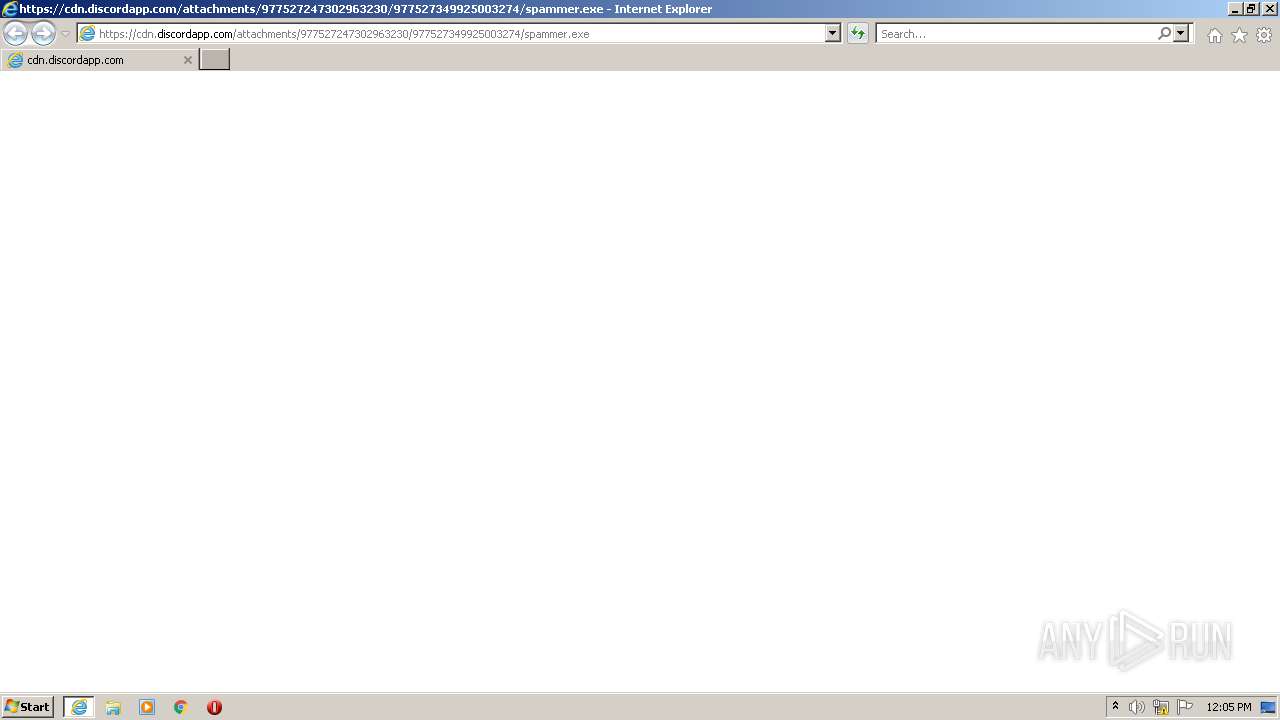
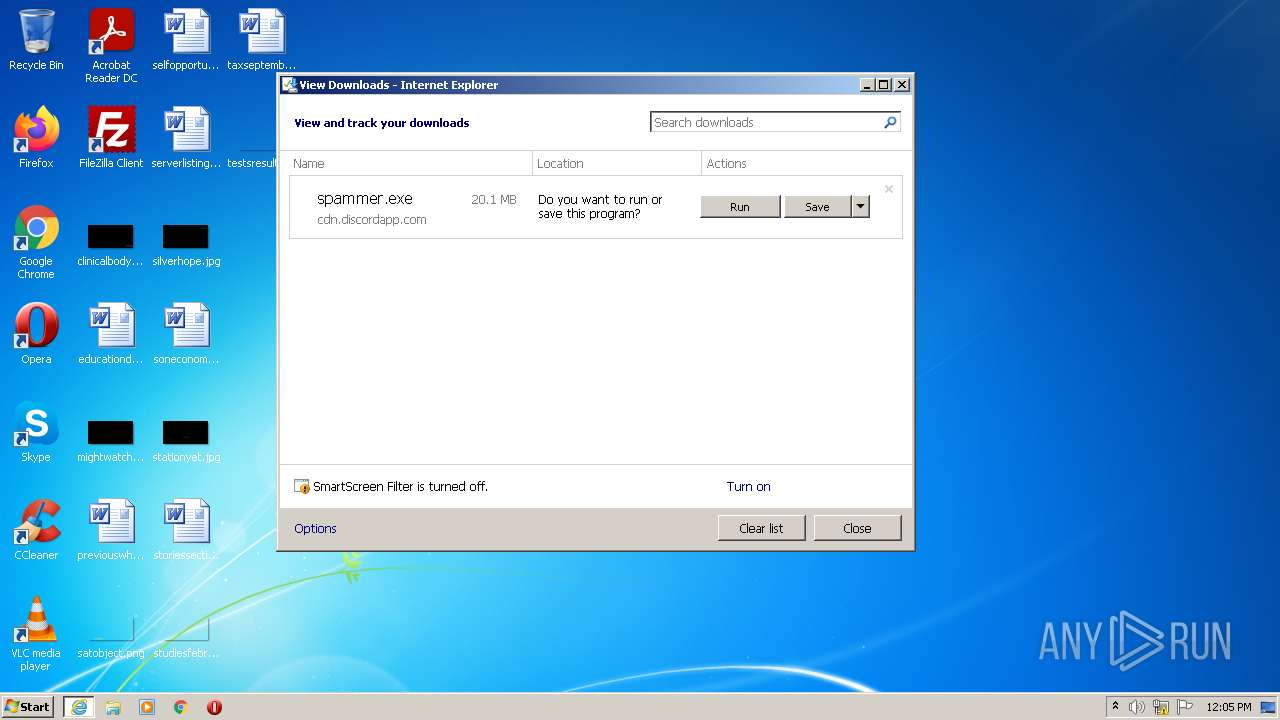
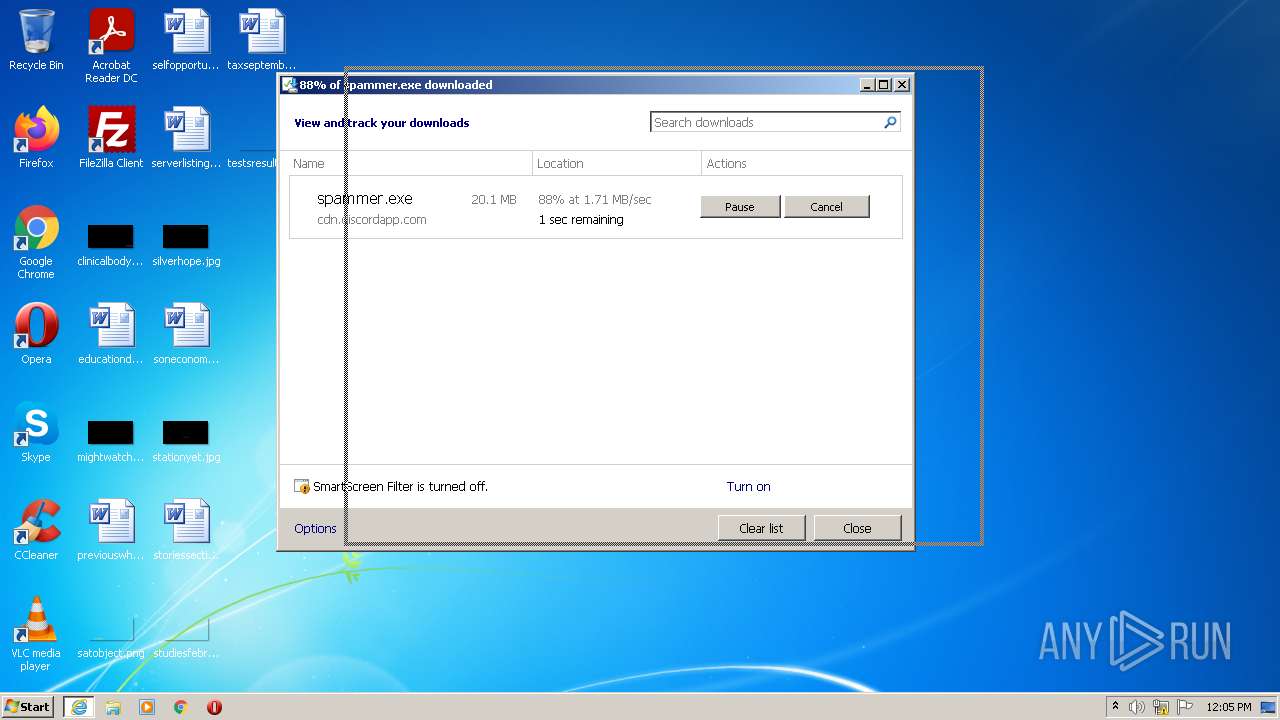
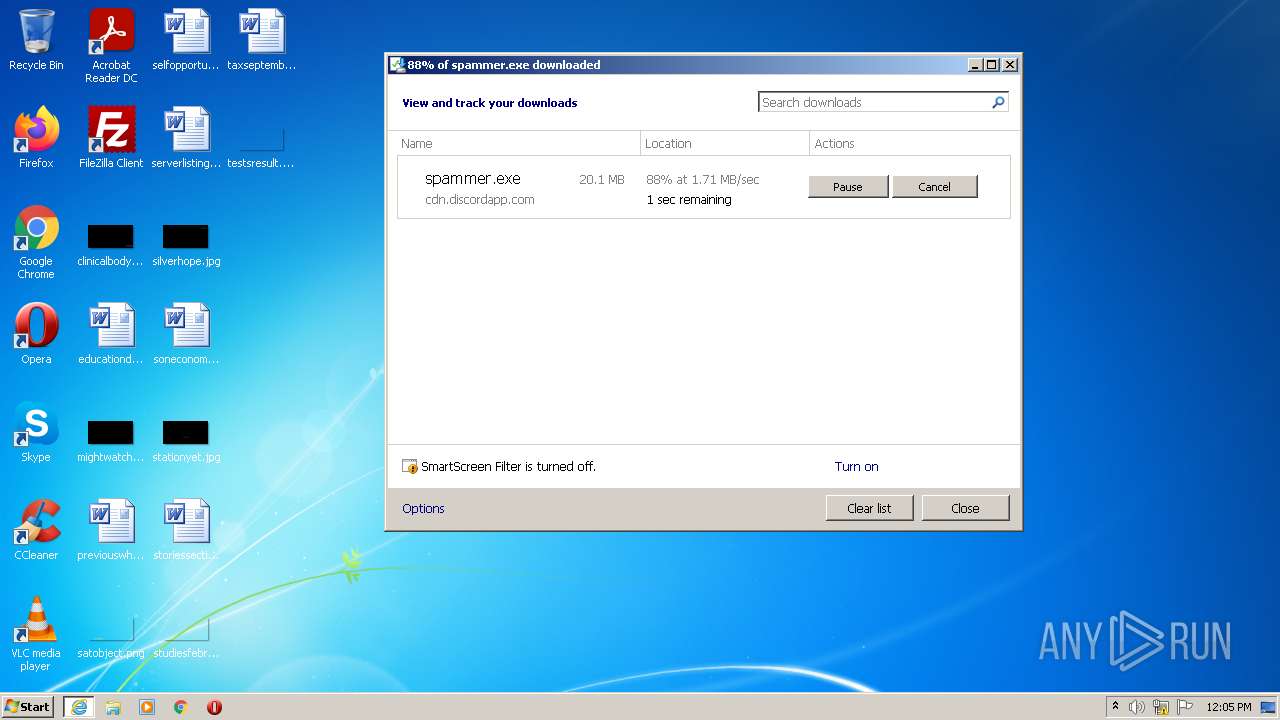
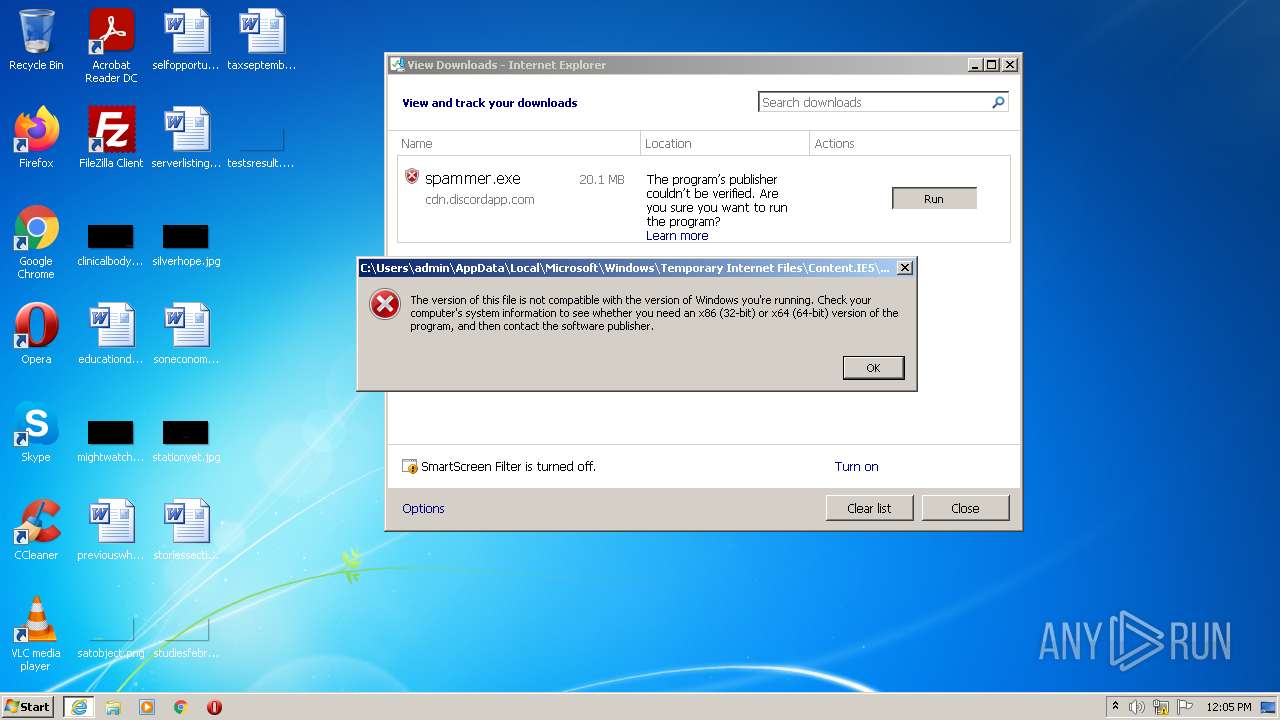
| URL: | https://cdn.discordapp.com/attachments/977527247302963230/977527349925003274/spammer.exe |
| Full analysis: | https://app.any.run/tasks/0d11c6a2-eddf-4792-8248-0186ea084586 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 11:04:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7148FEB32DB3ED8A42ADC005566F0963 |
| SHA1: | 37C8C8B746F270B99462587F4A3535DC423D64F5 |
| SHA256: | D00E148D716C57123DC72AB156E9B0A6C81C051221AAF4E7B00B846F273B024E |
| SSDEEP: | 3:N8cCWdy6//jrkkWCyrl6ES/J:2cry6XjrkKgoESh |
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2664)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3376)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2664)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2664)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2364)
INFO
Checks supported languages
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 528)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 1548)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 1600)
- chrome.exe (PID: 1620)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 976)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 564)
- chrome.exe (PID: 1880)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 656)
- chrome.exe (PID: 848)
- chrome.exe (PID: 648)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 1620)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 848)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2272)
- chrome.exe (PID: 124)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 1796)
- chrome.exe (PID: 920)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 604)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 1732)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 1320)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 940)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 2636)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2032)
- chrome.exe (PID: 388)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 1680)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 2772)
Reads the computer name
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 3376)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 1548)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 656)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 648)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 2620)
Changes internet zones settings
- iexplore.exe (PID: 2932)
Application launched itself
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2364)
Checks Windows Trust Settings
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2932)
Reads settings of System Certificates
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2944)
Reads the date of Windows installation
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 648)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2932)
Manual execution by user
- chrome.exe (PID: 2364)
Reads the hosts file
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
87
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=66 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1944 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3148 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=56 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=2832 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2092 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15041542998873345728,9741263054049288636,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
38 484
Read events
38 232
Write events
243
Delete events
9
Modification events
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960898 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960898 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
481
Text files
469
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6288C79E-93C.pma | — | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\spammer[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{DA88F0BF-D8F5-11EC-B13F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{DA88F0BD-D8F5-11EC-B13F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF01D510B6D9F437C0.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\spammer.exe.jbllgbl.partial | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
195
DNS requests
128
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
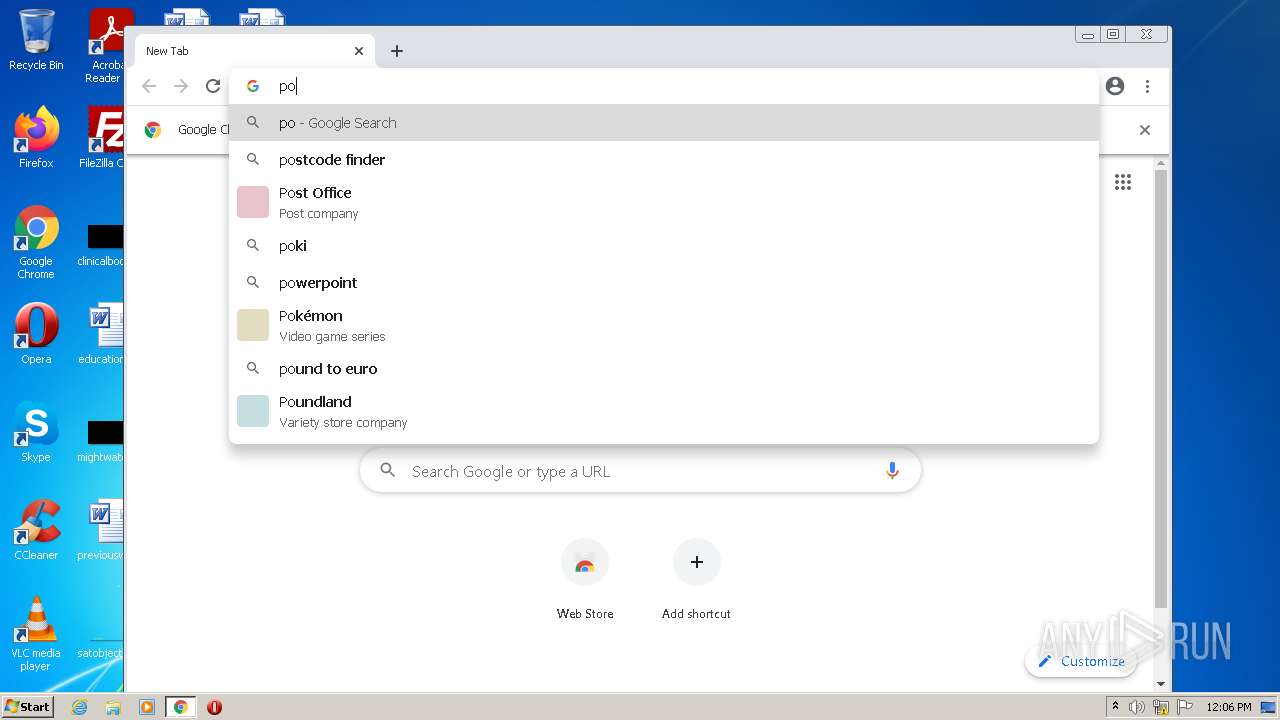
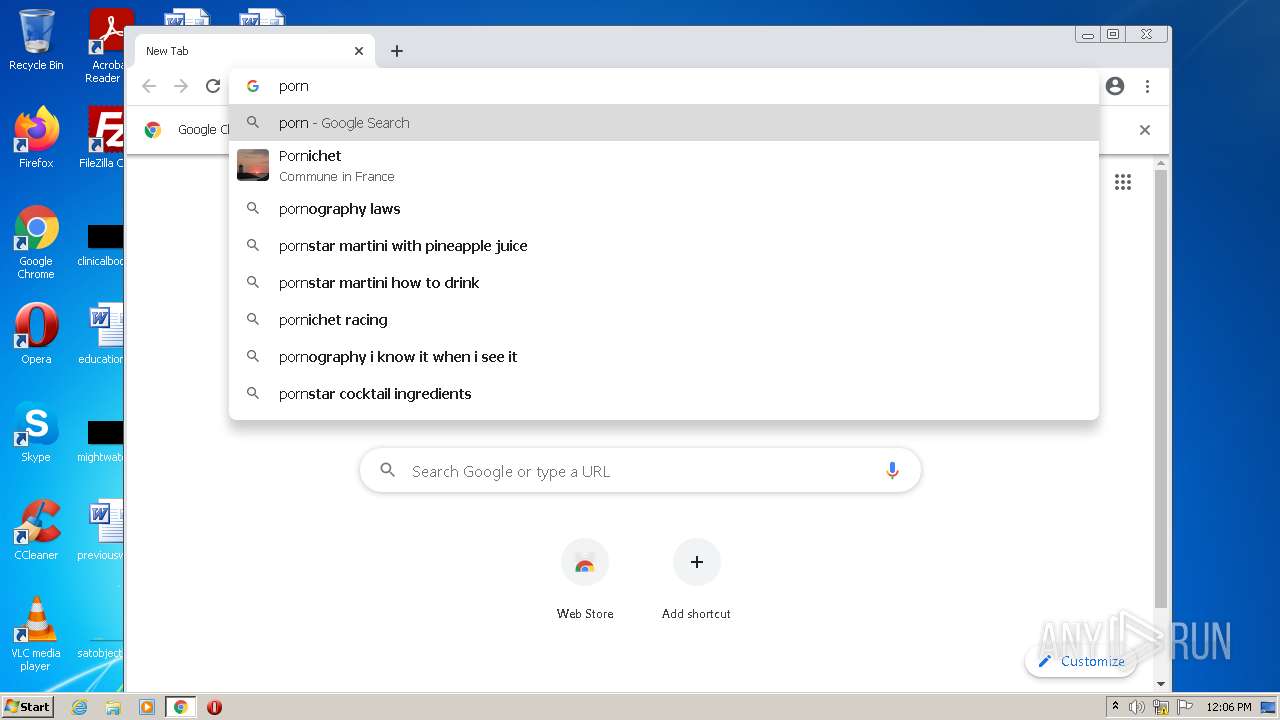
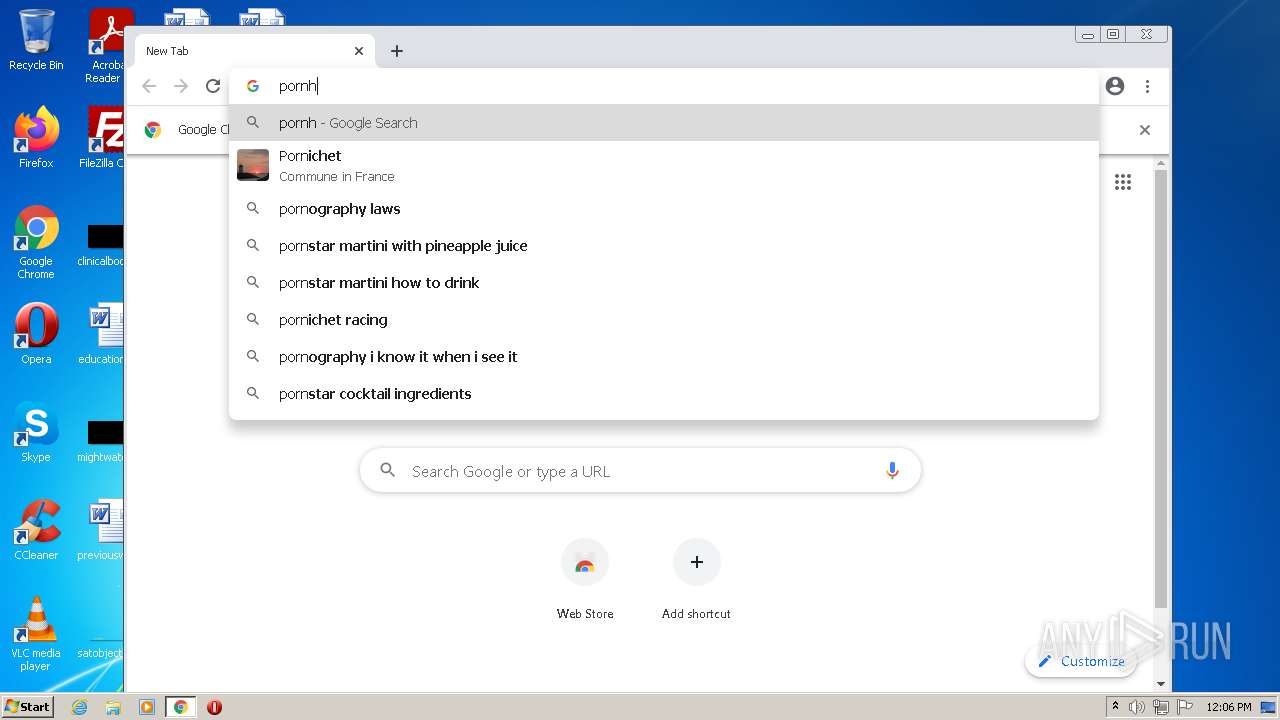
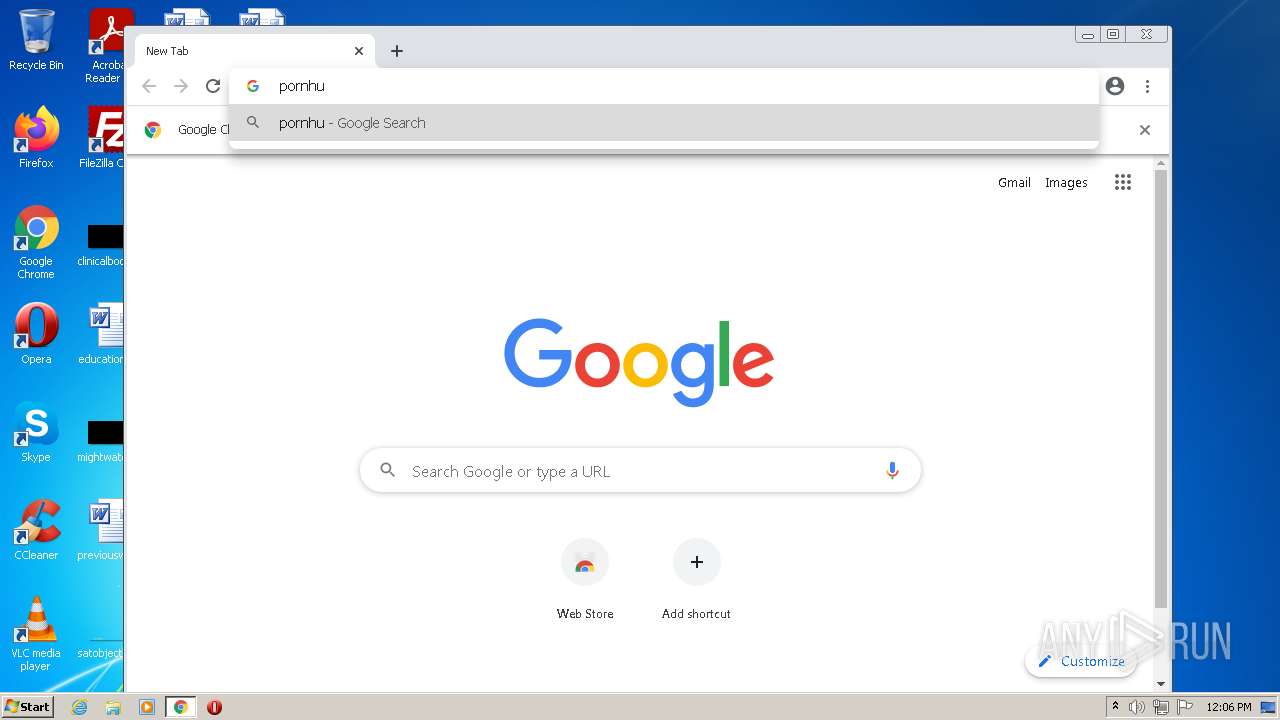
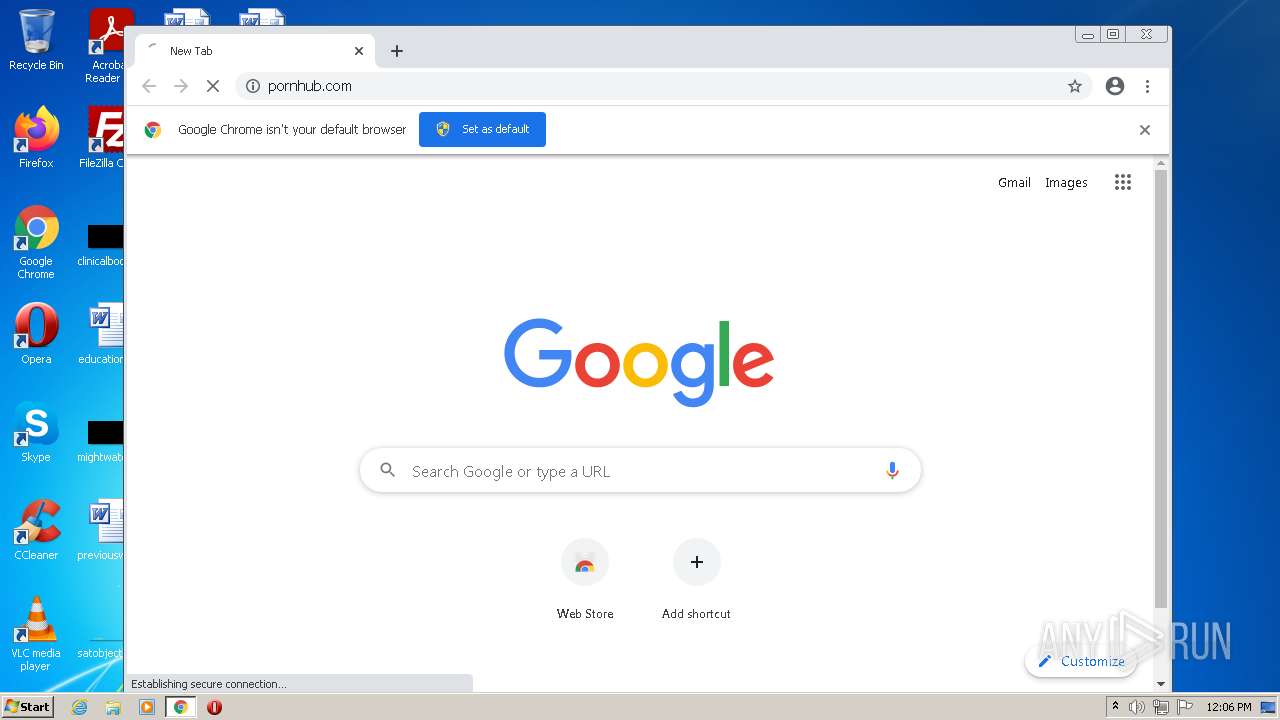
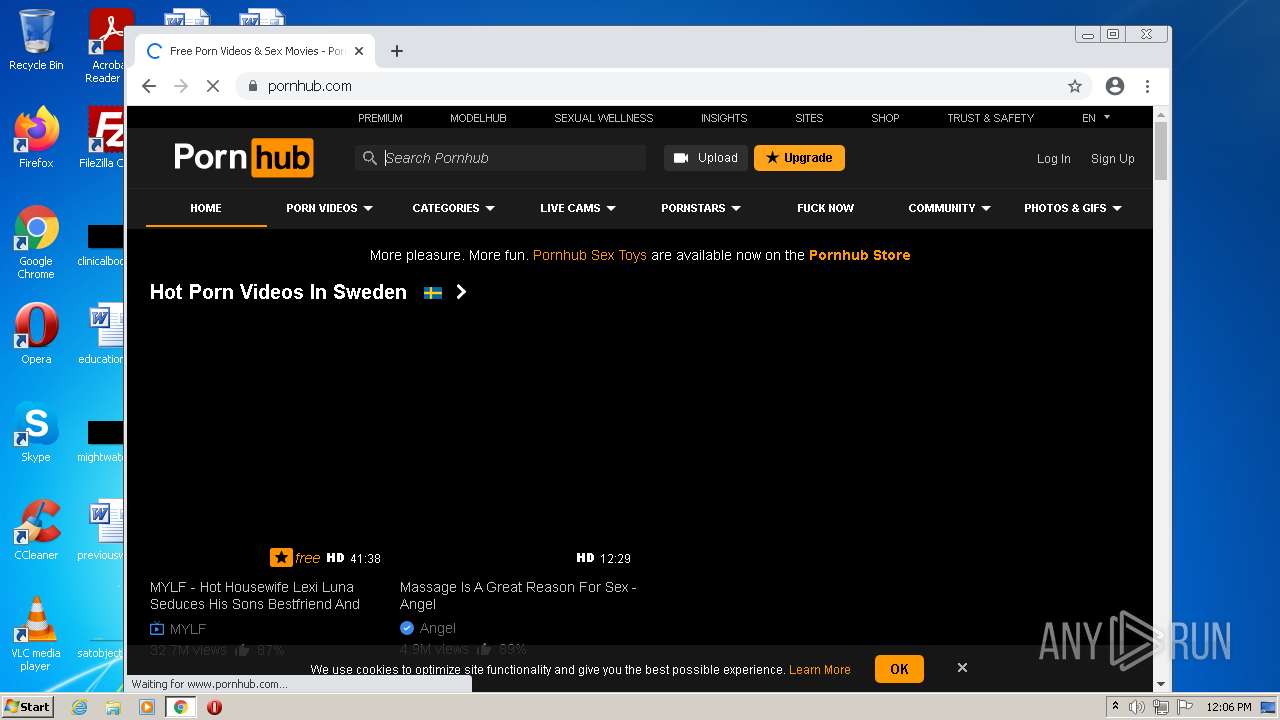
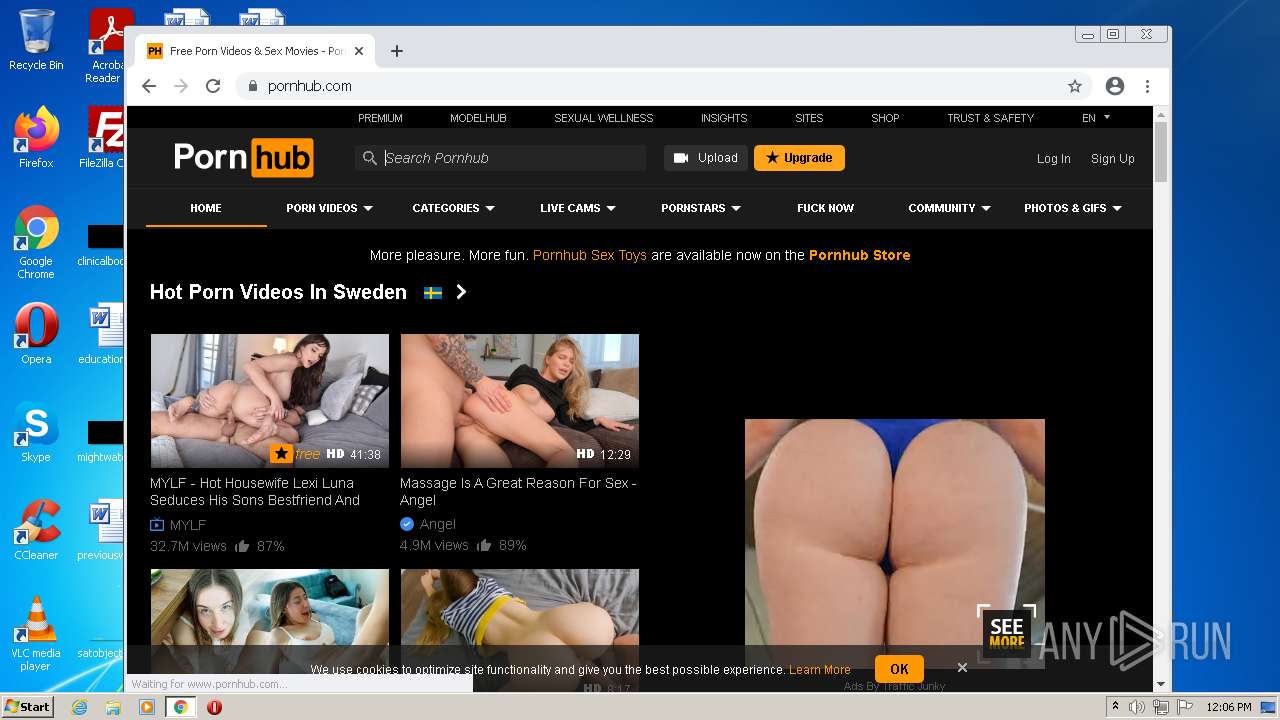
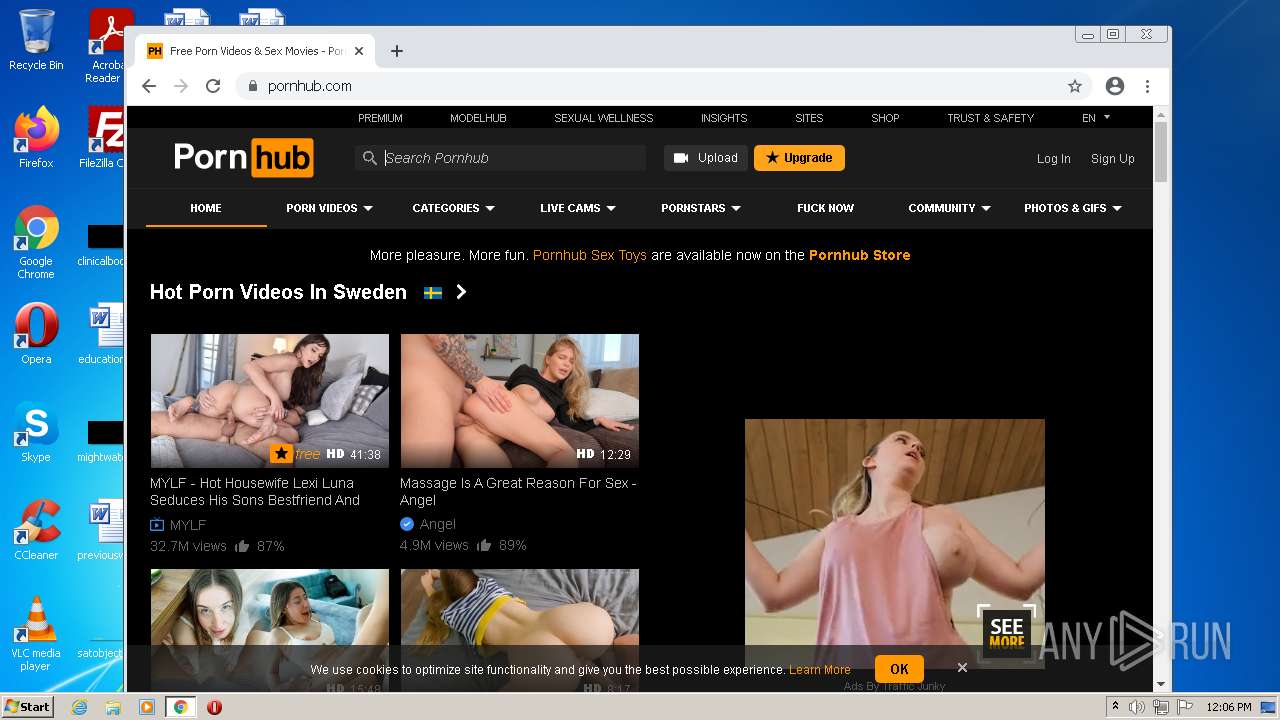
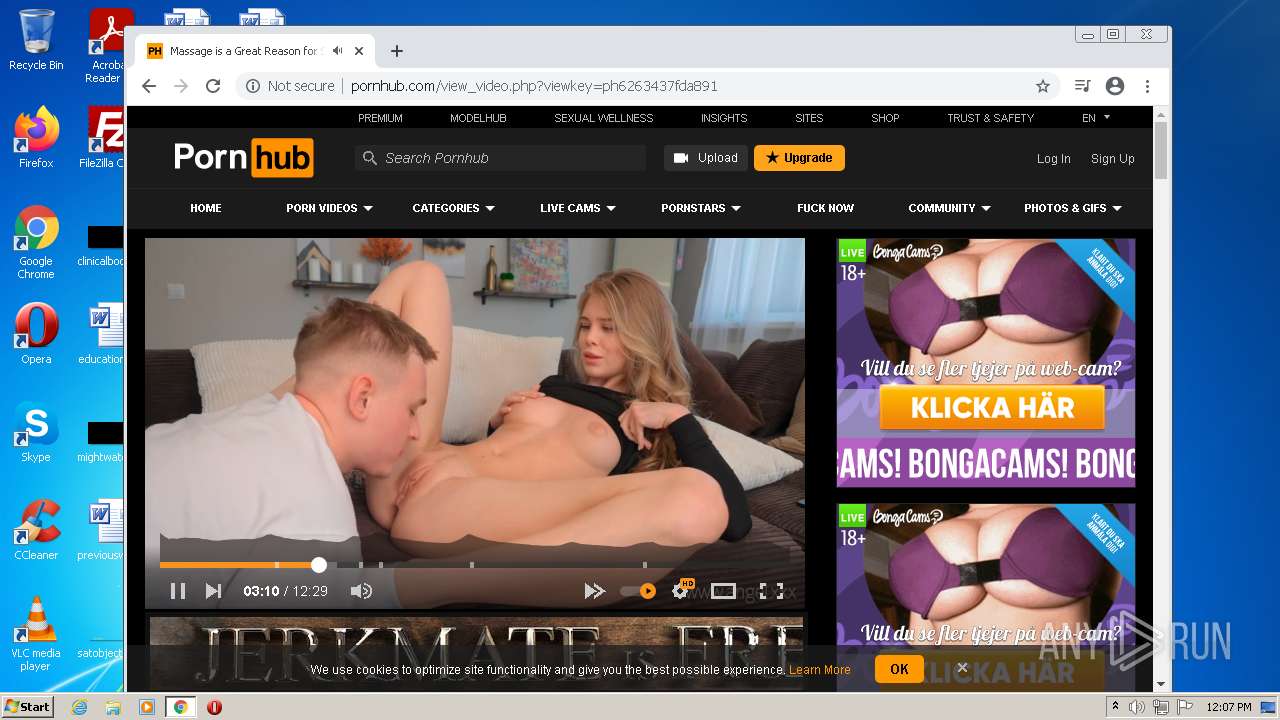
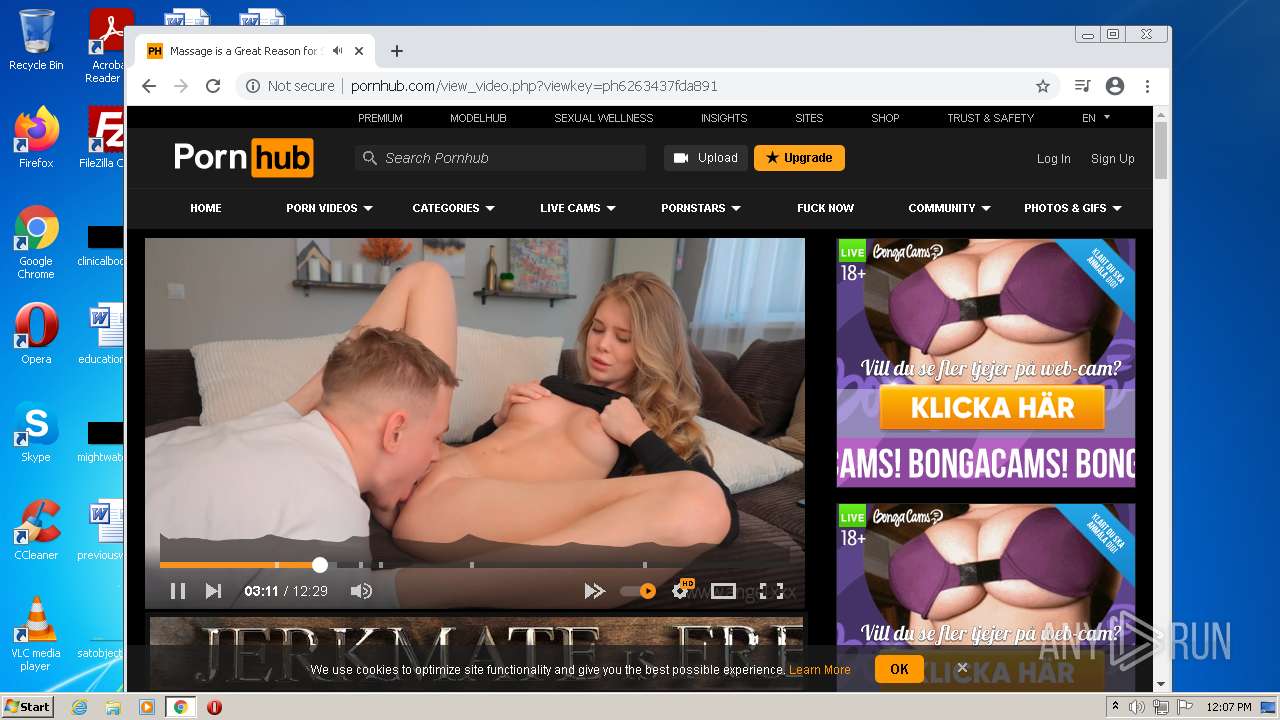
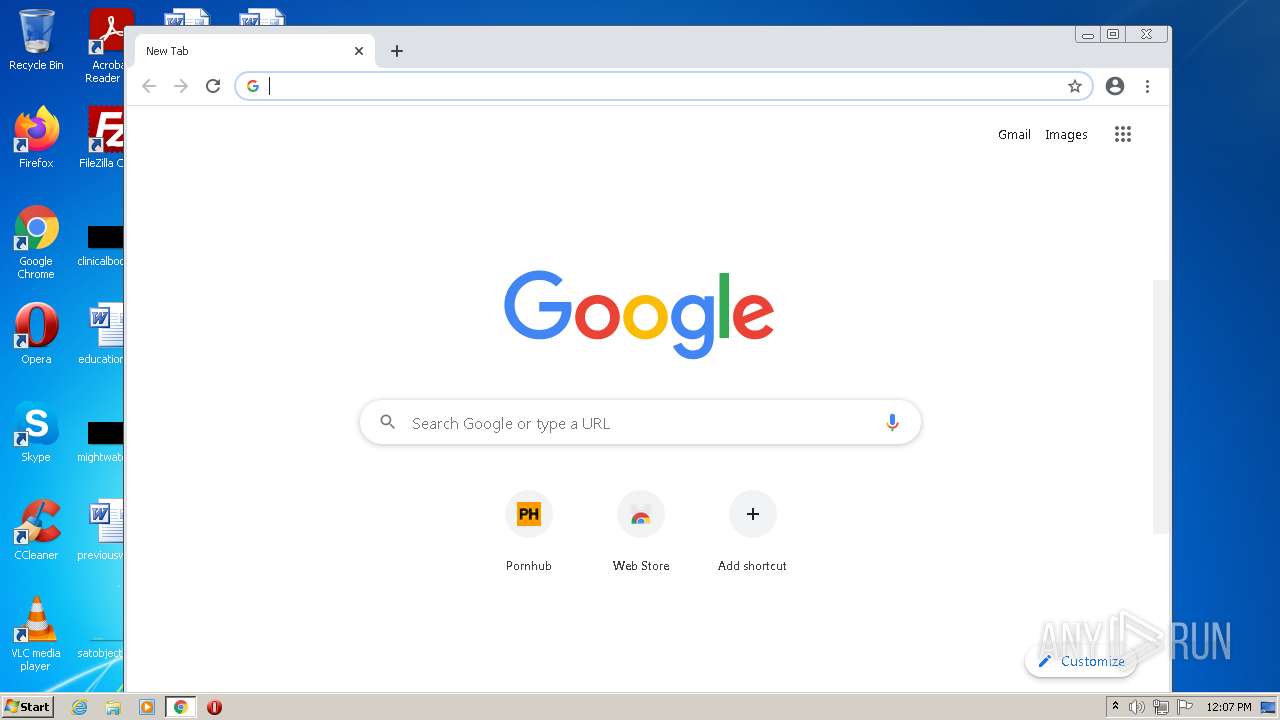
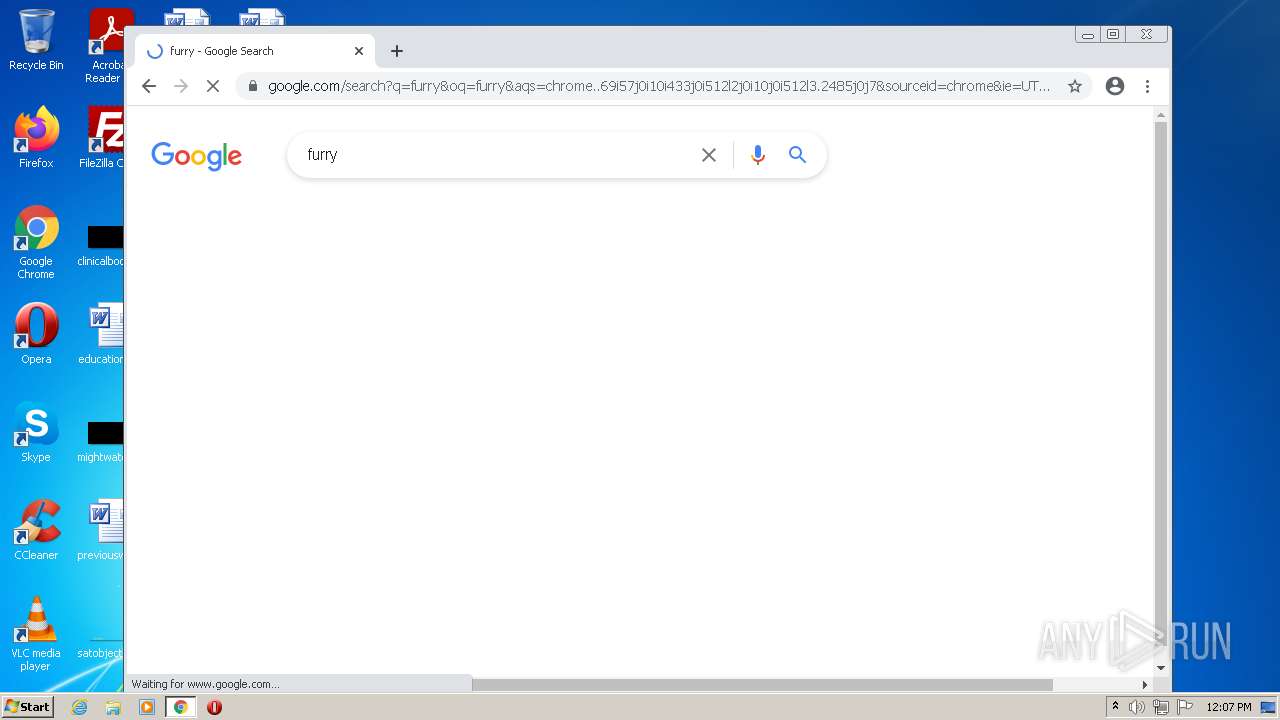
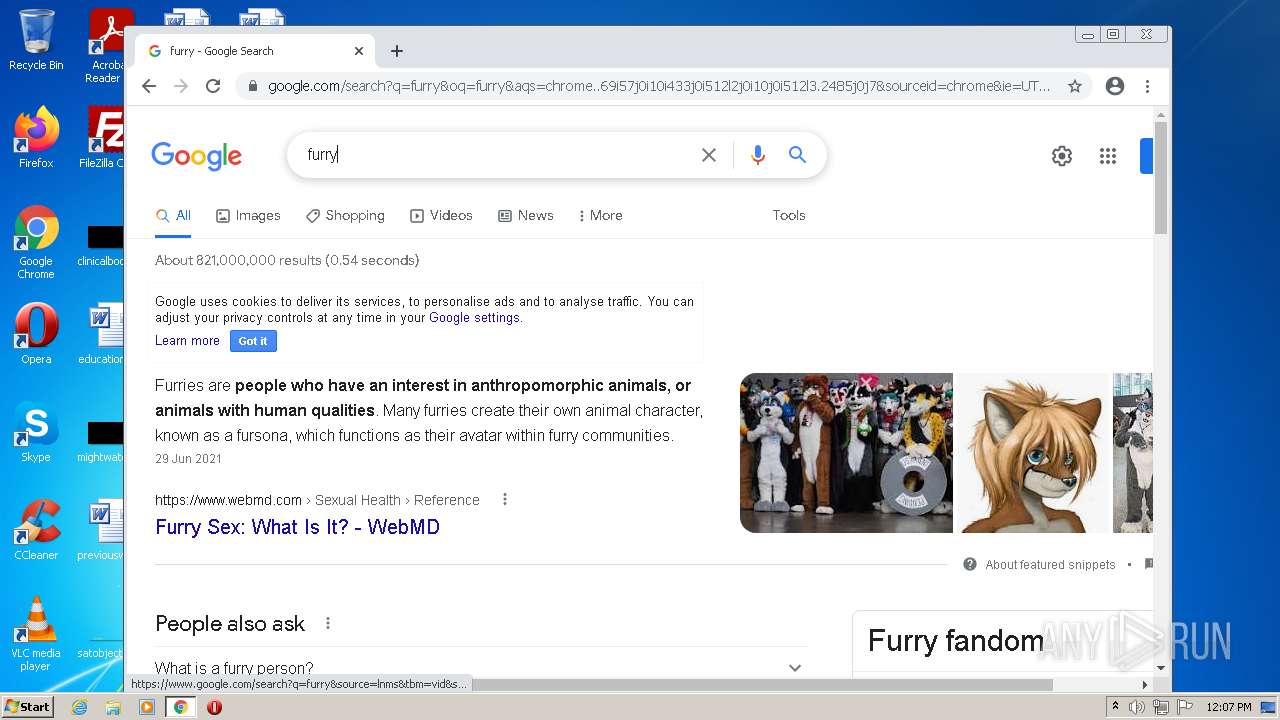
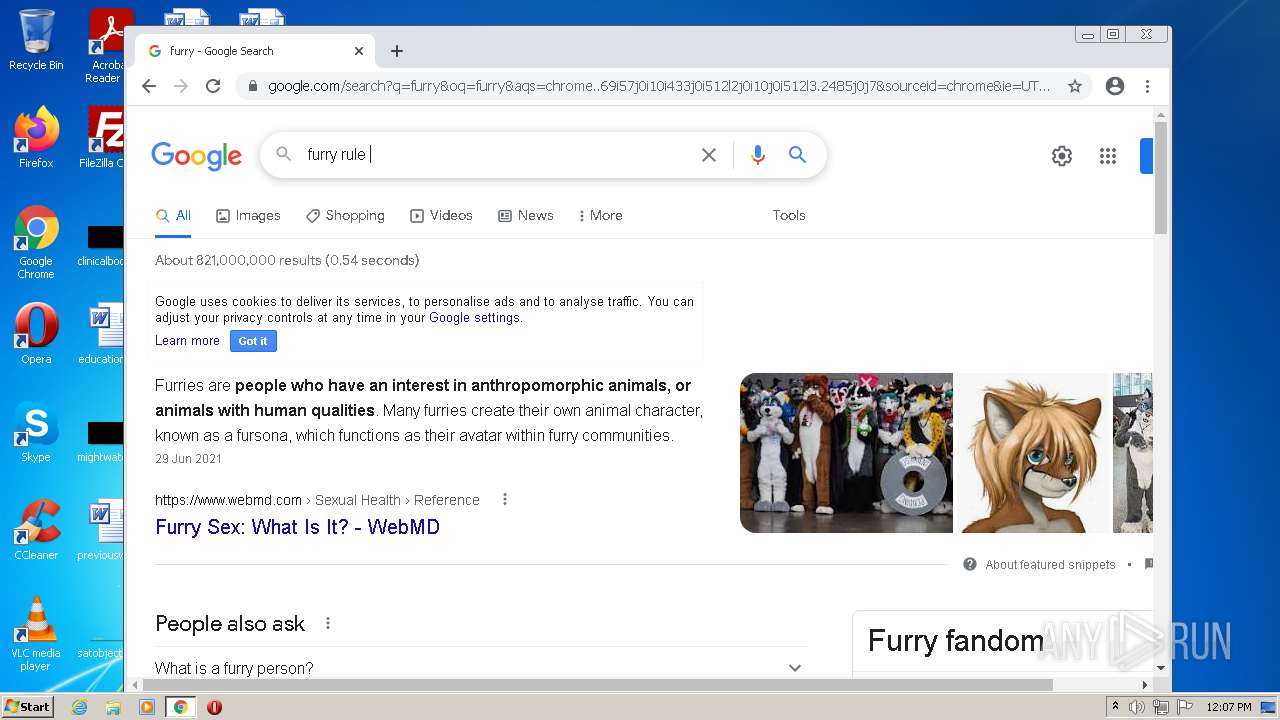
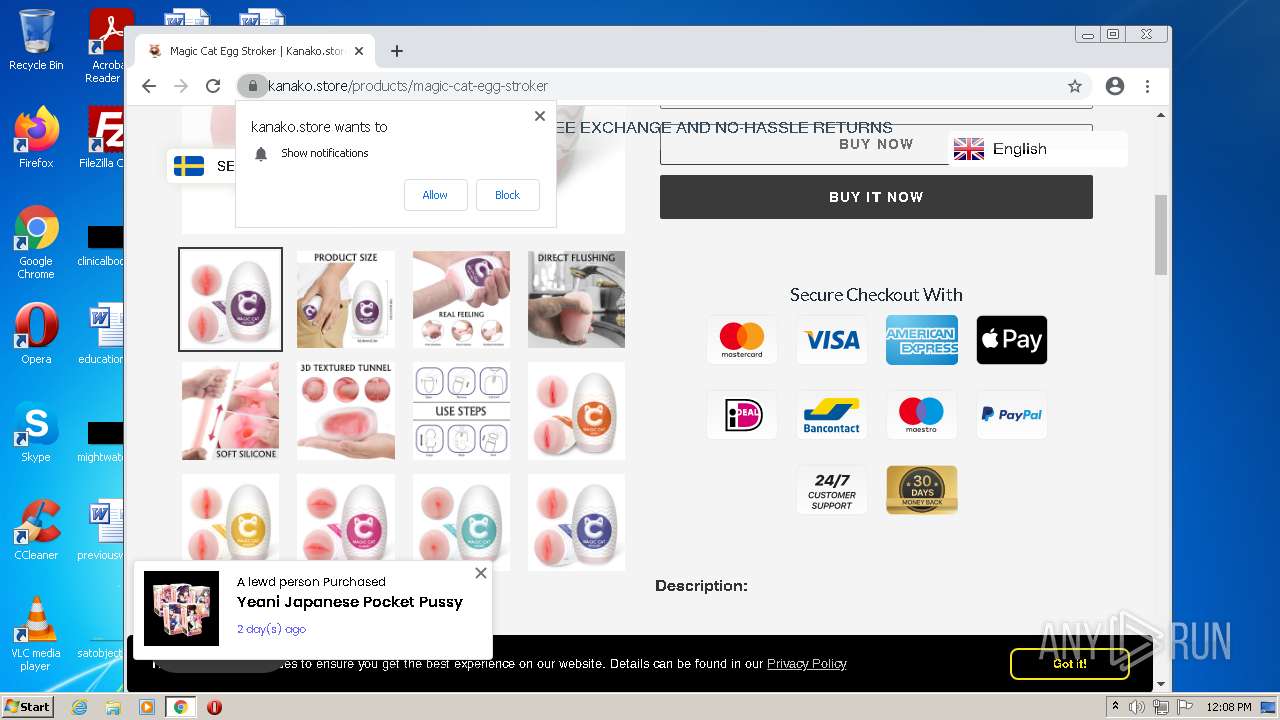
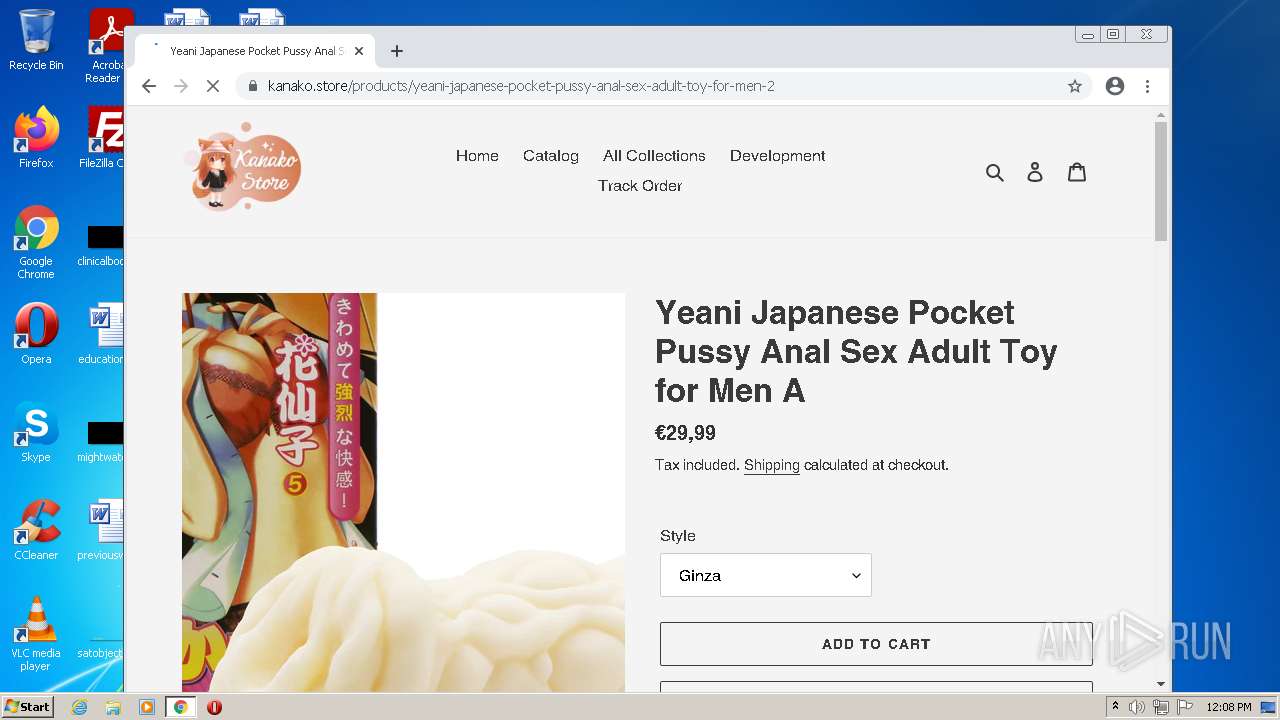
2944 | chrome.exe | GET | 301 | 66.254.114.41:80 | http://pornhub.com/ | US | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adcnwfujgjhw4hm33ohzaszanj5q_2818/jflookgnkcckhobaglndicnbbgbonegd_2818_all_d3foivhotrbk5dz25o7uqe3m34.crx3 | US | — | — | whitelisted |
3376 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2932 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2944 | chrome.exe | GET | 200 | 168.119.165.96:80 | http://ad.tjserv.media/images/delivery/e094f7b0c1c4b826b36c.jpg | US | image | 83.3 Kb | unknown |
2944 | chrome.exe | GET | 200 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?6c58e9a874571630 | US | compressed | 60.0 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adcnwfujgjhw4hm33ohzaszanj5q_2818/jflookgnkcckhobaglndicnbbgbonegd_2818_all_d3foivhotrbk5dz25o7uqe3m34.crx3 | US | binary | 9.74 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 178 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adcnwfujgjhw4hm33ohzaszanj5q_2818/jflookgnkcckhobaglndicnbbgbonegd_2818_all_d3foivhotrbk5dz25o7uqe3m34.crx3 | US | binary | 2.85 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adcnwfujgjhw4hm33ohzaszanj5q_2818/jflookgnkcckhobaglndicnbbgbonegd_2818_all_d3foivhotrbk5dz25o7uqe3m34.crx3 | US | binary | 5.66 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | iexplore.exe | 162.159.134.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3376 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3376 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 162.159.134.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2932 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2932 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3376 | iexplore.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2944 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2944 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3376 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2944 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
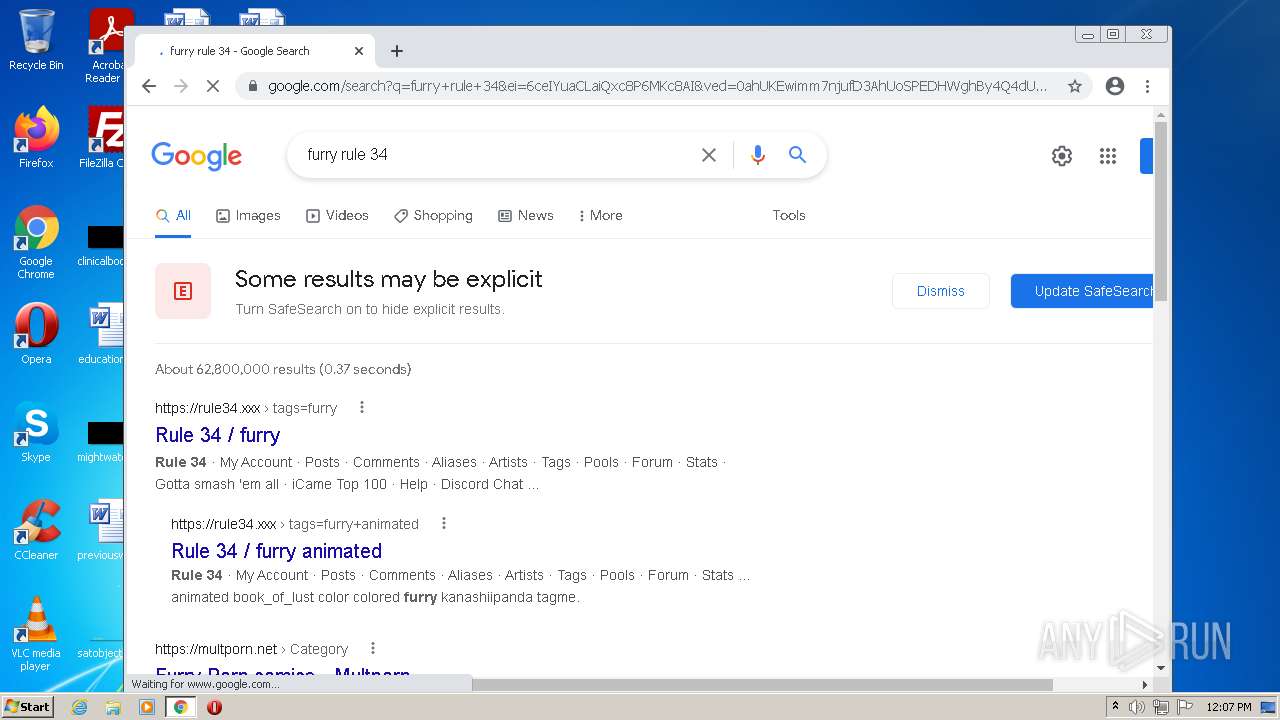
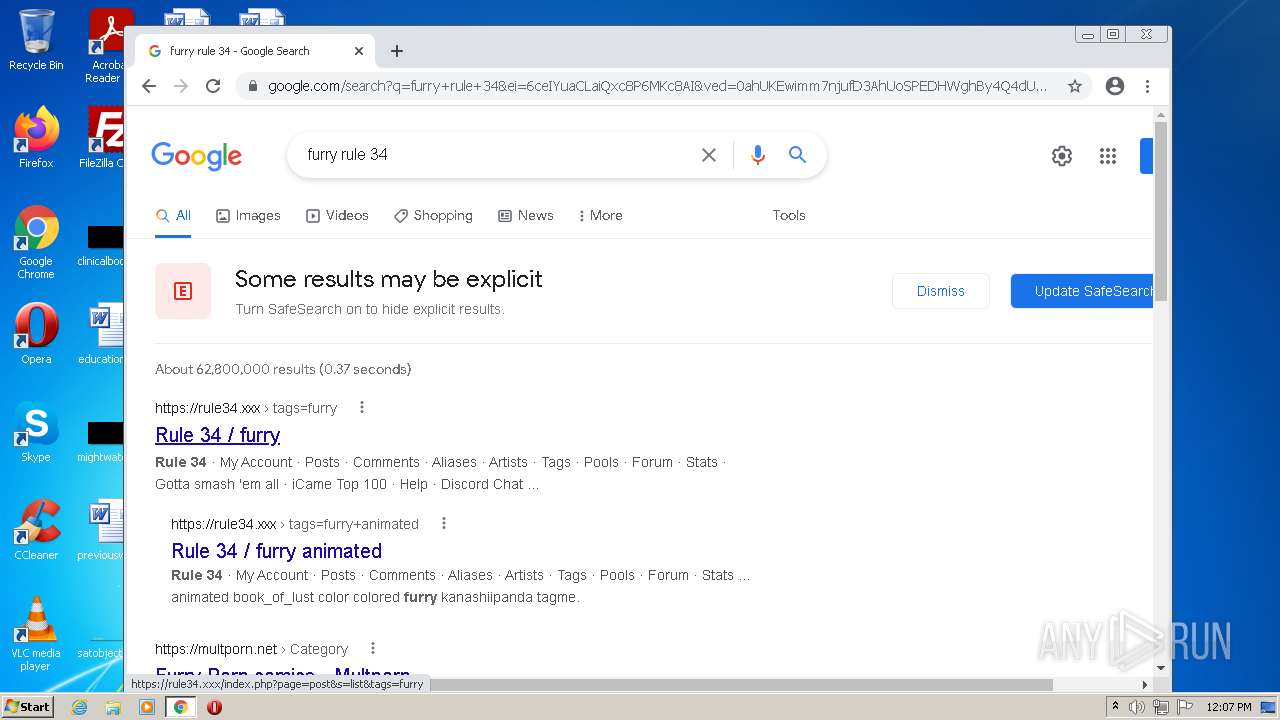
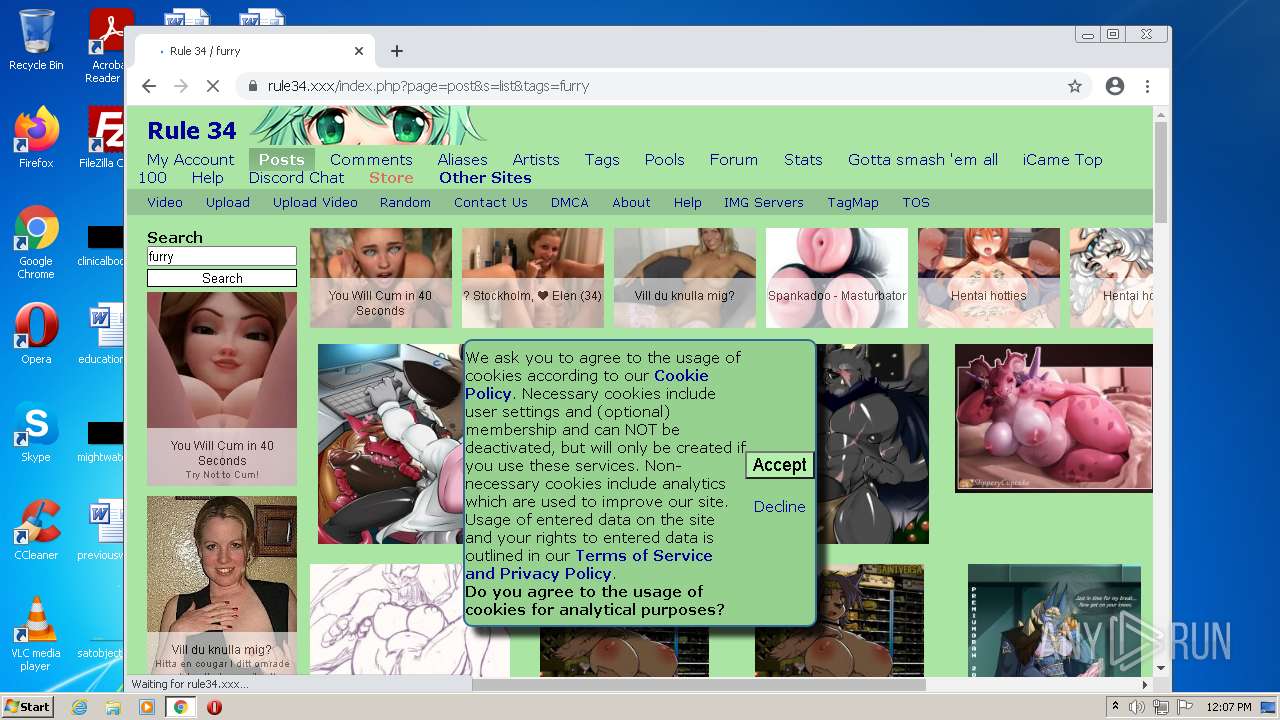
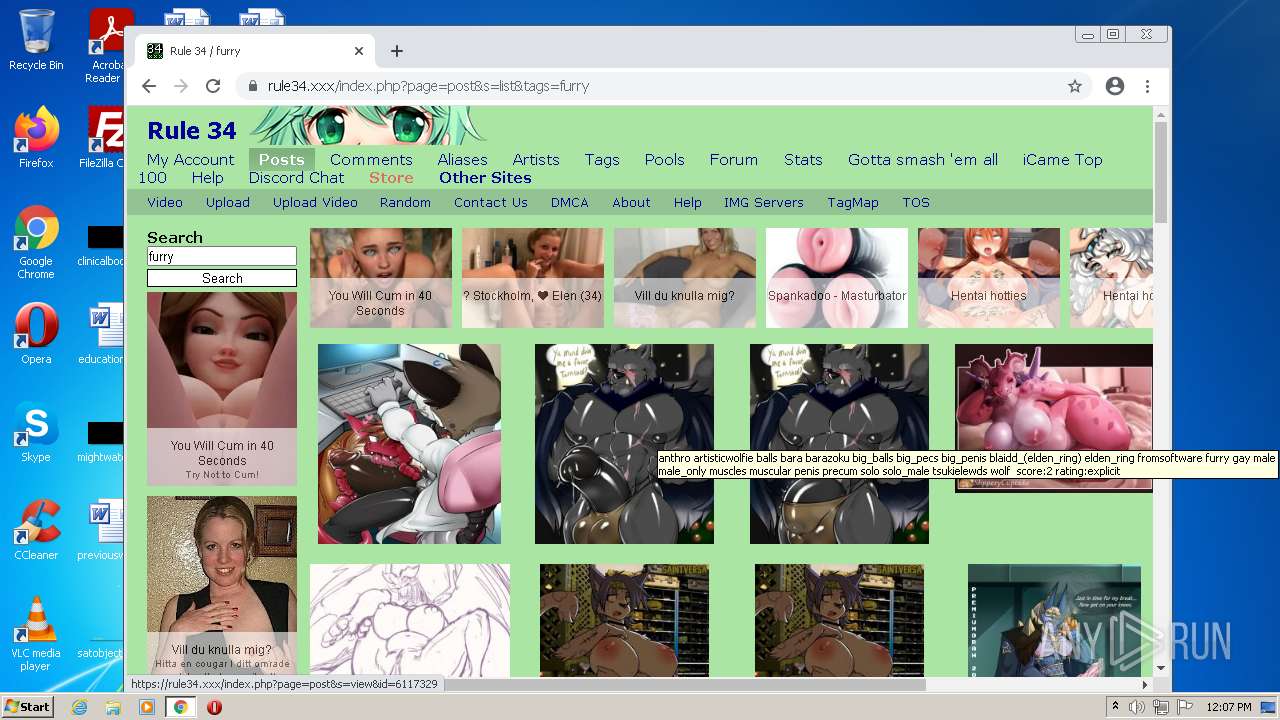
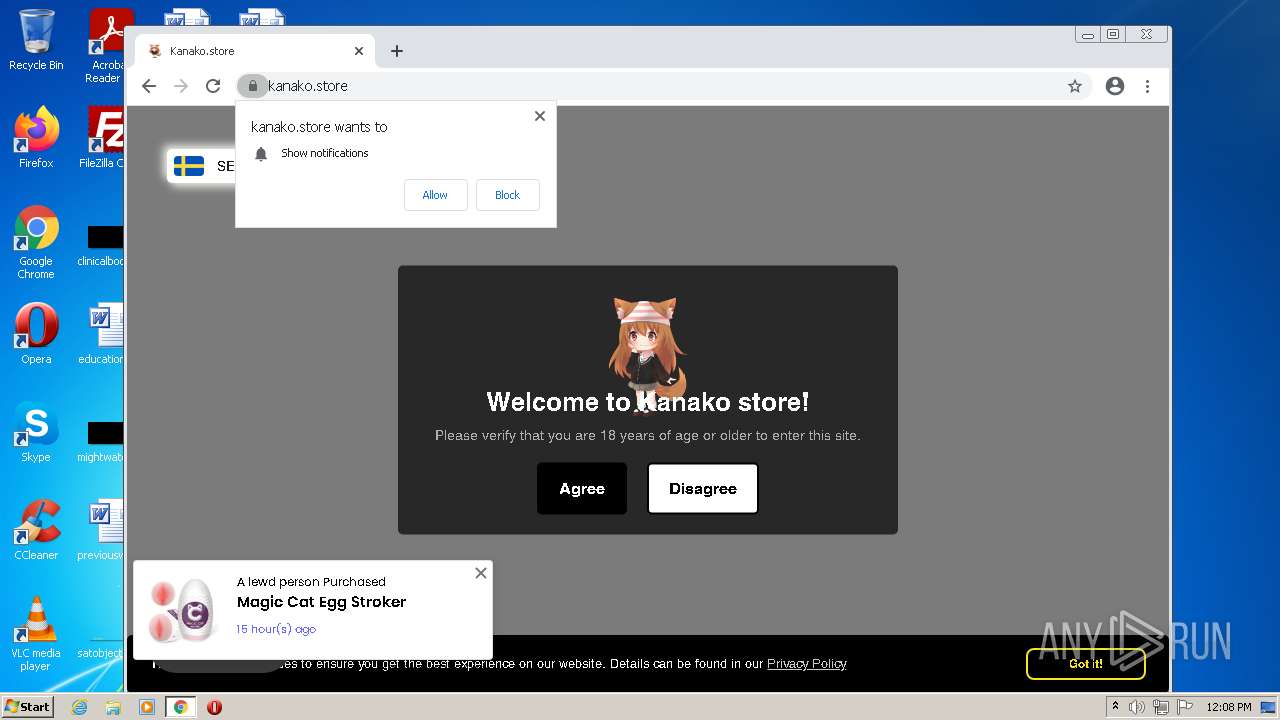
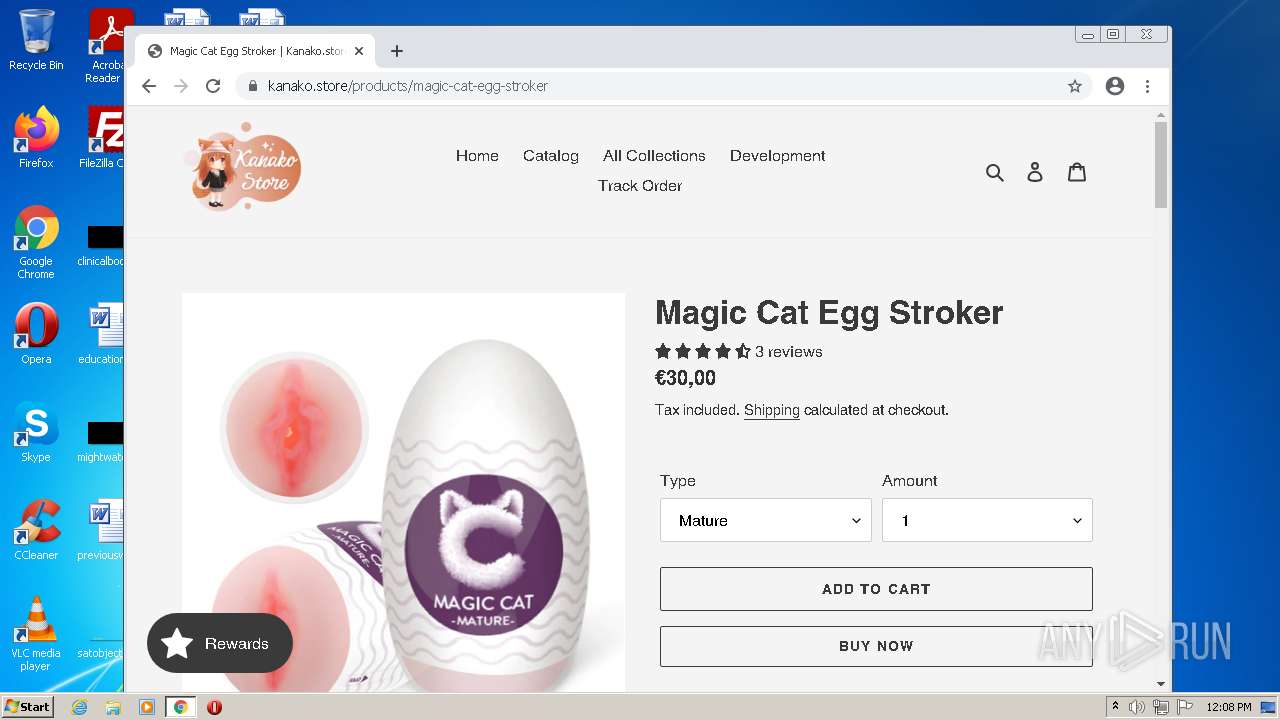
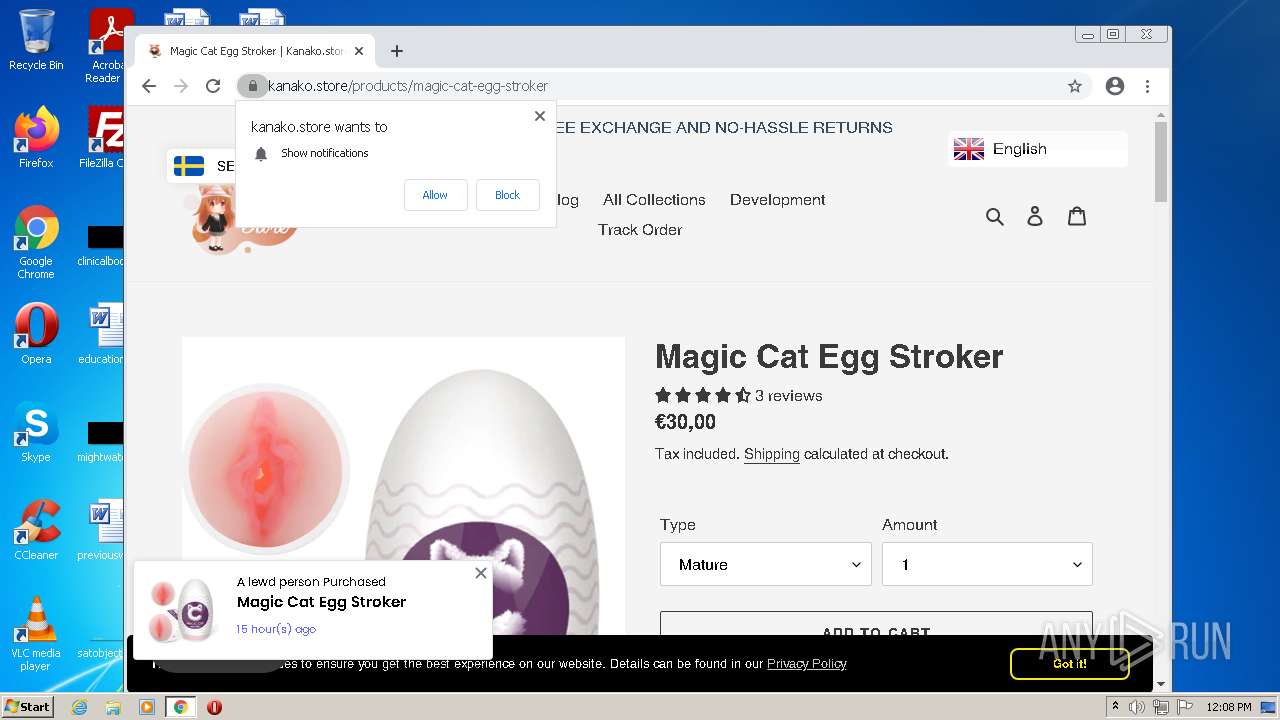
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
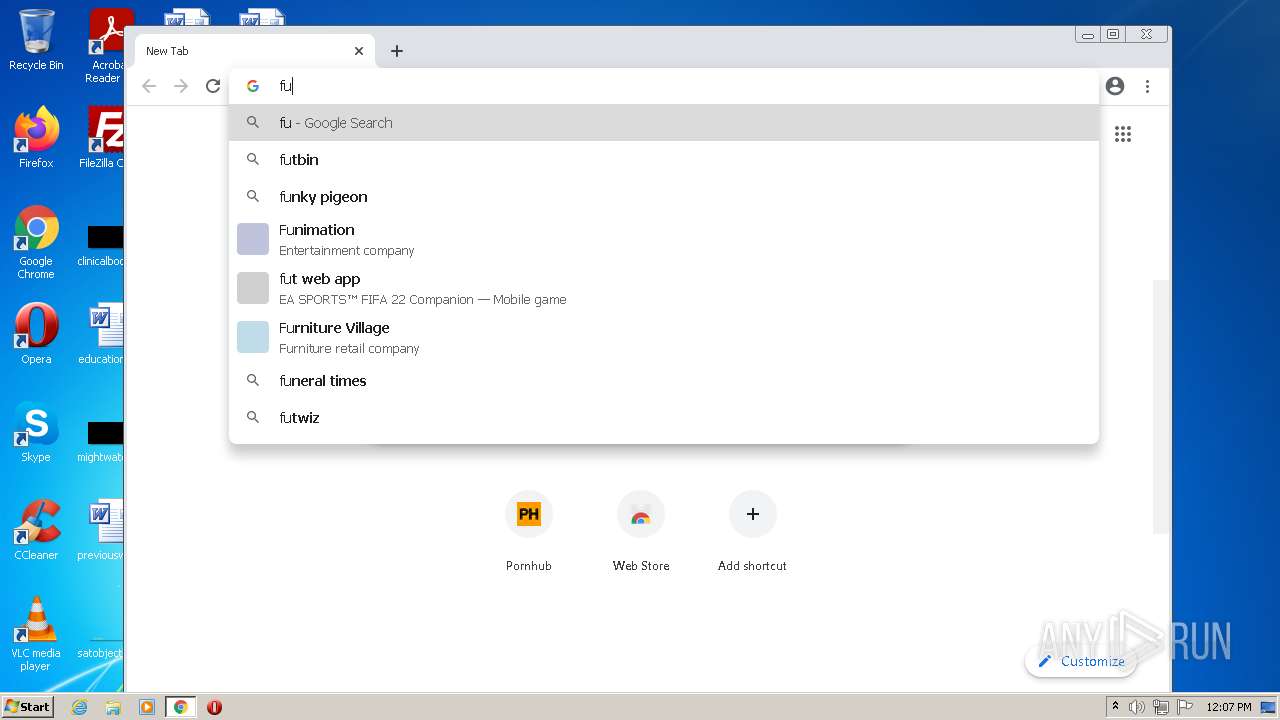
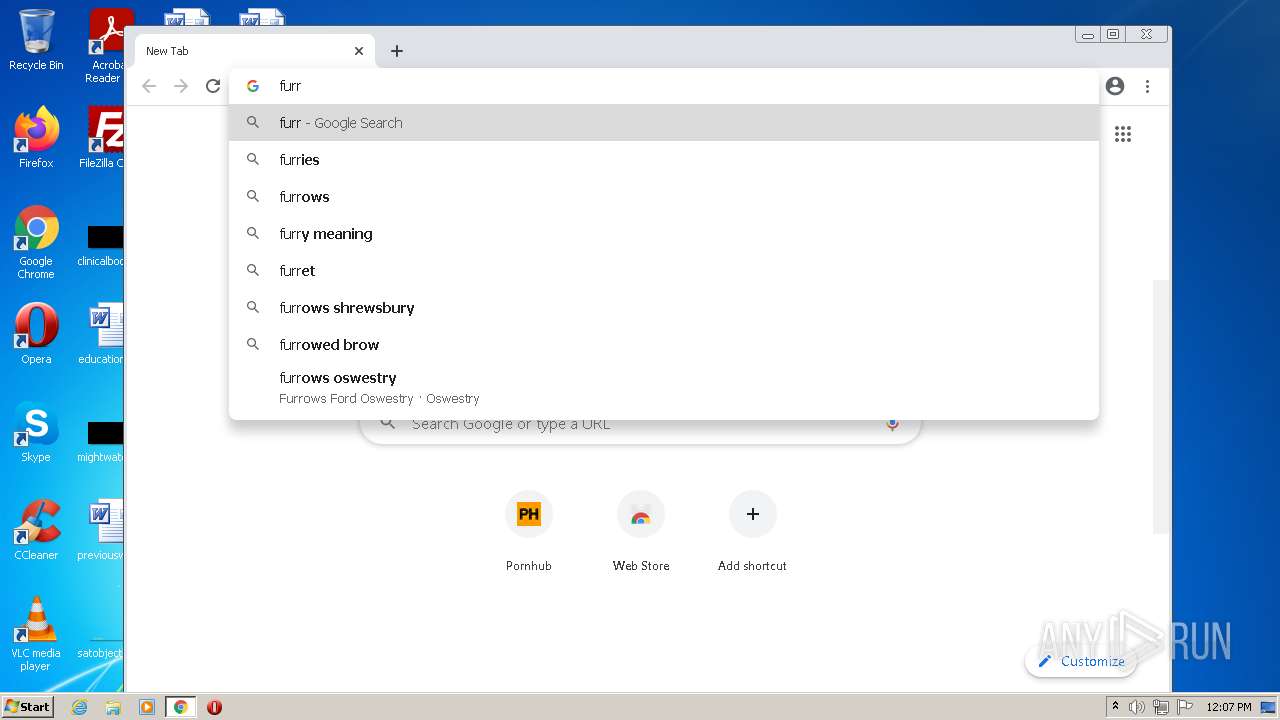
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |