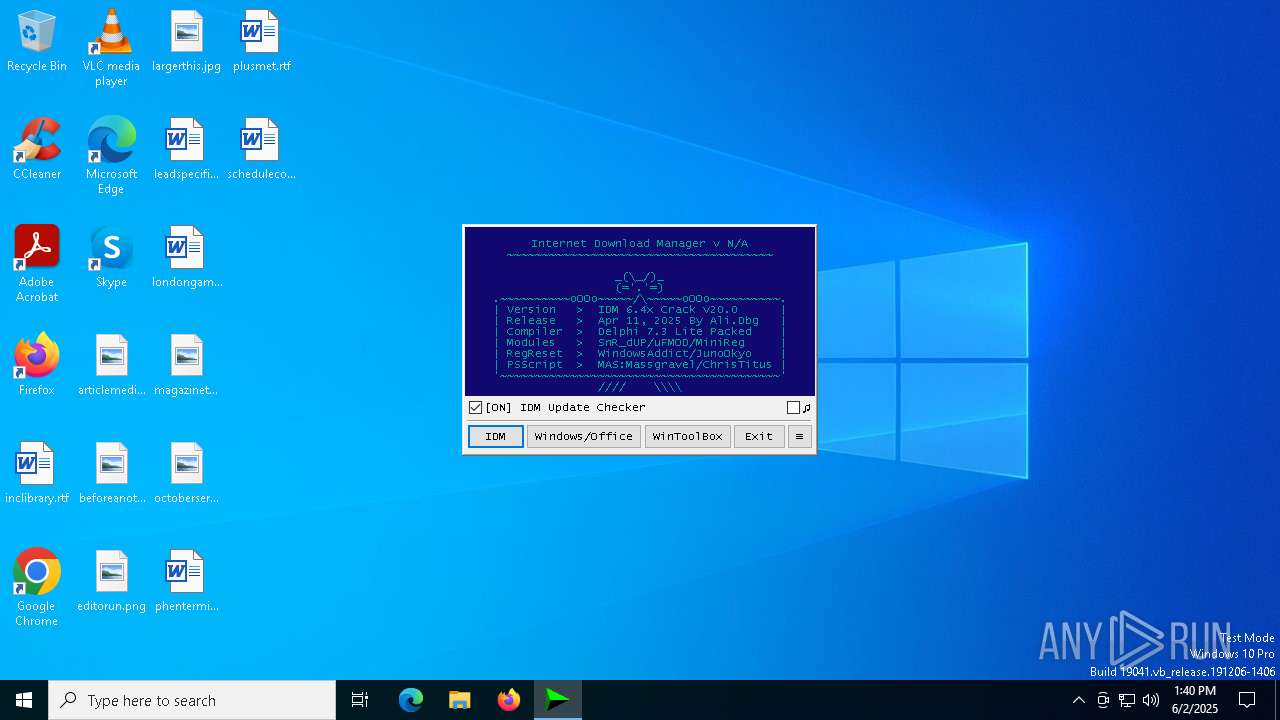
| File name: | IDM_6.4x_Crack_v20.0.exe |
| Full analysis: | https://app.any.run/tasks/42701b96-509e-4d21-a414-5a23be167edd |
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2025, 13:40:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, PECompact2 compressed, 2 sections |
| MD5: | 7235C81D6A1990BF7301194A9F778F9A |
| SHA1: | 300001BD1550BF827E21739470EA07984691497E |
| SHA256: | D05FFF510254E92AD35A002F6224ED53D2557DF2D9F158A0FCBD6574973B68DD |
| SSDEEP: | 1536:pqou2aP+PP3cjIwYKixQchFR1tREvARbB:I12a+PP3ckwY9xQchFRnREvARF |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3364)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3364)
Deletes a file (SCRIPT)
- wscript.exe (PID: 3364)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3364)
SUSPICIOUS
The process executes VB scripts
- IDM_6.4x_Crack_v20.0.exe (PID: 4620)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3364)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 3364)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3364)
INFO
Checks supported languages
- IDM_6.4x_Crack_v20.0.exe (PID: 4620)
Reads the computer name
- IDM_6.4x_Crack_v20.0.exe (PID: 4620)
Create files in a temporary directory
- IDM_6.4x_Crack_v20.0.exe (PID: 4620)
Checks proxy server information
- wscript.exe (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (v2.x) (50.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (35.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 51200 |
| InitializedDataSize: | 96256 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
131
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1168 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3300 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3364 | wscript.exe "C:\Users\admin\AppData\Local\Temp\\CRK_UPDT.vbs" "https://idm.0dy.ir/" "Version" "Download_URL" "20.0" "Crack" "C:\Program Files\Google\Chrome\Application\chrome.exe" silent | C:\Windows\SysWOW64\wscript.exe | IDM_6.4x_Crack_v20.0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4620 | "C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v20.0.exe" | C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v20.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7700 | "C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v20.0.exe" | C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v20.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 051
Read events
1 036
Write events
15
Delete events
0
Modification events
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
| (PID) Process: | (4620) IDM_6.4x_Crack_v20.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\PowerShell\1\ShellIds\ScriptedDiagnostics |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4620 | IDM_6.4x_Crack_v20.0.exe | C:\Users\admin\AppData\Local\Temp\IDM_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 4620 | IDM_6.4x_Crack_v20.0.exe | C:\Users\admin\AppData\Local\Temp\CRK_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7628 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2560 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3364 | wscript.exe | 188.114.97.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7628 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7628 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
idm.0dy.ir |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |