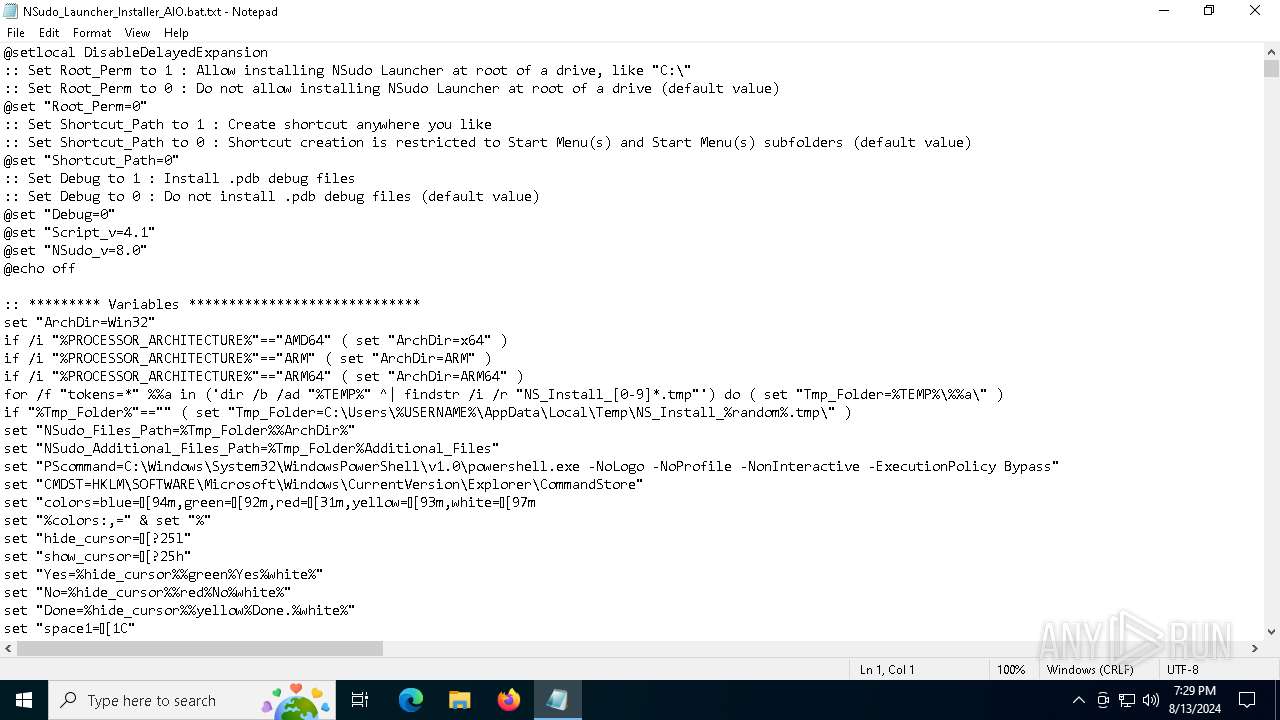
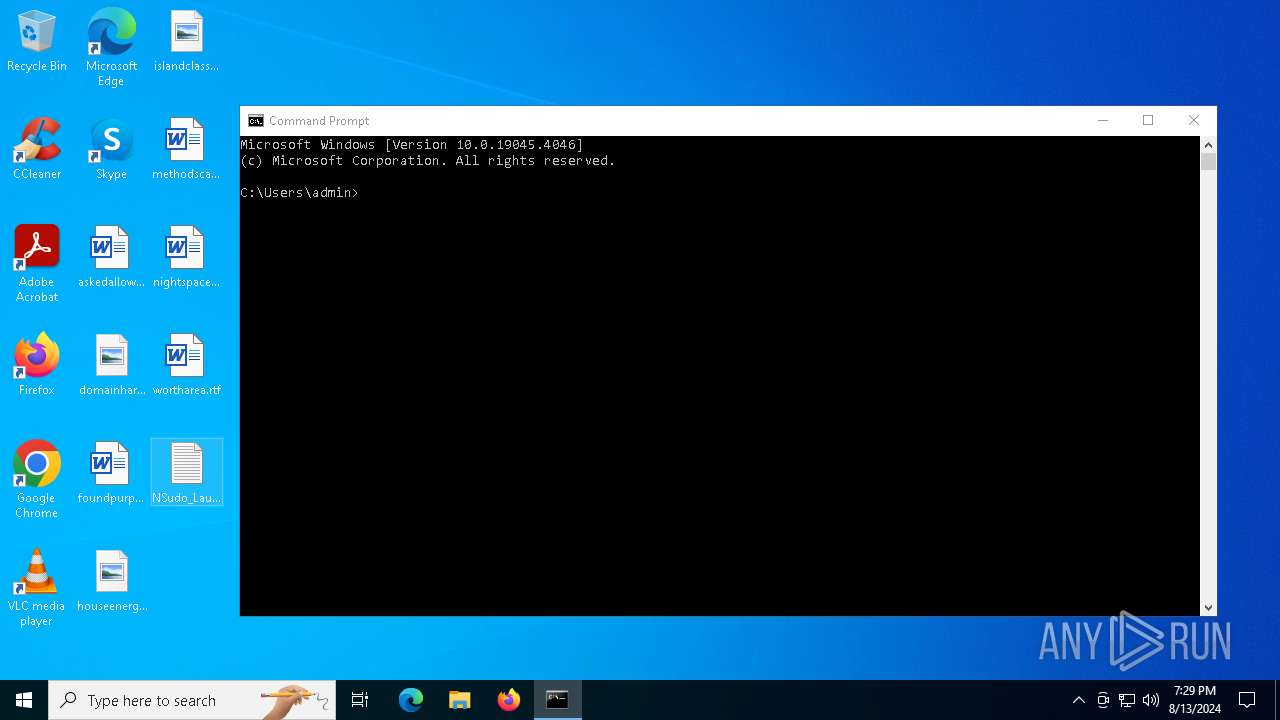
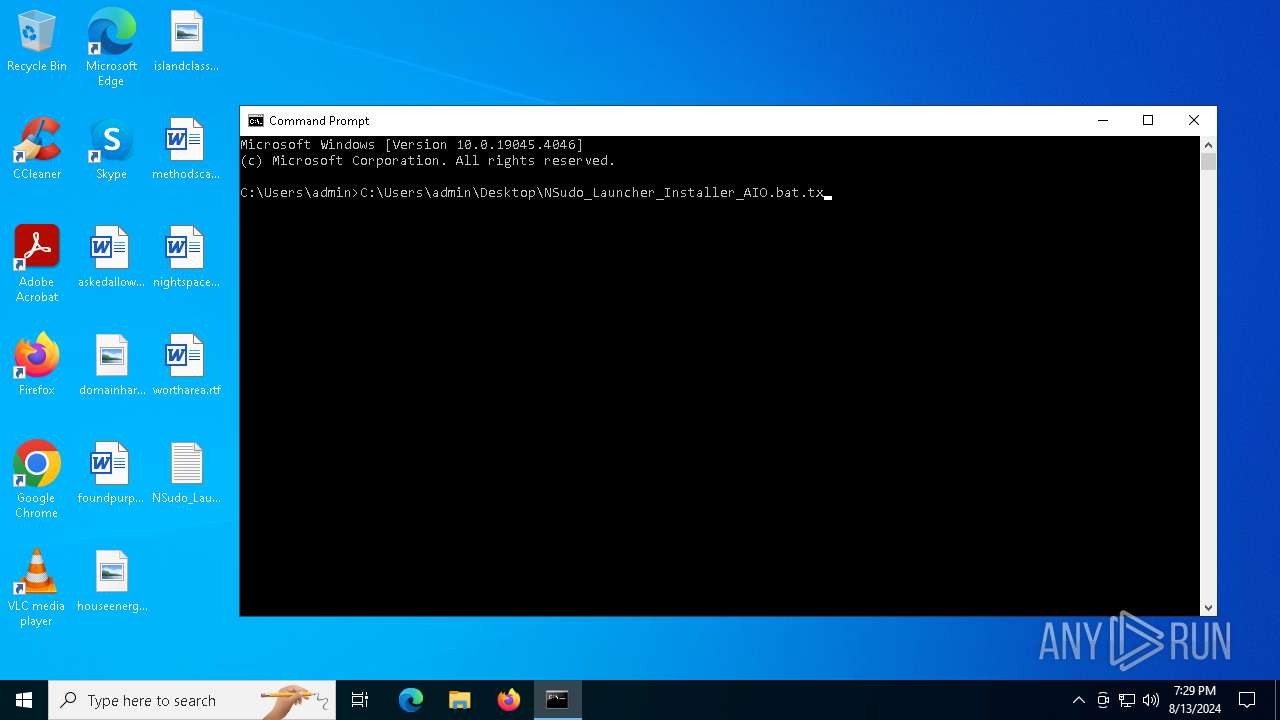
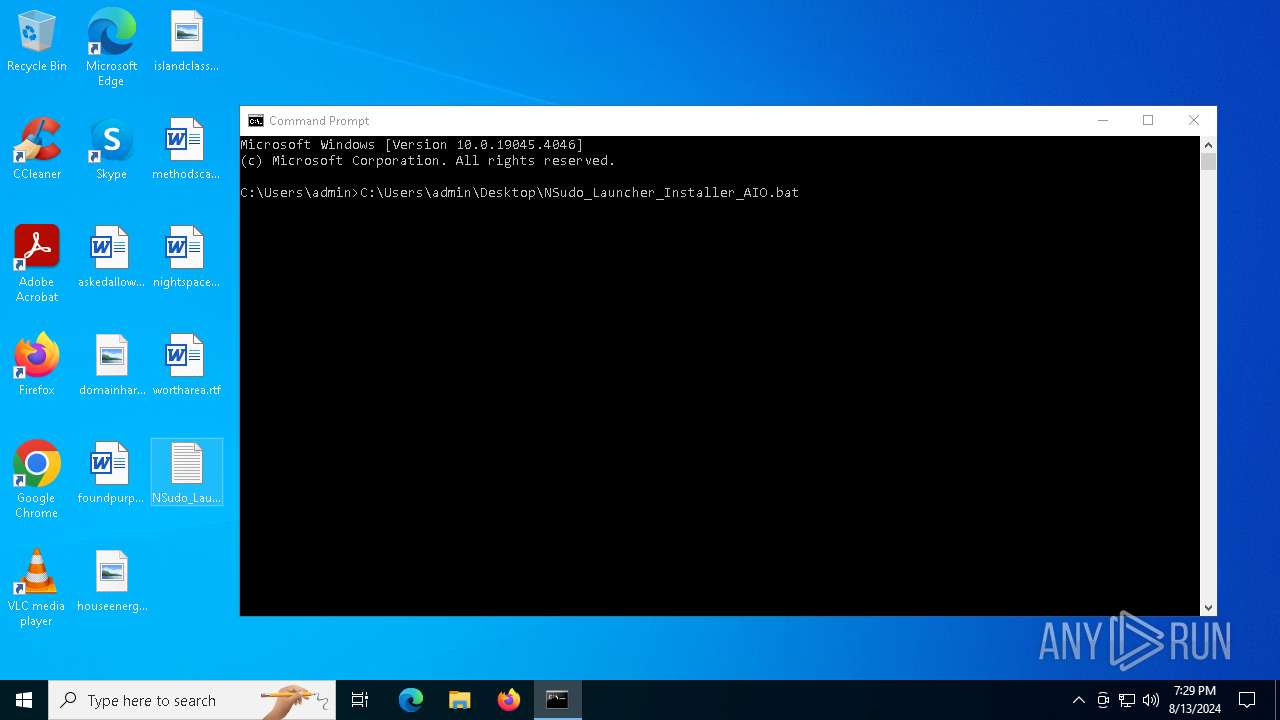
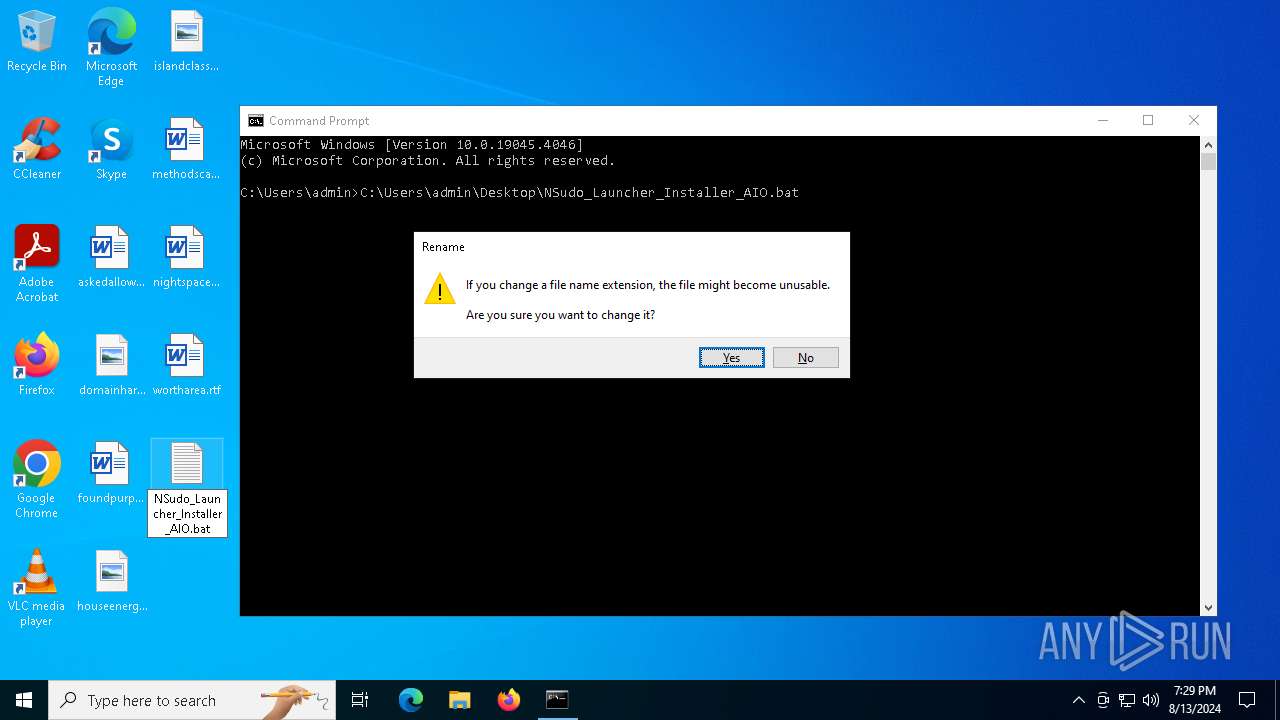
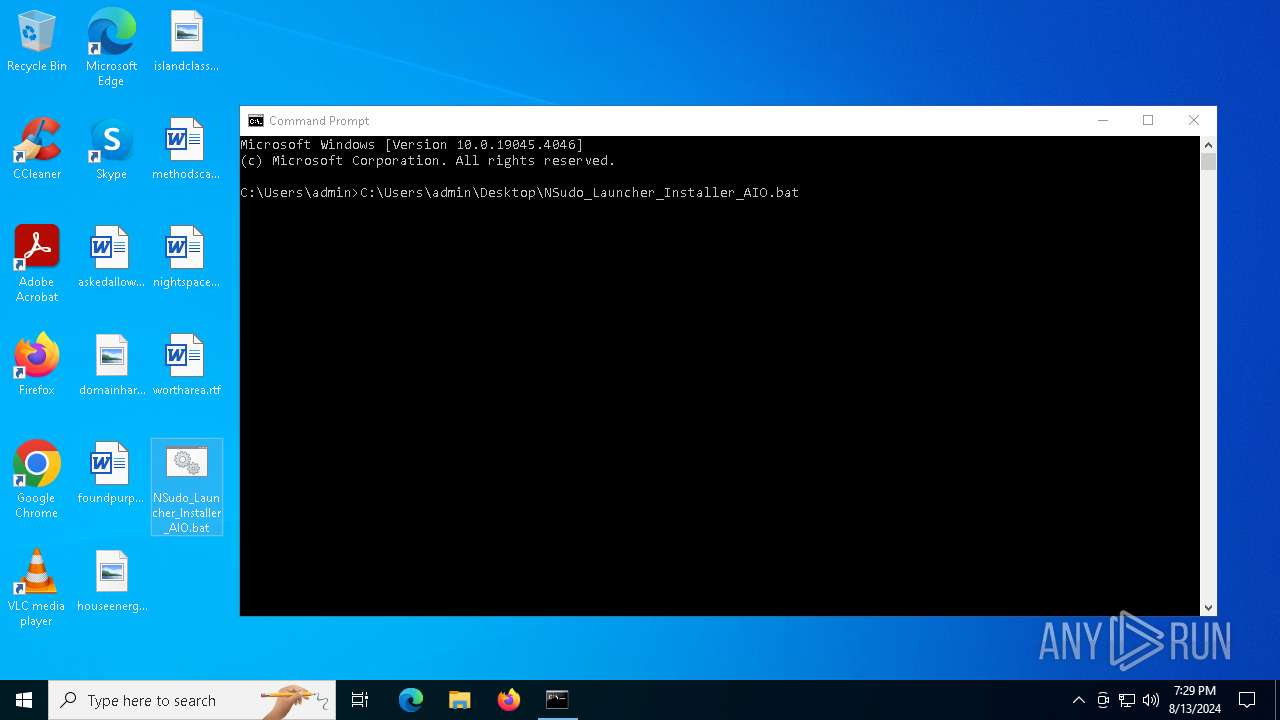
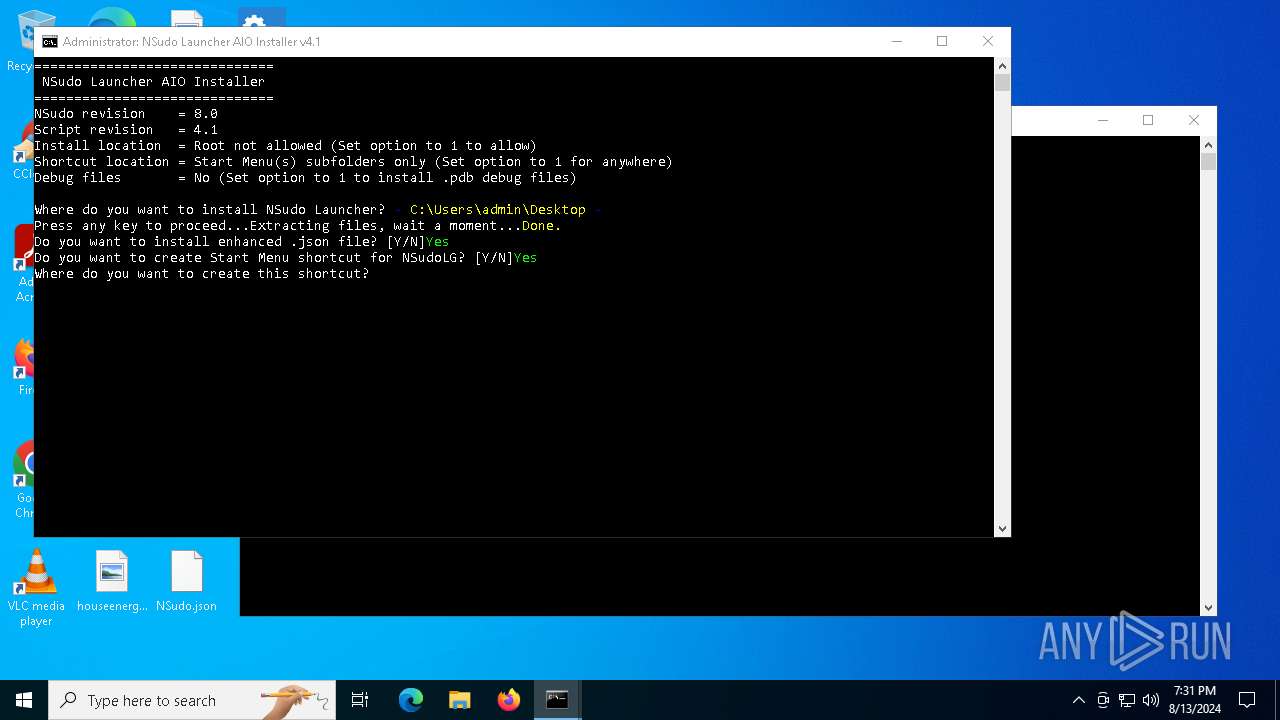
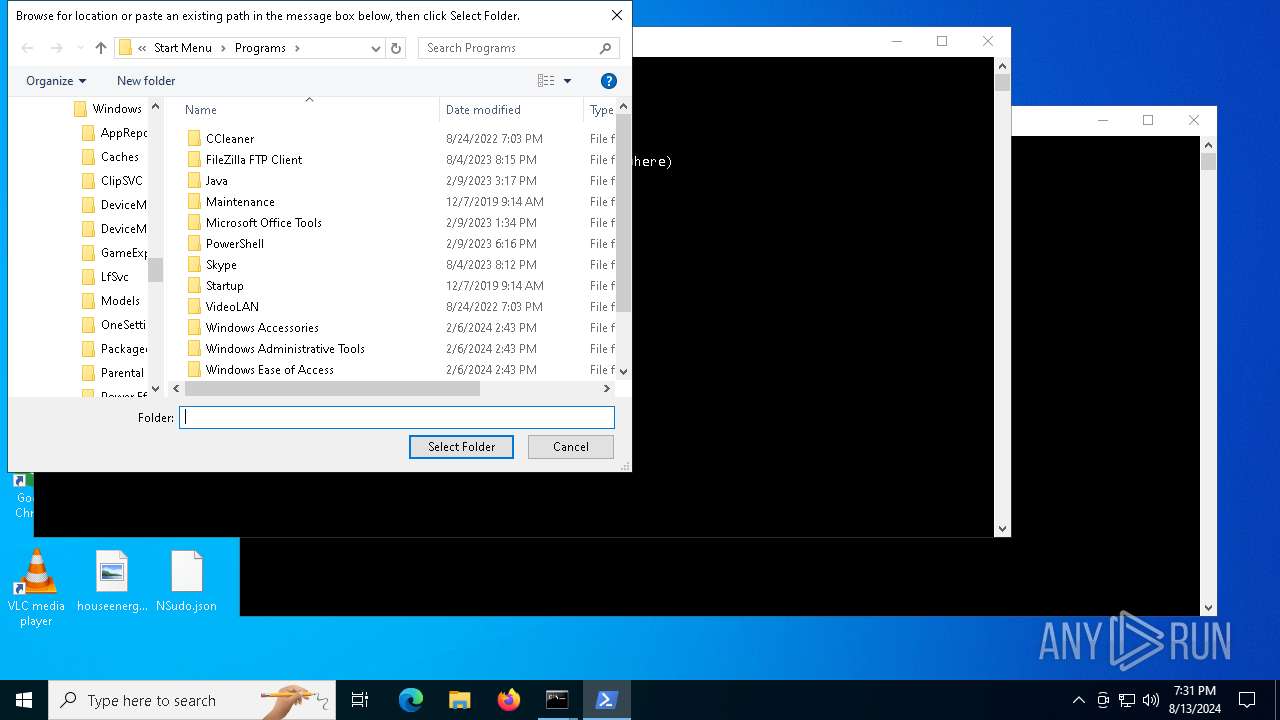
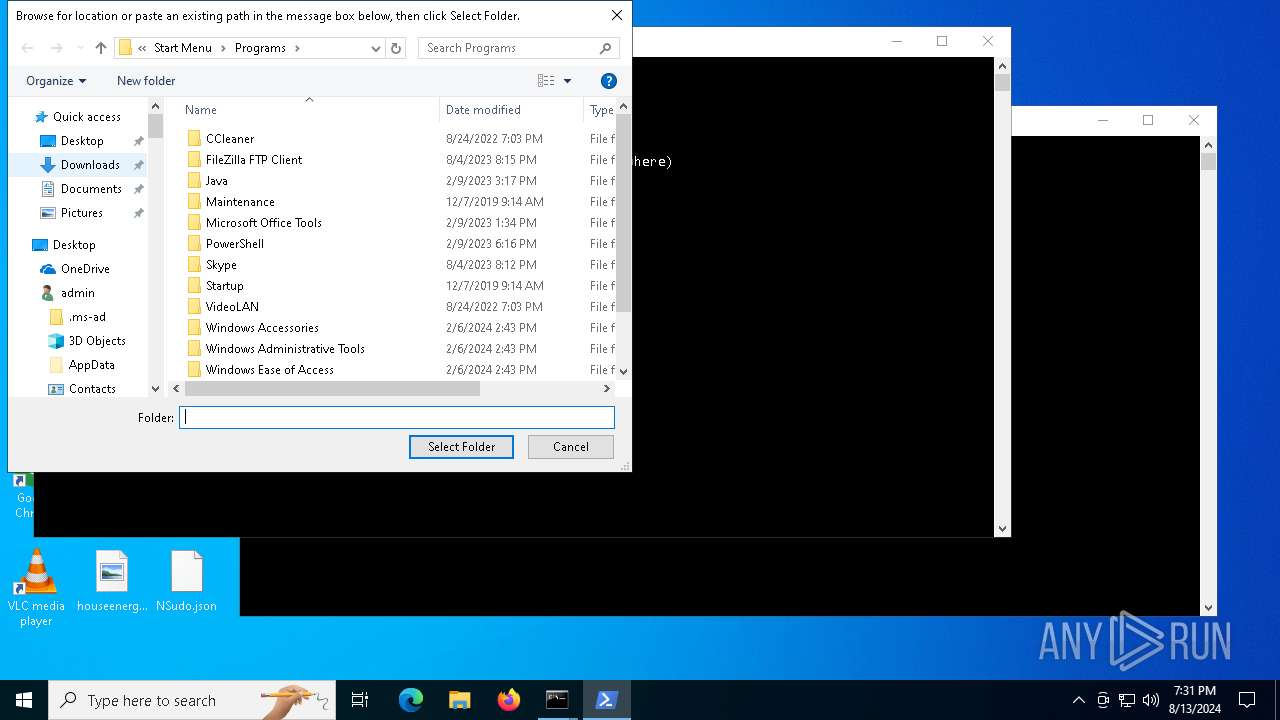
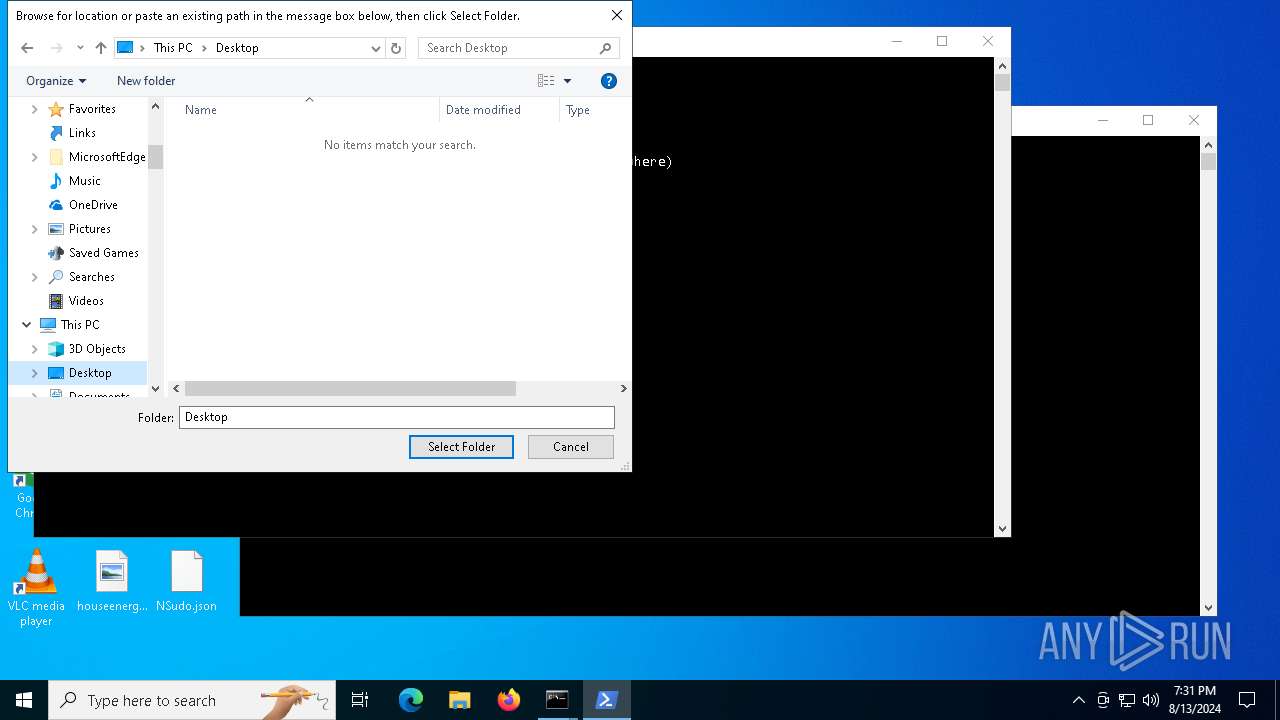
| File name: | NSudo_Launcher_Installer_AIO.bat |
| Full analysis: | https://app.any.run/tasks/bb78bd60-35f1-45f0-81d8-199a36317460 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2024, 19:29:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (527), with CRLF line terminators, with escape sequences |
| MD5: | FD6D98200EC732D81BA9D3D061CF1AA1 |
| SHA1: | 1E646411BCEC962CE9FEE2BF36B16DAC822C8F07 |
| SHA256: | D007171D3D29FF0153DA7DFF82A9203AAC410A9FF86EDEE5B18E90C5077DD82A |
| SSDEEP: | 98304:qQWgoEfytoQNoxkRB01EXT/sDV/zMtroKnd9g3w:qioZyQN4kRCwT/azM1V9Uw |
MALICIOUS
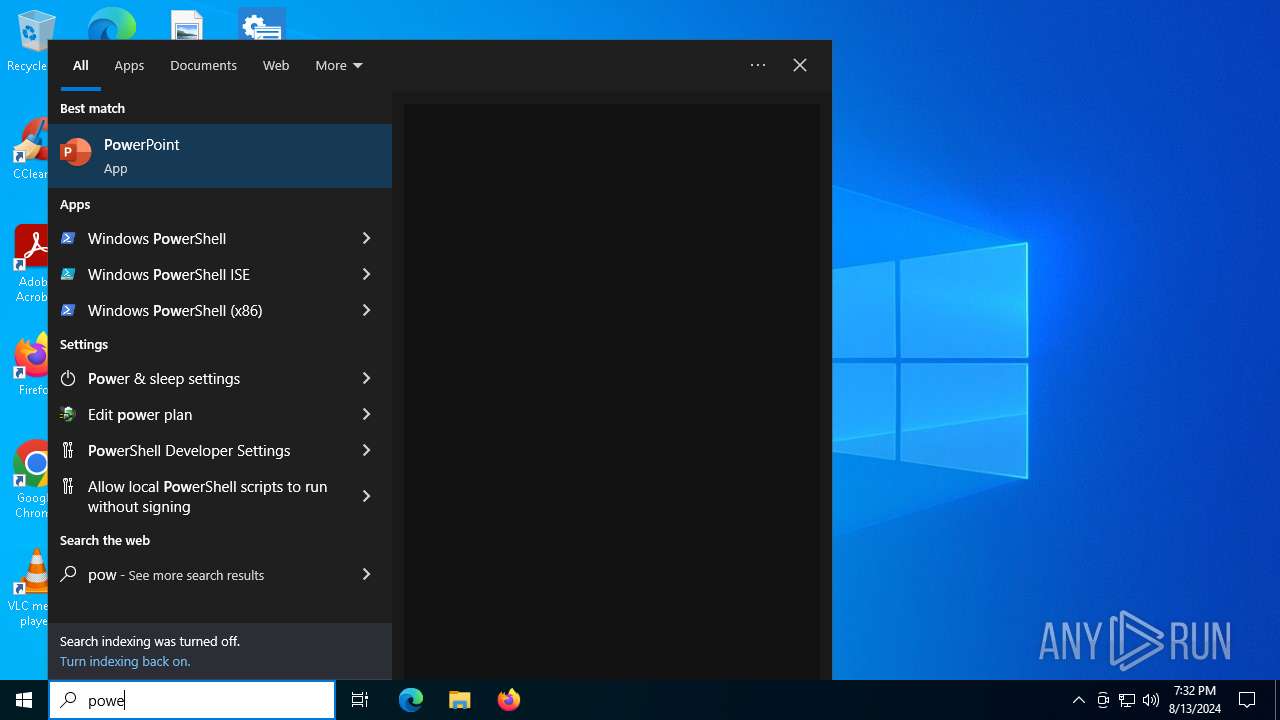
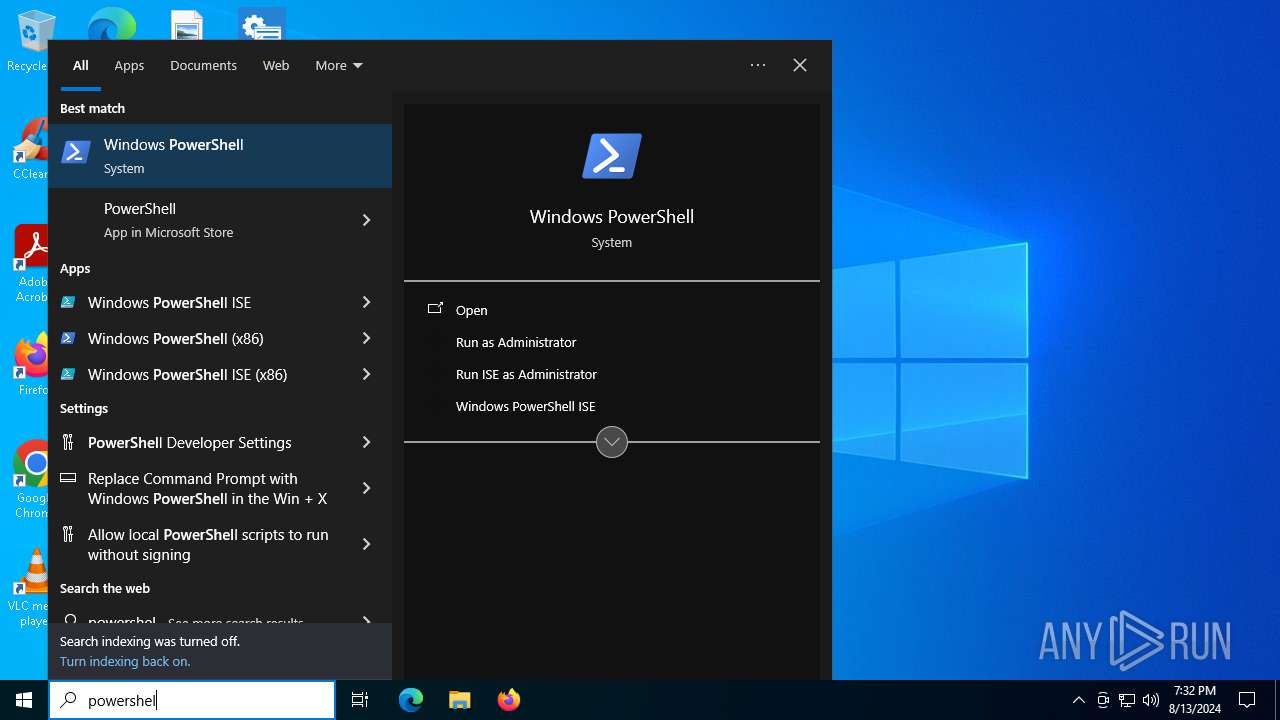
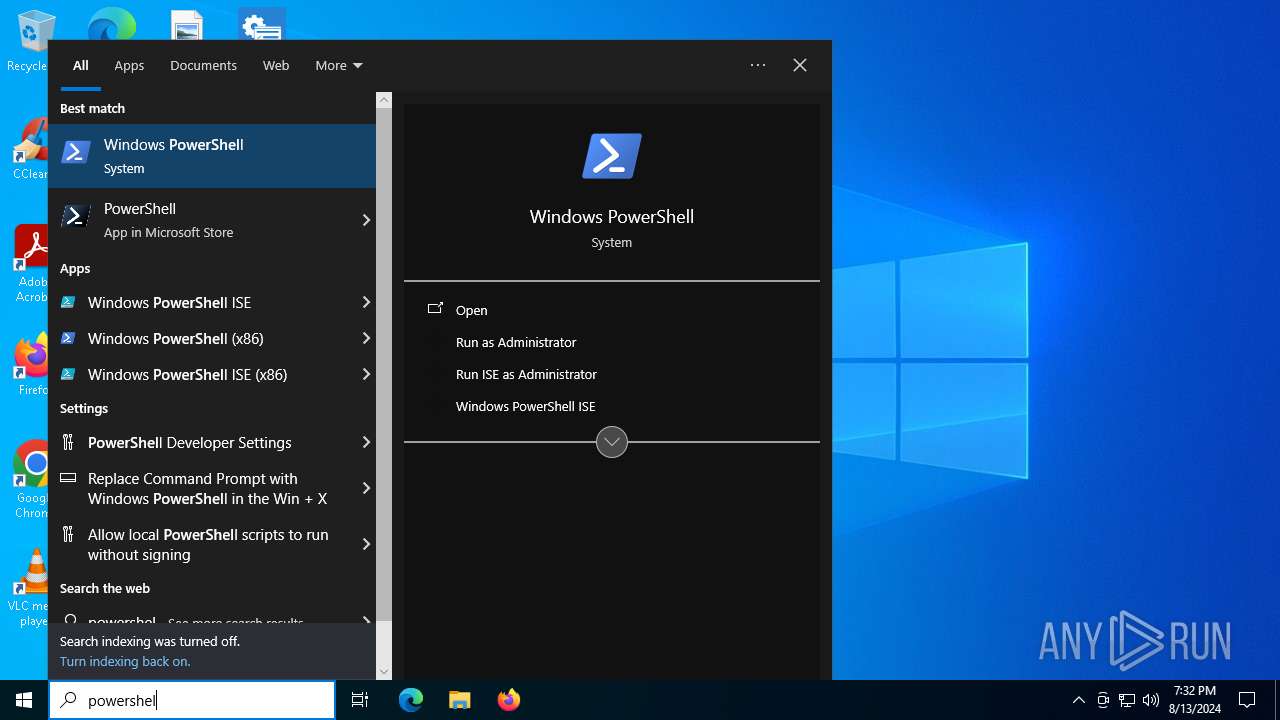
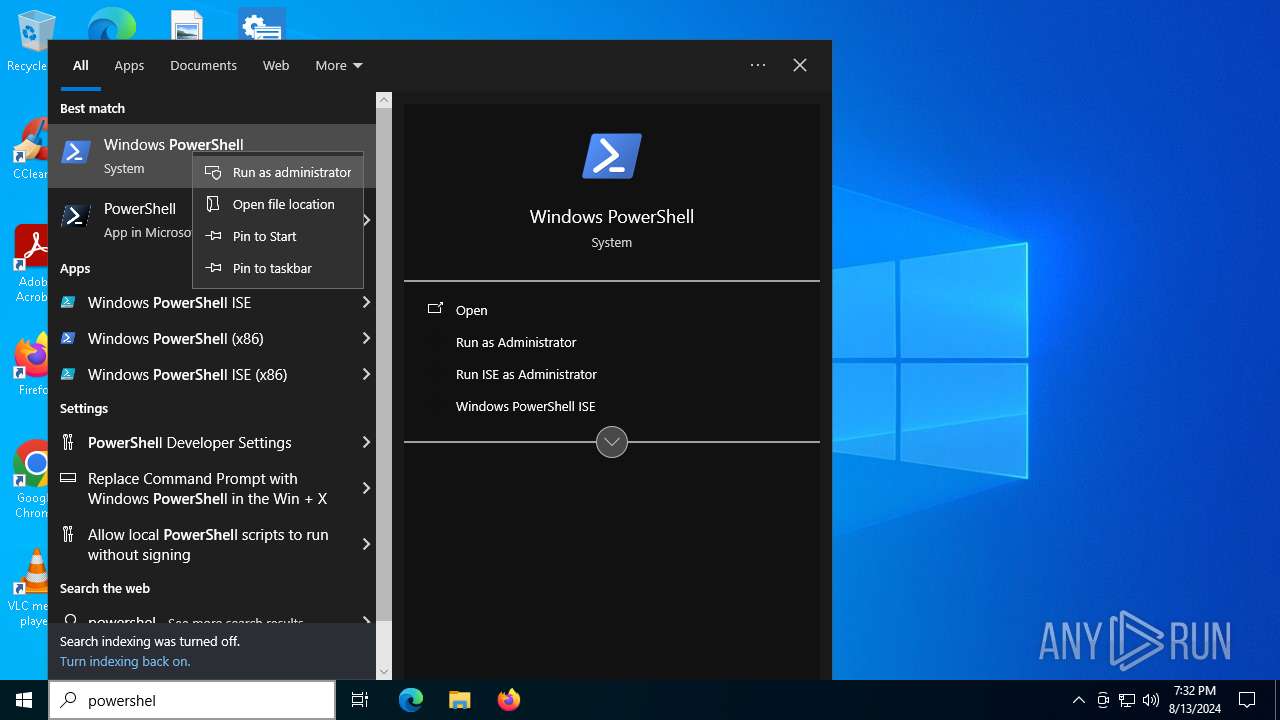
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7056)
Bypass execution policy to execute commands
- powershell.exe (PID: 7528)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7888)
- powershell.exe (PID: 5880)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 7860)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7056)
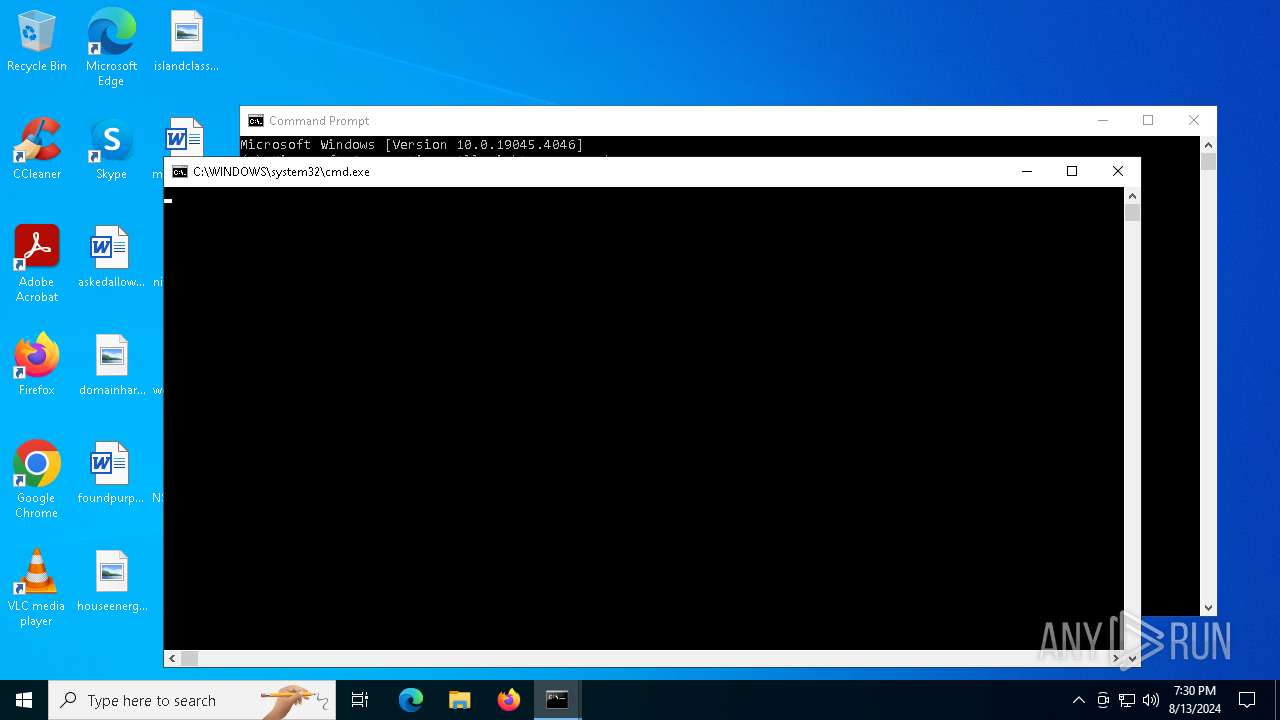
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7860)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7056)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7056)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 7028)
- cscript.exe (PID: 4160)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 7028)
- cscript.exe (PID: 4160)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 4160)
- cscript.exe (PID: 7028)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7056)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7056)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 7028)
- cscript.exe (PID: 4160)
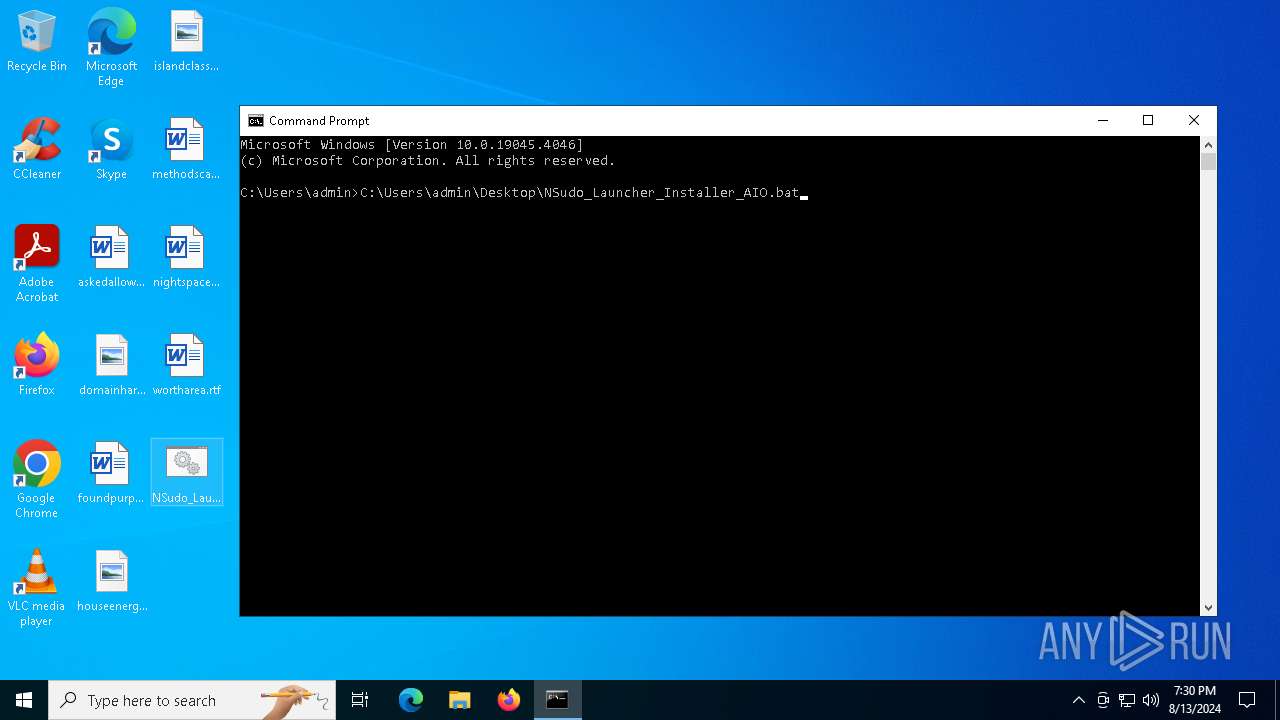
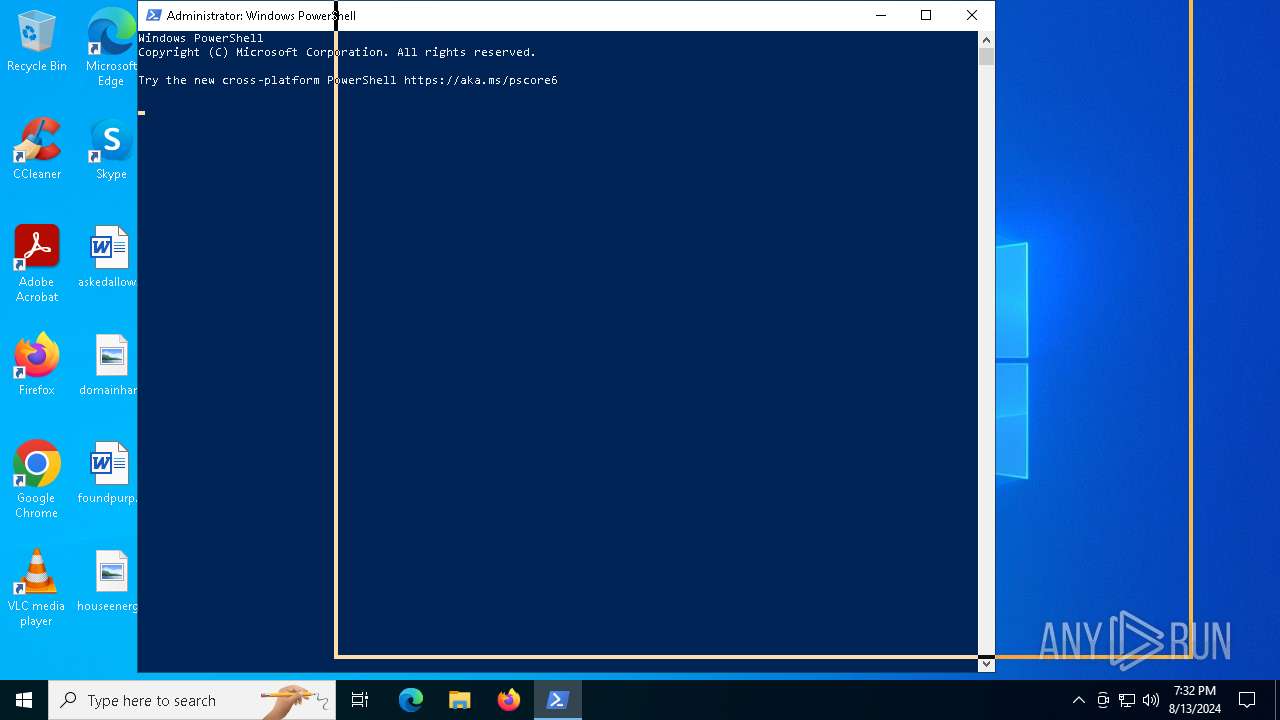
The process hide an interactive prompt from the user
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7056)
Unpacks CAB file
- expand.exe (PID: 7116)
- expand.exe (PID: 6568)
- expand.exe (PID: 6532)
The process executes Powershell scripts
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7748)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7056)
Executable content was dropped or overwritten
- csc.exe (PID: 1288)
- expand.exe (PID: 6568)
- Robocopy.exe (PID: 6544)
- csc.exe (PID: 7948)
Drops the executable file immediately after the start
- csc.exe (PID: 1288)
- expand.exe (PID: 6568)
- csc.exe (PID: 7948)
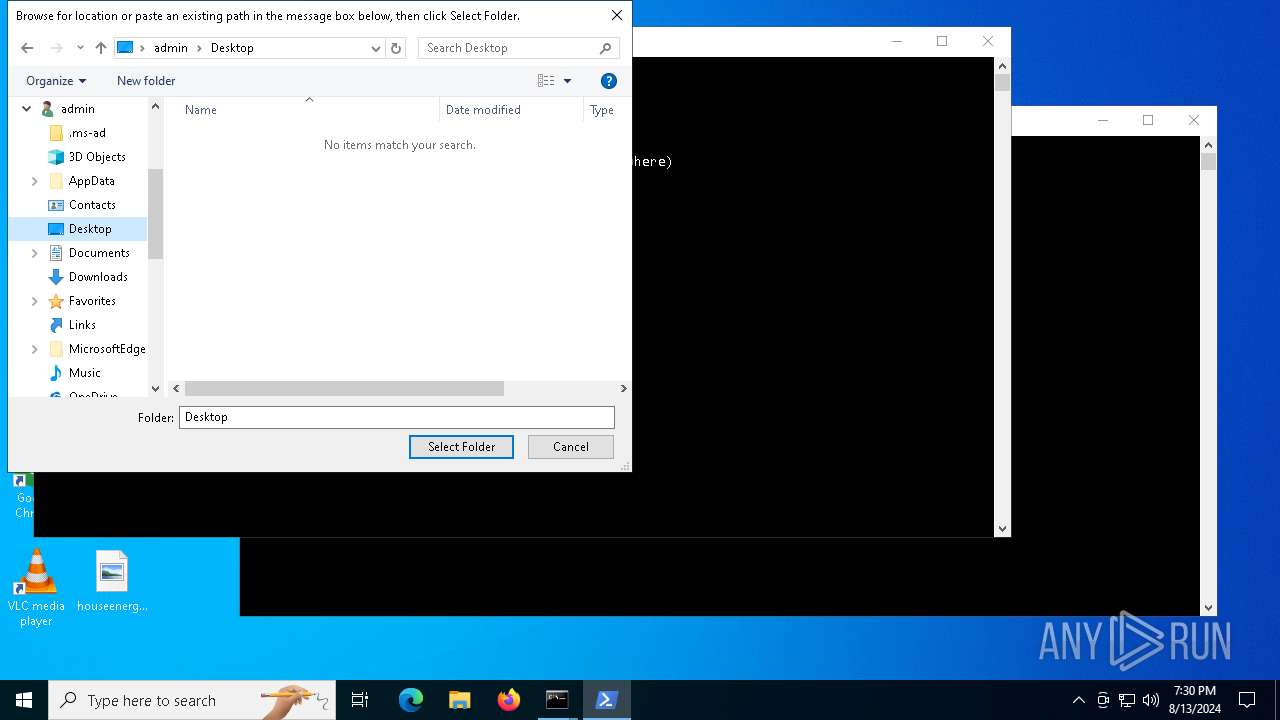
Creates file in the systems drive root
- powershell.exe (PID: 7756)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7888)
Searches for installed software
- reg.exe (PID: 6152)
- reg.exe (PID: 6992)
- reg.exe (PID: 5240)
- reg.exe (PID: 3648)
- reg.exe (PID: 7704)
- reg.exe (PID: 4644)
- reg.exe (PID: 4084)
- reg.exe (PID: 7184)
- reg.exe (PID: 6432)
- reg.exe (PID: 1116)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7056)
Hides command output
- cmd.exe (PID: 7508)
- reg.exe (PID: 6432)
Creates a software uninstall entry
- reg.exe (PID: 6152)
- reg.exe (PID: 6992)
- reg.exe (PID: 5240)
- reg.exe (PID: 7704)
- reg.exe (PID: 3648)
- reg.exe (PID: 4644)
- reg.exe (PID: 7184)
- reg.exe (PID: 4084)
- reg.exe (PID: 6432)
- reg.exe (PID: 1116)
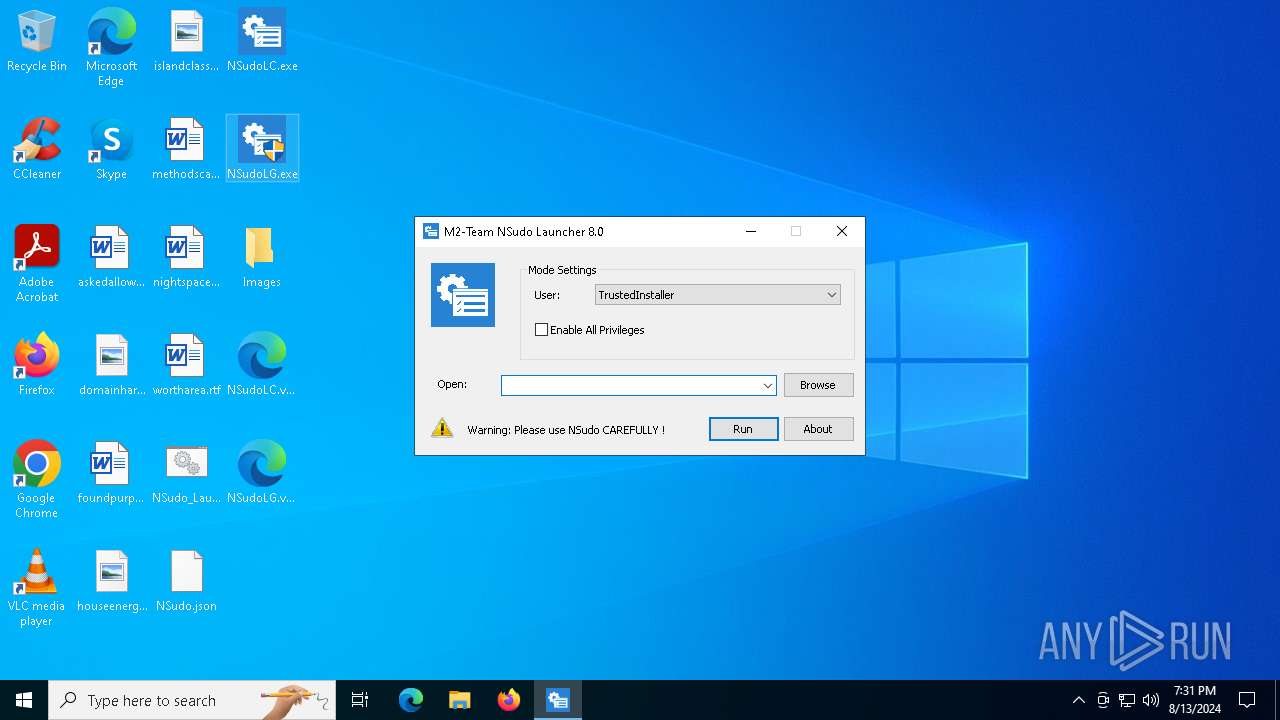
Reads security settings of Internet Explorer
- NSudoLG.exe (PID: 6200)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 6612)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 7028)
- cscript.exe (PID: 4160)
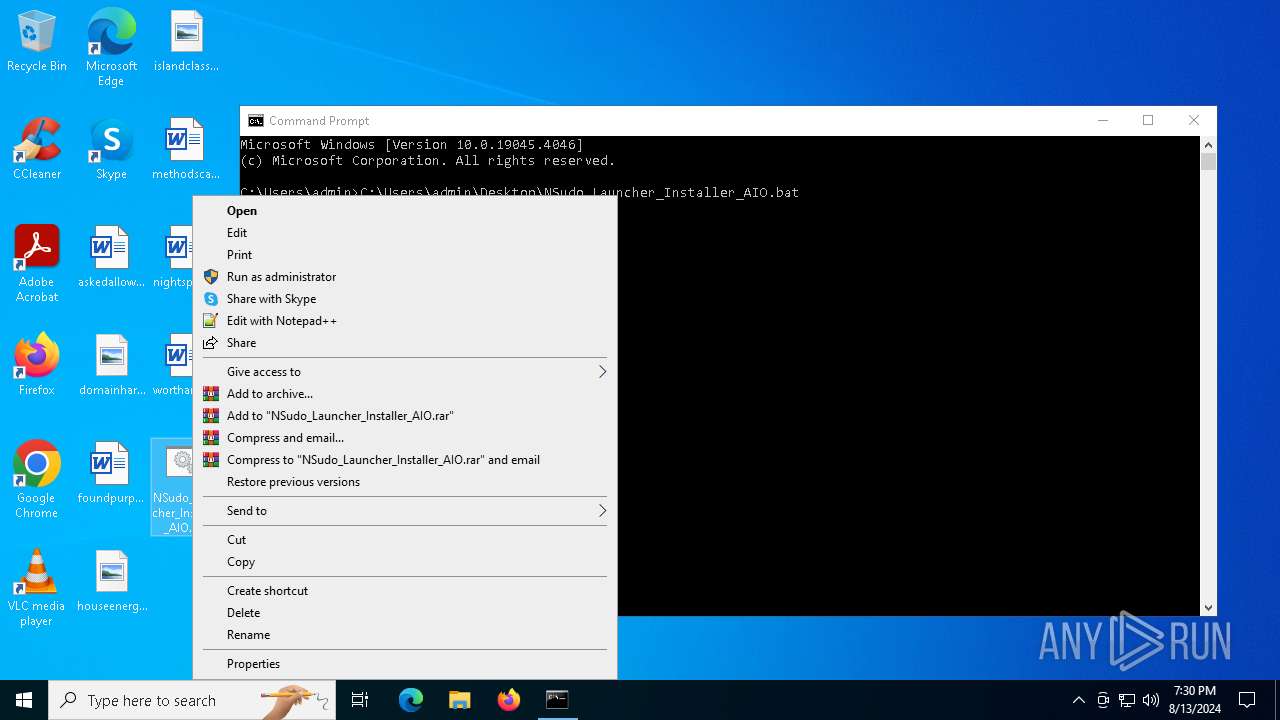
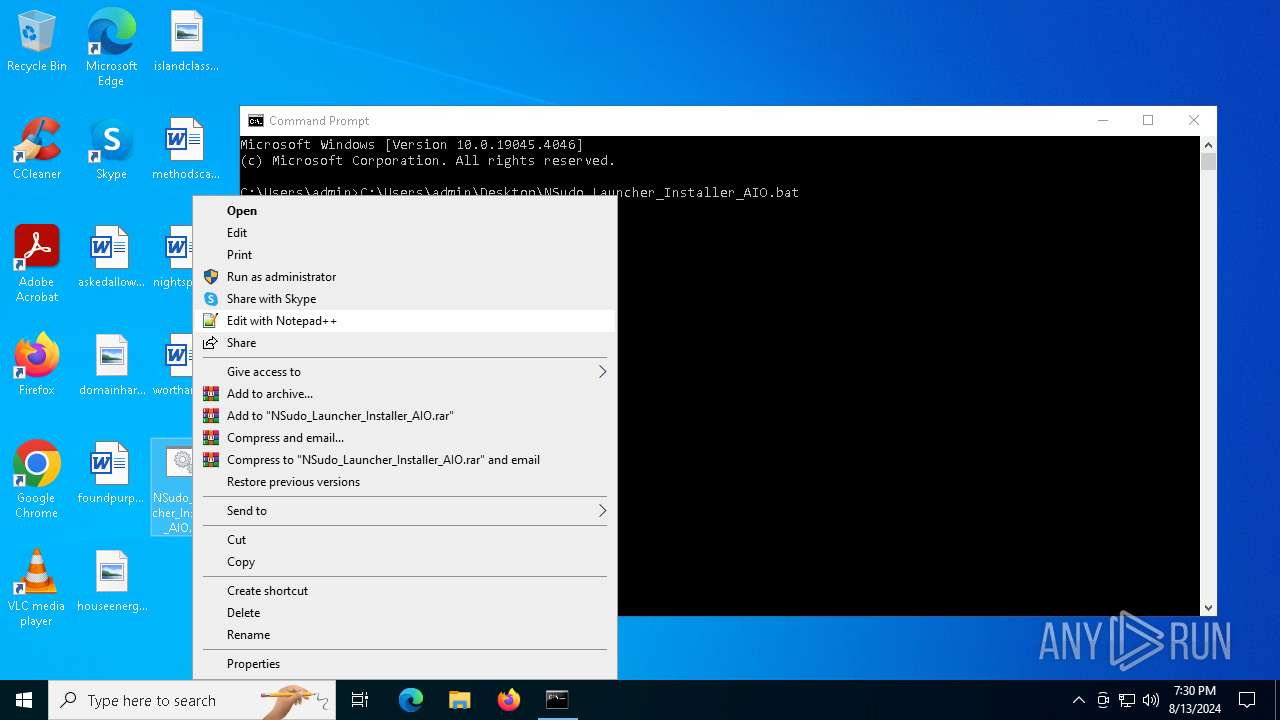
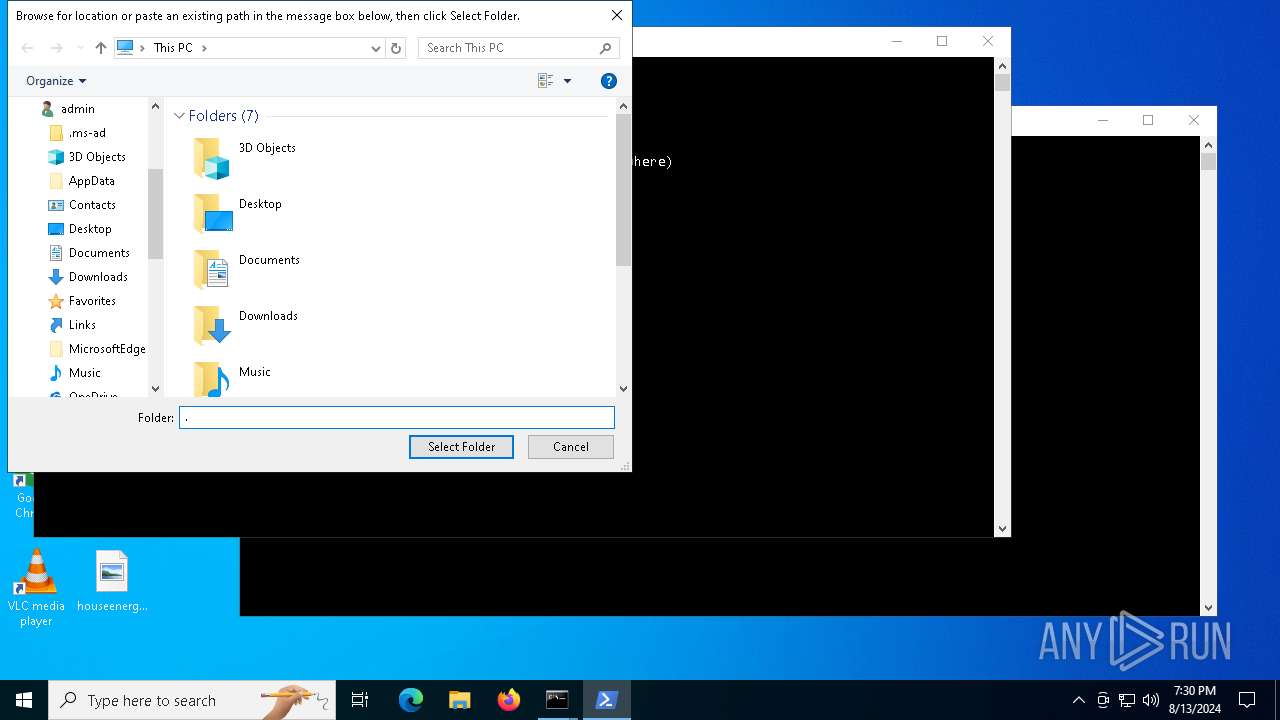
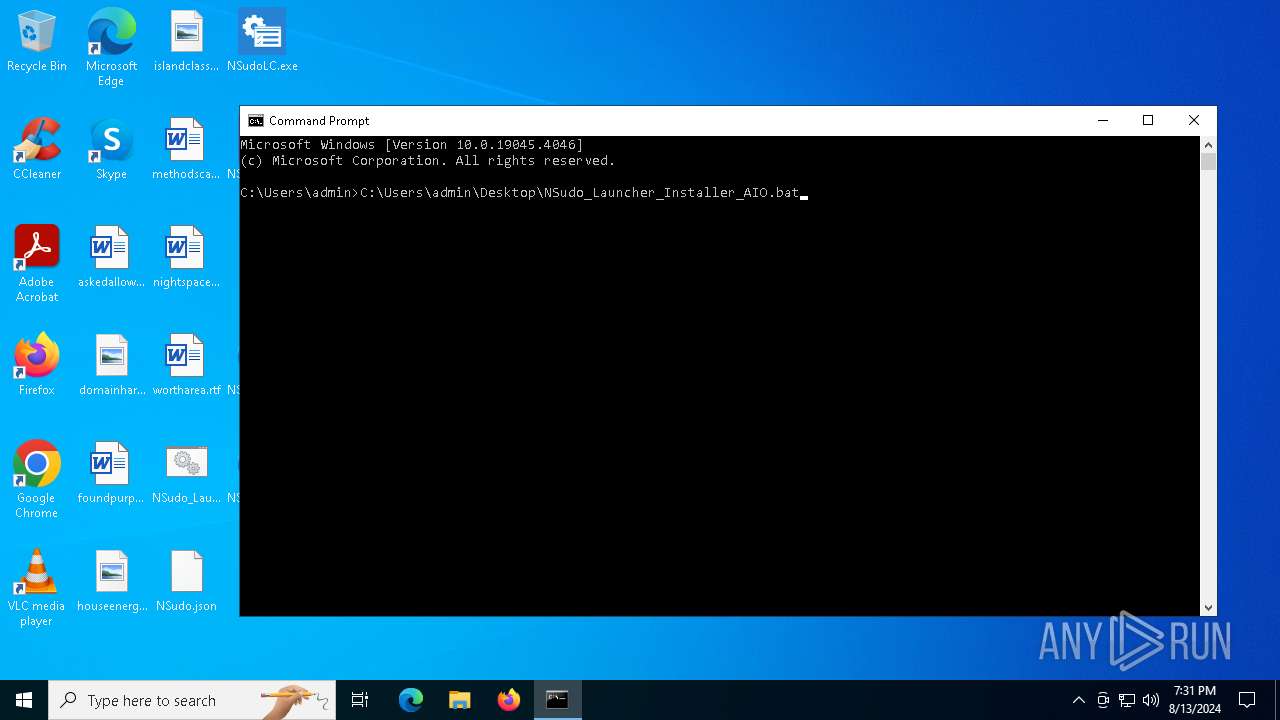
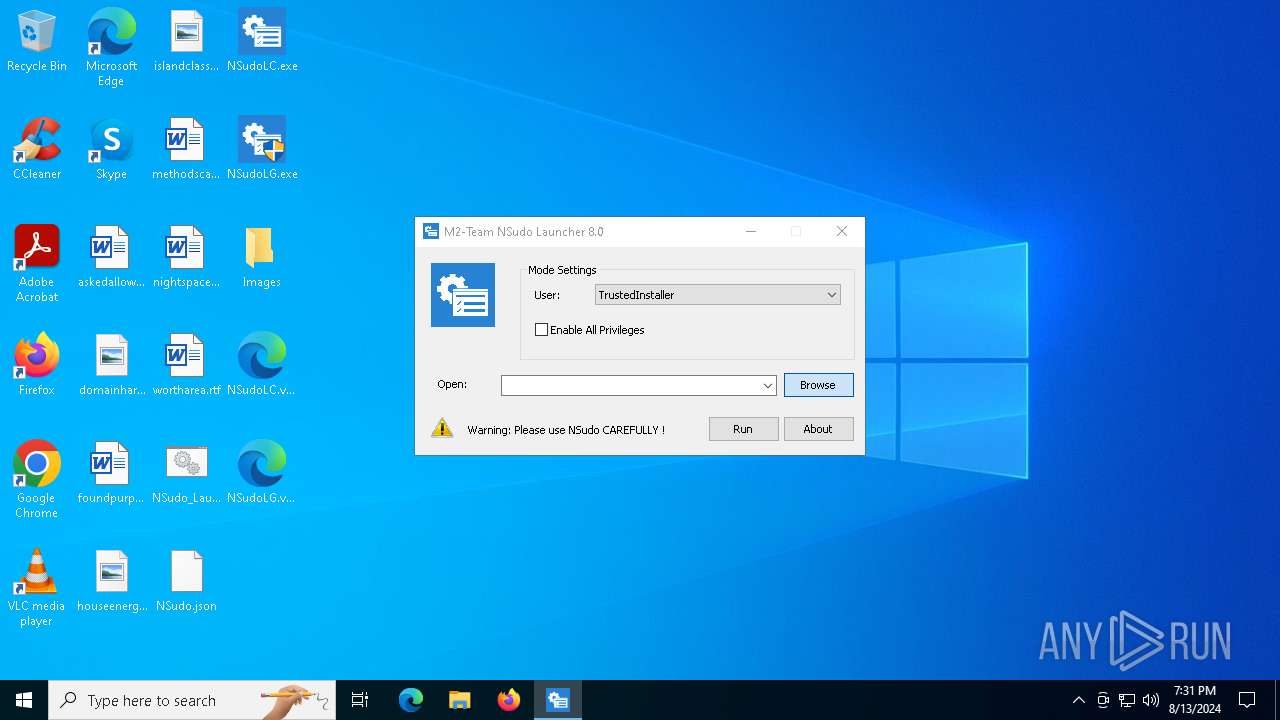
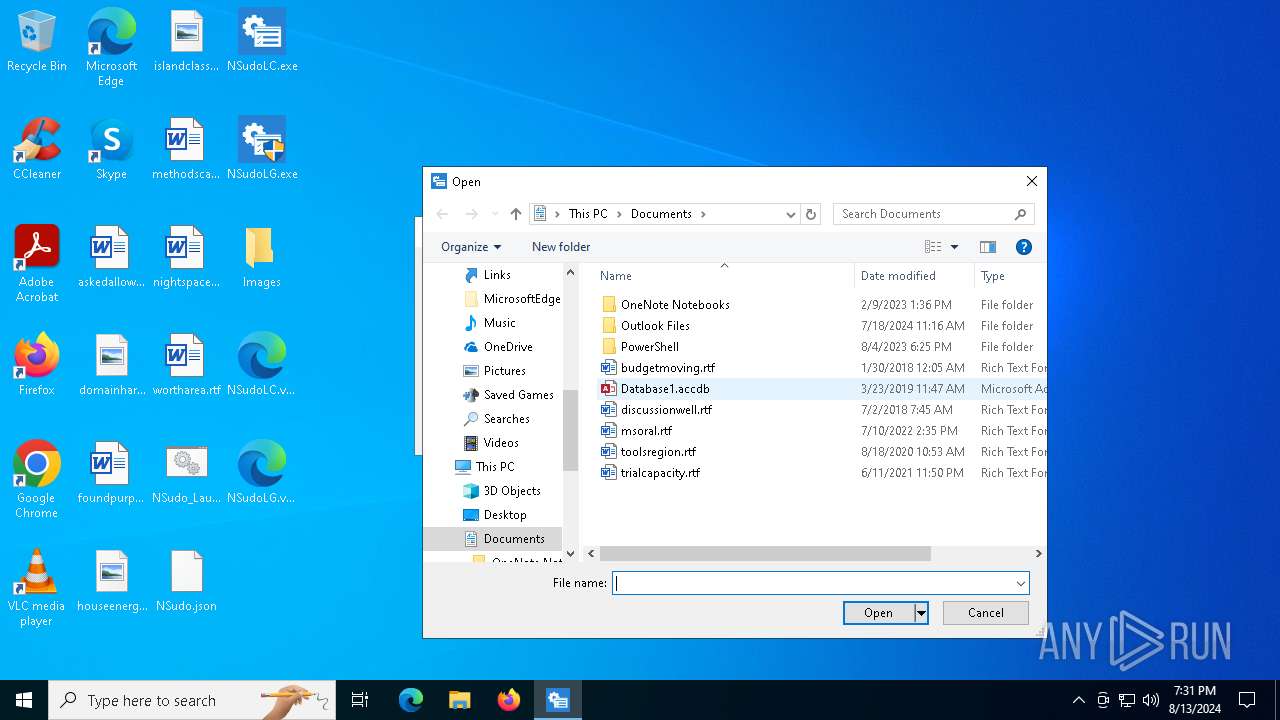
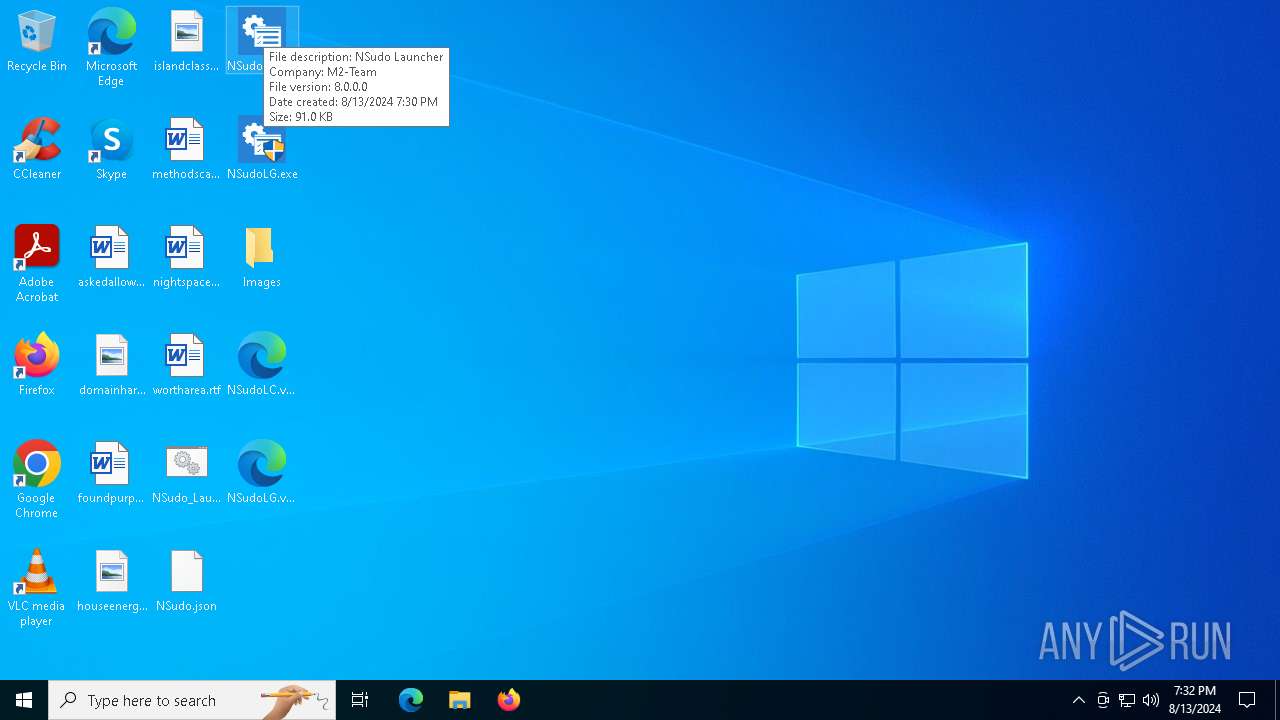
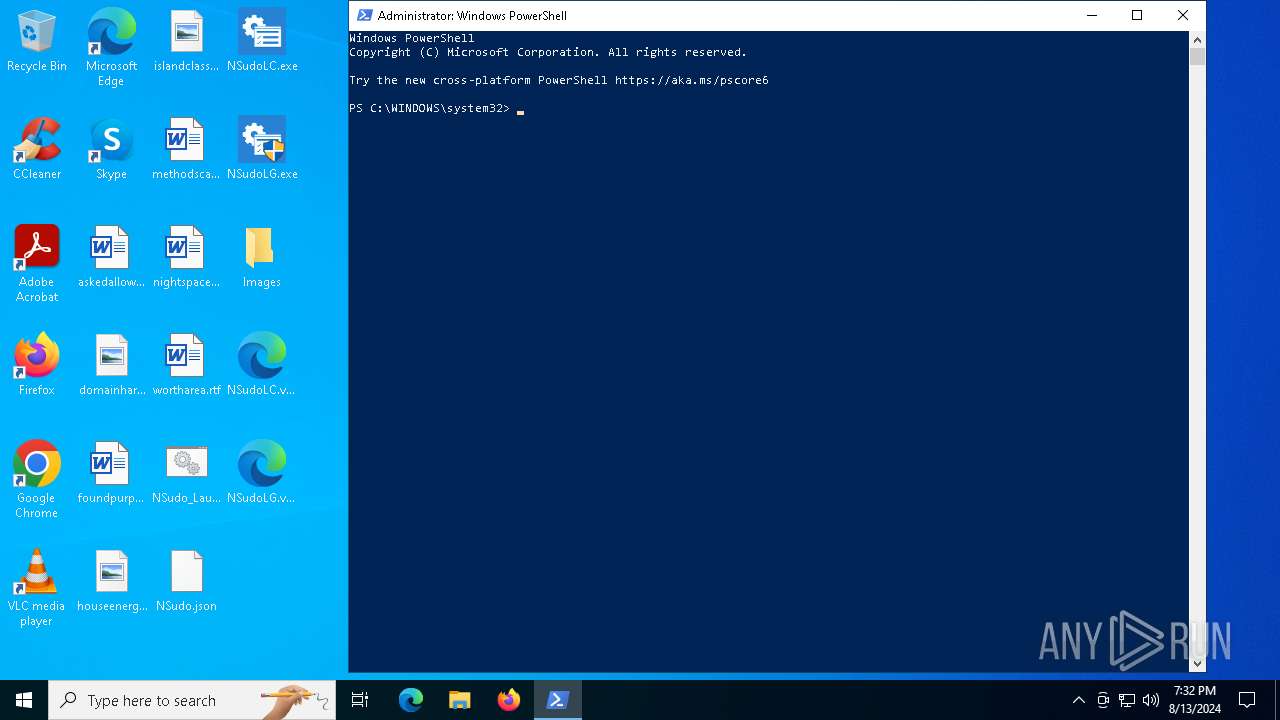
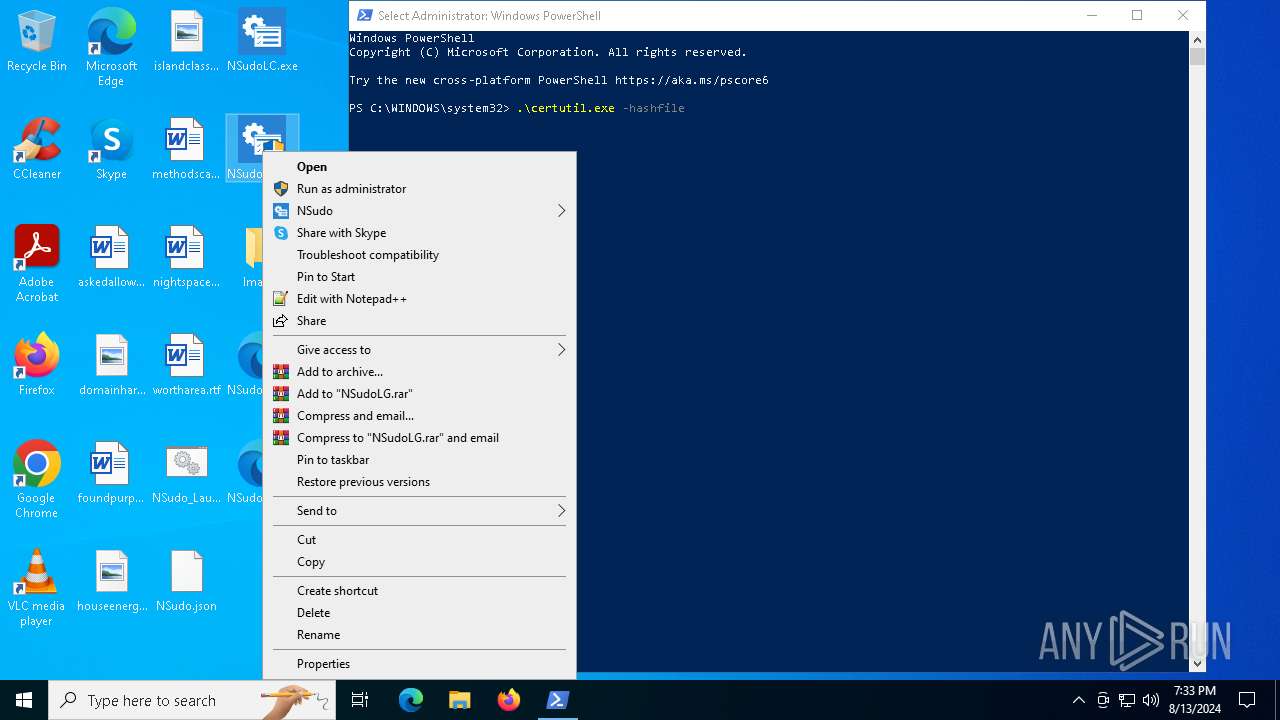
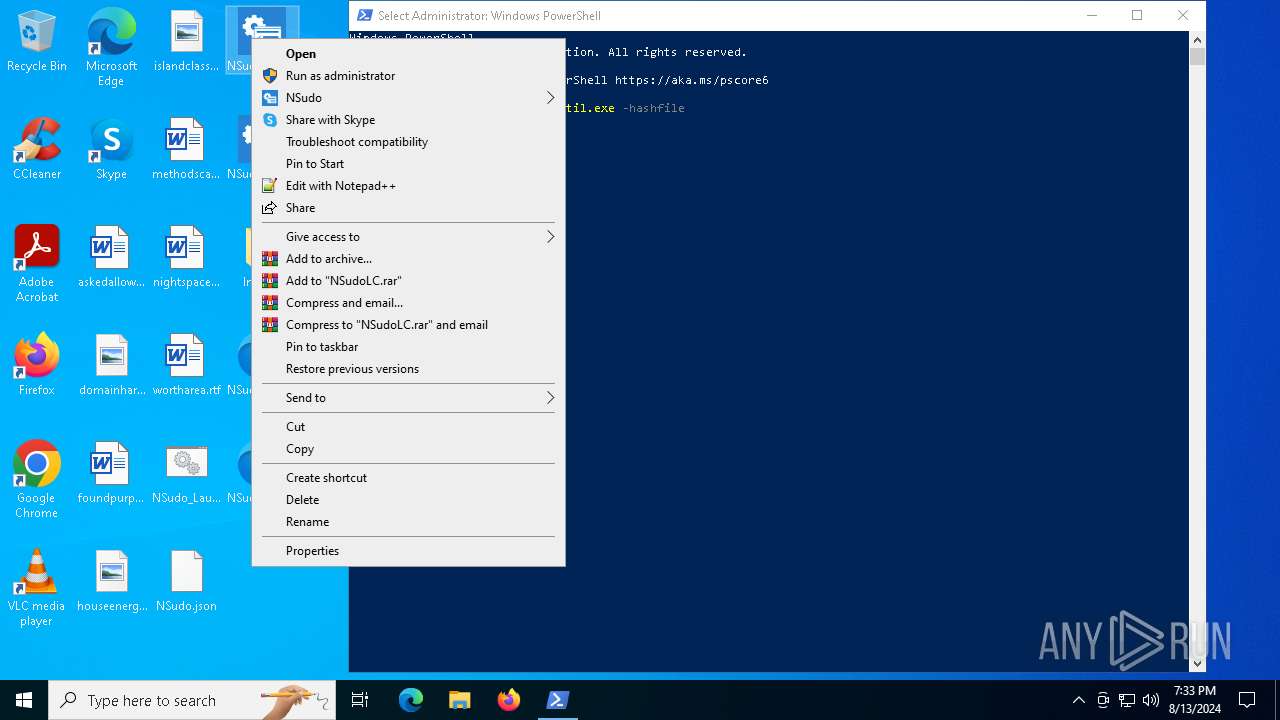
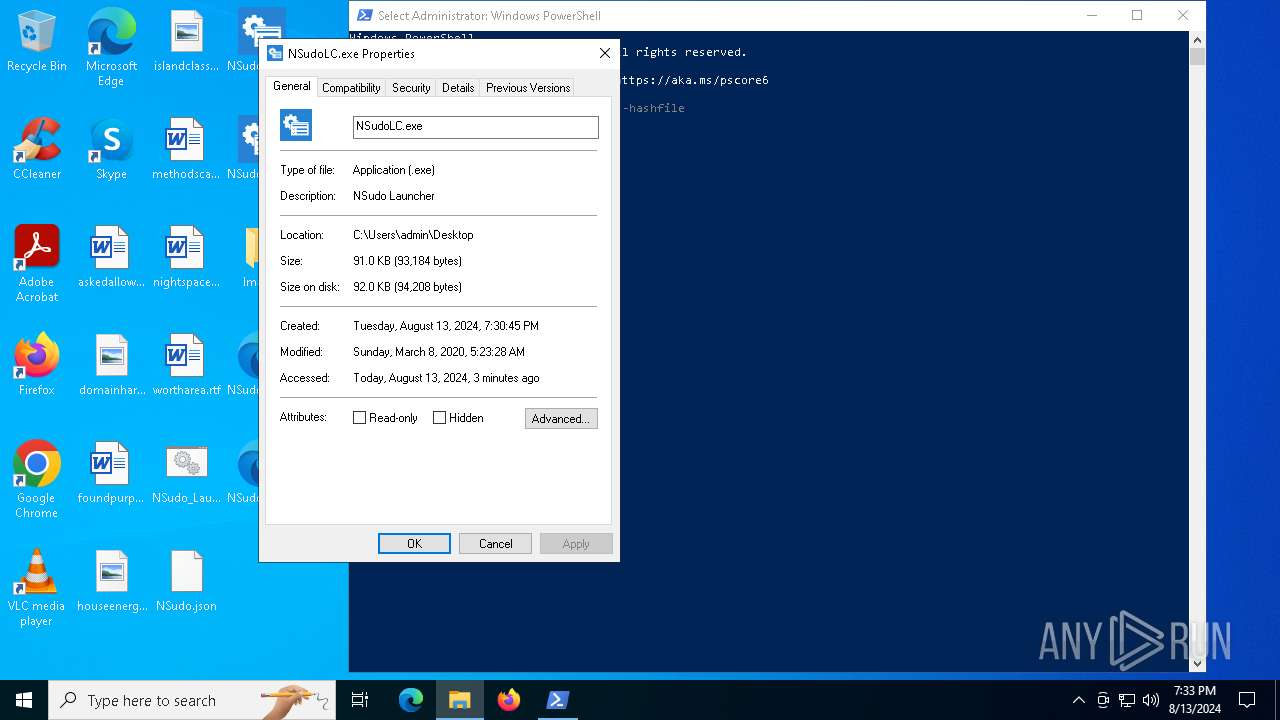
Manual execution by a user
- cmd.exe (PID: 7344)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 7860)
- NSudoLG.exe (PID: 6352)
- NSudoLG.exe (PID: 6200)
- NSudoLC.exe (PID: 1664)
- powershell.exe (PID: 7872)
- firefox.exe (PID: 4316)
- NSudoLC.exe (PID: 7400)
Checks supported languages
- TextInputHost.exe (PID: 6968)
- cvtres.exe (PID: 7280)
- expand.exe (PID: 7116)
- csc.exe (PID: 1288)
- expand.exe (PID: 6568)
- expand.exe (PID: 6532)
- csc.exe (PID: 7948)
- cvtres.exe (PID: 7968)
- NSudoLG.exe (PID: 6200)
- NSudoLC.exe (PID: 7400)
- NSudoLC.exe (PID: 1664)
Reads the computer name
- TextInputHost.exe (PID: 6968)
- NSudoLG.exe (PID: 6200)
Reads the bytes from the current stream and writes them to another stream(SCRIPT)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 7028)
- cscript.exe (PID: 4160)
Create files in a temporary directory
- cscript.exe (PID: 7448)
- cvtres.exe (PID: 7280)
- expand.exe (PID: 7116)
- csc.exe (PID: 1288)
- cscript.exe (PID: 7028)
- expand.exe (PID: 6568)
- cscript.exe (PID: 4160)
- expand.exe (PID: 6532)
- csc.exe (PID: 7948)
- cvtres.exe (PID: 7968)
Reads the machine GUID from the registry
- expand.exe (PID: 7116)
- csc.exe (PID: 1288)
- expand.exe (PID: 6568)
- expand.exe (PID: 6532)
- csc.exe (PID: 7948)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 7756)
Creates files in the program directory
- powershell.exe (PID: 7888)
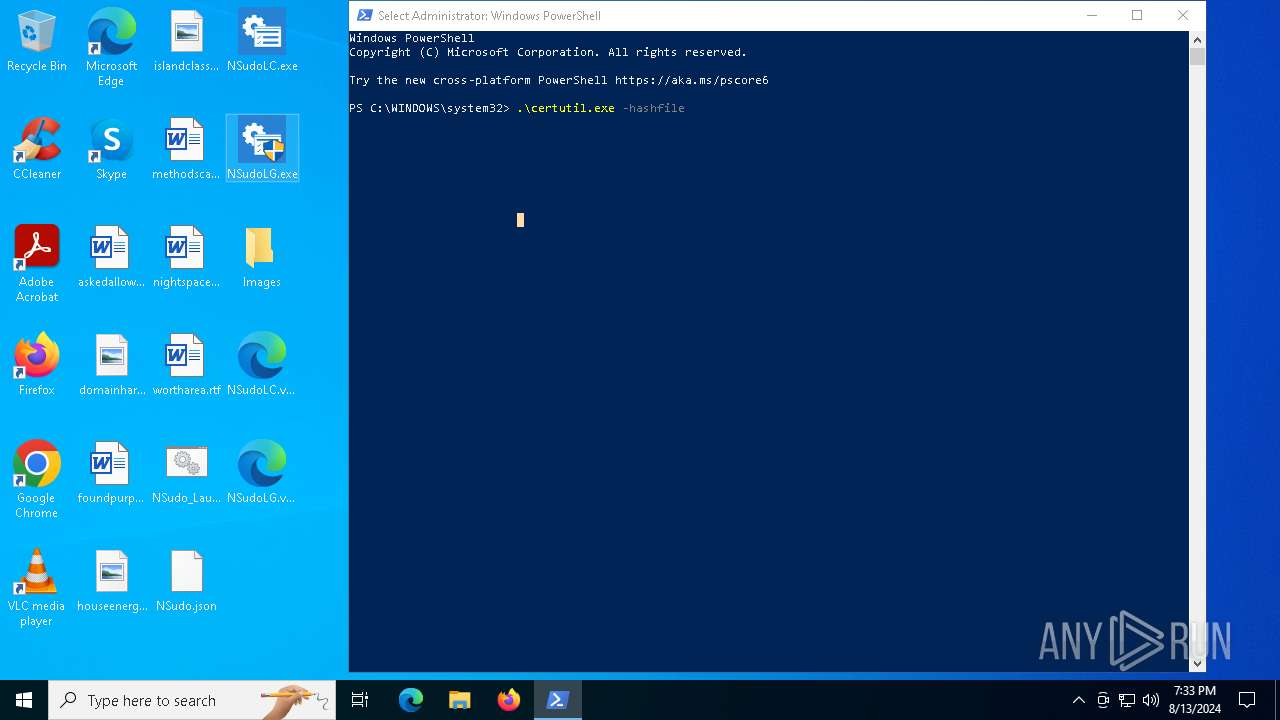
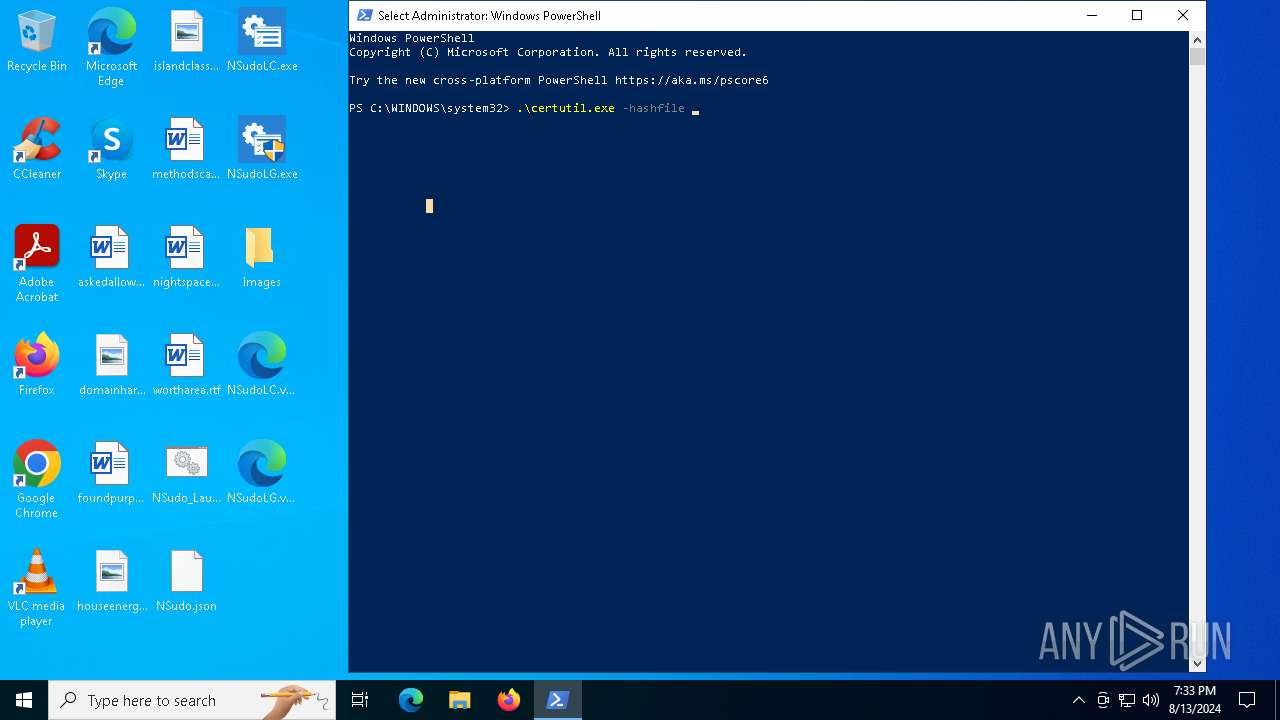
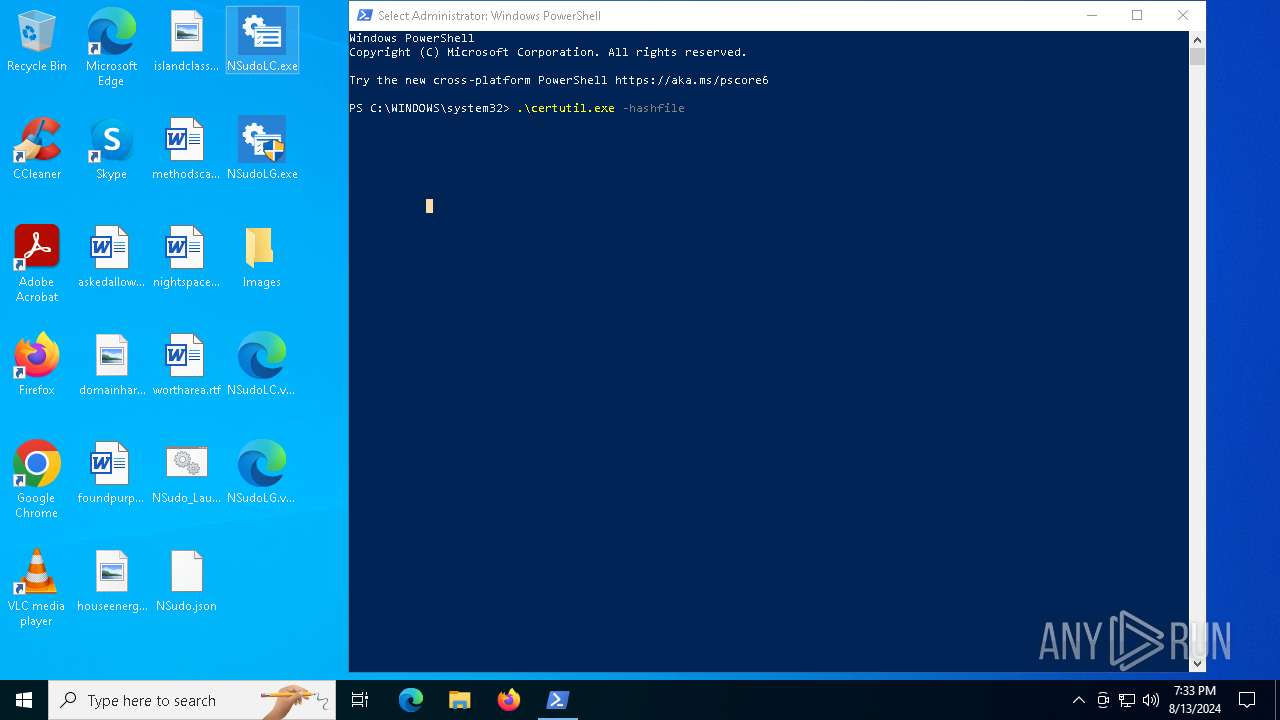
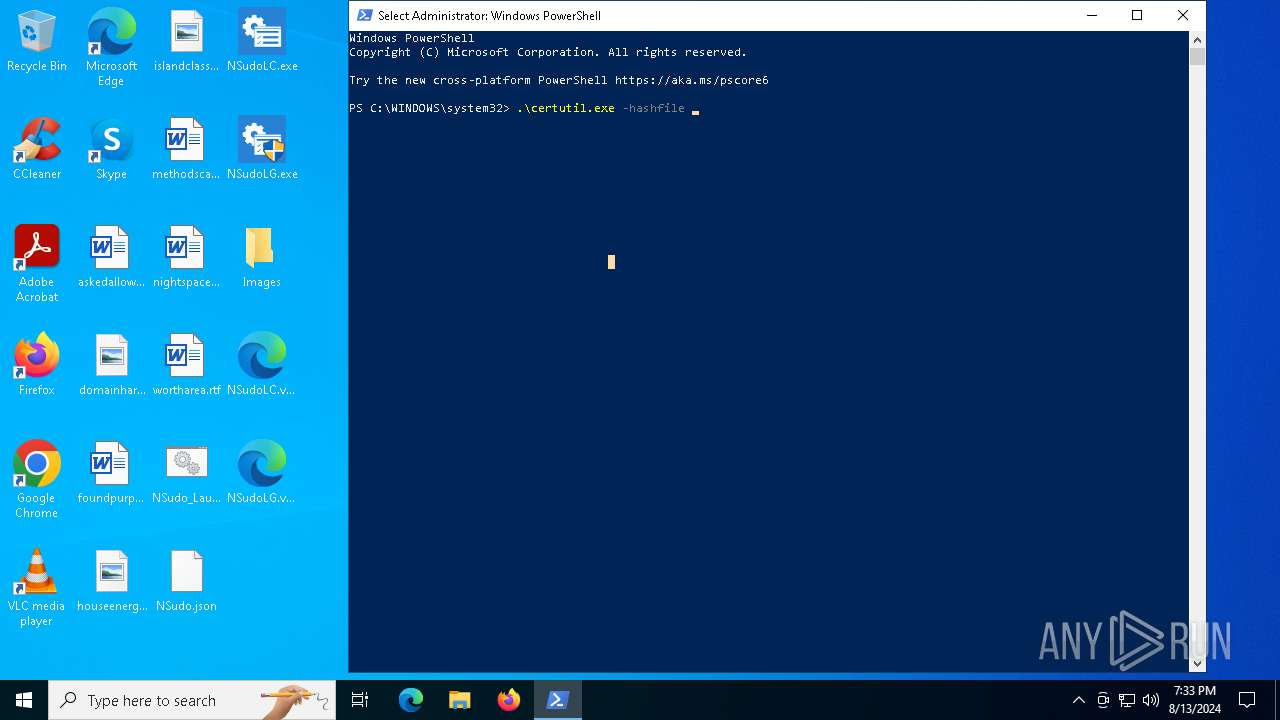
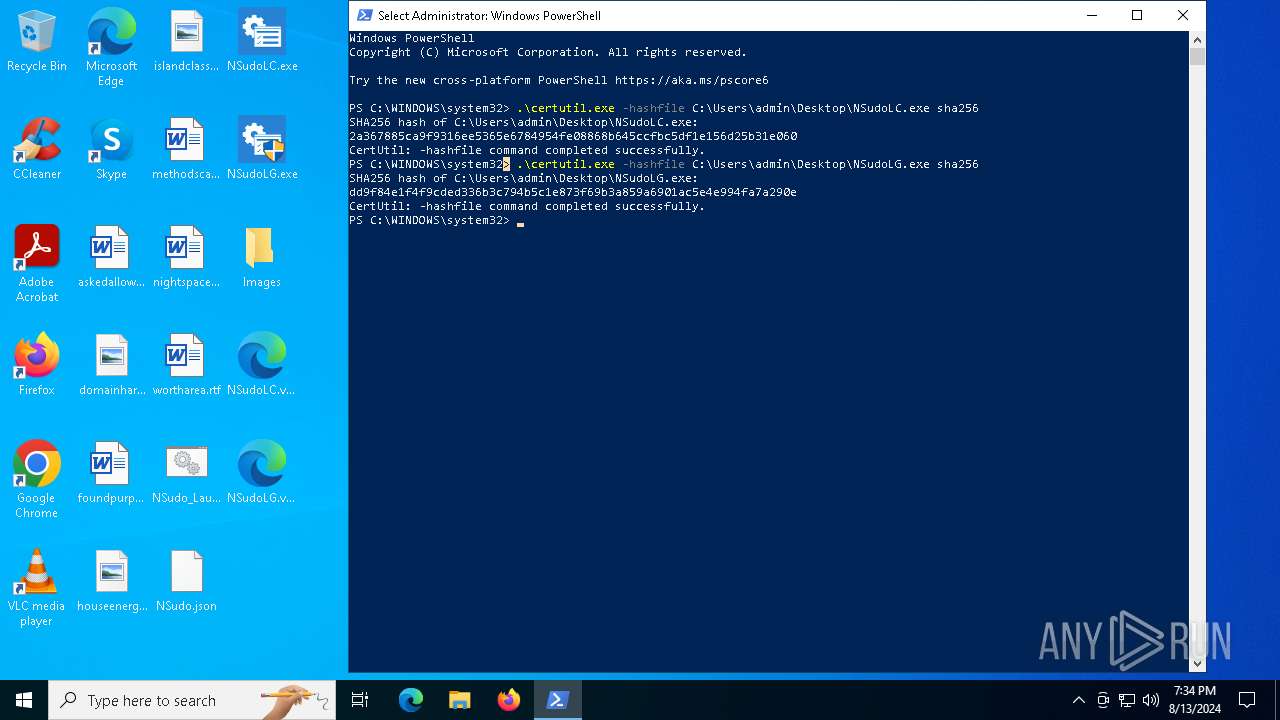
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 6724)
- certutil.exe (PID: 4192)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7872)
Application launched itself
- firefox.exe (PID: 4316)
- firefox.exe (PID: 1292)
Reads Microsoft Office registry keys
- firefox.exe (PID: 1292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
238
Monitored processes
95
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | C:\WINDOWS\system32\cmd.exe /c dir /b "C:\Users\admin\AppData\Local\Temp\NS_Install_17576.tmp\" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | choice /C:YN | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | reg add "HKCR\*\shell\NSudo" /v "MUIVerb" /t REG_SZ /d "NSudo" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5612 -childID 3 -isForBrowser -prefsHandle 5604 -prefMapHandle 5592 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1512 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7ee2c2c3-c701-41cc-b955-bd6583447543} 1292 "\\.\pipe\gecko-crash-server-pipe.1292" 11179d7fd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1116 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NSudo" /v "URLInfoAbout" /t REG_SZ /d "https://m2team.github.io/NSudo/en-us/" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | choice /C:YN | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\1osnknwk\1osnknwk.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1288 | reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\CommandStore\shell\NSudo.RunAs.TrustedInstaller.EnableAllPrivileges" /ve /t REG_SZ /d "Run As TrustedInstaller (Enable All Privileges)" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1664 | "C:\Users\admin\Desktop\NSudoLC.exe" | C:\Users\admin\Desktop\NSudoLC.exe | — | explorer.exe | |||||||||||
User: admin Company: M2-Team Integrity Level: MEDIUM Description: NSudo Launcher Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
Total events
78 388
Read events
78 092
Write events
275
Delete events
21
Modification events
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E0000000F000000000000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0E00000004000000030000000F000000000000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\14 |
| Operation: | write | Name: | MRUListEx |
Value: 02000000000000000300000001000000FFFFFFFF | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E000000030000000F000000000000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (7528) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\17\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 6 | |||
Executable files
8
Suspicious files
149
Text files
53
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7448 | cscript.exe | C:\Users\admin\AppData\Local\Temp\NS_Install_17576.tmp\Rebuilder.cab | compressed | |
MD5:76543EB72D7ED408ACD3501F73EEC3A4 | SHA256:E5725C537D2579D397EEC430D587F26F9126ED4324D445B9D4657E31DFA23A7B | |||
| 7056 | cmd.exe | C:\Users\admin\AppData\Local\Temp\NS_Install_17576.tmp\Rebuilder.cab.tmp | text | |
MD5:BC06846A22FCEF6EC7C84A16F7883791 | SHA256:3A4251ED32F5FA593D48309CDC01EDAD670498FF676F8C811F6F98867ADC0F21 | |||
| 7116 | expand.exe | C:\Windows\Logs\DPX\setupact.log | csv | |
MD5:9192F762AED9E0BB2A8691CA706740B2 | SHA256:AFBA6D436E11E231F9AE083134C523FB0DFFDAC85D5E9AA004619C60A1DFFD60 | |||
| 1288 | csc.exe | C:\Users\admin\AppData\Local\Temp\1osnknwk\CSC62E8E2CD6BF4F2F9D6738D7D14D6B.TMP | res | |
MD5:C54DB65D91973C1D23606387E6304B58 | SHA256:769F2F22BECA71C59B90456BEAEA83C1FB49F7E5888CB6A2DF361C9BAC0A3AD8 | |||
| 7528 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ozbsls33.ufj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7528 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4g2nbp5r.ct3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7528 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:89E96D513C6AACED79124C51AA6864D6 | SHA256:8C054B6843DF13DD1DFD2BA4B790D4A5717D6D32B8E4F9B04257A003755BB9B0 | |||
| 7528 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1osnknwk\1osnknwk.cmdline | text | |
MD5:2AEA89C6B2D1160AF80410E9803204D6 | SHA256:5F60C1762B1984A3014FE7743B65F4C732810744A73A868D84E540D789911CD6 | |||
| 1288 | csc.exe | C:\Users\admin\AppData\Local\Temp\1osnknwk\1osnknwk.out | text | |
MD5:05DF97ABF7EDE574A86457B0BBBF5DD8 | SHA256:204A251705AF9F54D9675232E30C55B9258C78969D7073498FA1C741857DFB02 | |||
| 7280 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES1321.tmp | binary | |
MD5:AB68015FC095B74370EF4F6712012997 | SHA256:9DC7ABCCE77E6BCC1BABF8F84D159B082DAE7811BA2E4484B285A3CC3988DE47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
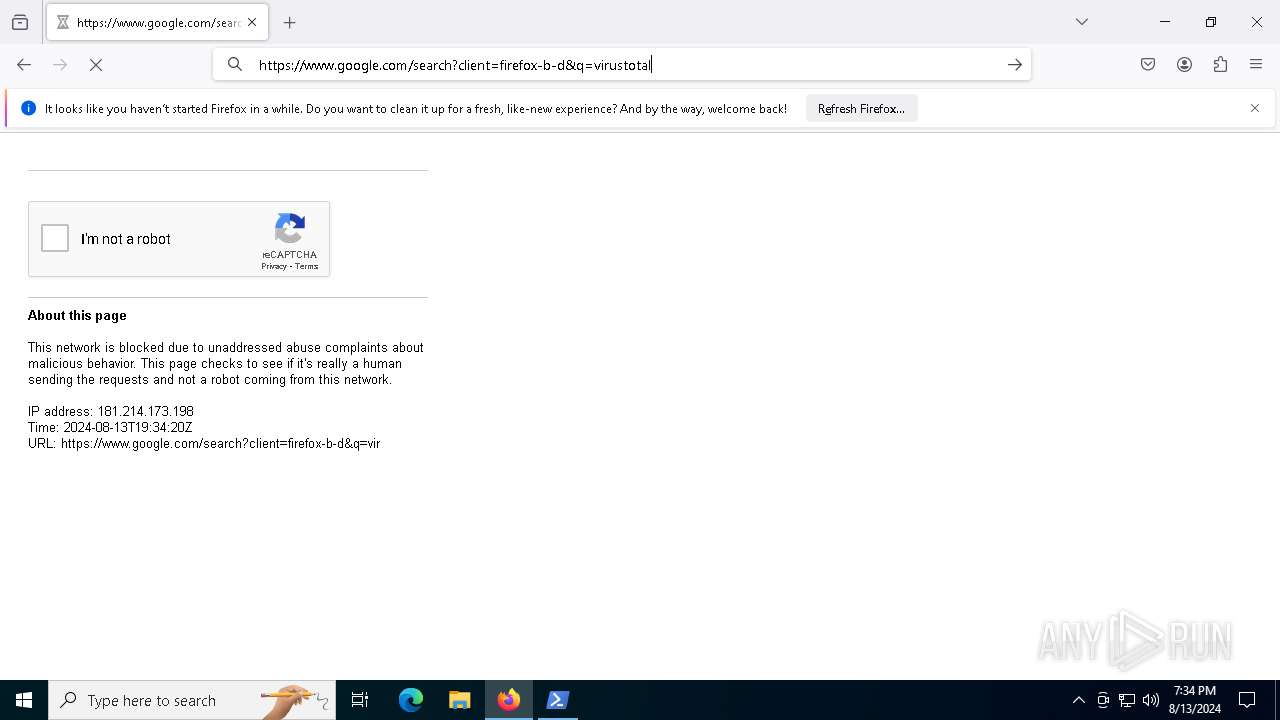
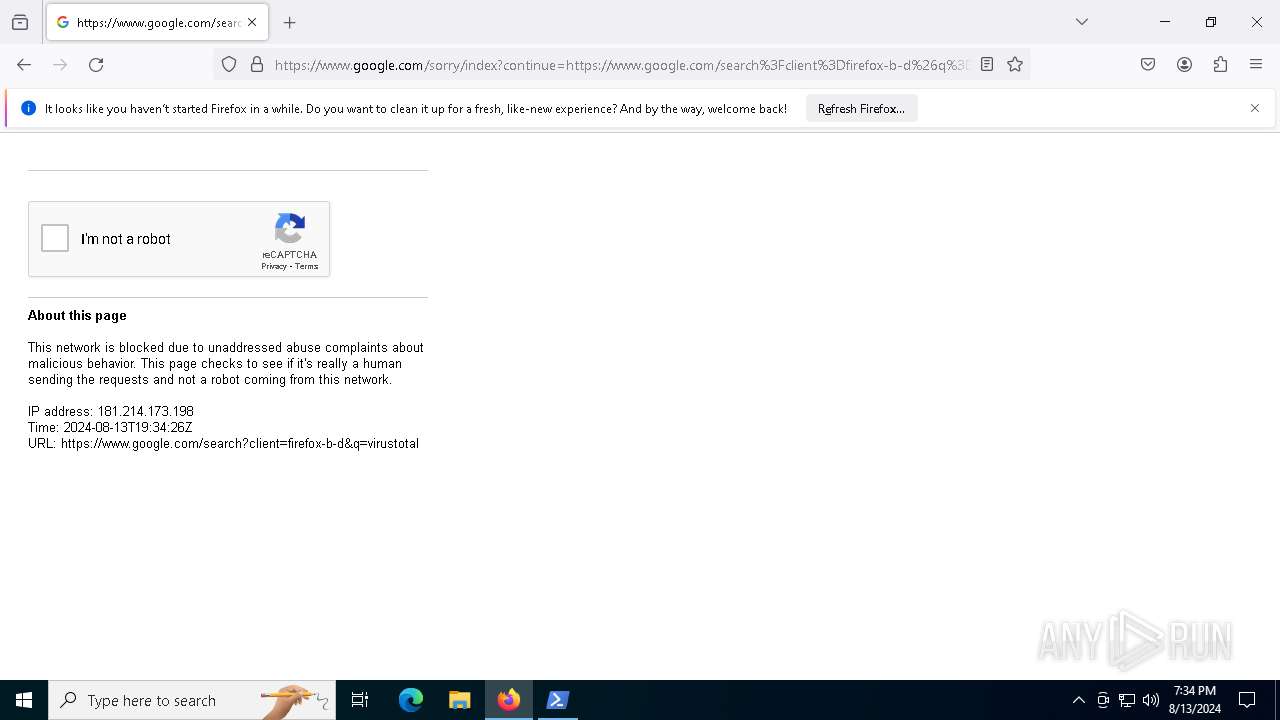
HTTP(S) requests
26
TCP/UDP connections
109
DNS requests
100
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1292 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1292 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
1292 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1292 | firefox.exe | POST | 200 | 2.16.241.15:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
1292 | firefox.exe | POST | 200 | 95.101.54.122:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
1292 | firefox.exe | POST | 200 | 95.101.54.122:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
1292 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
1292 | firefox.exe | POST | 200 | 2.16.241.15:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
1292 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4060 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
812 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 104.126.37.162:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5336 | SearchApp.exe | 104.126.37.163:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 40.79.173.40:443 | browser.pipe.aria.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | AU | unknown |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
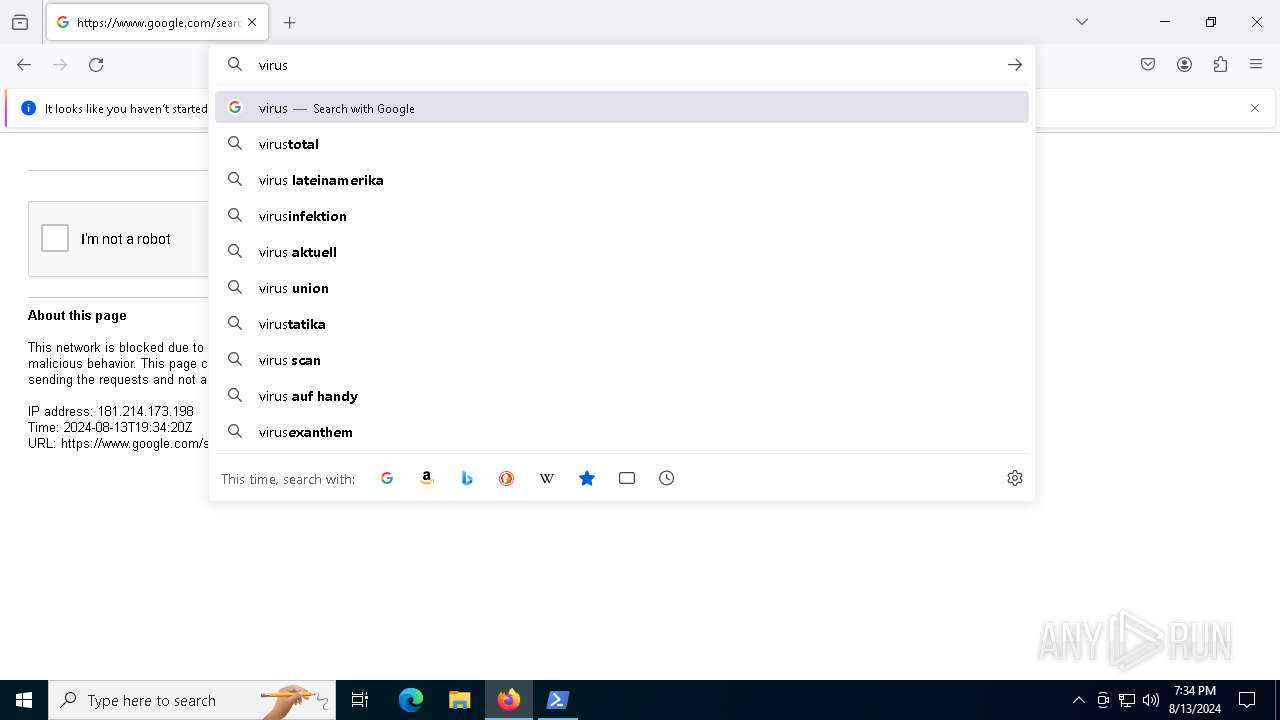
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |