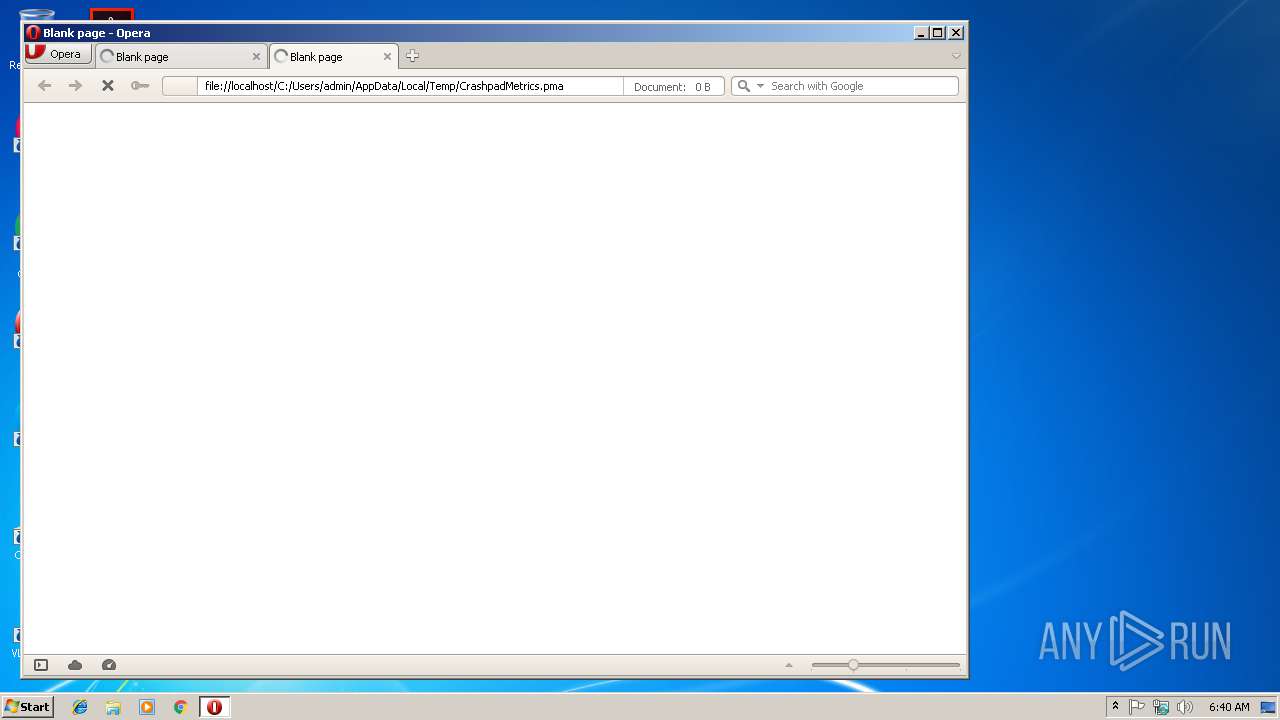
| File name: | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma |
| Full analysis: | https://app.any.run/tasks/614145f3-e027-4a8d-96ac-9dcdd2514ff1 |
| Verdict: | No threats detected |
| Analysis date: | February 20, 2019, 06:39:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 9543068B6751E1F3E11F91D72EE78D95 |
| SHA1: | B1008DFD703AAFA529C36C9E68AEBFA6237105F8 |
| SHA256: | D060AD21AE6E04CB58668CAA52ADFCA573E018102CC07554D2ED3EAE11AB7785 |
| SSDEEP: | 12:bHikaXhVMMBKEKSCemJKlkQITagigpCbUlQpYJ0X:bWROMMBS+Mkv/igp1lYYW |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- Opera.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
31
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
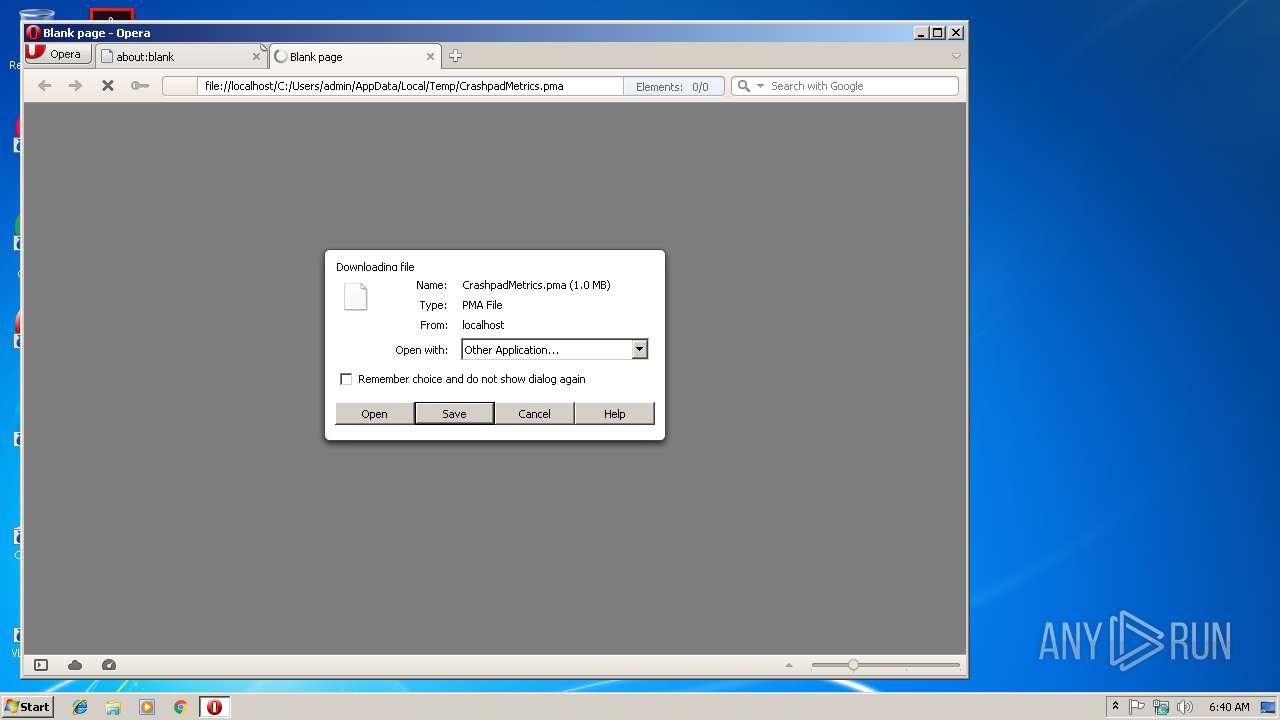
| 900 | "C:\Program Files\Opera\Opera.exe" "C:\Users\admin\AppData\Local\Temp\CrashpadMetrics.pma" | C:\Program Files\Opera\Opera.exe | rundll32.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
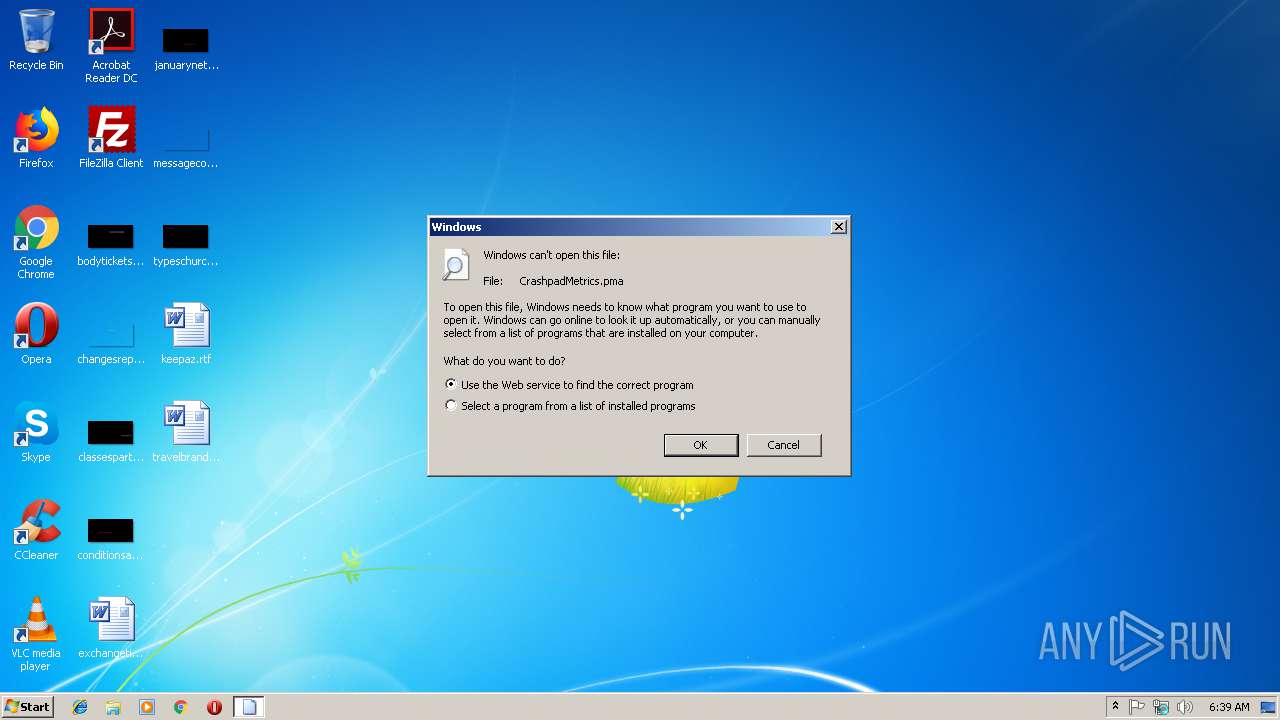
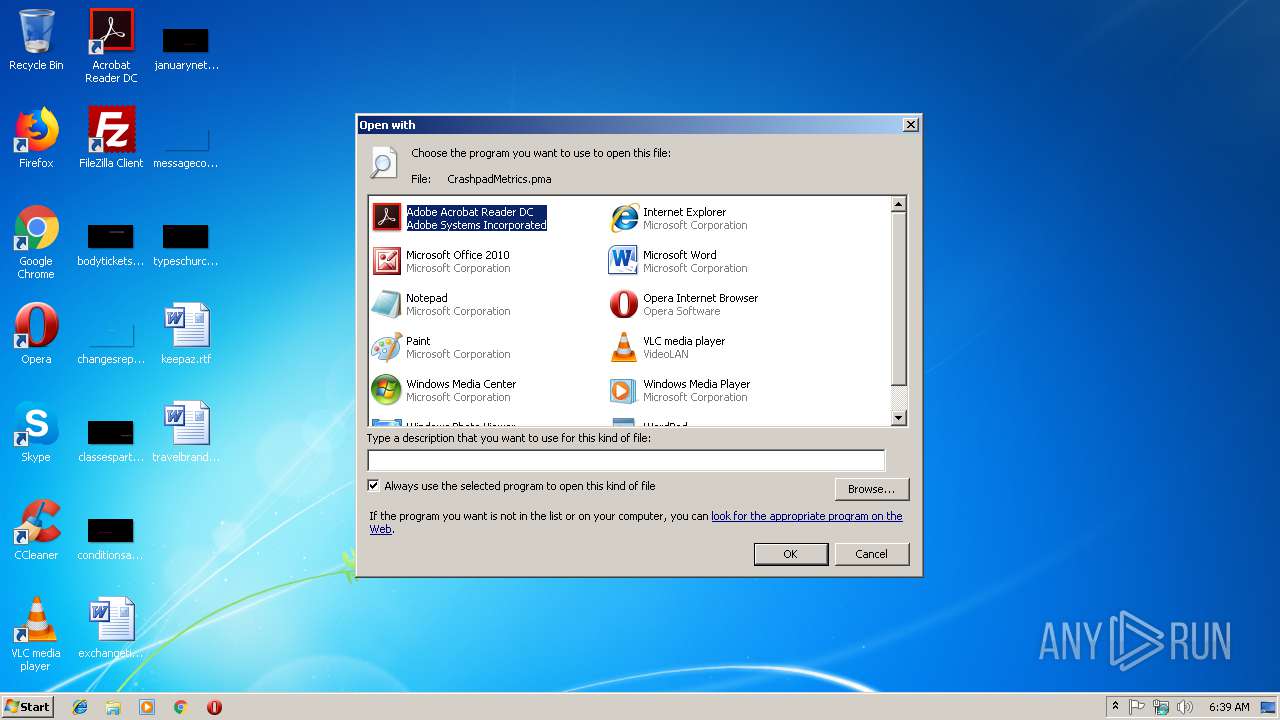
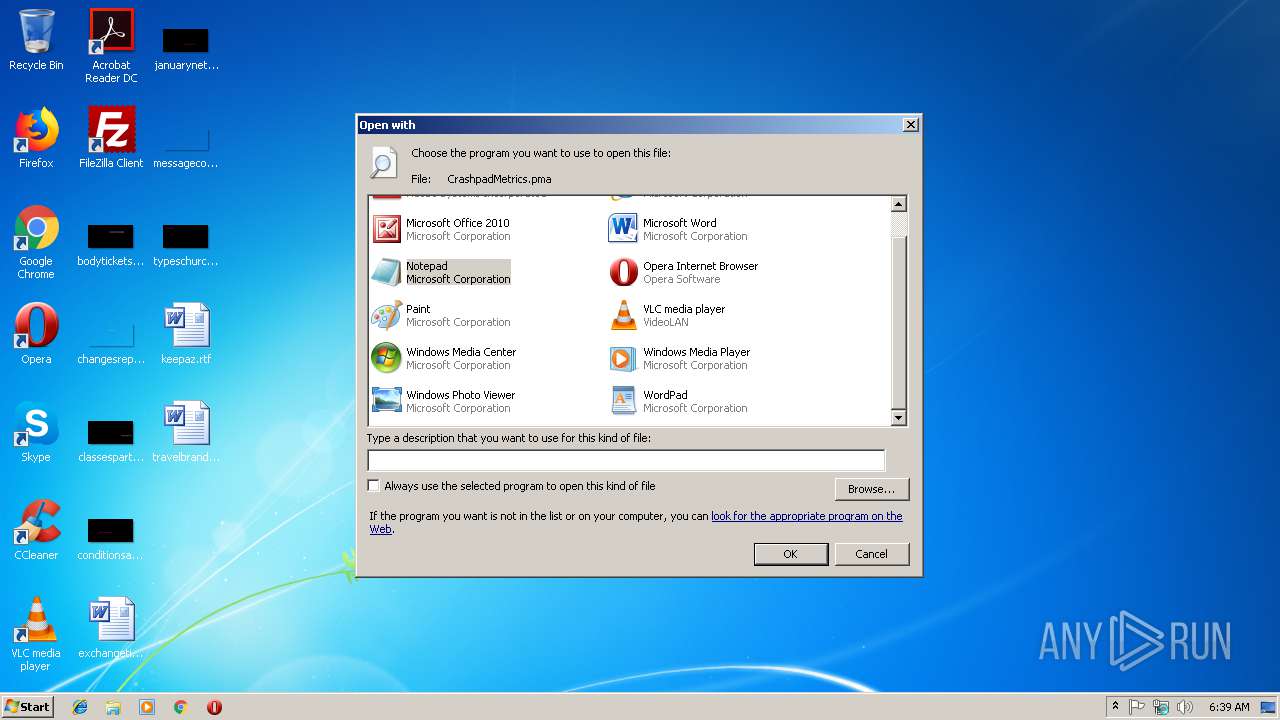
| 3004 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\CrashpadMetrics.pma | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 022
Read events
892
Write events
130
Delete events
0
Modification events
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (3004) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
17
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr1F8F.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr1FA0.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2166.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr0000V.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\S61D0X0FR1L496XIVWQ4.temp | — | |
MD5:— | SHA256:— | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win.bak | text | |
MD5:C6BB9F4ECB7995E1C8BF8D4B2B5E0369 | SHA256:AFF3CCAE88267386AECE32D6C93F89E91B9705B3852C4DBD057EACF2BF0C9292 | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win | text | |
MD5:12C651A8860A153DA69C27B8B3A7497D | SHA256:8194D79307B130295CBF59C98AB578228D32DAAD916BFC22A34AA365738EB9B5 | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:7C7A04AEDC9A5FA28E06D2FAE0A339E7 | SHA256:290E53F1ADF6E18B508EC68E26546E3330958820E42E1B432155C0B017180785 | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:862918350A7912B081EA316FDA269858 | SHA256:FFDC398C6C5E21BB8979E44171E2C4646F0D1EAAB8FA96254A05BFB4C54E0D5D | |||
| 900 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opcert6.dat | binary | |
MD5:1AA8644C9261DC10F7247F6A145C1DD2 | SHA256:58A8933F65361633C6AB194000D312DC9D566F717B1A16814A0DBEE24A60EBE3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
900 | Opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
900 | Opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
900 | Opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
900 | Opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
900 | Opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |