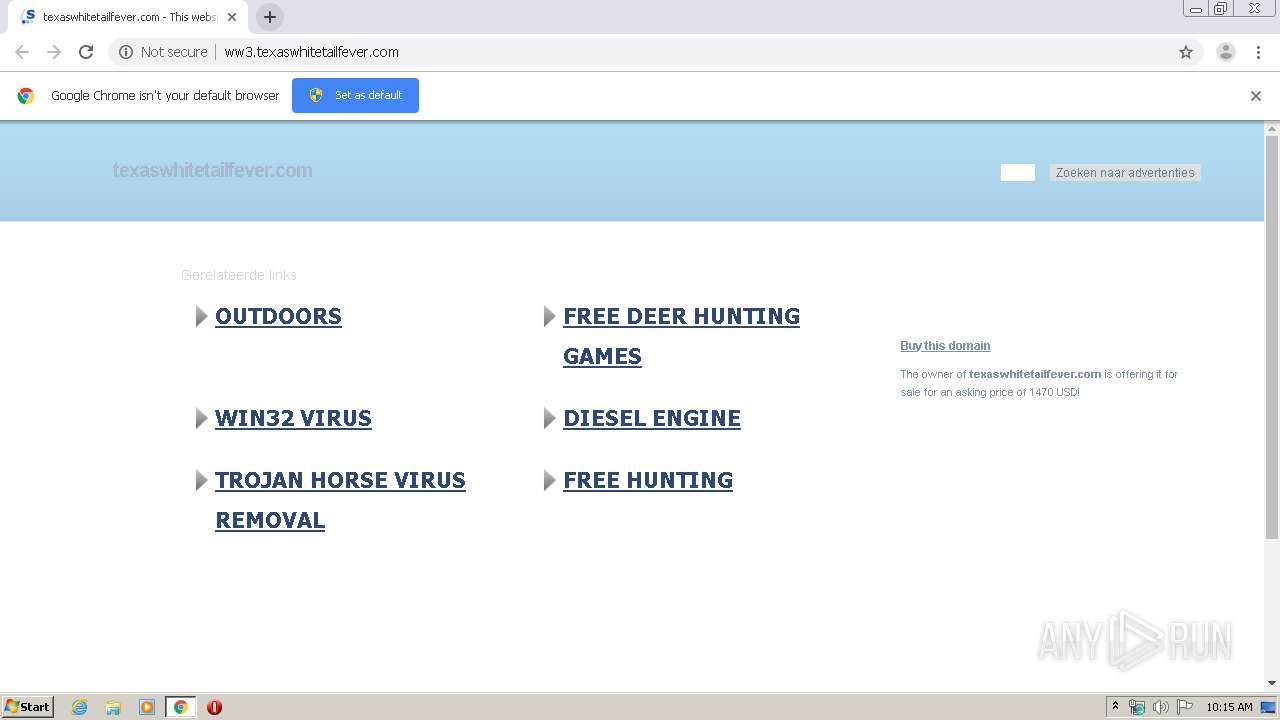
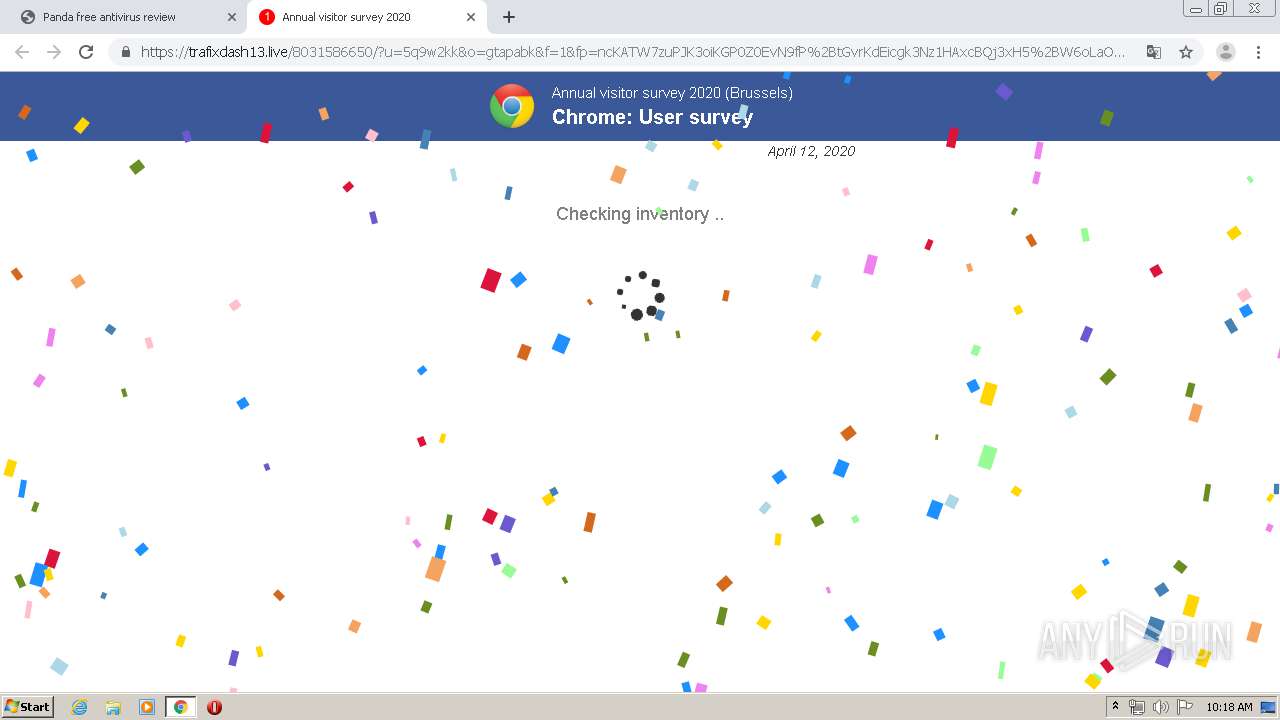
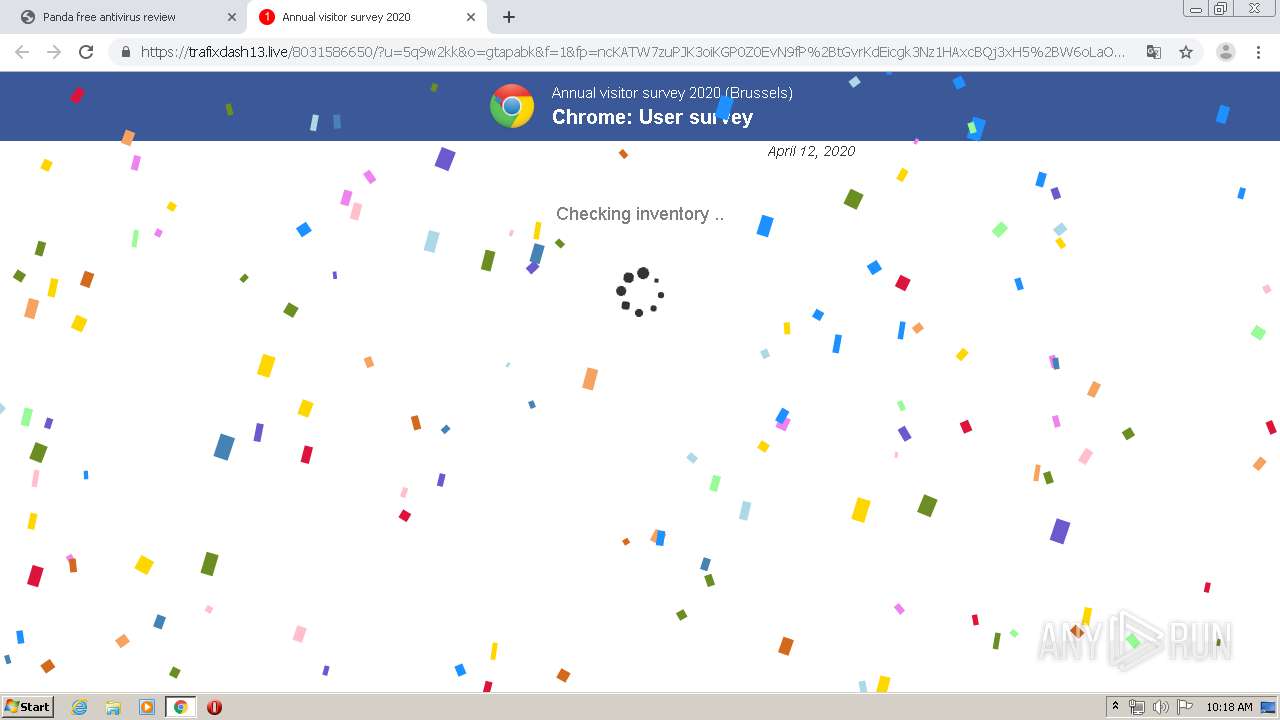
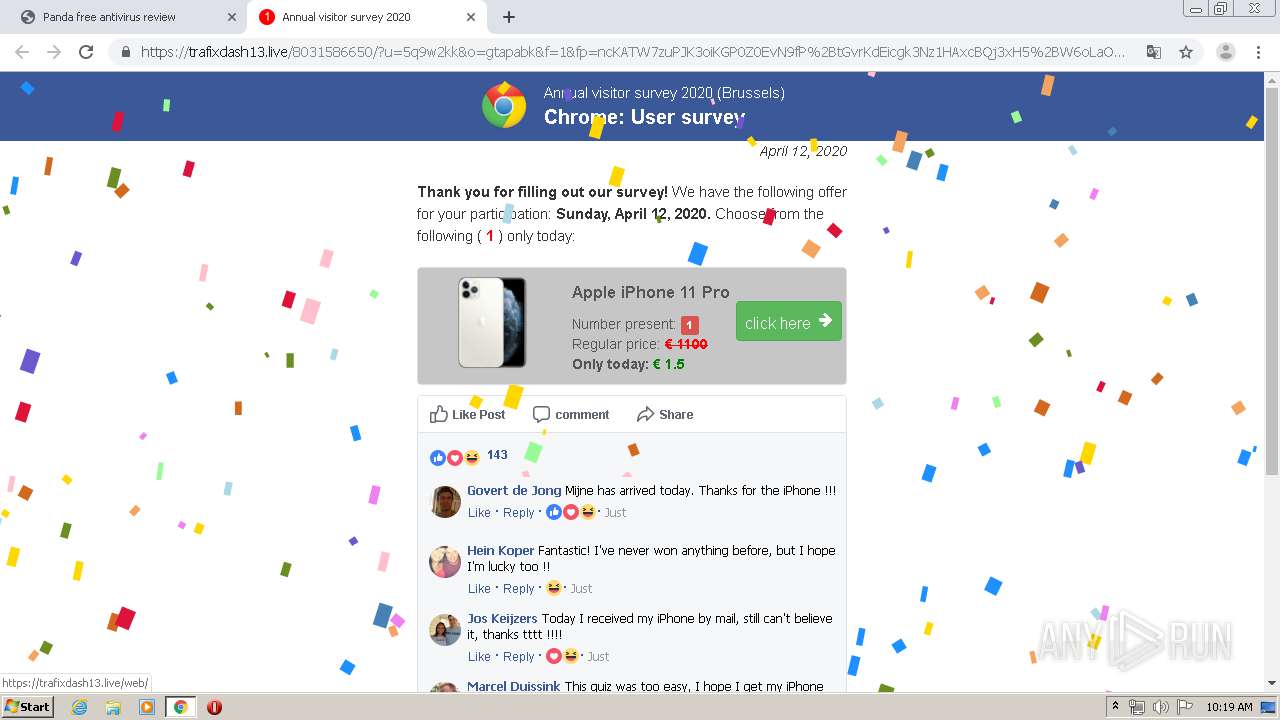
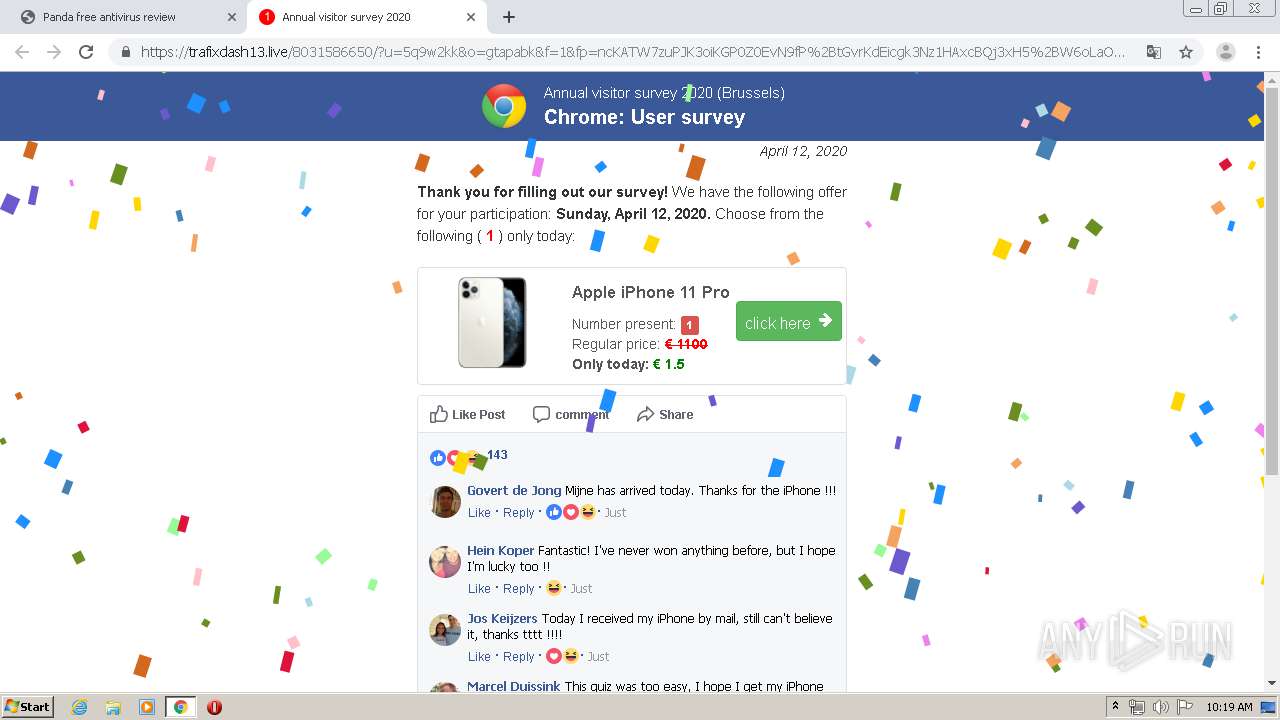
| URL: | http://texaswhitetailfever.com |
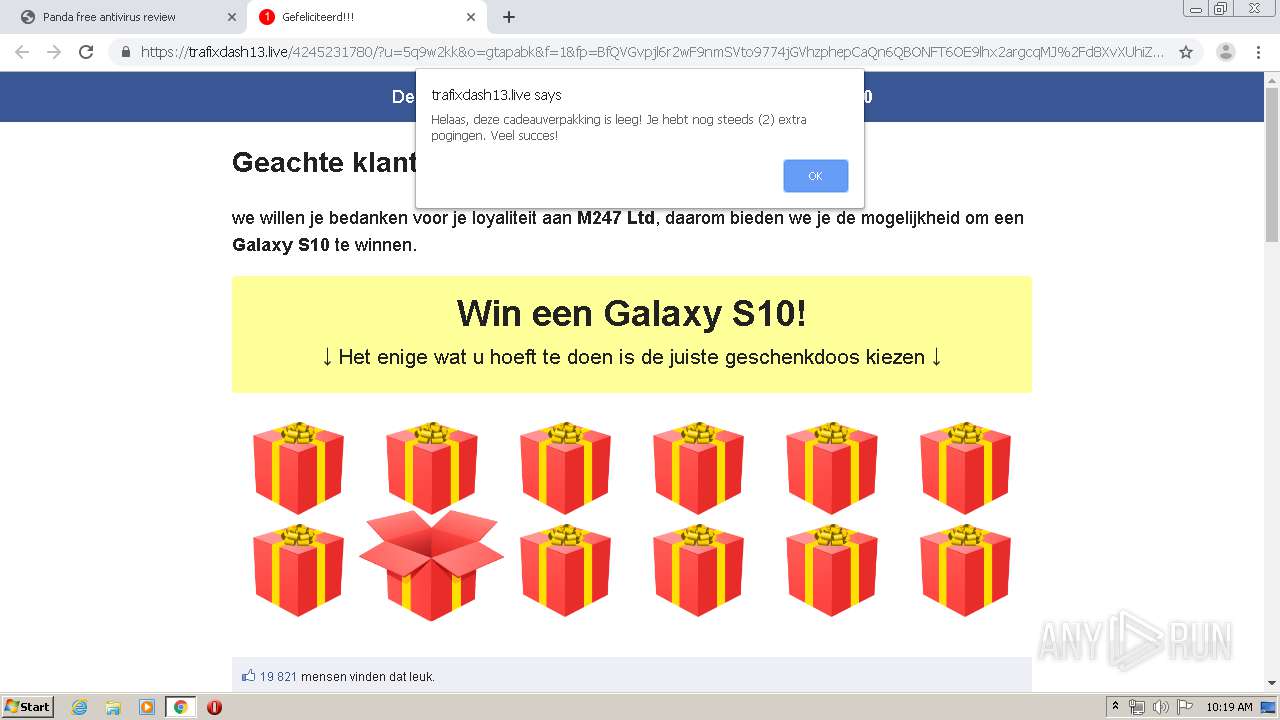
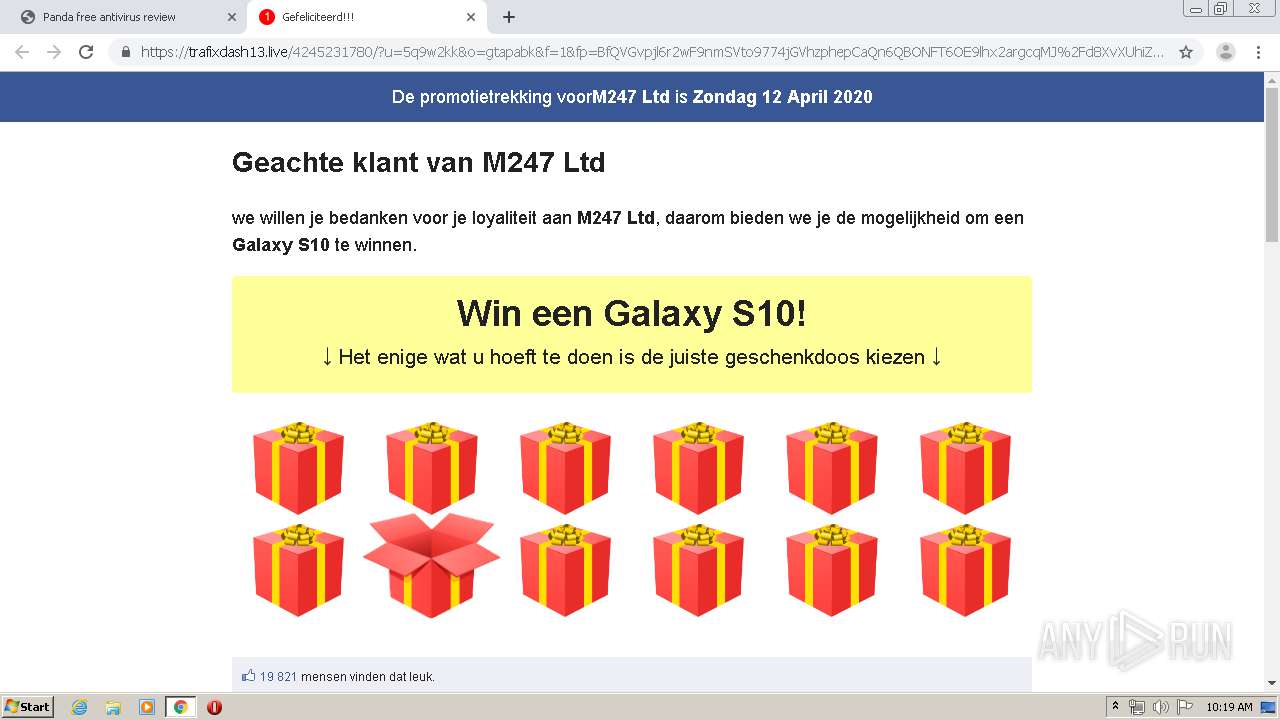
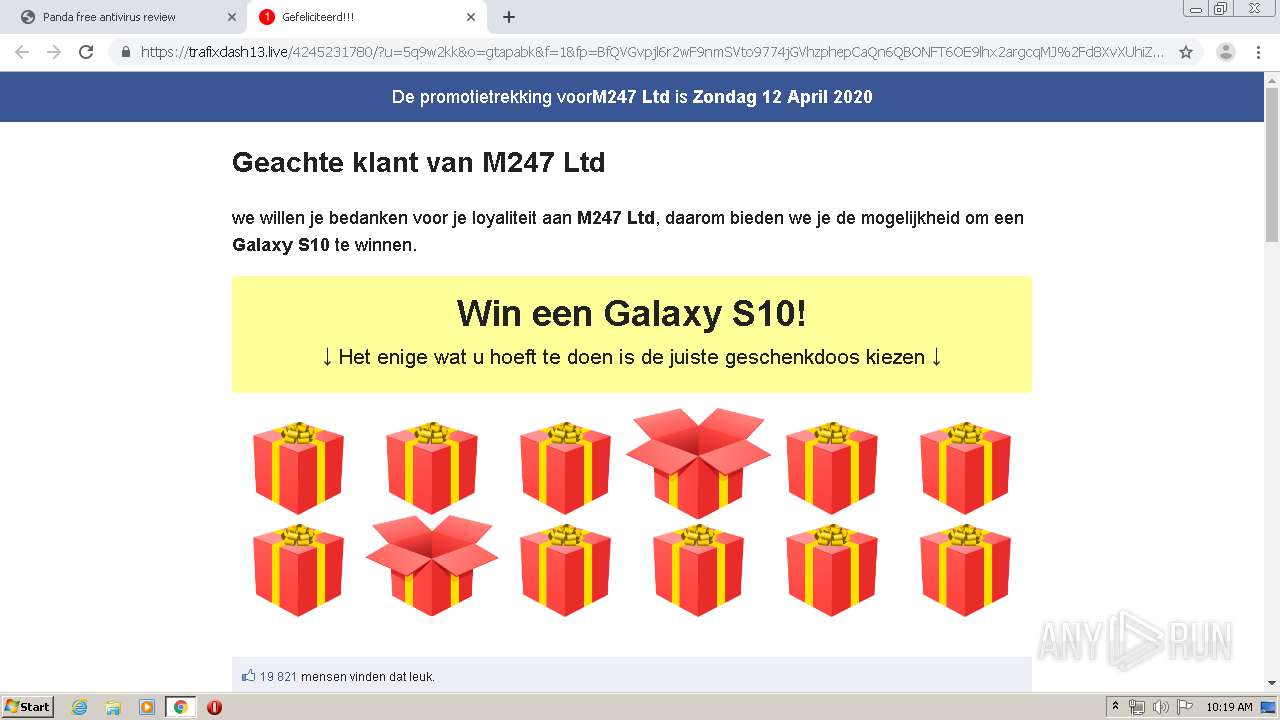
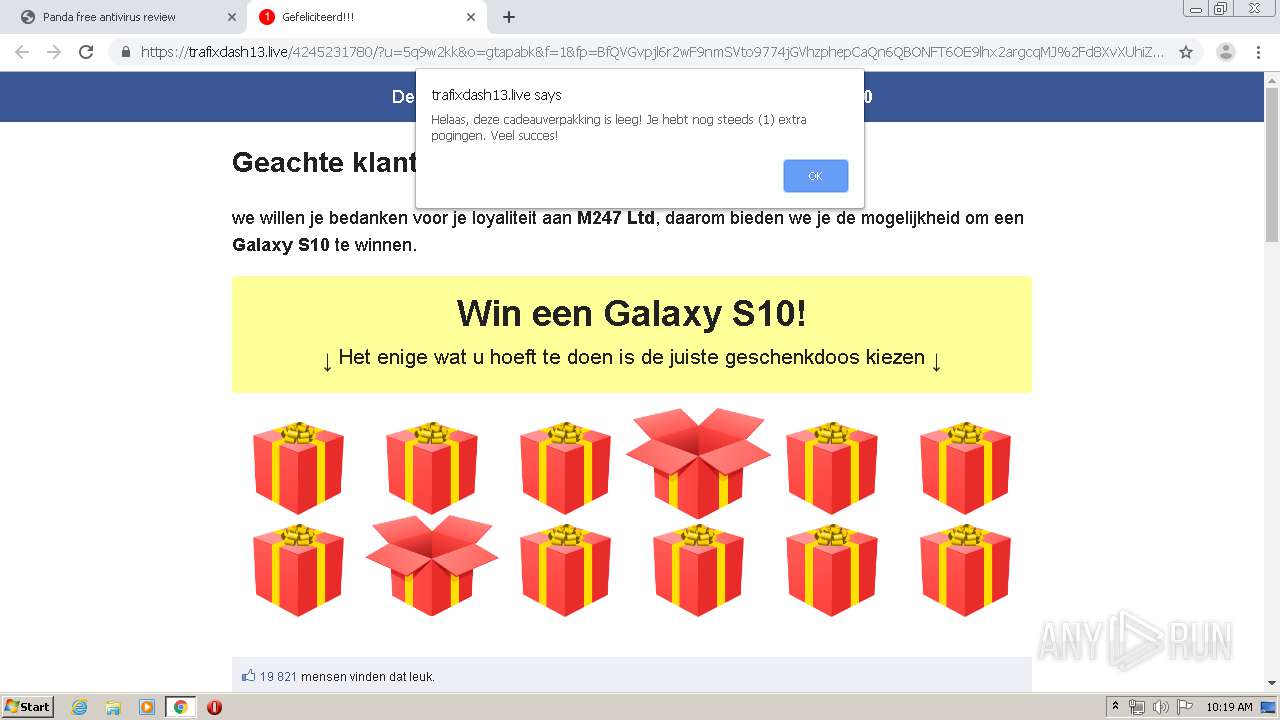
| Full analysis: | https://app.any.run/tasks/0ac36723-3f56-4a47-b778-e9408af05b0c |
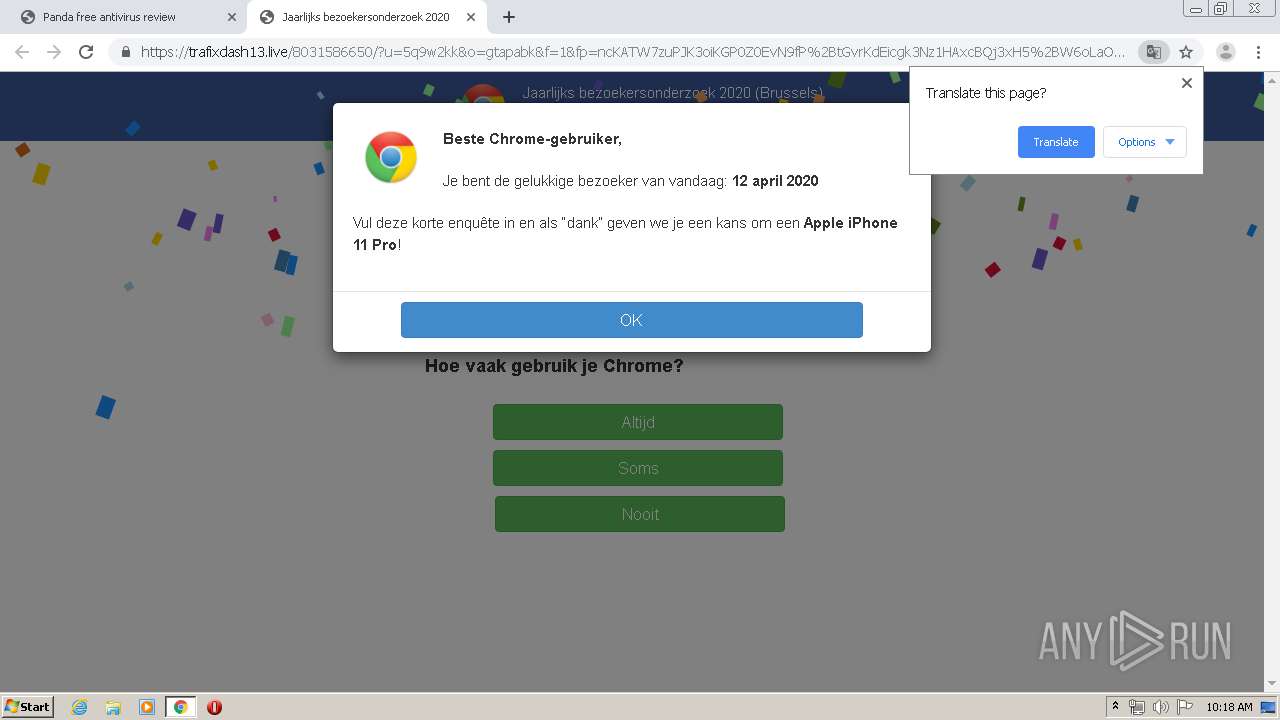
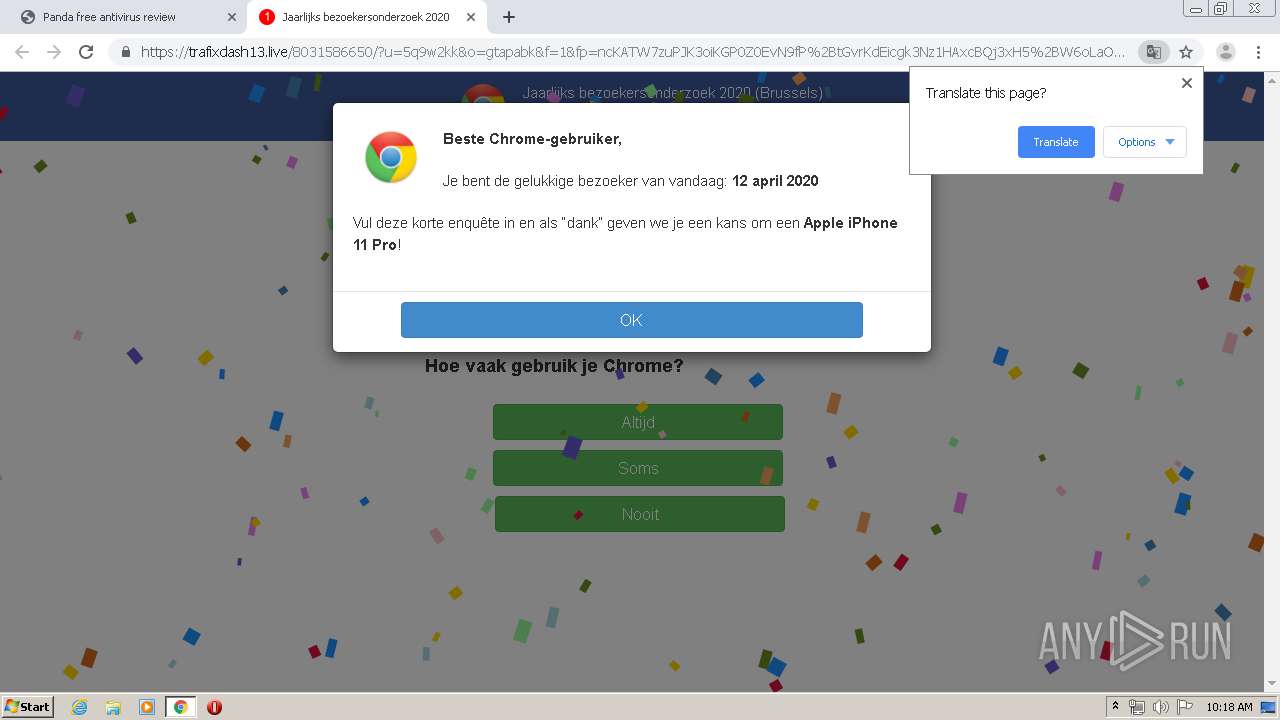
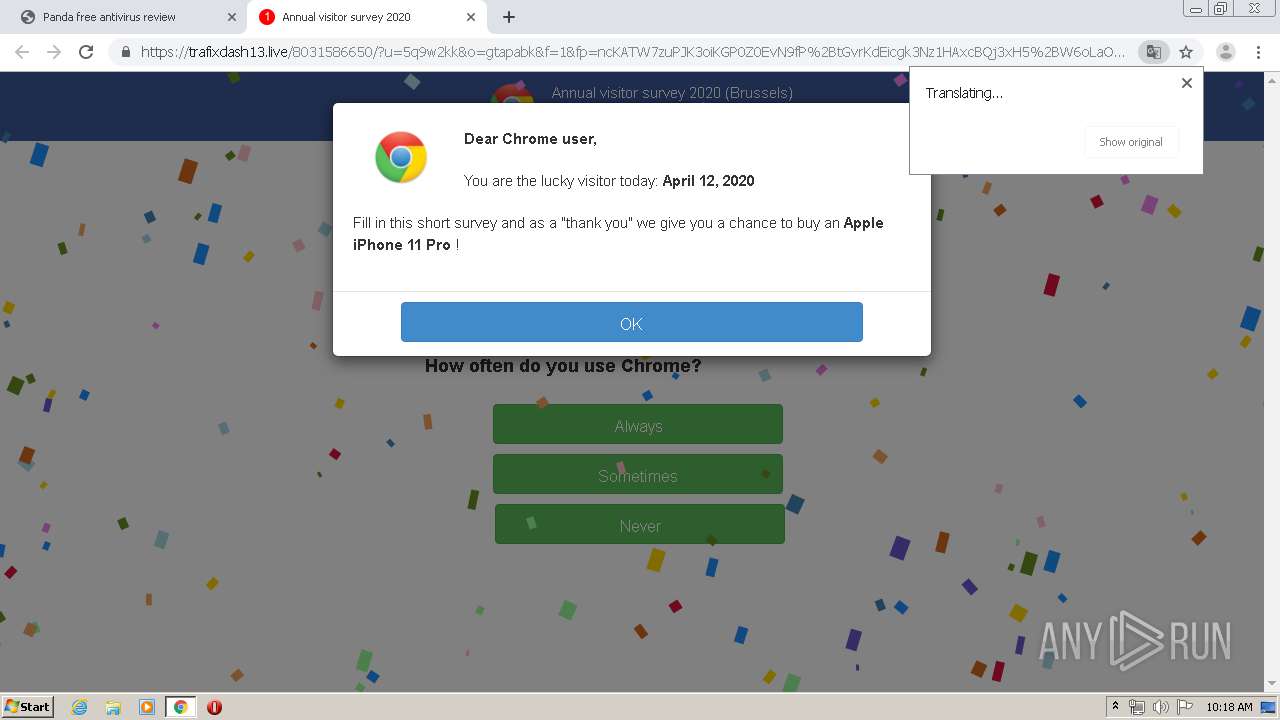
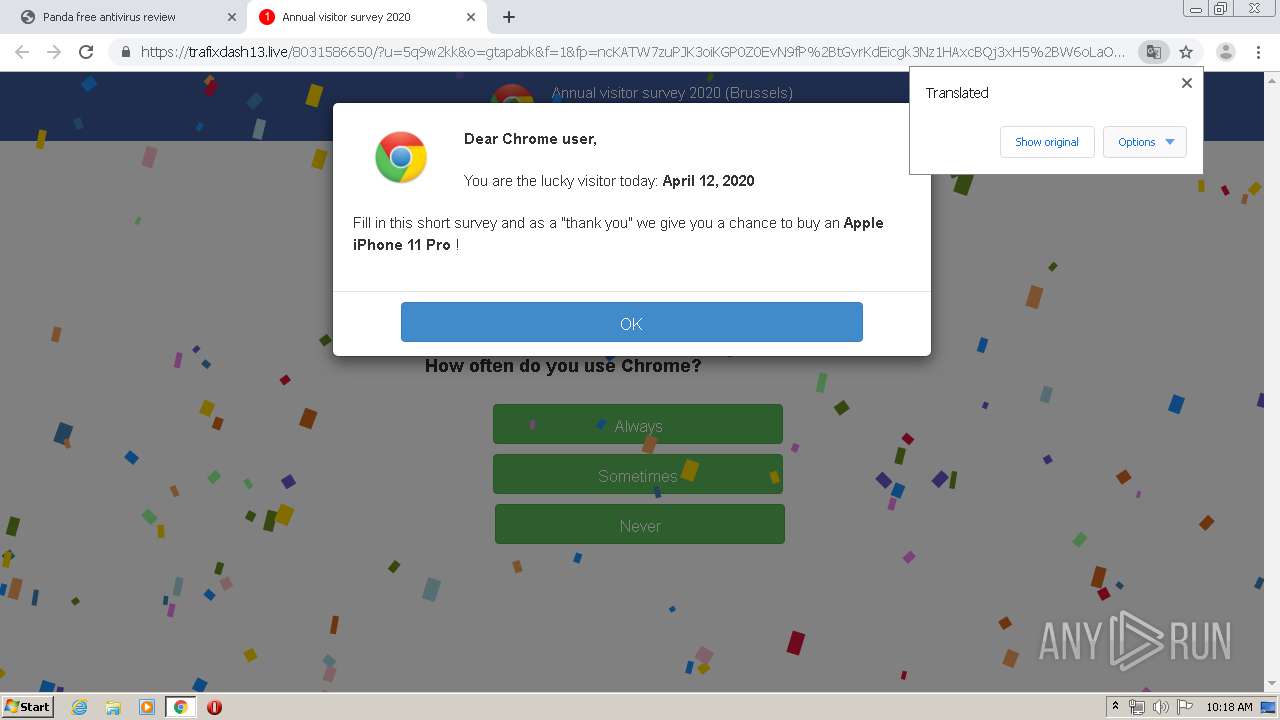
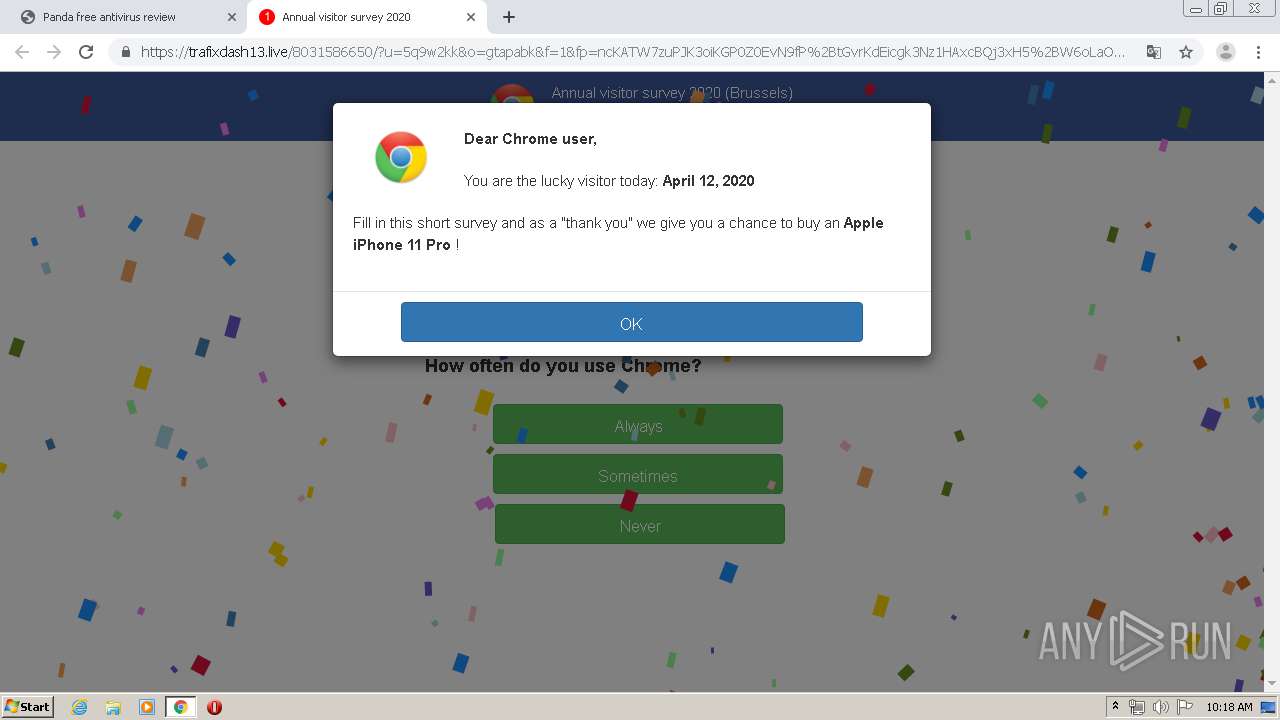
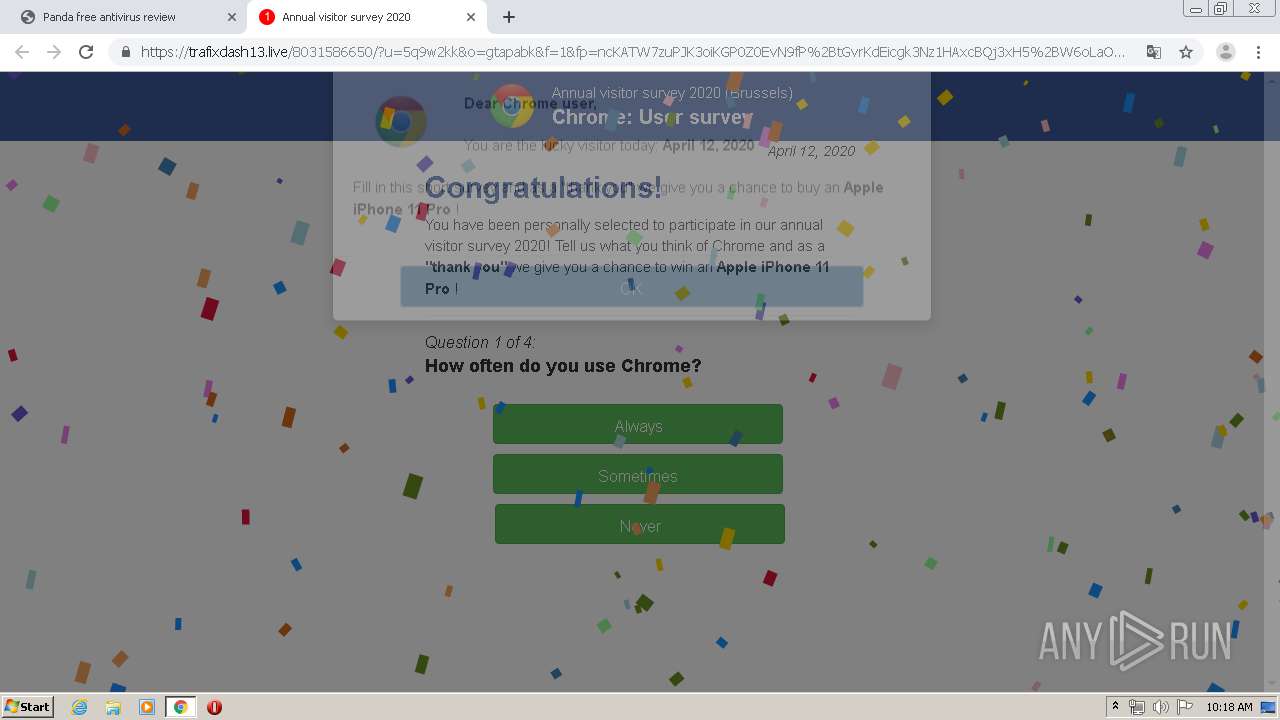
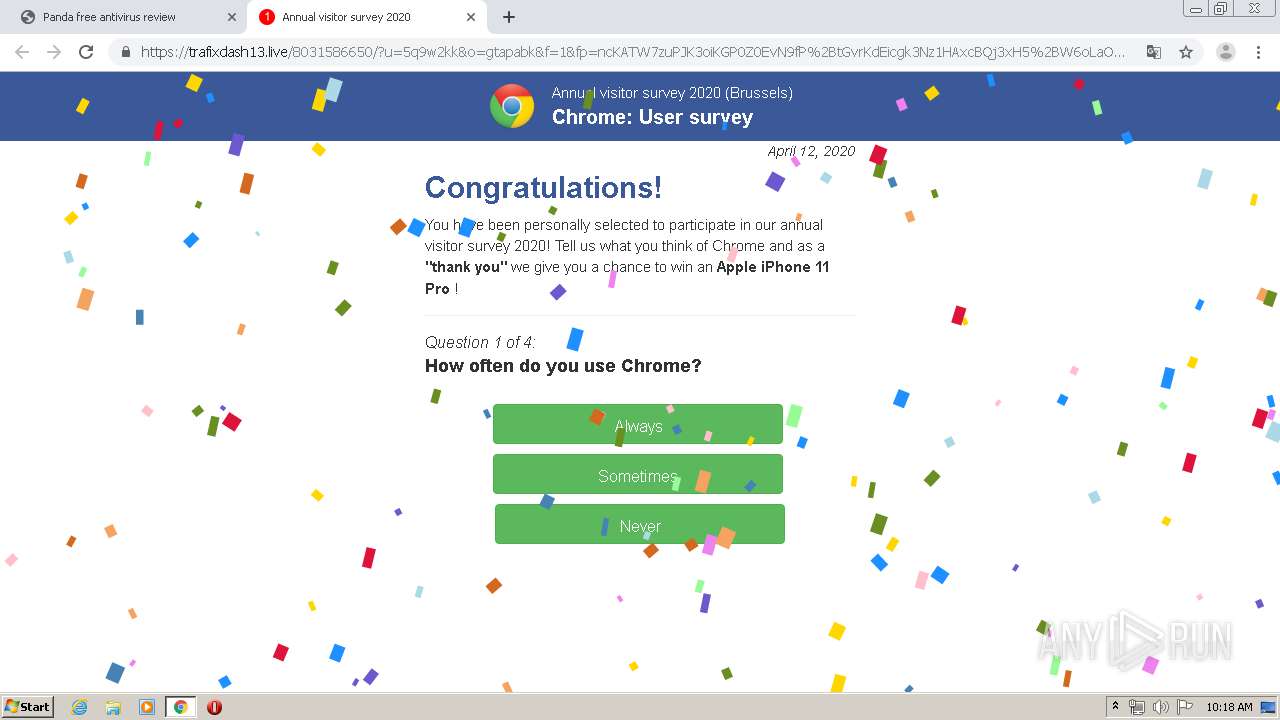
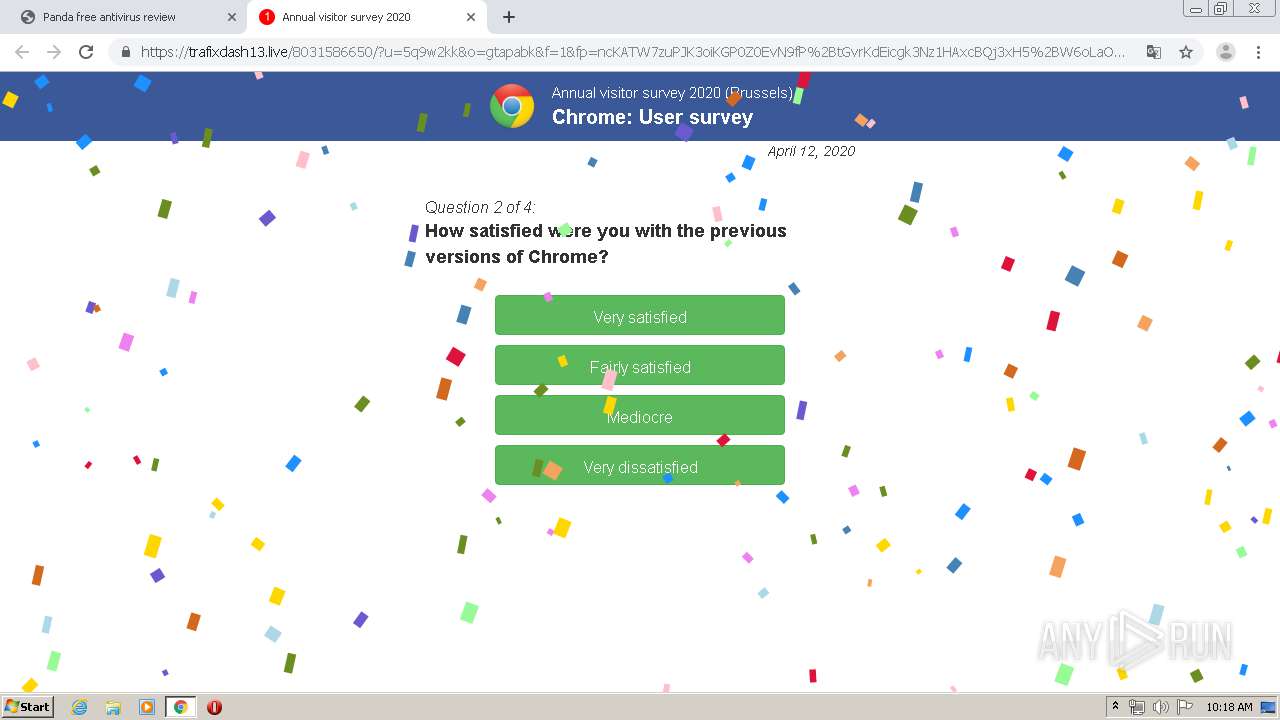
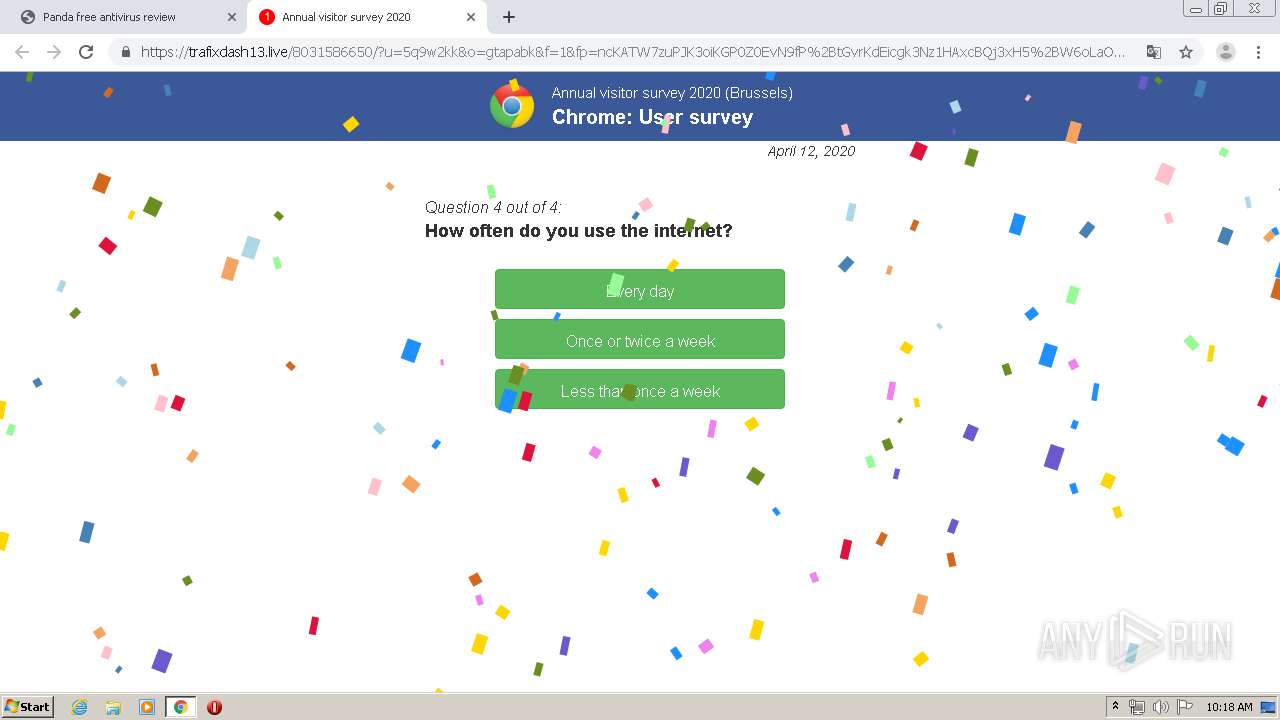
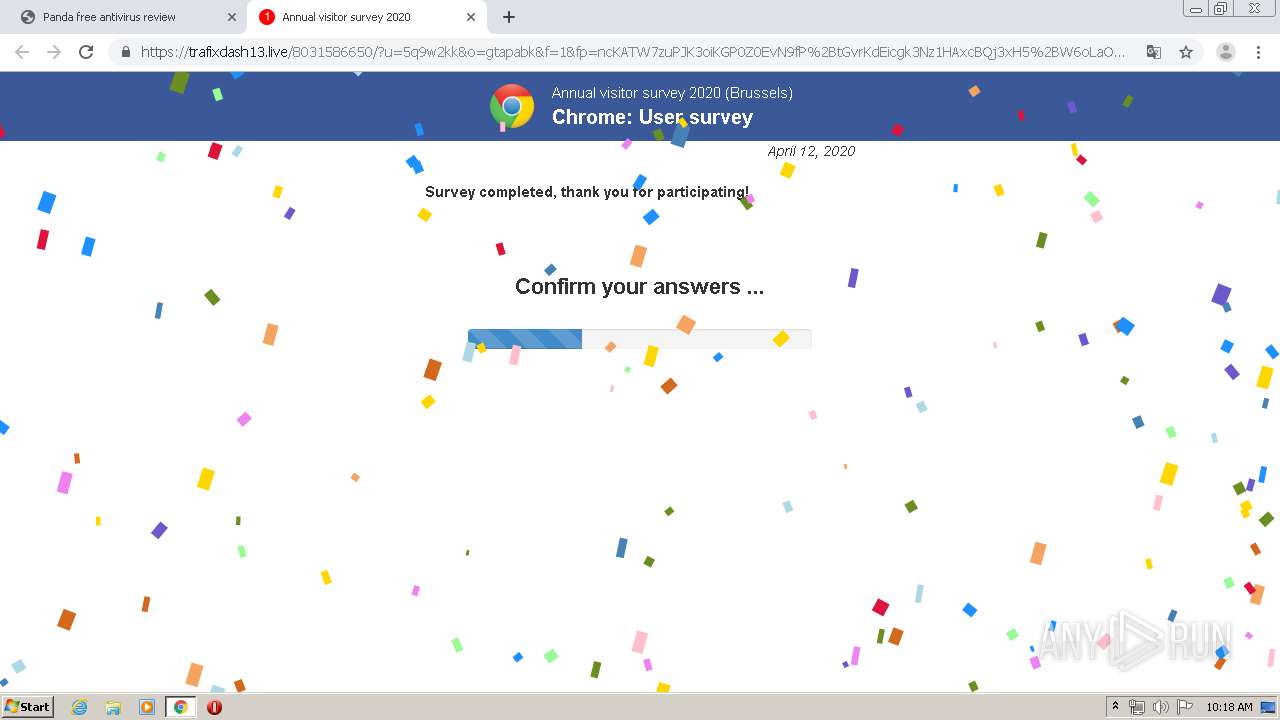
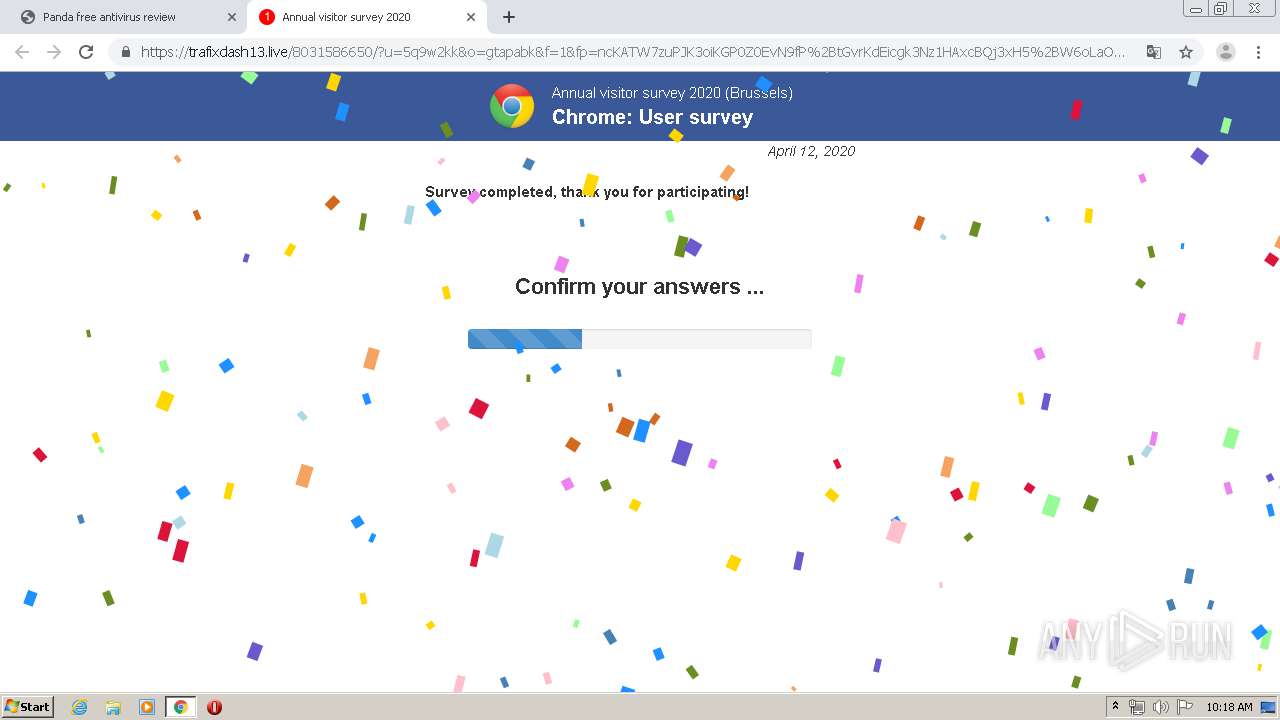
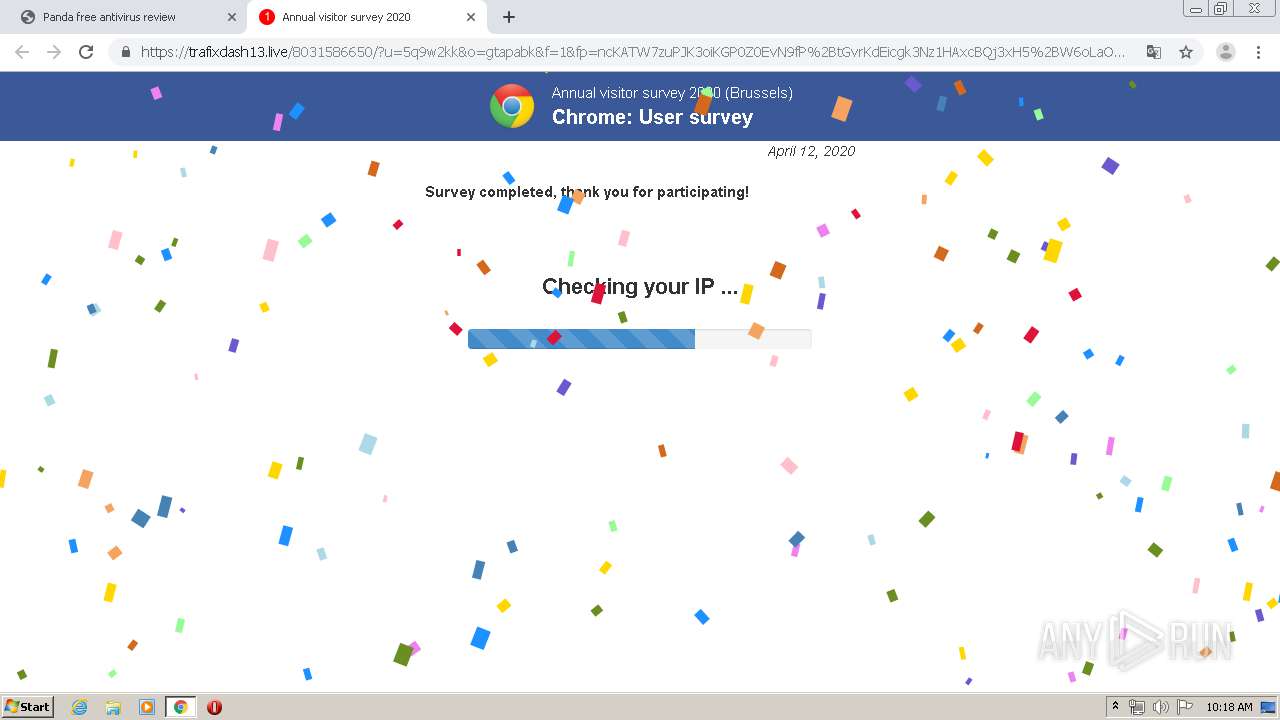
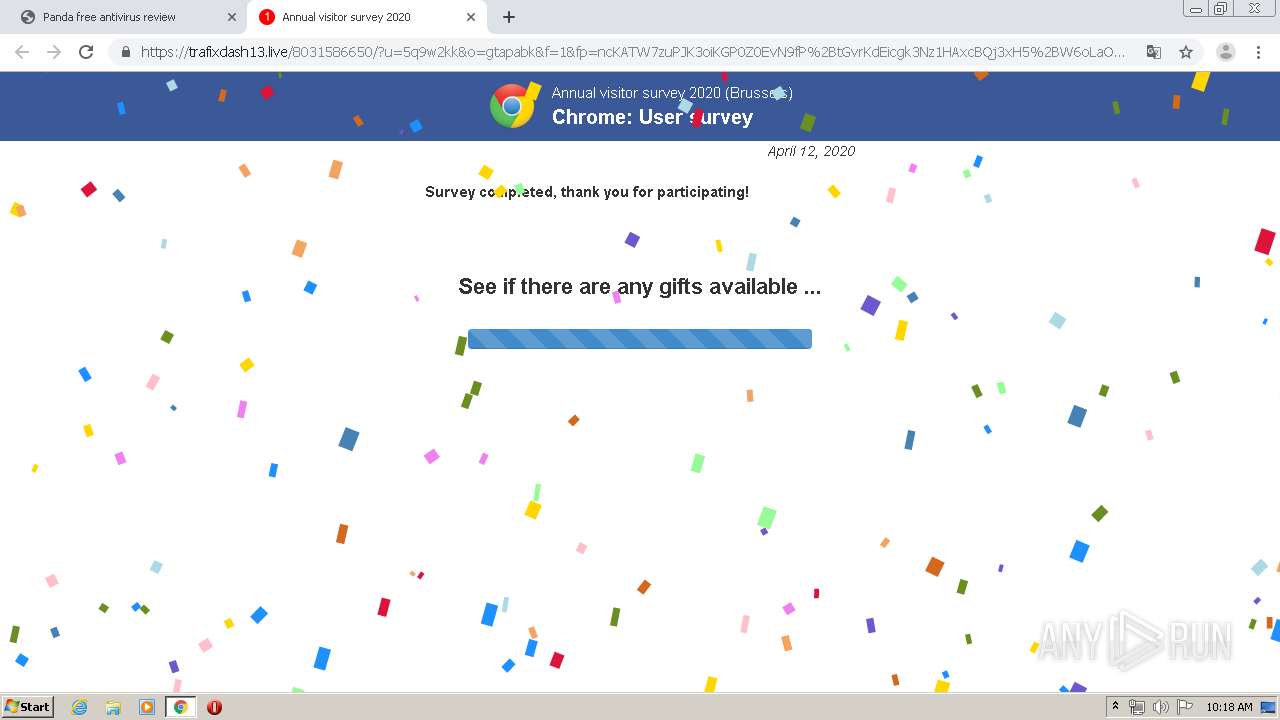
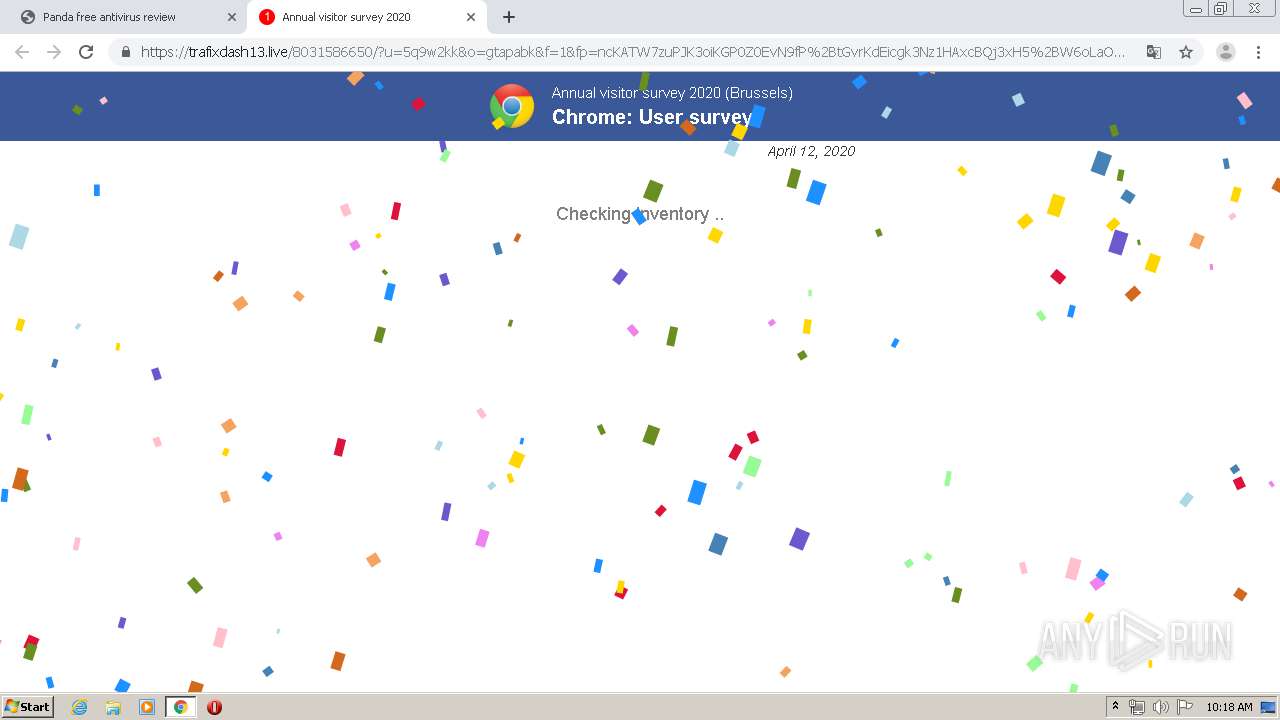
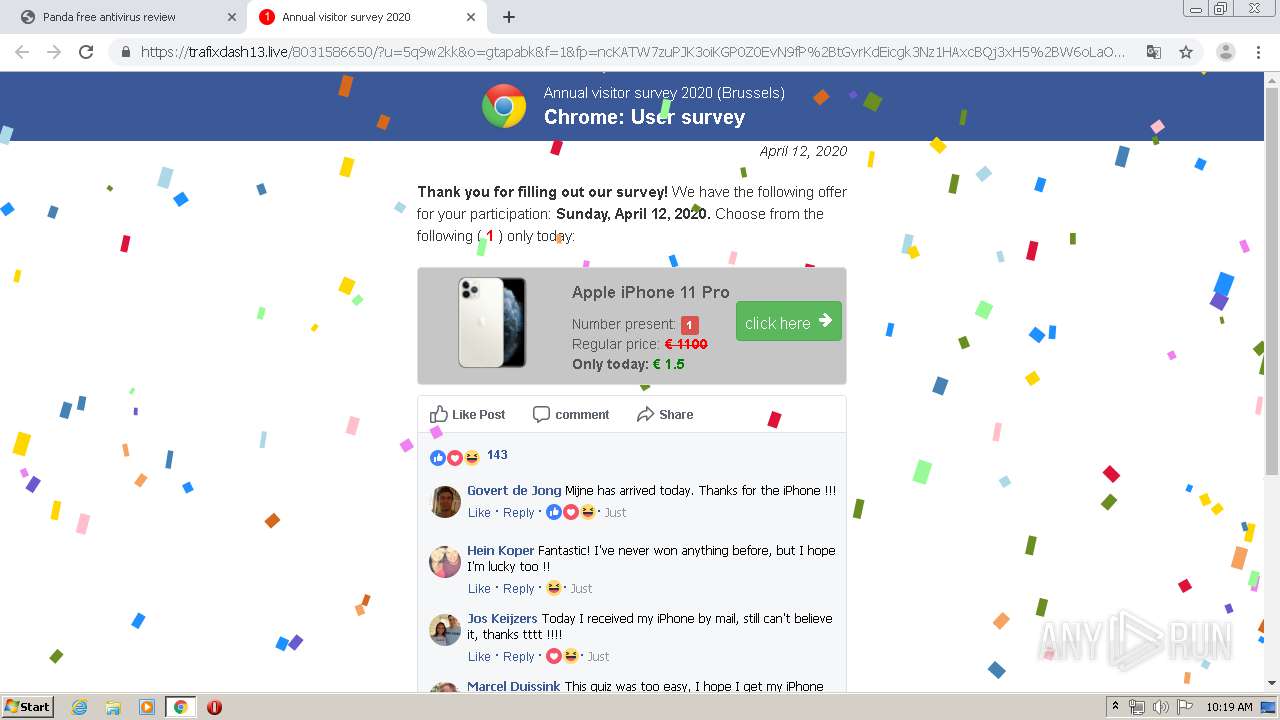
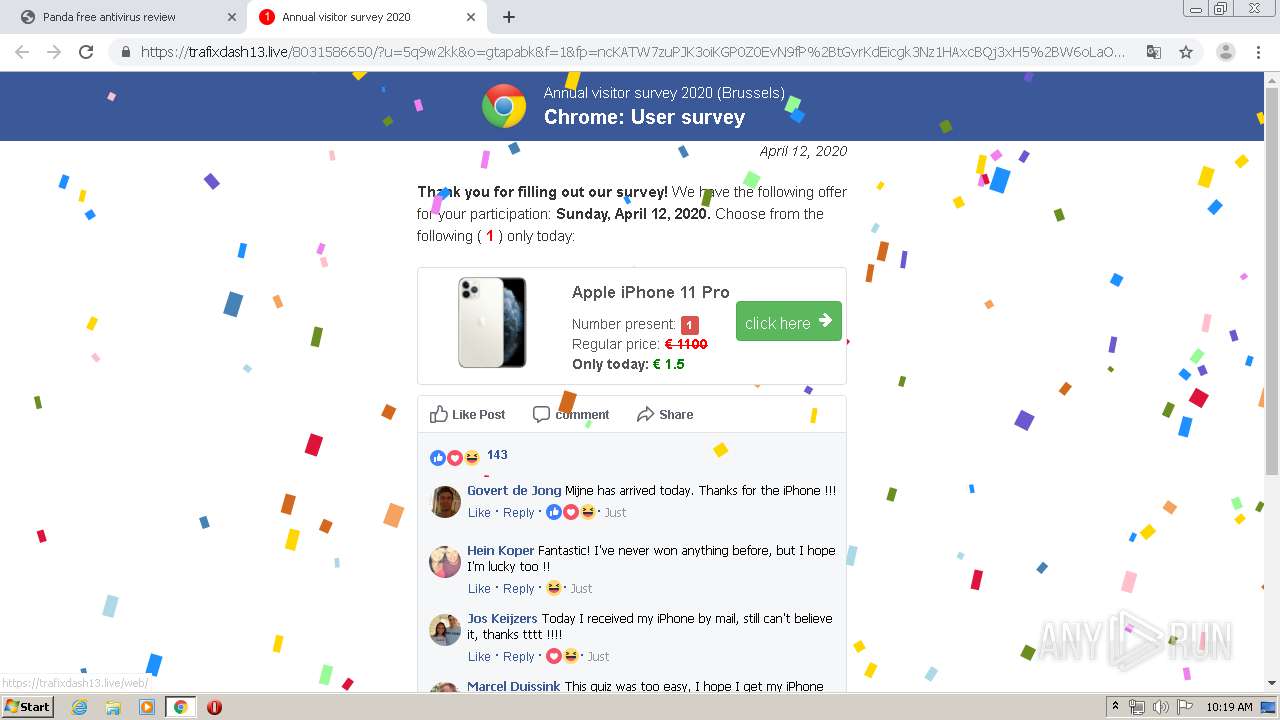
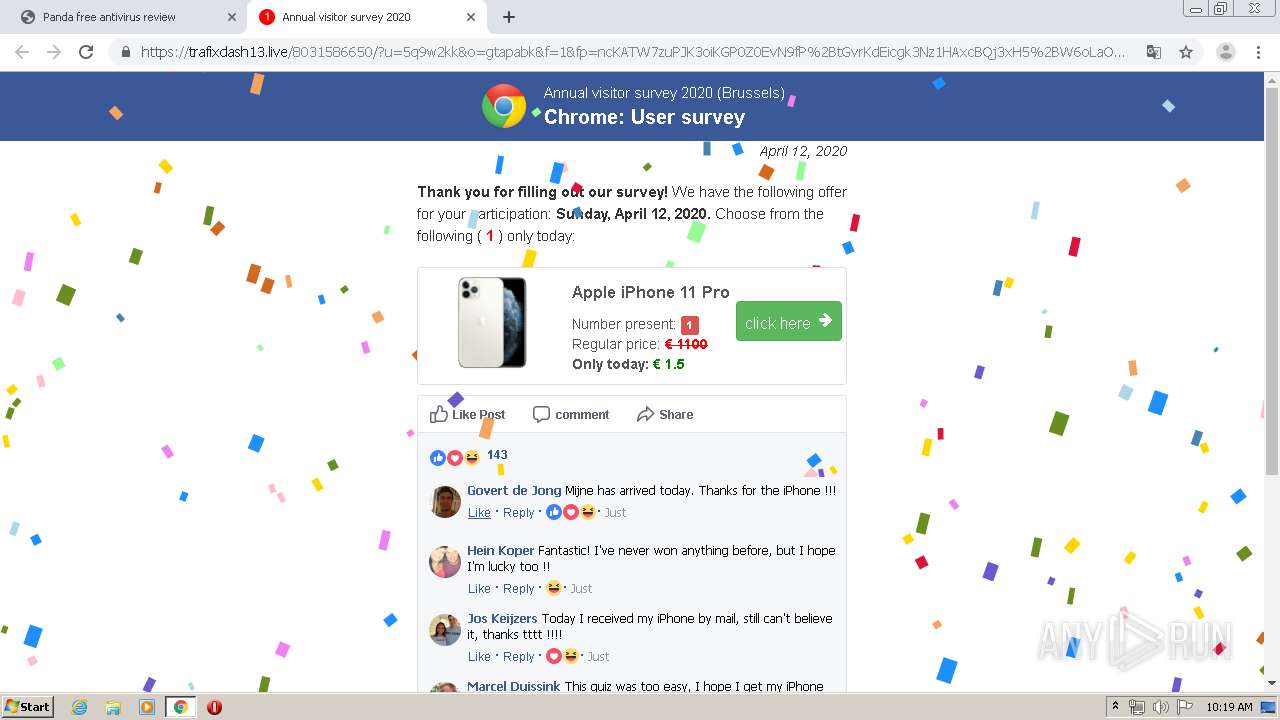
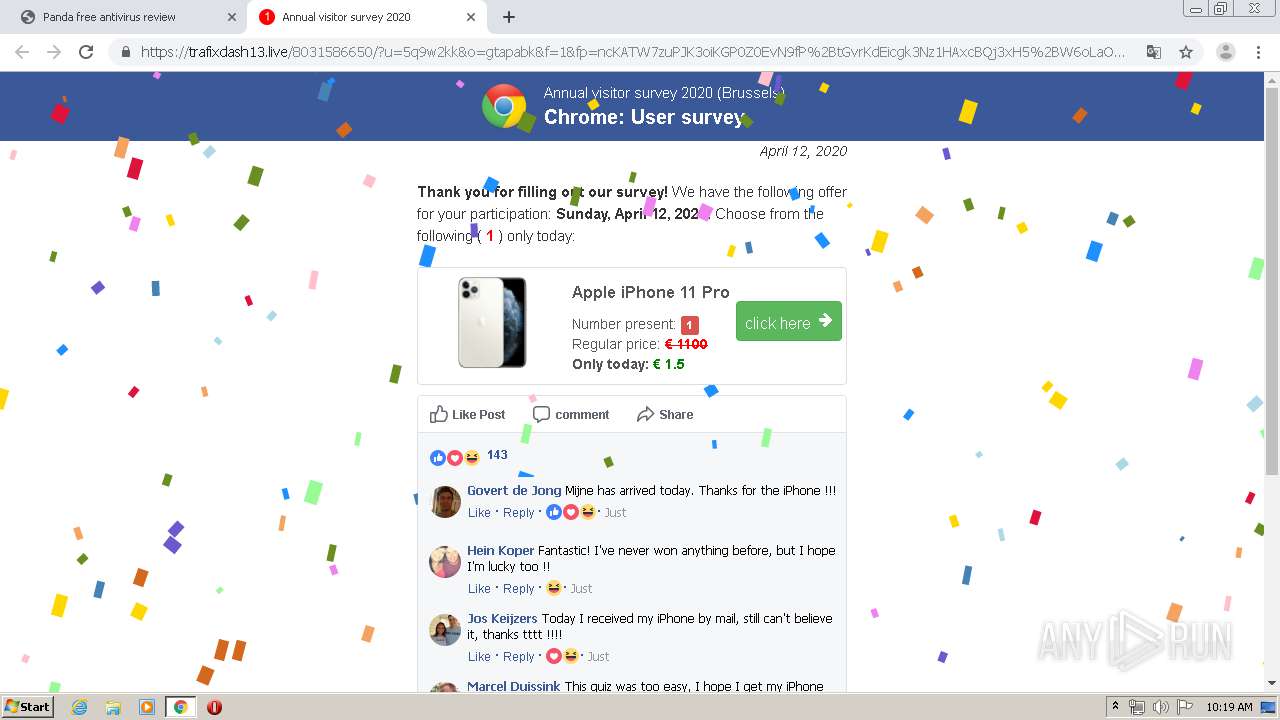
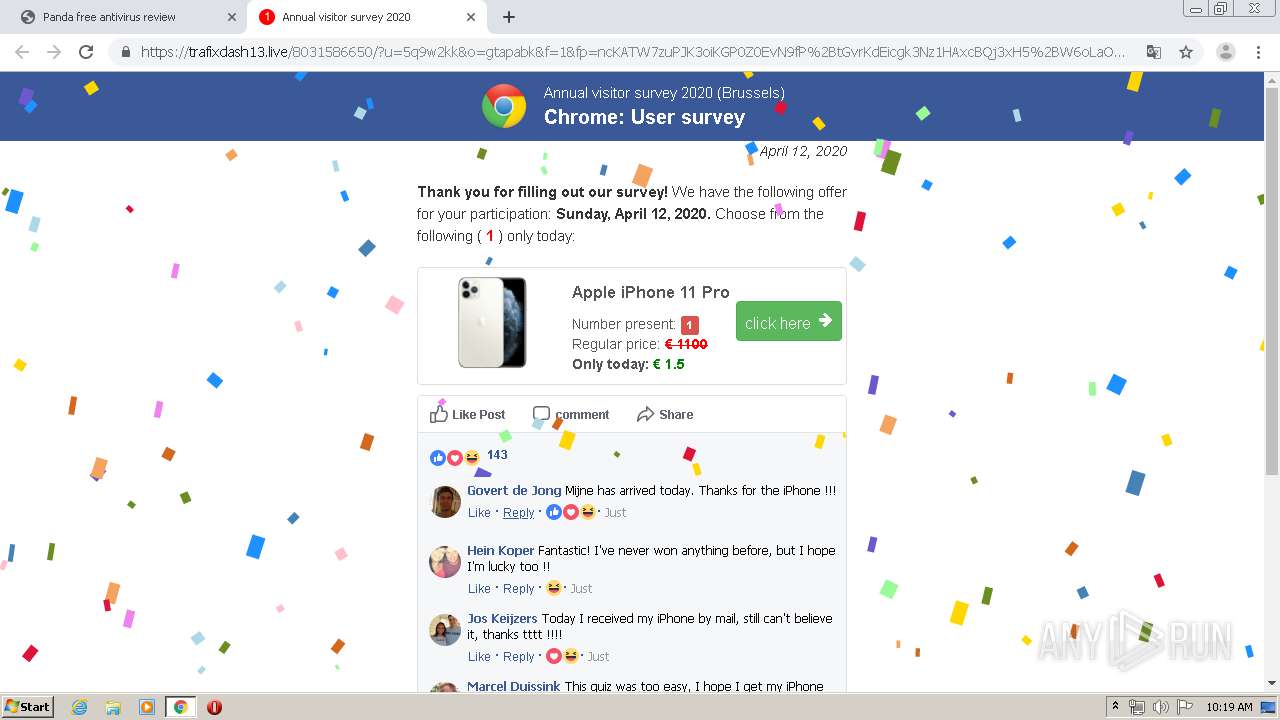
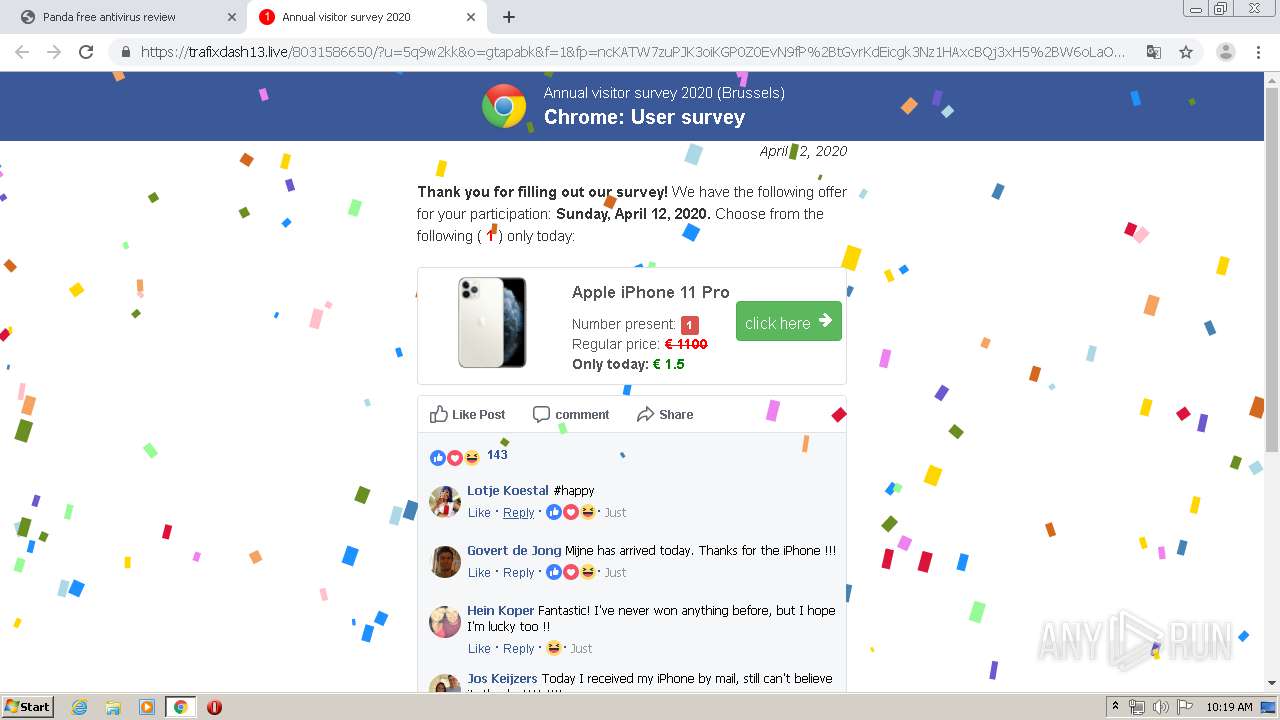
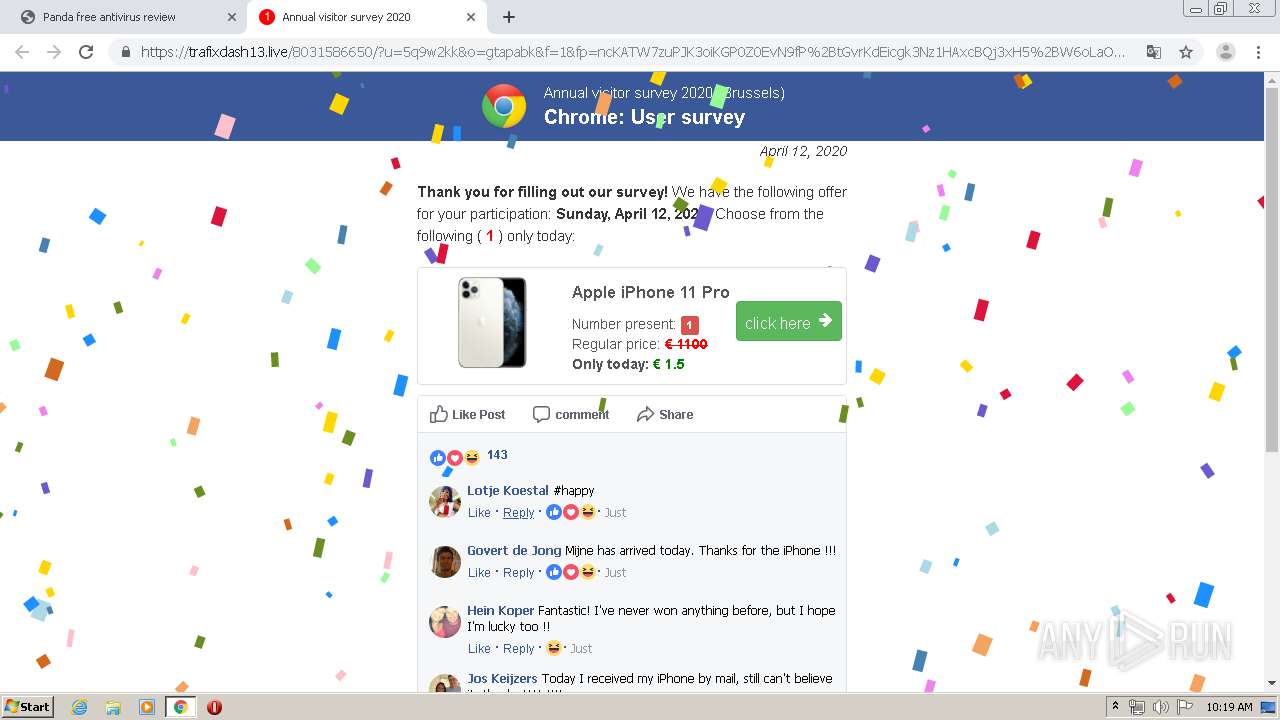
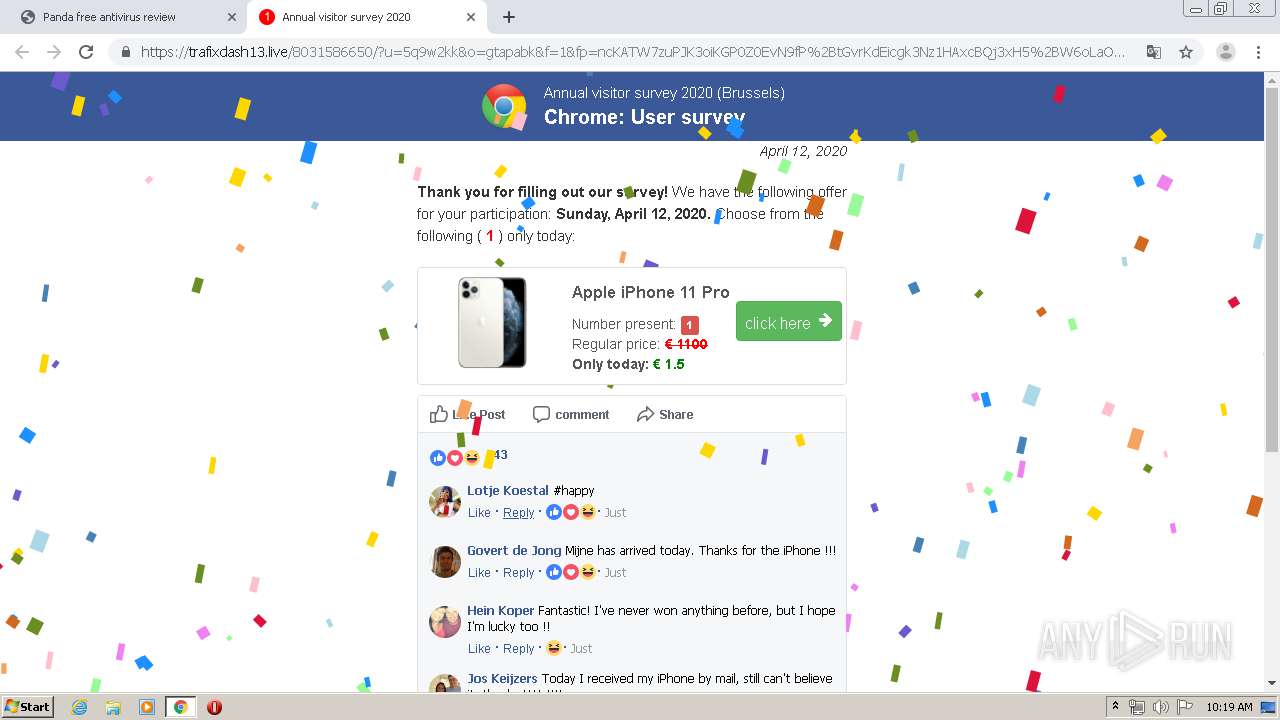
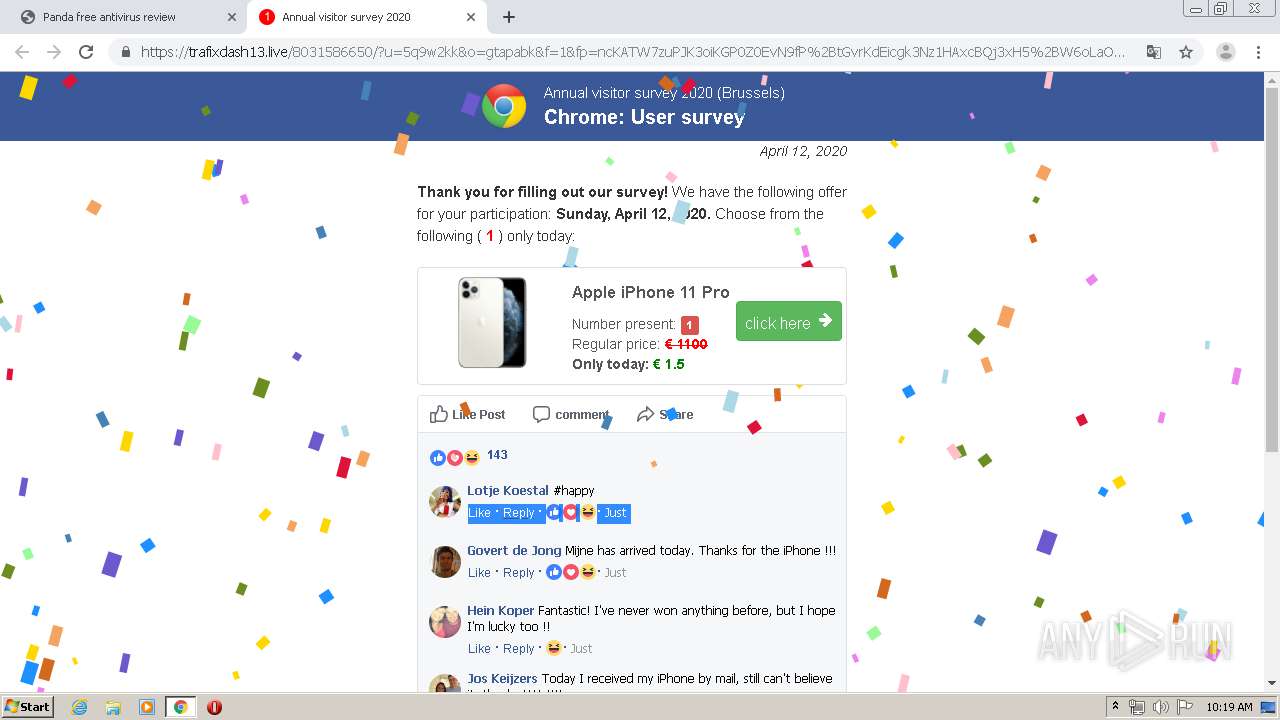
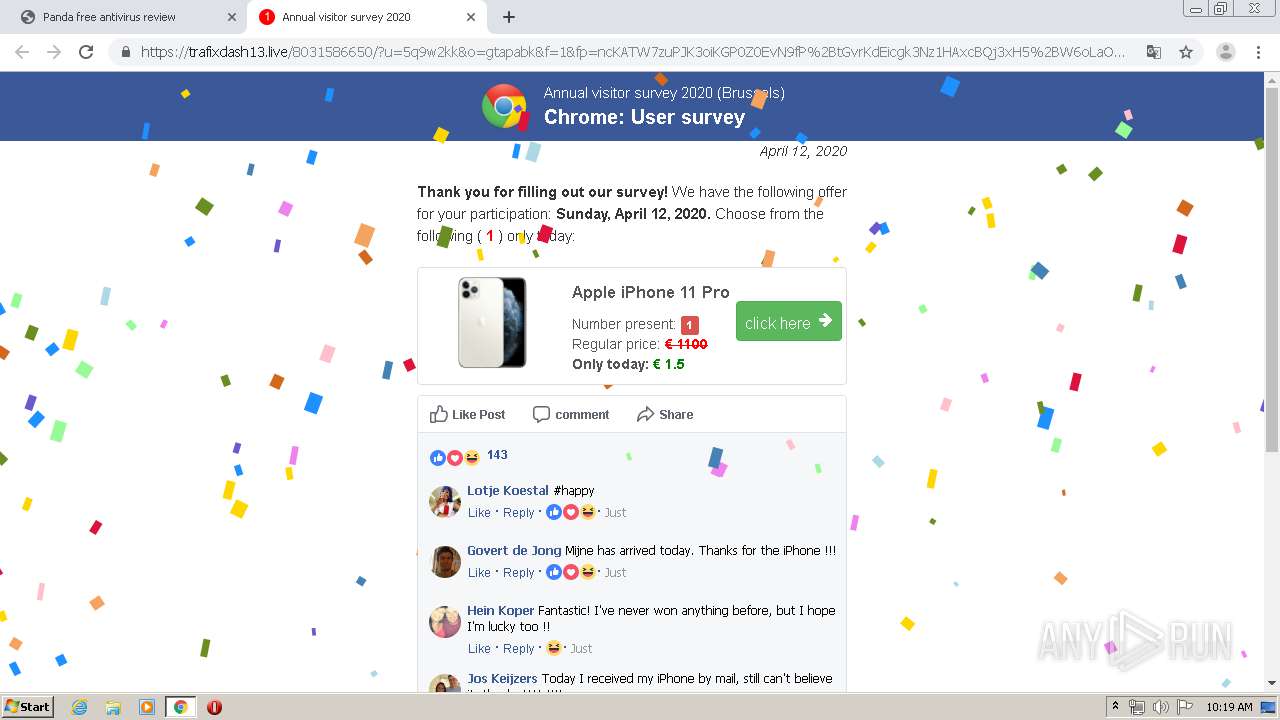
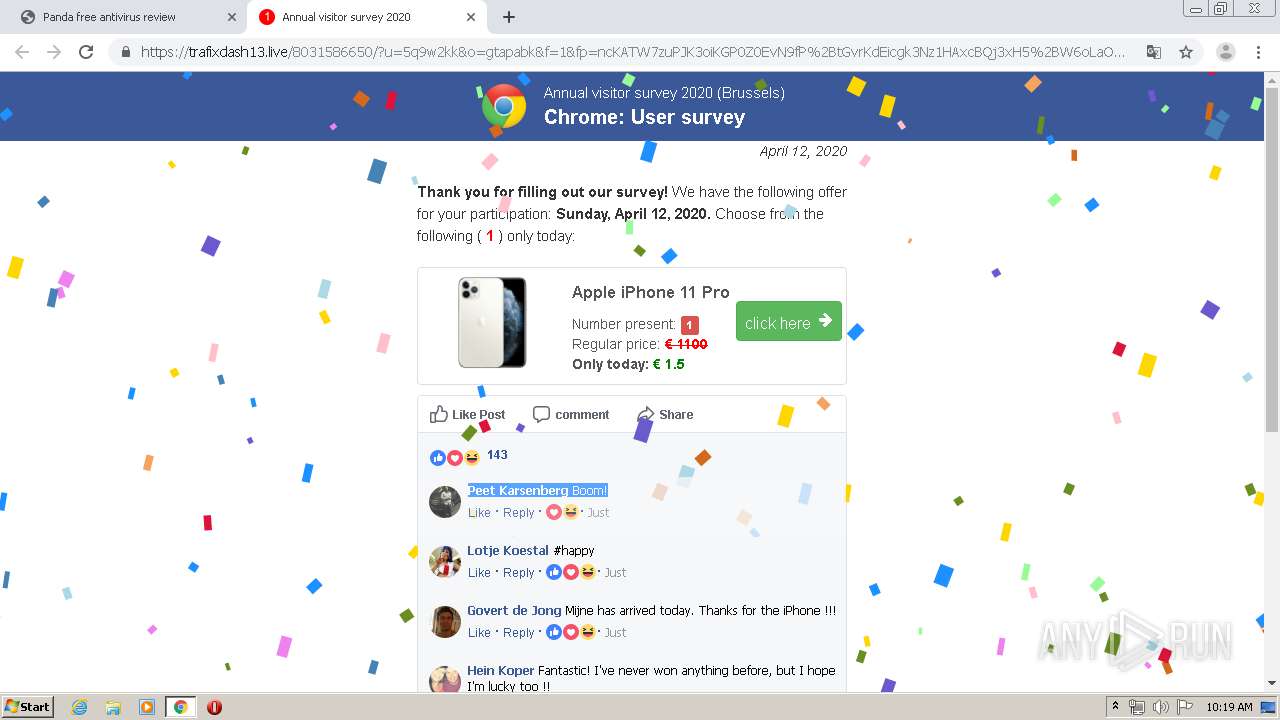
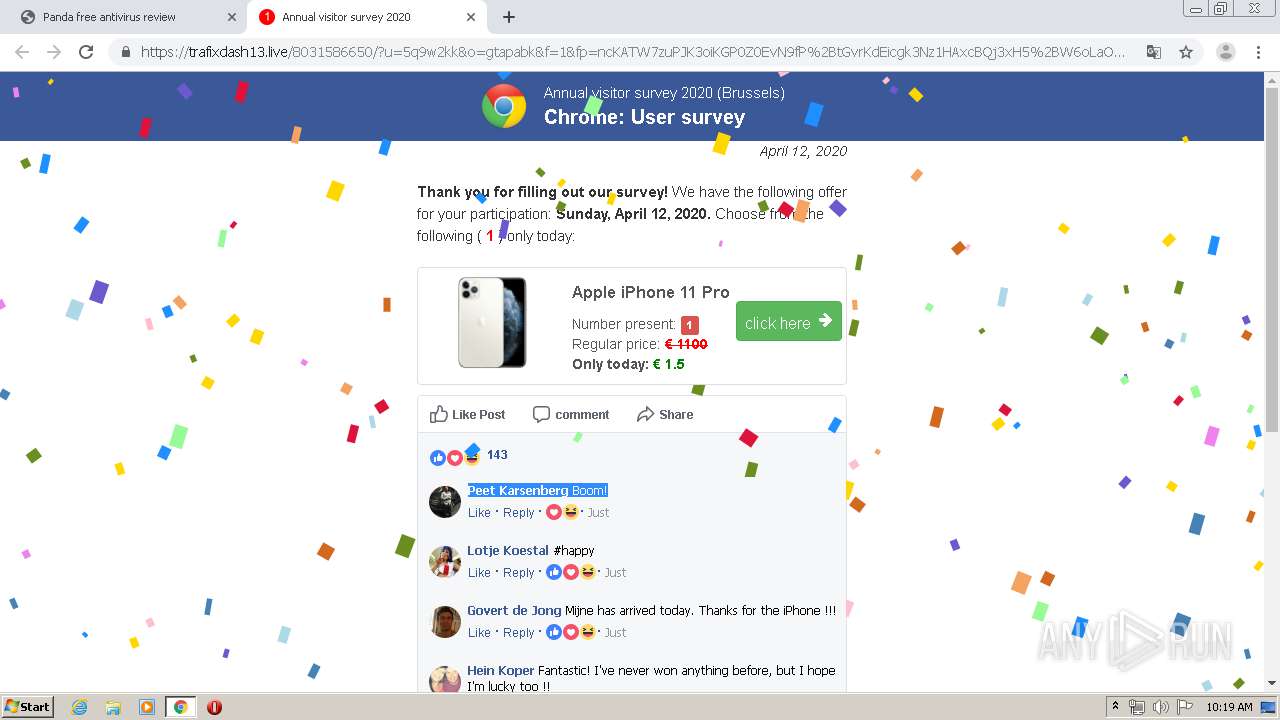
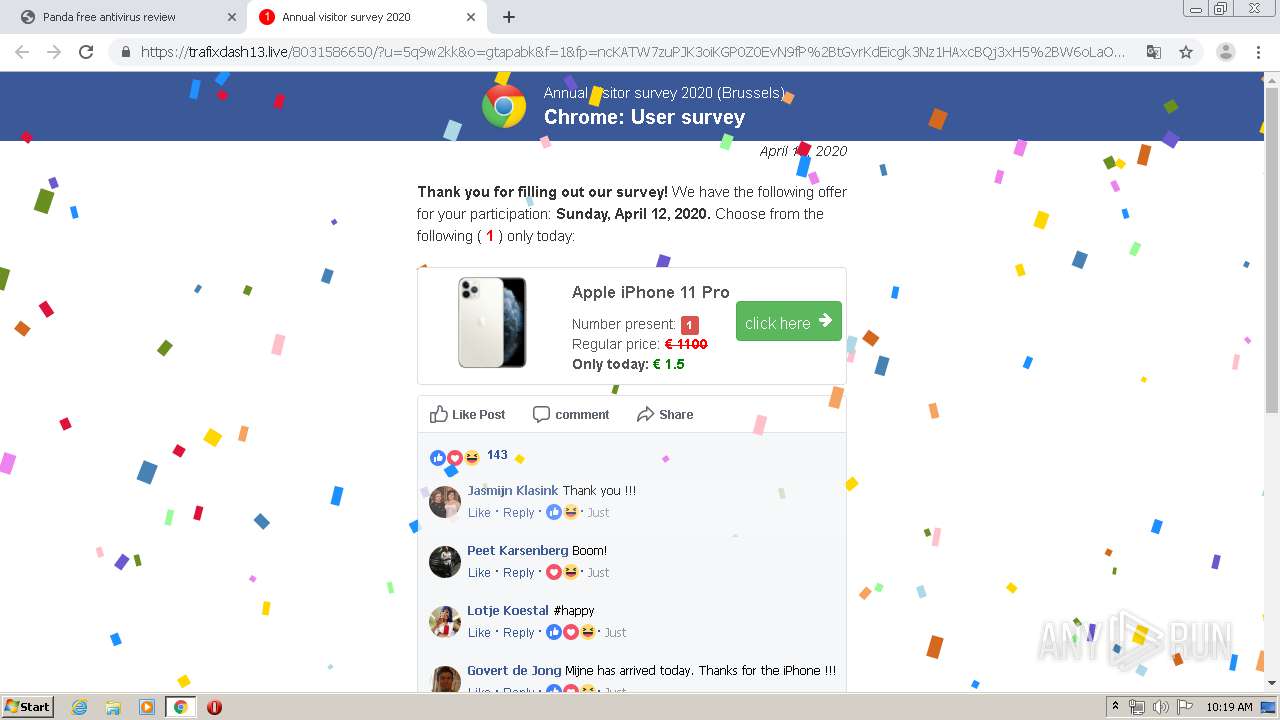
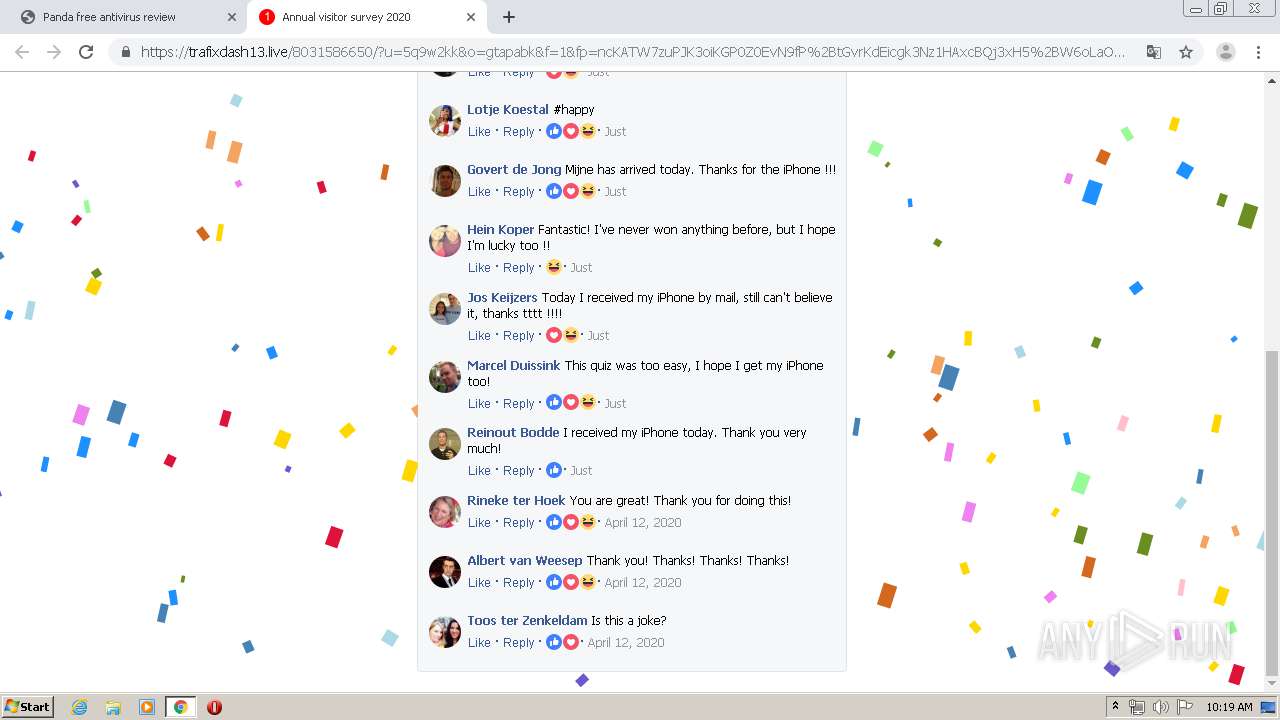
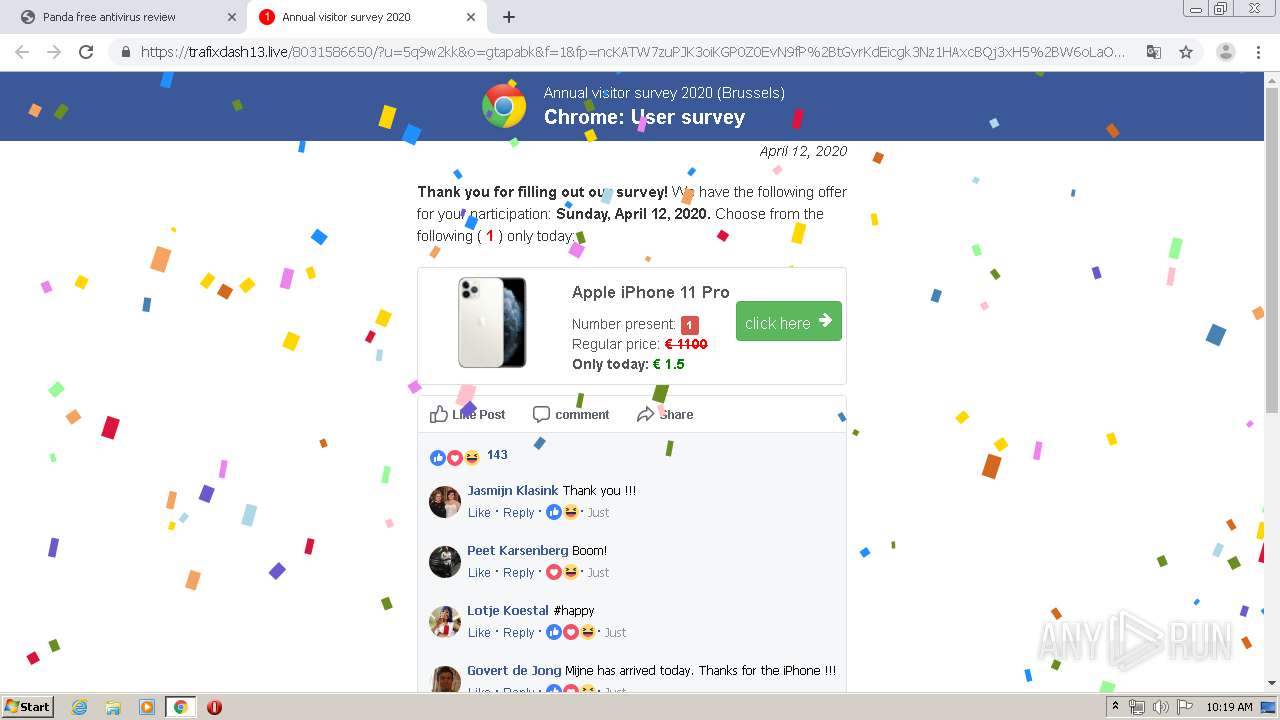
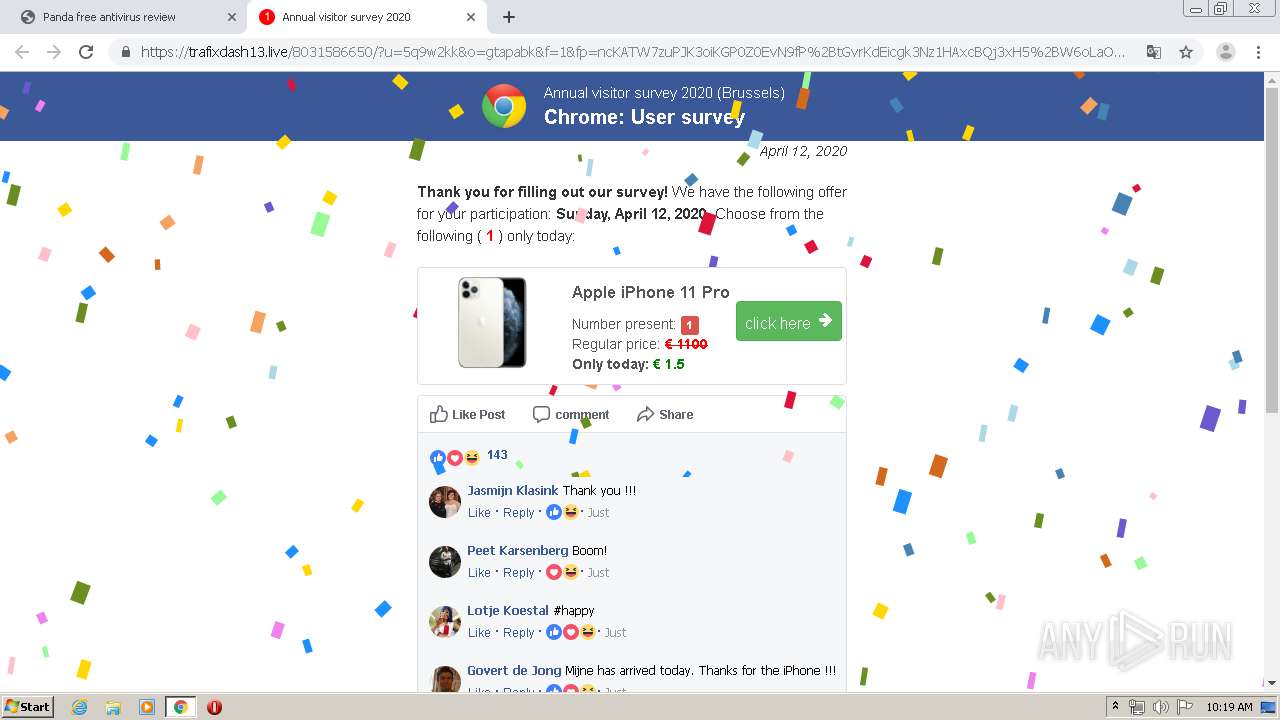
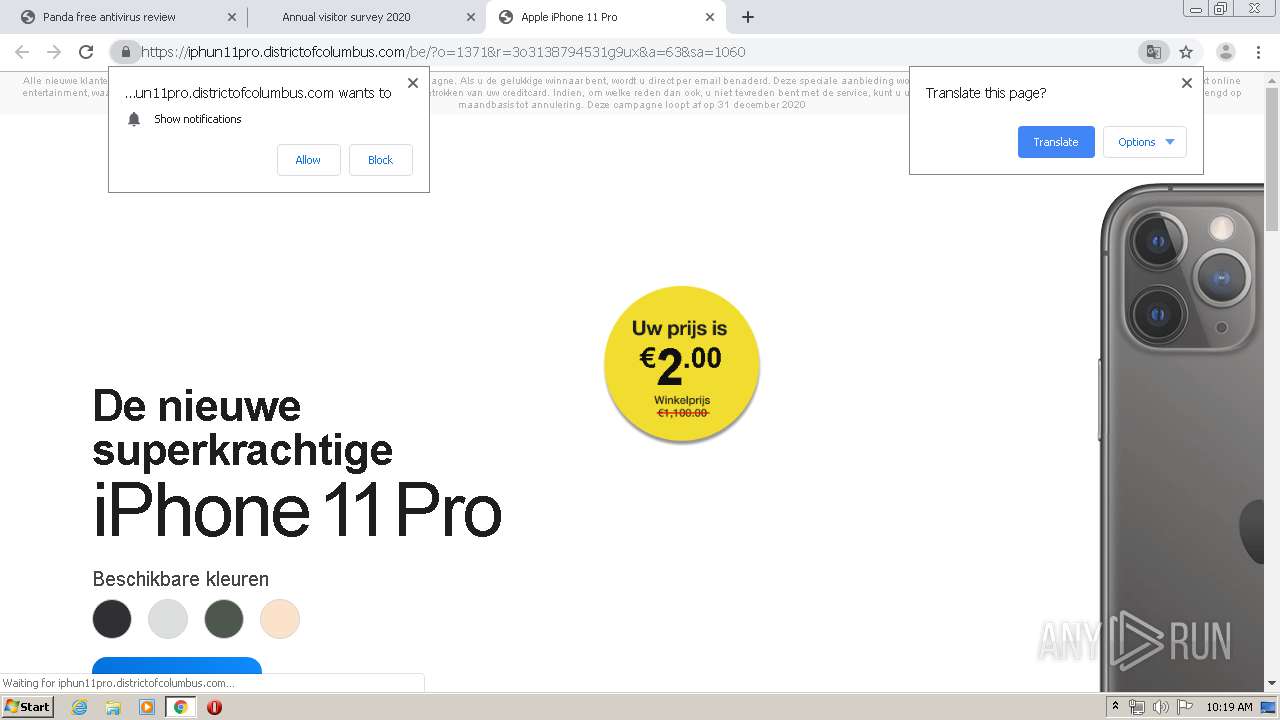
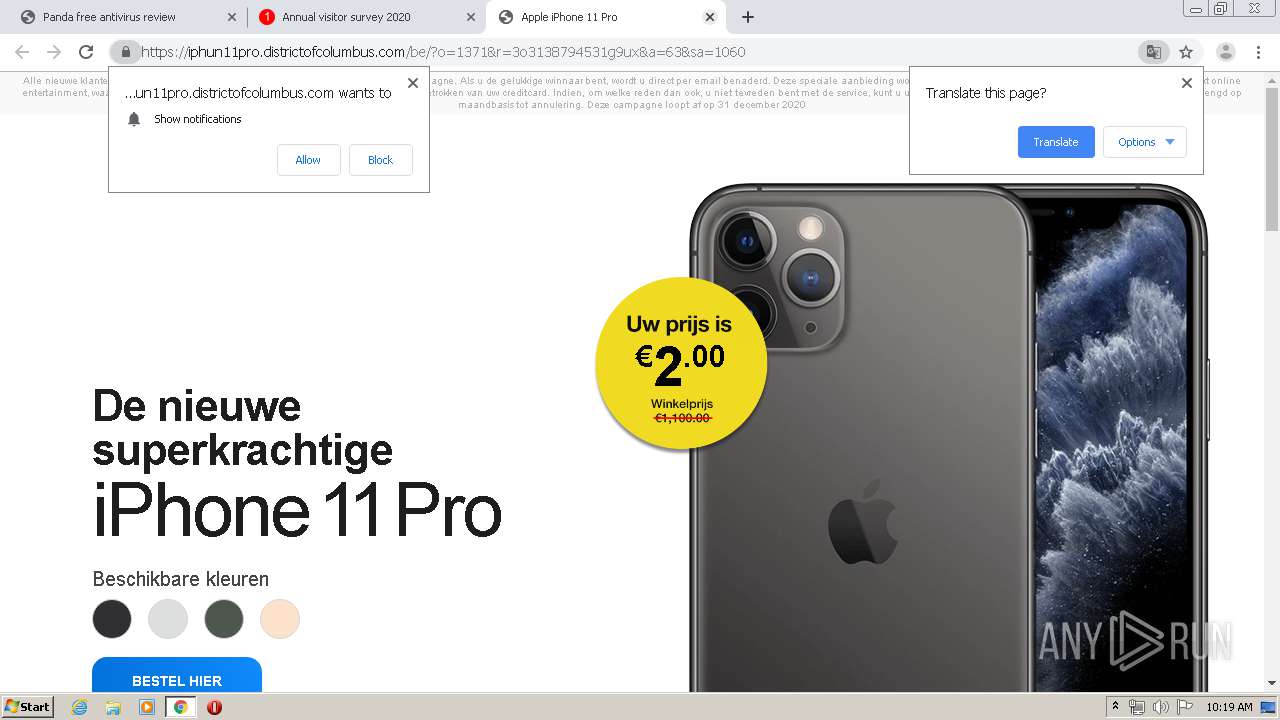
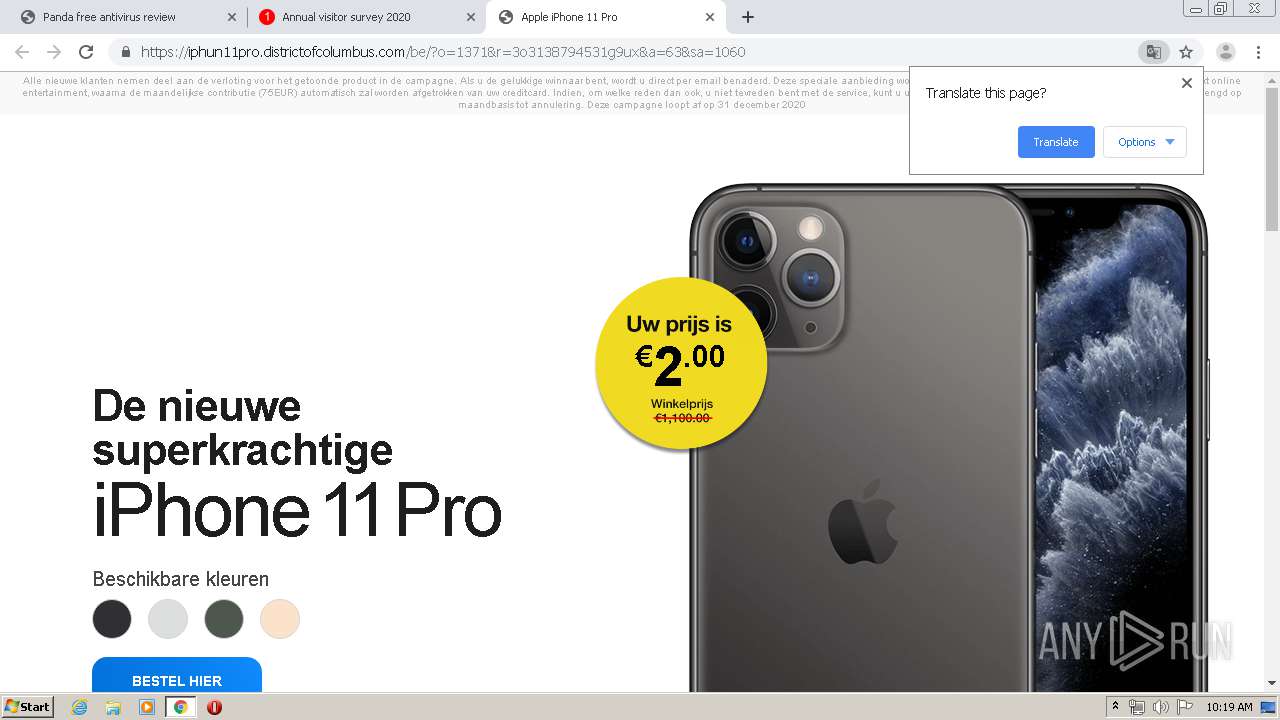
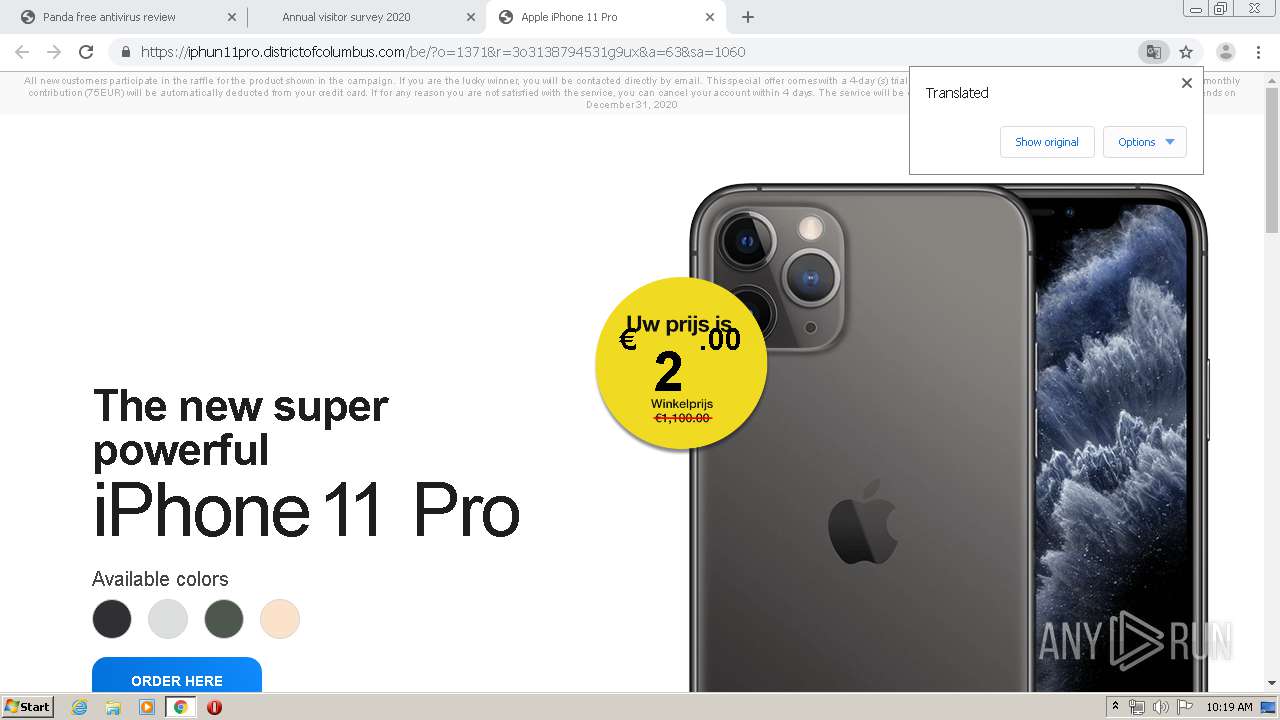
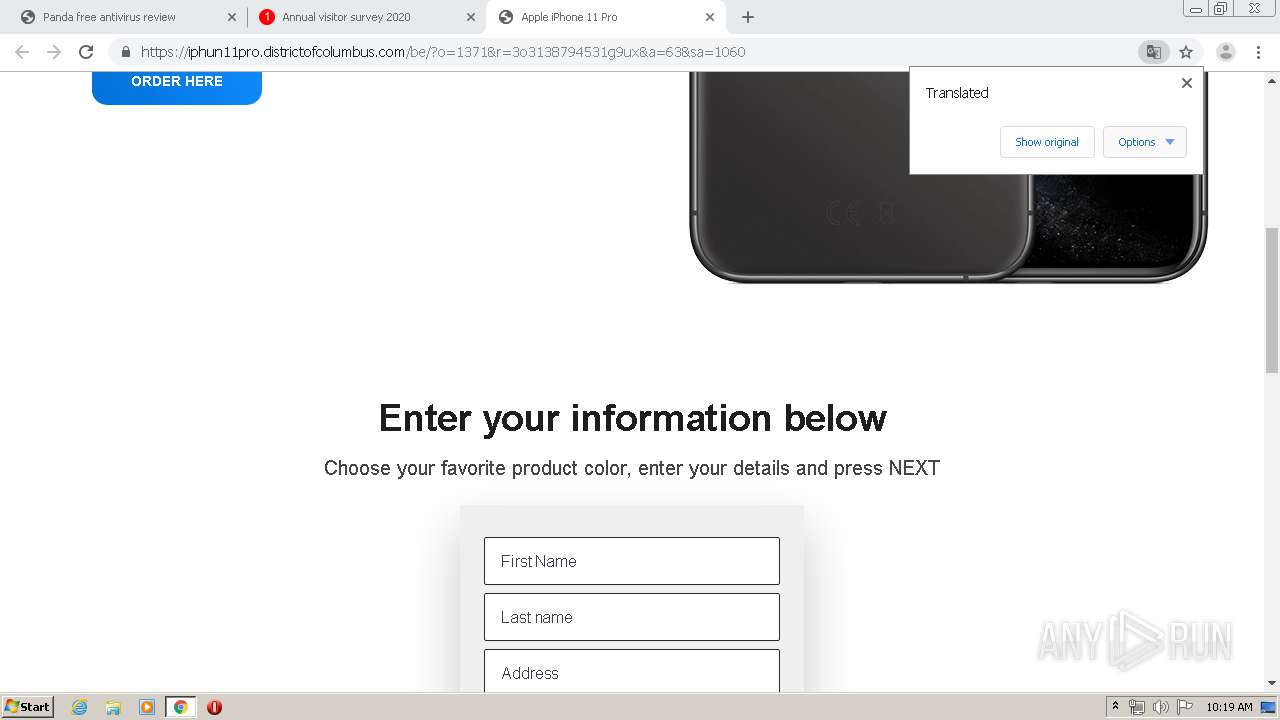
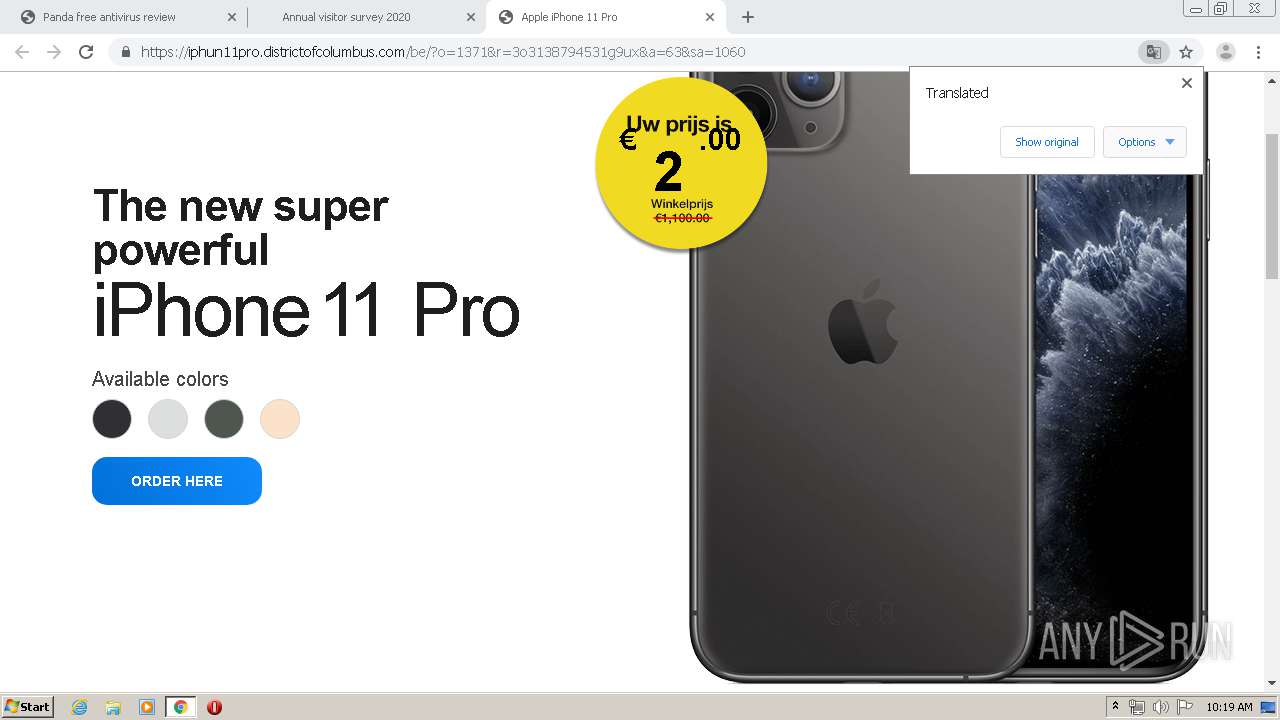
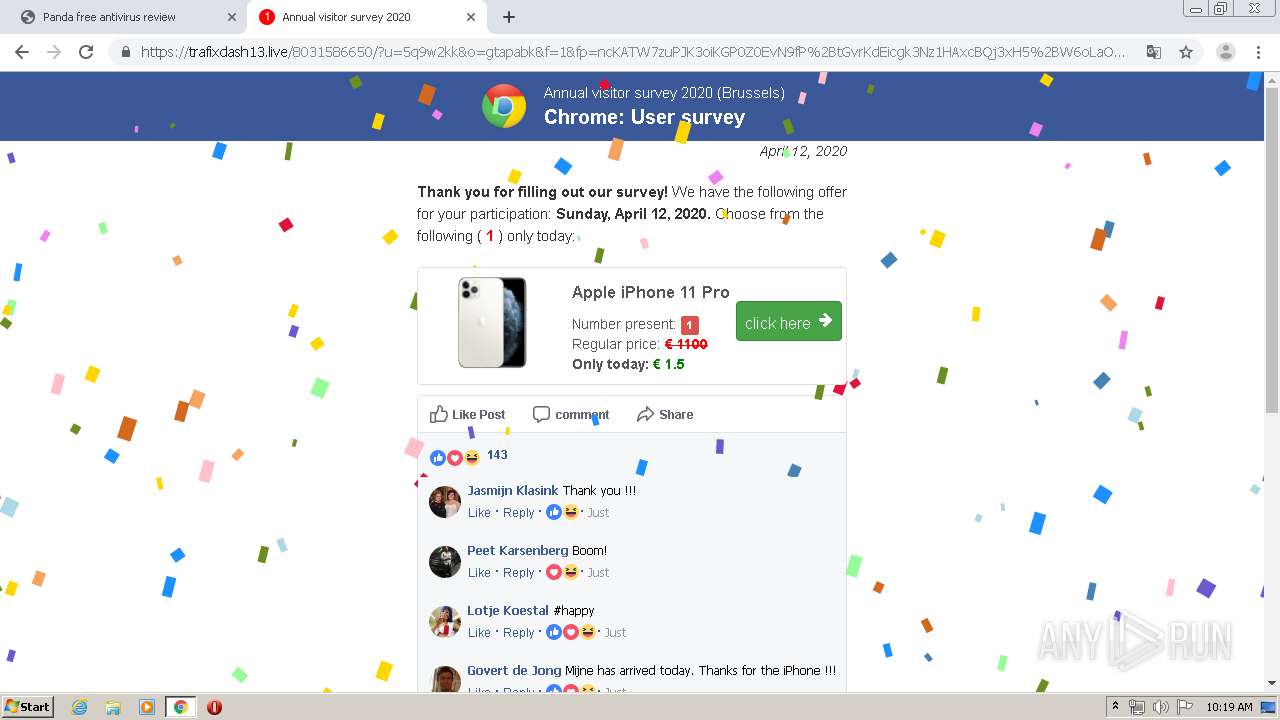
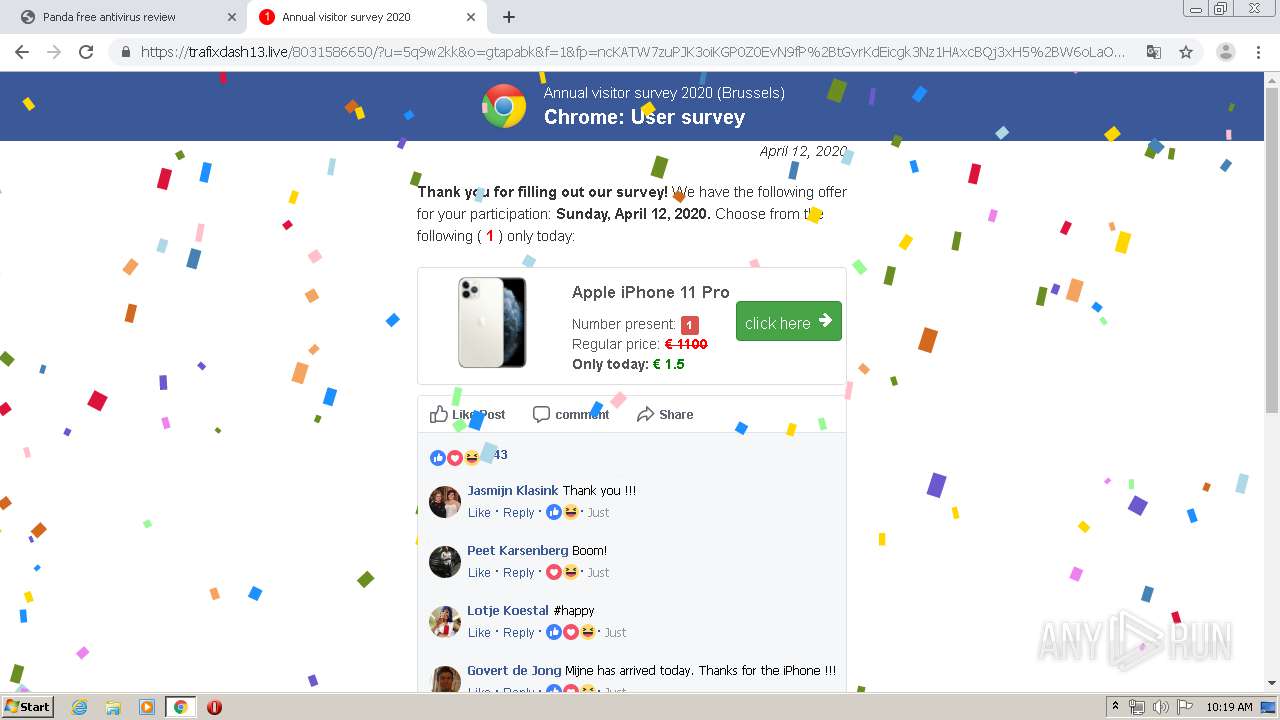
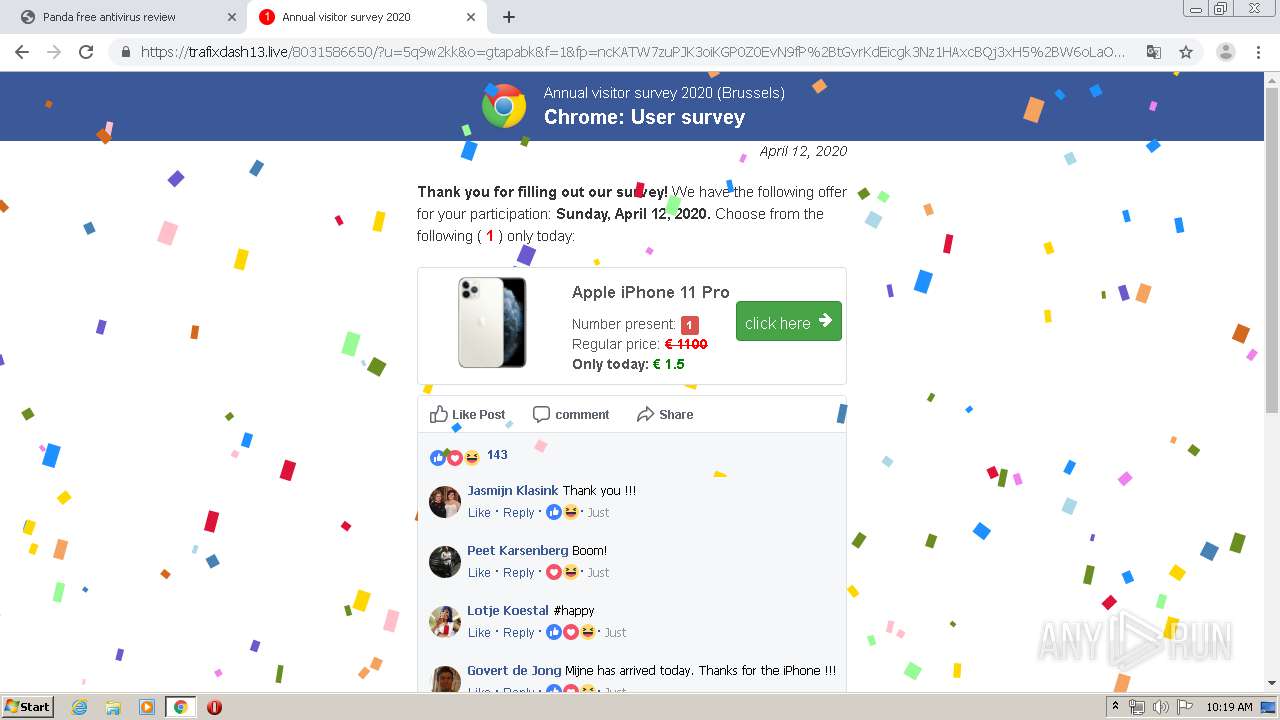
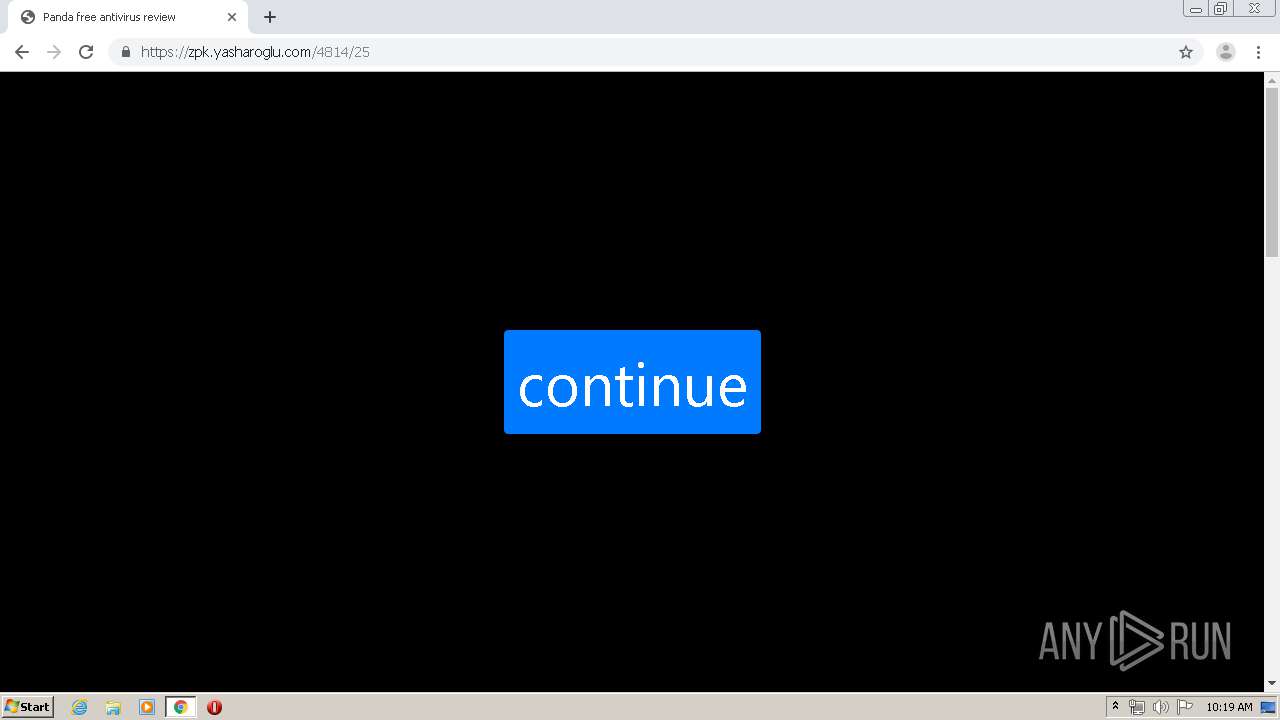
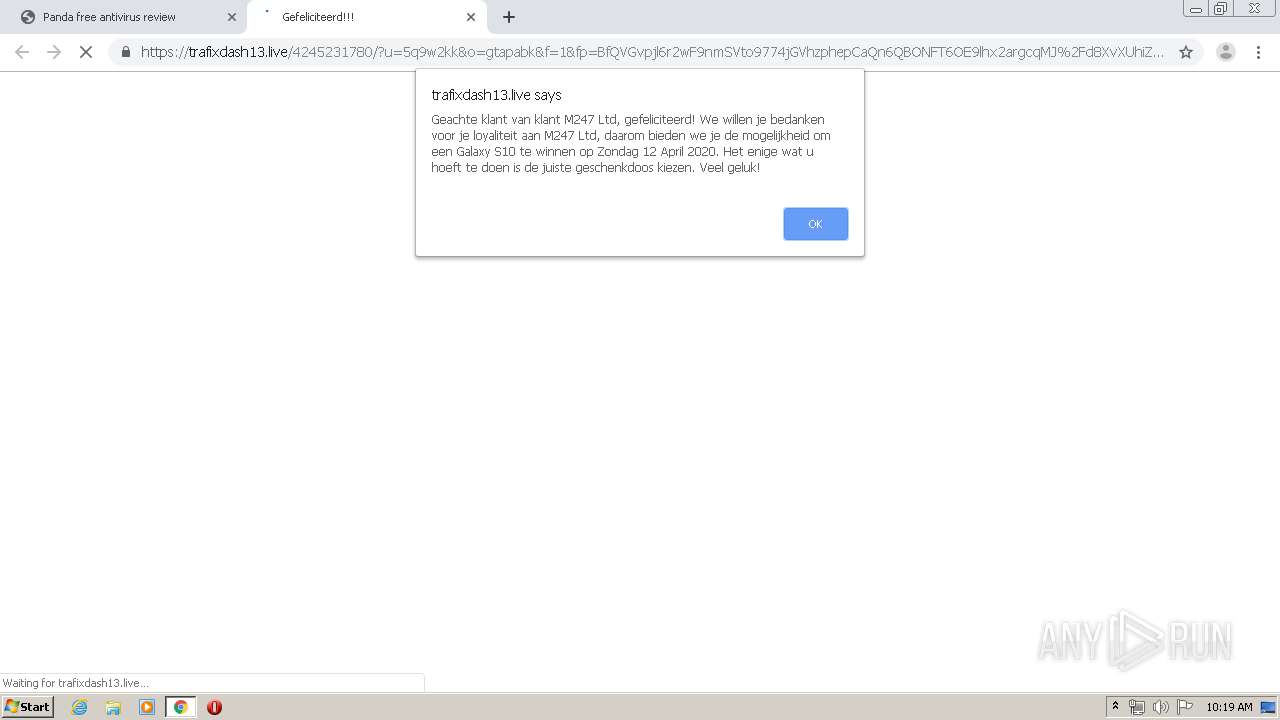
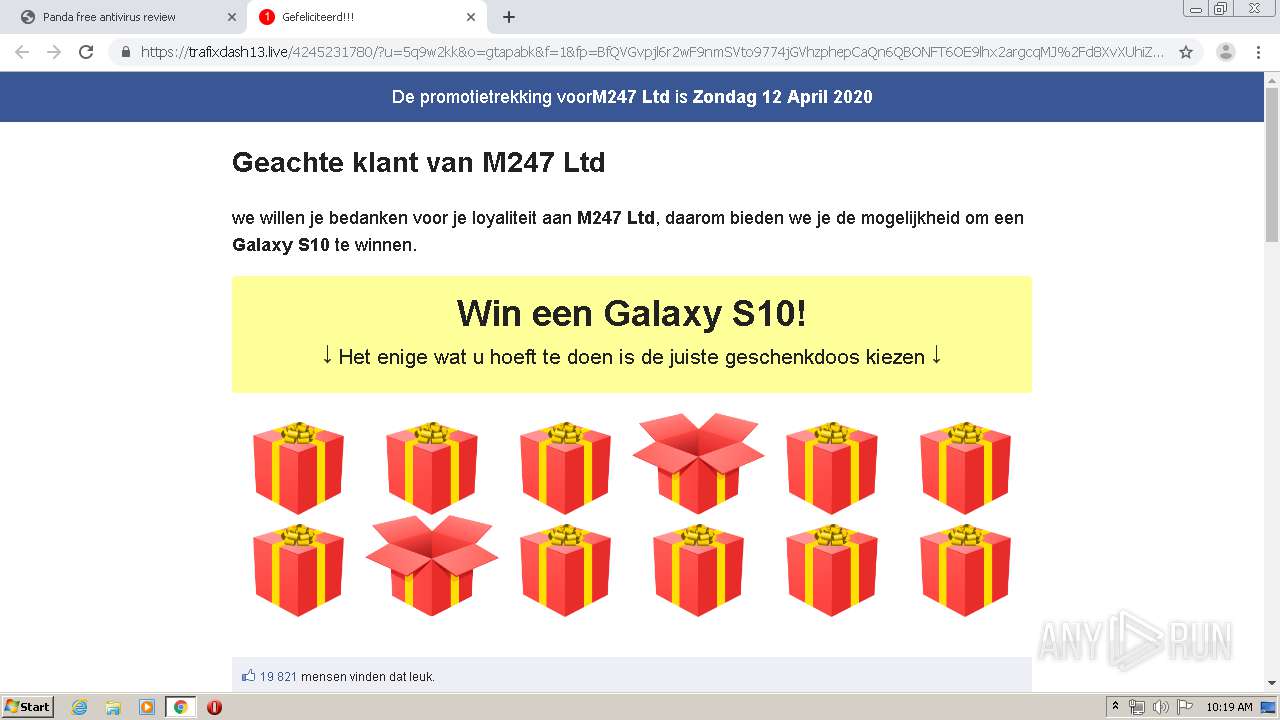
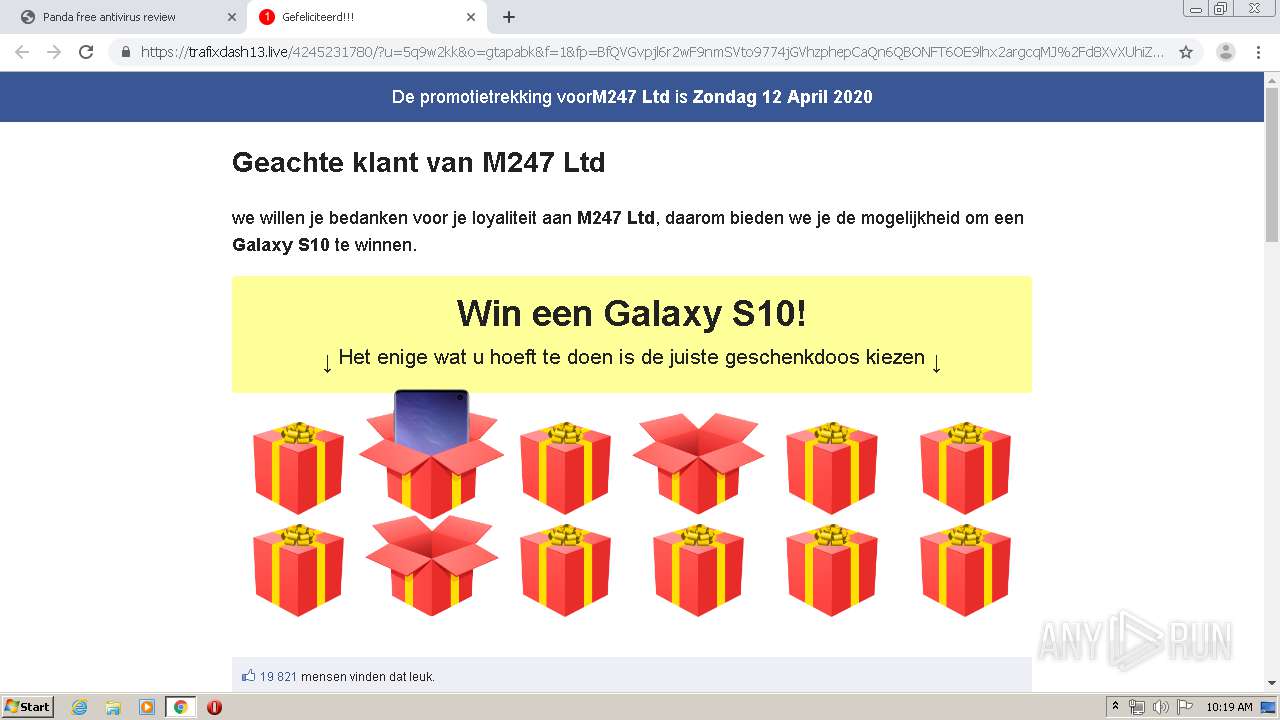
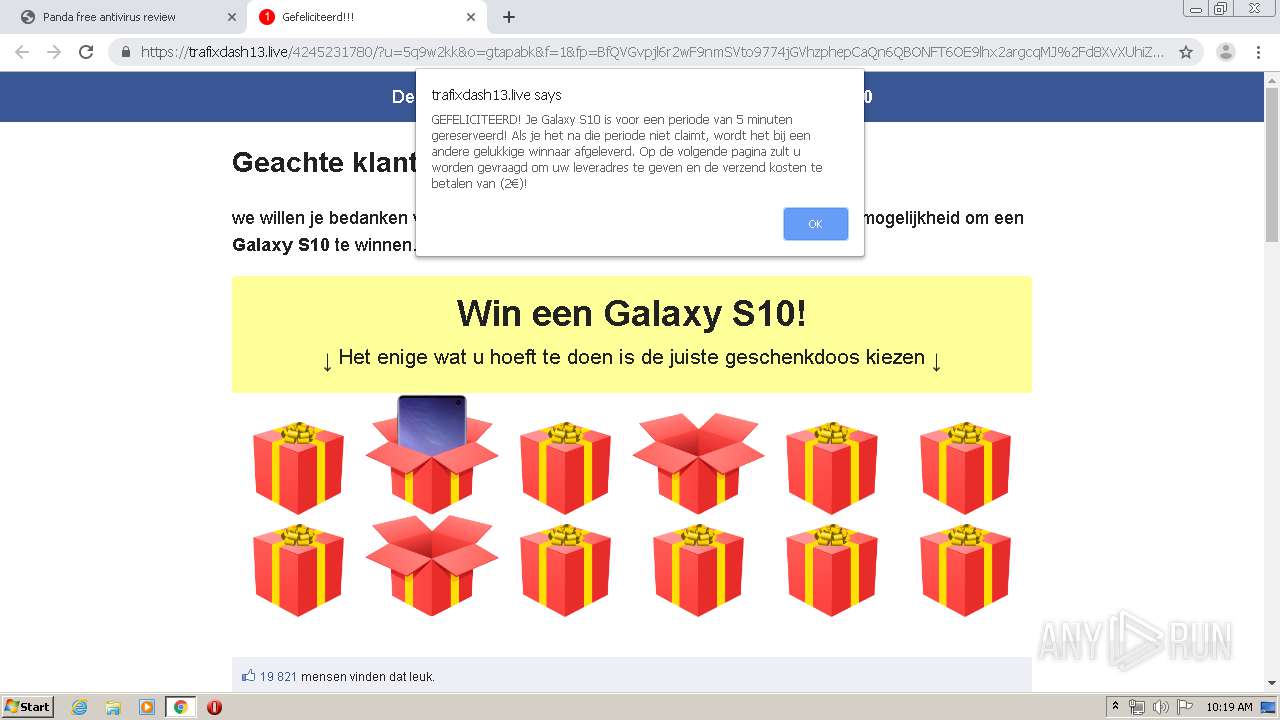
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2020, 09:15:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CA0B394EAFEB5059ECA9C0A4080306C9 |
| SHA1: | 92F3C575F7F149E66AD7144355724A18DD8F1CAD |
| SHA256: | CFDE3C75164C2F19BC026BC88032C12C73BFB5DD785A957AAED9ECDFF5609BD0 |
| SSDEEP: | 3:N1KKAEAIjbdIn:CKFAIyn |
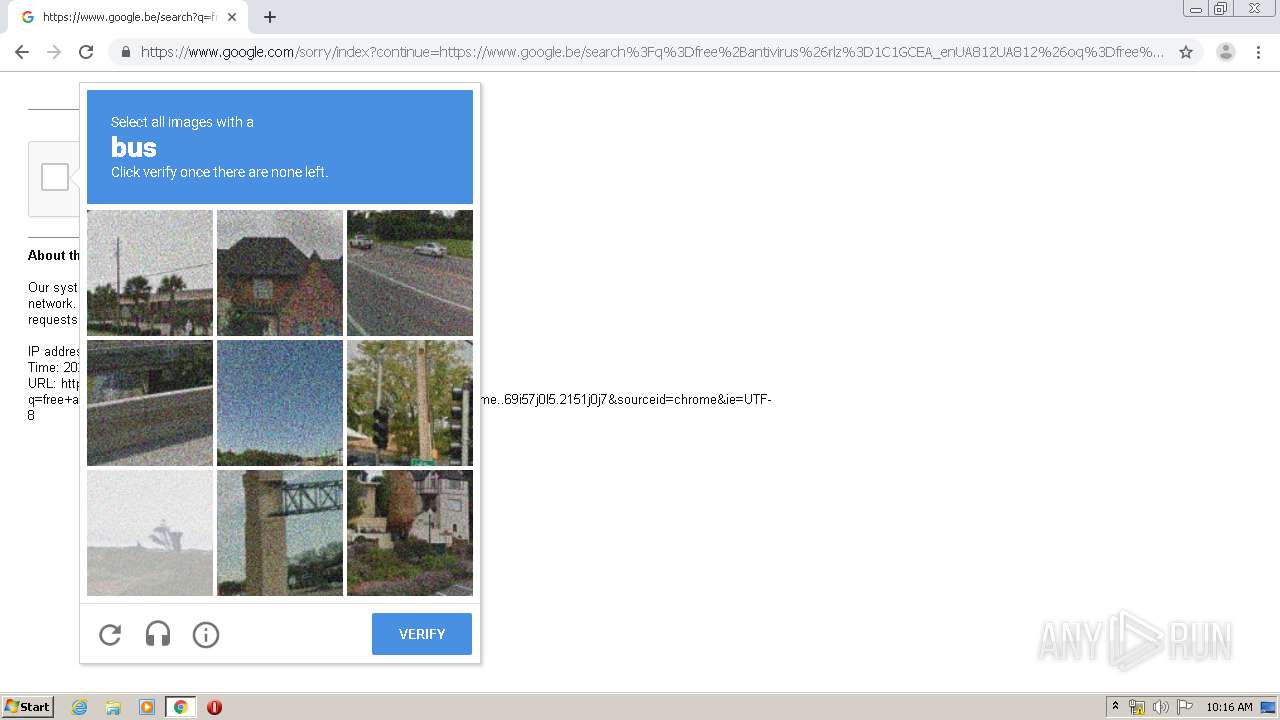
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 620)
INFO
Creates files in the user directory
- chrome.exe (PID: 620)
Reads the hosts file
- chrome.exe (PID: 1520)
- chrome.exe (PID: 620)
Application launched itself
- chrome.exe (PID: 620)
Reads settings of System Certificates
- chrome.exe (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
70
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10338258783803194679 --mojo-platform-channel-handle=2500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14543730452919168406 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10810587215508467123 --mojo-platform-channel-handle=3860 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5048136262848070481 --mojo-platform-channel-handle=2136 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://texaswhitetailfever.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16643085737038181036 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2279198365384794212 --mojo-platform-channel-handle=2592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16482898880072112607 --renderer-client-id=60 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2720871710301112132 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,501384025232579413,16192838387217102681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10193115011135406343 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
920
Read events
796
Write events
119
Delete events
5
Modification events
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 620-13231156530571125 |
Value: 259 | |||
Executable files
0
Suspicious files
256
Text files
477
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E92DC32-26C.pma | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\74ebb7cf-5021-4a54-9b22-9cf2ac2eaecb.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e22b.TMP | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e43e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
183
DNS requests
108
Threats
10
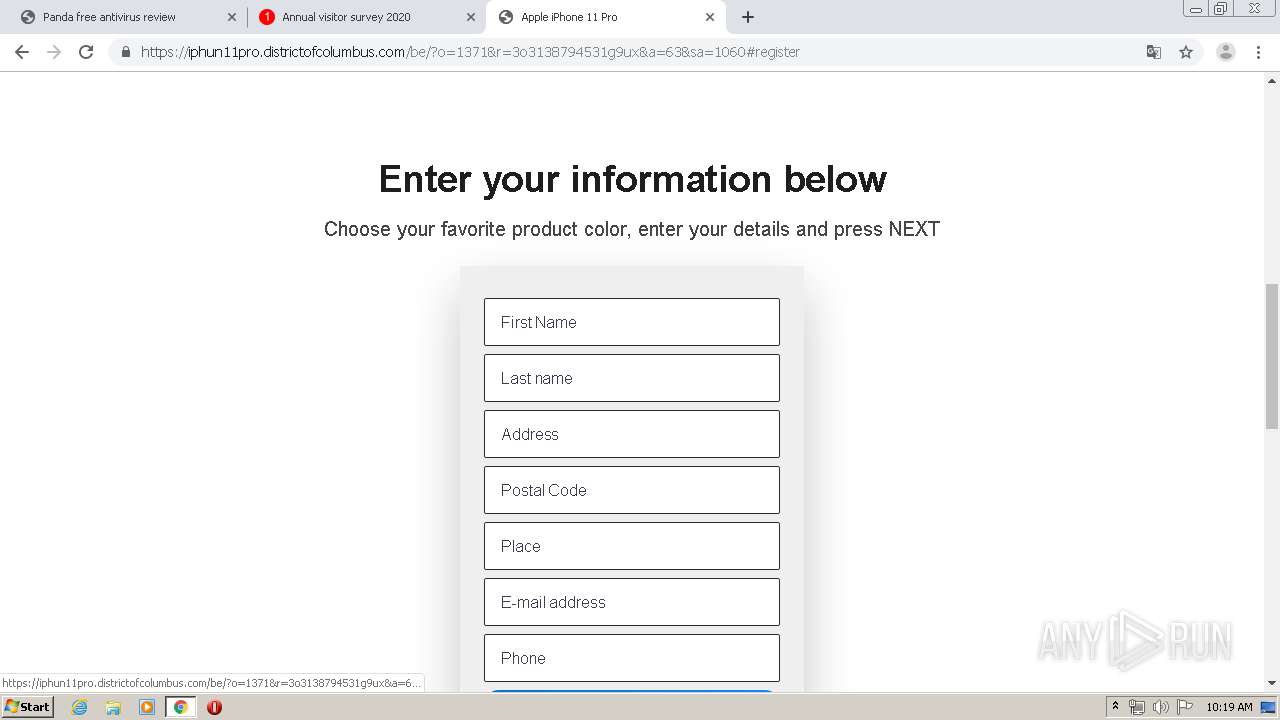
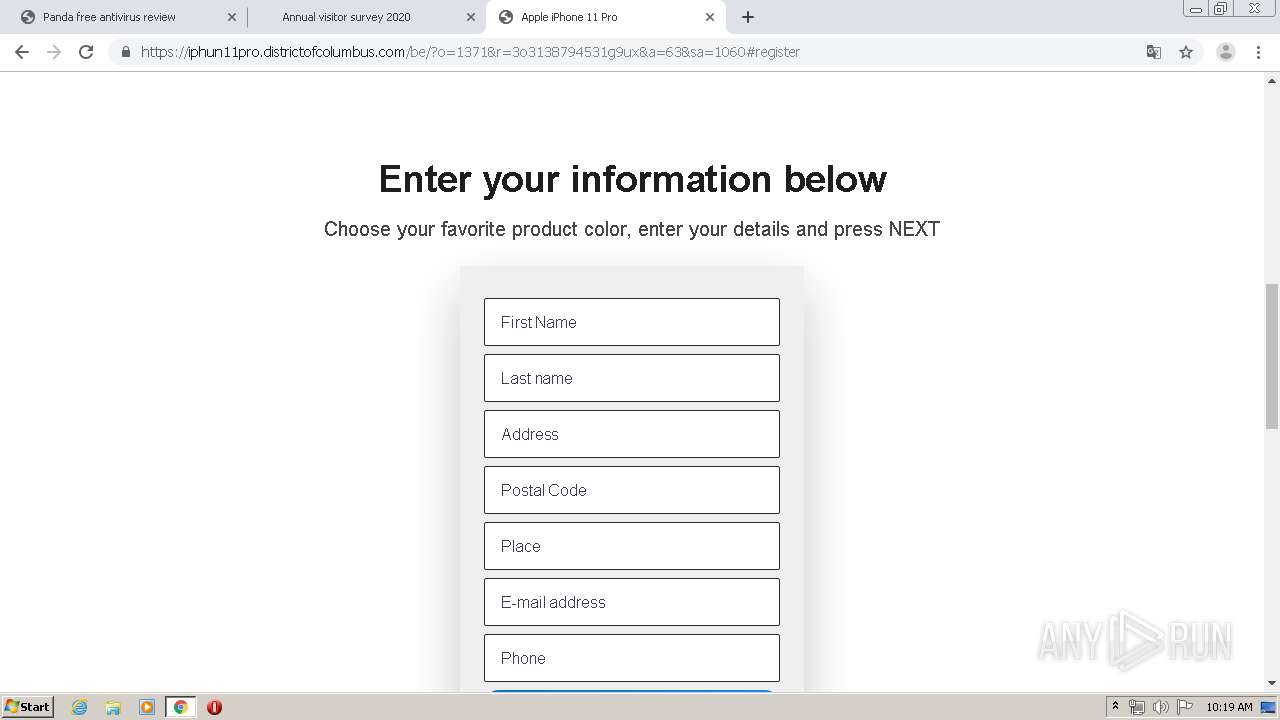
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
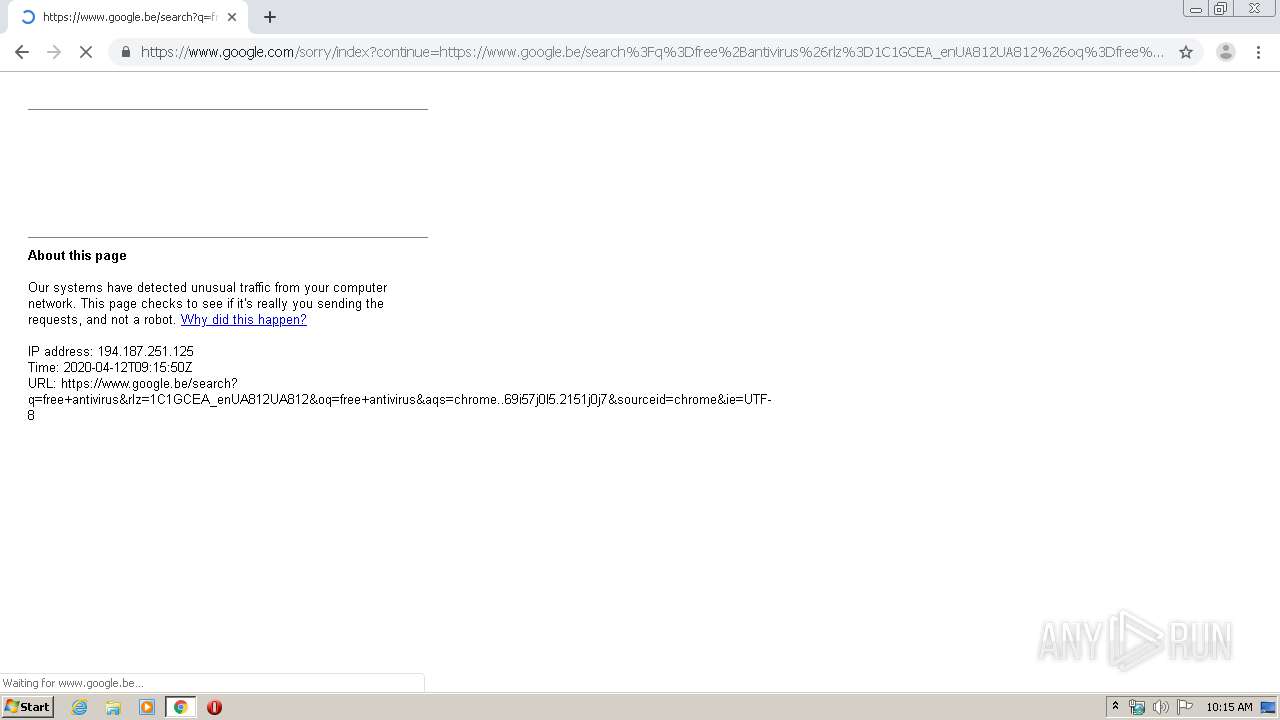
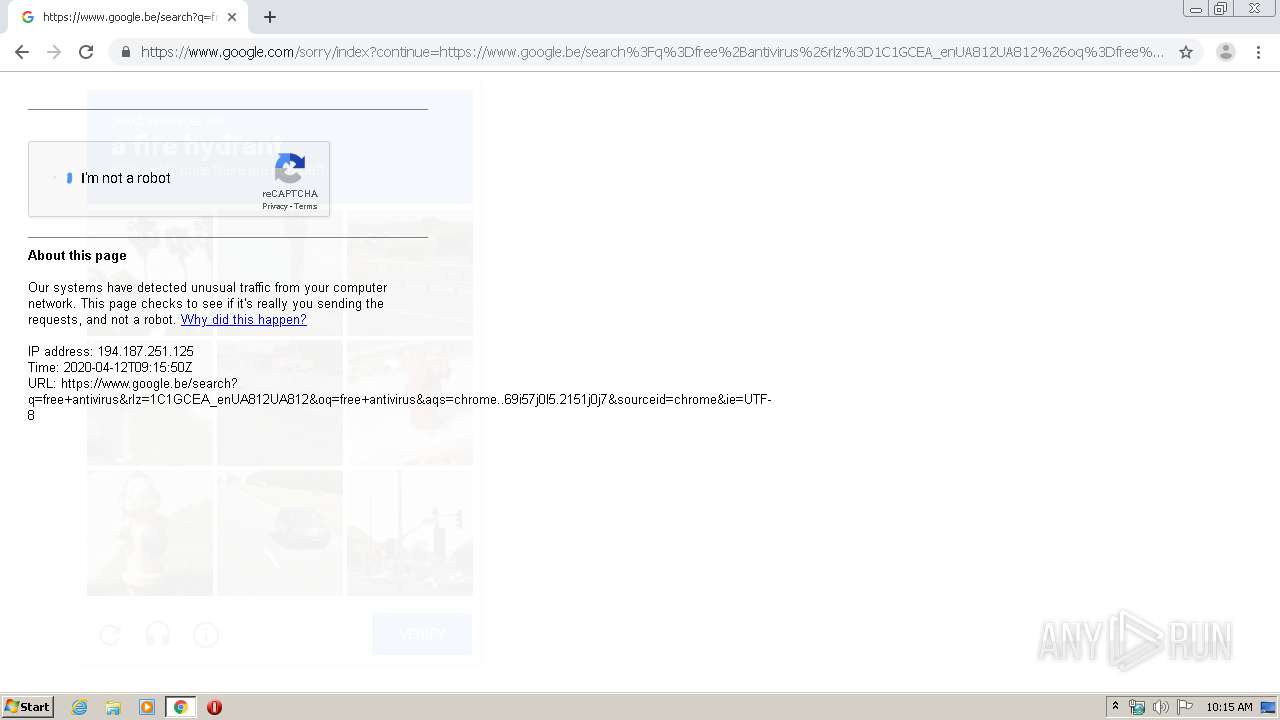
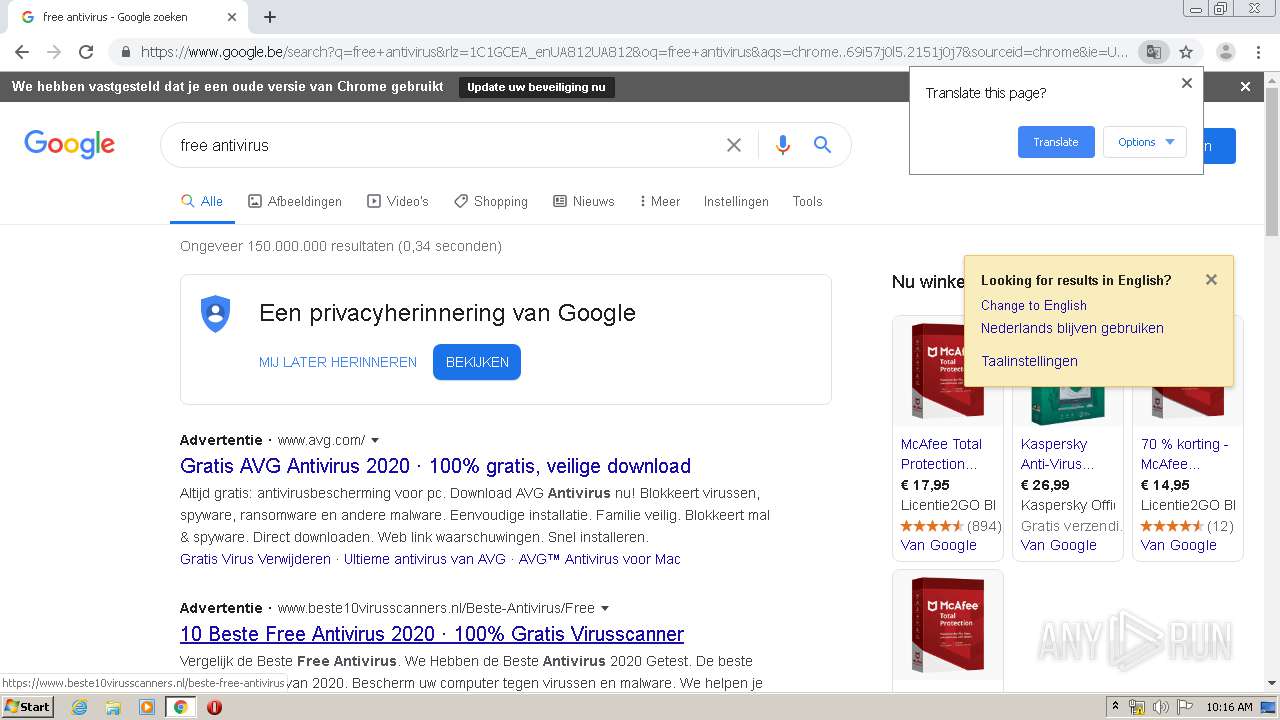
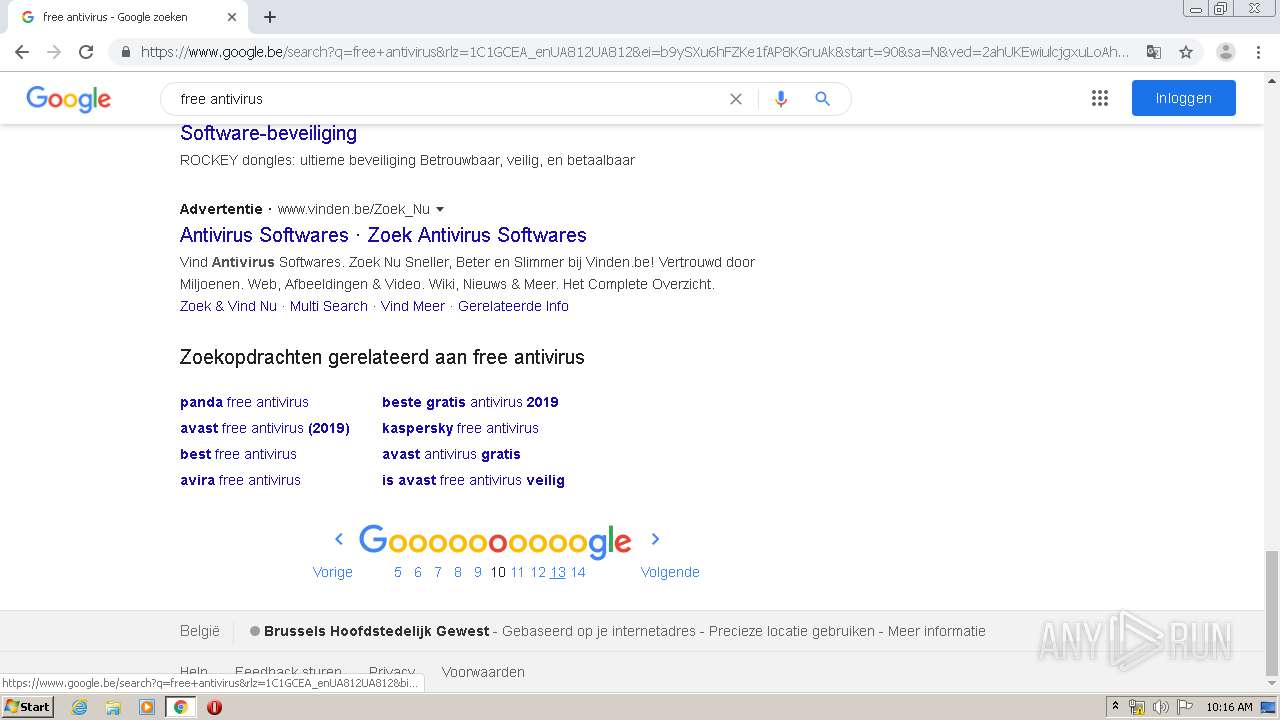
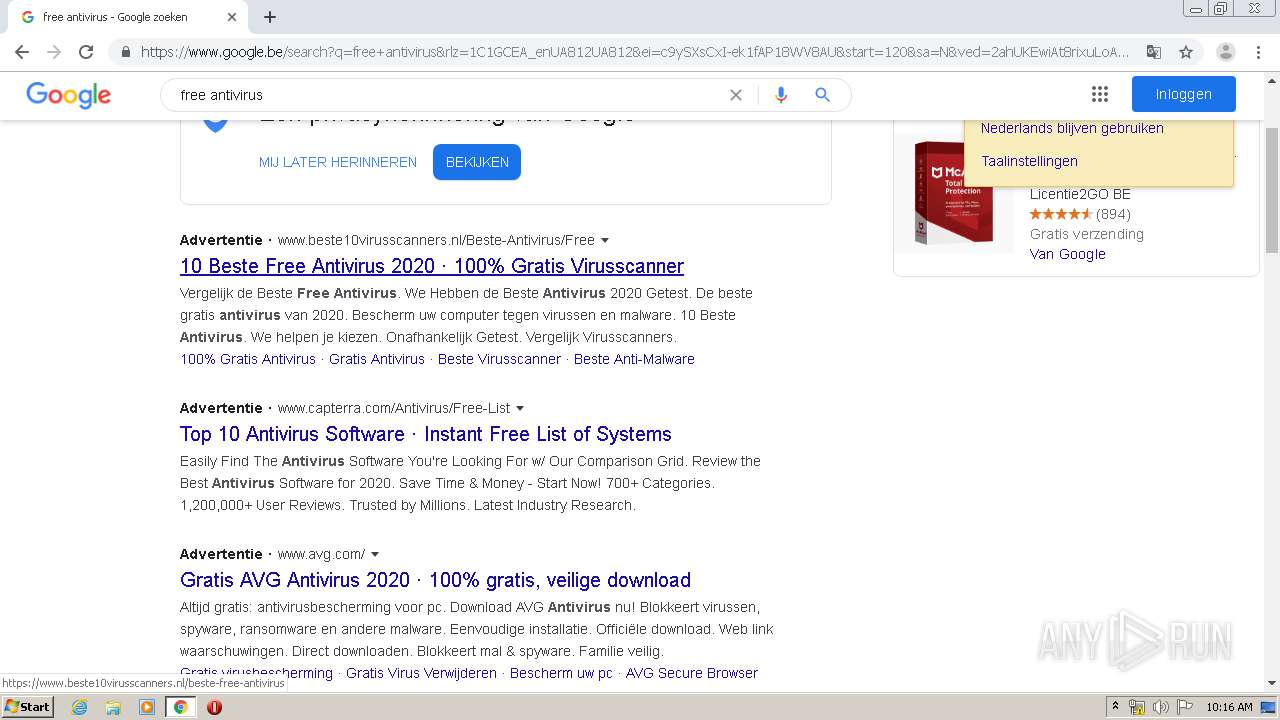
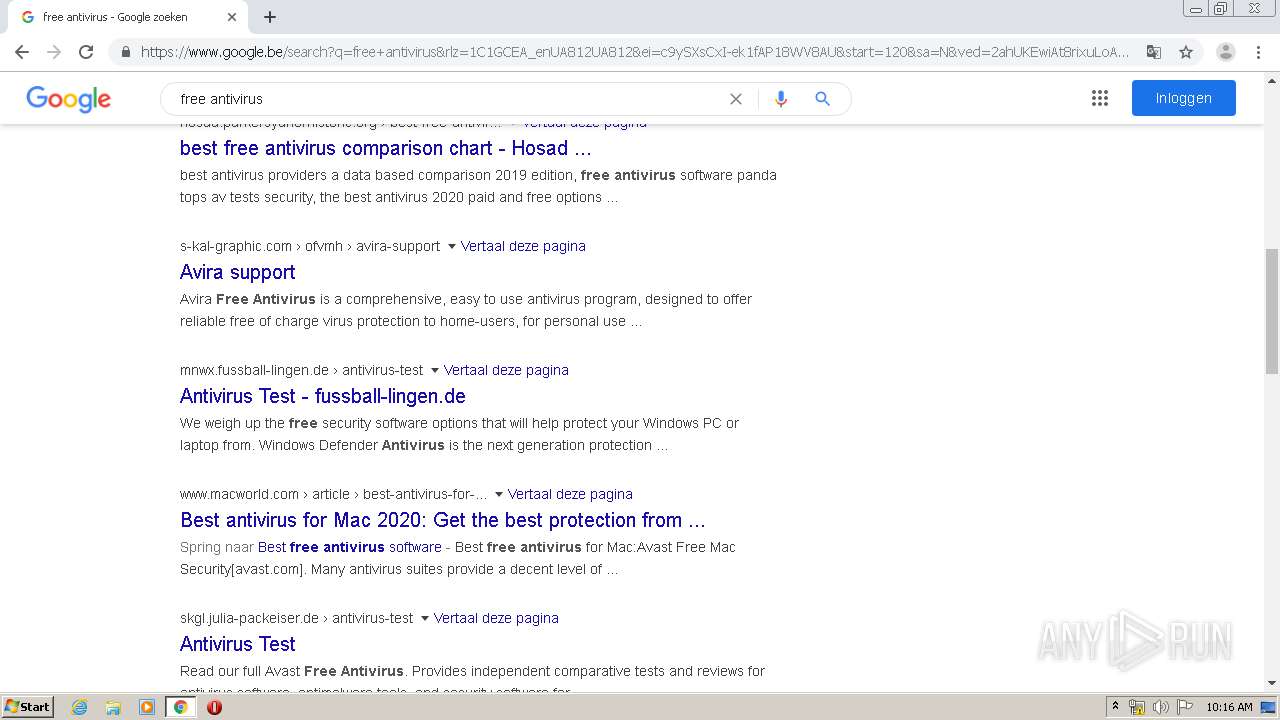
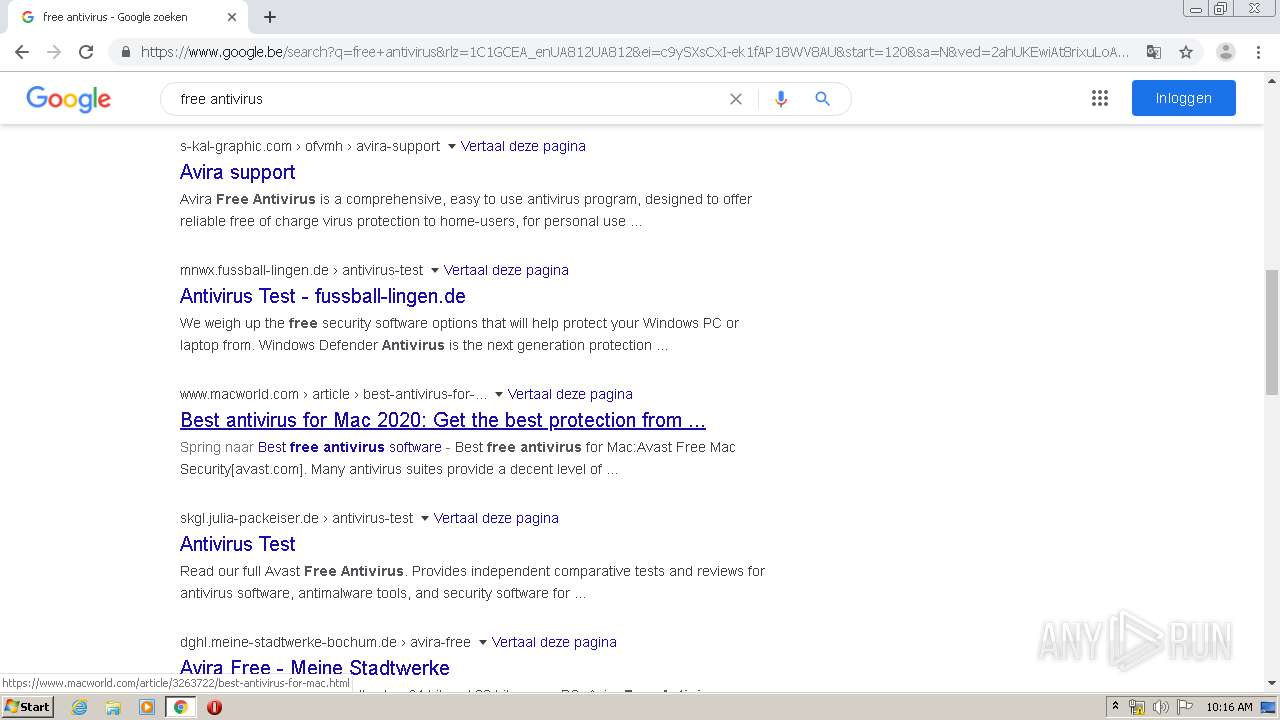
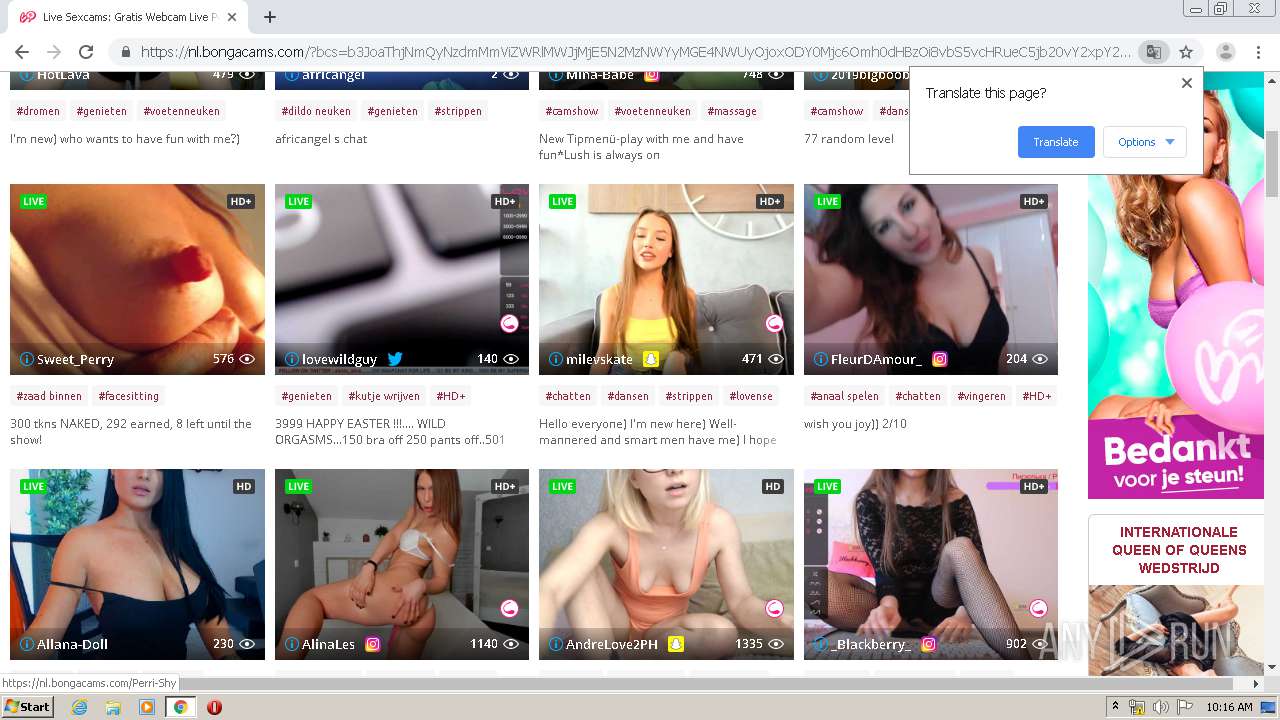
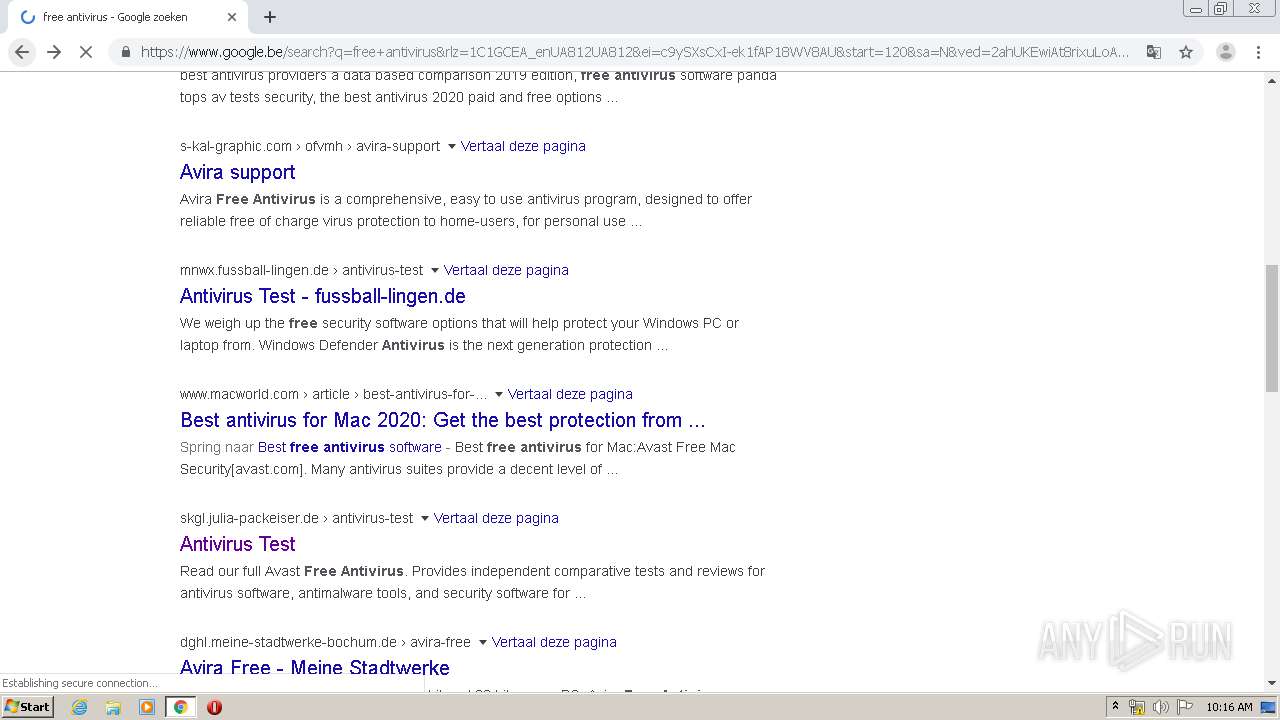
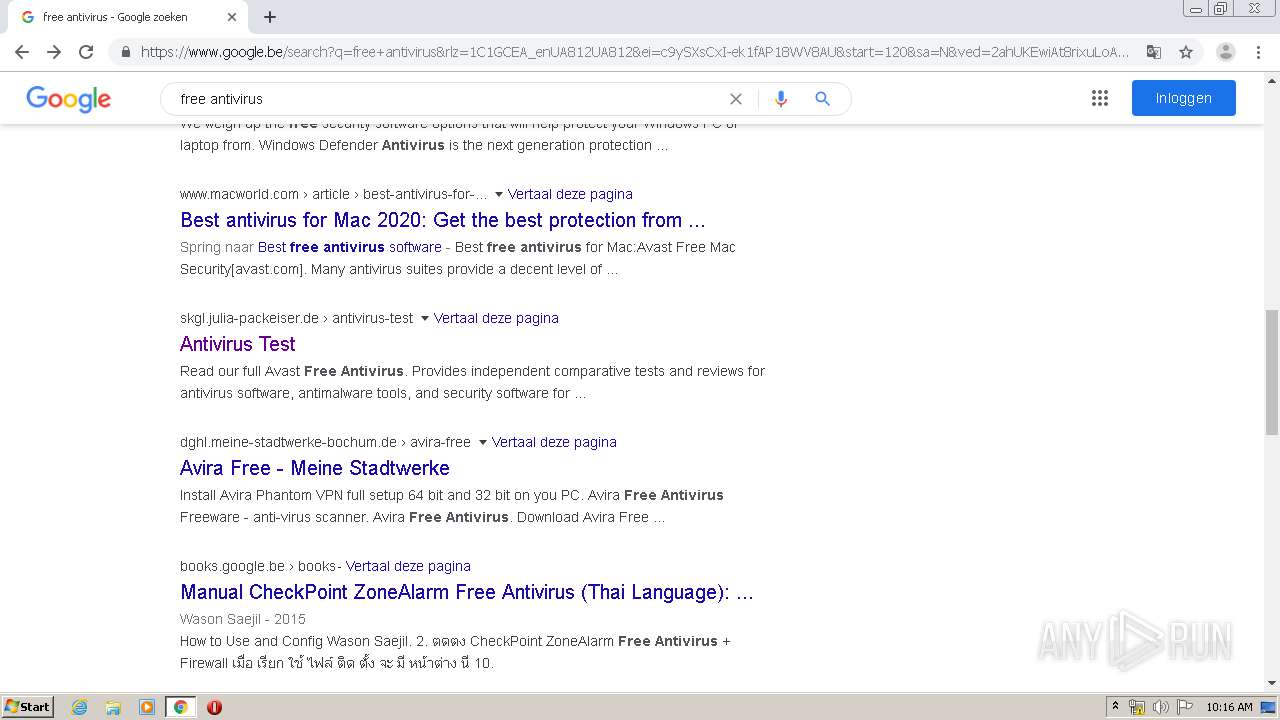
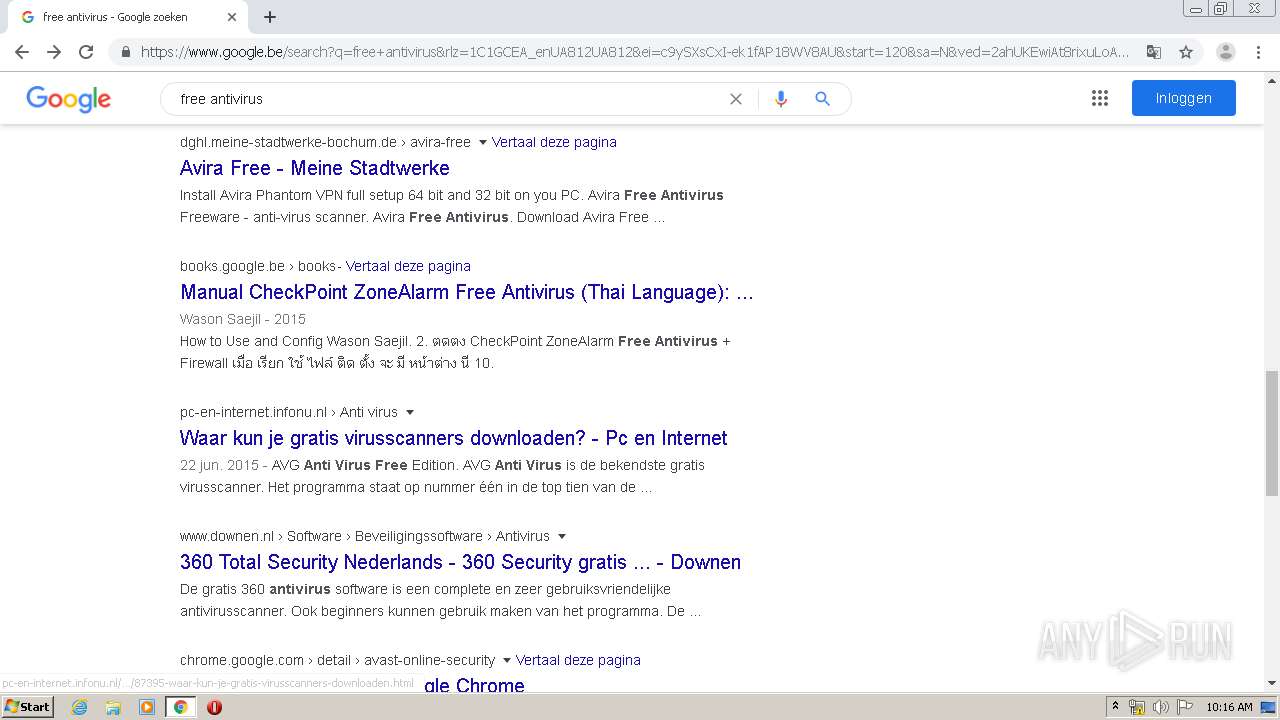
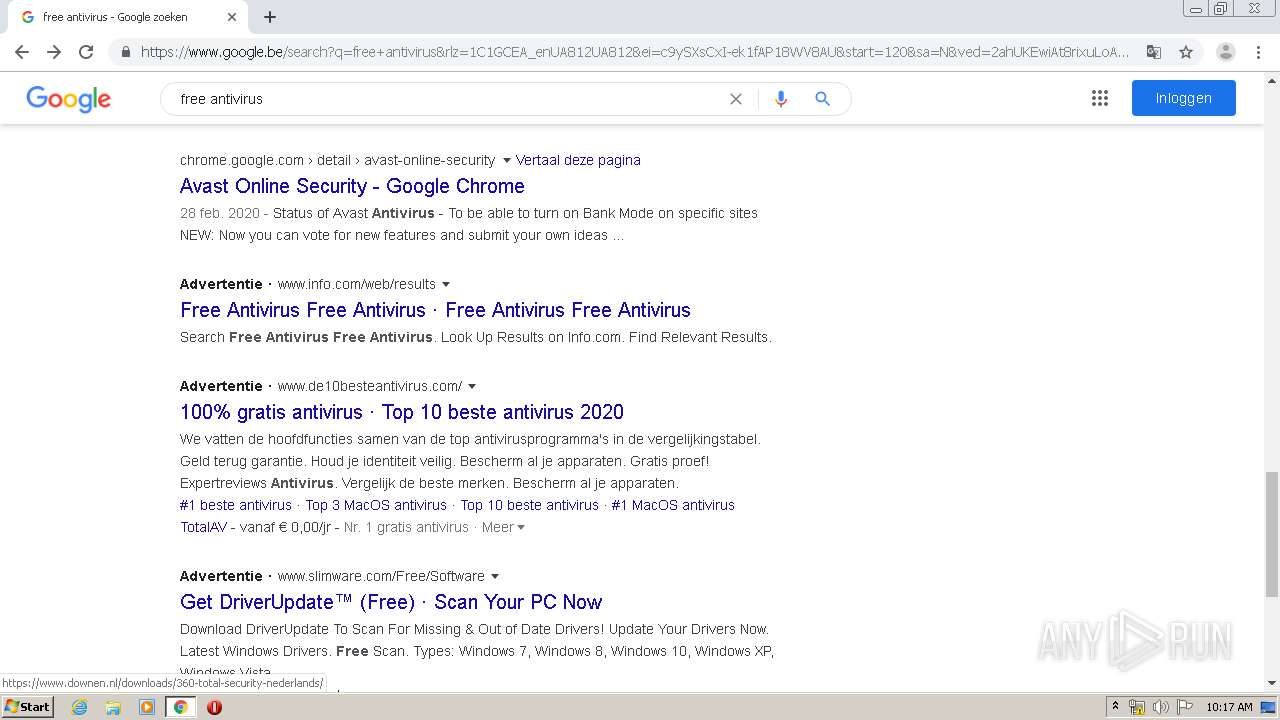
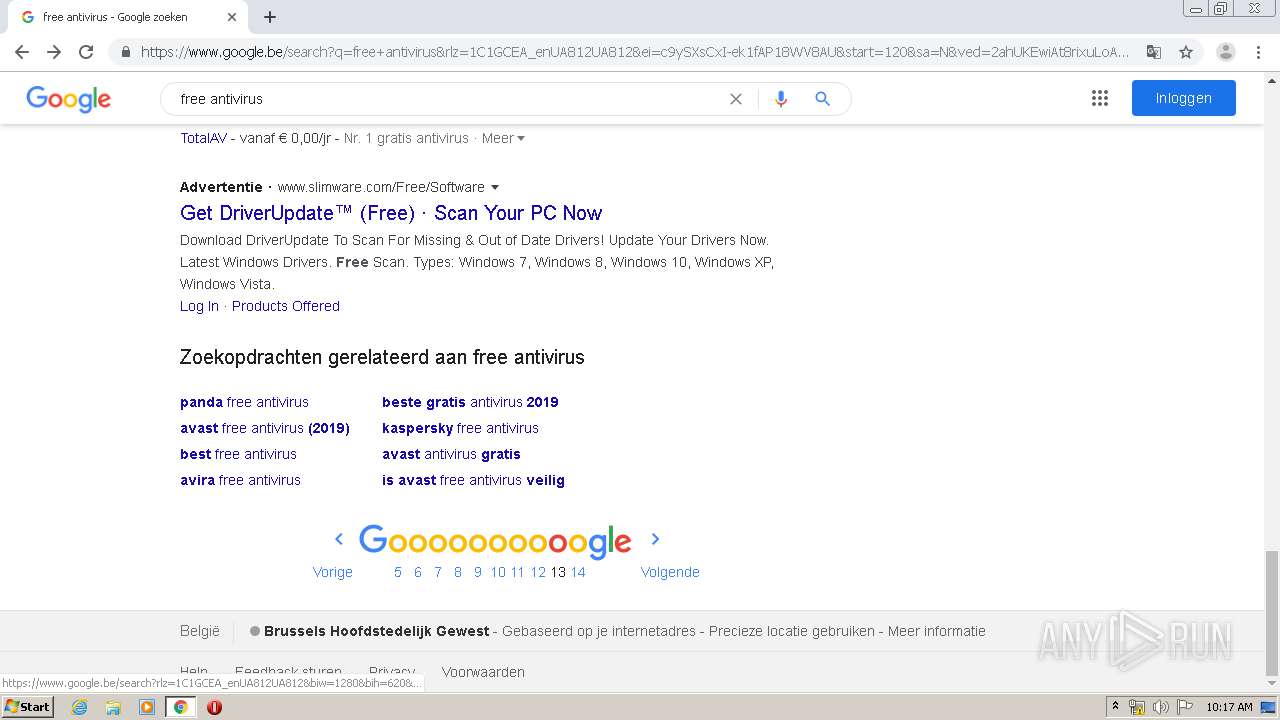
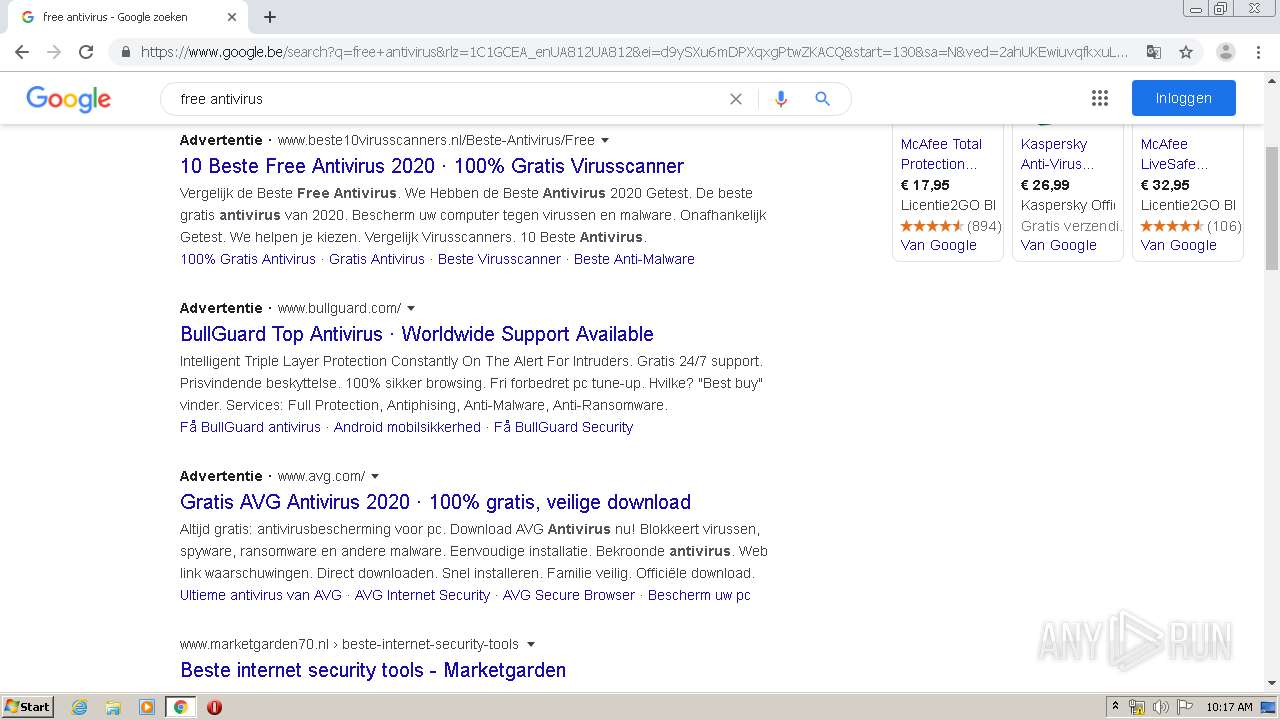
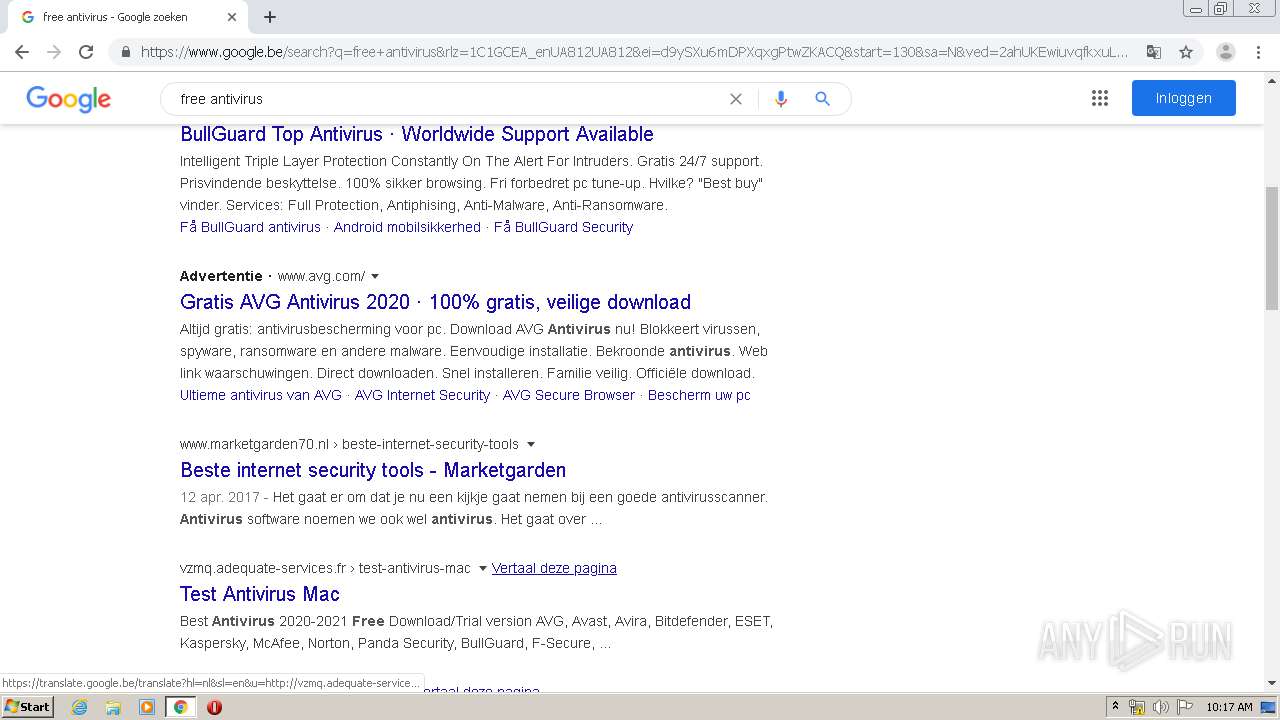
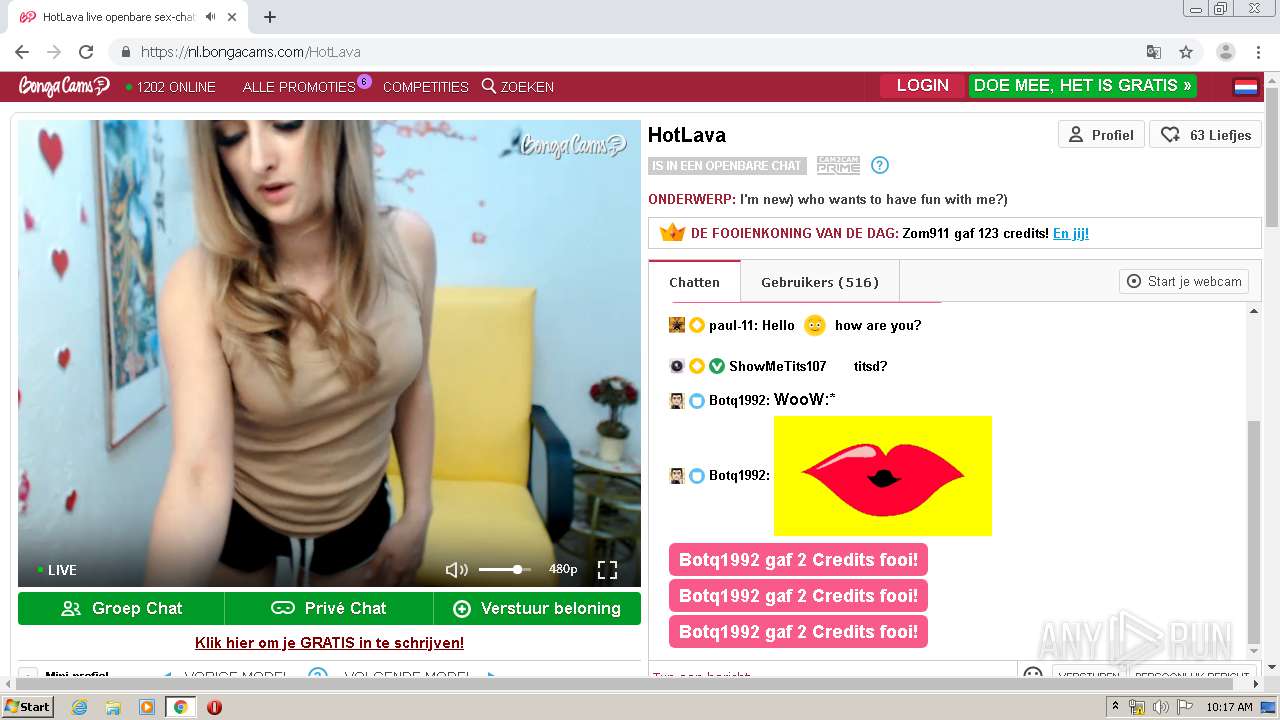
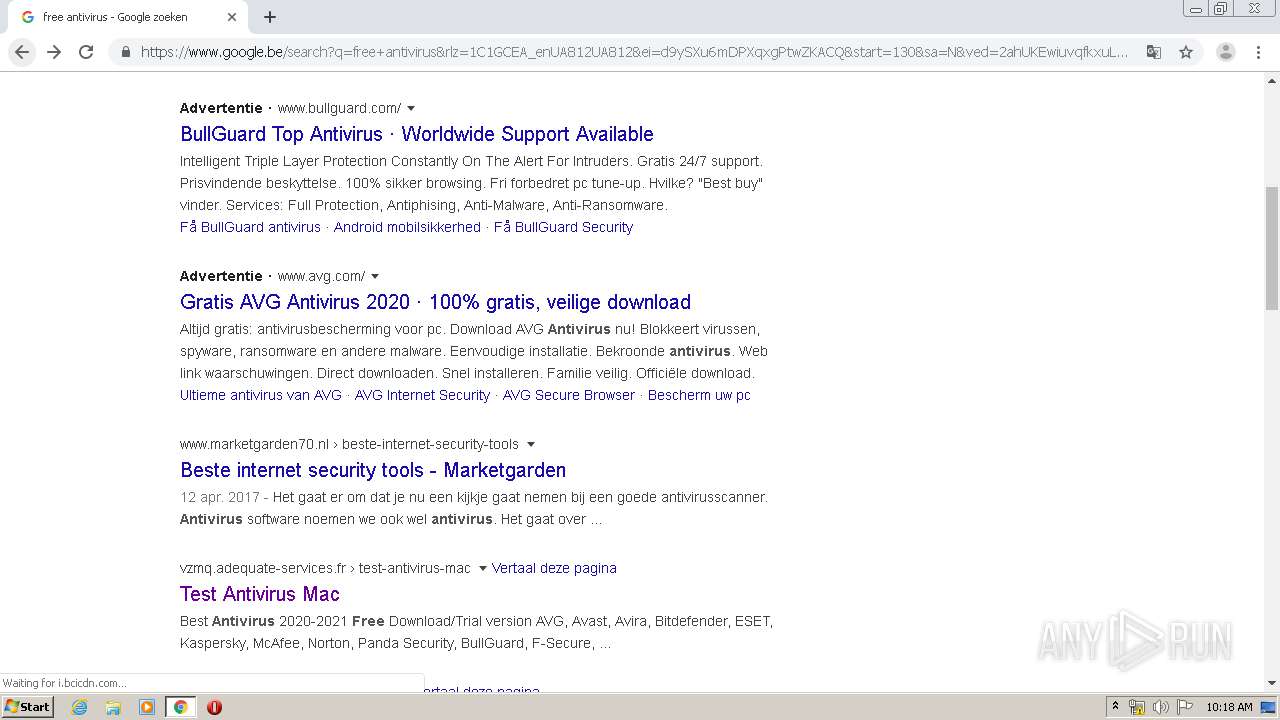
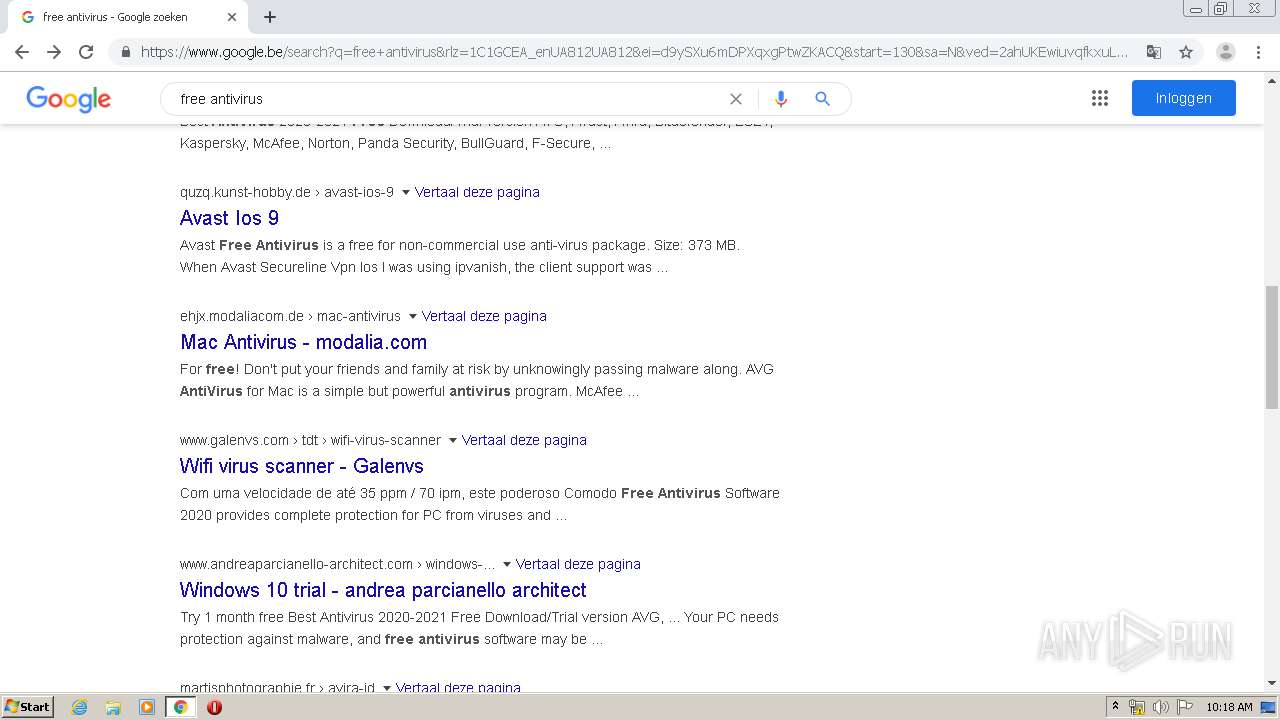
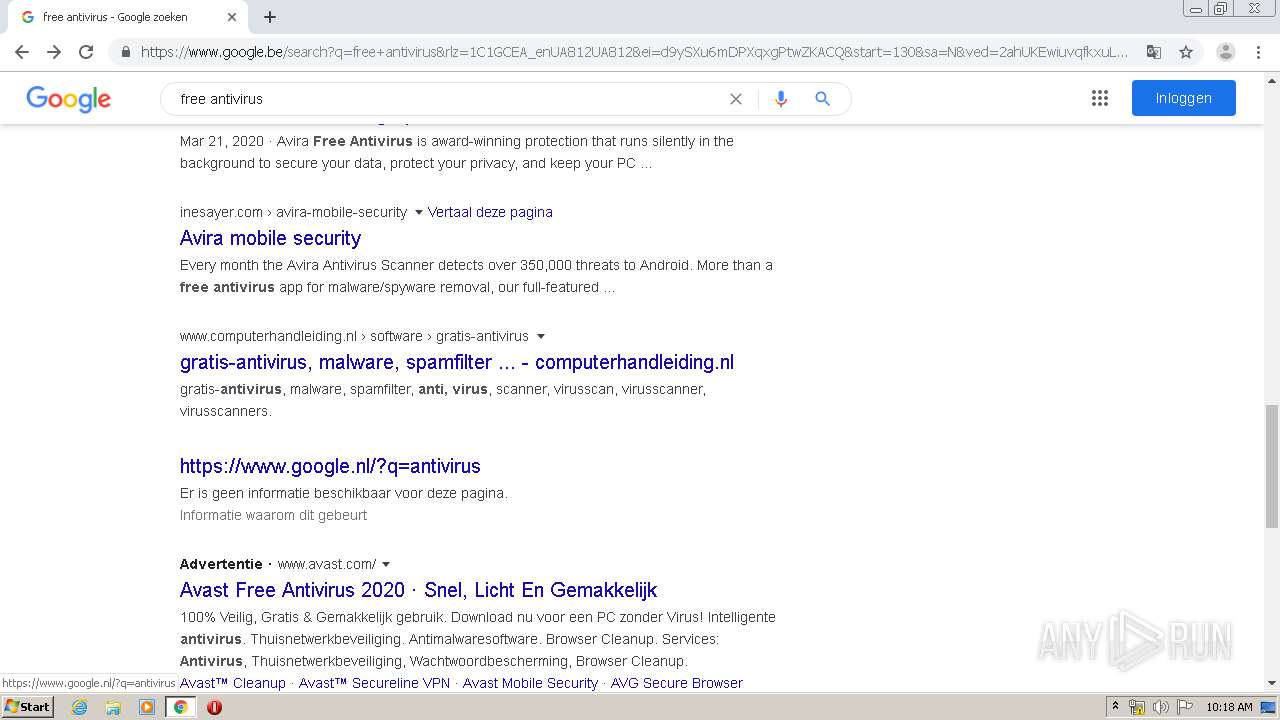
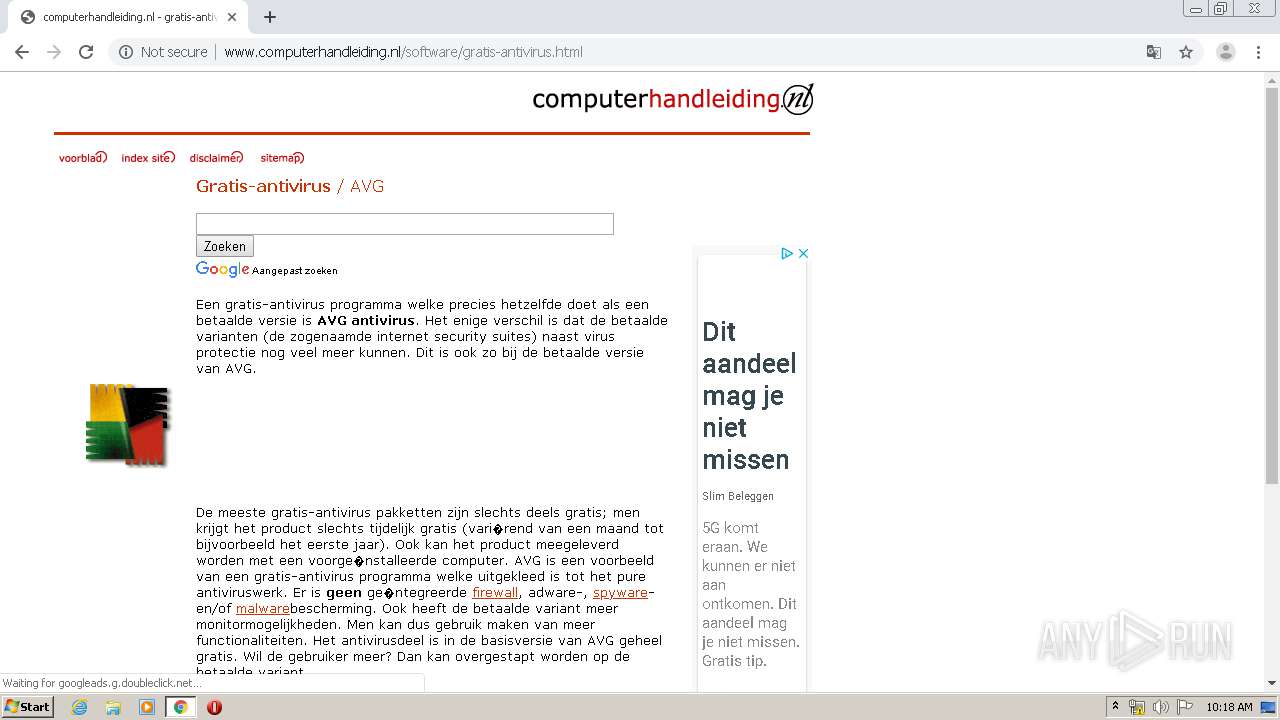
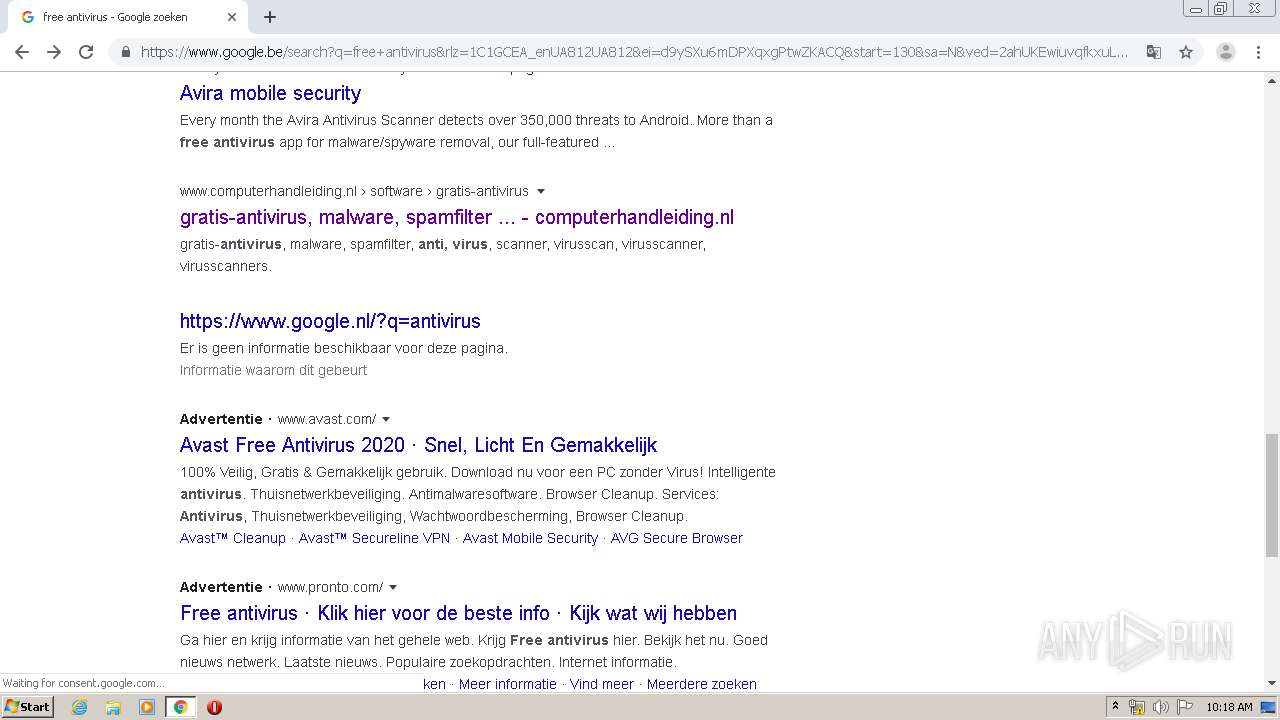
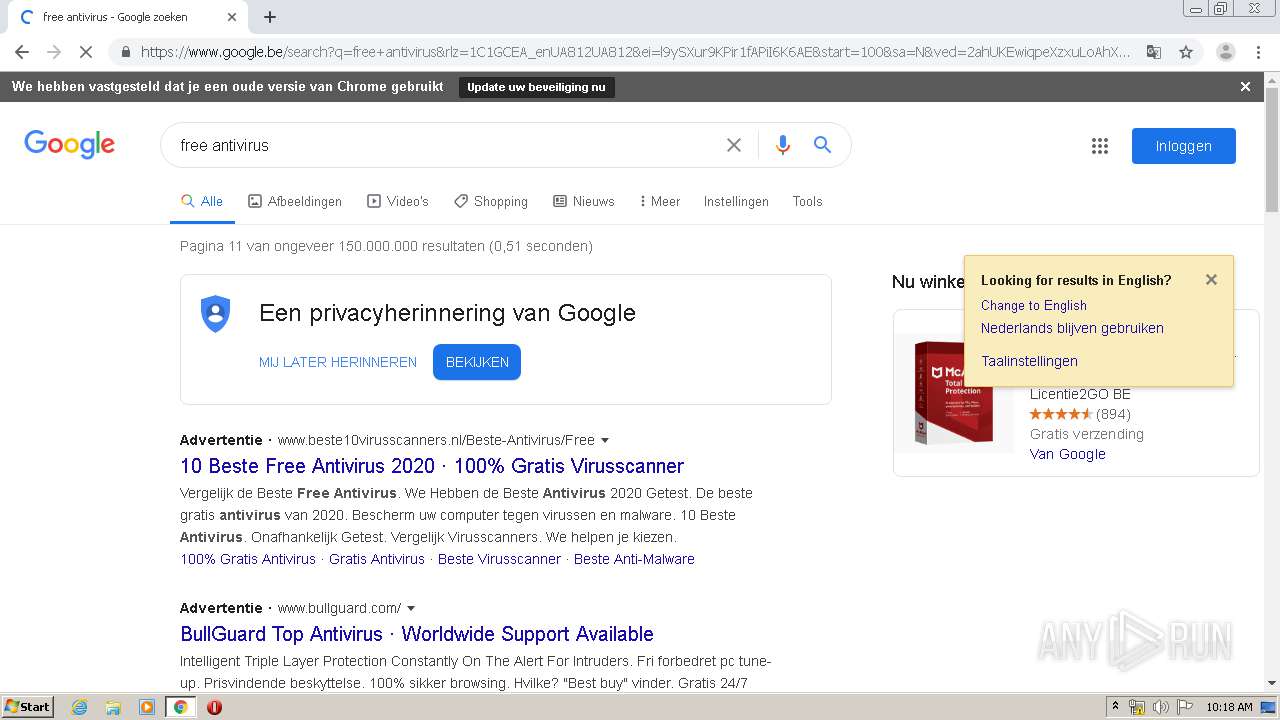
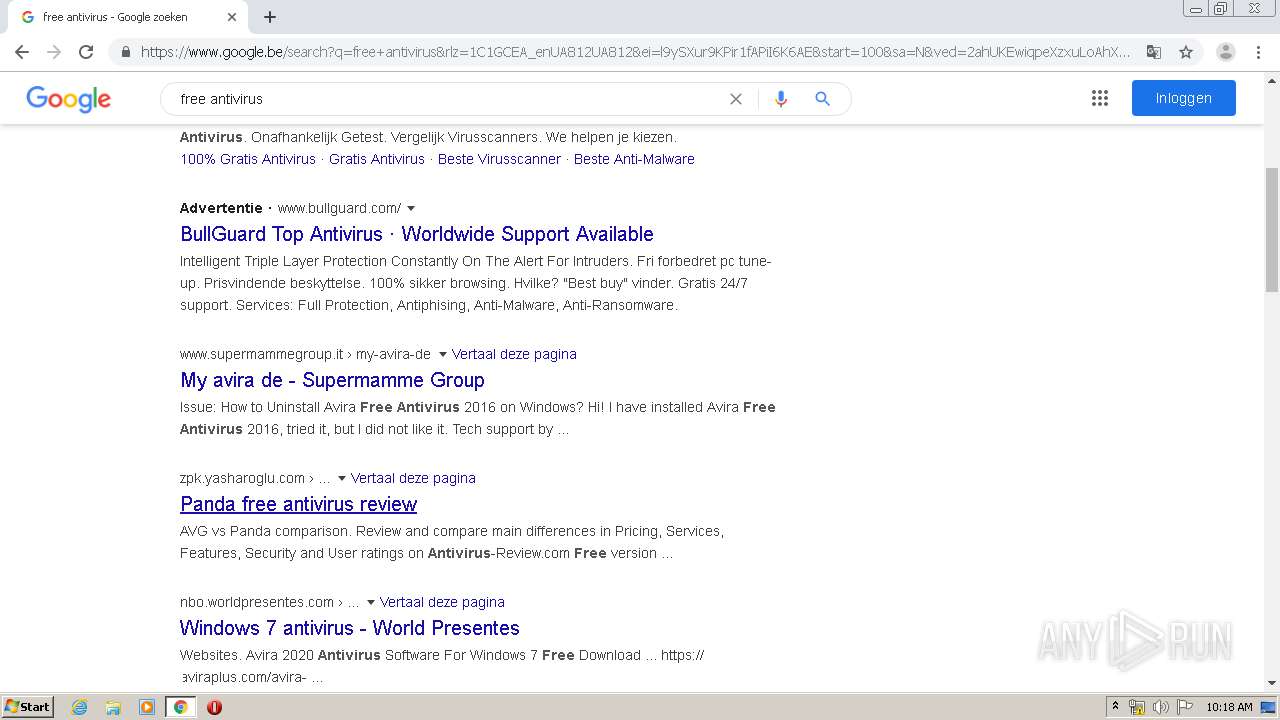
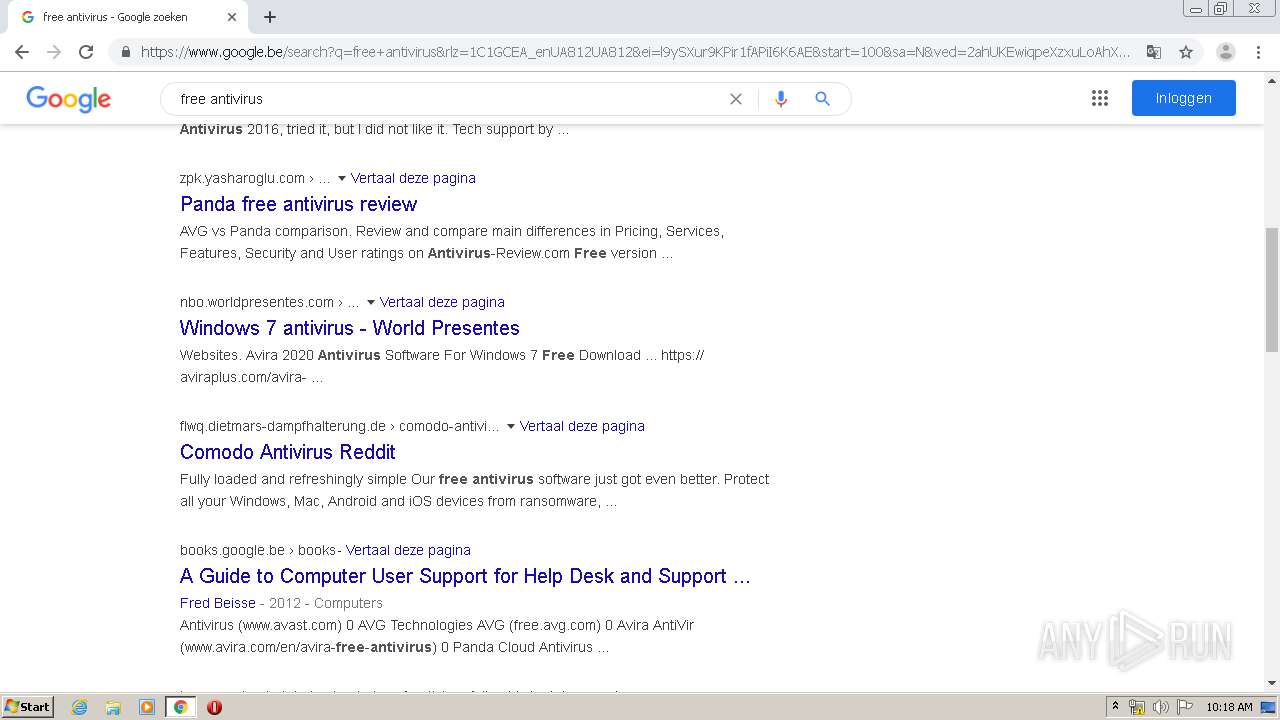
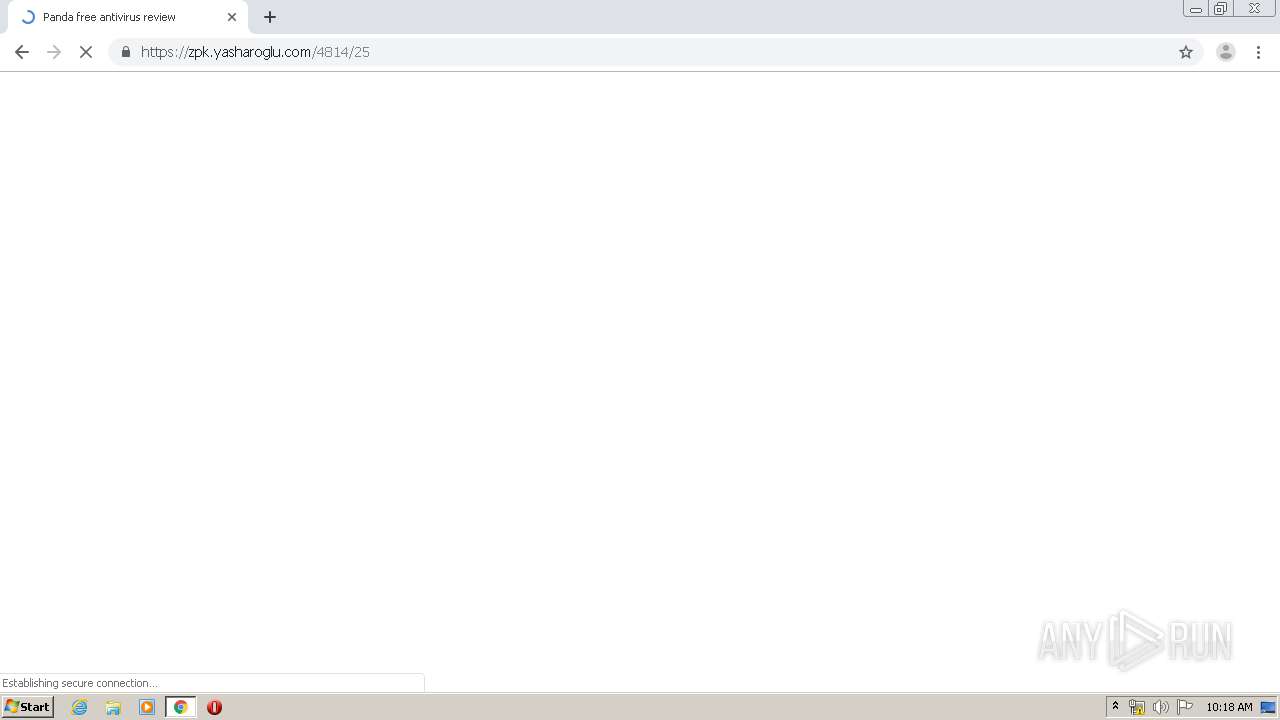
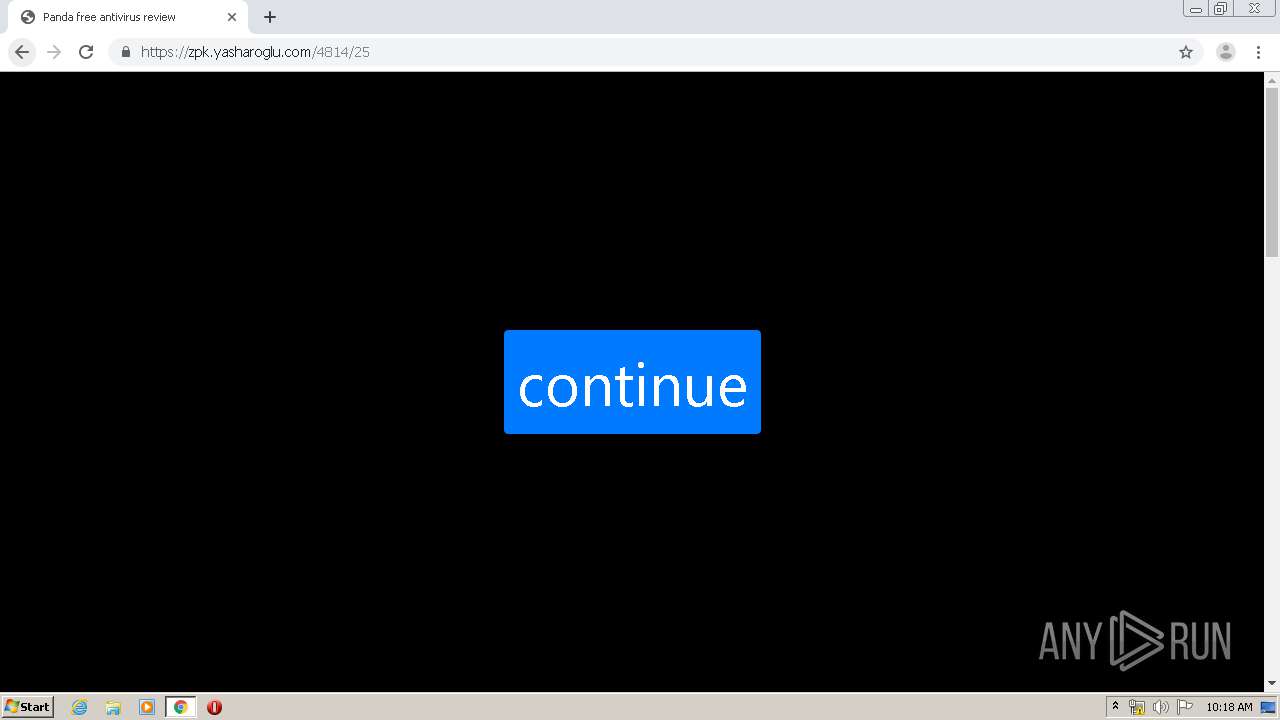
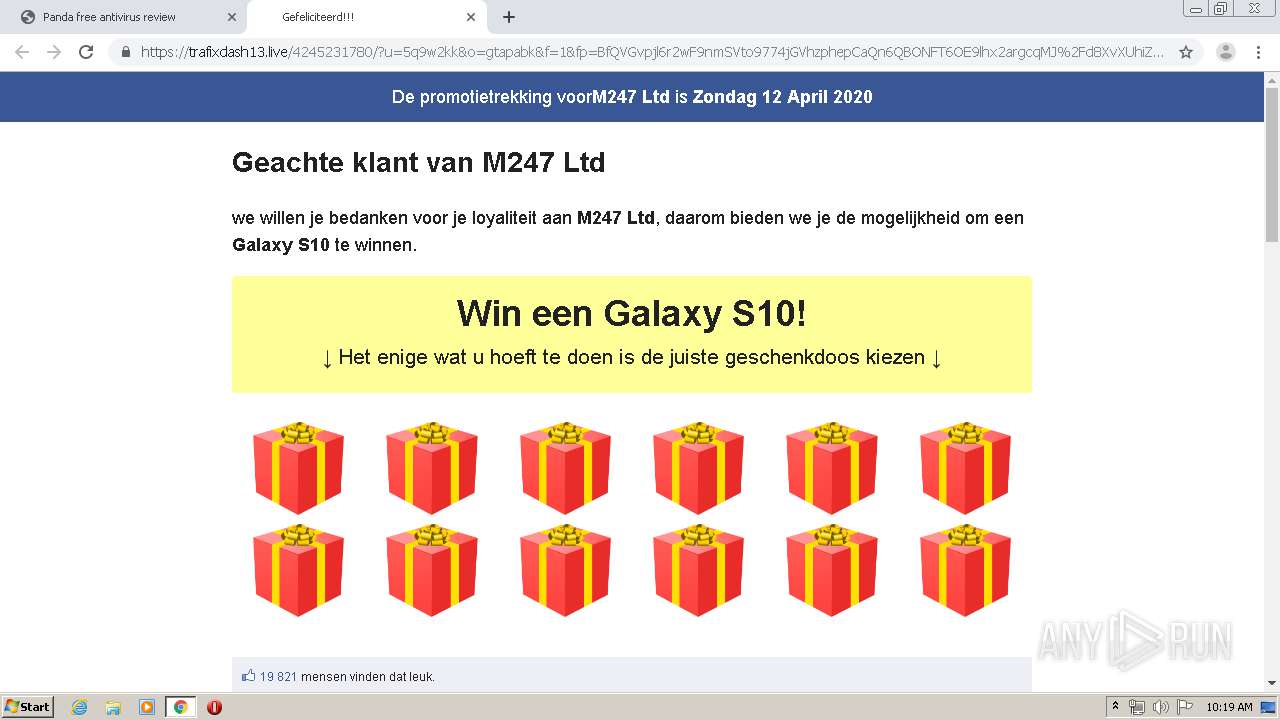
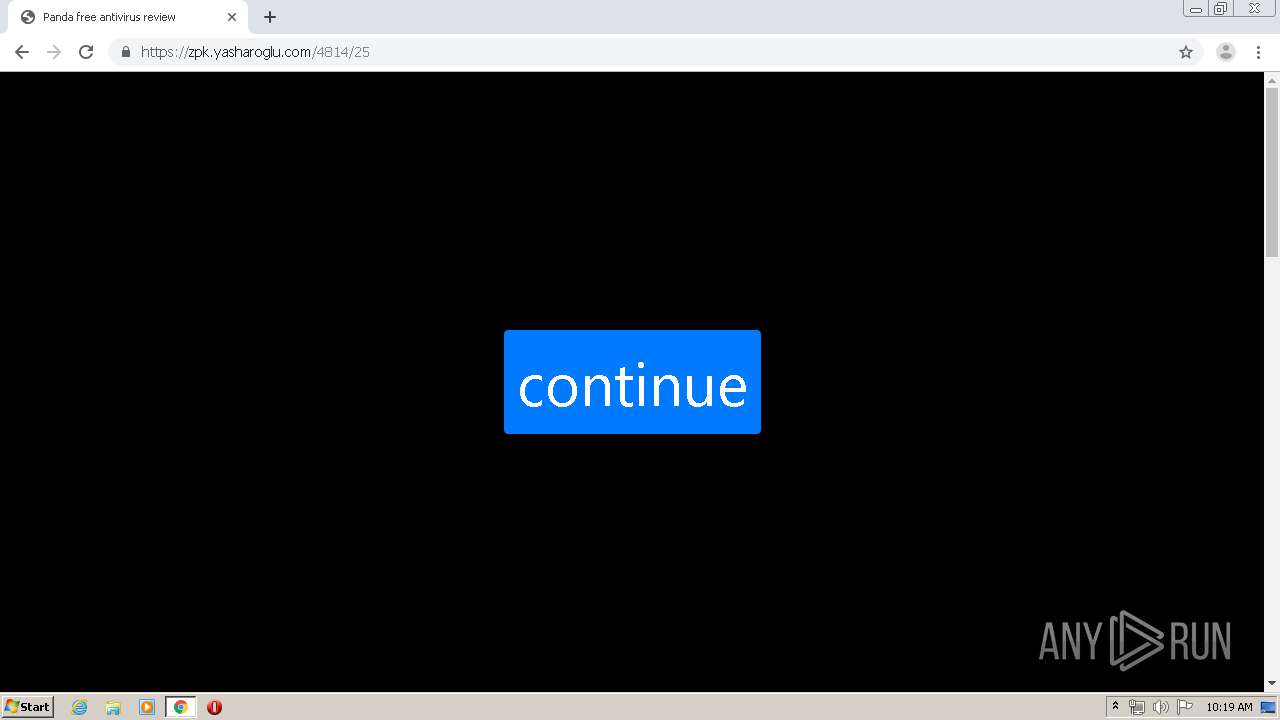
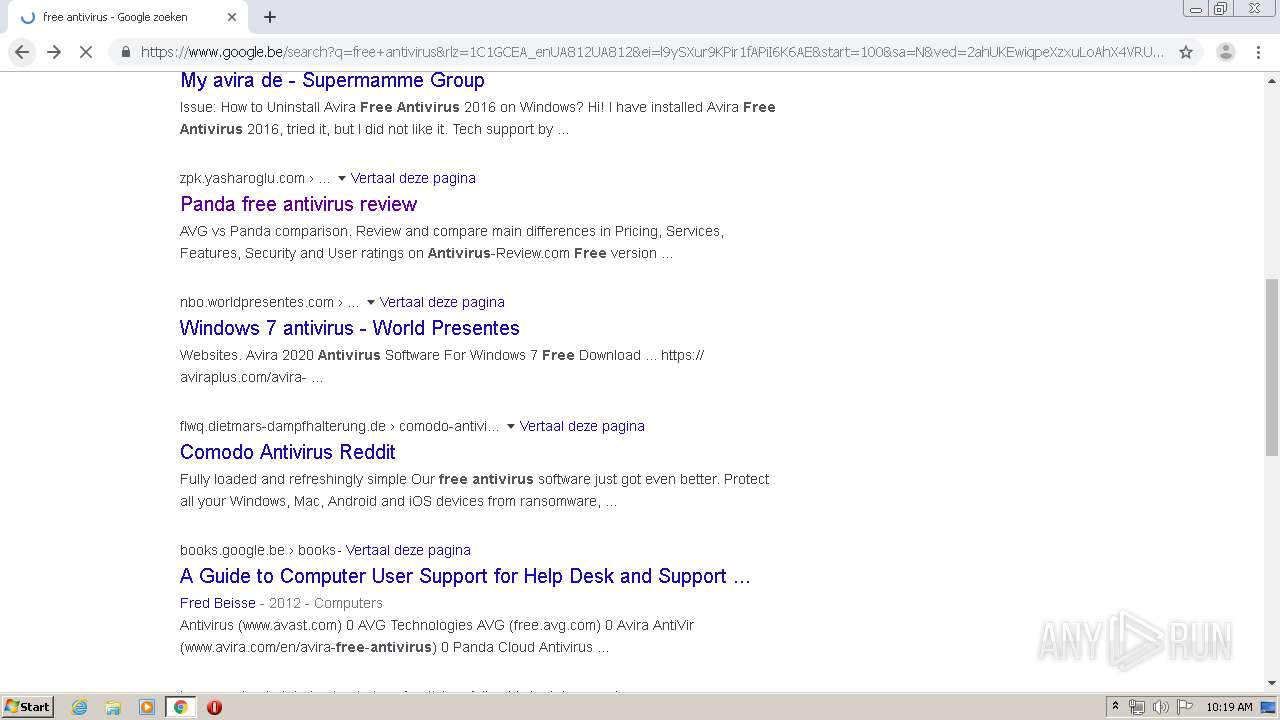
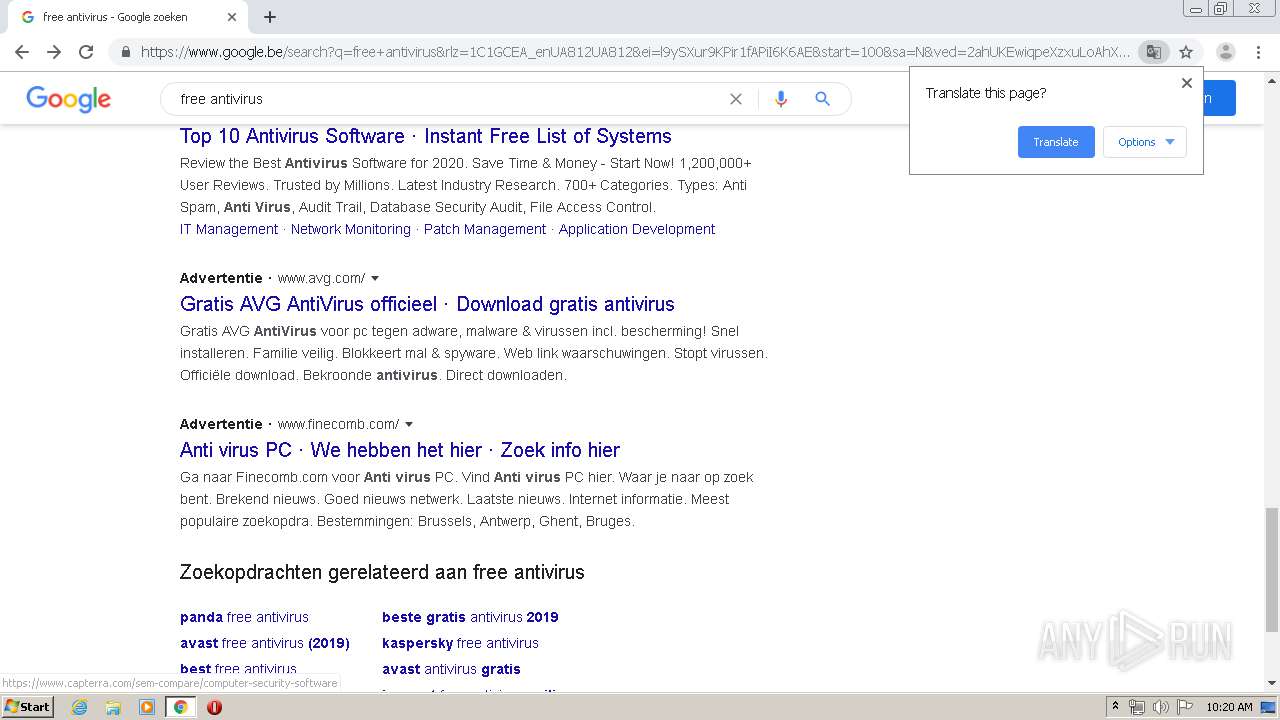
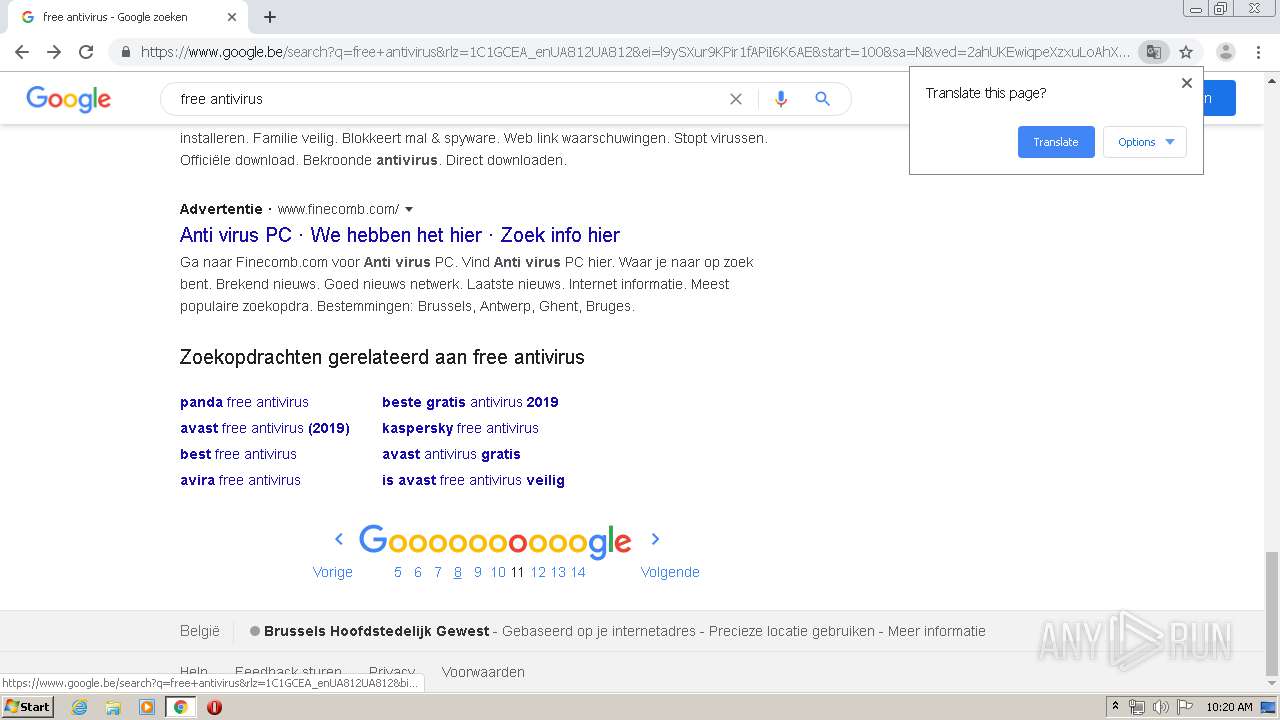
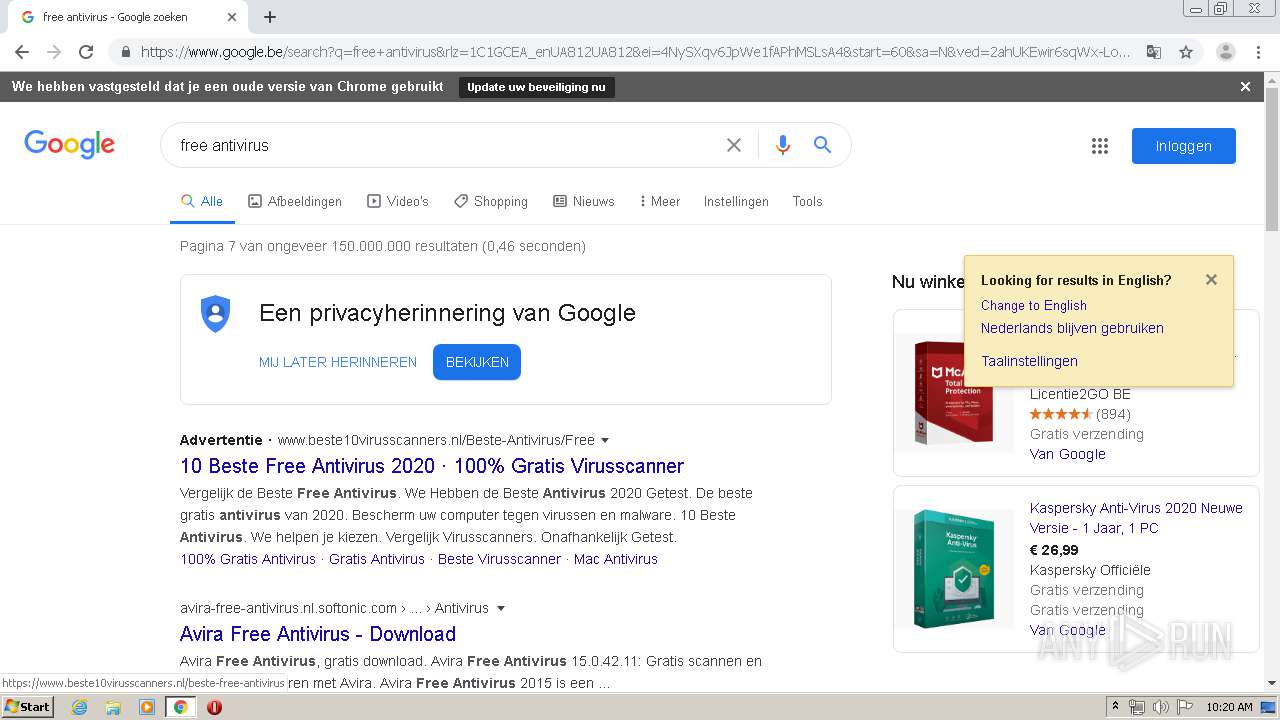
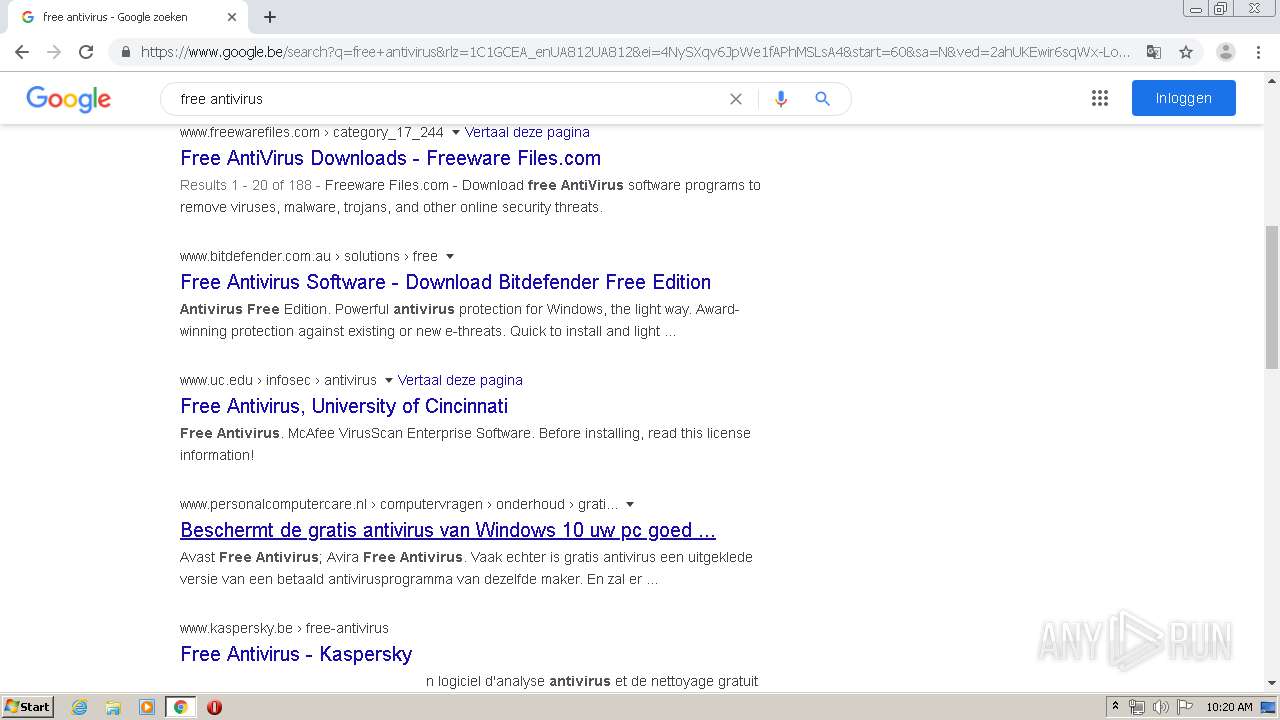
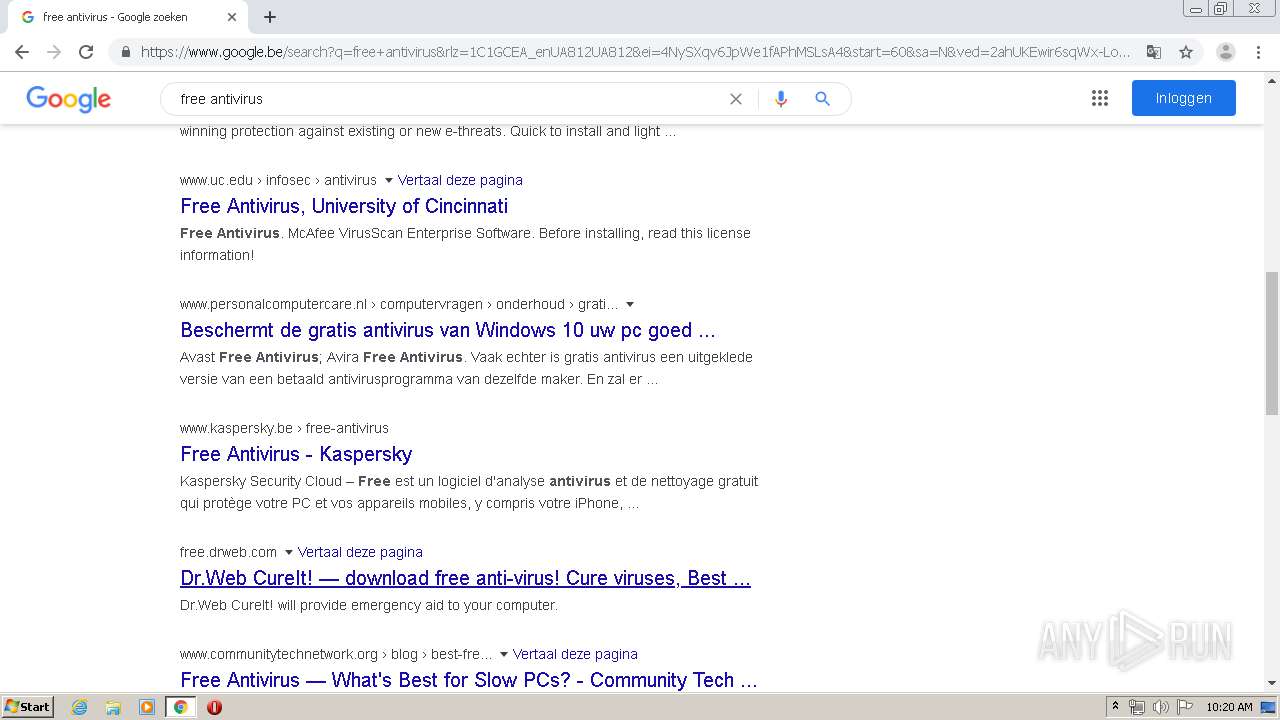
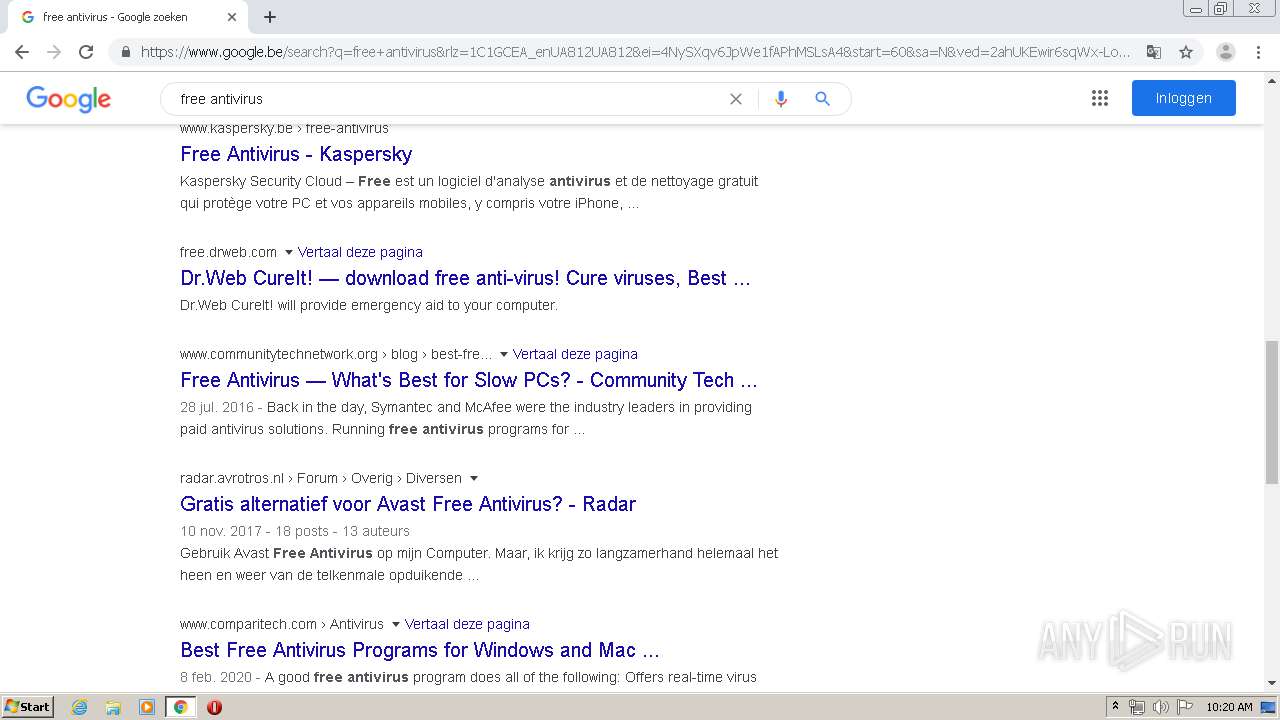
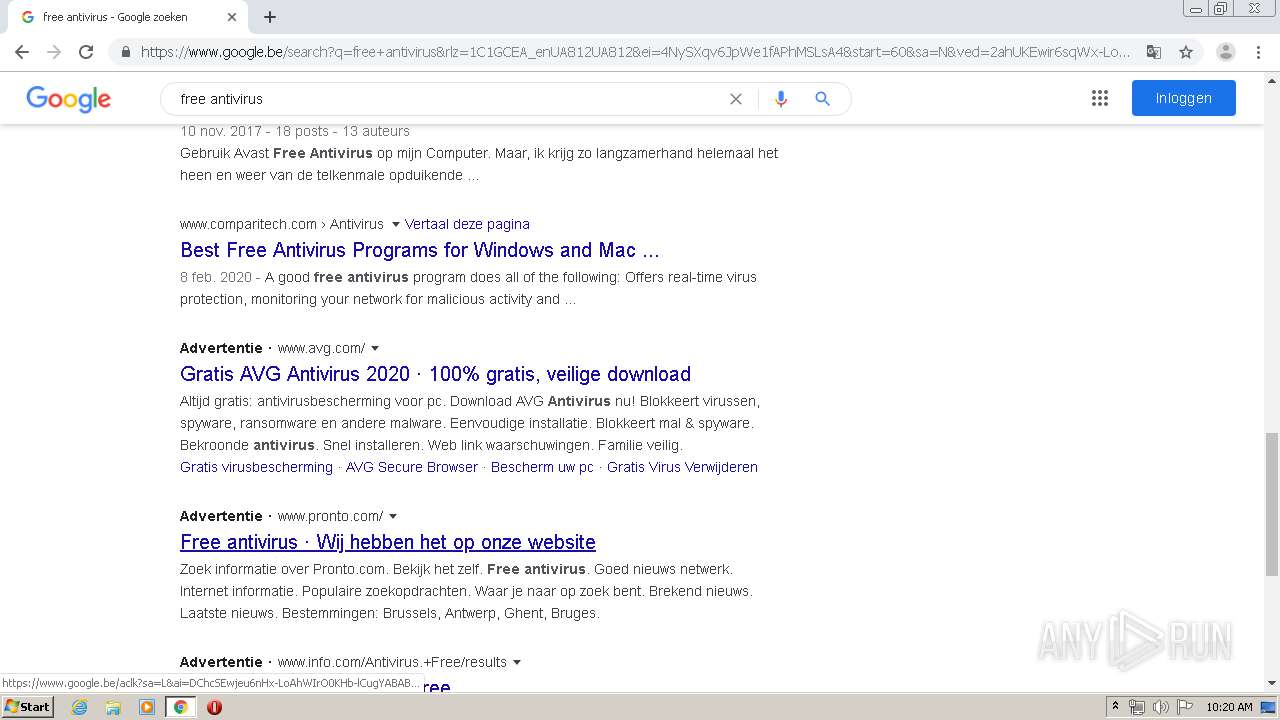
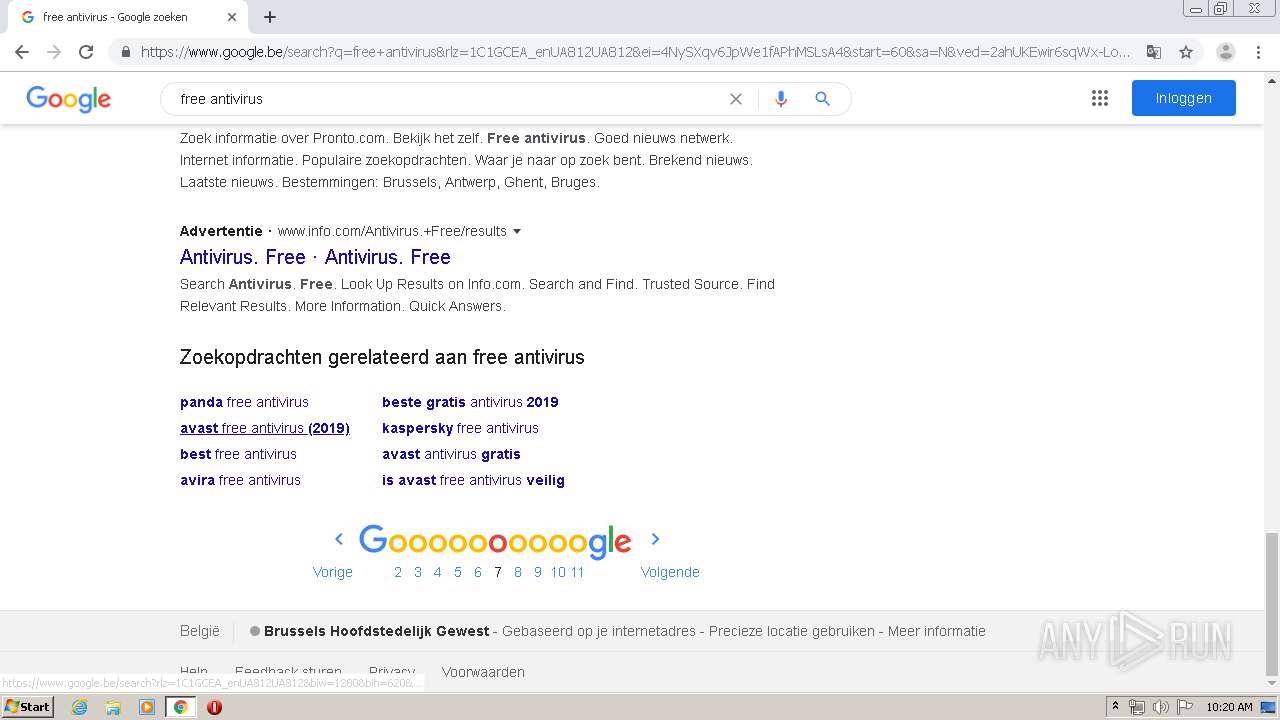
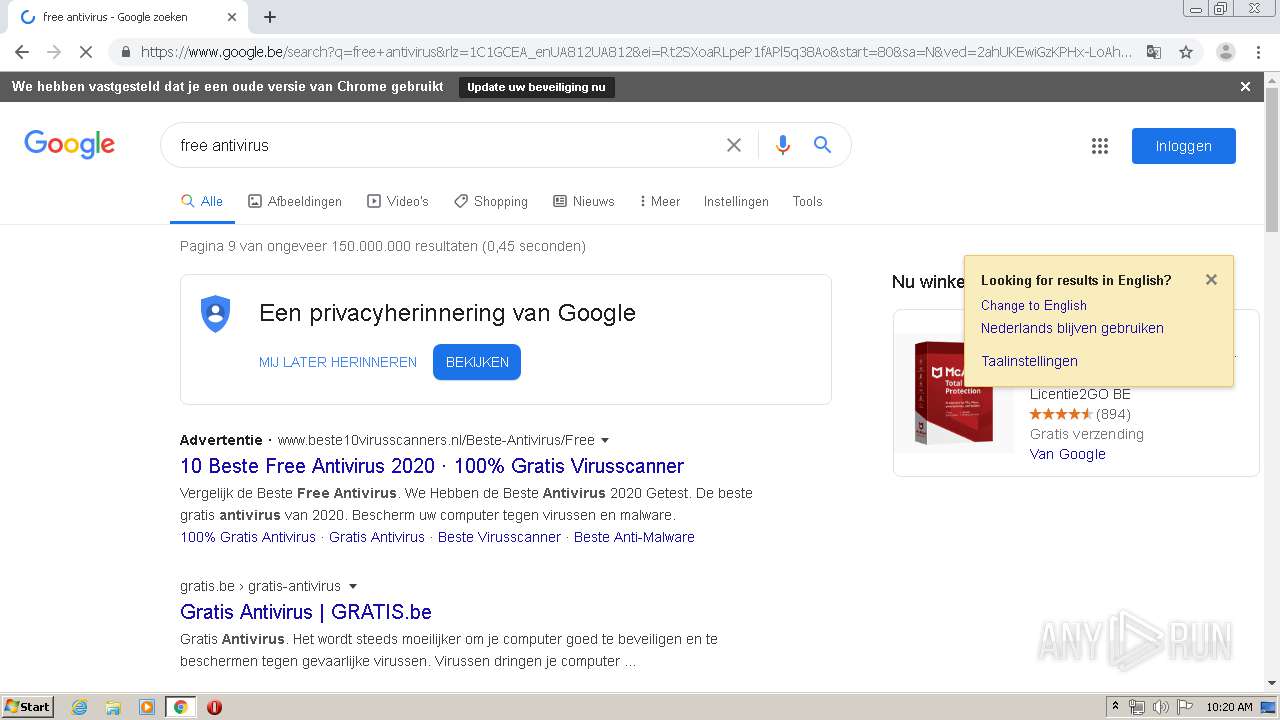
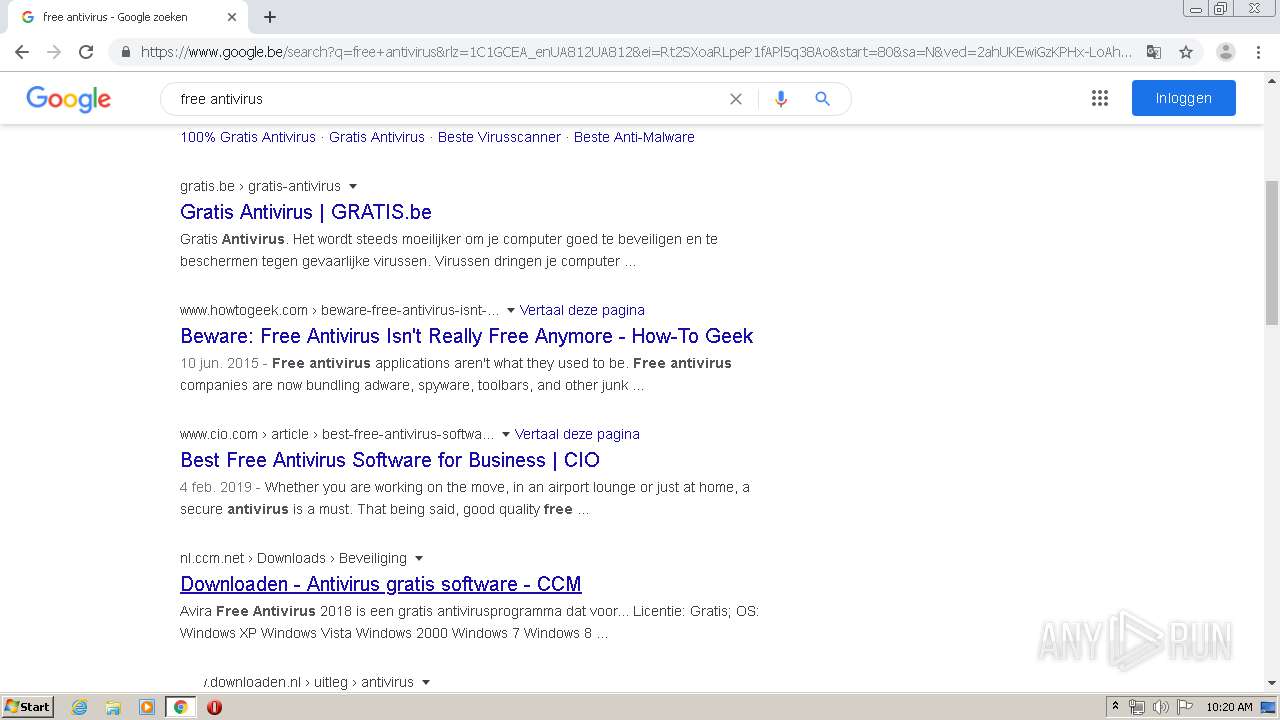
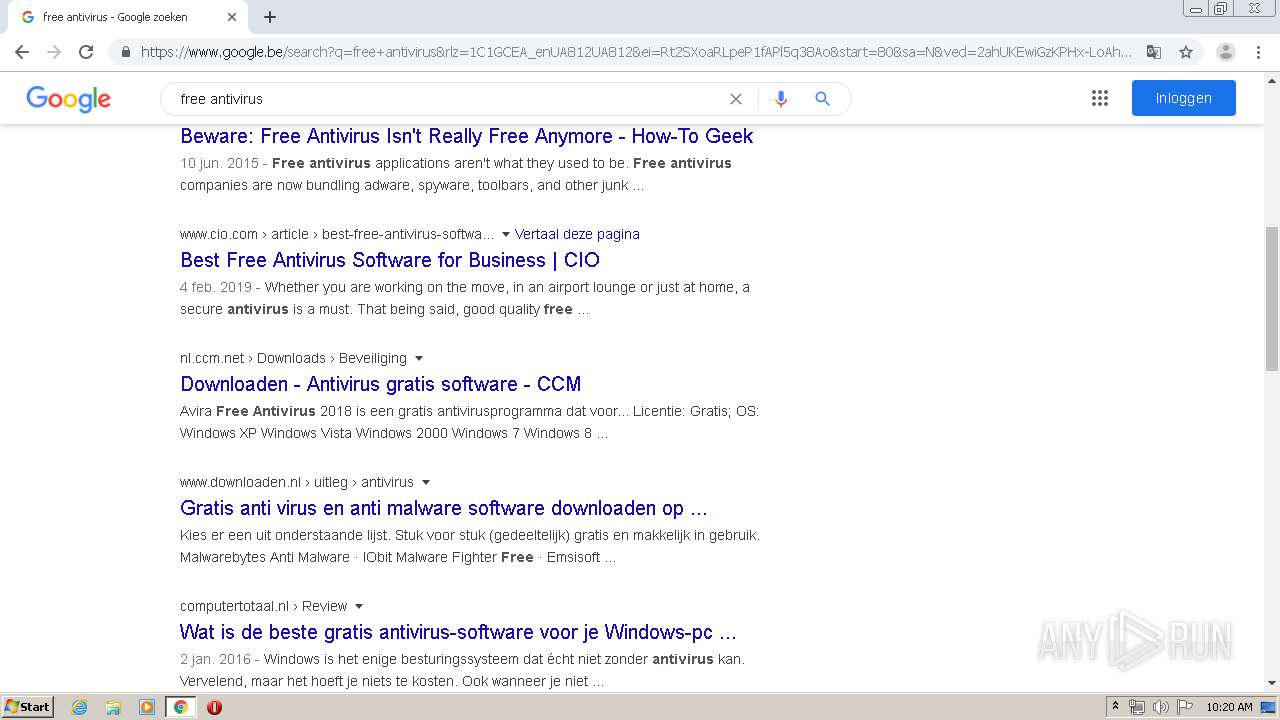
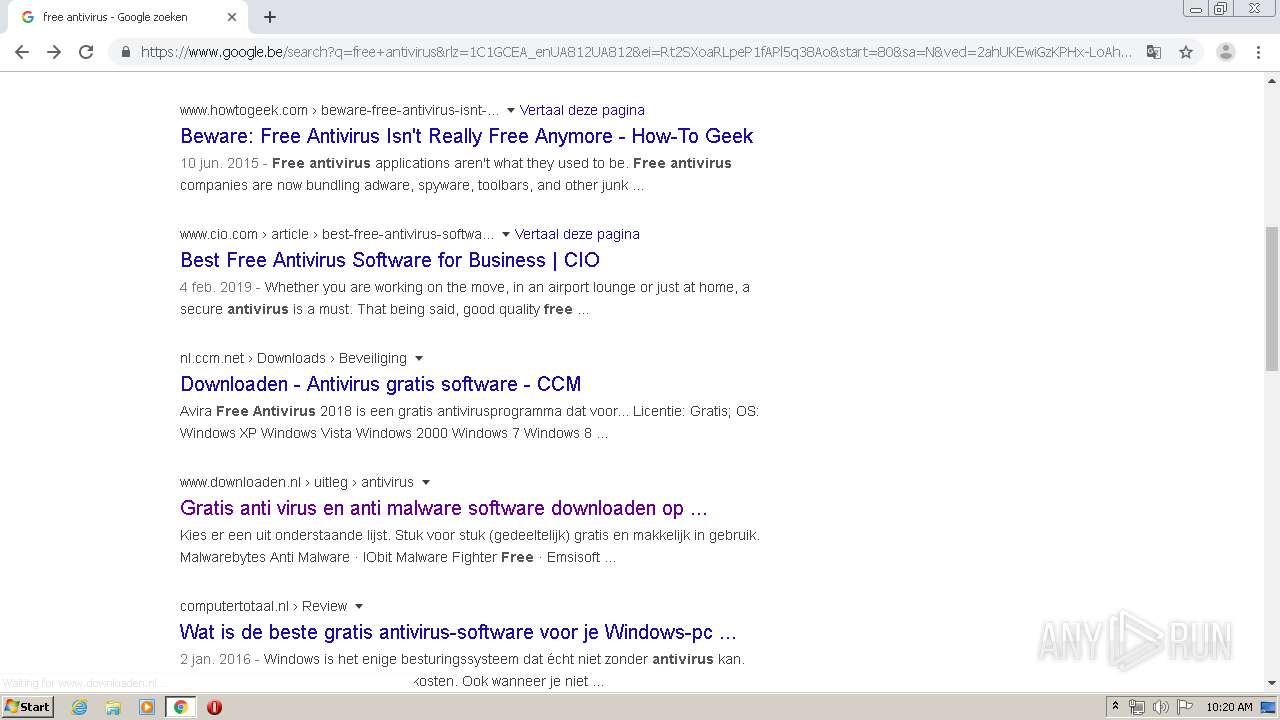
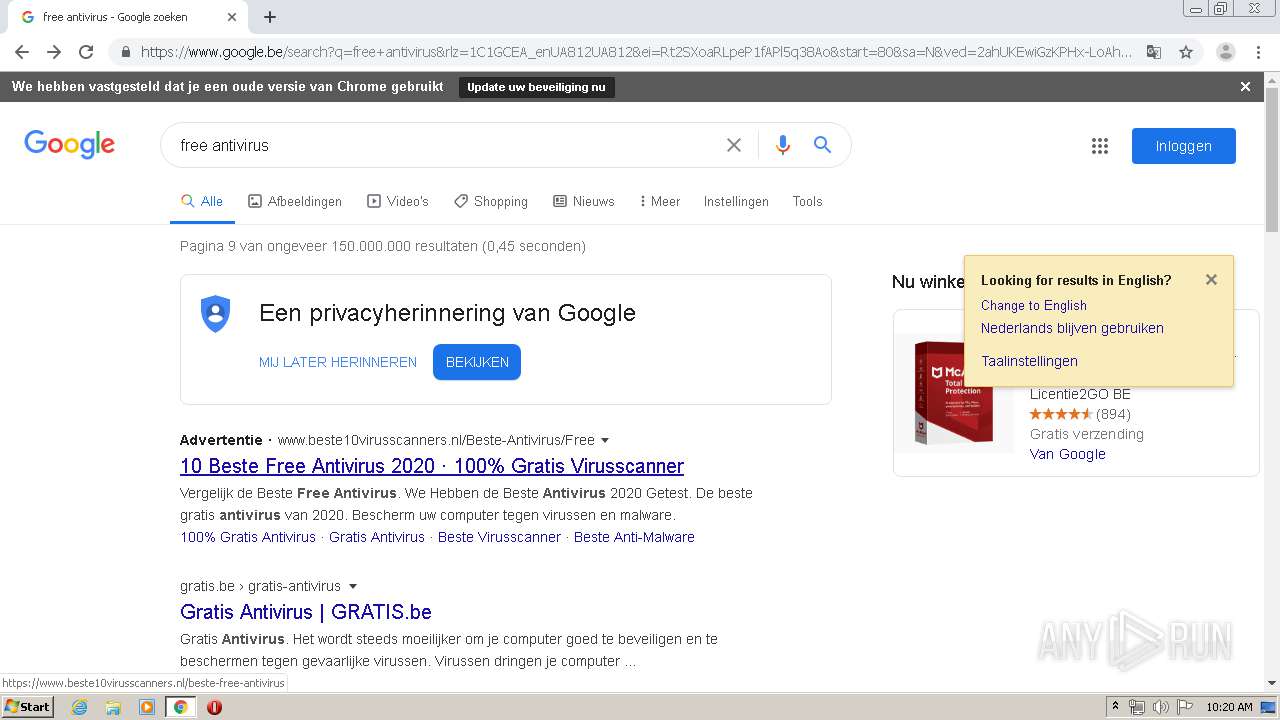
1520 | chrome.exe | GET | 302 | 104.28.12.15:80 | http://skgl.julia-packeiser.de/antivirus-test.html | US | — | — | unknown |
1520 | chrome.exe | GET | 302 | 104.28.10.236:80 | http://vzmq.adequate-services.fr/test-antivirus-mac.html | US | — | — | suspicious |
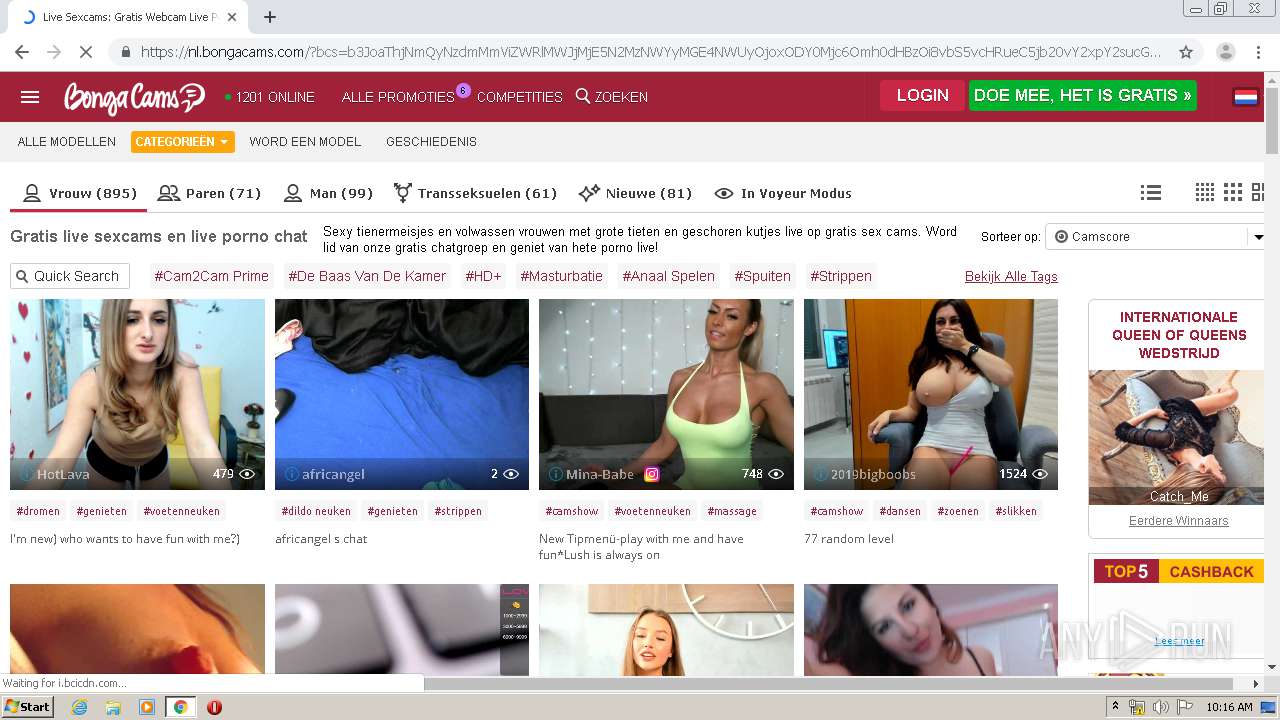
1520 | chrome.exe | GET | 200 | 208.91.196.105:80 | http://texaswhitetailfever.com/ | VG | html | 426 b | malicious |
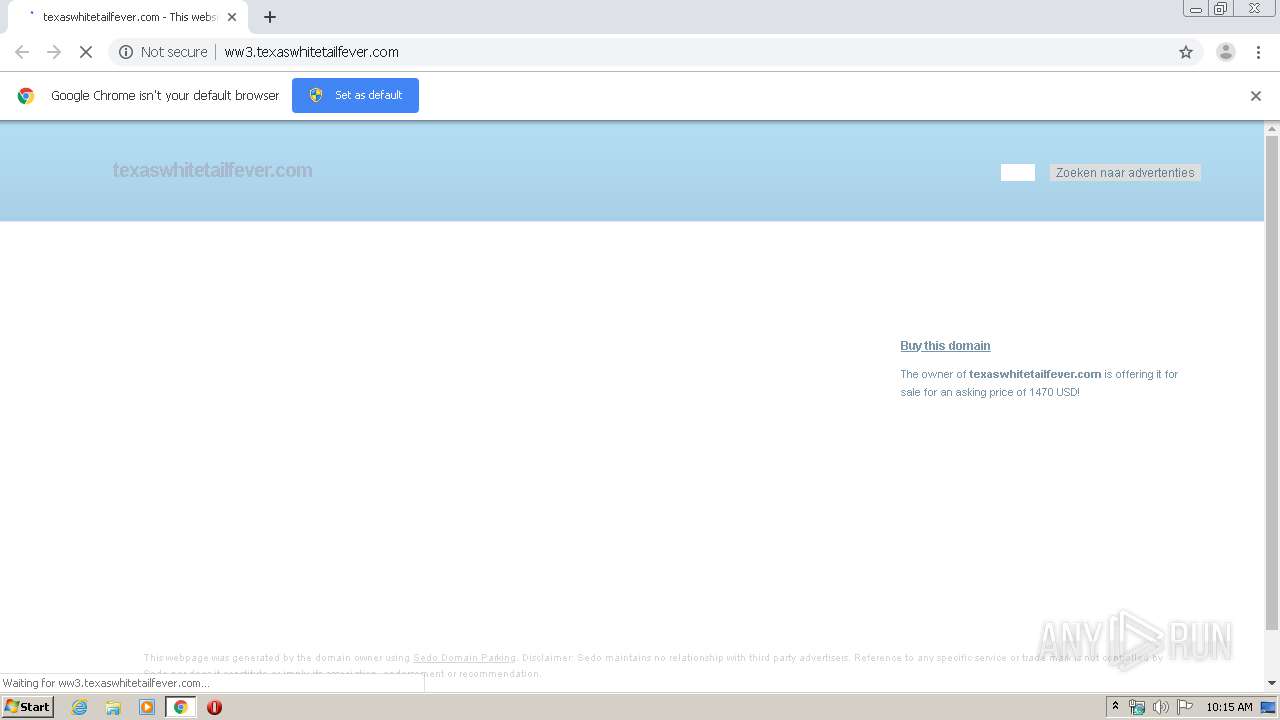
1520 | chrome.exe | GET | 200 | 91.195.240.77:80 | http://ww3.texaswhitetailfever.com/ | DE | html | 9.67 Kb | whitelisted |
1520 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
1520 | chrome.exe | GET | 200 | 91.195.240.77:80 | http://ww3.texaswhitetailfever.com/search/tsc.php?200=MjE3ODczODc1&21=MTk0LjE4Ny4yNTEuMTI1&681=MTU4NjY4MjkzMzY4ZmExMjc4OTE3ZDQwNjJiZWIyMTE2NzhkM2VmNzQ2&crc=4dc6419086761572a266080ca4ff5aa07bc059da&cv=1 | DE | compressed | 9.67 Kb | whitelisted |
1520 | chrome.exe | GET | 200 | 81.4.96.107:80 | http://www.computerhandleiding.nl/afbeeldingen/algemeen/index2.gif | NL | image | 417 b | suspicious |
1520 | chrome.exe | GET | 200 | 216.58.208.36:80 | http://www.google.com/adsense/domains/caf.js | US | text | 56.6 Kb | malicious |
1520 | chrome.exe | GET | 200 | 81.4.96.107:80 | http://www.computerhandleiding.nl/afbeeldingen/algemeen/logostandaard.gif | NL | image | 2.13 Kb | suspicious |
1520 | chrome.exe | GET | 200 | 81.4.96.107:80 | http://www.computerhandleiding.nl/afbeeldingen/algemeen/site.gif | NL | image | 397 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1520 | chrome.exe | 208.91.196.105:80 | texaswhitetailfever.com | Confluence Networks Inc | VG | malicious |
1520 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 172.217.21.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 208.91.196.105:80 | texaswhitetailfever.com | Confluence Networks Inc | VG | malicious |
1520 | chrome.exe | 74.125.4.166:80 | r1---sn-aigzrne7.gvt1.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 216.58.207.65:443 | afs.googleusercontent.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
texaswhitetailfever.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ww3.texaswhitetailfever.com |
| unknown |
img.sedoparking.com |
| whitelisted |
www.google.com |
| malicious |
www.sedo.com |
| whitelisted |
advexplore.com |
| whitelisted |
clients1.google.com |
| whitelisted |
afs.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
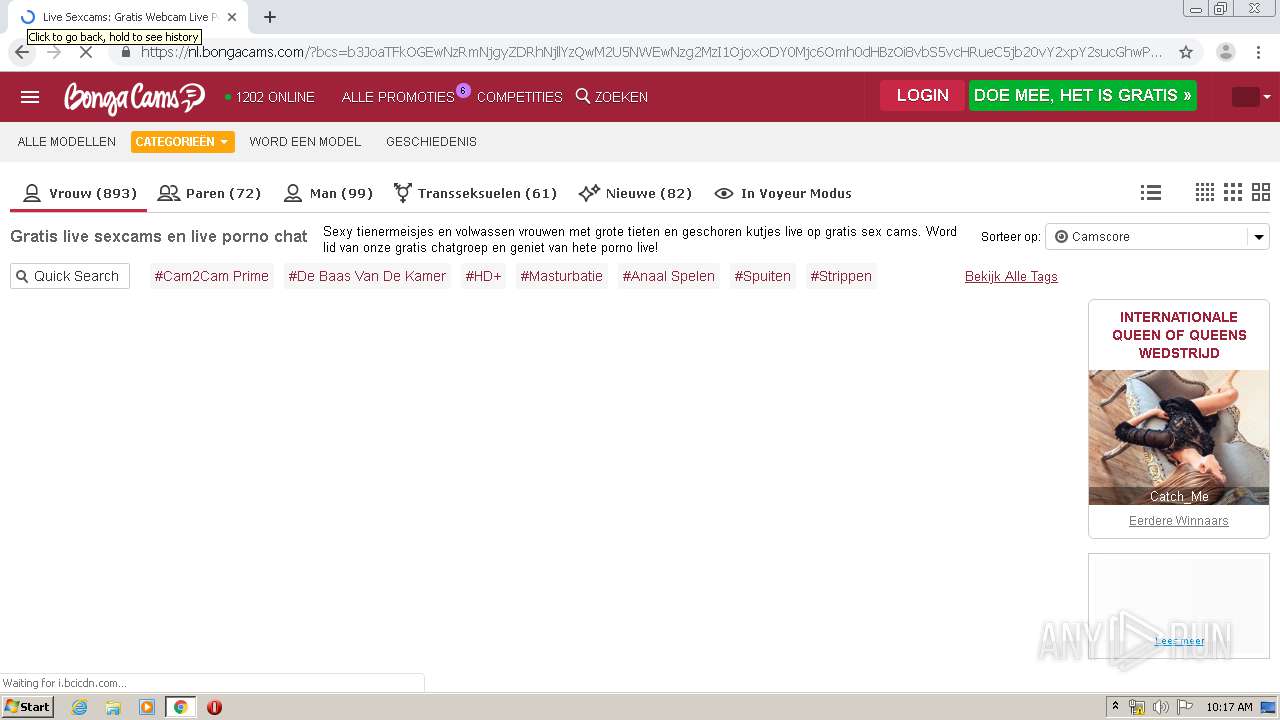
1520 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1520 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
1520 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
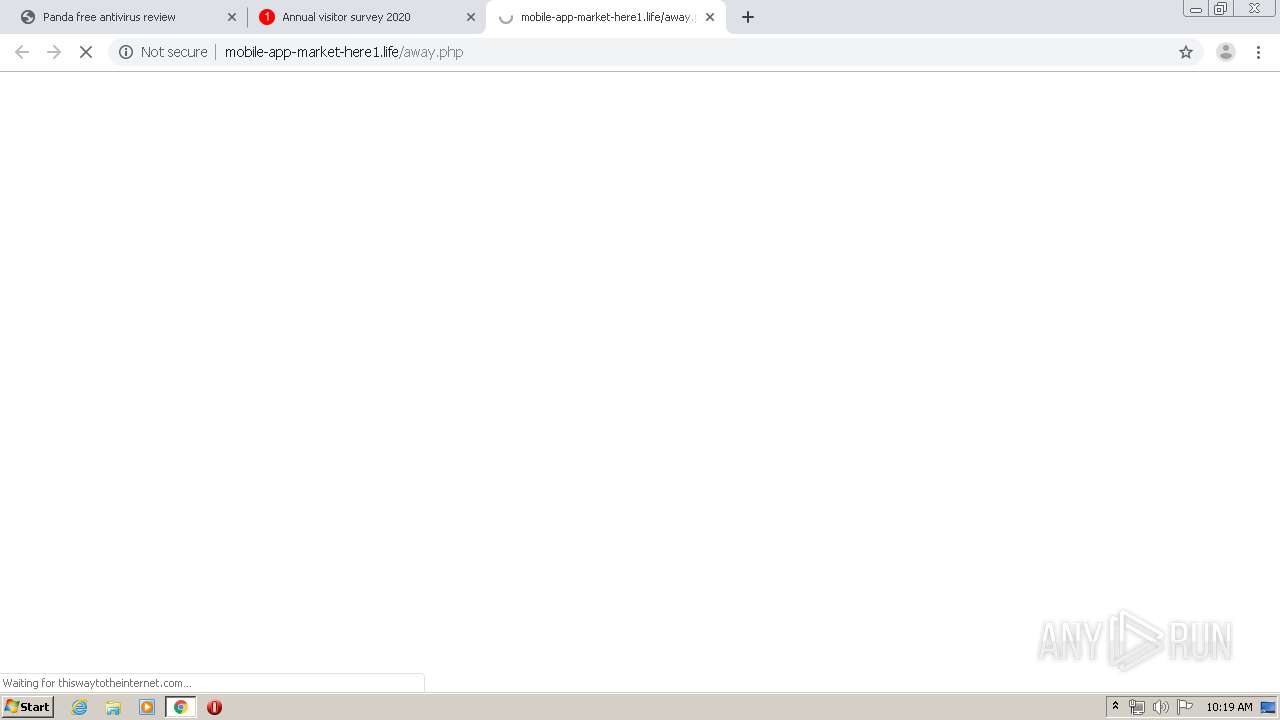
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1520 | chrome.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 23 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1520 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1520 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1 ETPRO signatures available at the full report