| File name: | Server.exe |
| Full analysis: | https://app.any.run/tasks/5b90ae9a-b348-4359-aeea-4dcfbcbb2e4c |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 10:43:32 |
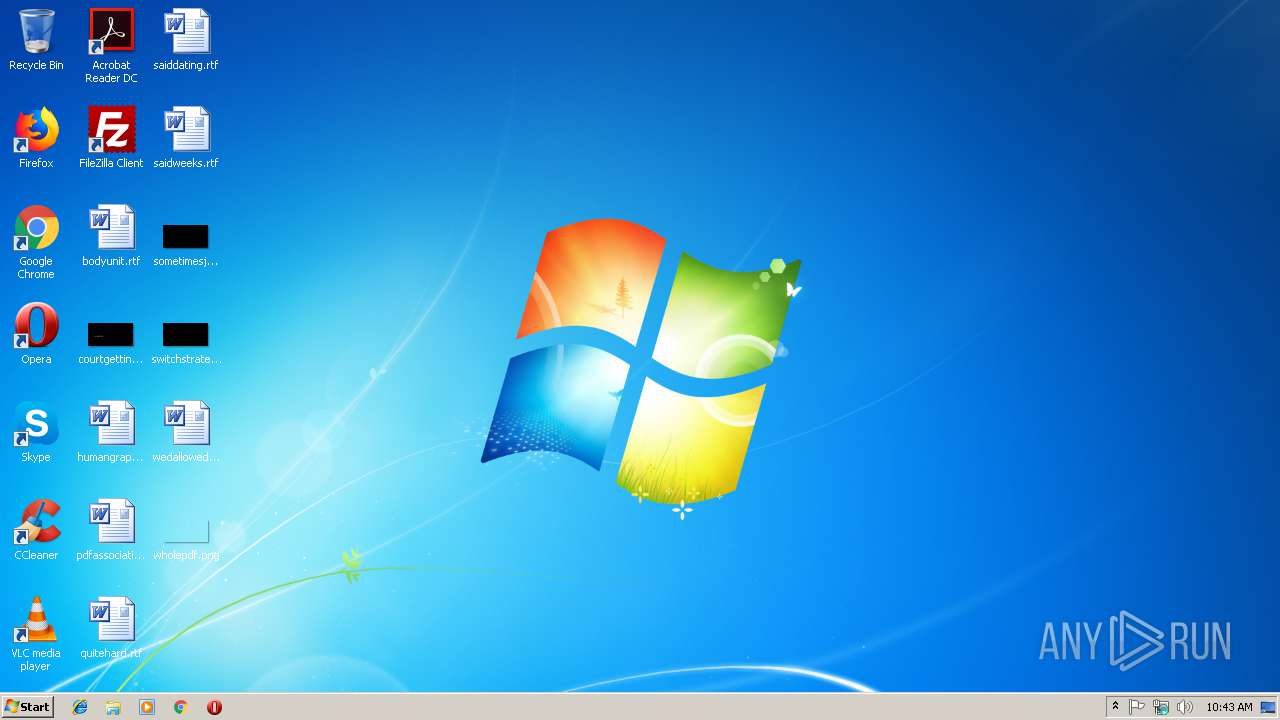
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 0A24F96D93F68F85770012FA44E8E444 |
| SHA1: | E18CC7ADF17B79A7E5162D51CD66E560DD1F9A3F |
| SHA256: | D05B5F13BFA9082F9087DABC3C4D15471209B1DFE8B27272360558DBA2C85D43 |
| SSDEEP: | 384:QyIdmF+TXCsj0DOgEm6/glRXC+MGCIeNFYXsq3bHtiNDXJ/URLR:QyIsF8ysqjGWyjk1XlH01Zk |
MALICIOUS
Changes the autorun value in the registry
- Server.exe (PID: 3100)
SUSPICIOUS
Executable content was dropped or overwritten
- Server.exe (PID: 3100)
Creates files in the user directory
- Server.exe (PID: 3100)
Connects to unusual port
- Server.exe (PID: 3100)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 20480 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 61440 |
| EntryPoint: | 0x14940 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0000F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00010000 | 0x00005000 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.859 |
.rsrc | 0x00015000 | 0x00001000 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.64048 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 6.86743 | 224 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
XTREME | 7.76338 | 2032 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.DLL |
PSAPI.dll |
advapi32.dll |
ntdll.dll |
oleaut32.dll |
shell32.dll |
shlwapi.dll |
urlmon.dll |
user32.dll |
wininet.dll |
Total processes
30
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3100 | "C:\Users\admin\AppData\Local\Temp\Server.exe" | C:\Users\admin\AppData\Local\Temp\Server.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
63
Read events
40
Write events
23
Delete events
0
Modification events
| (PID) Process: | (3100) Server.exe | Key: | HKEY_CURRENT_USER\Software\((Mutex)) |
| Operation: | write | Name: | ServerStarted |
Value: 2/11/2019 10:43:49 AM | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | HKLM |
Value: C:\Users\admin\AppData\Roaming\InstallDir\Server.exe | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | HKCU |
Value: C:\Users\admin\AppData\Roaming\InstallDir\Server.exe | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{5460C4DF-B266-909E-CB58-E32B79832EB2} |
| Operation: | write | Name: | StubPath |
Value: C:\Users\admin\AppData\Roaming\InstallDir\Server.exe restart | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_CURRENT_USER\Software\((Mutex)) |
| Operation: | write | Name: | InstalledServer |
Value: C:\Users\admin\AppData\Roaming\InstallDir\Server.exe | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Server_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Server_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Server_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Server_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3100) Server.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Server_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | Server.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\((Mutex)).cfg | binary | |
MD5:5D38D7BEB4E83F77469716F38C7D4873 | SHA256:8B68CCC1E60FA0B1D96BA6D047023C4434141DD6080A90A32D8479961CAF16A0 | |||
| 3100 | Server.exe | C:\Users\admin\AppData\Roaming\InstallDir\Server.exe | executable | |
MD5:0A24F96D93F68F85770012FA44E8E444 | SHA256:D05B5F13BFA9082F9087DABC3C4D15471209B1DFE8B27272360558DBA2C85D43 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
37
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3100 | Server.exe | 173.46.85.251:81 | updatechrome.duckdns.org | Abc-hosters LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
updatechrome.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |