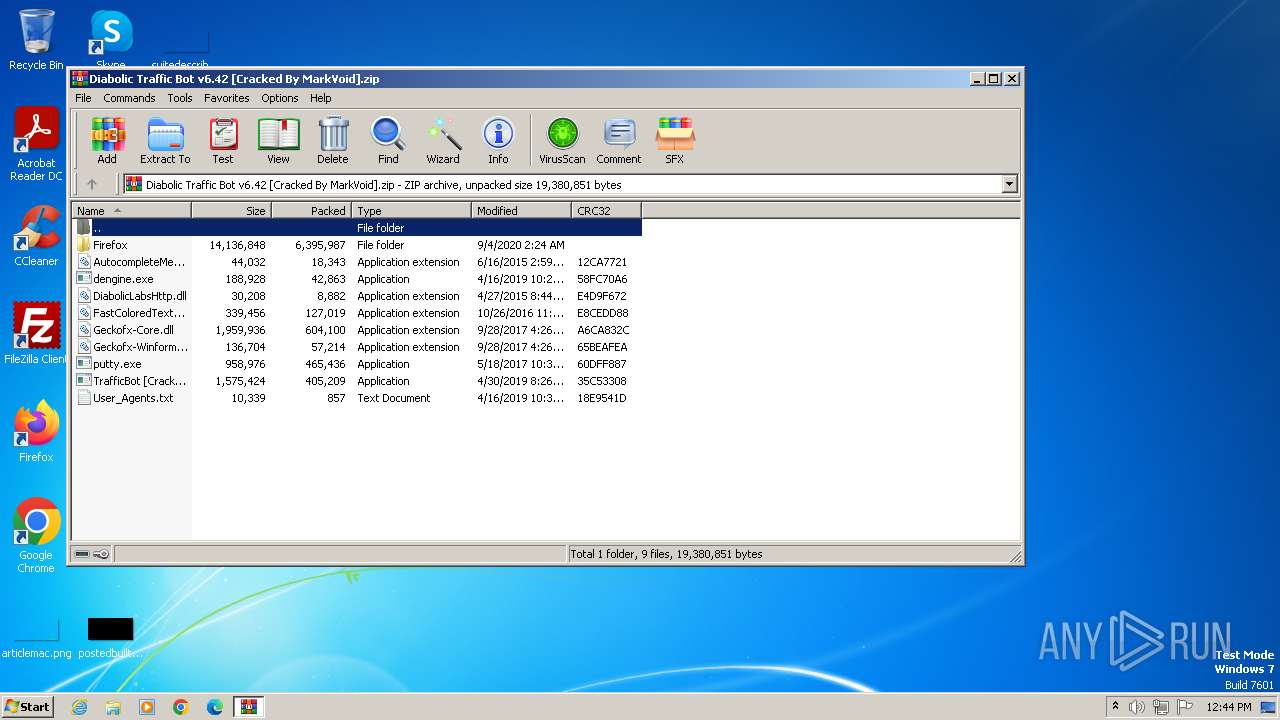
| File name: | Diabolic Traffic Bot v6.42 [Cracked By MarkVoid].zip |
| Full analysis: | https://app.any.run/tasks/f079e484-845c-4d9c-90ce-5a379d8fc48e |
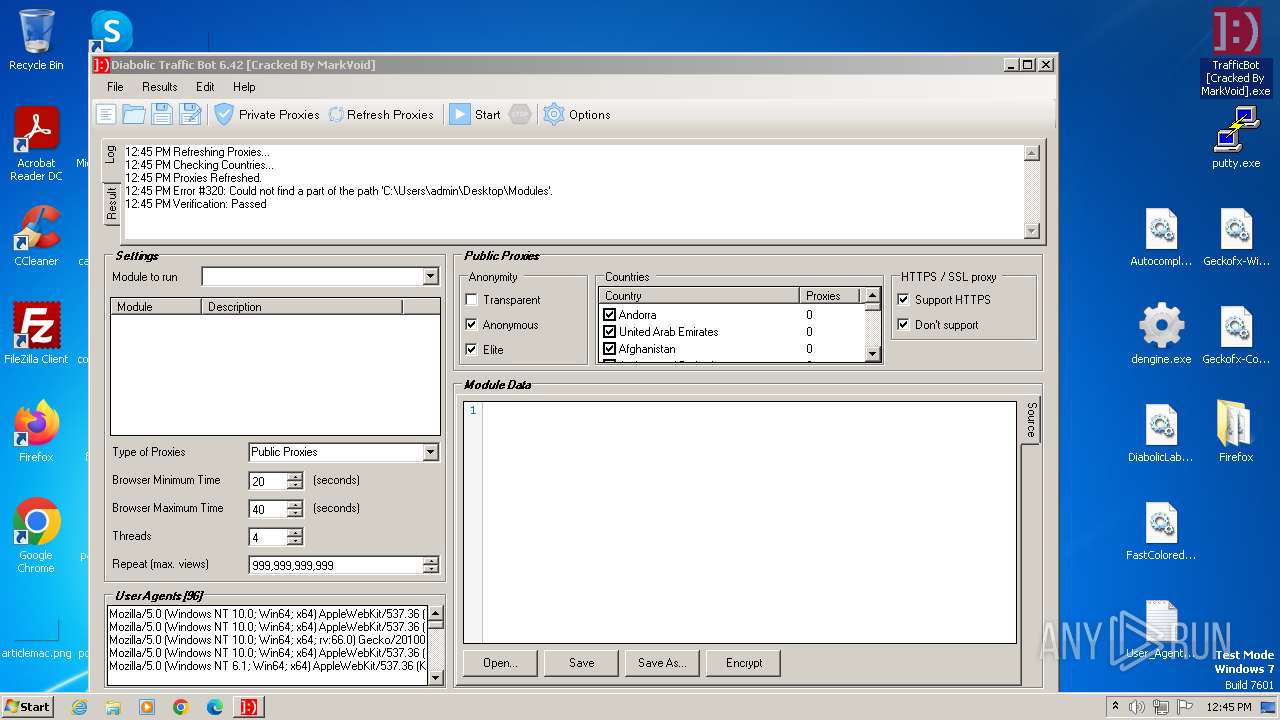
| Verdict: | Malicious activity |
| Analysis date: | October 30, 2023, 12:44:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 370E783A1F4A801C8CF14CA94AB995A0 |
| SHA1: | 9A9610BF81987F4741CEF2C02F232D322EEDA38D |
| SHA256: | D0250B1D2C287D9F2731C7240464D07E1EBE0560C13062D856124ED87FFA2F4A |
| SSDEEP: | 98304:iXAkGQ/WghqMKQ1UlDItuXocBNShI9IhMbVCkXPuZqwiICwM8C7A8+emiDuuTd7y:+UHMt+LXhAPN |
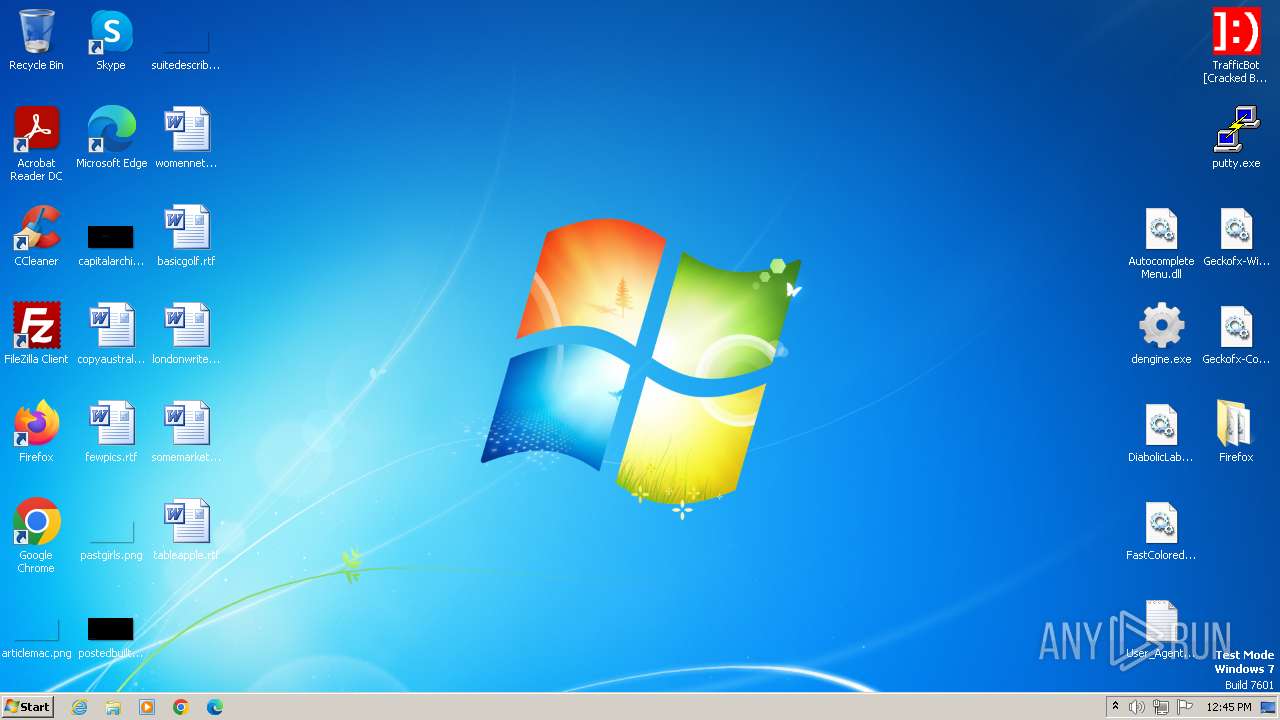
MALICIOUS
Application was dropped or rewritten from another process
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
Loads dropped or rewritten executable
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 1796)
Reads the Internet Settings
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
INFO
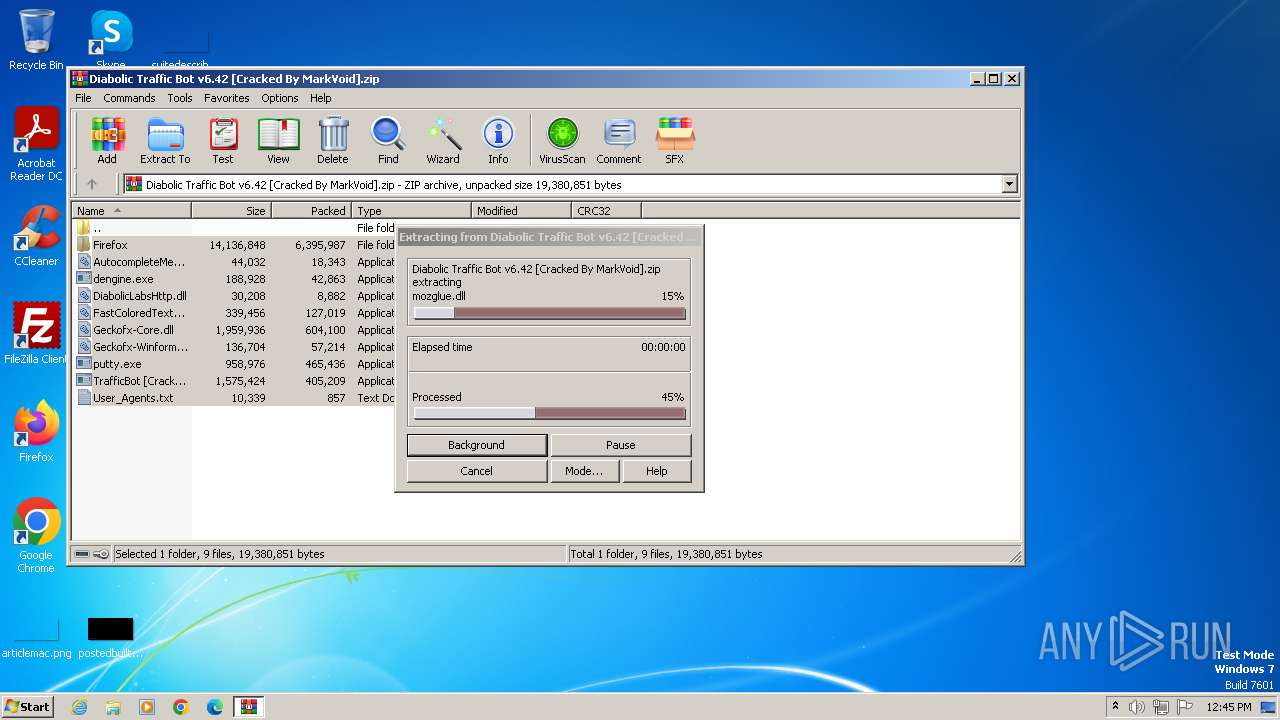
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1796)
Reads the computer name
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
Checks supported languages
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
Reads Environment values
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
Manual execution by a user
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
Reads the machine GUID from the registry
- TrafficBot [Cracked By MarkVoid].exe (PID: 3704)
- TrafficBot [Cracked By MarkVoid].exe (PID: 1372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (33.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:09:04 03:24:48 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Firefox/ |
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
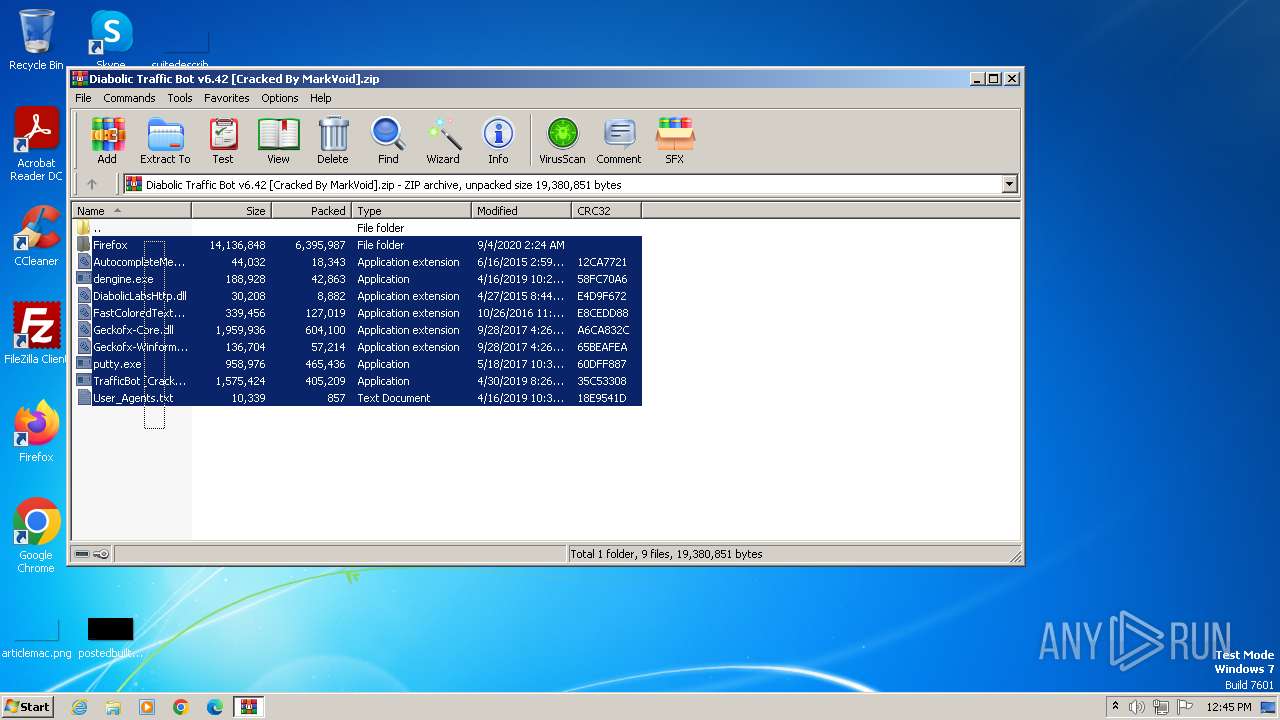
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 1372 | "C:\Users\admin\Desktop\TrafficBot [Cracked By MarkVoid].exe" | C:\Users\admin\Desktop\TrafficBot [Cracked By MarkVoid].exe | — | explorer.exe | |||||||||||
User: admin Company: Diabolic Labs Integrity Level: MEDIUM Description: Traffic Bot Exit code: 0 Version: 6.42 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Diabolic Traffic Bot v6.42 [Cracked By MarkVoid].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3704 | "C:\Users\admin\Desktop\TrafficBot [Cracked By MarkVoid].exe" | C:\Users\admin\Desktop\TrafficBot [Cracked By MarkVoid].exe | — | explorer.exe | |||||||||||
User: admin Company: Diabolic Labs Integrity Level: MEDIUM Description: Traffic Bot Exit code: 0 Version: 6.42 Modules
| |||||||||||||||
Total events
2 395
Read events
2 374
Write events
21
Delete events
0
Modification events
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (520) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
28
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\AccessibleMarshal.dll | executable | |
MD5:59CC6AD62CDB45A281A602369DC69FDA | SHA256:F16C9311830CA1628448AE4ABA4B54DF33AC1CD1682BCBBB129E4B28D6536B6C | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\mozglue.dll | executable | |
MD5:67360640285661EB1004C704D760F7AD | SHA256:0EDCFA424F9DA0D1894D99B99DB4DE8EA1B31F7717E8E14DD643F87D4D1C8EB6 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\breakpadinjector.dll | executable | |
MD5:8BD17858D43DCFF0B5336C6C5A6B8A17 | SHA256:B13177B1DB8E44F333FF63080D97AED8E51767ABB2FECD5DCA3E565C81685E60 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\msvcp120.dll | executable | |
MD5:FD5CABBE52272BD76007B68186EBAF00 | SHA256:87C42CA155473E4E71857D03497C8CBC28FA8FF7F2C8D72E8A1F39B71078F608 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\nss3.dll | executable | |
MD5:165FA7CD4A06C3B14EB24FFCE036F69B | SHA256:4C965AB79D4C7131F87D5CDE7ECC8923BE8D26E86F4EE3A6A15463AEB97A413A | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\softokn3.dll | executable | |
MD5:A7FD2CCE764CB5F5F2CD3AFBEE51C8A0 | SHA256:B6F798B688E15AB2041E177D7C13D35AB936A5532F90094F595E19299BF9625B | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\nssckbi.dll | executable | |
MD5:CB2C4AB44B14C9567015EC4352A4FBBC | SHA256:E807076EDEFA13AA292A6DB354F98A8243C868F71988C7D80954B14816107588 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\plugin-hang-ui.exe | executable | |
MD5:CA7A4661F14428D997C436224C44F31D | SHA256:764A165A2C9B99CDDD81353E304F2BCBB5660943CB019A4CDD6E176F5D2D3543 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\sandboxbroker.dll | executable | |
MD5:E15060600DD74BAFF625E75132BEB6AF | SHA256:C58556EA4237F702C5893756006788CB17B5EF16B8D97BFEDE1C51432C35AB79 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.38675\Firefox\plugin-container.exe | executable | |
MD5:E428725AE38BF1803CCCBF348D280D39 | SHA256:70AD689E89C97476474F209A802167EB058DCE71C7EEBE83FA633C8920B24461 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
prx.biz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |