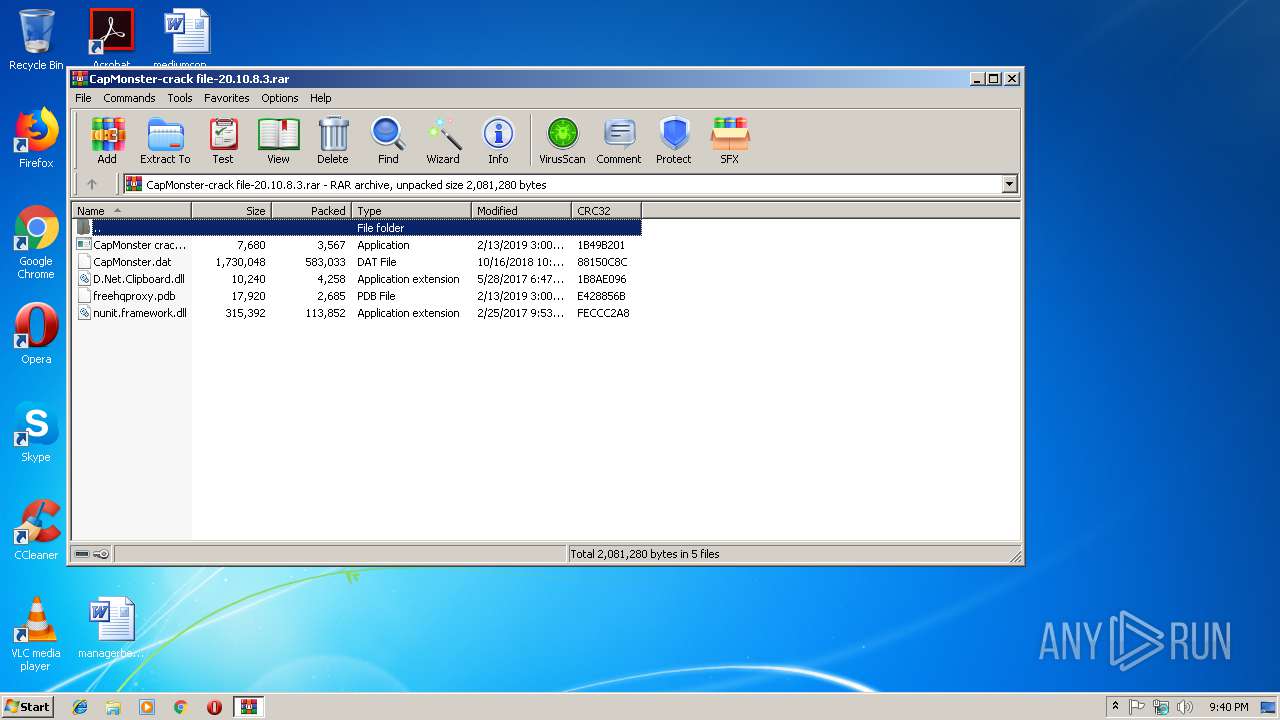
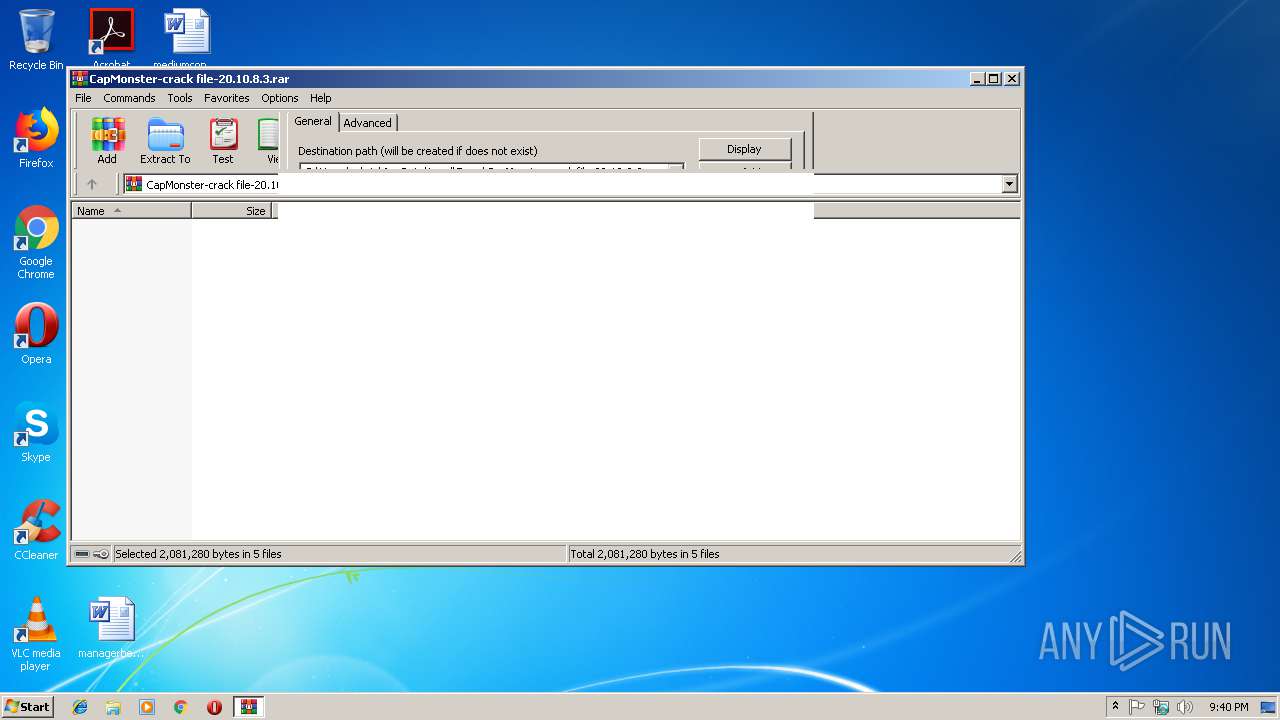
| File name: | CapMonster-crack file-20.10.8.3.rar |
| Full analysis: | https://app.any.run/tasks/d8de7558-60de-45ec-893d-49189b7c91ff |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2019, 21:40:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 980F9A46EC7EF9EDB591831D919C3EDF |
| SHA1: | F13AE1086692A58817AEA284E5CC038BB3C53FEC |
| SHA256: | D008A33646B04A16D1B31E6E06C3571C6F8382FEE4B39F5CAA3EEA622D322DDC |
| SSDEEP: | 12288:njV+iWLxzmECR/OdoBSObUSuuNBTg6psaWWSBY2GVQaPPscKidmrz:n92S7FOdAv3fsHsHMcKB |
MALICIOUS
Changes the autorun value in the registry
- CapMonster crack.exe (PID: 1912)
Loads dropped or rewritten executable
- CapMonster crack.exe (PID: 1912)
- CapMonster crack.exe (PID: 3652)
- CapMonster crack.exe (PID: 2724)
Application was dropped or rewritten from another process
- CapMonster crack.exe (PID: 1912)
- CapMonster crack.exe (PID: 3652)
- CapMonster crack.exe (PID: 2724)
SUSPICIOUS
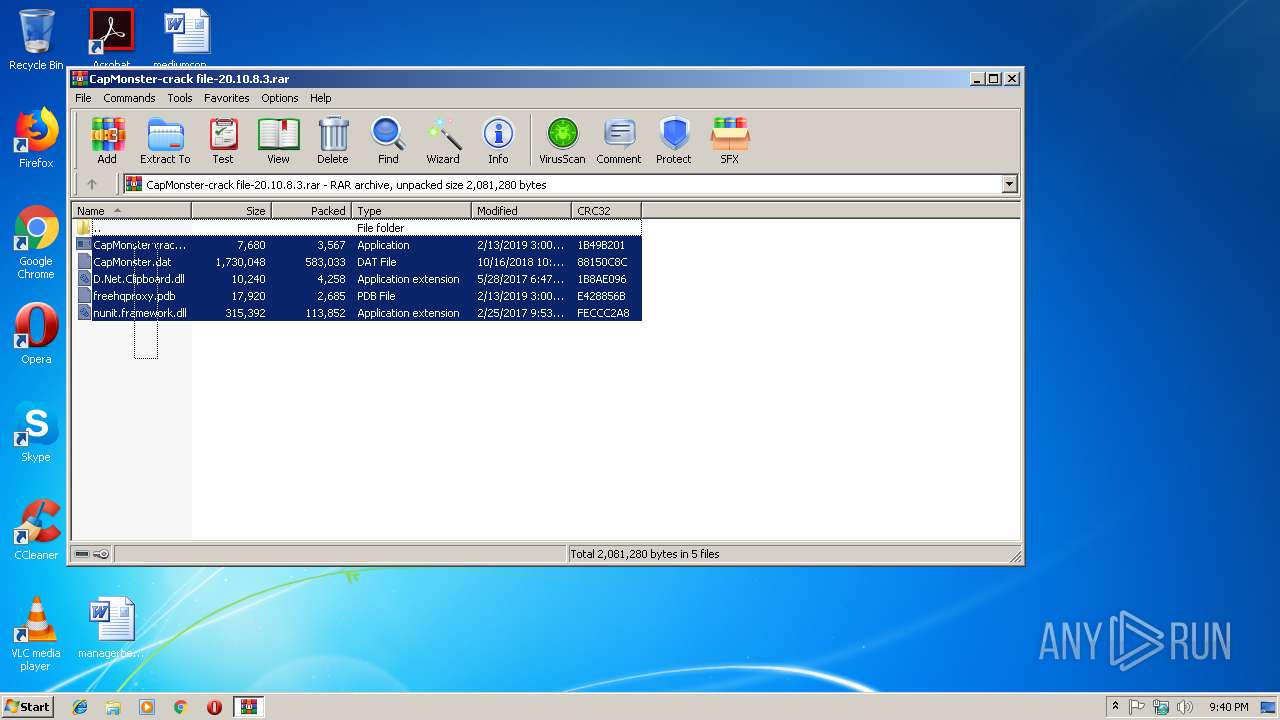
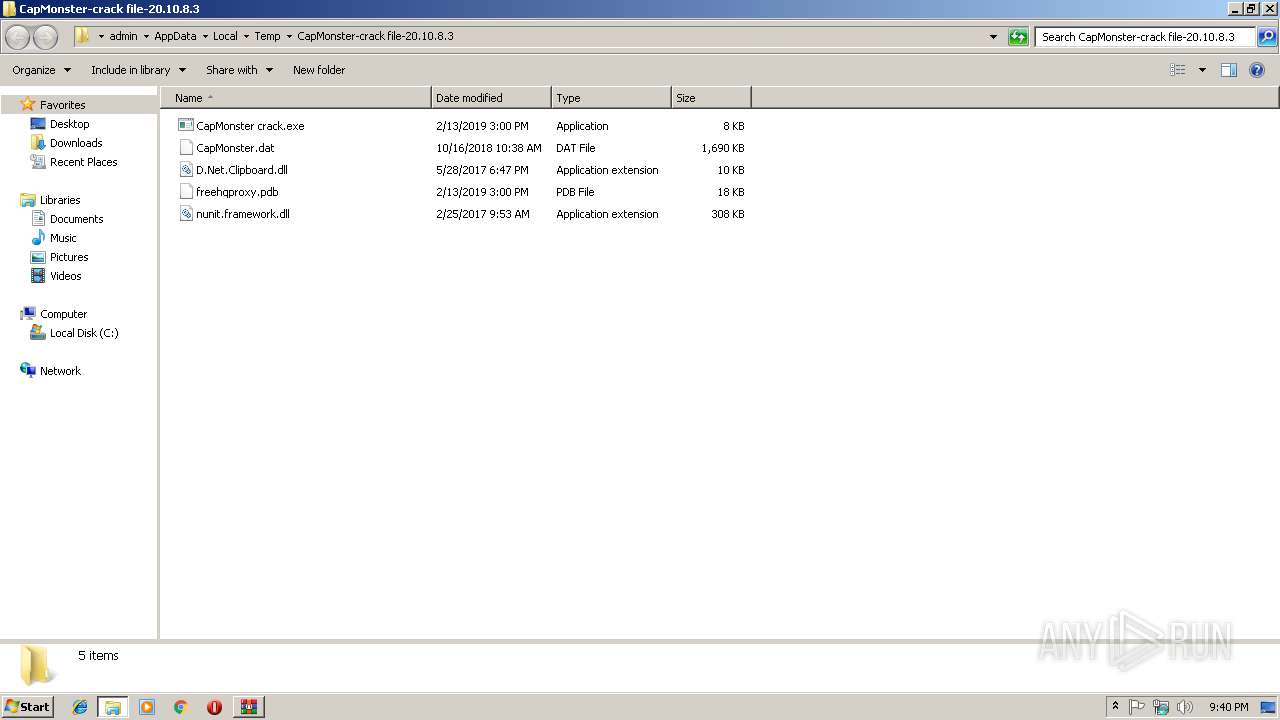
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2980)
Creates files in the user directory
- notepad++.exe (PID: 3636)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
37
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
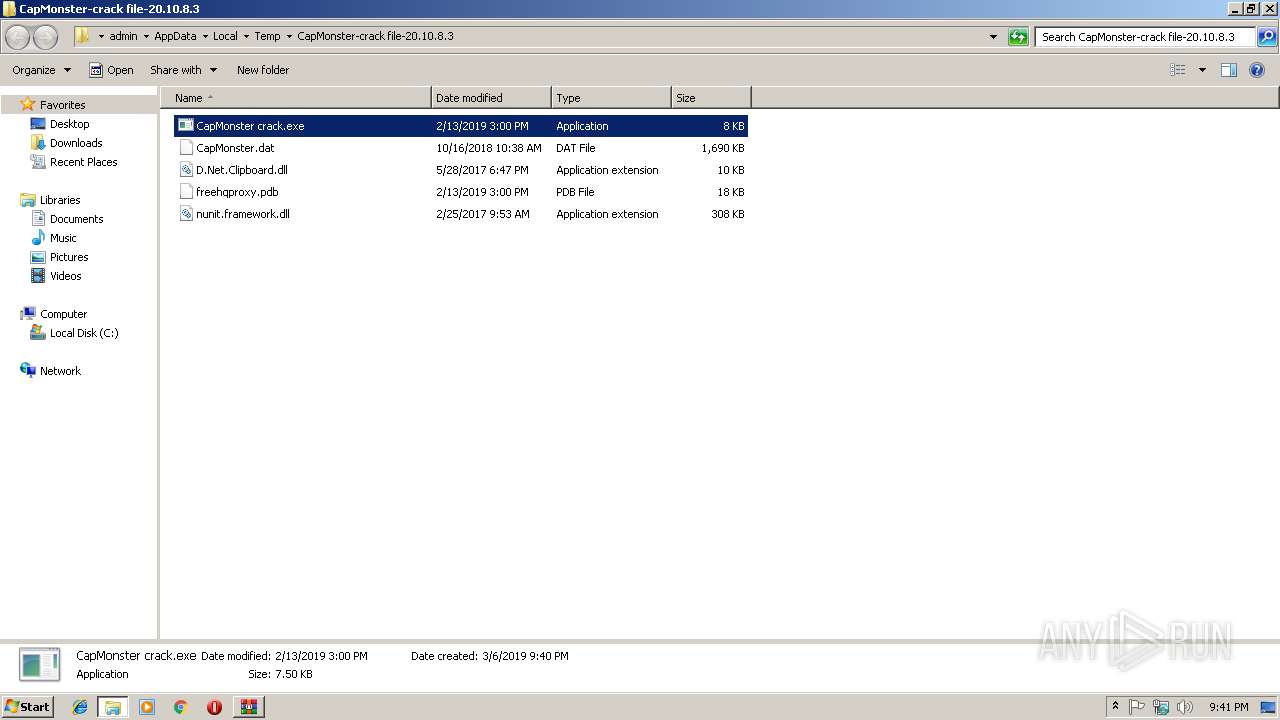
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
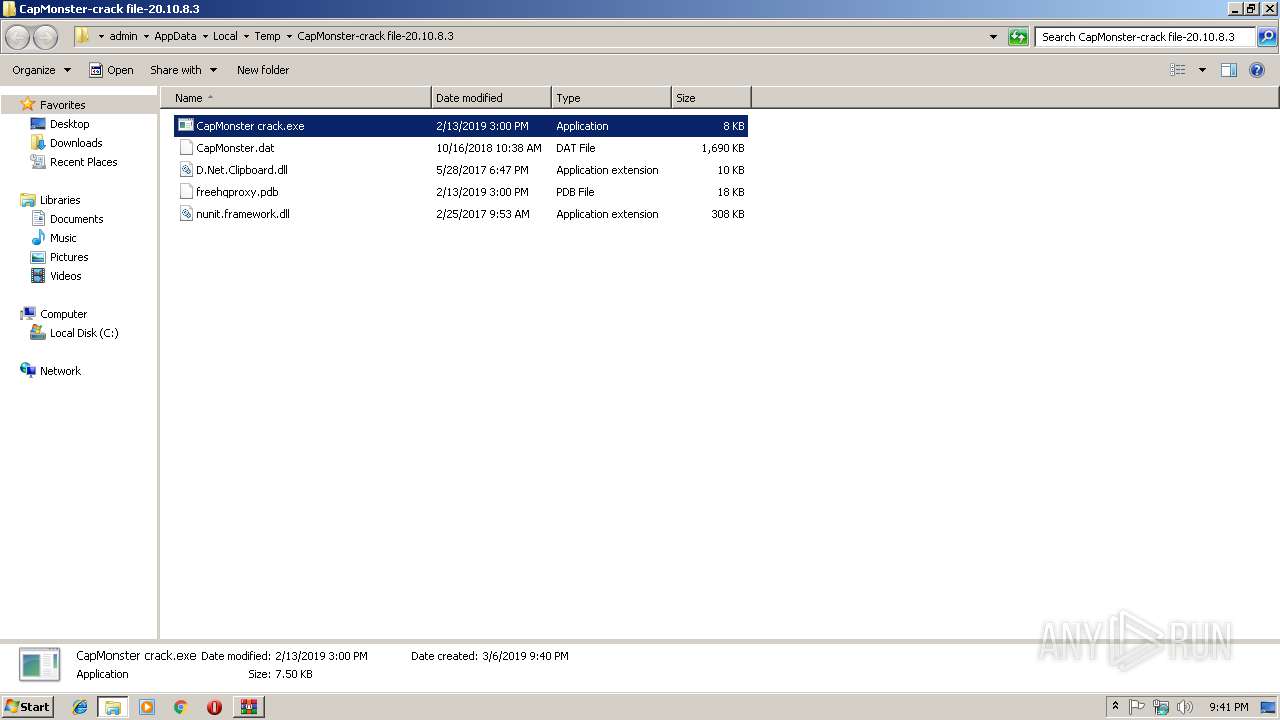
| 1912 | "C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster crack.exe" | C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster crack.exe" | C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster crack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
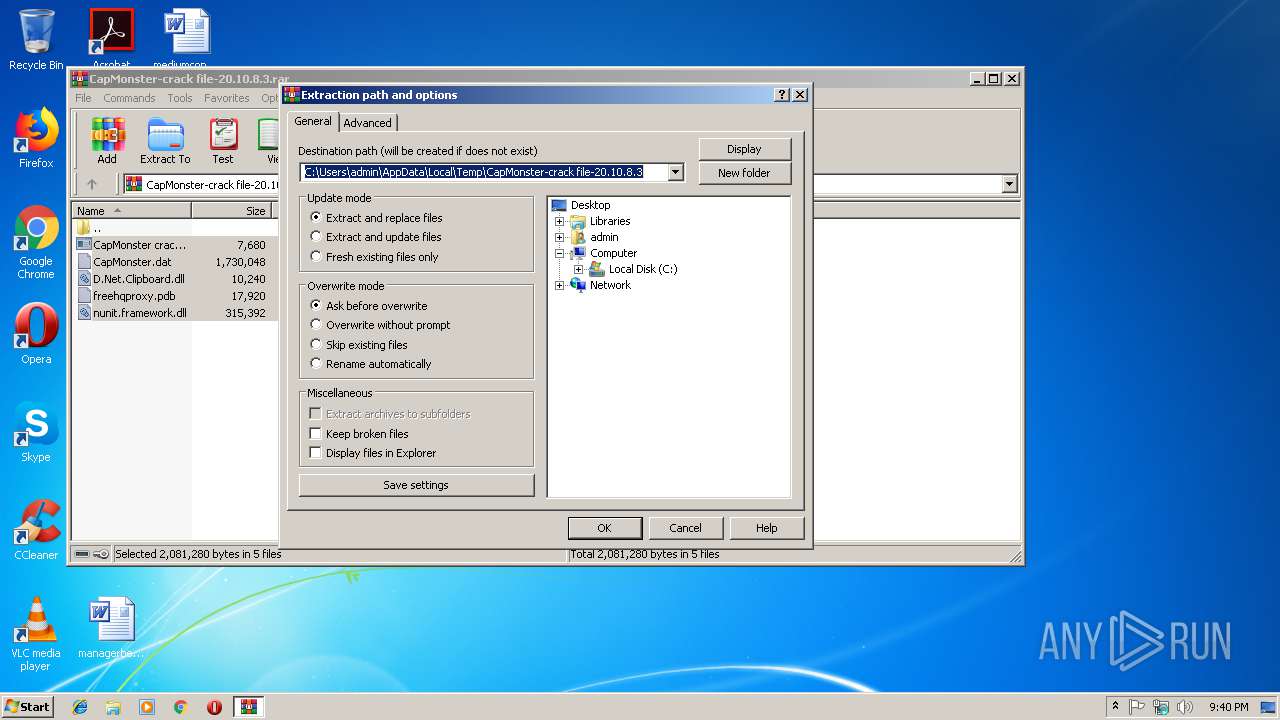
| 2980 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
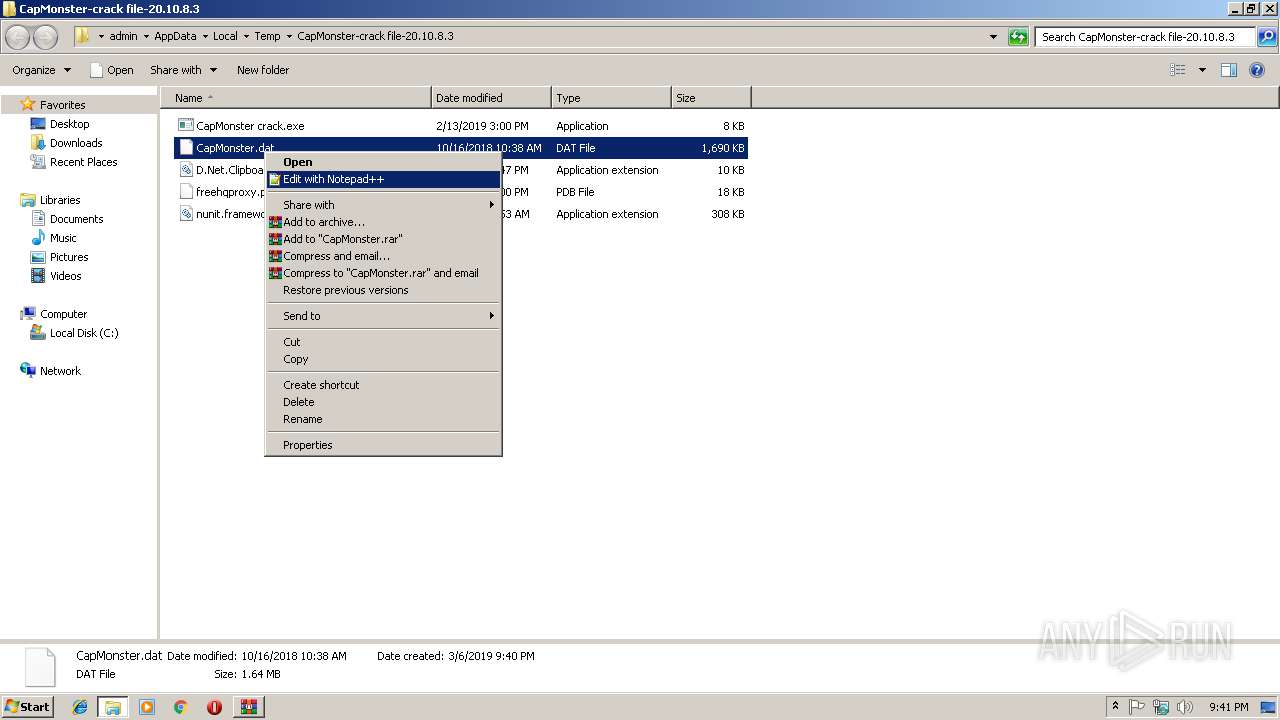
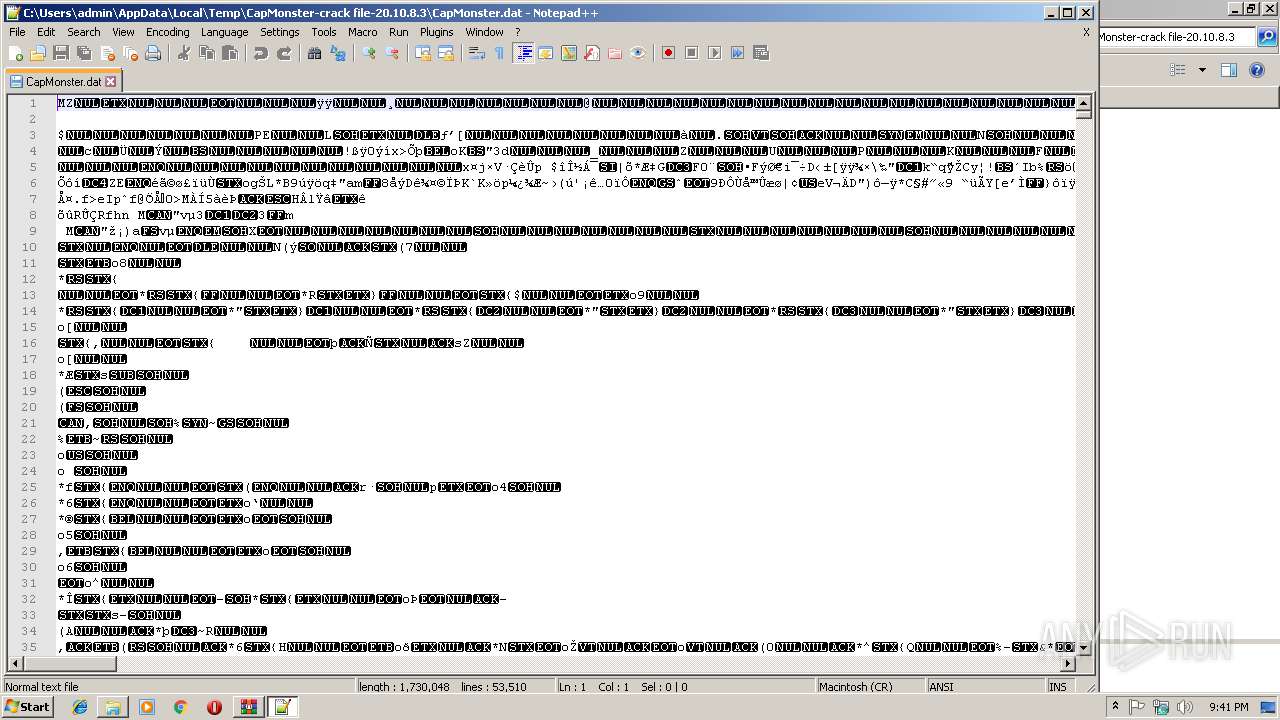
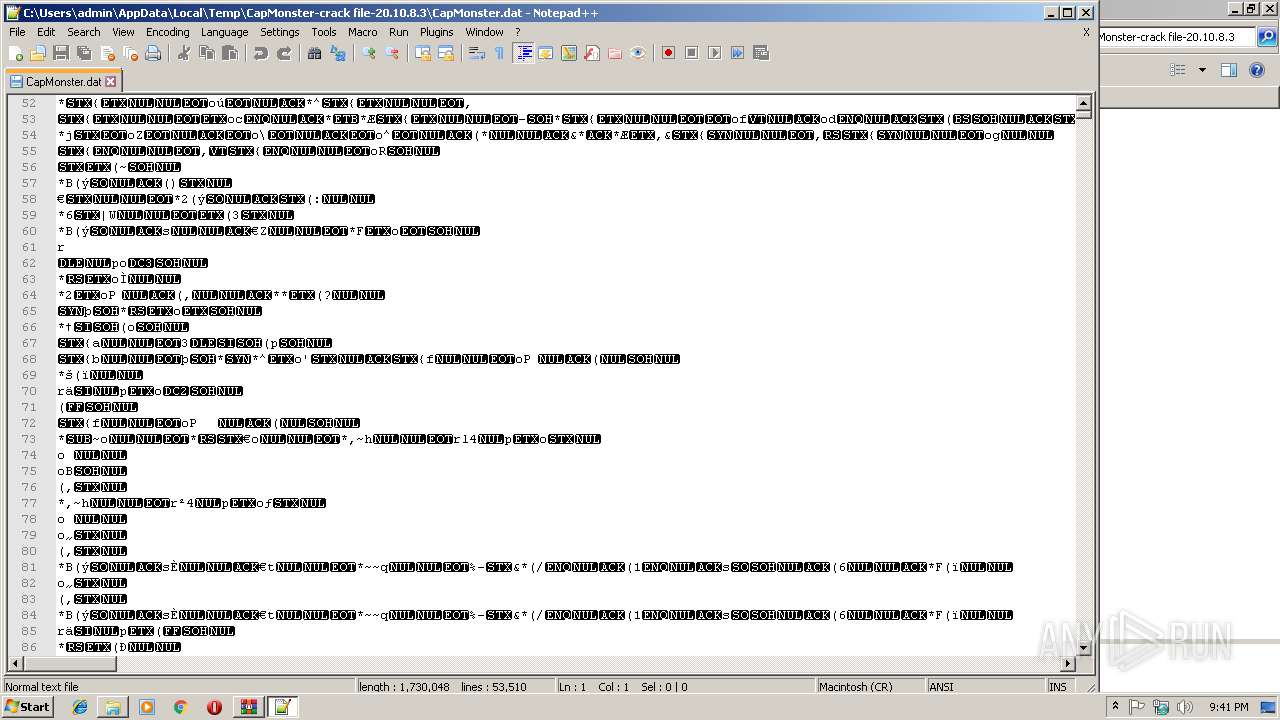
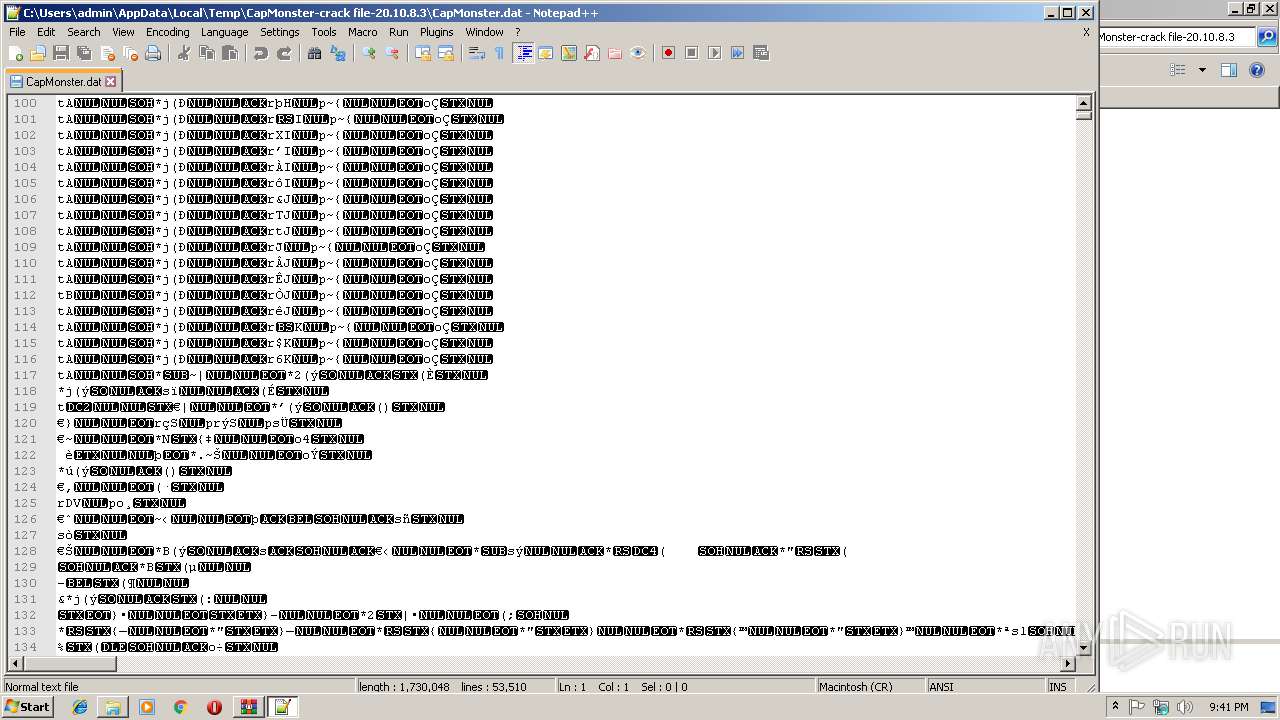
| 3636 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster.dat" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster crack.exe" | C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster crack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
520
Read events
473
Write events
47
Delete events
0
Modification events
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3.rar | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Extraction\Profile |
| Operation: | write | Name: | Overwrite |
Value: 0 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Extraction\Profile |
| Operation: | write | Name: | Update |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
6
Unknown types
1
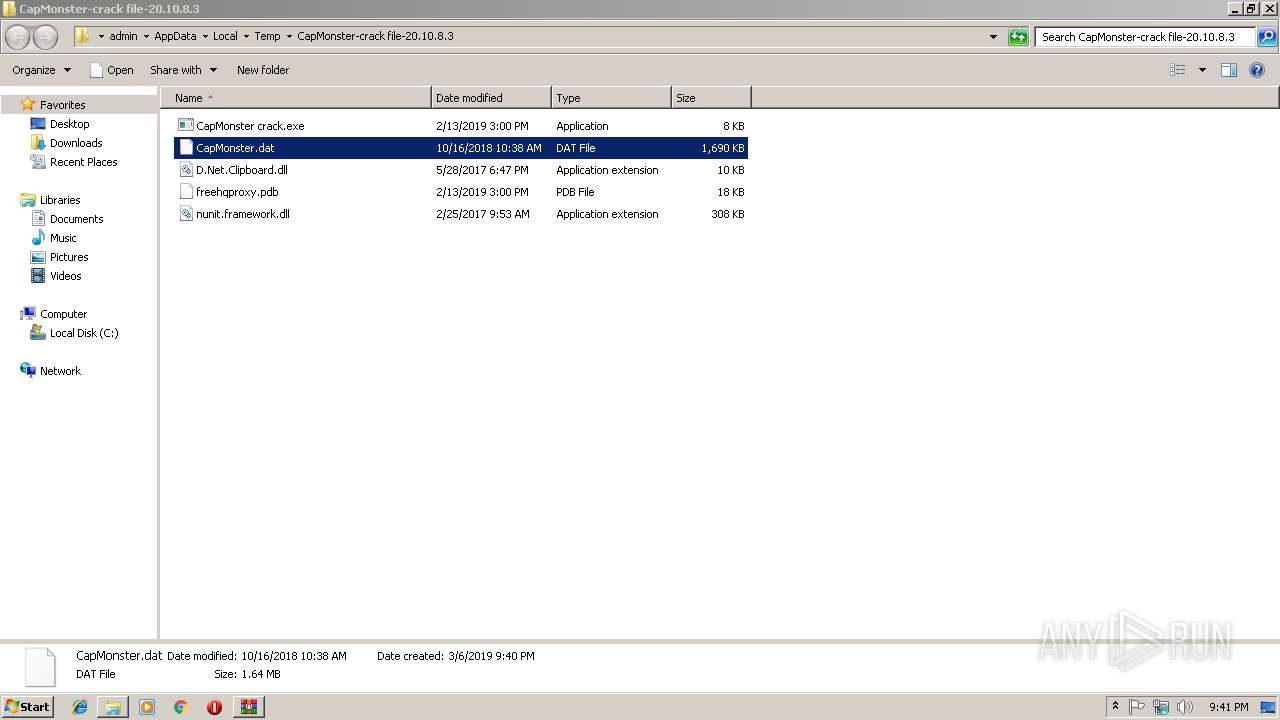
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3636 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 3636 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 2980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\CapMonster.dat | executable | |
MD5:7AAF3C14E1FD4829269B67B5AC26C9BC | SHA256:2AC25AC1D658D7A2F44609445B988E67F5623F061B5C549A2D93AC7B204F8AF9 | |||
| 3636 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:44982E1D48434C0AB3E8277E322DD1E4 | SHA256:3E661D3F1FF3977B022A0ACC26B840B5E57D600BC03DCFC6BEFDB408C665904C | |||
| 3636 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 2980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\D.Net.Clipboard.dll | executable | |
MD5:F9EE03E8A24E30B1934EFFBFA0CAA831 | SHA256:B2797F1EE18DA029E14C1FB0A7BEB59E14F3DA054859CF7C64DBE73C6E4FAA45 | |||
| 2980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\nunit.framework.dll | executable | |
MD5:36CE7E3DAB60DB5A585DA34B04D1286B | SHA256:017044C6137FF4DA5CD672CF633DA42BDB6C0558CB473E71D9F75B591F003420 | |||
| 3636 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:AD21A64014891793DD9B21D835278F36 | SHA256:C24699C9D00ABDD510140FE1B2ACE97BFC70D8B21BF3462DED85AFC4F73FE52F | |||
| 3636 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 2980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\CapMonster-crack file-20.10.8.3\freehqproxy.pdb | pdb | |
MD5:B8C8DB5A1CA1A639290CF229E135D9E7 | SHA256:FF538DDC20C7BC577DBB2A62353C441AD591EC27A817757B97C8991475F158FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.106.80:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | unknown | der | 727 b | whitelisted |
— | — | GET | 200 | 2.16.106.80:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | unknown | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2876 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.16.106.80:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|