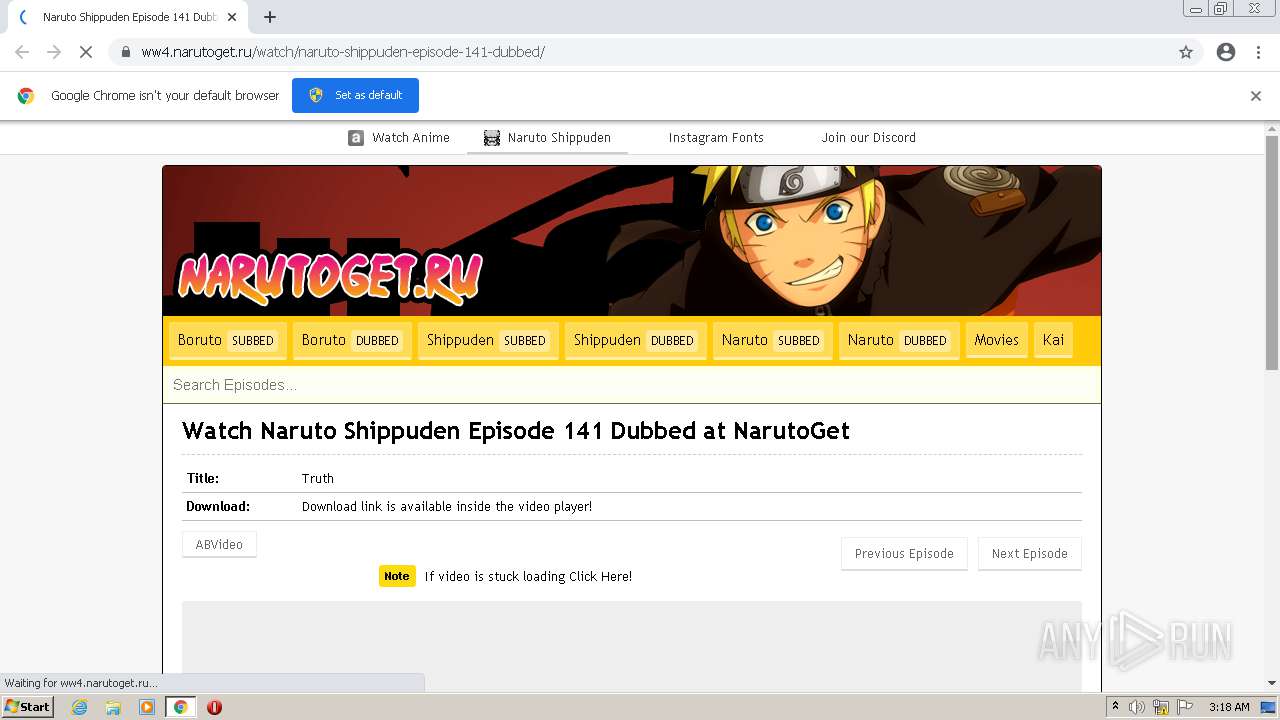
| URL: | https://ww4.narutoget.ru/watch/naruto-shippuden-episode-141-dubbed/ |
| Full analysis: | https://app.any.run/tasks/ca199b65-dae1-4887-80d2-4fcc3cd63556 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2021, 02:17:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FE7512DC85580C574675D5D07D9F4D48 |
| SHA1: | D2C9E6DA704D4745F15396BD6D269DC9288CC804 |
| SHA256: | CFEC16E78710622271E64901DE5402B23B36BB13B2F8D88EE26940C724B2A8FC |
| SSDEEP: | 3:N8DcQ8zGmvsIWOQBu9VMaUxEK:2djmvsCQBQMafK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- chrome.exe (PID: 2368)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 1628)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 2012)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 3344)
- chrome.exe (PID: 1768)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 1540)
- chrome.exe (PID: 3028)
Reads the hosts file
- chrome.exe (PID: 1108)
- chrome.exe (PID: 2268)
Application launched itself
- chrome.exe (PID: 1108)
Reads the computer name
- chrome.exe (PID: 1108)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2012)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 2516)
Reads settings of System Certificates
- chrome.exe (PID: 2268)
Reads the date of Windows installation
- chrome.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2720 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://ww4.narutoget.ru/watch/naruto-shippuden-episode-141-dubbed/" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3320 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1040 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6eb6d988,0x6eb6d998,0x6eb6d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 086
Read events
12 988
Write events
93
Delete events
5
Modification events
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
25
Text files
99
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60C41955-454.pma | — | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF2b4082.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f6f08948-9507-450d-9904-27084ecd5efd.tmp | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2b4072.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\52b8eb4f-cabf-45bc-963e-55709b414fc9.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2b416c.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
89
DNS requests
52
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
— | — | HEAD | 200 | 84.15.65.77:80 | http://r2---sn-cpux-gpml.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=80.233.134.134&mm=28&mn=sn-cpux-gpml&ms=nvh&mt=1623463607&mv=u&mvi=2&pl=24&rmhost=r1---sn-cpux-gpml.gvt1.com&shardbypass=yes&smhost=r1---sn-cpux-gpme.gvt1.com | LT | — | — | whitelisted |
2268 | chrome.exe | GET | 301 | 185.78.22.41:80 | http://musict.ir/pushak.html | IR | html | 237 b | suspicious |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 554 b | whitelisted |
— | — | GET | 206 | 84.15.65.77:80 | http://r2---sn-cpux-gpml.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=80.233.134.134&mm=28&mn=sn-cpux-gpml&ms=nvh&mt=1623464179&mv=m&mvi=2&pl=24&rmhost=r1---sn-cpux-gpml.gvt1.com&shardbypass=yes&smhost=r1---sn-cpux-gpme.gvt1.com | LT | binary | 9.63 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 554 b | whitelisted |
— | — | GET | 206 | 84.15.65.77:80 | http://r2---sn-cpux-gpml.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=80.233.134.134&mm=28&mn=sn-cpux-gpml&ms=nvh&mt=1623463607&mv=u&mvi=2&pl=24&rmhost=r1---sn-cpux-gpml.gvt1.com&shardbypass=yes&smhost=r1---sn-cpux-gpme.gvt1.com | LT | binary | 5.76 Kb | whitelisted |
— | — | GET | 206 | 84.15.65.77:80 | http://r2---sn-cpux-gpml.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=80.233.134.134&mm=28&mn=sn-cpux-gpml&ms=nvh&mt=1623463607&mv=u&mvi=2&pl=24&rmhost=r1---sn-cpux-gpml.gvt1.com&shardbypass=yes&smhost=r1---sn-cpux-gpme.gvt1.com | LT | binary | 9.62 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 554 b | whitelisted |
— | — | GET | 206 | 84.15.65.77:80 | http://r2---sn-cpux-gpml.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=80.233.134.134&mm=28&mn=sn-cpux-gpml&ms=nvh&mt=1623464179&mv=m&mvi=2&pl=24&rmhost=r1---sn-cpux-gpml.gvt1.com&shardbypass=yes&smhost=r1---sn-cpux-gpme.gvt1.com | LT | binary | 9.62 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2268 | chrome.exe | 91.228.74.134:443 | secure.quantserve.com | Quantcast Corporation | GB | suspicious |
2268 | chrome.exe | 13.224.195.79:443 | rules.quantcount.com | — | US | suspicious |
2268 | chrome.exe | 64.233.167.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2268 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2268 | chrome.exe | 104.21.47.203:443 | ww4.narutoget.ru | Cloudflare Inc | US | suspicious |
2268 | chrome.exe | 142.250.184.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2268 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2268 | chrome.exe | 104.21.82.130:443 | cdn.burstupload.com | Cloudflare Inc | US | suspicious |
2268 | chrome.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
2268 | chrome.exe | 151.139.128.11:443 | assets.revcontent.com | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ww4.narutoget.ru |
| suspicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
cdn.burstupload.com |
| suspicious |
i.imgur.com |
| malicious |
assets.revcontent.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.animebam.se |
| unknown |
trends.revcontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2268 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2268 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |