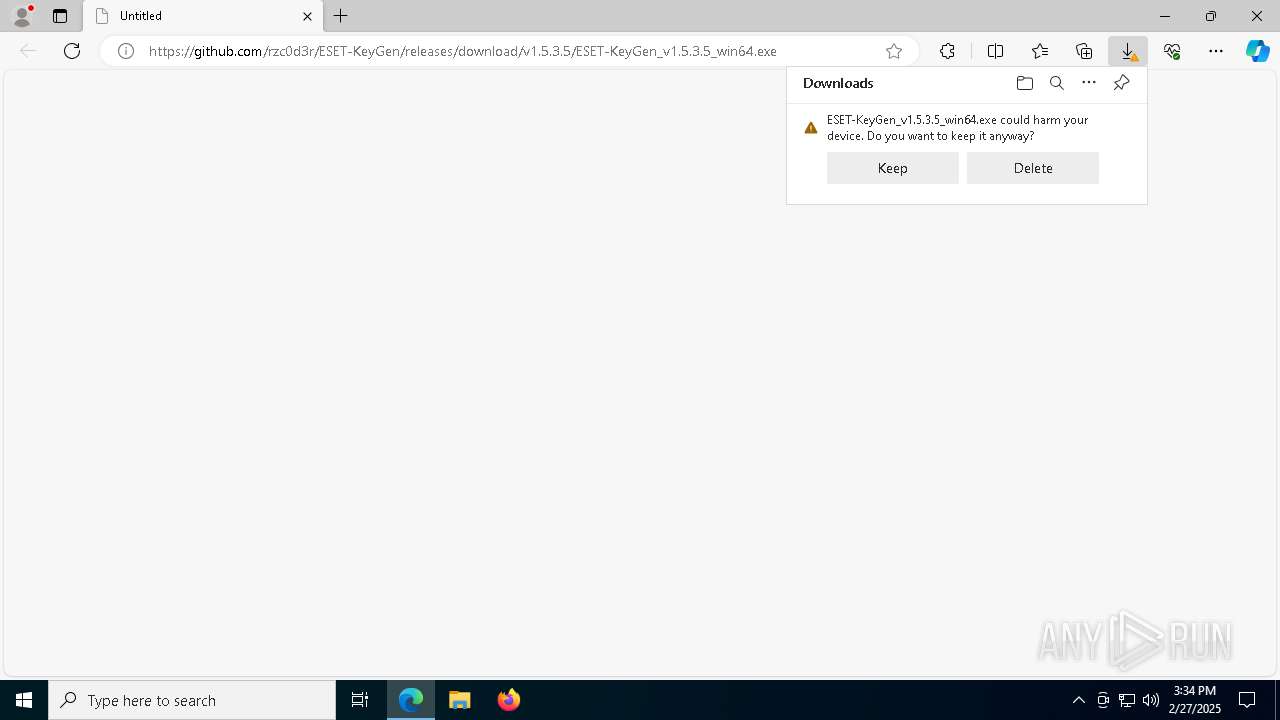
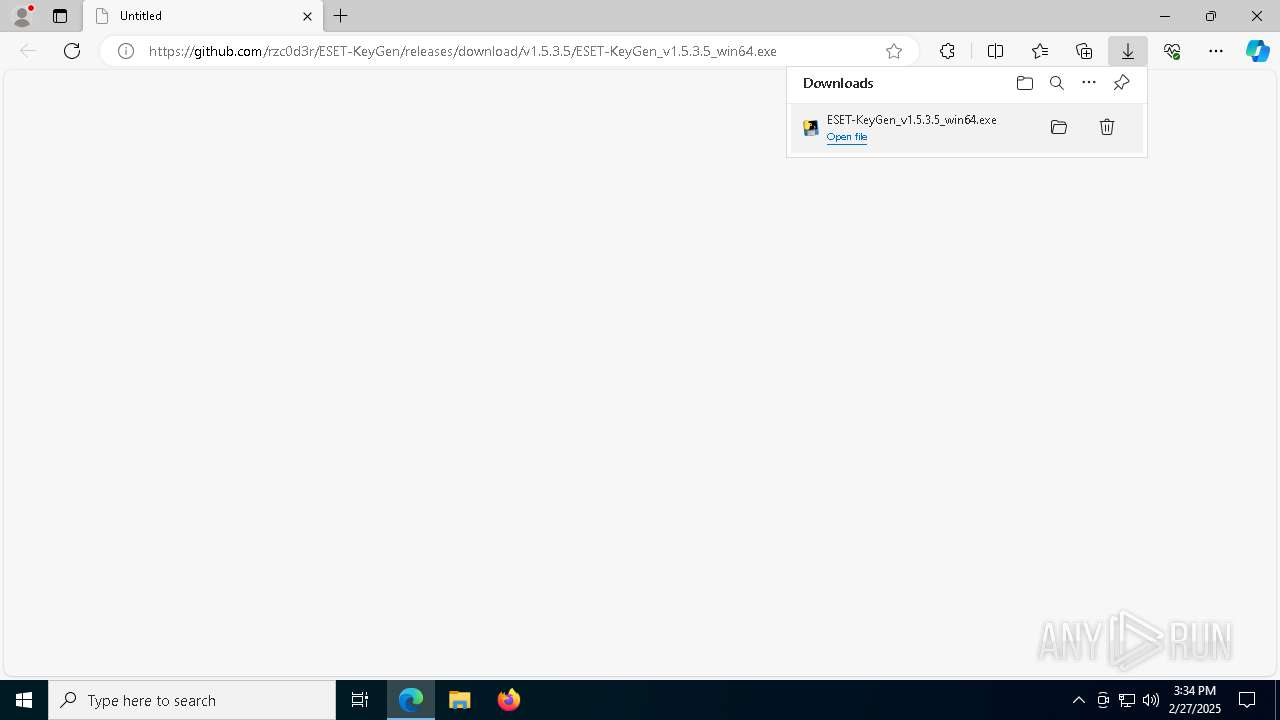
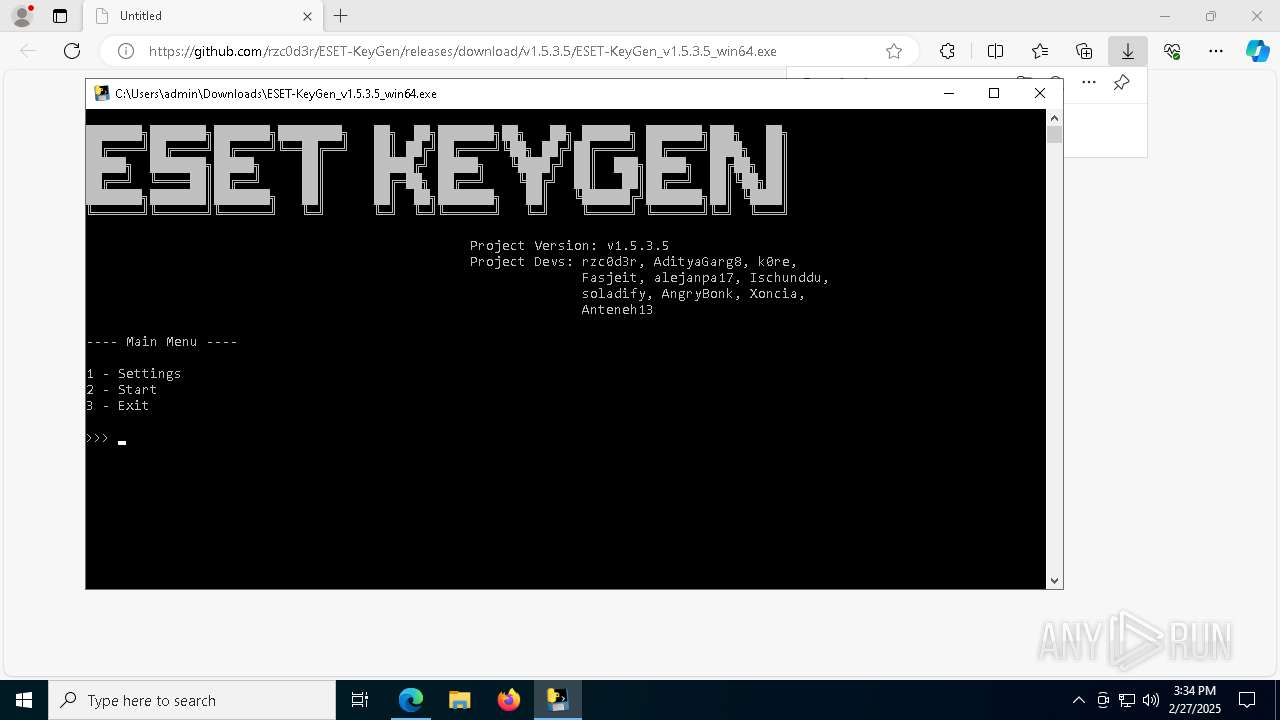
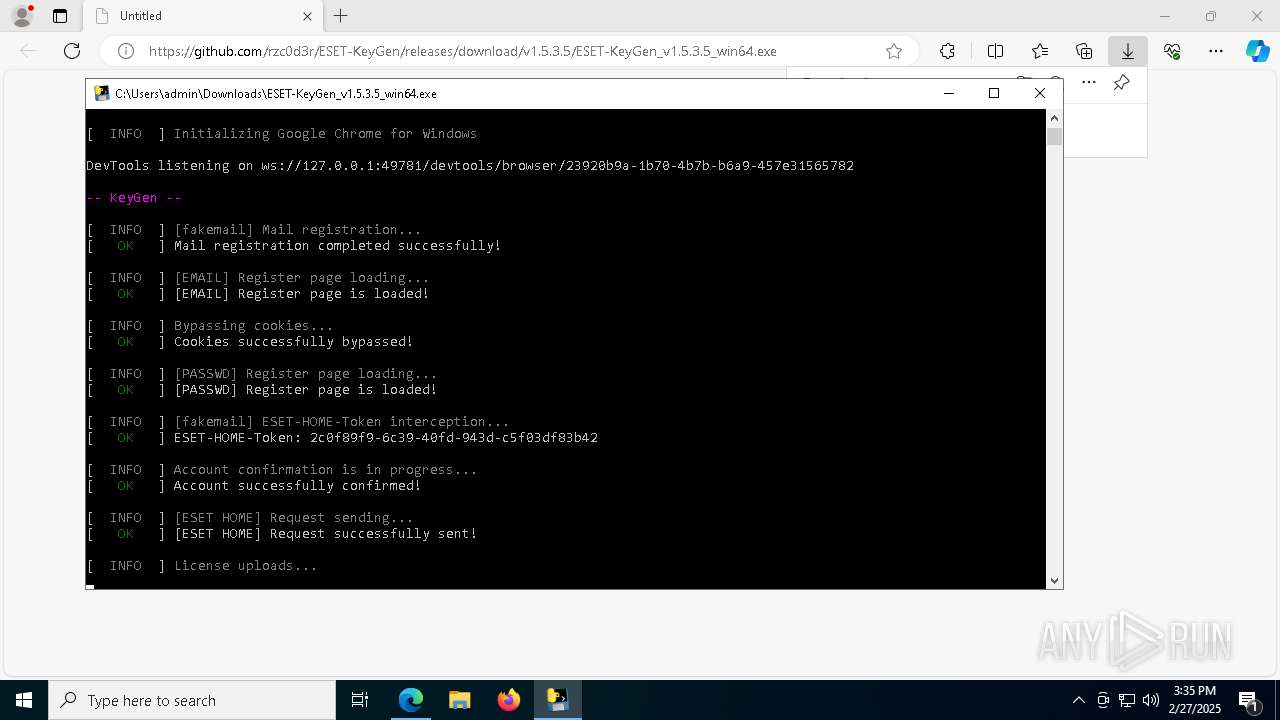
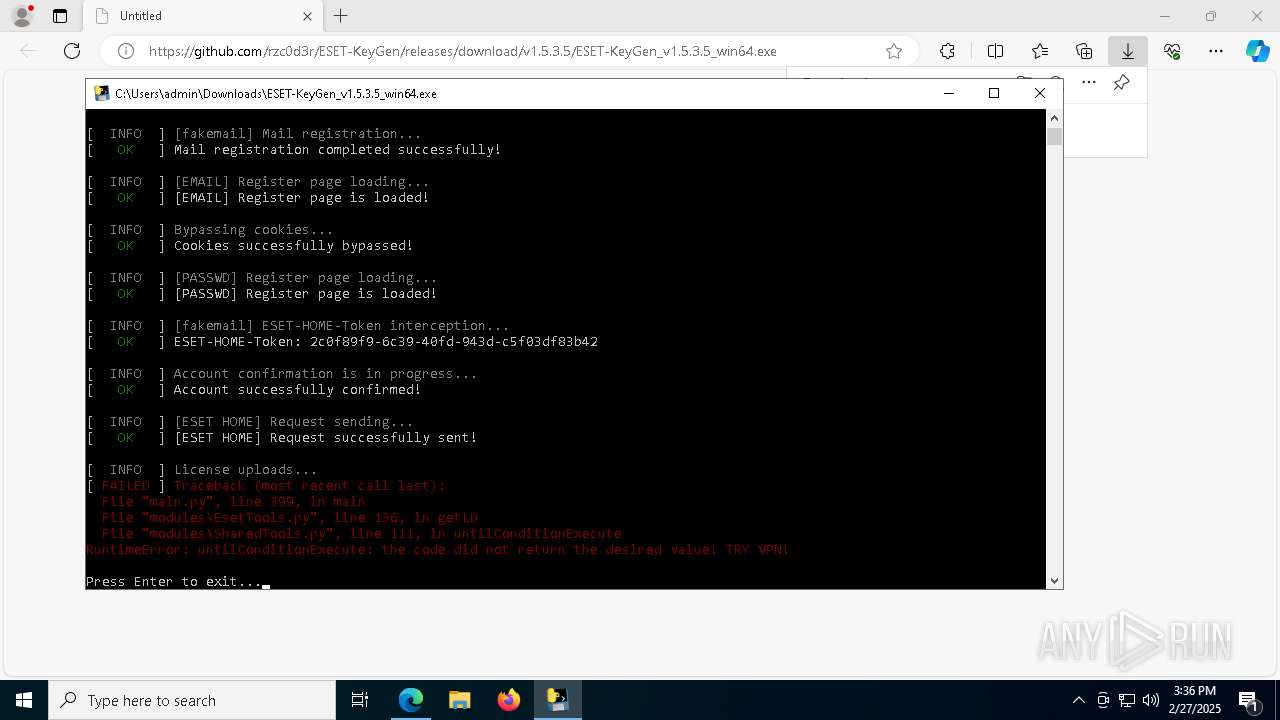
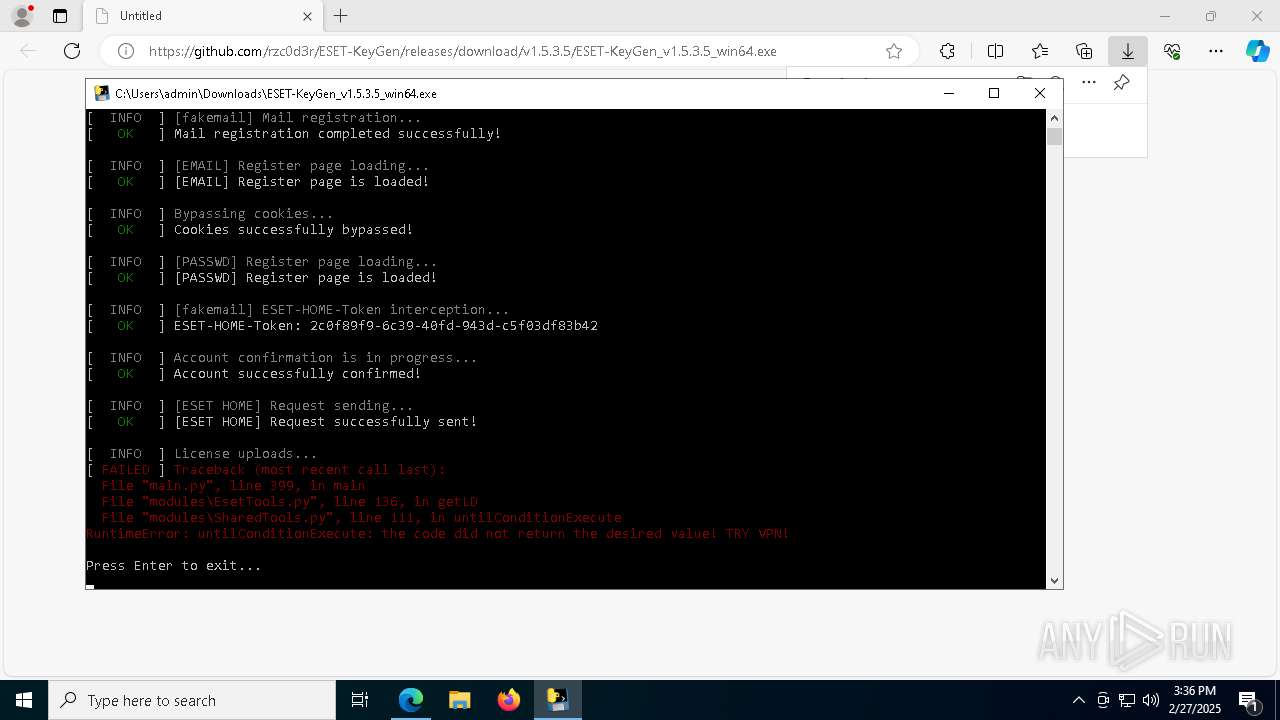
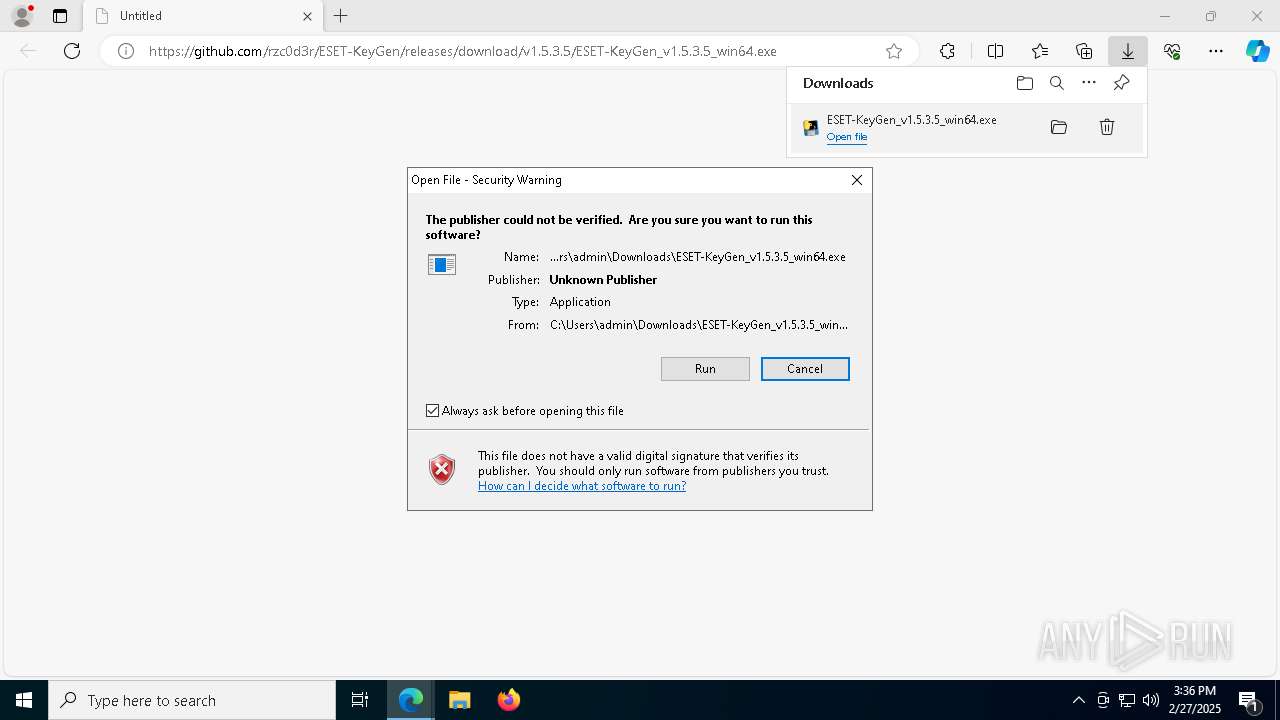
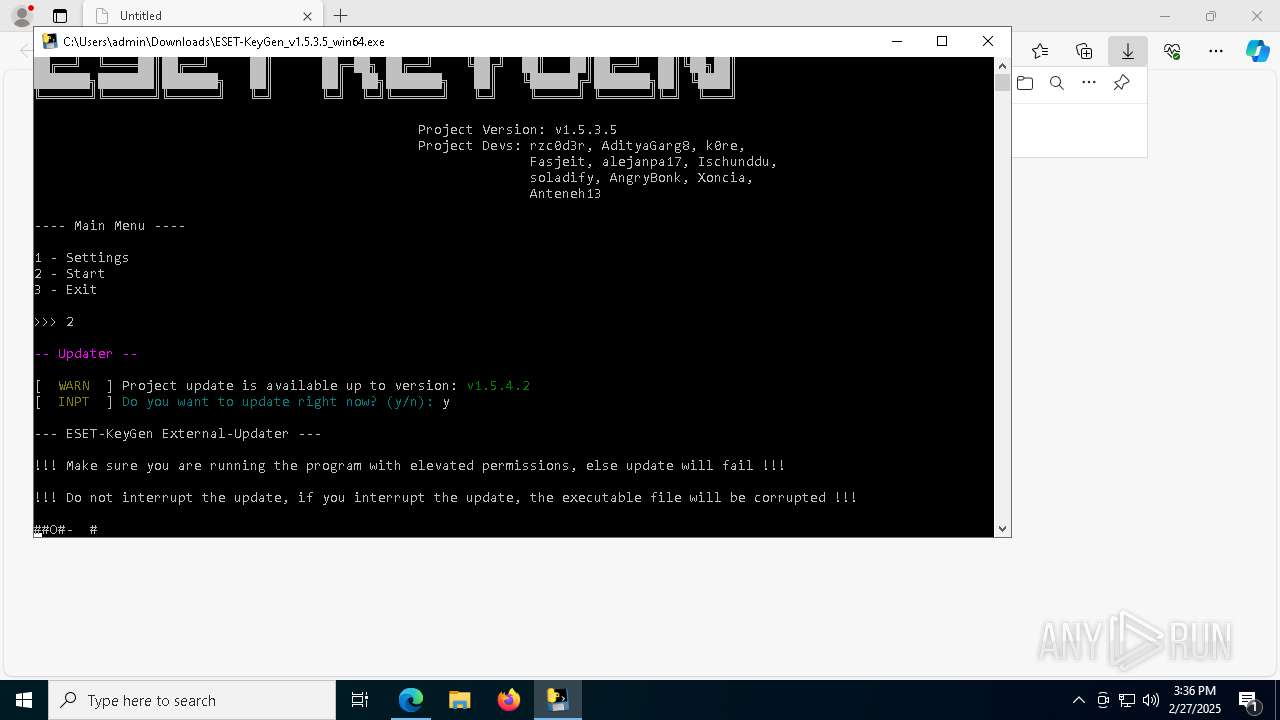
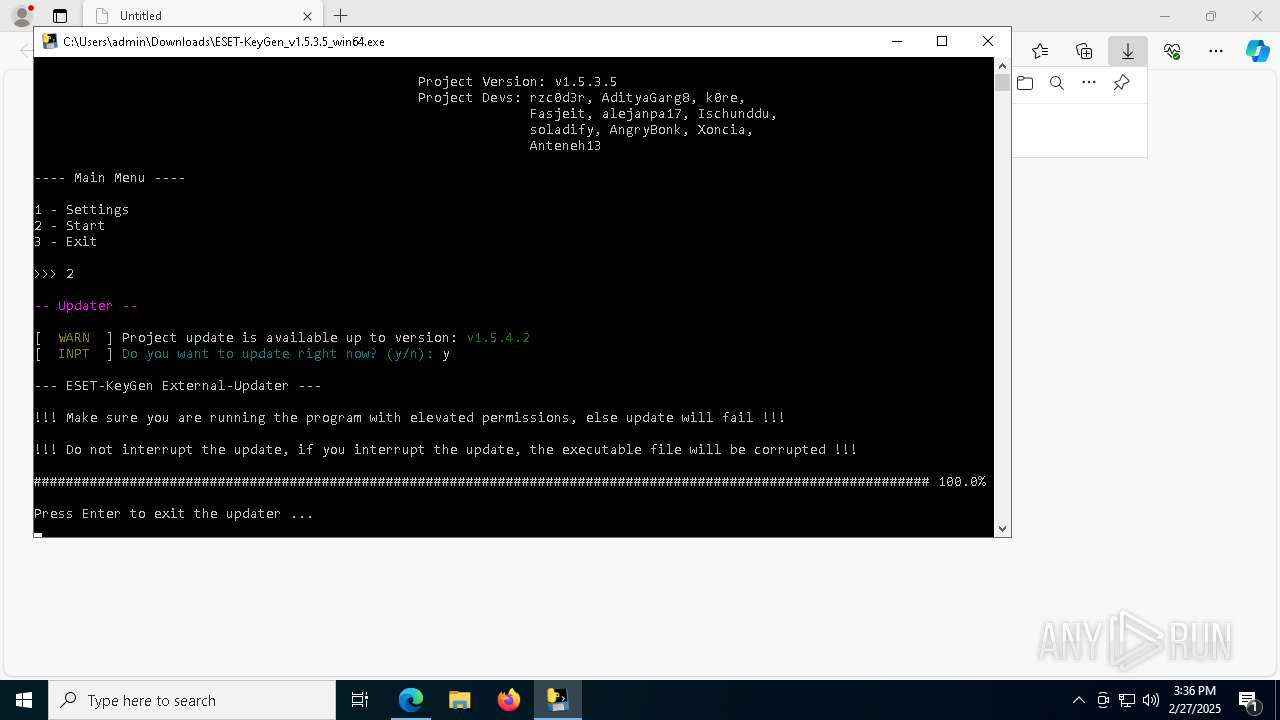
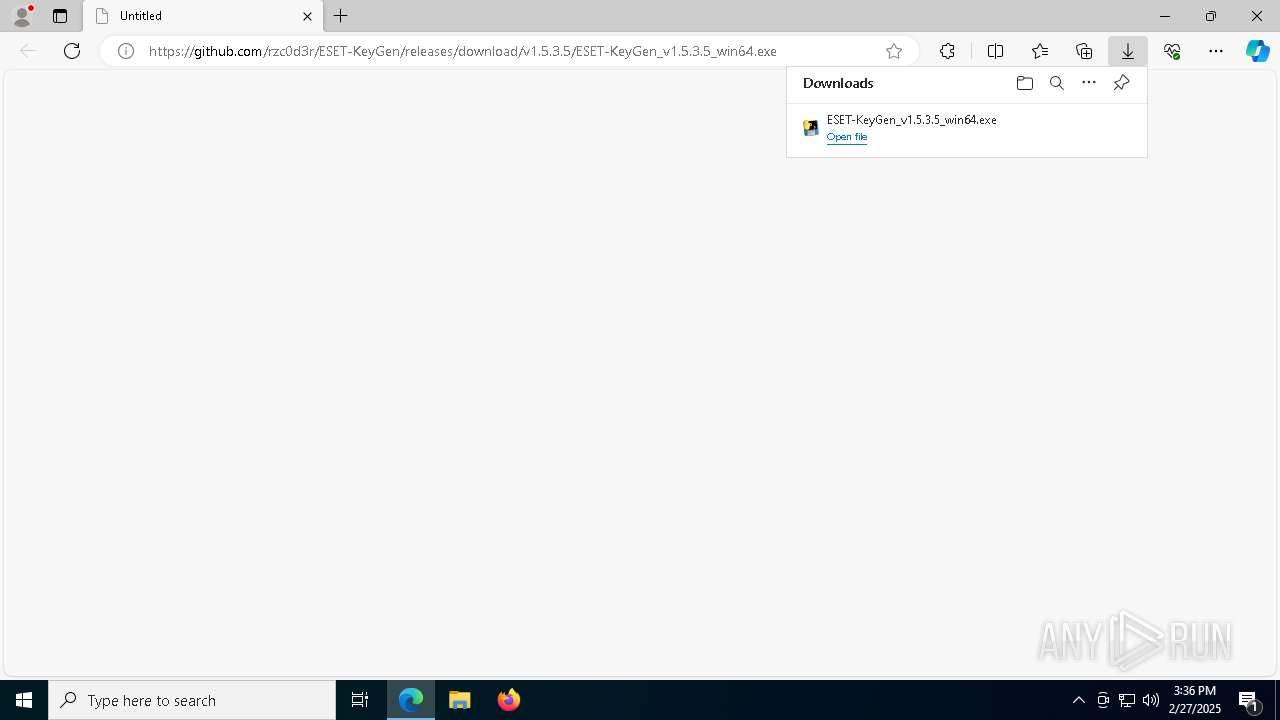
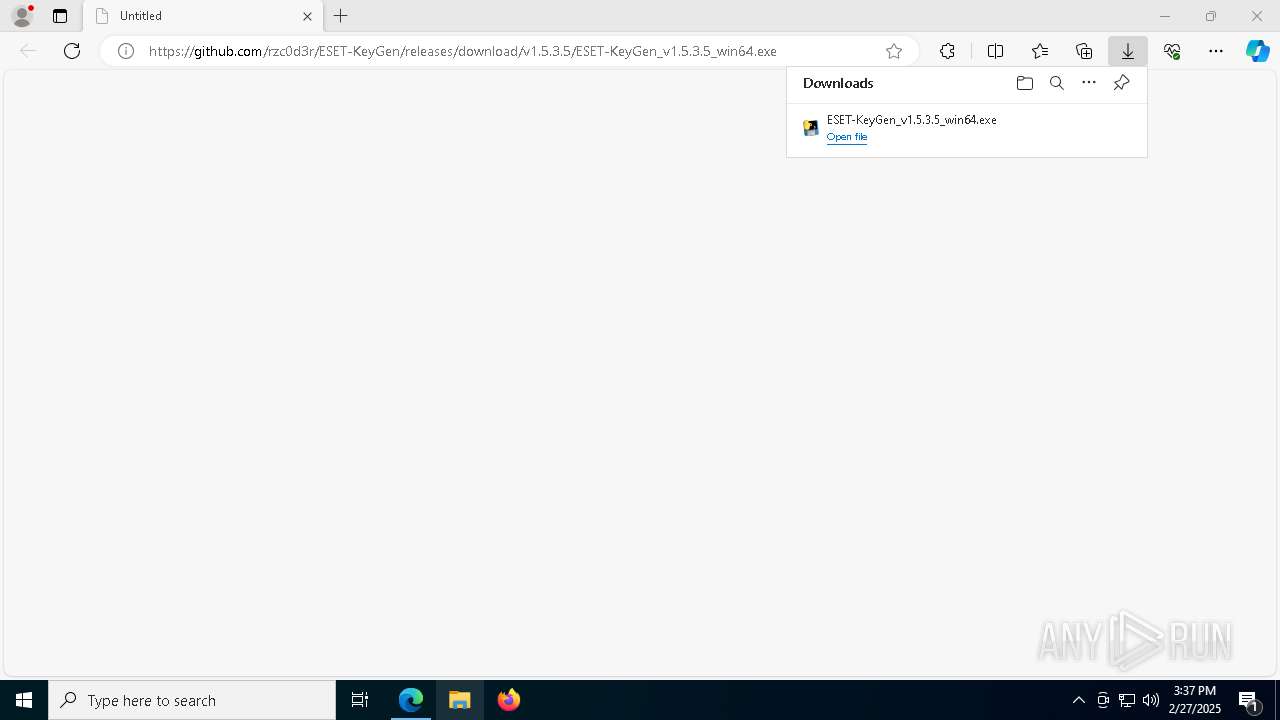
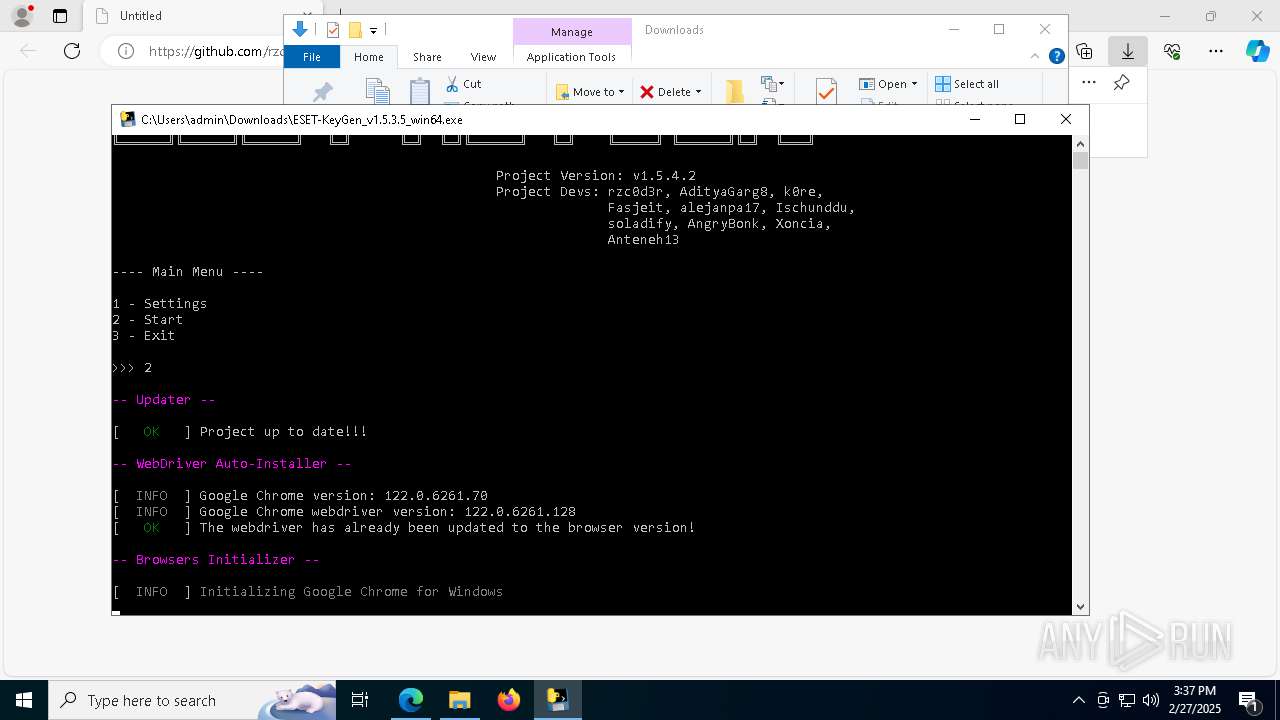
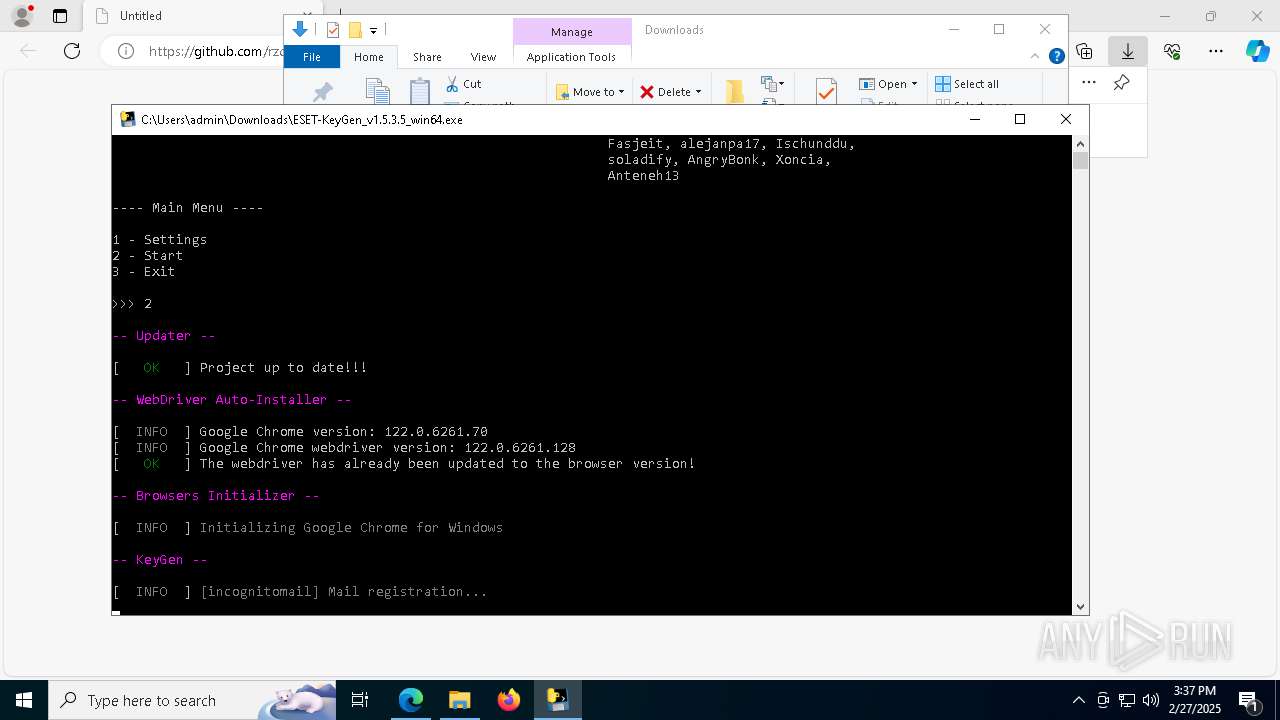
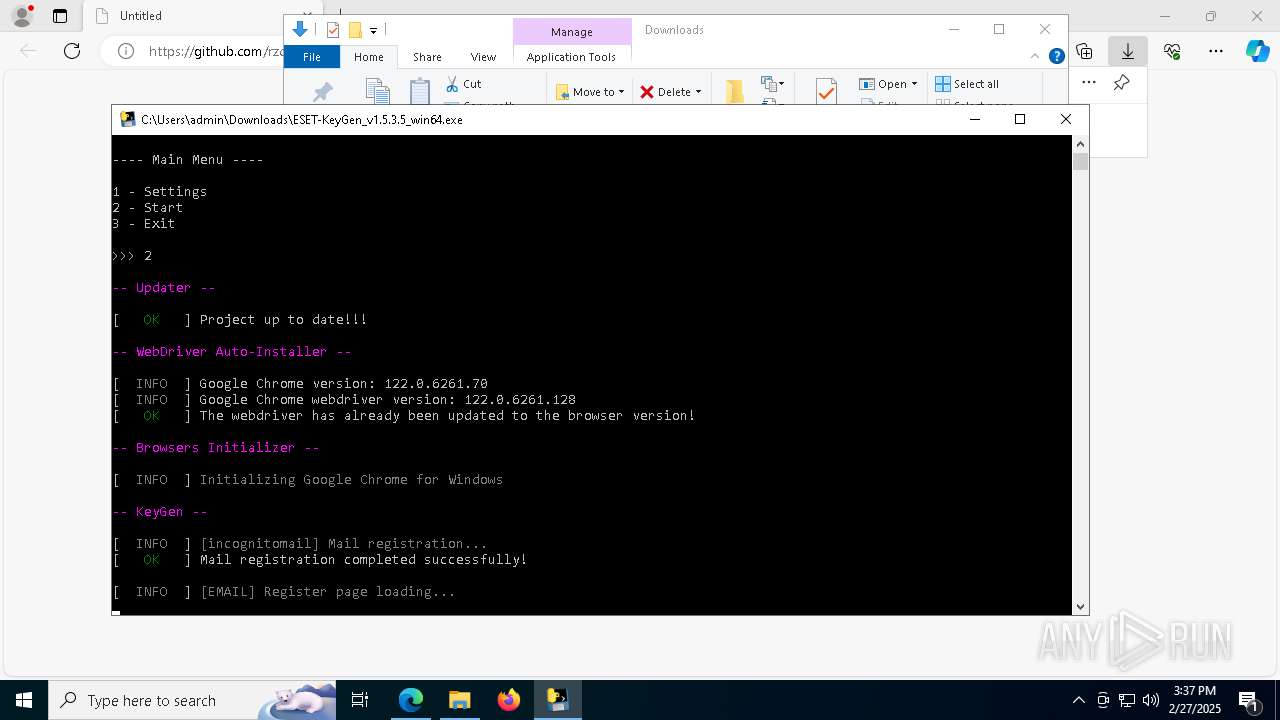
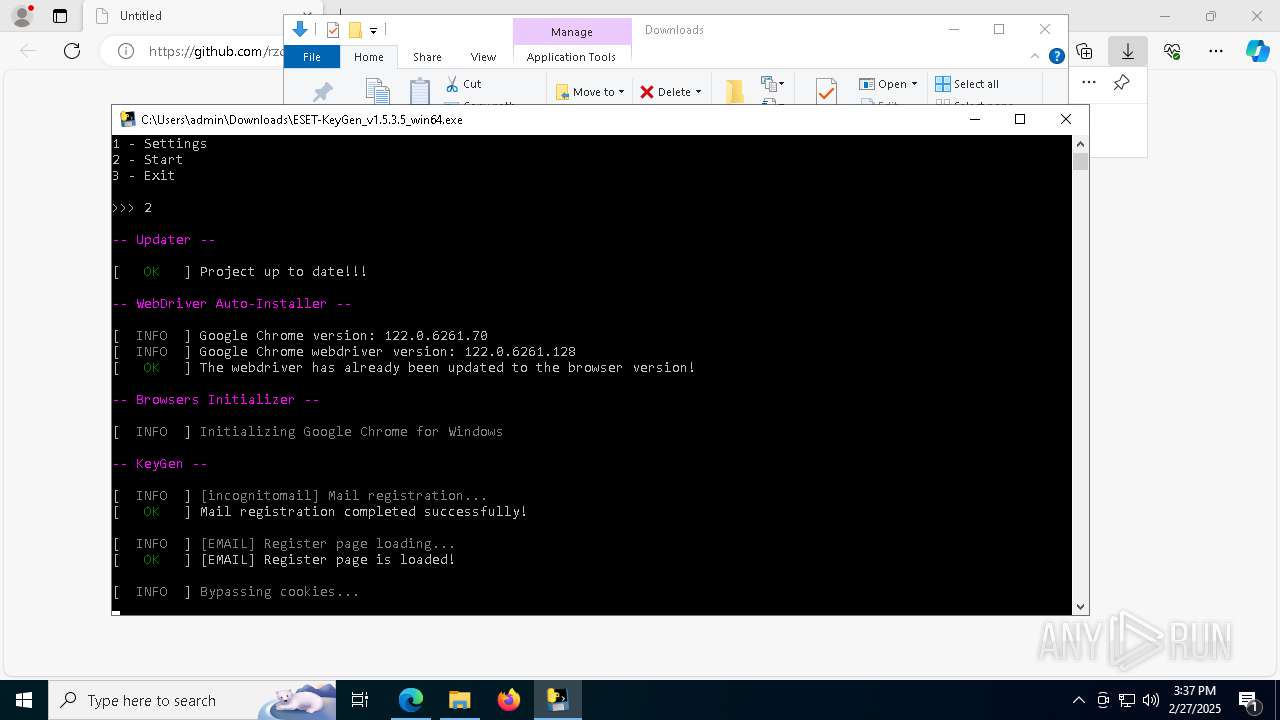
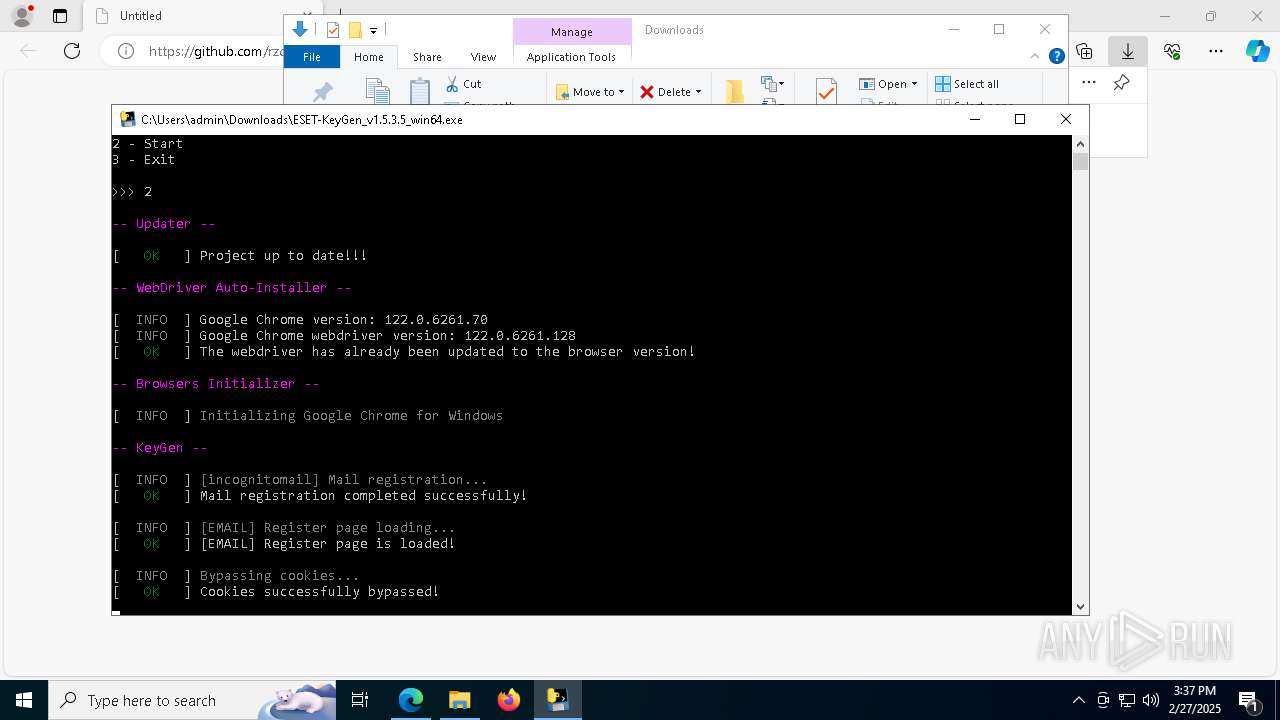
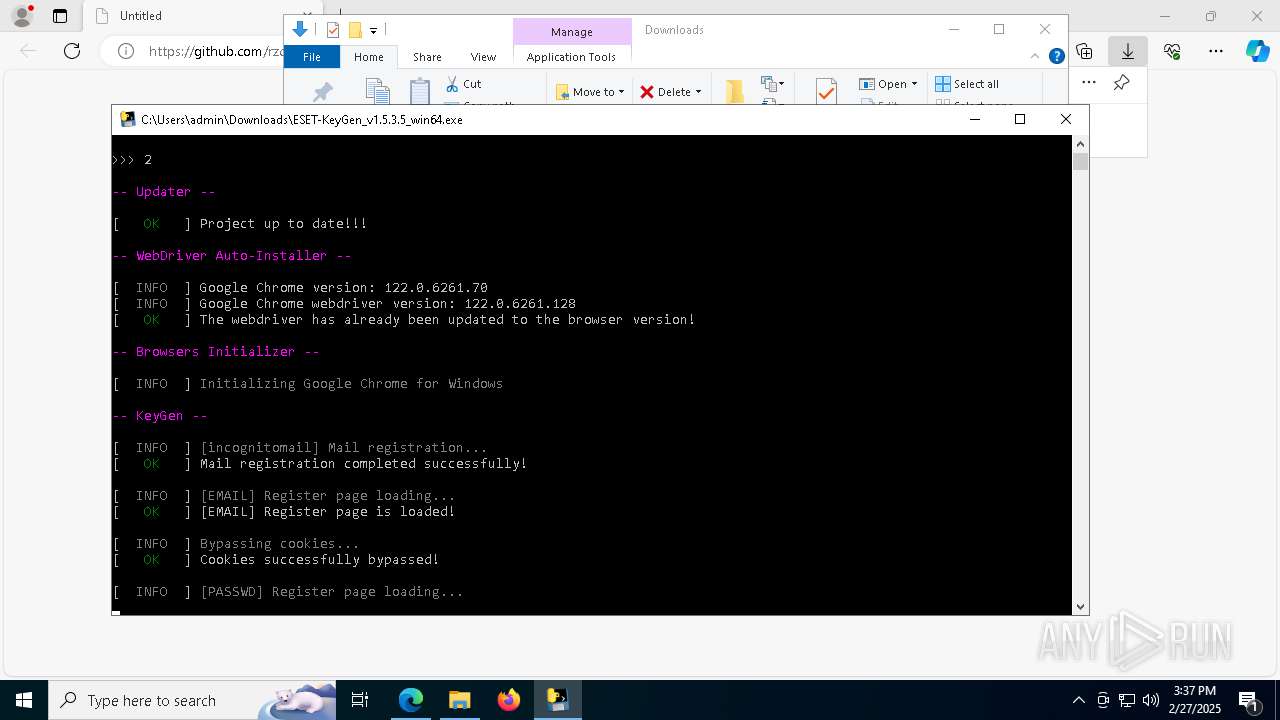
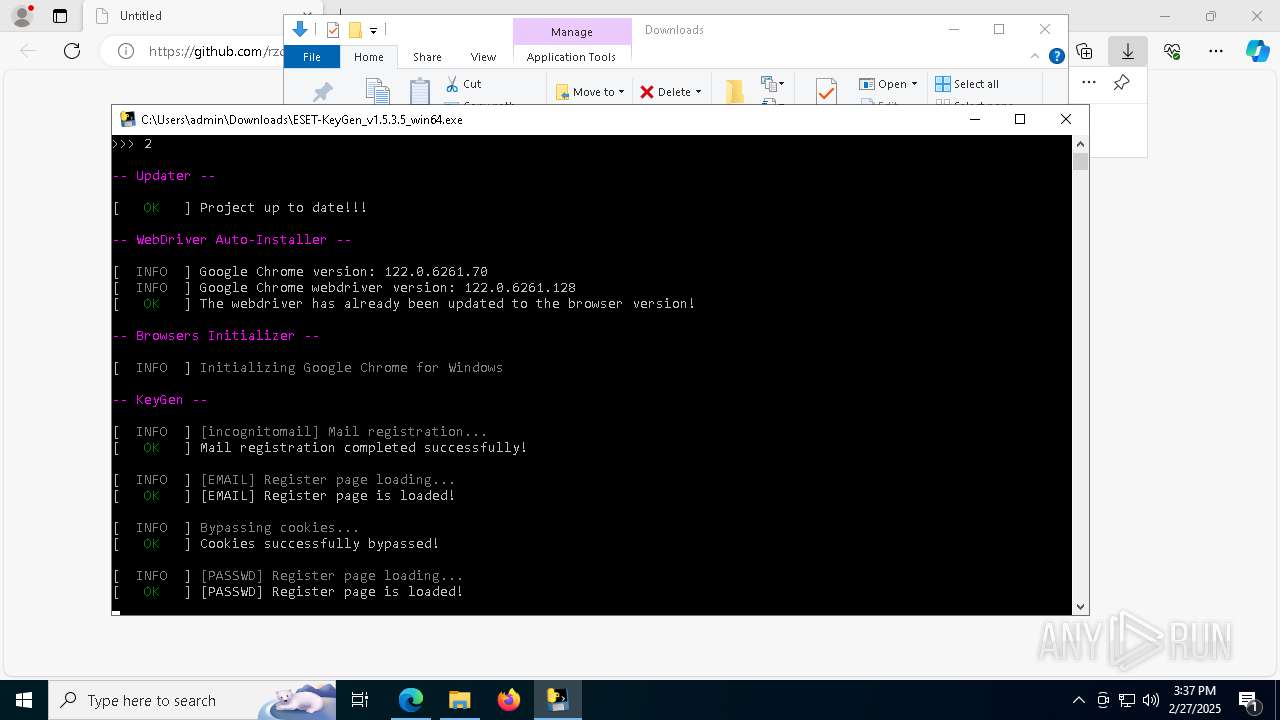
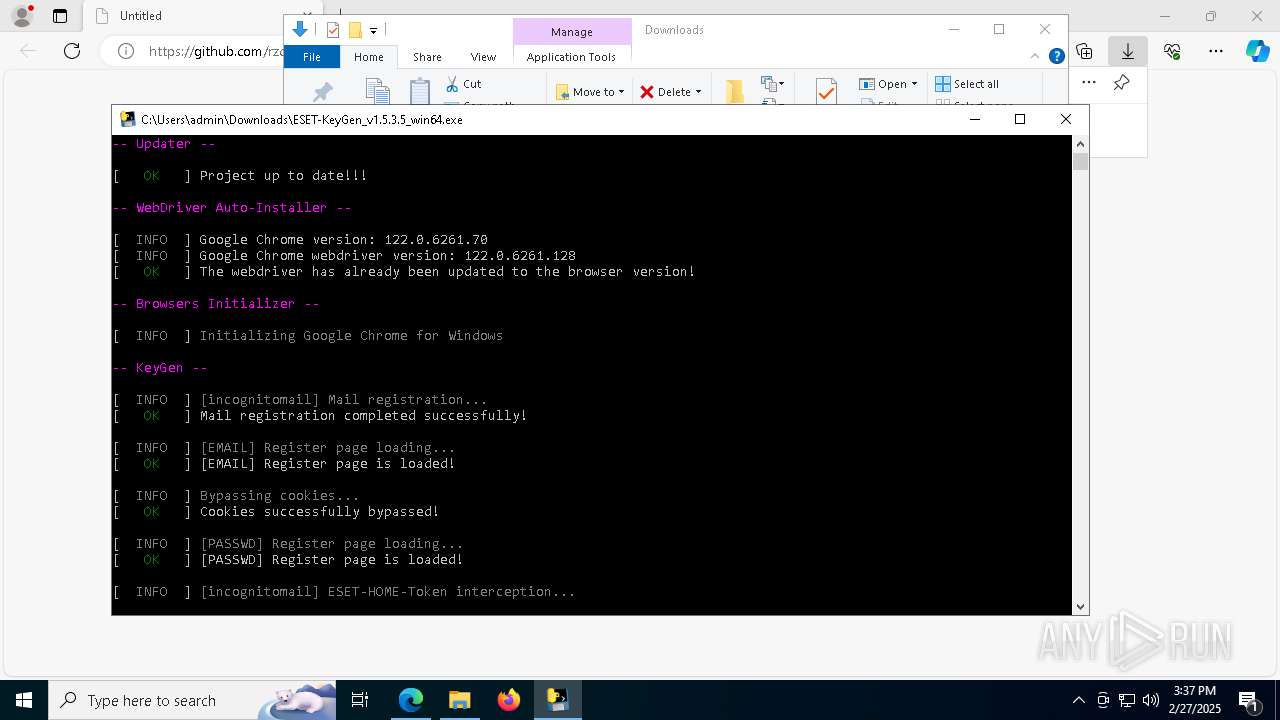
| URL: | https://github.com/rzc0d3r/ESET-KeyGen/releases/download/v1.5.3.5/ESET-KeyGen_v1.5.3.5_win64.exe |
| Full analysis: | https://app.any.run/tasks/db9b87ba-2569-4fb5-8639-d60c7203804a |
| Verdict: | Malicious activity |
| Analysis date: | February 27, 2025, 15:34:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 32ECCEA52C062C4121FE3377A27D427D |
| SHA1: | EAF5C7FB52883C62311BC58A06F4AEA9BEDAF98F |
| SHA256: | D039F55F60DF00D61550C4F7E098FA3CE7B04791D9415B6C3123975FA093D04F |
| SSDEEP: | 3:N8tEdnurQKqjLBJMkCmeMfgRIkjL6TUCMhLN:2u4rQX/MseMoIS6T3MdN |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
Executable content was dropped or overwritten
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
Process drops python dynamic module
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
Process drops legitimate windows executable
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
Loads Python modules
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 9168)
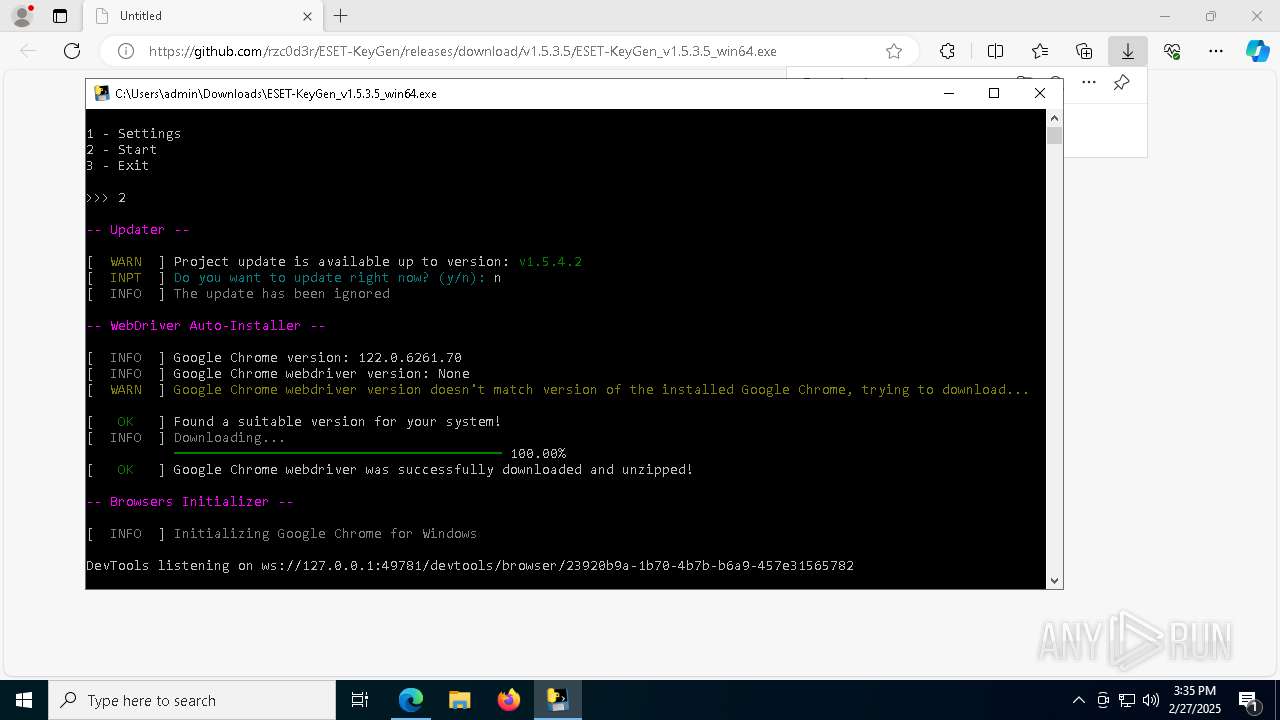
Starts CMD.EXE for commands execution
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 9168)
Application launched itself
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
Executing commands from a ".bat" file
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4692)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 7428)
- msedge.exe (PID: 7708)
- msedge.exe (PID: 6388)
Application launched itself
- msedge.exe (PID: 7428)
- chrome.exe (PID: 9156)
- chrome.exe (PID: 2244)
Reads the computer name
- identity_helper.exe (PID: 6048)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- chromedriver.exe (PID: 4944)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
Checks supported languages
- identity_helper.exe (PID: 6048)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- ShellExperienceHost.exe (PID: 8844)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
- curl.exe (PID: 5436)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 9168)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8744)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8744)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- slui.exe (PID: 6620)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8744)
- BackgroundTransferHost.exe (PID: 8476)
- BackgroundTransferHost.exe (PID: 8912)
- BackgroundTransferHost.exe (PID: 7172)
- BackgroundTransferHost.exe (PID: 9184)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8744)
- slui.exe (PID: 5720)
The sample compiled with english language support
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- msedge.exe (PID: 6388)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
Create files in a temporary directory
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
- chromedriver.exe (PID: 4944)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 3364)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
Drops encrypted JS script (Microsoft Script Encoder)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
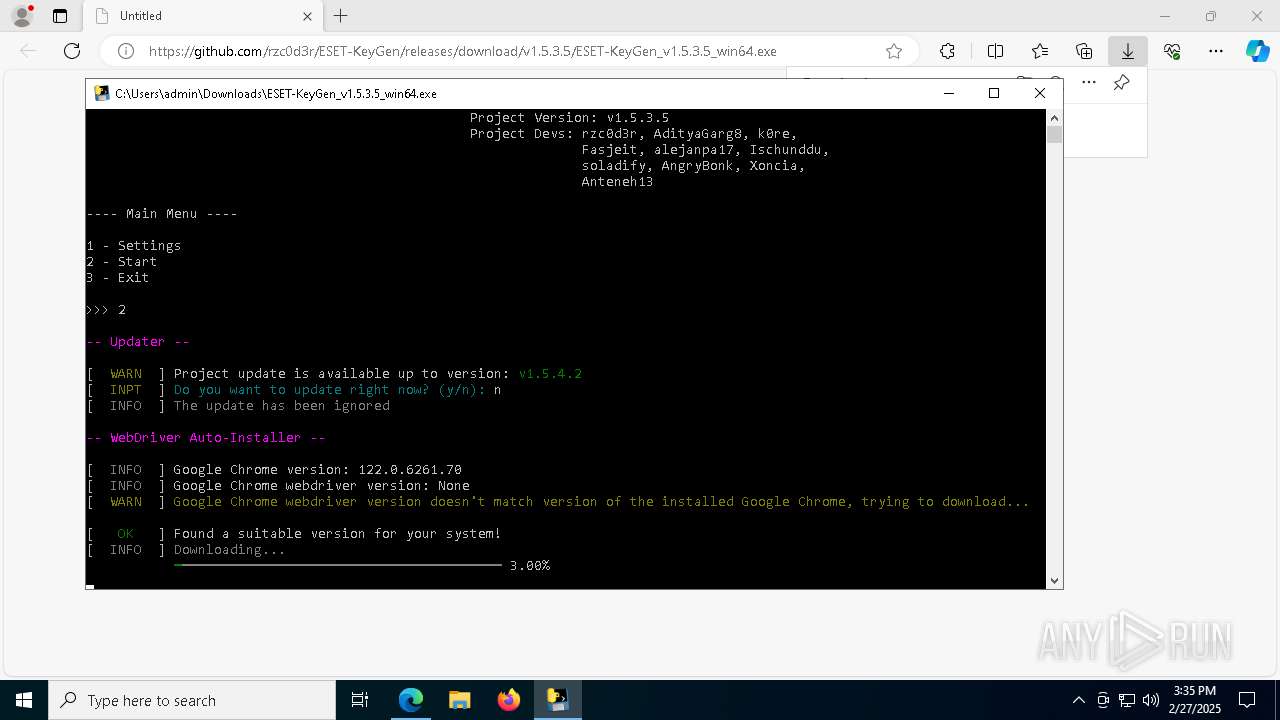
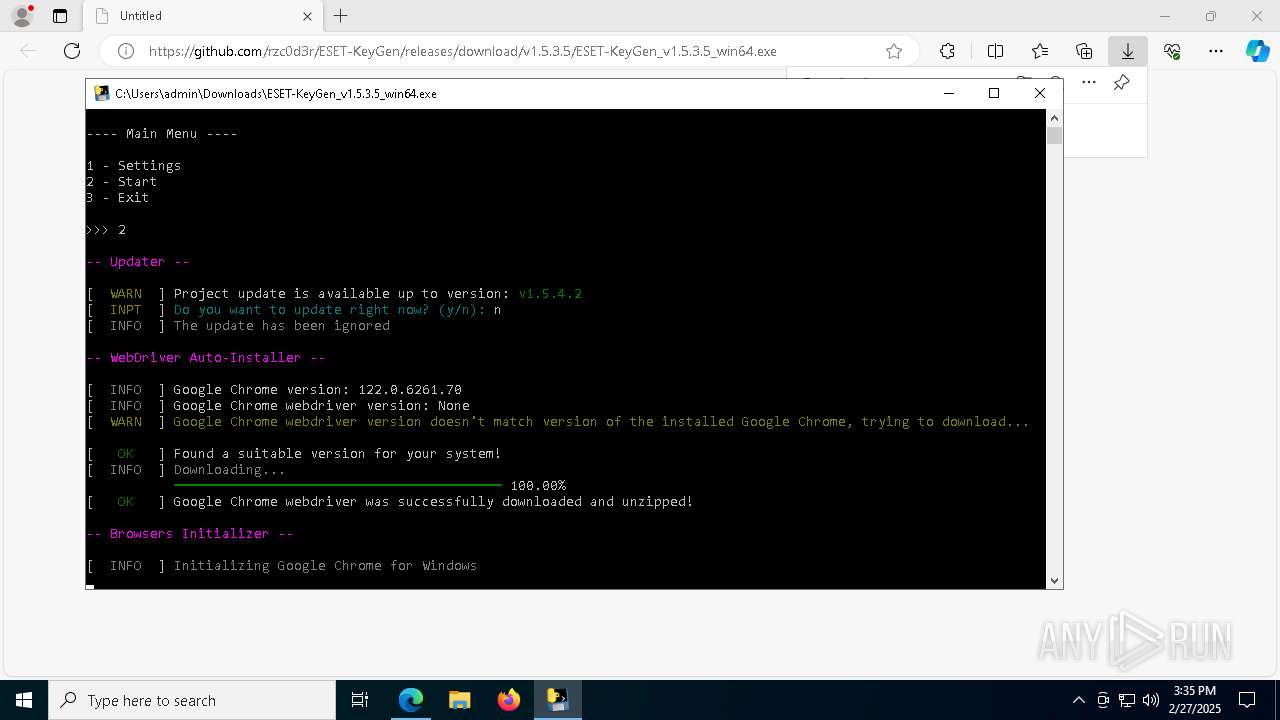
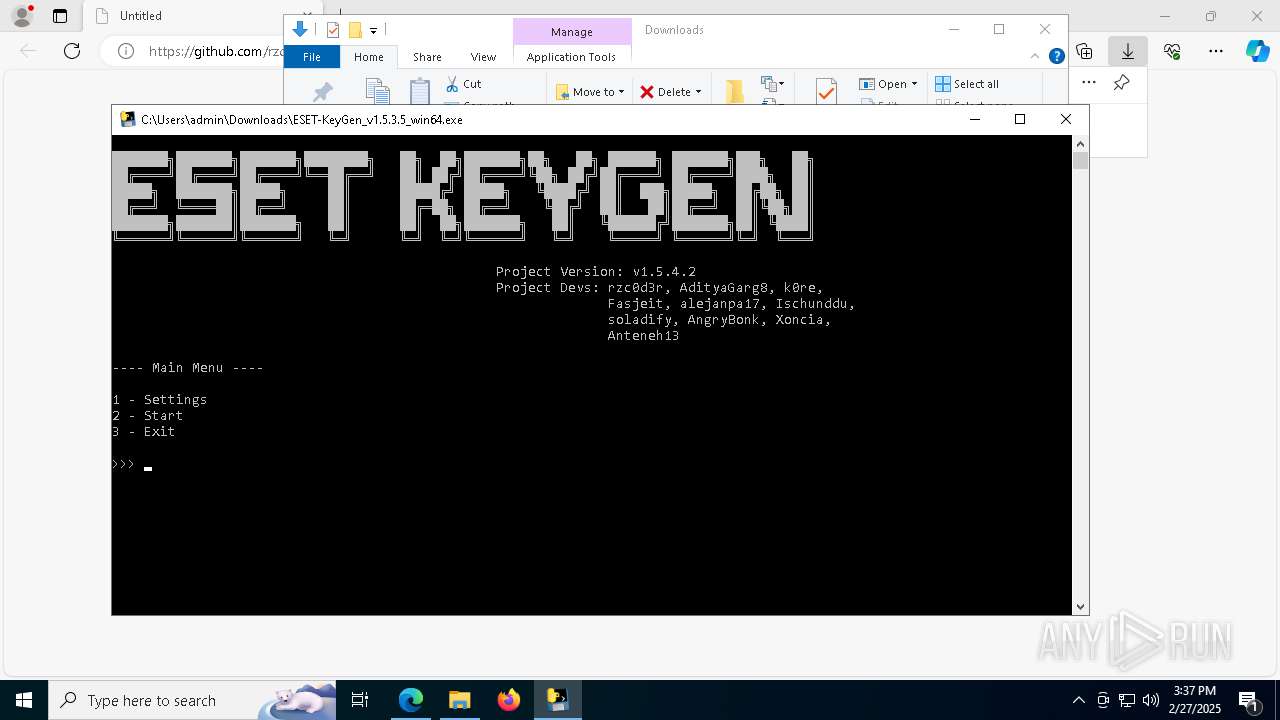
PyInstaller has been detected (YARA)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8580)
Checks operating system version
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 8672)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 896)
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 9168)
Execution of CURL command
- cmd.exe (PID: 4692)
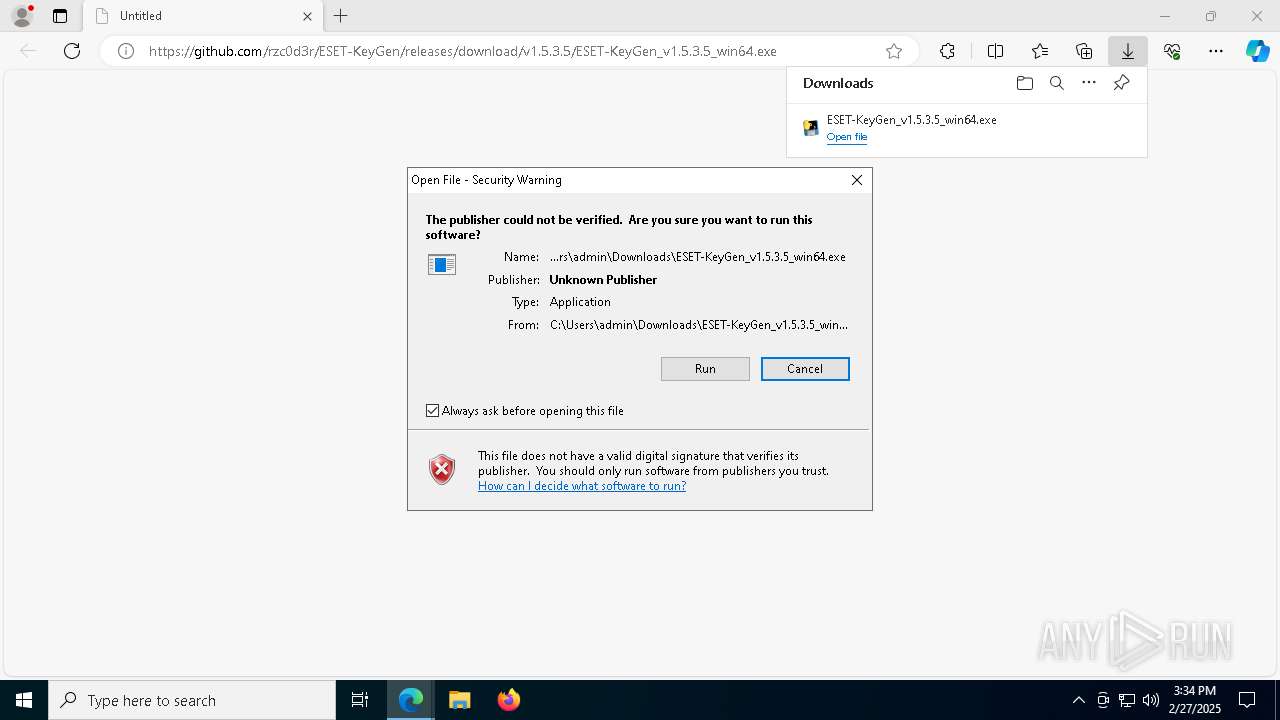
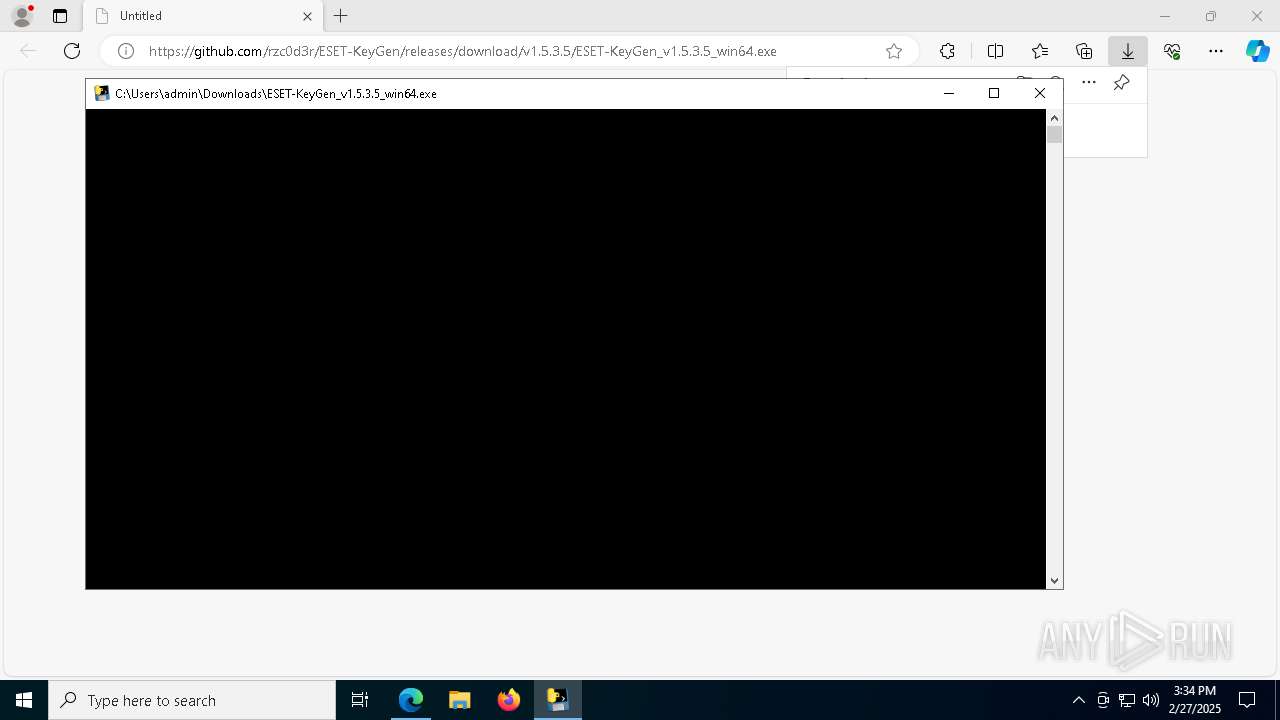
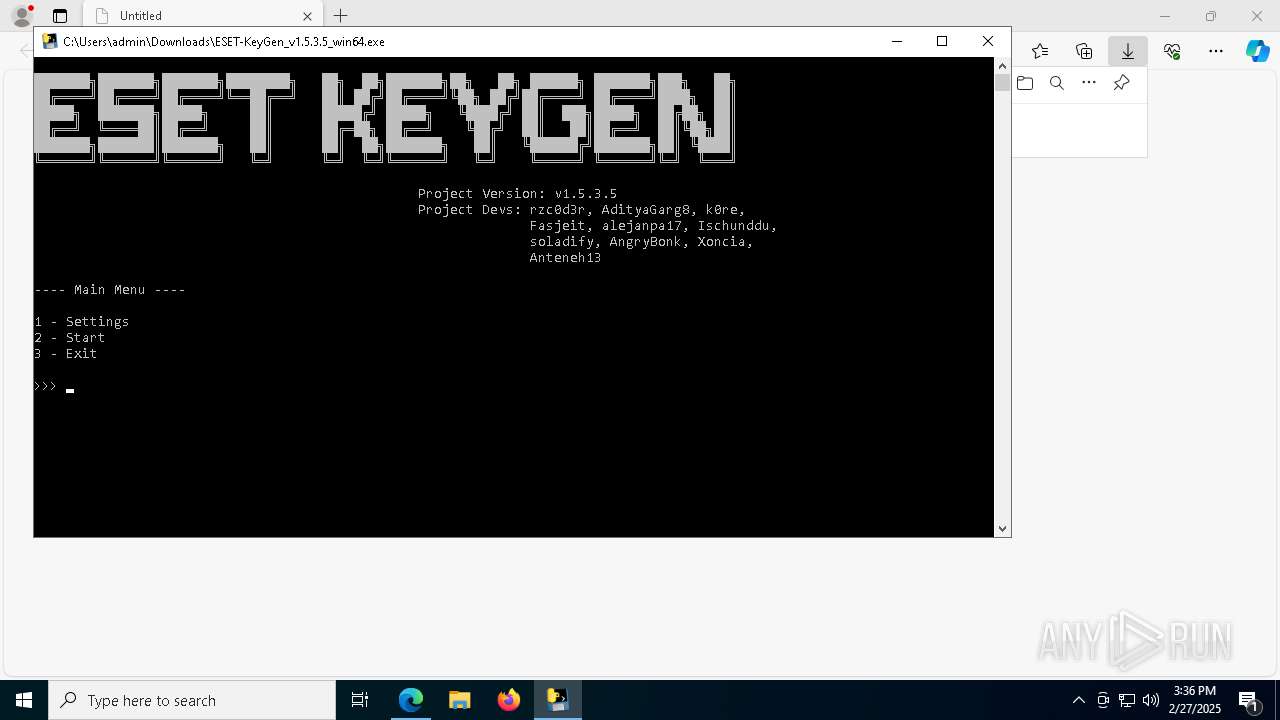
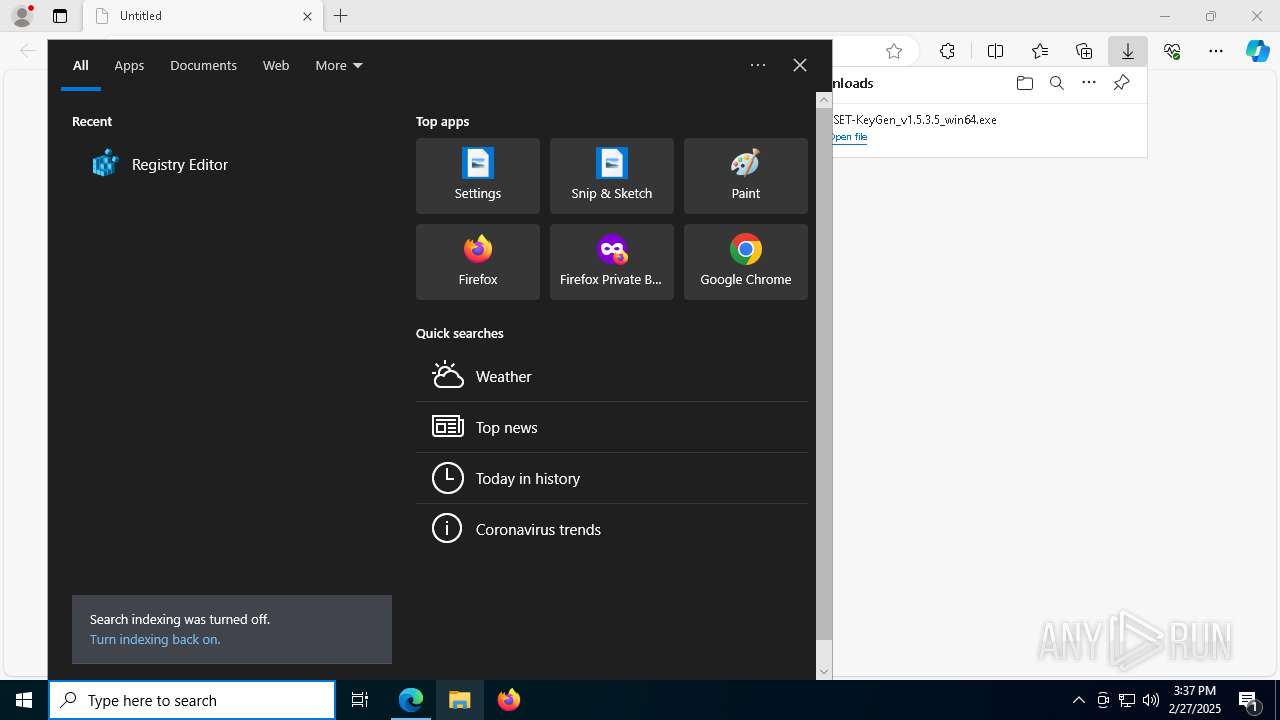
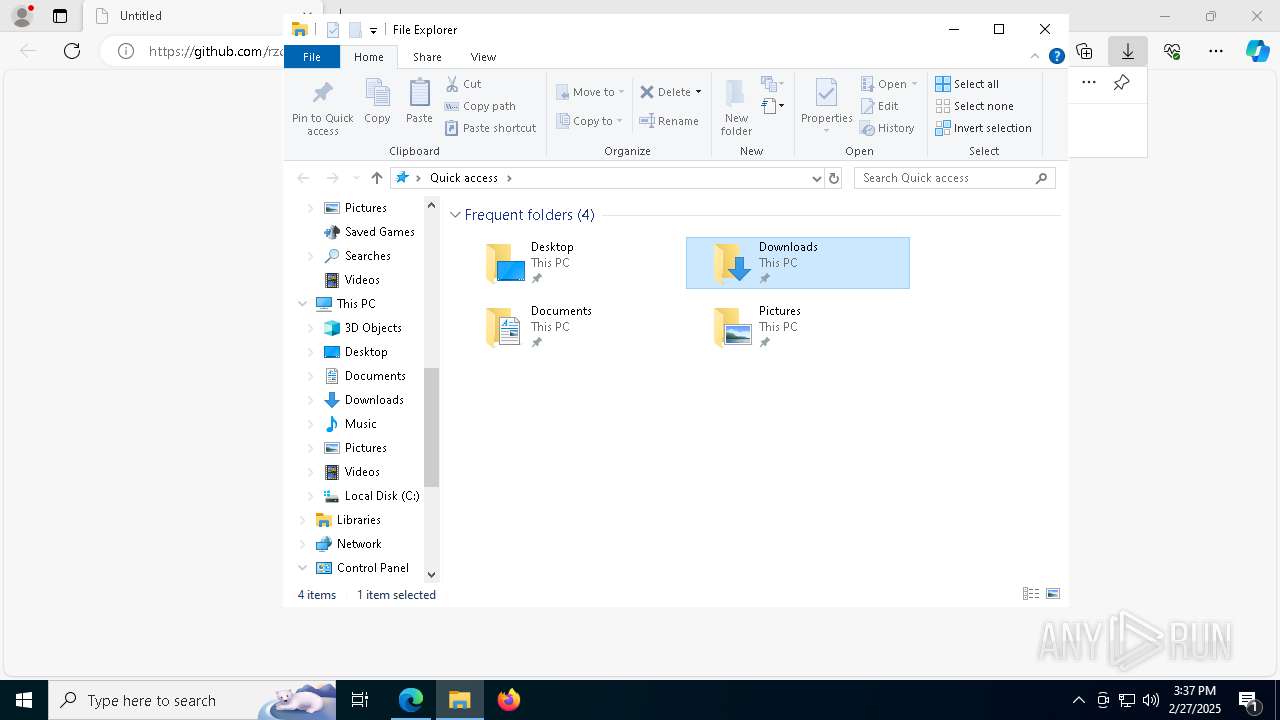
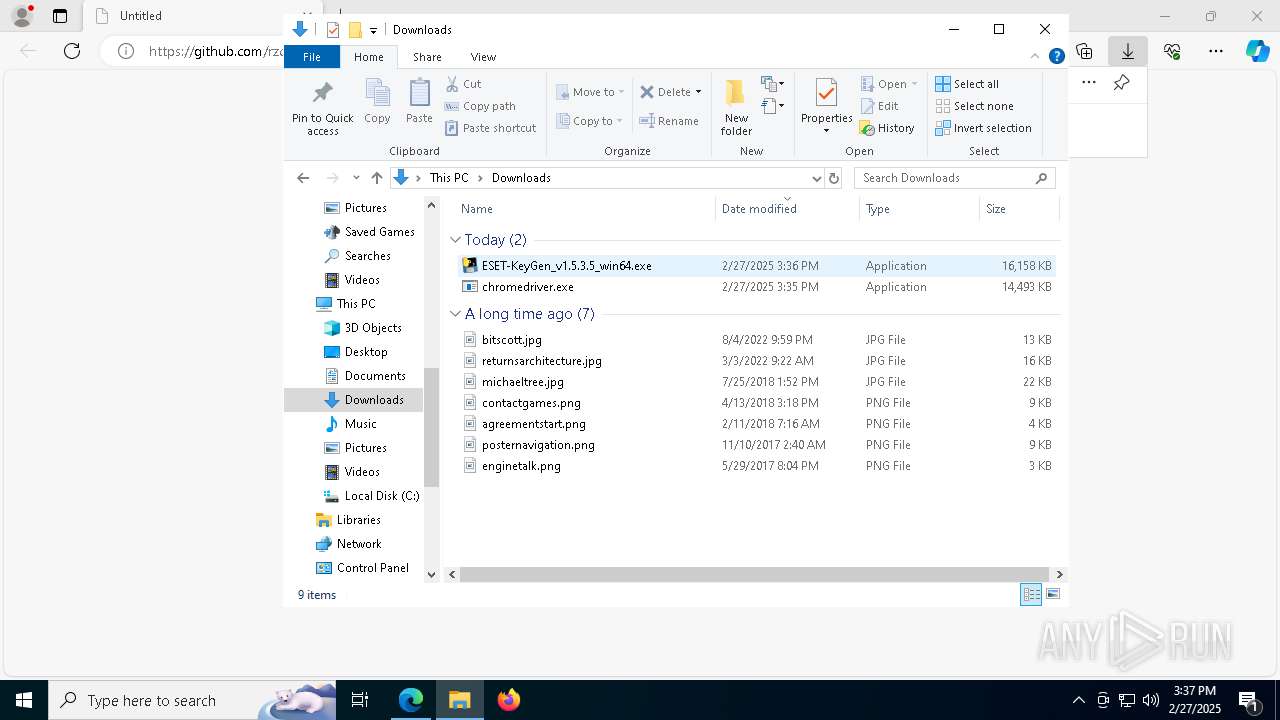
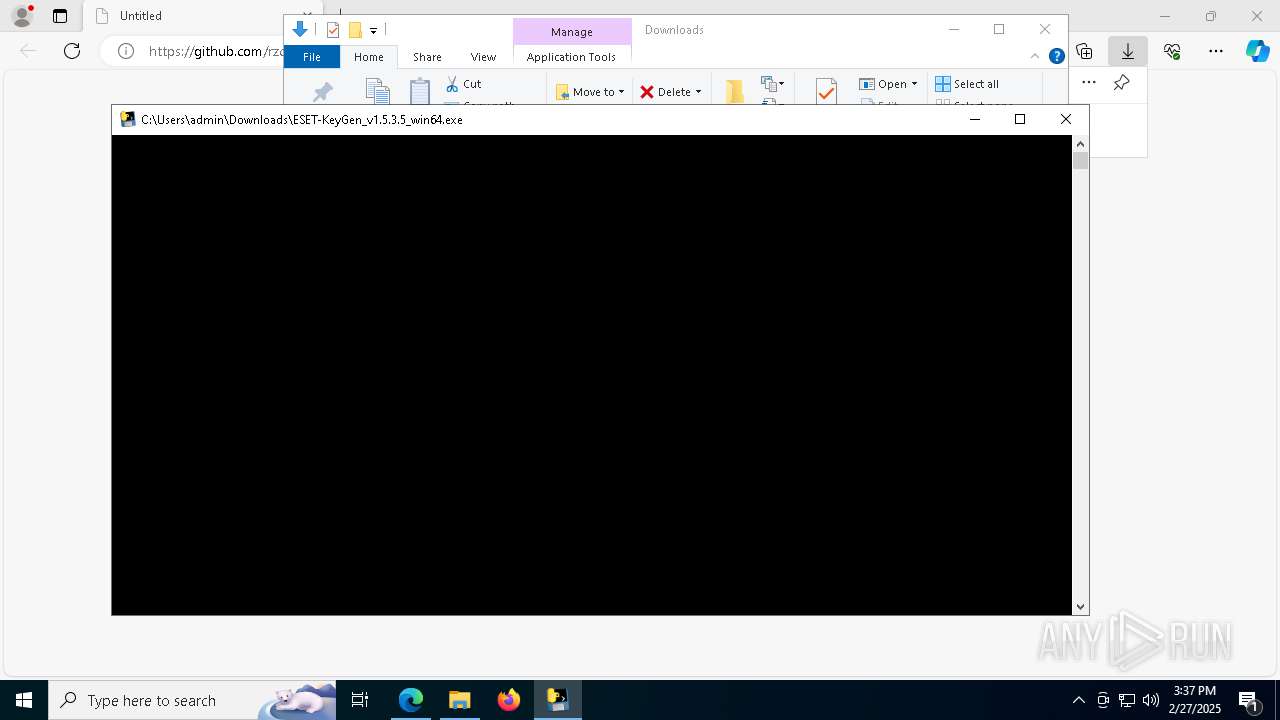
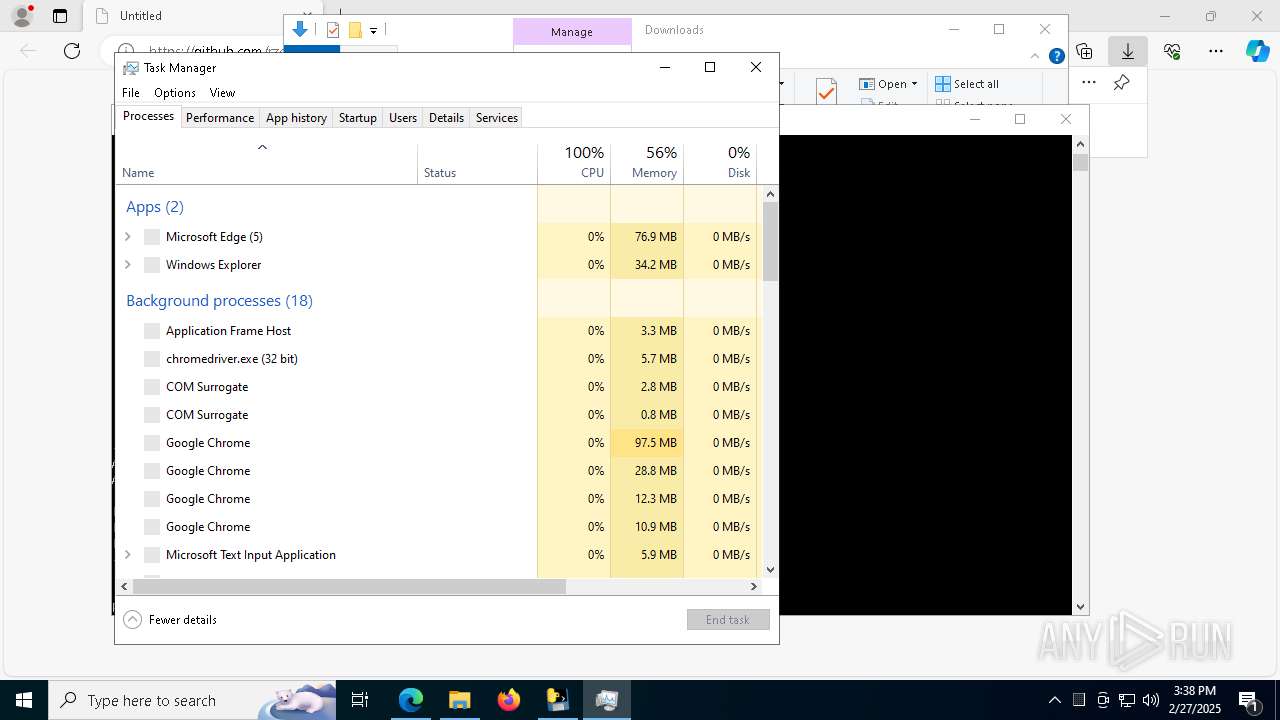
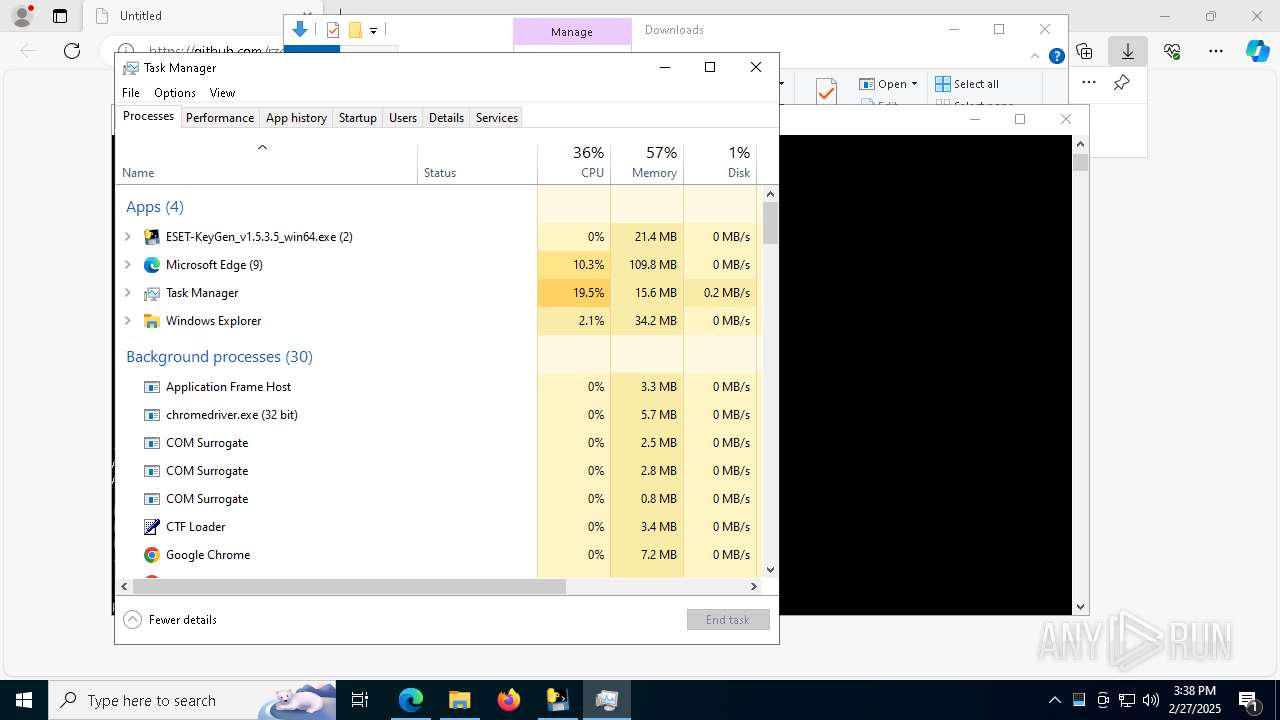
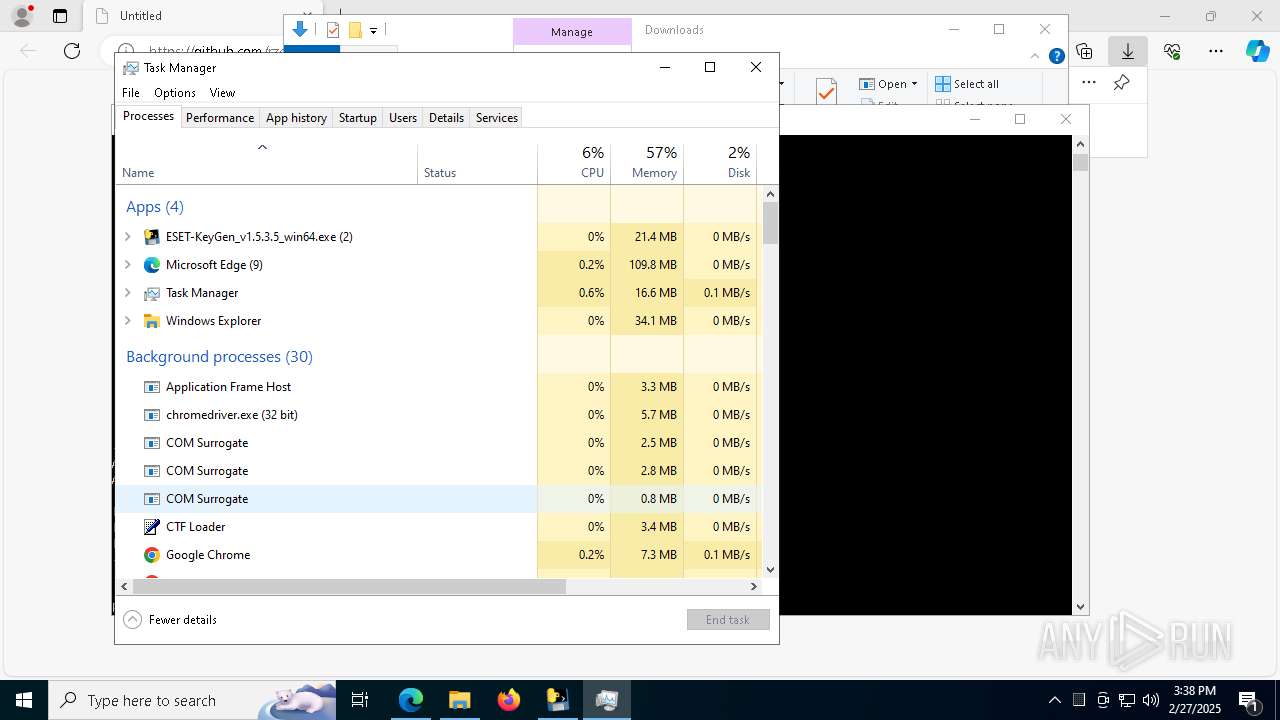
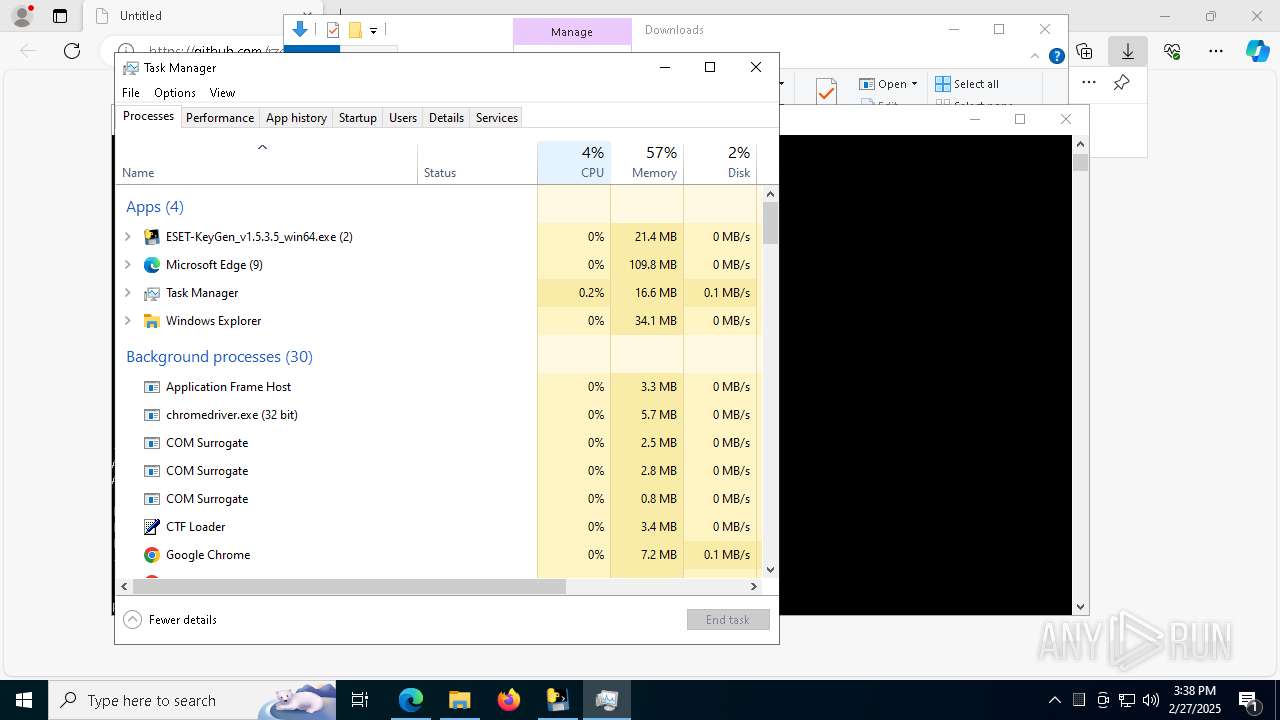
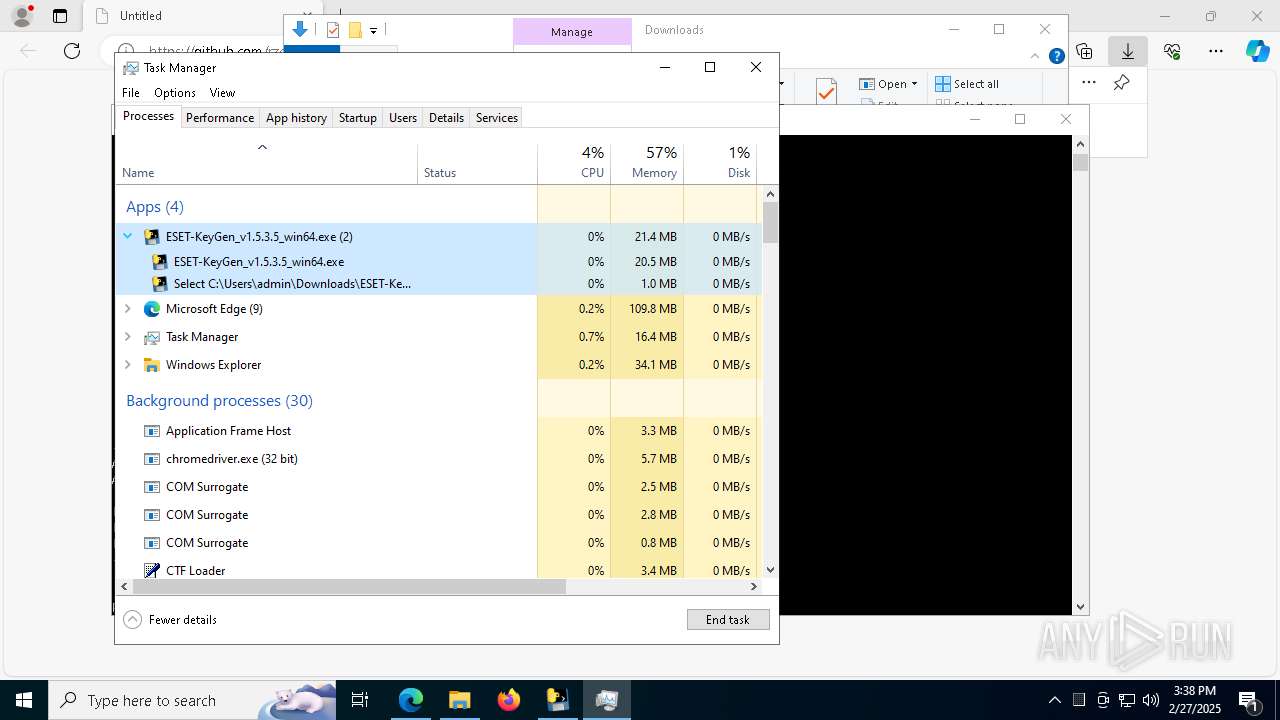
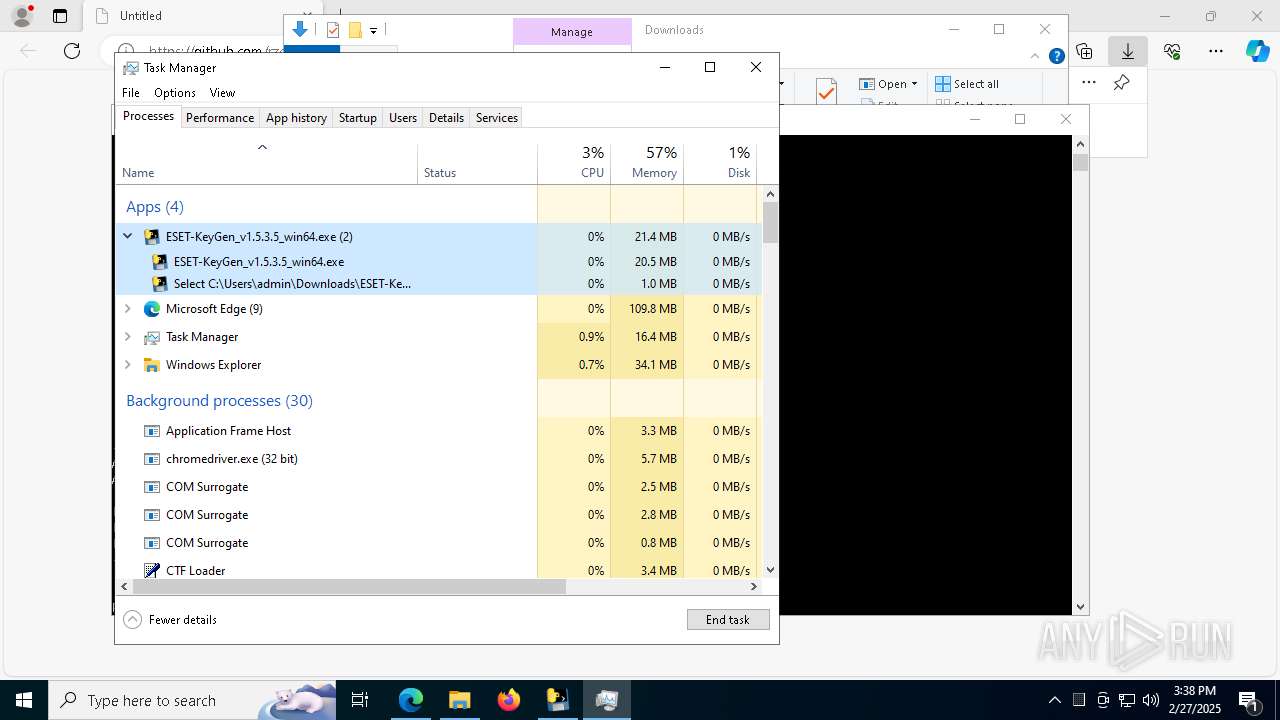
Manual execution by a user
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 7372)
- Taskmgr.exe (PID: 2420)
- Taskmgr.exe (PID: 8240)
Reads the machine GUID from the registry
- ESET-KeyGen_v1.5.3.5_win64.exe (PID: 9168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
246
Monitored processes
103
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4196 --field-trial-handle=2380,i,5516032205116309845,17886519158545109296,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\scoped_dir5084_441050890 /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\scoped_dir5084_441050890\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7ffc891adc40,0x7ffc891adc4c,0x7ffc891adc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 896 | "C:\Users\admin\Downloads\ESET-KeyGen_v1.5.3.5_win64.exe" | C:\Users\admin\Downloads\ESET-KeyGen_v1.5.3.5_win64.exe | ESET-KeyGen_v1.5.3.5_win64.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6916 --field-trial-handle=2380,i,5516032205116309845,17886519158545109296,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | where curl | C:\Windows\System32\where.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6568 --field-trial-handle=2380,i,5516032205116309845,17886519158545109296,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --headless --enable-automation --log-level=3 --remote-debugging-port=0 --test-type=webdriver --allow-pre-commit-input --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2964 --field-trial-handle=1512,i,12010356890152938621,5189107259210591613,262144 --disable-features=PaintHolding --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6552 --field-trial-handle=2380,i,5516032205116309845,17886519158545109296,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ESET-KeyGen_v1.5.3.5_win64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --allow-pre-commit-input --disable-background-networking --disable-backgrounding-occluded-windows --disable-client-side-phishing-detection --disable-default-apps --disable-hang-monitor --disable-popup-blocking --disable-prompt-on-repost --disable-sync --enable-automation --headless --lang=en-US --log-level=3 --no-first-run --no-service-autorun --password-store=basic --remote-debugging-port=0 --test-type=webdriver --use-mock-keychain --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir5084_441050890" data:, | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chromedriver.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
16 494
Read events
16 455
Write events
38
Delete events
1
Modification events
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F3B7DCB4B78D2F00 | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C14FE5B4B78D2F00 | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7D828CB3-4CC7-4B9C-BB1B-C58C9C8A8DD3} | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1E8A58A6-0315-4C3A-B7B9-5A23FC98ECE3} | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C18B14B5B78D2F00 | |||
| (PID) Process: | (7428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
220
Suspicious files
782
Text files
128
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b6bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b6cf.TMP | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b6cf.TMP | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b6cf.TMP | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b6de.TMP | — | |
MD5:— | SHA256:— | |||
| 7428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
181
DNS requests
130
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8744 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5380 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5380 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8732 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741190957&P2=404&P3=2&P4=Q1PHLlf99Ya28qY0m4v0aGYJkRpZ57DC7MveXWRFUQdgxkBEMEChjBtN9ZAhr8IelQv2CRXiR714WyzEjE3dyg%3d%3d | unknown | — | — | whitelisted |
8732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741190957&P2=404&P3=2&P4=Q1PHLlf99Ya28qY0m4v0aGYJkRpZ57DC7MveXWRFUQdgxkBEMEChjBtN9ZAhr8IelQv2CRXiR714WyzEjE3dyg%3d%3d | unknown | — | — | whitelisted |
8732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741190957&P2=404&P3=2&P4=Q1PHLlf99Ya28qY0m4v0aGYJkRpZ57DC7MveXWRFUQdgxkBEMEChjBtN9ZAhr8IelQv2CRXiR714WyzEjE3dyg%3d%3d | unknown | — | — | whitelisted |
8732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741190957&P2=404&P3=2&P4=Q1PHLlf99Ya28qY0m4v0aGYJkRpZ57DC7MveXWRFUQdgxkBEMEChjBtN9ZAhr8IelQv2CRXiR714WyzEjE3dyg%3d%3d | unknown | — | — | whitelisted |
8732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741190957&P2=404&P3=2&P4=Q1PHLlf99Ya28qY0m4v0aGYJkRpZ57DC7MveXWRFUQdgxkBEMEChjBtN9ZAhr8IelQv2CRXiR714WyzEjE3dyg%3d%3d | unknown | — | — | whitelisted |
8732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741190957&P2=404&P3=2&P4=Q1PHLlf99Ya28qY0m4v0aGYJkRpZ57DC7MveXWRFUQdgxkBEMEChjBtN9ZAhr8IelQv2CRXiR714WyzEjE3dyg%3d%3d | unknown | — | — | whitelisted |
8732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741190957&P2=404&P3=2&P4=Q1PHLlf99Ya28qY0m4v0aGYJkRpZ57DC7MveXWRFUQdgxkBEMEChjBtN9ZAhr8IelQv2CRXiR714WyzEjE3dyg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7428 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7708 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7708 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7708 | msedge.exe | 142.250.185.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
7708 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7708 | msedge.exe | 92.123.104.47:443 | edgeservices.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
business.bing.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |