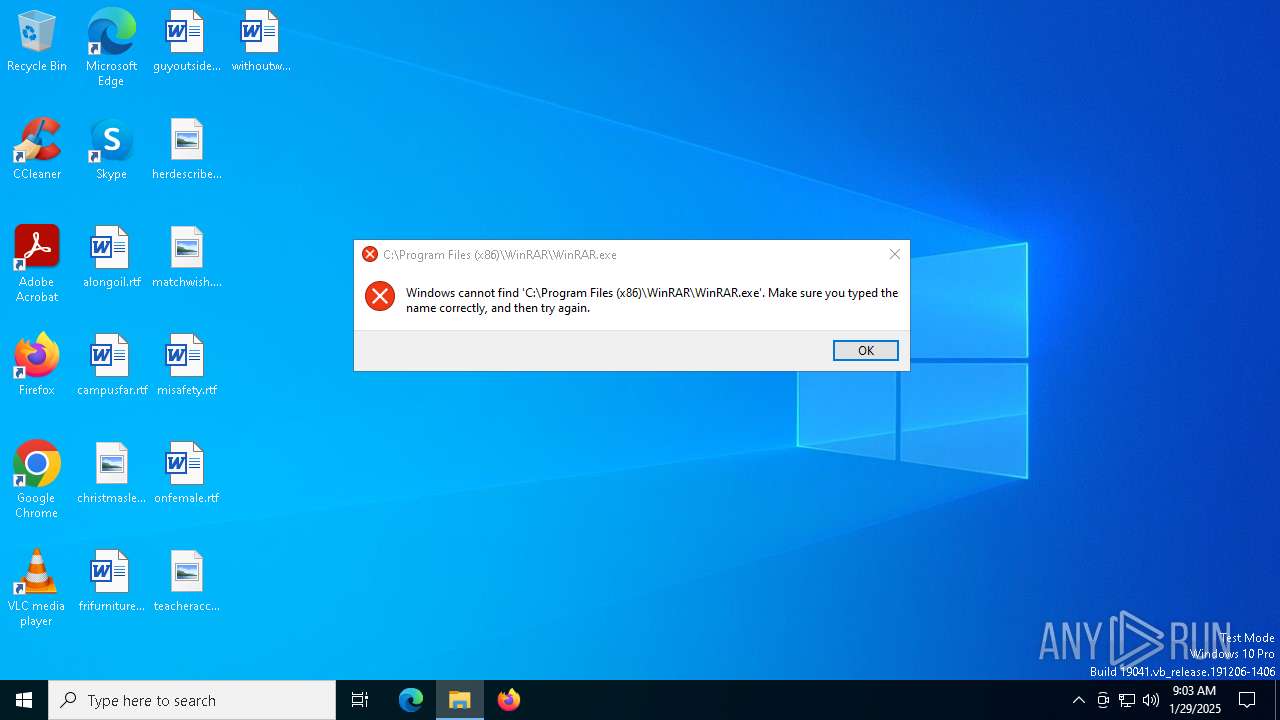
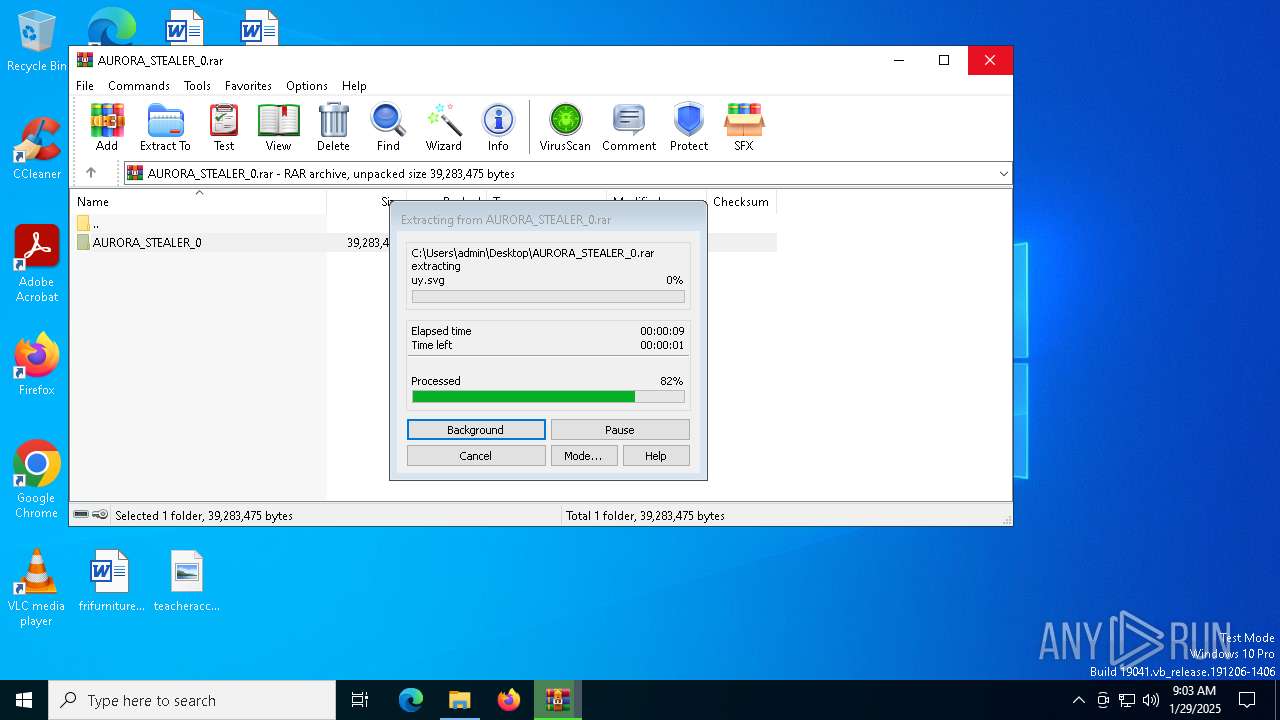
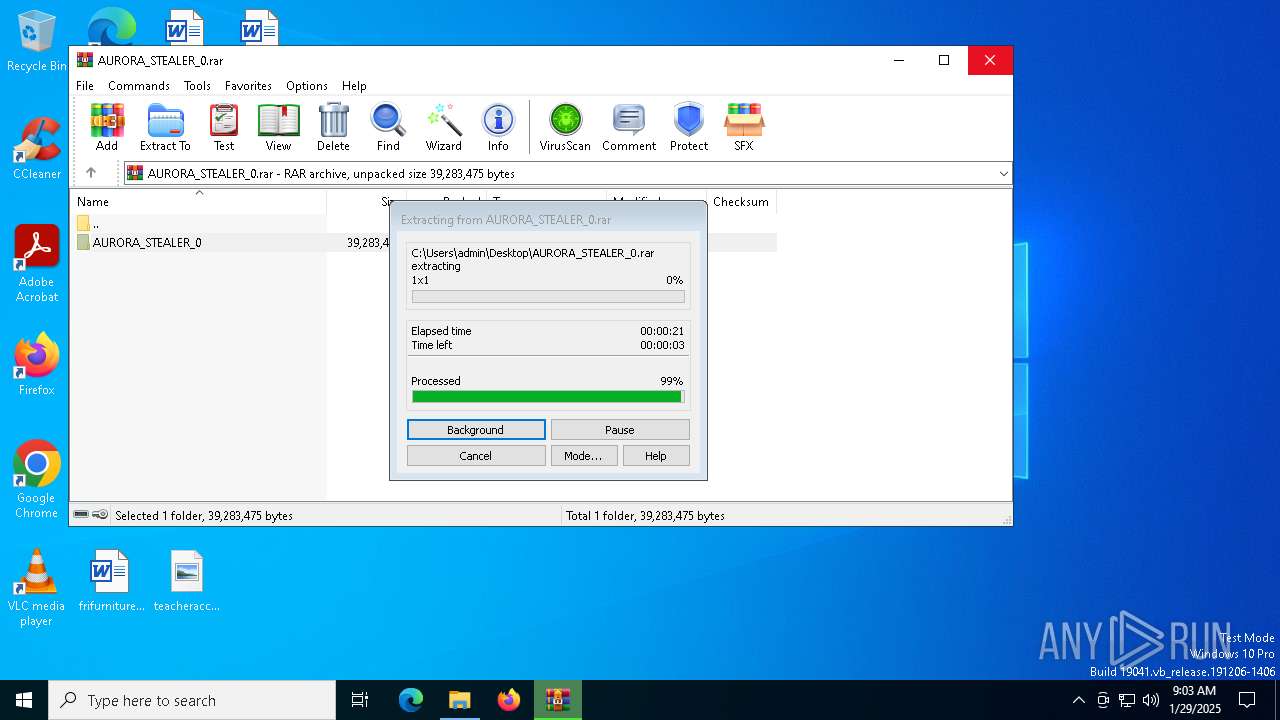
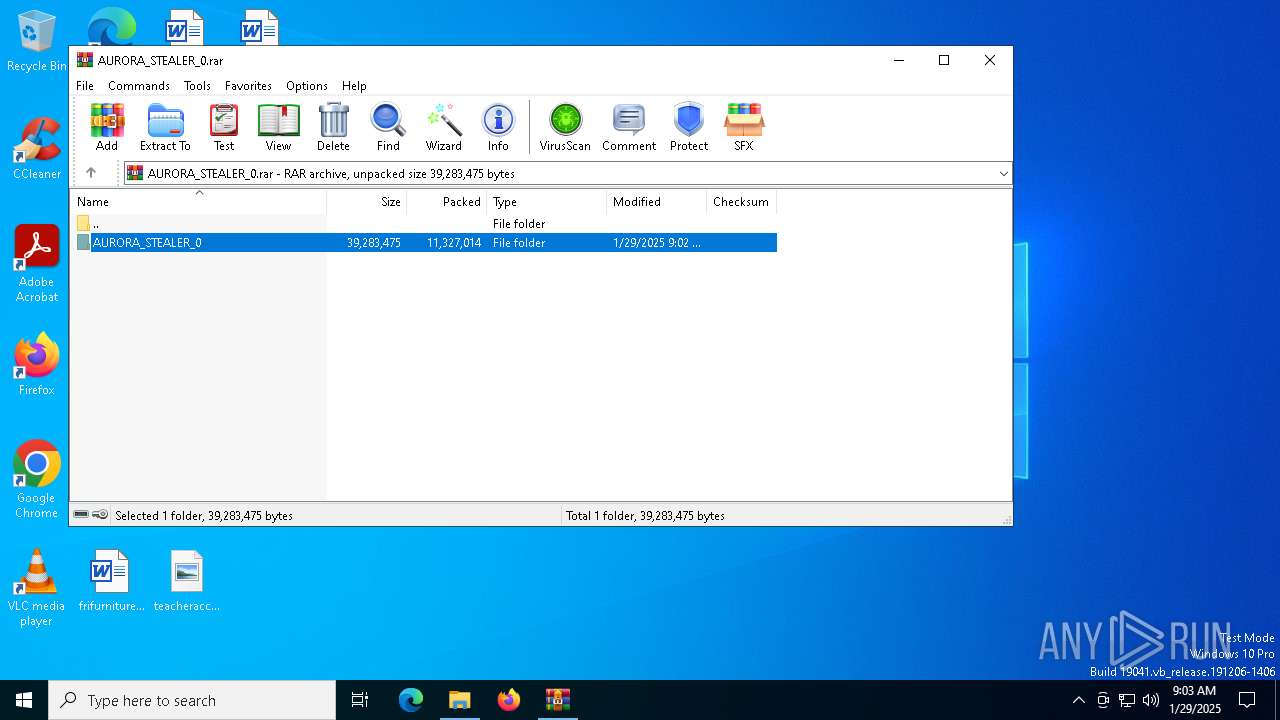
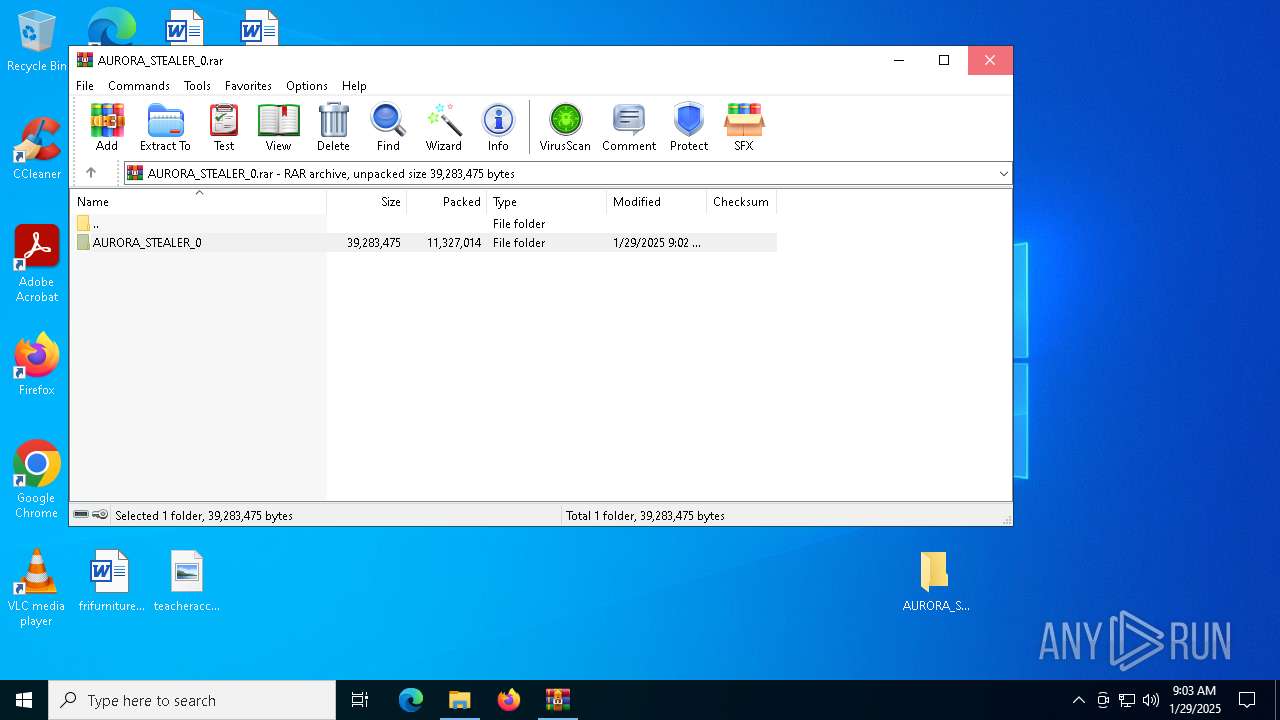
| File name: | AURORA_STEALER_0.rar |
| Full analysis: | https://app.any.run/tasks/9d480cb3-ab02-4c7b-a5d1-19268b2c206b |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2025, 09:03:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2F6F35A4D3EB8676BA2195BEE35D2A53 |
| SHA1: | 000DD6CF0A25738CAE77F1F08C9A06FE4AD6106E |
| SHA256: | D03171BFDA4AAD5EB768B08E8AB636169D437566E45FF8F68FE0D530DA5E7B60 |
| SSDEEP: | 98304:UBphkWHmcyw4A+Nyh8ULQqHmWb2vaK3U2c5ycKfb3HDE/0SDJbp2Iu3R9Y9km/mQ:iw/NBJEknGUzTpv4ZAJKUy |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6740)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 6740)
SUSPICIOUS
Reads security settings of Internet Explorer
- Aurora.exe (PID: 1144)
- Aurora.exe (PID: 6848)
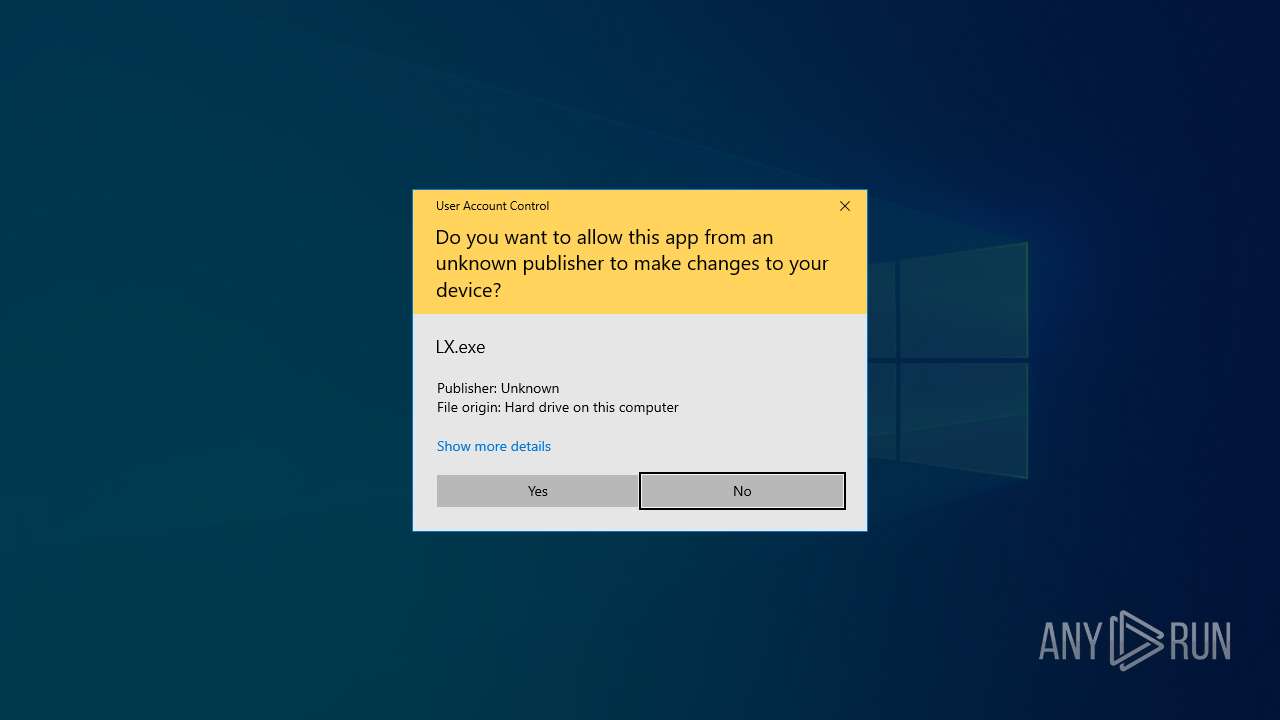
- LX.exe (PID: 4384)
Executable content was dropped or overwritten
- Aurora.exe (PID: 1144)
Reads the date of Windows installation
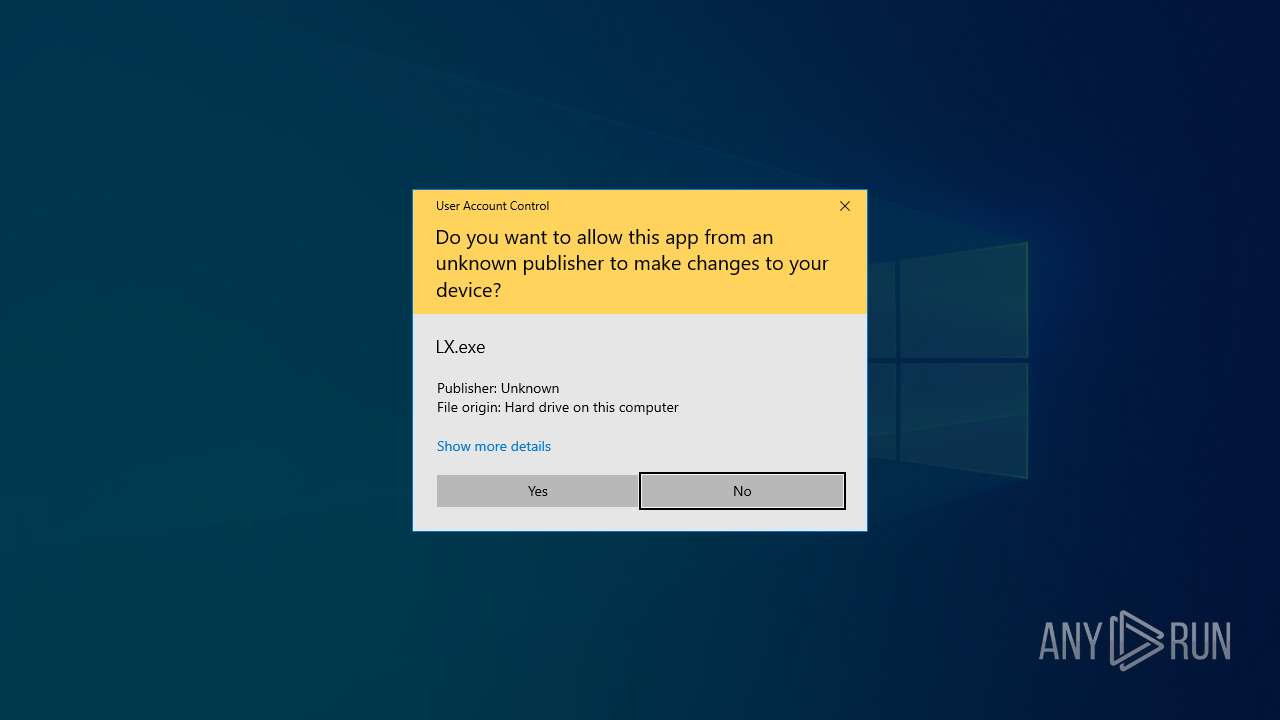
- LX.exe (PID: 4384)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 6740)
- LX.exe (PID: 4384)
BASE64 encoded PowerShell command has been detected
- LX.exe (PID: 4384)
Application launched itself
- powershell.exe (PID: 6740)
Base64-obfuscated command line is found
- LX.exe (PID: 4384)
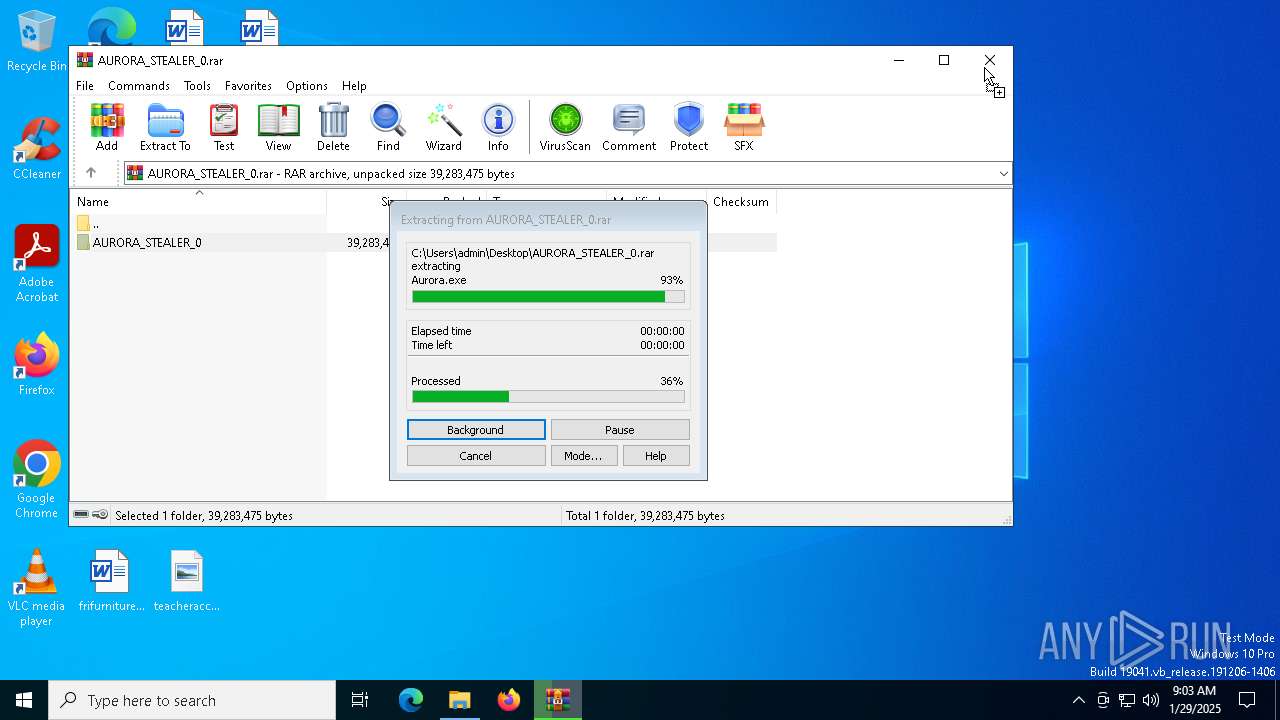
INFO
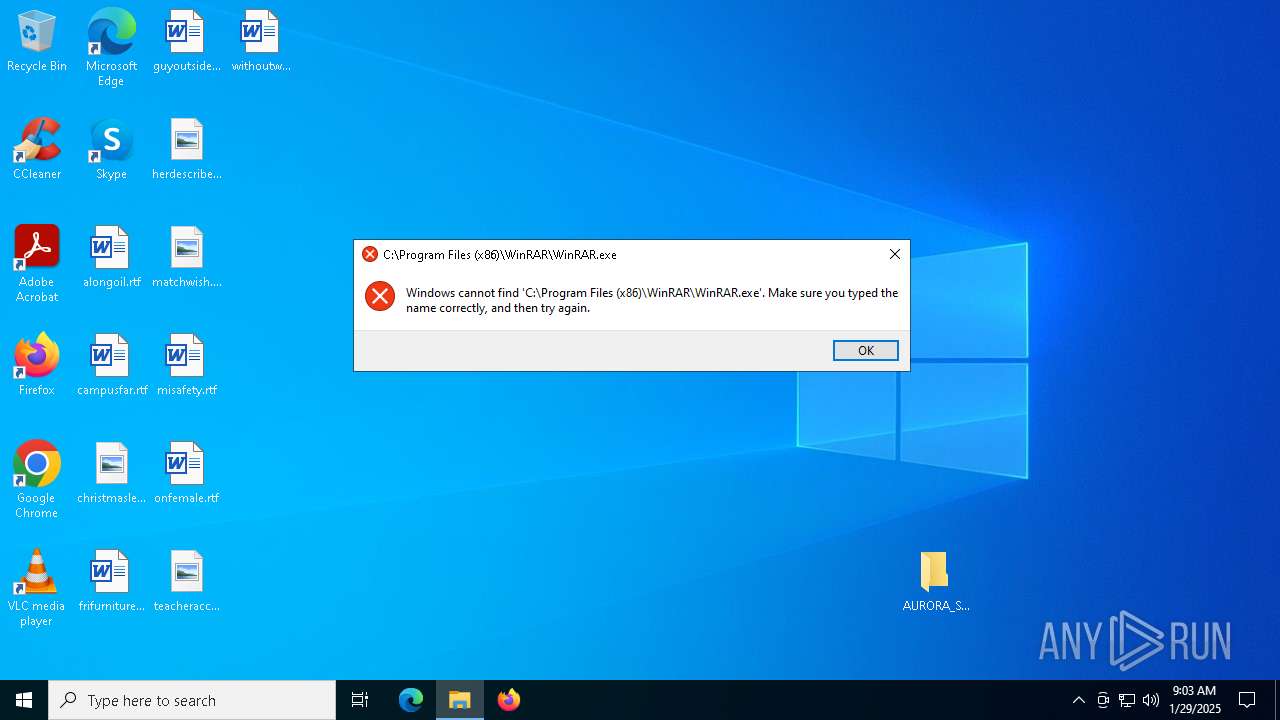
The sample compiled with english language support
- WinRAR.exe (PID: 6584)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6584)
Manual execution by a user
- Aurora.exe (PID: 1144)
- Aurora.exe (PID: 6848)
Reads the computer name
- Aurora.exe (PID: 1144)
- Aurora.exe (PID: 3772)
- Aurora.exe (PID: 6848)
- Aurora.exe (PID: 6960)
- LX.exe (PID: 4384)
Create files in a temporary directory
- Aurora.exe (PID: 1144)
- Aurora.exe (PID: 6848)
Reads the software policy settings
- Aurora.exe (PID: 3772)
Checks supported languages
- Aurora.exe (PID: 1144)
- Aurora.exe (PID: 3772)
- Aurora.exe (PID: 6848)
- LX.exe (PID: 4384)
Reads the machine GUID from the registry
- Aurora.exe (PID: 3772)
Process checks computer location settings
- Aurora.exe (PID: 1144)
- Aurora.exe (PID: 6848)
- LX.exe (PID: 4384)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6740)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6740)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6740)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
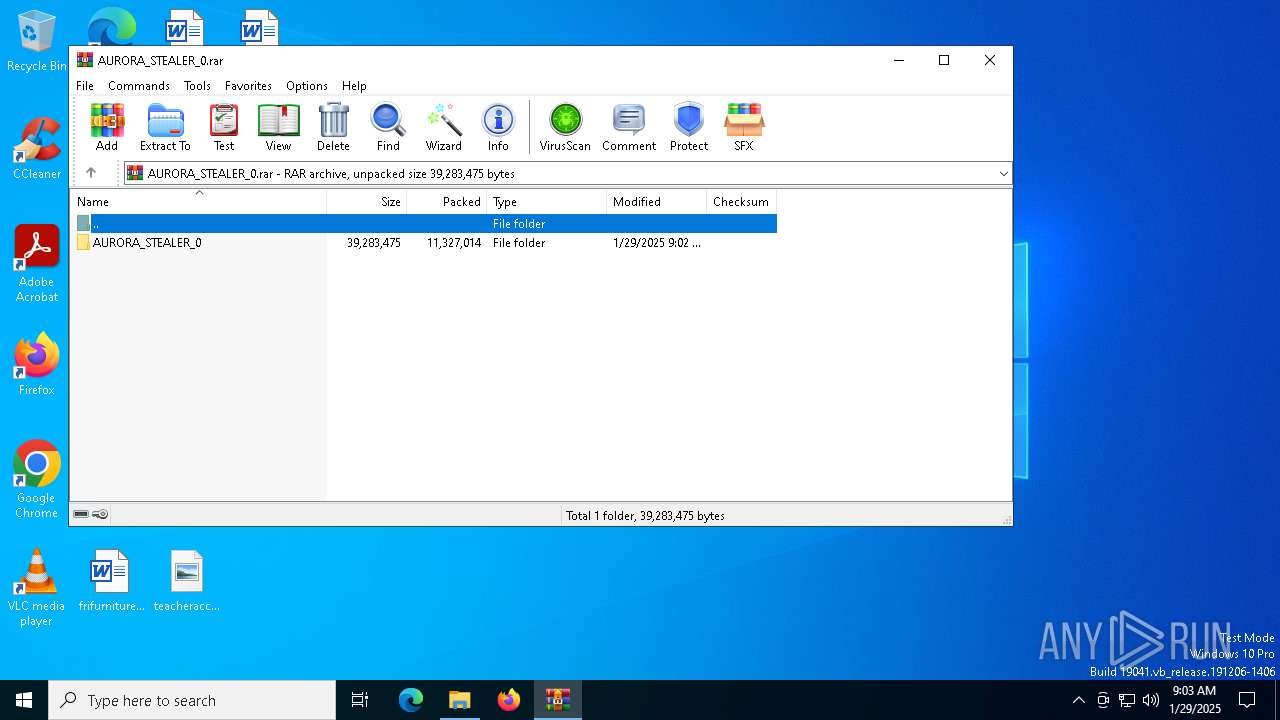
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 8082786 |
| UncompressedSize: | 26750976 |
| OperatingSystem: | Win32 |
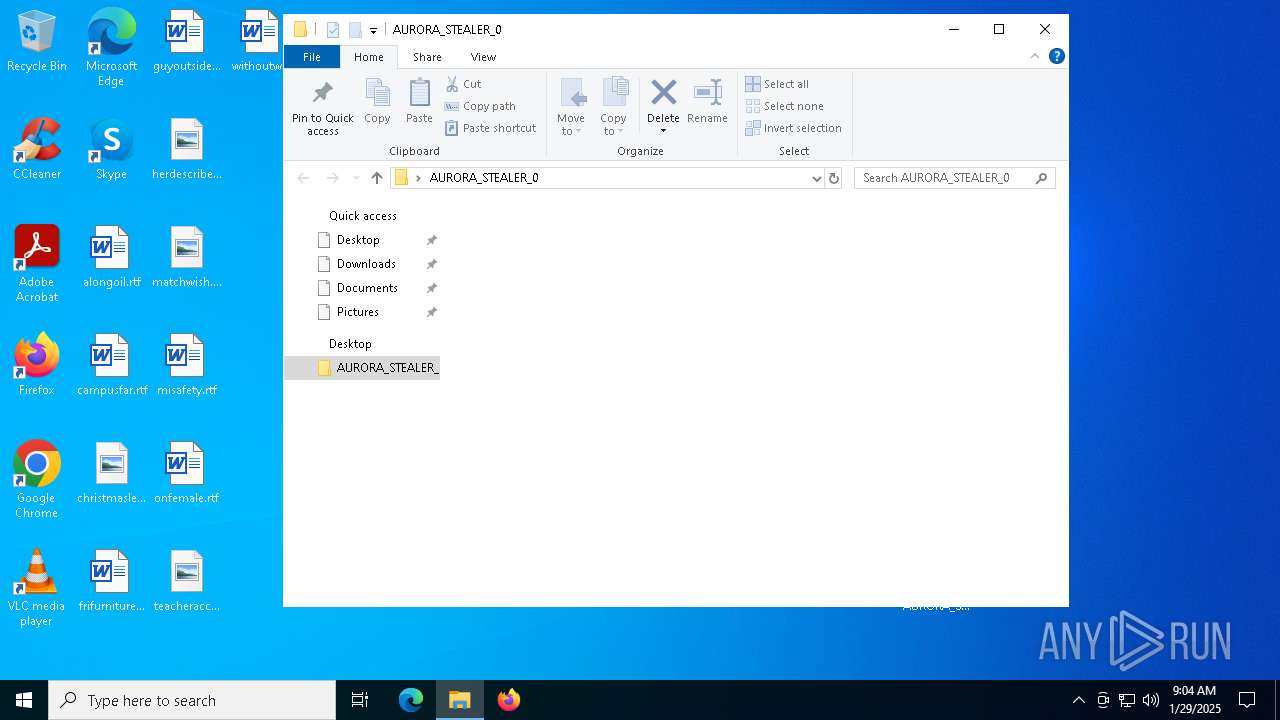
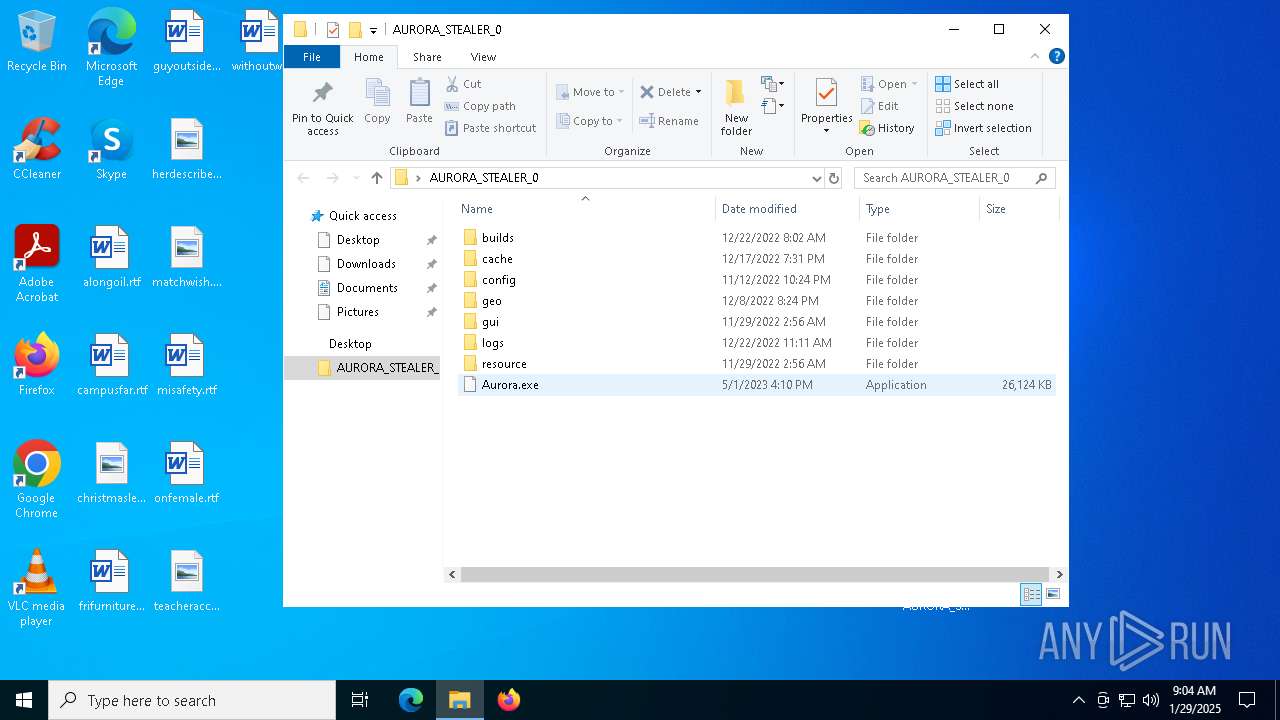
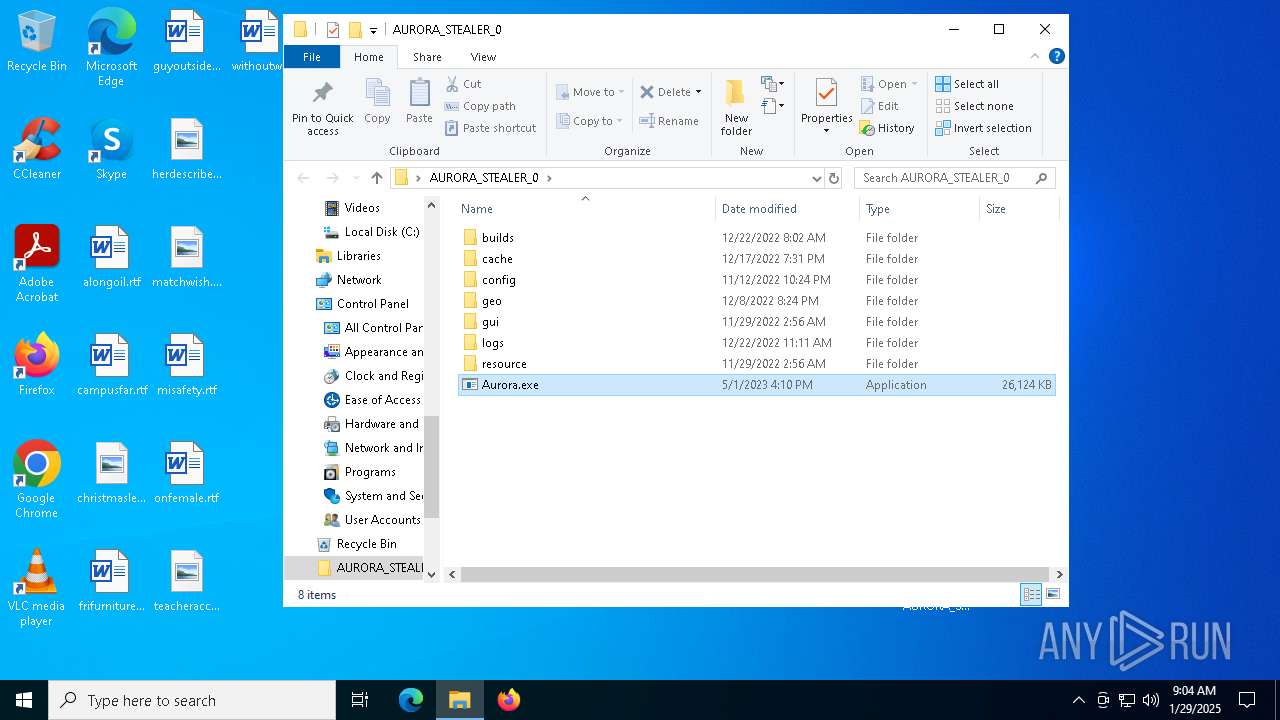
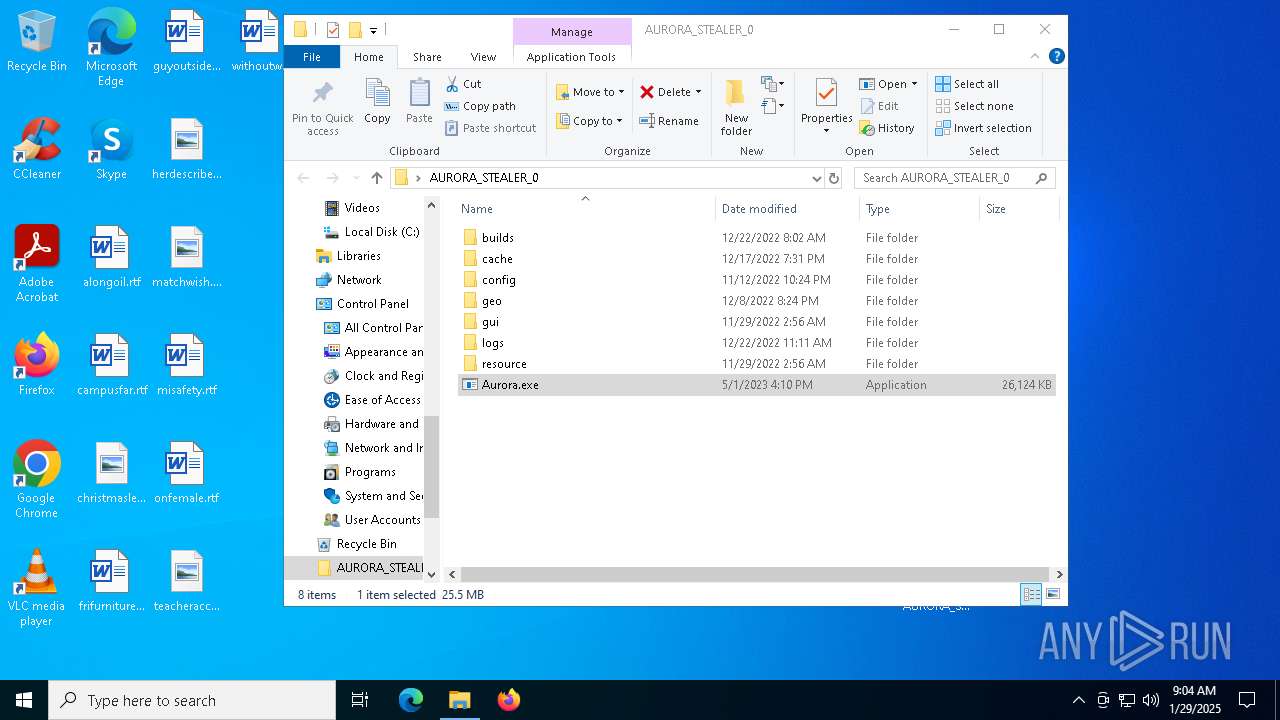
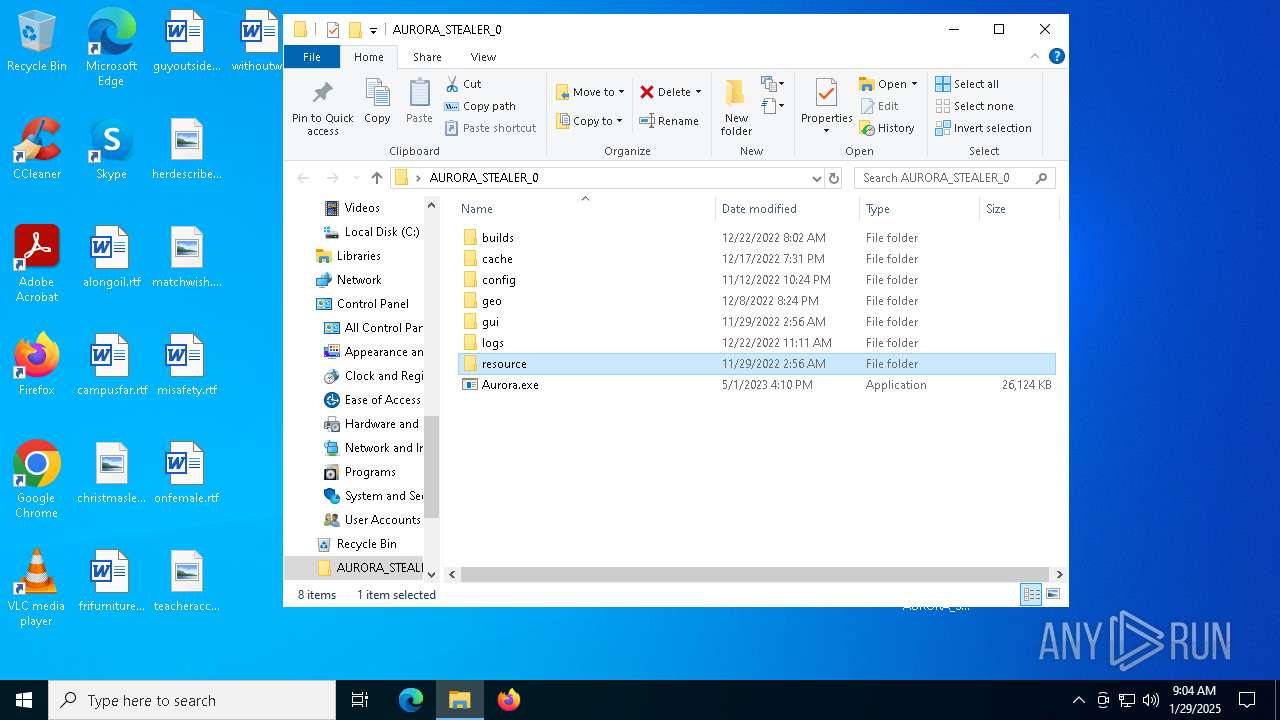
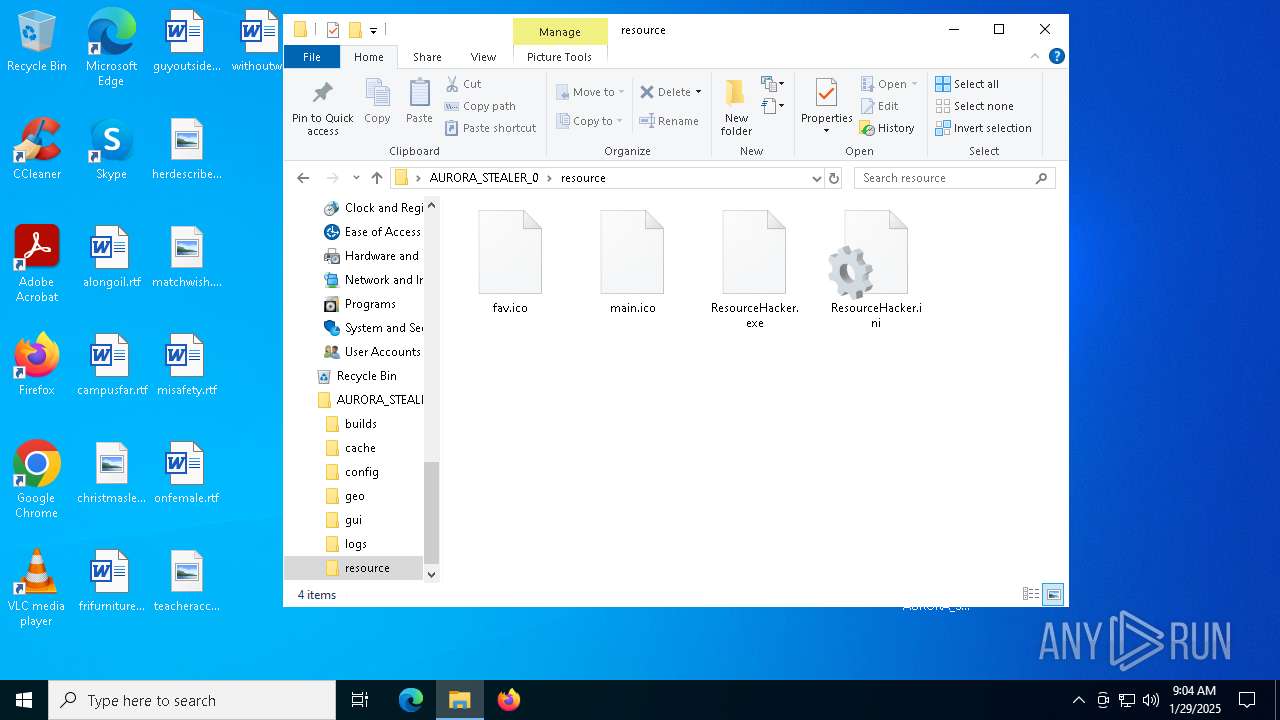
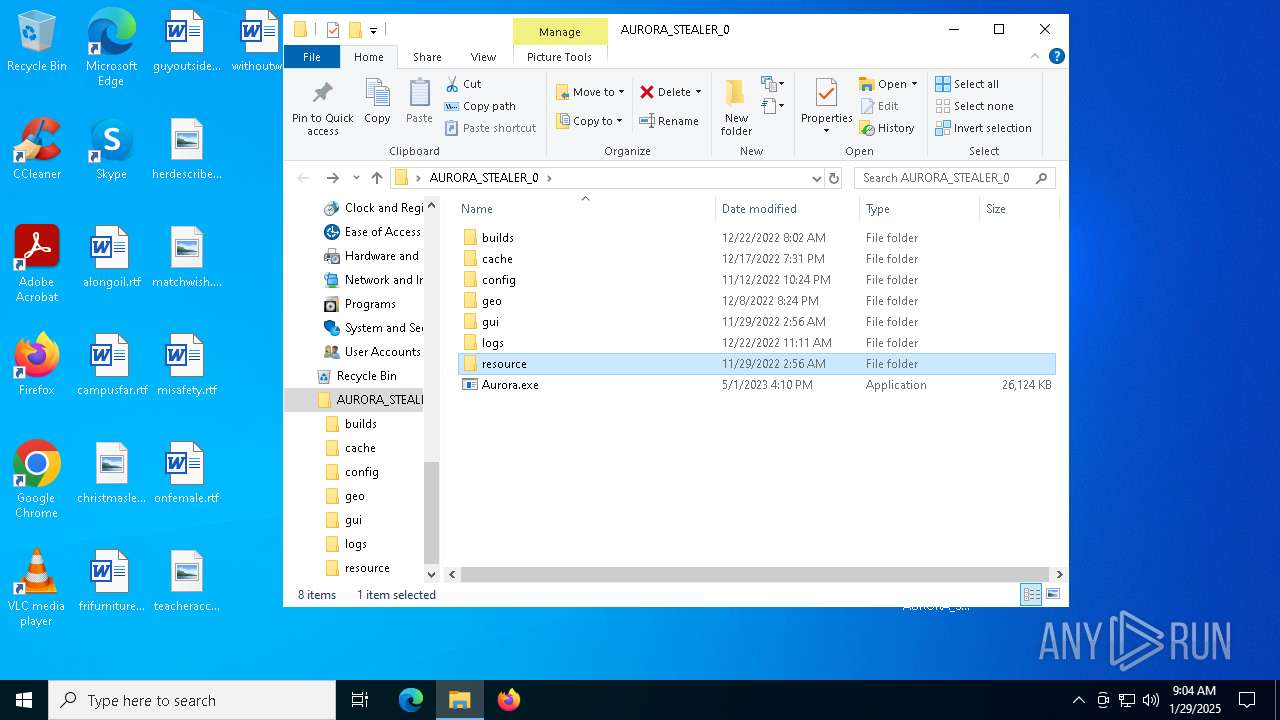
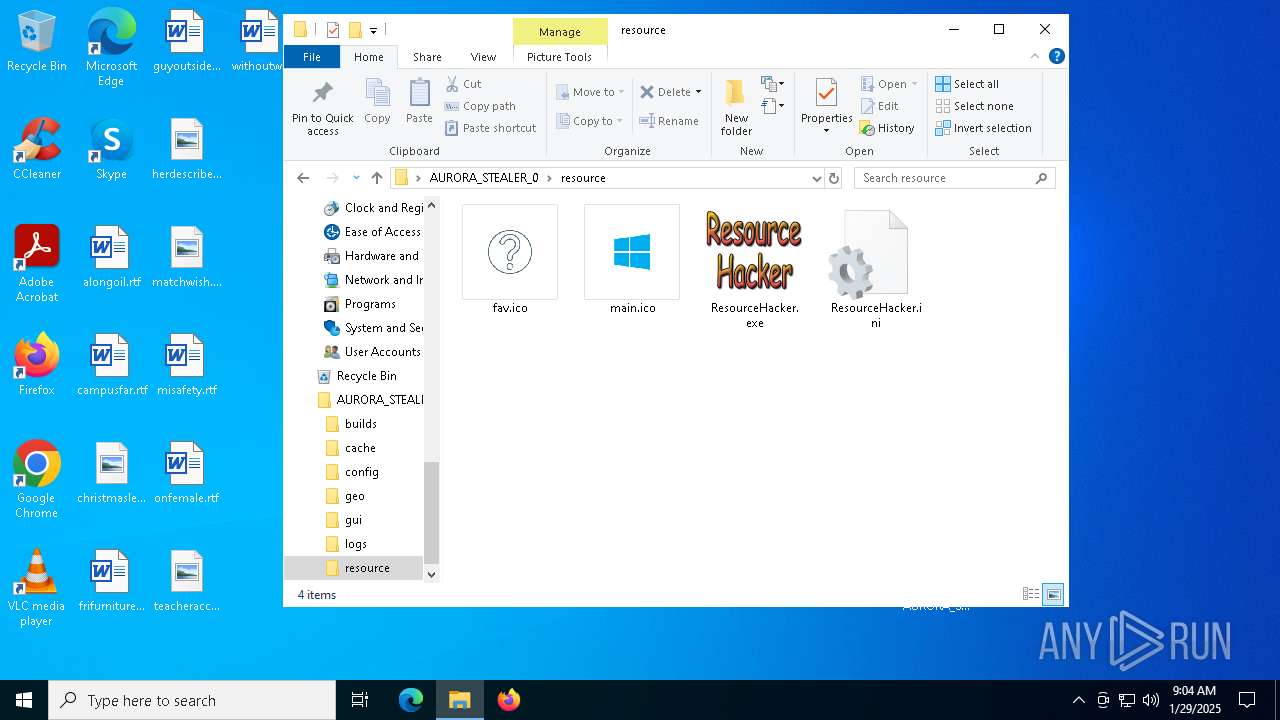
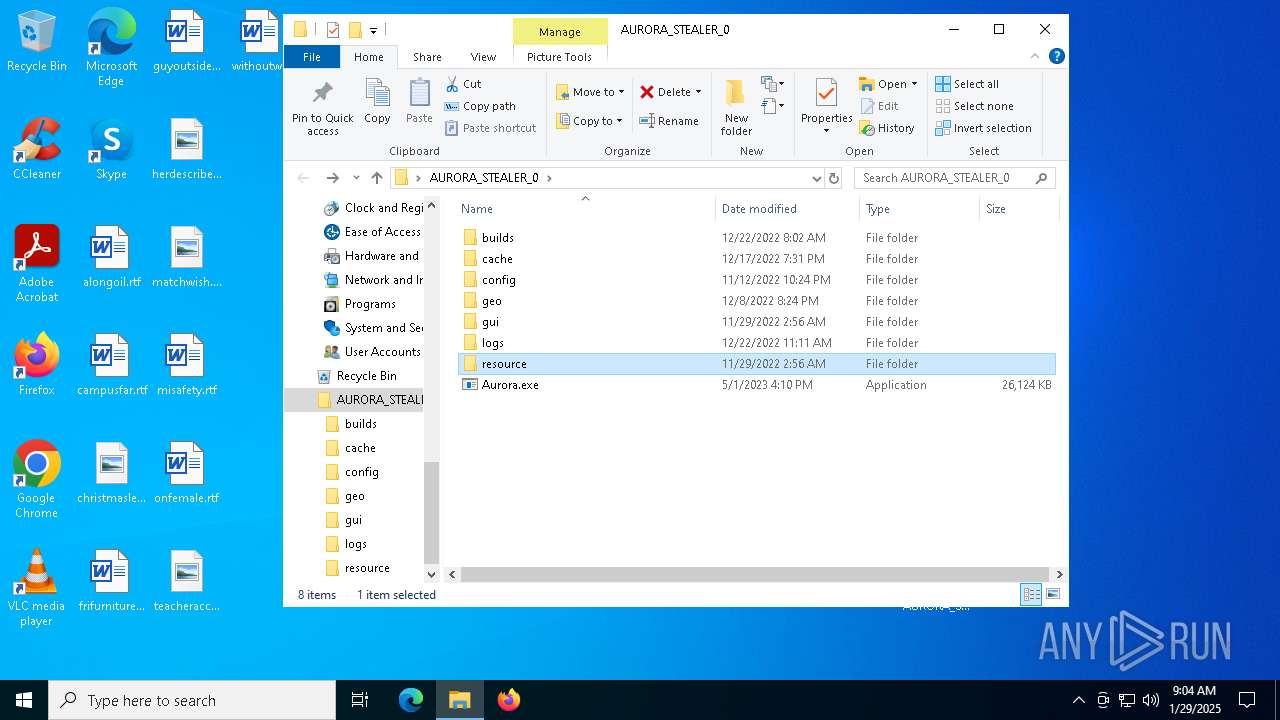
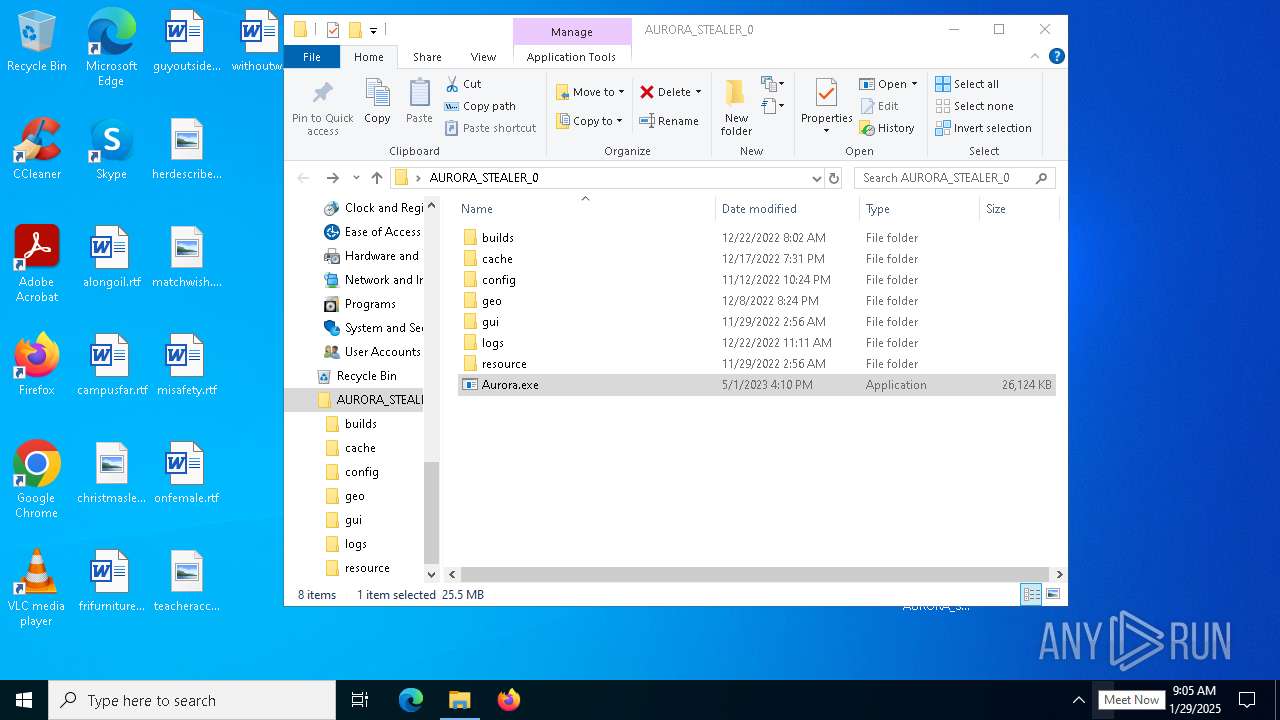
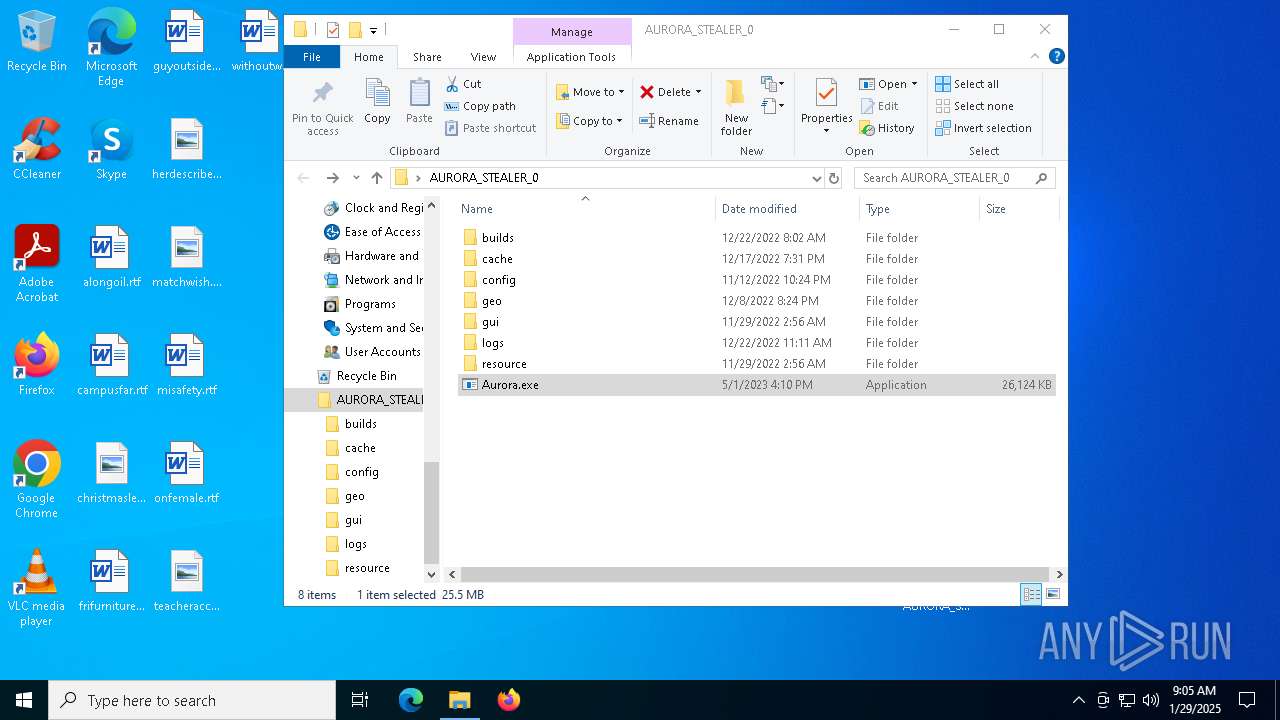
| ArchivedFileName: | AURORA_STEALER_0/Aurora.exe |
Total processes
146
Monitored processes
15
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" Add-Type -AssemblyName System.Windows.Forms;<#cfg#>[System.Windows.Forms.MessageBox]::Show('','','OK','Error')<#pmm#>; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
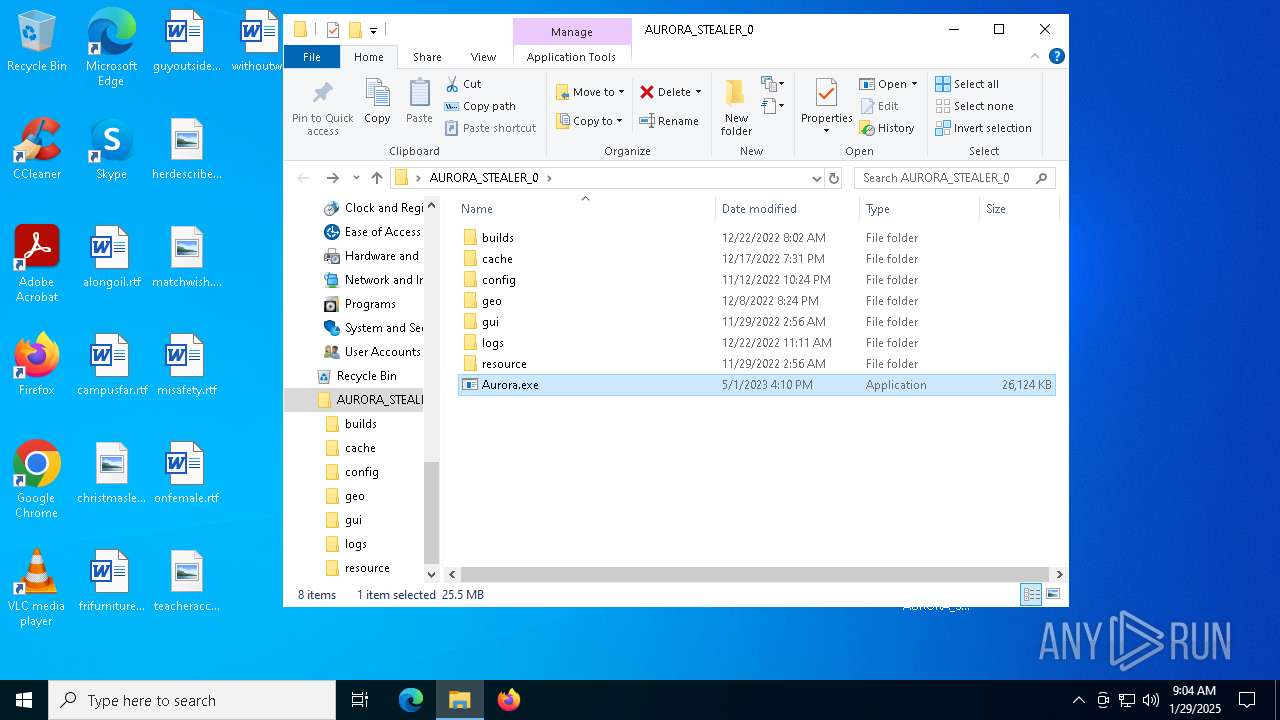
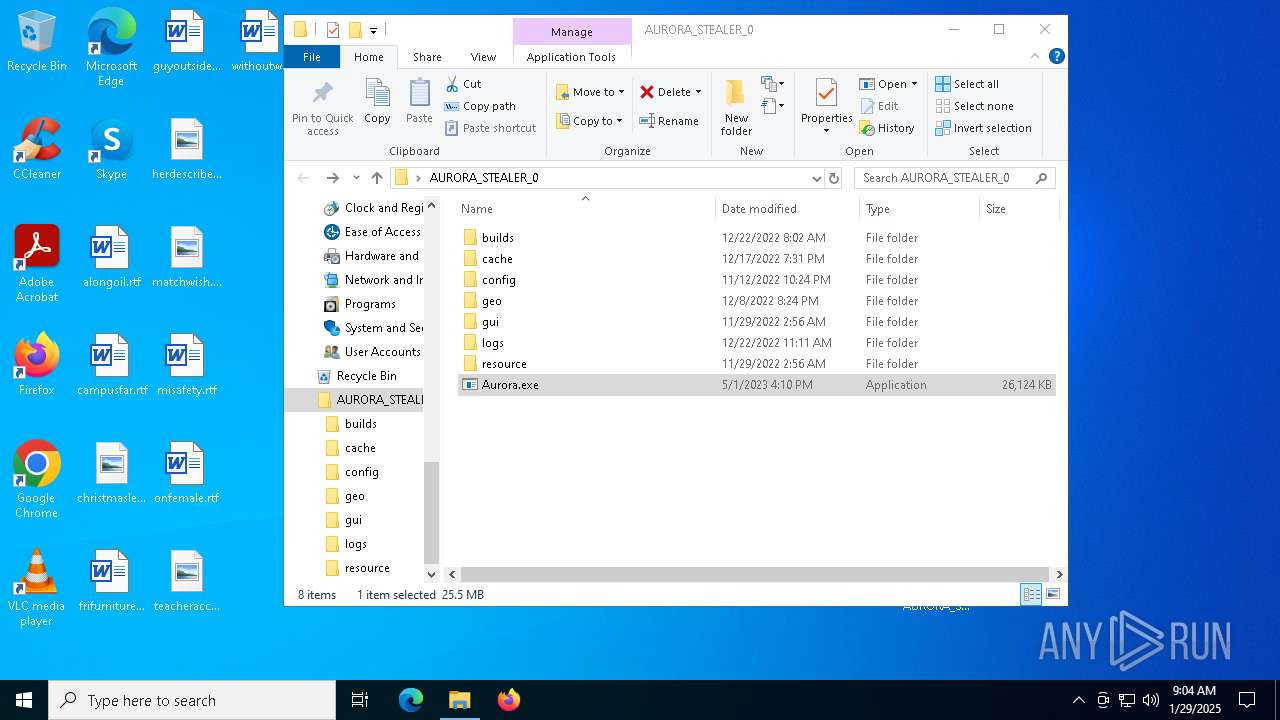
| 1144 | "C:\Users\admin\Desktop\AURORA_STEALER_0\Aurora.exe" | C:\Users\admin\Desktop\AURORA_STEALER_0\Aurora.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1740 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Aurora.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\Temp\Aurora.exe" | C:\Users\admin\AppData\Local\Temp\Aurora.exe | Aurora.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4384 | "C:\Users\admin\AppData\Local\Temp\LX.exe" | C:\Users\admin\AppData\Local\Temp\LX.exe | Aurora.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 5104 | "C:\Users\admin\AppData\Local\Temp\LX.exe" | C:\Users\admin\AppData\Local\Temp\LX.exe | — | Aurora.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 6160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Aurora.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6196 | "C:\Users\admin\AppData\Local\Temp\LX.exe" | C:\Users\admin\AppData\Local\Temp\LX.exe | — | Aurora.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
22 089
Read events
22 068
Write events
21
Delete events
0
Modification events
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\AURORA_STEALER_0.rar | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6584) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
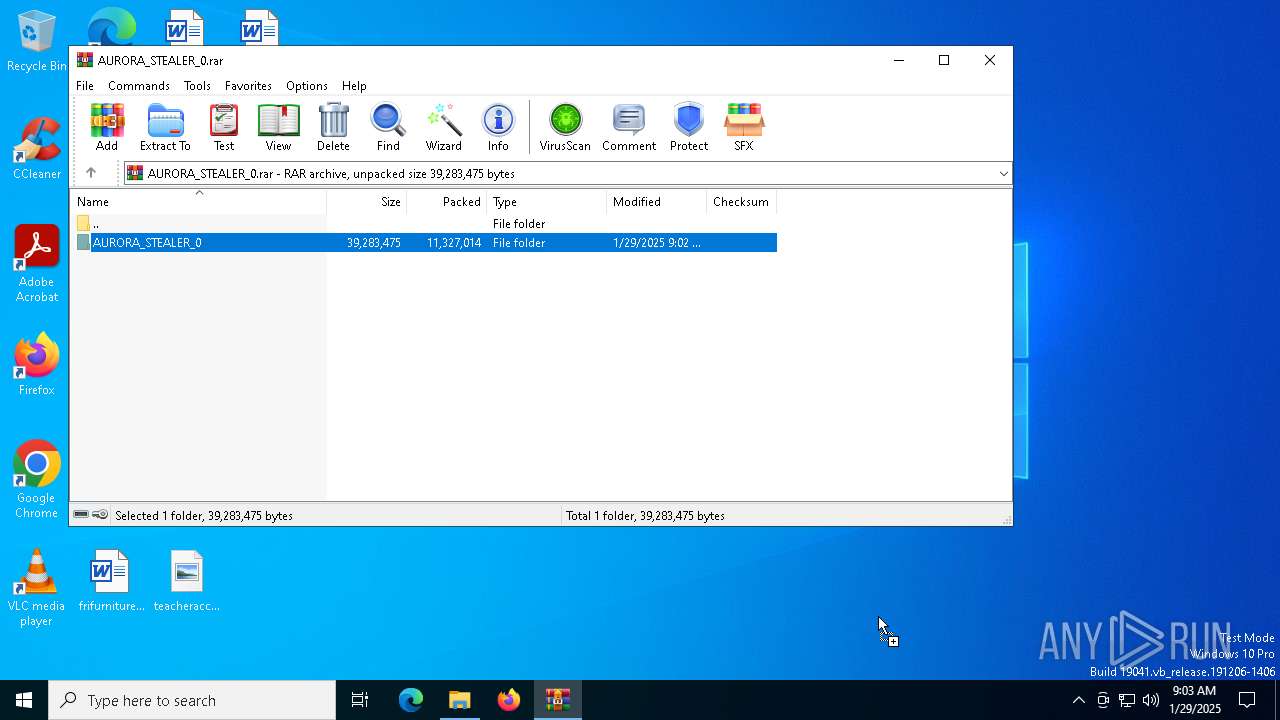
Executable files
4
Suspicious files
6
Text files
565
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\config\telegram.txt | text | |
MD5:500F9BE435AB7D322F8452485ABA41A1 | SHA256:50AB5ACE46C240A851A4D508BE2CC9B7AE4ADFB046683617807471F425F7028A | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\css\flag-icon.min.css | text | |
MD5:79FB36DDA0A235254C3E31BF00B57065 | SHA256:623702BD791D4553AE7226C2F48E26052E359573EB59FA98D819E9B248593E7C | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\Dashboard.html | html | |
MD5:D48D1F160FF80990E5FC123886590158 | SHA256:EB071635072B9F1CCF127D954EA2678767441E77E5C4554FE6E7D22AF1178962 | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\flags\1x1\ae.svg | image | |
MD5:7847726D0663899A3E31B3E21B6D2B68 | SHA256:09943E355944D6870F74093D858503DE204F02CA78F70122A5A7D74897134B6D | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\Dashboard.css | text | |
MD5:5C6C327761E1BF42C558E4B0DCD06B50 | SHA256:53E58CFBA48EA164D29A192EEB6817795171198A08194E57C870DCC0681BA4AB | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\flags\1x1\ad.svg | image | |
MD5:E15DDEABBFCE297178193B7858043EBD | SHA256:5F301EEE62631C50459507A29617AC02CC8106359DA22B9705D3B73E50DCB839 | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\flags\1x1\af.svg | image | |
MD5:FA735E43100E6BA7D02AFC2D27FF088C | SHA256:F0FE67D6B190381B4B7A039173C8D74A2DC8F7773CA6AC79DE25B0B14C8B80F0 | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\flags\1x1\ag.svg | image | |
MD5:53A600867BAB3B2284DA8445E7D9CC93 | SHA256:B0EE8DC5572DB906F3765696C41FBAEF3DF72651FE0EAA306ACFAA310AB80D06 | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\Aurora.exe | executable | |
MD5:EE0A49CAA656FE8693FFEC78E69E864D | SHA256:34E038A53F367FEDA9EB1FFBF71CA6AF8AC9ACE7A34D86C43E1F197C8988057F | |||
| 6584 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6584.21812\AURORA_STEALER_0\gui\assets\docs.less | text | |
MD5:132C2423299CD3874E86643001800E9F | SHA256:A0A82F68375EF66AC9095C9C57754CEA503BB15982360F10ED1DA3095CB50FA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6824 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6824 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
396 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 95.100.110.91:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |