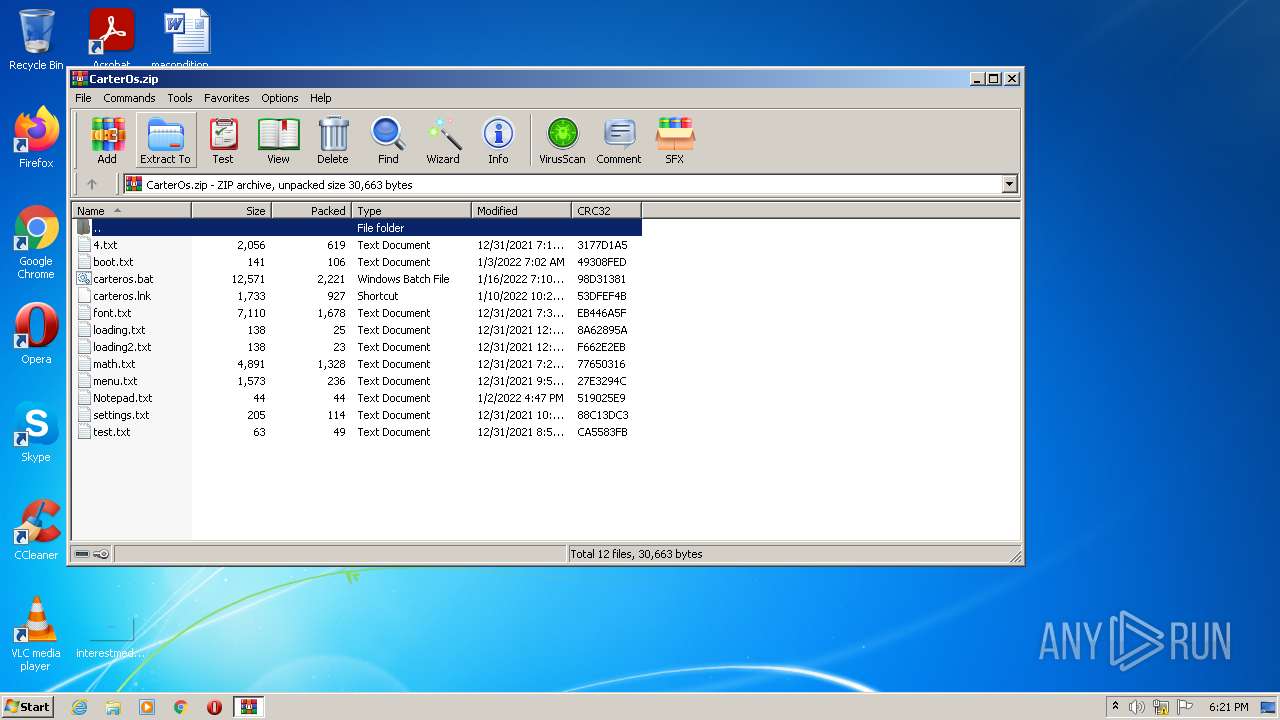
| File name: | CarterOs.zip |
| Full analysis: | https://app.any.run/tasks/e4ee1660-d8f9-409e-8369-f271b0b122f4 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 18:21:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 24EF4394FC1A6F227D82D8EC4536550B |
| SHA1: | F370D79DCF0FADC349D44EEC398321E8C6A5B4AD |
| SHA256: | D0487C7F2A690CD415D38BA75A4DA5253BA54E40CBDE2F117FFAAC1AD7C358AE |
| SSDEEP: | 192:dzJ/3hfnmaof77GHtX+RfSu7EwyglXflV3hrN91l32Rs4CP:bxfn1I2Ht0SusgFlV3lwXCP |
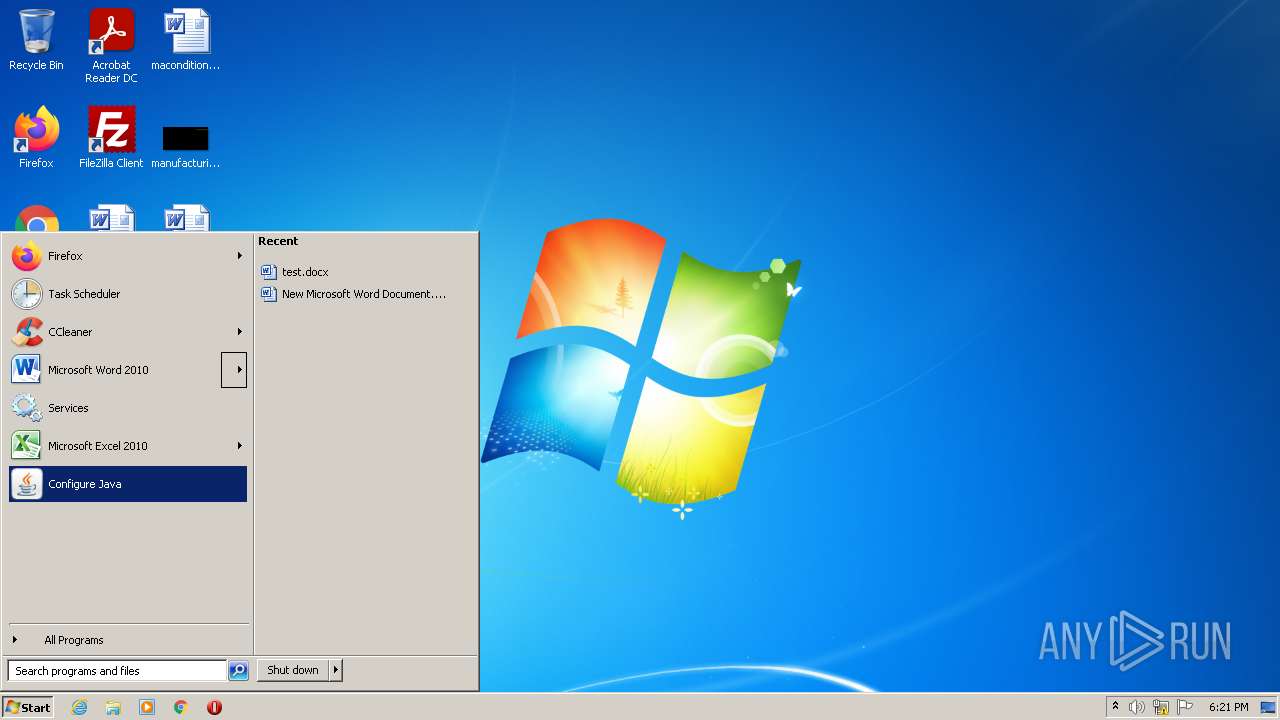
MALICIOUS
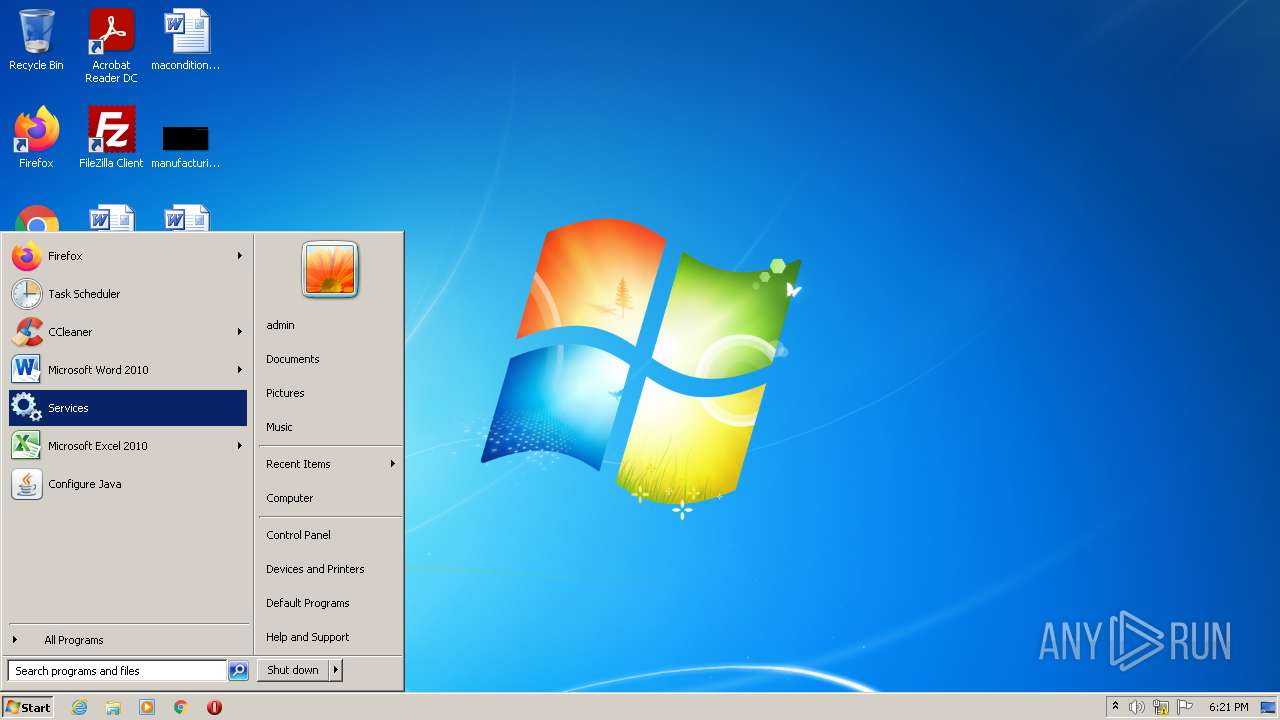
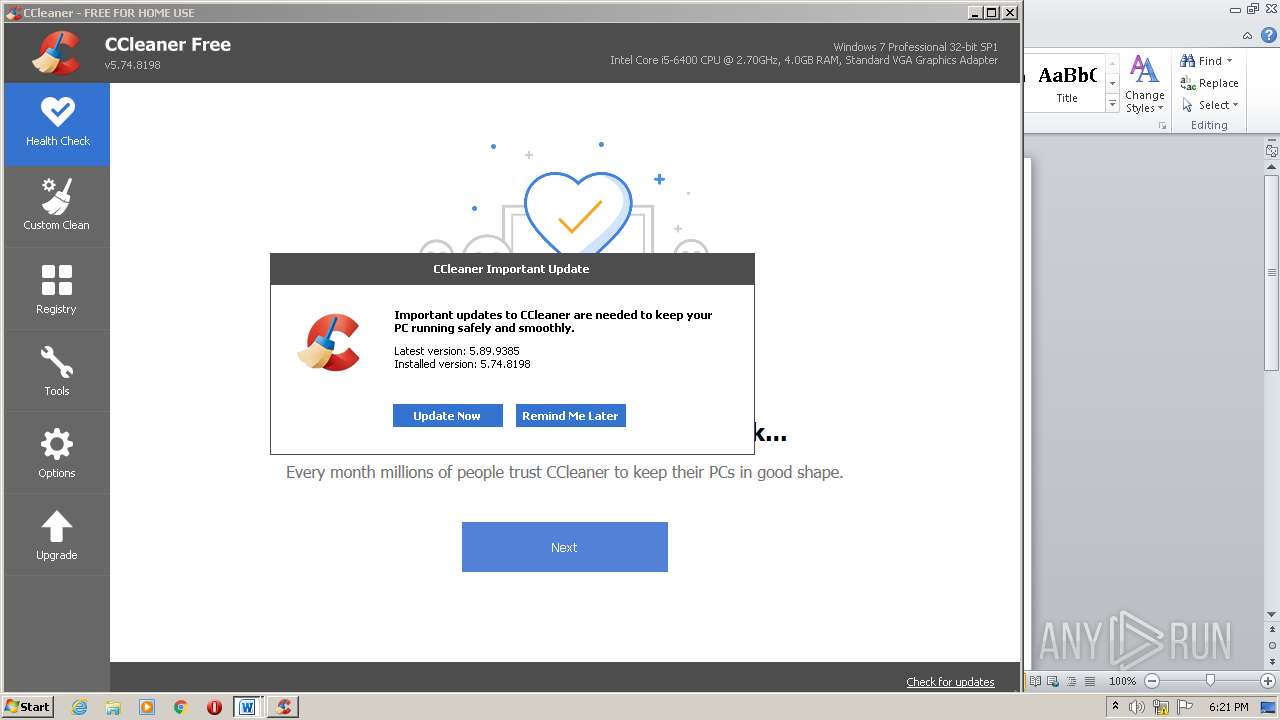
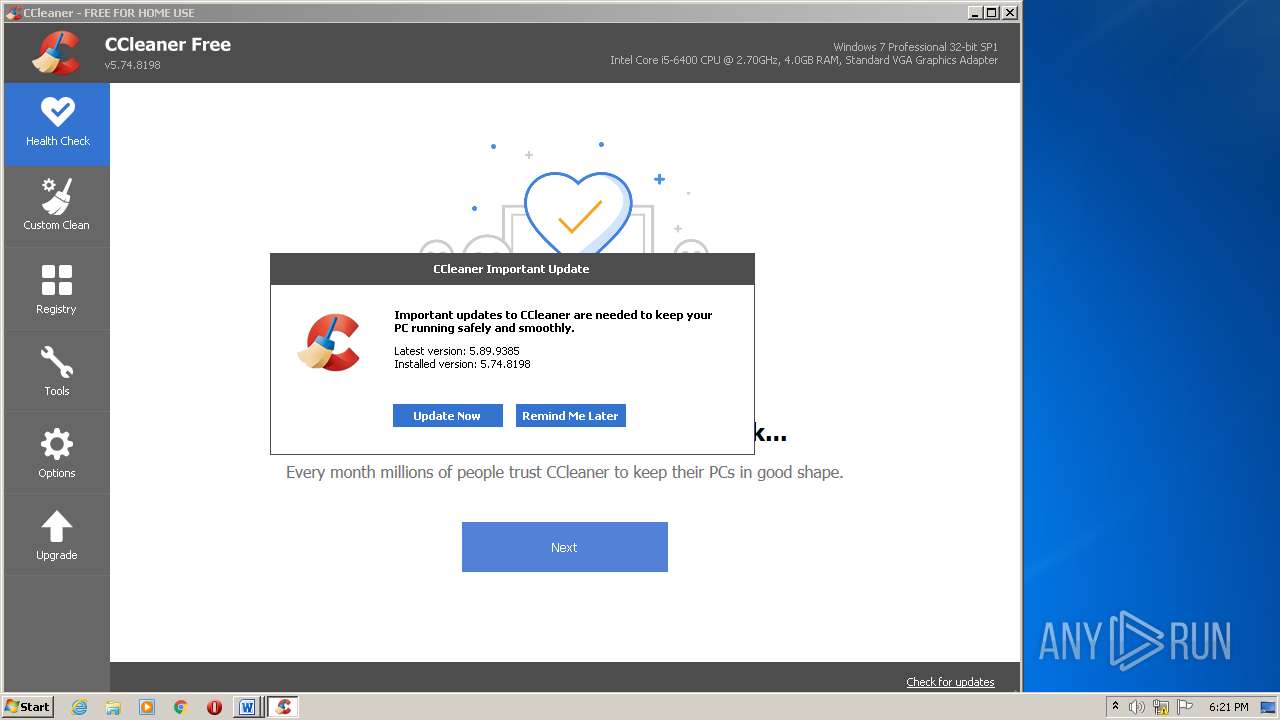
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2516)
- CCleaner.exe (PID: 4036)
Loads dropped or rewritten executable
- CCleaner.exe (PID: 4036)
Drops executable file immediately after starts
- CCleaner.exe (PID: 4036)
Changes settings of System certificates
- CCleaner.exe (PID: 4036)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 1472)
- CCleaner.exe (PID: 2516)
- CCleaner.exe (PID: 4036)
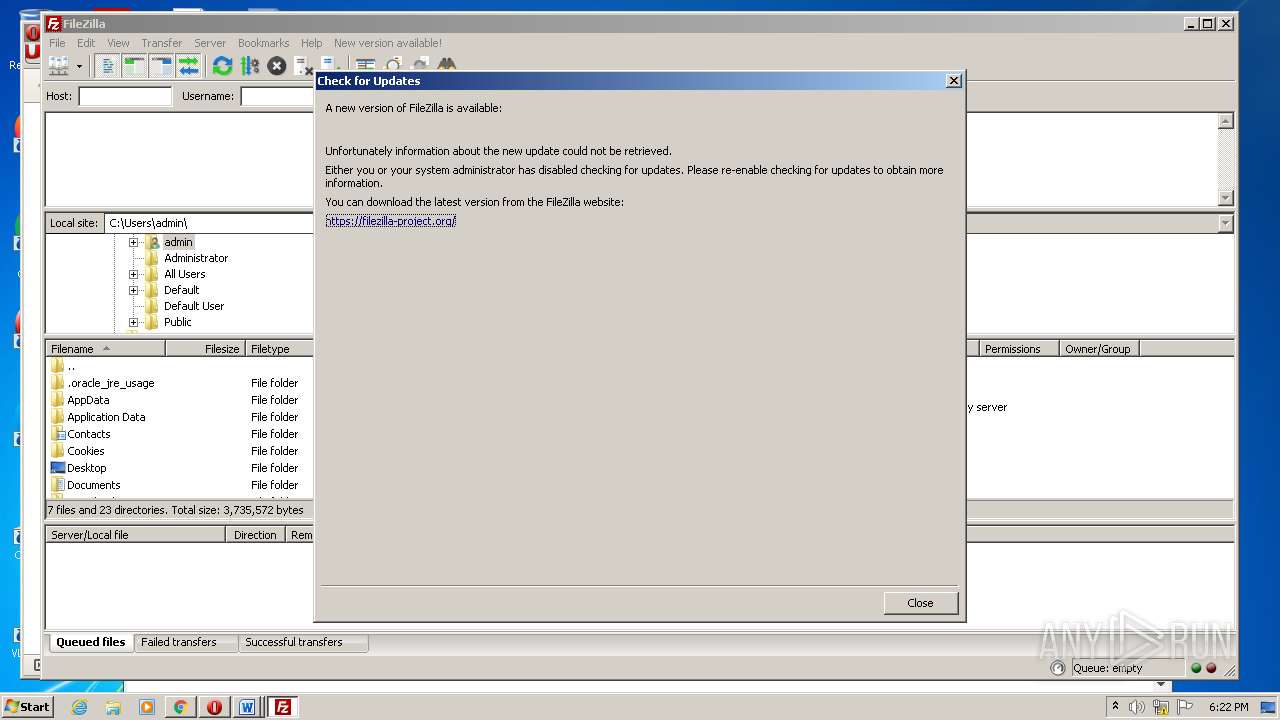
- filezilla.exe (PID: 3224)
Checks supported languages
- WinRAR.exe (PID: 1472)
- CCleaner.exe (PID: 2516)
- CCleaner.exe (PID: 4036)
- filezilla.exe (PID: 3224)
Reads Environment values
- CCleaner.exe (PID: 2516)
- CCleaner.exe (PID: 4036)
Executed via Task Scheduler
- CCleaner.exe (PID: 4036)
Drops a file that was compiled in debug mode
- CCleaner.exe (PID: 4036)
Creates files in the program directory
- CCleaner.exe (PID: 4036)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 4036)
Reads the date of Windows installation
- CCleaner.exe (PID: 4036)
Creates a directory in Program Files
- CCleaner.exe (PID: 4036)
Reads CPU info
- CCleaner.exe (PID: 4036)
Reads internet explorer settings
- CCleaner.exe (PID: 4036)
Creates files in the user directory
- CCleaner.exe (PID: 4036)
- filezilla.exe (PID: 3224)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 4036)
Searches for installed software
- CCleaner.exe (PID: 4036)
INFO
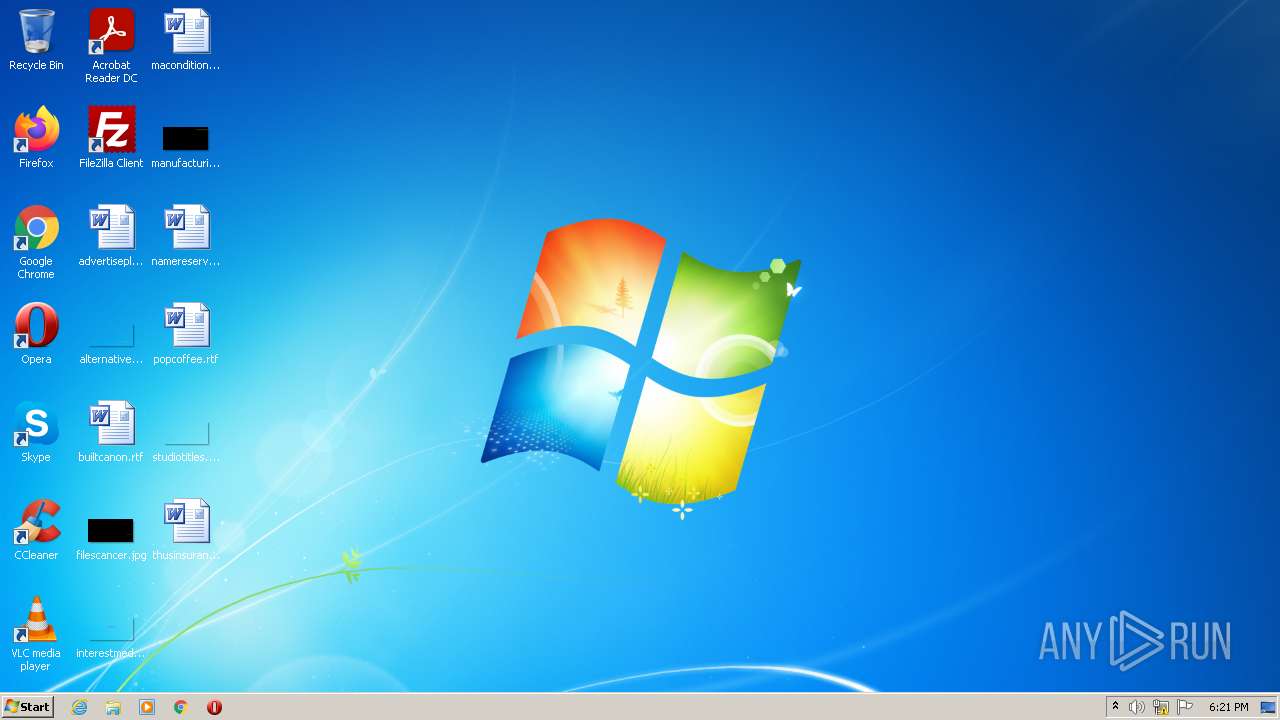
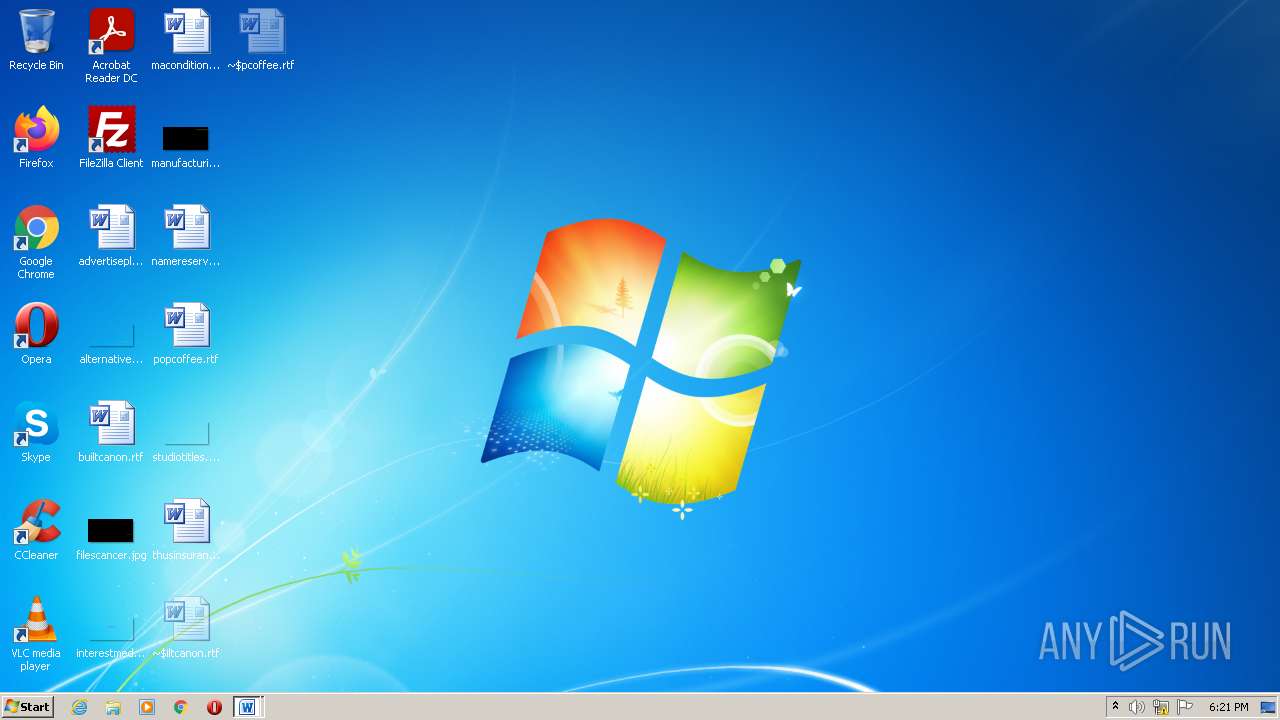
Manual execution by user
- CCleaner.exe (PID: 2516)
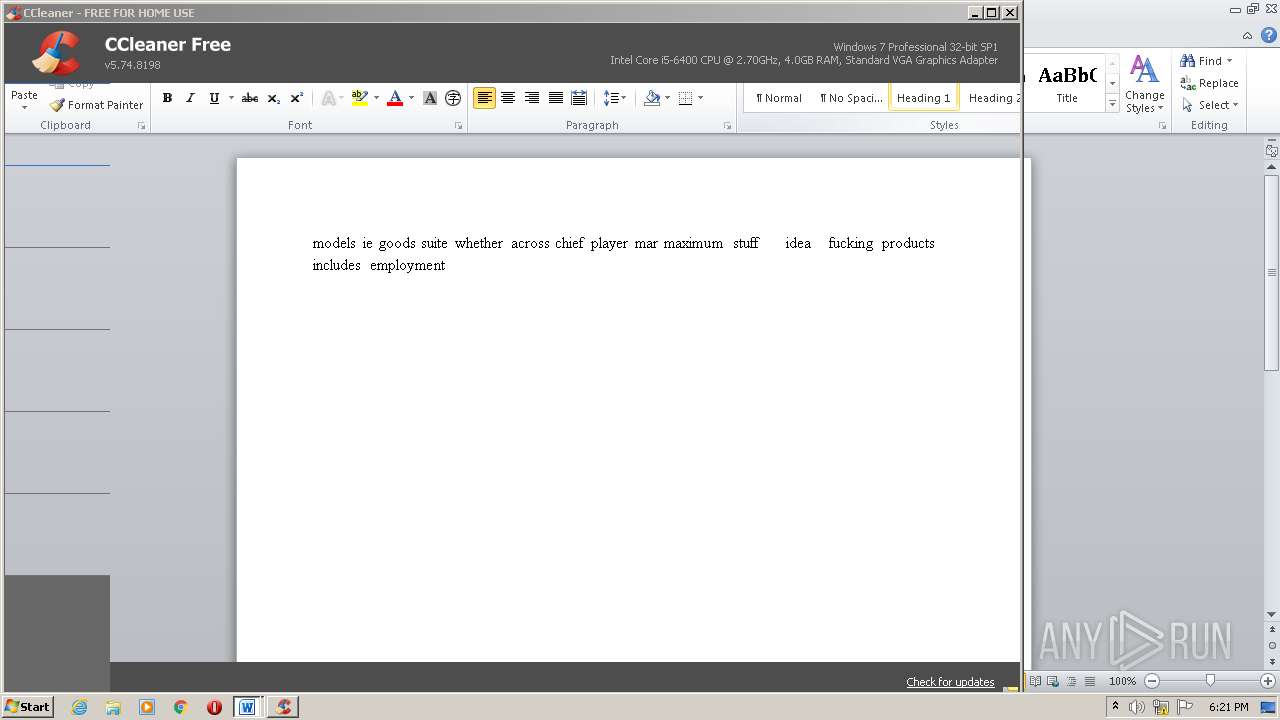
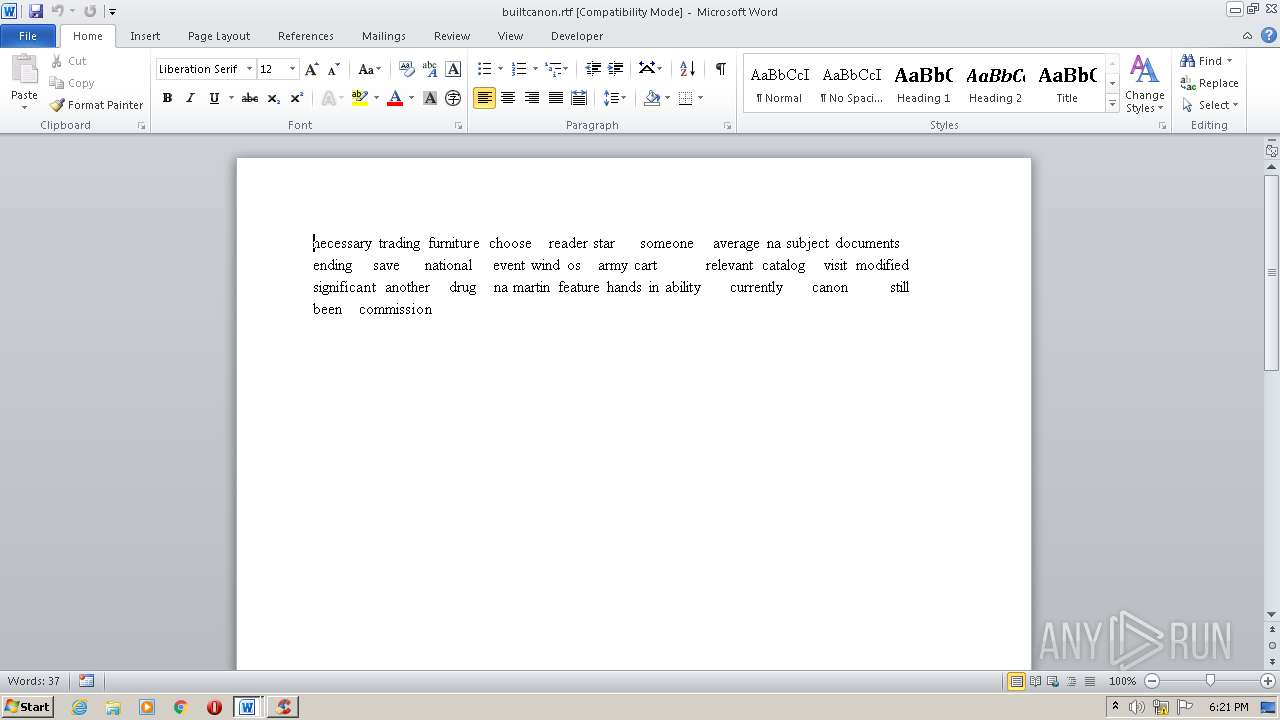
- WINWORD.EXE (PID: 672)
- WINWORD.EXE (PID: 1236)
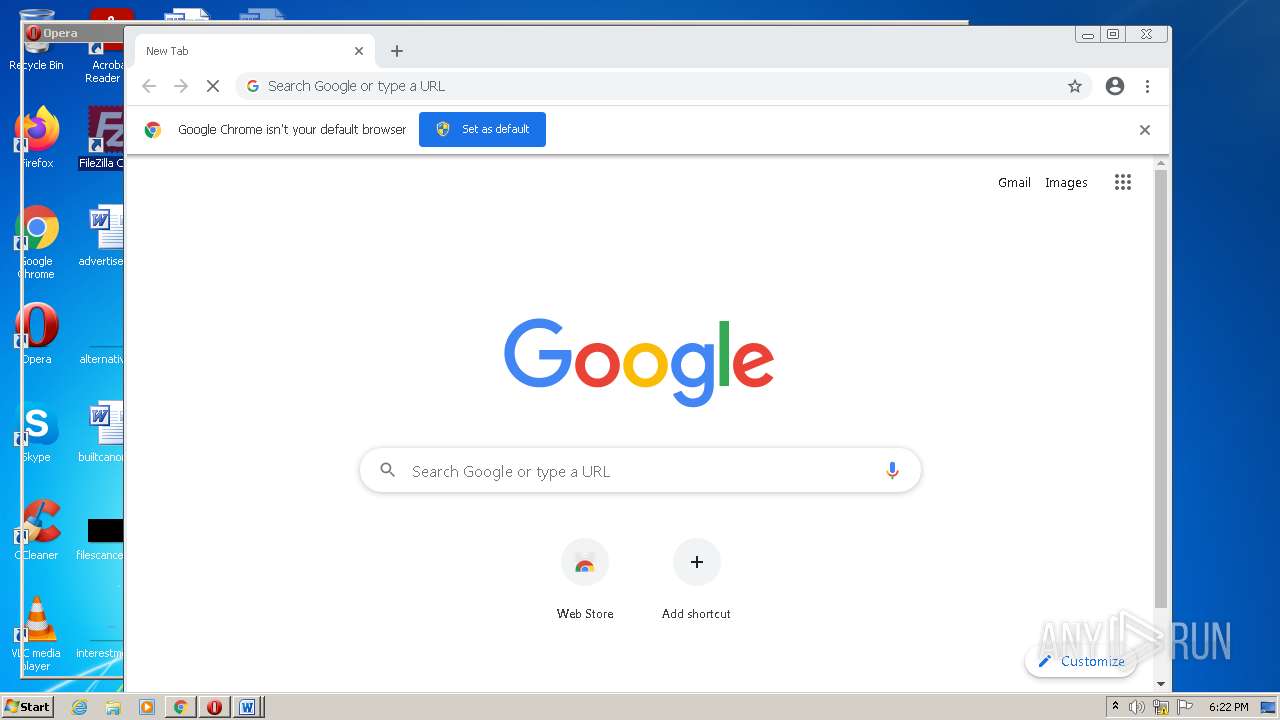
- chrome.exe (PID: 3736)
- opera.exe (PID: 3568)
- filezilla.exe (PID: 3224)
Reads the hosts file
- CCleaner.exe (PID: 4036)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 3280)
Checks supported languages
- WINWORD.EXE (PID: 672)
- WINWORD.EXE (PID: 1236)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 2804)
- chrome.exe (PID: 568)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 1176)
- chrome.exe (PID: 2916)
- opera.exe (PID: 3568)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 276)
Reads the computer name
- WINWORD.EXE (PID: 672)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 568)
- chrome.exe (PID: 3280)
- opera.exe (PID: 3568)
- chrome.exe (PID: 276)
Creates files in the user directory
- WINWORD.EXE (PID: 672)
- opera.exe (PID: 3568)
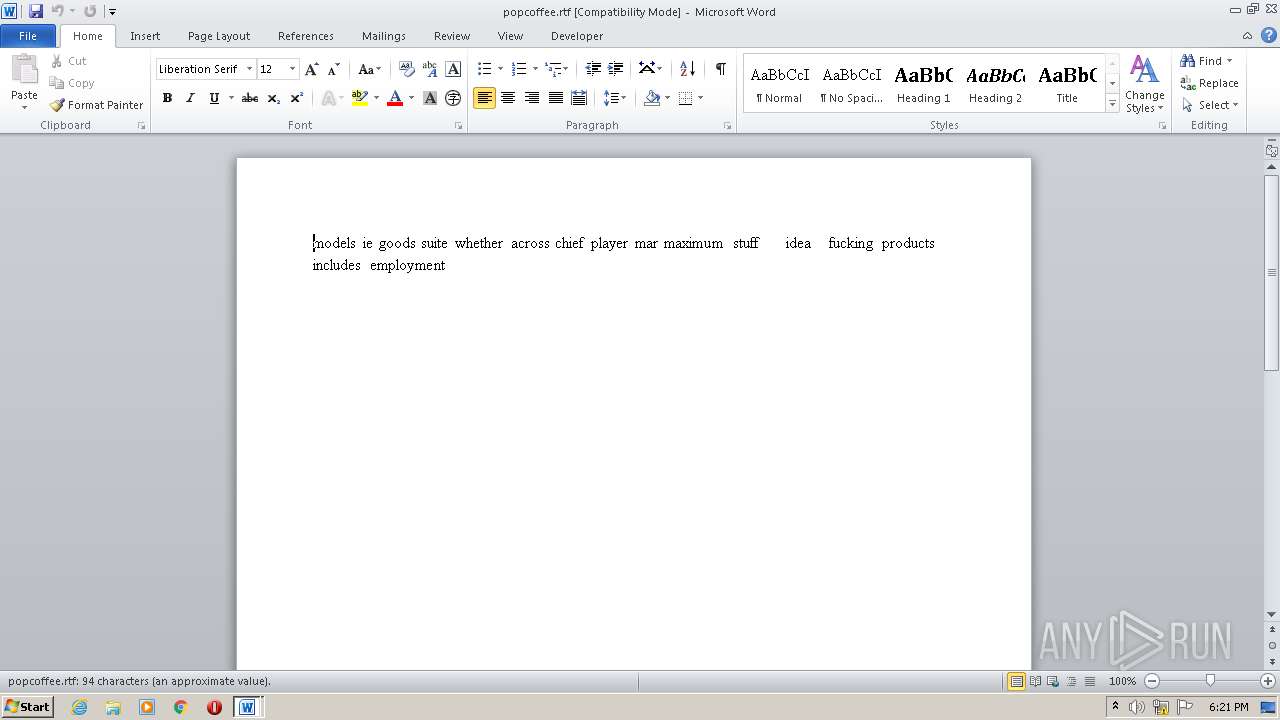
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1236)
- WINWORD.EXE (PID: 672)
Checks Windows Trust Settings
- CCleaner.exe (PID: 4036)
Reads settings of System Certificates
- CCleaner.exe (PID: 4036)
- chrome.exe (PID: 3280)
- filezilla.exe (PID: 3224)
Application launched itself
- chrome.exe (PID: 3736)
Check for Java to be installed
- opera.exe (PID: 3568)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3568)
Reads the date of Windows installation
- opera.exe (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | 4.txt |
|---|---|
| ZipUncompressedSize: | 2056 |
| ZipCompressedSize: | 619 |
| ZipCRC: | 0x3177d1a5 |
| ZipModifyDate: | 2021:12:31 07:17:29 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
55
Monitored processes
17
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,5563952549043187320,6290202440211271481,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2960 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,5563952549043187320,6290202440211271481,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\builtcanon.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5563952549043187320,6290202440211271481,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\popcoffee.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CarterOs.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,5563952549043187320,6290202440211271481,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2832 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,5563952549043187320,6290202440211271481,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6db3d988,0x6db3d998,0x6db3d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
20 618
Read events
19 603
Write events
795
Delete events
220
Modification events
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CarterOs.zip | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
29
Text files
41
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR40EF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR442B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 672 | WINWORD.EXE | C:\Users\admin\Desktop\~$pcoffee.rtf | pgc | |
MD5:— | SHA256:— | |||
| 672 | WINWORD.EXE | C:\Users\admin\Desktop\~$iltcanon.rtf | pgc | |
MD5:— | SHA256:— | |||
| 672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\builtcanon.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\popcoffee.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 4036 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QA0DA1V60XNN6MQK6X9J.temp | binary | |
MD5:— | SHA256:— | |||
| 4036 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ed7a5cc3cca8d52a.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4036 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\auto[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
36
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
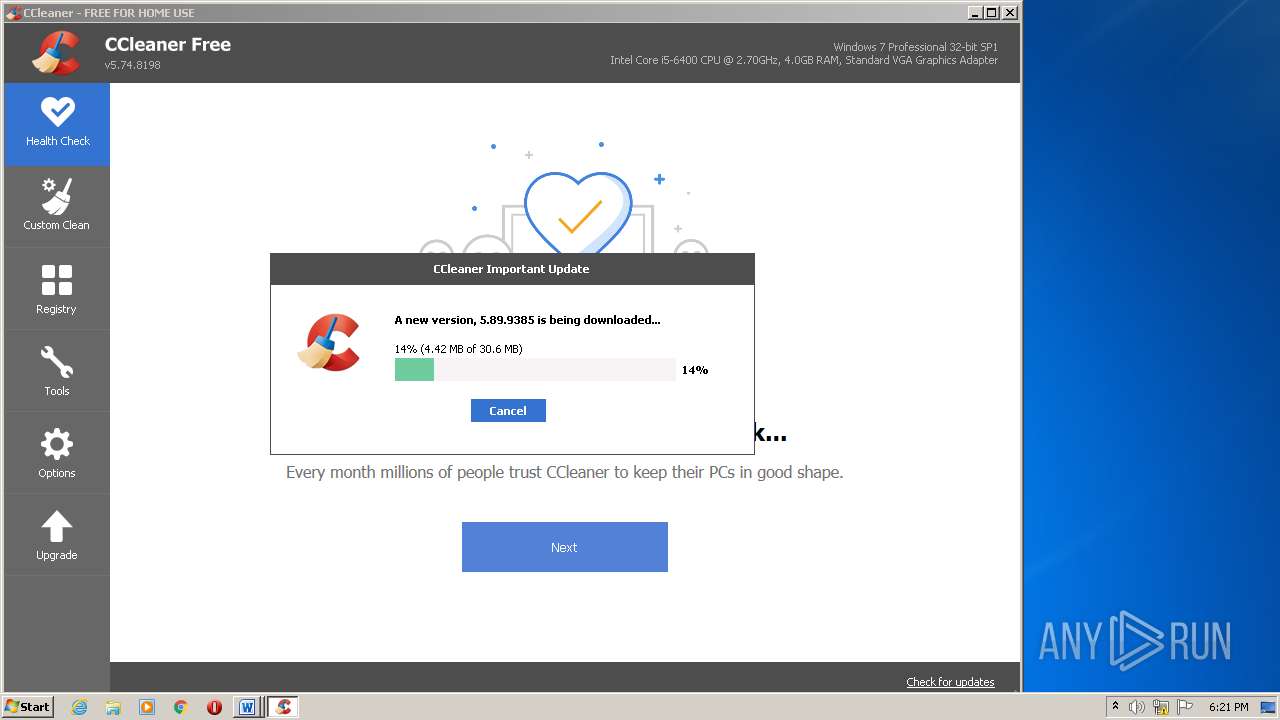
4036 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
4036 | CCleaner.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/auto?a=0&p=cc&v=5.74.8198&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&o=6.1W3&au=0&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | text | 61 b | whitelisted |
4036 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
4036 | CCleaner.exe | GET | 200 | 151.101.2.109:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.74.8198&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | text | 14 b | whitelisted |
4036 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGCDPAjbzpoUYuu%2B39wE%3D | US | der | 1.40 Kb | whitelisted |
4036 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
3568 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
4036 | CCleaner.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a133f780359fdc90 | US | compressed | 4.70 Kb | whitelisted |
4036 | CCleaner.exe | GET | 200 | 23.32.238.107:80 | http://ncc.avast.com/ncc.txt | US | text | 26 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4036 | CCleaner.exe | 104.107.160.105:443 | download.ccleaner.com | GTT Communications Inc. | US | unknown |
4036 | CCleaner.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
— | — | 69.94.68.205:443 | analytics.ff.avast.com | OLM, LLC | US | unknown |
4036 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
— | — | 151.101.2.202:80 | www.ccleaner.com | Fastly | US | suspicious |
4036 | CCleaner.exe | 23.32.238.107:80 | ncc.avast.com | XO Communications | US | suspicious |
4036 | CCleaner.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4036 | CCleaner.exe | 69.94.68.200:443 | analytics.ff.avast.com | OLM, LLC | US | unknown |
— | — | 5.62.25.43:443 | shepherd.ff.avast.com | iomart Cloud Services Limited. | GB | unknown |
3280 | chrome.exe | 142.250.185.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ncc.avast.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ipm-provider.ff.avast.com |
| whitelisted |
shepherd.ff.avast.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
license.piriform.com |
| whitelisted |
download.ccleaner.com |
| shared |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4036 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|
CCleaner.exe | observing currentModeType changed - Preview
|