| download: | getisti |
| Full analysis: | https://app.any.run/tasks/af79f44d-a23f-4d37-a351-57298302a3ca |
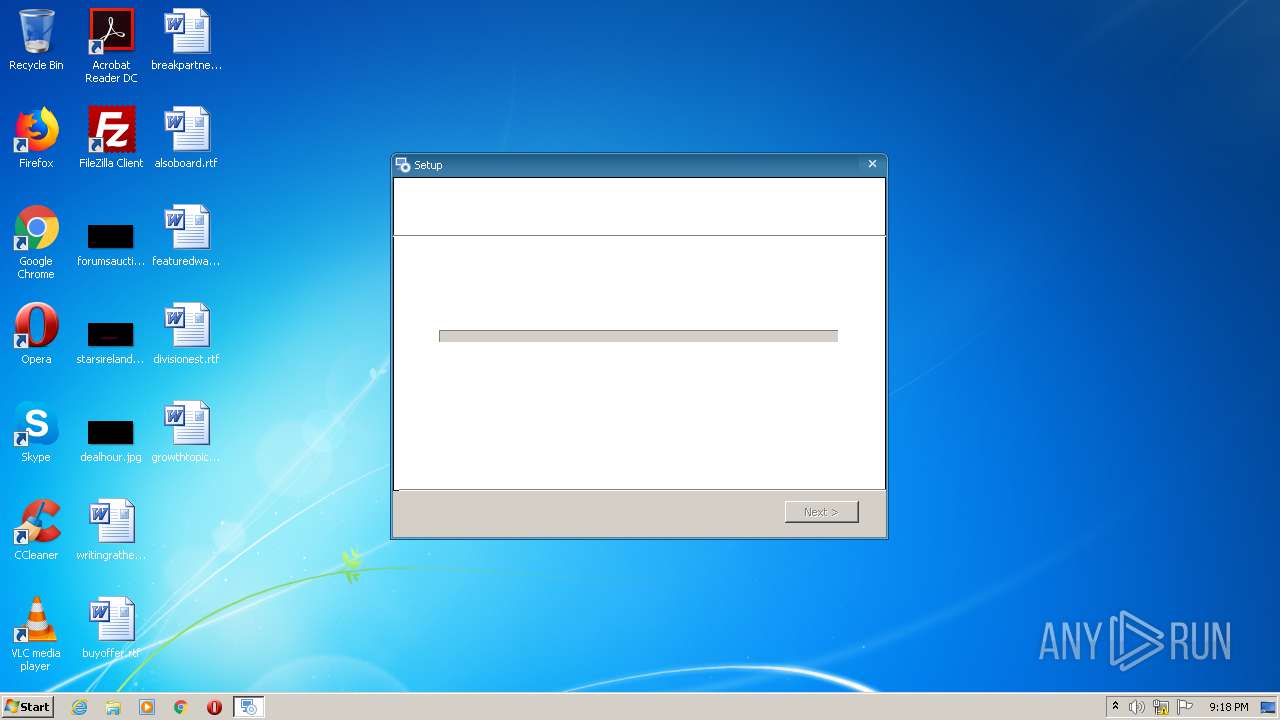
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2020, 21:17:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DC9EC4298F9EC8BF4EA539D9DD56B8EA |
| SHA1: | A3FA902012BAB0560B2FC31E61FF6AAB8A415002 |
| SHA256: | CFD98068EDCBF1EE1527C5368F49127C177087451B6B189126872D9DA3A16A3A |
| SSDEEP: | 393216:zUB/G3RgkFc+gfZsFUF6wt6Hu0GsbRC9gJJblX9yYiDN2sRD9Qan9bSPKsWTE:zUBOLc7A/HNDJ1lXAYyxRD9QaKD |
MALICIOUS
Loads dropped or rewritten executable
- getisti.exe (PID: 2696)
- BrowserAssistant.exe (PID: 2152)
Changes the autorun value in the registry
- getisti.exe (PID: 2696)
Loads the Task Scheduler DLL interface
- getisti.exe (PID: 2696)
Writes to a start menu file
- msiexec.exe (PID: 2816)
Application was dropped or rewritten from another process
- BrowserAssistant.exe (PID: 2152)
Actions looks like stealing of personal data
- BrowserAssistant.exe (PID: 2152)
SUSPICIOUS
Reads Internet Cache Settings
- MsiExec.exe (PID: 2292)
- getisti.exe (PID: 2696)
Executable content was dropped or overwritten
- getisti.exe (PID: 2696)
- msiexec.exe (PID: 2816)
Creates files in the user directory
- MsiExec.exe (PID: 2292)
- powershell.exe (PID: 1972)
- getisti.exe (PID: 1248)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 2992)
- powershell.exe (PID: 2964)
- powershell.exe (PID: 2856)
- powershell.exe (PID: 2884)
- powershell.exe (PID: 2456)
- msiexec.exe (PID: 2816)
Reads Environment values
- MsiExec.exe (PID: 2292)
- getisti.exe (PID: 2696)
- MsiExec.exe (PID: 1524)
Reads internet explorer settings
- getisti.exe (PID: 2696)
Executes PowerShell scripts
- MsiExec.exe (PID: 2292)
- MsiExec.exe (PID: 1524)
Creates files in the Windows directory
- getisti.exe (PID: 2696)
Removes files from Windows directory
- getisti.exe (PID: 2696)
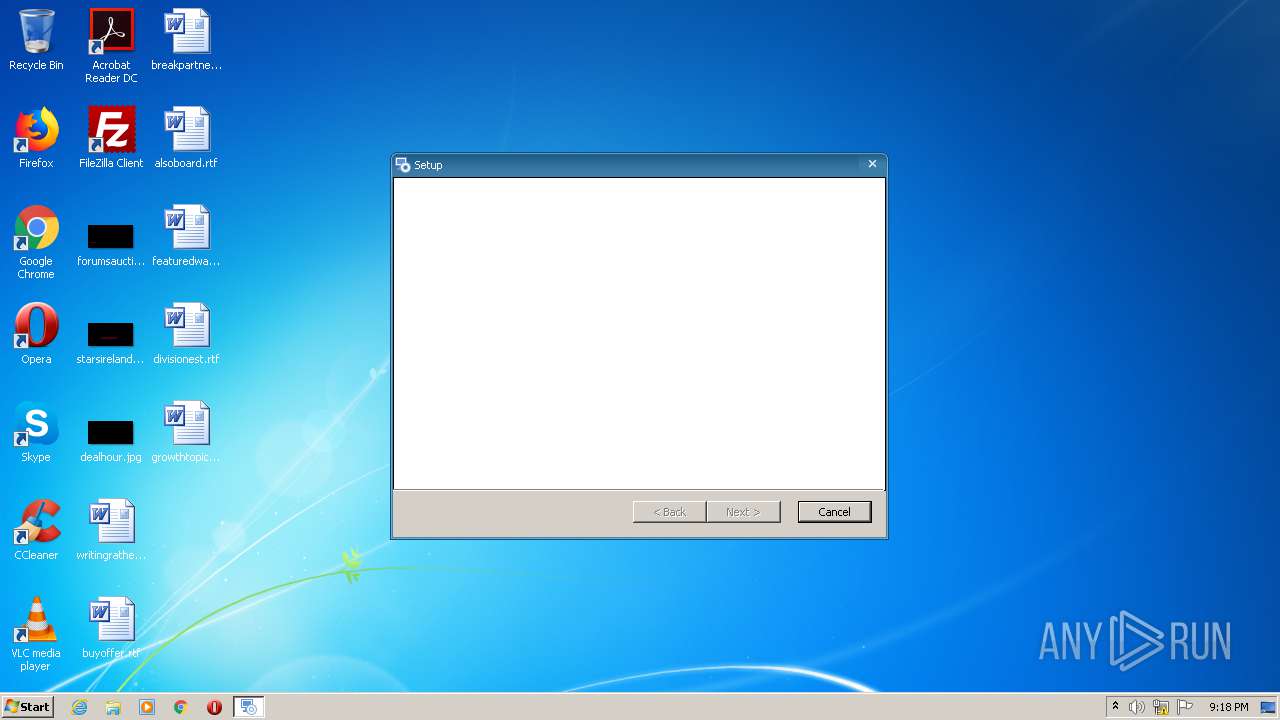
Starts Microsoft Installer
- getisti.exe (PID: 2696)
Changes the autorun value in the registry
- msiexec.exe (PID: 2816)
Uses TASKKILL.EXE to kill process
- powershell.exe (PID: 2964)
Executed as Windows Service
- vssvc.exe (PID: 3920)
Application launched itself
- getisti.exe (PID: 2696)
INFO
Application launched itself
- msiexec.exe (PID: 2816)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2292)
- MsiExec.exe (PID: 1524)
Dropped object may contain Bitcoin addresses
- getisti.exe (PID: 2696)
Searches for installed software
- msiexec.exe (PID: 2816)
Creates a software uninstall entry
- msiexec.exe (PID: 2816)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:13 13:11:03+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 1167360 |
| InitializedDataSize: | 528896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd670d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.38.0 |
| ProductVersionNumber: | 1.0.38.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
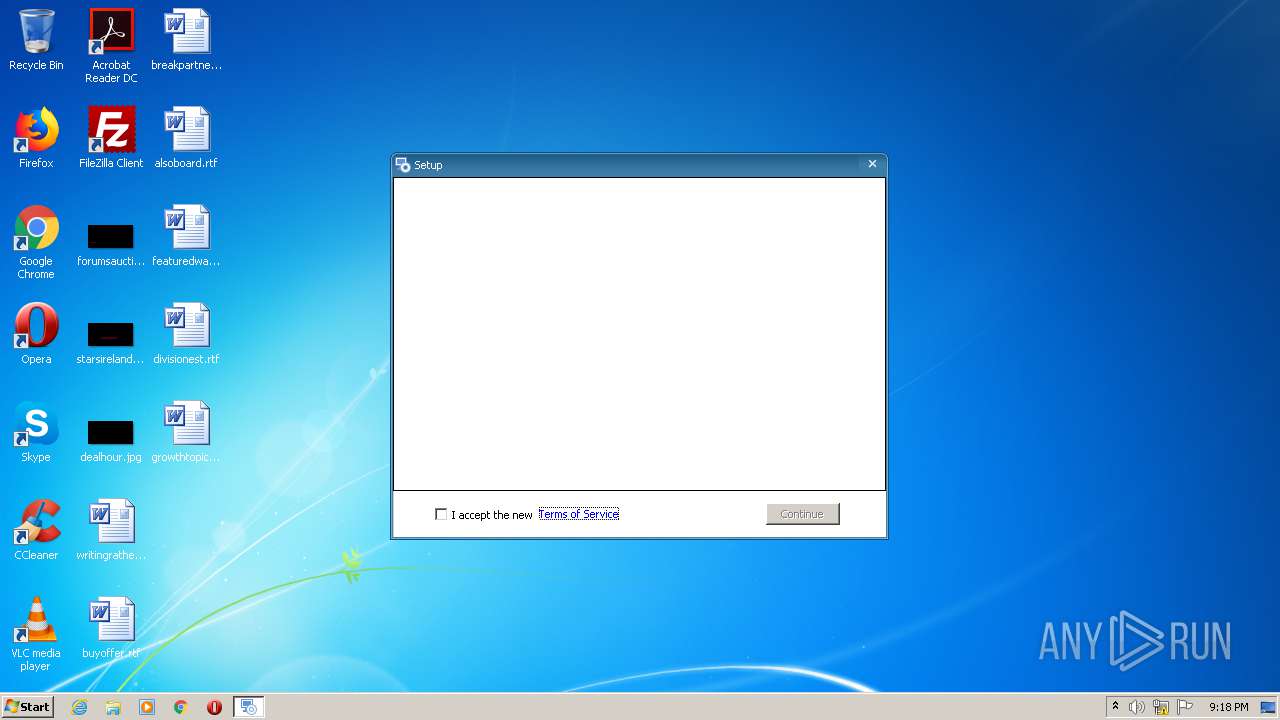
| CompanyName: | GamesLOL |
| FileDescription: | Direct Game UNI Installer Installer |
| FileVersion: | 1.0.38 |
| InternalName: | installerN |
| LegalCopyright: | Copyright (C) 2020 GamesLOL |
| OriginalFileName: | installerN.exe |
| ProductName: | Direct Game UNI Installer |
| ProductVersion: | 1.0.38 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Aug-2018 11:11:03 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | GamesLOL |
| FileDescription: | Direct Game UNI Installer Installer |
| FileVersion: | 1.0.38 |
| InternalName: | installerN |
| LegalCopyright: | Copyright (C) 2020 GamesLOL |
| OriginalFileName: | installerN.exe |
| ProductName: | Direct Game UNI Installer |
| ProductVersion: | 1.0.38 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Aug-2018 11:11:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0011CFDD | 0x0011D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64696 |
.rdata | 0x0011E000 | 0x000548C6 | 0x00054A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57287 |
.data | 0x00173000 | 0x000070A4 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.14879 |
.rsrc | 0x0017B000 | 0x000152F8 | 0x00015400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.35773 |
.reloc | 0x00191000 | 0x00014F08 | 0x00015000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58767 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.35766 | 820 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
62
Monitored processes
18
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Windows\system32\taskkill.exe" /F /IM BrowserAssistant.exe | C:\Windows\system32\taskkill.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Users\admin\AppData\Local\Temp\getisti.exe" /groupsextract:101; /out:"C:\Users\admin\AppData\Roaming\Direct Game UNI Installer" /callbackid:2292 | C:\Users\admin\AppData\Local\Temp\getisti.exe | — | MsiExec.exe | |||||||||||
User: admin Company: GamesLOL Integrity Level: MEDIUM Description: Direct Game UNI Installer Installer Exit code: 0 Version: 1.0.38 Modules
| |||||||||||||||
| 1524 | C:\Windows\system32\MsiExec.exe -Embedding A085635E223B059FC20391C10285A076 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1972 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss776D.ps1" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\AppData\Roaming\Browser Assistant\BrowserAssistant.exe" | C:\Users\admin\AppData\Roaming\Browser Assistant\BrowserAssistant.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BrowserAssistant Exit code: 0 Version: 1.38.1011.29570 Modules
| |||||||||||||||
| 2292 | C:\Windows\system32\MsiExec.exe -Embedding DFA50F86D93429A35EB2465F4EE99903 C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | C:\Users\admin\AppData\Local\Temp\getisti.exe /i "C:\Users\admin\AppData\Local\Temp\{59D63F6B-F39B-4FE6-997A-AB8FA3AC3A08}\Template - Flow6 - FHNID.msi" AI_EUIMSI=1 APPDIR="C:\Users\admin\AppData\Roaming\Direct Game UNI Installer" CLIENTPROCESSID="2696" SECONDSEQUENCE="1" CHAINERUIPROCESSID="2696Chainer" ACTION="INSTALL" EXECUTEACTION="INSTALL" CLIENTUILEVEL="0" ADDLOCAL="MainFeature,BrowserAssistant" CHECKBOX_1_PROP="Accept" PRIMARYFOLDER="APPDIR" ROOTDRIVE="C:\" AI_PREREQFILES="C:\Users\admin\AppData\Roaming\Direct Game UNI Installer\BAv1381011.msi" AI_PREREQDIRS="C:\Users\admin\AppData\Roaming" AI_MISSING_PREREQS="Browser Assistant" AI_FOUND_PREREQS=".NET Framework 4.5 (web installer)" AI_DETECTED_INTERNET_CONNECTION="1" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\getisti.exe" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\" EXE_CMD_LINE="/exenoupdates " BARETVAL="0" TARGETDIR="C:\" AI_INSTALL="1" AI_SETUPEXEPATH_ORIGINAL="C:\Users\admin\AppData\Local\Temp\getisti.exe" | C:\Users\admin\AppData\Local\Temp\getisti.exe | — | getisti.exe | |||||||||||
User: admin Company: GamesLOL Integrity Level: MEDIUM Description: Direct Game UNI Installer Installer Exit code: 0 Version: 1.0.38 Modules
| |||||||||||||||
| 2332 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss7B59.ps1" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssF786.ps1" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2568 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Direct Game UNI Installer\BAv1381011.msi" /q | C:\Windows\system32\msiexec.exe | — | getisti.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 116
Read events
3 022
Write events
1 082
Delete events
12
Modification events
| (PID) Process: | (2696) getisti.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2292) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2292) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2292) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2292) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2292) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2292) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2292) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2696) getisti.exe | Key: | HKEY_CURRENT_USER\AppEvents\Schemes\Apps\Explorer\Navigating\.Current |
| Operation: | write | Name: | (default) |
Value: | |||
| (PID) Process: | (2696) getisti.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
88
Suspicious files
33
Text files
2 067
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\MSI7325.tmp | — | |
MD5:— | SHA256:— | |||
| 2292 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\tin744D.tmp.part | — | |
MD5:— | SHA256:— | |||
| 2292 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\tin744D.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\{59D63F6B-F39B-4FE6-997A-AB8FA3AC3A08}\Template - Flow6 - FHNID.msi | executable | |
MD5:— | SHA256:— | |||
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\{59D63F6B-F39B-4FE6-997A-AB8FA3AC3A08}\Template - Flow6 - FHNID1.cab | compressed | |
MD5:— | SHA256:— | |||
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2696\frame_caption_inactive.bmp | image | |
MD5:3D8494DD57AE17B57726E6530FC60237 | SHA256:196BF30CC41139CCAECB41584FCDC4A61842C246F81A3C7C4A6BA2A5BEA4038C | |||
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2696\frame_right.bmp | image | |
MD5:2E805B0982CDA361E322E201DF8CCEFF | SHA256:C3F2A56930697C4DB1EA99BAD9F20D7B750F5795181A63EB608C57B7643EDD22 | |||
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2696\frame_bottom_right.bmp | image | |
MD5:C288357164D52B2CFD695C792074323B | SHA256:709D6FDBE00694F7DC115E923188F62CDC72D39E739280A1AFF072D1A49D2674 | |||
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2696\frame_bottom_mid_inactive.bmp | image | |
MD5:7610648B8E31404E1621A7A5B510B86D | SHA256:48837B62A6A6BC71359FF74BBE8A672D6B23CC30344C12E006698F069890A2B3 | |||
| 2696 | getisti.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2696\frame_bottom_left_inactive.bmp | image | |
MD5:1B38EF93DF0C5D4C6C2A10CA0115A28D | SHA256:4292EA3565B63946777D999352A1986E8F5950F1E8E51F030443F05DBDBDE57D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
19
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2152 | BrowserAssistant.exe | GET | 404 | 99.86.2.13:80 | http://pads289.net/ext/fhg?key= | US | — | — | shared |
2696 | getisti.exe | GET | 200 | 143.204.208.145:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAj820iN9FsHQT%2F6jENt64M%3D | US | der | 471 b | whitelisted |
2696 | getisti.exe | GET | 200 | 13.35.253.5:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2292 | MsiExec.exe | GET | 200 | 172.217.21.196:80 | http://www.google.com/ | US | html | 14.1 Kb | malicious |
2696 | getisti.exe | GET | 200 | 143.204.208.79:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2696 | getisti.exe | GET | 200 | 13.35.253.198:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2332 | powershell.exe | POST | 200 | 54.236.129.133:80 | http://logs-01.loggly.com/inputs/1f667d94-35d0-4958-aa21-54e5d3fd784d/tag/browser-assistant/ | US | text | 19 b | whitelisted |
2884 | powershell.exe | POST | 200 | 54.236.129.133:80 | http://logs-01.loggly.com/inputs/1f667d94-35d0-4958-aa21-54e5d3fd784d/tag/browser-assistant/ | US | text | 19 b | whitelisted |
2456 | powershell.exe | POST | 200 | 54.236.129.133:80 | http://logs-01.loggly.com/inputs/1f667d94-35d0-4958-aa21-54e5d3fd784d/tag/browser-assistant/ | US | text | 19 b | whitelisted |
2152 | BrowserAssistant.exe | POST | 200 | 54.236.129.133:80 | http://logs-01.loggly.com/inputs/1f667d94-35d0-4958-aa21-54e5d3fd784d/tag/browser-assistant/ | US | text | 19 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2292 | MsiExec.exe | 172.217.21.196:80 | www.google.com | Google Inc. | US | whitelisted |
2696 | getisti.exe | 99.86.2.13:443 | pads289.net | AT&T Services, Inc. | US | suspicious |
2696 | getisti.exe | 143.204.208.79:80 | o.ss2.us | — | US | whitelisted |
2696 | getisti.exe | 13.35.253.5:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2696 | getisti.exe | 13.35.253.198:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2332 | powershell.exe | 54.236.129.133:80 | logs-01.loggly.com | Amazon.com, Inc. | US | unknown |
2456 | powershell.exe | 54.236.129.133:80 | logs-01.loggly.com | Amazon.com, Inc. | US | unknown |
2152 | BrowserAssistant.exe | 54.236.129.133:80 | logs-01.loggly.com | Amazon.com, Inc. | US | unknown |
2884 | powershell.exe | 54.236.129.133:80 | logs-01.loggly.com | Amazon.com, Inc. | US | unknown |
2152 | BrowserAssistant.exe | 99.86.2.13:80 | pads289.net | AT&T Services, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
pads289.net |
| shared |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
logs-01.loggly.com |
| whitelisted |
ocsp.sca1b.amazontrust.com |
| whitelisted |
crl.rootg2.amazontrust.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report