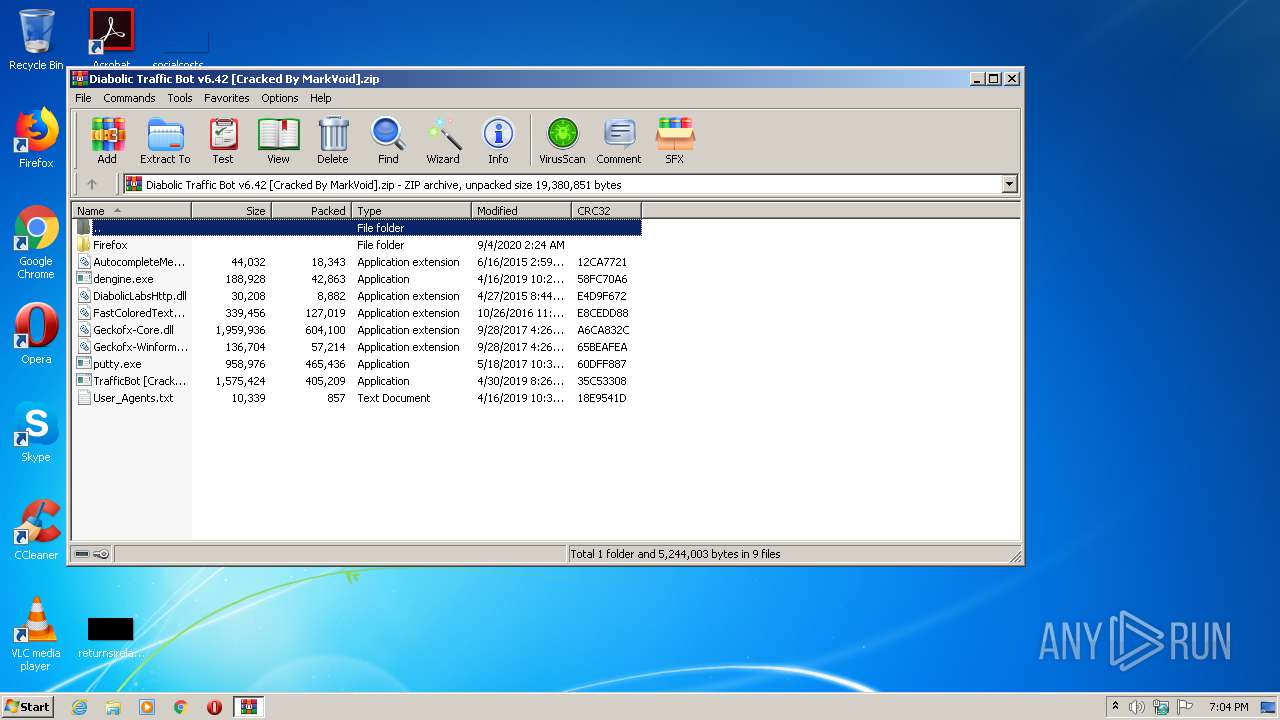
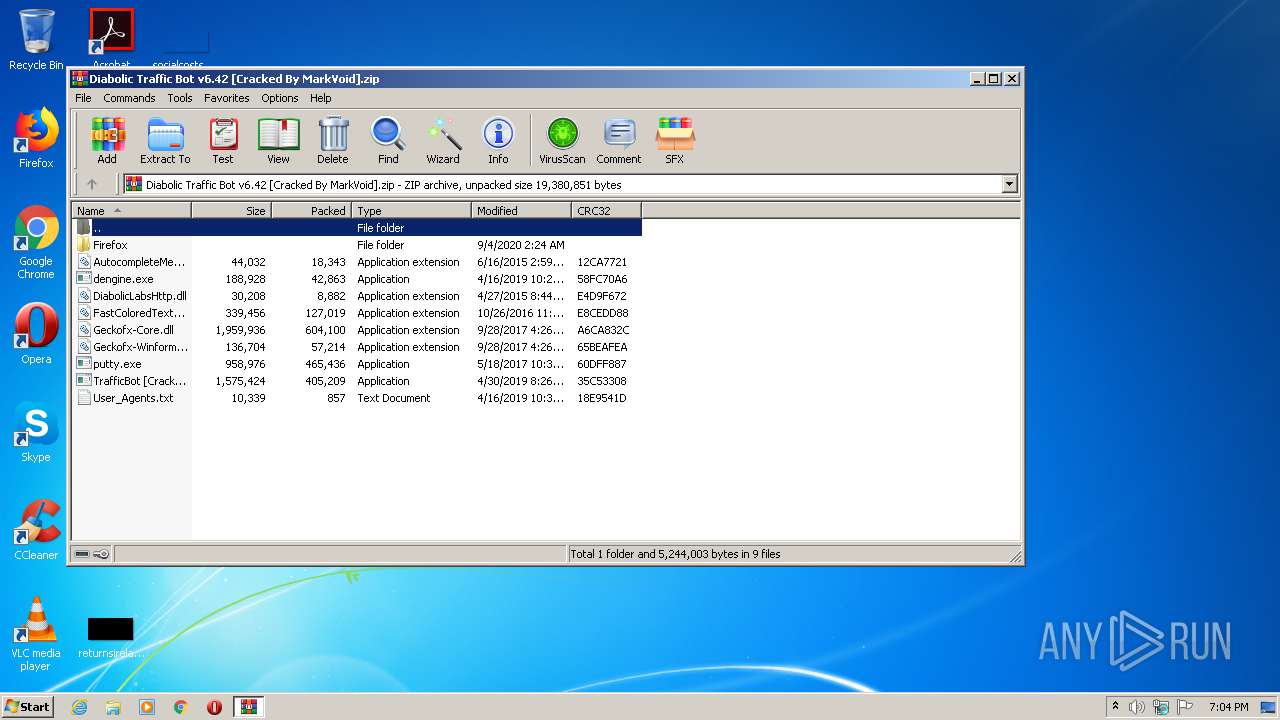
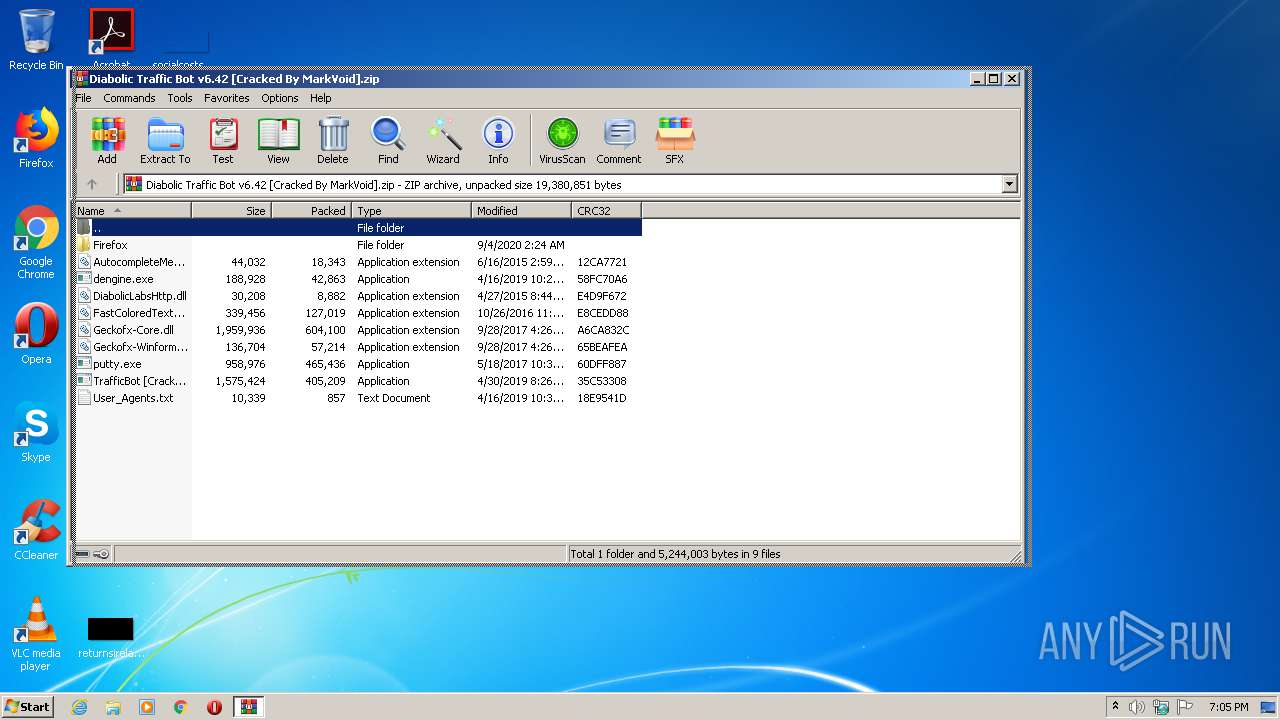
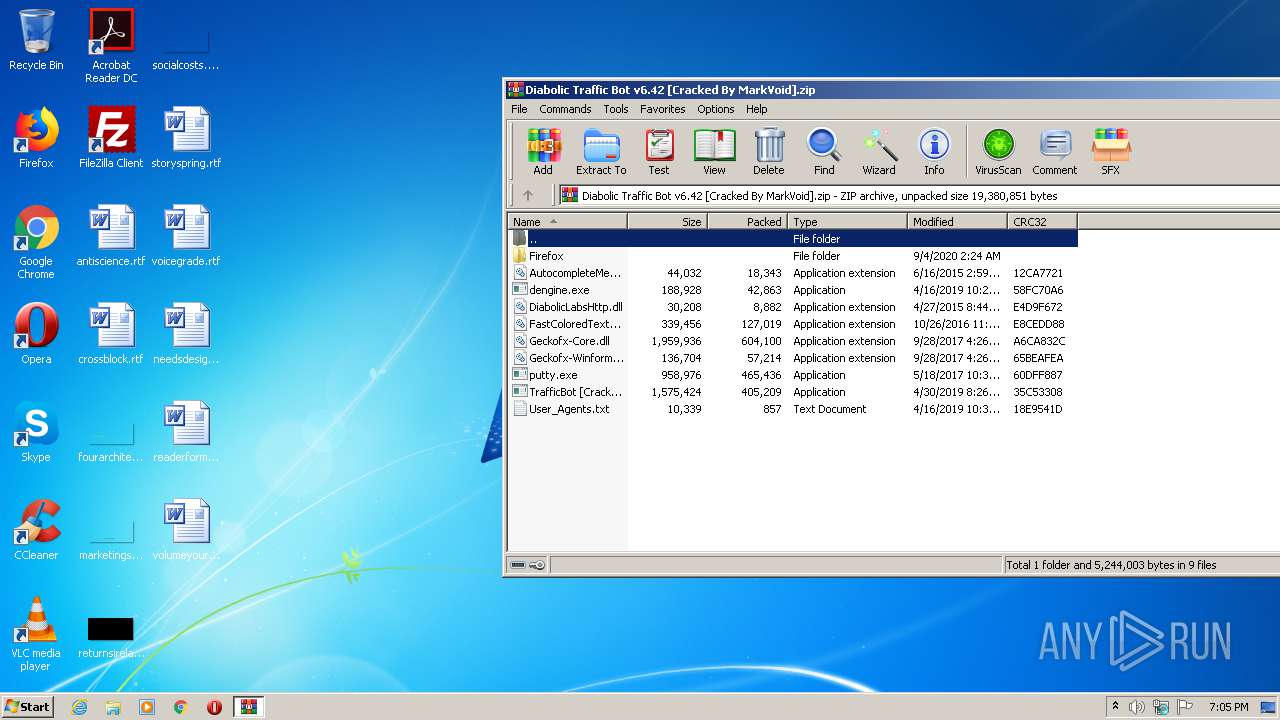
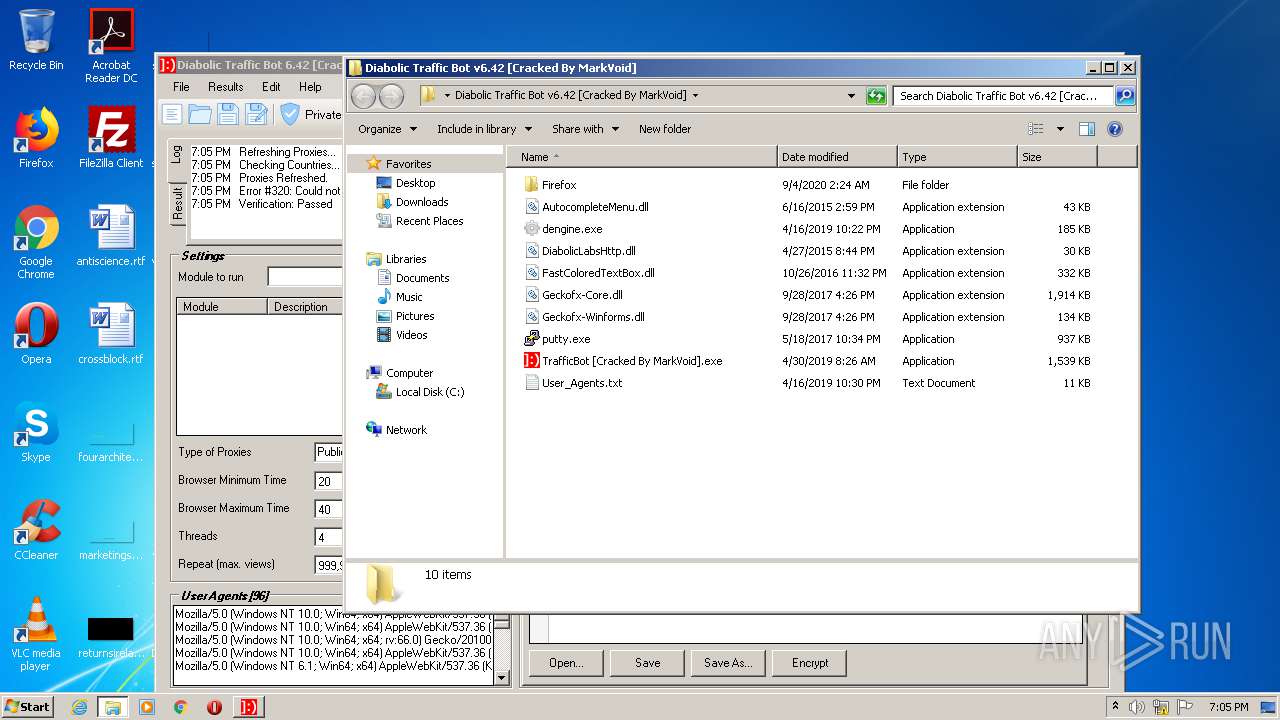
| File name: | Diabolic Traffic Bot v6.42 [Cracked By MarkVoid].zip |
| Full analysis: | https://app.any.run/tasks/f9c52c24-ce2f-4d5f-8fd8-013994761232 |
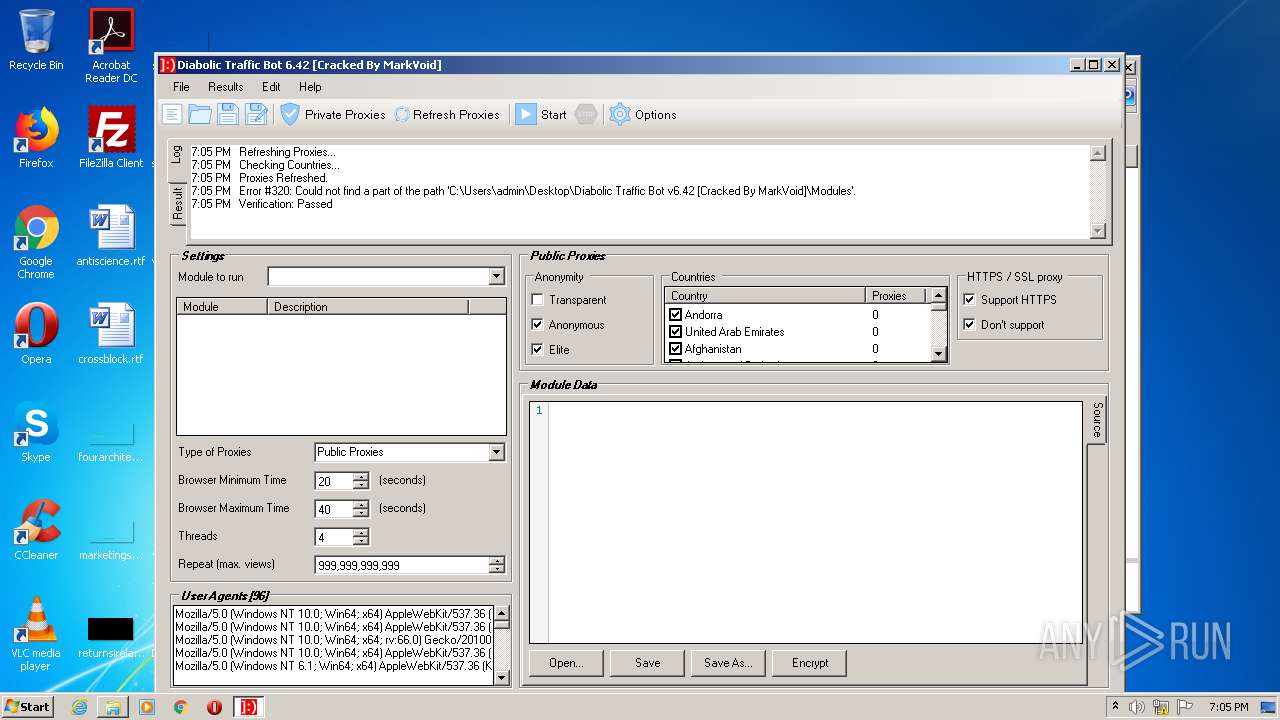
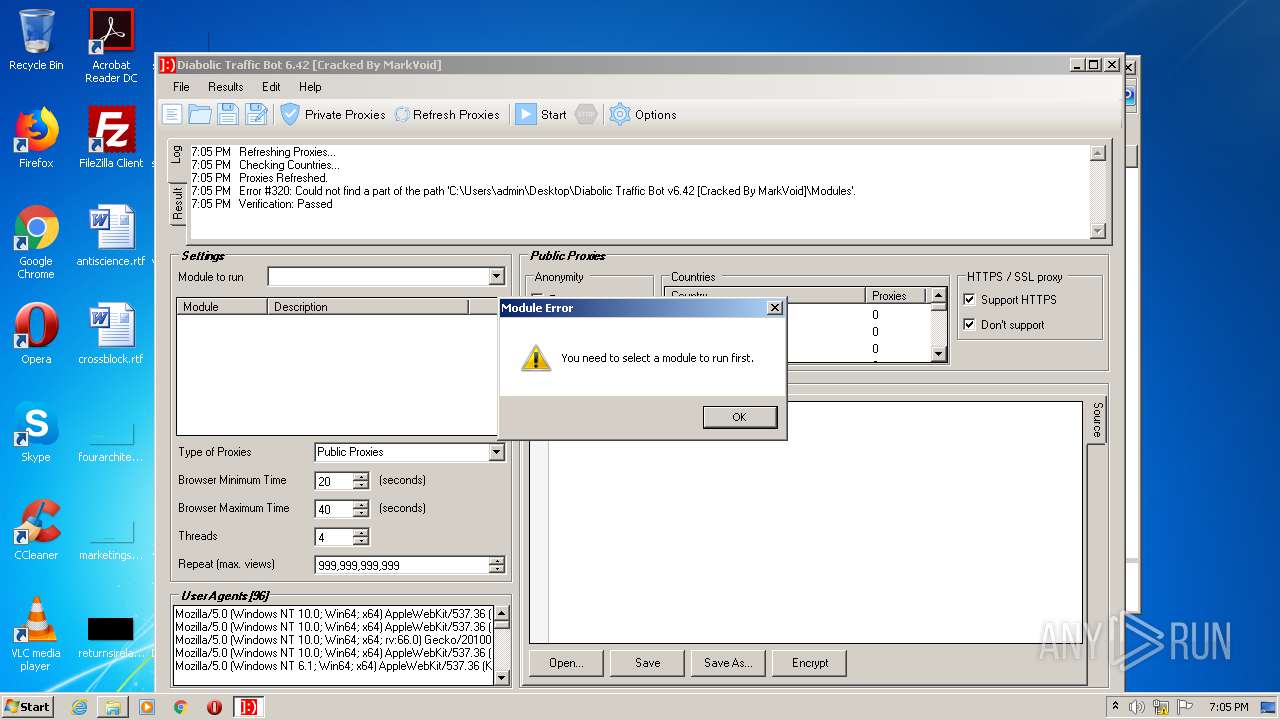
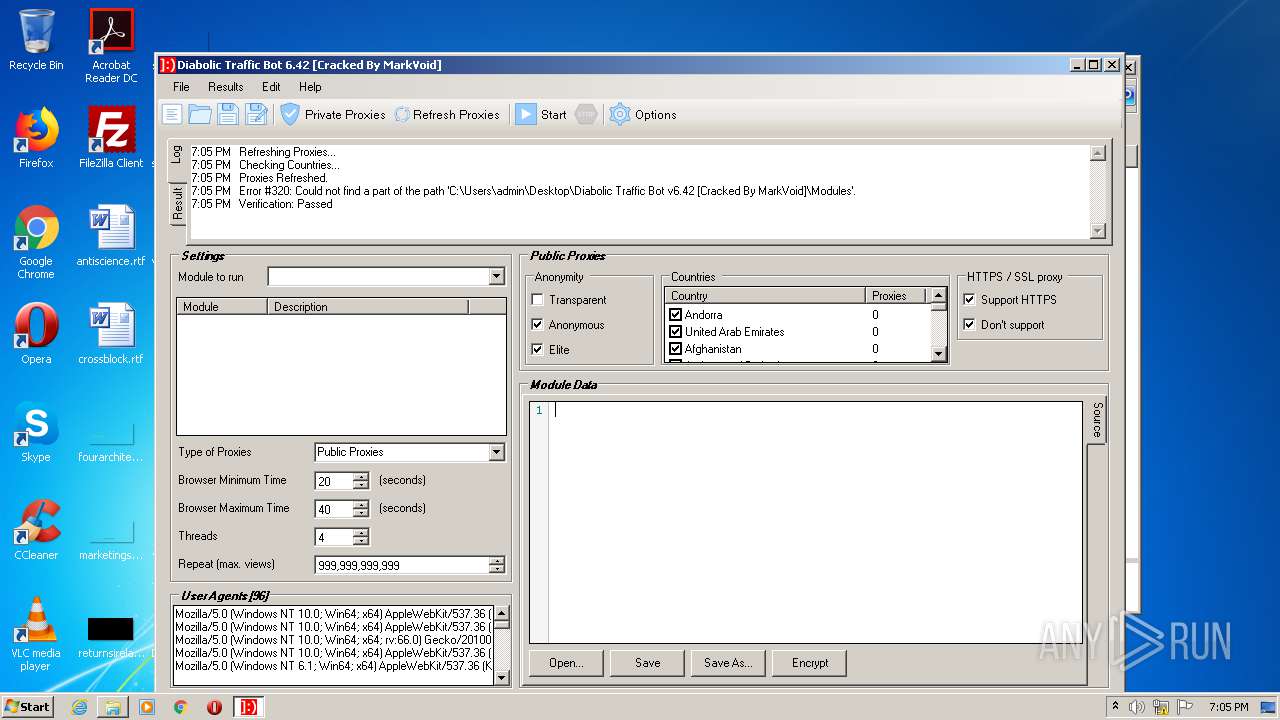
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2021, 18:04:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 370E783A1F4A801C8CF14CA94AB995A0 |
| SHA1: | 9A9610BF81987F4741CEF2C02F232D322EEDA38D |
| SHA256: | D0250B1D2C287D9F2731C7240464D07E1EBE0560C13062D856124ED87FFA2F4A |
| SSDEEP: | 98304:X/FyFuJ2QZLg4IOFSKzuqtWRR7ioinAVFEH5KInuxhNzC7n8xNNlU9ytXhLltyyd:X/QtCdIDGTcDvK5nFOEK17ye1NUbz6d |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2948)
Application was dropped or rewritten from another process
- TrafficBot [Cracked By MarkVoid].exe (PID: 3604)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1012)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1012)
Reads Environment values
- TrafficBot [Cracked By MarkVoid].exe (PID: 3604)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 1012)
Manual execution by user
- TrafficBot [Cracked By MarkVoid].exe (PID: 3604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (33.3) |
|---|
EXIF
ZIP
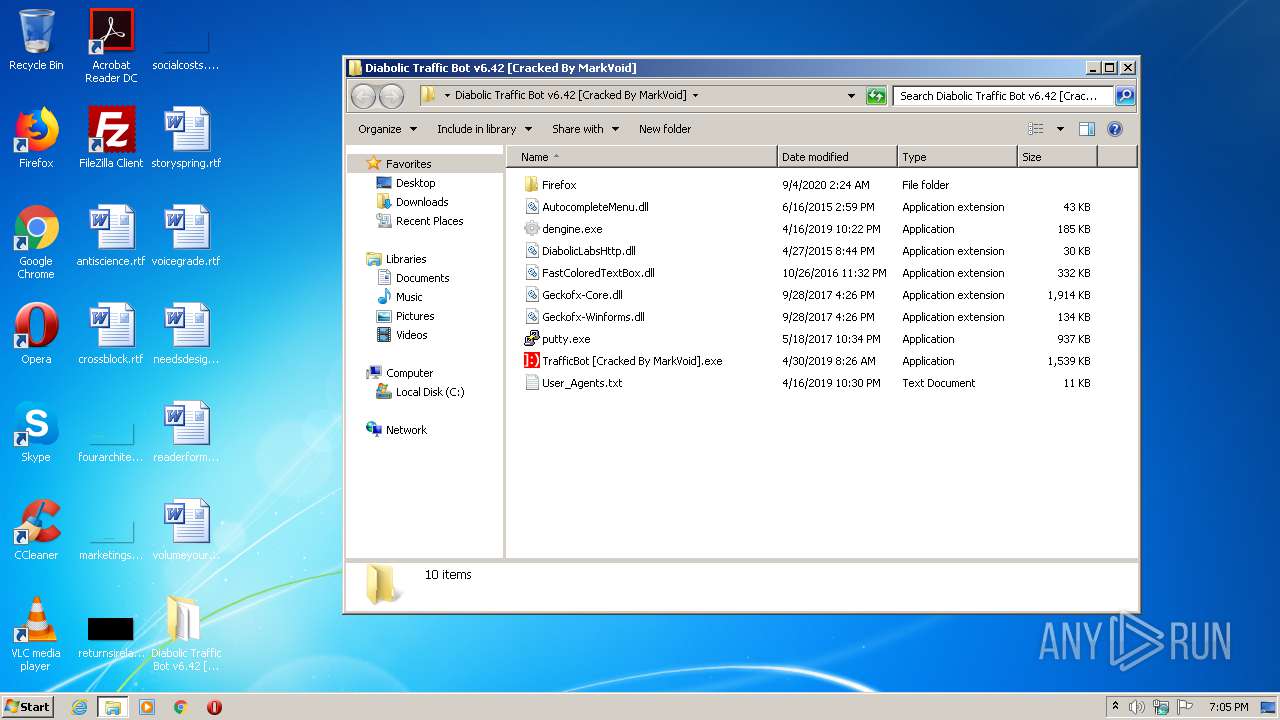
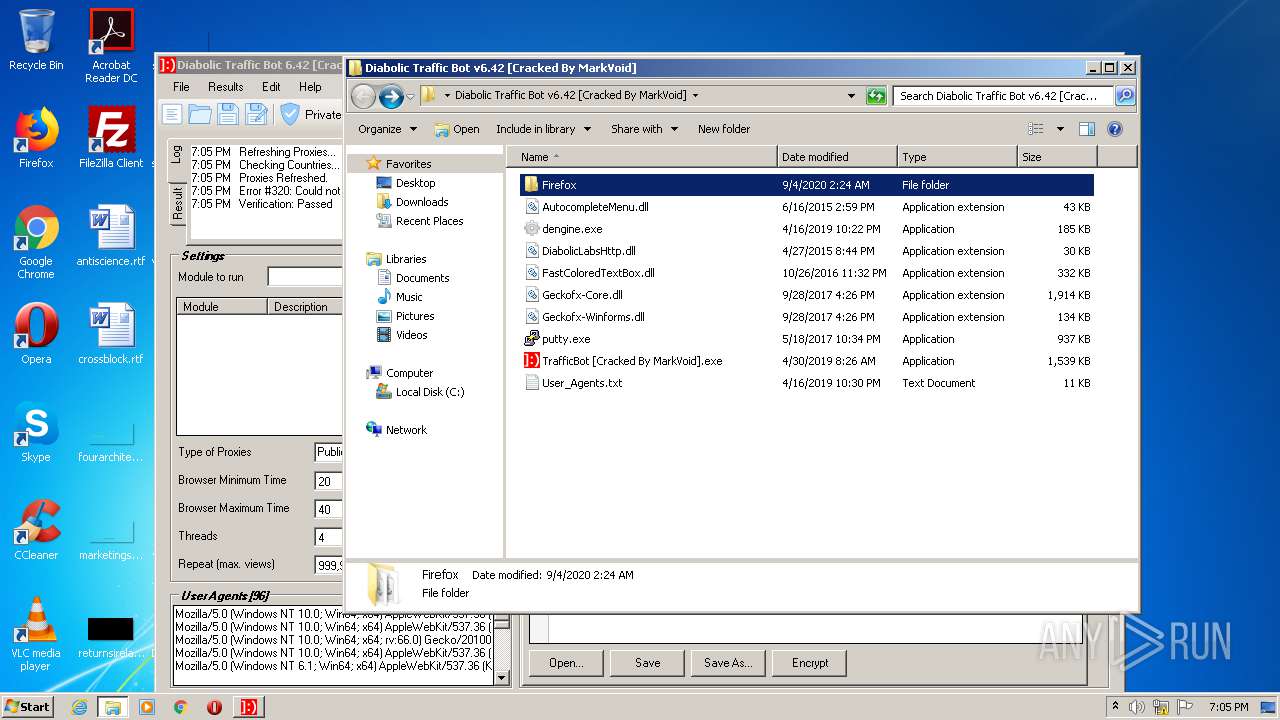
| ZipFileName: | Firefox/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2020:09:04 03:24:24 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
40
Monitored processes
3
Malicious processes
3
Suspicious processes
0
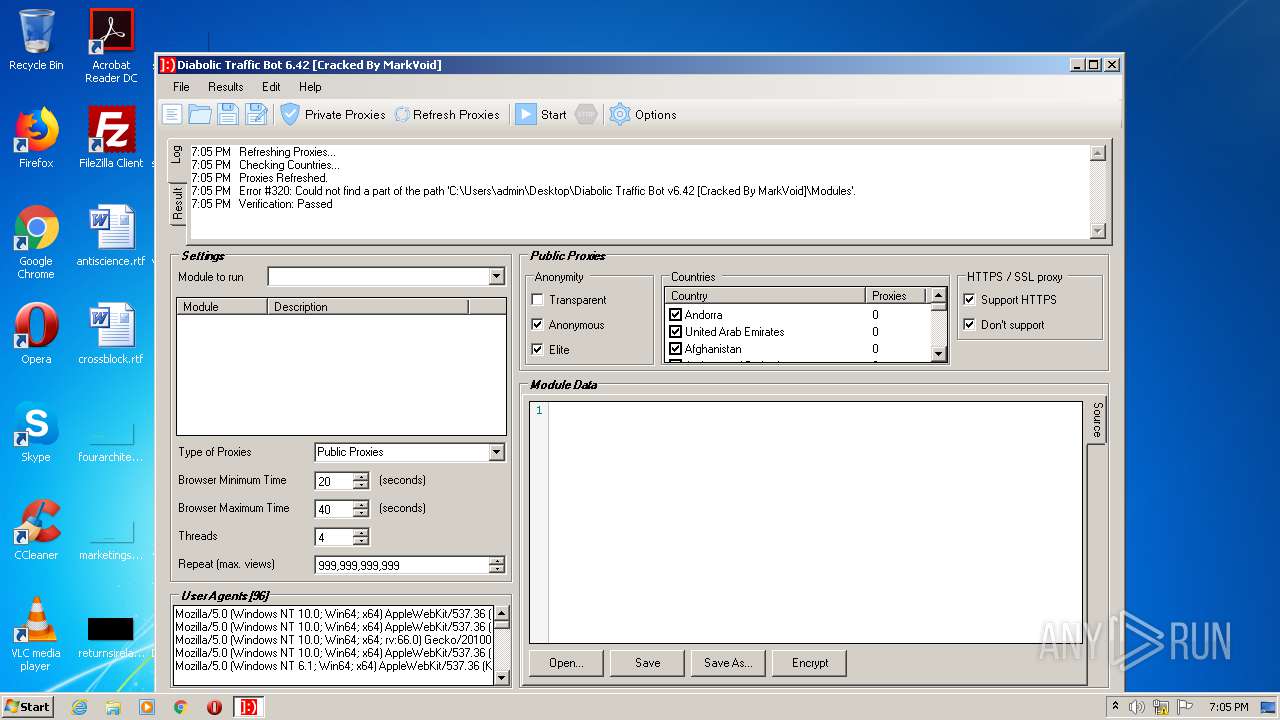
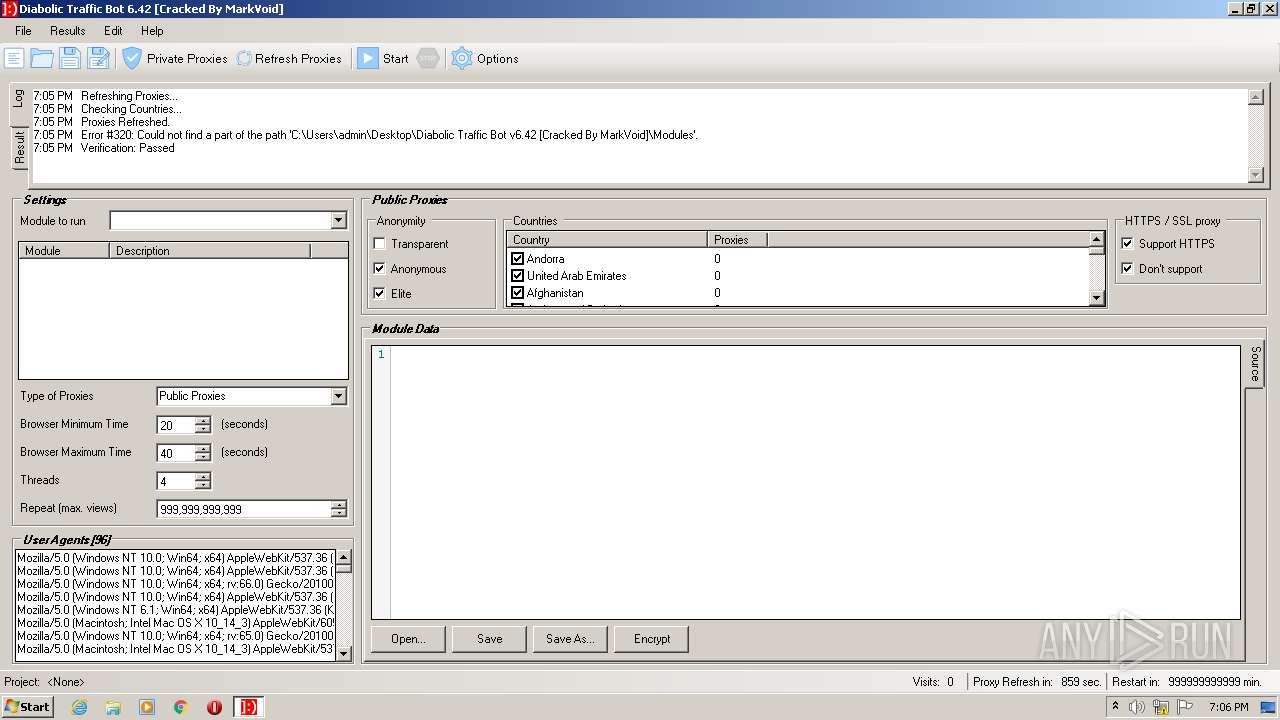
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
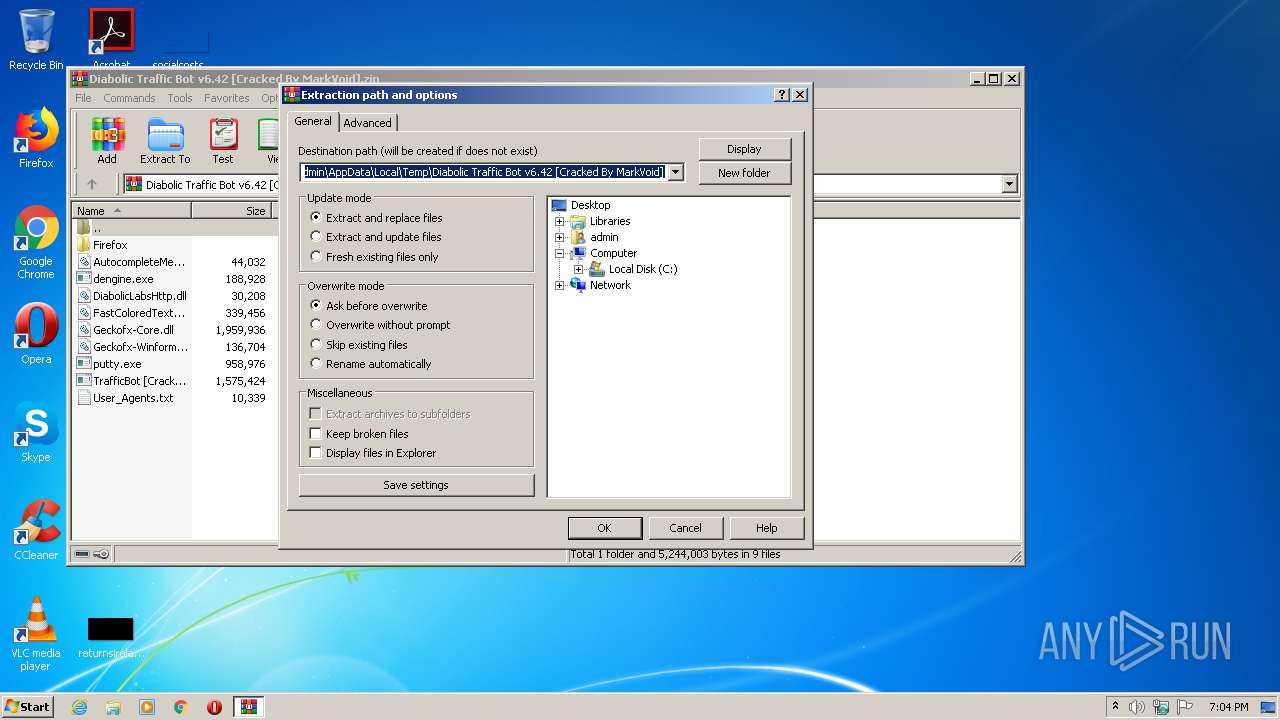
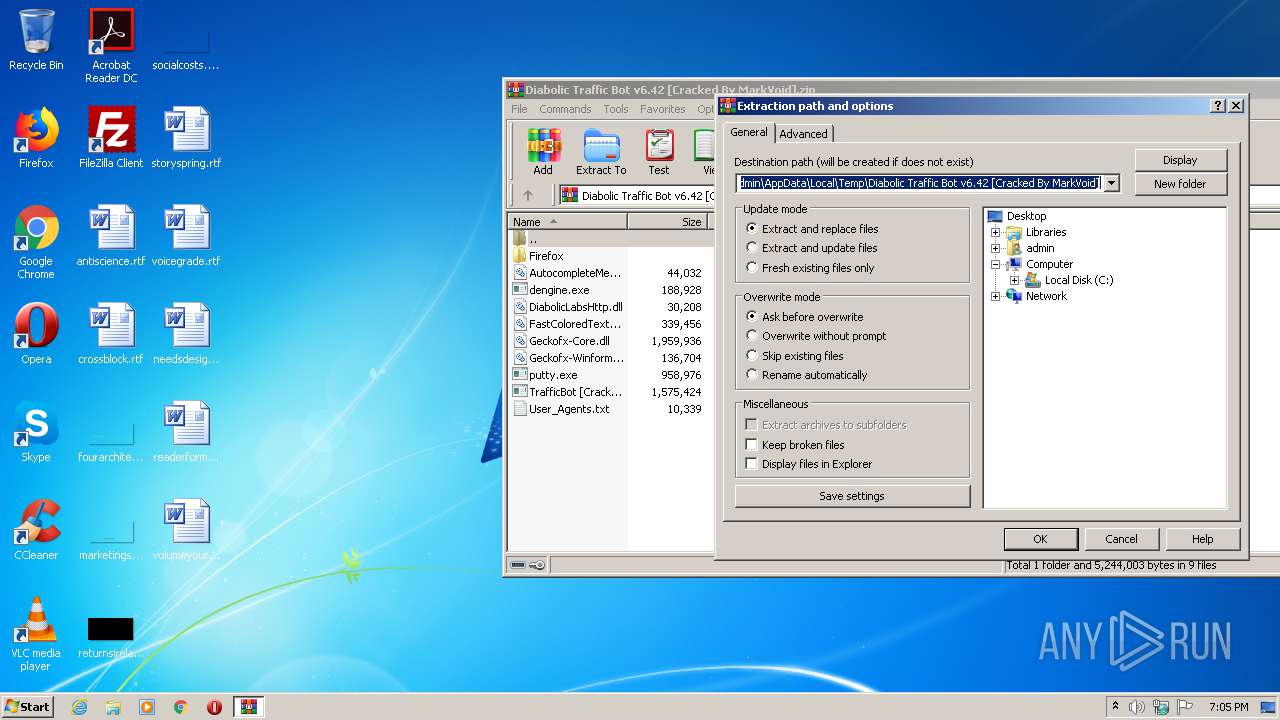
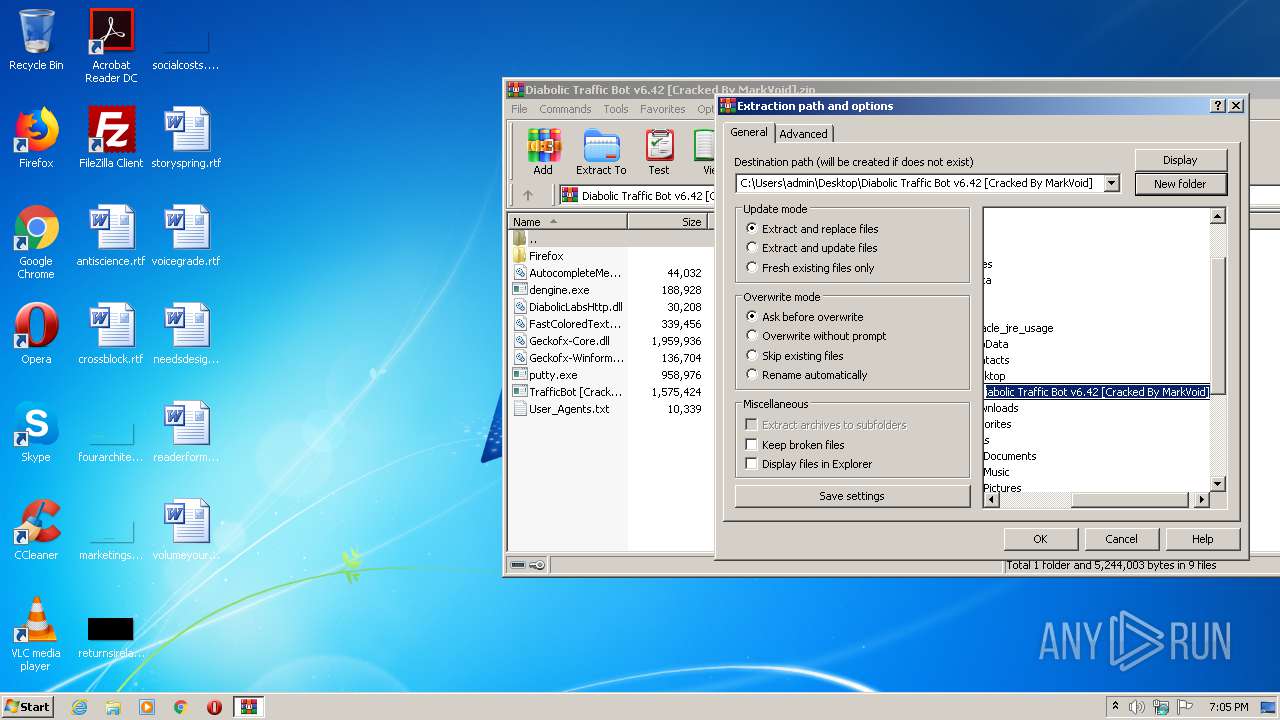
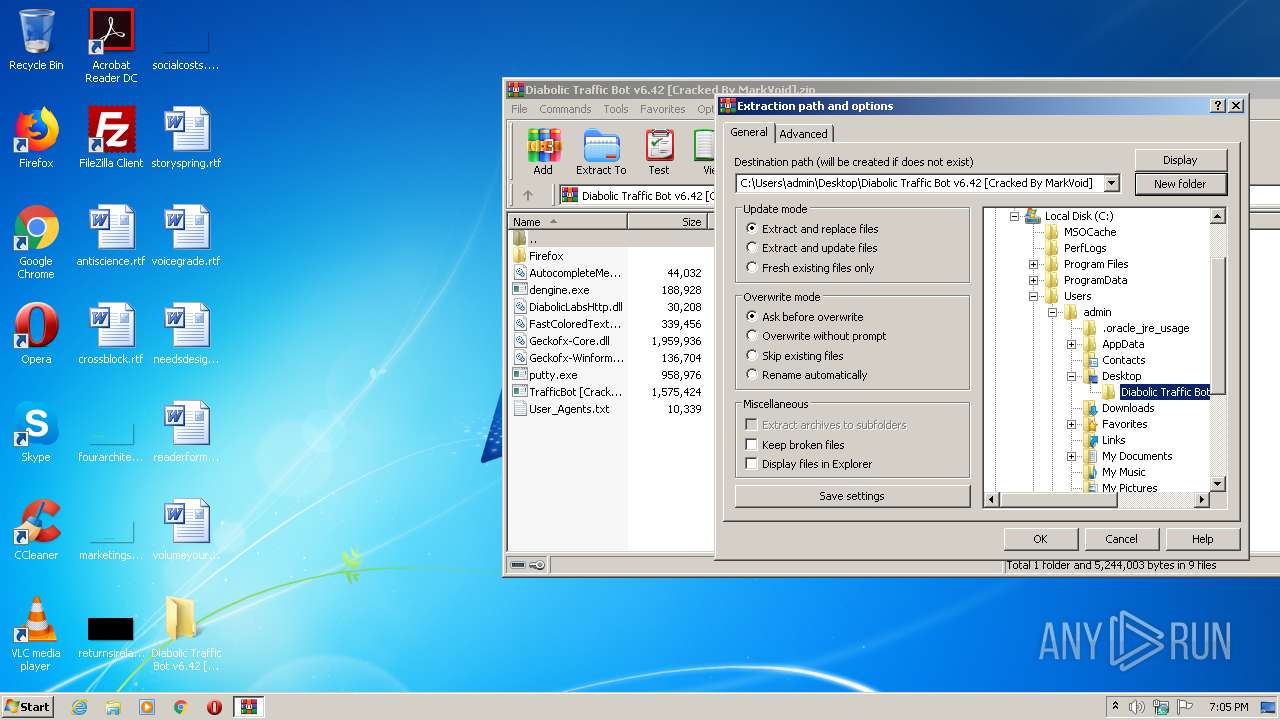
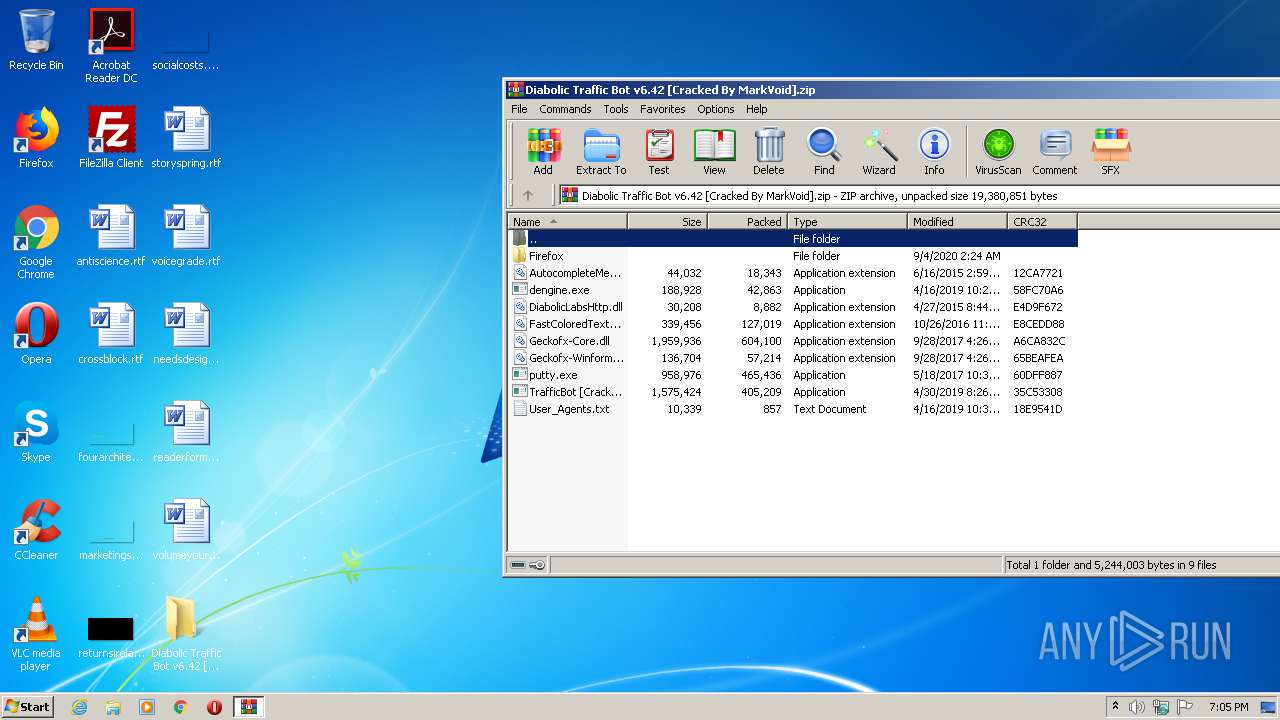
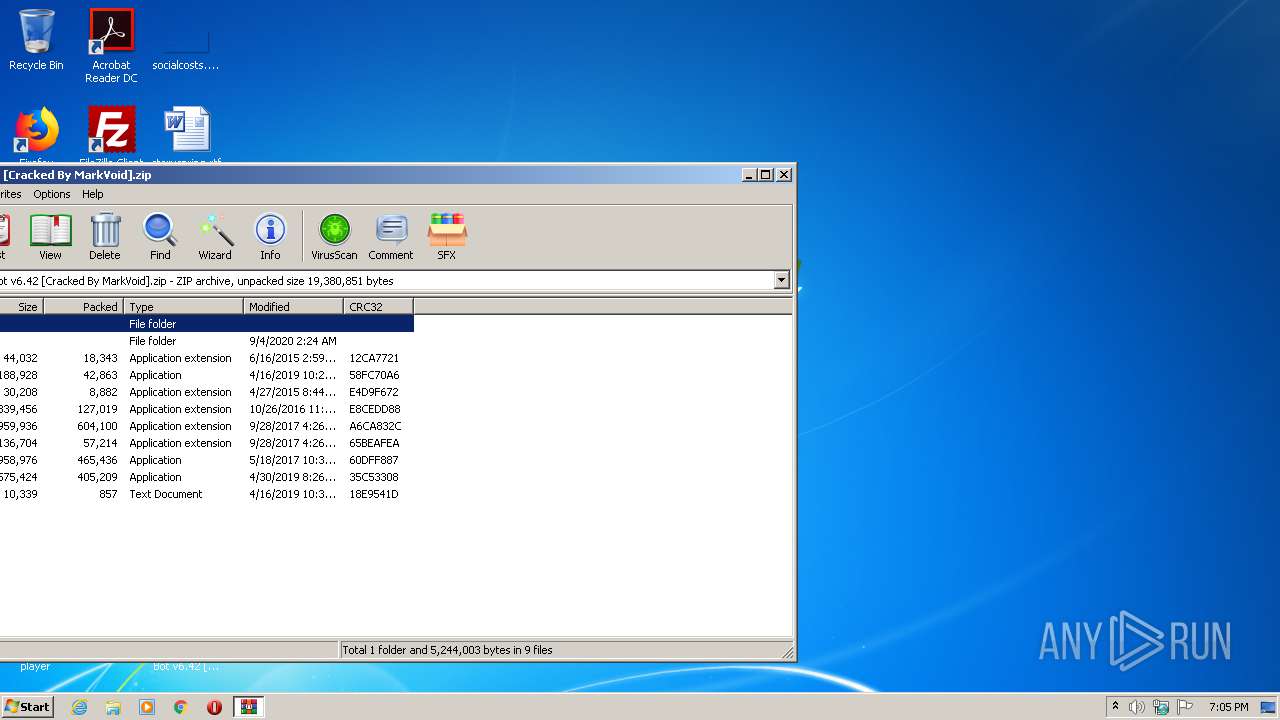
| 1012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid].zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2948 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3604 | "C:\Users\admin\Desktop\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\TrafficBot [Cracked By MarkVoid].exe" | C:\Users\admin\Desktop\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\TrafficBot [Cracked By MarkVoid].exe | — | explorer.exe | |||||||||||
User: admin Company: Diabolic Labs Integrity Level: MEDIUM Description: Traffic Bot Exit code: 0 Version: 6.42 Modules
| |||||||||||||||
Total events
885
Read events
833
Write events
52
Delete events
0
Modification events
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid].zip | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
56
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
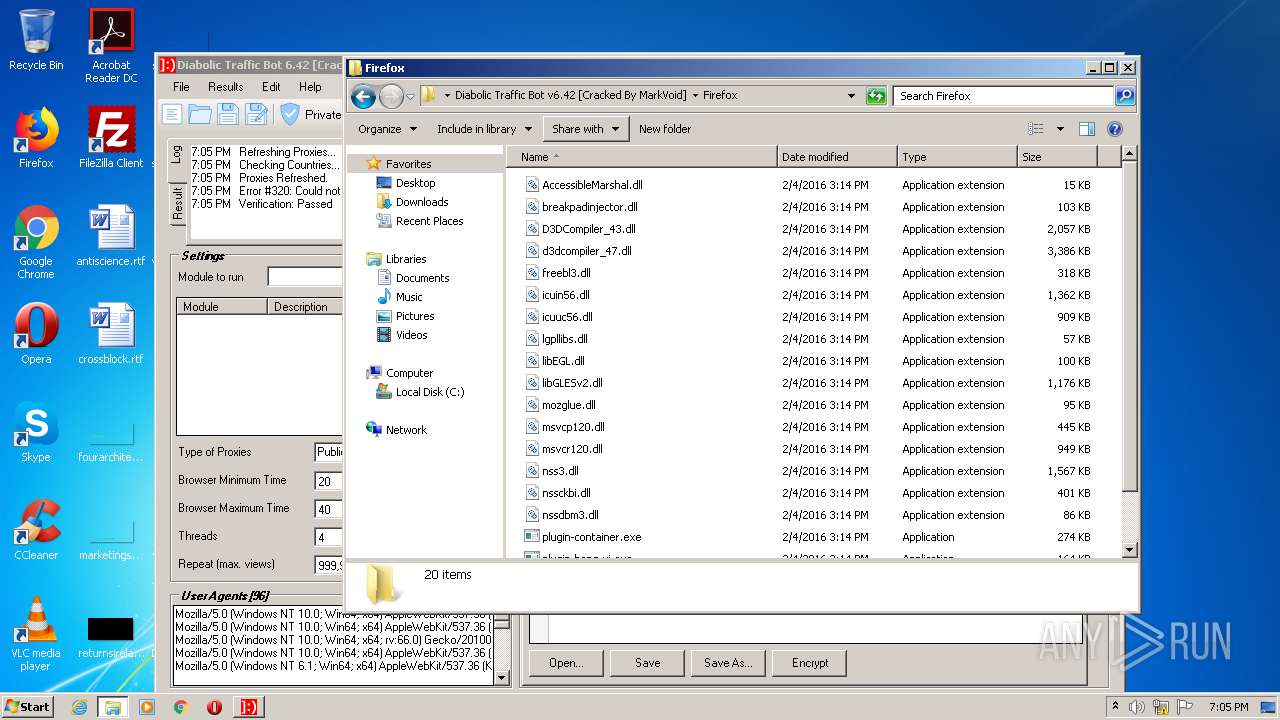
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\AccessibleMarshal.dll | executable | |
MD5:59CC6AD62CDB45A281A602369DC69FDA | SHA256:F16C9311830CA1628448AE4ABA4B54DF33AC1CD1682BCBBB129E4B28D6536B6C | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\breakpadinjector.dll | executable | |
MD5:8BD17858D43DCFF0B5336C6C5A6B8A17 | SHA256:B13177B1DB8E44F333FF63080D97AED8E51767ABB2FECD5DCA3E565C81685E60 | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\icuin56.dll | executable | |
MD5:109A802AAA0177266CF0D045B8C26C56 | SHA256:58356AF3F49E25ED2201D3367EB3CA49DEC8EC78D5711475719778EBA3CFD8AD | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\libEGL.dll | executable | |
MD5:F761BE1F6E49B08A8724496D1FE16343 | SHA256:6806DEF406AE61AFEDBDF8C3D70E5FF8B85B21DDFEF910080AE263932A6E106E | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\libGLESv2.dll | executable | |
MD5:9191452050C86F3B6CA9278A276E0F23 | SHA256:348703ADDA8FE086CC8DB304C8638D4A496A4A86F2AE3BE916CB52A9B787C28A | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\lgpllibs.dll | executable | |
MD5:6E218202CF13E07DF71B28A5CB797387 | SHA256:8546698D1C5E38CD055E41ED9B5787BFD0299AAC0C2923C5759884B5A9B944B8 | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\msvcr120.dll | executable | |
MD5:034CCADC1C073E4216E9466B720F9849 | SHA256:86E39B5995AF0E042FCDAA85FE2AEFD7C9DDC7AD65E6327BD5E7058BC3AB615F | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\icuuc56.dll | executable | |
MD5:CD75F5084539123B8664D05A42649498 | SHA256:DB4A924F2DE1998590918702ABE526CFC5579646C8F327E14E445E62B1F789D4 | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\softokn3.dll | executable | |
MD5:A7FD2CCE764CB5F5F2CD3AFBEE51C8A0 | SHA256:B6F798B688E15AB2041E177D7C13D35AB936A5532F90094F595E19299BF9625B | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid]\Firefox\msvcp120.dll | executable | |
MD5:FD5CABBE52272BD76007B68186EBAF00 | SHA256:87C42CA155473E4E71857D03497C8CBC28FA8FF7F2C8D72E8A1F39B71078F608 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
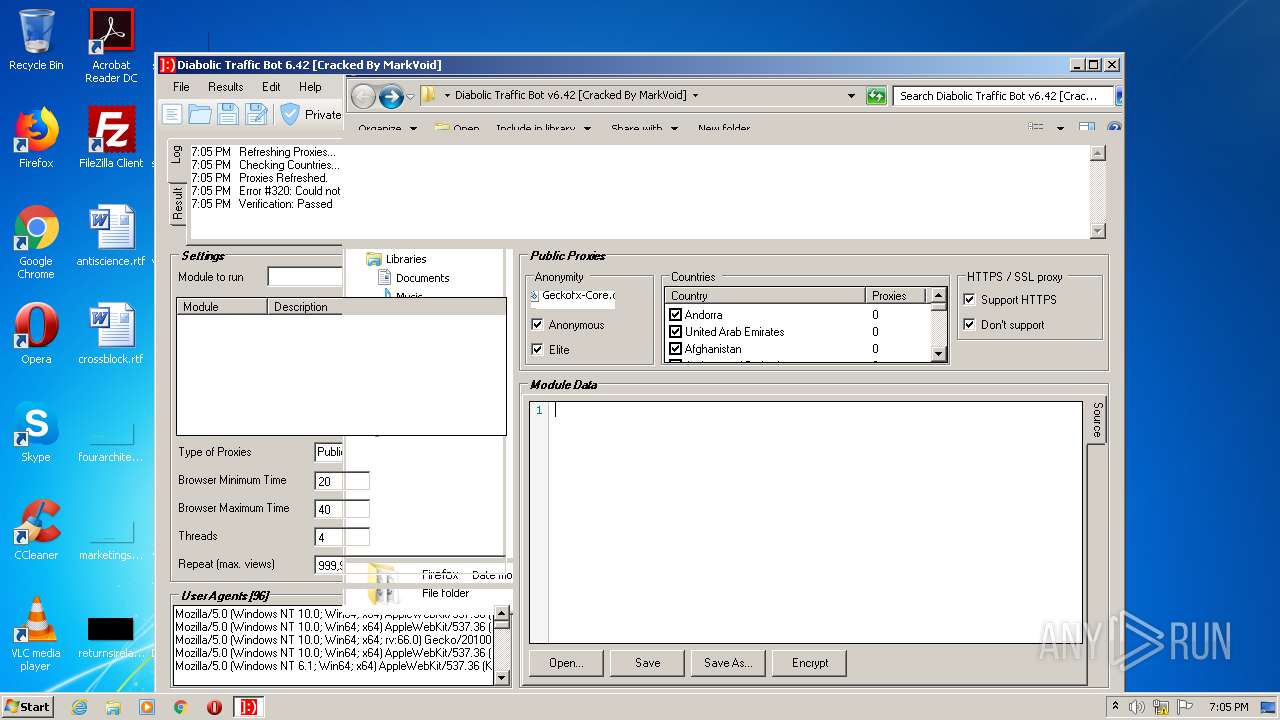
DNS requests
Domain | IP | Reputation |
|---|---|---|
prx.biz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |