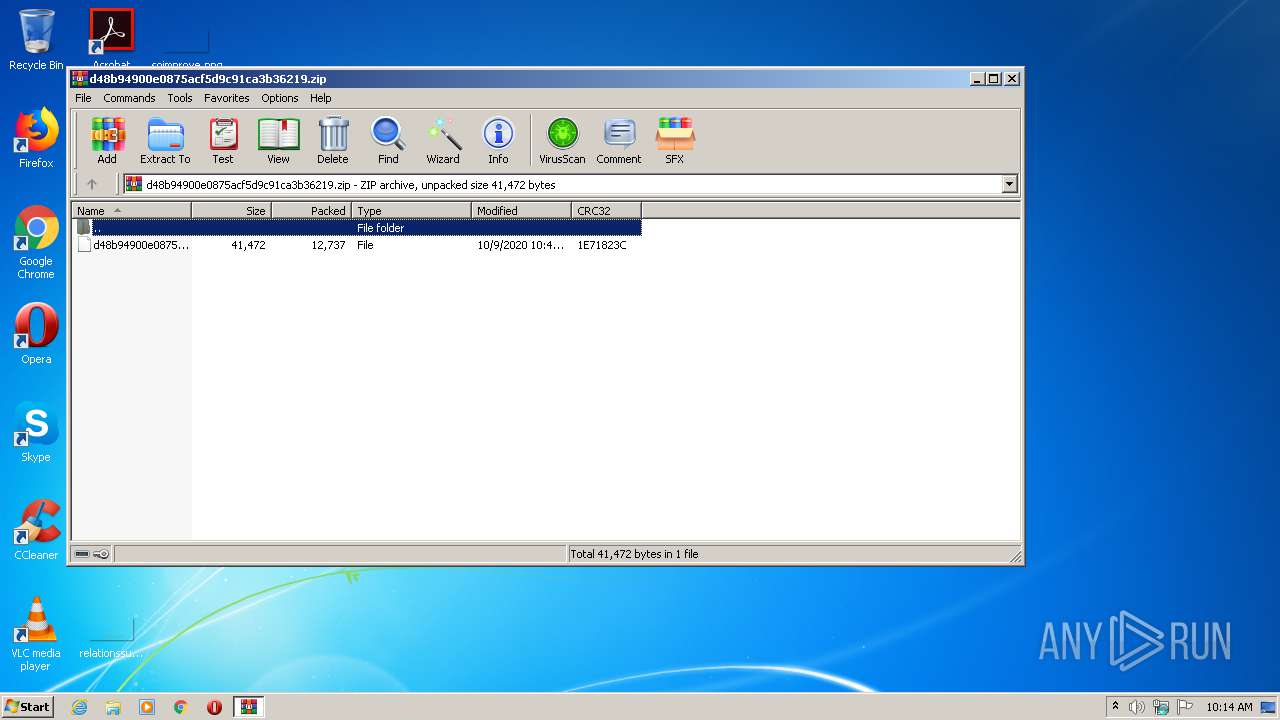
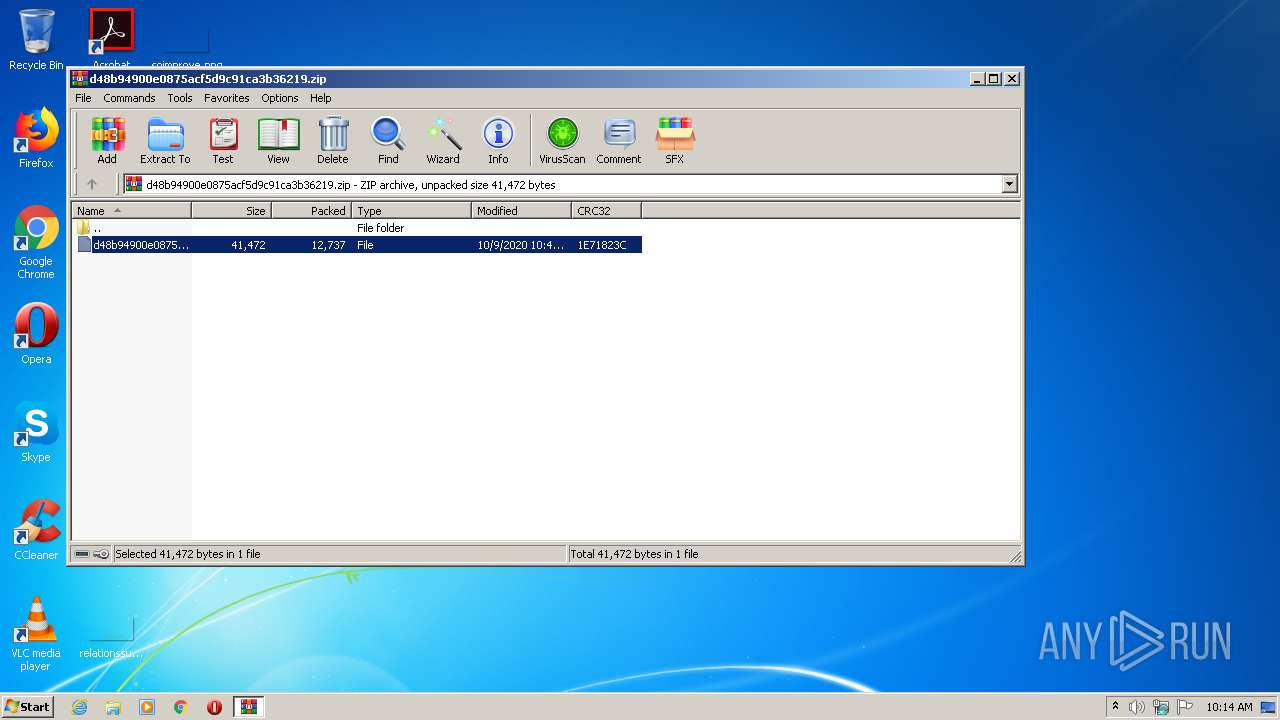
| File name: | d48b94900e0875acf5d9c91ca3b36219.zip |
| Full analysis: | https://app.any.run/tasks/08f9780a-73bd-4d78-920b-98b1e9fef609 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 09:13:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8F5B4B7D47C840D66F90F6A6E4DA3609 |
| SHA1: | 2E88BFB2E993AE69390B3C72650245456C5D166D |
| SHA256: | D040A84A8FD4D0184B6E3055FCFF50AAEDB0DE7B21D485274B25D010FE402B79 |
| SSDEEP: | 192:Mhl9UWIM6CHDJuKX7udksYUPE8UB/poqGtdPVMeZp7I9vbh/wvP6xDWFnPIfdOQ5:MOMXEKXqksijStt+mhCvbgpnPIPB/i+V |
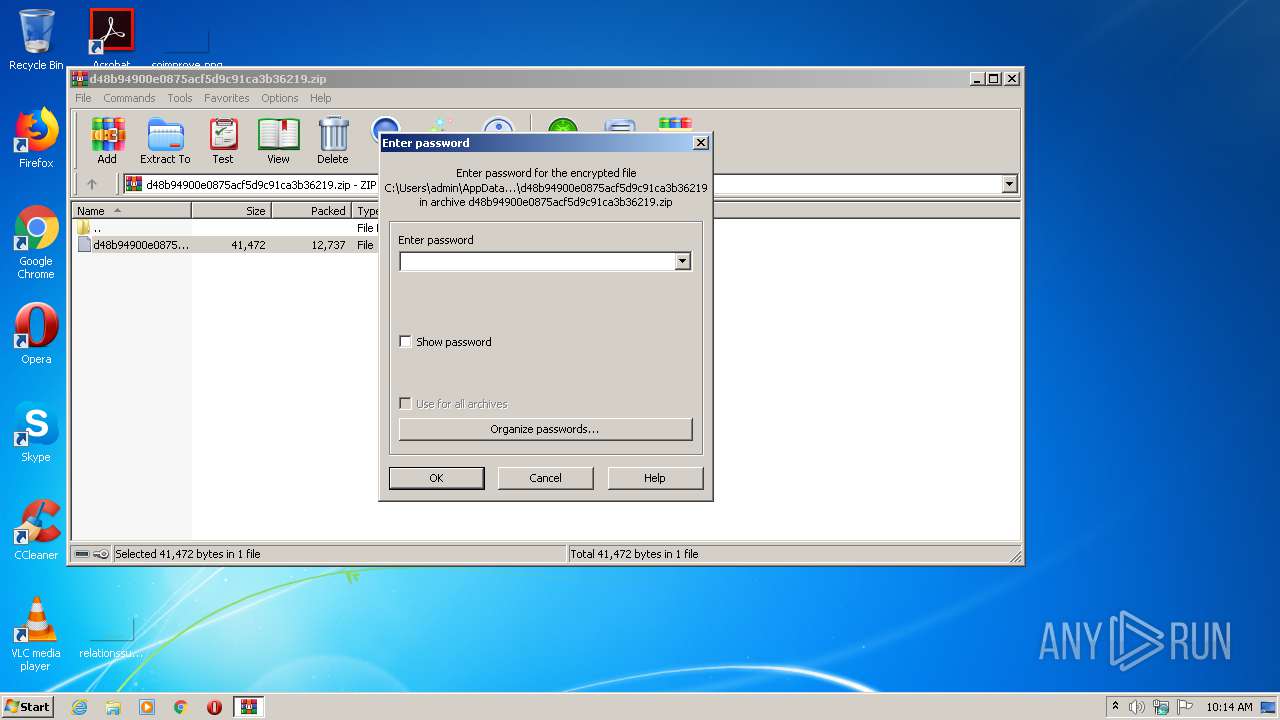
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2948)
SUSPICIOUS
Starts Microsoft Office Application
- rundll32.exe (PID: 3268)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 2948)
- iexplore.exe (PID: 2688)
Starts Internet Explorer
- rundll32.exe (PID: 2680)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3548)
Application launched itself
- iexplore.exe (PID: 2688)
- AcroRd32.exe (PID: 3864)
Changes internet zones settings
- iexplore.exe (PID: 2688)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2688)
Reads Internet Cache Settings
- iexplore.exe (PID: 2688)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
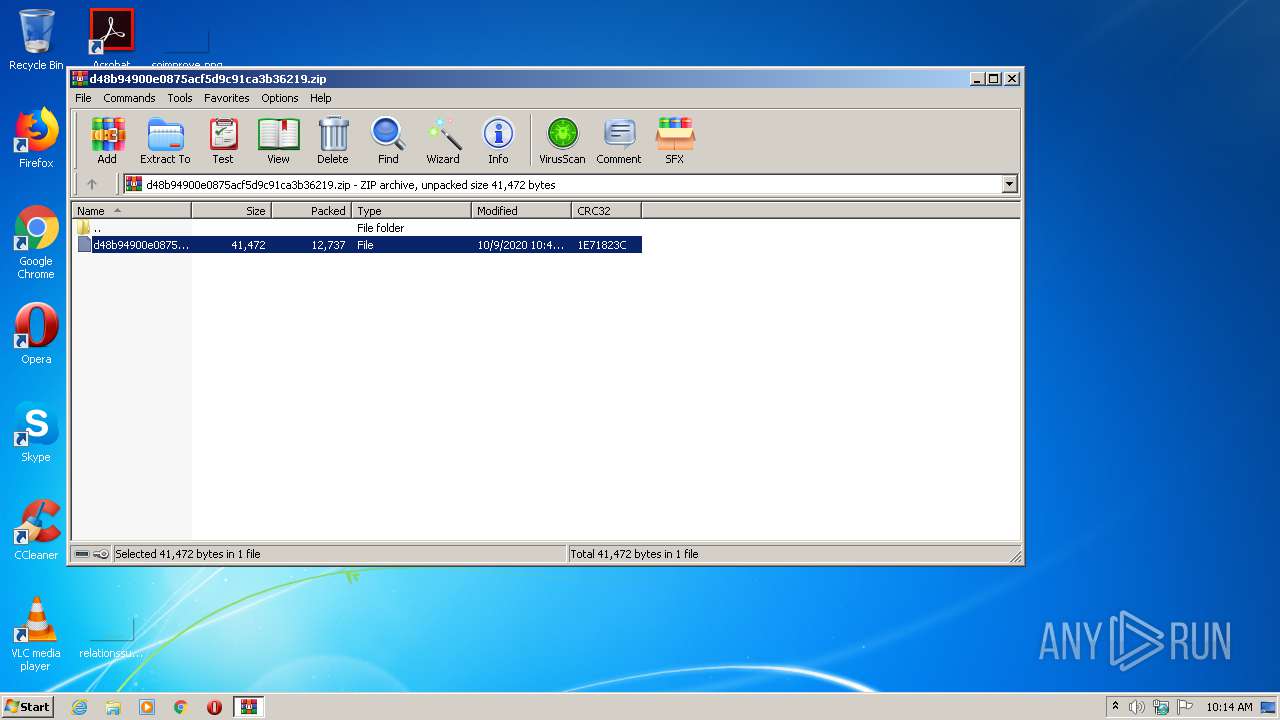
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:09 15:11:26 |
| ZipCRC: | 0x1e71823c |
| ZipCompressedSize: | 12737 |
| ZipUncompressedSize: | 41472 |
| ZipFileName: | d48b94900e0875acf5d9c91ca3b36219 |
Total processes
42
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
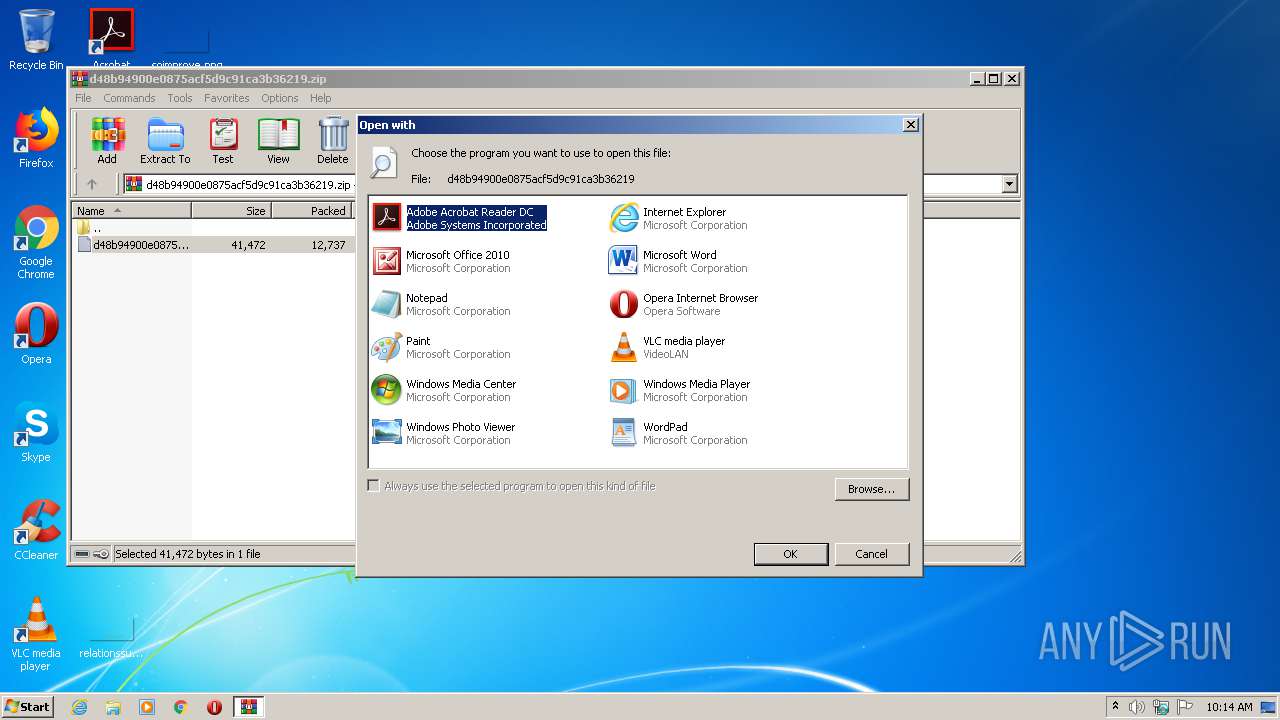
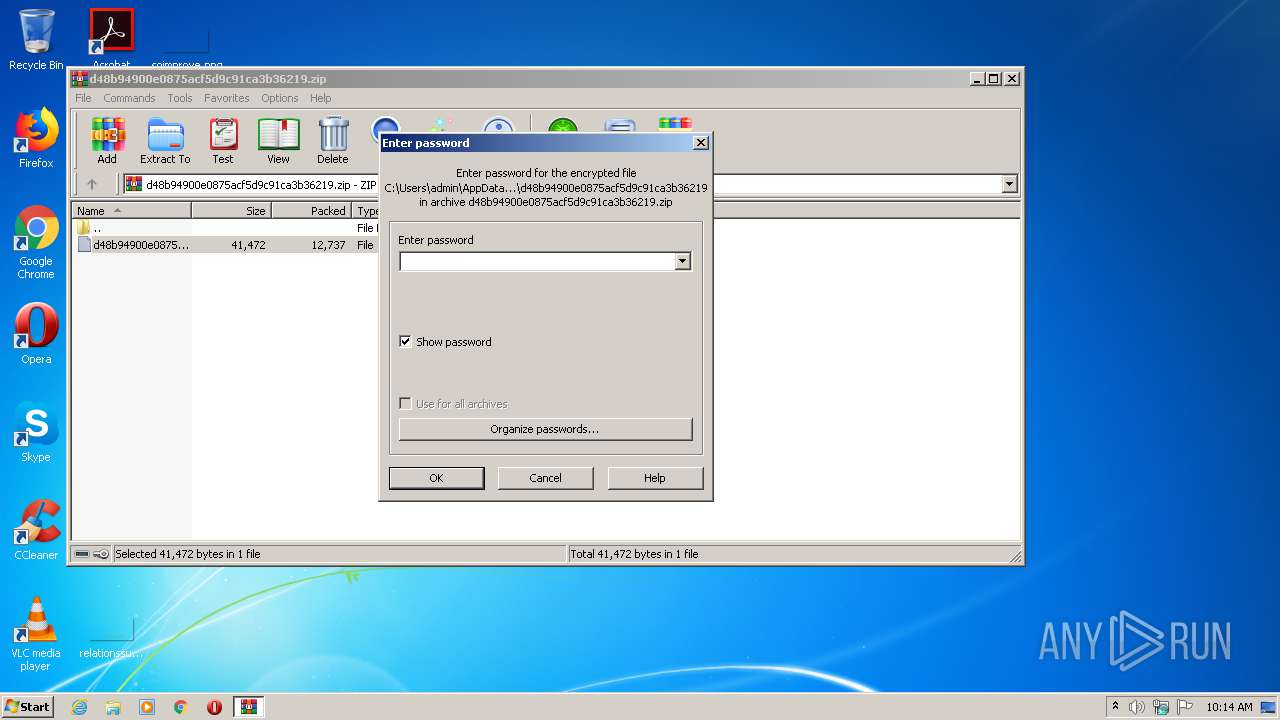
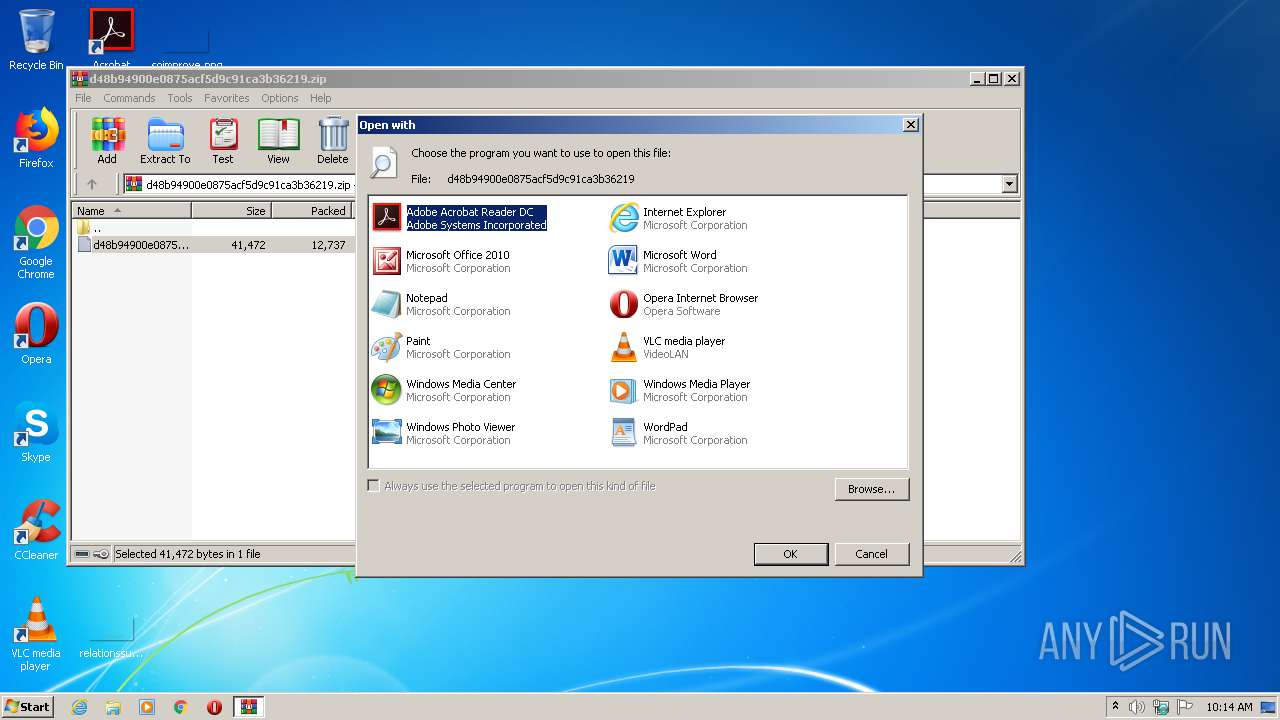
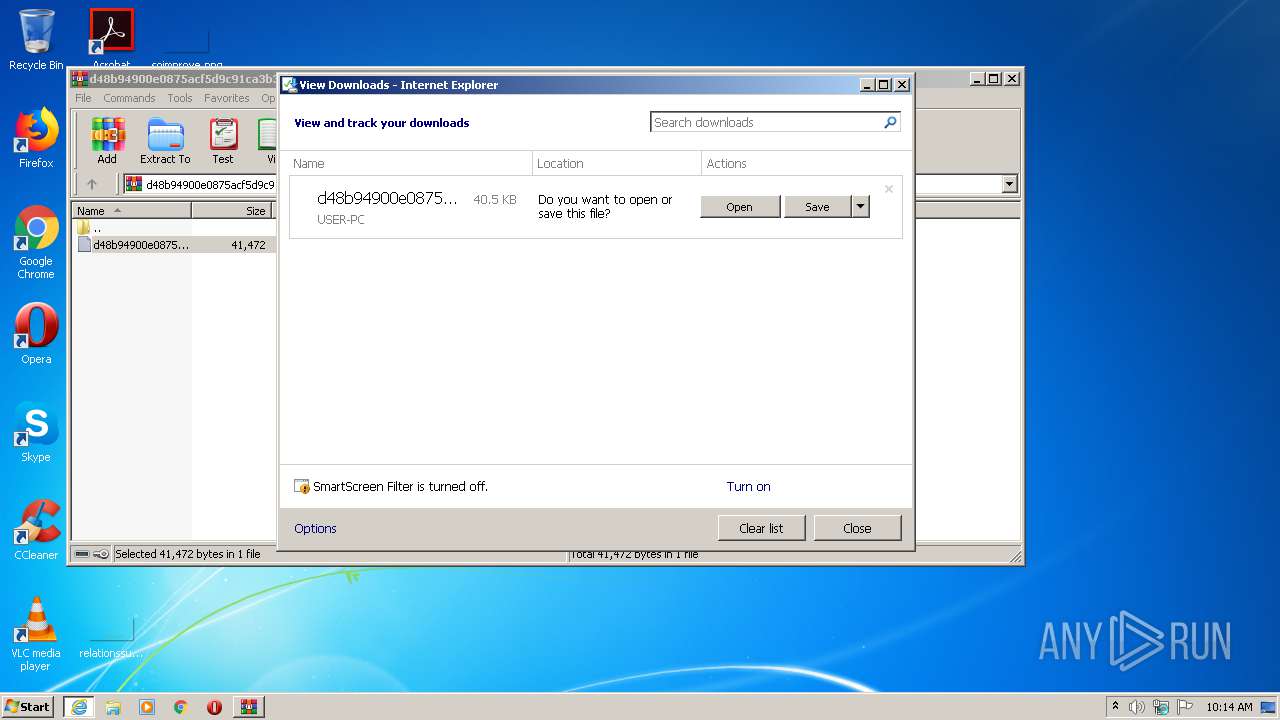
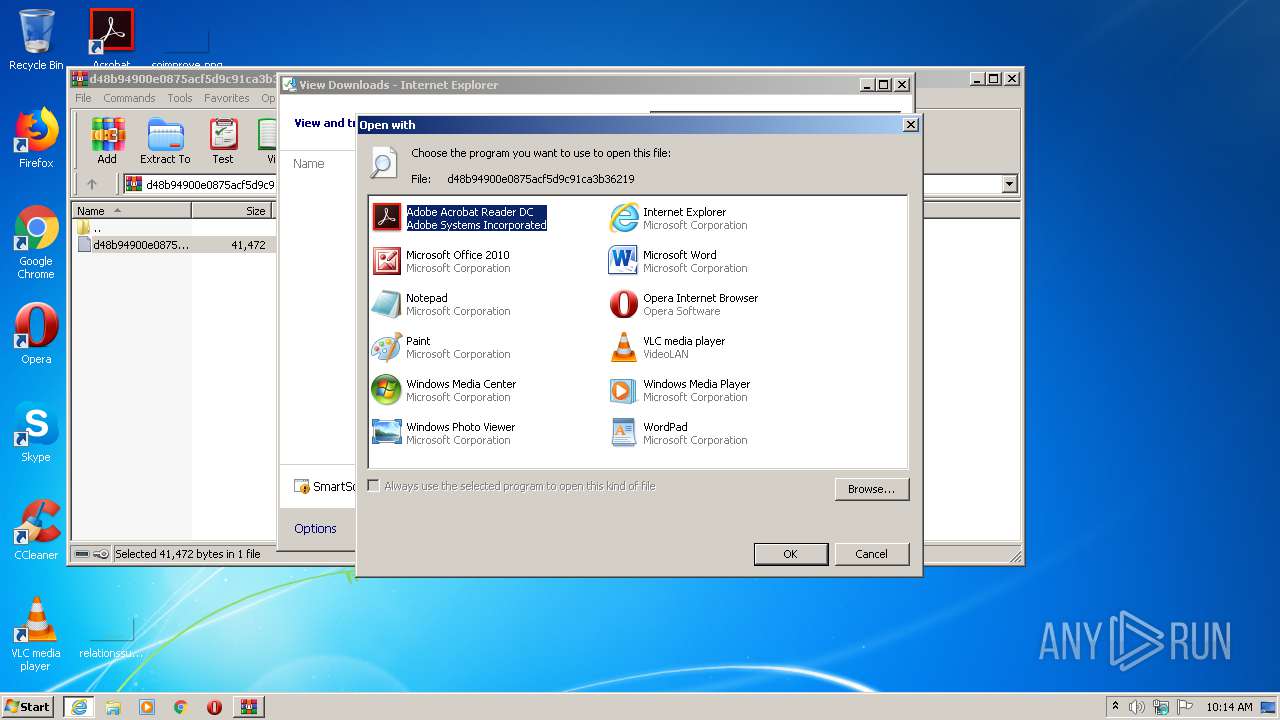
| 2680 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb2948.10324\d48b94900e0875acf5d9c91ca3b36219 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb2948.10324\d48b94900e0875acf5d9c91ca3b36219 | C:\Program Files\Internet Explorer\iexplore.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
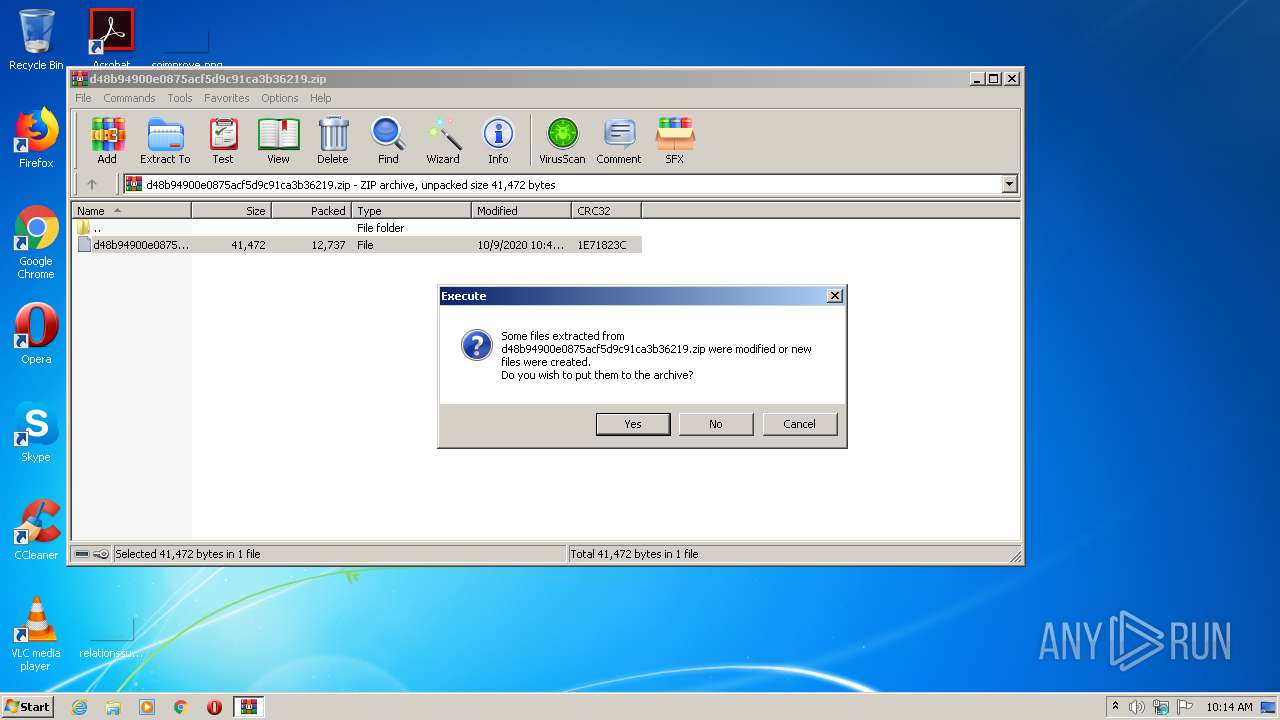
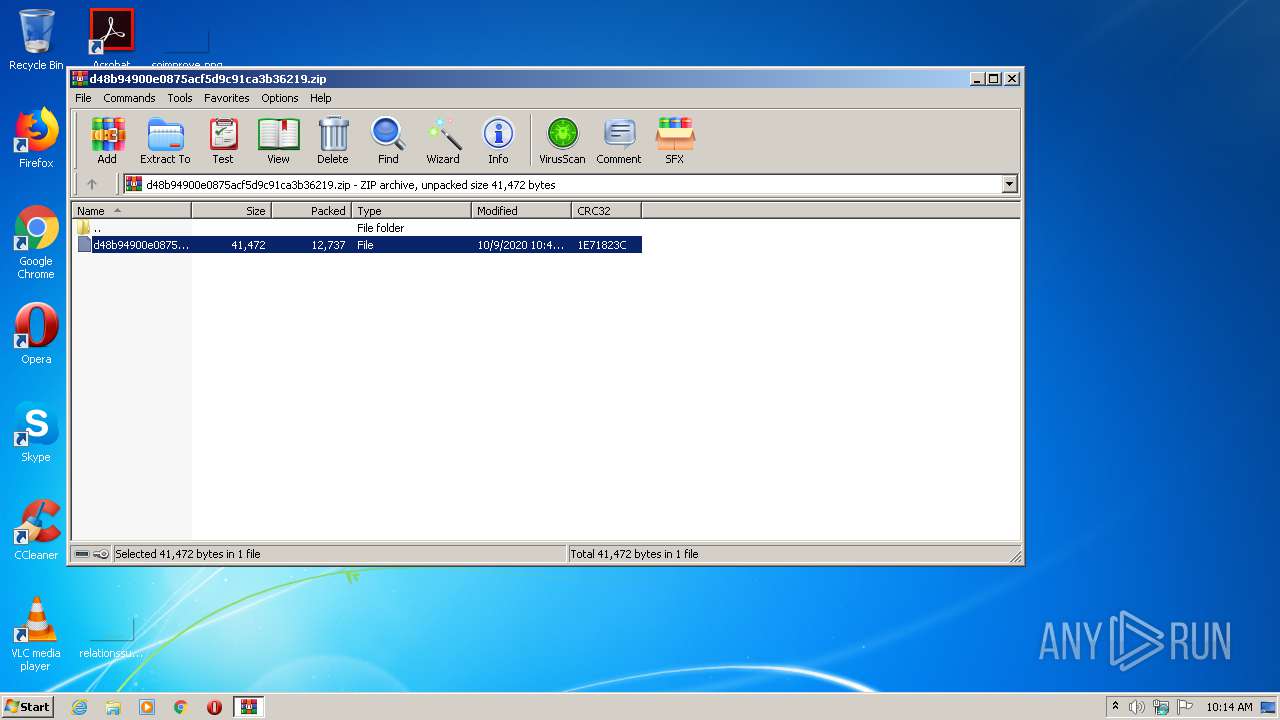
| 2948 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\d48b94900e0875acf5d9c91ca3b36219.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3268 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb2948.7428\d48b94900e0875acf5d9c91ca3b36219 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2688 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
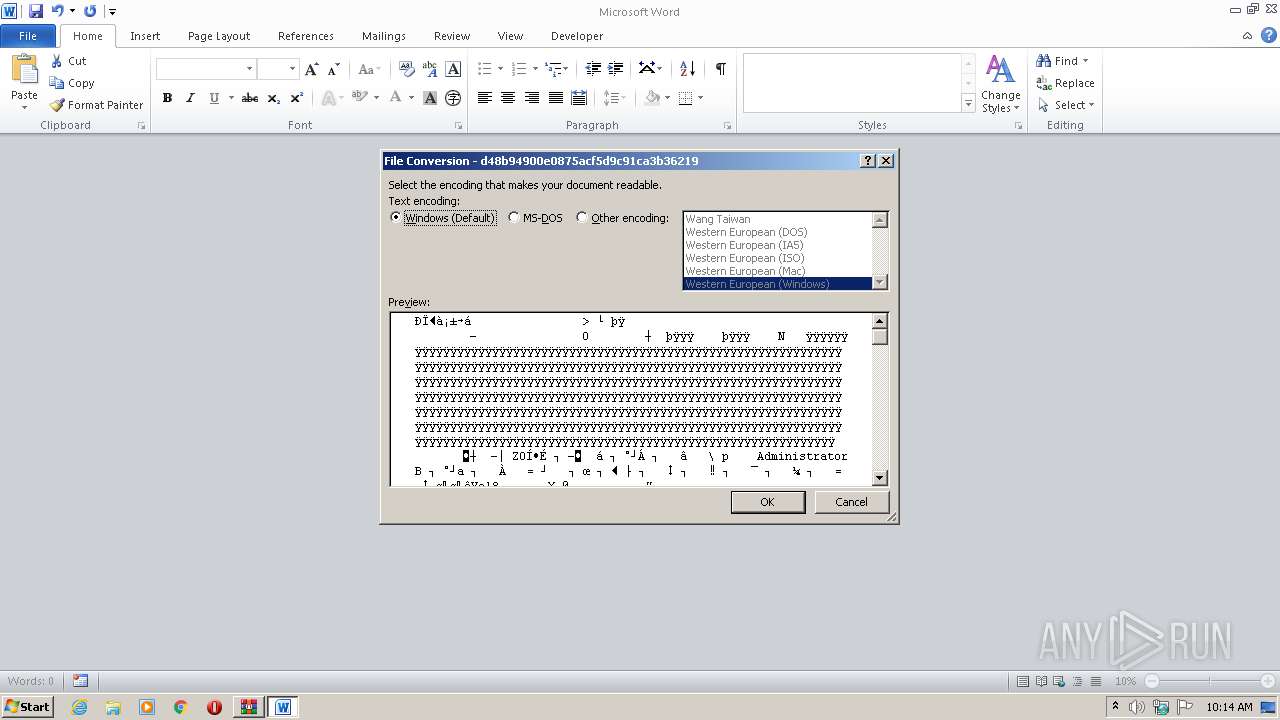
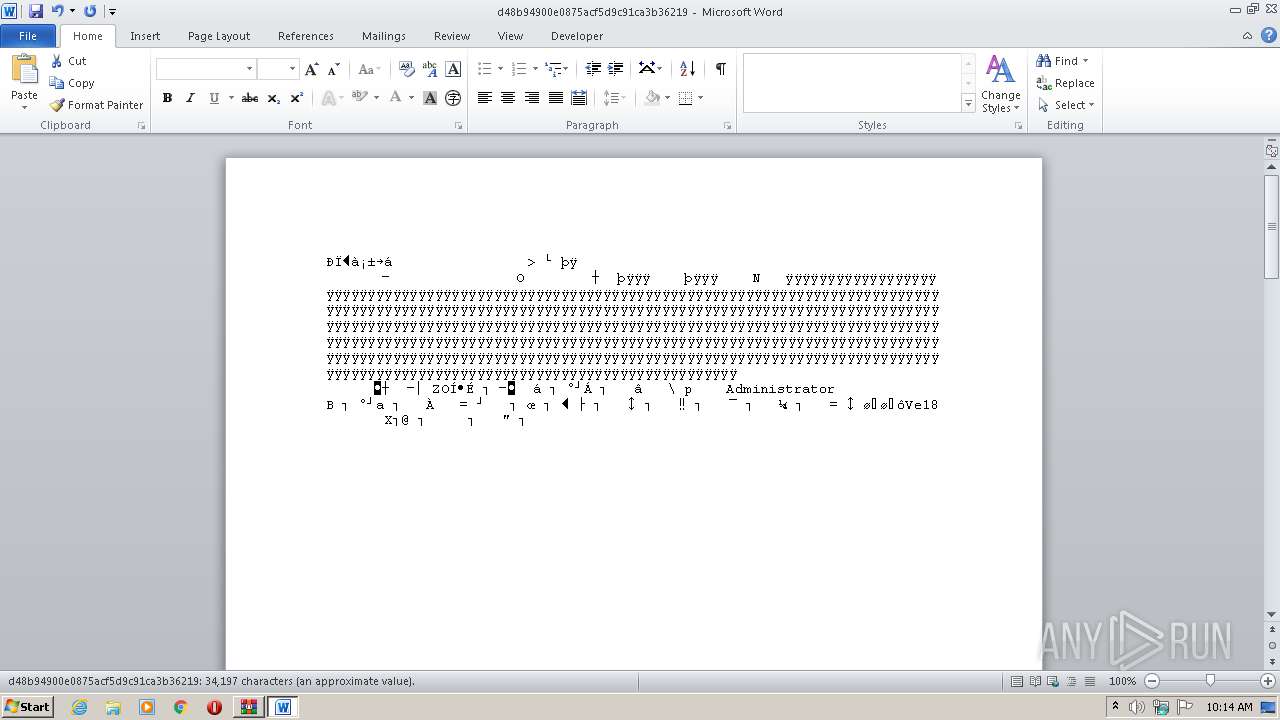
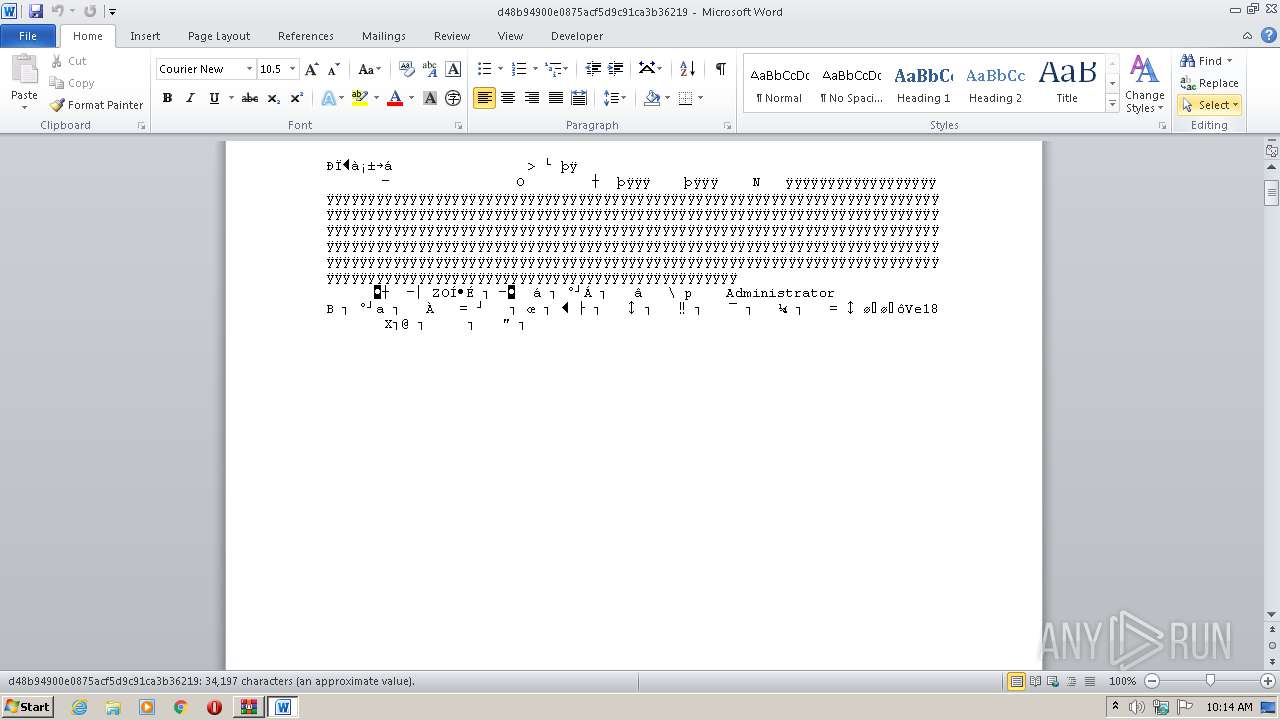
| 3548 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2948.7428\d48b94900e0875acf5d9c91ca3b36219" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3564 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb2948.10324\d48b94900e0875acf5d9c91ca3b36219 | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
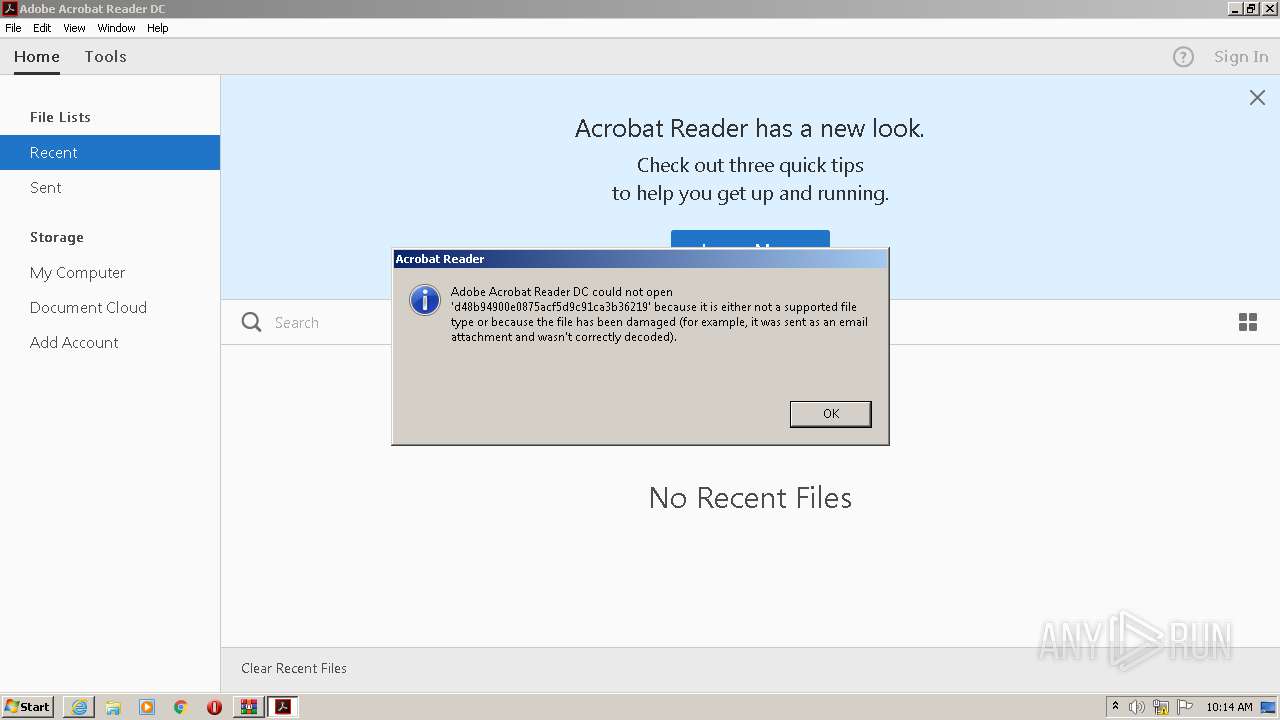
| 3752 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\Rar$DIb2948.10324\d48b94900e0875acf5d9c91ca3b36219" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb2948.10324\d48b94900e0875acf5d9c91ca3b36219" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
3 500
Read events
3 001
Write events
367
Delete events
132
Modification events
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\d48b94900e0875acf5d9c91ca3b36219.zip | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3268) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3268) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9D8D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF822C480BA7292587.TMP | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF062849555C0EF4E4.TMP | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFAC38CB85FFA0EEFD.TMP | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0001.doc | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0000.doc | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0002.doc | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3D3AA9C2-1116-48C2-BB3B-0A04FA92B321}.tmp | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{F3DFCC28-20CF-43F7-98CB-93290E0A891D}.tmp | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{2B66E7D4-97D7-481B-B74F-87B57A98096B}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report