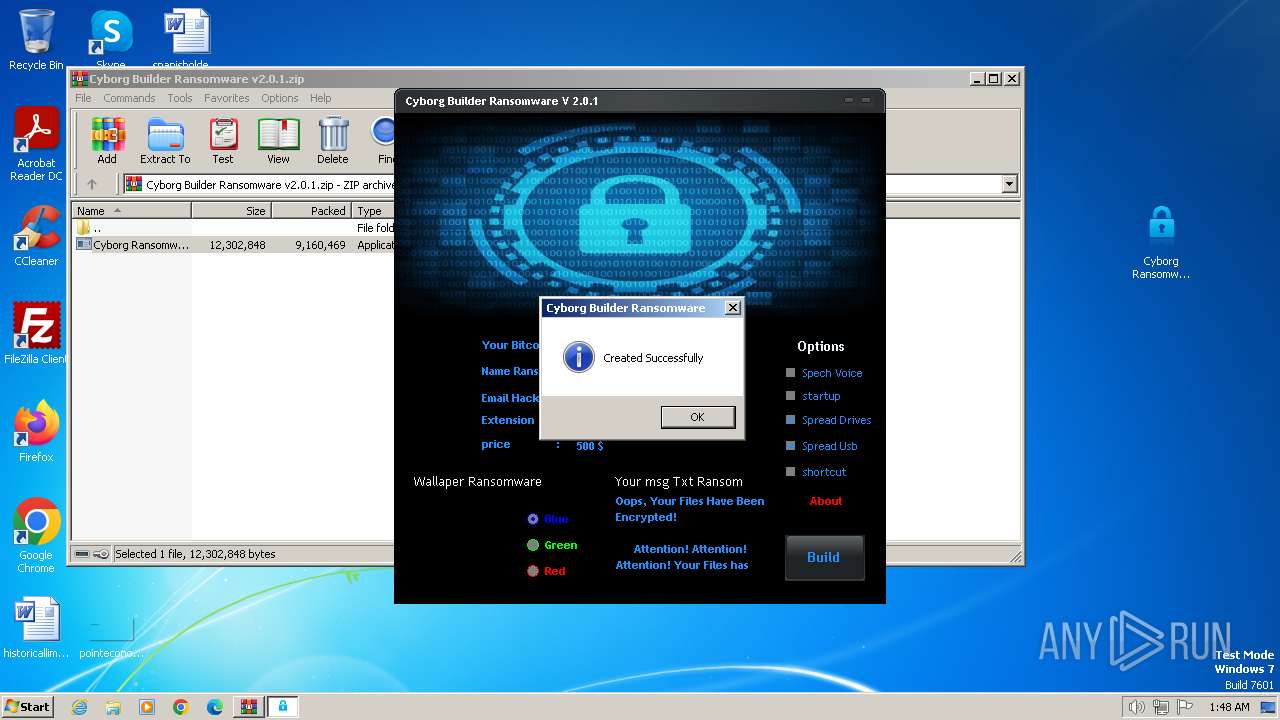
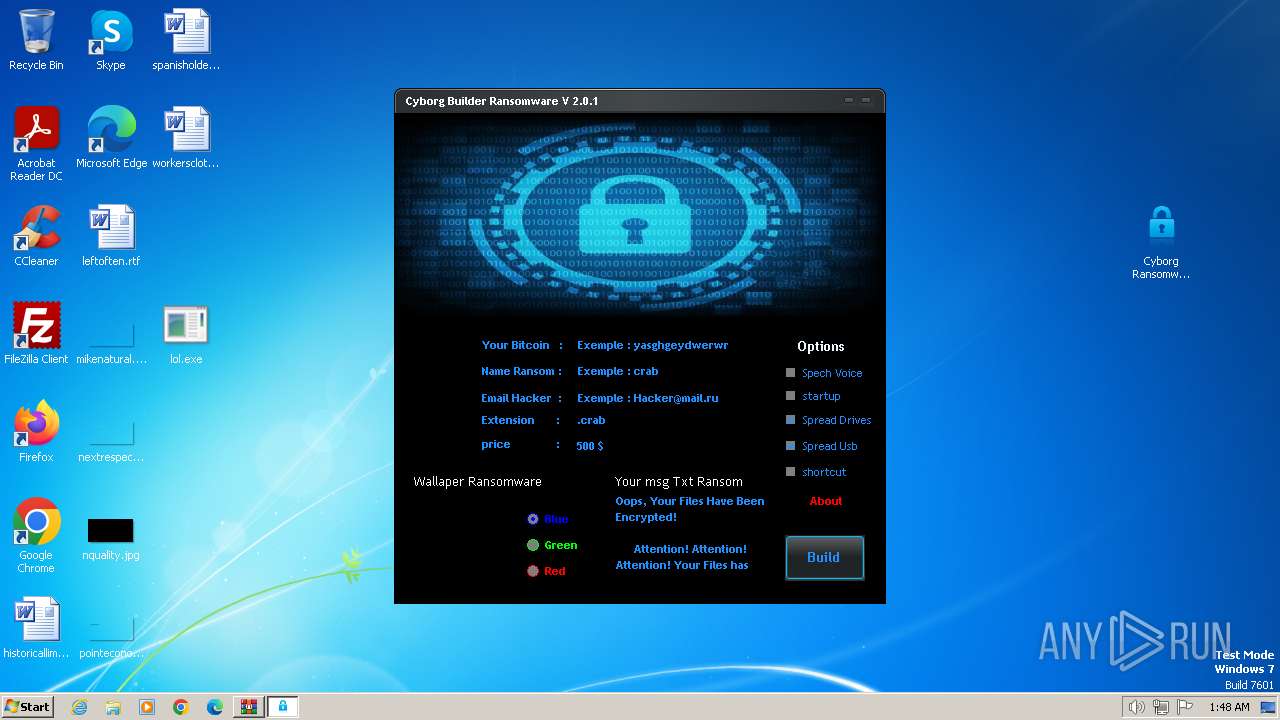
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4052)
- Cyborg Ransomware Builder v2.0.1.exe (PID: 3660)
- lol.exe (PID: 3772)
Renames files like ransomware
- lol.exe (PID: 3772)
SUSPICIOUS
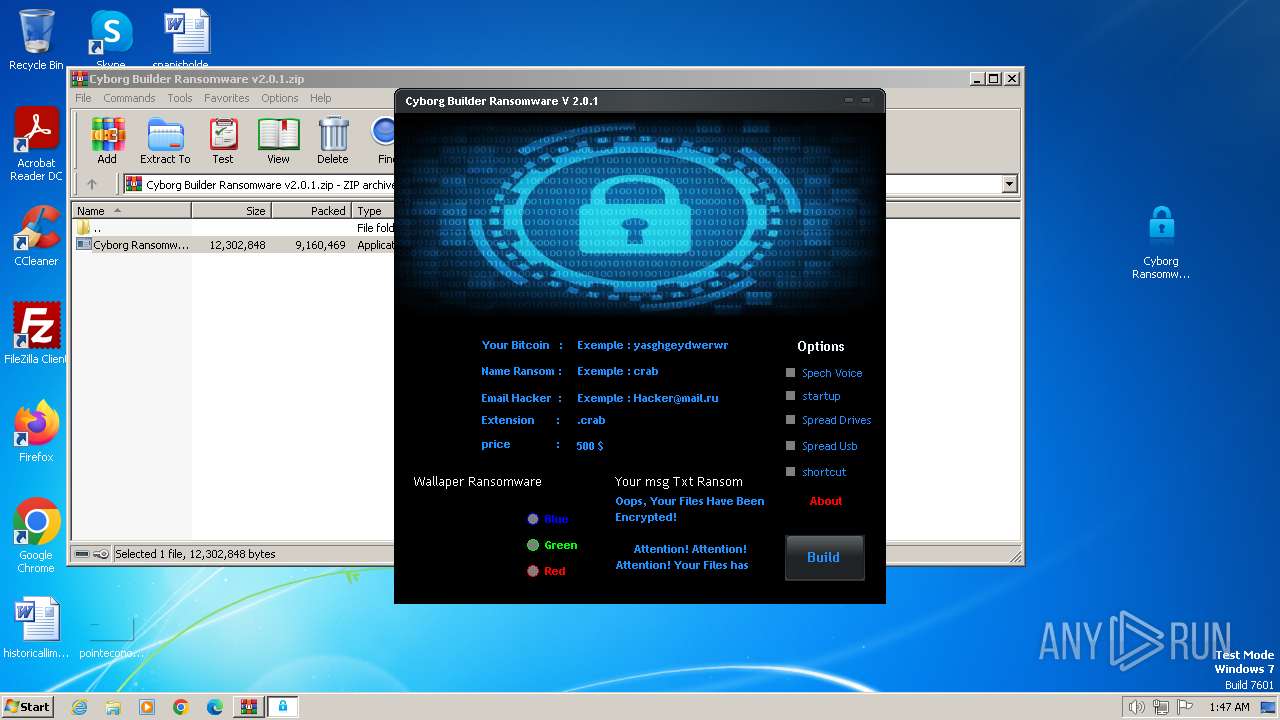
Reads the Internet Settings
- Cyborg Ransomware Builder v2.0.1.exe (PID: 3660)
Executable content was dropped or overwritten
- Cyborg Ransomware Builder v2.0.1.exe (PID: 3660)
- lol.exe (PID: 3772)
The process checks if it is being run in the virtual environment
- lol.exe (PID: 3772)
INFO
Reads the machine GUID from the registry
- Cyborg Ransomware Builder v2.0.1.exe (PID: 3660)
- lol.exe (PID: 3772)
Checks supported languages
- Cyborg Ransomware Builder v2.0.1.exe (PID: 3660)
- lol.exe (PID: 3772)
Reads the computer name
- Cyborg Ransomware Builder v2.0.1.exe (PID: 3660)
- lol.exe (PID: 3772)
Manual execution by a user
- Cyborg Ransomware Builder v2.0.1.exe (PID: 3660)
- lol.exe (PID: 3772)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4052)
Creates files or folders in the user directory
- lol.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2022:09:29 18:08:32 |
| ZipCRC: | 0x56e51f18 |
| ZipCompressedSize: | 9160469 |
| ZipUncompressedSize: | 12302848 |
| ZipFileName: | Cyborg Ransomware Builder v2.0.1.exe |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3660 | "C:\Users\admin\Desktop\Cyborg Ransomware Builder v2.0.1.exe" | C:\Users\admin\Desktop\Cyborg Ransomware Builder v2.0.1.exe | explorer.exe | ||||||||||||
User: admin Company: Cyber SpLiTTer Integrity Level: MEDIUM Description: Cyborg Ransomware V 2.0.1 Exit code: 0 Version: 2.0.0.1 Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\Desktop\lol.exe" | C:\Users\admin\Desktop\lol.exe | explorer.exe | ||||||||||||
User: admin Company: Host Process for Windows Services Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 2.0.0.1 Modules
| |||||||||||||||
| 4052 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Cyborg Builder Ransomware v2.0.1.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
9 088
Read events
9 012
Write events
72
Delete events
4
Modification events
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Cyborg Builder Ransomware v2.0.1.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
4
Suspicious files
0
Text files
1
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
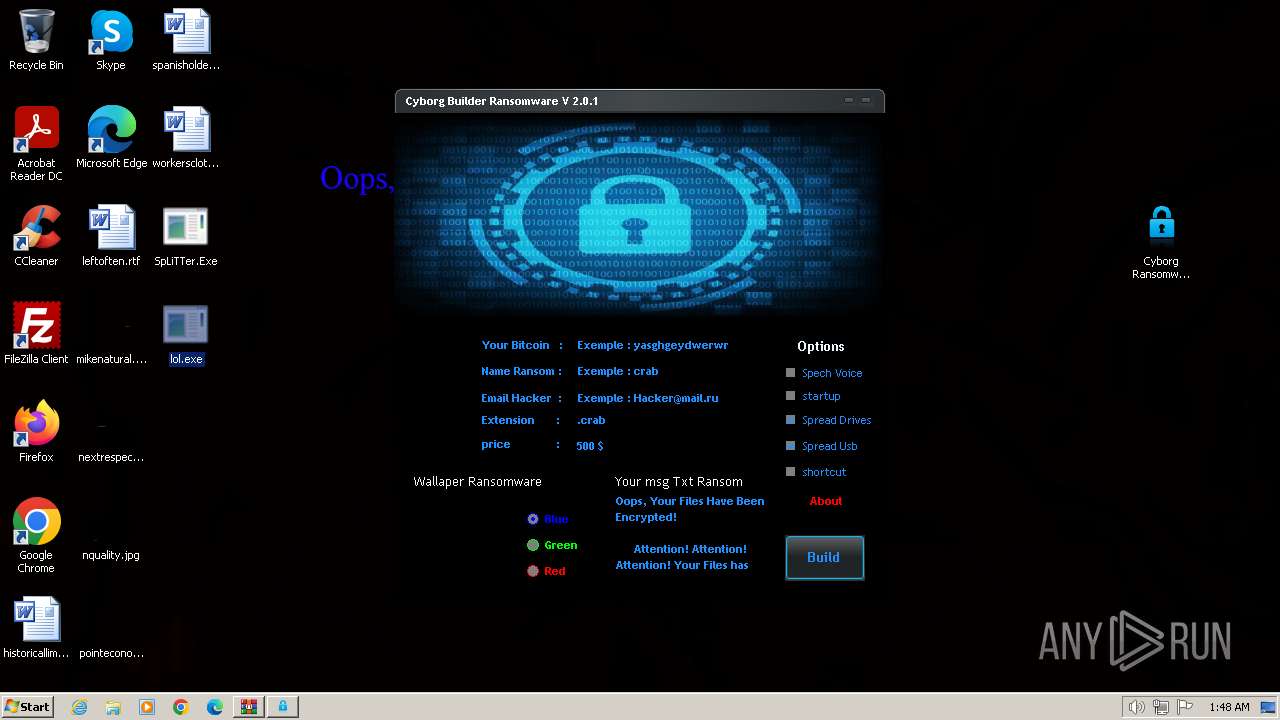
| 3660 | Cyborg Ransomware Builder v2.0.1.exe | C:\Users\admin\Desktop\stub.exe | executable | |
MD5:2B66A9137EFBCC4D1709B7EB8BFAC948 | SHA256:244BF592932F60EF82D117C3D7281764FF82E70C4DECA21CF0B04DA2E1AC99FA | |||
| 3660 | Cyborg Ransomware Builder v2.0.1.exe | C:\Users\admin\Desktop\lol.exe | executable | |
MD5:D4E91AD761E6428172585130B51AF713 | SHA256:EC708061770969F395F200E11E55B855AF677144D4D83942621864744B416C68 | |||
| 3772 | lol.exe | C:\Users\admin\AppData\Roaming\img.jpg | image | |
MD5:E5C7A2E97247CA1F28166FF4FF68F694 | SHA256:E635E2A8E306C8CA7C67389DEC8C1EE912E855E6E532BBDF3A962DCB51EFE31B | |||
| 3772 | lol.exe | C:\Users\admin\Desktop\SpLiTTer.Exe | executable | |
MD5:D4E91AD761E6428172585130B51AF713 | SHA256:EC708061770969F395F200E11E55B855AF677144D4D83942621864744B416C68 | |||
| 3772 | lol.exe | C:\Users\admin\Desktop\historicallimited.rtf | binary | |
MD5:B42B4CC7BA339E24F3587CD7D973DAC6 | SHA256:490768549FBC293A8BB5C8E7C84807441C1E9E67D1BECD86AC6E44E652064F47 | |||
| 3772 | lol.exe | C:\Users\admin\Desktop\leftoften.rtf | binary | |
MD5:1E6179EA6FA3F6A39FDF6A01F1AF3946 | SHA256:06FCBF4301F1AAA8D3CE494B3B623C00E84E516901F7FDC1EF7D94CA0C25FCCC | |||
| 3772 | lol.exe | C:\Users\admin\Desktop\historicallimited.rtf.crab | binary | |
MD5:B42B4CC7BA339E24F3587CD7D973DAC6 | SHA256:490768549FBC293A8BB5C8E7C84807441C1E9E67D1BECD86AC6E44E652064F47 | |||
| 3772 | lol.exe | C:\Users\admin\Desktop\nquality.jpg | binary | |
MD5:8713D09B652187366F9B4C2D12615D5B | SHA256:264AE6388C9BF64AAFD16C3360C189010D7230FA4081FF4C134CDD6D9C2CB5DB | |||
| 3772 | lol.exe | C:\Users\admin\Desktop\nextrespect.png | binary | |
MD5:B65411DDE3E5AB0DD8143B929A93BCC3 | SHA256:B0E45D3EAA4257BC97A080223B9DC1E07032D4533B7501203A4EA8DE648CECA8 | |||
| 3772 | lol.exe | C:\Users\admin\Desktop\mikenatural.png | binary | |
MD5:FDFF9CAB9CFB3A849699AB21ACD5343F | SHA256:F4751960A5A7AC8E58C28018F45BB1D3943ED65E8D6E2044ABAA0FAF68038C82 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |