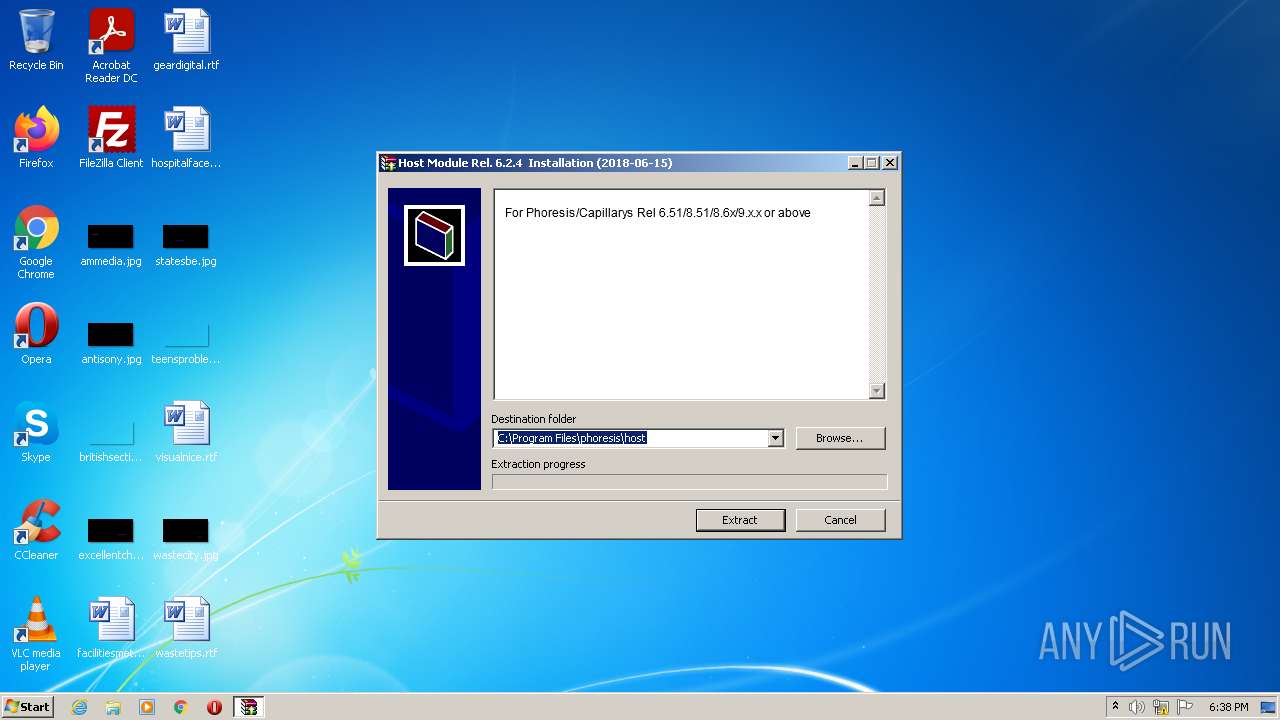
| File name: | Host Module Rel 6.24 Installation.exe |
| Full analysis: | https://app.any.run/tasks/eca0d8bf-5720-471c-9181-5c9e6eac25d7 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 18:38:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 5D78C49544D9336D7FED6E88552333ED |
| SHA1: | D5A8F341C26A3EA36187C9D4FBB336767E2C5A74 |
| SHA256: | D03D1A2EC18E381680BBDFA15A2B9F532997CA52198E057D277402972965CB89 |
| SSDEEP: | 24576:oFszWS5LyzKPvHNDaSZ3QDpGwVyRt+JuItFvIWsfTpx0BOU:oJzktDN3QhnbtFvIWsfVi7 |
MALICIOUS
Drops executable file immediately after starts
- Host Module Rel 6.24 Installation.exe (PID: 500)
SUSPICIOUS
Reads Microsoft Outlook installation path
- Host Module Rel 6.24 Installation.exe (PID: 3660)
Checks supported languages
- Host Module Rel 6.24 Installation.exe (PID: 3660)
- Host Module Rel 6.24 Installation.exe (PID: 500)
Application launched itself
- Host Module Rel 6.24 Installation.exe (PID: 3660)
Reads internet explorer settings
- Host Module Rel 6.24 Installation.exe (PID: 3660)
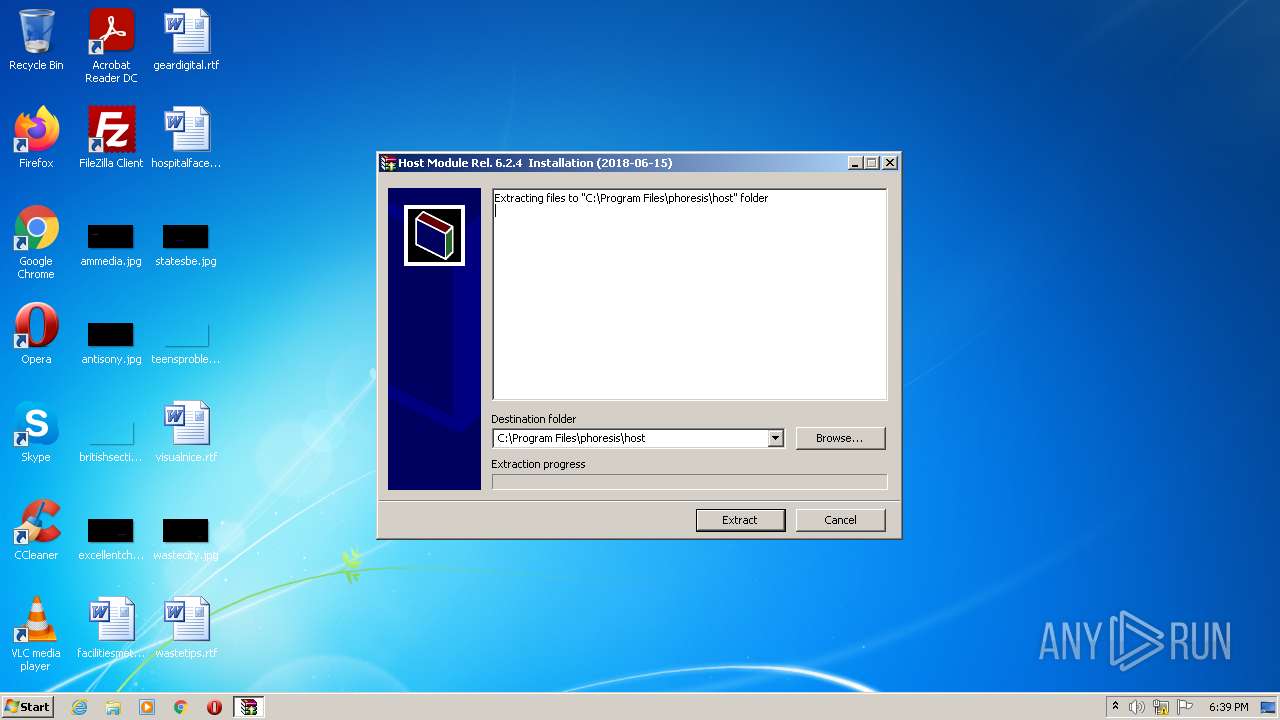
Creates files in the program directory
- Host Module Rel 6.24 Installation.exe (PID: 500)
Executable content was dropped or overwritten
- Host Module Rel 6.24 Installation.exe (PID: 500)
Drops a file that was compiled in debug mode
- Host Module Rel 6.24 Installation.exe (PID: 500)
Reads the computer name
- Host Module Rel 6.24 Installation.exe (PID: 3660)
- Host Module Rel 6.24 Installation.exe (PID: 500)
Creates a directory in Program Files
- Host Module Rel 6.24 Installation.exe (PID: 500)
Drops a file with too old compile date
- Host Module Rel 6.24 Installation.exe (PID: 500)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0xb4b5 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 90624 |
| CodeSize: | 72192 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2011:01:27 07:34:32+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jan-2011 06:34:32 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Jan-2011 06:34:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000118E0 | 0x00011A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5511 |
.rdata | 0x00013000 | 0x00001C15 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.86778 |
.data | 0x00015000 | 0x0000FF2C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.51849 |
.CRT | 0x00025000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.213101 |
.rsrc | 0x00026000 | 0x00004078 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.6547 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.24143 | 556 | UNKNOWN | English - United States | RT_STRING |
8 | 3.26996 | 974 | UNKNOWN | English - United States | RT_STRING |
9 | 3.04375 | 530 | UNKNOWN | English - United States | RT_STRING |
10 | 3.16254 | 776 | UNKNOWN | English - United States | RT_STRING |
11 | 3.06352 | 380 | UNKNOWN | English - United States | RT_STRING |
100 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
38
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 500 | "C:\Users\admin\AppData\Local\Temp\Host Module Rel 6.24 Installation.exe" -el -s2 "-dC:\Program Files\phoresis\host" "-p" "-sp" | C:\Users\admin\AppData\Local\Temp\Host Module Rel 6.24 Installation.exe | Host Module Rel 6.24 Installation.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3660 | "C:\Users\admin\AppData\Local\Temp\Host Module Rel 6.24 Installation.exe" | C:\Users\admin\AppData\Local\Temp\Host Module Rel 6.24 Installation.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 263
Read events
1 248
Write events
15
Delete events
0
Modification events
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3660) Host Module Rel 6.24 Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
4
Suspicious files
1
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocEng\user3.txt | text | |
MD5:— | SHA256:— | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocIta\DVSE_LOG.TXT | text | |
MD5:C271B91E1DF40D1FFB4417AB7A70EDFD | SHA256:3E471447AB6F684EE0A31AF62C450F67DF9F0ED55987A48290EBD311D59AB256 | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocIta\user3.txt | text | |
MD5:— | SHA256:— | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocIta\DVSE.LOG | text | |
MD5:C271B91E1DF40D1FFB4417AB7A70EDFD | SHA256:3E471447AB6F684EE0A31AF62C450F67DF9F0ED55987A48290EBD311D59AB256 | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocIta\DiagrammaWorklist2.jpg | image | |
MD5:C69DC131BDF49C7BC8D6ED186B913AD4 | SHA256:2CBB28A949D5E20B798BE38A30422D9A8C86D8C42341D395FF025EB3E37A0541 | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocIta\DiagrammaWorklist.jpg | image | |
MD5:5FF10478CF64F484BB4C1106A4B83CFC | SHA256:30B554EDE7527B38D3EEE72ADA0CE924D2508F92559E0FC2AAE19B31B3C82995 | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocEng\PHORESIS ENG.txt | text | |
MD5:F0FC113B0FA48DEF888C480CA29377F7 | SHA256:199CFF968FBEC396212393F6AFD3FE9BE01BD4369C928C2A82251AF2C0882066 | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\ijl_licence.txt | text | |
MD5:4AF4A6BBAE208290B7510E108F3FCB11 | SHA256:EC9F26A3A880586295C245A0B35AE8A3AD42F7CC2CC81ADCA722669636AABBCC | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocIta\Specifiche File Tranfer Finsiel.txt | text | |
MD5:02C07D207544C3DEA79AEB915378B823 | SHA256:4A44E0C0E22A5AD6ACD239E0D649E3242B094243FEA9DC9556488CDDA4851F2B | |||
| 500 | Host Module Rel 6.24 Installation.exe | C:\Program Files\phoresis\host\DocIta\SoftwareTeam.txt | text | |
MD5:F7505465D2310A88F8F3DDB1148A4B16 | SHA256:7D41AC42DBDB9C01768591230EC744C605F19F4D6BECE9485F9CED2897F27B79 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report