| download: | START.exe |
| Full analysis: | https://app.any.run/tasks/5c9c8070-9777-45a5-b795-e56b08e390fc |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2020, 00:31:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2896EF2DACEAC7F7120B7DCC4BA35C10 |
| SHA1: | A71810AB693AA026C13C643C5FB2A9FC1CB5B22B |
| SHA256: | CFFFF05B209D835316DCBA6719C0DF39D72BD586623AF6817E78B78AF55DE8B6 |
| SSDEEP: | 12288:u1hbYUuepKzerRgs527VL7gdI+sg7uJ8cfrA1D5EWjaK4aRH05saRNOIkJ:u1qUujeu/PgdIA7uamqDiQl4aRUvkIkJ |
MALICIOUS
Application was dropped or rewritten from another process
- taskhost.exe (PID: 2720)
- taskhost.exe (PID: 2128)
- taskhost.exe (PID: 1584)
- taskhost.exe (PID: 2692)
- seting.exe (PID: 2636)
- winlogon.exe (PID: 1640)
- webisida.browser.exe (PID: 536)
- Webisida.Browser.exe (PID: 1268)
- Webisida.Browser.exe (PID: 2680)
- Webisida.Browser.exe (PID: 3888)
- SecureSurf.Browser.Client.exe (PID: 3324)
- SecureSurf.Browser.Client.exe (PID: 1412)
- webisida.browser.exe (PID: 3704)
UAC/LUA settings modification
- reg.exe (PID: 3616)
Loads dropped or rewritten executable
- webisida.browser.exe (PID: 536)
- Webisida.Browser.exe (PID: 3888)
- SecureSurf.Browser.Client.exe (PID: 1412)
- webisida.browser.exe (PID: 3704)
- SecureSurf.Browser.Client.exe (PID: 3324)
SUSPICIOUS
Executable content was dropped or overwritten
- START.exe (PID: 2556)
- webisida.browser.exe (PID: 536)
- winlogon.exe (PID: 1640)
- Webisida.Browser.exe (PID: 1268)
- Webisida.Browser.exe (PID: 3888)
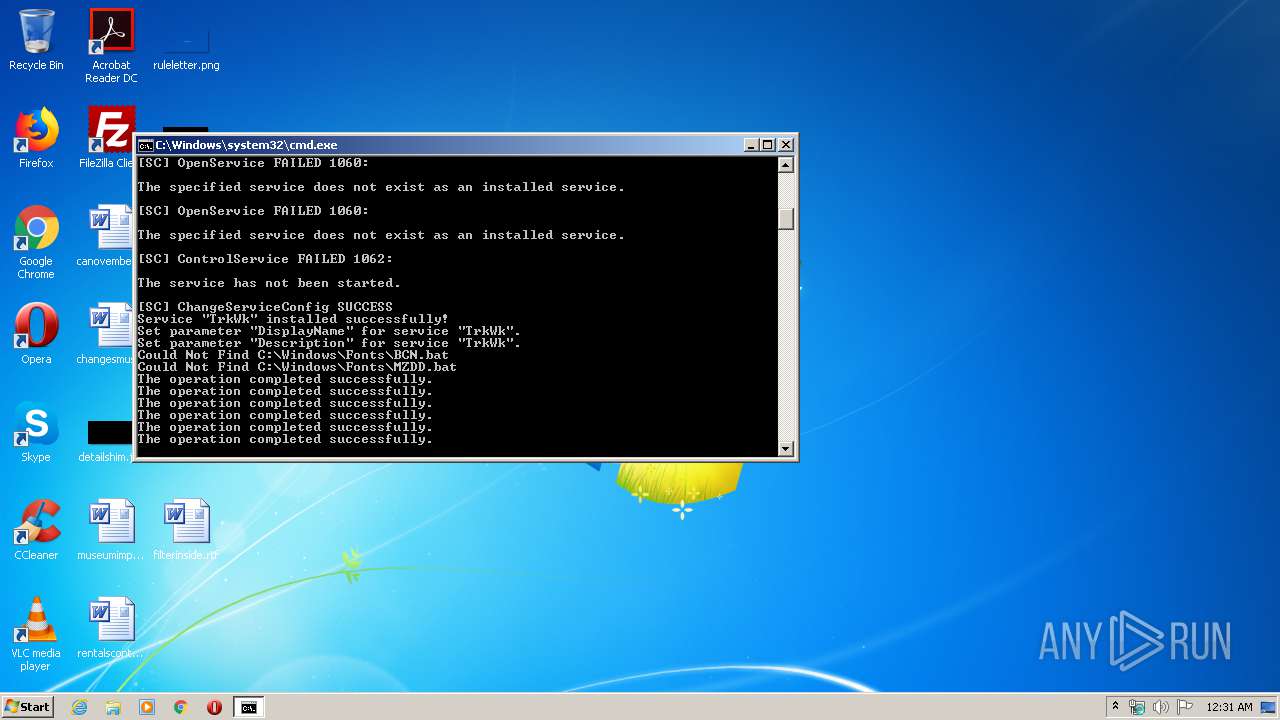
Starts CMD.EXE for commands execution
- START.exe (PID: 2556)
- winlogon.exe (PID: 1640)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 4020)
- seting.exe (PID: 2636)
- cmd.exe (PID: 3536)
Starts SC.EXE for service management
- cmd.exe (PID: 2156)
Application launched itself
- START.exe (PID: 1488)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 3536)
Creates or modifies windows services
- reg.exe (PID: 2952)
- reg.exe (PID: 1252)
- reg.exe (PID: 1632)
- reg.exe (PID: 4060)
- reg.exe (PID: 4092)
- reg.exe (PID: 2760)
- reg.exe (PID: 3428)
- reg.exe (PID: 4016)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2156)
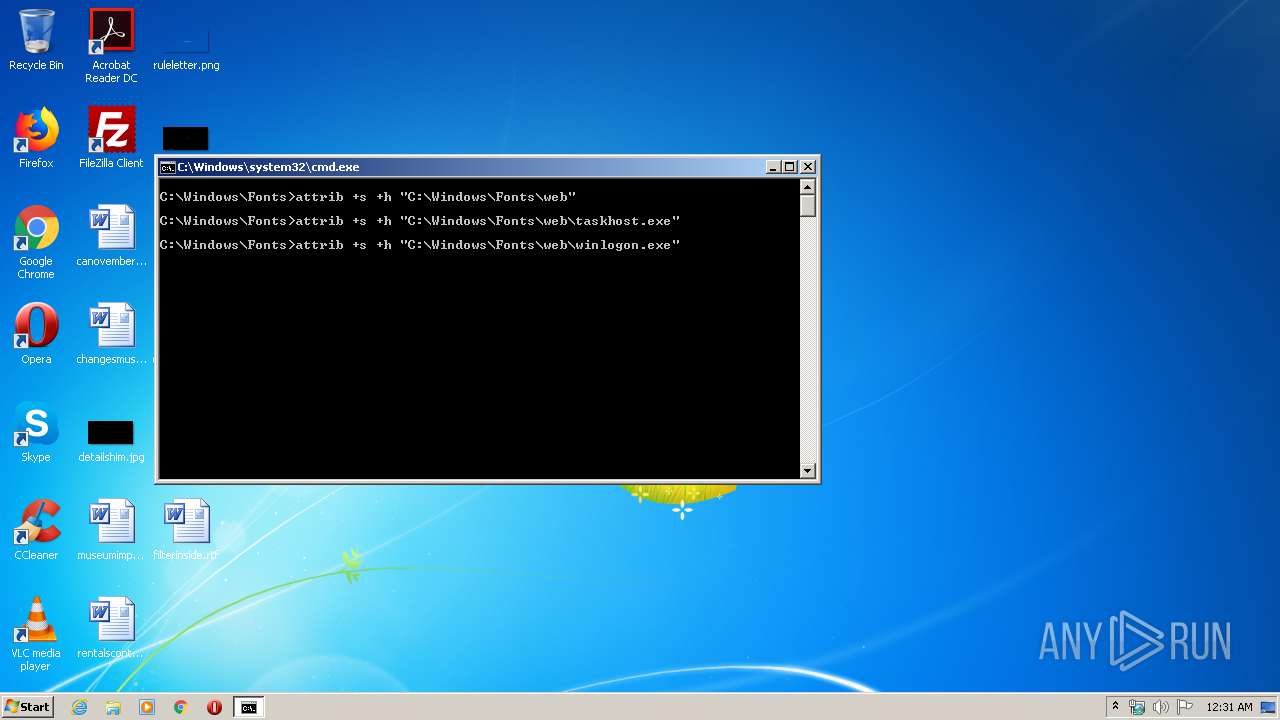
Creates files in the Windows directory
- START.exe (PID: 2556)
- seting.exe (PID: 2636)
- webisida.browser.exe (PID: 536)
- winlogon.exe (PID: 1640)
- Webisida.Browser.exe (PID: 3888)
- webisida.browser.exe (PID: 3704)
Executed as Windows Service
- taskhost.exe (PID: 2692)
Removes files from Windows directory
- cmd.exe (PID: 2156)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 3940)
- webisida.browser.exe (PID: 536)
- Webisida.Browser.exe (PID: 3888)
- webisida.browser.exe (PID: 3704)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3940)
Starts itself from another location
- Webisida.Browser.exe (PID: 1268)
INFO
Dropped object may contain Bitcoin addresses
- START.exe (PID: 2556)
- webisida.browser.exe (PID: 536)
- Webisida.Browser.exe (PID: 1268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 00:14:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 101888 |
| InitializedDataSize: | 38912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x193af |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.0.3900 |
| ProductVersionNumber: | 1.7.0.3900 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Oleg N. Scherbakov |
| LegalCopyright: | Copyright © 2005-2016 Oleg N. Scherbakov |
| ProductName: | 7-Zip SFX |
| PrivateBuild: | April 1, 2016 |
| FileVersion: | 1.7.0.3900 |
| OriginalFileName: | 7ZSfxMod_x86.exe |
| FileDescription: | 7z Setup SFX (x86) |
| InternalName: | 7ZSfxMod |
| ProductVersion: | 1.7.0.3900 |
| Created: | 7z SFX Constructor v3.2.0.0 (http://usbtor.ru/viewtopic.php?t=798) |
| Builder: | crocodyli@yandex.ru 00:10:54 13/03/2019 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 22:14:00 |
| CompanyName: | Oleg N. Scherbakov |
| LegalCopyright: | Copyright © 2005-2016 Oleg N. Scherbakov |
| ProductName: | 7-Zip SFX |
| PrivateBuild: | April 1, 2016 |
| FileVersion: | 1.7.0.3900 |
| OriginalFilename: | 7ZSfxMod_x86.exe |
| FileDescription: | 7z Setup SFX (x86) |
| InternalName: | 7ZSfxMod |
| ProductVersion: | 1.7.0.3900 |
| Created: | 7z SFX Constructor v3.2.0.0 (http://usbtor.ru/viewtopic.php?t=798) |
| Builder: | crocodyli@yandex.ru 00:10:54 13/03/2019 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Apr-2016 22:14:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00018D6A | 0x00018E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69221 |
.rdata | 0x0001A000 | 0x00003FA0 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.7721 |
.data | 0x0001E000 | 0x00004B90 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.63636 |
.rsrc | 0x00023000 | 0x00004F14 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.72364 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2117 | 777 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.66881 | 2488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.16649 | 4392 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.53423 | 9832 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.66751 | 62 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
130
Monitored processes
86
Malicious processes
11
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | sc config TrkWk type= own type= interact | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 252 | cacls "C:\Windows\Fonts\web\webisida.browser.exe" /P SYSTEM:F | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 312 | cacls "C:\Windows\Fonts\web\winlogon.exe" /P SYSTEM:F | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 440 | Reg.exe add "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v "ClearPageFileAtShutdown" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | "C:\Windows\Fonts\web\webisida.browser.exe" | C:\Windows\Fonts\web\webisida.browser.exe | winlogon.exe | ||||||||||||
User: SYSTEM Company: Webisida.com Integrity Level: SYSTEM Description: SecureSurf.Browser.Shell Exit code: 1 Version: 6.0.0.9 Modules
| |||||||||||||||
| 884 | cacls "C:\Windows\Fonts\web\taskhost.exe" /P SYSTEM:F | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | C:\Windows\system32\cmd.exe /S /D /c" echo E" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1252 | Reg.exe add "HKLM\SYSTEM\CurrentControlSet\Services\TrkWk" /v "ErrorControl" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | "C:\Windows\system32\config\systemprofile\AppData\Local\Webisida\install\Webisida.Browser.exe" /u "C:\Windows\Fonts\web" | C:\Windows\system32\config\systemprofile\AppData\Local\Webisida\install\Webisida.Browser.exe | webisida.browser.exe | ||||||||||||
User: SYSTEM Company: Webisida.com Integrity Level: SYSTEM Description: SecureSurf.Browser.Shell Exit code: 0 Version: 6.0.0.12 Modules
| |||||||||||||||
| 1332 | C:\Windows\system32\cmd.exe /S /D /c" echo J" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 940
Read events
1 850
Write events
90
Delete events
0
Modification events
| (PID) Process: | (1488) START.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1488) START.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2556) START.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2556) START.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1584) taskhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\TrkWk\Parameters |
| Operation: | write | Name: | Application |
Value: winlogon.exe | |||
| (PID) Process: | (1584) taskhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\TrkWk\Parameters |
| Operation: | write | Name: | AppParameters |
Value: | |||
| (PID) Process: | (1584) taskhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\TrkWk\Parameters |
| Operation: | write | Name: | AppDirectory |
Value: | |||
| (PID) Process: | (1584) taskhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\TrkWk\Parameters\AppExit |
| Operation: | write | Name: | |
Value: Restart | |||
| (PID) Process: | (3616) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (1564) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
Executable files
36
Suspicious files
2
Text files
15
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | START.exe | C:\Users\admin\AppData\Local\Temp\7ZSfx001.cmd | — | |
MD5:— | SHA256:— | |||
| 536 | webisida.browser.exe | C:\Windows\Fonts\web\gecko\MemIPC.dll.download | — | |
MD5:— | SHA256:— | |||
| 536 | webisida.browser.exe | C:\Windows\Fonts\web\gecko\protobuf-net.dll.download | — | |
MD5:— | SHA256:— | |||
| 536 | webisida.browser.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Webisida\settings.db-journal | — | |
MD5:— | SHA256:— | |||
| 536 | webisida.browser.exe | C:\Windows\Fonts\web\gecko\Capinet.dll.download | — | |
MD5:— | SHA256:— | |||
| 536 | webisida.browser.exe | C:\Windows\System32\config\systemprofile\AppData\Local\Webisida\install\Webisida.Browser.exe.tgz.download | — | |
MD5:— | SHA256:— | |||
| 3888 | Webisida.Browser.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Webisida\settings.db-journal | — | |
MD5:— | SHA256:— | |||
| 3888 | Webisida.Browser.exe | C:\Windows\TEMP\etilqs_gxEEAayjhcVzoVZ | — | |
MD5:— | SHA256:— | |||
| 3888 | Webisida.Browser.exe | C:\Windows\TEMP\etilqs_OPJan6Q09f8FbTm | — | |
MD5:— | SHA256:— | |||
| 3888 | Webisida.Browser.exe | C:\Windows\TEMP\etilqs_X8L2nfTK4Lm6rwx | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
10
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3888 | Webisida.Browser.exe | GET | 200 | 85.10.204.74:80 | http://surfing.webisida.com/GetUpdate.ashx?v=6.0.0.12&rnd=637153363100220000 | DE | — | — | unknown |
3704 | webisida.browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/flash/win32/NPSWF32_32_0_0_142/xp/hash | EE | compressed | 189 b | unknown |
536 | webisida.browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/raw/memipc-1.0.0.1.dll.gz | EE | compressed | 7.09 Kb | unknown |
3704 | webisida.browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/securesurf.browser.client-win.txt.gz | EE | compressed | 221 b | unknown |
536 | webisida.browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/raw/system.data.sqlite-1.0.84.0.dll.gz | EE | compressed | 485 Kb | unknown |
536 | webisida.browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/raw/protobuf-net-2.0.0.668.dll.gz | EE | compressed | 77.6 Kb | unknown |
536 | webisida.browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/raw/capinet-3.0.0.1.dll.gz | EE | compressed | 56.9 Kb | unknown |
536 | webisida.browser.exe | GET | 200 | 85.10.204.74:80 | http://surfing.webisida.com/GetUpdate.ashx?v=6.0.0.9&rnd=637153362963032500 | DE | text | 24 b | unknown |
536 | webisida.browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/Webisida.Browser.exe.tgz | EE | compressed | 426 Kb | unknown |
3888 | Webisida.Browser.exe | GET | 200 | 159.253.20.204:80 | http://download.webisida.com/files/gecko-engine-win.tar.gz | EE | compressed | 35.1 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | Webisida.Browser.exe | 85.10.204.74:80 | surfing.webisida.com | Hetzner Online GmbH | DE | unknown |
1412 | SecureSurf.Browser.Client.exe | 108.177.15.109:995 | pop.gmail.com | Google Inc. | US | whitelisted |
536 | webisida.browser.exe | 159.253.20.204:80 | download.webisida.com | Fastvps Eesti Ou | EE | unknown |
3888 | Webisida.Browser.exe | 159.253.20.204:80 | download.webisida.com | Fastvps Eesti Ou | EE | unknown |
3704 | webisida.browser.exe | 159.253.20.204:80 | download.webisida.com | Fastvps Eesti Ou | EE | unknown |
1412 | SecureSurf.Browser.Client.exe | 94.100.180.90:993 | imap.mail.ru | Limited liability company Mail.Ru | RU | unknown |
3704 | webisida.browser.exe | 85.10.204.74:80 | surfing.webisida.com | Hetzner Online GmbH | DE | unknown |
3324 | SecureSurf.Browser.Client.exe | 108.177.15.109:995 | pop.gmail.com | Google Inc. | US | whitelisted |
3324 | SecureSurf.Browser.Client.exe | 94.100.180.90:993 | imap.mail.ru | Limited liability company Mail.Ru | RU | unknown |
536 | webisida.browser.exe | 85.10.204.74:80 | surfing.webisida.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.webisida.com |
| unknown |
surfing.webisida.com |
| unknown |
imap.mail.ru |
| shared |
pop.gmail.com |
| shared |
Threats
Process | Message |
|---|---|
webisida.browser.exe | [ 536 - C:\Windows\Fonts\web\webisida.browser.exe] impossible to find URLDownloadToCacheFileA
|
webisida.browser.exe | [ 536 - C:\Windows\Fonts\web\webisida.browser.exe] impossible to find URLDownloadToFileA
|
webisida.browser.exe | [ 536 - C:\Windows\Fonts\web\webisida.browser.exe] impossible to find URLDownloadToCacheFileW
|
webisida.browser.exe | [ 536 - C:\Windows\Fonts\web\webisida.browser.exe] impossible to find URLDownloadToFileW
|
webisida.browser.exe | [ 536 - C:\Windows\Fonts\web\webisida.browser.exe] impossible to find waveOutPrepareHeader
|
Webisida.Browser.exe | [3888 - C:\Windows\Fonts\web\Webisida.Browser.exe] impossible to find waveOutPrepareHeader
|
Webisida.Browser.exe | [3888 - C:\Windows\Fonts\web\Webisida.Browser.exe] impossible to find URLDownloadToFileA
|
Webisida.Browser.exe | [3888 - C:\Windows\Fonts\web\Webisida.Browser.exe] impossible to find URLDownloadToCacheFileA
|
Webisida.Browser.exe | [3888 - C:\Windows\Fonts\web\Webisida.Browser.exe] impossible to find URLDownloadToCacheFileW
|
Webisida.Browser.exe | [3888 - C:\Windows\Fonts\web\Webisida.Browser.exe] impossible to find URLDownloadToFileW
|