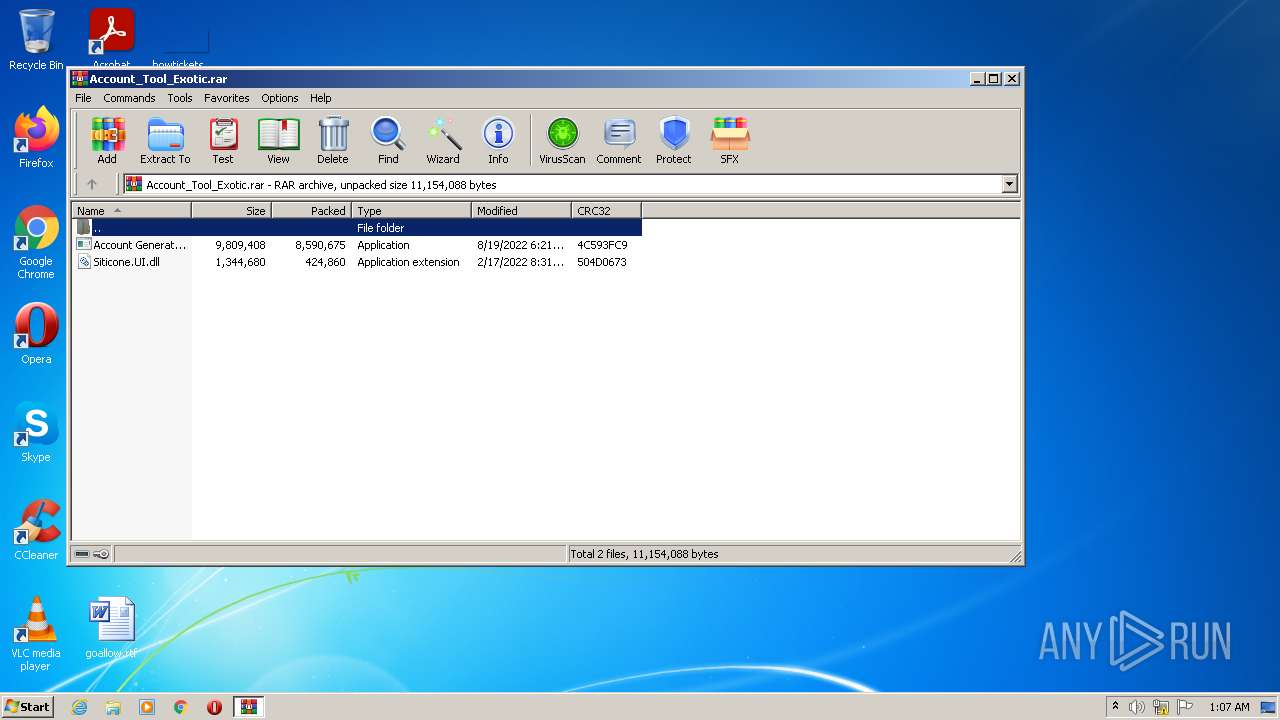
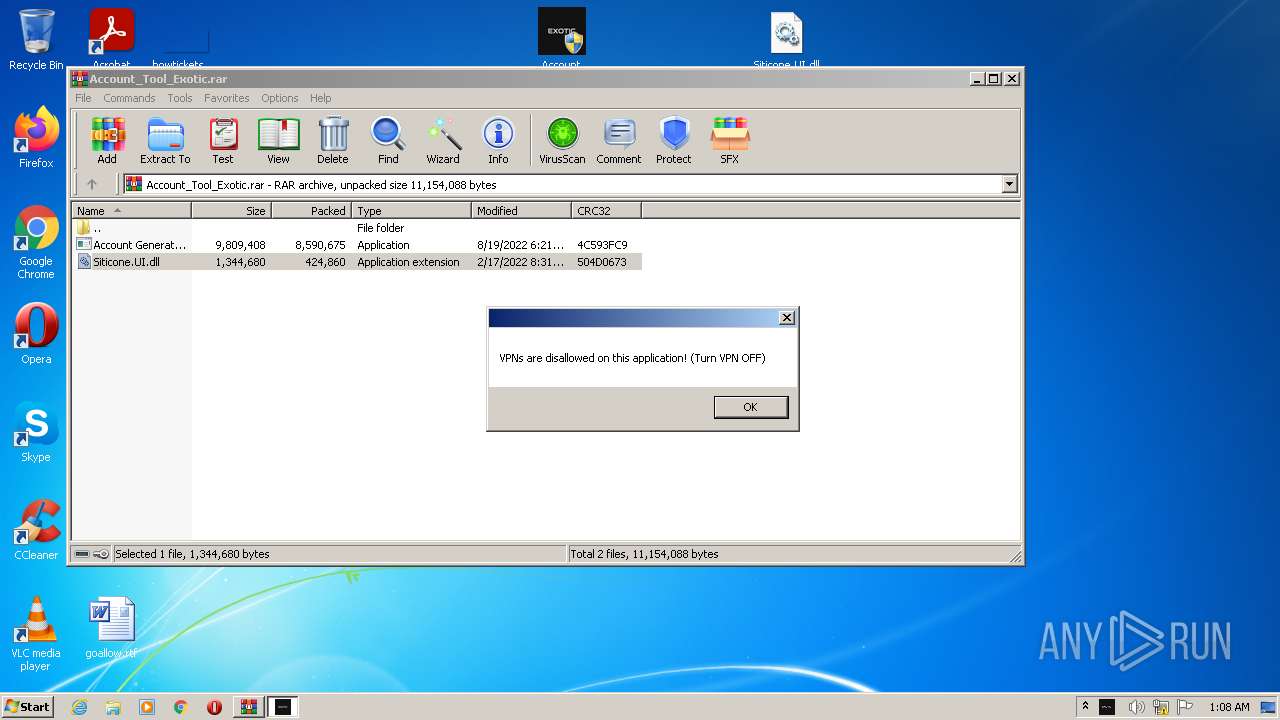
| File name: | Account_Tool_Exotic.rar |
| Full analysis: | https://app.any.run/tasks/0d7b7c46-b0f1-4e0c-85bd-020841fd0e04 |
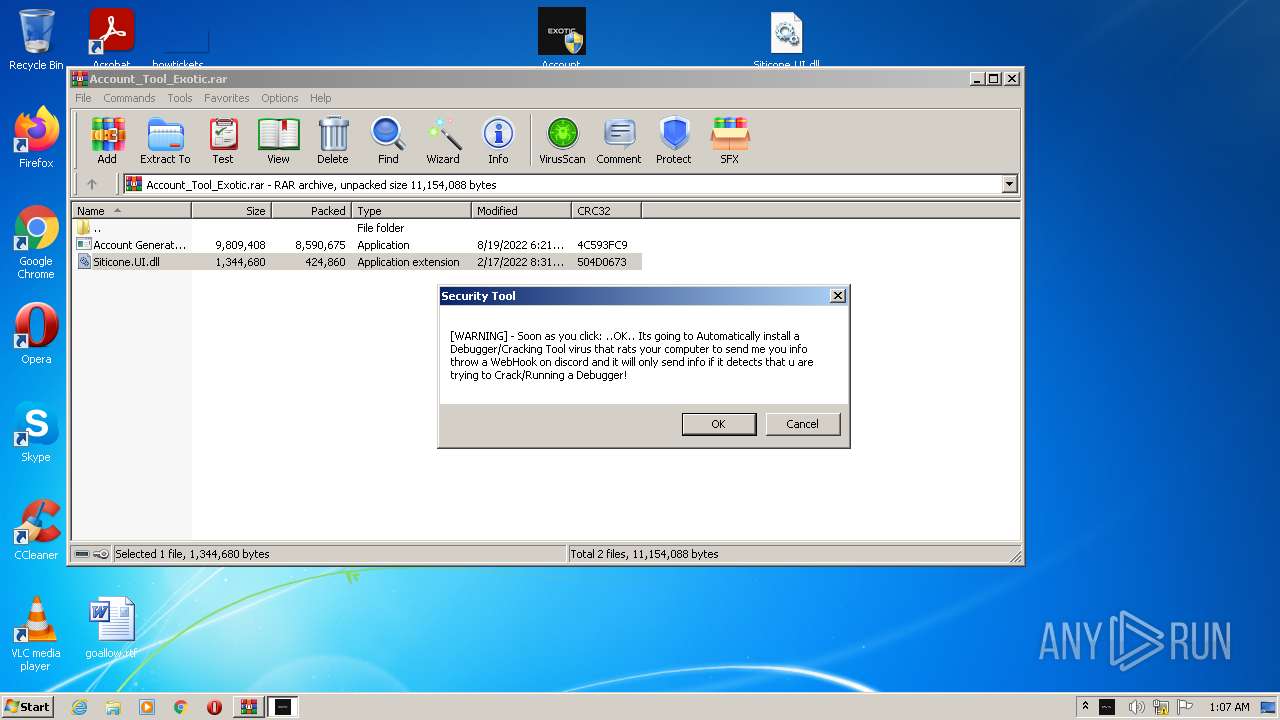
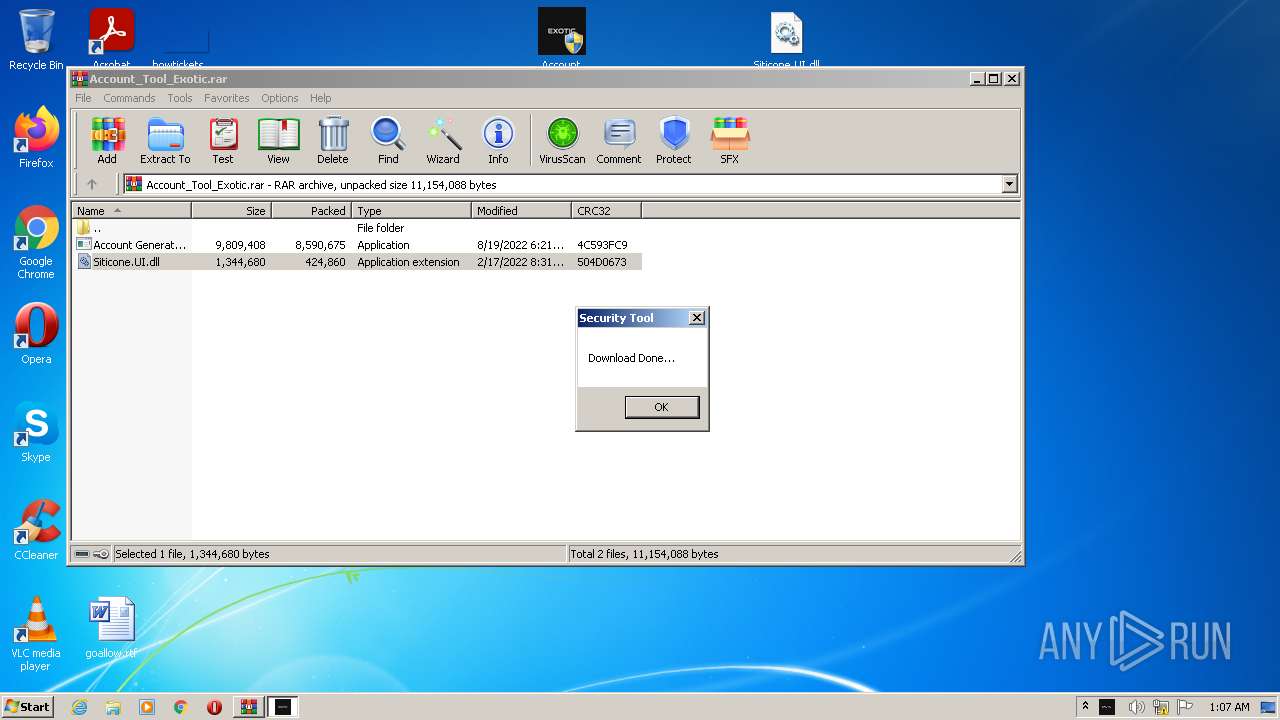
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 00:07:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C70F51E0DE5DDFF3BE3AB1D208FF7042 |
| SHA1: | F1814CB7E5CC5A99CA5D773B619BF41D5EBBE4DE |
| SHA256: | CFDA3C8121BE164CDCF43766499D23349FFCD56C59AB98056B7838FCF44DD790 |
| SSDEEP: | 196608:yphSKKxset5Th0d+IZDToLO4SwpT7HOeML/mhJJp/XKw1pUq43zRqQpZ:shesetNSZBULO4SwMeImJJdT1n4Zf |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 4076)
- Account Generator v8.1.2.exe (PID: 2364)
Application was dropped or rewritten from another process
- Account Generator v8.1.2.exe (PID: 3484)
- Account Generator v8.1.2.exe (PID: 2364)
Drops executable file immediately after starts
- WinRAR.exe (PID: 2552)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2552)
- Account Generator v8.1.2.exe (PID: 2364)
Checks supported languages
- WinRAR.exe (PID: 2552)
- Account Generator v8.1.2.exe (PID: 2364)
- cmd.exe (PID: 3120)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2552)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2552)
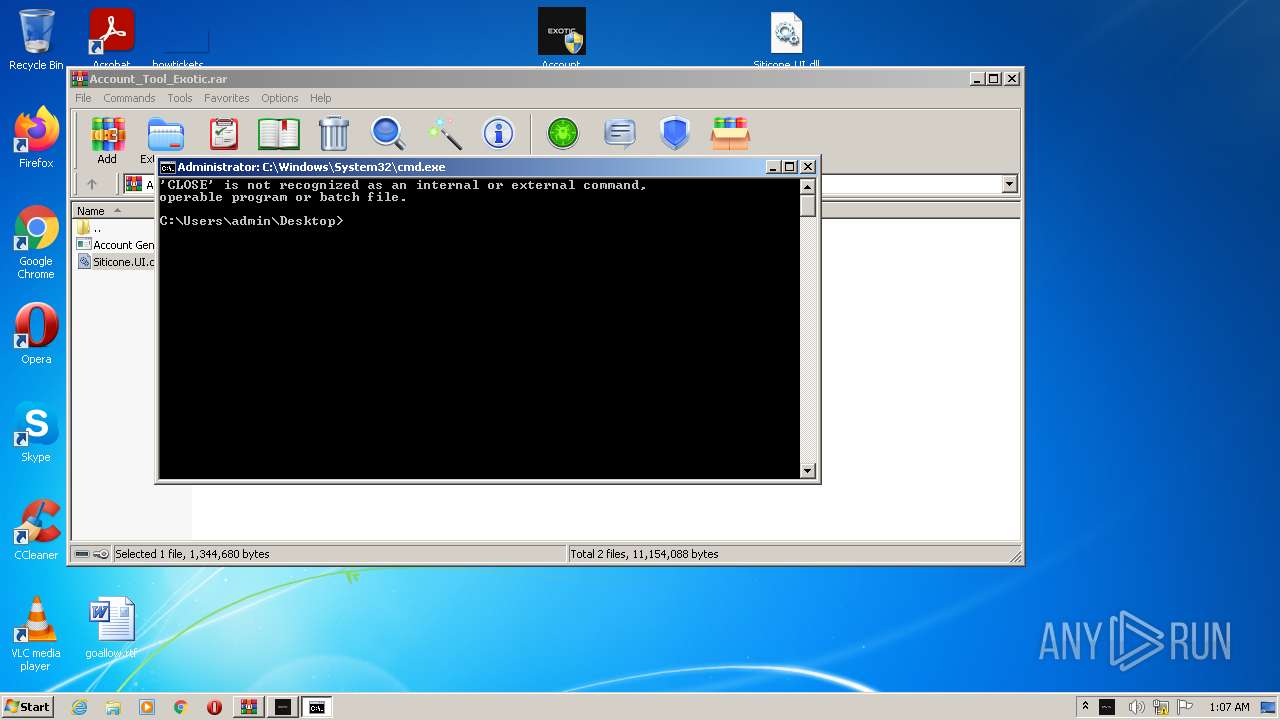
Starts CMD.EXE for commands execution
- Account Generator v8.1.2.exe (PID: 2364)
Reads Environment values
- Account Generator v8.1.2.exe (PID: 2364)
INFO
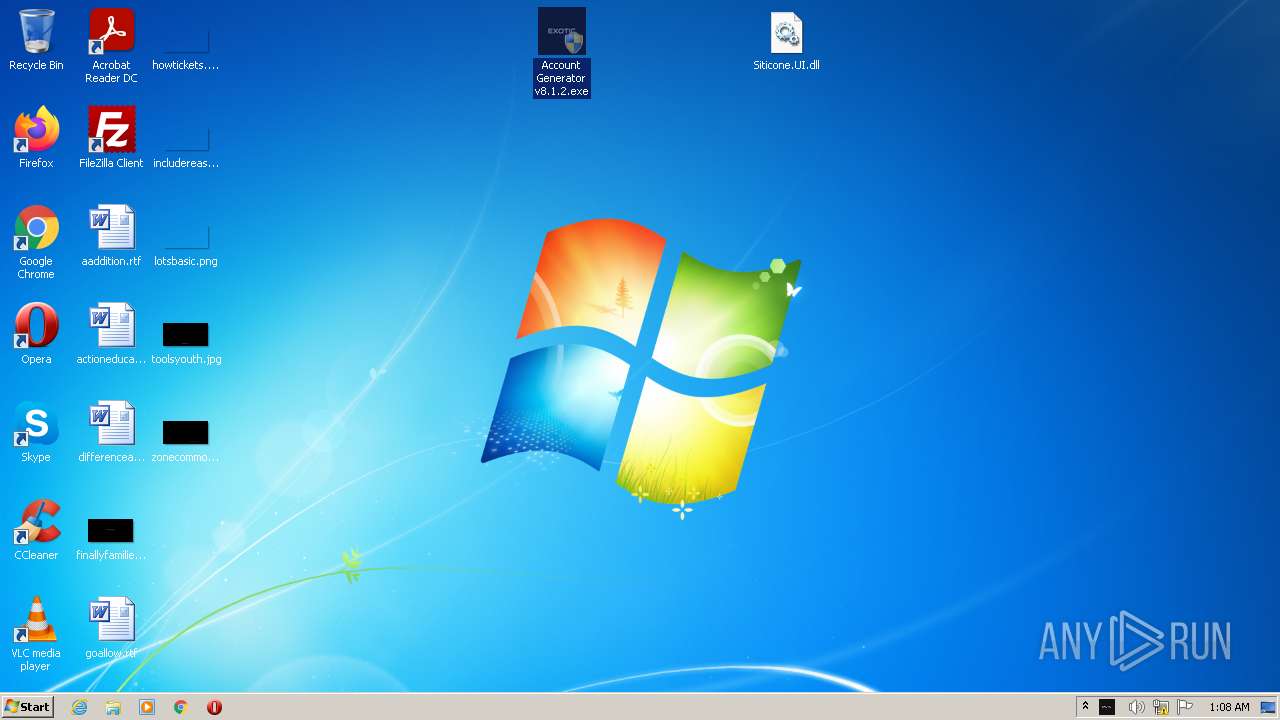
Manual execution by user
- Account Generator v8.1.2.exe (PID: 3484)
- Account Generator v8.1.2.exe (PID: 2364)
Reads settings of System Certificates
- Account Generator v8.1.2.exe (PID: 2364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
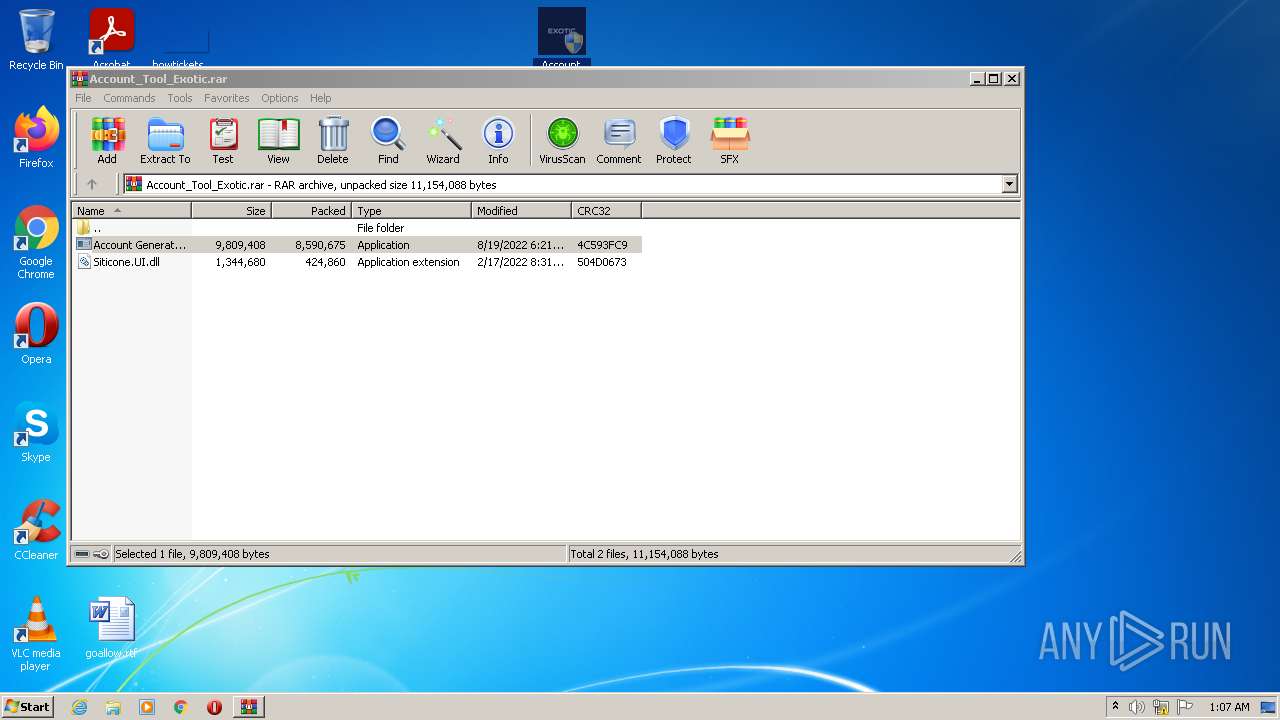
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | "C:\Users\admin\Desktop\Account Generator v8.1.2.exe" | C:\Users\admin\Desktop\Account Generator v8.1.2.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Loader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Account_Tool_Exotic.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3120 | "C:\Windows\System32\cmd.exe" /k CLOSE NOW! | C:\Windows\System32\cmd.exe | — | Account Generator v8.1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\Desktop\Account Generator v8.1.2.exe" | C:\Users\admin\Desktop\Account Generator v8.1.2.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Loader Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4076 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
4 386
Read events
4 331
Write events
55
Delete events
0
Modification events
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Account_Tool_Exotic.rar | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
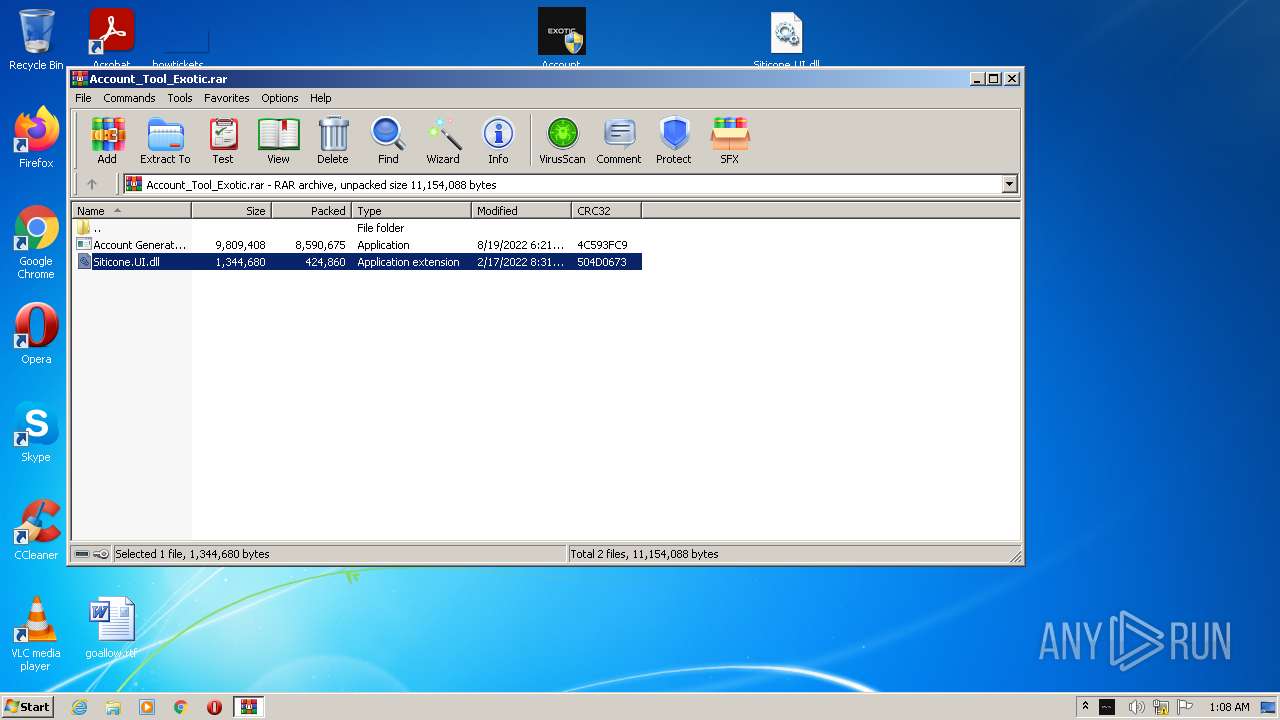
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
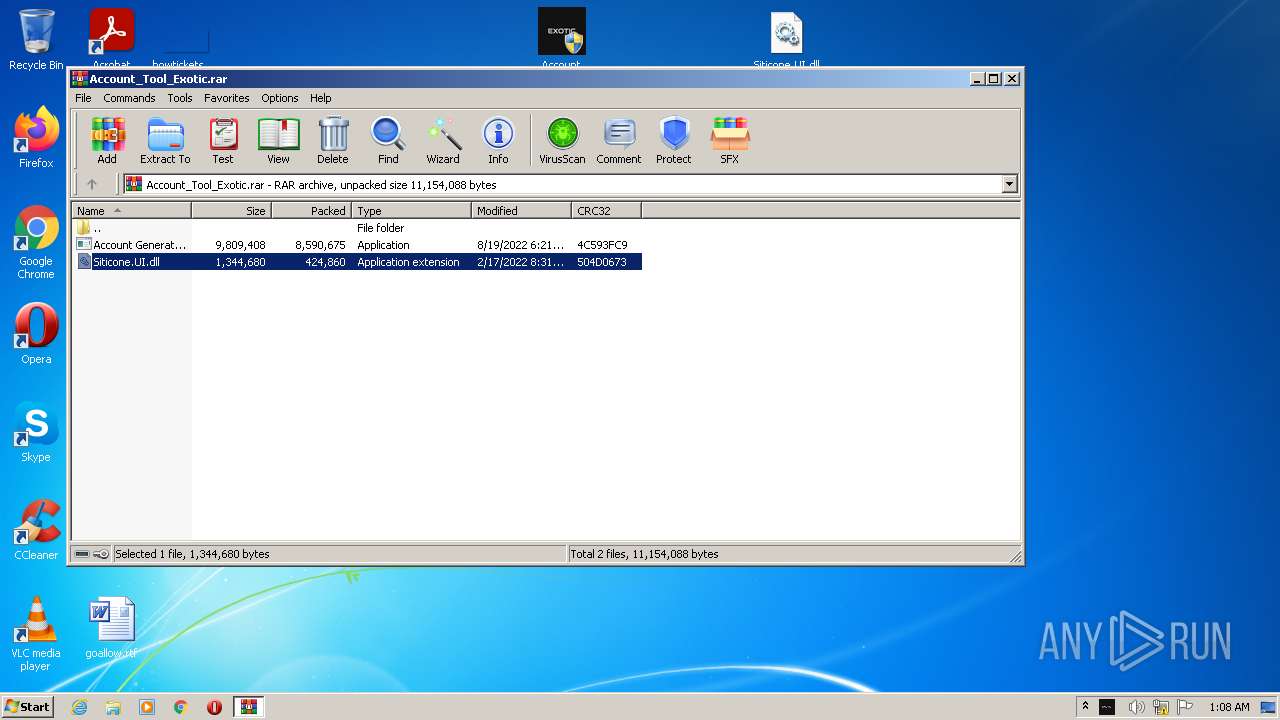
| 2552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2552.11569\Account Generator v8.1.2.exe | executable | |
MD5:— | SHA256:— | |||
| 2552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2552.11900\Siticone.UI.dll | executable | |
MD5:750C58AF2E56B6ADDECFFCF152520AB8 | SHA256:27C56A28CBDE094157206DA1BFCD7A395111AB97B8A5FF600B11C2175DCEFB26 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2364 | Account Generator v8.1.2.exe | 188.114.96.3:443 | keyauth.win | CLOUDFLARENET | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
keyauth.win |
| malicious |