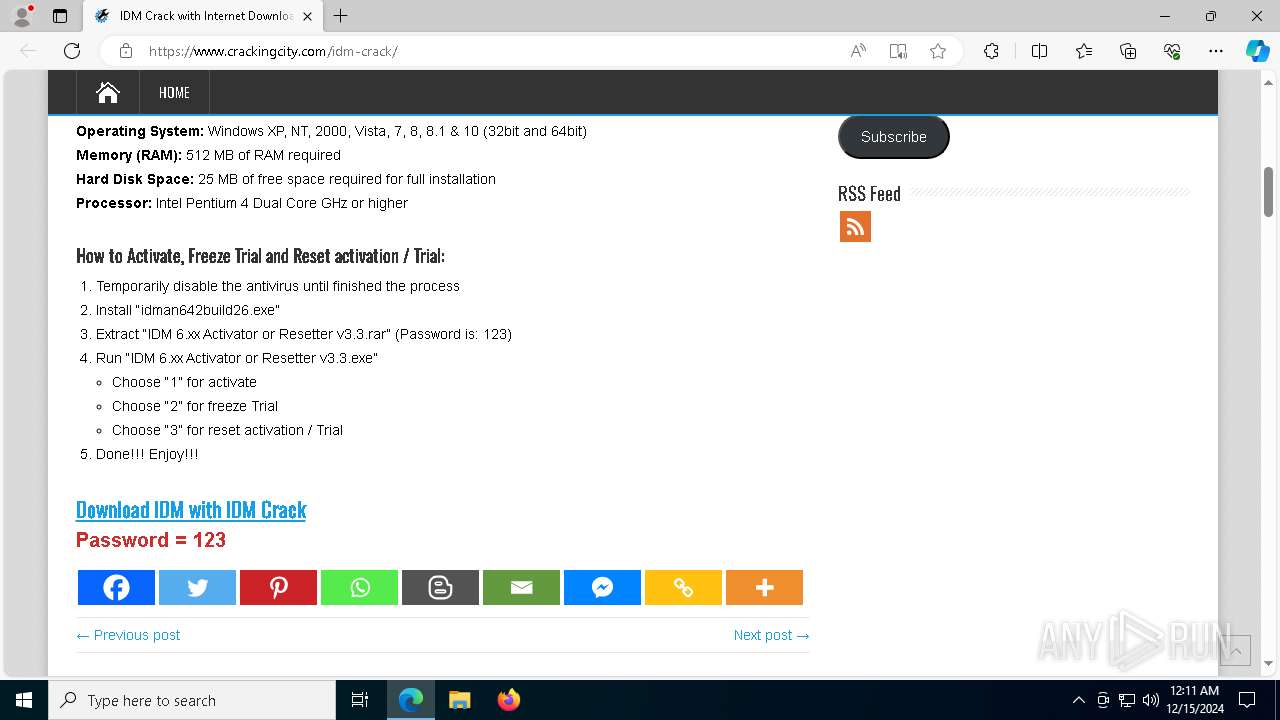
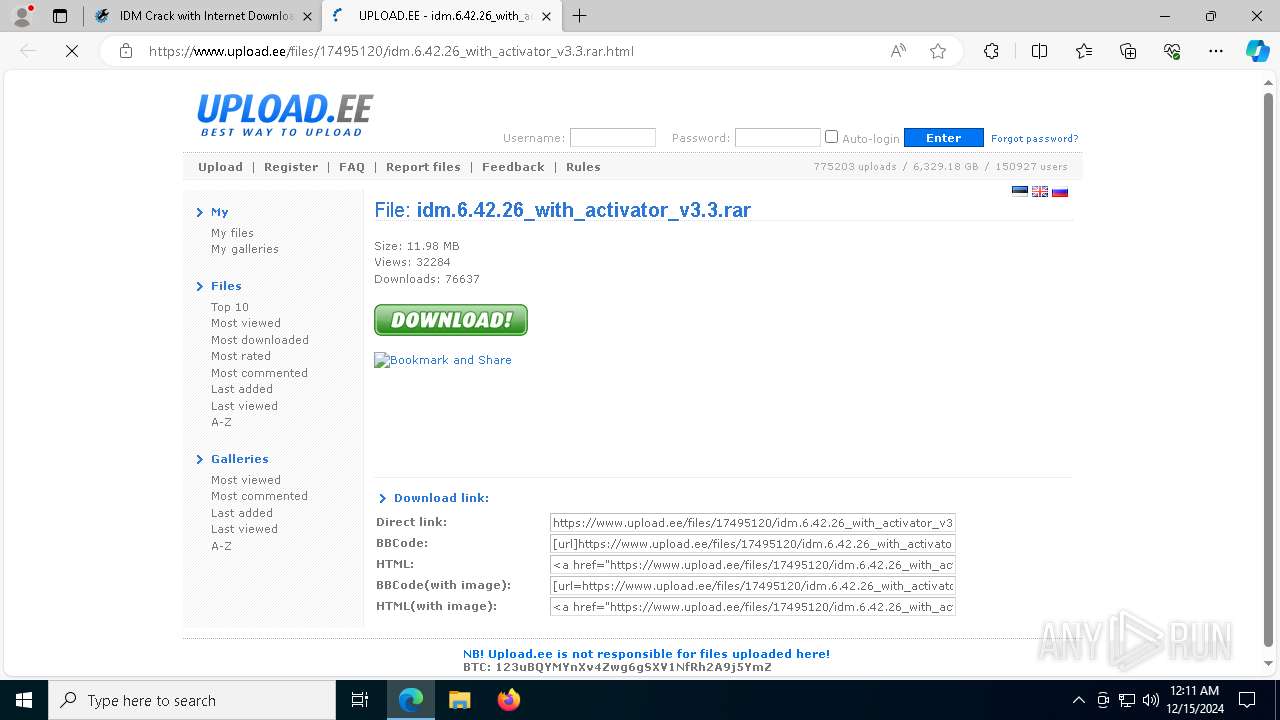
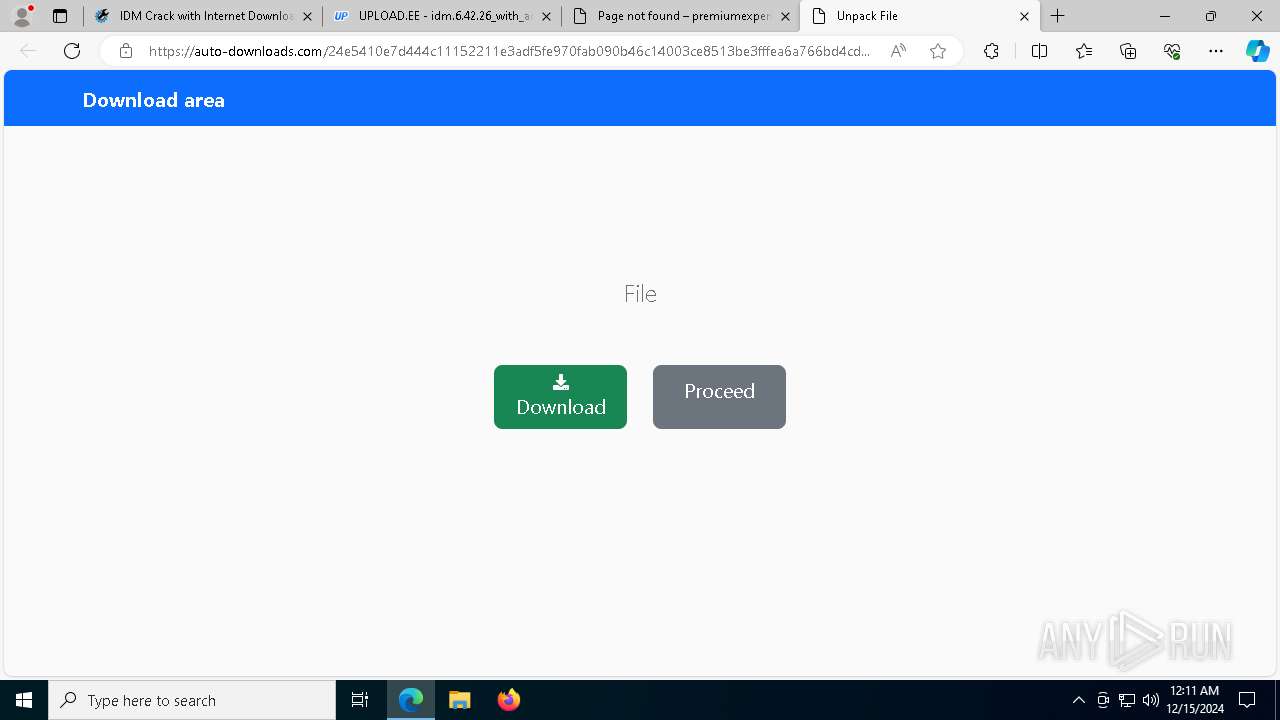
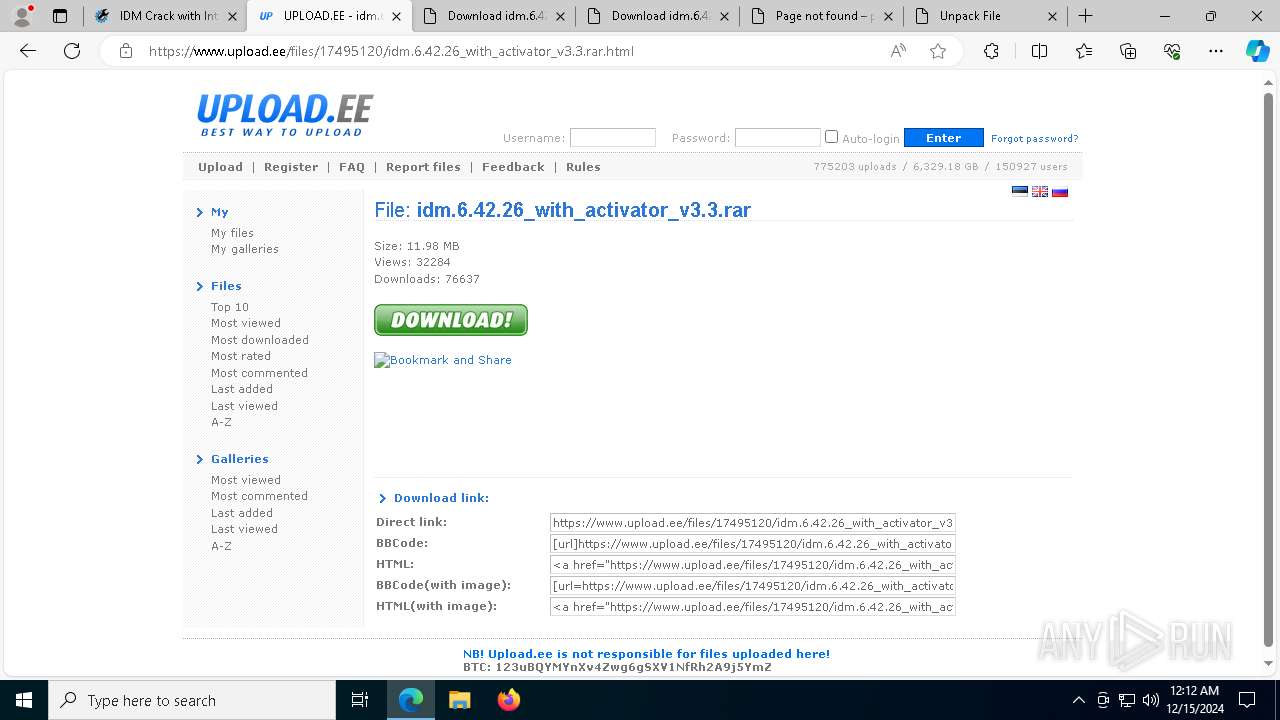
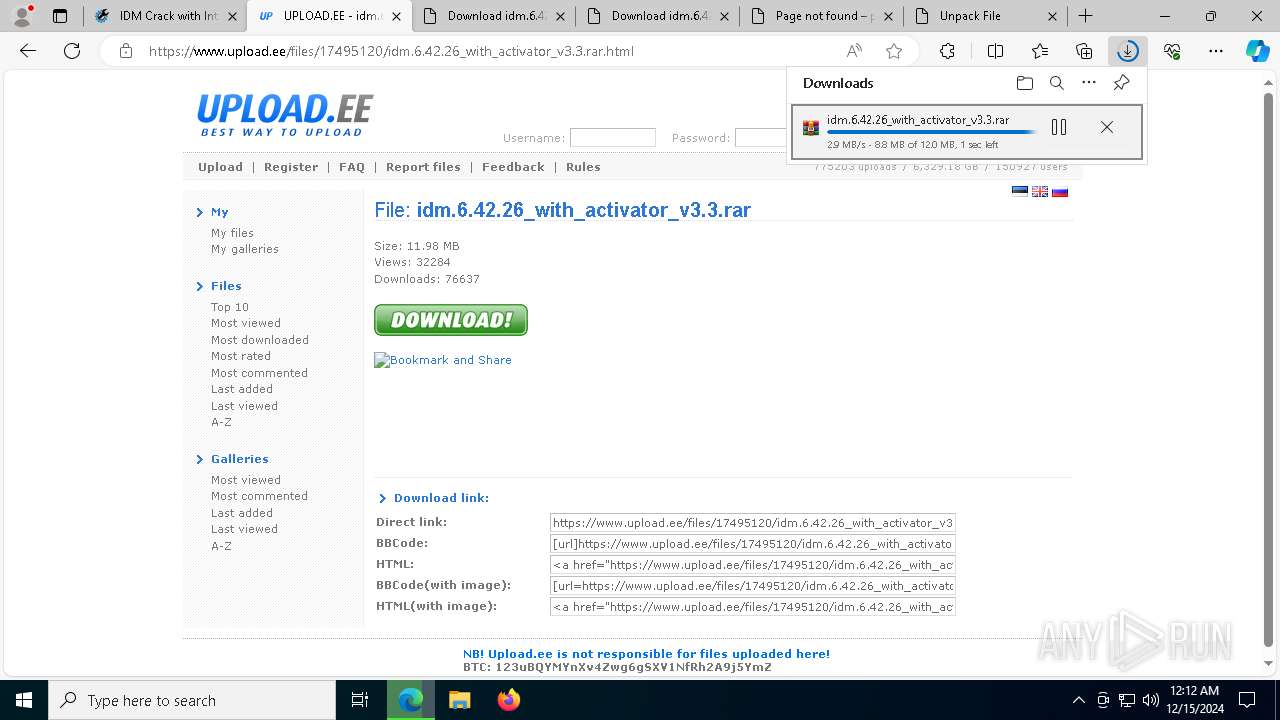
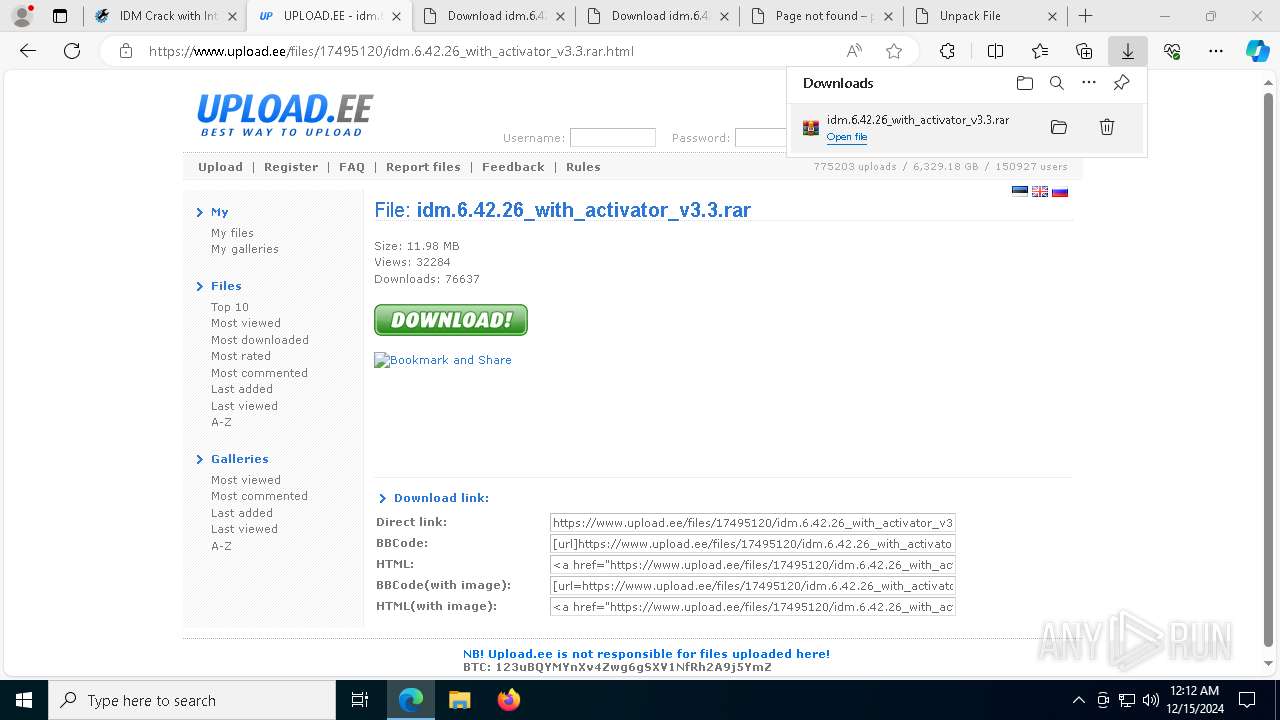
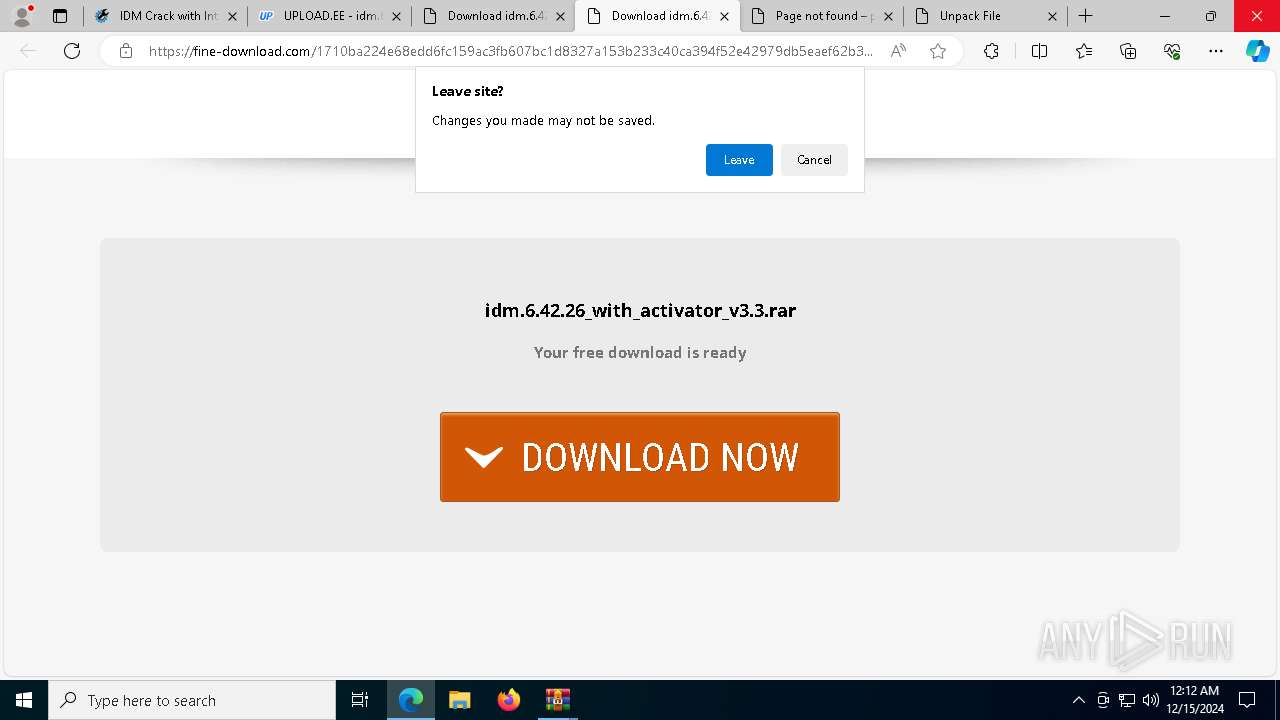
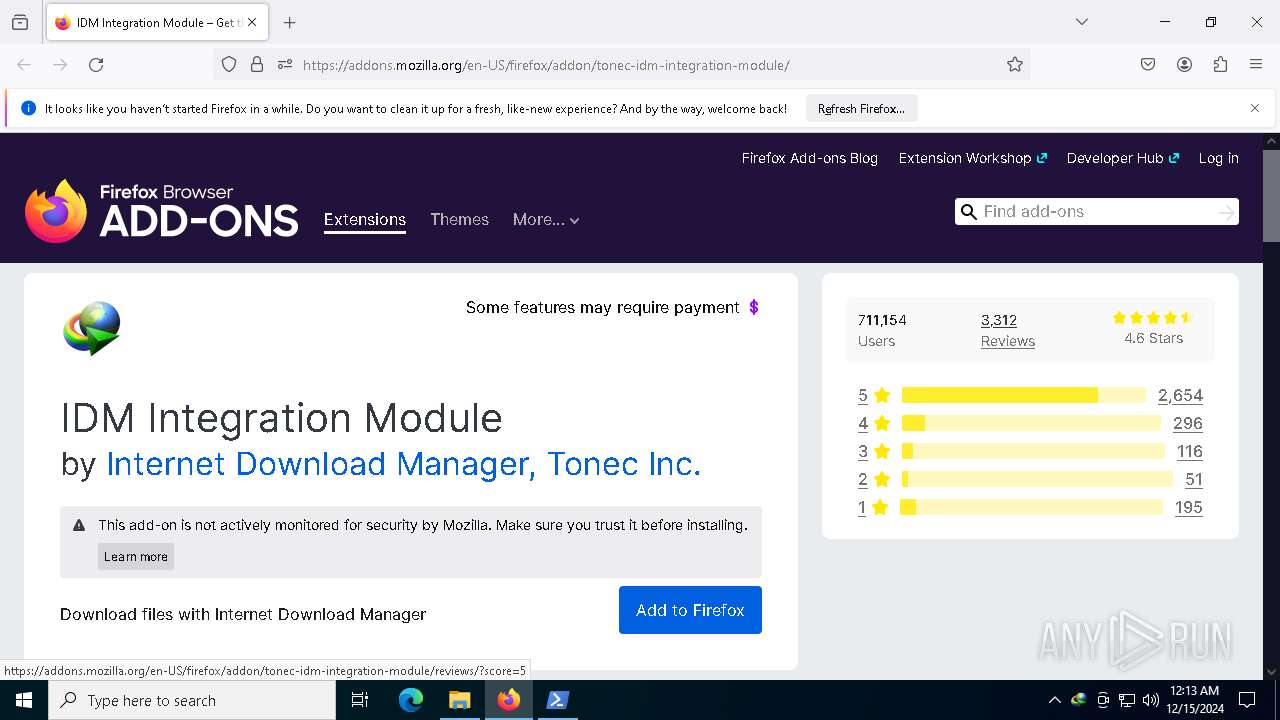
| URL: | https://www.crackingcity.com/idm-crack/ |
| Full analysis: | https://app.any.run/tasks/27450b92-ba6b-4634-924a-49a11b27b214 |
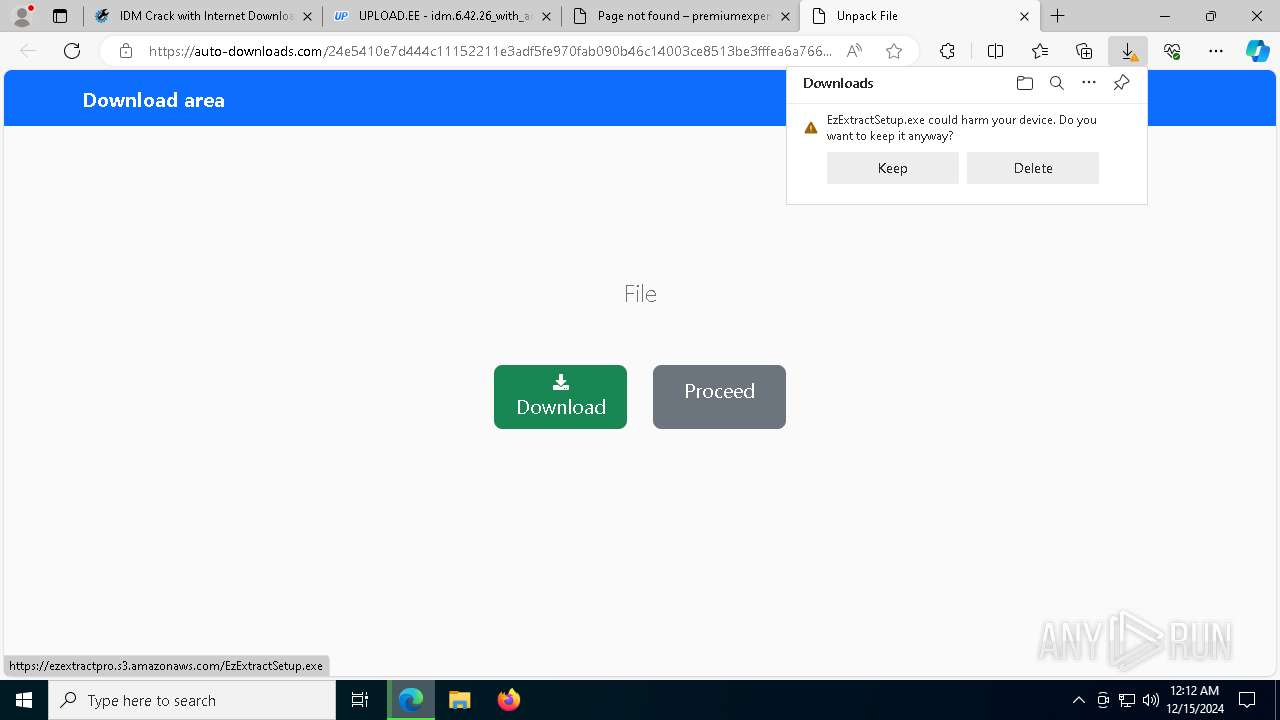
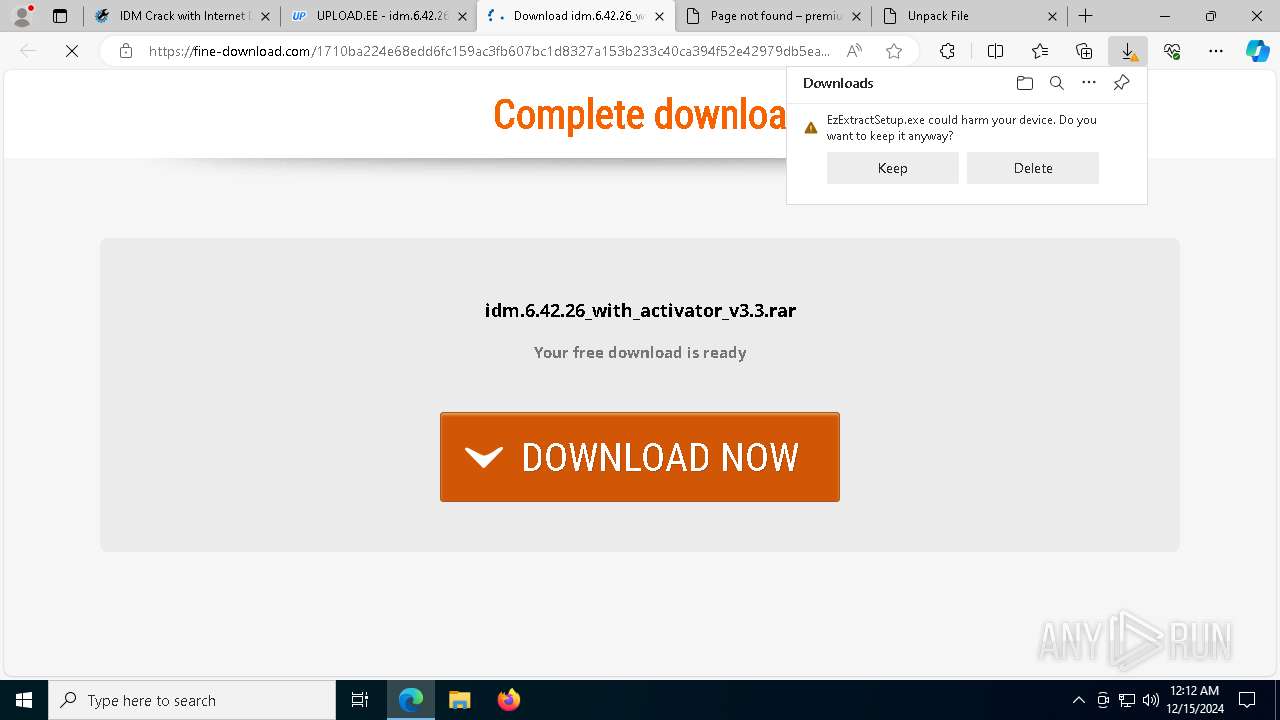
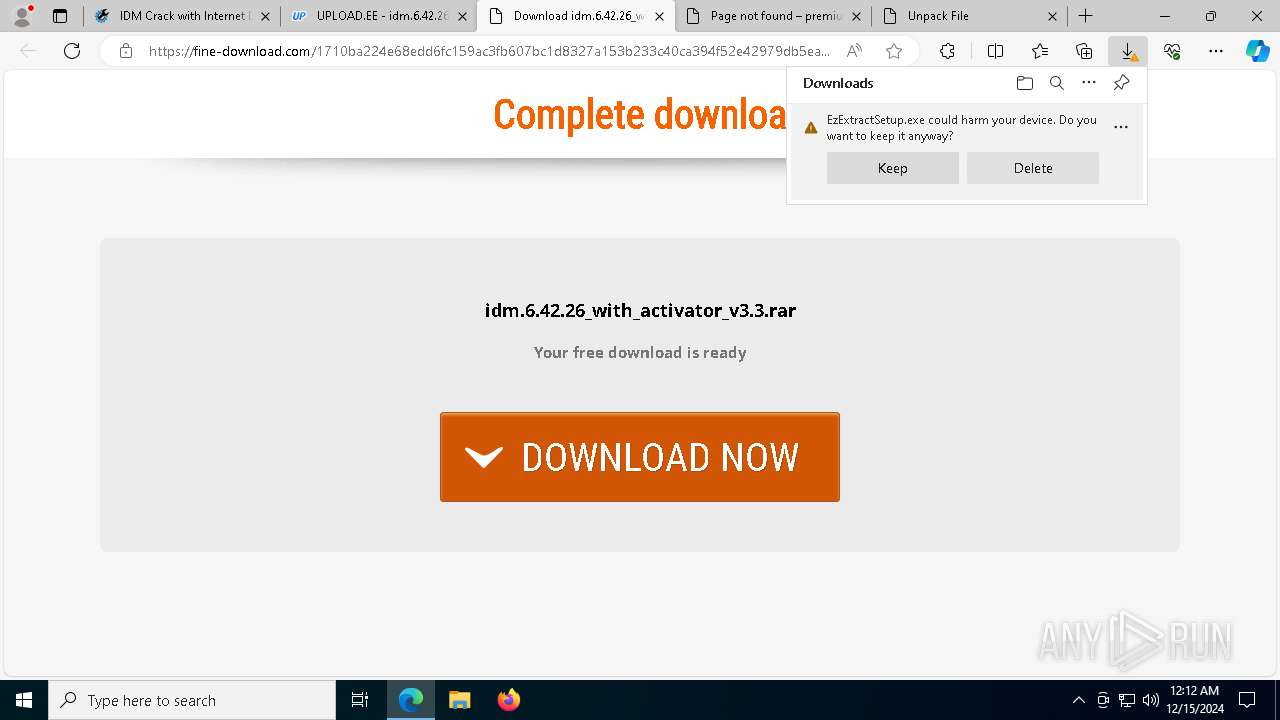
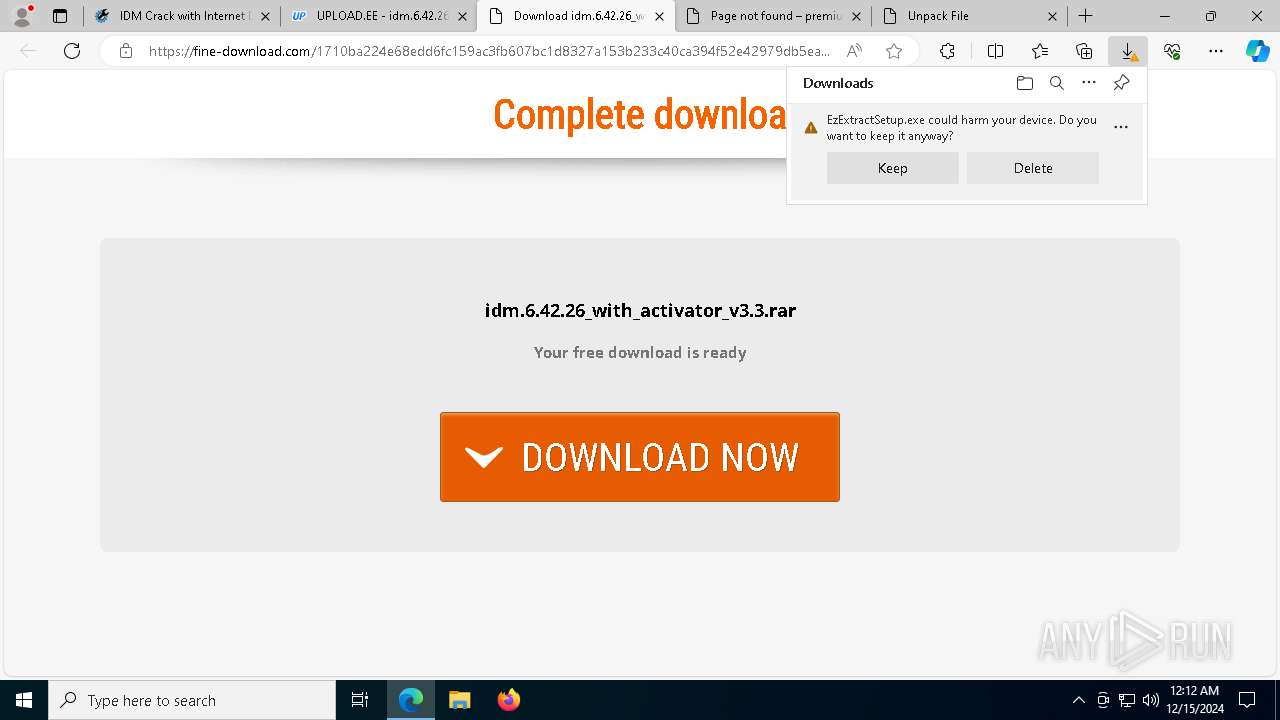
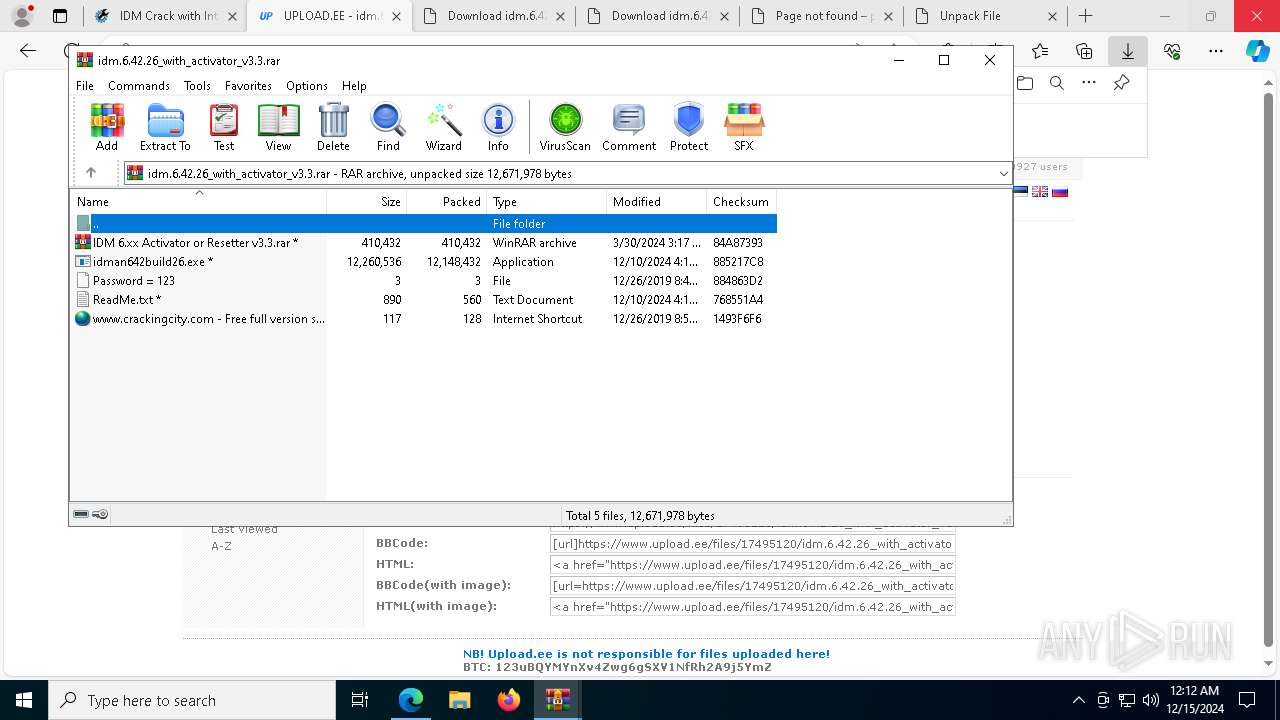
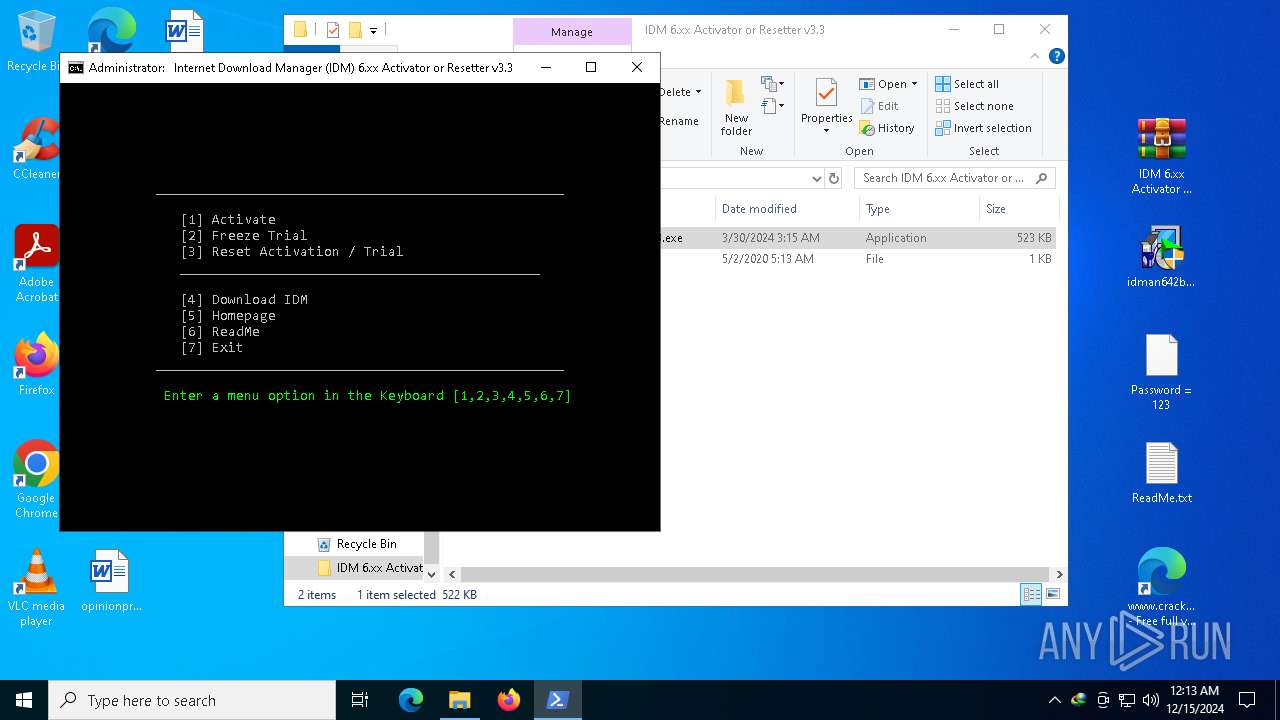
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2024, 00:11:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
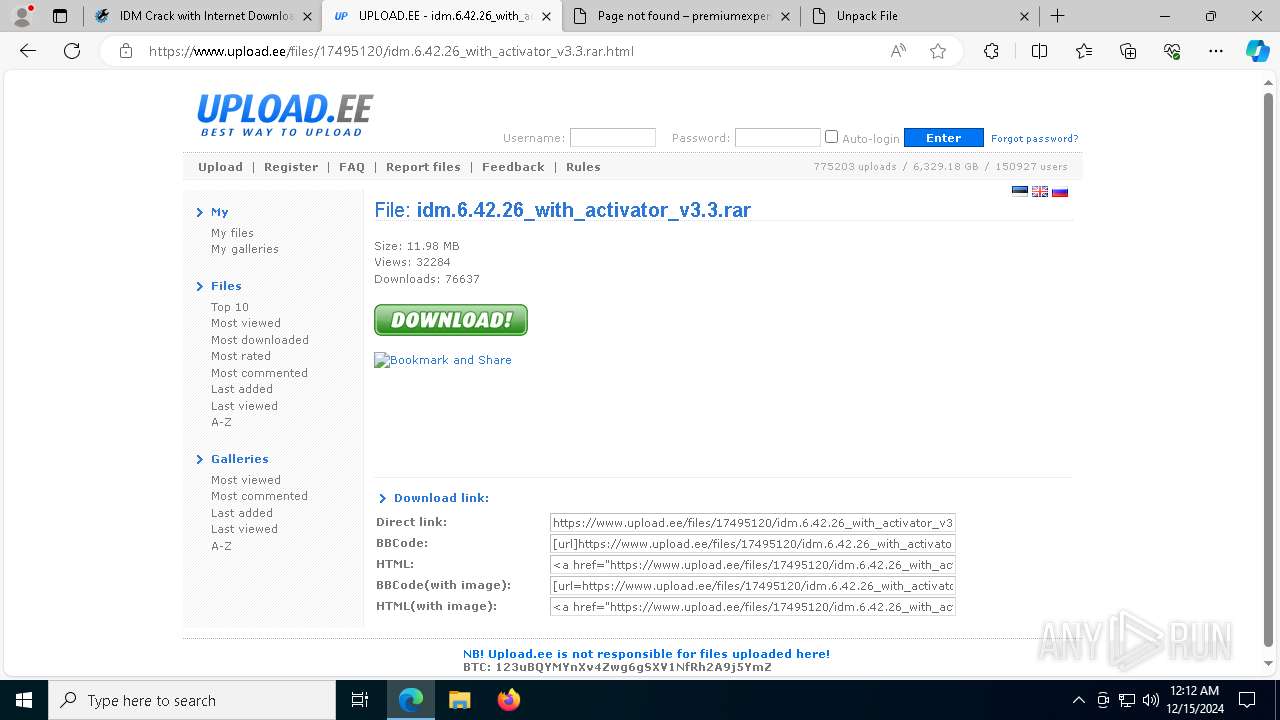
| MD5: | 5D91DA13F2DE9367F54F80D3D118E9AF |
| SHA1: | 4662EFF267E35446C40CD13D31ABBFA09801E272 |
| SHA256: | D00B8E831BD1D0303B23DA37F8CDB7BEA97B696F593F1DCEE29E152FD8CBBA48 |
| SSDEEP: | 3:N8DSLbMLF8TKtfl:2OLQ9 |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- IDM1.tmp (PID: 7004)
- IDMan.exe (PID: 3620)
- Uninstall.exe (PID: 7284)
- IDMan.exe (PID: 6656)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7952)
Changes the autorun value in the registry
- rundll32.exe (PID: 7100)
- IDMan.exe (PID: 3620)
Starts NET.EXE for service management
- Uninstall.exe (PID: 7284)
- net.exe (PID: 8012)
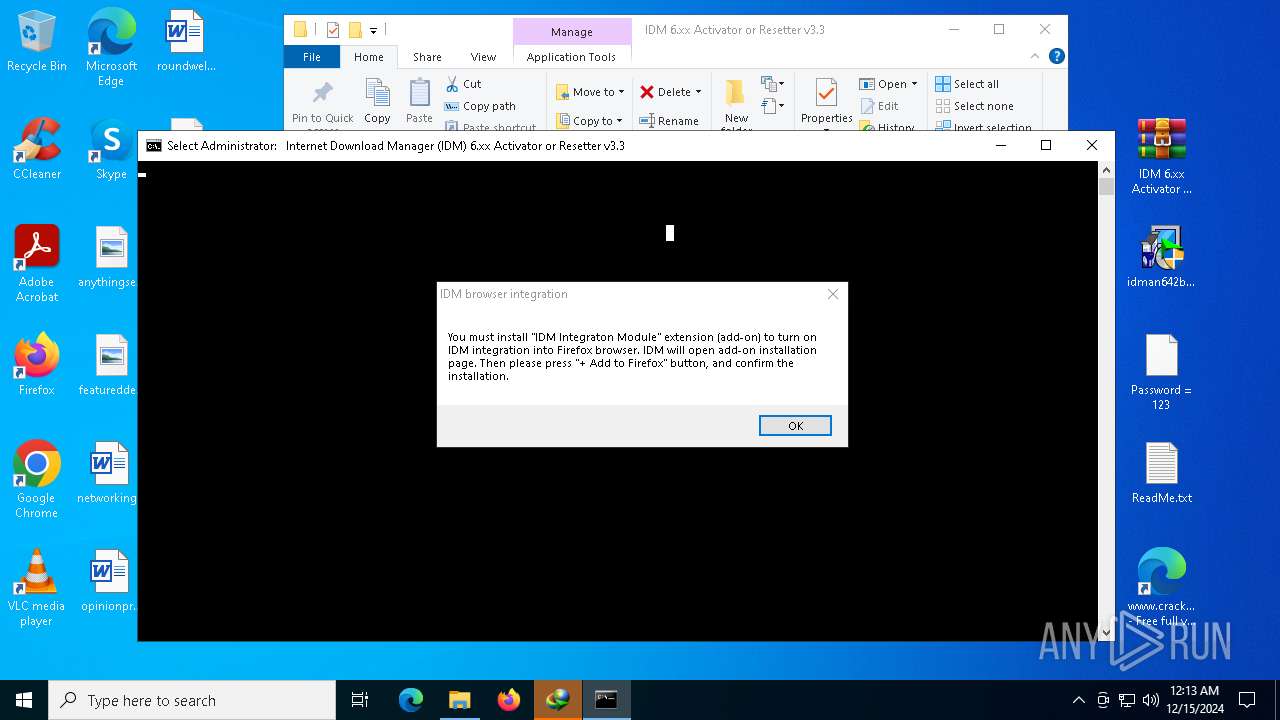
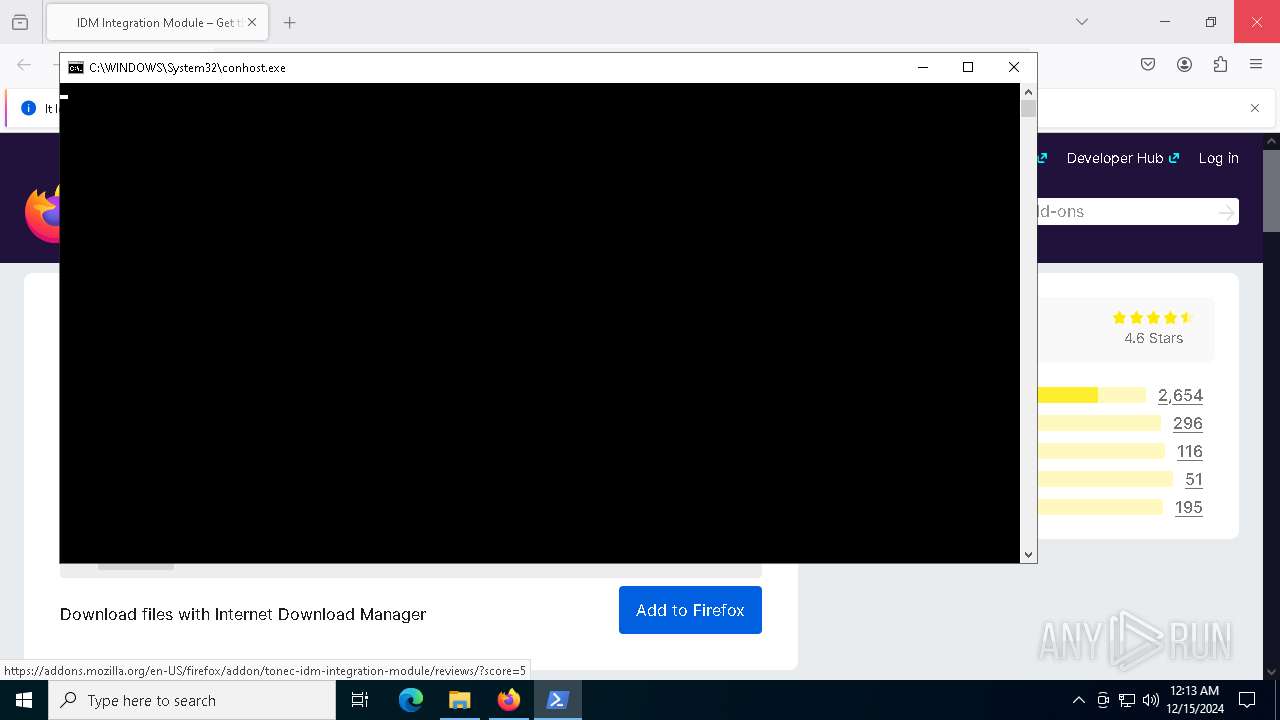
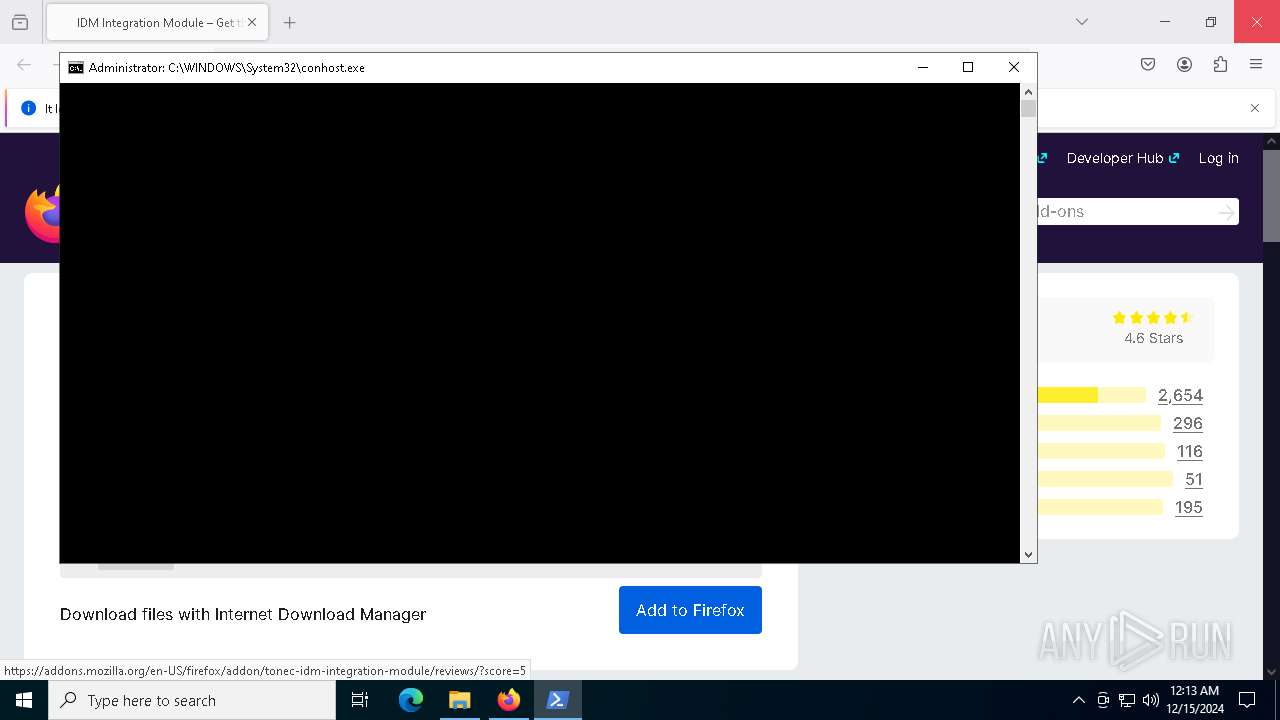
Execute application with conhost.exe as parent process
- powershell.exe (PID: 7604)
Adds process to the Windows Defender exclusion list
- cmd.exe (PID: 7952)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7952)
SUSPICIOUS
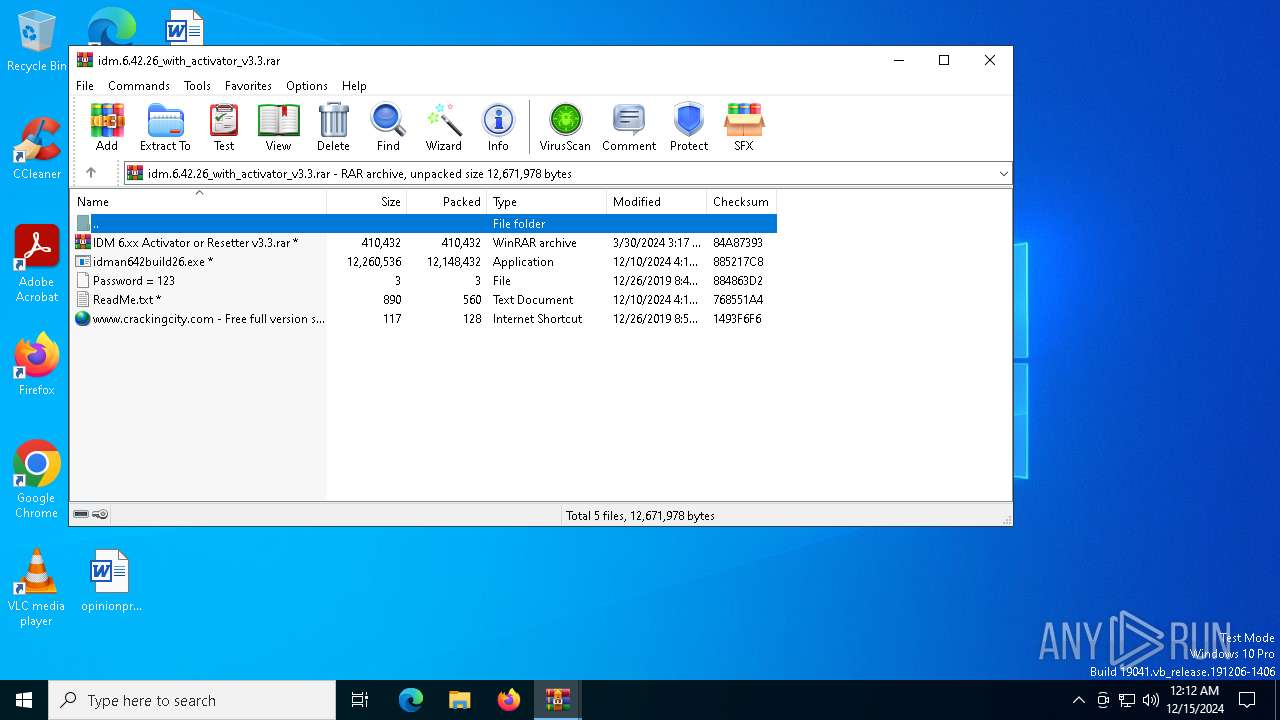
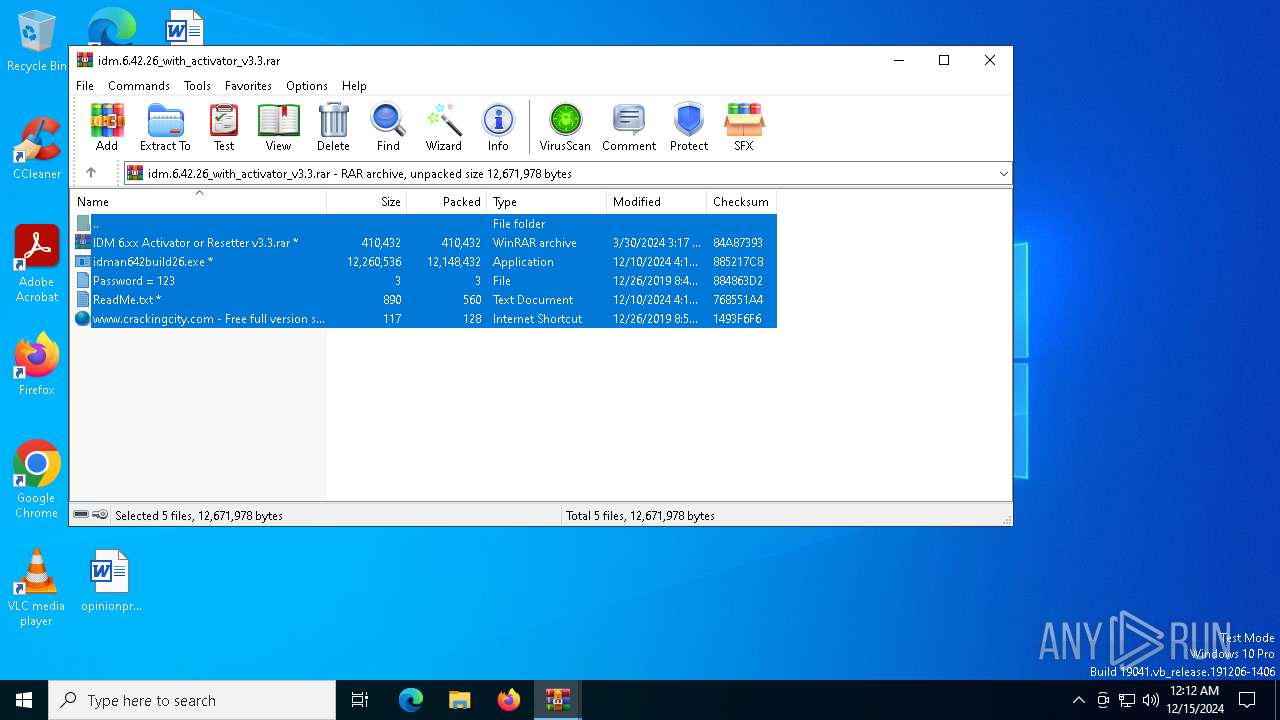
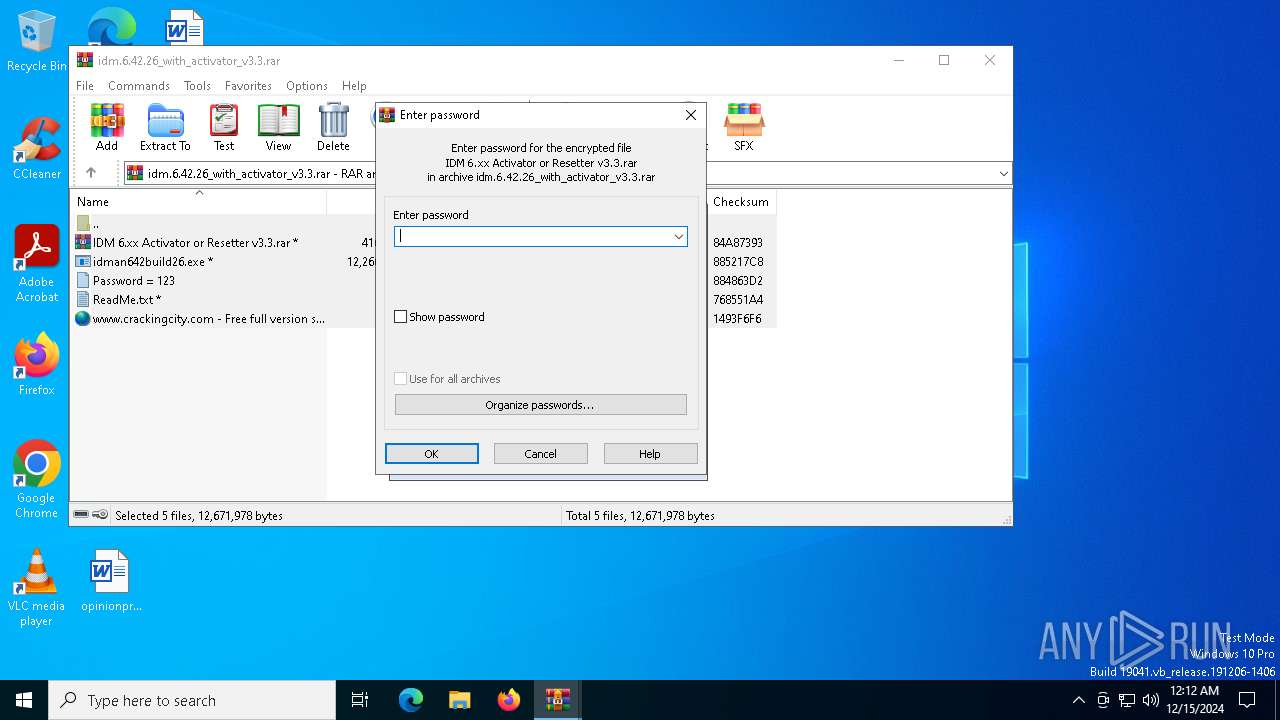
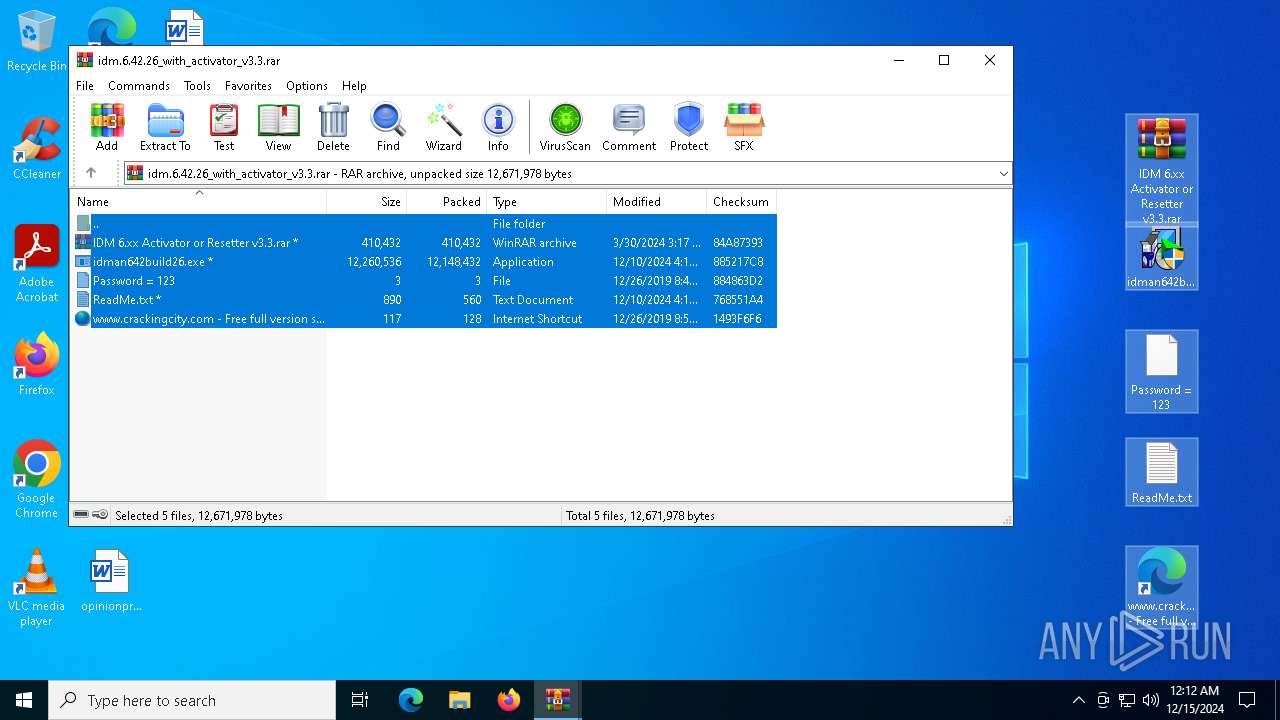
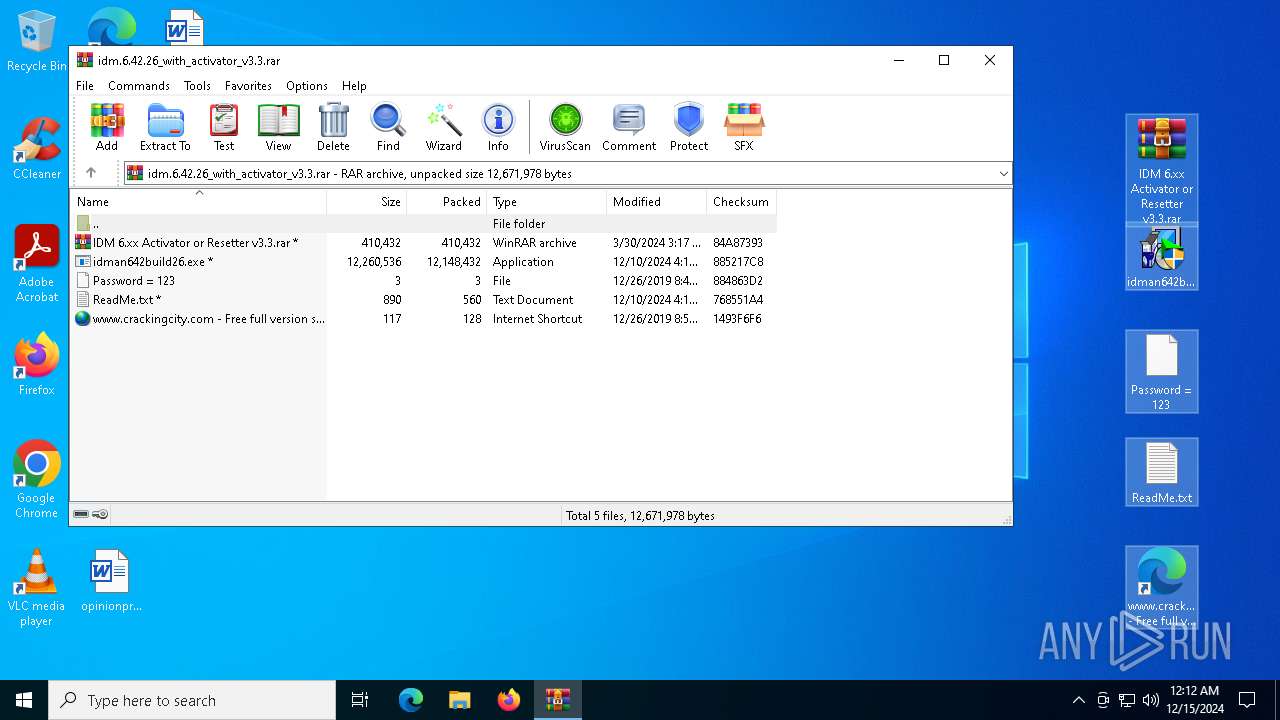
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7772)
- WinRAR.exe (PID: 7428)
- IDM1.tmp (PID: 7004)
- IDMan.exe (PID: 3620)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- Uninstall.exe (PID: 7284)
- IDMan.exe (PID: 6656)
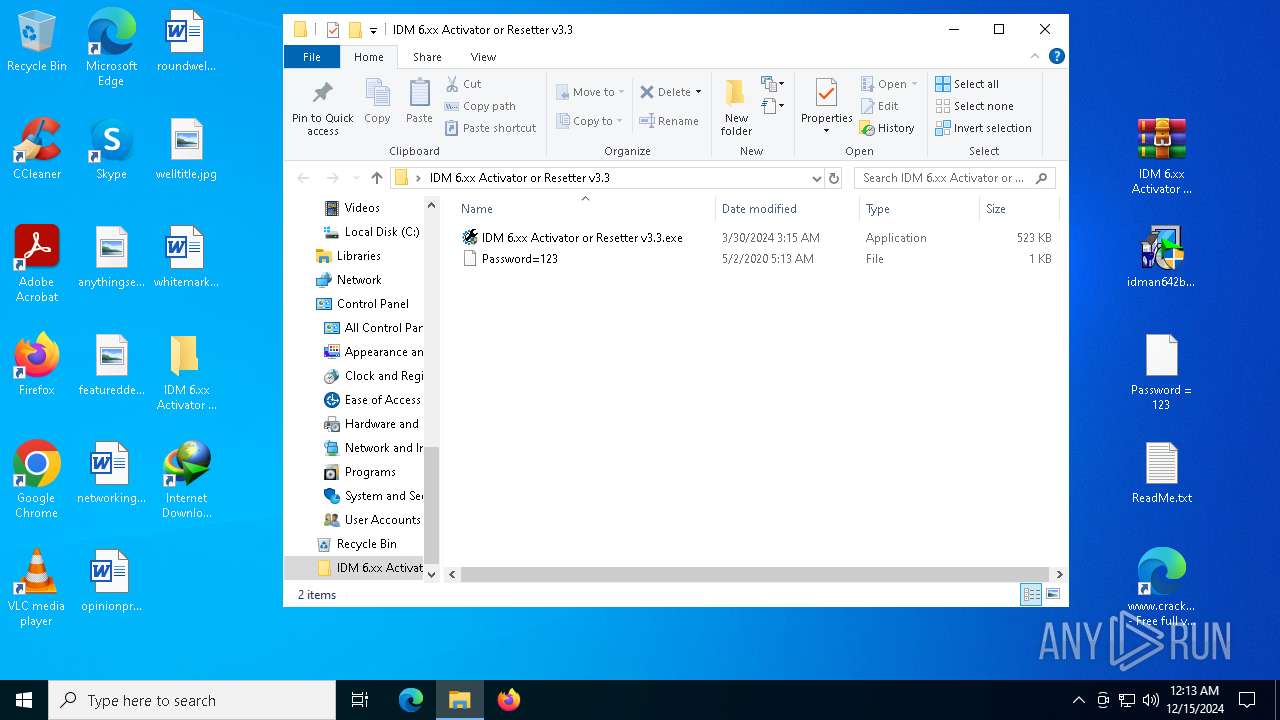
Starts application with an unusual extension
- idman642build26.exe (PID: 7000)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 7004)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6636)
- regsvr32.exe (PID: 6472)
- regsvr32.exe (PID: 6784)
- IDM1.tmp (PID: 7004)
- IDMan.exe (PID: 3620)
- regsvr32.exe (PID: 3260)
- regsvr32.exe (PID: 420)
- regsvr32.exe (PID: 6284)
- regsvr32.exe (PID: 6452)
- regsvr32.exe (PID: 1348)
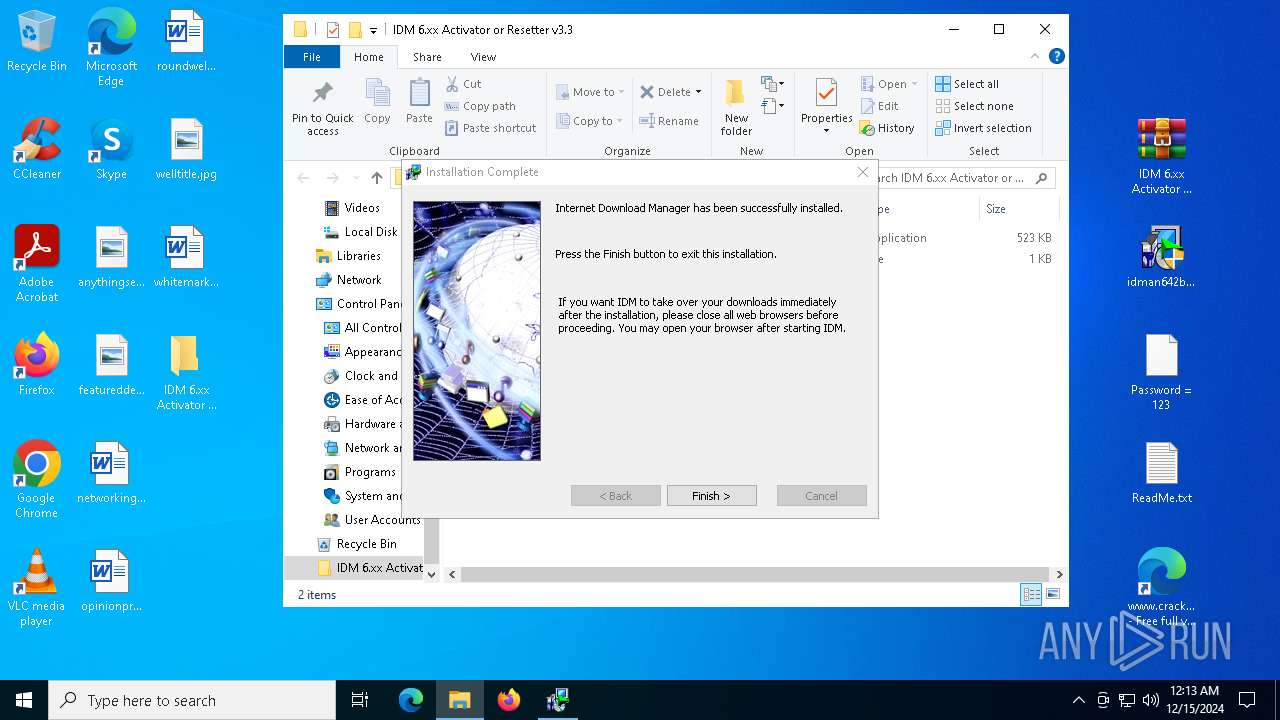
Creates a software uninstall entry
- IDM1.tmp (PID: 7004)
Checks Windows Trust Settings
- IDMan.exe (PID: 3620)
- drvinst.exe (PID: 6700)
- IDMan.exe (PID: 6656)
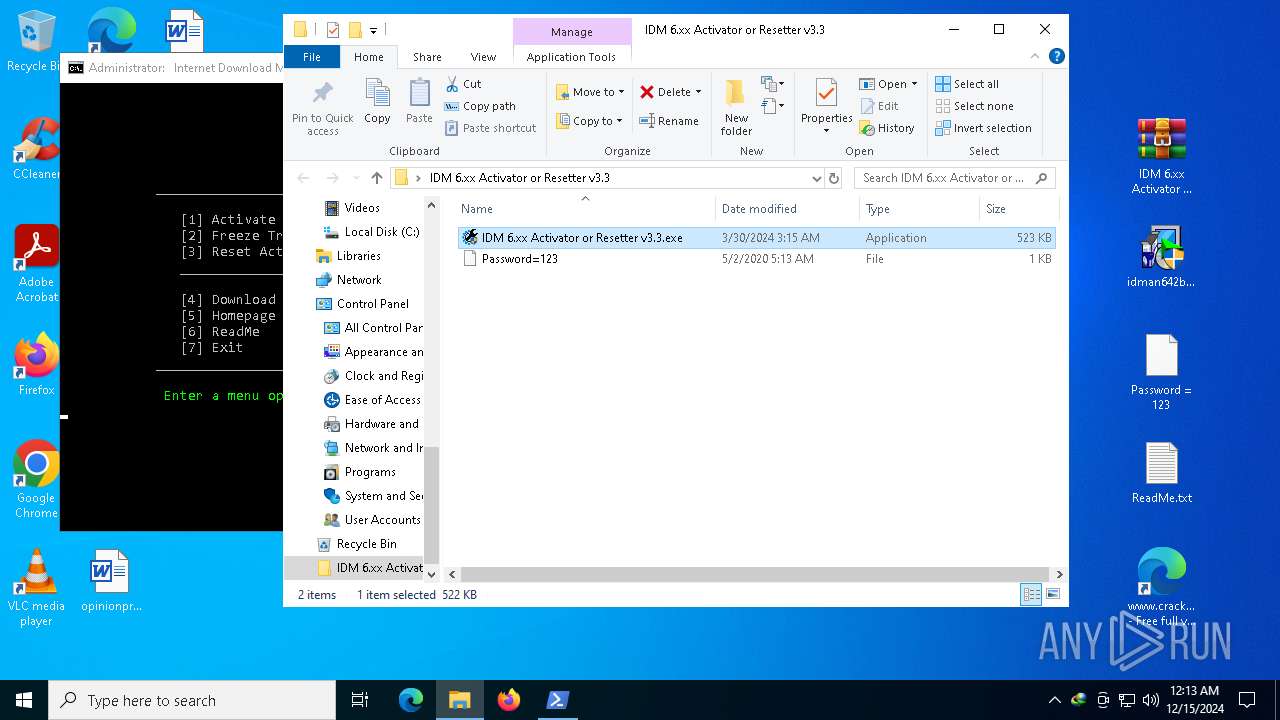
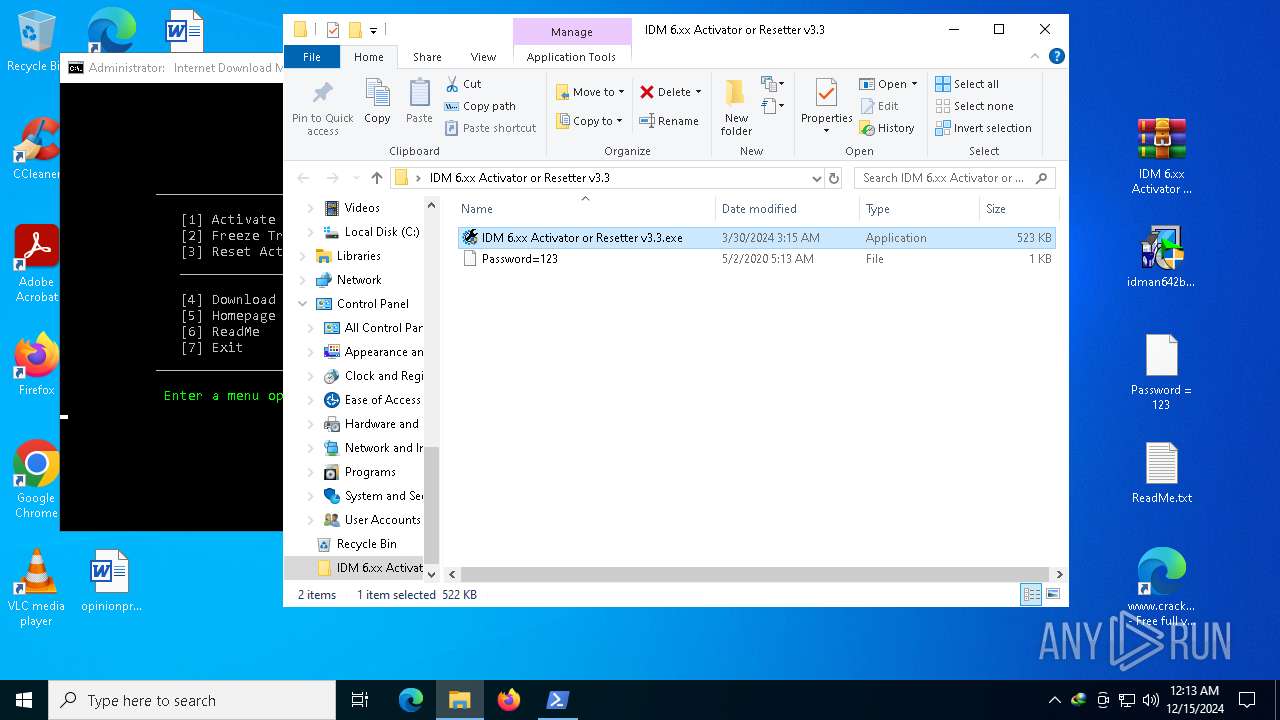
Executable content was dropped or overwritten
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- 7za.exe (PID: 7984)
- IDMan.exe (PID: 3620)
- drvinst.exe (PID: 6700)
- rundll32.exe (PID: 7100)
- 7za.exe (PID: 1740)
Drops 7-zip archiver for unpacking
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
The executable file from the user directory is run by the CMD process
- 7za.exe (PID: 7360)
- 7za.exe (PID: 7984)
- 7za.exe (PID: 7904)
- 7za.exe (PID: 7708)
- 7za.exe (PID: 2076)
- 7za.exe (PID: 1740)
Executing commands from a ".bat" file
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- cmd.exe (PID: 7388)
- powershell.exe (PID: 7604)
Starts CMD.EXE for commands execution
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7648)
- powershell.exe (PID: 7604)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 6280)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5460)
- cmd.exe (PID: 7952)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7952)
- cmd.exe (PID: 7600)
- conhost.exe (PID: 4336)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 5488)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7904)
Starts SC.EXE for service management
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7904)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7952)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 7284)
Application launched itself
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 6280)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7904)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7904)
Drops a system driver (possible attempt to evade defenses)
- drvinst.exe (PID: 6700)
- rundll32.exe (PID: 7100)
- 7za.exe (PID: 1740)
Creates files in the driver directory
- drvinst.exe (PID: 6700)
Creates or modifies Windows services
- drvinst.exe (PID: 7624)
- Uninstall.exe (PID: 7284)
Script adds exclusion process to Windows Defender
- cmd.exe (PID: 7952)
Hides command output
- cmd.exe (PID: 5488)
- cmd.exe (PID: 5728)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7904)
- cmd.exe (PID: 5728)
Process drops legitimate windows executable
- 7za.exe (PID: 1740)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 6252)
- msedge.exe (PID: 6492)
- WinRAR.exe (PID: 7772)
- WinRAR.exe (PID: 2092)
Application launched itself
- msedge.exe (PID: 6252)
- msedge.exe (PID: 1080)
- firefox.exe (PID: 4300)
- firefox.exe (PID: 716)
The process uses the downloaded file
- iexplore.exe (PID: 4504)
- msedge.exe (PID: 6252)
- msedge.exe (PID: 2084)
- WinRAR.exe (PID: 7772)
- WinRAR.exe (PID: 2092)
- IDM1.tmp (PID: 7004)
- IDMan.exe (PID: 3620)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- Uninstall.exe (PID: 7284)
- IDMan.exe (PID: 6656)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 3888)
Reads the computer name
- identity_helper.exe (PID: 5244)
- identity_helper.exe (PID: 4468)
- IDM1.tmp (PID: 7004)
- idman642build26.exe (PID: 7000)
- idmBroker.exe (PID: 6352)
- IDMan.exe (PID: 3620)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- 7za.exe (PID: 7360)
- 7za.exe (PID: 2076)
- 7za.exe (PID: 7984)
- 7za.exe (PID: 7904)
- 7za.exe (PID: 7708)
- Uninstall.exe (PID: 7284)
- drvinst.exe (PID: 6700)
- drvinst.exe (PID: 7624)
- IDMan.exe (PID: 6656)
- MediumILStart.exe (PID: 6516)
- 7za.exe (PID: 1740)
Connects to unusual port
- msedge.exe (PID: 6492)
The sample compiled with english language support
- msedge.exe (PID: 6492)
- msedge.exe (PID: 6252)
- WinRAR.exe (PID: 7772)
- IDMan.exe (PID: 3620)
- rundll32.exe (PID: 7100)
- drvinst.exe (PID: 6700)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6252)
Checks supported languages
- identity_helper.exe (PID: 5244)
- identity_helper.exe (PID: 4468)
- idman642build26.exe (PID: 7000)
- IDM1.tmp (PID: 7004)
- idmBroker.exe (PID: 6352)
- IDMan.exe (PID: 3620)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- 7za.exe (PID: 7360)
- 7za.exe (PID: 7984)
- 7za.exe (PID: 7904)
- 7za.exe (PID: 2076)
- 7za.exe (PID: 7708)
- Uninstall.exe (PID: 7284)
- drvinst.exe (PID: 6700)
- drvinst.exe (PID: 7624)
- MediumILStart.exe (PID: 6516)
- IDMan.exe (PID: 6656)
- mode.com (PID: 7844)
- 7za.exe (PID: 1740)
Reads Environment values
- identity_helper.exe (PID: 5244)
- identity_helper.exe (PID: 4468)
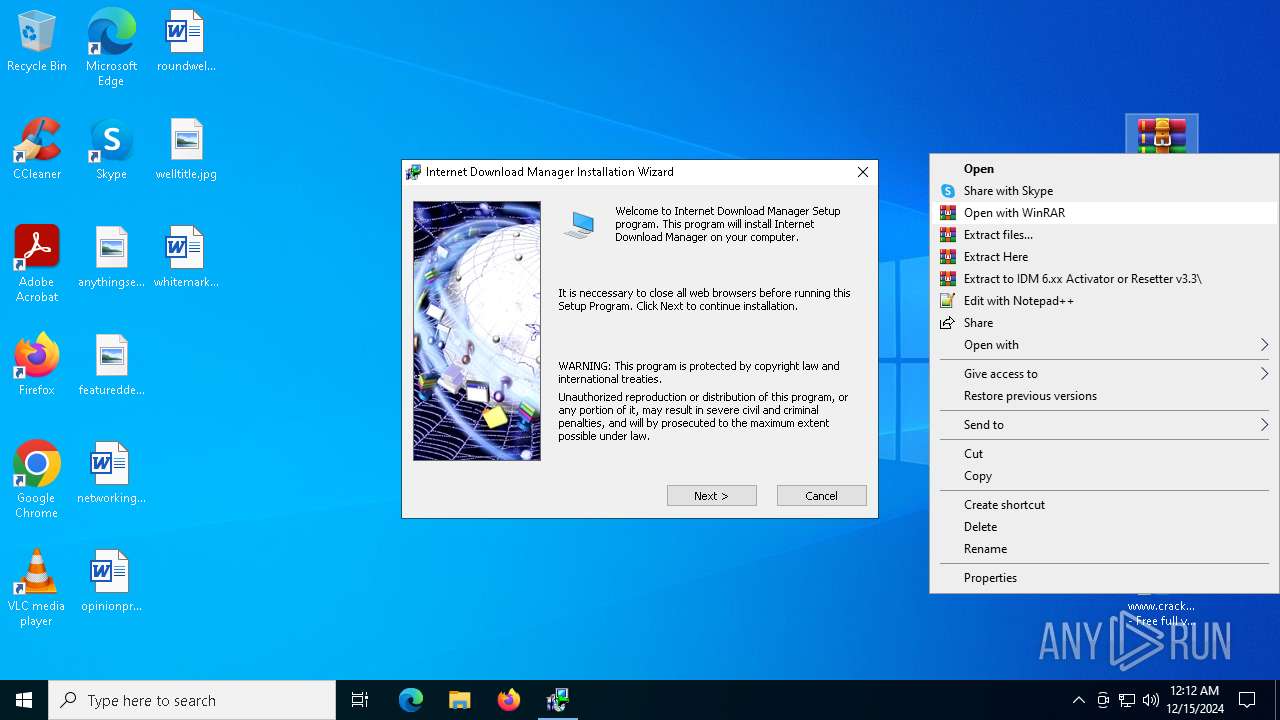
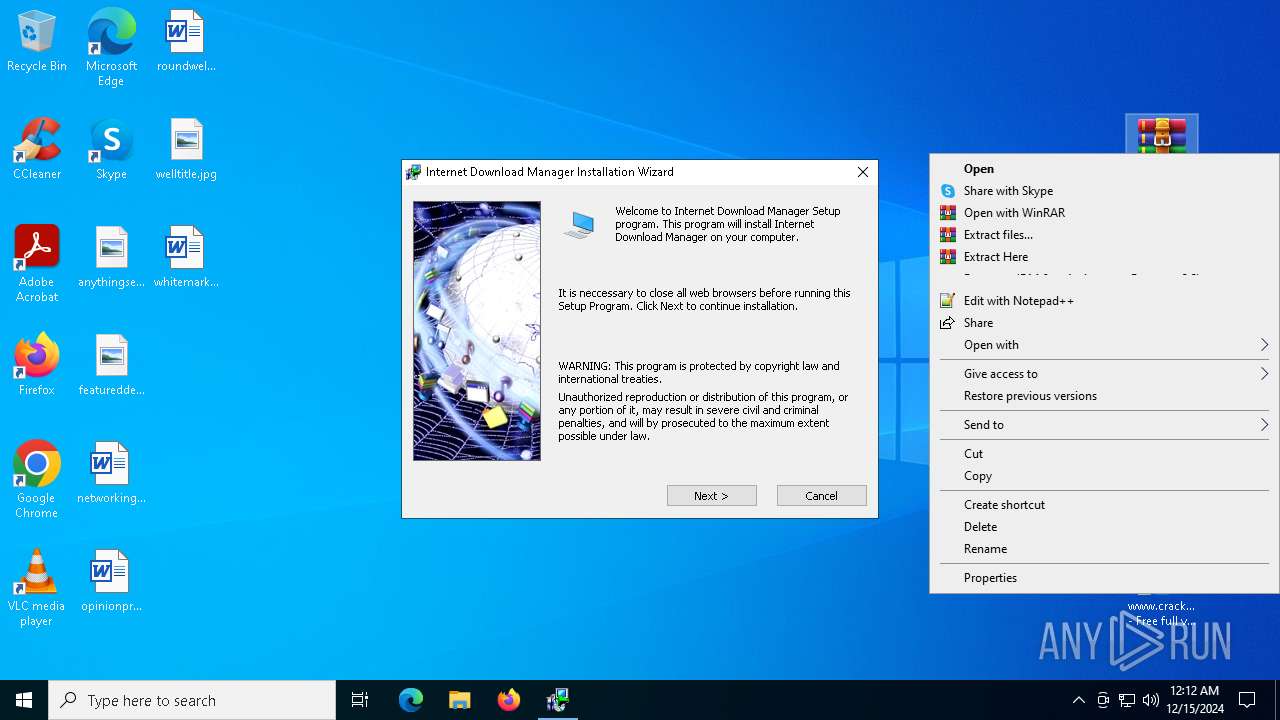
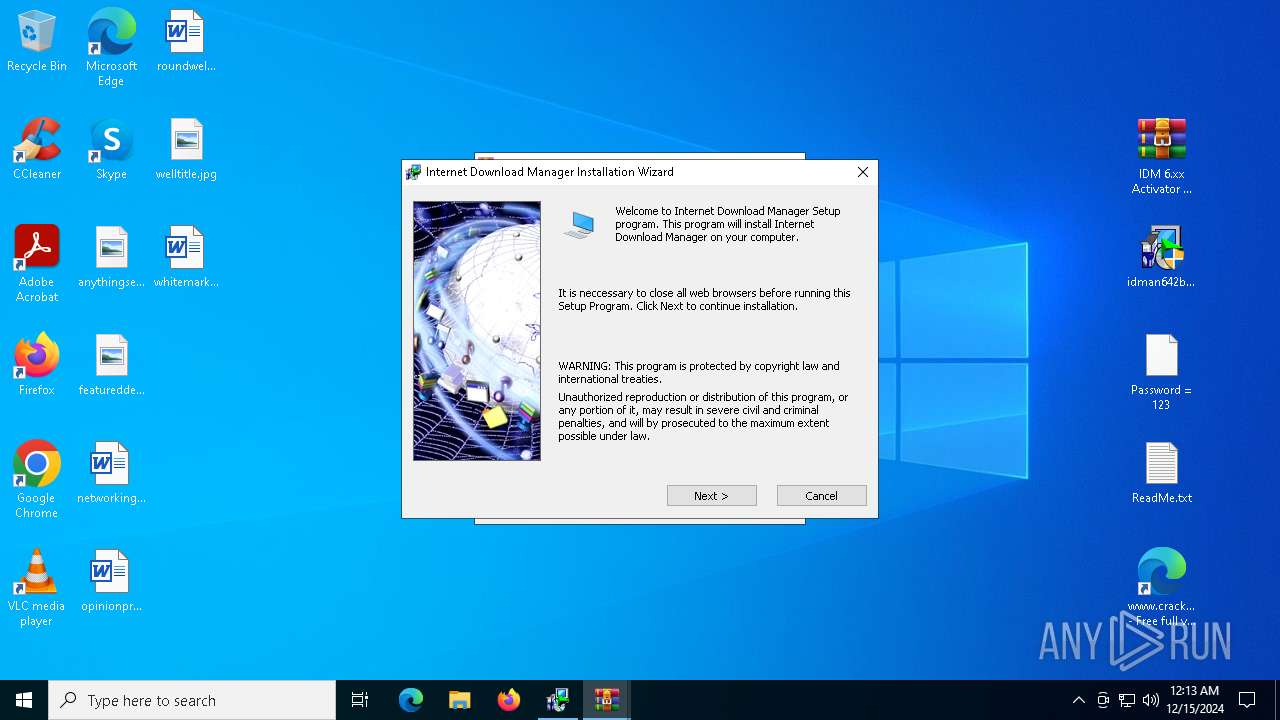
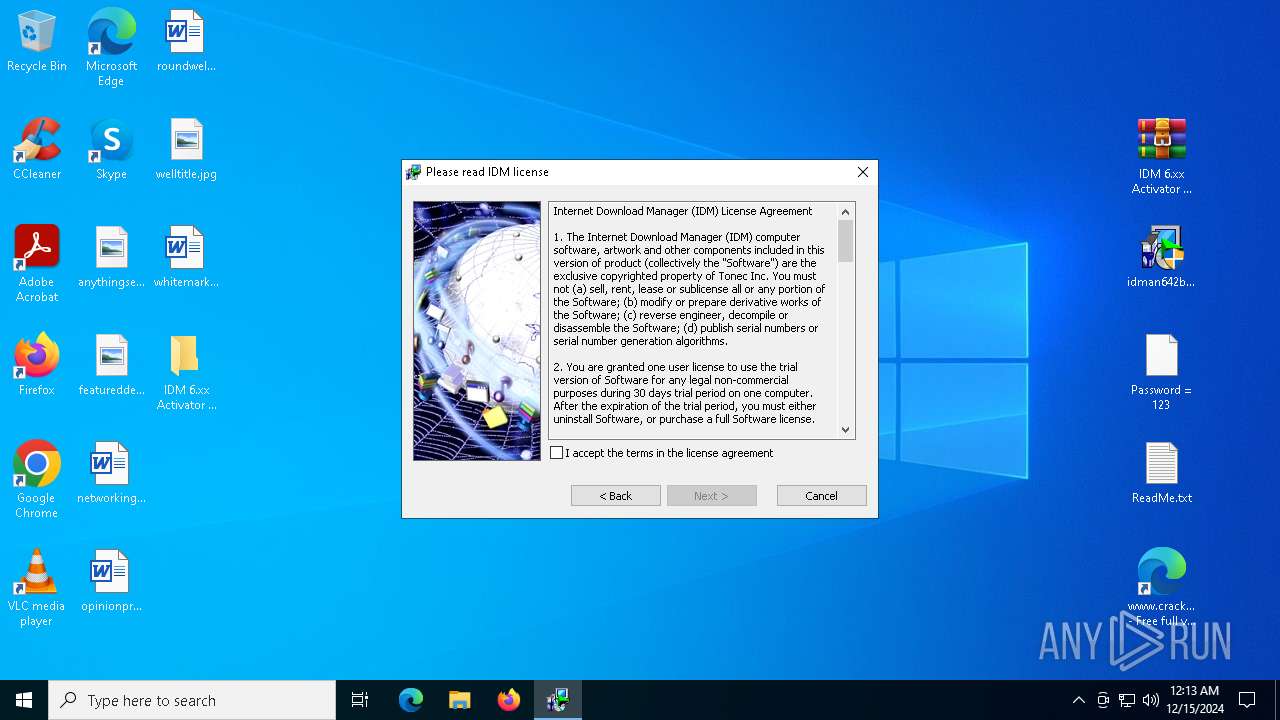
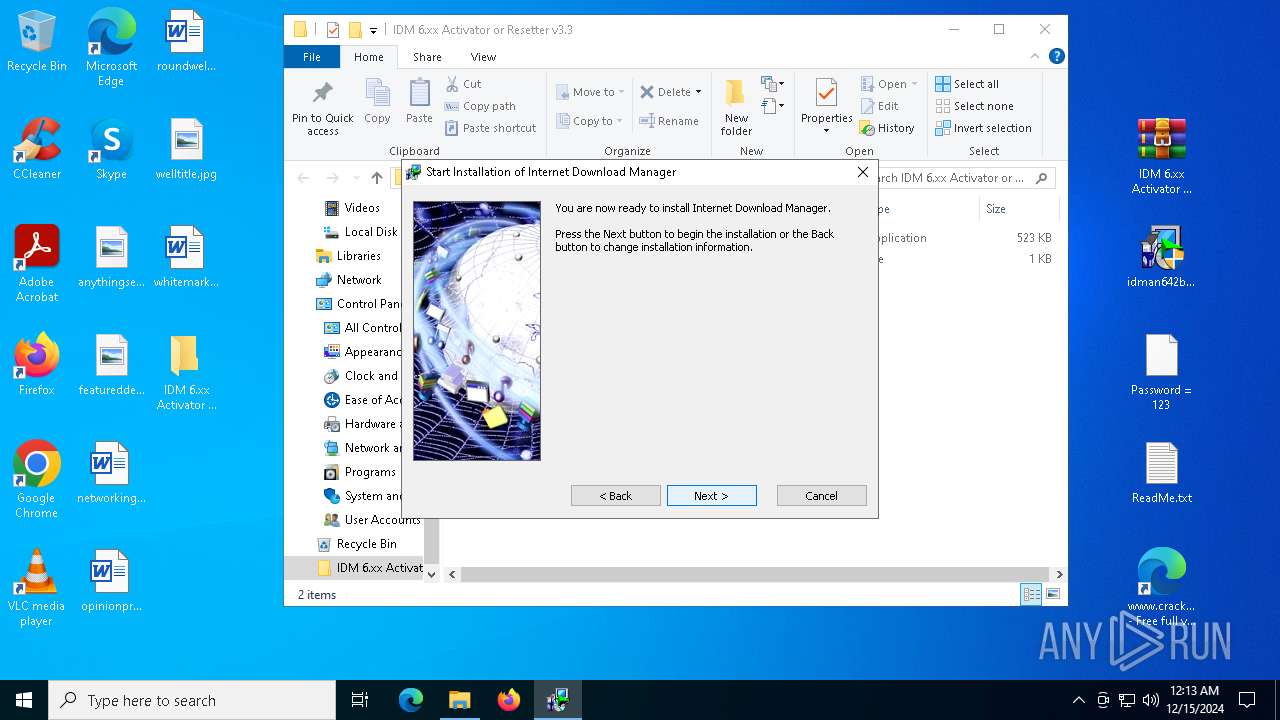
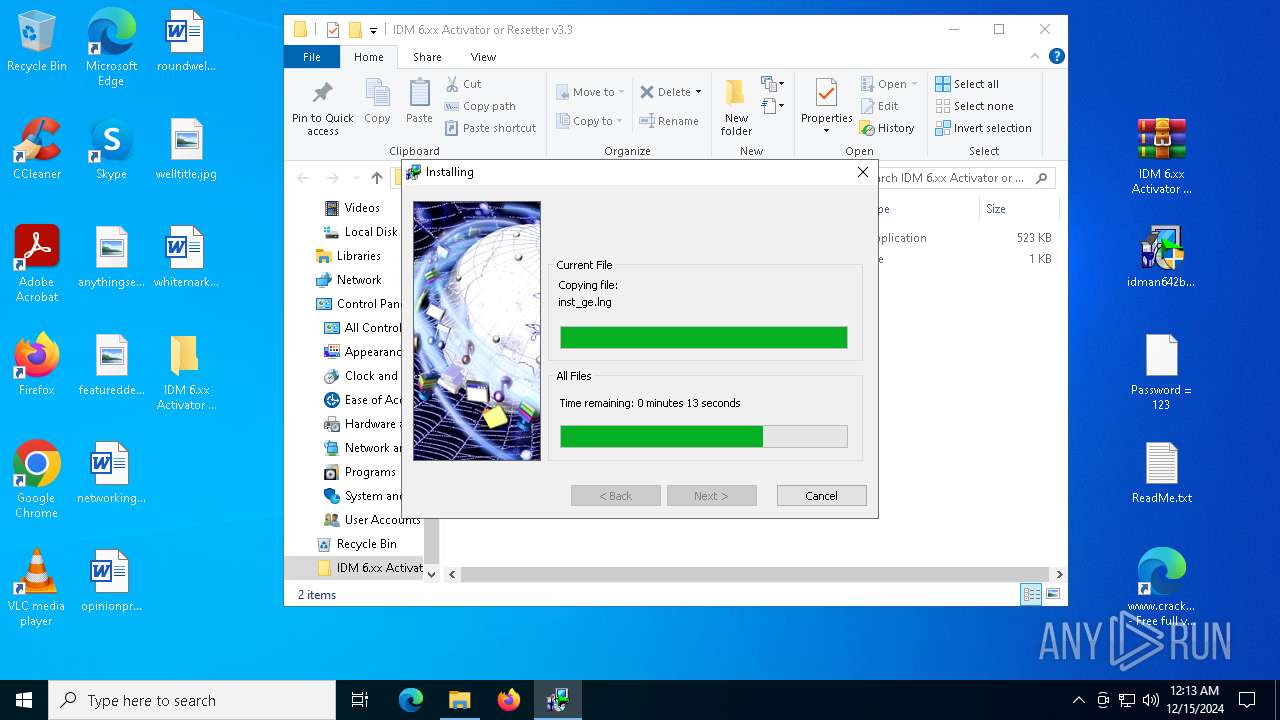
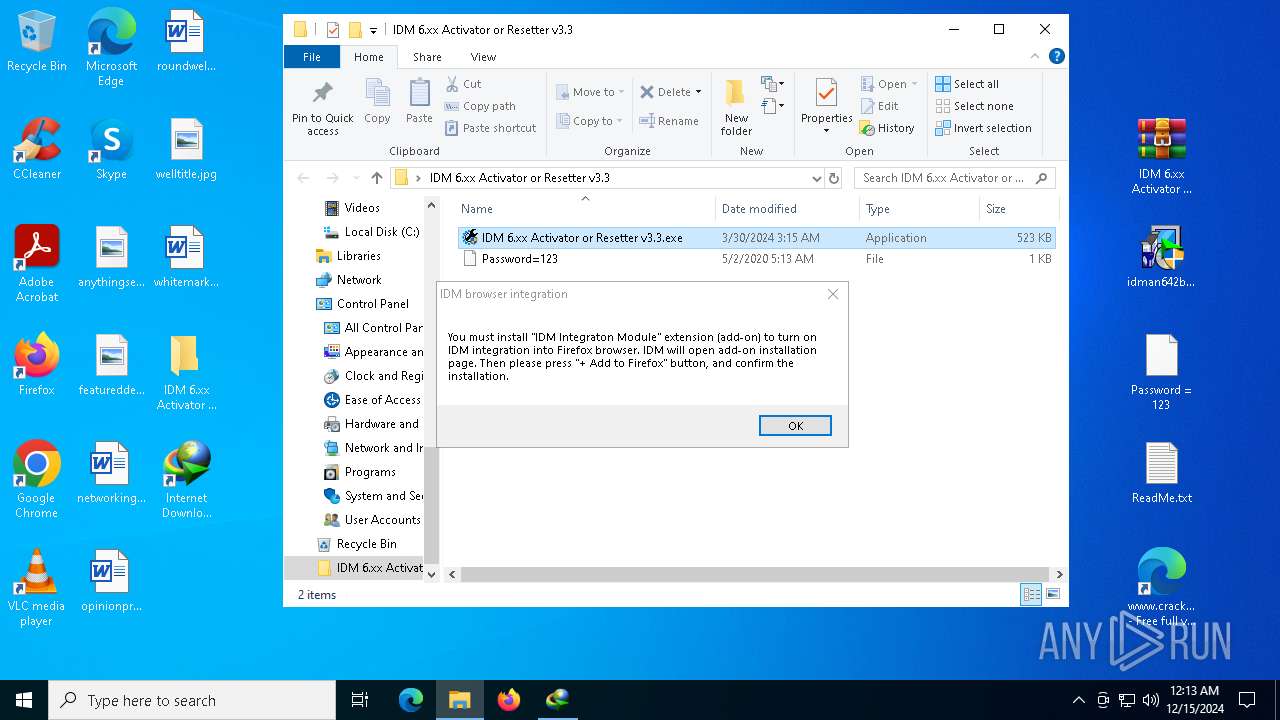
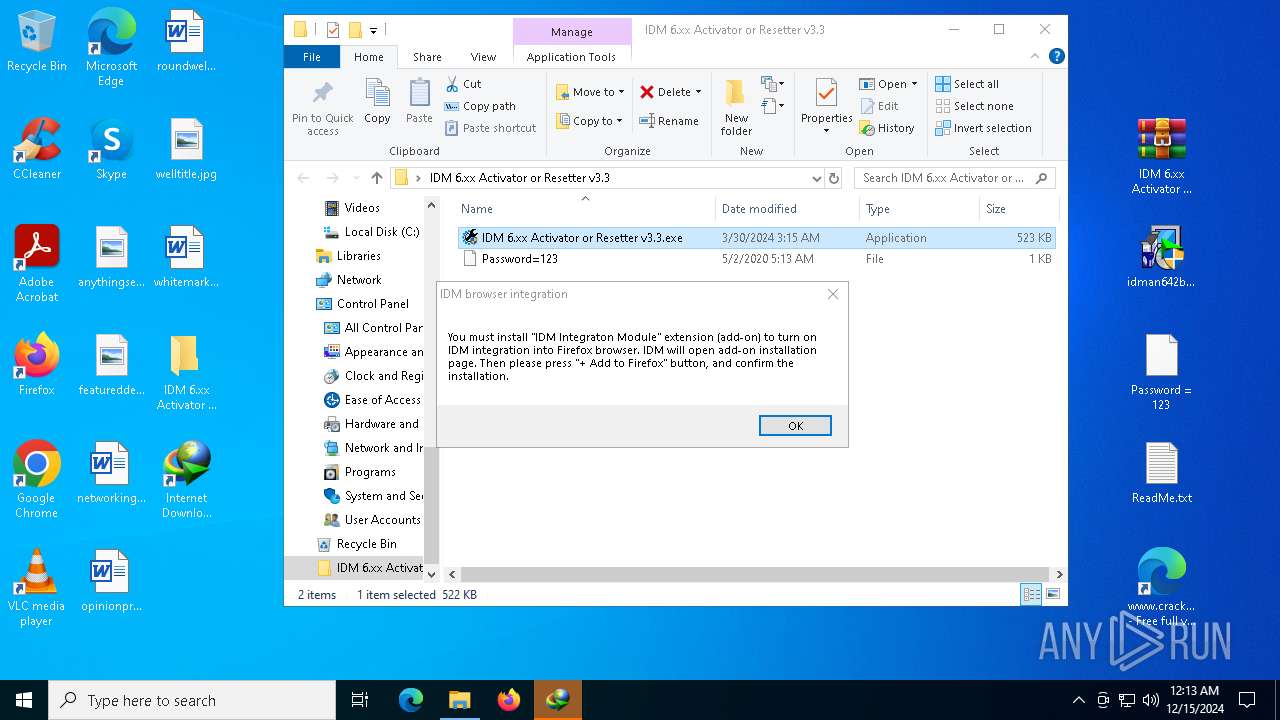
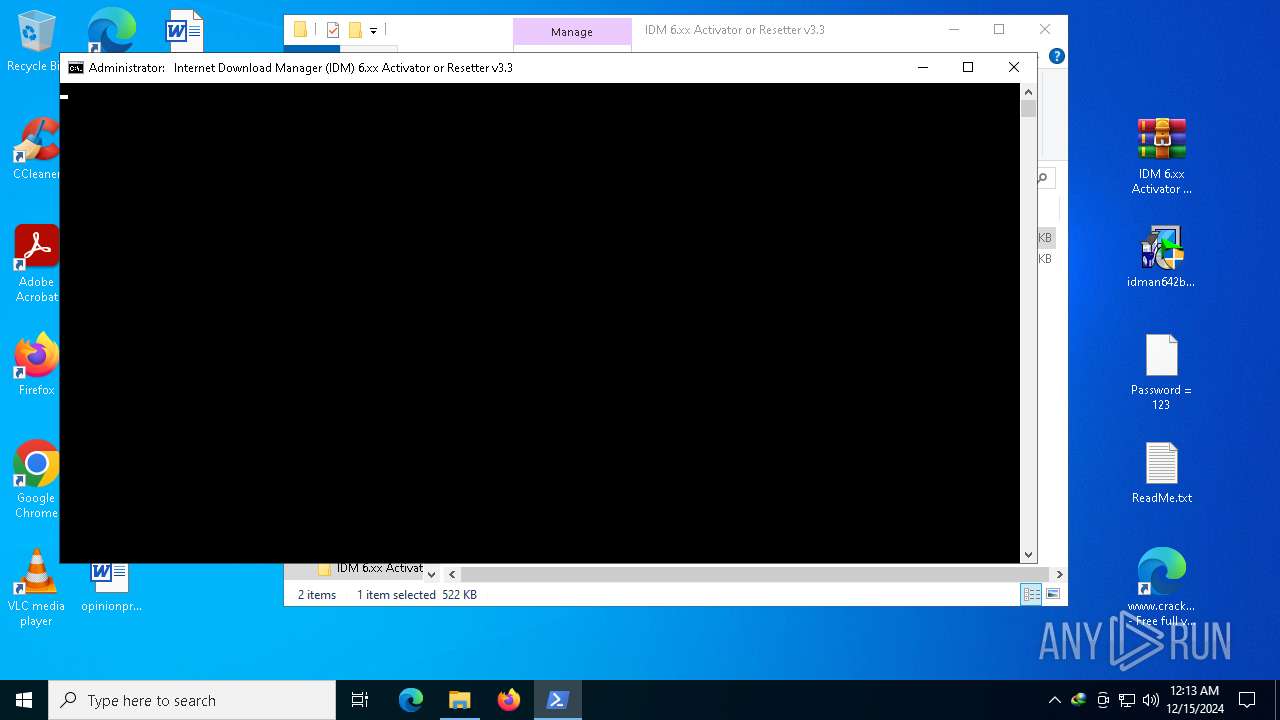
Manual execution by a user
- idman642build26.exe (PID: 7624)
- idman642build26.exe (PID: 7000)
- WinRAR.exe (PID: 2092)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6372)
- firefox.exe (PID: 716)
Create files in a temporary directory
- IDM1.tmp (PID: 7004)
- idman642build26.exe (PID: 7000)
- IDMan.exe (PID: 3620)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- 7za.exe (PID: 7984)
- 7za.exe (PID: 7360)
- 7za.exe (PID: 2076)
- rundll32.exe (PID: 7100)
- IDMan.exe (PID: 6656)
Process checks computer location settings
- IDM1.tmp (PID: 7004)
- IDMan.exe (PID: 3620)
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 6928)
- Uninstall.exe (PID: 7284)
- IDMan.exe (PID: 6656)
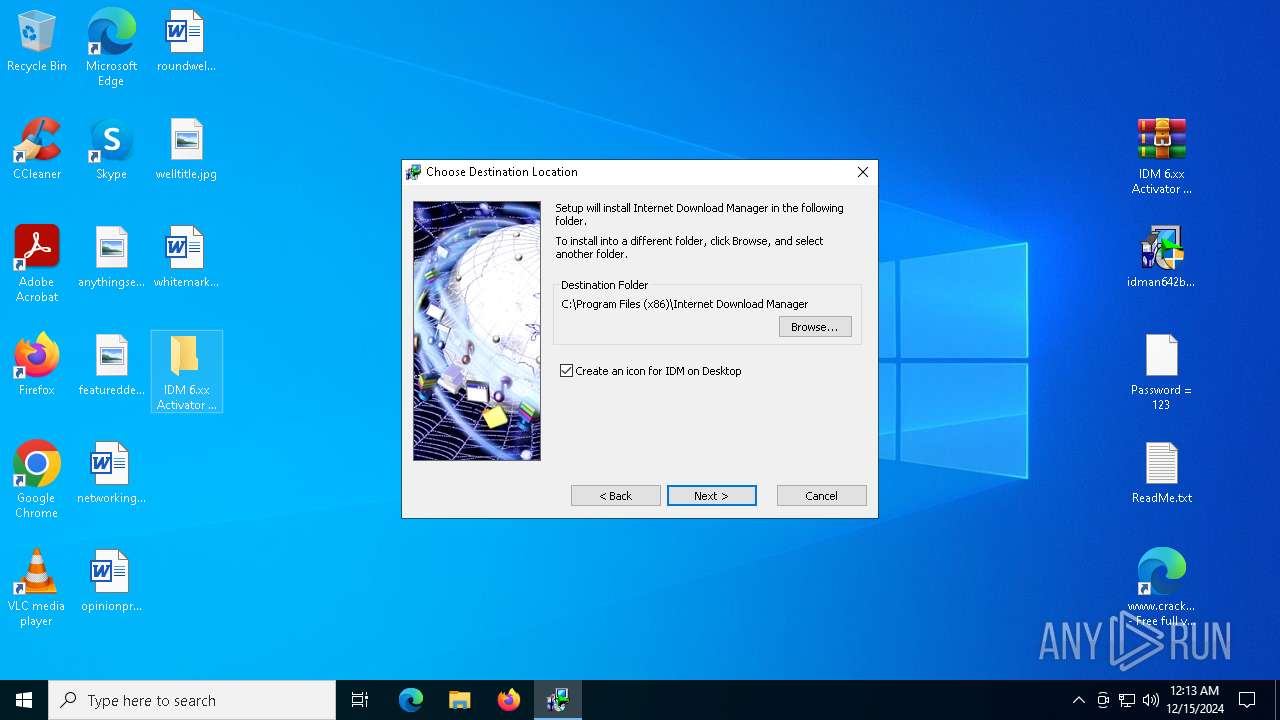
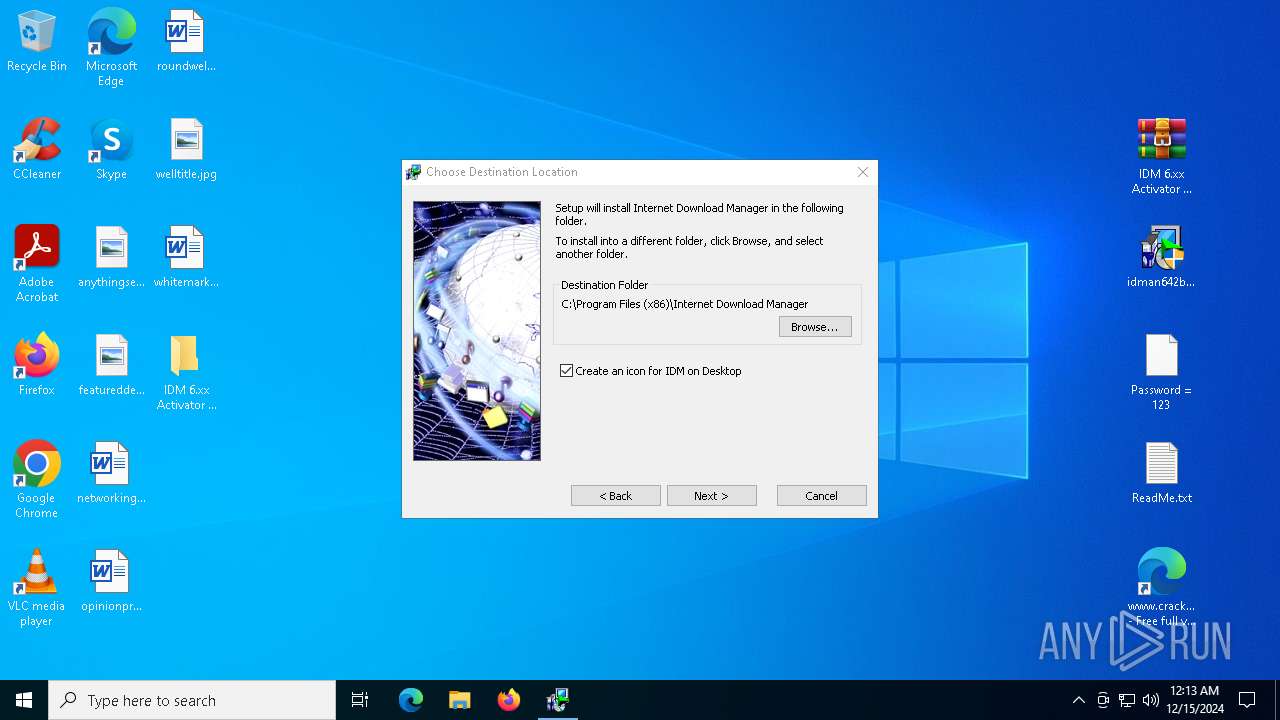
Creates files in the program directory
- IDM1.tmp (PID: 7004)
- IDMan.exe (PID: 3620)
Creates files or folders in the user directory
- IDM1.tmp (PID: 7004)
- IDMan.exe (PID: 3620)
- 7za.exe (PID: 1740)
Reads the software policy settings
- IDMan.exe (PID: 3620)
- drvinst.exe (PID: 6700)
Disables trace logs
- IDMan.exe (PID: 3620)
- IDMan.exe (PID: 6656)
Checks proxy server information
- IDMan.exe (PID: 3620)
- IDMan.exe (PID: 6656)
- powershell.exe (PID: 6004)
Reads the machine GUID from the registry
- IDMan.exe (PID: 3620)
- drvinst.exe (PID: 6700)
- IDMan.exe (PID: 6656)
Checks operating system version
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7904)
Reads the time zone
- runonce.exe (PID: 6208)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7132)
- powershell.exe (PID: 7552)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7132)
- powershell.exe (PID: 7552)
Reads security settings of Internet Explorer
- runonce.exe (PID: 6208)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7132)
- powershell.exe (PID: 7552)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 6432)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 7768)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 6432)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 3888)
Starts MODE.COM to configure console settings
- mode.com (PID: 7844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
342
Monitored processes
204
Malicious processes
16
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | /s "C:\Program Files (x86)\Internet Download Manager\IDMIECC64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --no-appcompat-clear --mojo-platform-channel-handle=6816 --field-trial-handle=2300,i,2244844903294092369,16960915066448286238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
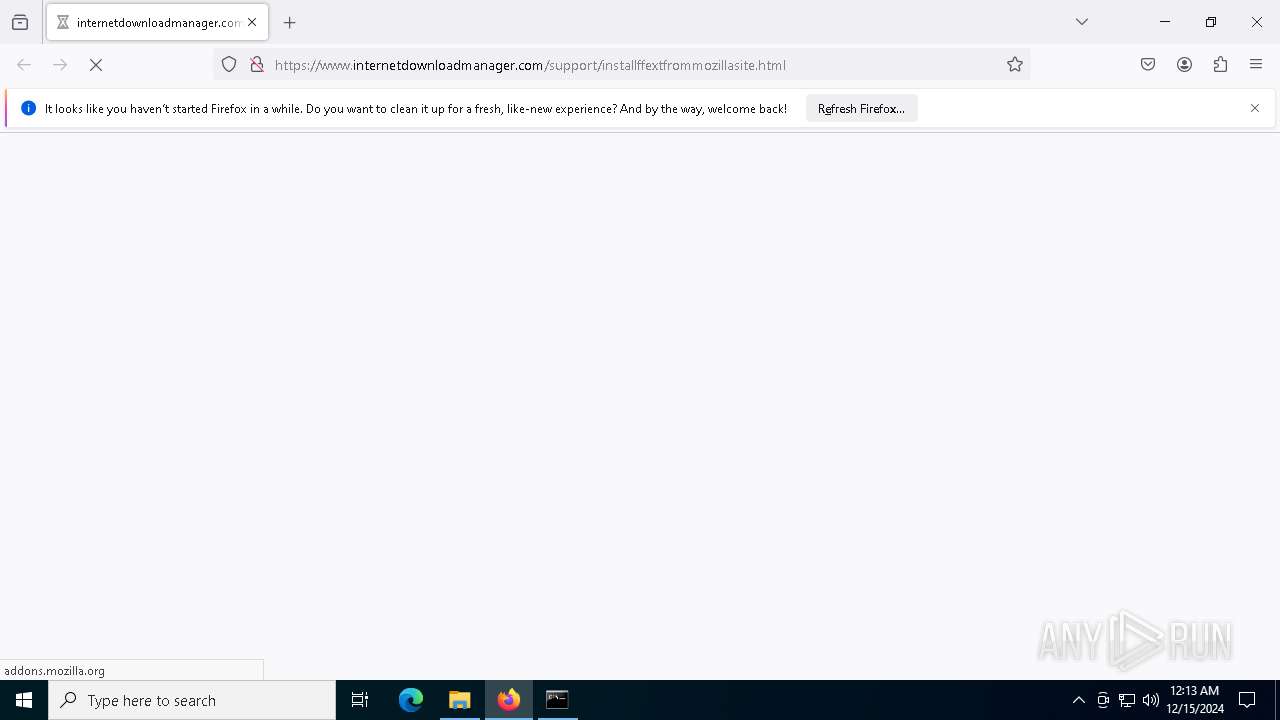
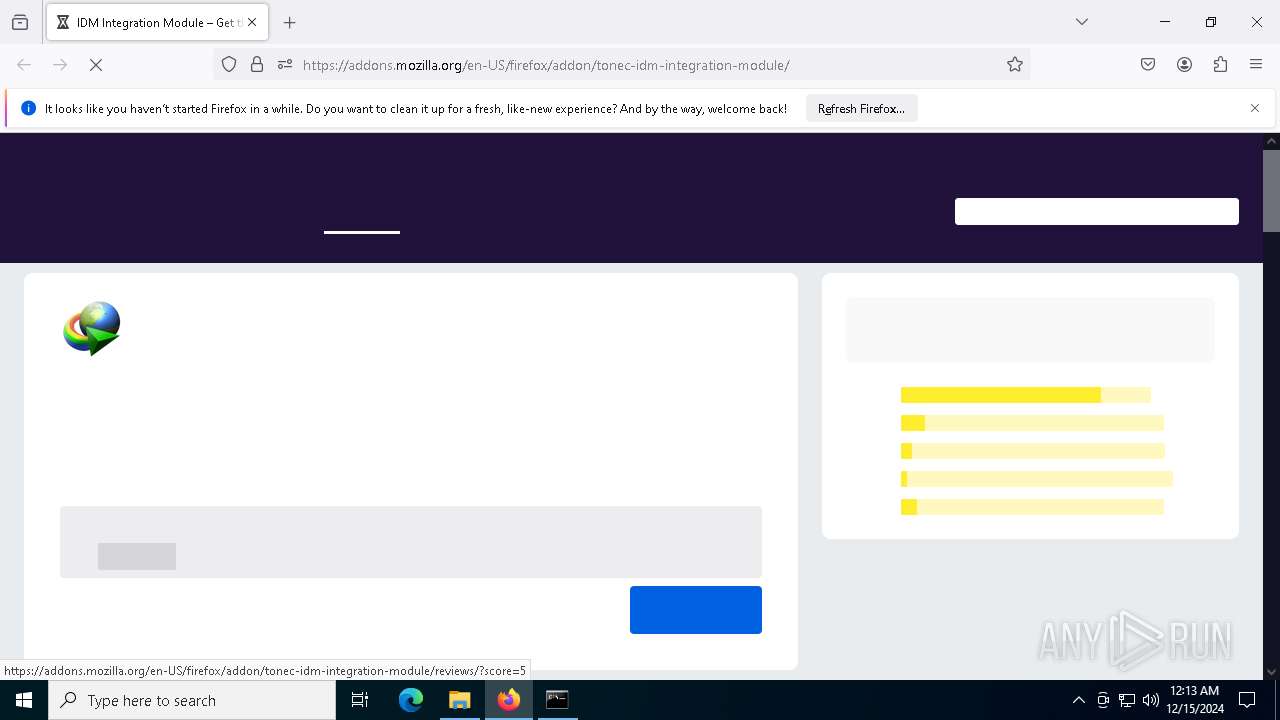
| 716 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.internetdownloadmanager.com/support/installffextfrommozillasite.html --attempting-deelevation | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 880 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3172 --field-trial-handle=2176,i,8764279284399479271,13583753781949104683,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | /s "C:\Program Files (x86)\Internet Download Manager\IDMShellExt64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | reg delete HKCU\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=6668 --field-trial-handle=2300,i,2244844903294092369,16960915066448286238,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
91 971
Read events
91 219
Write events
611
Delete events
141
Modification events
| (PID) Process: | (4504) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4504) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4504) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4504) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4504) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4504) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6252) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6252) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6252) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6252) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
41
Suspicious files
443
Text files
159
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
271
DNS requests
380
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6812 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7496 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734254473&P2=404&P3=2&P4=gEUwj5vvThnaqiibwj%2foEc3UTPDf8o0rXU05POhZGahfBvWDRIGxlsLv07ViPya2eRTAQAskMgV7NYNCxvLiXQ%3d%3d | unknown | — | — | whitelisted |
6812 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7008 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734254473&P2=404&P3=2&P4=gEUwj5vvThnaqiibwj%2foEc3UTPDf8o0rXU05POhZGahfBvWDRIGxlsLv07ViPya2eRTAQAskMgV7NYNCxvLiXQ%3d%3d | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734254473&P2=404&P3=2&P4=gEUwj5vvThnaqiibwj%2foEc3UTPDf8o0rXU05POhZGahfBvWDRIGxlsLv07ViPya2eRTAQAskMgV7NYNCxvLiXQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
716 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6492 | msedge.exe | 142.250.185.131:443 | fonts.gstatic.com | — | — | whitelisted |
6492 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6492 | msedge.exe | 188.114.97.3:443 | www.crackingcity.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.crackingcity.com |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6492 | msedge.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |